Phishing Analysis
Detailed analysis of captured phishing page
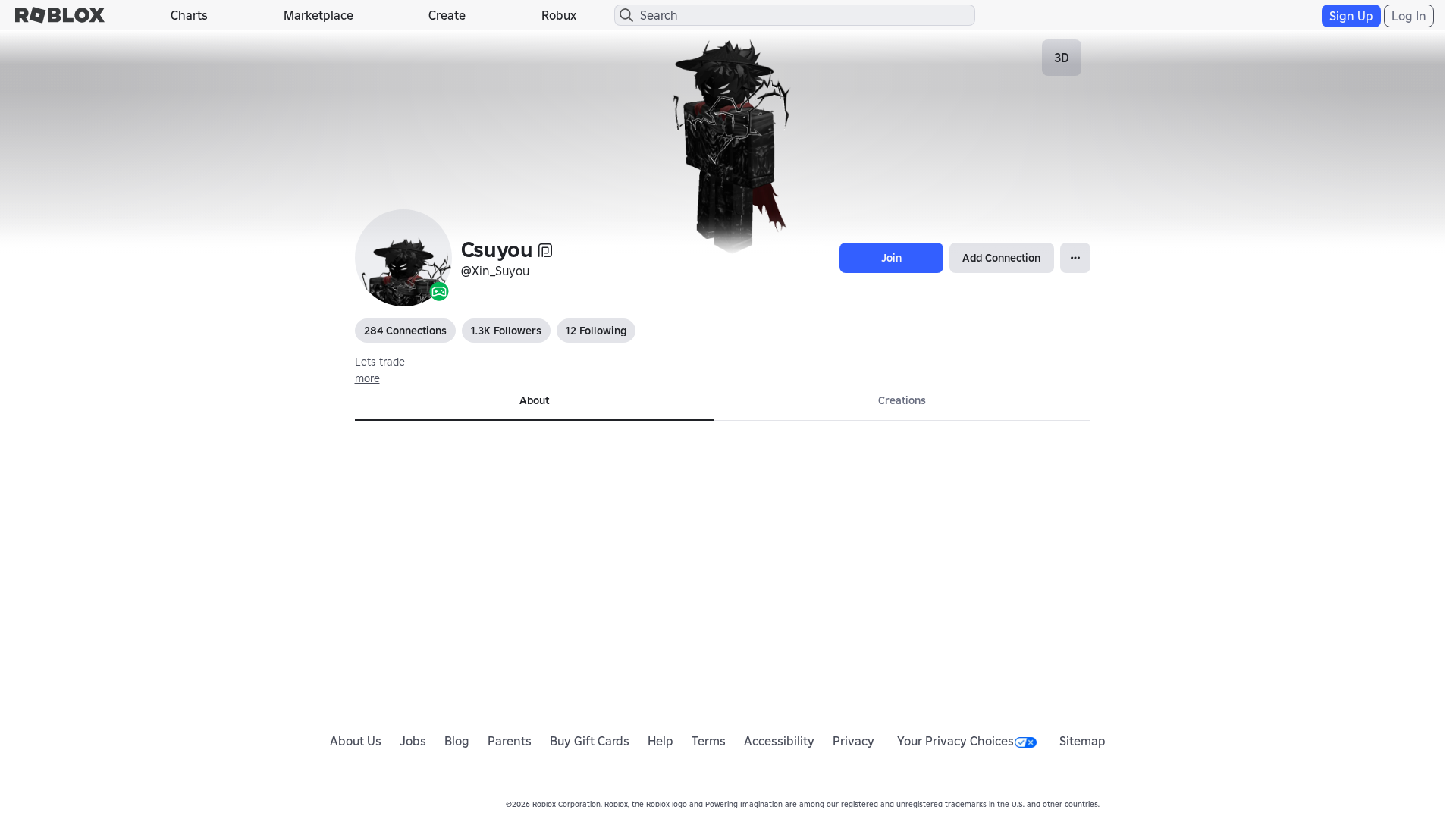
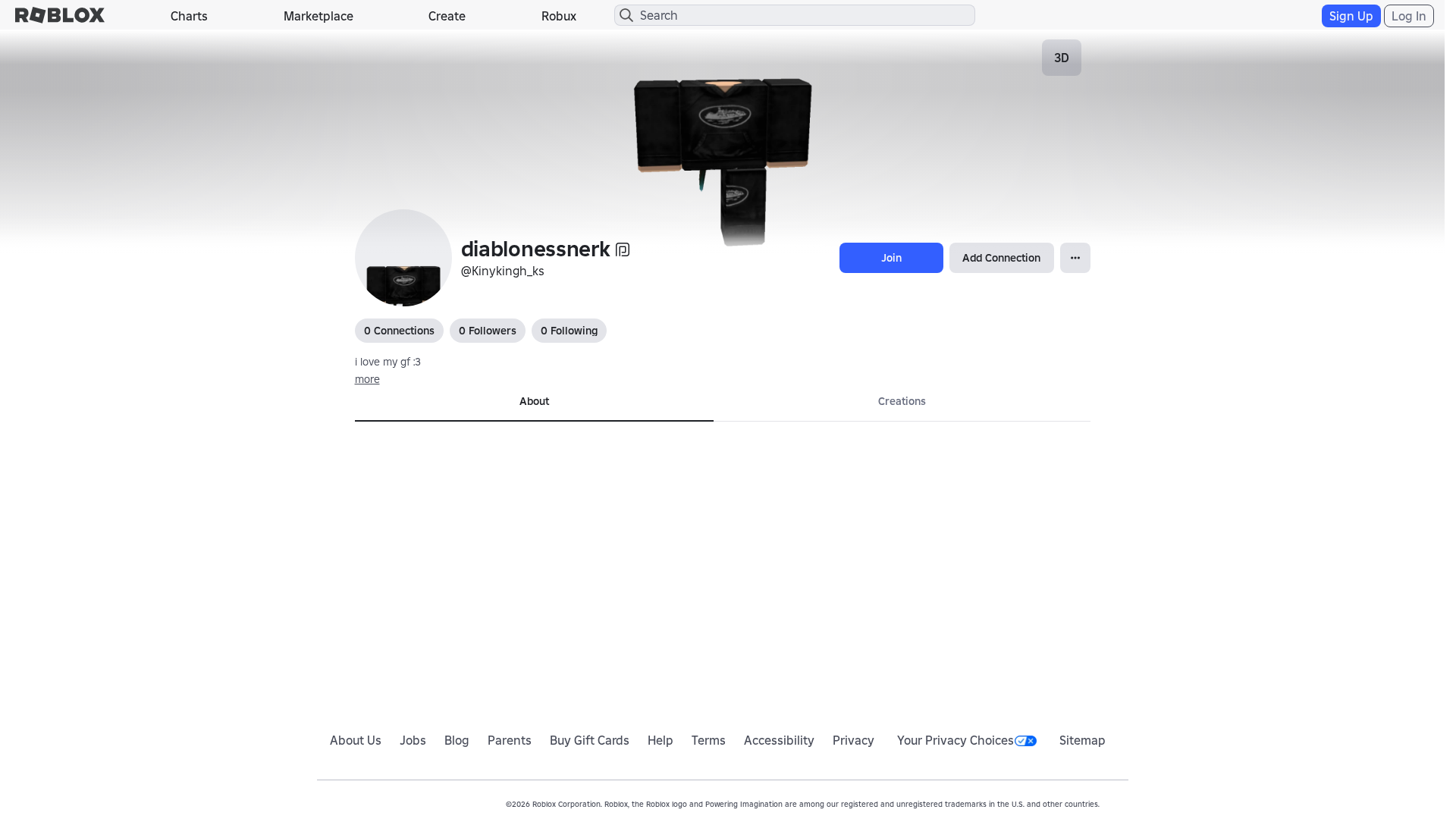
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BA43E9B2E1202837517FB6D6F469B30691D3D70ECA8657E2A1F863660EDACA1FC17407 |
|
CONTENT
ssdeep
|
768:09KXWnhrqRQXkCl2WUj4MYuO5BeVP2tT2jWZ2pz2OH2Az22P2tT2jqZ2rLXpmY8J:09KXWnhrTXjUj4MYuOzexLpt8mg |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b6366343999c9ccc |
|
VISUAL
aHash
|
0000d3dfffffffff |
|
VISUAL
dHash
|
cccd36340c000206 |
|
VISUAL
wHash
|
000000cfcfffffc3 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
cccd36340c000206,7171311907862626 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Impersonación/Phishing
• Objetivo: Usuarios de Roblox
• Método: Suplantación de dominio y mimicry de la interfaz de usuario.
• Exfil: Potencialmente datos de formulario (credenciales), basado en análisis de Javascript.
• Indicadores: Coincidencia de dominio, ofuscación de Javascript, mimicry de la interfaz de usuario.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://trades.
- https://en.help.roblox.com/hc/
- https://js.rbxcdn.com/dd0d34c6d7afd472e5636ca7645e703dd18502fc01c8211279879f64c847dee4.js?v=1932220416
- https://search.
- https://voice.
- /catalog
- https://feross.org
- https://httpx-www-roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.
- https://js.rbxcdn.com/2f0fd0c2760ff1898187af6df3b764f4b08f77a315d0a33654f105f61b0ea6d0.js?v=193418460
- https://itemconfiguration.
- https://inventory.
- https://tarobi-dev-test.com
- https://engagementpayouts.
- https://js.rbxcdn.com/462e800b726c0831ac8fd9372e042ae1d3cfa579b201a3648e7bf59f443ad5e1-TranslationResources.js?v=309050876
- https://feross.org/opensource
- https://followings.
- https://chat.
- https://sourcemaps.rbxcdn.com/internationalCore-db1cf6cdaa102b16.js.map
- https://тест
- https://js.rbxcdn.com/098e80c8e9f4dad5295663f4a79f9a64.js
- https://accountsettings.
- https://js.rbxcdn.com/a3fe79f1bfdd96b7f0ad20eab2de7a05.js
- https://a
- https://app.lightstep.com
- https://a/c%20d?a=1&c=3
- https://mui.com/production-error/?code=
- https://js.rbxcdn.com/1d87d1231072878a0f6164e84b8cfa6f90a1b31b18ba5d8f410b947d4b029fe8.js?v=1976850794
- https://premiumfeatures.
- https://www.rblx.org
- https://js.rbxcdn.com/964fdc5ae2518a2c9c9d73f67eee026b844e68c2d3791ac6c8e28c0f979a3854.js?v=1159767586
- http://getbootstrap.com)
- https://httpx-www-roblox.com/info/blog?locale=en_us
📡 API Calls Detected
- get
- GET
- https://help.roblox.com/hc/articles/30428367965460
- POST
- https://apis.
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 255 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site likely attempts to steal login credentials through a fake login form or social engineering techniques, using the look and feel of Roblox's website to deceive users.
Secondary Method: Malware Injection
The obfuscated Javascript may be designed to deliver a malicious payload, or perform other malicious activity, such as keylogging or information exfiltration.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Heavy
- : Light
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
EnvironmentUrls.js?v=293815115Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for httpx-www-roblox.com
Found 2 other scans for this domain