
Phishing Analysis
Detailed analysis of captured phishing page
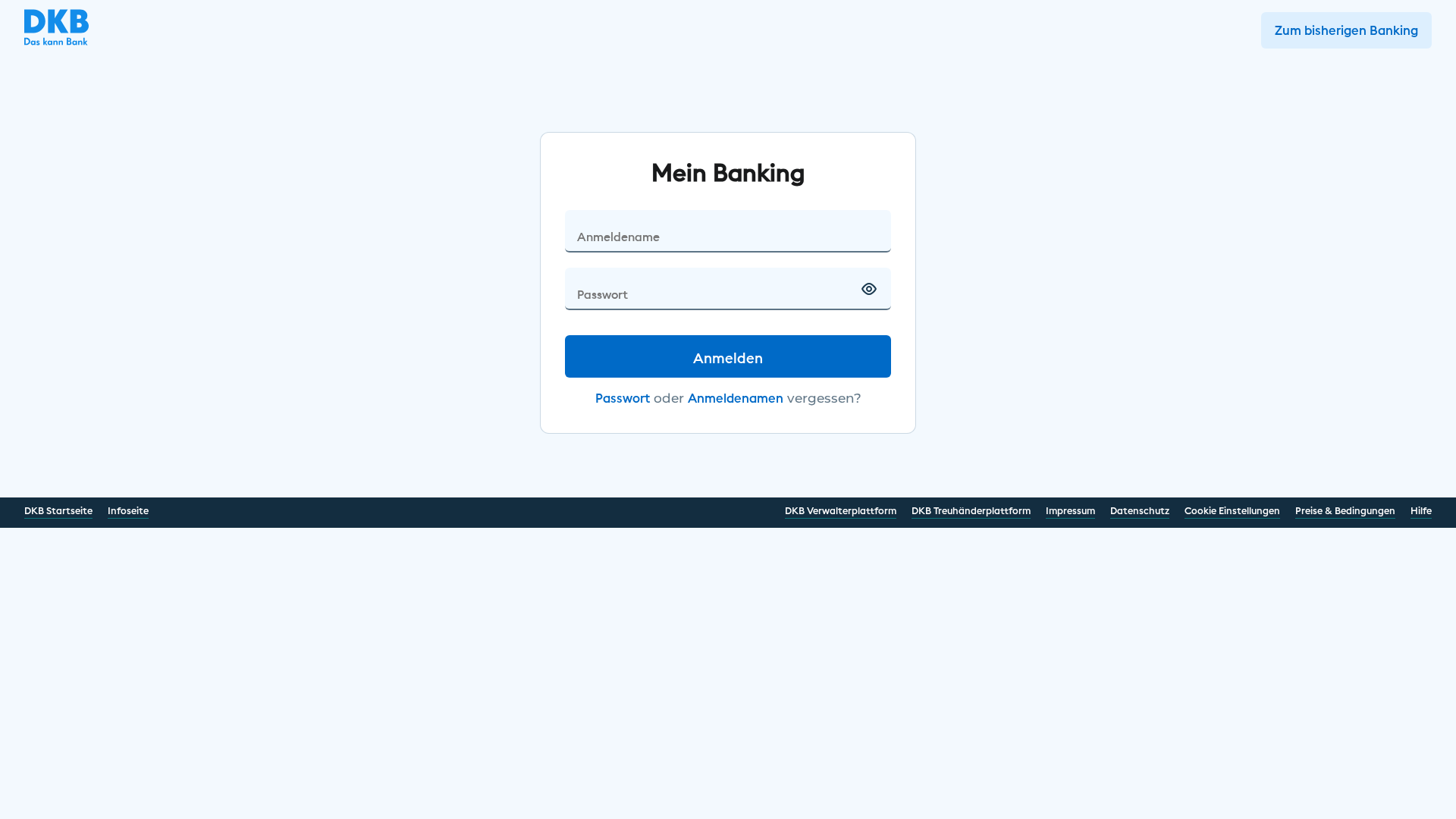
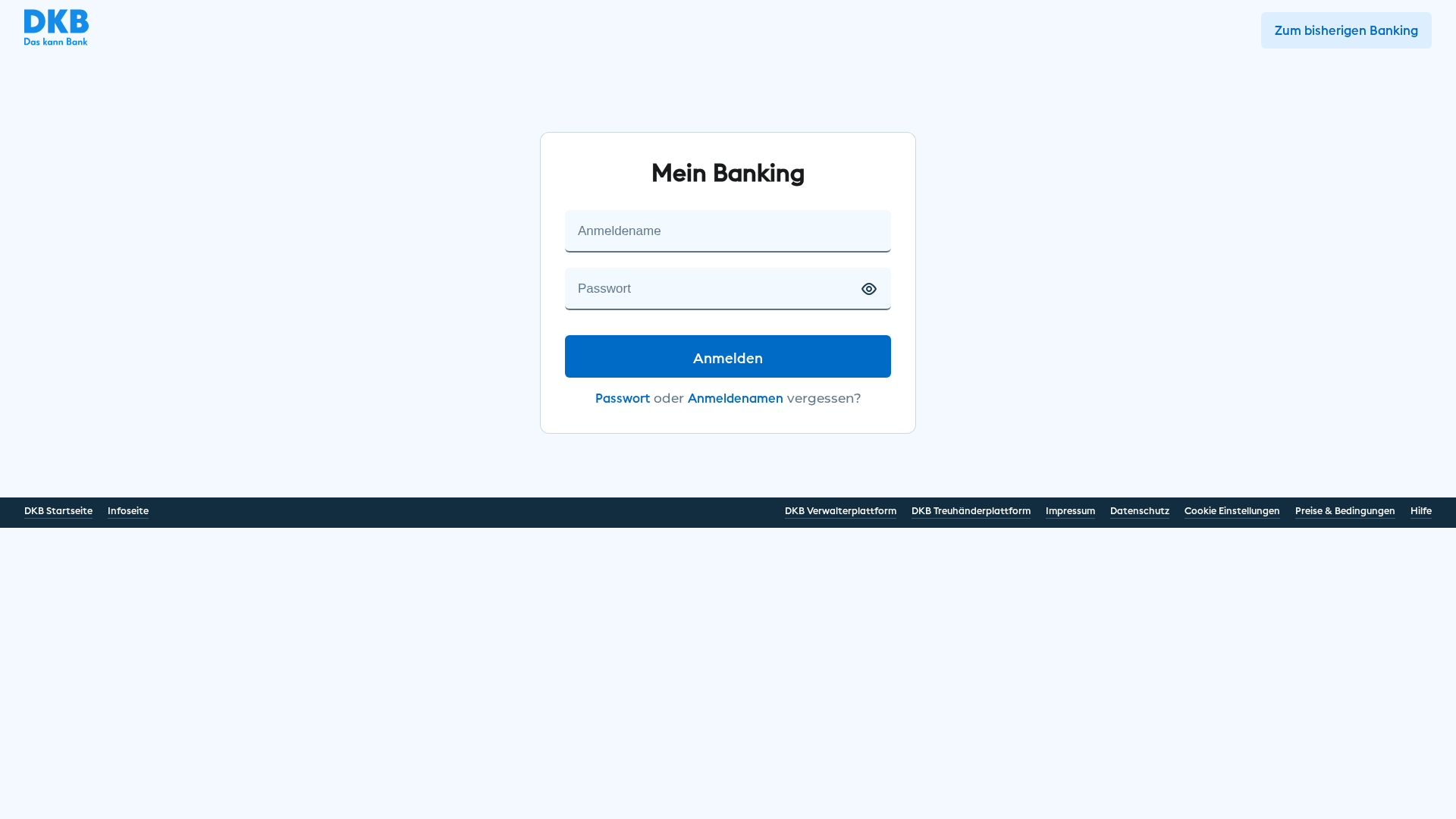
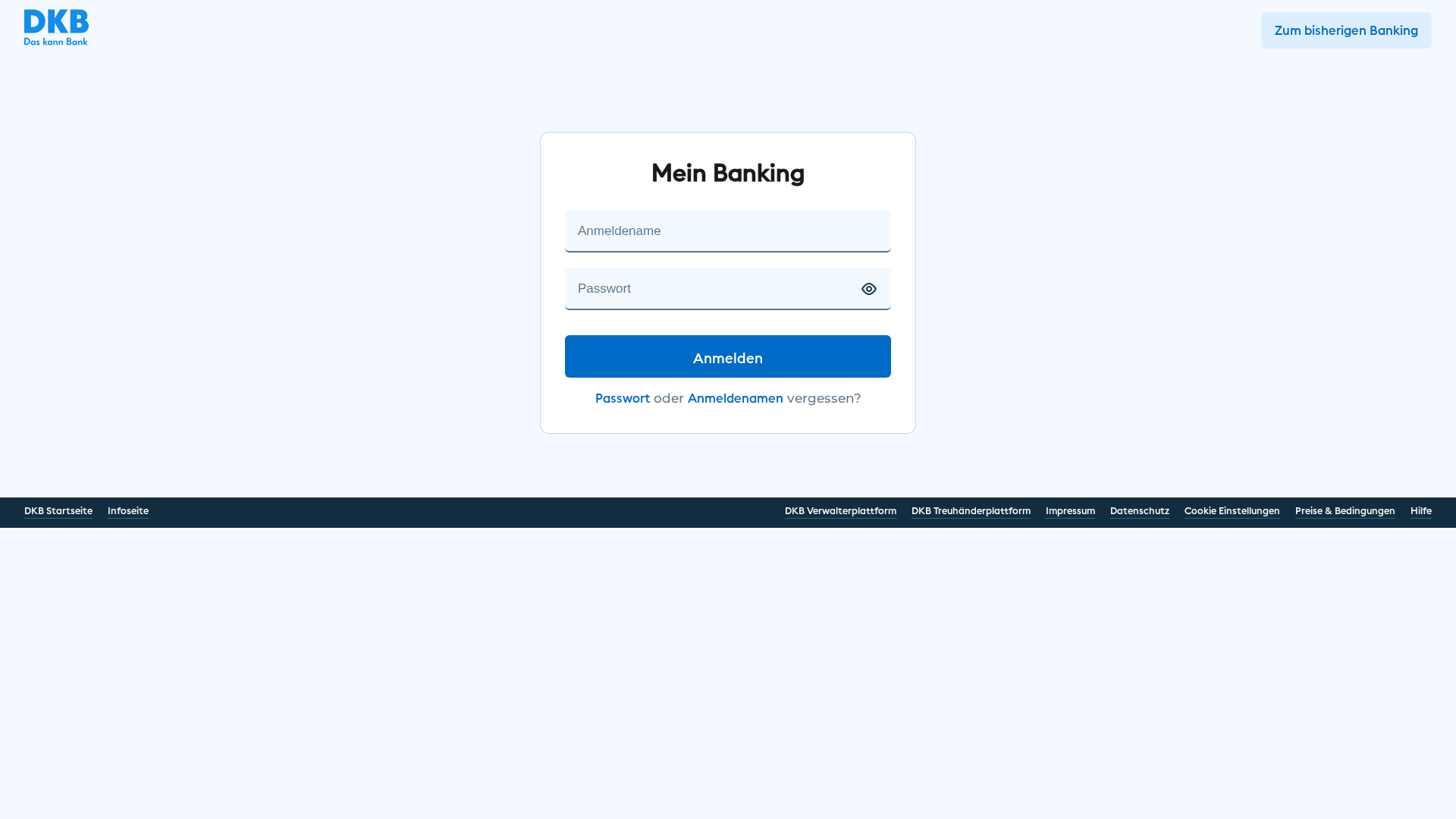
Captura Visual
Información de Detección
https://intranet.universe.us/esien/bone/
Detected Brand
DKB Das kann Bank
Country
International
Confidence
100%
HTTP Status
200
Report ID
b5de4569-f2e…
Analyzed
2026-02-13 19:37
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BE41C071100C7C3F4987EBF88BB1A78AA3D9D605C86B160661F8E34C5EC6E52DD806DC |
|
CONTENT
ssdeep
|
48:xz4DKxXJcUfos/HSLtTeA6Bs4adBadxf2:xXJlfLq6+dwdxf2 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3e2cc1d76e21919 |
|
VISUAL
aHash
|
ffffffe70000ffff |
|
VISUAL
dHash
|
94294c0d08180008 |
|
VISUAL
wHash
|
60e6e4e40000ffff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
8c102848304d4d30,0000000000000000,00100c32b2b20c20,08831a1a1a180800 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de DKB
• Método: Suplantación de identidad
• Exfil: hot/hakona.php
• Indicadores: Discordancia de dominio, formulario sospechoso, suplantación de identidad.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🎯 Kit Endpoints
- https://koncharapolei.alwaysdata.net/dkb/login.php
📤 Form Action Targets
- hot/hakona.php
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not belong to the target brand.
Suspicious Form Action
Form submits to a PHP script at a potentially malicious location.
Impersonation
Visual resemblance to DKB's login page.
High Risk Target (Banking)
Targets financial information.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
DKB Das kann Bank users (International)
Método de Ataque
Brand impersonation + credential harvesting forms
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
🏢 Análisis de Suplantación de Marca
Impersonated Brand
DKB Das kann Bank
Official Website
https://www.dkb.de
Fake Service
DKB Banking Login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal user credentials by creating a fake login page that closely resembles DKB's official website. The user is tricked into entering their login details, which are then captured by the attacker.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
intranet.universe.us
Registered
2002-04-24
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
DKB
http://delivery.dbcorp.in/AMGCOUJTWR?id=75301=cB1WCAQFCwYATF...
Mar 27, 2026
DKB
https://wordpress-209642-0.cloudclusters.net/aa/dkb/login.ph...
Mar 27, 2026
DKB - Das kann Bank
https://biancacastrogomes1769819760631.2292159.meusitehostga...
Mar 07, 2026
DKB
https://biancacastrogomes1769819760631.2292159.meusitehostga...
Feb 28, 2026
DKB
https://biancacastrogomes1769819760631.2292159.meusitehostga...
Feb 28, 2026
Scan History for intranet.universe.us
Found 10 other scans for this domain
-
http://intranet.universe.us/2951a4/intro/login.php...
https://intranet.universe.us/90f177/en/deine/login...
https://intranet.universe.us/90f177/en/deine/login...
https://intranet.universe.us/
https://intranet.universe.us/esien/bone/
https://intranet.universe.us/esien/bone/
https://intranet.universe.us/autes/midle/
https://intranet.universe.us/autes/midle
https://intranet.universe.us/cuntie/diens/login.ph...
https://intranet.universe.us/wp-includes/me/at/log...

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.