
Phishing Analysis
Detailed analysis of captured phishing page
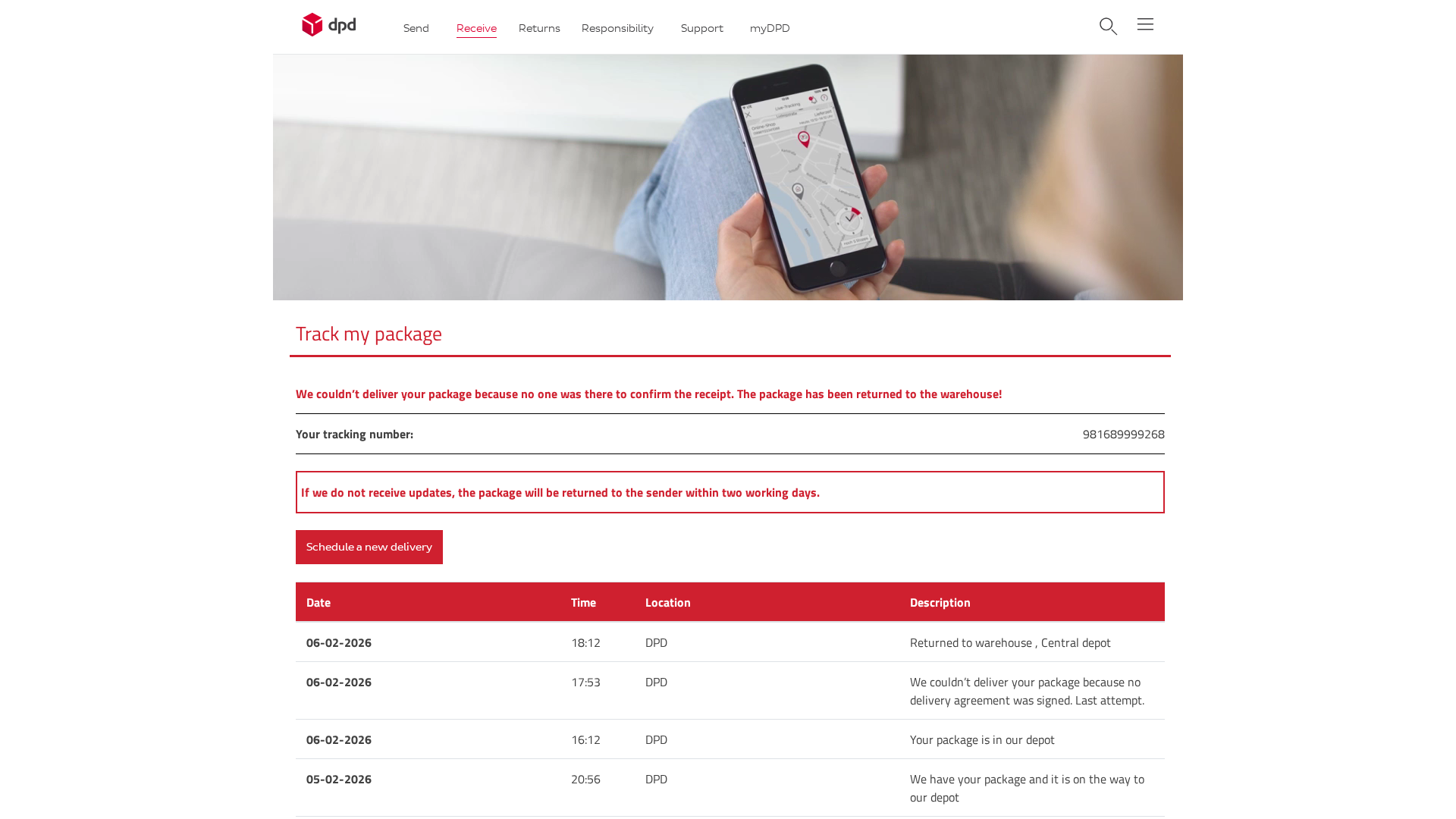
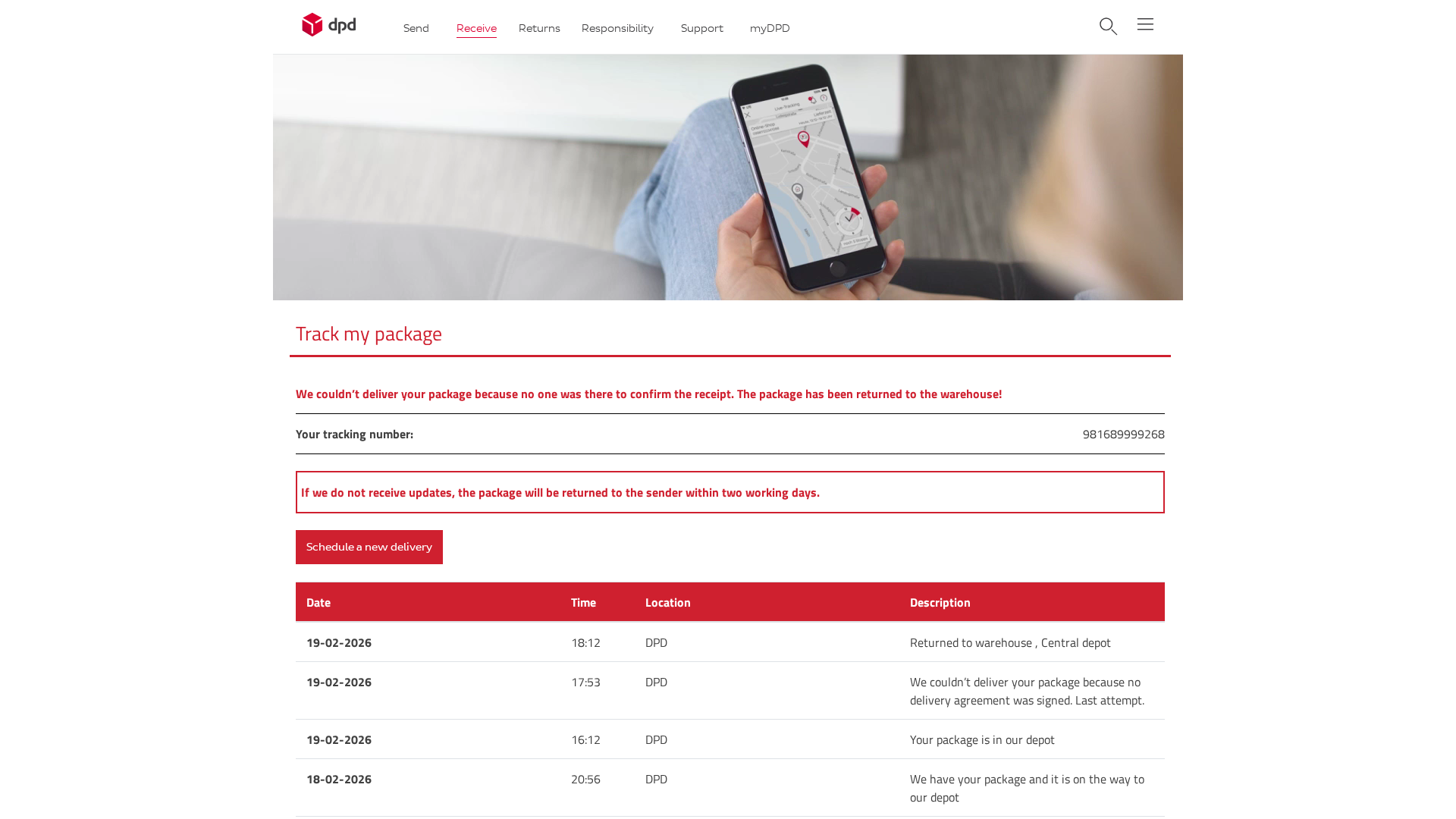
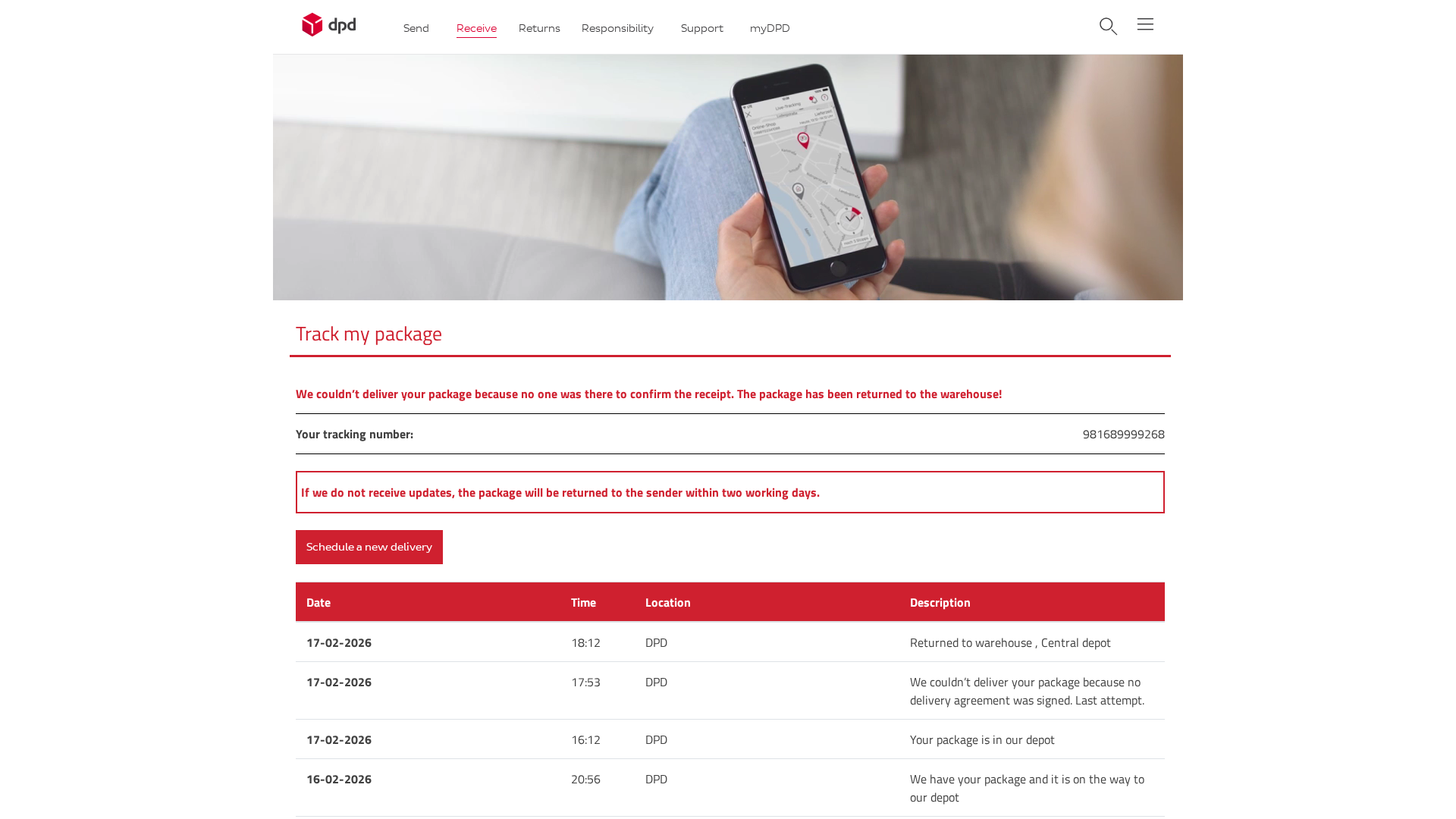
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T128B2017094B5B63F009F7391A7386709A3D39383CB520BE567F8836D5B8AE84DC23169 |
|
CONTENT
ssdeep
|
192:bixLoxwz77qKHv/ySchJrVUmZGkofXTCReWyRMOsUFf9kIT/JO:mx8xw7pvKpJrVUIGk6+TxFUH/JO |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ed6dc19a92963c92 |
|
VISUAL
aHash
|
f1c1c1ffff83c3ff |
|
VISUAL
dHash
|
23030727392b1342 |
|
VISUAL
wHash
|
e18181d7c781c3fb |
|
VISUAL
colorHash
|
07200000006 |
|
VISUAL
cropResistant
|
23030727392b1342,67e5258787c39767,0000db6464649b24 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Clientes de DPD
• Método: Impersonación de la página de seguimiento de DPD
• Exfil: date.php (probablemente cosecha de credenciales)
• Indicadores: Dominio sospechoso, Javascript ofuscado, acciones de formulario, marca DPD
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- ./app/wp-content/themes/DPD_Login/css/styles.min5b21.css?ver=6.0.2
📡 API Calls Detected
- GET
- POST
- https://whos.amung.us/stats/
📤 Form Action Targets
- date.php
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 22 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site impersonates DPD to obtain sensitive information like tracking numbers. The form data is then submitted to `date.php`. The tracking number is likely misused to obtain more information or credentials.
Secondary Method: Malware distribution
After entering the tracking number, the attacker could redirect user to a malicious page or download a malware that steal information from the victim's device
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : Light
- : Light
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
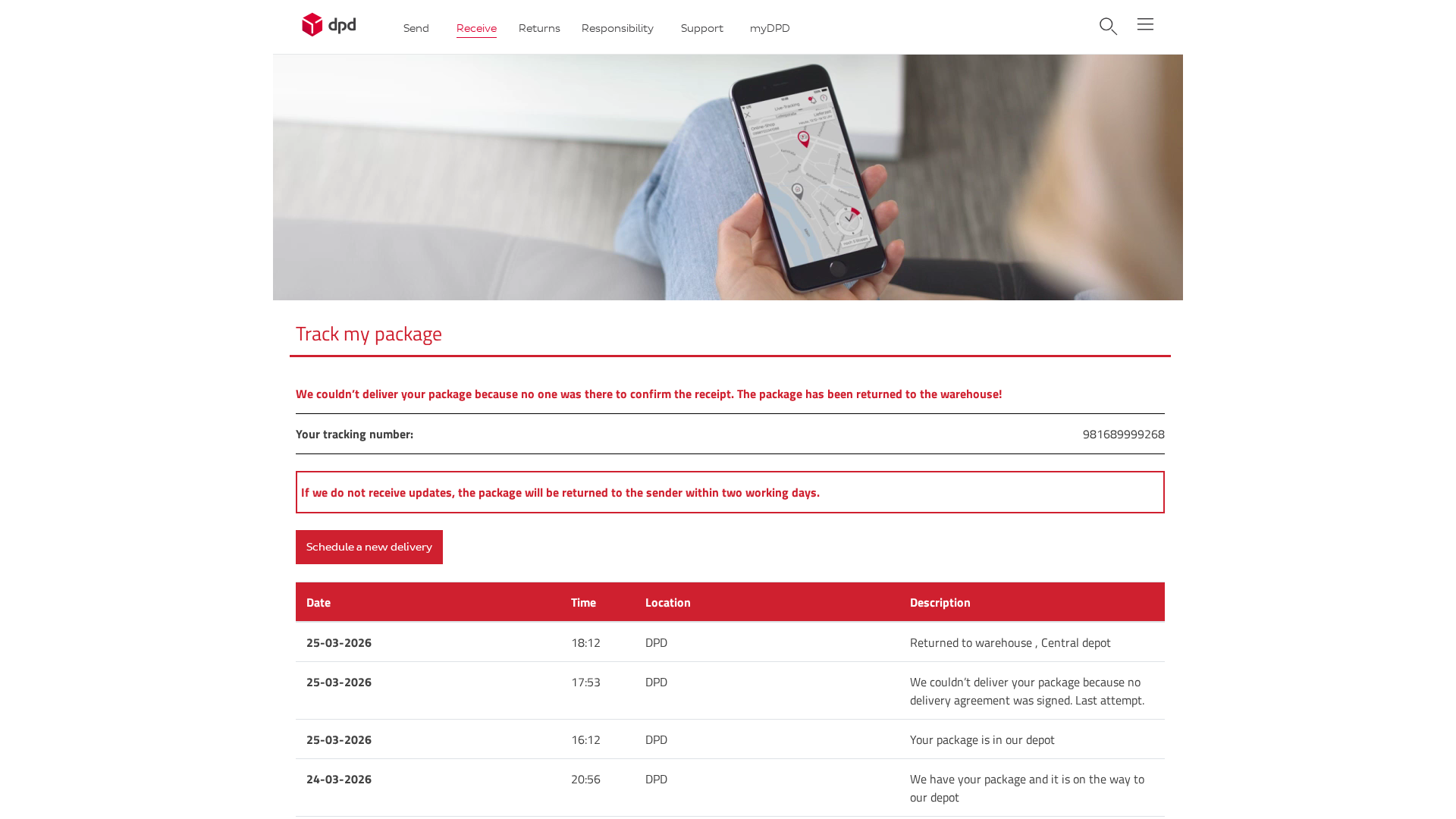
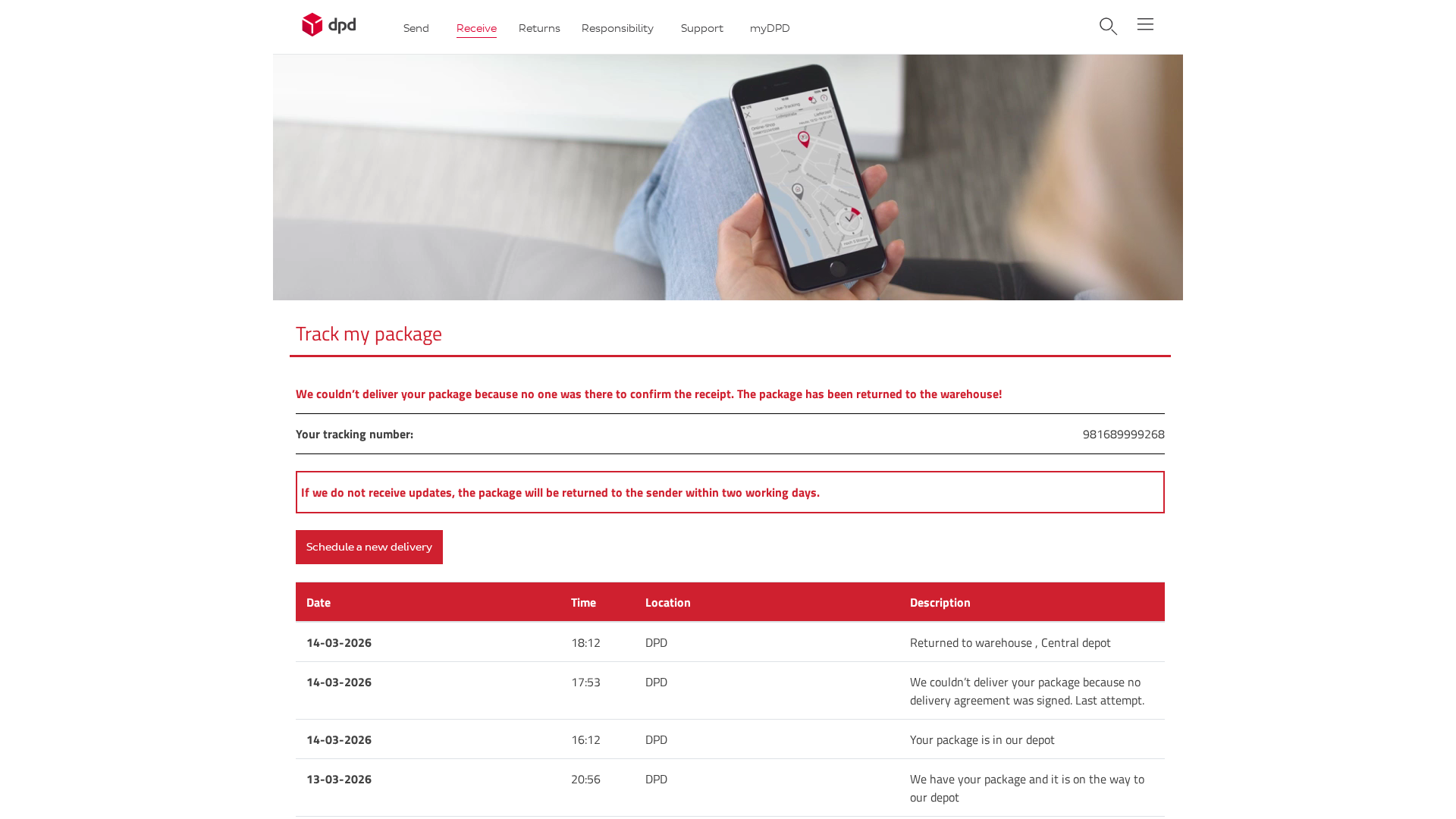
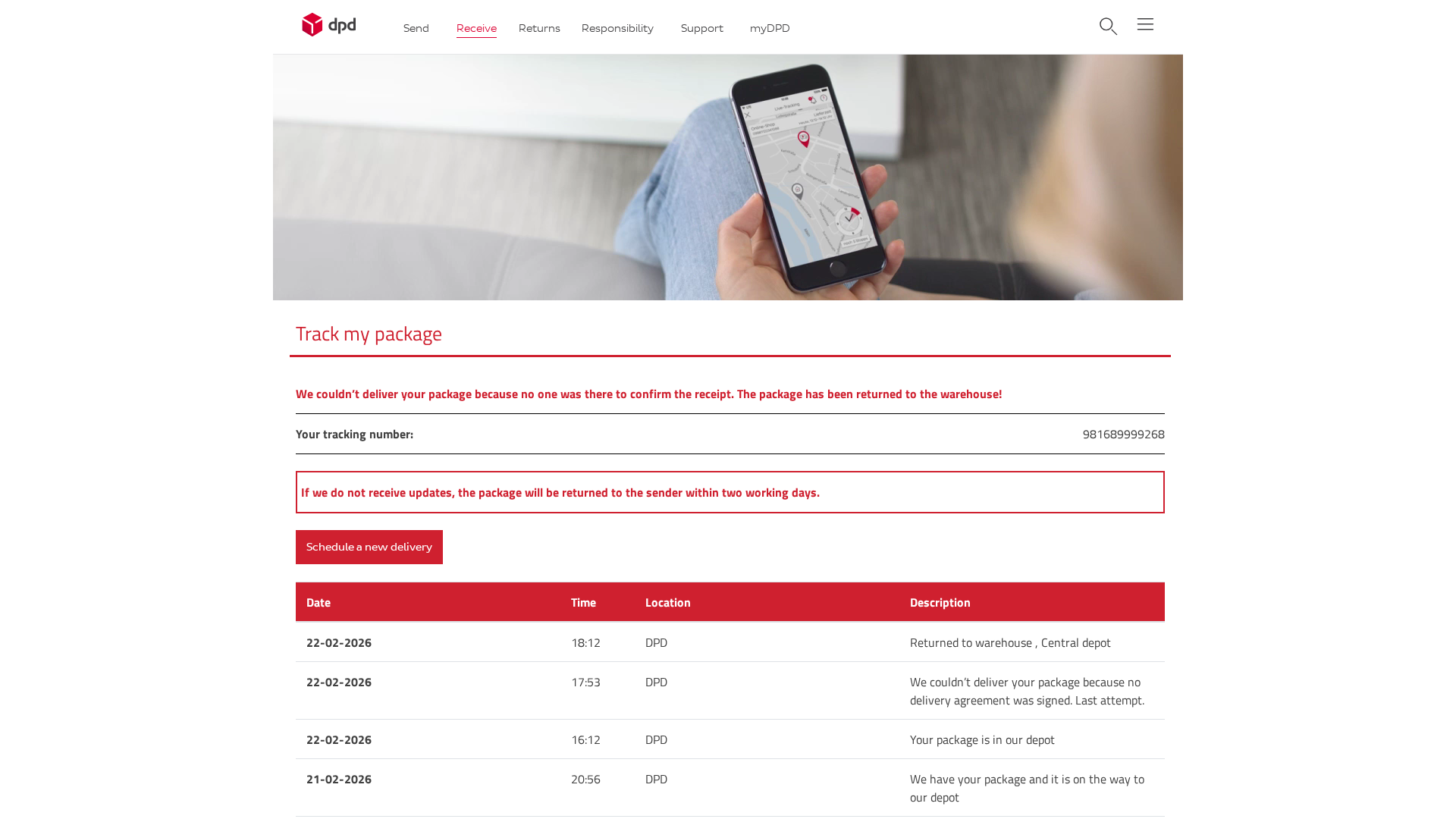
Scan History for 165-227-112-65.cprapid.com
Found 4 other scans for this domain
