
Phishing Analysis
Detailed analysis of captured phishing page
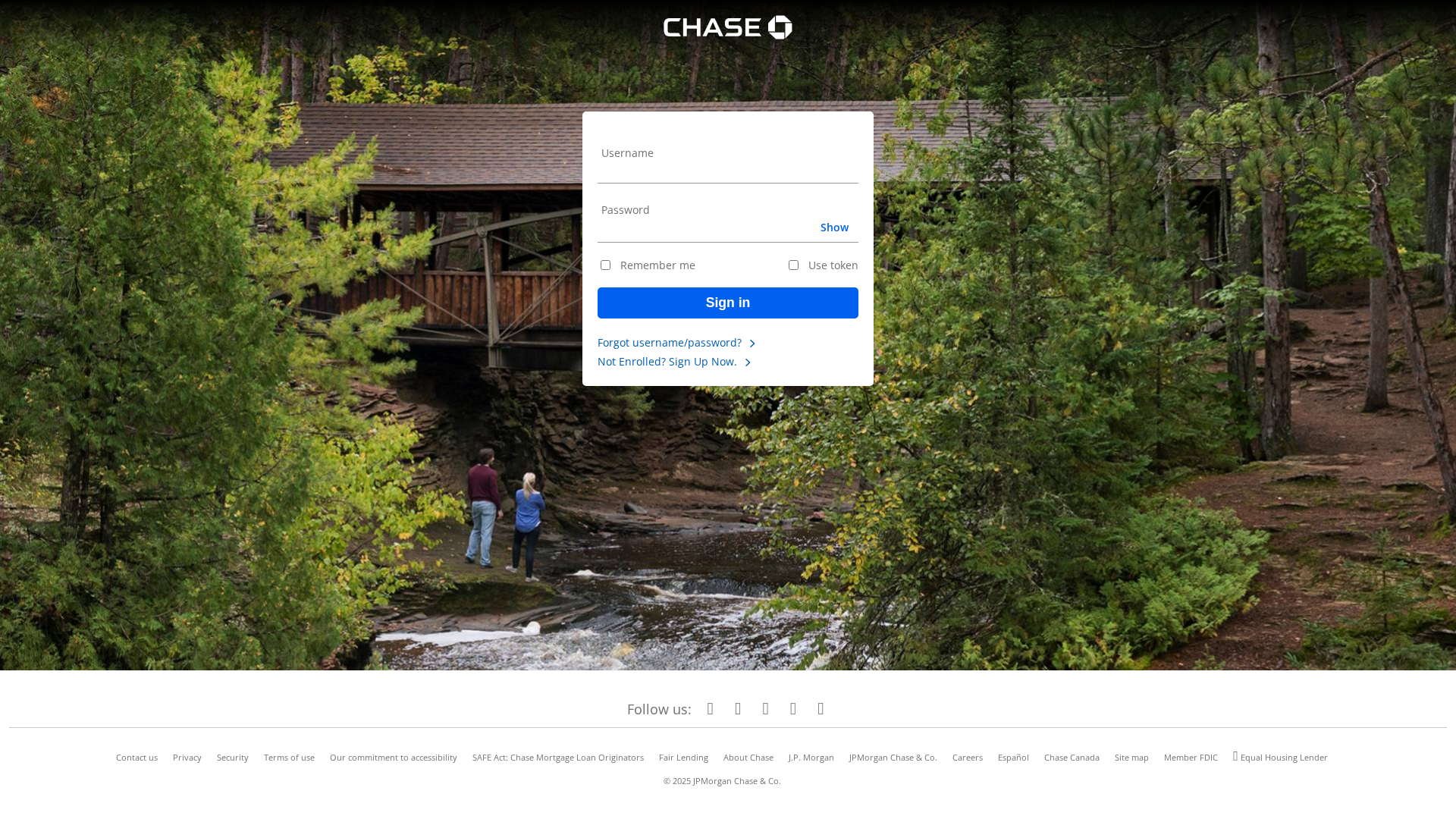
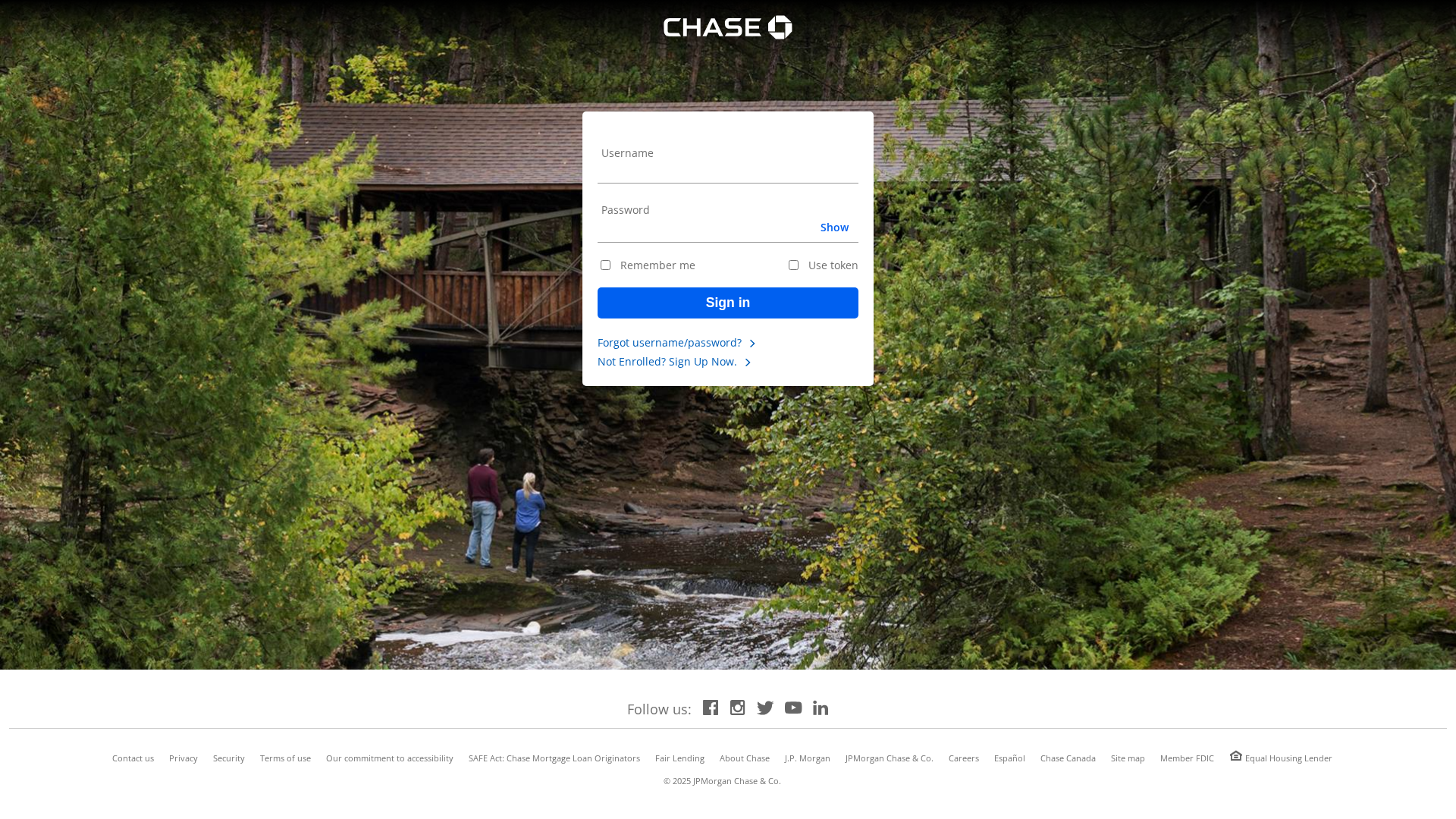
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1626112F14584A42901A282D18E32E369D386D574DF730B079AE5E75EBBDBFD8CC05079 |
|
CONTENT
ssdeep
|
48:TXjLFTNmTNMitOKsanfI6SfnCw02hse5SnCw02hsesdQ5YpP5hvopBliFOo6wXmb:TTLG4KVZS6l3ONl3/2Ex0ZN |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c958e663b30e35e2 |
|
VISUAL
aHash
|
001818180000ffff |
|
VISUAL
dHash
|
91b2b0b0dbd2e200 |
|
VISUAL
wHash
|
007c5c584848ffff |
|
VISUAL
colorHash
|
0b580001000 |
|
VISUAL
cropResistant
|
d4e0d4d0d0d6dcdc,e0e1000800150800,1db2b1b0b1dbd2f2 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- https://api.telegram.org/bot8169444691:AAHcxqlXwOXM8LzVaVFJy8etwpaqZ0nk7sc/sendMessage?chat_id=1418778003&text=New visit%0AIP:undefined
📤 Form Action Targets
- post.php
🔑 Telegram Bot Tokens (2)
- 8169444691:AAHc...qZ0nk7sc
- 8775874274:AAFJ...6m1DDWEY
💬 Telegram Chat IDs (1)
- 1418778003
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- 2 Telegram bot token(s)
- Kit types: Credential Harvester
- 28 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 28 techniques to evade detection by security scanners and make reverse engineering more difficult.
📡 Infraestructura de Comando y Control Telegram
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.embassycoffee.org
Found 1 other scan for this domain
