Phishing Analysis
Detailed analysis of captured phishing page
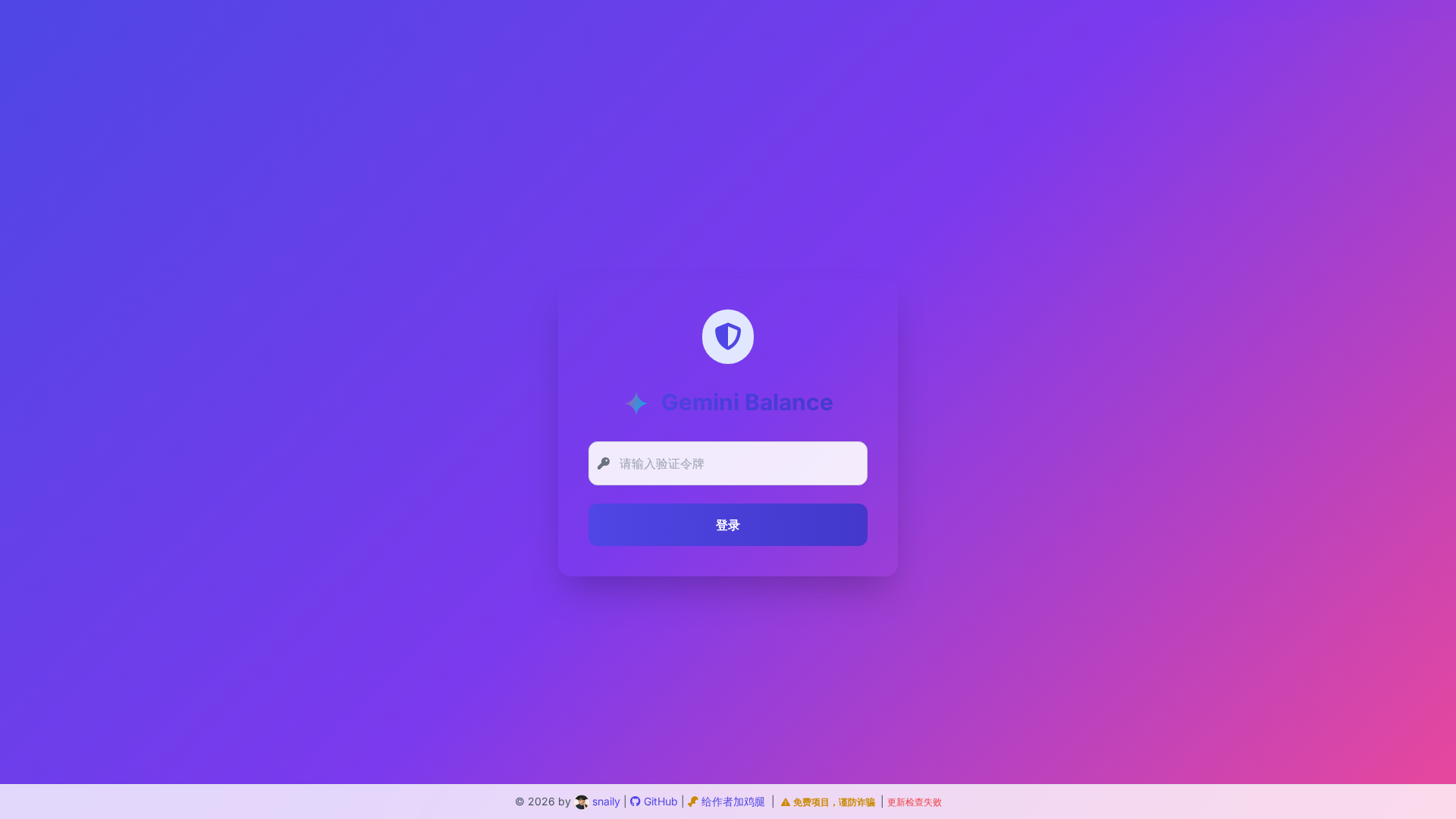
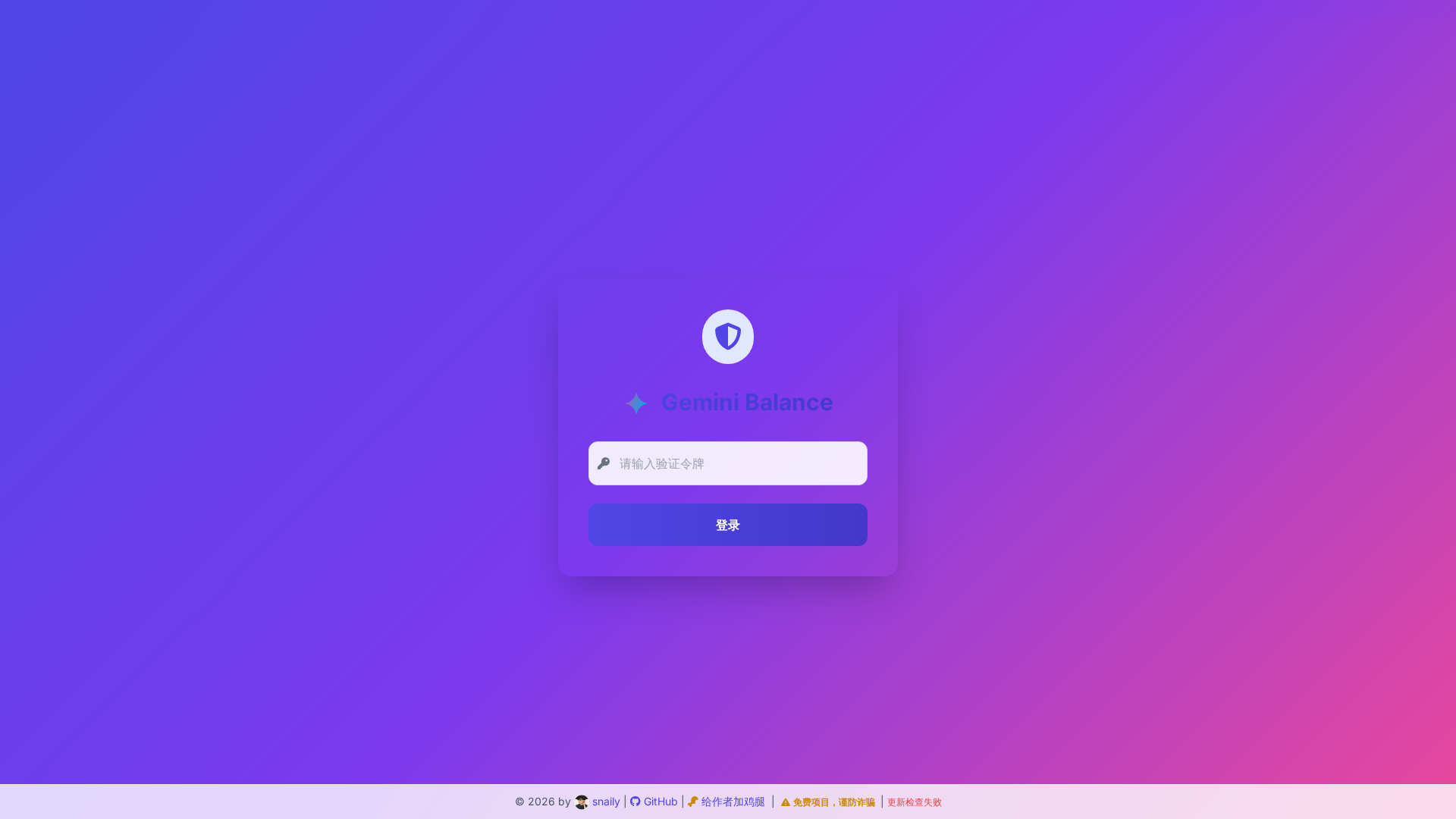
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13B71747852D107B76103C9D0F69AFB2AD9E5CB58DA23584BE2FCC2CB0685C68DD4A361 |
|
CONTENT
ssdeep
|
48:x2TtaaR8cC9AhiQ+ouOwKSwLaOSHyNT9Zb9NuNP5WfjhqbPQLjqS1:x2Twb9ACBwLaODNht9NuNP5khqb6OS1 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a84bf318d933f60c |
|
VISUAL
aHash
|
000101031b0707ff |
|
VISUAL
dHash
|
fffff7b7b3cfff5f |
|
VISUAL
wHash
|
0103071f1f071fff |
|
VISUAL
colorHash
|
00000000030 |
|
VISUAL
cropResistant
|
aaa2a2b2b2aaa2be,ffff7f7a4f4d5e6e,fffff757b3b7cfff |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Gemini
• Método: Suplantación de identidad y recopilación de credenciales
• Exfil: /auth
• Indicadores: Coincidencia de dominio, ofuscación, idioma chino.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- https://evilmartians.com/chronicles/postcss-8-plugin-migration`),m.env.LANG&&m.env.LANG.startsWith(
- https://tailwindcss.com/docs/content-configuration#safelisting-classes
- https://tailwindcss.com`}),...e.nodes])},container:(()=
- https://tailwindcss.com/docs/content-configuration
- https://mths.be/cssesc
- https://tailwindcss.com/docs/content-configuration#discarding-classes
- https://tailwindcss.com/docs/upgrade-guide#prefix-cannot-be-a-function
- https://tailwindcss.com/docs/upgrade-guide#configure-content-sources
- https://tailwindcss.com/docs/using-with-preprocessors#nesting
- https://cdn.tailwindcss.com
- https://tailwindcss.com/docs/upgrade-guide#remove-dark-mode-configuration
- https://www.w3ctech.com/topic/2226`));let
- https://tailwindcss.com/docs/content-configuration#pattern-recommendations
- https://twitter.com/browserslist
- https://tailwindcss.com/docs/upgrade-guide#replace-variants-with-layer
- https://tailwindcss.com/docs/installation
📡 API Calls Detected
- /api/version/check
📤 Form Action Targets
- /auth
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 18 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site uses a form to trick users into entering their Gemini login credentials (or a 'verification token') into a fake login form. The entered data is then sent to the attackers.
Secondary Method: Phishing through Obfuscated JavaScript
The site uses JavaScript, and more specifically obfuscated JavaScript to try and hide what it is doing and how it is harvesting the data.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
cdn.tailwindcss.comSimilar Websites
Pages with identical visual appearance (based on perceptual hash)