Phishing Analysis
Detailed analysis of captured phishing page
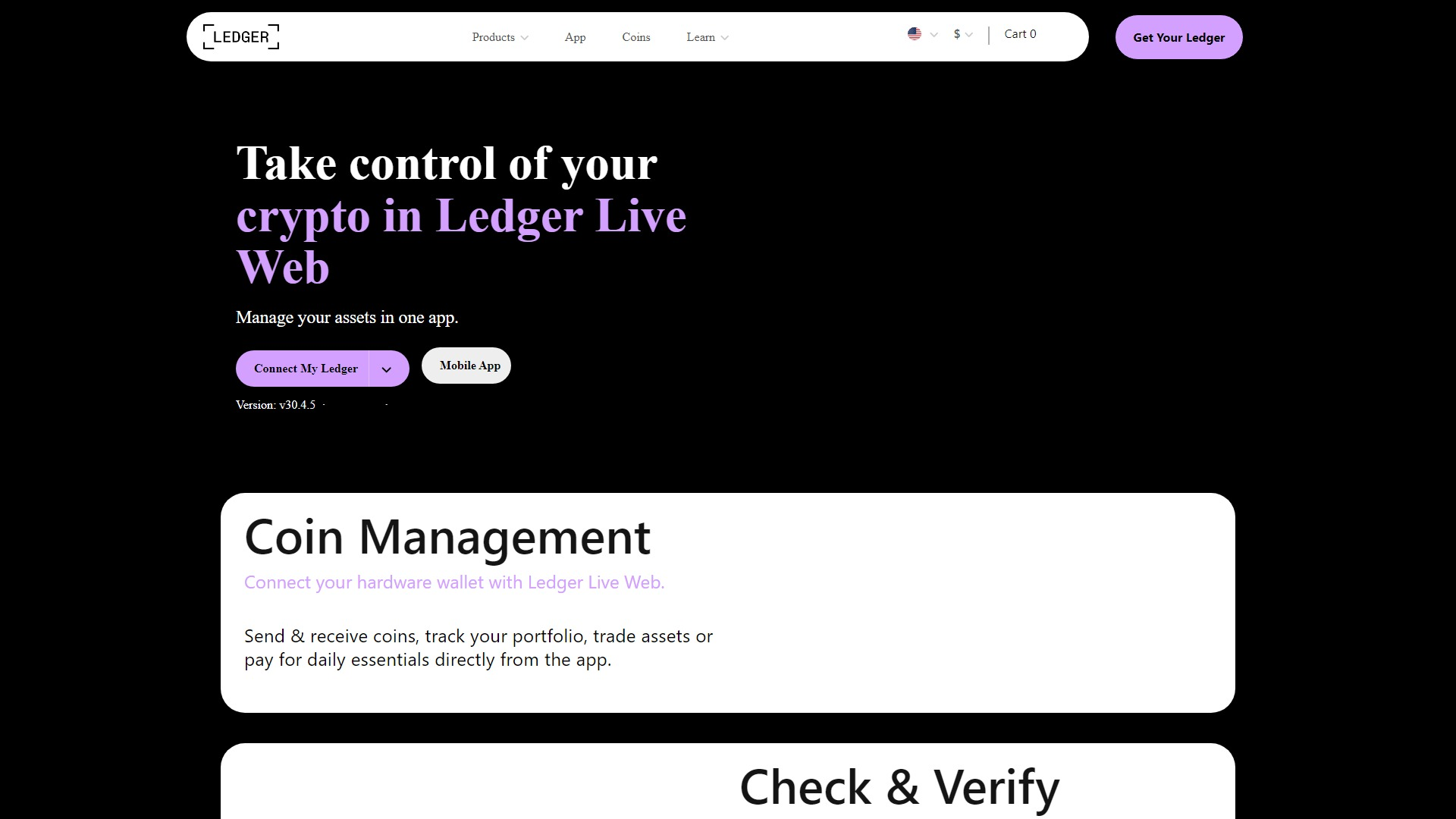
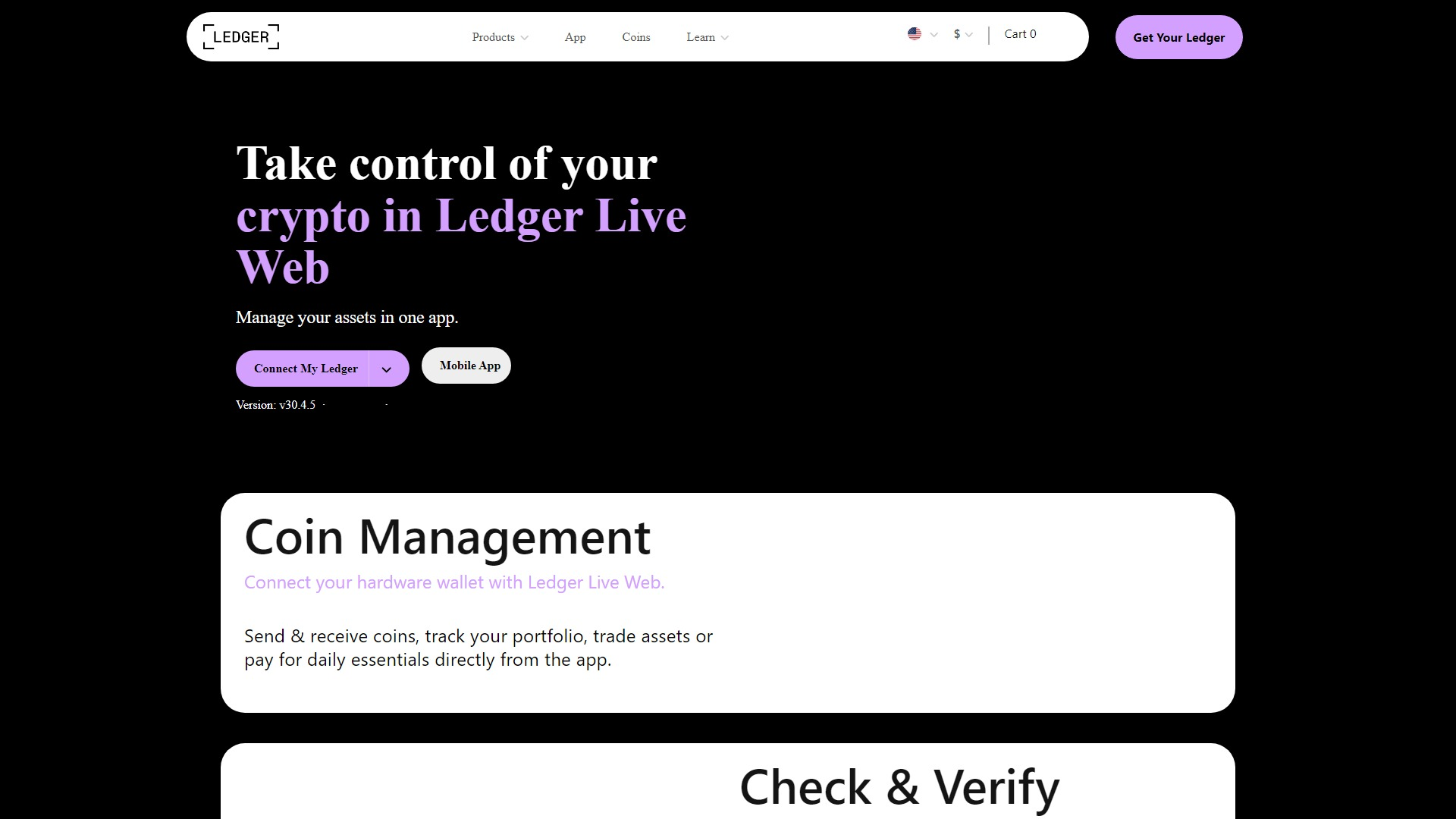
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15EB1A513F34C2167079702FCFB6BA0E8C24B849CA29A9A04A1BC721E53D55CDC37E9D8 |
|
CONTENT
ssdeep
|
96:dQXpPG/R1/7SKc4t0wAdSnQ2+FYr5u7vQMuw4Sghzyb4/MRreZCm:dCpPG51js4t0wAfTFSaJe+bJeIm |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c16bd4906bd1947e |
|
VISUAL
aHash
|
7c000000007e7e7e |
|
VISUAL
dHash
|
d8c0c0c0d0d0dcc4 |
|
VISUAL
wHash
|
7e0000607e7e7e7e |
|
VISUAL
colorHash
|
3a000e00000 |
|
VISUAL
cropResistant
|
a280c1899dccc0a2,c03030d098383080,a2808ba3a3a7a781,d8c0c0c0d0d0dcc4 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Ledger
• Método: Suplantación de identidad a través de un sitio web parecido.
• Exfil: Desconocido, probablemente robo de credenciales y/o acceso a monederos criptográficos. fromCharCode está presente.
• Indicadores: Logo de Ledger en hosting gratuito, intenta imitar la interfaz de Ledger Live.
• Riesgo: Alto
🔒 Obfuscation Detected
- fromCharCode
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 4 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker likely uses a convincing replica of the Ledger interface to trick users into entering their login credentials or seed phrases. These stolen credentials can then be used to access the victim's Ledger wallet.
Secondary Method: Malware Injection (Possible)
The presence of obfuscation may indicate that the site could also inject malicious code to perform actions such as keylogging or redirecting users to fake URLs.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for hellp-ledgerrliv-app.webflow.io
Found 2 other scans for this domain