
Phishing Analysis
Detailed analysis of captured phishing page
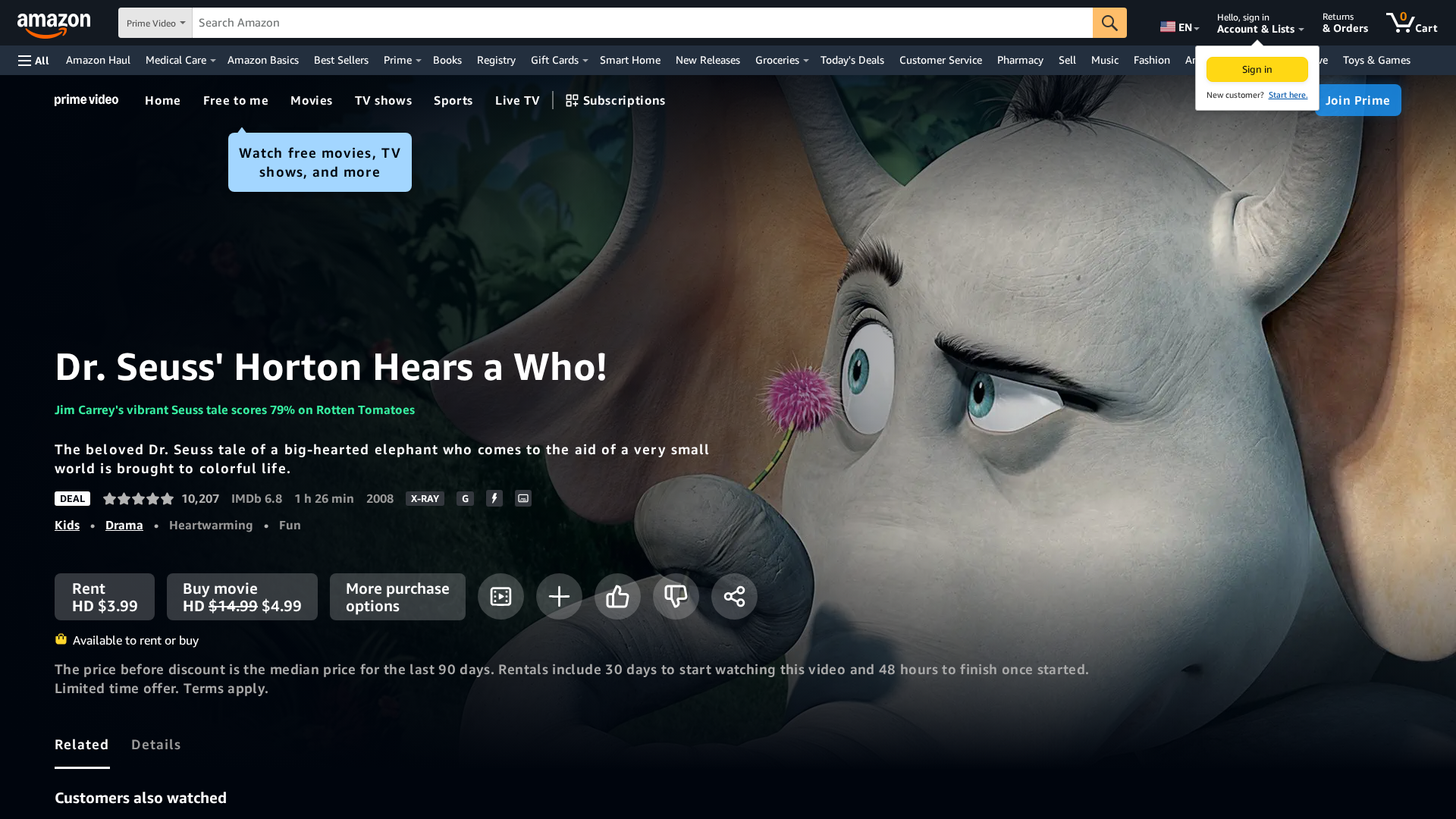
Captura Visual
Información de Detección
https://28kjhga.pages.dev/-/zh/gp/video/detail/0P56VHS4S74YPJIS71635ADLO8/ref=atv_pp_tt_16
Detected Brand
Amazon
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
d37d3095-e67…
Analyzed
2026-03-02 10:20
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11D44D8F69294007312279BDAF679B75D21D7B16EEF0686C09AE4076C1FF2D46A12BC30 |
|
CONTENT
ssdeep
|
1536:hH4Z4jRiWN+3nOFh/kggggHQI2duiwJw5TIymOgyYcR6jf5L67ZO6jw26jepqf63:5ggUWNL/wQPdW7TGqEqJ5X7Rk |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
92854dc8cdde9a9a |
|
VISUAL
aHash
|
7f470f0f0f0f0400 |
|
VISUAL
dHash
|
e2defcfcbcbdac38 |
|
VISUAL
wHash
|
ff4f0f1f1f0f0400 |
|
VISUAL
colorHash
|
1b602000000 |
|
VISUAL
cropResistant
|
808082d2d2c28080,e1493919c8a9a9d0,42b0565327231be4,f2d2c0b0ac98f8f0,ffffdfbaf4ccdcfc,e2defcfcbcbdac38 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /gp/video/collection/Musicvideosandconcerts?jic=8%7CEgNhbGw%3D
- /ref=nav_logo
- /gp/video/collection/newandupcoming?jic=8%7CEgNhbGw%3D
- /gp/video/collection/mgForYou?jic=8%7CEgNhbGw%3D
- https://email.aboutamazon.com/l/637851/2020-10-29/pd87g?utm_source=gateway&utm_medium=amazonfooters&utm_campaign=newslettersubscribers&utm_content=amazonnewssignup
- https://logistics.amazon.com/marketing?utm_source=amzn&utm_medium=footer&utm_campaign=home
- /gp/video/collection/Awards?jic=8%7CEgNhbGw%3D
- https://sustainability.aboutamazon.com/?utm_source=gateway&utm_medium=footer&ref_=susty_footer
- /gp/video/collection/primerolatino?jic=8%7CEgNhbGw%3D
- /gp/video/collection/streamfree
- /gp/video/collection/BHM?jic=8%7CEgNhbGw%3D
- /gp/video/collection/AccessibleCollection?jic=8%7CEgNhbGw%3D
- https://www.aboutamazon.com/?utm_source=gateway&utm_medium=footer&token=about
- /?ref_=footer_logo
- /gp/video/collection/inspire-and-uplift?jic=8%7CEgNhbGw%3D
📡 API Calls Detected
- POST
- https://
- /gp/video/acquisition/utilities/monitoring
- GET
📤 Form Action Targets
- get
- /gp/video/search/ref=atv_nb_sug
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMDAxTjRRNE1BL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /s/ref=nb_sb_noss
- /gp/video/auth-redirect/ref=atv_dp_react_sign_in?signin=1&returnUrl=%2Fgp%2Fvideo%2Fdetail%2FB001N4Q4MA%2Fref%3Datv_dp_react_sign_in_return
- /gp/video/auth-redirect/ref=atv_wl_tog_sign_in
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 9 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 136 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Amazon users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 136 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Amazon
Official Website
https://www.amazon.com
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 136 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
28kjhga.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for 28kjhga.pages.dev
Found 10 other scans for this domain
-
https://28kjhga.pages.dev/-/zh/gp/video/detail/B00...
https://28kjhga.pages.dev/-/zh/gp/video/detail/0SC...
https://28kjhga.pages.dev/-/zh/gp/video/detail/0RY...
https://28kjhga.pages.dev/-/zh/gp/video/detail/0PM...
https://28kjhga.pages.dev/-/zh/gp/most-wished-for/...
https://28kjhga.pages.dev/-/zh/gp/customer-reviews...
https://28kjhga.pages.dev/-/zh/gp/customer-reviews...
https://28kjhga.pages.dev/-/zh/gp/customer-reviews...
https://28kjhga.pages.dev/OXO-Good-Grips-Easy-Clea...
https://28kjhga.pages.dev/-/zh/gp/customer-reviews...

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.