Phishing Analysis
Detailed analysis of captured phishing page
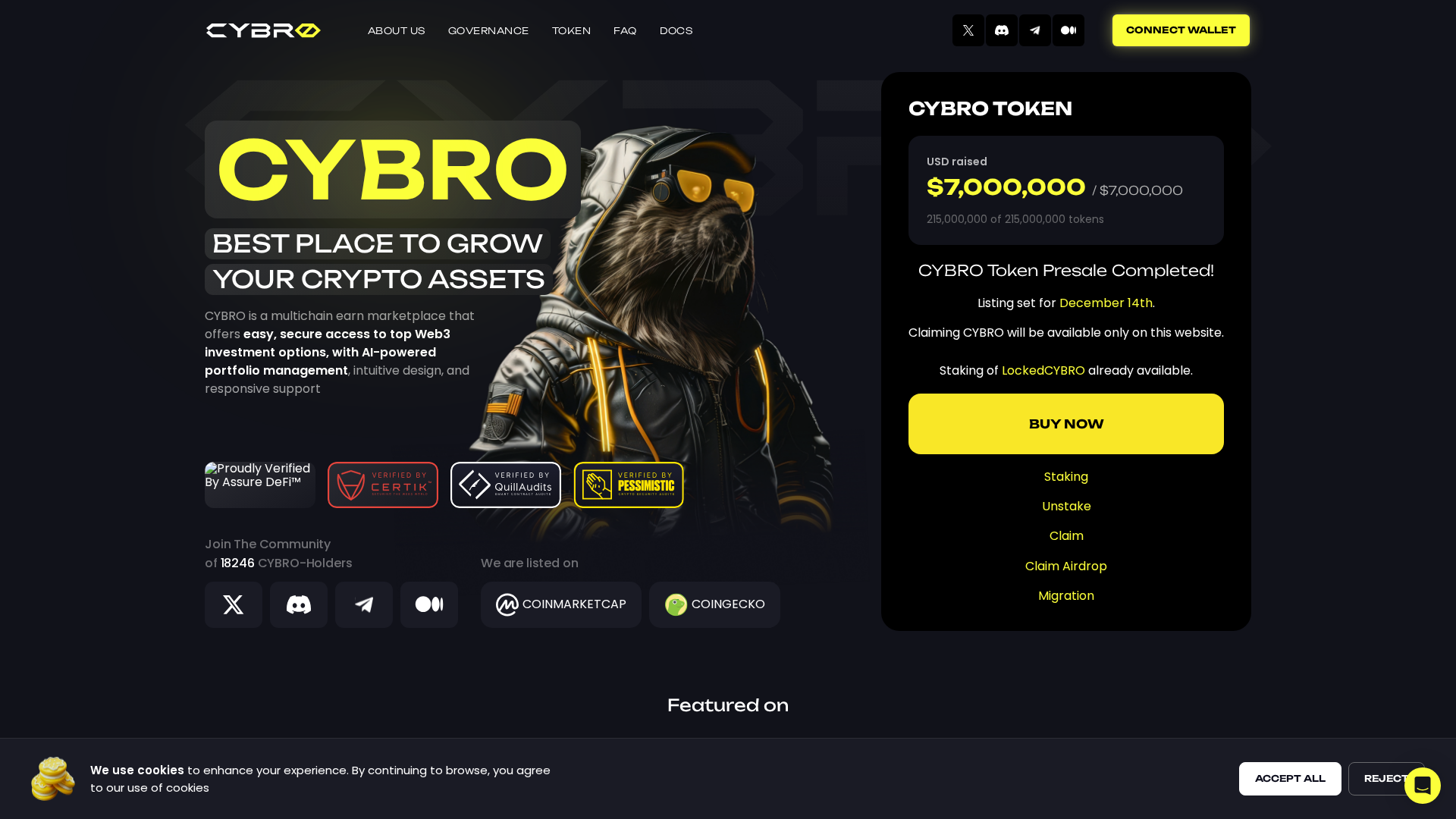
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BEC34CB07145B527123347F770B62B037259510BCA4B0E54B3A8EEAAE7F9C93B4936C9 |
|
CONTENT
ssdeep
|
1536:Wt5c5Wj9wfGXZ1pYTrN8XgWgLx4TESLwsGSMBDLw1j90+1Lmjz4:8Rj9wfCZ1Kh8XgW/TTwsiW16+1/ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c6c4693db43d6994 |
|
VISUAL
aHash
|
0274707636000083 |
|
VISUAL
dHash
|
86c5c5ecec81f403 |
|
VISUAL
wHash
|
62747076767010ff |
|
VISUAL
colorHash
|
3020001a000 |
|
VISUAL
cropResistant
|
b53dca545c093333,0205324d4d320d82,86c5c5ecec81f403 |
Análisis de Código
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAJAAAACQCAYAAADnRuK4AAAAAXNSR0IArs4c6QAAAIRlWElmTU0AKgAAAAgABQESAAMAAAABAAEAAAEaAAUAAAABAAAASgEbAAUAAAABAAAAUgEoAAMAAAABAAIAAIdpAAQAAAABAAAAWgAAAAAAAABIAAAAAQAAAEgAAAABAAOgAQADAAAAAQABAACgAgAEAAAAAQAAAJCgAwAEAAAAAQAAAJAAAAAAzAVniwAAAAlwSFlzAAALEwAACxMBAJqcGAAAAVlpVFh0WE1MOmNvbS5hZG9iZS54bXAAAAAAADx4OnhtcG1ldGEgeG1sbnM6eD0iYWRvYmU6bnM6bWV0YS8iIHg6eG1wdGs9IlhNUCBDb3JlIDYuMC4wIj4KICAgPHJkZjpSREYgeG1sbnM6cmRmPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5LzAyLzIyLXJkZi1zeW50YXgtbnMjIj4KICAgICAgPHJkZjpEZXNjcmlwdGlvbiByZGY6YWJvdXQ9IiIKICAgICAgICAgICAgeG1sbnM6dGlmZj0iaHR0cDovL25zLmFkb2JlLmNvbS90aWZmLzEuMC8iPgogICAgICAgICA8dGlmZjpPcmllbnRhdGlvbj4xPC90aWZmOk9yaWVudGF0aW9uPgogICAgICA8L3JkZjpEZXNjcmlwdGlvbj4KICAgPC9yZGY6UkRGPgo8L3g6eG1wbWV0YT4KGV7hBwAAQABJREFUeAHsvQe8ZVd1379vff296X00oy4hiSKKjMAGGTAGgyk2JKb+USA2xk7sJMR2yN+BOJ//3zZ2HIIDmGAIGOMAxhBcwA5FBBMhAQIkmlCb0XRNf/P6bfl+1z7nvjtFo4LA2OHM7Lf32WfXtX57rbXLOTelH1w/oMAPKPADCvyAAj+gwA8o8AMK/N9Hgcr/fV2+9x73er37RY9KpdK791J+8OQfNAUECa6Kq+MahTNce/3rX1+9r86bxrS4U/Mbf78AeF91/H16/g++wzBVUAQwPvjBD/Ze+MIXdu6DQUOf/vSnGytWrKg3m83It7S01D127Fj7mmuuaZF38Wz5P/CBD9Re8IIXlHTtIq26Z0v/9/1Z2dG/7/3ot7+QArUvfelLlUc/+tHtU9XNl7/85RXbtm3bOjQ0dG6tVtOdQ5rN1Wp1DXlXER6jsBFcA1crCgZ0PcBTmSfNLGmOdLvdQ4T3dDqduzudpbsWF9t37dy5c9ejHvWoY0We8GwPbanTFtVe59T2DKb9+xj+BwEgmQTxg9kwqD3AiMa+ffsuQppc2Wg0Hkf8IwHKBaRZT/ih7jvN6B0AWLdT9ldardaNSK2bNm7ceCv3/TaRps691z8IMD3URMyk+R79hRmCpgogVC1x3XLLLevPP//8J9Tr9acjXZ5YSZVLKtXKybYNsqCXeh2ehXohLB1weoN2zCB5SrsZA7pHuGLCbEwTUSVcOxWSvS7/Uu9btPOz8/Pzf7Njx47PXXHFFQdyS6kJG4ywau6+1GqZ5Qf+d0oBiK4RHEZvWdYNN9ywem5u7mfa7faHkACHeX7SRVyrcG38Ds6rp+t0smvjt9v335X5ynIskMuyrSPqO6kR3BB/GMn0Idtqm8v286g0ygcRWz7+vvb/3jQYItvWeqGiQhwcOXLkCePj4y9H0jwH1bSupDRptVkUEwgGDOgeoqIQIHoWRDk+HbiKBP2YU+9PSmwJyylJSp1ljRFv2TijkXK5LdRZ2lQJMN2D/fSRmZmZ96xatepzRWExOAifZrv1K/s+CyxT4fusYQPNCaIOAGcYov80RvCrUVNXl+ngVLsASU3elezPrEPPoWTy5ROZ3U2Li700v9BLc3O4+RTO+6WllJbaldTpiAwQWO2lRr2SGo1eGh5OaXSkksZGE64S4eEhwFhVS1pHrofiU7doUIApaqXisH0EV6W0hain87mF2YW3jU+N/ynPFyyE/pw0WIj7vrz6nfh+bN0Xv/jFxp133qmN0HrjG9849prXvOYVjcbQP6vXqxfaXrUQnvaDIzv6EpIAJgqYLGGCZ2lmppeOHOumew720v57Utp/sJIOHamkoycq6cRcNS0uVVILqwijJZy55H953wlA5Psq8GwCponhXlo91UvrV3XT5vWdtGVjL21cV0lrV1fSxEQ11WrLoBKMlEdX+u3stx0J+oSxybEnoN5+Hfeff/3Xf/1dJJx1SeC8886rPuYxj+nbeDTr++oqh+X3VaNOIVx9dnb2nyBxfhVCb7eh2hl4tj1UQjHQB0CjdOmk49PdtHNXL33j1mrae6CaDh2vpIVFpQVcJKdSpVbrYYUXpQGYQeBYbnlfhgWU4U5XwLEo1EKKIbFmkRsLtGqo3ktbVnfTxdu66WHn99IF56a0eUM1jY7a1FxRuy2SlEJE5ctB0EMNxyBAIrEssPibY2Nj7yS+XQ6k+7GGVRT3vfOWu/C9q/OsNX39619vXnbZZbAkJWycZ09MTPwHVNXDvdc4RcLUGJ3aNcFIeVJTaWFqLAGaew510649SplKmp2vpg4q6Njxajp8pBoMa8DgLmO/Awr0MyCy5ClBEr7lU2o/zE2ktaaybp/jvGyBYSXVIvLi+Bz1ohqb1Hfplk567GXd9MjLUjrvnBJM1dRFKllWCSb6FjMygOTsLDEpuPnEiRP/Fhvpz70fpI333w/X9w2ABMZ1111XYbW3fdttd5+/dev63x0aaj5HIjHjacEdp8kxHZep6oIag1p7+fDhdrprRy/dubOajgIWGJCGhlJqNnupDgPrqBslz979VcCU81luCYSzAcc0Z0o7mDfCJLKcnL6UMAATQM0sVNLBEwmJBYi2ddKTHtNNj3lESls31cN26iLNVHEDkrBLXzuowADS0lL7I3ffveNfXXjhhXewSl5/8pOf3KP/Sq2/8+v7AkCApwlBQupgIP/y8PDw/4e6GkaUF0TKsxfS9YHTbnfS3r2d9M1vpbTj7lpaalUxcDF0AY02iiIhRjaQCyO4iQ/gjh7LQGqjbjIAB4AEOwJMZD8NVMbxfBA4Z7vvpytYrDlkmSfmqf94ShNDnfTUKzvpR69GQl1YBez1LBkFUiDJjM4mbWetBikWuP4Ns87fiycDNPP+7+r6OwWQG5PsG9VVWbfffvsF52w55x2NocaTBIrqCo41BILLcaKhjoUgcO7e2Uk331JJu/fkEezMSJDIUF0GTpYCTo5cRvS5AGoimVqomH1Io6OD0ghJ4SWTDQaACId/lvsy7SBgyrxlXKThT7SNsmxTG6lzD0A6vtBN11zeTs++ppsecZmSs546gNu8fRxhbqnWlLrYRp/ZvXv3Ky+44ILbVWns77Who1X8nVx/ZwBSFKOupGnn6PHjLxsfHXtbvV4bASDOODQm+2s3dYxdVdWuu9vpyzeltHtXA7VUSUMAx0tiC7TSCaAsgQpV0gdRBlIdxSAYlUYCSWNYo7pkeAkAi+3HEe7H88Bn/fvBdDyIPAPPyzJKsJX5Aty09TAzwf3TvfSjl7fSTz29mx7+sBrtqyNVaT/lRH9ylW1o1IBG8zMzJ35u5cqV7+FxDVqG6if8Pb9s3/f8GjAGG7Oz8/9ldHT4VRIVMS14Qu97ryh3lnTo4FL68hd66Y5v11OtjrgHODJQxpTULcETnSkA5GpQEF8AEXc2aRS2EaAya8nwYDT3JcNPBYbVl88G0/bzn1LWvcXbNlXckZkMpOdc1Uo//cxuOm+baq2G1FWtUVi+Wmg0pBGzvoWFt4+MjLyGaNbAekoo6fc9vaTX9/S67bbbhjAGFz//+a9uecQjLvmz4eHmY9stLZIwkFE0XPxRwrDDnb751aV0yxckYj0NsXjn8y4zq2CeVOR/5On7OS4DiiekifNfRutgxCCQlEY1gHMMabSfqT4aMmyjPrMpYhAc1nWvz0xr88s8+JG2iBvMNyiNynjbpdraT1vYC0nXPnMpPeMa15SQRliIPIo+2ARdvVGvc9TkRk4Y/NQP/dAP7S5py7Pv2WWbvmfXbbf1AE9lcdeuXVetX7/+z9khX9tqtTWeMXElvBIDqQNTD+xeSF/+X8yw9gKccShLS117UagzBekDKBgmMsyPp4vE+uFI4fNTDOtBICnlGoVtJIiOT7sQmbOVzO2DwnoESOkTKEFi5EnpB9MMhM1f5umHiSvDpXF/B0sRDz+nlV71gna64mF1BlEtz9ZoW3EtNRr15uJi6+DBgweevXXr1htKGpcJvtt+kPu7XQnlVxgdTSXPoUOHnjM5MfVnjWa92lpqt2BuQ8oJHtWTE6/bvnwi3fq/oShIqrNNoMHpuTCB4/w2QBQ+jBBMOjtR+MtAKgAVQBJE/Jf4A6pNw7oES50ZnMwTQAcOIAXYzvD+3kAhw603fMNnuB+UND4/9d78ZfmlX5bToO5pZm0HWBD92WcvpWc/za2TBqvmzjRzf6m0BS0bS0ut7omj089fs2HN/ygkkQPT4r+rl834bl998Bw+fPhaFsX+0AW0dqcNeyqs0vAPqtaHamnm2Hz6xqePpkN3VFJzohFg0Qbo5v3QAb8A0SCgCvAIKIGSJRW+YXsZjj9leABIfWkEw2rueyGNVKr3HMwzNZllsX0GU9zZQCPX7u35YBn9MBkGgRRAI8Ln1i3AbwfQT7y0lf7pP26nLZsBkSvq9jL63WvXa2zwsKDKGaRrMa7f9b0CkeT8bl598LCq/Bo69vutJWfnef8qVBZkqHFy9NDdx9Ktf3MoLc3WU32UqWyHlVqO+7h+KIAyiEpfSRSb7PingGkASAEen9PLEkRKK6LgCk7fW0AT0XCrijoTULEAiW10YpbpNqpkHoYpjWx8yXjuAiiD92W4lCJ9IBVp+/eWMxAX+U6976cB1IDD2Vq91kmv/X+W0pVXaBfZd9pvP6ApkKohjdL09PRrpqam3vK9AFGuOup/yP+cBp4lNo7osLz0AHqMnipqa9fXD6S7P3Uo1ZvOr1VjAqUAT4BIsJSSqASRvgTM/pmAFAwSUFQYai78HBY4xgfx+2ASPIIog8qR72q2zD3CVsjho3ll2Xg7YrzXICiM6oPoDM9OSkvik9Kf4b4ElivadcDtKYHdR3rpX/yjxfS0J2ETKaFJpKQiO8o+VZpDjcrRo0dfg7T/roOI+r4711133TV87rnnLtxzz+Fr165d9YeLKu5ML8Aj4xwvKd1xw66049OHU3NyCMaxg01kPkAoaJaBk6VRjutLJOyiZUnEM8osgRS2EShZ9qm8D6blsEDqS6MCSEqg0rmq7SzNoxxuhxw8zO49kiCeyzQYG6CwcwUATgIJ8X1A+fxe0pR5+mmL8vr35DNsewXLbftTuvYZi+mnn8U9e7DtciuEZKZiG6iC1L929erV7yp5QfxDfkm+h/wqROfigQMHnrtu3boPAx4oFx0LyeNelbbPHX97e9p/w+FUnxyGAGz+dAWBw59tL4hSRRRUvQ8OZ/AE6jSoA1zZFzR5ar8sjSIuAFOASnAFwGhKER+SSWkiFYg7GUhZlQkUJY5qrgGQVHEzqLWDh6qsw3ifyVcC4IwAOQNoQjoKiAIYp+brA8ck5h9IZ14N7Ds4HPvcJyyll/1UF4A3TgIRA7SKJEL93vM8ZrwfKXmSW/vQ/X3IAVQuEoL6H9qwYePn6vVGlV1l93Q8tgkzZHIv7fjMN9LRr6C2BA9iuas0wXX6DvGs2mKSFuoMIAkugZOHf7G3CuPdY3WDXgQo2fRFBRCQPwW4SgAVPsM4gGTSCEcWys7Zw49wBlKAiHsBBK9gaI/ZWjUdQa1h1mWQRV0+Kxz3/bBx93VfpOmDpyinBFtZVvncduzAPnvqoxfTP/lH3TSECdBalkQdVrNr7Xaru3//viece+65ny95QzMesqsYPw9NeW5PPO5xj2t98pOf3HbJxZd+emR4eJyFrjbMqLufpX2h5Nn92a+lma/tT80pln9Q7i70VTnfrmjOYdSGqgPoZCUV8qTgBvCDkhw+jiMZLcrVslqi3HCUsQQoWkgL1h5TlwVJtmoZstlVMEZtB3ch7CtaDTq5O3hFAiN8loHonSdrXY/yGuMFoMlJ2gkVnRV5lMMVZcHmZSrx3Henxp363LSnxBkRcUV83BuHs741kyl99Y56OnaYvbRLO0hJKCatGVWc0G4PDw/Vms2h51xzzZPfz2LjEXn07ne/W0w+JJdte0gumOrbEZKuNj0z+7cTY6OPmZ9fbFEBb38Sa01Qdv/1N6eZr+xK1YlRNg01UAs1BGNKKVT6SqN+OODE7Cx8oVXCK/s9qtZ1C9+6Qh0WHK3gCx45nAFkg3C0rYv61JbRZwAHlqia9uIcYkVSmRZrSMSXEqmcrbWY9rsdcow1JDdDSxCV0qKUHpKiH7ausj4CgnP5/vR0cn0wr2XrmHilXYcq6WmPXUwv/2kGG+pfEDkgedwaGRlyy+jG8fHRH3nyk5/cAURo8/xGCkV+RxdVPyRXhd10BGpaPHZ0+q0BnjkMH5ZzlBb2osLm4KGbvp4Wb74jDU2OMdPisUyGcwESZQ19KgGjXx0AUDXSCR9VG0BCnWlYI4cymEireqsaJ4i8l0ZhVxG2LuL7IkLqFmBy903VV1fq2VwkjAdJnPl08eFrBlHIa8Ems80jA1noBDACae3qXlrBEVcXIgWS8aYRTAFQy9ZRXJRJQABEHAnDL++LNINxNK+f13zeu/ejgXDO2l76mxuH0sTYQnrBs9qkkz5KokqDgbw0NjbyuGPHpt+8YsXkP4VXrHQhsHNxeA/+kjTf8VUaaBhsr1i7du075+cWkC357G+oKE53Hb/1jjTzmS+m6uhIZgroEiQyXQUlwzN4iDcu7gfjs30U8TwPEFHFaZJIwgkgyyj8UjqFDWWcLvTlsh9cVrUhpfI0PpNGBgokmSTTlEZkDz/CcLEEib4nHp21CZ4TbI4KpNjHMh+uLM+iRMMgQCJMdB9UPjfZvaQr48v0njDYyYLjK587zxSf0Ywut04vvPbI6HB9//6D127cuK5caDzra9o559n/FsWfPdHZnqpTPUXI67uXXnLxw24qDoIpbeEO0OAAzsLdO9PsX34i9SamUodDdt2QHqQgVRCBEb88iyIbw3MQRBlMgsp0jixVDfeCRYlUGNrmyYAcAFHE5ft4XgKoBFiAiXxFfEYDZBFMuAATkqdkvpJJ20PGUkTEB5MAUoHJ8EO1kc+0M7Nuj1RZjDRTFH1mUAgUnkuTAKv33OQB5oOzg8s82mN7D6f0L182nx51hTNF+iDgyQpvquwALNx6yzevfPTjH/3Nknfx9EH++U5VWIVdPJtXu+CCi/5gdGx4eHZm3neaePGPbnum5eiRVP2vb0orjh9J3YmVqdMYS+3RqXCt4fHUbiKR6u6lChwYgs5Q3If6gqkx9R6UTjxUWjHBh8goMM7X13pt0qnW6gBBqeQ/AVYCauA+gJefsbZMGZYjEuwGYVUdas/7UDOgw0c6j7zLDEEVQCoYmgGEtKSEClw0exy6B4c1JNLkBCcQx7vx2pASaY79LdNaTh5AhU+k8UEHw+GoX5+yBuMDYEVaw+UzC9iwMqU//NOh9CurFtLmjZzWRFnR7qrHZVBlwxc87MI/IOs1Be8UIuR6cJeZH/RVqq4D+w6+dt2GNb8NeIrzPLYHKWGn3/P21LjxutRdxevoiwxB9UGAACLWhlJHEI2uSK3xVak1hj80njoASqbGSUSoExKpZHzB8JBGASIBgGSCayGRBJBGJJIuS6MMkBJQ2Vdymb5wSkTDgib8LLHCZqIfWd3RGf8XAJL53ss8De+4cpJCKmXVJrgEnba8i5Heu350jMVI15PMr+TKYAnSBDf79zzvh6kkh0uDG9/2FWlKIFnfLCDdtKaVXvPypcRELABv28nQGhsfadxzz6HXrl+/9ndKHuYOPPC/kuFBXYo/vjjRuv76L126ecvG93fa3ToSgSZCInuC3dP57KdS8y/+W+qtPydVOLURL98pYz2vwUEciVlpLaT6zNHUPLo3DR3enYaOHUjNuelUQxJVSNtzsQM/GAHwKJywjJDVqg1YH+qjCHNysYpEqiKZctrMwH6ayGNana0NFogFWVE4wnKF+5I5VEuYEvFD+mDjGPYKvggCwuH4Y0kCu5xZ5XzmZ2ZBlyZYAhgbsx+MK+aq1hPqUgpSTtCGwEm+8fEMqRTP8KOm8j6nt6wRzORd90A3dOglFympzenVq8IrlEPjR5797Od96JGPvOKAvHywU/sHq8IqfCxA8LUvvviC32J6ODQzM5elj9MW7J72jjtT48NvR55uoxPIUNof48Xe2Xu8uByaAgU2wMtUX5xO9dmjaejA7azhjKb2+Oq0OLU+LU2sTqo89GKoiRoAkRnmAzKIeBmmFCl8gNTlgGPeV2NVG9CGVFI6hcRxNkfuUrKBkNKucl6neqvwTN/GKqHwoj7ViVcceSdcqjVHOFnys6J/dtXS9KsMLKWyq+7m0eBet4qZ20QvJNI0EknyOMZCmgRoKTPqLXzDJ7mcp5+G8qWjgN1A2X99/RDvps2lKy7txlYM9YKpTgueDV96yYW/RWOfU/ASxtnDB3ZR3QO/yhXNHTt2PP+crds+NDM7Z+WggBFFCzmpkarv/I+pvuNrqTcyxZBluEr1aF7u8KlhR6xpBIThuJeKDHe+SoCdxIq1YFqxAUCtRdWNwRgpjU1E7aU6yuquBBGAokzVW39NiTzaSz2NeaZLgqrL0A8bKsBIGBQIyr5Pnrz+RJzx4SiXThddigESQGJIgs+4L/7g2ZtCWshg7pV+kb4AkjMod3yOYiPN8E4ZjwN0AuFkwNyPe9tVQMEzTaND7fQLL1/ADuNkJ7QSzFyd8bHR2l07dv7U+edv/7OSp/HkAfx5wBKIWUHlZ3/2Z23e2NTUqje4YNVvrYz2tYfrr0uNb3829dacnypL2D1QKzpkLkFmA+mFM4wyPJAAehcAIk3XDShSOXqb0/tTA1U32hhOrcn1aXH1prSIZGpzSFrjtYbECSWHKAgbSvAoYSinpi8wkJC+ZtbpLNI2TPFYN8p2k+/zhaQCWG5QakspUBwdwrpDWl9IzG31iSCyDqK4k9kmVhU5lY9FJbyMstxXmSc81CguU6lKO0ok5LcSaT1rSZOotiMAaYHjGmFrUfggkCyvbEbpl2wo7wWtEnpkqMsbufV03fX19JM/5kAW3bbWMntp1cpVbyD48Te96U2+tMn8h4wP4Ar+PYD06a/+6q+GnvnMZ3Isdc8vbNmy6c3T07O0igUZWl7BrmkfOpCG3vprzFiYWdmUGEH2OFdlB5eHLmEf+cx4CBvPy7i4L/IZDjbCShO50AIBOiOTaXHV5rSwamNqjU5SNM/bztRkbgZNSKEAkMwmrpBISiU3cL3XfMvPCmmDlHLJoYPq69AvDiBH+CRpFfkt07rydNte2B2BAv4SRdit/lUG9QNMpgsH/cCkGt337n02jSQ6zlqS4BGugyCRhpLh3pxpvfRdgD96opde/aI5DupX87qUBULFycmx+u7d+39x69aNv1/yNp7czz/C8X5fr3/966uvetWrEu9yrfip5//0u/layQrVFZfcZcRWU/0Tf5oau2/GikN1qVtoaEkoA8vh5WrLOPoZVwhwbgo5ZKAIQ1goFumKYV7FvmocvycM8ObsiWx4+6IYe0KFIsJXZQCnUB0BMdphXHYx6CSogw/f9M4UQ336nvICkm0WN7eUuvPt1OGwf8+pFw3xFKAbxPnrHGSzB2bHC6mRxVekNS6eF34JiPCRFkoMw24uuxo+MtRD/XB6k6a0uFfl2XfplQPL930a8qwfLtLaP5c+jh5N6bKLW/TbzhYtYbELAF925513vOd1r3vdAjxOvCFcNpN0Z79syv2+SoTu3r33lzdv3vgfjx+biY3SoBSqq7vj22nkPb+a0vhGiK+4pOgzuL7E4ZkjKA8tmmLYiyEc8fG8jC/ioJz5I2n4hDE6Ij1gVjq1J9akhXXb0uLKdaldQxLCbJcElDhKsazKZBYQ04X0wT7Az/faQTju26otX60pXIu4VqcGQ3EuYCKZEscmKsPNVNX3HTaa7AJiCRD5VaUZ2kbRztzLwEAR7ANDhmT7iJaSz30uD/2fYEHQV6TFuJf4tqxw1jV4b3xxH2m51zA/xNcbX/SsufTIy3v5SGzGUXtqxXh91659/+Kcczb9XsnjqOR+/LG99+tS+uCUWGNHDh374ujY2Pm8l0QzHbN0ANf48FtT487rU2+YlSznunb2LG4QSKVIHkw/+DzkjoSxPMldgMf0PssuAyTAS/2uLy1u2I5628DO/FBWbTR0WbVlwPRVWgEgwdIHkiCKe0DE5w0NtwCV/lKXhVLApDNOlVcBRPWxemqMsGvnSQCaKpB0qjQ0Y1zLQFLeRqciXoaEBMHPQEKYAiCn/i3aLpAESzDObGVW/Ciz8E1Tulg5J16basV4m6Mfc6yyOECsrNcdGR6pzs3P3b5q1dRjiZmFzx2cT+/zinbcZyoSlFb6nXfu+Cfbztn2jukTJ7LtYyswYnt3fj2Nvv91LHBsATycex7oWHTS+1OdTSSuDxTuSyIMpu0/j7S2lmaX+SxCLpVsEFga0eLatiGVOqx8L2w8NwNJicSrqGHvhDSSIYXkKaSREkcACRKdafVDEgV46lkCEW4JIoDVwgWQBBRxGuB1QNRk5jM0ihEPAARRDDclEcGTriKiZEjplyAqbSO7Psu6kWpNaRTpCt9wOP44qktVZj3S1WdHODHw1CfM8vYrXzMBUKHNtIV4+Wzn3Ttfed552/+w5LX57usqxsPZk2md8w62iZoTYxOv4msZUsD20CqYxcvmQ1/5JBulTK1jO5toCaIj1ZlAUT5T8sSiXTC+yGfxQe2ogCIsKFcZlZbUyJE5UwGiqJjnsD1WkHvNZqotzabxO76Shg+sTPObzmMpYB3rMdgUvFUU0ghd4XpQOEgf9hKgAloRVrVFmPsKoKxUaSDzhggXHY0+xOF8VA/NVVoszfLtID5s5XvTQ2PYNJMsImKeCQqb2++i/Siv3NXyTvKxcJPzOCV3pjYMjZdov3XEZR7cYFbLLwFUglCVuJEPAd51N2tD2+c4702vyGTSDmpe3lLSHwEgeHb/ZmT3C0B+55iPGy3ddNPNTx0eHb2KDz5xUoDhB6M4fJvat92auh99f+pccHFqjC2m2rDFZgoJhBJMZwSSFJIQlhWEyHBhOplBZKYg1LKoD0JBoXLGab4gGGnFtYTTFjLS0lxkFEj1+RNp4ts3pWEANL8ZILE350otm0RMq1k4BCgaxINA8uAaMXynNybslF2AKO4BkTWWK+SCS2BZN43ypSV1vtJins/OzOIafIGayWIamQDACEMZqKAcvIii7TlG8njpO+13EZL5QRwf8U2NmMKYtkhfpo0MxY208bF1+drS0RP1tHtflQVGFk89sYWAnJ2d6Q6PjFz11Zu++sOPuPIRn/SjVmRxcfis1/0CEB85kg4tzta+eGx0GGt+yaUVpSSmDms/138m9U4spfndc2mB73HXeaersWIoNSYwLJtmNSGOHkjb6M2gL3UkYsQJAYKEZb9xAQsiIi+zEZ9HrOnzTYCvBFGOzOkiL4kCUOiBHrqkMX2ImduhtLhuKxJpWyxKVjkRxok4JNOpQBIUQqiURgWQCkAZX0F9LUsojV9BpSTKfsz4kEKSoLXIbIizzMd5swLNGlIpVjzoyyCQoq92s7yCHvSM/rqarTTygxAuE1B90CnoZ5DnBVki4GAMQBeRddLfcXczbdsyT3k5kjWhLhut1TXrNryEIj5Z8rys/t78grv39jglPzf3rGc9q8tC09ZHPuLK3+WzK6M4Wgkn2afqHTyQun/8ppSm1jDLgGDIyy62devoEm4hddjhkBh8nASHKlCZ2x+r9M+gK+OMNk2RqPAG8vjwlKzlfSQ2bwZicZvzQuGQGE5JaEd9+gjT/wPRpu4Y2yROyVl6iLxk1CQP5he+eSMOX46V4SizrN+04U5uX9mOrE5IAZcXOOYxOx1mWiwHxOIjJQd5owZqEVi4k3zIb5yWhKgMWgmkopI+7WxT6Uga9OReAJ2YraW1q5bSFCcFnO8IJHbrLWHz9u3n/Hc0znF4X/XnIYi71+s+JRDf7hFkS898+rOeOjU1uQZk+jXUvHCIuJ/75lfTyCKLhxselrqL84hrpst1AcZ/wi1s7dbxVlpgelsfZ/RPokrGWPHltYJQMKSJNRWJoUyzuXbDe5xvQ0QPym4YR0zcmi4S85eIICC+z70yQWFoBEwcGXjg6gOpmCO76TrGBKB5aH+aP+eCtDi+QoMAtYZ4p38VNLUSyH0xAVOqMiVPS3WmBNLBdW2jkFTeQ6QqceYJJ6CNw7m/5hd/q9DE5aQ51mdmj/dQa6i3KeiEaqOIAEnRlezlbtk1ysiOV+hYgWcGjKuiHn1AFbEnF731XsejTA8Chrm5e08Dm4idAlvIQhEf+GzD47VPecqPPY3Id8J7W0LJ937dF4AqN954o2ytjI6PPdfW2TibU2EhrzU3l37jbz+aOG+YfnjhULqAqfLGoWYaq6C6AAYf7gZQGLM6KNVi2ag1zevwjPQab582UHX10azmYo0EovXBZO8LQBnM9WaiSdyIi+c0iHtjBFEQ0FvCAaRob9zmexOEM00MvdSjzY3ZY6n+jS+m5sbtaW7jOandaHJSALVG4fF6UQBIsMRJJD7knEETzw3jMmBMg6PB8UwfG0ngCCTfy7VdNr1NmRAypvdyaR5pNMeKcQAJg1uJBBn7fY+uFP0heVxUGypNKdLAIGogSC3cfHaz7K23EUWEzzzksOeeJpJoMT5ZHNLMBOSYmph8DoF3lbwvsvrwtOusKkz19ZKXvKT7zne+c/ull172H9hHGuGkP7TpVvglm3THjtvTz7/359MXJrenP53bn94+fyR9e2kmHekusexfScMsXoyxwDZMa6sqbFRYTwvQTiwxwqeX0tKxxdSeZYUXsIW45bmLcXEA3t4XVwQH7kvilM+znxMsp4UiIbeXCWk6n+eUMtMw6ZyiMCjqxw6l5rEjGCfDqcPHoDMYBAXpQi0u51m+z6AoyxIo0Rf9cGWdACfKKO7JYJ48UnITvEeQp3nUm0z1MzdOtUsgyWMHUziel2GfexAC0gcgXXPymVe0y7p0RYSWxNxCNa2cbKXVK+CFCEZGwWP421t36cMu+eC11157BAw4Ay9KMs3J131JoFBfVz326qvHxyZWYqlbDe935UJu+uaX6W1Kj2FtZbEzFCb7X7Tm018AonRib9rGgbEXDE+mq9jWuGR4LG0YHkqyxL0qpCXrfUompBRgas8v8GQ+VJvSqc5XKGp87s23VWMzx5pxhfJCqkEMHjkCHchZCi33U2mU75bjbHUQMEpRieW7HM+uP4UqjWqLc2n8m19BGm1Ns5u2F9KILQBVj2pNCaMkUrIooQZcKaFUadVq7Oln6eO96SBebKHQBsMefw/AUZ5flLVF2pKh2vhOkMsAo8zY/DaSDzULMv2LtpfMsFVECQTfdnHJgD3nLInsYJQMLUgjbQSTY2bvgWY6d8tc8Zxfqmm1OxMTkyuvuurqq4m8E3dWNXY2AFXWzq6VNWl8cuIpvKNGw20tHaZmpvLpU1+5LqVVY+loewHWS4iUzkcXDTmSaelBCPw7sxzQneHL3kwXXjY0kZ48NpUezgbolrHhNGYOFjOWAkwwEDB16XzneJZMGuQ1VkxrwxlMNXbmA1DEByGlcm5Spk8QyRbnSxIHffuB8kmRPG4pI/JJWYLYRAFY9MfQvp1IpCNpbtuFaWFyFYfiMLADGKoxpIvrQyBY2yeDKvsZEICFtNpwodq0jwoQ1UrgkRdT3s+LFSrP5QLtrdxO8wqIGWZs82yqOv1v8LkbH1NEXMo4I6LpxAgMN3c7R7MqdP1J6RSECG7CCtKEdGOZ4Z4jdY6PsL0w6u59LpKz0xz9mHgKd+8tMGDxRasiTf/PvQKIpezKW/7qLRa5km8YPX5hYVEA0SU/pl1Pd++9O33wm3+cLlz5qLTAhmbRNgQS75CTSEmBmk0XM21u8m8BIr1nYTq9Zw71AAB/EjD9GEdYr2Quu21sJE0IdMCkZIoXWe0hAGkvsSURZ9UgDtKoxrJAje2CGuqxppFAnCMpCEr6AEy/e5mgyyDygT04mR7lnb4MsO2OlZ51LM2niW8hjTadk2Y3Yhux91Vh4VQbMIxrGQ6HTjKgQ0IBdn1BgyTK/jKIsjTyRBMA6wOJMjHalVsa/h5405fhbT4tMM3X9ZsjLCS6hoRusM/B1aC3fcuX8WA7dY87HnL6EmEUF923nwr32YVaOnwMwIxxzIWHwLMqr+vwnJQrwcCstCin+0UVfe9eAfSkJz3Jva/WX//1py6q1SoXLizEmgFn3p3mVtJtO27jvEFKw2uaac6zNf0iM3u8F33UnmZyN9MFKOYRAOWI++jSXProAj3kYwVP4Rz0s8dWpscinbaPjmYwod58qbXtFzBhQkVwAKoWO+NL7IoHHQQUUkkwcUQTRsEAqSJVJa5DLyg80LgIGmkJy/5y+4s4IioY2Z6H9uDZ8N4dqX78aJo9B2k0PpVqAN33KPsqja0OgVBKo6zWivUhQRQgWfZdKe+rQH71qUyv7wZunv05S8sdkFGqqBa2UWu+x1fbABNbJHYjJIz9yklz90sQYZS7r61Kc/UiAASJ+E8dkonP1xxqpG2bXG6xP6kir/k+5YXy/ulP/9Eb2Z3XlKGU0697BVB5ZHXLli2PmpiYqjp9pwZ/AIRFrHb66m0c2eBcb0uRfx8XfYxrga4pibzOQ9WNIskc7Z9sLaZPHtnFRs2uDKZxwbQibVcy9ThgD4gEU0cwNRzVlAGgMOhTR8kY9pOj0hkNYMJo52OmjDAYgXgKe4gs1uX/fPUD3NrC5fuyvTkaCUGblUb1hZk0eeuXU2PTuWl23eacDaArDlQsIZGURgNAYlJegCNLn1qoMs43IiYElUCKDRVWAwNUA+kFkosHin16bpcpG6ZT5cIxtjM4LzTkb3IgvEMa+bzsCYGIYwCEQY4kGgVE5aKl48zLRc97jtXjNKQAc6xSB+eEJuubNm16FEluKLEQGU75c28Aqowc4CdpuPjo92MsMQxMCKl+nOHczfW338jryVtCfUXCUwq+r1vfY1+kPPOeB+xHObLqFWA6DJhwzxieSM/mbY3HIJm2jg+nUcDU5iyOYOqGPUJuFkIElEsFsWTAFGZhYY5yBZSfy1U6MU0PQCER5ACXOM6AKqgesf7xeW5XPCd95GDtqBfSrZpGdt2eGieOppkt56dFpGeoNAZEXxoBhVBZSh0dkjdLmAwiPzKfJZLKChcSyDDPwwkc8pA3pBF3qjKXBpQYAinsGNTa/CEW5ZBEzbEsVgRXtF/SEHKshXHNmyDudwki9+PoYjgBdGymlmYB4wre83c85PzVNDYy8mjv+BKsJMiEMWLgOiOA1HlveMMbTDbaqNUvb/tlbmhqvKP60JFD6brdH08XrnhUmkd9PdjLFnmVYLJPgmkEMPnsY9gfHzu4AzBV0z9mJvcMwPTIscm0kdncMMRYKsCkaosP/weQADu+r/W2kY58gDL1Fmcpj5EKoBrMDJsAqlkCSk4EY+xiBg5V9y/bUQIphjQs7DE7rJ04gjQ6keYA0TznjrR23VdzgTCm90g+wRDGNVz1MzWxVhSAKsDCvNs0NQGFxRhhAQV4sooTSNnx9hthTw0oETM4BBWtSR0mvfPzfOJFaTSECU98qG8ab/sFEIIP6ZKNa2d1w37xlnJYMeGYBz8BwW7VyimVTAwYZmNsSdWbl5N99DOf+Yx7n/3B1ycOAXXbadc3vvGN2lve8pbECbUNV131+H9NzjE3FSmk4ndovn7b19N//+T70saV56RFFx4egsuO6hw1GuJzuLWAaTOMXg1or1taSB+ZOZzeNn2YDqujq/zcUjONe/4GyeAiPNtD6HiIFz5s799nQrdg2AIzxtnWXJphuWGeV4qMs+Y6ddVVd2V+Yk+7yumRbAOMErVxeH+qt1j3Gp9kjQupQXkKOVqR3WC4jCv8vCaU08XMTbU2kMZwvgcAZR4aJYttSjwXUGHMACRApNHsKj/iUOQHIASFMzMBI4g0yH0W20u0z321VROdtGEN63Fa39KNv7y02RwZHXrfb/zGb0yDiYQj+uSr0IQnR/78z/88RaTOk57wpC00dW3LVxttBcV6EHvnvrttPddp5Z1c0HdwZ/FKpmMQ9QQ9Px81cAVb2Rcwkt88cyQ9d++t6Sd3fTO948ie9I3OfOrwncURAFVHOnQJd5itdVm4xLZFyyGNKNBlf7cn2kidBQzk4+35tH/hcLprZl+6Y2Z/2s0McRpw+cZrnTQ1pRPMcZSXf3Of6bcqDcnRdUZ4ZG8av53jIrRLptT53d9wVf1WanLfCJ9wdanvGvw8yFBlgWWPRdJkP+4ri2kYNxTPeTGw8IfIO8Tp+yblDjGzayLNGoUz3NS+4jenOkfmOXqrUSxwBE12Lgl4AnmJHfgTnAuawY5q8TV80xw+zuzPsSRPySjPOey69glggMhOgQkTnHSdUYUdPLhO/rVXrFm7nZOHFX7j01U2YU0DWnxKZCcfxqFREJrq4hJxOq8yLt89NH/z8oAjMqWLkErDWI77AcG/Ob6f2eD+9MLmePqJkRXp4bw6vZqZmSKchdYAjmLNDeBMyAwFW65ot0TV3Xx3IR1hAbGHRh7inMUk76StbI6lCdRpAwkYKpF0fkFE0ZblBsAirueIR6IN3/mVVF23PS2u3RprSegBpJGvXJO6VGk0IttFShuWKFBXeYqPklKlaS/Rr5pGNX6cgsT3xGMdpypTwbleFAoQcef0W9MlHE2xn50TTFmwFTlUzUzSkUOPSSuPYFssvs7w5odbR5hxocKYWMZMjb4iiCsdeF9bAwbI8jkwcUasnDFy7dp75BOHuke2+5sNECkwoXhf4DWdAzM706Xr1qdJNk0b/EqOP7q2REN856gET4ApWrscZ5nfyVUU118acFX7Ydgzxn8ABn5gcSaWCf5VcyI9YWgybWNvzkVNTlCgqmA0bcwgkp6IfBobQCJ/EB9Cez8Pig4KpqVDaaw2nNY0JtJaNpkmsJ80h5E95DWHQKJ/MLiLtJJRtQO3paHZI2lp44Wpw1pXBlG2bvK0X+DgBAvStIrUcOXHk40VV64FDs9KmGC1FWEWHAkZ31HdAqY4dsvUWyChOHMfaFBssNonXiXvol7bfhGFvb0QNbQ41Lx9x82wQKkUUn37DchxXikKgNEreT8yMryNolKJCcOD15kA5AcTgv/YO4ovKRSEcp1lnhnOgdkdafXoGjrj594gB7T0I48t9O9iOBjGfcCOkkQjbe0jKcLeP8jLxukYMOl40TZXwEdYLff+NxY4Pb54NL2wPpp+HCBdijQZ55mn+JZgjrMRFXIGEWCgdQIn+xCWZx7U1z+CZNrHuYsKKFxZG0tbmlNpQ308DSMpXM9qQW2h5BUmM3uEiT3B+p1f4NXQC1NlalPAzJ8BicVHV68BjVsesty1IIGBHAnwtEMK5XAVUOW1aWVO4ZRogocY3cmSSGhaUgaH6jvsNM6MtHjpYQlR4/v/HoBTgoYwLZizfy8ffWAmNjHGM4gTQwNGNWrNwECBCcl+EvvOBCBp4cXMt7ZB0W8OG2KxcxBzuv3NNNW8kFlOCzGLKcczfz4SEySNOrKh6JJAAtk6R38UYvVcJ7XCwomgiAd1WZauXAGXHpfAXOM+gMH8AWyaK1B5L0SKXIlKWs2ioOCZp00ePQlxr08DbGYAief6AsOTc56Edxf97s50um3+WBqvcCS0uSptB0zjqDsZtiSQ7IQ+Rr3h3t6vpt7MIdTaRRThF9mAvAwUMKVaowH9xUfCDlJBFIDC1lEi6TqAqUY7VG198ABy6Z9feCylUAZRgJlSch/gD8d6h9qLaY69yRaS1NTRXIjh/sJxZmEzM83ehvVzzLahojSgL3wRZiPdc1PhjNdpAHr9619f4feoTNxkmrjGE4dUFFP4EkCL6RgfdIRJ6HhhlRtChbQ2W/voVYzJMd9pgrohldimYNYdoz6wUgBGTyefiijrztdAxECwfHqaTxFRxoloVd6XG4bIe2ng/4tESkvH0y/CyKuwkzZgQ7EqmuYwhPkeDW3PIMqjN0sjw9ov+qqtPHr5XjRw2rm4J85BXdJYlS4aWgEwR2QJa1tBr2hbl93MzsweDtgBorWXcR5qfdg70jSm+7DRd+m0gfJWCMBBusTUXfsnJFBWUB3A1BFMqrBC+qjQIgwoM4joRwBK4OhKMEEXTkf0UM1D8wfTHINptoERC8GUgF1+g6PdWUA67yDTJnpBj9FztpO1NH/fvgkmumIDdxIrTgOQPb/55ptN1GQzc6rjOjhFFmYQNtCcC6+8ZoICg/CKu+yyyhJMJYicMnoInE8WozbQtbSrlEpx8AzAWZFlBwgJx0Wk8XawvEpwxH08LJ8UaZdv+9lCKhHvEZl1jF5Xwt/MXoDuRRjHTwBIm1wPggFLACUkEg0RCLqwdcirLxWyy4Cq807YLCz6VGt/+mzrnnR5fWV65NCatJZyta0WAUD0idHeYca2uP+GVOXYy8iqi6CJX6b1UJsMVqVlECl9skojNqRRNqL9ZlJeD1JhFQAaUGWWkUGFT19iMxW+6JeSKHgEEYlKzdbhNNKdT8cafLACiUwwnXfpH/MxMGrvbiMF636WCe8RGiu4aYKJ+e3btxM8+ToNQJzIL9/A4AckK2P+rgWEACU544KzDQSaKitH21BBIJAKIIQkMm4ATIyAJvHDvLarfaS9pJpjrzRUXpZeOU8PZpq3vMog0fmSEOVDfG7jGowrE/iMatm2K2ZwSCTTvQ/1pvsJJNETsZE2+U4XqkcbSdvGBbs+cCJcAEigkb/NyBVkjUK9fap1MF3XOpQe31iTHjO0Oq1BInl6cQHwuLTSq4+k+RN38nLggTSx6nJ+xXlDSGMXO2VWto+kqOEMiZBGAaQsYZyR5RmaBjQSqZBA2QzPICpy8gwgKVkFkbyJwZ7pprHf7B1Po+0T6dDctrTq4X+bJta/EiP6vfSuL0HBbVCUDas0xH7Y/GMf+9iS1ETlS5PhpIvXlr3vvehFL8KiScNdCGq18U9CsvI8whON53AAqRkug0pgNVBfzXiu73MarI8kUhqNslo6zjtTk6O1NDXqgiBbGcQPR1ryA7Y6znUYl2L6jtYahhbLcUX4pDhaXKYzXkdx4c9DIt0FjPaLcH+JHfdrGN3vXjyWvkXf+KFnfl+S2Sa+6WL/jrwL5oMK2XXDd7FzBoLrN7G7FM0fbh1I/2HmW+kv53ano11UBnFeLSUSIGoTt//g36a9h25ihGOXANo6apTzncyEivUj15EIN1nzacS6ET5rQU3Whhq4euEbbrCGFD7hZqwn6bteZPrCDYZdj6rxTSZmfEN0ctslH0xrtrwa++wKAD2PDCiGIX6xTDP07Ge/oMmXWHylPfoy+Oc0CVQ+XL15M88qjWwY5ljLbrPyLIDYWwyOlJInUM5zG6A0ydKolE7eG1ay4CuhEFsa203UnLOiUiqp5rSbfGY6B4H18j98F/YcpxFjZHENBGlXGVvkWb7th7TezHM+iV2F/hyS4FNLJ9KTAMIjUDGrGaWKfzc6EZRZGlH3cji3zXL6qo2GTiCRXAB969Le9D+QSs8dWpeuHF7FulWd5QdOFwTSR/lJ8DvSocVdad3k5Wnd6DYGDPmURrSFBTwkDRIlZmyGlSvMx/QBYrzgCOSUVqo24WdISaQLw5oy+H10aJ5VmjTLs0s7w8sQqo1HfDJVN/8uNtBl1PsN7SBJIp1dsSENFOArrxdcsEWcxDOfD16nAYjl6iD/1NBQDPwAAjmCif5htPj1KyWKujurLytTXekQlwQyYMxnOD8zTRkO0Uq6DCSkDkjpAEqXA8olATf2+mCijDKvHbB8aLLcK55HfPb4W0REb3JkAM9CBi6JKsO3ygqe3QyDPtOaAUiNdD720ZhM4HlWWYCGvCVg3DpR3fVVXTzL0/pNzM4Yz+mfze9OT1s8lJ4/sj5dwkE6T/QuAqQe60soy3T7sc+lPXN3pW0Tl6c1gM0tmQAS7YnFRwBQBUj5fTXUJuF2rBdh+IbBLJAETgkg/ABgjsvA8Zl8oMwW9tfodGpf8FcprX4/a2MPAyT0ino7vTjOGtSRSgWpqkNgwcgSG5Gg+HMagIp4ipMFFNMvKQJhQHPKAlVEp1ixspKYwQSAyFEAqe+HxClBtGwnZSmVAReSBjApifwUm34bW0nwlIDKQBJwjqqBZtlOG+GQKdscoXxfRC57RbqI4I+9Kq82bV3LzTqo+U2YfCuG7kVIpPUMFH+kVAkq4LSPMpAEzwCginAY4KSx7McBpDt4V+7Vs3el5y9OpGeOrePFg1GeCR9PN0ykYxjhew9/LK0fuShdOH4pJ/hWhkEfQKJNYR8JJJ3/iGsD9CoLPcgjysEHNPm72SWQWNykH/nbSICsizFPfTMbbk6Lm/80VYd38WbuZegYZKwTArZA5jRISSM9pZ49MFy87jNAUB4W170BiJ83mlWQAIeCyDKNhtfZROTYcNg5GhoBhAI0wVwzkU5Q+WYG/xk9Asf8uYzs2ziZYhzpBAY3qi4X+ARO7N2Ez33EQbgAWU7TL9PuWk50Kvczh4tennRTxJ30yARFvkjLh5e4t/w7AdJe2rYOBnFwA/bleiR1SCZ8QUSzAhABLDLq66ZJxbhPl1eH0p+159KfHbszvYqPTzyer62NsuWygNpiixpbpp52LHwr3bZwazp/5PJ08diFaUV9RUzz/f1UN301jKV5HDYLMKnSBJSGf15yJAG1ZqlU55hIBcfntNKx0TvToVWf4/29T7C3thVFsgVJtsQ5IAx93IGZO9LWKaHJSKEvBHJHYQ3Hl4MqxJx23RuAKrt27WagYWFGQYFFCmTJm1kLGMLJfKqjyECZSLB/BVhKhlhjn9E2jJtl6UO5JfiIj3ABoJBCJXjwB6VRBpggykCyauso68qh4v5ebwYfZPAYk4vJ95Y5RQ8FxwEad5T+un1SEs20gqgEixKlDEsTn0Xb8FVnHqLz56z+K2tSf7E0nV46tiadPwossa2c9terLDZSz01zX0g3zX81XTh8KW47SwNr2KLhEI8goQ0xmEjXJl/+zRA2PCg/Bi7PleLsq6eZ2rF0qLEv7R9F6ozdyORllDNVF/ICRJuN5Nk0N9MKSeYRF/uK73pfWJk0OYQ6hnTrzjvvdIwsE4mb8ippUd77FY4eJ9Eqf/7nH1z6nTf+9qL7NxZugXqe9EOiR+FOMARSWFwAt6whkpse6gmWrOIyMUtJE2AhTQZT7rxx1lVKMJ/FdgMc1Mj2569LlRYA43mWVEXZZI622lwbccp1hqhTUhS3AwkN+r0IxnIAaSY6RE+pAErHZV00JTtu8trLcltMJG20tbwuxL5yNvfbMwfSjy6eSE+cWMHKPm+2ACKlxUiVr4kgz26c/1L6zNznWRLYkLY3tqZNjfVpVW1FGq2OYfizmozBrnqzWFf758h9nJIP14+le+p70pHmHZyk3MdhvRXsnW1MJ1jJPdRjnw5pZiudHQ+xxSP/bBnCIbMwiEdQ3nd7ix//+MdbYkJsRAcG/pwGIJ/xKnN6+9vfzup8b9b3xbmiSKXHMB8Gn+Ck/6THJmKFm8oLoMhs1w6yLQMBzRl/y3qzbrXEeBrRhgiUSSKPAEUFKq5JrK/U812zUwEUQBJY1O3Is402tij6pGKjE0X5Z/Kip9G2wafRuihQYjkAlEixKIq4UQrm/pCkrPekWpfLivL549KAZV3CYLyBpYPrOFHwAk5fXsDXTVi8ZVsEyUCaseqkPzbCftx0umP+Br79zDkoco5XxtIobrgyQt0ugmK/UOpM9TjLD8dYo+uwxQLQllZg56xOR2usGdXuwX5Vg7CkgmvgWPRmaQE1yOTFQTLc5NWMYlzQTH89h/52eWcjLYkJfgVxuTNF6DQA8Tprb8YtWjLxktnxLIFkB+CASezQp9Urz6Ub7uK6WgkRS85IwHD+MYt/9PlfgMsyjBX1oQqD/EHaIm+RFcacadpfqrY+kEjXYe2pjC+n/2X1A03IBUeDcqOEc665H3mGgKMzWkz7CEl0bv1mRJO+z7vfB6JMcdpl4TzIYzADzTQRzR+l0CbEuc8/hCR6GOeTHj0yzjGSJk9Ua7zJS2VupK4CECv55+LkEpLqBHzl9BLySkXpehlT+S6vSlU5qw1NFqHzUnOJtTTXigAMNKqxNhfLUux98XooZXEx+Hypczf7z5ULOKZIW6Kflko+DGjefEhLnJGuIIV6xWd+zBnXaQBiryO98Y1v9GGLzIedPko3e2nBTXaka5VVAEJtLynoAESKSgUHIj5UEWFfcPP1ZomrqhtCavl7Vn5XsGxoaATzUchy2JFunCCi7ABTjjM+bB/KdjW7RfmqtkEVV5YTeak9t49GcNmWfEmpMnxfvv00eeHbJmwNfw/DRdR59vl4UWR5IA0UdxJ4crfjqfGWJiOF8UWsA7kg+TE+sv6wdjOdMzQM851RudrlwQMAADW0SURBVFtPn0snncgXPw2KTZSVkXW7Mo6kwSi3vCrrAVU/3WIaWWX7AI7SXDM7ekNZ0t1FxYO87THCMRjv4ymPXI9CiPBiX3yZpfLa1742ng3+OQ1APOzxGRfTcCy2fcCOWqidtRsN3uBvVNcinjilTeOULHHOBkaG+pKZEFTw8GOFaYoflRvme0E1CG05YbPIdFAQ6ckvFgVGOJljmcEk68QVYW9UbUjfeBPB136HncpCUUHET6fjMqgkWgAJRkd+M+f/9i3iImC4DAz4ub+ZyUZHmiIhrYv8dcr2yISDogmY5jiM5rko64tLn4IsK64i7L0SOOL5A08DCE3i1nKzk03q/Ri65/Ltpcl6ZpFF5X7YFmjFjUOzdMaVVzyHJmg2iICjTARUrsjKcGDTRsRg9r21FcNreA2d4x4x+nMd8r611ObEXmqDCZeOlyvhxutMAOKANi8ekXhhfn6PDS0vC29Uh1ki38Bh+m/CeH73C8b5irL+0mI+azMy2kgTfIVjaNh9pwyoFkZDG+aGfWR6baVTwCPArI7oAlA0gnB2uR0RLhpkjPf0M0Q0v5zO70LQ6Tjk5kuKuY5+GeazvEHfcHGZ7v5cSh8v+2Ye7aIGRsQQIJpdZPuDegWv8xmvnDr4FXfey5xwZdhU/Kco1FAG/e2cA1/JTvk6VJpHbC2tBE7UnVsQ8VETecvKLFtRgxDJjvt+2DgS5PqZ2bG7MDV0cS8AZMOLy7oWF+f2cNsrMFE+6vtnBFAx76+cmJ6+2995t65gAnCusZ4xXNmYDrb+NwgHQIz6lm+P4o8CnJWrhwM4HgVYYn1hiWeDIIswz7KEkNCQQiDhlCICy0vVKSBUffEp3dzbeGaKzLjlfOVsTMKyvEI+xC9jJlQcZcrk3IecOddiOP5Huf4xzalXRPXjcyDHZaZGuUTEPiAgmgdE877vX9Q5WJ7d8NJAjdzhy1Ac8f3nMNklg1lk005eIliFwT2K0Wi9MtZ/Sh/vS6CG+inKIzr3zbQkOsnZLtSZlammFjvH0saJR2tEQ6cMIIuR9zMnZu+mpMq9rQWdEUB33XVXCL79B/fdfd7s+TJTAUhLWCRnZXWsthlg7Ej17pYAjyJ8w6bRNLmClwDJucC3lEuJ41sC2kGdkD5ZUgmSUFek9TVmQeXsg99DS8MjdX5qA4MQlZenl6Z1lOuj9ghLqOznsMQp04Q9NKDKAojmjTolvh0xH38GrtPufVak7SeL+wIBPi4y6enADrMcNo2RRhyXAkTaZvkZj/pXWUKpxkrQ6JcgKuPygV0+FM6S3BzG8zis0ISEDFFnVmHcFNKu37GiTUrLGKDWXlbMbr/mh+/TaUvNLu1MGyaez/YU7915zAQ7gex+9q63d8+eXeSsFpiwlJOuMwJocXHR9jWvu+4Te6567OMP8qOta/n4kPSKLk40NsF0d4VTWgFo1mzgpT8+GuVoX5zHrCsYpnTK4CmBo91D23keag+mah9NrB1KI3waVzvJ0RXfFQq1qKQSLIOuYAjp+iCyS3aZ9iixlD6YD+TlGCttcLU13j6gHJPZDTtj+ExXRBfPyiRl2tI3XxnWz2UCIOpgaQXpyeIeU+SFABFtNU2kMyMuKFnwtAwP+JafAUUkl2vLgmWamdkQYdelltWZRVpoUV7xTCEjjcJq1ueKNpsUc8RB6zEPX3HaMLWdZDUw5VdIWL+u1yvzS0uH/vqTn1CF1cDEGd/fOhOAesz3u9dee231ne985+F/+Uu/tqMx2QgA5QZ00uTweo5ebOf3QXkZbTWfbOHLY8F43z+koWHf9CXPMnh8Fq8jA4pS3QkcO68KDKkVwMmqLEsVpQ4M0Cim98EECYMTiJkWRXwQqKAURJQBw3zNwtOTSiaBpLO8TOrMHO/OellX1IRfJA4AUofR0SYLIOAiqMZ1nT4KZG0jbSJVrNVadxRRlGMRuRUCRrWmn1ujXz4zJj9FqlGPSyeqBRsQ3eFe0yzy4KMBIz6+8KYUIsKamQMb8H+U7SzQSciGlVssrLz4la1Gmp5u7fiTP/lvh8SCmOBh2eoy3ZmNaD8o9Fu/9Vsmmp1bWPjm2lrtsTDP9jmt4+zOqrR2xZVpdMU0n37BwENyKLSy5FHKlK4EAs+oWuKpnlavGQl1p+5eXGD1VUmligM85UJkVjk5f5Rrp3EBTsuXEUV3JHymtCS2lUVa01CuyTQgBVOTBRylUcwUS6xFjkz8IthnYnkvS6Ik22GkTNHzvgiEuiBOoMcaF1Npv4rqdD9mhyFNs+Qo227W3OJ+F8quhB/PigTZo0wyCxonIWquZWlqafly8DljjVeiaUOWkEpeeIF9aUol1FJvIa1qXJDW8JNa8tYHcsu3eBcWF79BsrmLL7649iu/8ivLhRd16J1JAsVjbAfJ25k+fvwrGMQvo/Hxv4seHmItaO3U5RwL+J+oINaEEKv8ycxnpGv3CAAZHz3FQ1qmiZXNtHb9SKgrASPoAiikzzM5p/dk0cgmb5RhEYSVIN6rokb5+FSD0wAuEzjKY8RSvkzJjrS03vodXapEAaNRb7g0sk2bpRxtJdy/cmf7nOW2z93BdLku6zS/zCnrL9QL0kebyC/N67JBX9Rp3dZp3n7FVmPlstuLOxGSY/VIbzw6BV+pIm3kuw9y/fjmhyhZGlkWxjIpsJ2LS+IY10zTS/vTJeue1FvB11FY94t8JIrz0Menj3+FMO9iyr0zX/cGoN7dd/MjU7Rzx523f3Xr1i2c/fYXGyAVhnSFbyCuHL44HW38DxjIuRQMr1BP0ZmC8YStNbYhkFAa2KvXjqQhjGRnaGaI9SNAEXZSoboEieCR+TqB4zWOjTXGZ4OHOMnoGoajPNIW6ePtEZL21Rx5FJma/02YqOQb9XUYiN0CSAssOQgo5YjL+9FYmRIcsuXWu0y3ACkx5RWtKtIvg8c2l20ARHCsi/RRQtfpX50puSDyfHgw3vwBvFxrVBkVUG/+z51tyGDwkXeZsuQhv8PcI7Oh4qEX/6PpRYlmiXsHijDAy5cggzgHFnal56x/JGp+GPXOV+L42gK11aanj3f5eXA+wZJqBRYs+bTr3gCUbrnlzzpXXXXV0Ktefe0dN3/l1junpkYv4LcxKEQTnZN39XPTNJt0ykEbV9o9ITW4t6OCRykxMdlIK1ZlW8kWRGdlPM70fSAYLoDjM8tYsXIoTeEanGkKSaS6CyYU+SVa5KFcfVqo6wOJmzLOui3UI7cN7CLrWOSTxAuo0QB1jNqSWSS0AWYp/cGbeBIRETpZCtEm2xDtYptFCcRMtcFgaPGOtSvofjDcAWK6sn3hl+US36+/jFuOipBJ/H5RlAOSHBy63JaBAgyaVtAQDpCbjzBznnTBxkt87CP/9IbQ9cePH7/z1fAeDNTBwhkNaDMp2c509ThE3XvGM57hsyO82vyFBlM8++so8UD3MEevhip82rfHAjxDoFxMlClegqeJmhE8Sh8Nbe0PRWsJoBI8ATryhdQpqDhO+q3nTqQt28bT2Dg4J15DO9tKgKdQaaEuCQ+CURUYZQUDKbcoO1Qj4NNYd+1KQvM7I2lqRSON+3F0gGU9y+3IIBY/dCeApK/A0sbJsy1nXBmU5blv+23YQ3f5HDgLnISHGQQjnv/GjYQ9ltN5frw8Qx5rSao9yozyrat01Bm2VeFn9WhaHQClHPtgvPS33fmSJzj/S19lGHJmnkP1l4xf2du89hwGpciDN/BYXstzEh4RA2IhF8DfU657lUCkY1OV757hHz508DMbN276Gb4CUSwocui7N8JLhI9IM72vMdI2haqRwYLBS9tEtTGG6nHG5XTdaaPqo5Q4JYCyXHXkswhIvkm2P1auZUGS/G55CJZgKmUrKfrGtr1F2vmM/0EcCRRgIkJaBRllfrSKP8TltLTDppLIdtVgwDhANW9pb/m4vJRC2eXCLG/ZeC9TZd96sxTAp5JQt6gzZ2aqZ8uv4/TD5qMPuU3RnGi3qs0rMzyXe8a/1kXvTKfEE2D2oYrLEhA6kDHaGylz2hpb8Pvnb07Pfdi/TlN8G9tvHmS7iQ8r8GmXgwcP/C+ydcCAWQdJcVIzzgqgr3/9bu2goY//z4/feM62c4/zsakp7B0KU42xUtq+NE2zGSSBSsIb7+WIEABuZwik8hXoIKidK5z3MsZR5mar4JlC3TXJJwHcMtbPK9g5XwCkIFAAqKhfcEmEXC8bt0g8jW7L97Jppa1mGbrSuHbFXOdszbZXkRhlnggM/CmKy1wp4vtx3AcJAICs84P+GUC5H/aljV2U1dkgiAT8sm1ksRmEWdUU1eSyy5vSp0LpHp/jowy/guaP3sRgQwQEHcu0RQkuIB5g2eUR2x+HdK3313/47mQN9XX8bz72lzeQpQ4G/ABUdKlfxEDgbABKH/vYmzu/9Euvr/6n//T6nS998cs/v3LFiqefmDmhVKp3eT1kuL2JkXQZU8G7YHDe9ZVBMlHGaf/oBI8jvIeECgaeCh7SKvbHUXcT/MbGCJ/5VQS7txbSCsz2AUfe0viWaPEc4Jh/9WpO3KH6rDODWrtAiZeJGAyR02CDKmPhMhvXnG2SscwMFzgbPI9h4FfQRF4AsFQH5Amg+IdnZfhUf5m+PAnmZhAFmKjHD/l3NK5pm3VqE2m78Ih2lNLErOYXWHqFXxZOXHnlYM4XRjmjMehCJzOICmlU5PGt2AVe03701CN7523mIxC+tx+F9Tp8TKF+5Ojhz7/5bW/eWfBeft/rdTYAWV232YxfZG4dOHDgY+vXb3g6cSF9IAFTSdRY63Gsjn6BjvOiHASxs4541YIgcCtB5ztejO94LrOUHKQqnnOUANCMjTf5GgSf11V1CRrTBXiy2ittmXI8SNQmdsWKFcNpEkNbW0CVp5pUzVlG2EoSP9RE9vvMMJ5WeC/o3XMbm6izqs678JQhkBbdIEbPDPbJvtETm8//ZQmXVUB0K+LtYb6sp2CwEol+efitgSGdpRFtDhBlukgbwWSbB/PRTO75Z6O5Sj/fLd8b79dCYr2IOkoQxdIIBTfYjrpr5mvppY96Q1o5sYrZFx8ttYN0x7SHDh7glY20CO8Vw3KqqJHQKdfZAGTS3vwt81rgI+9933uu+zfn/NsjIyNjq9CXNMP3J7tpvOVrIashCkedosOukLo2I3VtVOHHPQWaBilik2JDEZ2tFBBAw0zRBY/2k0sDWbpA1FJiFRSzKI1Nt09WsHkrwyW4X3TNgKPXRIS6xI/85I269aP6AUbYUdPbKP7bZLdVJqY4/cf76SElitmfki2uwivmLtFflxdyv6MIbyyKy7+WngeQgA0pRJ3aRW2NYADUn10qhWw3dWSaktt2SztVI/HhLNqwvhfPvOvXYxmoMqVaH0QARP7Y1kdfdLXlOfGiZZVuja9pHDt29Mh73vtHn6Ggxi23cARyoHjCp10i7KzXm1Fjv/qrv1p5//vfu5Mvtf5PRByV2iShyRuQ3bVprPvDrDYdoIO+sJZr7HeUdHY2iFjqeNKY307EWRrUjzM0bZY679zHgTPSlMBRBVmul1JNkLkssHYDnwRG7akeg3TmkWgQSSD1Z2oRV8QTlhkBTmdk2D0t14Rw+nFPnCvki2wKOzvhrBcA503aqUacb5pk9d1Zm8BVYg5jrw0zs1KNusAZywTMhlywjNkUvoDMsyXjc5qYrSFBnZ2ZfyTK8a2XrNKdwenyeaNsCsQsqyzX2ZhhfJ3hMB2QpFFXtCHnk77SbYQfJJ7v3Zau2f7S3jnrz0Xy+Y1vQdntylt5LK/luSZMpvq9/6XKs16yvjvNpgh+9du33/qnfLHqH3HMlTd2fIRjOXRluirtrPKSmgAhyiXyeFqMllIkOyKDwSayQMCQbaQMHAmlARujjST96X6Znvwywv2zCYxtpZb5VVeO2DCuS1WgrURcjGQlmGGBU6RTUjQAa5NpvBLPi0dRhuXFqjH+ktvpvHgnqD0hGGdqyCtiHQBehfiPOIFsP8OLv97jcpezRzhLCdtD2LJtV9hFSiIlRtEf4iONeXDutZXSqaST8Ya9Cq8IkxZgxXOGvIutQJ3Fw+PpSZc9i6WD4coCX7XVxJCn/vqAPCazPHfI6nLBUeLpf+4LQObo8ZXOpec972UT1177ks9/4fM337Rm7dor52axjVjK7LB7O1FhY7X+tHSs9knOCK0hi2ssuWZ9GaPjfxAjCAJVwU8eMYDGkeN3nrWVTGviU8Emo1yJdmnAYx9DjCqZ5VujpbQKEBWACdBExQWQCKsuBZ9l1JEW8rasJ/v53nK0oVpst8wjiTSulU4ZONpuCH0dBagEDBj2uV4Z6Ku0HBlP/GMXVTmey7GJAaBQN6g1gBQ2oCDiYfRJtQYxg56CLuhDW/ENl86C+d+/MrAEnfENPmhxJF2x4Sd6F2+9IqRPtI8qRkZHaocOH7xJHsPrBjw/YQv7Bd1L4P4AyFd9OpzKd0o/vXfvnj9GCl0ZXYmGM3XuDadNQz+a7q5/EE26AULS2qCmHRT5MoXcBYUjbNMktoSHEfEhBXwZI+6DIEEdk5kmL9apLpziK5JD+kBkidMHTtznOLsv36xjVBXEguYETvGeAaKhrcGdGRUgpM4AuA0gs99UbvLlrMluM7Y+FuYAE6/HKKW8+pMFmG//vI/47OWw6ex7ETfwKDgUEpvstZAStIWy3DuzjX0ARThL8Gwe2M4MqtzeZYDZdK/s59oEao23OI63vpCeffGv8Y7YRMUvrXigrOTl3t17/phs0xddtLHy4Q9//T7Vl3XcHwDZnN7733/D4iWXXDL2nOc/4y+/eMPX/tnUiqltnhtS9HU4ErmqcVFaO/o81hY+y/HLtRAsmpXFbcEUgaDYCdVCqSHGbYWXxPefICKZBB+0e6S/NlI4VI+qTtXjTy+U0kc/q63MK410X3Vyaj/JRq5Sy1rLBc8yX+QhbzBC8NpeqJ997tlAtsQwrF21xtYTdHGKQACSPo90O4WzsZEjB2OQRJ/6j+J5/kM/DTjQYLI7UfFGLwBSKtnGDKJikAQtrS/TcfkduiIummA4N6WsCGOBd8eOpu0rf6J36ZbHIH2cukc7u7z7Xj9y5MgOeQuPG/CaI/bRrGhaWcaZ/EKLn+nRSXG9HTuua19zzXMddvv3H9j/bn6ARaKFKeRZab+2ft7EM/mU2zGkCIwSADSQ/kKA3Hlbo5oyTld2Uj+Polxn2BrmJ95OCqhsgGYbyaV6mRnSyjokqgAQQOYhvSpRw9R9tDizpMoKWyeXW6YPBgV4yKvxrSvLK8AkkE3n1H6R3+rwpx7cxRziA+6uXU0h1VawfuUi6BjGdTmjVFr6XYIwhN1ioM2268xOQ5g0uNjOwLaLrQknGIRjS6Tc/igMdV8qyAZ7TuugCjoV5SzX52RliM/63ZKeeP5LeqPNCb8BDbGlBVMfeLl/3953y1t5LK8JQ8n7vu43gCiq+5WvfIZXMVLjWT/51PejL3cPNVk6Zpw6wlp892b1yAVp89iLeT9yF5Z9ACyAUTJJ5jpjKhpu48kteGB+3/EUxEhkL8EgUGItibhQdWErORXNY0gBYR2WF4Aj3hmOkmcMN8Q2iswIo7cEB+lVQ5FPAOmKNih5JJ9+qDqm8LF/hkGtylOCCSZnbn4Jf4mzwy3eonA0BXjpYgZJ6ef+BEMFUensT7iBdMWzABPhPGMrQFQAyX02+5P3zwRPCSTT54lJltAFIHkdfam3J124+qW9izZeWVniNKnttIfy8NDhe3b/xHOe9oGJiYlGwWO48tACKGq7/vrrW7/8y79s4fv27Nn9djfdoBlTIB9zoZPPn3oGupbD2UaH/VMwAZHvqTztFmc0mVlkIa/SZ9nlwsqZURb/BXACSEokYIILAOEHECMb8TAv3r4E2+6/aSuFvVRIn7ArtHlC2lCv4KMRgqUEjvcCRoD5+bsRPsk2PjbEb2rxEwnOy2lvgIepflaHRFGmL+iFPRWAVJIVZUOkuPDkG92IPuSBkftWSqWQrtAnJIlgCEAUoIB2fank9D7uSz8DKaRS5MlSO6b5/F5Ip3J77+rzXtzjrRo+yUjDVIE0WR7u2bP3D2jWvle+8JVdeUy4aHC0+qx/NAru72WhXU4rzv/Yj/3YxHOe9+P//Ybrv/qSlStXX8QrHx0YWvP1kMnmpnTu5CvS7Sd+i9HwCAjKa7oyglEbYIB6DWZCi8xqpGsfOIRLXe8pnSypctMcLUqlEkxxLxMQKTJBKaaTOaaR6BJXsOpkjumCYoW0Cob3gROPgmyC0ZG9auVIrIy7riMojQ/Qk9/+eAxklo8TzMz4hQslvtJViUJi/ufWKBGXwzQu7nwWQW4jJirwESDmr3aQ9YXvLM3+UWbQqhiUEfZZ2S7SaFTngWkew34ZZCRNL34mXbnxDb0tKy8ppE+YEWxbjNTvOXTg1uc87+nvh6eND/71B515UdL9B1B0lQz39+rxtc7W+eefL0oP3377rb+LCs1EoCMSo82Pz22feCIf5X4SH9Q8zKhkVRlx7xTYlWKSxaEybO+gngQzzo6HrYSvOonXcEnDLRcE92+fATlOUJSSKmJ4HnFhC2Qj2+e6AJr1hHQomCKArJxLqeYUfxUr21vOmUjrNwOgKfLyYUdaRttYVNSxbNHjRTx/gnLVumYcN9m8ZRIbaATJ54G1bKT31WMUn+uwE9Zj16Od0X4lUKHCbHdf+mR7xoHUt20izOBwgMQgKcNIH54tq7IcbnKuOdXm04rRH+49ZttPQmP2NcRGwSt59+3bbv2PdP+wPJW3hIvGSpX7vh6IBLI0C+++9a1vnX/lK1859eKXvvAv/tenb/zkli1bnzJ9Ypqvt1XqzljqqLBLVrwkfeHgP+d4xhTUAmRCFeKFSHYKzsiOLQ0LpEMxogSRDMBpbCs9OG4UK/QCqeA1jZAOuZ+mGZw6y5hSMhkOqWWcCCRfAFUQBXgyNGWoB9a0l0Y50mE4ZpGky9KtAFzc57xZGuQ2mH4VU30sipiZ5dkZs0MTBctscZY60R7bghsM59blv1Gq/SWR3VS1lu3VD8cD27YsdViaiD7ltmY1NcSSw2fTk8/5UG+ssaq6xLv3zJqld3tyYqK+e8+uT7wUHsLLBjz1HfgHJH1srWx9oJf9a6O23Cdp/8XHPvL/Hzt+dJGjrfGbCDawzdfdVw+fl84f/4V0Yv7LqbPEApbbBS7GsTAHjsIuCcZzI5Gy+gI8ha1koiY2TICLivqEo4tKDe0rrzw66QZlZIbkEW7Z2VaSVxlU1jto61iCIIsd+WIvLs5aM5oFoWVar6CO2Vn4JYNsg899EzYb0y1/+pNNrmF+v2uCbY9Yd2Lbw7d03frwYJxbIu75xXoWwIutD6VHSJdBaVMMNiRN2DXFzCvbPUV6Bk9sbeCXM7JMD6Q8X55tVb6YLlv777vbV2g4c1w1CBAH5utHjx1d/MhHP/KbkKDPS8L06IFdLOU+uOuWW27p/dzP/dzwm970e/t/4sefVdm8eesTWRdSRgYolUSr+DjS0Tm+bL/0NYzRKQiebQVrhC9hcAbTYWI2Igt1o82CU91MH2WnmLQCQhsj3rcKgmUJJcHmZ9thj0gfAaERXdo/bldkO4ijpKjROX67XhtG5lu3EtEzS87UYoES49u2CAwN5Lyjn2drGcRQOQB8sm+fMqAEWJE+2JFVuwOi7GtISftIW3PYiQVtH4wrnqneTKMEz+n1l9MGXeK5qtB0qH8Oi3X5GPzk0JW9x677WdZ1a5yg0NQI26ozPjZevf2O2974z3/pZz8CDyvvete7XPfBunvgAApm2/kHeEma9tve9rbZ5z//+Y2ffP4z3r5v374vjI1P8F6dKIEBylcWry5f+2K2klazFTADA3n9h5lLSCGeSjALCsIDFhkb4p8zMjLPRUOlg2DLzCkkglKB4gWYTHGBUJ9qg0j6caNXXBJaYBU8jXQyZNnGyKM/mGBZJBREYTNRX0iuaEeWPNEgCyvBdFIao01XujJdFDDQBmhAXQLCesNBk5iJOVgIl1P+UtKGr+TheSmNlD4a/g6UJju4YQs1Z3uPXvuLvUZlnJ+blSXypNeWR/v27fkChvN/lXfwkJ+r89hebhb+A7q+EwCJkCVGm6ps7qMf/dDrjiMW+VytbwoyB/CA2RKvQa9Jj1r7L/iNjZ2osLx2Eu/LF8zPjCpsH9SXAMo74hQPUUewSwSEGitANMDYABGM800PidcngYwdvMgspmKnX3Bw6Qm6PKrxB0d/kWbQ9ohMZbklaKjQqFxirl7QBKgiQ/knpyvvHDa5fvLS7L5EOQkwAAhgCJjl6TqgQZXlXX8GVwCmXA8SRDpOS9S/mC5f8freVHVb1e96ywuq7MobefThj374dbRlruCdhrO8LHtXNvN++Q9ahZWlf+tb3+pihA2/+b+8ad811zz1+Jat5zy15SobdJFKHd7pnhzewIevL0g7jv1nDjNdwEjIv7FhkzPBLQ0mq6sMBXUjEPe+ax/MlsDhFPmFA2RViDx7ggU97CyB0JcqhfqSCcZZrFNvpWCIfnov8MIOIW059feZsyjLK9VdxkUhUaJV/LH9ALi0z0yT0SRgS1iZON9bv2DJwM0zrwxcba7ct8EJQO5rBnkZLv3l9JRNoSHF2OtqV7+Uzhn+d93N9SdXWt0FqirbUekOc6L/a1/72uv+1Wt/4ePwrPK+973vO5I+9ozufEcXJHty5x3veMeJl73sZc2fefHz/2jnzh0fmJzkneceKOHSqNaA277y8emSlb/ND7x+DKO6iRrLG5KZASzAIU7i4FaxwruEsS0DKwBCY9pLBsVUX3UXDmmF1BIZvjNWXpKsdFl05bwCSVtHosZz/DC0YZ6gCceDbHwvq9e+Kior0KcxlqFNNsyvFo7wXRnVh7JX8Nkf+1aO62WpQ52lvUPf+hKQ+nM4g8zD8SGZ4FB+EyM/LwdQqDL6EwMAId3k1xxT49tpw/Cru1trT6+0Onze0gZ6wQu+MFbbufOuD7zoJc97r7ySZ/LOp5HmQf75jiVQSjuiARy4765evXr4d373N69/4U//zI+sXLlq4xIrbLLFtjmLWT9xEYtu69Pe6XfzduuFIYmC1ZYw0I1ytJd9CuDAFCkikWV09vMUPgBBnF8dtZwshbLxXEqfcpFPm0ZpJXFlRmZAYXQXkkoGK1VKCWS4vKxL22TYn2lg/2vlqpHYb3MfbGJqiDc7WK3GdvNyBmnbrSvaXrQ/QBBS42TQmC76RSD6dEa/KA+qlrPMGh/96lR2pqnaj/e2dl7C2pvSX4ADW+yecaaA+/btveVHn3r1Lzz84Q9vcWb+xJ49ezgsv+P7AUCZtDSod/XVV1dRae35xfkbHn7FI58zxsXGI6vULqpmYm6cfBjfz5lI+6b/GBBldRYdpZiSTRJdysd9ESnjI1gSWSD1CSxomGUxnVZ7louHGs3ZCAUgjnbVHoR31iYoYk2qGMX9EY1xKgCVOp5QjAVB0tpGgauac7PUfbZhDraxE0B6nrPWJdPc6fDMUpxWjNeZ8kQgptsBUFUV7XIQUE/YQBKo7A/t41bzL3zDOqrP97aDiOxMN8wu/m6+qP/E3sbFVwAe3sbnABwl2ofO8PBQ/dixY0fe8vtvevktX//qPni08IlPfMIPZ37H4KGM4gMPhr7zqwd4Oj/zM69s/smf/LcjF1500S1bN2/9qQbDke8pIthjaQ5gVNLmqSswqgHR8XfwVa9LC0lUNEDggJRB5xPvnRXFFcSUqlxB3ExQb0PtyRwYod2zzCzDmXl5M5SjqgEwwGW6wmAVcDJWbpXTeMEkowWcs8L8qlI2bi2jZH72bQXpKcL6wgDW8I01n/IYSgEY2xlgoDrKPxU0lnGq6wMJsAqeXm0XH6K6urf2xLW89cJ3nvmuHaXaBnbZG7WF+YXupz/9iVf83pt/+8vwhq2o97ld8aBnXfZu8HoIVNhgcSl97Ws3da699tqRN77xN3c87rGP37l505ZnkkI2ZxCJBG43r3g4Wx0b+DroHyCJLgYg+U1RxYwpREwsFpq+yBNBn3lZYlxlABDBgVJiKG2WVd0Aw4wnS7wXT3oBIzAy2PK9ABIMLiA6I1Raee8sruEmZizqZeAFaHjGf8rNbSiliyC2LtNktxw2bT+P+Yq8Ob64L+ItRKDpRzohwneiu7W7eN//Kb3Vx15egMczPoIHWmNZm/ZLN33hF//5L//cx+FJ9Y/+6A+nefYdzbqC5AN/HmoAwe1Hpy9/+a/ar3jFK8b//W/8u68/4eofObKZrY743XmxQa9URoJh88orOMF4ftpx5Pf5iaLzo1mO9sCLdxHOxmxGlXGRbOAPhOUajJbxmeh4cCmIHsw0DBMBiLMrM6nm/k971wJcVXGGz7nP5N48SEICeRCIoIgBFSiKiFWEsbQKgyBtiEpL8THTUTtTZzpTtWplWp1xnFHraOuDKRRJRgaqqFXRtD6KTA0CIQRLGUgIeRCSm+QmN8/7OP2+f8/mXmPbYaYEAmWTvbtnz549+/jO///7+pfa0BSrQ/WzsQkglawI9hSGNdBUT409NsbT1AcZ0I079B47HaZlW1IkSZ9xdTy4DJM86jTgasDQ1X4Vh+/ENnPXESM1tiKWFvi+GcO2jjjlIXig/gILiKqq9j68Zm1pGdrCjcFCKPKdDfA0nxbWJZWOn9MNICTZDDvb2rfvzxFI+/7Hf/XInuvm39Cbn5d/PdWHABQc0lEgQsPkjZkGTeqzjSNtv0NgtvqyIAUyFoGkLD0qy3SGAEZ/wrWEI3GZI8INVjiRQEcaGI0lFypAekoEmIAHYBB2ZDeyUC88R+pDUGsqRaFbyUt4zqZm8h47aXkP0o8DlwBQeWE8vjpu1TUBIu9DRAEM80y/7So/i2IPmLogMA/eFfO13gzwcJCLMg8LqcCDFYZmdXXVutvvXPEq2sC9YcMGggdC85enFTx84QgAiG1KEBlWVVVVZPXK1b5H1z1UCRD1YH/99Ri8AnhsdoaoBFVO2kVGTsoCo67tM+gVbMYErNpnpqkRAaH8hAsqig6MOPihGweVolikGlTfJtXKFvuaUQ0k4EA4G0iPAmtqwTBSCW0YPiSUw6/BJkkjefUeGxxMk5bhticOHqRrhzNMsTmG2Zbv1f4hF+ChYjtHD2S1Pist9IDlaZ2HVYVQBI3axA/rAHsJTQdkTrP6wP51q26/9feoe9fGso0AD84kVpRHS5G6WP+zOxIAYqakTeHGqg5WRUuXl/oe//UjlVfPvbZj/PjcG6FrCIXH2gIUmLUZxtba9ORcozBzvhHo6jBOdm2BTh+wNKCCJyYSHAIIGymARhw0OoxxaPFStpn4eaGNBCIcrnrajgeg8QFpNM1O0Ijxr18lwMcJoiH5Bn7GoWUZaNiQ4uNPguVtZZVHbokX8e0LRYXwDuYBYXGLd+A0HwtnX3iMIislcL9ltl2Mk7b0OI9Q6ijOeMf5cqYBtvXIHatvew117tq0dRNn2LmKlELzaQcP0hwRCsR0tWETxqq/qo6Wlq71rVv30J6ZV86uy8nO+Q42sTmpyRxVyLqSdUReZ4pRlH0VMnWJUdv2EkCTgQX6qQARzrRi8ZGaUA3xAwY2YjRYNJXiNY249PMFcOkVa/txKdfqh42JiIxrW14KkHgNI42L3GqXI8DyCO7bUeBRoOB1opUE+BOPqJ5FgJKHcAtpKyDrMI4RQDB2NeHci2Uxb/MqM9aV4bBwZCViSGKYJI2wq97f3xfb/eUXP1179x1lqGvX5jeE8siKCURksUfEjBQFSswsMx+rrt4bQcH8Tz71WM2kwqIvc/Pyb0xPT/dj2gNTpxY+bK5T4YdiGnkZ04zctMVGS2etEQi9i+mPIlQB59bUKkYBDFkULAmIZnVKXolfs96GwIV0FaBUGKtUnmPmEqp3yIv2ET9c1VhsYFIGNm6c+gwBSLWnNKuAiE/ZYGKgxGOtMJ76Ua59LXEZwrj8rinvOE/gA8qwkjvusRzN15nRQdx1qZ4WSsFUwn4oUgoGO9srKnbc9TNMUQh4Nr/GU1E05WExhooF/2k1ZwJAzDAKUAwQfRAuKVmT/PwLTx/r6OyqwMEus8dmZecOyPZPxBISgK4zgJKGIyKLcuZBD9ElRn3gLewQxSk0jhyhQNyHL40PSqQEZhtM9jXvySgwr5GsAESQhGsEqGcJpK+Dio1Cw1/xSVzbr28ARNLINrUgNRI8IJBY4D16tF+BSAUwTN3QEVWAFFuCqMwX8xKObpyg02F5+2+23E2lRjQwwREzgR5Kj3Y3HW4sLTXN1Xyi6cCzzz394xdfem4f6tYsK1sP8BRD5mnVYz1SFL5pJIyUaSQS/jdpOgAY6Jup8ZSUlKSVl5ejpoz0t7d/9GjRxMkrBgcHwMa4qRefHgzXr/AEGhcWhAdCx429dW8aRwPP40AQ9NqS8iCPcEKU+9btwULKJOxJoUsusgq72JRZtEuqIdcIY7ed8eVZNIWAgS4sPik14KjicFG6vs8GZIUpFsa4iCPUyAYO822DcJjDIrFQCEYKdNGsGtg8yxTLvJAItL052kBk5liutsVWrLXIxDJarjbHM0SqpB/hrDp0dxu1tUe2Llm26AkEB0uWloTLt5d3oY4HUccjJvNIJhJ+ziSA+FrWAqmeZ+HCpSmtrXU+HGhvrH9lc+nUS6f9MgMKEaEdnYVnbaK5WNHUWgZZALtdGwNfGfvqtxlNwU1QEXcpdlcSSJgjA5hUo9tjOgQSAaLBY/tVmA0MAVCCXwCmwPJ1ECmgMIzUBdEUKyPYYBWA8C77WiqUcVCIb3z6CJAwARL8UA1I4GB2DvhoN5zRSy1nxyIr1nKZGe1zm5aLSzFoWG2EnBH1Y1kjdDYP/PPwP55Ys3ZVGea2jOzsSb0VFds5s05NKuyqU0o8I4aNeSYNK4E2Vlt7KJKRkRFbsGCB98mn1u31uj2fTJhQODVr7NgC6ONBLy3KNdYQOTAiDJZF+SYjJc+4aNxcY2zK9UY3FAG0BN/CgGAYaKOqYainQ49NLT21VwRy/gzPKcE70UUG9KpB3OdyWsbRVj9DNojgODvEhWKPqjnZpLwvLJEFQ7Nx3R9LiH8xwtLgIxDoV+yKRJaIQ5s7W6HHp8hyd66wrPrvmeGTBdBOh4WdkHUUcJieFcGKYafP73c0NTfu3lz+x588+tjPP8Q57g4s5OuqrNyZCB79ajw/8oblOhuG7+VnxZpMslkar/1lr29bU1hY9ACokScU6gEE2CTgZTCyAxaSLHdSRrCRsbn9sHGo6WPjWHsZPrtWHFc0EwoXxoD6oKHA3kg1NNsS9iaUSFGdOHtDGw6xvTibU/fjz2vqJWnabItx4lQIcYkJ3BNKZbvKD8qIPwGPCSKBUwVlBGPgChxHeLUVOTnZjISSTYs9LlDTBHYFJFF3o9/Z0dk5UFd39Le337l8PaqiF3UWgxjAqQktLJPqnFHw4H02haTvzBuCyLTlIvfChQtTsDDft2PHjug9a++fsXz5bQ+OH5+3gAus0EUlWyPAaPFBElQKSFhFZHSEmo3ak3uMoyf/YrT3vYcBP+hv9M7Csoo0gAkNh5lysjrFmpRsFAfWcNDY10OgAsCGsztcSxiBRJBqQMHF6/A+hAPoGO8SlmfgdGSTgrFzEF/MBMvZNwv6T6dDOM41Iv1gVcOAgyISDLEkrNUlpTxxoumv27aVP/Pyay9VY/+WE4OvYFkVIdRd2JZ3CJwzDh6886wCiO+n0cCgUO1duXJ12pYtGxnmfuH5V75bfNnl9+Xk5FxMzaGDorhQxdfyEfs+6iBgAC3cbbQGjxn1bfuNho5dRrD/AylhkqcIlGkcKBdOAYTgLJRClmBw+xAyABunMDY4tKBtg0UL3onUSgR4JCbUja4NKJNTC9iPZTpDEuY2CyxPuNhw9k4zzOAEIxZK4zQKXoTvglueOLqpmkKAg3ksF8+qOHmy5XDNweoX7nvg7vcQIYy6wWz6RlId9LKGJkX5zFkzZ4uFDS+wZmloSsMzb95NvqysdD9OjqZAmLnxD2/cNrFw0pqssdl5GHzEXiesSYUR1oYnRQaBQOIEEqCmDewByjIHQ0KZWoJHjBOdB41AbxX0IkPxKOITSB53Idw02GSAClrObIFbAYogIrDgakoEV01l6J4eWR8aHyyHlIWAocvdTR4MN3jNIssbm2K4ByYBOOPAaFJx5BVyxmME2YNkl1x6XywJd/fzLI8kZMVttLW1NtXX165f/aMfbEVw+5IlK52BQLDn8893cB1PoqB8VqgO86rNaAEQ88O80JL6UDbyLl1a4m9ubkiqrPwbWVju6xu23ortQ6sys7IKcQ3FT71sBVS+yEhSFrI3JsMhADYmZRCuy+7DOe3d/QGrs6fZ6Ow9Tmv2hBuwK6AB8tNRPII9XUPUiODw4nkfXHUMFcEik6hYturCKjK3OwUgzMCpRdlWkgunFznycBBfHlT+gdLhpGRHGOePhsGeKJyDIkFxswINi6jnU0yV9+RkbCSDaQ+01R9vbCi784cr/oTL5jlz5rtycwv6t28v57YbUh3WAwtI4Jx18CAP0mB0R5NhZdKSGrkxWu1duPAW/86dH7mhKZZf6rj1r2y6CYL2yvS0MVegZwIZCaesY980KRF7bup59pjgk3oG1QA6KJNQkKVgTp1GYZz7Go72WQORXmMg0gN/L8487cGAAY+wxbGDJqbrkBqew/lZXhOAND1On+Vx+UBl/BjY9AHpABkUbMnR0eiWywAm0ueqQA49iOAs+RCMIItKmwnGt5xYBmxQrVxXV2dVbV3tlrvvvWMHMtyC80md1167KFxR8U4Plp9qdsWyjxrgsGZppFTKO+p+mTc0XzGAVOMqKChIuuqq6301Nbvdhw4dYmWm/Wbd03NmzJi5JD19zA1jxozJIEAGBggmLLlXYCKjgGTCmocPYdKWKDb/KOhKbwigkoaWUBUX12xshTeEg5IgGTslSYoAZXrcO28TBb7NToMuAYykgSmVECc8vTiNmRPEWGbagSmIjw/UVG3/xcMP7saDXTxWqbj4W+Evvvikt6GhQfeuWFZNdeAdXYY1MtoN80iqQorkKiws9F5++dU+nCbj+fTTHaxY59y58wvXrrl3Xl7+hEWpKSmzU1PT0yiEKsF7AI3PFdVDRsaWcIV0bUCxpW2jIKCv/ouLpwlCZcQlTnjJPMkdTLY6OWKs89LdHewK9fTsbmyor3j51Rd3VlbuOo6o0W9/+yYHdrIM7t//9976etEMT1Y1qoHDMtLoGlBXo/dX51MDyYlBSM+sWdclpaenJG3btpnhbDjv4sW3TFh6y4pZWMB2TWpq2pVYXDURuxJwWBU1Z3CfF9XNyFyaZgmkJJI+yI1+j10TKhzVFEcY7mikkErZEfkoxCXIRyKQq3eFQt0xbPeGeuSufY1Njbu2v7V1z/sfvkPQkC05li8vjQWDof49ez7rx+iyFo41cJi0Tp/+UWmGVdiozOPwTDHPBIwGk6u4+BrP5MnZSQ6Hz/Pmm+W8TzBREM/AkZ2TiqfPuCwzM2u6z+e/BBq5CjCom+VP9kMYZo+NrIbsiAqhuGfeZk3iIgW0IeMkWo5NadbH+KR0vX04XzkSCWCo4XhPb8/h9rbAAXTBDz7z7JN1SKQdlsBwLFtWAoLYO3jkSGt/Tc0ugiaR2jDfox40yOOQORcBpDPPvA8HE2SIazxTC3KhTszw4MA0B+ba2CC0ZIF+yEyZNy9eMh4yVX5mRlZess+fCzaTjUNmM0ClUiEpJ4PHeQAYNyxBSlBRjoF6fmsQi//7IK93g4p1YAK4FWBp7uwINEFmaXz3/bdPYNlKAI/obTMm5qrMKVOmQBuVMXiooXnABg3BpCmNBs05BRzWC825DCBVgngZEsEk1AlszjV9+nRPRka+22tFXS3BoBNyE5/ToKJfZCu4HMjk9la67pkz57jS/XLUkRHs6bH27q0kpeAEFS0ph/YTADQCaMgzxrj0dOwLdUY6OhrD2Eo8CPY0nMpo0PC5cxI4zDjN+QAgVRL1q8sjjYkgAol+gsSRmZnpzM/Pd6LH5kpNHY9utAdKxQYdkI1MHLBmQtWt2dISNI4dO4To3zQTJ041xo1LN5CO5fPhAE2cAhqNemL9/YOR7u4TUfSsIthgGUU6mrrQJUA0YDRYtPvNl5xjIbrCz7Fsn3J2dfk0oBJdDS6GOcaOHWsCWGYkkuIYg5M8o9EUaDRShguLnc6Q1Ynl6S5XKAagWG1tbcOBkQgS3tOWiZw3gGFhEo2u4MSw89mfWF7tH+6y/DpseF0kAkH7h7t8RocNf/68u/5PFXXeFfQUC3Sq9fF/A5BTrLcL0S7UwIUauFADZ6EG/gVDWA/ZLvz5/wAAAABJRU5ErkJggg==
📡 API Calls Detected
- POST
- GET
- https://www.google.com/ccm/geo
- https://api.wallet.coinbase.com/rpc/v2/desktop/chrome
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 33637 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 33637 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for cybrotoken.pages.dev
Found 1 other scan for this domain