
Phishing Analysis
Detailed analysis of captured phishing page
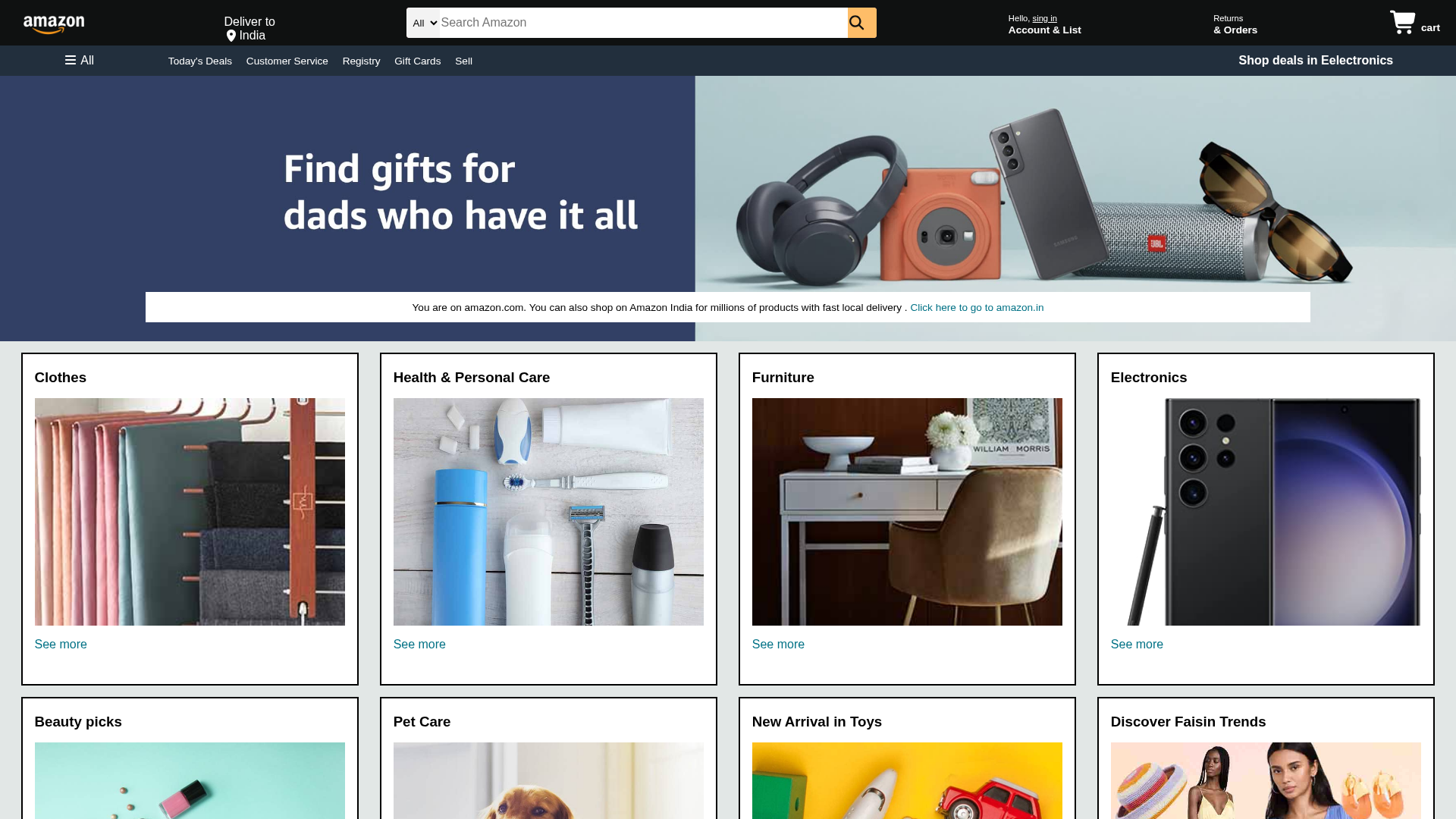
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1929199706082BA3301D7C2E6DF359B9FB2D886A0EA43970557F4D39C4ECAE5ADD25910 |
|
CONTENT
ssdeep
|
96:Tt0JJoDDDyUj9VwU873VeMJ/Iopb/CM/8dhre1R7K1:BIJob4P9/8dhryR7K1 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8e19394edcc94e4e |
|
VISUAL
aHash
|
000301ffb430ffff |
|
VISUAL
dHash
|
72dbdf9464656565 |
|
VISUAL
wHash
|
000301ff30b0ffff |
|
VISUAL
colorHash
|
07207000000 |
|
VISUAL
cropResistant
|
8282e2eaeae28282,dbdf9be46565a565,62db1adbdbef9d9e,d9e6766663697926,4c9736666d595932,adccd9b3b7b7beb6,616c6c5e1e7e7e7c,1d06028602029a9a |
Análisis de Código
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Banking
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Banking Credential Theft
Victim enters banking credentials including account numbers and security questions. Attacker gains full access to victim's banking services.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for poojitha-teella.github.io
Found 1 other scan for this domain
