Phishing Analysis
Detailed analysis of captured phishing page
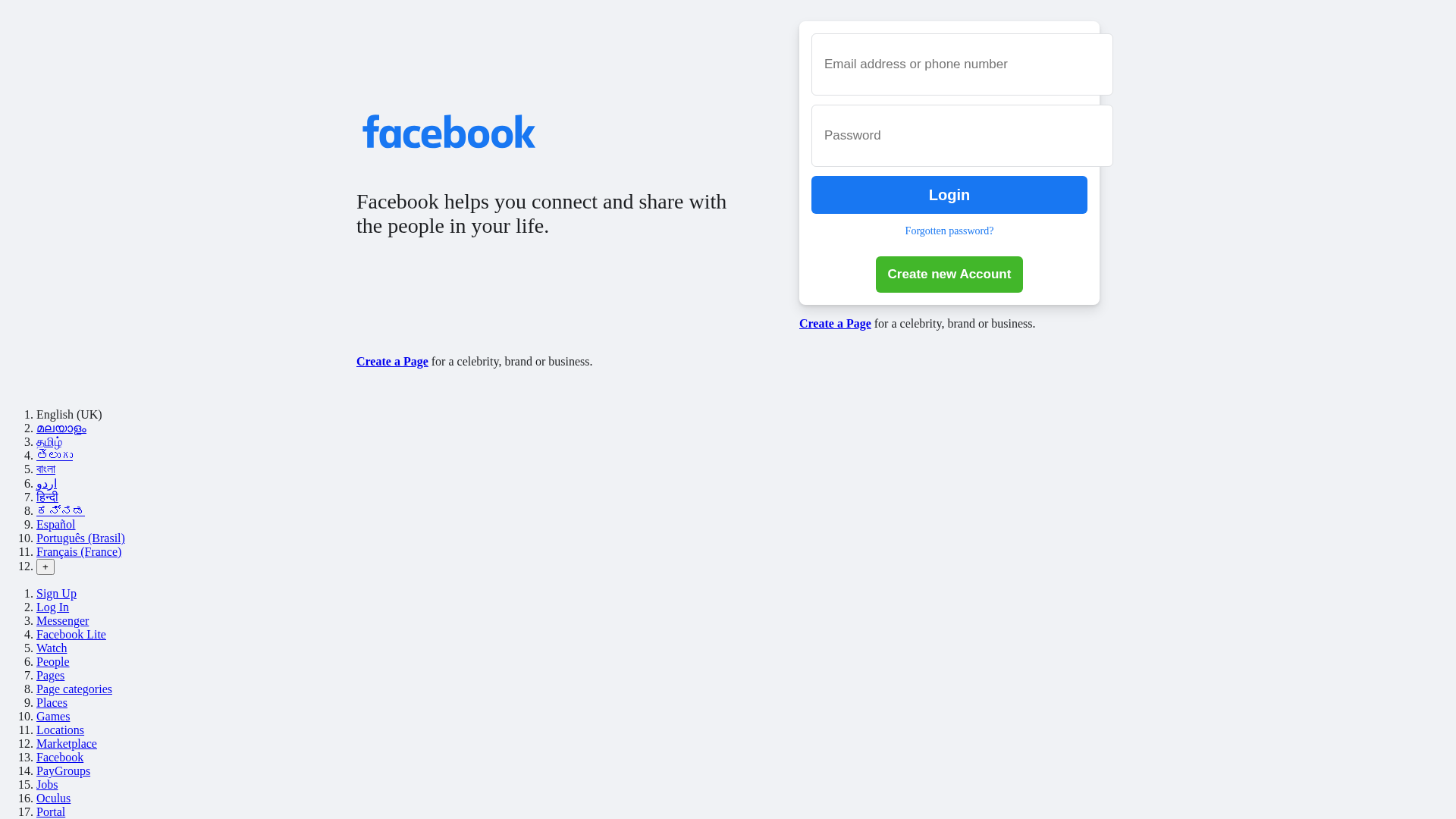
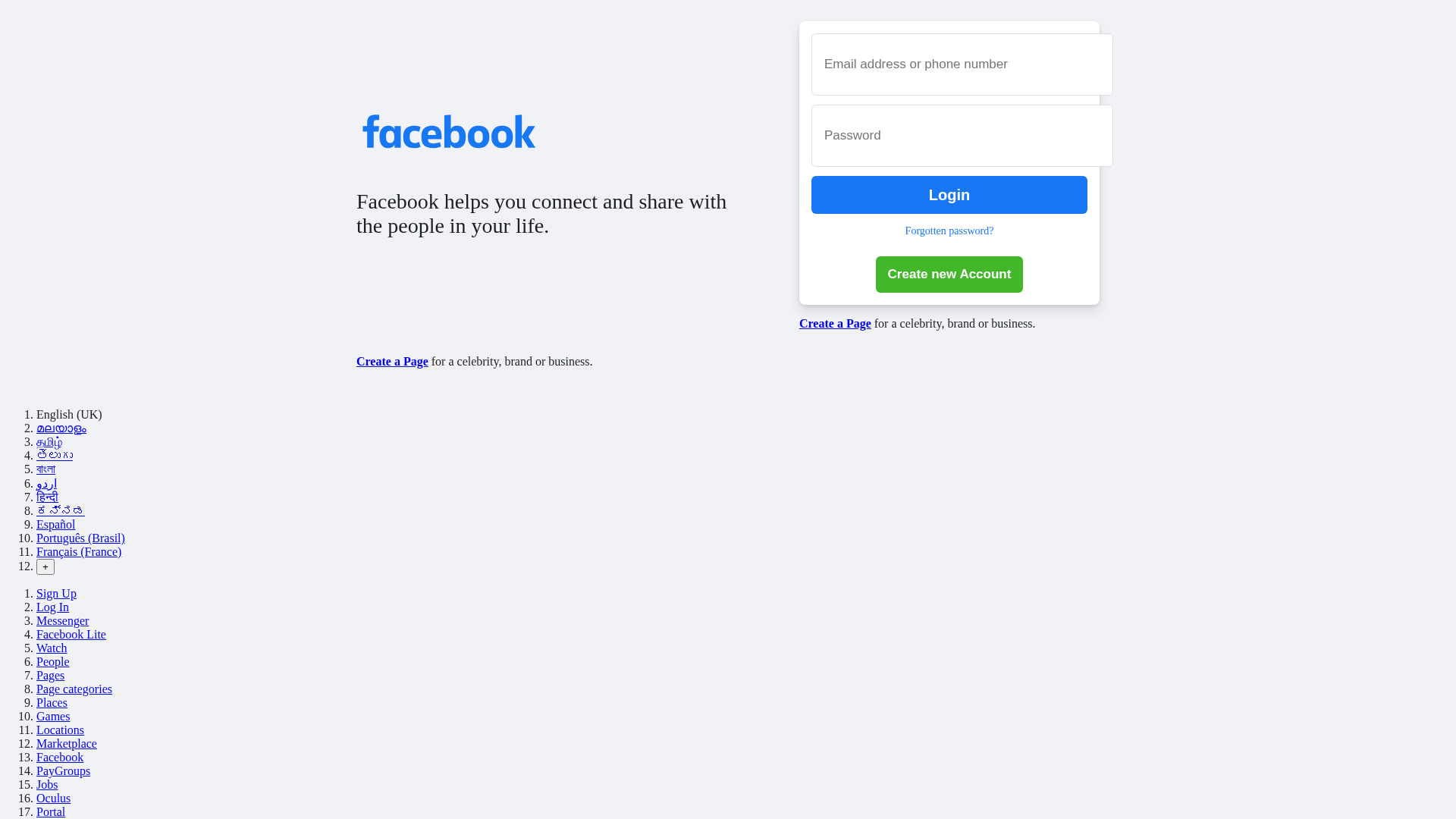
Captura Visual
Información de Detección
http://jokersec0120.github.io/https-www.facebook.com-
Detected Brand
Facebook
Country
International
Confidence
100%
HTTP Status
200
Report ID
b4a19452-9f9…
Analyzed
2026-02-27 11:18
Final URL (after redirects)
https://jokersec0120.github.io/https-www.facebook.com-/
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B151B62A709C645B0BA2335C3E52B7BDD76345AB4A691F063450AD4FB8F2B178C091AF |
|
CONTENT
ssdeep
|
48:njNXLcDS5DuSNVHvKIPcPm4X4C0aNWxaLCw+0k7/rmnRqccArORlsQ4Asau/k7/z:nF6SLNU1RjcfRB |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a07d929292d3e56d |
|
VISUAL
aHash
|
ff83d3df7f7f7f7f |
|
VISUAL
dHash
|
38b636b6a8808080 |
|
VISUAL
wHash
|
0e0202807f7f3f3f |
|
VISUAL
colorHash
|
070000011c0 |
|
VISUAL
cropResistant
|
38b636b6a8808080 |
Análisis de Código
Risk Score
88/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
Telegram Exfiltration
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Facebook
• Método: Suplantación de identidad a través de una página de inicio de sesión falsa en alojamiento gratuito.
• Exfil: Los datos se envían a un bot de Telegram.
• Indicadores: Alojamiento gratuito, logotipo de la marca, formulario de inicio de sesión, envío de formulario JavaScript, token de Telegram.
• Riesgo: Alto
🔒 Obfuscation Detected
- unescape
🔑 Telegram Bot Tokens (1)
- 8512653224:AAEE...X3y6jEBc
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Free Hosting
The site is hosted on a free hosting platform which increases the likelihood of malicious activity.
Brand Impersonation
The site impersonates a well-known brand (Facebook) to deceive users.
Form for Credentials
The site contains a form designed to collect sensitive user credentials.
JavaScript Obfuscation & Form Submission
JavaScript is used, likely for malicious purposes such as exfiltration, and the form submits data via JS.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
Facebook users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Telegram Bot (8512653224:AAEEtBb6K...)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Telegram Bot (8512653224:AAEEtBb6K...)
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester
- 1 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Facebook
Official Website
https://www.facebook.com
Fake Service
Facebook Login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker uses a fake login page that mimics Facebook's legitimate login interface to trick users into entering their credentials.
Secondary Method: Data Exfiltration via Telegram
The collected credentials are likely being sent to a Telegram bot for the attacker to access.
📡 Infraestructura de Comando y Control Telegram
Bot Token (Masked)
8512653224:AAEE...X3y6jEBc
Bot ID
8512653224
Group/Chat ID
Unknown
Operator Language
Unknown
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
jokersec0120.github.io
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for jokersec0120.github.io
Found 6 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.