
Phishing Analysis
Detailed analysis of captured phishing page
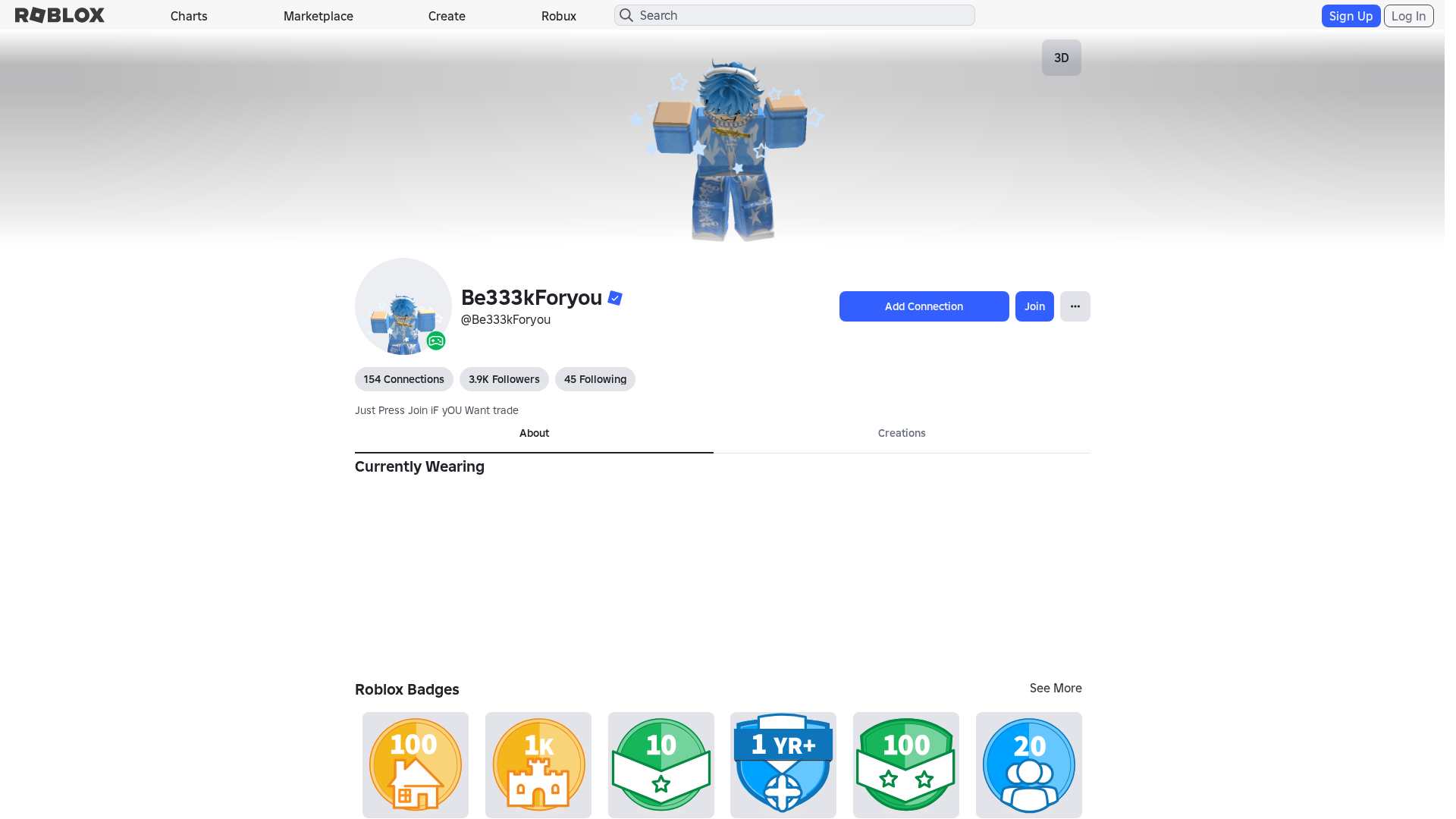
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1AB93B9B29251243320BFB1D5F1297709A2D3D74EC68287E1E2FC636B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:YPpXWnSraLquOVJor8BPmzzXXMd6MiucCOK:8pXWdLquO+kmzzXXMd6M1cCOK |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e41267933c9ced91 |
|
VISUAL
aHash
|
0000f3dbffffffc3 |
|
VISUAL
dHash
|
e8e8a63638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
07002000080 |
|
VISUAL
cropResistant
|
e8e8a63638002606 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Sitio de phishing de Roblox diseñado para robar credenciales de cuenta.
• Objetivo: Usuarios de Roblox, probablemente en España o países de habla hispana.
• Método: Se utiliza una página de inicio de sesión falsa de Roblox para recopilar nombres de usuario y contraseñas.
• Exfil: Desconocido, pero probablemente exfiltra credenciales a través de una API personalizada o a un servidor comprometido.
• Indicadores: El dominio no coincide con el sitio web oficial de Roblox, Javascript ofuscado, acciones de formulario presentes, detección de envío de formulario Javascript, TLD de código de país.
• Riesgo: ALTO - Las credenciales robadas pueden conducir al compromiso de la cuenta, la pérdida de artículos virtuales y un posible fraude financiero.
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /catalog
- https://www.roblox.com/info/blog?locale=en_us
- /login?returlUrl=2069911119
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- /login?returnUrl=
📡 API Calls Detected
- GET
- https://apis.
- POST
- get
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 825 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The phishing kit is designed to capture Roblox account credentials by presenting a fake login form. Submitted credentials are likely exfiltrated in real-time to an attacker-controlled server for immediate account takeover and further exploitation.
Secondary Method: OTP and Payment Data Theft
The kit includes modules for intercepting one-time passwords (OTPs) and stealing payment card details. Users may be prompted to enter OTPs or card information under the guise of account verification or premium service upgrades.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🦠 Malicious Files
Large obfuscated JavaScript file containing credential harvesting and data exfiltration logic.
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : None
- : Heavy
- : Light
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Scan History for robloxc.com.es
Found 10 other scans for this domain
-
https://www.robloxc.com.es/users/7048358411/profil...
https://robloxc.com.es/users/241551989/profile
https://robloxc.com.es/users/1539346212/profile
https://www.robloxc.com.es/discovers/?Keyword=
https://robloxc.com.es/users/1958949928/profile
https://robloxc.com.es/users/316088579/profile
https://robloxc.com.es/users/518931499/profile
https://robloxc.com.es/charts
https://robloxc.com.es/users/704835841/profile/
https://robloxc.com.es/users/2123049659/profile
