Phishing Analysis
Detailed analysis of captured phishing page
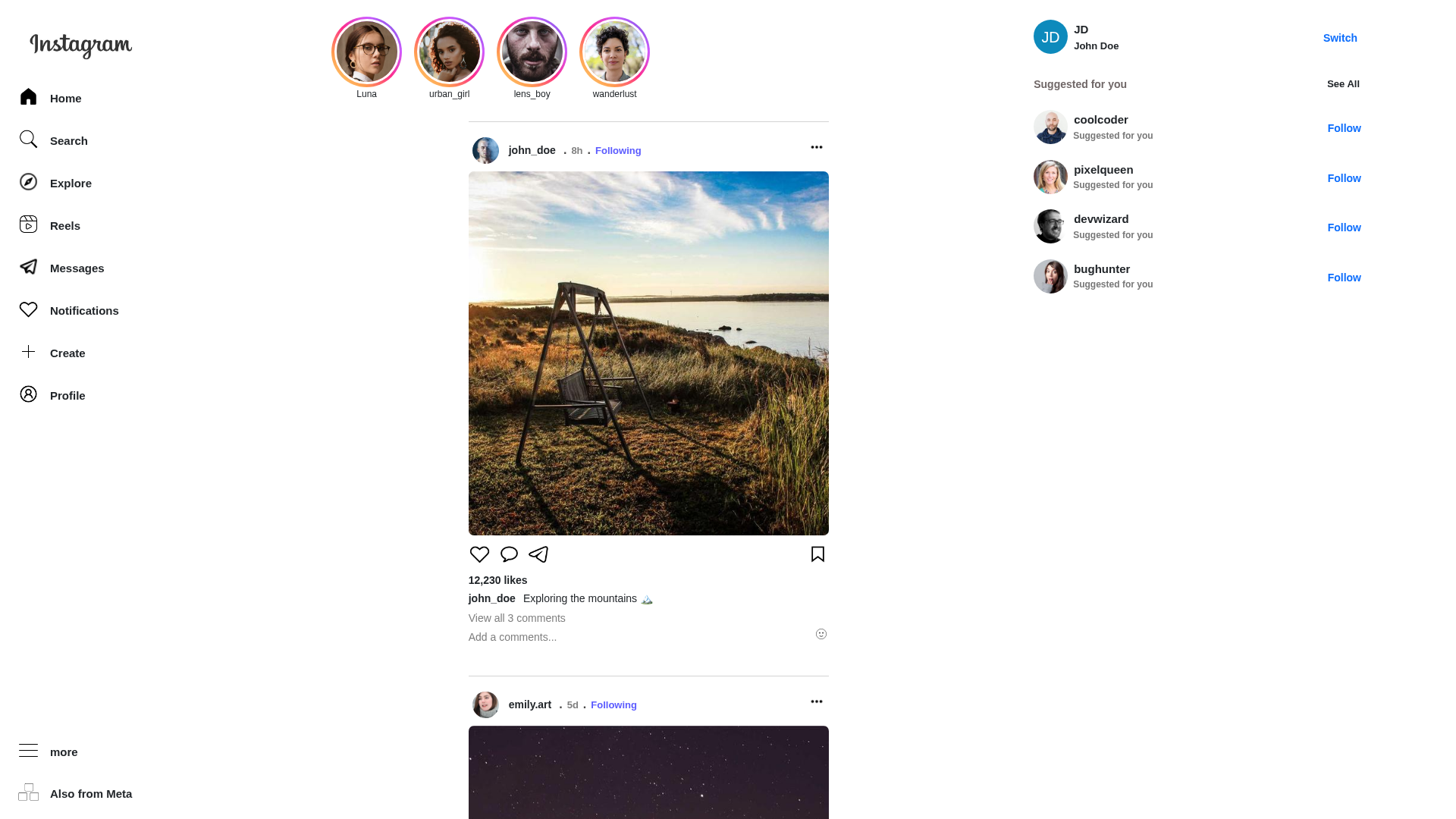
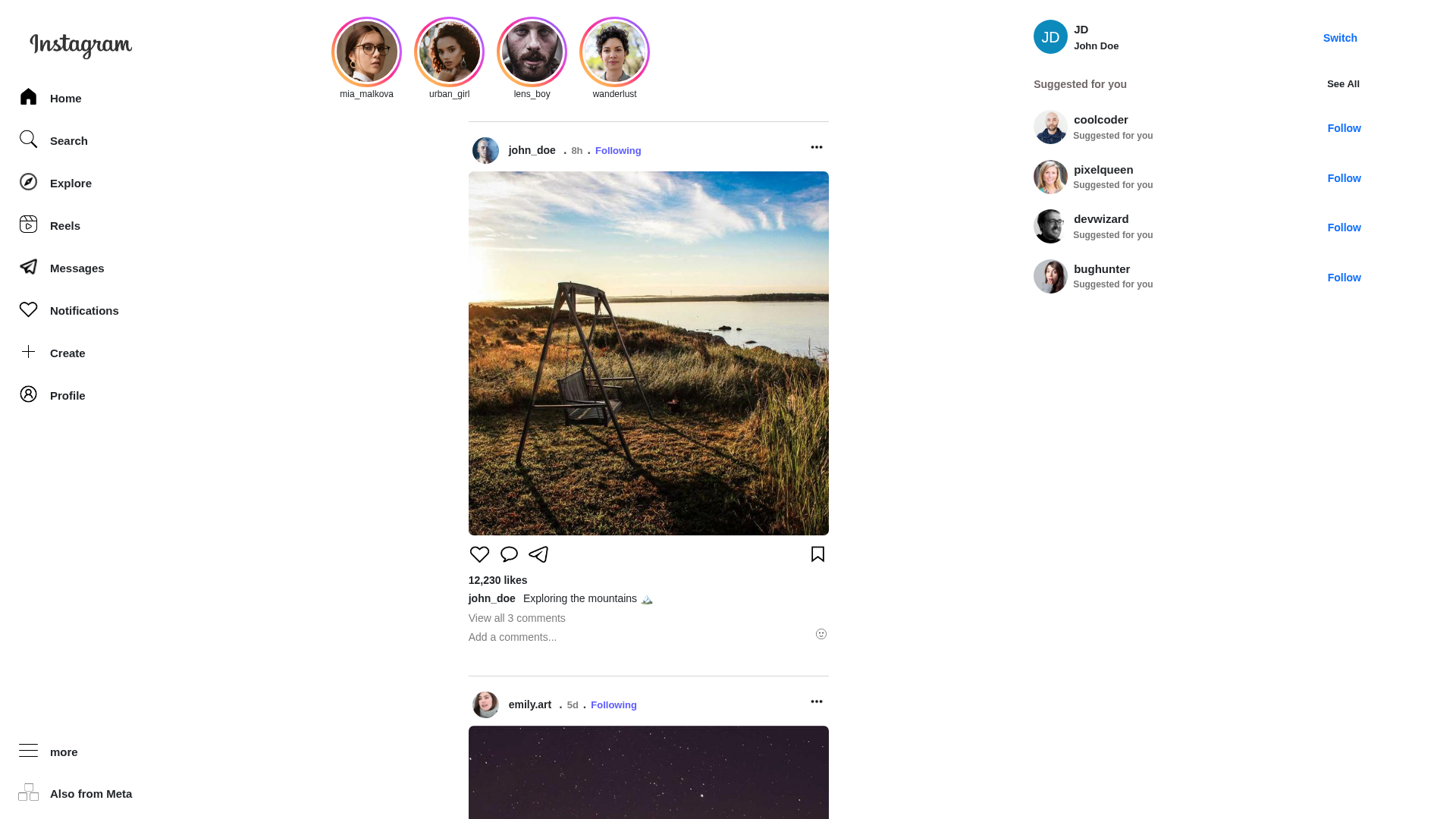
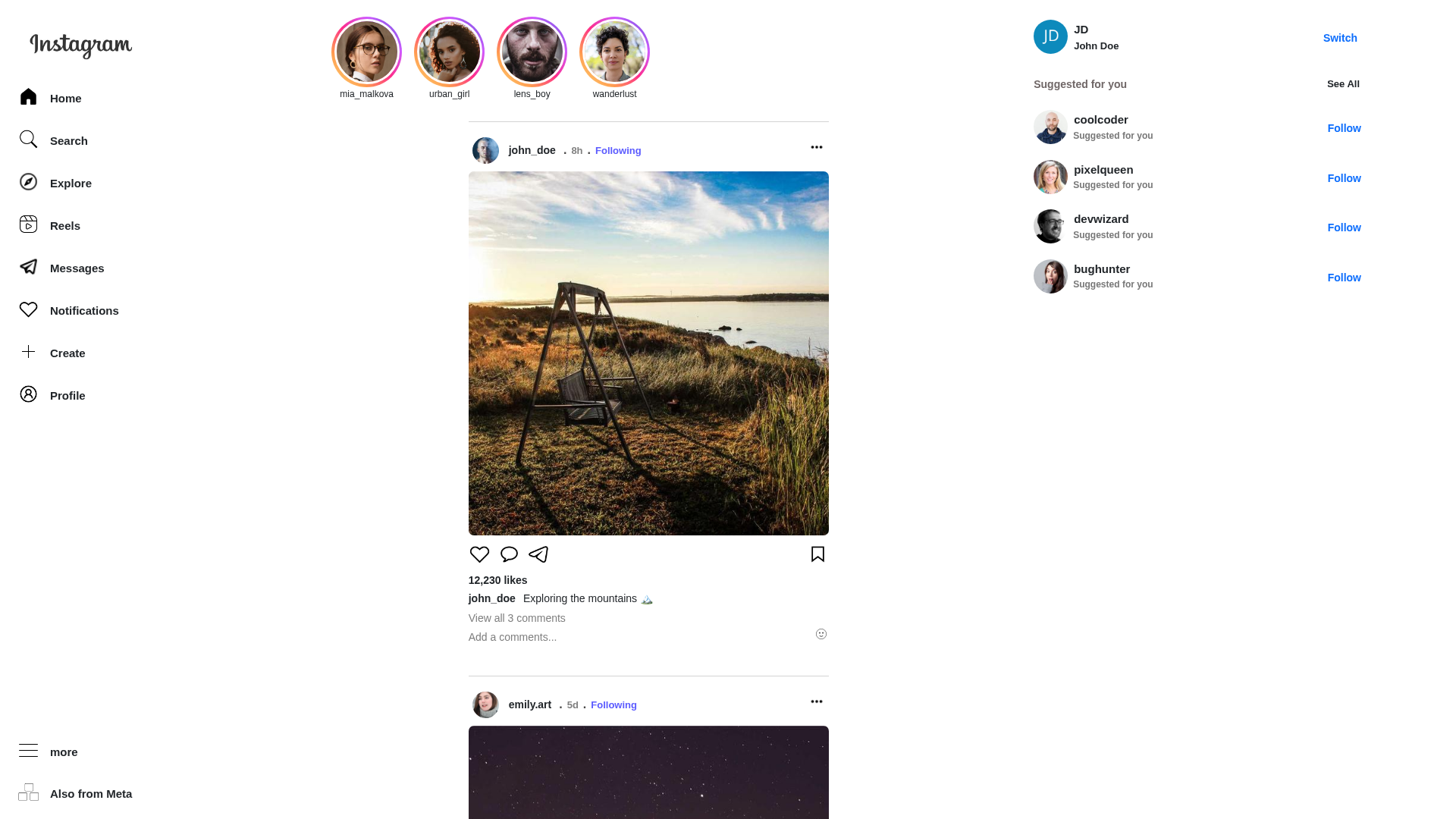
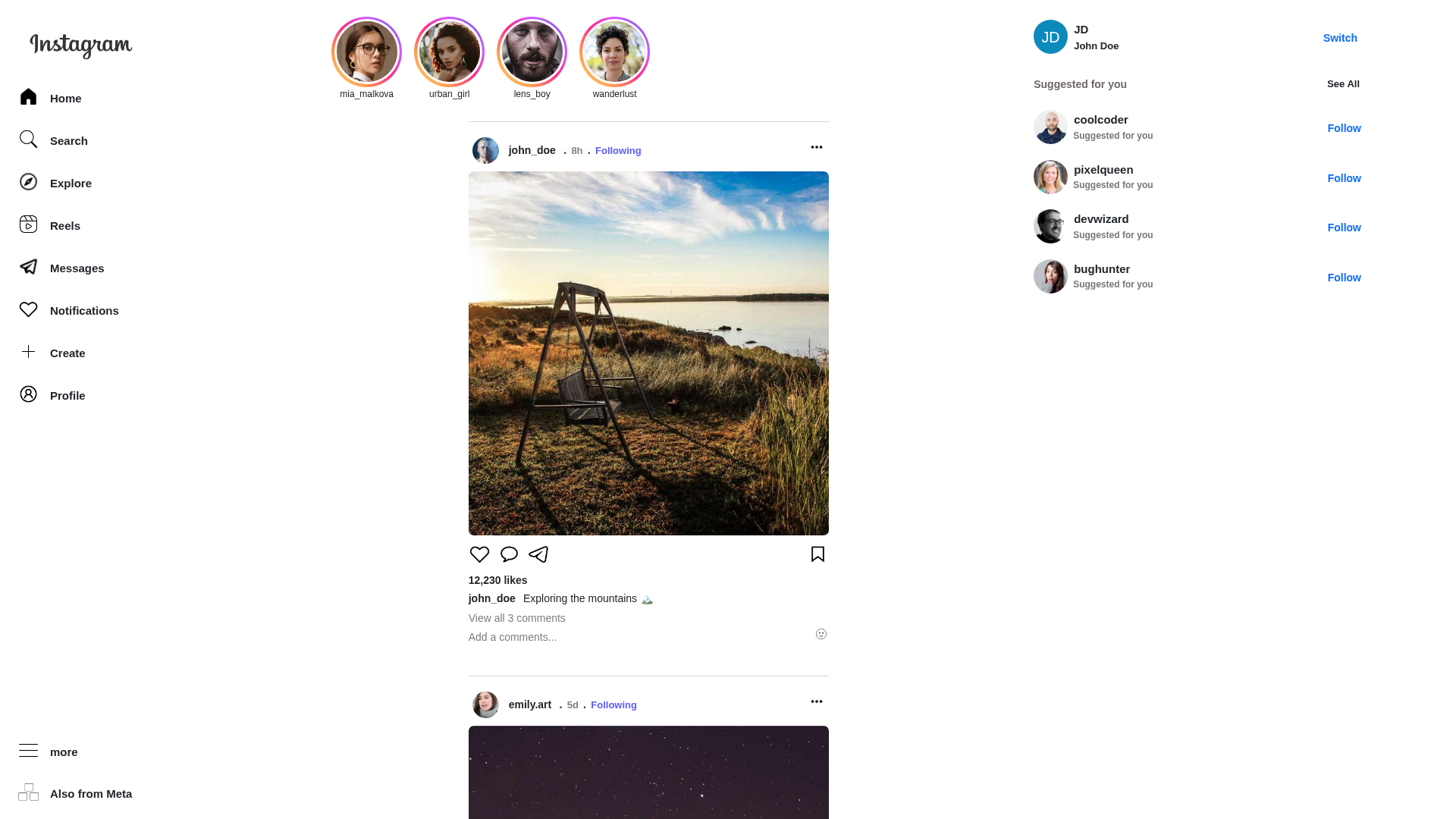
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D752F679C2E690371127C8C3A9352BBD70F293BDD8321816B2FC93990BD9D85BD42E59 |
|
CONTENT
ssdeep
|
384:1JWMAO0LdHg0LRVA0LHdI0LTCE0LRAo0L0xb0L/B10Lu/w0LHx10l3VA:1J1AOMHg2VAKdI8CE8AotxboB11/wexX |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3cccc8c33cc3966 |
|
VISUAL
aHash
|
cfffe7c7c7e7ffc7 |
|
VISUAL
dHash
|
b28b8b9d8d1d108d |
|
VISUAL
wHash
|
0b414147c7c7df47 |
|
VISUAL
colorHash
|
07c00208000 |
|
VISUAL
cropResistant
|
b28b8b9d8d1d108d,385f8923571a4763,a0a0a000501008c0 |
Análisis de Código
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- log.php?cmd=_update_information&account_wall
📡 API Calls Detected
- /data/stories.json
- ./data/posts.json
- ./data/suggestionUsers.json
- ./data/profile.json
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The phishing kit presents a fake Instagram login page to capture user credentials. Submitted credentials are likely transmitted to an attacker-controlled server via HTTP POST requests or similar methods.
Secondary Method: Social Engineering
While no specific urgency, fear, or reward tactics were detected in the extracted text, the impersonation of Instagram's branding and interface is designed to deceive users into voluntarily submitting their credentials.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🦠 Malicious Files
No specific malicious JavaScript files detected, but obfuscation techniques are present.
📊 Diagrama de Flujo de Ataque
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Fake Instagram notification/link │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM VISITS FAKE LOGIN PAGE │
│ - Spoofed Instagram login interface │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL SUBMISSION │
│ - Victim enters username/password │
│ - Form appears to process login │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. CREDENTIAL EXFILTRATION │
│ - Data sent via HTTP POST to attacker server │
└──────────────────────────────────────────────────────────┘
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Fake Instagram notification/link │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM VISITS FAKE LOGIN PAGE │
│ - Spoofed Instagram login interface │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL SUBMISSION │
│ - Victim enters username/password │
│ - Form appears to process login │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. CREDENTIAL EXFILTRATION │
│ - Data sent via HTTP POST to attacker server │
└──────────────────────────────────────────────────────────┘
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.instagram-clone-mu.vercel.app
Found 1 other scan for this domain