
Phishing Analysis
Detailed analysis of captured phishing page
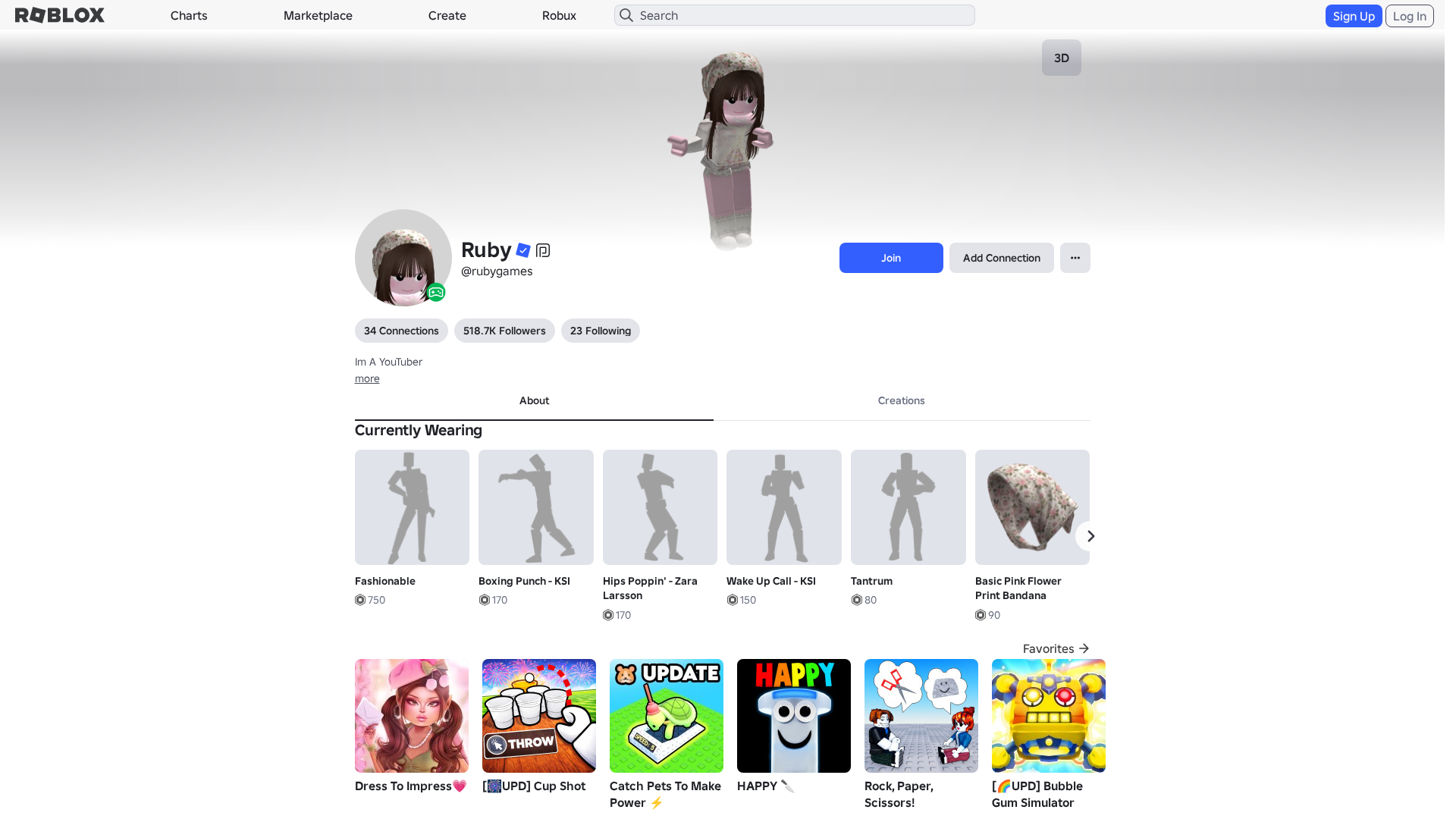
Captura Visual
Información de Detección
https://rblx.foo/s/robIox-profiIe
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
c13055d2-2bd…
Analyzed
2026-03-24 23:23
Final URL (after redirects)
https://www.robiox.com.py/users/286858877668/profile
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13283107292542837617B69DAF064672ED2D3D70FCA4346E1A2FCD39A0FD6CA1E86340D |
|
CONTENT
ssdeep
|
1536:gRGXWnSrX12eBLsghDgfngJ7gG9gElgf0gFWgFhgjWgw2gUIggAgxHdgjDg4Xg2j:6GXW+1ncOVf8X9cYMKns5xgdBHg1kSey |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b41766439994dd6c |
|
VISUAL
aHash
|
0000d7ffc3fbc3c3 |
|
VISUAL
dHash
|
e8e8363012120f8f |
|
VISUAL
wHash
|
0000d7ffdbc3c3c3 |
|
VISUAL
colorHash
|
07200008040 |
|
VISUAL
cropResistant
|
e8e8363012120f8f |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/1018553897/Bubbly-Idle
- https://api.injuries.lu/catalog/5104374556/Tantrum
- https://api.injuries.lu/catalog/16814551841/Basic-Pink-Flower-Print-Bandana
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- /login?returnUrl=
- https://api.injuries.lu/catalog/293316452/Archduke-of-the-Federation
- https://api.injuries.lu/catalog/86499753/Woman-Left-Leg
- https://api.injuries.lu/catalog/63043890/Purple-Sparkle-Time-Fedora
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F286858877668%2Fprofile
- https://api.injuries.lu/catalog/14906248118/Light-laced-cami-top-w-skirt
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F286858877668%2Fprofile
- https://api.injuries.lu/catalog/134461027154007/Caramelldansen
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/3576745472/Fashionable
- https://api.injuries.lu/catalog/124730194/Blackvalk
- https://api.injuries.lu/catalog/7202900159/Wake-Up-Call-KSI
- https://api.injuries.lu/catalog/73936874216309/Cute-Angel-Face-Cheeks-Dynamic-Head
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/128384059763592/messy-layered-butterfly-cut-dark-brown
- https://api.injuries.lu/catalog/72706690305027/Catwalk-Glam-Fall
- https://api.injuries.lu/catalog/75036746190467/Catwalk-Glam-Run
- https://api.injuries.lu/catalog/72082328/Red-Sparkle-Time-Fedora
- https://api.injuries.lu/catalog/6797919579/Hips-Poppin-Zara-Larsson
- https://api.injuries.lu/catalog/10147916560/BURBERRY-LOLA-ATTITUDE-GEM
- https://api.injuries.lu/catalog/837025054/Pirate-Swim
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://api.injuries.lu/catalog/138641066989023/Catwalk-Glam-Jump
- https://api.injuries.lu/catalog/86499793/Woman-Right-Leg
- https://api.injuries.lu/catalog/4646306583/Curtsy
- https://api.injuries.lu/catalog/837025325/Pirate-Climb
- https://api.injuries.lu/catalog/103190462987721/Catwalk-Glam-Walk
- https://api.injuries.lu/catalog/17758492892/Necklace-with-Hearts
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/100929604/Green-Sparkle-Time-Fedora
- https://api.injuries.lu/catalog/133509892267013/bunixi-pink-winter-shoujo-igari-mori-kei-coquette
- https://api.injuries.lu/catalog/64082730/Rainbow-Shaggy
- https://api.injuries.lu/catalog/7202896732/Boxing-Punch-KSI
📡 API Calls Detected
- POST
- https://kyxn.dev/api/shorten/TKvzwH
- get
- https://apis.
- /api/shorten
- https://kyxn.dev${e.endpoint}
- https://kyxn.dev/api/shorten
- GET
- https://help.roblox.com/hc/articles/30428367965460
- /api/pageview
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 209 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 209 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 209 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
rblx.foo
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/1p8tkN
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/www-roblox-coms
https://rblx.foo/s/users243671918813profile
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/LX0Gyi
https://rblx.foo/s/rxgKLr

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.