
Phishing Analysis
Detailed analysis of captured phishing page
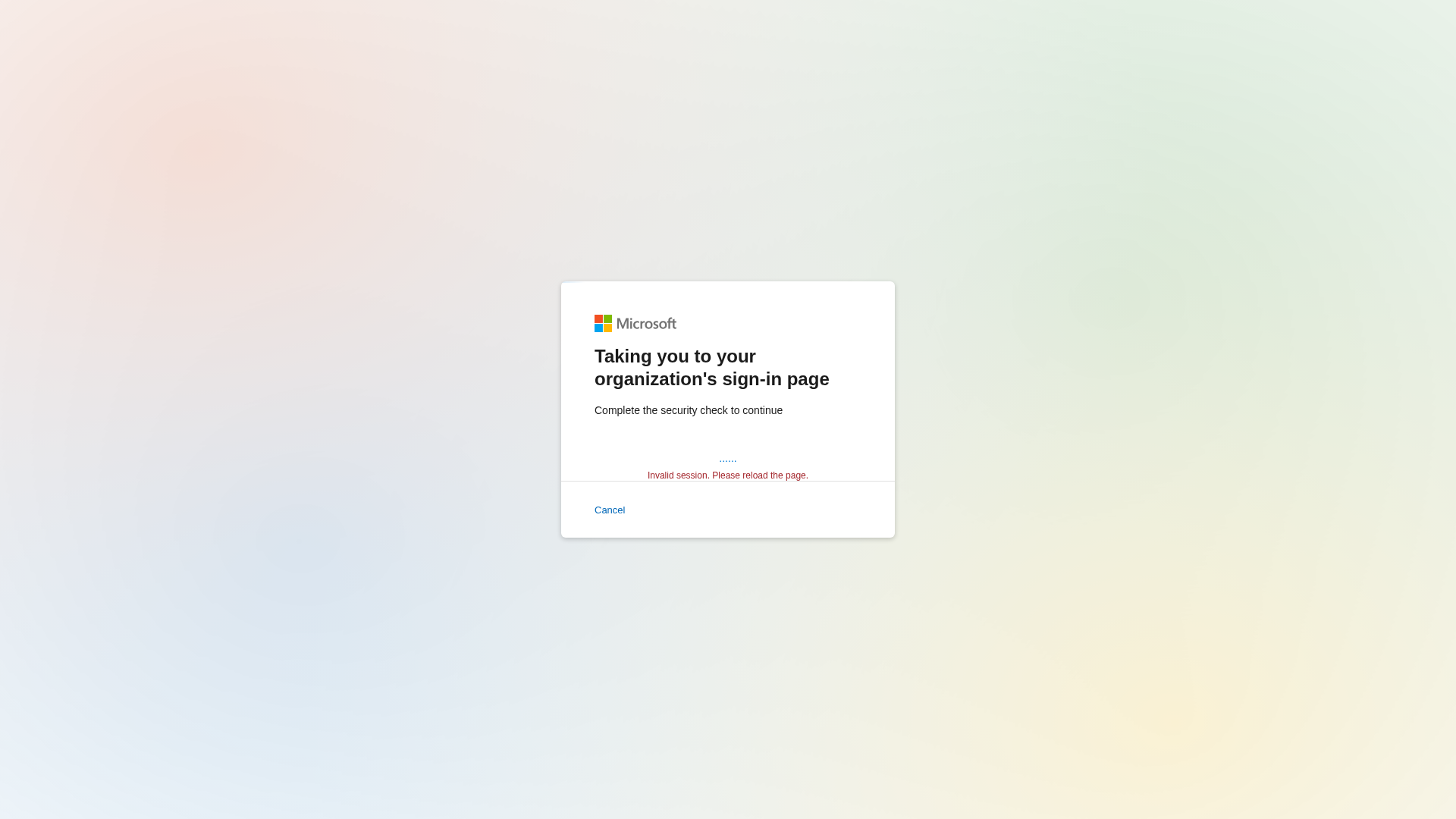
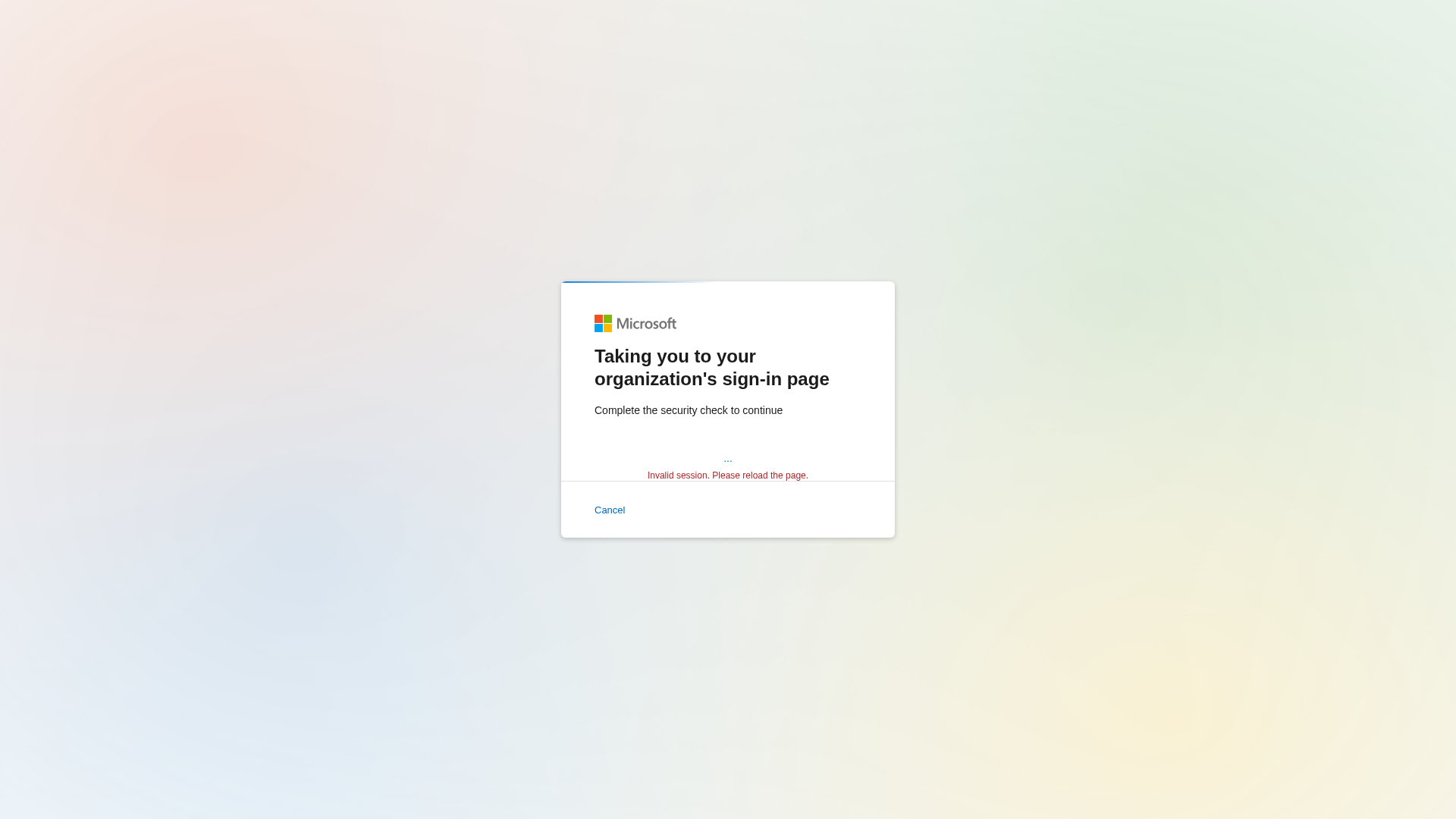
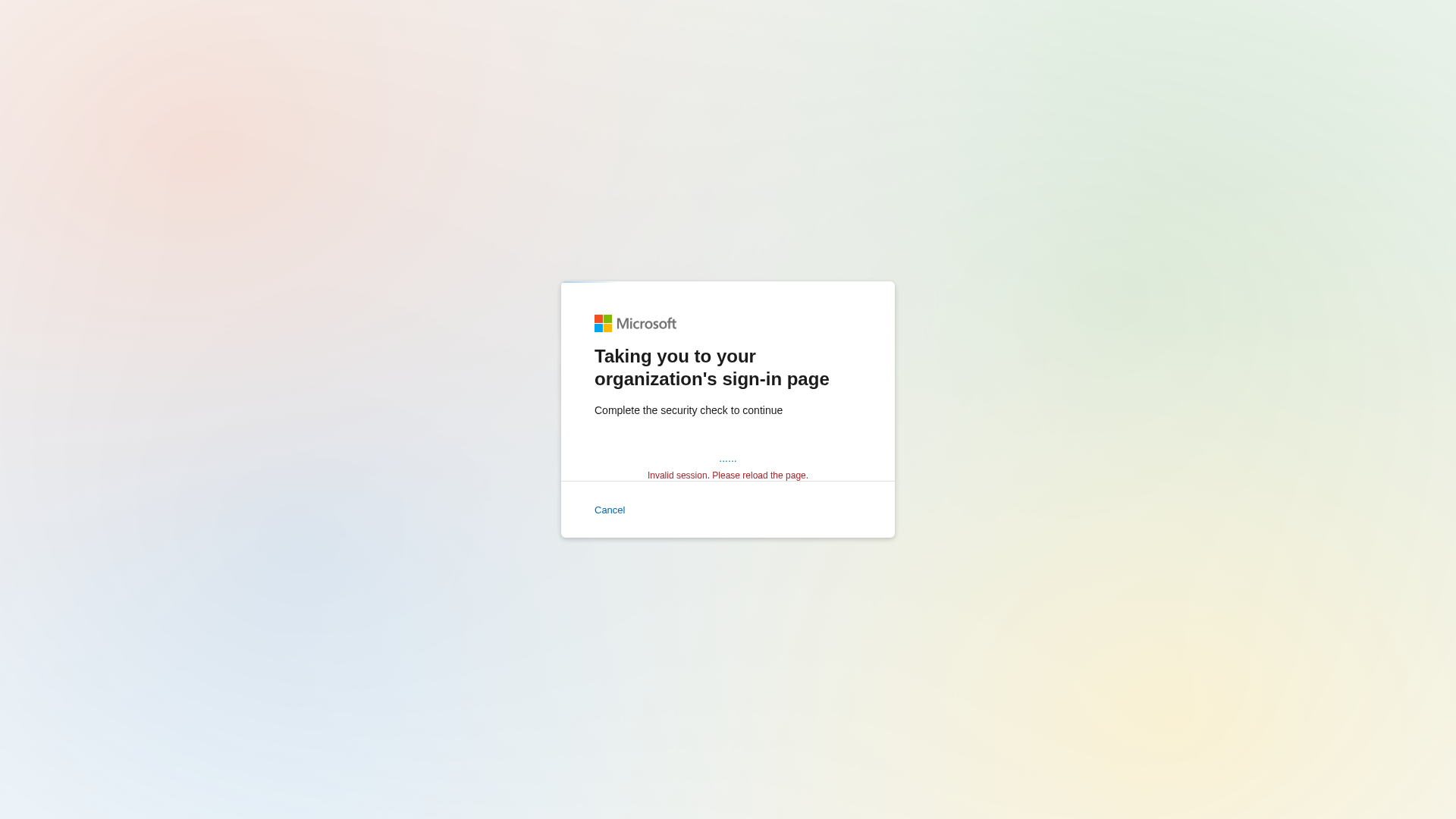
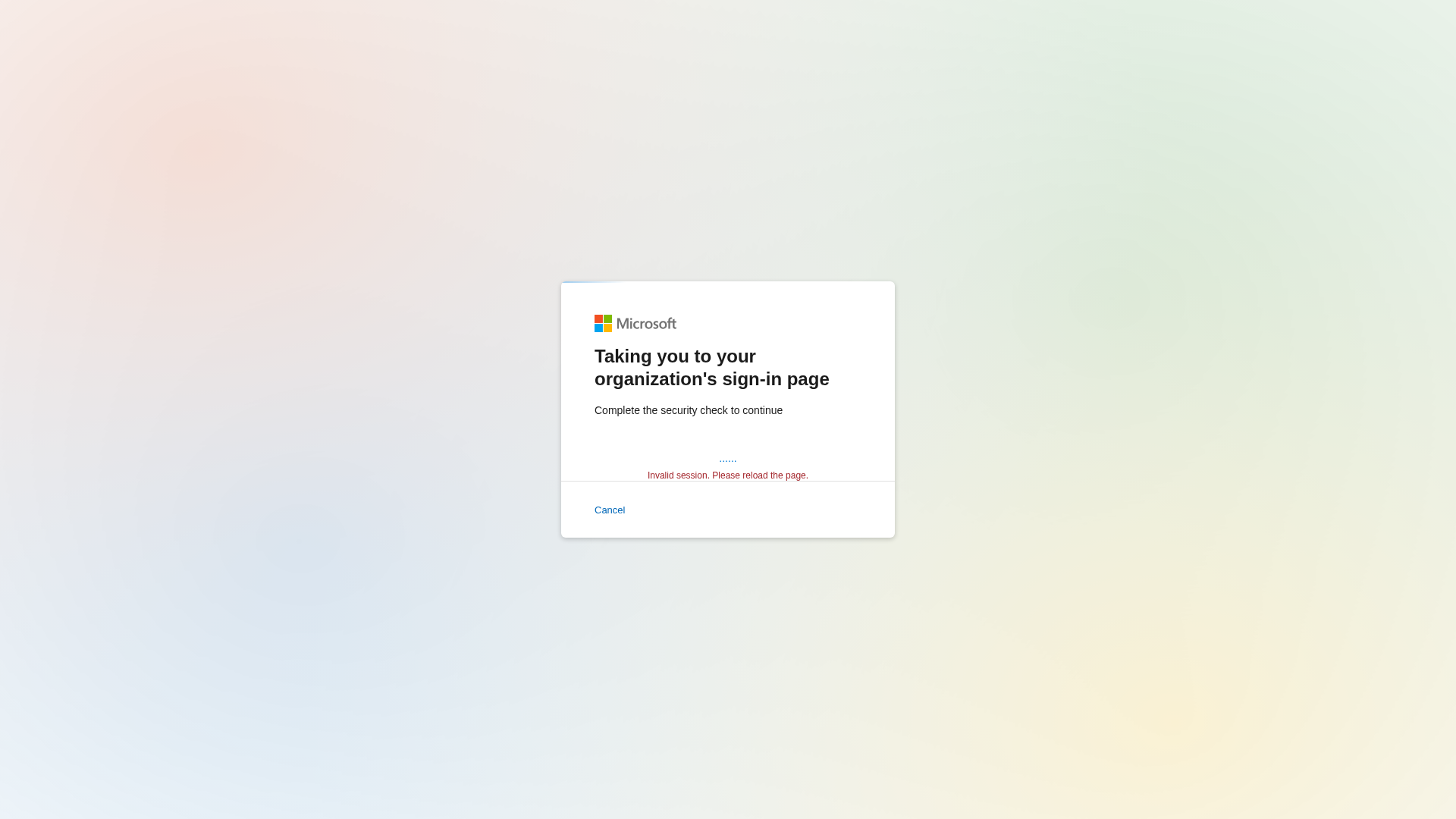
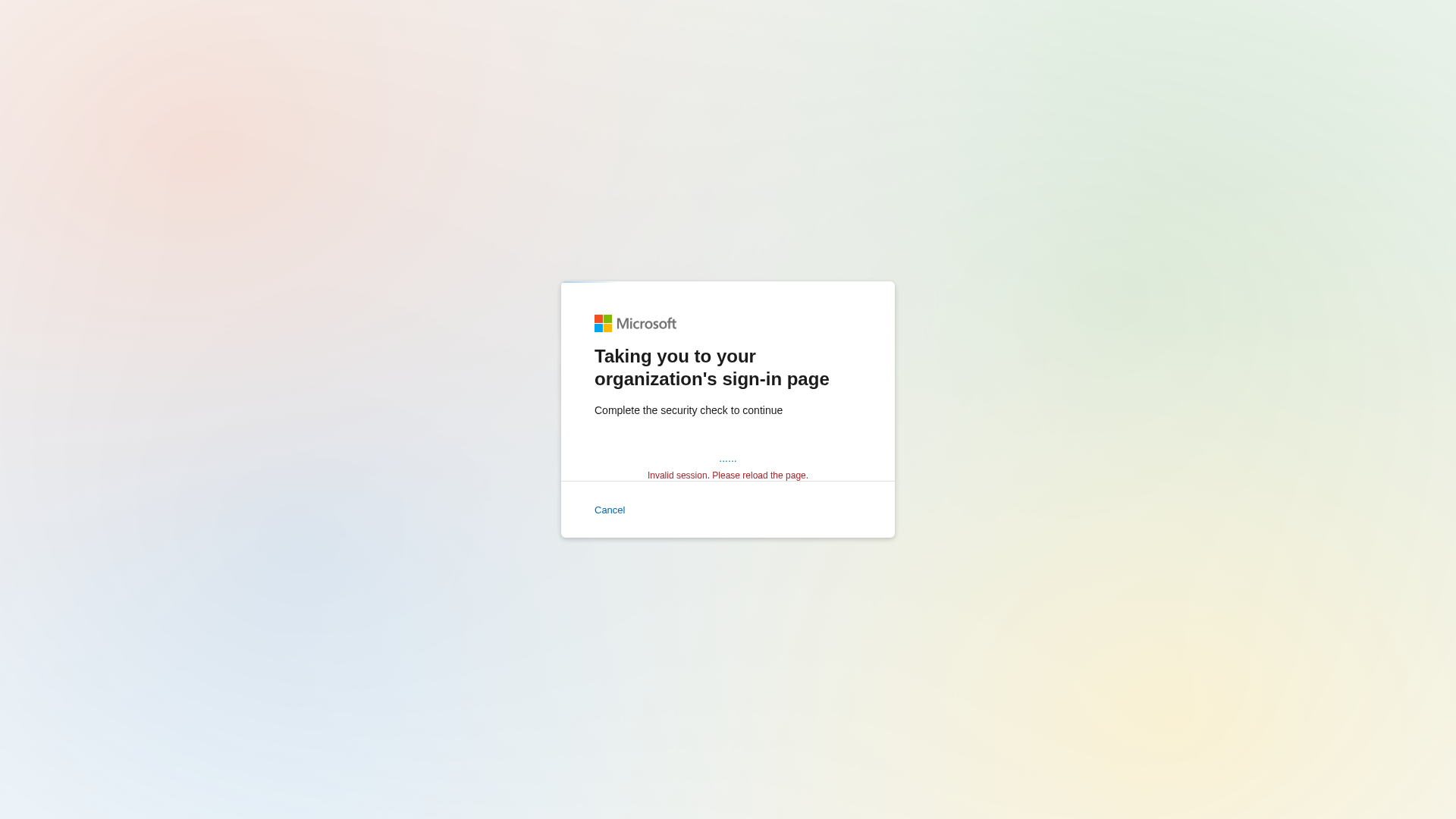
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E3218E68E448993747A3D1D9A5A1A35F3AA0878CD7130B055FF8139927DFFA8CD021D9 |
|
CONTENT
ssdeep
|
24:hR/nTxVx/cIgDETsCVlWJnPaWNPALc756Fl+Nit8zZrAd:Ttf/cIgwYCvATPW8CMiN |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9b4be68cd933c88c |
|
VISUAL
aHash
|
180018081d1f1fbf |
|
VISUAL
dHash
|
7161717b33717d79 |
|
VISUAL
wHash
|
391818081f1f1fff |
|
VISUAL
colorHash
|
07000088041 |
|
VISUAL
cropResistant
|
7161717b33717d79 |
Análisis de Código
🔒 Obfuscation Detected
- atob
- base64_strings
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 3 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 3 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev
Found 6 other scans for this domain
-
https://pub-60feb3b0da144b72b0f8c76714a15abf.r2.de...
https://pub-60feb3b0da144b72b0f8c76714a15abf.r2.de...
https://pub-60feb3b0da144b72b0f8c76714a15abf.r2.de...
http://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev...
http://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev...
http://pub-60feb3b0da144b72b0f8c76714a15abf.r2.dev...
