Phishing Analysis
Detailed analysis of captured phishing page
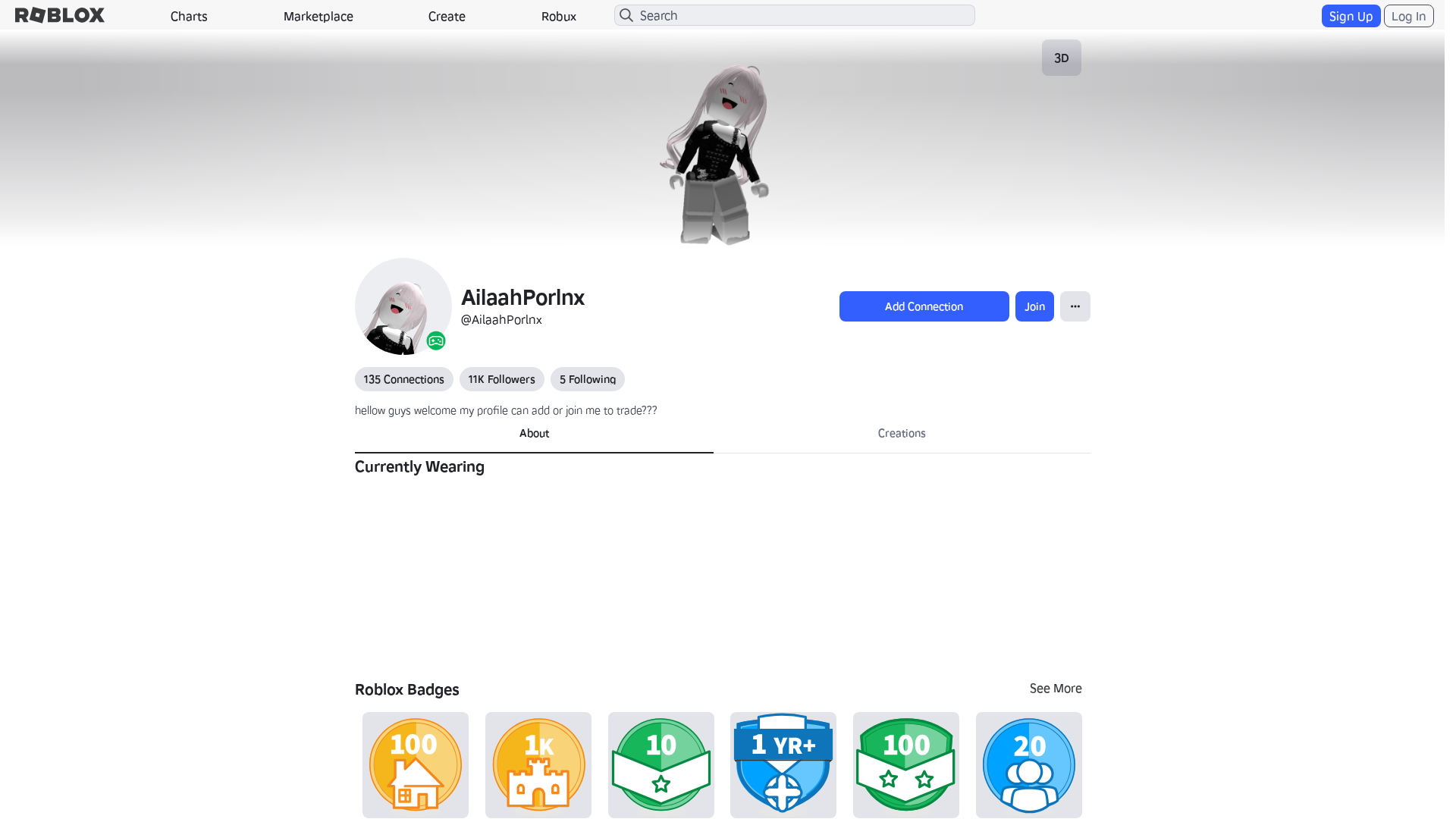
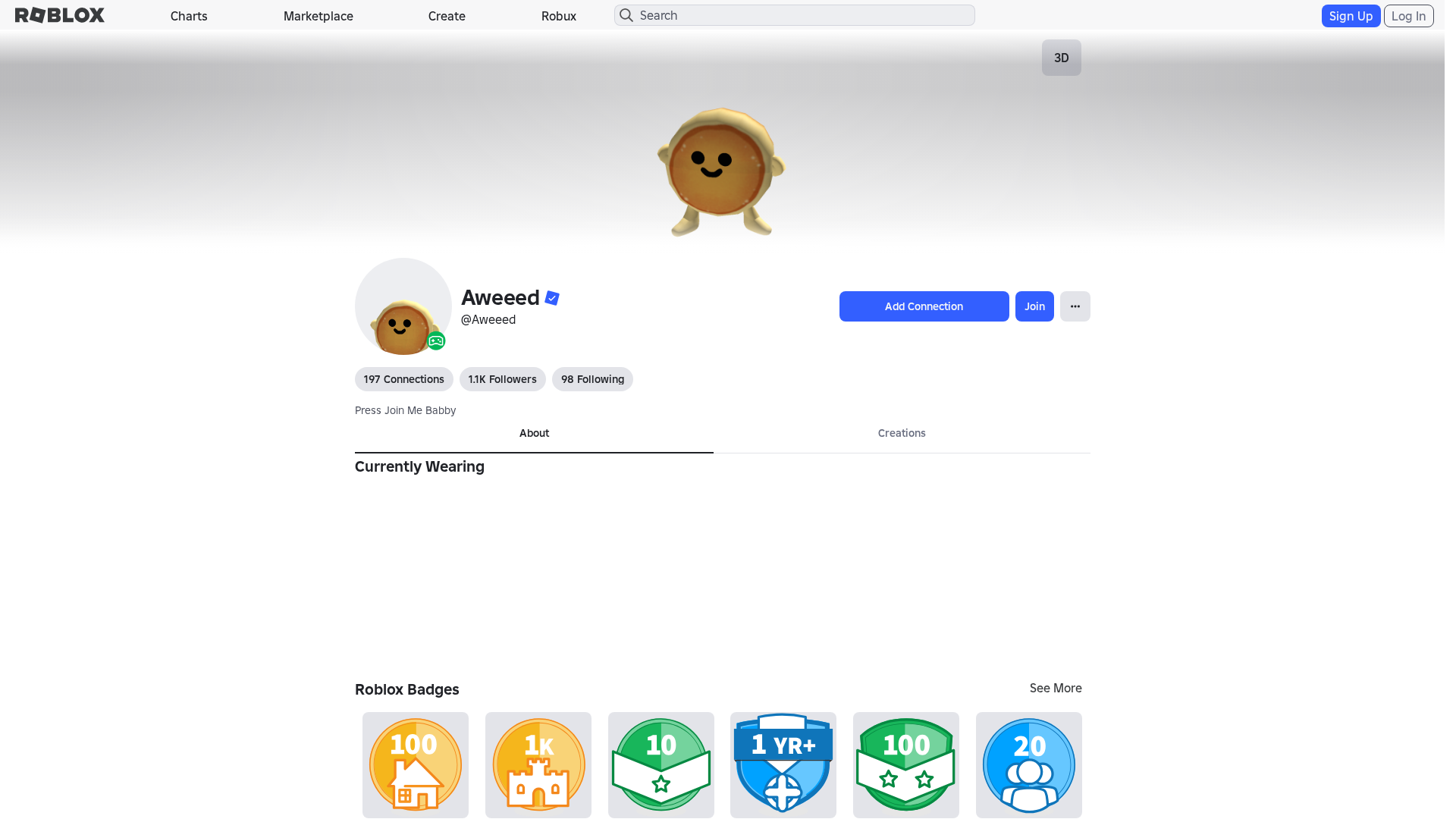
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14C93B8B29251243320BFB1D5F1297709A2D3D74EC68287E1E2FC636B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:AOmXWnSra02uOSuor8BPmzzXXMd6MiucCOK:pmXWd02uOMkmzzXXMd6M1cCOK |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a41367933cccec93 |
|
VISUAL
aHash
|
0000f3dbffffffc3 |
|
VISUAL
dHash
|
f0c8a63638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
07200010080 |
|
VISUAL
cropResistant
|
f0c8a63638002606 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing por suplantación de identidad
• Objetivo: Usuarios de Roblox
• Método: Dominio malicioso que imita a Roblox y posiblemente captura credenciales.
• Exfil: Desconocido, las acciones del formulario sugieren una posible exfiltración de datos.
• Indicadores: Coincidencia de dominio, JavaScript ofuscado, acción del formulario /search.
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- /login?returlUrl=2058347444
- /login?returnUrl=
- /catalog
- https://www.roblox.com/info/blog?locale=en_us
📡 API Calls Detected
- POST
- GET
- get
- https://help.roblox.com/hc/articles/30428367965460
- https://apis.
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 106 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site likely impersonates Roblox to trick users into entering their credentials, which are then harvested by the attacker. Form submission likely sends data to a malicious server.
Secondary Method: Redirection
Redirects the user to a more sophisticated phishing page that mimics the login process.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for httpss-roblox.co
Found 10 other scans for this domain
-
http://httpss-roblox.co/users/1721859/profile
http://httpss-roblox.co/users/2058347444/profile
http://httpss-roblox.co/users/1776344257/profile
http://httpss-roblox.co/users/545015728/profile
https://httpss-roblox.co/users/1567517298/profile
http://httpss-roblox.co/users/1338275603/profile
http://httpss-roblox.co/users/1776344257/profile
http://httpss-roblox.co/users/1721859/profile
http://httpss-roblox.co/users/1092230912/profile
http://httpss-roblox.co/users/302054218/profile