
Phishing Analysis
Detailed analysis of captured phishing page
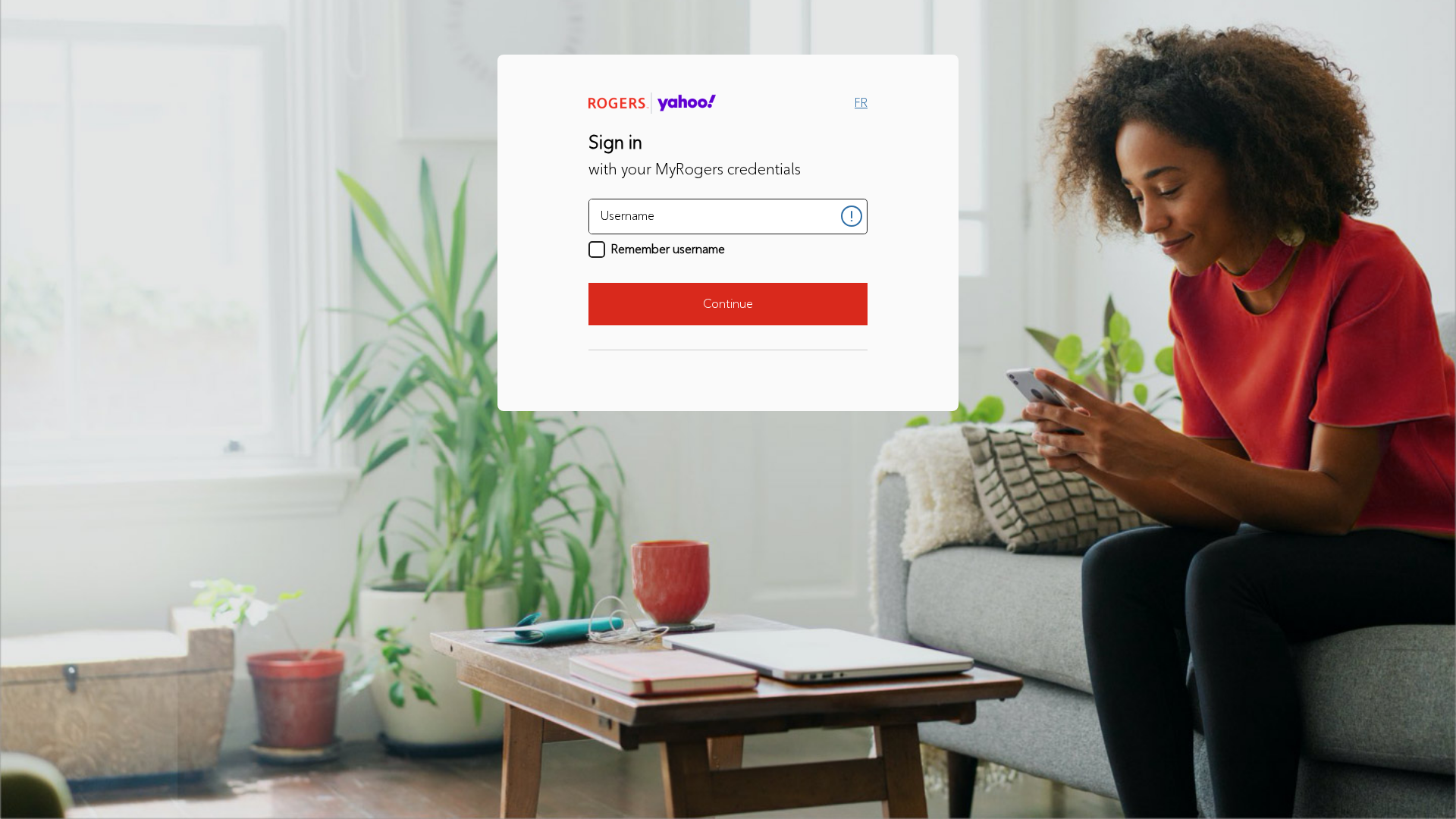
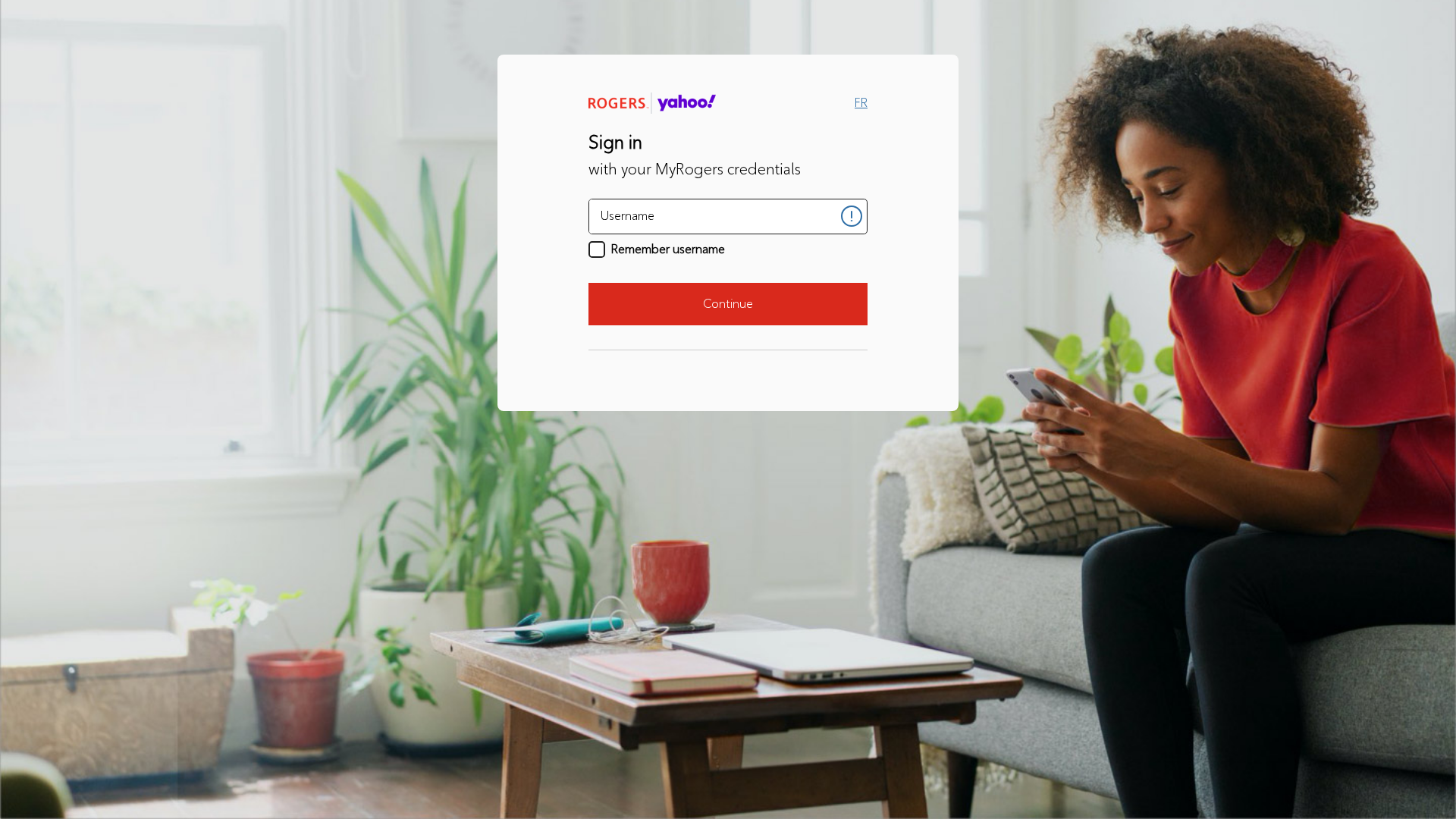
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1EE4131A210125C3B4263D1D5B7FA7F1A72D2809EDBC7290092FCC3ED2BE6E44D81D566 |
|
CONTENT
ssdeep
|
24:hR/CcuDfTJ0HmapRcGAgPD0sMl/2VY0S3gC/IsmN2CV6lTupDKgP8dcKM5hNDc8D:TXCmrcG0++BqwVFYmgP8d0Znp |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
da8a2ad925b7352c |
|
VISUAL
aHash
|
fdfcfcfcd8c88000 |
|
VISUAL
dHash
|
393929283019010d |
|
VISUAL
wHash
|
fdfcfcfcd8c80000 |
|
VISUAL
colorHash
|
07400010001 |
|
VISUAL
cropResistant
|
393929283018192d,78606818f8727e67,3434b430f0c0a0a0,393928381019010d,0010243232040000 |
Análisis de Código
🔑 Telegram Bot Tokens (1)
- 7079059082:AAHc...9R0AYIdk
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
📡 Infraestructura de Comando y Control Telegram
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for yahoojkj.github.io
Found 2 other scans for this domain
