
Phishing Analysis
Detailed analysis of captured phishing page
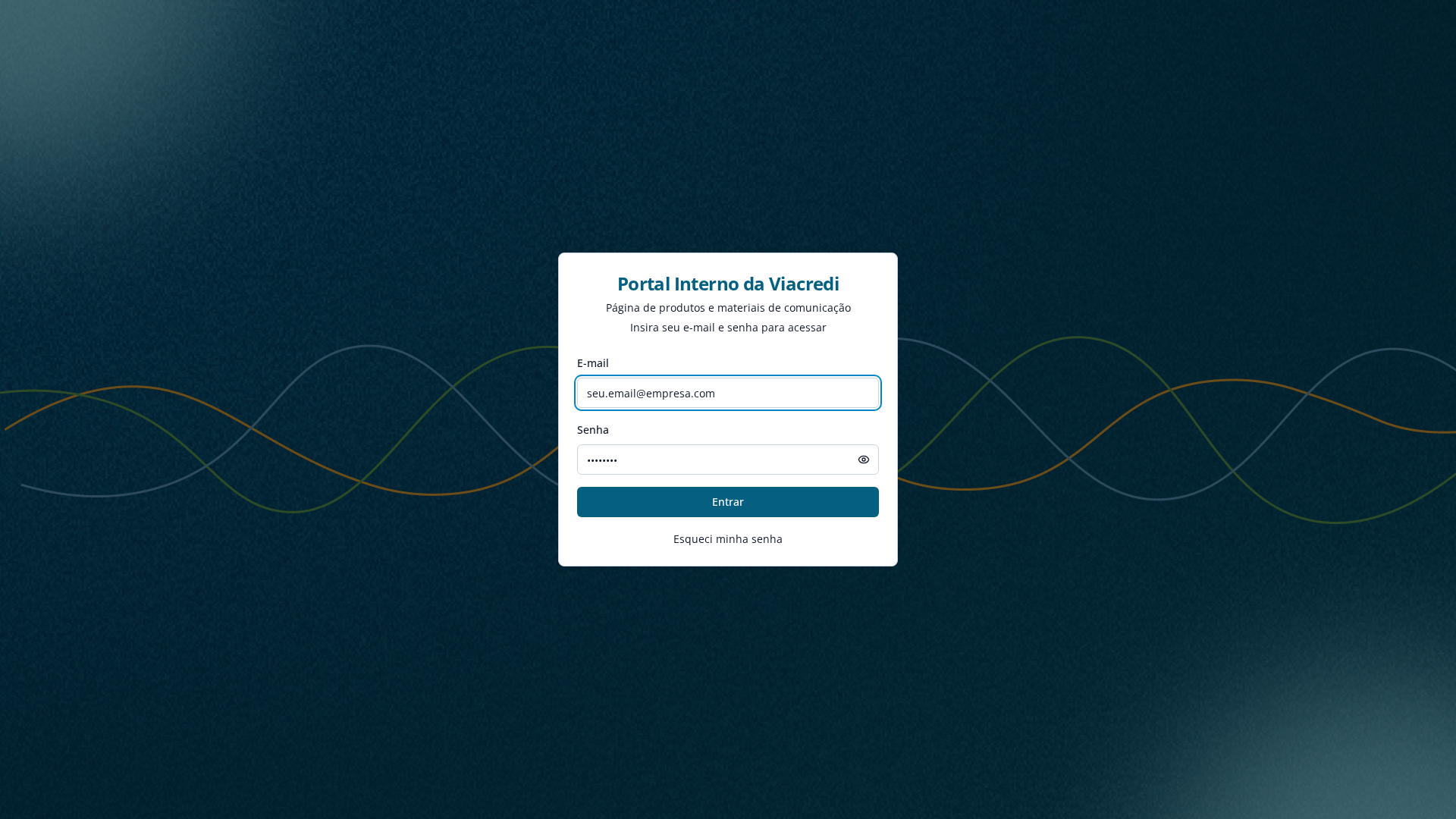
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18CA1C73214801A3F5627C66CB6E0F203669FC21DC9A7D966E3FE41BE37DAD50C623564 |
|
CONTENT
ssdeep
|
96:Tle46YATqrkPNQV83SQT839Nks93EcYbvCqi7:xz8q9NJBZYbvLg |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ddde277689d88822 |
|
VISUAL
aHash
|
8080181818180103 |
|
VISUAL
dHash
|
200c32b2b2b34f33 |
|
VISUAL
wHash
|
f0f0f8f8fc190307 |
|
VISUAL
colorHash
|
380020001c0 |
|
VISUAL
cropResistant
|
332bc278c051558c,200c32b2b2b34f33 |
Análisis de Código
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
📡 API Calls Detected
- POST
☁️ Cloud Backend
- Supabase: zgbkvhzxgpbtzhcwdqfr.supabase.co
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 18 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 18 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
