Phishing Analysis
Detailed analysis of captured phishing page
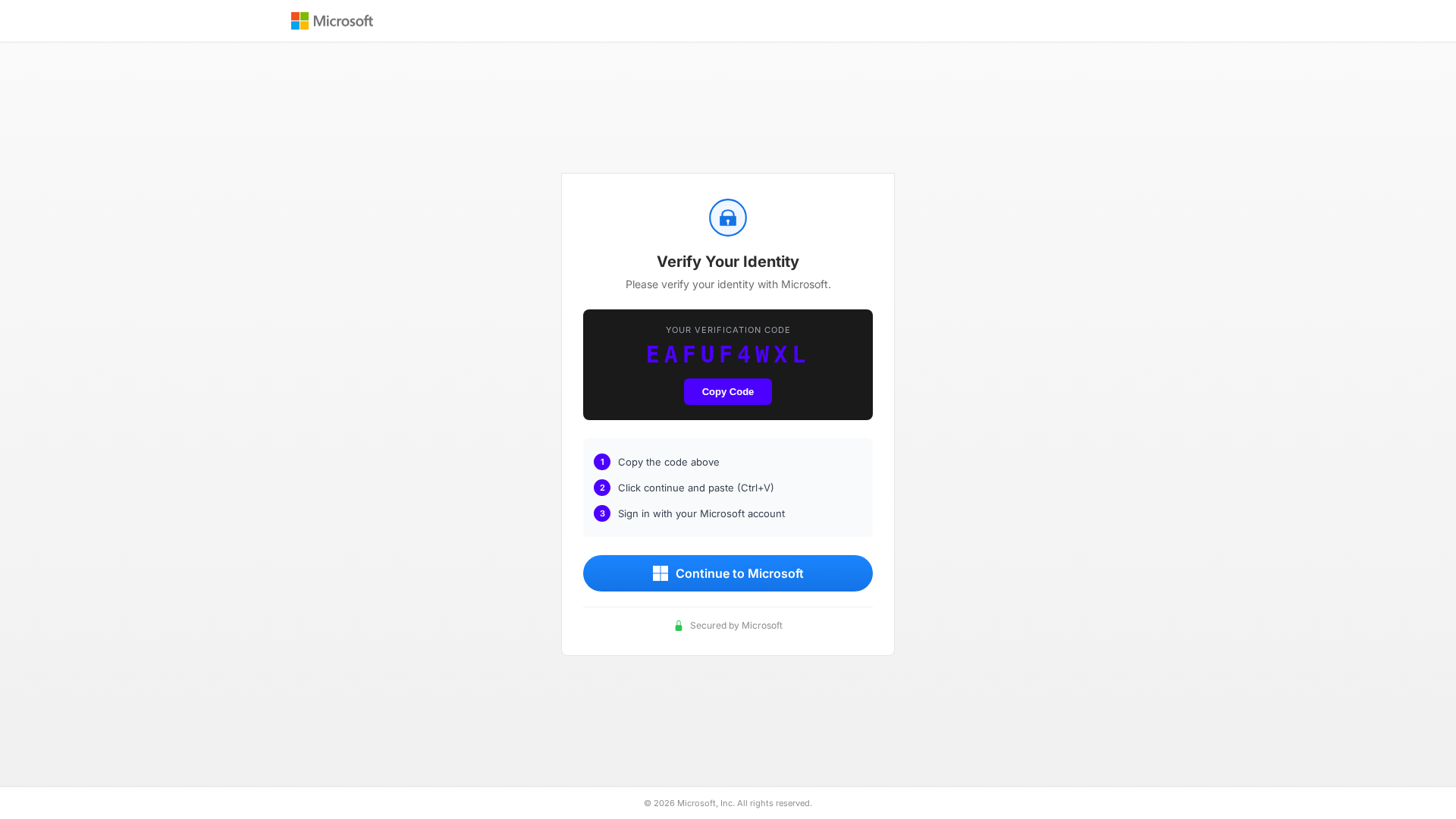
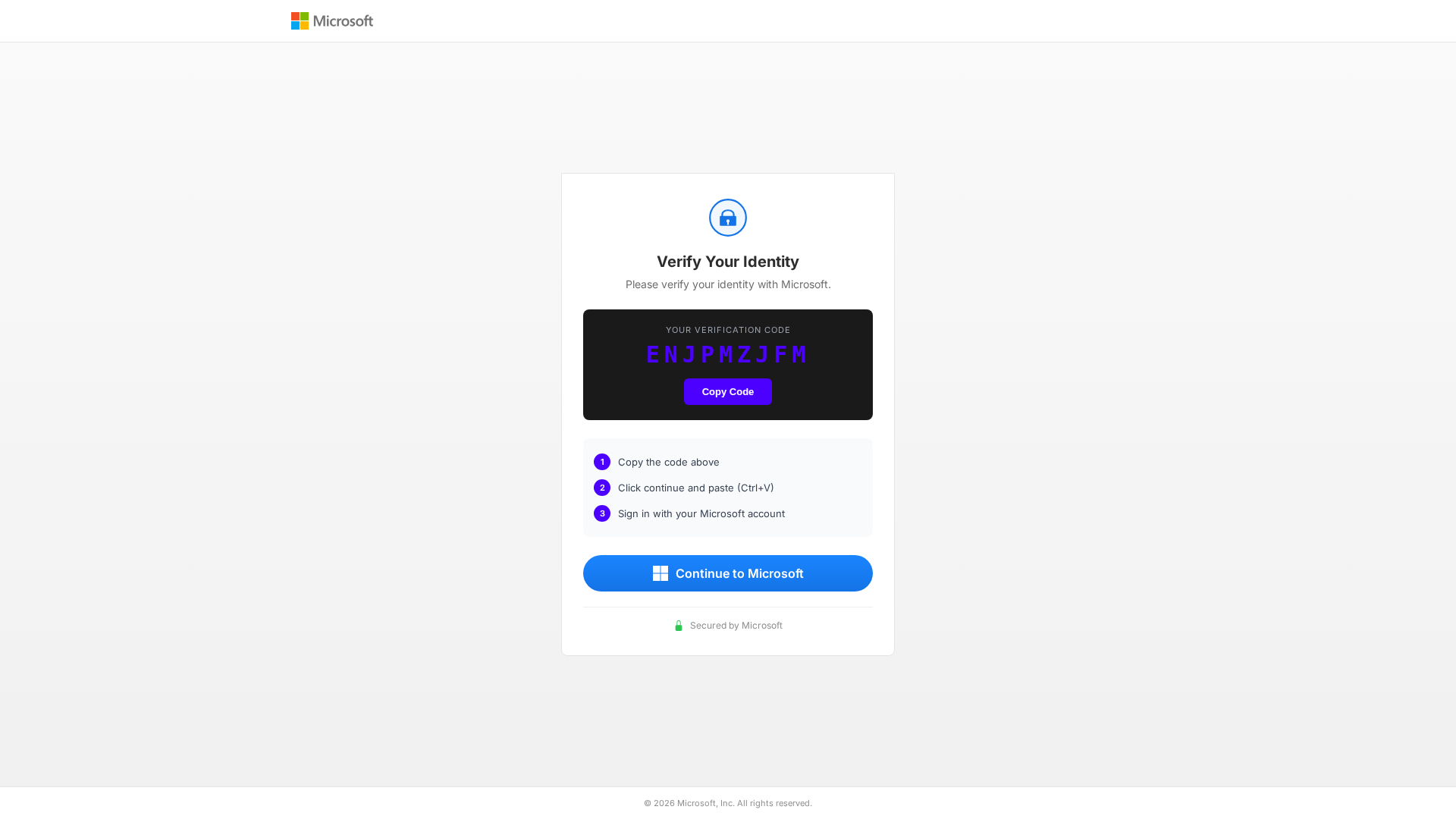
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T125E1843653188AEE95CD938C5B293B9A336592C4B27703406B974264EC49EBBFC37950 |
|
CONTENT
ssdeep
|
96:T6jNt2NvO4DZ+Stb/jY+eo4hAryAes9mBYYQgWLDmy43oggGFljzOIDi3auPq+:y2pToSBjlevudl9nN44PoVD+6+ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3a68c9933269d99 |
|
VISUAL
aHash
|
ffffe7e7e7e7ffff |
|
VISUAL
dHash
|
24320c4d4c4c2801 |
|
VISUAL
wHash
|
ffffffe700001800 |
|
VISUAL
colorHash
|
070000001d0 |
|
VISUAL
cropResistant
|
24320c4d4c4c2801,616955554933334d |
Análisis de Código
📡 API Calls Detected
- https://microsoft.com/devicelogin
📊 Desglose de Puntuación de Riesgo
🔬 Análisis Integral de Amenazas
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: SEO Poisoning Landing Page
Fake Microsoft page designed to appear in search results and trick users into visiting. May redirect to credential harvesting pages, malware downloads, or serve as a trust-building step before requesting sensitive information.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for secure-device-auth-office-com.dporozok.workers.dev
Found 1 other scan for this domain