
Phishing Analysis
Detailed analysis of captured phishing page
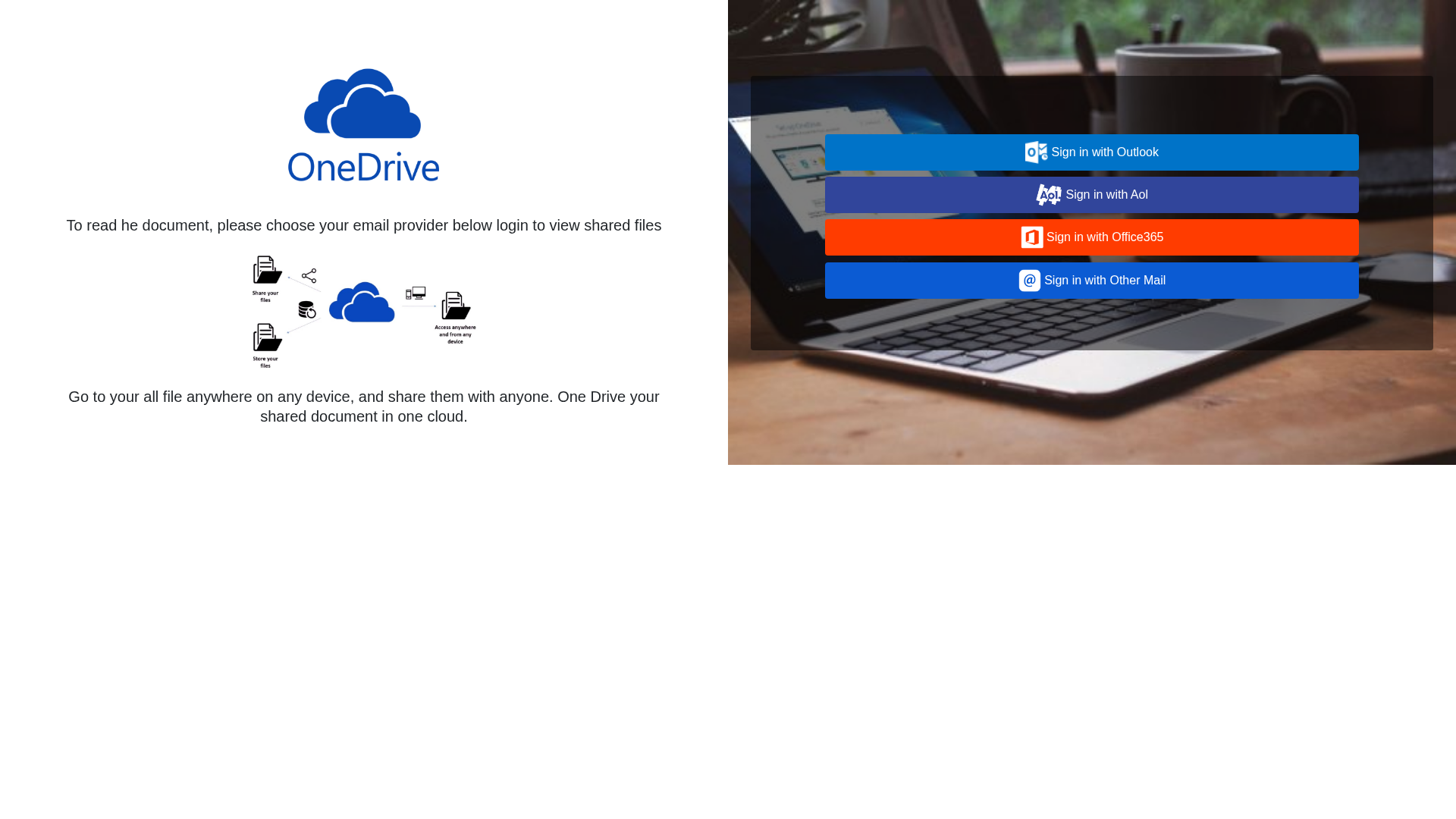
Captura Visual
Información de Detección
https://dvh.cil.temporary.site/Doc1/
Detected Brand
OneDrive
Country
International
Confidence
100%
HTTP Status
200
Report ID
b14ba542-84b…
Analyzed
2026-03-19 16:22
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F0D16270D029CC3B418785D8B2B59B4F3691C255CB230B0467F8A3BE6FEACBAED55254 |
|
CONTENT
ssdeep
|
96:TggUUZUbEArkGAnvI5vPelvpAiv9301C5b2K8UnKAkRhfTKDI:3/2AykfvEvmlvtv9EwJ8UnKAYhbKE |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ce4ea8b96466a6a3 |
|
VISUAL
aHash
|
f0f0f0f0f8ffffff |
|
VISUAL
dHash
|
2424242420000000 |
|
VISUAL
wHash
|
90900010b0ffffff |
|
VISUAL
colorHash
|
066000080c0 |
|
VISUAL
cropResistant
|
2424242420000000,fc987a32f4e47939,b2b210b0e4f0328c |
Análisis de Código
Risk Score
74/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing de credenciales
• Objetivo: Usuarios de OneDrive
• Método: Suplantación de identidad a través de una página similar
• Exfil: Los datos del formulario probablemente se envían al servidor del atacante.
• Indicadores: Coincidencia de dominio, uso de ofuscación y presencia de formulario.
• Riesgo: ALTO
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Suspicious Domain
The domain is not related to the legitimate service and has a 'temporary.site' suffix.
Obfuscation Detected
Code obfuscation is a common technique used by attackers to hide malicious code.
Impersonation
The site attempts to impersonate OneDrive to steal credentials.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
OneDrive users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 11 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
OneDrive
Official Website
onedrive.live.com
Fake Service
OneDrive login
⚔️ Metodología de Ataque
Primary Method: Credential Phishing
The attackers are using a fake login page to collect the usernames and passwords of OneDrive users.
Secondary Method: Obfuscated Javascript
JavaScript code obfuscation likely makes it more difficult to inspect the malicious content.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
dvh.cil.temporary.site
Registered
2020-10-10
Registrar
Unknown
Status
ACTIVE
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
OneDrive
https://dvh.cil.temporary.site/Doc1
Mar 19, 2026
OneDrive
https://dvh.cil.temporary.site/Doc1
Mar 17, 2026
OneDrive/Microsoft
https://dvh.cil.temporary.site/website_7d666046/
Mar 08, 2026
Microsoft OneDrive
https://sunwardamerica.com/wp-con
Feb 20, 2026
OneDrive
https://dvh.cil.temporary.site/onedrive-D8-noredirect/
Feb 20, 2026
Scan History for dvh.cil.temporary.site
Found 6 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.