
Phishing Analysis
Detailed analysis of captured phishing page
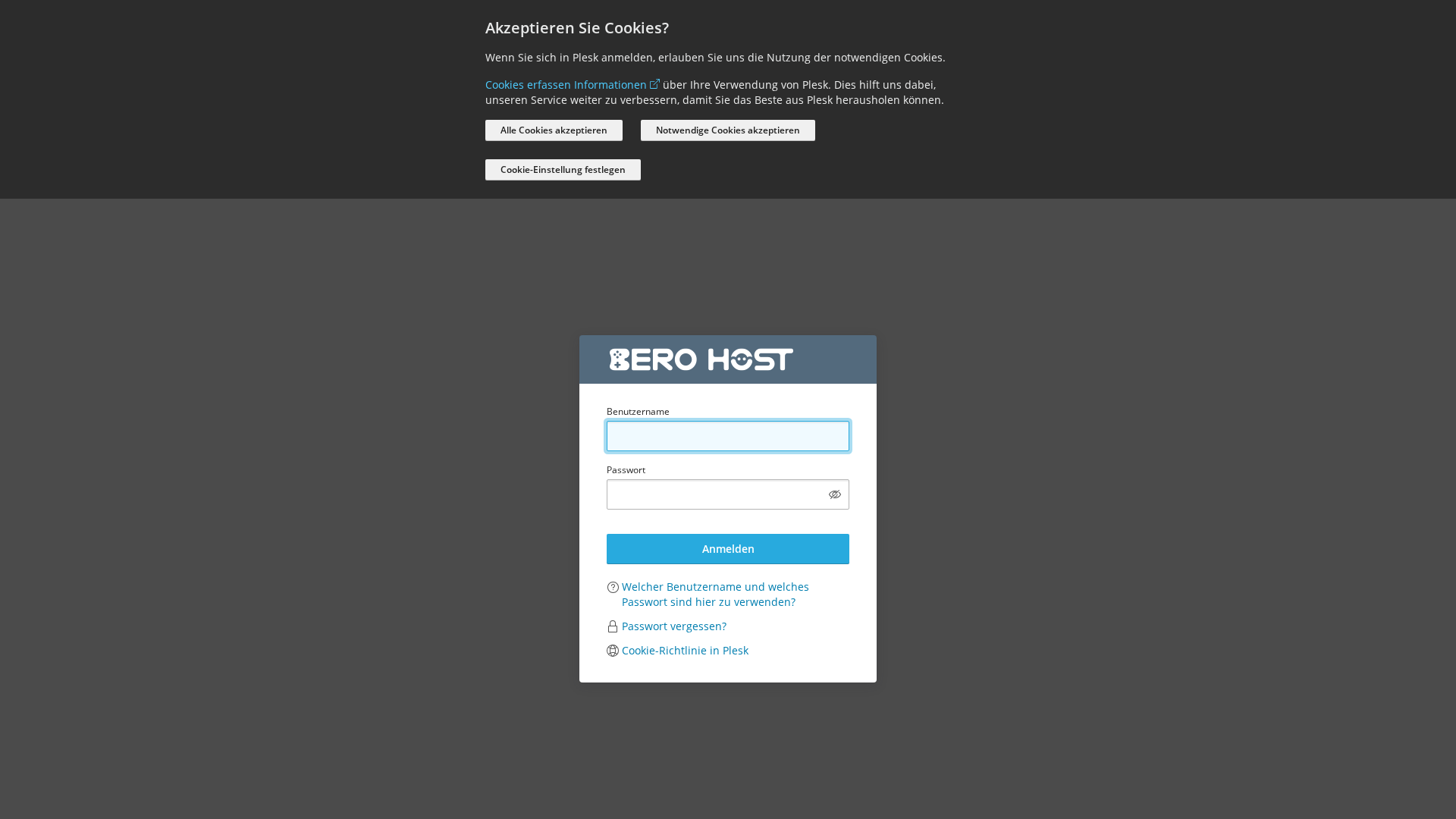
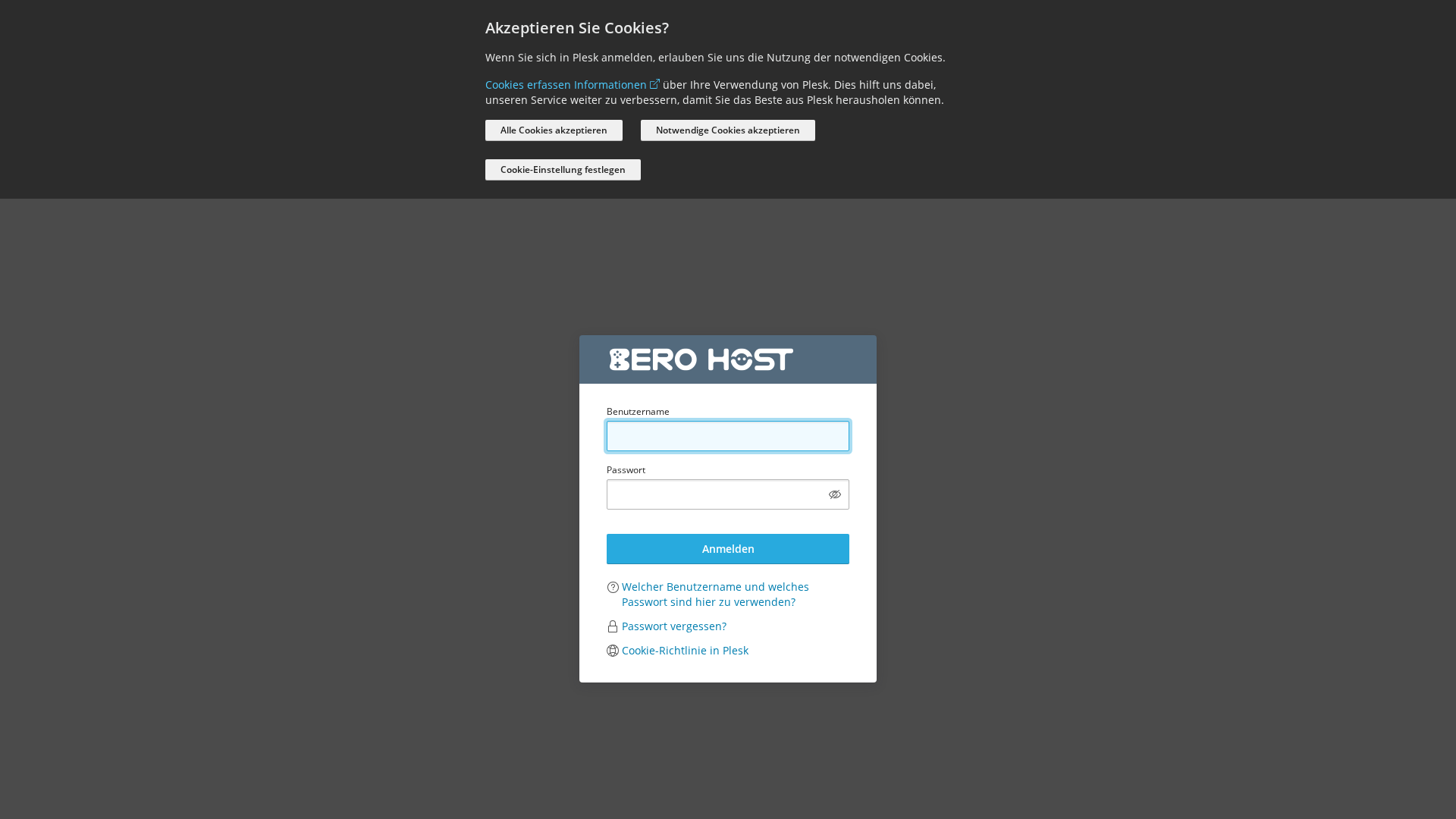
Captura Visual
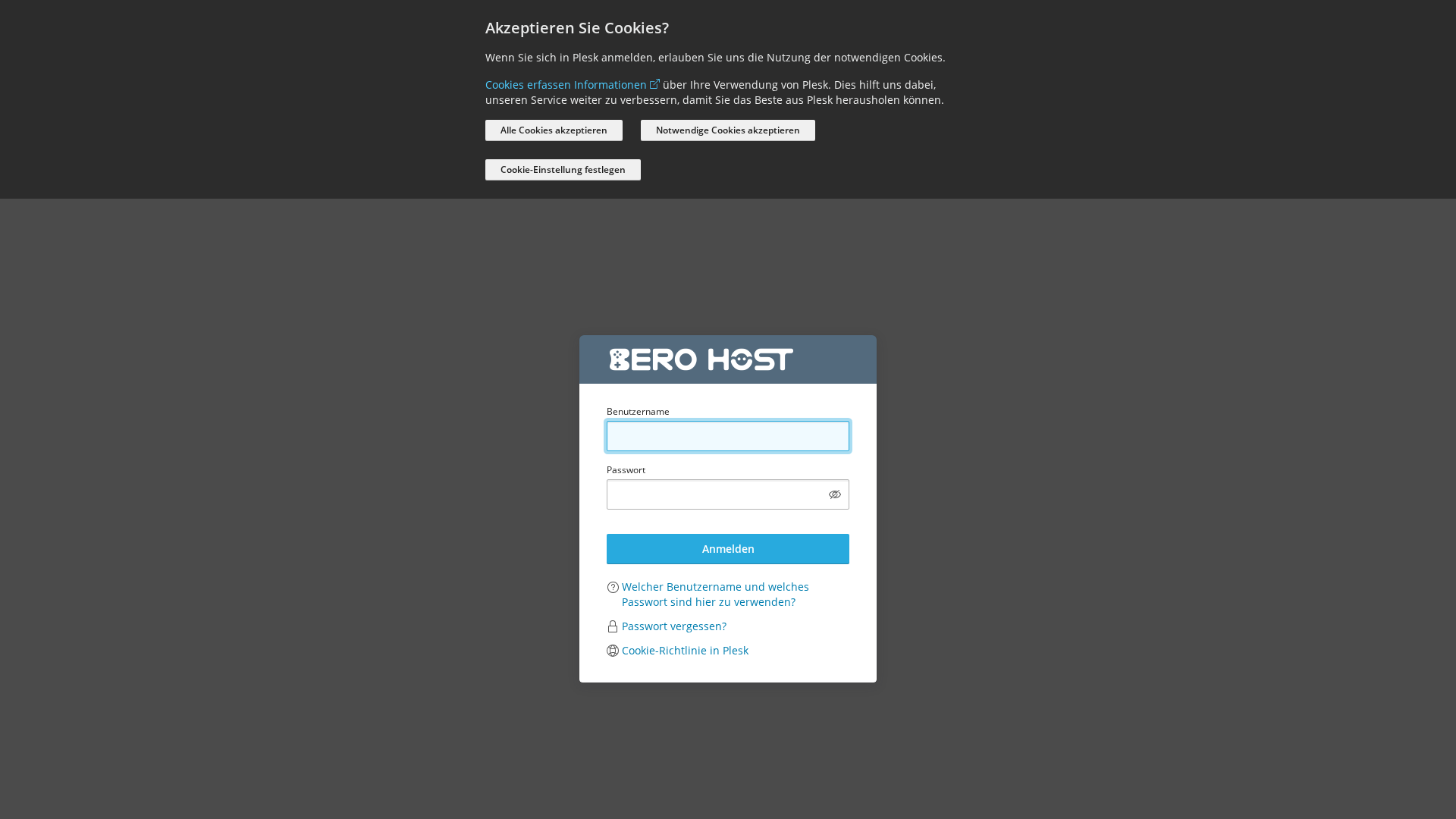
Información de Detección
https://actualisatie-account.web7854.web07.bero-webspace.de
Detected Brand
Plesk
Country
International
Confidence
100%
HTTP Status
200
Report ID
c6e33508-309…
Analyzed
2026-03-17 04:06
Final URL (after redirects)
https://actualisatie-account.web7854.web07.bero-webspace.de/login_up.php
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T149F10F32944CEC3B23231FD17592B714E2D6C76ECA421610D6B9439E0FEBED2E44665B |
|
CONTENT
ssdeep
|
192:8HSJikYMzvUAZ6C3CYEQctxdUAKe8I+jKkrAr+jg1rA+j3rrALdv:+SJikp8AIe7/AKe8I+jKkrAijg1rA+j+ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc666699333133b3 |
|
VISUAL
aHash
|
0010001818181800 |
|
VISUAL
dHash
|
70624cb2b2b2b24c |
|
VISUAL
wHash
|
001020381c1c1c1c |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
98a6b2803336b8b8,70624cb2b2b2b24c |
Análisis de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing de credenciales
• Objetivo: Usuarios de Plesk
• Método: Suplantación de identidad a través de un formulario de inicio de sesión.
• Exfil: Credenciales.
• Indicadores: Javascript ofuscado, Formulario de inicio de sesión.
• Riesgo: ALTO
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- ${(0,m.default)(`/admin/report/download/file/${encodeURIComponent(n.file)}`)}
- /logout.php
- https://support.plesk.com/hc/en-us/articles/12377667582743-How-to-log-in-to-Plesk-
- log-in
- /login_up.php?modals[cookie-policy-preferences]=true
📡 API Calls Detected
- GET
- https://o447951.ingest.sentry.io/api/4509632503087104/envelope/?sentry_version=7&sentry_key=c1dfb07d783ad5325c245c1fd3725390&sentry_client=sentry.javascript.browser%2F1.33.7
- /admin/copilot/gen-answer
- /modules/notifier/index.php/notifications
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Age
Domain age is unknown, indicating a possible newly created phishing site.
Suspicious Domain
Domain unrelated to Plesk, and has a suspicious structure.
Impersonation
The site impersonates a Plesk login page.
Form Submission
The site contains a form designed to capture sensitive user information (username and password).
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Plesk users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 110 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Plesk
Official Website
https://www.plesk.com/
Fake Service
Plesk Login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker sets up a fake login page that mimics a legitimate Plesk login to trick users into entering their credentials.
Secondary Method: JavaScript Obfuscation
The JavaScript is obfuscated, potentially to hide malicious code that could exfiltrate the stolen credentials.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
actualisatie-account.web7854.web07.bero-webspace.de
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Plesk
https://affectionate-noether.109-71-253-24.plesk.page
Mar 17, 2026
BERO HOST
https://bom.so/td9IVM
Mar 14, 2026
BERO HOST
https://bom.so/Klachten
Mar 14, 2026
Unknown
https://zealous-satoshi.109-71-253-24.plesk.page/index.php
Ene 06, 2026
Plesk
https://www.web12073.web09.bero-webspace.de
Ene 05, 2026

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.