
Phishing Analysis
Detailed analysis of captured phishing page
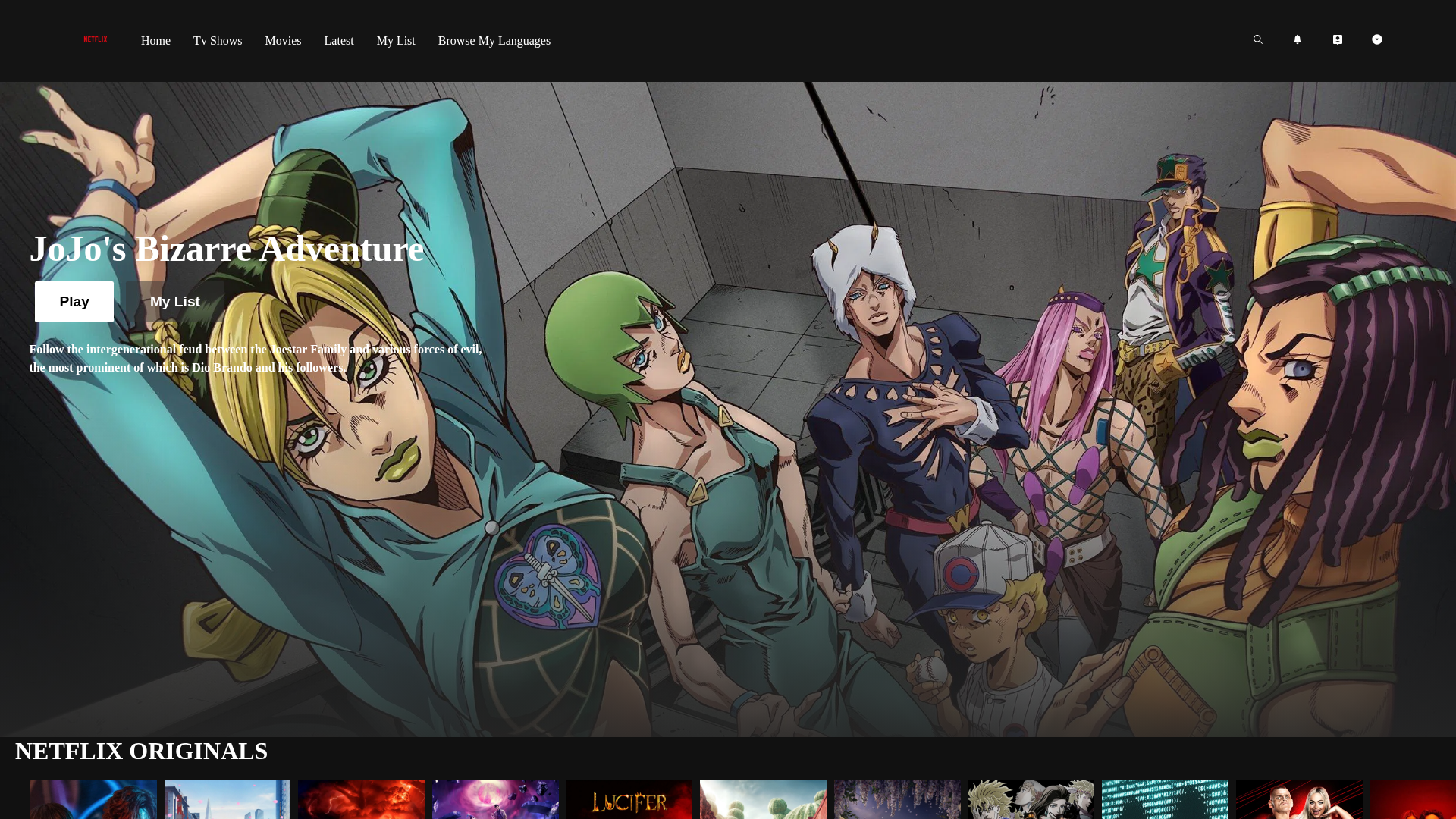
Captura Visual
Información de Detección
http://ahlamv.github.io/Netflix-Clone
Detected Brand
Netflix
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
ab8582c7-5f2…
Analyzed
2026-04-07 13:22
Final URL (after redirects)
https://ahlamv.github.io/Netflix-Clone/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T151C212638E9540DB7716A3D041171F698841CC3F43A28A4CE1BED3A4B7F6CEAE55B398 |
|
CONTENT
ssdeep
|
192:EeHMqnabaMFLinfU87LF2Px/0ELb3tI8UT214Deoocr0UUGUUN60B/:XabaILicw5k/7nXPjcrFF80B/ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c0eb3b04507f5d6a |
|
VISUAL
aHash
|
00fffffefe300000 |
|
VISUAL
dHash
|
c8ed4a9494e4ce94 |
|
VISUAL
wHash
|
00fffffef6340000 |
|
VISUAL
colorHash
|
16609000000 |
|
VISUAL
cropResistant
|
9eb2c31b3596d4cc,6004e2b999899080,9990929a8a9d7938,bcbad68dc1a670f0,c8ed4a9494e4ce94 |
Análisis de Código
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔒 Obfuscation Detected
- fromCharCode
- unescape
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer
Code Obfuscation
JavaScript code obfuscated using 8 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Two-Factor Authentication Stealer
Objetivo
Netflix users
Método de Ataque
obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 8 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Netflix
Official Website
https://www.netflix.com
Fake Service
Credential harvesting service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 8 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
ahlamv.github.io
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.