
Phishing Analysis
Detailed analysis of captured phishing page
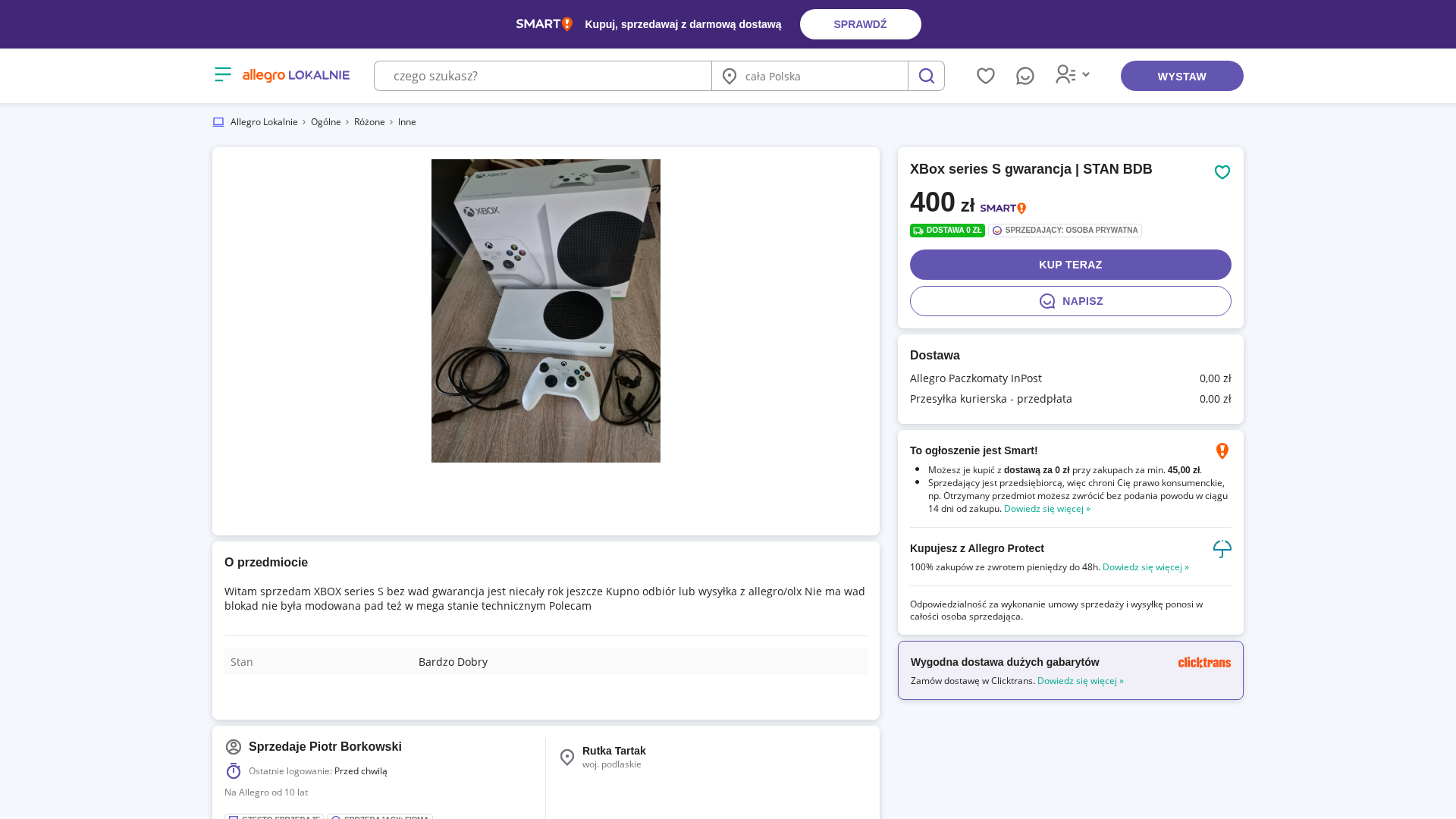
Captura Visual
Información de Detección
https://allegrolokalnie.76748219764164.bond/?id=8h1b8R4U9O7b4K8v7x4k9i7L8y3O8m4W&fbclid=IwdGRzaAQ4tsVjbGNrBDi2o2V4dG4DYWVtAjExAHNydGMGYXBwX2lkDDM1MDY4NTUzMTcyOAABHsTZSvlRpbZ9-oqaY3ZrwuZCTSxCvI_jWrKNQYfEY_rNNx6yMJPxw_BbObuQ_aem_6Blvxt1Iu15GVG9BYer8dg&sfnsn=wa
Detected Brand
Allegro
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
d56df550-177…
Analyzed
2026-04-01 07:48
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T126733BF1A2B052B9418BE3D4EA36B725329791FADB8287D581D4CF886FC7C48DC57884 |
|
CONTENT
ssdeep
|
768:4vc34SiXM/JpfLVVEEs8VJbxt52QVkmHLYKUxdXmtygdlcVIz5zie7tBB3UM0Y:4vc34SXkr8V5TcQ50KUwtcVAxPE+ |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b9394e4613394b79 |
|
VISUAL
aHash
|
00cfc9cfcfffffff |
|
VISUAL
dHash
|
6913939a9a629373 |
|
VISUAL
wHash
|
0048c8cac99bf8bc |
|
VISUAL
colorHash
|
07000200030 |
|
VISUAL
cropResistant
|
6913939a9262b372,241a5a7a3a5a5a04,eec2f3e6667939e9 |
Análisis de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- fromCharCode
- unescape
🎯 Kit Endpoints
- data:image/webp;base64,UklGRh4jAgBXRUJQVlA4WAoAAAAMAAAAPwEAPwEAVlA4TLMfAgAvP8FPAE1ADIA2bGNwJcUB/X+w7WwnRPR/Ami7Jfwy21rd3RYocU+ySOEnWnILzmx1AwD18xdAAEnvQFa2BAC2RPEOACZJ2QAS3fLFX96NEkmzhezutrzz+wNI4un+o9u2RV3elCSeQFvdaPhk8QbwqrLt7m7bgG2pT+IrkZRI29zc3my37BMpCcTFbtvc2LYkXiUApEjbzaa/yxccH5Gi7Sj/ETybawlgbYJpu5sfZGsHtapI/miqIEm4SgAgADCp4vZQkvB9K8R8335Jsp6HJDX+KmpGRFRXiNQnjjE4BrmRHcHoJ6qeR/o9J44/QmRFRFRVJsk66YAxhsYYgiQlUkJVbb1YD8nDkWPYCqoBCTuJiQJu2sYY1vEgyfEo3kpIOPyjDVjSE1GF/RsvlKSNFSHsIsYYwBgAcBmA8EdRkgxIMnZhl2RamrdFkdUQricCEKB1WSQlQBRPR0kmReFcpiQAlPQJIiZ/c86JzMziBX86TtREZVYVLuZ/aK3SU0BVceJobdLvixjBykKt4sQxcdWXZpCZlVU10Yez8H2uYGZmVc3V85RA4bs44xCBtdYEtO2pLylF8H23WJoT5yhUqT8Ac60Vh1xzRp1QeF+huIDc1lpcdeAiP+T7vokk5wIALe6ZcVrP9gMyqwoAuSYA7hmZgVjFOuWvMnEm11rr8GbOwFr1e99n4duRJEuSbNsiOPr+/x/Xj/ce9zH8IRFwGAT8kpfxC74VSbJs27Yt7fcc93xsjKfy/58yGI/3e6EQBI5jOEbgBEGlUKBs23bbRtoAwSA5VBj1/38Zhp2bnSniAej/BPgmp/w8+8j57PLsb2/vd/HgRb5R3lm3Ps4qFgsThRZaBWKUXPwc+Ac3GP64fgRcNw4junNdGaTBt1/nVKKkVlXkV3lsFUrFpEwr4SMf4pP25xTaWrtgo4UAKiqq+5+belNRxdVU329XiMGtEf/m1/koH/KR99aRnipT8eyCk3aS2M/+jEH7lFrTyoyZZGLgOnH+wonTXVF/oRY3MadULs5wxr/59VGXa045pQSCLIQRRqQWwUvGgzgkI0X6heqqqKg4f6GiohrIpSLmFeQ0xnPXx11hsiABGByMMy8aleOpJ09jGtTmZKIZ64OH+gv1F+rN+QsV1V096sO41HSxRuU0d925FW+MU2CMMRNjr1+ncyYmZ5V98cVBuISHH/9OfTgfzocfPSrqTUWlZKZvKn1zFbQtN8ZUE8lbtjjm4Mx8qMmdj2PbLEwpCFsmAqDiBNS/8+PfqX+n/kJV8U1kVa46FKn0C+fDslr4Acdmj7fzhTHGmecje9/f9IsvvjhnhMAB6k3Fjzfnc66HifkL1bwFQU+SlNfN+axty9Ob3Jdl6bXMGGOUq3yUcwY7RuTMmTAL3NRfqKg3ADSBhnCla7hiMcleam1v7x+qrU4n5cernB0VNsurxLapssXCKFmIcHBz3pw3bi5cMXmkzvr16I98msh6UMc/0/L6lH2Vno/jbT23tm0t5THTmdFCeKTSHvKghYIIww1U/HNzAgY13bR6tEUCdm1+7LK8si96eehj7XQ55fT7c0wERqk1U560ydUqVIhQlDvcnA8V/zAMNPSOPGq5B7iqO1or3Qtpq7fTvXbsuBwXo9AmSRYr2yjXa0680qL1JvgWvjapMazbvN0Q7NixGVNufhxGg9K8zbmcx+bCwwoaMdOcpt++rFeOHC9u/AhwAzRc+q5vi9mAg3Fw4ULIIOiGiUAg7oybwPngwU29OW/qz9Sbio7z5tdnPR4/Hxf52XyK7/Qpv9B7rQEYAwB2umS+Hy4u8PUfuFBe63zWftazfNJX+to65Lv8lB/0YTEQDACABxqY4P8ecs7P4+c5T3qnr/kLfco3+UYfs0bzDvhYxZ6+4gFAAIB1qc2P+Xn6OOf76Qd/br/zp/U5zxsYHziqrpxZwMNnbh7mvtqqmQfrWa7n0bNQoa8zecz7+jk/5sc8vZbWAH4XhwOI6mqpGriBBwBwc3MDICtNTKjyajOPRdl6W76tivEud7XIhWcqZyP0YLTycT6+Y2EEPnRzcwMAJ3utZlYq36hsv//7fD1bTlUqUqb2dJTHnmNXsybAL7j5enMoarm+5xUAbm7wVebmAgC1jmI0tbbVvtpWRTVwBfz0D8/58vQhVMOIRgcAYABu2jvBDQDAA5SWpVmag5aVxbZc97f1/G3lKz8l5fp+qIEhmgkATG4MAMABLgQ+NoW9ZzUevU9Rc4guQoQKvlVUAogQ02s3lONtvr/Nhz9t4psqRfaX7M/r66zWzJvklDF9ecHarCKITNNXOJ1GmQri1jdChQ7VPHgwebGB6fnP8+0vx9vzOH95e/wktDu7czgfAHjYb87D2hVKlnIWs1JGo6c7j2JwgA4d8vYjDx4uWHcIcnv+sZ469FFLM80B8NBPvfKuiXAHWJipkrpPV628+E7DHtycWwe8F+jm0GzeT2vDaG1ppplmla1wONwAgUDYtm3bykWfcrrzPZU8i9mnt0L7QISIrC3RjGQnMZNEzwRwfUeAwwEWlrGVi5vHwlpZ1urIAz72YoQKMEP5jgsDA5INDc5spCKVwAGZYjq2N4tO3hYjd1jrPd1CGAIAj+IWFy46cYKhYXU38G2H00tNDfk8gDecysd7Y+/ZCE1hEbOQhwt8qFBTTV4c6X89mpnk0Ddu3TggDesuY3tNed5aUeHJg6fqsmsTQvbpw+D2Tr3k5aiI4+w1rZOlpgzgBgR0Ry+JGmqqaUxj8uAQpBmwwW+Bi4sLECfk5fWfL/bpHVnYsbYkMiIsCVaXgzqhSVMNNXRwoFtRNQYYAOACLgCezEtdXmVrQ4czNDRKUzOHBuJrQcf/ZTc6Neoc3AD0qwjvxvgF4AYQAKxmXgCLw7s1tsl8DC4QwrYSXLjoVTSBG2Tc7Cii6BIHALi5AUAf1mVdAIrFb20ZsgABgBcCzQYb4TMgoRdP+rtX5ACjAQC8+4YXOgCsLCzzDFzg/Tc0QKG+DNnQrV508S/9u9e/UHWBxzsAYOgAAF5my7VJgo+JxiFu2dCm2WeUkWLZSo0O1fgEIABA8FsQoAQAmsKULU6IW7xEm6EjECoq6+6a8MUBABgSA7gN24g4QELk/Te2kv5vEBETMBLgQZKdJLxjz1peay1vt10SwrakBNvGiKy11l5rfdpbBXYlgscGCc236XVbwAx9SUKSiL/5GzB7QEK1hIDMt+VfkoAA2QiJzP4n14uEQOSs23Z/kSQASZYAMhfPeumlOwIkCUVwWbZ7Rz+jimvO2i9Vugw/3S+z1lqDmEBbfOmXFmGI91qrOAmkHZL+JklGtl0BmUnUSUyrd3ydfV1L4GRmkhp5Zvb6utnbAktScuY550zkz1/PWFVbgcDPOefs6d8+7l1vc845+/g/qAK2n/PWX1RJCN2xfXbOmdb+C0j9rlrZM/ky3wTqVWpbkr33UevPv61umoxt/7NViVfrysb8MD99ZFnYkgI5Nqa1KlWqJNtOi6pWCcledrYqvWzPGpOItrSUJ8msncxuK7WzbOzZ21YrqArN2XsLtfZYbT3vJLgFUUGe5+xNZZurZ5JkZoyMVaLnfbbr8cw4tpC094AHRElyeU6LZ2wFy1VnZhtopSTP3QoBCUkZ2sRW2wp+yYwAVOXsPUHqnSZ57sngGSehDqJfbfH8MMZiJgGiErWVZ88oyXMPzCaAkzwp4+K9Z1z4QZ19SICcc04ZBYm2JDy5RF17GzJzznmeTHhXKEle5+W9T4zmvJ8zAkJbLs/znPMk3ntnzoQ5J5JMk0hKkud5znkd9t6YZNt2bbfRXPuce9/7HwBNeltSOeu2Y9mB7FZmKcvZAG9KshCI/8y9Z68VIX5mG3xLkmRJkmRbRGwedenH+eDrV3d1uAl5kiRJsm1bkpDE9v31/+5j8pn5dL3lzVecrRyMIEkyNGvbODx52bat2pIkaa218dDlRwIqIqqibGzOHMnMzPyXv1kDzqwAMzNzOgSHMbmZgqioiLwn8vDioc07waMOnAVAciRJsiMiqubuEZlFeuju40d8Br4Jx933ZnpmCTjwP/REr+8OzjGsu6sqM8LdTFV8Sbat2rZtVynlUlvrY869NolZ+mOWfpkhSHwpMIoDPYoCMz8x7b3XnGP0VmsOtW3bMPADbXTKzlcAYNWSJDERcfDCw8ysysLuntmhZRIzM8uWTPRk6ivQJJeZmaVlpsGGqsqsyswH9108FOHJk887km3XtiRJNsZca597r7tHVDXGzUuz0xxgRBZGFIDP/sfdmRnh7veevdecw2MkSY5s27Zl5pE1xtxADgMYsXHOxZevTdmVywa+HGCw5uzK8Eg+2LYtmxzbue7nfb/v+/+/qKtZrNFi5s28t5kpcmSHbGc7dYSxc4fOnDEz0+LhkTRSd0td1UU/fPA+93HMlEZrU+5bkiRHkm3bElGPyKzuHmPOuWhjvPe37e/Av7hpP2KM5xyguyorwk09SZIk2bYtSUQsauvsc+59Xte1+2D+pHym3q3r2u/dey8z4XAFyW7aSGWu2ToZ8utR27ZFkiRJ+uj/fxFRUTNzD8xsZjyKPn5mKIZAdwNVFfjhg+uqo/AYSbZq27ZtRWSprW9S6pBUOGGzspdxjlZLerJtW7Zt22pyaWPtj235Cc37RIt/77tYUcJFFAiKbd+zeg2yAYrC6BC/tW27tm1JUm3zvI+/AQpRxhmPgS4msIlhKmB8Vi/lrrm/DBLbRpIkicq+x39777aCYiNJgiQksvcR/tsLNxWO2EZSpF6mudYNNdTA25MkSbJtW5JExLqP1fUMbEA2/zlYuza7W+h/s/vn4FuQJEuSJMkCZPWs7v//2luakG9JkixJkmwLSSyyPrsvv92doRxqIEkyDtm9bYT89/9TJLmxvbmISOasLK7qruae7p6ZntHMSCNZZBLYy8zPnqVzLjMzMzMsM+/6WMdsS7LIGuZmqupiyqxkiIjnub9d3to2KZIk2fp/EQUzc4iIjKys6urVQ5uZjvbd0YXhKTPjQFFmZIC7gaqKCHcBkBRJkjSJiKqZe0RkZkF3T/UO7XfMfC/AL8UMb3P/7g3oLzPfQG9Xd1VWZmSEu5upxAT4w7Z/kdP+/66Z1SQbd2F3E5wX1dcL6m5Q6kLdlbq7u1LBpcILh5bUjVexClIcCnVIAsQFIkR29z6OmdmQ8u77f9+SJFmSJNkWsnp33R7r/z80qypciGIbSZIkiRY9c3v6S/vNpIcjtm0jyZk95up6rkzrpIN9exYoSZIkSZIeABKL+pL79hv5/z+Ut6zdI8yUCQFq8foHh23bBhKV23/j/5ph27ZhqOz/k1eHEgaEoKmaxL3Zm23bbVtr27YiAFKyj8+5c/x5179Y9/2kHSyRAFZ6UiEoNpLkSJLMs59pzZWmFRDbNhLkUHNI/wU/sg41bRswAEKg8/9HH52Sfj50F933z8WN8Kx5z8u9Nh4Mf5m3frwXpRH3wmqXBaltH8qguMP4+D2HxxcX/mVGefNRHptwYZdxfOEksRVqUZ7TBL+ELT/GR22piHKAIKtQDyN4qREgyHfrjY+5CiDFAuAQzx4Pzq5fEkWaJaA5AACFfeQZVOQJhW1c9UX7w9vafly7/V3t/ap8G2ehjiubGl3d14UwALlEQFoK6kSf1sX75HziI7GzZntxHevol6MkGvUeFlf1RtN2RFnc+DmOLhZvj1uoODzhGu/MgnPXbqtxjk/QF9YFmC+NcQsNquvIPuhwefJU8qJ1XamaIQPq9OmYa6jTtC8swB3dFHvenN6pf3gDYAEusJDwyfT5TbaZaeztu25YxMp++/L28iu/dHJc1Xzn/Xz8/vPXpMM/er2+v77eyFa+5fev/uunsv76+8/5+9vvTv/cutP+8N+/v+if3+g37pfdz/SFp5/7/29/9Pe/P/3732aqd7j4z5py9s+bbw2fPLvp05rnU7NWZs5aHv7d7xvbUwPLZjw1xnjAeDLYljY9THBwkYhfcP/3v9kdFFwps//sv/iX/PN/xff/rl7JZ39Qh4ptevT+/LW3rFOjrQ92DI5K5ZbGFU9//7G5K3XJW6Hg1hk/dH8N3k/vyTqQIEoqhlU/jGF5R7fYX0yzARAD2bRRdQcm0BAH/ODZap+zbHjBcTYnY6Gv5BO3T67qusCHKBZSIUVOiwJBrdkxmhpNQoNBjkfGduaqVGUZVelfYjhg92XWY2BGR1uhCuTuUH1sHEDgiIEpTXPvj9svXzNeGQvBcAEkh4D/GAB9/y+P5RuMAEwTzd5I5KxInedbPFFefP0rd3q1qrIPenrWZygxgFAbAUYDY9vZjz7USB4koDSX5qxVr/fgCk9z7gVsPpmot3lhsagkIgNz05tsdPgKP5/DGaY4JVkrtpAQ6+gVYGNNadjiSuIWU2d23ufiYXkxK1NLrZ0Z1Ywl0HZm1TURBx6KgHckscWWVoYXVr5VQ5q+YzSI+rVqiv7AR45Pnz7zySLuHAnADAAAAChQldTBFZ+uEQzmDdGkkzDiG74xYF6iUEBTbzWKZR05RtTSkWRmrF5WF01bLZBlgZowTeKiseyKuqgRAkEo31VbM++PSlbFpEDocsx/spvLoRxbXVQPjt4wJBVR/20VxoI086iPVSa/CiP6KTNhkNQV8ML9gh+9tfQ+jRfalSElhEw0CAKcsKEzwzYuFwtFWEp59SaHnWllSMs4TtHTdutq0iHN4APuuJLsCuDCv2aNHx6f3l4udVn1g0ZbEUuCcXmzSJEzsIzQxt7RHkrfrbeT6Y8+eJgKCREBwHgY/tB+tWf63kvIM0uWBwDw+/8Cfv+/BJp/+3/cOC/grefS2SjLRrAQs5+MSGV3pdrn/QC5Xrut0YBiKBRRTCagl8JyRdVLPnjObGxgKRVYrs4HxGbJLImNkrUawSHkoHwQWKMfMpErKbHTHyI00UNUg6oYE1RZX+asvEjsaMKa5bySbIVSmnCRc89WbbCidMcvREL7Odc5GWJgxMSwT4vfu/JH5V/QM0UhhUWWkoe+RdL5ABeggwogBVD9sVBowJACKniABgIxgQYAATQViEFCpUoBzaqEuafUQ2XhXVZM1gW7opzQS+yIhBLHEDZGKQCPB+ftaJ06J47RShiHu6vadihB2zVqrJ61kpbGr3nebk0MvkY2bRh4Emmux+v3h0OufcGTsiCQSETlcj71ynMLbjhoHLeMAnIBORw6ASfT7Cni+DA/HgKClwfbiJhdEqYESmqp+u/BPMPZ0OEXFboTt1DXyLGQ4swlKNfJTHiLRbFkXZwzOZw5GRec1Lc5tNsJ77W05fpRPxGsPA6QFZhvfnb39+Hr7fAr23v74XwpQmEJov4K/Pa/yH/3n+Bv/o9hHoOMCCg8uDmM0eIVmRPldOMINBDQPU5Go0gKReoVSxSrqiBWUIDOv6YJWu3VBbVsGccUlIE5k4MSGo4wN/ZIEyOzXMXgiJfJODfflPQWRVKSUgqnO6+TVWzFj1L8gGfteWs9ecVSkPwQbO2qMihPaRU25aRURb0QEKDps+4Qnsr3K3r43skbmei1ZsLOc9AhQkd36KjcxC+O3qKmKJAiFwtAI8pCZUgOE6MBwJSUzg/GDHAwgBgyiYbGFIpBkVagLnRnTPxYGgrbkkF+EIKshBWtiqpNLkyloZYFGzU3iSCsm7qJIe/U1z09h2qC/R5td60synJRBmvmatxL+cFeXzxyLtyBKrWObOyB2HimDa/DKv4Qxw/lWHqOT+7M6AJ0MAomBj1pTleP226dNv15+HEX283GVbZ2nOWVvCuqrWIZabB0JIsSCmFrUF06ebkR5G22DQ64PNgJXYLYLHJbFX5TjiCUHKwhFj2S/0S2n8anINIq2FraAwSfytmDfFosXwz6bOfjzvGxdNfRTDQg/pX0d/8IfP8PZQp7pjvFne5nmEGKUf/N/1bKYypcj38dYAnLYGxWCFpkVB1THFNA1JW+/Y8clDBp2p7rqeQEnjsxRJ6yaiFBMvc4I4DYNT67aVB+qNmGaWJqeooKK46OmmnYh+fK9PLxDY7fRjjAFl4LEiSAyNItI0pta2VsXurqjxmCGqxEWpL+Hu6plV+9+9nhtnxeNPL0XhgJGEJYYffcFvbw6aOHMAwohWLAIlRAQWKUJACLwwAwIYiFjR30HGCARNuggCW6tKJzhSlUqwoigRAFUBU2AAlU0QpWa7QqmbIQSj9lWXf5t/d9dogCXTSmZdLPkyGvot7EozgrKZJQ4z99ycvHn4qbPLH3EPgxVdZ5Xxs6krg94AVaCqKSbRXTDOvCUrpywAoHYvhieFiIvJITrxFsqNfB3270+eCiISQpIjazgIZf2BaQlNkbV+rgbwXKFWW5V+q09Fi5G93Ektd6dh6SUpTL9LIulaU4ZPRhaKijdkJifGRXb1kIYEUqIsDiHiPbR/yd7flntc80PiyvXUwHOsoVQTnNv/tHRuYStFWim3v6uPx/8b/FLweRJJD/CngVYBVrvNMFYiZKSdaTXufFfpHbIDq0wFIP9yxH5+Zkp/MJczP4rcUwNyu7BxTnqCEGH+/E7IT8Wn86BKkHUJUsUvFUY4vGgac3TO2sgxO++ID3iV9NjlgRIARBUMhtUJRsxF13U3O1dgzpxC8pndpLF9rtu/XwwhqDamvf6ZX7HIgQKifccXcvibU4AF4KARAADBSAgcDkICiEoV2sESRqeiyBwBhaNqGAwblsqBajAXmiY2gDYAwKhlDEigiTNoA4ySc+yxhaJQAD680WRRNkME8ucjdCHecrv5WfV1PRQX4gkvDJ2Ma0aP2z+8/ofu4zYjaCvJ3yB/eIjj/aVcGoRuskZBjPDx7R0h66ZUEw78Uo3eXdJKpvyivjpV5cfXTfHkk4YE9wNzPUUBsEIsawOGWDveLoiRUGpyeysrxyOV5rrnZuX6x3saS2dCJ6oYWIxrSgWksooMoIGIARADBAQEScwlnoy2WB80z96/V1T2PafUy35UmAmkKraHtwY6hZyjg8rOxieY+LcbEHu3KaMZtQzKj7O0vVwVDX0i/uTu6qNu0JU21yJZ5O21ed0ZNY5CwXFOXhYQ2IHKQkeqjzFf03eYYjnPIv0C9QRoxza3zn7lCJQiMfX1e2iyiLpbStU7W/H9xr1KzrNCoEHOSp1GihaAiFPiYC106lVktZYIDDZx9sUnoAaQtSZUnq1He7AgCwmJtSxjizTBwNiyoiIhaJBKBkdFWLAQHA5ATBl1CGsCzveixgF4wre9iFTVVXrZ2aVMDulG4XUgQEBTVAxDItA5tpY1Q1XmgRPz7KjEIJq1cvrLev+72bRrJqnnwA9dHDPb/gz7/+k9wcdACMSkujLj6qx6TnYzet978+jP4exqpUo1vgGhMutWl8tgW80ZvsF9COIKE7IUtREyMBEKFrIg/dVdv3sKDHfAcK9t5X+DDKzIImNkB1YAGlHZ9ejcdk93ZVmc1pOVS1fCt3tiiAMHIyOwaUUkgJxFpRIQAAAMKwdy0FAAAATKErUpTl9HVl82qVOw5AJu4hJyDh8T8LrbmnADmYMccRrjr1tqbbdrhn/3T1zL0hEjlOc1ykAHEITvN2mizjsgSmZn45vnI87c/cYiLi++F7HerHnzFpi5sQnAuj4A5o9FQwXym9/zblTxqebQ+t8+uO/3f+q/IHoll7bw2tpCUKYbDC2tUPZewOumZRa4GIFjxLpGjnlgAhOp9ial6Z2xdQAlDc0q1yE03IgQCCoEsgwLtALLi/mMbFYTUBrJWiClAAEEABoRAGYiEIRDEAdP8tYECGNKbFYGmDgqIoKyxSVG/0stSmMUywAE1pJEhqS27Qcql7PIpEsLyy7BY7SzTTFKhBQ7E7mQMkoiE2zCQxgiTkBZtzfPx+vvP/0f4+H4ZHqTqJjB69p+J3Kza8WsOsujMIz925N2lYwPi61TFiDL5O8g+TDUWdKplwai4qgk5iEIJBCgYiDDbudyb1G5Tm81KAJDwriYQv9uyn7Enz4G+4Qtco4BCjqqz0XlAAFgclURyBrygaJeXoMeuHt7Vudtg2h1i7gNfMy7A5xkImgK2Ja4piNzuM6DjJTZGar4c+InAa7bu3OzlhmuoCyo23+orGHue0Tr5HzbtWOGMGJorKcnEa3aDJLR1DTFyBAtIMaktZ1S4sZ6a42FHenFx6dt9Zb06Hcl/PPG8vTh/RaSy9mCo3IBXdyOvk2WkcRjy1eRjbDRzIdMwKbiNbr1JXhU0VLUhMpDqhJfbgHBDRZIAoKbhYwjCBMAcjTZqceNKaEg8IAHiaHGAabeUD1u3czWXGpNM6BgIIM6bZEkjew+Guw1TpQAnNrQPDFqAIlEELJKGlWO+EfVypwCESbM3jnY/WlCqhEJGIQCSgIAkAAEBSajHSNgkdy6/5j24YIwOF0xAU2CBHnJHfGug8jmd5no8QPBd0VK5zowx66BEamjMmqEDJtJ1rYlzSV7JymHH2RfaIQLYQahAWbzjLRW7AAJqZBEAyYuGrYdDVAc82VYuVU5HYbWS/DhuZUD3wxzRrTSgKTAu68itRlYJGVLl3517Z1VBYTtdPn3+5nnngFt47cE/texNFExhydtdzdXK55jD3J+xb+/MoVzoXf8zjeMp7XAqL2/XLe+6YpGPBNNTe0xtPBMrp6Xb6bYJ2JUWJSVnqJYTl4hCG9ym3q+HEDitSoUq0EQPKwDnT4vMHr052zc3N3eVw5YQ8Wv0G93CwIDCcqLGszG13nlAEuSr3u427ShO0RmMuMCqNxOaWYUXHCWZns1KtgIAoRFXtNCoaG9PJVExEjHKyvakGi7W2DUvKjCGGHBQQYJfNQLv/RNuVojFB7pwpgpq5VXNhxxYCxhhhTKIS2MsVMUiMwbQTipYuLbXWXeGW0orpHPbVp1b3IksOKgFBhqQkAgUWUmUUBAqxgRXY0GTIzuaqegCLpsNKJUO3gqHTbBofDXnAoNuIRjIcpRirQT5HrJVL7CezJ6QzKxLtsMKjQU9ji4yxH39h2j6bwgx7ZCj85Z76Am1ExiVH+eZ0EkUJna0MjuOpS+VhzZMbqL41VxXdjA4VKmwNTLkJHl9jVm2hKEBV8cAQB6iAimhwdFClsiFmyFEbm/HZ6+e1WWlr2n4Or9fR9KszsxySL9ErgNu4+wtTczDxqi+m4dvcRY6JRB/kv0ITJWBUhHO8V1APniMhgegZnLNEZ7QAbbrMlxmWnvJOPx6Pzybnth4SAQAAWIJ8PrdrPn/mD1e3N5udx/Yknrlni/5keFgW2jmUnfSvWDm5bYcHOIWtYf0gH+Ilt22LcQCoEaHLQILCx+HuyNO9llSWaMm2K2WVh6MdniufM8DDh7MaJxv12tgnBctV0ZheGYAwhOdQw34ua2ymKGhuJDLsWZYV1vuqGUNj2nlXu54N1KqGrc0Atxmpwrsvkg000E7BYvsosc3z/RT9fEpv88acrZqPRt0LPbrV6McUqhEBScaRpEAAGsBBSgBQABUCiiNrrLjSMnX08ZJbGD++m+137z5LmVux1f2o9a7vHbSY3k81X2uZCg8KI7FmSVsPwt0W6gcxLwZokGu4v8NLA/7CXe6/yE22FD8KV86rdw8o5i5s0Iv9ICr7ZM+LElM1/oaB6cQD1i4DOTwstp5HSRHiRA4zrqm7QTm8t8QAzBK4O5K0feJYWoETSxfqM44UKcUkNnNnscNyP8OJJl55rY+u18yPCtr2BXq7T6fZY9U9Bc5uAcyjjUUki9QF/6tZq9SihkiaC9xWgOfYixRbfpTzibjJclmmS69tv/9VeB7uvj08kNVptyD4MBNNAWppp3JVP7dffpLx3G6S83WfvzGIxTGOyLJU5eYOvBnI8mAeUrEkGAuZH3RwFa7cJW5EKBRVL7UiiU/j6RBjaMGVXAE34boFiQmld7kMUbJ29WIrq5dSrt6hofXcVE4BAHbgmQAmSA+QgYSylS2zvDIKiMbAbFNFGXYWETTcS9M0pbkJQIVQQACWENFL6M71o/lj8Iz4Yz4lzy3e5y1hMqP0ld+rfrcqA9B0JGkCNkpQm8YigCqCGFuCBcQsfJVG+9HIkdc4TwX85L4l594bp8jeqj+bPoSM22DagWCDttRBTUOhRQhomU7Qf1GBMyFwjKxVKVlSt6UuPx1WjyzqqJXVg/kzcWXNftatdtuBqHkXuyXRoWQzTPRa83VbXO3b0Fw4mOtQ9GJzvxdMX95VUgVXqXL6mEdVL/sPnZA65nQeiV5mW6BIYOqz4ee6tXcuwmFQzTJpFxkIUAgmA4Jtus7dxm54BW9zKFaa2fQkK+GTxfGA48QYAICQmxU1o0BwwICIAcQjQ+IuPDrAqsWXSZjDs/e/Xvej5A7cZ3VCsEA0AFCPc7kJL3cmPF97rhsao2g59duoUFWoTH1AoTGMWgBQdculwYOSQZaJn7tWb+RQNQKoMTZ1LEeZpGFZaUrn1EtDadXG3W1n4xYdttLsrX1gSUdoS5An5gcbyek5LJmGYQILD7GCbQLM8yWEyWQZGiCTySYwIMEKGGMrLFUHPCcBMansIphLMdIAjRxNaJ/On1eYg1/13KH4YD/aCeRa5Y8c3HuaNB38mzv0tnYVap7J1DICBgJMAMBR1RqLmeQb6uv5cDIR49z84EcGt54lBPthOYIlkmnbKNMo7if3fY4hXmmi8d776cIkmJnA02ljJUAD1CP+/uGvDj2VnddxXzAzUzMpbwIfSApXx1t9OQ3mlq05NO+0v8+Y23wbnGZ4ZnO4iROELno756lfQBmLNnv8ONOr7dODnsKDj86bfelJO1zGmAKI8RR/+XOfDmUmFQrEmjK2IlCuEEHKAZFovbS59ts9xPD1YLXN1WXnyCN3ObQY40aANMdKYGcneR9aGAGImRCxsPBGNI1cNGd2N6pHPXijd6xaijzxSC0FbMNs2mYpuazPHO/WDNRiawXjbh4iQhWK1QIVUubJAbpthRLAmt12S7Q4Vqx0VybTBcZxNIiUSWhQFcWniiRaUonw7X0UT6GLGRozwlHLa6OgudldIiVWyEPQAAcl+uXvZrqqg11XHDAZFxvZZmKQqQNqSqSVu6xOzXbNoKYJXdeXNGXvIQoxSQtinvzww3V/j/h7Yaim8YP1p3w8hddl3Hb7RZXpgHL+taU5Uq96+1RHOkAHMBkiRHKFFhTCUFWYapEyfHTMwo8r+vJ58vZIZA3f6W7yvW83LCROwgOfe+A4ZjuORHYcKMcjRehisKxFk31WzslsFsjlvQjfYZ3lgXiFXUNbGjL9hnwZQJeMLLZZBeAQDc77m0tyH+ftsbtjxuKCbuFiZnZFOdvO7uHylsnt7cTQzdSJd8rterVrbm19t3Zs2yZRasnVXG7isP2oHD1oiQ6jFDXxlFGkSMQWHEGDsH/qTdwp763REW5H6g6aFPSsRKaUMYGFLrSWdSMCyN0aVy5wWLexOF+a893Unj2Y+xzkAh7VbGmhjTNWgIAiWtYhNNSQEVVLBbwCjWKloACgCmQ0DeLt3e4c3RTtUgGrjVqyDQ5oHZGCVnMhV5Dby4MRcO/Dwwf7lfuwjNWz4BhhYSYOQGF89KhXNHdR8CEvlHSu8NgKj4wTAAjALALQNjUWQBbAbrmOxDSEsWiwnkHks19J2iBsbBC8bJZE7YEgYNBOEJmEa//5p+Tv70UfKQZri7Ne4+t5zd4ffXtN5TPlX9j2exzLT9T4R+hTqd3zPS+KJDoVvYhRUQFKtdGkAAzfxo3Nxw/9yt9s0StKHrfz5ZGE0oacTueDKeah4X08cNEqaZnI20gHJ2MuK54MpF2zQ1VyNFtsJ/eou/mYu/PY+qIr4ovOielu0EWUM3eUHZP9i2qLC77ZD+OKHhECcNj0lUPJKZTV3VhhhrHnVm139KH98WDO71JtAQvQoDVeTujunEx1j1fT34XD5MPlW0fLI/lMPe3a2PEYywDgIWZY4RxTtMvNav2RDzenuUAztYeYLx3ivMXWEZJMQYqKaUgB9rz7trsejvd+58b4rGvB19lXKYbWVZ6t6gsrwkrBATgEZKKGsGKBWjUFifeyb7aYIhktomoASlYflLFtryHXYNk/lVuwQGEYmnJZnnrLJk81ORnGRh6/uX2Cr+PvXPnTv/DwxfHDAdSPyl6pjuSK5xWe7wj6Y/ipvzKDPaguAn2kHCWS3e/JPagAwHgnNUhv9r5yMGGdI0Dk1PtZKdUJtm3bVIlF1XyPfmZrIIaKKUSVgMIorjgkgcWkHYmBtfQVHD9Z+/3q/LdG1wj7xeVh0Ckb3PVLkq6Cvk+yL13kQ3BfbwEbecSvbs0AHVdvik9dQD+J002ocfrSFVdRhyJ3q+VseLi30uYLdRRTDQceWd/nelW3axF5Z1FP26+Bm0CHtxOAmeIEAABktYiUMAd3x4/d2w/5HfgkGGBI8kVIHXm47iyiI08nV3ElDlbo6bXnSlnqw7BSdW5hXCTsk8sB5/z8q007l24sHzmSXi0yGqiAI1TqYjC2xyzl8I6g8DqHJE+JAZaAWUDJoLueq7e2F2bWz3rDwtyYRdsziJPDSaTonmbd4rFj082SXEwBwANwAGMj4il5/F50coCwXlwtzACi7T7aqSc6M9DcNpTTUX2GKfFoCAGUglKoCEoBKHOZmQ4KjWMAkQAQqARRQB81OXdJoaVQk1DAs2VLG6U6IgFBALDi3tZ1Je/STu+kQ1LrdJ1YkH7Srl8IpCKXAjqgMdNykAKc5hpAkVxf8w3SCEANCBMxl4ykAMYuaX26wkoLrkKC8NaOCyBWGZaJEoCBazEGmYUAmAJgS+LF8GvuBdesc9RgUl6e8yBncWRScp1Vu+N2vZ3Rio9KO5nxJz/32lr0MEnBQtwA8vxEfvsfzDQkrXNbafsHquFxTUpfUX4xTFWJahxFdfgSNHC9HxU4C5QQfC5ekO2Y34038r8DoMmYgKg3IJJVKGdfrtIfwsnPMlLlAihO9hZOsmK6QLvpm0U8aQ7VGFjQYO6Mf2YqnpsMF6ZA++LZV7br4lseSztes+uuJRMJxqKpEwAB1QJWi6ZsJTFSzlzDYBjFC5GL6QY3Mo7unFdPnVuE5T50SGNUyJVyM9hthUNjGctiS3UFACwEIDfhyyLA9luRdeUsK2gshsOKE68X+kox+endp9unx4vjTiwiIAIw6F3H1cOMNcTyR0JJspSZVK1RUZQiAQBEYuF5hiQ76+yp1BPbUTXWzYAL1seepNPDRedckptxcp48EBYPtdW0NFaZLFImg0xLFlat9qQuPxCqP3t2XlkAzrzt5wytBCCwaY4tzznz1AQMyNSKIEAuHWO9q4pq5NNDAcA2snXFCiWIOLmpwJiOyi0WBgITMFJnpjO/7PHDurzjud+5O9pcqvgStB3hUdOUlUbxyFx4AFDnQ8FfzQsv010Uitz3+nH8///emw72593TXlTbI/mUh3w2QzWnbxSDY0ZLoCf+c1E/7Ngg+hiChDAONN0Shb807yQAq2pRAAAktuBJQbWKZ45+WuBBBEq26iyRu5lhQIqj201wxDiGhfFiFxswMuu3F4PlF+1SlpW6Wi9Xb6CbipJwh1ErJpUBiCjUSgEwYq0MFKqoD6EICIMgWThe5gyHywhSuCbksPvkDzEf0h23V2RtHIFIQWREJnF4MdYV+uS25NYaYdJSIqISiQjhUA/WF7hEIChBD6dk6X7bmmvmw4W02vYMslItnMDejxcQQEFzd2yGZQkWgELFgq22MhEcdUGNMlKDQUBXbaZLrWjs4xEVf9FkTSc2zrmtZPV6dIgdg8SWA59iyYwATXae50opw6WzPDt0VOOa6pr5rf5BisT7RduV2CxizPPyb41OCGSBCWAChmthRYV638iuKh0MJtXzC0n3uQHmDGSJychA4GMZVmYKQgEssGcio3BzyJbVEcyvL+CpMvjU5qjURkNjRdN6gbQUGOo2Ky5VcRK6jyX8Msw8gvXt5W696f5pP/p8NbRM+a2x5LXl/cntdUhLHmbQjjqOVEeVTZ8xaRJqMW7y9gPJtwcglc3OBp7CZFUEAKFPeFDU8Zl4Z7uQuthkVS5w98ilOtSwpNjdzroVEX2P3H56061hpzkrzMsPV2KAOBokK1bel95JKflgY1VZgwBNlwB2gxde1lG7JGhb+HaatCXttDtsgTChe55n+d+gl/8sqfPVPNcep+Bt6MjN735++W/cnTqvbZUc6nTUZm7Dz7E/rNxMXo2mOpFFrVDbzIgUbuRBhRggizqVB5FCGzWVMndo4zCWjAYiQHDod8CFHFUcDR5DWKoAFg15iDCwNcSa8cncaLlK0RGEdLPGPv4wp4mx6NobsIu97Rab3UM+KNC7ao7lYa8chrnStjFaTngxPm7Tumwo5wqIEAThLkblEfZoxCZdCUZMquTT5cdWxZcICokDYLyoN0sBlvf3yLzB1OS5NMvY5USR3MNr73zdbT2366qzRXNeOUq1KEApBep9aNuEgiCVLo9QvkhGmgTaETj6sqZ6Ne0bZ7ms338BXHKm63yKmhVk1hejEtAbiBv39hmdx2d/XPgxaMS9P302n+vF/+KjN+Xs334eps6+9gung5BLapzoaq1NB5XqpcFMG1JDlyiHPz908XC9zzDswpAC5u2oZA21PoOLzMg+dMsr47yWLh+Yhx+0TNHJNpg9OcpuPYxk4iORuEROKlLXbM9OnbAsSA9ZIaAUsYBMDQkVLwVyYKVJs10pE+/um9vJhebps+75sj446PV3Jx9+9t5aW5MU/sxj+TcyKa38R67+4zdctzAt3G/Y/mvi+R/WWuWWbdRiO7q2V/CT9rvw5WmzK45qB6KxUVFCogSNwTlG9sIlW7DQsUQwlJZoIKoWiiNKAXAQACCiAYyotsxatXREVI3aUowTcwfH4FVEGjtSbHUUJwNX8eRC78maGwmeY/Ze6Gw8PPd0oybxkuESlEW8iTaNYeGYVr2ZC7Itm3mNcKouGeiRPtbdirLzpUcXF6YoyXx8s41vdQsQRkyVESzXrlQUcB6ZmppIAW+CpCEBVu1NtQIfY0w0KdnN6ZTEfYxqAzUQhIIUxx+IbxgkbuIVSnoU8IoKIK8vT6fCUP2oZWfQeGuokotKZM6dvRZcs15Hu28858qZOc4DcbLHtWbqdXtv+Y+d9Oj+tVipXQ87zKY9S+aTSNzC9nW58oa0VDNMyfvJE5EUkQewAj2jY2jAJsjmsocqTkpYInh4nUkvoYhblPgUb4HagcfJIgJX6pLWym//8wkPFKI5v+9c03ZcLQMgOSJEGBMjOYbmGkppNLTxxlwcXMOOtqR/o4M2DJvHDx4drFlZwRUhVWzwInoL7Ou/F//H/wX/h7v22yBrr+4Ke/61++Y0OsmOTJYV9cwr8j2tHfIDW6074pSBcSN0gRSWUQT5Xewbfy5b1Xm7mCilhC5asIDWezUKIMAg4d2wl92G87iQbtkF6DKO49142E2YzGKb1k0SaaG3tjL3RkvSemzvLp8fAJN3Mtvjhl93uMX8evwev8hX+EpAbRuedf2Jmvj+CEnRlBHj2MHVV+tndUrRu7zIXj4LW0jcyhLvlImoRwVZyKwYBcAaJrYGY9a90SFUFKGZAEYJB4Ap6EIYgxGkCJDr2XRVZ/TxMBT8DhU7nnMxTmygYeCOdIEOkox18+Lba/r+cxb+EO4IwLPpUNHgVrosJNWAPLrzp1itL/KXeuW/bBdFp1LyjuR7eT2Gk2YDO4oRaxw2Ms/6jMc2g9h0zsAS8WrwlYaK+kSc5VnMYxiAzYoOUGCDF+QpNsy4srPCk2skLvnu/q4xkE5O+8ZY0MXSK0jszmdNJ+uXcJdroAkr22cRw4pCFhBBYCAng4+gUZi4g9f0C7kxJQ6Hm4N6mGGPrRTR+8Qnx19JKSYog1pMrnA22U8C/8E/10baiDOj4YhqKpxjlpxgHXRzduhrnuf57UHtnbGIREmNRiUH0OQOPbTV+wzGrR8GFTSVMoVg5IDRRYhSAGM7wrQpZ60cD9/ye89uq7dCcrbb6bQ44Lj7Bi6g29ksx8WdZjBC2n7hFprKoGDHvCI1YwYMdYbrvKOLVq6jExWPH2n77IpOapYJ3s02sQG6i2YDG9bKSepare7VodpxtVkeauZJXT0fNQp2ASYS1jbcZScCYWSe8W6vb8KbOVkdx7A6q6CUEwaiUPjqzCAC5m3t2plhgmpAVJOJ2pWAymZ8ucTw7mxVj3/2PT/QMBFgICJMyfsRuzmABYMUm4KfQMjOAGYVo0d0DsPXlAxDwenFunLpzt5zdLPCdWiGemnsOeYL68BHJ42/0ZOypLbCZ4k5G3HkslwUSBslKBeyX8njh1O9dR6o2AEFBslbGQjRCTG0maDlVa4NbzdtG7gunNP8SPvGaDnBhxUdId5W069uo7CgCeNWaUSkAdpIsksZEzOFKEYIalQTKjnOd3t7kVyfzeV6HA6qtOSwmCRrgynMq6t6VFc3pDE45EK+M4GSYDQYaQAKSqeOmoOmjekxM5zlKL/FbCaZ5F7d8TqOajOfpzHbwhSgQSXjKWhCzk52Oym73UIJaWZ4kUyPD3a/1NiW82J8sEBjljTRWnjkjiedm3nH99vF9eTxVeq1uYZ+PH5jijeLY+ZofAOXPGf6Vl6V7enlYiH5SP3ZZg0RUkgugTrqcPpOYtz90BtofCZxAx6blj4VInEPe1GFHA9To9vqqR6VA+sBUQrFEm5hBYt5ggdV6IzEIO3NAUds4F12RgOwVTC6KqQwSzCAUBYUMIzOg8dIqoA5AMy6pSpgFlhmAFKxAHb+fn/0z8/f/fj06EewxL4qFvTEBaUHpymoDHtgxfBalbJoVuoMx1w0ec/0QPMeOxXmTzP/DYJGpAjXn77lh7KGVjxueP7cXlE/akol+9Yjhk6RODZKR5bNdmG9MYVx9pQtUgjTJDDeFge8QekwRgST7v5y92O5VmZyM8EW5GTzrM75FnwOLKif4MvlahdW5NS4EoQI2pJVfhADCiZ2EZLj3RI+kDDlpZjt8/uCsZ3bwU5Qg7bbqELsZJ91W/OS6JX6JaXLeMZjcphj2wjP4V2dJtmwA4Deyhuyw32SRsbxduhJcizlkUazqK0GQUgjbHu9GWv0271iAUQdQAGVg6lO8utxOLoioiLkW2nKPXEjwlgd7CBazXCZKJdyMV+cFBrswjcR1Twlc/J0+leVKKlJk+vhV9fevqab0za3/mpxMieT4CbA8oTKgfRoST4a8sH4zPQHMki23U6+I7aB01wKwaM5GtN8O7EoHlc22vUDO2CyUjphvqPvwXe8n3TL//fd6fOytetQ59ulEztRACHD/t3pzh8CyKnLnLilMaZyR5NdP4VkSVvbCvoOj1/eWMU2z9060nHXt9rqBx0r1FGnVTifNBTqlD56v/7y7/vWo8vVUYeStR+qw70IM2wUc1QfFJO0wwMN+FxN2/72+O7mcvvy1Zr14M4nZltvnPSraETQECxe6abaa3Ev5lfhLI34meI8wA320YRjY/gdyywXX9aMGv378IUnQy58oI5oPkYXAbC+n/6OAYDUEQzHpW+Xs7/2o7SaZbaTaCYbUi3b7nAdo+4QhNyiB6RYmCqXRVqBU266G/3yIB+m6RPr1FEr0KzuxGKxcc0UBJkuBYCn/VJr02a+Et+osbXrhf8IfGBv7PcYmOhlZDViA2MBerzq67UceNaKC3IGxAKCU2/mxxidRWAs2O92duau3RIAa0TAFgBQo5BGe92ooi/vluegi+21IgEakXw1e/mIZ5Eho5Ul56ieJ0al5/CFOQ3elWzxZfxxrIQzKb4dv3fplt1zCEpGGslzSG+DNpLvg/fHn63lEUf3FC2nc3RGiHPnw96Tt4YDzsY1zdyQV3c2X+VKjlEag9KWuzioqT9Qg8m6Pt2xPtUfXhc7uwe9lJc66T1DvEEBBghTYZcTygZhAmTGAmszSETr72EUBXZR4i5oDQJlRarARaO4GqRb86v7/h17/HFdv9qaSi2YDQsRoEFvIVZoAYaUsuEgOsZwWYejdrAeTDSXXVvieeC8oxV9UVQgy4BAFsR6vLlpwtM9StfDgoibaWO7fOvyvdoeyjed/O4XPkGU49SBWxCnoFAqczleAq5kO0xlogHLIFlw0MePH/1ddPdt1vBEAAuUHatM17Iuv9Ao2pOsQGDUAAJDauN3eO9g+p78S+k3ESpRFmFOO0WISoHQwGAiVR0kQDoCoqSbfv7J7OyUJqTtaWUCRGM5ZwA2DWcGOxJFLLfKo2i4p5Sdrod6Ze4oosbEsMGjfiQfdA2g4jpyC753bNsWjHziAEqXhcJXFectClI/fV78JbLLAevnqeyJZyL37D6SE90+qghxx1Y8iNmtFE2zIcTh4l2Nwtus0CdnI5+vRhrRM63HH1BNrOgVxmuPZw1ZRUdEH92ucVui4ziZKdeREi+si9tT64wY7NV44mm/jJiKkee6Sn0Xj/WwHaqxwVtm3MlXiUEwCJCLdIA7ibYiSoEidvnWA0I9BsMIsjXasxOTMsQlmEOgGb9dDgF0WkwQSqeQlZpggxVgXDKVRGPQiT6e/U17tO+n/LidPSgb4jmNQX157mNSsjQW0WGgJgguqACgRHuAaTg2fUWg67dKeWwcsYSKs4QgbeQFc+feqNiOjz28n/hqWR8p0r/K8E+5zBfpuWs2Ahvj9bqWzjBdnjRvKMbFvZ8+HiFUFhdIstjcIak02wJ10Woe4cnr9K6cq2wLuMUi2zpqi8mnDPkApDwPIq2GyUOepeBPbiVHs3kZ50cnuotwT9shBdF4hr/qiEgJh9PBYCJYAIEnAqbEbNrBJQUO5DRTpLXJ0+quV3SIa+0qygRyb751pZzVVc+Gmr3nBhnQPLy42C7xZ/tMrgqptrrLGmStlbtInioImKdGNClfk4u0sBfn7Y+VcQi89muO/X4vqNVbuzNI32Ye1BrIJ+Tm+oS6n3DuJQ6+al632bnhXscYD6XfJrioq52mM+1OsHpcfKa49OWedabYJ0OVD6L71kT74FIIavde3ybfJngCQji+D5liXzUaOiOMqnXcRMYWb+22uTq9vYlu74GZk44Y1sSeaS/7uIABoQAlCcCw3LIQrLnSBlgiNAdgZABtYqyBoaELmCIgVdHNokyhfuysANMFHnh++vW14qtH4DbhvNB406antBXXxsJ4hxxWcJwwzDG/Iltm5gtrrCkGhz/qEGeJypswDZ0RZ0zOq+NI0Q9ZCq+z9tNj/oLL987dHzxr9mVs1qXacngN/m8++P/3n0olap/IrBFCrX17LP3Eow3YFRrLhUkw0FYP9Y4cdsvFAyLbrii2hAL71GRMTY36aSSEfO/lb/9/IaGdVq8/fPNVMP5k9vaJHPNISSfaZZMoQIRgTqmCBAEImHgqBAnEhQANd8sklbjI25PW7ykAYKKwHNhtHnFJVHJMCasZbUVUO3jtNC7a62zbL9i2EvdJoNDAU813QG0LELjHEoWDUMmRuQPkO+fvvF5Zi1HnsF+5D1shLj32cTyN783spjzreZI58uyaH3Ou+pwuvxrM5br5adOpt84zqcLZlDUohnGa4noYgvmNUIYeusP1BEZRMY4KJUldEc2ctmWsy/oem/LjjKd5pvcqfLjoC+QptmtyJfS9zj0aZXKQtBraWAmrMHI6O5szC1E30ePlo4SyhQQAcNybGwCJs2iys7Tt5pMMHwtDoTQQlCn1unAaMSyKABsbWbmcpgWiJmVgQJi2vtf5+Vu/+OnxB3es9v2UXArmb/l6F+t76b6z4ywknAeQHPNYZ5h4eimsT6sRfDUdGjROxQqR0HyGMxCXW5jqaAU5aBgSjyNNLp0O01Ld/PlSuWcWkSe3Tubq2r2RLsw5g3LODR4fjMvzzdvniXcWvUqYW9HHUdSoO9NnDtTvd/+bzaqm3ZP+iWSLTW2Mza6WYeaiDkX19WKRnrzGrUuib+a34pG+9We8kyE1dSIGUAVkkqIBMaBCQTEIiIWisoqSWlhF2wIluZCf7UyEYUA3F4pUWA0sOuYFYmt9/Su57RIuIrvHyQzGa7+WQ2MutKcVdbhu2jPNYHIo9VtpGC3q1bh8R+5vDnf343n3Y++9LBpz9U77LqdBYjTXDFa0la9FR8E7psNp9HXCmZW23EIRHgcb6sYgu0/9gm9P46UvYHdmBFwjAj9m12/OZ3b/Vq9PamPFn2VBMTb2mCgykViNvYiPd3KxSQHGsKg9j+lTRhTANoQgCeaQWrKy5TRbYuA1HMmNPEUJnbvCahwBhLL/+X7AcA5GM+22NCIGE7fXj3BOHA3clFqDv4AfygakaEutjYmggFzCL0m4GlC3DYZ9/ereu36pR5daP2jyCqbzt/Ip1dGsMRC/OuNpKDs/X9T8avAJlvOF11E6mAF9QAHUrW51Ws85wIHycHTb0NWWFxBfF6MPbYR1FVPO8v/9z8w/0tEPCsvzwIY5JpYP4UszVaJhLaOUn7T9NYdtFxuAAZoIbcBly+rmoPcsY8dR3esR16gRyhN2B3pXLWXL7TXtsPuURPPN0jPGKJy74sEKEnODEKRKdMKYDYJOZhVCElFiYoIAC4U96nELImGApRZKMYGg1OkAPUxHxDlLUYZCZy0nckD6Lxgqs1HpKsY2WK/6+mtgOCenQxS1I8mNDSsZegrvOudLlQ1rbKYZVamKN9dP9ckH4Yrx4JpZ27TOfq6r50Xj4aSxCitUBy8eUdwnIwVI1zv5auwKVG0Ji+wjfbhbq5VOvdcJKxH0+4rLgi3ZmLf3K7Kjjxgj4TiWIzNbN+vEkm7Zr4bWbXfYE9c7OXQcLhU0l70g3AV1CCnDQTnROOQQhykBkJ1ROwchZJDWZj0GAACgLFwOFmBYtO76futWw4uiQQBGwhL2QBrO1Ko2Q/IGFabAtYqyUhQDkBnarB4HW6au7JzeBIdOZUjnOys5jJDTVA1p3+f0/ZO4ujvrn9PQzSofpDef30djbpwh2zFV7crng9hIfwpajHyj6TwDUz23RExURXs/c/3ldFK8cfKuD34cQcY1F3Q8Wngr3/Pen336g/lxragJLPYWyigwHbOe1lqb/c8ePR92dZ8TVg9Omcx4nCZqCayeitTwyEe1rKL1IbSuw3skICSPGmZbSTWBQYSACJGQSAIFEBFkQDhuv86NHpcPZQdjOpWpRgpZZqYoeO5xwIZpUUr0WVVb/hdprZKrAk5sPKyvX8bXi5Ix4dJ8Uo4WG70OPv7Rs6Xtu7eeI7DO1hLKKUxT6Lmh17vq44k36veIqd0YN5hQ3Ztr/fjpbBTCNdW5cJGu0+jkjMwlvYrrLK9OGg56e7YDy2LreanXVUM5esBNnlg6lrCkSfncjuVxRZ6BJ/N4kqHusliGJCjxeG+3GruA0rhCNa6KlFEqDOgbUgs0iYXZdMklTiMHhToW4UgDCCiharWhUQDAghwzKONpR10JcQyAkAhhq9QkYzCgMRaAhwvlVKloM0keUKuVEYKT2KV0xdUGarXQCG7SN1asDkXiIZQJWZ84AMapU8UeP52Wdb48dau33jXeX8O/2YK/u1z/5Tz4/57RKTxpc12z0Mnx02DsTkQq5DBJFBKx6cGEOH9W73+8OTBePbz77nuGx1/78Va//iGUSUX6MjavaN7X9dg9DRZFFOteLQaQNlrO9p7xnkW7h11lwLqgIquTmyrIa/iIHu5iSIB/qDPhUw1WNQcYSoCghaK3zroqJRtgyCTab20uGMYtJjRuvM9esDOGmzHnUedTvk7TR1qXrhov+DFyIBNzDieHWryzqi0QJ4eecnV+IAeuwxmWGlbCJZiLViEj6sKMshiLjfTGtAEkTcVdGMrjP/9Iu/yuaCA5TWlifhv8kGVe3rr69msBJ8zdjkhvIJ7Hz4l+820FabqjcQzq6NzLzDzGzztoVFOiAMAym2lp2MO7ReswIq7g06+3R7SxcZXrzZDQ1Wl0VAOnyQN7jIsdjkVynSoDcJ6ns2I3aONMQxSZlNrcZvvcphYIGnQ227BLigARux2mu4AW5IaEaNddJq2Pn3v74ZUB0LAAG2jN3K0yCjCQAEwayNpPe++n78v5OlmcsS/4/Gj9/c0X2vb9X/++2+KsPx/5u9FEBq76yuUjvu2krOGD9uS1WHLx8uBvB1hL05PKNHWe2mLkizbW3aRJ7qSu0gaK7Ug2bsckye9NkU9N/TPh2PPnA7w8CTejA4+nZUQ/Tcup0eXq9xqCoqhvmYaWBZfpD+Kt/bN1a5dtshksc8LSXaVVbkdsqbj5LGY5WSYlugQDIS4eH+P3x/exgagKCgel30oINSQIQeOBEgLu97zctqZmIR0zn9ILggtr1t1drhTR49ec5LsZgWW4MgY3R7q1ewQWBaoBltN0HhDIYhbnZIie3sQVhvK67VoWNohQHdt2dt/qrk5zP/hEvc61bq43FEJiOBrKwTdMf8Uwfp2L8ULf0refOuL47NWcClb2Fs+3pPgqxXFx8VwIAQdXs0YEU/78Kq8fqme7FbPDOpzhGlEnRq1oG1ZKmq/VS19TL2jKz5aMkjjkrsCGXoOp93R4iNFgGKzskjjhF9uN6vvxx9llEg27wSB6iQAIDTTjiZcxyXGTNmN3Nt8fUSpCGGY3QSporZQ+42X2llJanYjl+upXAXSLVQvAJtxFTGVd3FYqs0ie/+14+cFv/2qb+kYcYNDA+lAaHF9VTrt/WvuWnYvz/P+cYxvve/yF/jfP9jmVdtCvm+W+KxruHOXE6bQUW731XJ3G8SXmDwtMaNbLxs4dTav90OOJnfUX0Bgdee5VOVWiBIyNbR8hKN3bcTHA0W1W2sSdU7JQBQQQWQqGHtdxCqTADhHHTNIgRotkFkkimLP/s9fWbQWKEzJxloxTuRkhEICYHBQK4ctedm5hJbdyLdZOHQHnNvUBp2pMb9Ez8prFe5KWouu0sZvjq8WX6X/5CP9GyIyyoVOSyEhP8KgZx13xnXRXKDmS24ZCYuRqvrKG+8c6eEK/XV/aaoY5Su6GkQgFAE8sg7vq9FOZSjgZrvbXS/VEYSDhAGXXwZ4tx5yP+fwlbl/YJpjb4ilBkgLykE52m7evSjV6CGocbkxrVj2T1LmcNMsUzKq0FIBtjiURAlCgElvhJ0N7wnBl2p6co3lyf817hQK9ySafKLCsWOztyQBYDMCECXEowF57d5asEAITFAxXBki30qTjRlAGOUyGYYUCFoJSrsotLmPKmtNYBUAK2E7y/r8Pr7+/qfxAM4+5kCvO4X5L0l67bEx8uGGVzo9X1jbuN+XY9WnOvlLzFsW1aYftPPlk/rb+2i357jibpMbaLqYmQWnjAfMl9MJq/vXbSPbSp4t2e+1gRkfsfE8lCND/ISpIqEdOnJ3uUIv2o1C9FINCIYcFfMDq0B4UQ3ZUdbglCmcwulUpAohoRo43vhcNU1Ccd1JGiTIzCoAkwIBgNC70XXzsRY0KBnTpnJVcwypW3Ti5ZFgPhAd+Ck5QExOjPOdE9ZFdXFBXJIo+EQXtkDv0oxMnK+UlbdZQtdjl6JUklYlRxxWepZVlsno6bwbmth31FQQADQAQMDiAtTaBdkPlcCQg+9V1rRyqYpY9znces605P90+t/FJbclZ1PifVrlaNYy9MB+RV+C3zRswzUWMRBgAcXOB1jbylu6d7YKqV4FqsIFDQaa5yNKNt+kWp8BZZXroRSe7D1jXfmccIqfcobbYMecCAIwATDSW7CVIwsgGMVyV4tOu0zLmCwZEkwSKqIMFw4oYbC59vRZBDWBBaA0IbSZCeNgvDoyEWEzOx81l5f+BR+vGpE2gMW3xvH142PfxVzPlEvGCfY/jNYkxbd54P3vHLY/NPGU05O7sMcgy4jrqa/eQt6DJ/oqOV+f49vBhPaNivi0E8R8rOgeY1UKWQSp0PbQ7bxa1Xm5Cg8qp7K1P4BaoXiN6p6BAOzpKx7aGTRexAsNS0at6COOWi2dgeSaP6vmVNyqDSURASkQAEDJEKc7Zz6XRjSJFbQpnW9ztbXjN0kLTvQeKNMF123eqTBP/cl//65fr42K7Es7Dak2p7ewuFdCCHzGaJsjeBrtsJJoDgFFPjCm8V94bKMsntAbDVIEsAIWiwJmEIDJCK5KowInpNU01M1ARTKroot9Jc/m2LtbvEX/zW/V5PL7UbwM1qKLJCT89H5+CICLTo9YTcbCtmSqOMQpxgmhmh+70Nv8AByvdB0bVWEeTkmkub9ltq+6YE6LOIQPPFYQ3pLsg4ZWcqVC4vhsBAPYowIZqsCCZE5BNoCJpgkGoXmqM32VJAaVDgnJJCKDI3KbvqdA0hcbYmoDWQgEcAaoptYlSoqhgojWH2TS38XR9vdy3bjqx92PKVx7EemZFvWQa0mzfyfHKKb/QYy9m8/ZZUubTp9jWSKbjbg20csWcYa/7Z42XffcM8ze79hjmTBVJva+cgNSmVqg1nLurbz7vTRMns09+TJNMC3ZOGbRIUl/ZriSTg1QSOlY8uJN06cCYzVVFLUb5WhuNoYsVU4vQ6WvH0JCgOJpXZQQSE6GlXnTJ8SE+zjp5NQUxrnCrzWIvwIBxITG5TaxRlb4Y29W/NljH5eDBPfDsEe9wV/ZUQ6voNmKYSOsWMpLdhI2e4GSiJNfIAOOGQUBDEBAAgEy4E6kWGQkFgTjSo9IQtXUik84IL5FwODO0MY7T8VgkrcEQZYkZGMoVrXURHJ5PjgRjdPPbt7pfc5yb4CmuQuEaHhdGBE9Tga7eAgUkQIqLevkybCelW4SSJAfMwxU4cOzXe8Fsr/jT9nHfIEJAWkFpsEZOIBuMBBhh1kaCXUfbvR3vyp3qEGOLGdC0iQkY2+W72kJsWMgYIIsyo0WAUgw49EE+cWpMn0RO0WJF548gjrd5f4nqEUxLpxRXjhkb7l/c6cQEgnj45ox//Wnbx8bJtD59dD/guHpTEBtR4DEWa4DNN1ueOb89+nSZnp8qt55DJ96RZVhJVRtMgoUTCMQYFFmk297SXpqqL3328vC4iFd4GqKqI3qyVucqFV3QB0vsU46R1EC9YwHqR6EEG/JIQ6ys9jOkMIJ676GjvXQfeXLuEIAILEkPAfuVvjj1E2J/Sc/WmRWsrDEt3VtDcsBYP39YrFl/vDVOMXvL+eK4Lzk4ughmrX6UOe3aamkVBOXSSRQBxiaPgk3L1BPg6PD8LHNsXBeMDmCIAi4fdR7m0AqlAAgqw4gqYww7tqT4hTExUoB5bhz2QVwNPQi6C1akNEHNL6rzP9m+uCnQBHGdxFDCffbTndd91V/RT+2Au+Uvwx+znEw/k7vL7kU9kwn5VkZZ6g3LISdMS8D3kHU4WdtXvWnhbBfvVWOBCPviLFe3Ne+eenrMuM12RVoA5mhMLIzi/CDr+/9xbx/fbTSHzZLEMrXO2igK84k7TJerejsRDcKMoARwC6gAEKKgCKGIZEYwS76l9arDd4moJV3FHoNUTHkVOsRx9eenX6PDd7D7rbu/hWNGfR0nzjLEkbYiN0Ys2Yy+P0rLhyWPF98XvyJmMSMzLeVI71yAJaZNB4LGEtrhtNjUvsUd73K9tPDy7MypiWwGv8BG6/xu7jv7zMMyUFQfsatumMgRIW6dkSdw6FRryTRn6TXONiTo7p47/QF7PT2HxmSxMcQymhrbVMmD/KTnPnT9xNSx6+gQ08FuOtuy71nHv2v8y706S2A21hHHPOL7XluYpWzKozuNbIMMZRDZ4a0yHIKLMaAm/ODvf3befzKu72rT2fKdNUAXEw3SwMIElQEAEAoGJRFCPQ5L2Jah3dcYlkdFT+23Rvu8gVRnwWEoMIus2IEfVCEONVoSjscjxnguG3ygVh2Nsjl3HYVxUmw85HcDZ1Av9qycwhP9gJ9gkdw/H/OO9MrvAmcBJoDEzOi+4kt7e3WyE1GTiEFAbhmJEeiNika7nwtY5rcEoDICpoAIMgDmfTueNBgYkJISMC6AFOpVBlUGBUIJKkMxMREQ1yWXFplmI1bN2MkaDs+FHo6xxrdWXNb6ElIaMWk3dnoYjjzT7sQw19cOhlhiQUeVuVs4Or9/qml153DEUwWZ1CnrNLKmREMYdFWKiqJpV2f7MwdylyCtpUOfekcTACONFLzQXQorfeBp1gxBDcrbVI25NNhVU2ier5eamdnd7vlq66heR/d6GxqWVmqU+2h9u8wxGqkWjnHko85YYtoatwLdME+35oPOEWO6lIO0pTGAF0oT5w7dKouY6yl6Ppufbz1Vq3BrlB3lKQl0KYKS14YvVUAUD7YKbAX5pzQ/BR/Nd+z6eFIIhuAuf41lNEApAQACiMaqmLm0jo93tdLFILSOyIhLPbMvi4jl43jWSb+3Hs+j64f6/Jv5Rn+fOloVLIucJJogxwlPc8hpiGDKn0SNxnam1cJ+11GtdVg8xiIfRdCsdNf1XBSXXkl2RLkSQwCy7Thse29elABgDQNEech7zqfLtHLK5Xyto640R0JAdQqwxBDA44YbdAsixQj2LBRIFLw/l1YusW2JrfbsakKrFkQBg2jcEAnYtNZQECdE3ichGeZMA+YDoIhyVuD8wKNniB95Na5X+XV38jkG6/tkPmW6ToqnhACuyJGI9XnupPKXWZ3vF+VpiravAAKsDAnautxEMAQGsWy0DJiFtsVueaHDtuqqI2RSHkd3aYko3CPqa1Ax6H1BM3ea/YvduJBQ4mBkG/eRJAPa7M17sk298OquTR+29H683yrK9Z7XYtMR7ei0XafJg4vOWR+2QIqMuT332Ty8WOzQd6daz9trvtynB+zn2Dnj3Jv7uKmXTOeFrvutHvfTbWY9CMmK2YnJ+Axu7YLccHlyc1glbsABJIpKgv/NxL9X0UIFm1Yt8DpEN7EpqSAGoAAAIktpOtRVr0PuqTt7HFaQnakmraPSLLbbjoyKEalaNpd4LOxyufRR1GaVpJCBs8gkxrKpT6WbSnOpF/o40wiAbWMCHPC1I9NJCTo+n93RVJaAAd7TXLZrrQvREblN37ppfb5wlTh/vz+ZYEi6GApAVgRjJa1sSPdptbJObBjQmCF5WbGxCSQAKqhqMmmOMCleIRRFQCB2Yjvt+ZE2CyEpaGjFER6pBAFBwfzOsHW38PbczXdf/HuO7i3AEE5zNM/J+4hyTs+98I6N9zcmR1Oemrk1U/1F8J2uR/MeLpXfr067RukE9juzj2gmnEgF7xAHDCT32YNKEsfbu8u2ezbqccTh2IcgVDrLEkHVqp5zCnRSXVW66UGCUlU7SpC1FNYW7Bkur+yxsmfb1jPicjxzT6CGYS1IAir8YWQWnKwd3Xh1qRI7AMUTmVxdbalOZFypqCSnD9JrUc6a2eg8MkHkJbUTJ72s2D1t4pI8tGFMmGxj9LSQMflah565mTWJiqAIIGXM889VPcpkCTne8W1Iru4/UbO0TQ0oAKVJDXfVXa+nOe0zV4cw82zATTIp+HtfZZRdgxjNNM8DcRd8Qb+9Wyh7lqREFyxX1KJQnRxE3g4QT6WQe+eLz9XMI+OgtH32rQtJTrI2tVqNVRwsGCeci4TASI9sRt4Fg4ZqvTBRAG6FqwnG6ju+mIbSM5OdgrrdUhIDEMadOihfdSgJAyJQo0/YM0hVLmUaTIWtjzSAUAoqa/ynN4sOIYqWzIIdMjtZFGXfYZ4m+0jYgAOb+yh2ptAT16jY3R9E28/PJ90pbUcvQwerACzbrWC7k1LadIz7OrfT7DydzygmwSSu2iouyU3DSgkDuc2b0EZg7chcCCLjZHCsadwkj85EFjT1Uappo0IF+CpnzmkVLXuNwk2AoKI3A8CHW8Jl1HQW9cNtSt7V2eFlm4FEBptC+fJVLIr9aqMEkxKN46xMiwLWle4ISbNYFzhe9HQWeppuQ8RGhVaWsxc4l5y5DhuFlT5KiyhIAKOZsLIQVbZDjbAoA2vQZAfyj7p/VnojB0D2C1Yd3m/wjLVBLJWkASjWIMxTDza6uBflqlfMvOHuMfvEwYvPxbYQZz+n52YGWp86Unsq1kcSs6ZTxdY2qZEmDm8ITwyjQBRGXJ++lqE8XQbpXKbANcue70zbaln2w1ycrHe3FlxbB1RurhDaZkcWOQlQwRQDUCUGkuoGrICtC/36fl2OFjBTOOyAZqnu3JKEpLFIYfiwrSkFXZjBLlVSIBBgJGr2zYICPU3N2ewljpdjsgQoXZ7decbDf/G18n52FvKHktA9TE6GjBkFDjyKsJrXISR6JbO87FtpOjo9yh8SLMLjpMPT04OOtSn265mkZjrkbstXPxqFgPAIIEFTRI/ObM5pphzsLJmqdiVEAjDYMr+QtAjWXfLcDKQVOkJOTXcO8wON0DCh1VPuV8iBbfdGzFvhRutECZvZZIkCsK2VHjhfNCMJJTKhlCqBhMFKb8REIKct16ynLbqL6duxLdVlommbdtllfsx5TO/K6IovrOXOHLNVVkFxNN2KveFyhgJF41UVkv9F2b/W4yGSsTMO4CcoV89vr1/uG0enBsAGgFWS6PYwbO9eHz6H3RVlh9slc6vuX9U0Kh2P1D3Bccwwn9QBtiqqW35RBIRMsygaCQAQMh8EaVxUAzbFT8eTKHt5Uy+NVWLJOYJ6FHUA3TkV0ZWGxxSRmjVyMxQe2/0U6fp8DtgTkYKgUgRzrrRMPBSFEEBgsJMAnAGNBq6ZmBnR5oI80I0y3vygoXQGmMOWGY4awKCAl6uTn7u4QTNApzEPXIzuSHkKwWW+kp7YZ3hAT3MySaUGfuVyJkO6PwSsCD1IAXUfLPOvMZqUJRDJNOi005v7xk1xXrkxalQhJGFVpIPaTWha2NkMGPbpgwqljGuv8zlHr2up6sOmUoY8wZhDAQAcoafsc0mRX47eTFI5Aoa6SOWD7DXuoBOlQEmja4mptx49v3tveNhL1LaWkwgg420Hr9nkRhskEiJRlIChbCOYp6QpbrFpqLdbqcHkUO1IHFbuk1Mf9OU530pdRQu4FMAOKrNMSfZixsqb+EV1bdmAkg5xDdE0SUzSv8H5MC2ACQlY0ZP07WKbLy73L+4ulgYAoKaoSpO5O3nNT/p8qadMpubiqdCrKAPpmvqWY9OxAQoioyaegeKMTavUGICF4UAS0cyWvLk7Xti+6f2mrqci0CwICLDAnmz1Sh7SZGiKwdXqfWjILOO5EyAT4zlii47amLimNPSutVerKx8mt6bTt2SkkpUBrMtBdZrzdothimjRsBpamwlGAiUcQJlQ2FJqJSigQQWCsNPZp/f5ixARNJz9NaAKHOh+QTdRWMwcCxjwqZmwKeNj3a/K2tyHYSWW7nojafJaDCwAqHP/zIqWD99mXDP9a6U2jymQB0vjhm7cGzZwhnwsECcqflctB1QLzxsGEJhED6/w3dgmw9QktsdFBcImirk2qk6nU2gV2M0wEw9KZWPQhSpF6JXOkbgHXI891yiYybmJExEZDCvjXDPoVe96Tf3pK7ZQY6bkoMsr0MjIiqbKTpFftQBuUkCZg1O7UHvPc/uS6csmxyxcYwWXQKoWITO9c1aK8yLcljtAkwY4zjxRFWNHOIQcMSG+YryCJzIZpr4uuV3ald2Lq+l4IDSmgaKlVaIsuReYIL0765GNKWeRj8uExNFIQEcmuYUK0bDfiQ9//OZ+1mgQc+xRvC0ggFa+vtXnsYXph9bK8zeWB3vn/ZKjhfbok7Ec8QV0xnB0tHGgWY6dkC00i92kLMSsuvtMHQcFiGDAKpgQMm8M3rLSQCisCgWI9VjIkO4I5X3TAsSCC+2PFSRSV5dSZSsTwzUiOmBcqkl39TDX8OH5xmTVUfGpNc52v6CXK/sjbiLIYEaA7BpcinxXbsKovKMvtGA/weSgUm2csrFQe/n59+PZTN7wX/0veJ2jZxEjQkjc+Qi8gDhC2aFcq/x9cF4WE5SwGhYIOGkyX07vzvvMr+E/WZJFLFMWt2W9iDtNQr2VR+Sdj9KRQRpBtPNkeggNplpKgFCP1hTjaOdS9si/efz6Dy6xlig9C5zvWVtHEdiYS5lE3hmVgaI3VPIKTGMMHlc1MkCS6bNzyf/Vf5PVuHbZ97HlIyO4Kl9iUYyvLabI3mfs2053OhlmmJyF4566RLNsFmY5RCghZnLZvLoX7qFwWIf1Q92EiVgR92Xsmnf3cJn5/HdeLHanaUxjTmmntSOeeMdKMnDLtqzqLC6aPXpTF+TYOq6SLtie2IkN5+YxQQKljkymH8KeLfUh05gndoVLCkWL3Px59dTajJIVHEI8r8AzjrL6Pv3ko0YUamHjwbVNg3jWXMxQS3Yv9XMoQIRq/um0ehW6+37wPLKJ87zhHFEqFMJwgMgW0LbD9v1yN1PnOjpSutWpnB0CDG2w6M0cU/dNXZTs8n/n+cq18Z/+/JX9l3ZM/94eT8KypDOvZQ23Cjec/ksqfOONLhLMQhPE4SlLMWe5f6/z/ECQi1FIsjPWFtYcn+8JSjxaFnG9nrbW441++gzWXKKPtyzbMYlvsdcYAze1xSmAXdF4dZXICwBImyWQFrDbZJox3GEZ0vSS9B4O29O6mR5a11zdzC1FNzNnQurZEPKAo2QmRSNBkQl0BKoZK0s4D/caqE3WBtgWlK4i8Tphqk9Fk7n1OmXK4AraopIbQ/FmaXIN2zAOYjZQlVUCfJ9xYH3NumDHdr+dPs5kecgZDZBMTzyTnkinJOCEwVSwC6tGi1wAa0qzxW35bMzIj01Rf9W27Tqmv1j9D4JPVtBe5p1t7E+JdfA5vIEvd5PVc1hVZFmgUF+T5na4IDQSczJHtU3WyiQhVpUO2kD2m+VNbsYEk8rORi1RKW+OVxAVDkDTn5Nb+6K66soq9c62DX5TKIPEk09DX1P2MlNfXpthHbw/nnHwsefWq2/gtfvWcwHn09Y8KihVrQgQyMBADNb9usWQDQGQSU1V11MTEhREYyYjQiAMFITjAopZlw4AWBDZw+fER4ove/QVrz1g6bQTDamCQqzPtYTDE8SZXvL06Gf7fJyOvlaQ4S/C7Xp3+eXO3+bztSsXhemEIqaFkjBPSS21RHemUxfA+WLjywOdYH9843zDmkGORFgK7DvyJKPlTCe/fvC4fGgUgKsOECmQbUqBpVJVjUGVCaQkCMAETZ71ZSVjXGcj3JcqjnDKdDkRTFpBgJh61EpGHbRN2IuTXW2huhSkJLlUijUiTMITS8lPogbwMhRWEs1EDhC4TNbrjuHsjuViiRU8axbvg2YRxMQBIpxxPg4pihhI2qklZ023mmqU2labuO/6THw2js0HG+qkXMSX3DM/Xr5C16fhhfMyxVB/SutPgKC5yhs7Np7gNtZpOhySotcEW0aYm5GeU66ZrD2qfu06NUcZJxwBklft3PRqNwxI4hPjwkeztFtZnSnZbWIP/Zkk2WKEycwioKO1zUJeGaxd2hf5MU4njcPK8WZoqzz7QvLi+h01OnnBZUtbW9LcGlF3ti/77TzRaDSYQZmtASuvyAaHerYLIDeAKQWGgQkQXtzxBxIRIAWySUohgRgiFngVCjQF6RP7Jr9+/nPqr27MBQUGS6wgUOaioSbbU6EbeDi9df3txq+wdtlpQCFTMUpbTybrP3i/3c9vX8fPzayd2hxvX6ZRaVAb7EOkul7P8pjPtV0ShIqQg2X30DJpPllXgrVss1gxXU56BBSDDgCoNhcIRUDVCS92dmBgfbcetnTrjkXvxurCpTmVMKUQNJ5Gdc6+J09znnKQ6JAlgtUoEMUgqbwZf7FfffNx3kRWl8anNcp0icTyGm+qCMNwJbG+J+CS1Usyxli3WteVWiBVQVV5bcwMFeg9amQ2Cklljy/vuDKEJC/qcUVIs0hdtRXKitQ9N6kSmdr0xmiEJmB+AgIuUuz0b/nOKph1wrzGtYM/Q/24zmGqbXkX8kofLznrJ2nKQZ/s1uK9vxq8G0af14y+dNp8yGVXjDrX43UKSqIjD99oFnFmV7qterlb+ibOpLvRCdeIQr2M/M8j+9CfN3zLQ7uvWo6ly4WPrxGkFyJPUM0Wjv6tOjGru+tMsNDVroiFmI8wXUDOj3zmd4M/zTeFCIFZSuqV26bNlAiCOWIDxo1VQXeEDQTTdDXXoQg2EiPJKsSikMBgLXT74he5/uEnVlDFKmMqDnJDx6P8TCklzBZttvwXDsfHYzKIRuaRfz44jUF1XC4X0SvWk5aHVv3z0E6LFWt/GMKyEMzFzKgOaSE47oleF8vkl09QLwEEolijDCC0w8A84UbSYDzTyxcAOEXEUFWtzo5v3T4+b7zDEJ3sbt2XWqdmb1hVHUodivbxK/jTzailYNb6WjikIRWJBlEzKrKCsPm49rPdp+c1Cu0TzEQ3BnHp66iq5uF9wwyYBHKTT3ADARPK5qUsVLILOkWhZBCDyM9XjvppfHKAY03AIWmdAWCgQLBILGRlManUhANKCCqxJlulty2ea0xv9ETFPJCA0nfg+Ho8+fa+x3Pk385aUFt+XfAQTnq/KSWZ5jOUrXUSJ/3DPXiS62usj2004dkMpJObo07xBW3YsTIRqFZrps4id4h145p+k/Sl8oltGGGsAV2QcJKt6gtIRVyHJ4rGZWzknL5hOLAZUKWsLxrMP0A/lVzWnOUZjyP/avl6SfFkl/X73D58z3doDfypSZPZbK81/tFq97e+eqaRMAZAWEYBhgece/bs3xEJOUqgigc2QAkGM3R2FCvhEKNsgw35R8mT2H017IwsMOdpDUFqXMfMuZZaffIhNzY91cZFQwZnnMfrUX7LZMgh64Tjvzh7XqLP32X3fuzziRgsyVUfJ6YkbYuc+8JA+cbJWFLGzMm1lI83pIgRyYSQlJJTaIFMyvz+siYmHXIRNXJJgkq9mdcTX7/rT6uvjHIouzVRi0I7WoM5qE+/bj/Uo3+9QJljqJarwtdbASKkltrSjSUimE1zFV5bdk9O1xlju12/jK8zVSDafURXV+Qmj0sRTt3WX6gQ4yU5AAcAaE3jN77wKo3+O5UwncPxuc7l0zXcb+m6QB8OFwM4Vx5znR7Gj2rDOkkagWCTRiqqrRJrkVZQNEYVMpYm7jBx3V1utz3llpmPiMiI7xyfN/QK+IjvGy4HOKQQO71ffiDx8GITYzpQu+aqjq4xr/Fd3V8zSdxUhsW0rpNSXx30+4DvWb9Nj08IU+20KRbutla9hIpENeP5nrthVX+aLuJxmuiB9ShK7WGGZkXO3Ktf2eyiUT+EQ2qitrW7zqqtXWFwisuQbdd0A0abiJcBedpqp8paqdpWQKjbqphNgcm44xstGIe/kZ4jOWqlpsEEiEBLVcKH7NjZpVLDbsuvLf/hw9efcxlwKntMAtbK2peZJNBYx+HjHwH/0lbnd4u61AC0795ei/n3Xbb+Kf3nd+OaHJxwgpzafu533p6oznzIOQ4LM+y3rURe19jup2l76O3dbvekX0Fh6ohrQVrooDt67g2Fu2Rs2oM6wFTsCZQCWo20WhcJC6sKHMjxxbTax3JXruS6J0ZPdz/jX/okGfMa2mFE2wY/wYyJRcTGov5MmV5o82G64Nr4l1N94F/UV0HyuzjmqwkV7Am1w1+ET+hGtTGWVduOSSwHMa+xYf10dVq2dW0TNmT7akgO29pg2UvDKdFF2Rh9HfNIybSNwqKdWC0TxufNcxXTMihprMZ2rKVWkSaZJ6zISZQ2JTZTySnSSkw3zMC7CvWItWlFuFnlSMS6s5fX3s2oyLujV2ZVVGrJxHPqYaPoRyFLkXEGprtA51gUkeh033THmLX/KG4HPfFuUrbv357nm+JjPP4OpPTJdFmOZQCEEnSrjmEYUOHg59hEDlkVQPJcSuaO5zupvwVBC9+P8qkYQ1p7bbQJ0EBGMLEIwS3BG6BmA0OSCgirAtjSJKypIGkOwKTMCgHVeIwGyQJn+lfXnMAP7i9Mm3BW1il7/bh/nMrlR3kFyRM8+vAc7y/fRuPF2SL38L2x9wd4750uM+DZaKk7UsQdwIY0GG3rNxANRS9pcrmVl+kGheotBbphZqHOPZgeM2EGbO1GHo2tS4bdQa9j3UdUJQ1C4EoNKA1BwSWptrijJyomdyR38ElZoqqZl0q/wEqDtqoCtbNGlrIky6lLPBItTTYUsSZtljDDbosfx7i0l7/ISynrq/6LCiJEujCogm3Ncu6CsKgmZmcz25xbAjh0MCG33eeTebW9aSw9WsZQw/sMsRwWA4V3wbz0WmnTMg6aYK1QxIQ1c93dghJzqIr13poUKJGlkhswMrmh9atcNluAiBXuFNkua5vACXbQSS1bQoziEaqOFiIygZWOI851dvIklYxPq2hr0kbGTjHeNXDJlsJUYsA5NLBidkuYf9qPeXCLrbZ1gAyqwiQi0SB0xggnSKPCcYT4nKpNx9GFRDkSLm8Q9S4R2Pk+auvx9I5m/WP7qGEps6NdYi5DWGz2wkoCpi1WYM4myjOI1Xk6VYBmLZVCqchFEy61MVFA0QEVXgbAhLC7v362Pd3Pzefndvm+GOpWP1QnfR9d39P7ygcfptPx7xN++9zJbW55L59Puse+xuAhjQR74kKz7eT2ApiERi7VQDrvFsQJ2f81zuJ5As82MYFtO5bGpBJZWVNCDLAQDM8qgQJSezjb7PUodzrffKuwVAdQQNPKnmxCljKyLBxHpeVMOmJpl8Jl/dSFSksJH11CVympPIQ+Nq7TtrpSc5KNEQJM9Sv4oTWzdWEzC1HdwUf9Yf0vTvOy+6czO9Vihmz8g415mZy95d1Fj5F6NOfaAYpgTuYpE2ZMY6YbfLRYhaUQfQZyhTvQY3Wzsy0bYkbsdJqxUPJt81bXJAsyWO/Nq88+F5NReSpDXE3WVtfOL28VU+jezU0k/RW2JBtMhqwYaYY8FQcSWwFhGEf1CZmcQG876a+nt0svbtRrs0krUfXvUoThZFA5xSJSX6RbvtooVYSlVHAqZJ5Oilq1dmsai6vL8Y6PLtTMuFoMVAyNJVAzneMyRnZcmImH7BhPUJTM27iQgvn2WZ/1MdufXE/b1QbsAyxyy+0sYLACAW2sihFCMSwggPQ8U2xkAjFQGGWHJLMzNQKmLa4++3N2CGvEvpy843oy9/T6gHcFa5b+xZswfWO+s87H+rjo3ZmOb6vu1VG5TniZevF6cjoS2glmpNOJETDjnj9GsPFuOP+nJ7b9WHRy8GGDm1nH7BzBOkPKz6jVxag5fLyJCRAoxWhHZIHOnLNHEN5OdEAoNk3bTpxwNGMbY4y+PQ8kUAMX1jelxXXXF1VmUnWDiE/hPyEy2tzoWr8ziRMDhgqb1hp9NI/AeSAj98sVcL75p4kro0u5WMitqYl59D7sejxSZdiHWv/Y75XfBc2oW4a2RahaO6Y25AvAldfc19q1T5uuNV6UMFLRuVLbTFOQa0N1GDgdccnL7LZUa1MIM1roq95mdgC2giH24R0FMeCblDtkxFY+b1h2A4dSv8gth444fSrCGAZDhLKRFI/6NBMIDOHhtWFbOIb6ZIsuMMmSIrJaPTyz/Zr81BlTGuqmIYOpe8XymmukCWdCakQjwzYXZdhCldJPPIGFflMX244J59eSzc1tTtXoAyRy3qLXUs20t1YVzFloDiAOHsz+X/s01zpLs6yAfsbQURUxIKZvueP2TXS3jH/6xXc6d3QIAIKA8tp/2oDvX3uIIIaDIFdJk5JBAGCwofExTx5z9gWlxK19Tr9PLkUyEAyypYEzey+veS5mPpWdtwfv7DULcBFW2fPwC68RvSu2ojSVABgZk3AJLEmLyb3Rd17CgVSwOke04hNHwRnT3FrJpeUFF8AHCbWEo6FYWJQDO+SJQVIwS0hEaGfcLj3v1cTpREcHTUIaqUJTTvssT+PRelg7P5+KaMX+Z+r/MuU/a/Guj5xJUap5dcgEKB6GR8I67H6f3U7c7PlFfiNhH0/+lXAS146pfNyAFG7YVxenWBFQRno+bt1FnOwamHVkXZtEWit3m13YxlbRiX4urqCbdkTosU1brFRGxqYmKmFuKZ/HK1BSONKWol9OGCdytCEN8OEhMszDmDlatZBXSHympA1ftjb1MLTLJO4Ub7j9ADbXBUYreKDBdMJsLEqO6FPxqMZDLwnWTAFSGvppt3EgbMd/ekS1cFsNvfMkPy0p1T22660fPIoQmDPzobTZK0KHZukcY+xqucWNr1q9n5ZCL+kwfT54Z2wis0agUOcKUodrV1EhQK4qatDqA896trYwMASYSRCiAvyOwwvLWQYAEEFK+q39yjmf7/t69wFOPCCIdeGhgiKyQwsAwY70O6+vpomeVbd4amRMZo90RP7POIqX3B8Pl+Z1HNiDv4eEhCliJEhtk9ZX7rQ7mSgQB0AB2NR7QAIe6XeoXVXHQSDZCJaQl5g70XIkQko1bnXvXrh5fb9zp3W14OjO9ByLk62+LlixlQCFAgAoTax0ltm+zE6hWWUBij6XGenpS6RGRRtZzm7+U/1/QtENEebBo1TzuiWkjo/xeVKhAey6Xz94ZVpbevnrYVh+4efxvDzka/FlhBhG2EryTL1Vdmy7iNaGYVnX0IROQq2satela2mMGaqACYu51vMvXo2tyArDoqRIkFWurNNVlcbCCTCWscybLttf3Msc6wR6eA4iQyShTR24SFICk8KmHBecM/ZJfrOdvaLvneYLDfLJCEYCo0zlxH2v97vTYrtmOby6PU/bFJFHmUWQz/qI3c4hr1AQnzLTZNgrqwYXZ6SFjRwPPjgFCiS5GR456pPg7i+wenqShpiMmrAqH8gKgB61HqMILmkoe9QdW5kJ4iZhO+lIEyAg2jpFAGxnL6HAWPIgQFNloaQymBBTEl0fBUwOQGmF0HK/5/XbzfTTP3/n9/dOGlgIIBpUtyTqqGsARClhj+vtfSW9MwJ+KiAEo5KiJd+L+6qlbnN+J3Q7OM8pEG5U4Twv11s2X3fOZLKYrJQEQAo+VX5J1yk/hAc7wtFABuzAEPZmt4OBpuSRKYJddp8jqa1Le2wYmCQrbptbT+ibcqOEgRuBqhoHx65uAGUJCICoAQCnqx4ptPppISKruhOJIZhwnHPmCUWnFVcJoci5I93fXBwp+z0e921ZXGfeS7Z9ZEShNg31DXw1NvGRAUoE+lzjyBwRSTLRGDvkzAxvtuDjnPM5xWBXBaOwklVa5HgpAv9qV3lO9eQUP2qOgWSxrKlApSNZcIRBSTvgihhXzJ4lDjED4gw0xDIClLopQqIY9IGZn9gZ48RkckgHhB9YK3uRAQlGt50npkecB+UxFDBhHNjMfuIbzS7DCgBUaP3hKRBmXOkMF2Yql27Y3sAirgzpGcBpqQBHjLLCpnLDvMlICbRvs0w9L7+u3aBdZ82c/fHZweMhuGN0q0gth/iJE6pihSICg3B0gdCzu4mY6VkZeZfLw7LCysNQBhShiEAKAjLpx8fvLMP8+17/YkgAwYA2yF3z2OhCXFAqqLisjw965INtj+ilC9MEIB10//G48u7szHd7OSIFJYgEyTAQnPMRMxytWo+aTDu1KHcApoH3+PrrZv+Ky6/jqpArmWlCQUUP+MYKFagYp4AgQgfC1P1pHHdIrZ3sFSlgm5/+YZ85xCDELI4OWEpzp2OzmTvRJmRJavLgelyVvQoNawLCXCdMTNfKJK3iQ8k42eiFWKIIkCuvDYuEAaEr7HHSLkSC6RG/W4iIqW+7FO5tIobPpK49CKqZYCJCUjNgQFgP0AmTme2aboUboI3dCYazZuzMT1njcA53yn0w2AoJeUdyl+YJB2xttV10BzVrYB7fGXVSK6/DDvwtzHWAkEJVeUPtkYqzOROirAd48l3RWCRfRF0oiShHVHmXXmfjR/I2afUK++5oN8oqJQnQze1ipJ85XMYl/GVi5Zi92tWpevyPMrWmtWaB6mDPaTdxLbmwj57XEFguFb/CoM0SwkRibrRZvXo+acfXNzeWQiM/uBNRU7rAE24pE83ZJc4OQe+O2mFbbZJrs1ZtcgU0YKqTQACz2DU2XjyOlYJYCt7gFfvTufrP158kARCIzFVCIjkXLUoBdEx6Xb3zl+Fl85nRhjLFzhdV4MUbTnN1BWlKwSpLgVGZY6nE1uTpbzv3G4/2tBn8GGrfZNupatIQeiS+Vn7EfNquYyBlu4am4LXSOWuXQFGcH440vrwWZ+V50277+r2JtzacDveVySvXd7i5qk2VQqXSDFnbvMQ7ORNyNtk39o2sRemlTuGwSRxq8ECB6wWsBtqv1hFFN6ZNMhNJmYd1Du/ynXqAzr4mjrqh6Mjtyr1gnghon+lWEuYyGRIhxoYypopDcHsOm6Auhavkhy6tiTVJMLvHl6IyjFnO8sHcH3rNbFr7HfNqtFIJgdHnEifPZ/YLdeUy58QsrizDpQuVndrZrFv0MGIonpDxs7lueP8JXWB53Mq3K+l+8jZoAyDsFANIfyhireTo7rPNEzxMb0S3RY6n6qXboe29bSyVnXeyc9jq+guytM+wzWM3HHN0ixttNUXFry2dhyZIZRt2xaEDHorNp9HQoms3y9nkyIEWxqlg5RiVBxmORmKbMMvbydjIkHOwdhkAuzTFoXadYIIRnIgBmM0mQIUdJNONHb+fSgn6/0JGmnC8NnrNudOrE8UBMQlu6m6jRG26DKDAcWmfMX/fW5Oihatn08wnW+ZOunocIDmaJb7bAlV1RgMUiYKfAKa7aW1c/YP3evI25L7D2Ckniz2uAuRptvvK5MdnfXWM4saDgzDWsjW18frHEsDTPPJSUj3wfCr9bYpTY+5x9H8Tn4hRmBshbCQQQKz94TOu4dxpLebQHvBdk+fqzqe5z9zPtCaUmETUD5W69orNPfiMoTqDYGZdvVrtlkmydG69NF1nYWmbEbCwDitY3qFXbp93erT6XN7HJmkRsZiXdt1RcwceF78wPcXbLOI37O0xT3MP6nGZZrharVxlpEjsWMnustqL7eQ7Qy0bQU3kSXeTDNc04Tq0RgNjIsmRuukiN1Wc4hnd0jx7LMOOXNBOXO5JWlvsqL1YBnwfsEN9Uiyei/tEJDGMDi6OsPStqHwU0iDDCj0JSmtBD3o0KHFbZk+33vSBEvL1g7ZX3r18vN090Wi0B0hUtpl46YCdRrbB4iQGTvKNFKRXTI4N61RbWXTDEvQ0uXOMyWCus+/E3bFIGQOj372e545DIfD/oLatGwBmMwKIWpmgqGxYAfaCujo2+T8GKJSKlQIyCQagd4MfGo0CGQBrzOY1f+kr74a7CzKJNSagmsfWywgfYvIzdv5u5H+MuBIUFsw+IpgX9mF00xyVp/ADgm0yCmrAvGb5kpp+tuxhoofudLFYF73vUYCENyeARlPIVTdnpsVYayZ9IQ7X8tOnyZ+/ePdPlZ/EfR3XJkNnLLSuUDmB7nb0GXmKw1vdZ3fXZ/V54dPlU1mrqKjpGlxd4ZmRxxXWEk6xT+naOhoY0StezqEWCR/NkDquTigzFE+dVcpRNnFa/6DWpbnLrsR9oJ7wOJhpYDJ2q2XYA4qpOw1vlJFMydwo4+R20MALiuGesccONbk+uGfyiZxWHvVRCnzMyjQCxZCJPsJ2CSEDV1R88U14psfJX4a/1KPj8wQZlKZmegx86PCz735hrx9s7knjejYd6MNYyMVQDpJrQhvT8KnH6vHD6+WGKovrPBYL6tibcLfqVAu3OF5rIrUN+gbzz5ypavw3e+K1D8evzPilMzuolOI2rSEgI7nkU/aBqg4+S2x981ngcv0txa5IRQ/vFa2tq7Nmol6zsAIiV8MIfGgAYBCc75XYW3SZANLs/+PgBDQBhA/gSKf5bgwGGGAFpNIoEktg2TAaiILLWajbECUTwDR6//CiRa0hBxh33Lnv+3pqiXFSnKZXPyou+pzMnxb+XPDXbCzd+uL9ktdp4oKnE3IxQCgBjasRpAEUxHLk1w/+2uk3zvVTtpmszSySYSl/mq01RkqhSBikEk3zq9/7kzfiRzL//Mz939HRgcZCNMeoNmapAcfwjHnXDsek+KGmu7n7FYxEZXqHf1ixRV2q7zFtO747WeZINyZfX6BEUCjodDgDi7IWXrg+QZqYkZIWNyVaQL+x3zq+UYyyj6v6Shjxe+0ke+k53kKjrjfzPU1NFDLBJCVQFEVUNhqIuhkUli1wjkFtIYYDrLPJ5XSBqErFGss1YcRrYt4plI6LzpvdbebZdFIeq+lCDfOoZ6iRwmKI9Rq8Kl/ufCMXtQ12LCNUImcASSKjCU0M1UFEYQs1c+WKiFImt/JS4WJun2dcJVNe4CzMiCbbMtGPRbt6W5NoFB2nnZqnTfIpiR0scotJir5j/gUCGjpglRhU74kgNmazifbkjp5qFV3zXIc4HlG7G6FNhNIS3TVY2sm8if1kCW8ALbmcKeNuMyvapTw2wKqFBbQOgFqoFTAVCmvsoLYJKAjcGx1vc89ODgKUZNLxj+mfRqyHgPn82WjFMIU7S3/flr9B/fpx6x8/710/vS7HhY9iTLximPjd0+n61UVvSc9QexRu9FnY8DZV7QBKXIUO+BrtFeGiLBMGfSUUEfKJh/YLNjPTSfhuIXMgrJJflFn71cwDZkqfVX34MEwVDAwd6SJNusPjt3DFlB66WXxfyrAP+IxYzZeeJ2+L9+l8hkWMafzUMXQ09yc4h15hDYXjqqWkikEsYzX60wjCKOBNZOT5SEhHaJ9Ux42lefLrsh9O/glZys1xu+CZxdDv7k9aw1KNbmy1SO7RiduJLhNYwnjjPk27+jp9FZJKEE4s+RQjlbBCaliaUTlxWwYoanP7JxDOr4zdcU1mJdbM5gKC9O7I+mE4R2fKQdgUt5XvxKV1hIauL0TzfvIWdKDNLTQUiAR5WGVR1/2pmbm8njFujtTL1IyRXJcmuOTejCTxSg5JVM+vHOlXgloDKXlZPIH6acoeUqeD/yq8mzNl1pewut33UZkx7cEGctUkHNurRjsvw9DPceGVBS1b1aREzLW4AgAAt+9/Kc9PW0DPwDDOc3X3s/f95DtHUGptCW41NlZez7NXMh4QI4sVRNIUz4F8MvP6xdXLea71yAAAFIoN19sWHkduPAGxkyQqnXpwiB/trDQjd0qeNREYNj64Pwufn5bu/gLm8W0YOIMxK4d010nfg4joL+fO+U39KTT0or007Pqy4QuY8oClICWmgf0xBF1uBw3GZ4Bagr3z8SumKxzhPKg5WAo/Eh2WDKl7SHDq5a2OLXq3AmIMG1sUNfJI53Y+XA58ClVm+4qFPinkCkAzmFAtvFSD3DDjOG1/xlRiVVXcrfA+eG0nQgvHnWNCLbhMy+ghXqqJKGp6a1FdU8VIfaZurxz2Fpp6HdSK7w/2anqBlr2ESDrs6J22DpZ1t6wJGR+Sy8rRuYhqXdE/08vNOaHeXV2mUg8moZjlR8KsDLQENPMMChaBNsUXcUsX59x26EYDZuVqyQuB1ElNNztgiiAn4IxJwOG+MiYghQejnvAJQzhvdNx6Q26WIiiKd2fgyvh+9XEGHoI8lUjqHasMKikFBmskDbVOz7bGrGSWMQumznpGnE2syciPzKjDLYeLyUFO62RTs97Mtwv/ZL63qV0DnKdMYF2krEd0ylhRVETQvTKYYtZjgh/1l8owoBXI4EgkncE0GREDMi9fm8YabBVAsAbaaF54/l+VnOF6ersZZ9YlQRRA1XWOXa+ByuUAqJAPIC2SbmRsZPKN0cBsCmMFdkaNe/3X3ole+fDKzDtA5XVo+32Y2wVFB5XxfUsup//0oXMeCz9jM50v8aRKVBRyjpn6WFmzeKTHtH/GQjV/WE8Pl3f24fs/wBi8uUEDMTTxe1C26YlnH1Isxr3cGQPiR11lUmJZkEoRAsppEeooYpsIeRHbkG+53cWUdwztR3if4+smkbQwLksNEubPoW65f5TxVYzjT/1VJm3TLdNMIURY1FVXcnZcHRQGKyWiff9KFQoDd69UOKVfBVeep5umd9Nze8LVBPuxZEdeVXV0hCkP55xOwdXV//jXy7nsljvseA88371XJDlOVubvSRjDbEe0zJVu8lyyQ59ndLOZdxhKM8gaNp5EJ4Q221QqlHOgj+1hAY/BedIanM3zy0ZXHIpX/3zsVcyZEuq0Op7vBMgSvXfFPFaKw01iClYIBUsYLyYLrE3ASpaoKoKyGbFR7qmbKS2Wd+zxSQ/JhEMBI05ThTLCry5eD+82nVIzfGacl6NfY7l1ij3nk6zZP16pl+KOuEadhvcrtF+ksl8CAGoymTccbXxUYEZQyyYy4lUJ0GBoU1vFBrQbd2lrfRl/7379LH1vfXdHy3HOw7WBREuBgiZO7FW2ud8jrccrlmD6oACJjI+l27SYcKdiI3OJNIY+NIan78j9ePkb1MydRZM2Qp+iTBxNlkifTo13bvzTdfC/J/xjOjbPpc8gXgk0drGf4N4r93U++NGMPoaxa5en259695nVv7tNqMNPfv5DLMyaHr/cVbbEvrkxMm5N2dH603tyzxvGQlApGQAQaZw5zkfbFgwtMEexEa8R70RByBa49rkBzi4LKnrxvIuJRbYDczXLiR46Xi1t64x1Ek/xSfUvb/XLlRKKmRhDo/UupYzP8PJLKlXFY2W8CVfTLLGc5ro+92mdJ9zLPpEfb+/laMTxWNO12LiWLg9S6P/xH4TDF1swDZsaWV9d+XLNR+XMo1S3qki2de+LPWpu8BTTJUtKQwYpnUeECiKOMQJUaFttq+wW0y4cn4ikxtWW/vmqBFfzxtFw1GvtxcCUILpHLTYARFItOHO7iUHlOe4jVYGsoszXNHeSotFpFqSx64KLBtdDAHwqZ0qRM05+5458xYi1XKOWpnjYNupZ0b+CURjlaP04qbosF13r7KSZXuLRrHGrIPnmdElskMLiWWFTG5QQiIXtgQVgPrZtNmEdkym2LIEETFtiKBTeOIz2tnmw51yCihhCqh1NVxNAd5E0uXP4ZGifwg95lYe9UaCm6Bj/uskNkOAnb3gkna57U0DUB4zXEm3XnZQflKrYZ0cvMT7we/MfpM6HufC39rfRy5ZEX/csAjPwaXs78Ks/eVP7Lvarx2+7EC9bMvH2eX2DnD1Q41jYGAK+eWbteFQwcrCJu4xMvrH2AOIA5c4v7ysAjDlRAnHqRQIbMCf8rDliw0IBr0NvWoeQKpymXmuLrebHZB3PTUUliGE+t/CQd7Efccj6xWhuxbboVwt/1vxdzYtMzBCBy7V3TfDm+ypbNPEyoDKvMabqqnF8bLvI20kb+Z+f9Ii/bLxKFLbR1DmV0mgNpCMn9f/03zx2tpFJcUTpvcxyXHxM5KPPvWslJKLZyooNK0ClOijhbX46Lc3L9TACe4zAgpf78BqN3XX7VOJYmq+RSpgvrqeIFbomlZBCSawfIInYMtPCKCTUnVqoHdHco1c7RAYKgTacH+X+naXyGAIJPicjVGP8BrwjUhg9QtE001taz3PTHNTZe6R1LIFWpiacyVvZaDxdLddfnec95dXIbFI1e0wmu6I1WcazaqmPtdlm26YvCsQAmO4aalfcJ6KCbg4aulShJXs50mw/EuhmusclqxD3linSD1syYMEAsPVqRTc/c+enXucvLl5t5I7ukFpUqJ6CEuGTmyMlR0jMqYDh65ha4bQyNLmJpxjvmzR9jniGfPJPLOHoMfaWVjsj9jaMprcxafOofR3GkS7v9XiqNwhxT9OjHHGZ+Eau0est9rldHyR4quCGvjO+SPGG9L2C9YGeWviR9QPmn8APD9+zounYEY/EWPYjjyZe6+BOuQGNCVTob0lvn+7rV9cfbKR6cbZR5tO9rPUprEvy1pJInVppOYcQsVaqvB/alyLio3gcqCfE8a8X2FAR/kZu1FiM0NGJWHXddL+oq57tDk0cROVO9fO2WOkb/L0Lqo819LEBRGmxTJMUq+Wq9T0YB/LYkcNWK9qvWfOlhZKV2Jd1uojLulRwWwS4cOGS8DwDs97NYnpwin6poHE2a/wB78hpR0ZWKA7hfVKUMRpXquY1va4NuxTLj1c3P9u1Uy9cF+8We4iBtyvFThW0GdgdBQ+T0fCwYUw9wFWzGxGrWRIJy+CvyEvlsKhHvILsN/T0QTlR+Zj6b+nyTVlQfQgEoKJhLA+e08bAeQ80gRo1RnqYUdLl0jIaZ1XI7XTqtrrwKroANds3s9WdUX7rF0z3mgszhKFFntoCDAbbOrI1bwymDuxuZxltlWphKdK2b3I+Tbbpqpxu//y718OHYcb98tlj/IZ6JTcbFOMjpofc6TBVFJQLBYN9wPRwh+JEUwCC3QhH0JH9kdUo/ajzm6nHQb3/8dNop9VggllUCELl5beeXWM/LbQ1lcoV4Dn229cSV191PF7StLzjc8m+jKmd8q3tGd2uduHpso2jxdonJuYvHyq532863UGPgKc4EAFHXMed/YfN8s+Kt+DUl2EGLyPCItEkb7Ytmdm/fG5nFtc3aSItq1bhqy7GchY7k2n9OMjkLVlhHuwr3dv9PPbHk0W5pdpNIn9+5BxowIEnAbAL6+lj0r7LD9UX4UfNNnNzDyuxt87t6lkOApFRyyvcWIK+Qxi1NrlxrO28hvWIPs4F2bTalq/lzx7/2z8f/+d/wAeYz7OPL/+Xc86Fb1XDlSSvtW7txP+Vv/5BP9VnpknamOWaFe1W/36mS5ZGEr18LVYZRTeeKQfra6i1fx9CGB9m1AFk0tflfDNujo5k1CB2ANyI0BU3/aIOrRgbJv2IIqakVbN1tR+z7tpluflyJtRJc9B/gfmRrNxjJAID3GHeyguLc6nosMJ2ynYKVddgle2WcysgwlABFQmD8jXuE8AArLoBwNYH0DDay66QAK1jGYNXtNlkzAAEAdM1znR0PNpQlpLMG/U+/Vzf4tXn+UvN02d9y7he/P7jz3pvTS4Pb7gyi2/RG3Uwb/Psrislju14WO6qnTpIQfeXcxojaJer3LddK6cHwJlhmWZrW7P+3MdZWG87f4Nnp9uTaXz66cQ0Xk9lC/Mdk2DrnL1Z4P1Fu9RKVV8v1fms9PHJvXP1+Nb9ZSM/8To9aKAfJ/bF2X+NV7F+6BxixeEx0yxgkCkAM8xlBjW5Z+g1WBiRK5FanOjFfZqI5IFfk779j7ffZhj7SCmOez3wtRkXVR2DQmJB41mqUWyVl1pnG5PYbBmfIuw+2f5101fqH2/+Frg9EeQK6ykMJyN0GFBSkxl2ZFhLnNVopVU6cHXbe4d9KZJmMpmONiNyGW20rqVOaSIXDxXvDGzDEkkMnsPY7IPyHpcfY45zhZ2M8NDi2SPrNeVlm7X1VX4Fk/RsoRRNPeNLtc5smmZQAA4rQZJAxswiJLG1tGzM4a6wIXklhjkMQC6u8BBNQUAbFk8oBY300T5Y+czYeJAjzO3k6l2lKdlKrprAzoxchOUszweV1AvnkiV3Dpehv8i7ZUENuWf6F8wb9Sr4DrZqktJQHs/dqtcSF+/c2p7ITE20Y/1ZohG5pqa8fpuwVCkwSa0FwJFAgJVtwkS7FAAIm26knM+VrR1gIoOYDutq7ffCkz4qfBL1TfO36tgQLfQIQ/Z4mcU+xR9O8YvAsf11Vf/T5a9fX52/o8fXS//o/afX7z+X/Afa/i76T6fberD9wUDbla+MTKzNG5w1GgEpRbEP0HYpyswEJ36l28q4NoE3lYi4OA+km7KPl2bbb433V37e8j80+jb5Y1fPj0Eqn23SI9AnWSj6YaZHqjTqdLmme0sx0WkzVE80zrH6LpIgs+TyLlSBqHswJ5zmddy2Qkx5rRKL/NNScTYrcax6UIYWZ8cpbE87KhJZWzYW8h6ZKUI9r/7xdJ50L/HkXuQzHCs1ejVHsPSYhJZx6lgMBpH2KUjYsEt8JKv2U+ZPMPUZIBCHHzsz8drmWmxJZVAE8CCDSsWINxlWBlynlRceA/vKx7abWeIWtckCmxOKVLBFtKFhyxQuOuZYu/yhLdVCCXd4eG7sqcz83Ti4tWFhoasyE4eGypZbSHm3gm5Q5f4pA4TgU/ALjygckiyUZSEk2m34Vp5d2YeLDOk4mZBGlHa10CGH0naqiqqK7RzPbx8368ixUmg7N8fjcW+/MaB+sEojVYnwxeBhM0ONkqNYROPXckvuW1ZYW20RdNHaoAX/H4KAKfUnM12vjmcudbyy4cmosFyAOQBwqfLLB9/bnTpDNDCi17bPPEya1E9eEchM/b5anvGWsqICcyZIvl3hHHfrJ1/+b9Tf5MsfDcrx6oOH+7n7kXp/LTz9D0R9OQ9Jm5AWrlzwvrO85Pr5qF/z0tz9MPsLn2b6x6eTozeRtz8wzSMJAgMJDA+AgPdwMvJH6QUHerxYsJZjh68vlv1rKajvlsUcdjmeNZsrnUx5wlX+CaR6YcfsUJnqLLZv9M9c/4QQzEW9CMlhVrHiLixI20tfiuvyMWkf6M/Ai8ZafbyqPgOV1ebhIPsgbIB2zl8QBhpR4cwx83SMqL/U8xhdcJ/+/jbxwb/8AMC/g+mxn75wmWmQkJOTFKMvyrFSMCziXDp32DbwAp/BcStiP3yoL1zf9pHgWNOIOifj+CZKwZ32+vWGRxNvyify2MYlCcK1U4XXEXsKCrN3X3YKJseqfJLu3o1uYJTWXuhfgk0ZAls8U/XaTotBdRyns39mXiqkUKaQ3bbu3eDrVOY0zpgeaAzUpITHwR68BAeoAKPEHNvxec7aA67YvgkxynSrorM6VdyAJ2vKdaQL7HqztutwtVgXaotqCX0xviaUqWGkoRYbd3oU8TbYzgQuUtqql3VlS048q+r1nHJ6YOsujPzJ8lS08OzmrEvFy+BNcwt6AQHmcTODZPPc/Hq+N7v0RIslYGE/zNfPhle4iIfrcO4WaUwBDthS5gmLeoPZJ/5sRW7W4jxJv/L45eK9cbx6n27peXX+HP3tiVY/njpZ73syvu7/kGKVuLNmXBKBoU/Gm3mspi2C97SYvfQeXdvaxY7t5dlWfO/t64fx6xCjzzhcslvfpL3PlWROQ33pyWkU/vr48Oszex/W8f8+kL+pdb2L57BeidnoKEefdhY/prozxYx55FC0Vr38WO4Ua9AhixaU0NO9d/OteZ9JfWAeyRecBj6Yl1r6VFC+TguTlr7LPtu24nNzLPr2ED/yZeQSnUlJM7SVKnjGrWPjKZK8y3fCMcP2eExISzQ1humPDADf5DPlWmGYE5/2mAXIEevTp+YUYbmuOWKHUfVR45StK0ogNLaaQ3ufoitrWh3eZJZFRFZhlC7DoldpOpOW45pwMDusB+b82ms8qSglC5WbKRmoDhVm6bIjGeVzDt3J81mmkEbeUlZ32D32Wlh9QpJ7PRLPuDLvsENAxSxbBxyLoEmRo8Eb9DJTmZm70WFJH1jFzVVx18Bw2C6jPhqWHXaUNjZTCNohW2Z6tX/d9Bq0qeK4PAH2BVRbvXnpVc1wjvlOBd4sN1Dw9p1TdiTsJOTXM9ALYENsgI2JHcnj4XcWPXxWQxRjwvtay2JM49eNtyZtAKCIjXRa/YD7GdheEF8uQA+hsY/fHmoWnXEQmxQQBvvKd7X6uXXvcLHPnTEl2uBwwFiGLDGjjrNMmo3XmaNOdQwsEkXAQ4gShqWtxCNjvZ/5my17f+zRC8I+u5nd4YT3e/xyC3+x8y9553D7ZucqaZW8zk4vbNmst4/OpzW9PV+t89Q36KtWn5auiy0EsXFPf/mCa/MWiZIEIZqi6HE7PBzDSnWJ3tylFjqpMD0N1yQ21eRvd8YKty+3/7k8DWA/V3CcdqL6mJmXpd3lpNDHY9bx/JZ6Z4y2UUKSeVIPorHe5TlFPeOHjPDAcRER8mTSTcVA9/PkQMeFy+jmPXkfPnfhF/S5zQTvyd5qfW+8ZBjyGQZgE71cqllei+OhxPhrvC6wOk7j4zmxF+V7kmeyw/soWR8zW2fwa61kZJzV5dGquD57WSb1/bY980+O6qgpqv7+OeVHHCuuL51p5uXeD+6/EbFBUtYUBaCUoBuAktHihnF9AnY63mqfUnKePBTizbhPKNUSYpA+OpQ40tGG2FY/GxyfTkeo17FujF/jctg+2jIMc2t3ut27stiQG18Ji1yLoIPDKSyKg50JZpqR9LI9GTccPaCj6u7koJUqleXrySSy9AJmlyRAFAAsMAClATBFAlYCsBWYEspsAsDESLFIZ3LaTmjwC310FynmYSucZyjURAmtQWnP/qC7o2MsGUJ5FtVEBZngVGDHao+JGh4QjUPkXMyil1C6jgROBPkICZXu7ZgLYDfHkcWbmpf1+vE1Rybb7unWlxddTtDXGTIfYxZ/mcU1vdH5mZPLPn7RYjyC+YdQjzX9MuNyiIfJ/S1br8+fx+K/tMa1MYOCoCMMRkTWY8EOuxoxQ7xBCyFCtd+Lu0P+ZfBwy6DssNsJ9PD6TgxbwEqIJUa59fWUkOWEgR9J1+Zo2mt0pZIVoQSEafkMO5a+5OXtnhbE8bC5xIrILEgxiavtB9WNIhcAN2M0YlDiuPqGJ53sfFZYVS53ErC4Cwcazcg4NmJFEGUaJ90+5FnRpmdiYCoO0YzeqtTllYcXJ32aOaH1my5LC28rM+E9GPGtSJdj75v8dIWSBmoywqCF8/i6uEqUmFTmTCsjLRFJrTMUfy8lyjqwoW+zHDkGMx+FXbnPce14pxUOw/iRgizdILO06XeS/VjIMh39dHxFtzGh7aPDig1iUazJLy6e4g21YIySuhTdNZkCnpzDoDJD3NKV231od/zTTfMPPWndHNSutXROfXakBgNobSsKGGEWQ5CdutQWgDFuQUKdEJG2G3W/FpmJWaCiFouqmJ1X1+jCM7nRLB+qSs4+UGp6SMA3Fd8feCof3+qva7mJLmJHJiZeHWUgUi0JIxtyZ5EWRIu5CIl9NQrNB5DYE6uhguf58tScLnv1yde3SHLcgLG3l0/L8oNaPlnLe8wtkUOVcQq6wnBdvc8KjscfvJ8yDaVSr2O1tAvlaviX4FKLX/oX6vLLv1zUQ5GDCUaaggIIVDmEWLoe1Td4scYPwh140T6n9co1nI9o1PvB1uWCgN/wS1ZIhcS4y8bMsc2KP1fIV8WRh1fYIeXLOLWl3KBoGCNAwjBM2hZt49nBp85XSSFOn6S3KcalKJwTOmGPTLNXmLg29jk8275h86T8CL2e1Md913EOOij6I0CsQy93czFr6+4Qumyoip7SYzlDOblmeVFX2UwvpDqvEK4328nM1KtZbFWs8zh9sjgqIaVR897aqY/Z6n5zOWLKQvikTjSSh0RX7J4BKMrSVef3kMRxeFTU4escX/uja4sjgirBMRjIw/QpTetspq/SrQG3FCxCRVWW747PuaKVl3GgUwKzOZ0JHlXjlZUn2BKgoQFOC8ogcbTDRX96VdLn1r5KrcM+/KBn6mU8wFPvAuigI/cRAQC1+vSXMhpUjFesQBcGLABIPHiyR89BAUQBGwHSFrEm4QoJbKVo95K0I5utLxUfyMCs8+ToX5DZEHgSE7hFezlISxMLIBMQnCpRxTHO2okOi2pi0Qo49jzLoxiugIE1otMuM5wKn1rr1B/p+MTvUdE13nf2t4V+6o99JD+dyu3+1I108TiIbb37zf8kSQ7j+PLUd/D4w0flu/vTD4P0yKbw/sLTZwa7xr/dul0QVRaAnoLEU5JQYmIU8VBUcyd23GN3DyjkeadedN1x08XNoYhT7uYgJOPzFueeD8VLu/jV10dYv8CExp7/LPqfvm/mcrURNXCIDtstP/1uVhecDz47S6qdfj1pe2Pe/duhWTqGNGGSVtgVxPARv8VXfA87vuJH3OOV2sP6YisOHMmnXmlmo2PvecPx5xOOiQx7Zn72eEHd5di5775SFuCE64Djiatl1mX36mi9M5mx5NLZkQfmXUGdQ3OBvpPYKpTGKdUlGch9wLnZni4vOmEl40GJSkR+O6lHxorwWdkifrzBmguXeKqu9fTiMYKaPIxx7hEpr871PD068Uu8b9xZ/rB5J/Dz3R5NfofnA2x1W9umVopewMCTE7on+dXnc+XFcc/lrgl5O3fzz0PX21YlE27iupvPLE56CA9TEh8hTc8ObpgNokJOzfDz+Z45Dmhsl8v5obqVUl/eQNO3+4sjpKUXW5ZzfNxC8N0JvhWDwQ5oNNEQXTciD9Sr4Iuk57nY5th7w0SGDNKbFNONiSlxf/gkKVGDAYYZhgIamYwmJLNINCnUQINjWspqoChVhEHoBIqBBalQ7B7Z9Qw56+cTWnKSH/c6s/paKfvZ+LWy7yo+qnad7B/sg8T3w7yU+Ky8mi3b3NE2Tp+ojA/OTwfzjwfHqdskox6crqmmmU5eNQyViKxnaDyyEIi4TsN1/ANn+vuj+zXlR2jNsw56OZaEb2pT5Ccho9H5NbeojzG/G43j17Bdas8RweJgPdPtpzv27W3fce8GCpSwDtNhQtJ1bE0ZrxJH19SV4x+crbN9cHldcT/yFV21p2m/6ni8ntiT4WO8ThstLfqms1vxkezJV8SUyvpx6sLtuViCqNeN+gXCNrW16y0iz5vSP9EVrUv7BCCDJpLdG9koyxrPc8liOU2Tj3O44WUcogt9Im2BntHPL0uwCy+detR5oJN4Aj6HfI/7i9H8VQMyzsJl13E8HnpNBEUiU5vHITqvx6XENYKxXZc3KXimxvVVSwqjE6ARjbUJqmDT3RHWrtKbpsGaSik4jUroVRNVqdnYzpW0f0hiN24zN3MwNrVRatS0YxEzZUUWeb+FP9hl8pYMZrogSxMWoqUbROAhP/oMI0AIS8gKAi06UV9n9aDe+Kx7uUHe/HKOvs7cLu+nVd9c/dH4X/OHff3mRlGhhSBAkS4vKpzzNqmcAFEHJ9xtKfgybN131XvmdWo6pTM4ydpRdyafF7/+Tj990N5Y1aVQv5setTK4yic1b9tJuaLC1MS6zE4tpywcx4/88qdyf3uDfqnfJ3+o9Pfv4Hvj0WFXUKYAySQaz3IwShSYQ/ooB5js43UVXe6ahGoiJti8bK+BvLkedy2xUXGx5+RtORVpreERjcdjDRi/2d/2cKuXviasHtLxlnDT+2kxWHIKY6pIzcoaXoPMNXPeux9yVq8WFzxWVIOvqGZ/caymR+d4nx2xAmvR6vHZ+qvaiJ2UM2zZjv0mGZDJOpNMkYzWc8C7XazrvfBK/HBdfEqxZng/mirOOTiIYcPRoi18Js2i23jeqLs9npOgLqgz7zOP9jnGQnRY7D0BFXf1Lwxvyd/eYRYjovEmaIV4oTsmXaqReyjkilt5tEFUz96r77TGyylCuK1qkSKRSHN5WJqb3bngYZVXrNpOSn4GnaZvWw6EM2HekuUe0tZFPfdx7qUB0dhqV649Pe4b9RAKdH3OUawwATuTIABOBZuAXDkHe4aUGn0Z4o1BMHAwK0EKqGAwGiwGqSiQsgQS9PWzcdy/7ob7mb1TbIL5Tt2n7/0KOiRq7R+P72pWuVMhSEEVAzYYTJxFvQgDFKd1jhS9kGb5vAiihRdFGT5alxRIY8CJjPYoVtdvEWZFYxTViCm1fm5qqFesAYQyLWV27d1u/8pEjQvN9fkLb1/jkq/7en3vwvdK7fXJdJw4NeXqUSjmCoaKI1og5V27Br9qHDc/01b/HRIoGJfxmlS38XQ1/h1Iy69sN/vrRwpP+VAItEbxukxclJt7mbHirWWEcVpqPFuc82O6bSQmmUO0ONZsPHmYY2VjN9iy0jps+3Z2fBrCah96P/Y9drwm+cidi+dlGbFQMTHKDPeS0zS1Rkcok3GAUuMTz5XEGTqX/XltPn9ur+Ecqcbj+LWHisOtrvc8u6JqcZXu9g3jKUTXw8/1YXfF+mgLX4GRSBIwx7Mn4W44hmnBpoeT26C9db491WmeW846oKKqGlcuYu1y4zhRMOW0LM4DHtICTLP24bFstpc7McusAPcQw7VK0bHpbuFS816ikWFu9dZaAOyDjau1xf7aMIkhPszvlWqCnbJ6+rWSV61MUllxH5vTxIQVAwxGAIMmWRIBIEfASrVwTmIG3SSrAGn7tAJdxgwIxGJQCCmAYBFWPu75Ore72smd3UHHyc+O13pfbquzer9YL6L3OBObEBnNLANLmcSCIEQkNOhglFwyLUn2440phN3Pi4q2sRnPnECk7UUPDY/XX079T/n0GzI0S0dS79q+DANnsWtZG15871k8Q4756+otNX+/6R9gRXws/HEelJHPgxk3c+o2xtRWAWMVYGFCUVDH+TZCPh8ZGghWqI6/spu5CH6RbC8GzoyOJ5+OaV7OMVEYR8b88nW5stquWtv5hbYKVYpOWWjtLn6orxzP8Jfpx+rwrjhVMAx6xtHpzFtuvU1X4GMxG3ZZMeIu52nYybFu4/nZ0zi7qlSYnClQPTwMDpYqhGaGLhSn4Qp4iC5Wwj5owvu5m8tpJnsYoOsLtObcHmsvAnTAQdra3D8V6DYFmBdMY9hsu5WeF0cXuoqhs4Pt0ZwpS0yuspvbR/P6x+MvT/2Cu08a8kr+9m7NYX5iltTqfAqMSrDmUHMoan7r3TF34AlwynW0GrCgdhERxY6UHVZguSNqdmpY1QsiIYwuKc0k3ywX+FIaE+vK9BC1E14N17Gn9xorMI2v2OEs2j3l1m3Z5jI/haswbaW9H40xA7INrTkBUC8YKjRKBVtBECt5iAqwkAKDiQdRoAhbuXf/91eSGfQG5NZh1cN1L58909kzNlksQRgPJnZKLAIkBGuY8WbzygGg5wLgoOENyUlnQYzkWjAdK28FARIUiRBmmy8+7TvF2ta1ub9M9CVM7NizzNXalpekjZSyQKWVmjaOpyXNfI7jsI5bU/CO7bd87aUlxJrIuxD9TMnGLk9gQFAkqOiEOcY6Y4yDfZvQpNFpDDPOdOx4rNzLX4Yw9tWQZcxz9wAqTObd70BE157jCXDtmJ2jzFSww5PoChSXwuE7PmdfS6wbOKMInVHh+5ncurjdNjBJ2SU9fVykcH4hvi1Jhx+/KEzPUikmoy91nOa7Ndlm+HXPn7Tnj2KL8C5PKkjpoia9lq6Td6PGz6Z98/rEry51Vazejs2sqzvQDxaTurTbR+dmbbY3lHk213C0UBn0IYwAuin2lz48OtDx7A8Rg6P+m81uPfS1HE61xZzX+lLcX0VOuy66nBRF1g0sTaaA4xF3f0YqmOVTUYkIxdgOh5TKmqlIw0bXyTDKPo2wvmocOctuzfr38DOLiZ0VXcUSL1Bgnq7jThyn+Tr2imSFHoemKSUHd4kw9nSrvq8wSUQAboGFZmuXRBrQnpuxUA2ivnUI7GuwMth4j8mVOxaBdAELHlfebf4rcTT3soEkqgfLa+QaFu2SdhTpgpdY1PsMtBDwKrSCmcl3B8xCABh5bIkjWWb99vNBtT3XG3Lmiavmo6scyWgDnEWRi9XBntMXn8hh6qIsTZvcOH+Y7VeY2y2LZMNurt6phe2sxcvGr/Pi9iOri5XHJ6pNyURCiL0ZCKFywjxDQ0GgEYNN8bg4shJJAsalEaORrdDKcTGRR0s/TMW6jdlxVnub71Z35YA9zbtGpbGxvCK4AKxv7Ey1qHehC+t1dL3g6LCRHddjffY+rVMw+qD7+eMzvdQXKXM5diTcMW3uBiVlJSa7tIw32tcnR+JPE17uY83xeufkJt0gk4Tv9d8uXJ2SyXUG2l6j0egZoKzzBNfQ3cGqQlcNO3T7eDU6LI3teHVY5auTo+7pIGseSiuqiDHGDUgHNjvTQMVJe6FVJDY63vRhxjPpx5+qXH50jK7Pl+w1XiQ1Hd/qMfF+jy4H0z58vODlDjOpJzdqK97CopRX33dK7eAq86ITOc2vUQ6cllOzXCvxpryzUbdvVzQfPX0pr6TKXsgCHxxh9zBXHl5fWqs7obL/5o7Mq2FPo2xW+5638+0seboC8H62rAHkDYwRwggxG9iF+9IAC+RK0/2KRV7G+Wjele/EPf3AgU6UvHiQZVDRQK7AXlpRwDipezqPcksAYPAazHXvwtZ10ZWAeSCNXp27ZD/ic66mmRhTIMdAH5yPzsCfQmZxCrkw2Q1Kkv35Kbx817k8iipKnCv53IZpH9chSmsvvjPHdLvIOdesLbRWSN/VkeqxbfjyZoKPB+q1nQpUq30jo40eR0DCQowK8nhynJhdgqrUMYIJWaSi0/fDR1KRUl4r69BA+AfVWuMrjjSJ6Em4gleihbYcee1e3eQfdTy3i4yMe7sb5RrptMp6vt1ksX9bjIKe/VzjT3Rfua77IuM65VO3T/SJeNl6IDxiipgbvE0bc0ISnp9iRiikT5URuP2EjnfMO85gRrhw0SN1YZpoT9eqDG33Xb3TDItmJTN9HaYUtG82jeUssjkIdSLoQ2CPL3g5OD3C8uBN1TY04AwNG9cMxW6s5m1wnu5cs/3F/POOapwHmN62PstmYF+NrR9dPKfmtNjjvny/cBZDGNCAdbmXXlf9T/fGsezpw4+VTxo4uxWGnhV5iVpM1LSC1r7Abw5R8cZ+ltjgyUP3MCg7Y+0S4DiKhOfUHFj0lHrqb8RN73wm2mKEQOp7Xqo7b416AKaDrKKAYfWIZDpBgZmQwubNrZeeH/38y0D/MPw4KPWBPM5xqamu4EuE1AAKlDqFg64SBdh8iA+FFGaCsh8b87t6rt+GG3Ss6NOc2qf2rT75Yex+sZ1tUUXasQ5VMtuKP52ZQJYkEEpm5SIRPcYaBwnM6PwbsnL/up2XzYphU7gv1778xP95395//KIMeRkKGtvfsbHuyy29vORqF/qhcdatMv1rcDu/MiAjmhwdsvQ9h7j+Aru9SscIbUi4DPNnxgUFO5v6juubiKek+6fmGMw9FqYe6u+MKYNSm/dHQWvR9nO5P+wY6L6qz43S7eHY9bwq14zZPkSu+6ZkQn+Pm8oa0KdmcZjGdolHhQfax8o6JwxP3zzuw9ss8vA73fPKT4Zxp+1ebV+0wL8Yv/vO7p9hkuy4r2zmq3xnUCvPFHgUIDBRJ2SJ6jOOuSPQVEzJTjc4zpXnBWdnDlRtZ7LvctJi7Ts1OV3cv+Q863u3eU3wFHU4xpwblwm6cxVY44+rmr7/x3uMI5RabnjWP8Zehh9nkXL3diT1jsenyxc3eeywDV6p11qmy8oZlguL7hDQNn5VXYpZbgPRm2zOhR30sSZZchMeljn5abphh5x1FqfjNX7EYzB6O/0IK17a03b95XPv07w8vp1XTt276W0AuGR1kGK2q9fai5WLocfrcInAfG5/7tfeP2kcggO14fhXGaoaqL3nFbKGeb/P19pUF7BgAQRK9X/W+8PLVRUfqNBuYzOn6dF60PwOpqXfJU1txP7eFw6aFQJMwVng4sfc99uqP6M68/xpSKIEA3LJbDWrR1selRJTEar7SdZXs4bnnWfsfaiLpZIflW0yJlnA+f3D9uy7Ma08YuHz1Z9lJgOopaqih/IH3Cv7UoIhAowr2V4stxjeu5uMLWhj6Wj2rnSTG3uJPkf3Jemrt95u1T2LOeXQbOawrKMS8LF1g7Ix8THNIjI/7/RDinfExlgYiTq7GZHzTo4GicIIM0nBDLbZTbNH5kecTbJGtsPLPhg1vlfBMKcdlinrwZpibQ/2MX0vFilv0V8/xEben0TH1L9FJVmDyzQq9PJVRxhMJDOiDN0hup2Wc6ZgFU7qdBE0Q+eQW93iP115vkMbFlihd4/Ypd2BQS5a7vzW0HhgGjQGvt+nEdXp49ybs5nSIpidgDgEETEw+t7JuYikqG6UlonbUYTWZ3QBVzUjIx/3/uUyDc8Pm2pT+oInCyzLzYu+M63O5Y6TroWEG6PENCyOS7Fcm4rtxz5wyAtz7fXqwjsBLhui1LN7GvWwHmykM1kpAPT5TGGopg5L7RaJHH3tExNQua9TzNjtjcIDVgEaNECNlO2Ju59zLrFbfax93zjhzZ7O4j7T44Wc/4v5qK9hv2LGM20y+uH+ed4/v//1n/T1tSBaQX5MoSfA7Hnr1g3WTEf6ogp870LNolATpck0B4yCg8/7SRNgmJI4LFjCWvzYIv/u/GH92eXn375vL6zPnz+9cvLDtXr9S/5/5Of/nx/WlKFzCI5tbl6X/DLy2pKXc0tlPCQDogYcm9pUJyyKCqCiAjAUnMa9k8s8gxPQNzuX4RuP35aFG5jIxFQKcpNo56zf4NHanh234lfffcMbrpfU9hHS8rdiZm5XOXbVKDqejWscoZX5tgnbD8M1OGYMrjZQwDlEM9iiG1aRBQdbs1Gr/fMeH8/kvub72kk7Hu1RPCL+4jV56ldMfsFL9DPAY3rpPoy0MR3LbHrX1HaLxDKefh7PWXbrfrwmJg/x0IldROKog5apeM4+0vzzwtdn9/U+9Jq9ZyL0wI5corsoV8IwOCPiVuJUTGK0ORdt+74lGq6UmxmloCoM46Bx2qA05WwPKmyTIb07P3IfjoCBfMex4rPxIu3wikVvDMVpmJO707iWd1LaC6eLT7uHpRIklQvO8tglK6OLtnRisI+aFKckoaPzrI/gZhzdh9X5wmw9LpkNftSpAEUVgLDdlwMghsmY9aGrOxFDH23IzEB+ACZVEPguUlW9DKiYdr2t7s7c0SkoXEDUDq7+dR8/O8dRcz3OKnVdsvxvB3PY2/b+xvvLvQlTE2PzWHrXrNCGwcHQVRv3bqaohOk5DVnhwTsRdrESi71WlIhSundWg+nvG52dcV9//PUL3+90F34du7bRWUqOeQlNIAAujixmajk95v6G5F35r077JE4y9sH3M1M7o6gEEaJgFKQUTXZFH/b9pftkgJgQ6oKQFLjeOMPHGB43lu6Q4YPCa78fXBAWtOaJr0y4F5Nic7Y/1fB4p4n0uqWNnPz4zq8L99RU+Lp789mPzzxO1jkFsY7MYg15sFWzTFilPnHJ/d31D8hO0+VY617jSN3mrhmDtfVzQLaJfTt8LCF9H4hLEa4Ttiv4uPFSOGtTGa5Jtrx2icmbnApdPCbg7WmH41xGs890ROw/4Lkj3TmlOj0pPTy5Qa+I3dCiifeTZzOKQ8mRFhopKgcIcF443UkcUMk4+BQcTVF7iM5MAq1ZC+xjJ6b0QDS8Erj6v3wOaTPdZ0lVBJapNsvItNXHdAMNT8rR1CeOABgkcOzCaHcDOklLpQkKS5cP+CRhjuwiKwnSpvtqa5rZlkMNWBOMIwWgLiGBLZyVUvXGVlQ1c8Xiheh83kEG9ckXTqRS4UWgLZg5/irnt+ZLRmCs/SBaUPDK6/G/zGCTLSJxasBs1u/fPylP2nl5aTO8c6NBcPoz+wdY7FzvXA73ziuR+hHg8agQNeWVkp48Gr1y7fzS6vdFVubWPr7nfAAQSF5xv/2gz3Z/i2qKODOOz4s97wQlu5kWnuGgU0yn6rKeyeRsW+bVt6FHLW3Fa1pwpX4eUQMEQgSou4dtDBmXKXB7ypdSvYZLmK2wRgWiVSRpiKdMBi333DjZf+COr3rjMQoHayZMxEQqhUyw4Xve2eFO+Jj6nl2owvNSvAWnW5y/h/8o8TQklQo5IJ7QqDFt224FlnUx8gKJe+EYfIAXHiYU8ubzQGN6TN0i7evoCA0NW/ia9pEREY4x/TiFp9raR9npg1kuO40juQxne5Su5rBoK4dWC33Jebkvf9reGI4F0aKfAUvx+MW2L34/1S9+QS8iZuJwe8sr83NF50kq29S4edBASXVAizCG5SxyNGVPVGKvvcZ1qqh7B05tyctWktszQ6pSC5SUmnb25Qp+dElrbGqgnAyoxXsJl8N9yItlQ2V9wJNZgHH2dlrVcVDGuQfMtIunl9yyjLy1st8t9Tr+/3YRNU4AmDriDjYWiZxUOHVZKwCspLws2FEjyIhlptT8GI81gIM4q/gd7gGALnBPshqk//l9yuQcbKZYJDszx99fPUORtCixPdE/7Dp9pZxMZI8e2g+53n3hXNZyXa3AA5RO7W1Wrtx0z4+NX8BGL63yc6OvXHfWAbJfpz/59JHfY/Cn/TM+0XriRGFB+lTvfH7pn+64zKpGY/qk8iLxIWLcq3H/cmqKukFNyFZPl2BrPKy9nGOJvRQ0pcKBLNTjYlw0Cjt8vcNclsCaCcKTIRpNqZHbQL9H3wckzNUuqtfnbFtlnhDzBq89pq8VcQkkp4rGucqHx9MZj6Ddk0MMjp8wOuZfGZ8U/WljJJhB5jCttPqcjWgjyotGde3JelmNc9OINAcXxmh13KG+TGO9a2K85ML87Ao99ftT56gt8bG7a0Z6uiG3a/csXmh9RODSsOze22eEEYTCsm0s64OoKPxj9bcn5YGbBxje387dMEudSZAixRjgJHIwMGpQDuVk9B5i9Ben3caWQpDCyCV6EkgHgAJKW6+RaR78o5jrAam1XOuSqH2XaRuynpgwsZVTDyAl7QrqvRYqCpXS6R3nhyH/Cv1SN6tJfbOUwe7EZ007oiSImuN22IeUXePplBirp6UzDoY1ON57pcNYSnWKgQ19n29fNYGm39G03eyhoEw/LehKmDmdyE23mhzVGoI8YAcoEO7sUdpD64AKEmjRlV5/louEShaBmmhC5vt7nvLqHCzfa4+YJZq5vn7xZvpegUxxGrZGNs/N8iSNJhj1LJ2tlz8/1N2bMc/fkr7v3G7e72iE5kABRCSL7X4VW/ty86a3QGvPNsu80ktzFrZfenbH5w/pDDIqVYmuY0EDvN6GE3RBR6JsGeZ232HrW7EfZMYHHLfqV0yhdugr1lGb2TqDBuaSdYdoz6pYFhDQBZchvL24XYdog8MsS3FQzBbADw1nv+a6zWEdJ2G83Mh+oEP4TKgL/vCsgMmQV8S2LZfo9/S4gmmvd3F7qc/e/UL9ZUNiDhwo2kk8Rb/6dzZI6c8y0/VnDgkHz2sMqrkXLyuhu94DzoCYE6EdNRkcv1IPhzflOi3Tk4o0M6HRBL4u14+9x28R5+dhrc48OKjegLvZjxCjwLziMqLSwcOBtvDJKN/ptuqj02pmcgWM4cg5K5GmwMtmVR6GI/UcB40yoCyVhriAe6RyrIsMC9VEpJyXFIBdDC3RViaGqf2p0+0dP9or/u0Grg3GRQ3W0PWzcqpdndb/e8E9pr2LJNMkUklCt/agwwoAWHnjF9xVBwjXVx/qqGFWA4iSsBkAGxjPw2c44KdsL0G5PW/004OM1sPpXU4Yz8ksL3IVinnVHK2kq+NW6g5NTjbp07ffrX8wwMwEKNLnIr6hrc4BLIj24BGIMDbfo6HTsg2YjBorzRjeNE+2XlQLELMMcldV2/2L++Uf3gvXjNoLK9xh5/0cMgoKK/vH2j0uraH+NP1gHjZCoSKNWMGF/3bJ5nHvvJJD0pZGaDQuSQMfFp8uKzEyFkxnBbFPxsQOw4S+eIwK076gn1yTrUH8POy+YFTNq8TqfdCYi7uA7d9Wvep6b5r1No2o11O5CpOSLsY8ZqCsTXDEBI6Kxbxin+HXhVVz18mdneyn0fimqmo9JoTTXN/Y6w/Ht1svEbucN6wjrsHX7NfgxfyV+cvCee9f9+6xly+VwTWnfUo45Y1xVa6IWBhn2HDdK3quq3Df6X3MqUN26xrEp26ciM6Y1ARWYpfbp3Xaa81Eyg5DHseA0uCzHgKUpOPgE31UqAszoAfhsSZdnC0NFW2730CdUWBeXa6WXZyZLmwvl/o9q15V4+J4whgBRSXUiggDGTGPQo36u+VdB5L+fgakyORwc3tJHtXxldzwrYYb3Kvq0OOd6V7iJjQCVZpw8Zey1savtl86qIBYM6/Zx3HlnsODgwFgyQIQXV8czn3FrDCAbBICSOOUDzzWGhaBeJshnAfROvKMJA1McDG1ea/84jiser/UYSJFmTlj9MfLeREBykxNX73DCqwRKt7GU895bBZZwh30kk0c2EA1wZgUHt5MjoVVMmZcZC+PWMSVQir4vtXdGhcQvSCyYUQC4IjRtH560k4fd/Xz0ekF+gOmsHABVS8P8zw/fTvnP28IpGg0oF2SesL4aPnr6JVRMm026cDaqJ1Fv+B6xPMnB5lLQ5BJGGtMwkeFXTBdABjNIsdcd/sijzQaoqNptxYh44yKVUDpt5Vtjkx92D6wY+OtAQvQ7KAGbGDfIt1IZGjzZLvHSJ+yRpy0GvTFn2PXu9yn/pD+81P8ZdLjCqraUz87jAM5uoD3S+znEB0ueARcd2Jb2j+4UoSedjrhHB00KwFXW9iOQ+2gSM6MKBzGmMCw21gt7FZ9JiiQkc5JRLdgMuQ3ajH0iAieJirnppNwA1iqeqV5vnjj5TzNaDgTywX85Tb1pUZ4Xp3zerJyr87Z9yQnidxCESKhmwQbtWLh4eXHrmTEXYe1T/eyXvGS7m6lLj+btSat6EBDXlKYcekTTnq8LBOEOdhWkCWcUudru1/X3gKCDvqpwDYQoBwL+FLeD2zONzauoRgO+brSBRzWvoZhVvvpz2+XVqLNG4fhZJ4Dci5oSFh6QitGWWUVHeTb57jDTIgk1sbx3qRPk1//+FNAs9rQRKN9tN/9/sT+0FbuqS1bLVMmzqfiGww+rTS7Q7Ix2oxJCq/g0C7OHBP2pJSTJ8Ac1+NPn31Dy942OqfltLIqZuYKgrF0vs0X2pP4tga3X0Rux0ko1YSw0/DsDj9GKBgNTTYzMKzuZOliY3/jxi5nZ5WyXzar5Sb3O/PMZ97xbvt/NxhNoOFJKjlfrURA0OS02J5OaPAzWT3ExOKFadDHeZ7+mNzNxmtqQh+1K8bVfVjHzHtf0YDTihZABqFEqxhTNnIjXDPEYI94OfB1/Bl6eRQvMLRHxJfopTJ2v2GdqIN4ZCyKW0RlAwFGosSQj7s4IrdDUrSi0bPsKdDti0PBFgnrcD385TR9kKNq0OnkbRuiC557G+i6mnGeosPzI+6IxFdmUQzIaoDWskHjybxWbjd4tPdz2c2ACOnxZcj5BX/9R6xVXFutyUs1nfD4PIfh64adUI0Z4Kb0LvYRoVsTQEpFxwQO0bLRpmAD+ka7fSzGefplHR/UoxjAFqrm7pNyW3uSORUc5KjQqEFlVybNcD5xkIVfwwFVmmaoFaEACiCgERCggnvTBohs+YotoCJQC4AAAEgQoBQAAAAAILrX+O97+2Rc6TyQMtdqAnxZOyDEHOrF05pfm3czocGtzRXWFjcq7P4wBpUmdqJEhjXcAIkEa08zVBIKTNQnl16mlfkA4v9KDzYLdqGnjglv00BF61JH/RpTx+uXylpqKrUTv/fAUkQPpgxev37zeVSha/HJG8rAZFvEqrn788rtl9z/c6m7OpOVhopqxDDJxpe/Ef6R6t8RtSeFbx9//JR2fb5qe6vXuHoLDMtFAMvnKw9DCaMiBdDwjvv0EWzqGvmg7gd8IfpznOez4xw7qKL57Njj9+TSLqg7zgew+LQqPplqFuCuLWlz8B6yEI6m86pwKFqcsQP2GpXJK/iY2K+qSwml1tfeCowkdug1+BTH4tL3uKmoc3RMQdJZ3yDFSup6JscTwpKjvTvUc/TVMUnHzoJqbucMlVW23mCxHE5fS7TTdXK+YKvqkKL5JyecnJpPIE+l3ac2i0naAYdTE9VpgIHFlPVVezb0xa/dZ+LumMcz+jywBMK6kYoobTPzVhhxGjbsVtskfnDA86T4DDIbpeSoDeRJsQZty7SqNlDL0aot5Qe6PQ5xgJFBfx5c77iuhfE6qWCO0fGIQ2JTLZaSDWBA3AEE0TItAAoVJEIJVClLQBSKQUWpAHRABwhQAAcguOP+iuY++hkaGFp8FWmoXxyWbzIFZpEVPZwe1Zqn1e6xxyEdyCB65lIWxYaCMyAN4qSu4Dr9aOssKfBVbsM3YqdSPhqLZsTZzus8j3OWrqPWWmXNN9+dCGvP3j9zGvduacen3sC1h6wwR00Emtlq2Ci3r4+fS0dnJ5rGstVaHnnruetFze3avXTHnVaxQt1KgoyYJIPLzYVbUcjJzFiTe/E3MLzoRp35ej4v7YLUK5/W3110RaoHUCG9oXEDH2HHlEXHq3LZ8mWumc4JvVrqmfgUvNl+B9lfX3qK2xhuy0NM8kNGK5NIpmVyH3zhuCecp+bI0ks+YuqC9cw1dHp4oI4Uss/JrJ9Jb5MiXIT7bWXdkkdMvBIu6t7ipF+JKIK4ToiPUD8YR3h4XSwBPQcq54hg+NhMxJJdX74n+YgVIVnUufKI6vST/TzJIX1BDQoBV4sH6YFkNCEXCx/fG8nTX7QoU7GaYHHx1CyuGe5ONszX9935Hc68tZ93340DE8rSTPYkWGrdEcAuMLJ1tao6Vq8onJMTe+RA6+cum/L5E2gltgCsEEXWjTRzxh93EIqP6PThca+REWfJASd3EwUjDV3TknzRJgKGlGCBlJZxN0A8SMs6j73DtxQtnFIIXrFAvfCxIACokpaAACc6GvgT76H4vEFNtApsO1XwuIKX9qSRRaspK7X4o/gfikV7M8w9BKgouJlYVQBdlETW6PBorGC74eY9ZdV9FTCIZ+bTdXuSIbxOvJN8gHdHOLqZetXqQFIacBbmG16/Cb2ZHrrmg9Cuc2zLuywYe33923gXHgJ5rqSsWhbiPuzjpfjUQJOBShmEB2IAogJNmCMmKoZKKukzzgo2+pIYSUHPMWfACs+ejt/pzSvPUgMkplI6I0xG+SK/B6/2T1MVylyGys6GsR65udvmuLMmlsoL1iPLFJXJQQGpcLCZjGQ85Fe5Sk4b+MGckx/Pbr/Yi7AVaiQlTh8YPjwWCk+5wlpxZP6EnqT7QADPk2cHTi9TDh9pclh/Dagz8fnIRa6AX5CHn28Hxv0ia8Gi31XvdTzqTNHYi3ScxrTLljBF1oBjKh+W9j26PFIR0ypLGBU7Qb8zbrVAKGJKen0eWIoQmaTYT7/uZv5S//Fn81LYdWO8a7teiQtHTjxatZ34hJ5HsyVHdMz7jA/3PwN3xEXyLE7i/VUOGh6acE2CogwK63UB5M3aacVPlWVgASdFq0VQS2TT7ltGyYzVGKAANItAJUElGoMGNUy8L3OSIwJjpDJqS2XCKFUhFOPghgP3wPitnmHDMOEy5Mh65cmwYA2M7crqqolzoiCJfPHy6zaLzXt/MJ1uSFCiRYvz6knXUhIjhvhZ+r30OXVnnNN13iW2FhByrZkcXl7b5+QGxnnK8Ds9tzZ7QGogMKCozXMGGr3d6L5yOX3U1GMFQhCRYTzq+dngc4jfhJ29bUMCLrmfdBHv5rYUhtV06goRGEmkFMGyWLZK+Ca7eZaQ8iJHAwlBhOCctAB4iXn89vmJpzN2JGWyWRyNCDK6F7NfZqp7VT37kZanETrOgATPYlY25vZx3Z9yBX3rBUweM2RoUISSArjwFkQqJXk5PkayQiQH0bGYS++ZnNBKGvbRKlvfge4AbbmE4qrsMRKvVoc0sqdrFJqiWkQFv2NqtN3zkxTPk7ooARNW7EuSWkabKGzo47tDD2jmepTO+jxDdvLkuyV6DV5EBKXlVBR6sA1E5IA6Cr/Eaw0tDLFOZJw0rTUwESBe7QK61K/vQglfAiKhFlnDrMzQR9FGZBA9m56uVckJW0nbdCthkbs8X/TMXZww1G7QdXrQeXewFkQkTNs0oLC3NN+5V5VIlgEQoFOzCn65ZuwEc8AcDh2NgNFNMTLSApFhvWK9alqOp6ytTHUGGOjgdz22W62rfdOtBupWEYpd6nvA77kOIlVQza5nuK4hBqbObfVxODh9OI61wwLASBpQDrCV37HpDVoZJRjnZ9rptBVrdQUH+clW+DIVUo7cyD5lmwe+8Ci8/Sktd1dmE+IxsZNSJsNkzMihS0xhdaSFdMW9X0tSlPJOC4CRSLlh2LI+zfZLnv+jdZpLdfEM9jTOH8eyZpkzFuFZecCiGLJJKoJlAUa0GoNHRpqhyUBACYXBQgoABWS+st6d25EGSTlxc+GCMDhtlRxjfxGlHk451LKNU3Gvtos+7+Cc08nsNvf3l4TEOQaPkqMBXqkR0lBgjAPWUTGyZcrg0y0Tyh41X6T5n1fH1A5bsSDvi1HnMQ63GZEOdjJLncnJUexC9TwE6rPFE5zI+M5IpDwgnLCd2Md3KK+mmr71BhRjfH3R7uNter3fHB/U516XuRu2S9JF0hCt0M6nEofK6QWnQJArk2Yd+QInLNNLs5PtCdUmZZVi+6x7NjG5+bgg+wvqIAC/4JqD/Ajn3tBFvbUOFUcYYYZDEAjE490+VvQl+OLqOtlNfqktJwDTthUECBHAcbn8ZLbu8ur714DkmvWcUw1nEWKbvkx3e1Nj6bZKbwsgWlZn9s7drrQv+LHr8277frjmdHWUme+FHlb2u965eGzndqW7KSBSePyYQW6PZ/Y8lINOYcKiqqBHsaqUCkwxw7Ryb6wMuGqyM+NNLfC0u/Ozf3g/p9QCUiCBDroHtZvOo8INfEEFfqSzYNNQoKcnHtSem9xhg+GpC5tVCyyQQPGcIEODovrNe9pGMwAvSAxe970HzVbpLuV2pkIHoH1ELM6a+eveFyePtOfx4Y+vThfTJ64CSRIEksQ4uY0VR6SE0ilTqFifcAyOJwb3oUeiOQR4CC+w6NDvspll3V0kt+5oWthLcaHxfmQdh7Wq1WbbeGvzbjEo4i3aMXu7Trhe97Z8WK9p3d4HzvSsdqY1TqlGsQJ2BD+PoMC8Xywrx2HneMVm+nmKq3T8b+D2L7EVoOmGi6mXVl/bdZtTCBNOjIXHhHZxXtPrlN/w33SdCtQGW79s9s07tqGN1IZVTsJM93hPkuKo9Nw+Ol5XvbWpT1xEeaCpYTOHdPsqFdmHmHzSKnNVYZ+Jiy0VPwsnXOVE80zMqTCwlgK87YXjCpmIrbKv2fv42LutO58Dk6M80a1eB8NDswOjotR7MQX08A1wEwZovid+596Bm2LV3hc451wnJGQuO11DrzdRgxLl2fxKPy8fZdbe/3fsNhkGvoh3nE3atDvjyXuJi3twdvI4r7Vu5/4Y3WC36/fdOgfuVsY4yrLbVpa5x74O+d27+yf7YVrTrl0yD/q+Kb9z/fmAnD26BNVXhyd3asxWeiUyoY1cjd/fe//T19bXKSZVvmymYDFZmoCmVVUpAr6e/RKChqIhiqLgA6oLlEvdB/mE1+wz9lz7mk14xCJTovdEtOnQ5c2LZ/MhrxDX5UQ6Publ2NfpF04xaLXrXN5T0Xx6hHtdmUz+yqvBRqtIG0GlHp9x/HJflv06vKeI07b2x5sRkQlCU7j2oMBw4LkKLbQ4WWQHgpksl8hvBk0BWOABwCMguUVFYZv8Zr/qUYH6SJvUYT09cAXFHFyI6Vpj4MEK1/xFn73T2uw3nS3r6XOmcZVxdkvzLbkmjffkK2j5m5gfTHJxnmkeTQZfUcH247vEqrUYTSt89/T4Twv+lxtc/X7RdrLVKKN23a4H/Z+bnlFHIsWc6bpZJT+TTnG5hHK6P3E7k8Z8lcnmATReN6vHcC57jOd0KTOb7dup93z2nKvfPkaQdWbHAu5Y79mH72qhC3PzOK+z642MQwykQ+T6kIOK4OCwLZEmZpk4wFGV60nrYWrd7SObBtkvP7rmDqQic3YSfF7nOQvXm4eNRXQ/Zsj06KhrxLA492noPXh7v6EflX+63j18nnZcy/nqrq9cc/E3/ymQRQGgAADhXMgFACzAHwAvu35s8V9CfwP/bSfPvwyHha4/6bdr2X0c/sLwMw/OlLRALfG/cvJ/Pgqt+9YyQslWUkVQtGItMnX6b2FIwX/m3/7NSIUiu3JnUvSpaFhN5hRhSK0WAh3RQXlkwQ7QFiCsQPQ2ySy+oCuTR0ZIGZRI6tcamAisdLdxxh51fDZjeAhcdsG57YybvGa1KrZpTmoQlaLr60j1icLMopPVYNpvZqNdekbWHq1zZTtWBIoe4Ew4GB3YOjkn3rTve2d6C9AnD8t4iGy6P8w9PFxXKQrBtOdlGKQLNKHdhYmhR4SDAB50EgmIBCgFuupkP/zV7fQx3/kXu92Vx2XSAuyO9bA0qbvESOc0JOmEMsvLGh/oLygdONZ59rUxG1OQFRE53nvceYQ5uuZH3XU3iTYCR2Ci3GZM211uX1L7br7YulYyk6jo+GpbuxaFl0/i5D1wNNtcNsztc16LyeiK6R95Q6pffA6+83/et+dRZeLpy+PD7a/Xqudddn/2YgDPT/Tscuh2+txjOfrI3TU36YLZJM6y9FnqfJ3x6ngw4ni99txb2Ld7vfEZ7ba5Ki/7882r69fs3/7Pv//v8o0n/8Hl5/3zWf8G7/TfUo/GnXK52bbGvlFz23Hptqef/Llv/vz5bz+vd72vx/vH/r6ff3y66Xm29+f9S62Pbf16w233Nn/nyDCaILWXci12Q7gZd/uRorXUhUAMaiPUqOvbukk18t6xf3JFbfsN4j1Vu3VW8tqpTO29QHGjsOtVq2sKwmgR+zWvO90kGwXQGvFgL8Ln1tuXk28ze3KT21JOF6GhoFMJImaWN+MRBVgoEq2vcfHWJRfAelljjp1taWsNwFIHNdpGSZrAdq6wX/LzcseIW3spxj32vrTsZUrLkGbw8Jwij/5VxBaSEpxhmGaDDQKUdFiHwlz2SDQhhwiiKiuwRCkjpCktHI/fHNy/4M0LInMnsYzy4EBjsyE47U4tirNlUHRgqN9ZRlAhQFknP9hljqeLLfVhkCMEWqi0FxfugVjVC7/nHERTZk1MDadxMicpMH44HOK3hOf66yUrT/3ZTPyawrkxPnxCfM2bOv5wMbrf+v9p/vAb7NlRo9F0z1yXMLcLzDLGeWd+92Cnds/chjFsnS2909ty8cEP//QX+E/APYWBf/TsV04f2RzP0fLdH9eRrtfcpJDhzTwo1/zz+ctv88pN4L/+io0SrXHgCiKoMGwlflnKIkqMgRMbF8Yvnih7fAWrF7dwSDgFWBoyWNriePg2szQnaSpo6qFMRjiNLF4qgDr9dU1r3PG1Ilk7m9ebZ0yT1IWUffExczcdrFIr1QOBFafpq7FWoywClb1Rzusf3X6oF541b3+dnx3JOQAXsSDtzTWw0/EUkyWDtVeUwp3cSqMzNVQUYJwjI55TrmE5uQUOwTI+7wVaj+mkp9j48LlZZSanvXeZ2/tRuQ8xJ04uQ3fNqycnjIYBdQpbo2sGyNXjrCO7czOK5khJckElSECoVSLQSiPopD98fDUucIcdXmBM8i5yzi0RKiZlHeE72D0CiUkU7b40RV14aaHiWh72e9646HzG80BpgZezI/KlbrcQrdUGIwc97eMs4q7uU22H4yRfzMNw8rmgzDY8CycNi9a2wToRYvLCXPTERVNN/drB16NfJ+1jb6ffbrpjbpOrDz7+0+/wb4H7Cv/w8ffPR/ZYjupRXDOrMmjfDHUFtVOPu2Y2e+uo41WyoXU2pA//PwMbw8R8ev72L/J5UvIuG5sMucLUV0gkyooGvIZBCHiKEDbdrCHQjgSATyoM9wCB1nKK2u904nGJWfNLW6M0lmKkzkYASgcFXecJJvRkWkO/3ySLvnVTznlw8kZMdlkOaizfeYKssjow0V2Q+zvtNmirBqHozuX75+SnWuqJJvbEDLfRV0IjSqCNALFNrwUgjD5Ve03qiml5mZ58DaaGWndkkbH4YDsS89D42vupFV90uH87WrJzotNTfPyep8wwkdkoS9jj4f3bEzC20Hu9aeMyw7gBhXVaam0BEhfdWZy49X6eQTZhIdGyEBgpEilWCAU3WrKcHobuGtnqzfkeGWJ6FT9oup1mt7WoRwyQhkSc6dRPHg2M9+AZ87Metmv4sQ/a+FoW/TQu87lS8Y9bKhYHJXKOHre/ZG0+AiaVsfDQO66OscYxOBaOTc8Z3YF2001da8xhcffh94D/z18WFPBf/vBf/pdHbz3Jc4RrsoEVGWRVV0w/DLYzHalaMv20gpxSi0ilCKhAIbVNNAUsHrDZlLpQIEjbC/9FnBYXQ0lNw1JLlyJKYTzKxuIdxnIBwiB4WAlo/KqY3+bEAe8QBg5LhBLZa/L4zdvQaTQXEaYz6ozr6jm+rEqZcehallQVda35keH8Pvny9eb5fl3M7qfO2ZlFNlm24TzzSbN3FbVwrV+r4zzBWiSObbldAV7mqm58XR/wKk6kqdq0jJK8xcvX5pn6Sml1qSqFZgY3HzXBs+2XGTldp+xc/QbbTkiJp1zbDk907j+o/0C4eNxx6fiXfkTk7FweDx5DulF+fvO/PN9qzxY30BJxNMlg3dpQdnawpsK1d7w37djTNHRwyiYULVCDU7CUAMaJHp19vDmBQ59c2ixVcGdyKuVZhYHoMBeqCSLhgGIkIMrPHhaEiXghQvmcvOX+FWy+eBeWW8UEHoT32Do2avuM6UBaO4A+GbRbnBbpHvvVP/ubk/6/f7Irgvx7760/T7EnODUp0coUZQFLZJv7EiUlJMhWtINQJUWECoFyBFKrgxODhZIUSAdAEmgRitXVGpQmBXC1ZpIIxCJboIoKNSM0YrVaVT5NFIw18DJIjo0XAyQSL60Aww4K1g6QG8FowNiGOKPDbUtNnG06Gjhcbi6nUVZRV38zkCQpIsA9WSkjux5Vpw+Kk5u/fbU/3zecG+nFyiSTZSgbM3gCKNaYN/eYOIfxoLENUov9YuC85n5kKOyQzHby85D1gkyQHAG4gV3esGXzxgyvKXZazF4Da0eFctbj8fBEgzWTqjQwwySjcqna/p1g/uvZK4i98Jsb1ziZmEQ4Xz/XLmv7b999+PQc/ngVa6K4ecEI0s581mmdgspg28mjn0tFK6/SNRuTG81SrWQal7oIYodfXl/V2W8frjpmkqKtk4bYkWoZkiu1xA7WlDh9MqXTLBKOE+JAaurld745xh7Pq4u1926f2N3uYv3tnP873+HtvwTwJyDy7zp9vOcPmqYsy57ibI0qq6R2tauMYCVhlqNcMEgAJRES98EEBgYVKQZgsFhgQSMUMQISBhuB1UWAMjgDi6VCrW6MAKU5ShlSTSlNAbBlgBJDJYJcqaFEiWPPlYQrNjSuUPBiWko7QcW0QhIwhEGiQSU+lVrvjQs8fTlE+TuWRmGcDXFLFTHKlBGAMpEc9p7FOHVcVbjKoESfB67JSvYqVJNJUATppsn13nHROSjUM0fN7Y2zQeIYtTU+PAQuhmVcl2MCO5AR5lQWGNlB5zYN1lRYO4gTqUFHiRncVE7t9Bws6GXVWQJw1z0oYK5WjVP/YURe74H/mBIHQPLyEHyvUzSPi+NN6b+tnn9DDEk3I2aBkZR0OY6KjROng2kFGgcuHEIwrRn3jGtoO555htqJpUsyIih+CmNJIwSQjRmUemiIGCGQaLnALBgSPsomHGrix+jzBeDnPxEVfPjj2XS6Tn363nff/qb/2xIp23Km9EhEGdnKpWiFZQ4HRBlKECFa0AEVZQYAQGQABtCcwWiGCGCRA0ADQAIeqKhKSkEAhEpBqFYsCHWFUGgBZ7A2BoGrAYAmAmnok0nDGQFpK0CgI4B2aSRQL5WIpIgsxBRe0IrkIj2FaUcwlk+dDw3z/dqJ42Fo2+YtfXPpfACS5T42QXh99iBzTkJmGaCmbFNHalXmpKqIM3Cdxh6dMnJ3NL6022UXCm0YkwOpSCVhEYpkQvyltm2eHZC6SWylxCPgul/yARjJJZ0iROYI1shaGEQYQ4MHbJWzpjMdXrlThyfFi9PDDCzOu6Y4PFNwbOawN3NjuSwFTlARdf4uU+/l5VLhnV4Gevqws95KH/Xa2uT9AJHv1cZlItTYs8v2/P6cUOLWvn740de04Z4/YJbA7ojnIc+D3sOQeIAtfCkBehjh4rngeTjaDrwSdgqvwE0PAH8BmAAAAAAAgK4/Vu+bvmmtLG+8HYpnbcpOWZRNtb4Eb9mRhEHRMkuQIDoIMwEABkwKgU0SDBCMZpgNyj/xlBtDREEBFNmsoAseRhAwVBgAjRZQhAJWRAUWsAMFrAaBMddRa0QoVhBqUIG1cTUYVWCYULMAQDNARBWWZaFqBbzqnbgQDPDCUtmTUgSDomKjwfbo4/fD2DT62zed8seNQrONbxLIBYC2EjhE+Ocx+59/+s9ff5z/vO801UaAJUxzr30bpiAMFsAMx4Acqd2wPbgxDLCQiECbF8sHwwJAy7gQ8eKeir1zEhdMbSVkqiRPPTKeR/MKwUwzaWbadHvs2dfNTefwkS/gLqSYtuJSTCfByDLf+ffytt75vfXV1W+BHxFWfnP5M+gHL6vwOueu5M6N+68uGTkHCUxIqHNwPh+/Xrv7Ps00etowIbuBIJ085Jg8RS7PLtE1v9wkHk5SGN1wxZJRjmAb7rLX5cpczVzpJflyf3z+e/D/AAAA/vfH77985z8/+b6ZD/l09wGv68PXy31Xu+CCPVu3uYk5zjRaCZixTDYsC5tQgyXIHIZcTTMQC0hLzYh0FCBuV5sGxcxMbJiMbeVtN8uGYROeM2BBk1giJJVR0kSAR7lJhXc5wHxXpVW8BDAWC6wWjVaLIJUmQwAAqMJmqIchDIAFAAQKA51AFhWlUahApSRQAmAQIqgYEVQZISoEiYEOOTRCQ6YQRJAJUKBoAckSKDjQIIUOVHKUeaihK+yqXk5mCEpKZckT1jihaQsG0TcsMSRpVs+dNoXHI0qhNTwGWEhs2xnsrdGOyWsLOnq7Pjp3WR0Gollda52looo1My9RS+3q6usrbNOe1bi4ZNG6YFGZDTdzD7nZQSIF9oopx/FSue6N2refSKqHlqSWEttkk0xKCUIT/t5jnE7TP5x53bY1Q2XL603+AvgJ+O+g8AEHPuDng8+vB3l/wJ+vnz7h0/d7oZf5yF7pha7vXdrmTdrYjCQTAAnBolQQXVABfqm6IO8QEHaBWwx2INHjExPCS2C0HdOFPgJoDHKNkcvANsSGsI3B7MdqsEM1wNYOBCCAEClZ4A+ASQNT4lcfHp7WzRZUbCwWBgBOVKyOFHaREmSQQhZyQMN8SA0N4uBIURDnomJcLQlIEkUFARSMABsUVVEiJIYAg3kfJPI0wv1c6W0YkrZkFM+4NViDDqAg8rZymCEVJPNmOMAM5xBgHYCMyk7L7b6oQalJP+6NpDdgjYgi5QbmfgIKU0IWxBa8ms6t2azN75tRQCXh2hK97gGZiqW09XKCRqo5iJsnEbHLd763VWK2rpxpZsuRBM51XxrtdaIaQY6kxb5jw/T6Efzk+WX1NO2SeJidaGqRbEbO5u0sDtOhvu5r/sLXl3R3HrZZaX8N/2NpSnAyrssRbuqGrnc246q9aLPt/QYkCQBaFJKDukg2nj9UOrFsSIm121C9sbrrkonlBEANq9qb2LWlkK2q0TXsDGkiDXagWdlDgLS0pKVisNZbrDK2gVnreShjEvQqbPlgFlI2Qktdyu8pcAq2VuHhFaXRqYDCAIBqizpS0dgwSJA5uEERdia3wuAVaOhUdTjIkn8RH5dnUCqpFNyDEhEFimREEQeiKFJimIEtsdfuTEgu2s9OJ1dohxx8v77gHDDNlXRPvISqUHyzG0PXMMEFpB5FShoi0Ijq2UETKrHbY457Eyse9Sqk18251GGVRKapdVjE1KiGO08/LZvAWUXKlbEfykHBrZJOlShUSVFuBHBtkktbMEWkYs+reIdiQzqdTp7D93QPKfjg3lGJldA6PejiZfuZnvP242+r3lo0Etgk6VgP6RC77MG5XPPNfP3L/dOjzpnu7901f9++lw4DuitaLjuItFKpQAGw0GK5RSCI5AMICRDgAiEhgKxAAMGCe5KHhgp1YESrwJZGQMytUQgtB3QgrdkgD9aYMmzLSWCL6UxCG6O3b15AZy8NzxMOT5Jgu2HrHSATmIrMPS7/j0IRYDG9oEVrhU5SAAIVRzVUpsqUIViWUS0DiIozd/DTesp5738zYDzCQYh6dbvg93w4R4ijcpRbtQIV1KghcXAUIEI1HKIDrZzmN69zzuT9h887paMFNO6aa2TXkOfoyg3yplMvuogvX/VeriWeQ1MkggNtXhJTGplS8p5cuRWIIyJEc41Iai3kBFnrNkmpGKEN6O64fKrMpJuvAkFo1Ysua/WhYQobNB3oYnTtmSyh0tzVdPXxLQzKJVR2rAJiTsikJCOK7tkldAHkkk02n53xl3f9u8vce+dmvHz+uYuXu7dBUs/u7XOoM3/6+vnv/qF71hzAHrbrg+my9YQIoBmxjXVbAUBKhbIINwAAjj0KgHQEhEwwAEIUoTK81blRABymi0qZDruK3thJyLqEHxKgGKBiGLOYj9HNdw8WNBAw2CDGZK9ZBWAjhrDVnKbpxYLATpJMikb/8v6b/8fyEd7Fi1/cgGESOBUA72gAVTSqUCulW9JhrE3LZGX9yjo9OS/TM7NWDhf18lsEXjdN1OT6rG/C13y8n5/9g1JTCQDVEIKTaESMu8+4lAByOqZx6mGz3B/XudNxmhW5wXvdWNTAdGyP4GEkdGIzzxxty7pXPZ2vYoVC5OAKZ0hz+/2c8b1APdU2crPHe2bQmpdoJDDgNaVWylIRw3a+1ddeb3f+erzXYG6RwxXitZf+vXMsmXSDqKK4bNQzHQEeszpVdvVdv6Xr757XIm+9+j29DHYWYy9CV6URGSHYXHFzZ7xLcDT4tzWeXz/HfZL5b9b//bn964M5jz1tXwdKAQHw+6LBjzNrnVHv7+pMSCDAIIsQihZXqeu9sWvyxQAEg2jE9KOd75bCBQoWrgvAZa5s1irkAhiIXhc2nYP2JJJV1MBmZs3IAtu6WA3fA2GETMVcPevYlrt7tgFwgge7OwZgXk2+wzdkUm17X0zzAB87yom5d7T022GaG3CiTNCgwZQLmyrbkx/9r/89v/9GIhcph/eQdn/UnwMvVpv1C0ymO2h9whKcVcj7fPPedzP0PRX6y4l1KgkYyZYZ5fW7rtWqGesincawnOa9wHXxODerWldpUua4UdAxkXrlrLXhPcKuI5SUjsyf+/9+tbyaJdwN9xQzSDpjNvX5ZEm31kG3TwSndoVfOhnCakmnqTXsEWPcjFNk5KZNYa3zwcqqYqJOblBrKbm+q222BVSxMCYLBctmJGgLi2cWNqwEQuaDHnOmDgD3LIggohFGkDw9JfE331jNbD7PdZ4N9zeP/3ffQdnTf/MLgP8/g59/9X//MzNTWO1QLatAjhMwcIKNO/a6z43yO2HdRKoV/ZjP9PpFnKE96sO37V9+2nE9YhrEm4WilHiEqPHs2skuCaso48QOu5ffufRX/ghtpq/AvNPd5K7mnNTNZyYr29C/efrF2Wk9zQ5D1HZNt7ERtoKY06ZXMDKpxrCEZcpvbHouwGTNUY44rms6VirEbuDXStDPoxQcE1WaG+TmCmV2ku2yhUXKTb3SvRIMR5G1F5w2WaNZToLyqgHcdLFYkQIpydtdKTNLOtUaLANwCJhomISRB404hk/aDwQlcNJNLSKReCQHY87i/dtr9svq/HHuOjfDJbd6dtDVYnQgQBlgVneNgkB6nkSnJQcZ/Il5HwnylSHk4P32iwgiMPD/7OT77Uhf5jc7ESNAA7JVpi5+BGDmRmysPkj73XTz+xGs81tS2l2vX9/hDxAFCnpgGyxYqfGez/c7Nzf3AUN1974+iVpI29l/hZC/z+eb7/6vzwcvr7km3POOVxFQmGBcS/kN0fLFo944N6jeU4ViolL3Tq8x72lPfvjr1/53WvmS8E632Qx3P+Ww2iLXcIlZ0I6Rit9G2FVXTxSszW0M6x4zD40dc2RemGYb9WQbGUKvEPMYPKJXnNlMY2la/Lv/IHpKTJpAArBoTCcHNklX8yADpJe0kqzOABgp2KYt7PUEd+aUCHVALQBTAbmUo1Sr2I1sdzJPXsOKEkASRlvQXm7G8AKTTpYYRI5OvaJNS1dN0Q334huT5hfTz//z37/Tu7/2fzZn1ctWYoD9ZgYm/9Dvh+Nzx4rCzuvqP8HygCAGCoOd2EtNuXIu1AKFLNVOKWuZLkylIhwRqOyANjIVpW1O21NTq7kzrDXGShndpDZSAZ5hDnMUkwCEodEw5uGh9oe/3poFhQ3VPjNh1FrUI3TymVGB1KEifPNOGDO9lE06mHfVjFJ2L/T4bg2lLdloDIKmhug5DneeNLxOX+EtuZaPkfs6PAFHlIkDKU61iV6MnhItgBDVjIBZma3oitTMLPCAIQ0UwpMkbSIIy44SDcms5clN2htDMCM+gM0ZDilXW0uiakVharcO1mrz/ff79azHchPLa5Uw7dRsyIkE1DLeuiWyw/2bczLf+2t/9G/vjb1290EgTYk7Kh58eGPw974VEbag5QIG/8wvMHv0zNsBGkAJAVpRDjUMhhlSucqyuIVJki5zsmSmUg92u7r/0xaeY/GkfE+uJWm0m7wEqejqsnCDiRhU3GKYJW2JGKmBtDIVhhr+tV3mkp0ySVGU4ee484f6g+kUm0ErgZ4spLBC2jtRPuOT4szgfKKi81pOtr93v+ZVBYTZddgTl2I7wmbNznMIDZnKbfT0AlwjCIcCi4QFCGvVpCi4yI5BBhCWDpOYIE2EWhIyaRA4bENRW7yMqFol0RamikgkhMwt1xuBtqJgxKVzdpGmMmLPWqDYbtMR6tdrx+/Vq4luXcXKnUgBFKYBakhDUoc/7s2o53/tf0vK5MItPKgEcCCLEC7AXGEyAAMwceOiRzDJCgBAMv/IbwyAiYXW7F/K2uA3aWgBRSkAMkiQUU5ESkPXMGvu4COoBrM06XO/cIRQ6EDzUhtgJJzZOs/+VdGjtwAuplLMEjxOTj1cQzVIM3mzvQovXODBNQ1HcKDcwmXzXoYd8KdWDcDqZOjkjB8kVWIlyVxsi7HWRMsod7BaWiGOHzKeglW08wqejXpp7cTG0DcXciJ36iNZjWPntWMxWhRphRVSmQVLEhwYZiUniAAIBmUa04B1LS+wFimyicUBCtlIL1v0TKkRYJMpNc+TL2CTMtpgNQSPJGvzKuQ79MxNlkGYbcId7zUymIBU7EwQYw9v9yHtsJabhnEwAveiKvcu8gEIfG/gSm0ABQAkk72lWY8uboC3+C6rea1BDv9EEAABeMeag5oHV5cAEYWoBMNcZlgFv2W80sAail6e8jSjMlRVyJVeKHgPScWGcWehlNIqGy6aUpah+1OklQIkfHjQ8AyQBKmzc+7Fg/Pv0zlLGBo6wx6jM1fU83N3NE4/kOQsNo2YvVxW7ptuU7Via+I8MBv2bFXyDFEjI41JZ5FKXmtqPC9d1OXezTU/gyUtlYiUtv/oR+81VpdmQSMK51opKQcJOhTI3Q+v75xIMBVVIkFbUuG4+MmBtccFj0HTCIBUse5Q5FuWtkfrvFJ7JWMzseWjAB3NTLbZNldMalS/cCXQLqgEwxUTKJgFWZmxTC2SjT+EyAGOXEkopRZW7ldQOcAtWpYyalTOEq4J5A2ru0fAGnSznkE+8AlCiOVAbwz2NdOgOxYG+2RjYNBzbgb7fKMBz1mTBceCD2UChCxDolHDGkilGTw/g3lRZcuZSYa5Bwq1GZ2vmO7WF+WSNUc5ydIYbNfXTOaqxvJqcJusDX7FJCIKSlV80Outs0JYzMHsEXN9uqfsOtcMILko1BPDOQZ/DPXc8o7vPN+T+0eFcYLbjBWIB+qyGmMyWzPV+LiL9jquyXQZiqvxLFwLeJd9QIoo6+zFuJ163/ev92cfJ4M+GMBC01q1C5IYwJa4RICJinXjxhsPUkMMq9077RaEwgLHI6M0VEObB8izlZtSpTlhzXPU4lp9VJIx5erq+9JsBvOrgefa4OTdBFAFtdoDBGABll1zbtf2ejbKicJDm9Id1oUUQO7dHl3tCBFDiJZ6pAA+mG1aWoMqZbwEVzFpFBImABjkUEyQMFlAInCutSIq2nTuv0FG8igmRJgs4oHyCBOikHSKCWICkEqIEGEKxwNAKsUE8dMLm1ouYUIEzQ0AmOQnTJAw6QC4CE4xqRQSJgnwU0SYECGS2ccbngCXGp5ep46lg6hVWSIhcYpK2J26s00FU5SOpi82hCohqopJ/NLnmYY4SQBQ8BZaceb5NVHObtGYE+bkFLoVE+jvrs+8gNEbERsvCg2CArqamWStCGuomeM9kKqomHeal5wCFUe63a+LaZcRzenhBr5p6owlD1DSEbVnv3fDjgSiCha9LBpaEbLvtPK+2JmT5EqcPsrbH6zfWo19Ywr9aI1bKGpi2ceuysqM8P/+9+Ro0/OkTqYdadNlbDtDo7/8OEejmAvwJJI0KUJDVKnRqFFVh+2Ge3f0sIG0X4CwIW2ONjhR0xagr+mzmmTZtCfipS8IEJKhF21ku6cySyPVMbf2Ol4f+2k7LkIMACQAQ1KHqNNYrp+J1YSoYnBgjYlKAFwGDkskD0dJeRQF7mgRxGgAckjHycOJbr1IfhzrJVgCPuKJlGAv55YP8OHklifYF9Ucul8cBjLeijInO7mt69RHFi0X4PLTKqGYoWbrg0RerK48eVkDwyZARr6LzRQBWASUSgQGsg2Xu9PXP3zeaqWw2uo1Sjfaj6woCxasCFPt3aWFqpqTTCFgMV5CKNx+czpNOlFwSIyBJxhcO81AYuosyCZc9drjvAIH8GRbc0O4k8pDcuPqbpkjpb8scYwbd+M940VIuIA+NdCR6aRRvdbbfn/h16u22JJAoGCh1paBD323eu4//8xnhzuYcVqbyDBOcsylzed/37M1Hu3pRaUqtQQJJhWJmVJuFlqVOeOtRswWeiTgjB4QVZHPjFBqur2QKCS0lS52FqCJI2XkfAqGMUbbWAj8h/DFcnx+lypJAACDbODR6ZKYDQwE5hOjtR7k5dmGqGMWd5G/z3vM5aKM0SpuEcAD80VWtc/sDgAebt+1KGKFTW+XAvBsPmFJLdAdBpk4vqcZPKXFtjyjdbk3d6auYFKBC5mhRfa1jQEArpl5NtUKt8lankXcXvCQFrUVeQ+AVACeq4VZoQW5Aki2QXp35nLBvG0ruTXQx8bx9SzODJ3h7cuBx6wbLjfTc1f+sBFiqcRfU89HhN9PCLo/7s/RwHHiMOSgqeSPFjICyqEYC7YFpCSm57rM+SQsP91fua9X7flc06snn3p/UGjKCUen6CHNXQmD6YkTEcmvlHdOLbJAWsGAc52nvSVkNbsNKSMY5wPawHbDJZlJk4fhTK4xwvVH61rqKPzqc+48beuGHy3/BNdKW3s9fllzmOe3kmrv9VybDe8JG6iter63389/ozp1YILpsvGl6c2d7U//ljfmh69/XG597N3ld7i+8/X66f0Vy7LdHT3/+3QNRgZfG2wFErIzW2Y3JWmrDiRSCcW6OpoSidgMiXOmI5AViCqfUpUAq6ZyIWITwiwQ5azdN2mb/ax+nmdljafv+93jBP97bwD4ceBe1vZG/GFnBmBgNzInrzMUMREjk0s4E9fPLmckLyHEROBTYgghIjbNYC0iihDipQM/IIQ410bzztSTj4VCYJ6EZfUm2jgWeC0tCHGqbmMTBwFHcqGuYmXdYIfPCTy7fTYv2glLiKWBELAUm1sbLwrOcJ2IPyPEq+2IrQKbRwO3BrLpDsICQLuoyN6RZrrMb6Yb+iMVKcll3/uEgWfVJlsER2NSwyyWIkXuFpxaTVRCfIWexBQw4tbIb/+OSFiOqeSjQmV3iokycPZ2qEfywATUO5dPrgJ3GoiwODxYMgS9Xjg1lrJHztjYzG5AMi0RsmMX6sOqc6PZiElrIxTSTpn6FRpo9rOeG47unq8eaMxk5M3be5HDMYlsi0i6Eajse/Ji99bFz/b09/8Y9AieeQ40KAHGMGbqOZvnXF77O3L+mXrw009D1Vrdg/gv+f7P+OQJa0+Z/5EDmdM4zgDeoq1WafVaRTlEkB2KNM1Bc0kTt91kDPUMthUktMGO6KQIUkwpGqkTEBWbS72oPuVKu6HgnrR94eaj7fRwOZb//3gD92ulhQjRlCW8CAD0371p2zFpZHYrTf+99kB4GlPOvTyJEBuZwBbEXi7K9fONRRGLGZv+ZxZCfMGL/CWXRrZhVBLAIAO4UR2IGt6dL9NlopFBDGttiL94rn2FMpjHgBgat7yZomUtRiojslwT2RmxlyuAWSbEck1KGaKeA7rj1IwQTZTbfaxFNDNJk1sjYiuQjYtukBCUOJ1XHVSWghtxO08sCyil4UlbDm+uXcN0yM6EkRbmwlolX+D0to9Z6CkplSq+GGZmDKIGcG1pcQY5mueLUxAKvOKk9u7hw5qeBGs0tHCBklxE8CM8F59hZJYOfuwjmvswtK8Q6uTJwUA0gXdg5XUO6zpaXjEDT19rih5uvrQ7zvTyGglrj8wVQPCAclOOhRKaS4i2QLy9Kb6AuXGh/qc0//CPQyfTslExo0oxUSRRj6nyG995nzD1cbsDYomJTd6W/4z5O29/a/FcfLXVG4JVnWiIoq4BmGjUBR1NERsQ0KSRkUUdE4ZRRzAZI2Zgd0oZUiK4gSCSMiQDOLV5+8b3X5fPp1968I0U8wO7OtXyo/tnpC4AAODFXPAFexFC7GxvAr2B5QMtdukaO2kIWEfeXZ/A5ib+AACqEKWBR1oUe/LTzFzPAjCvQaKOMkgySAVKS3TwwAJYaKKRATlzZjB5DQkMp2KgF8AYifCU3WjHrSpgC0faKMYgorwwsAOxOgBDqzXijZa1rxaJDa2vsvyU2ARNW6MWwBcmqhjYwE83IBWA8zrdTcZ5GRkXN5lGUD1L0ethLiGHSWhvyzu/T5pbSQXE59uy+3/d8o9NmpCEOYpNood2HUkkiZCJDZez8FmlWuAGjkebLs2/HZI2vGOcQ7TiOmeFohgSdmLdQVWdHJJE9xiUmDN6KbiK2qLpCHuoiNDjLBkhsGEKFV8WV5HKdHRXmJx9VyIedG4fcUpWTsCn1VZmc0DCSAl6megFA6EcUf/BP0k9vJVuDbPIoUviSIfPP/f5zq505106imHQqgWv2+ndcH5uz37dLH9+02w6KKXN+ZLjlI1MbWNrc2QPxkDQBOyouhFxIt9yHiJVUqDkxQNF3KpbCqWKwA0vhWsvYSuUp+z0WKE3jOve3v8vff7fXL1xccZFaPhKj/oKfcz2FkOI6QCsMTA52IMoAJuAXtPfqhAVfM0yFqoe8T3wSi+KmAQcAMA7s5INdfECZAqQQRewKmIXOe1g4BOJRg5vAA/NQjZoU2UARgGBmHU2GGRdQBsALyVGjGc4Kq2I3/M1S1lMi0Qp0IqYUVCCd8FZ+bCt1XpVI6rpe4Ff3YBGmDppoEvbZilkC9YkOZBIcKbhnEpTDq5BIw8ssDLQvP820V9fGiPZibBS6BkdGgMyBMjH/98UoKIMYRr4LRu9+GfwrmXF6G0jEpZwnmCLQIYxNJkBDuRTJInph2hipURmjIVKRVSIqjhTOuQkIobfGpFt59Y5ah8g2/CankISISEgnTVxmXfRYayf/OVHl7PP6BgDetpT6To4h+83XjrlTc34H/4zpUU2s4KTx6xfAtvEtP/+PL6MewrAJIYYAJBVg0Epfqa7uG9EvV3eliu2zEXzURFllbI0Mwa9VbbNBkYpURRIZD5u4bSRsdVCvfE0YBuQpIUspU3p1pKSFXkVWHG/uTZ3HcSRkcNzDn+wHRtP7k3abAC9dChDAIDnU4toztkNVgPQDBgA+IGCOaBqEbbFYuGFFkVMAOC21ojooKKleAA22ejA+ohy62slgi8QjRwO/FhCVJPheeKohBnNBew1A3A1gFeITYynOKc64mAeRZQuC/PLOvBTFUHsppw9JmrS/wtyKSGD+MJBs9tvyDRdVumAbplKo5TgcEkuokcwSeaiHDTSuOspsF1/IJgwAJlVlHSC8aHBoppDWToMMBkx3Y/0V0vkqvhkoDJl4WE9PvbwlDmprIDLwurie8Yl7ZOTxp1zrnQUeuGUCdG/hNZov+voJuwqBb3K9vTWeRMSUTdWw8KJ5AjAbdlUP7jOJFtGmm0eVvvvPtaPL1MmKZmACniAe9krN8qUaWia+r/75zSraqCThR8JTLIe7X9teemFggsqRBFQBSQr6l2uMCeSQuqRAYOrjTLIqAArWlpLiR0soyRjHgSaoBFuVHmsBGmge0MjBCVSIEuRAKbVG06y/HXu7a/Zfr+31Vd3dGNSeb34a/386T/qfVSA83KpAISB0tXKLs42+LfBdEQXTwhWD4guAwCIDQQpya6IDTnN7rBbtiu26+wS4NnmwDrEzlxwYFwc+1r4AkuaqCVvl2VQimgCno4QUwKFq3xAOBiBwEAL4GXFJsazGrDbg/iWE5+7vFHbZdtN3jA72jUj5hUUMLjqED8MwAITVfT7AviLBgIIcGhIaizTo7FmSZaa0rxm/aAa6KSukaIQphCCvNE98UoYVO2VppAe4qNfr+cXnQyeVeRLCdSkMJ6b8tDTp2Jd9GUBCamg5Mj+MFfapoJcmrYKBIgLNGU9uieMlZ0u3IDXu3Y+6dlyhZ2Zvc0wKBaOHrINMKRO33Je0yIyaQEExBUTIiJNIsobwE0vi8atyteugPd0mVCMXT7WmVC0psCcV0sa7kq5f9b/x//SxDd0UtSkWHM4C+fpPsf76K0GUIjBQQcFgHX69MfLV2o2ndt+onkJDz/FMBIqQihQlSJRzVtTnhUCNkKr2noFRJZkvUEEjceAZRRNqjRXx4MzYMos8cHn38bxt/b6XtvbUbTHeLjZOX3P//e6DilwpQAARcC4JsS3AMBqRCd3AGsAHykdGGiAwAHAcsQePSSAZ5gWgGd70VgY2CoQWwAYuEBmIwpMjBAfAXnXZsRu4N2IrtwGXJB0gBanl0k2g5eJEeVl4LeI2lwbgLGMAYZrj8TcAriEVsSHsbevKoMuuJXPuZkWMnDUOiNPlAR4dxcNFwxKXl4JRwQZejgQpQlVYzgjb8zNKIQTxmkC1lhQlp7OpLP161shNUUJKTnQSeQKV++FQjOn8US7kLiqP/SDdXITc5kFY1jIBlLoBGEkYo3gZfd/OEkHCpQxQAJOTaQ5E06q2CG3uVvkq84iO6iYxbCsQGX/uvgiQL5PaH/ybL5dT9ANZiAngR94ji6HEBsH+5yRtmifVpGtKwrVYSP0n/9vjsa/B/lpt0aqc++z8cvqwecaoQAUjRYpsWCN/BT76wEJKKne9Z3Uex40lJISC9UCqDEg9jQK42qVhjISD2UAi+mzyTrXWs5zP/eqpA0Zc1LWA6555r/23tq/br5Afn+aexvCweMc9uQplyU9jp29JPdSqosMwU8IUZct1CLEWgA+F2Rm8Zo5u+IGTGAAcMnWZCLCr/YHQjzY4IUmxKQGsNREjC1s4QLAhSkwgGrcW+D7VR4hdrAHIXaTa7criqhtq3hvsgDfgAGYMgIGrgbmALwiIV4NPJIORDs/sx3Rxek6Um2xRkow71Ug2lhDRYRoZCiwK6fzeMzTOF4c9XaoC3wWgS7IGlJrrulAom/OU/KISXCH6DyGbCh0SII2kR/S1aRw6vSj6Mx4kd6Zo6LGwgxFSTNdnzkLJayMEJztt9tCYVErydCCrschgk6aO6bDcAJcCnIM9rQwMYVuYnLXQiXDw+GAzggdkxz38hT20+vsIq0lnNnVZ+MSoNrJQDnPH28a6yRr22Fb88JldoxugAQ3FWMTac0hmDRRcwvNZr978h//8yI0EYbIMWPH/OmvBhIpVEAiIkEKqJWs/CR52Z8kFYWi7a95hfE6BlVQDRSbhrEkxa0wzOI807ZXh2xnuYFQ5vGNMqSwGUWnmzUkmgVXZdp5cjzf/cd5fYkXEfT/Z7c+kXOl6e73lnNNSdoudqcAeK97A/Cp6hFCNLNEh3wBnL/tIIZYQmGfWiIzbSBIQeDm9gddCNHI7JQUPHFroZ0xDeA4b/NEERGWTsNEmAb0AiADuDR/pAtRobUmmjg6MCOtJsSv2Yz4E3hrOmhq1wUK937dxPIAPKdWa8OqJTxe5UQRosYmCk7a1RBhesEA4HYqEdBoW/gPUR7XaFZpiFXM4aSozewRVTQj/FmA6SxiV0hiWB1AwjkqrzrhoeRwDx6wIWpNjJ6hKYS53MeYgWJdCgpGwDT1r9EbrmbxxQVlPKdPWSSb4dXMPS/5owVLpQpfOBRFH6ickE3wPLMilCKLgEVspDpyiPptmfdDt2nRPHKaqzUjzznM4JTTJpdUqyGwv6G8rRVwxxG1qsHryvWYlbVCXVTfHJlTRwAdtFZkRWSRGRN93g17Dr97ekZFNwRByVuGngkHKg2JnVSml337rZUNAAYlARrJq2t2R2mWQi5jjaJwmqNZ3QQTlFuzzrSE91rCmwZqHlbBnmHy6jIMokuEZbiU6jS49/7/vILcnnnpz/MZkNZtsaA8Pxe635scXy5lmH5lbd4AAP+aezO6PZGTAhAgAIT0bF7KicCp64w5YMCN3UC8Xq/lMTtoAKA4w9YIBgBpANyd0e28Dc7gkmeYwAs4bjrnfI2KVZWvYZABDOeVPBgo7nPxc/4rZdePEevUlfeAMSfMGXMkAL0Zzumrz4JCAG7P67k/hX4BUubkNWJ3IACZQJ6eis9mr41cOMZsv1vl+e6usslv0GERAABQVXEXvllJGKdQuSZED3SDprRZIS+QlzQEUkSoaL3DP8dCgArGWweNIKs9QRIx2YFkBbBqkuqZqGQUZg5LgD0m51hKNh37apHBIDpZdTTyxCLhoDkbuaSsKDLwKsZpHNEePZqTFLvM0piQLjSJkz5KHLAbEvNiyK88/307+bB0nGQ264LgmLRz7uh1b7zCRYELU4CDUgsxlkOKxhhqLDD7v5snKuo0VdZ3dTc8jwUglUONoIRYfp5u5wCANYspnMa7YVetKUnNQKkkDTAd21VKEITcEBVwY3ALK3KqFNNKFZ1jFQDMSRKBpLOD/ev6K+1CF5CajPjo262+vMyVj+Pbl7VtP9us8LaMFfiK1dtHLxwlFVkgAGnESzMuwACySQVsx2xiAA4iKaQDDm0NPAC4yDFYRll72C5dH9KJ+A7ohc0lhX2oOwZxVPPxLACwinOycLYXs6YuAIm0AeCzDjmVCwQAVJakdewCBG+tNCpScc9wHE4dQZcyK+qWmaM7AgnFovne2tjTLDQy1yUXVFGgigvmCniPSGTmmUD977AJTtXLmJLslnuZQwNfVE1ONXofZJZAUCZiGfzIyQlGKvIMjryhInYZkViYjHjC0MU1W7QzINbgB8+669c1N+3OWLmu6A3NrE+w2CFeTiv5mfxSQANADi2AE0YjQMLY3V1xIE8RLoIMj/hEABJDdL5IZDz8wD46Pw0JQFEFBWCVbrh+rIFABdvRmYQqQVdEHAAZqLaU28oGSeCW7WFKK9i0JjbOAppJuaGQyd3LX7y/9W72BurqoswflvnzO9i5tr/fGPXZVz7+4olsIhD41bBOIIt8cgjg2Nd+cslvCUCAFDw4Bcd08skh0YwAuEgmGTc2jazkk4qhZFLHDwB4MUi7fm+OSlG5TgdSMZJMfnLixp80kgE3yQQwAUgkBT8Oqi5sfpnkk43fAAzitsSn3GasPXQQAFqJ4CVAM84XAMiCQGWZGe+jdT8Gh1Dd22wvKaCSlWBGETGjaffK1yZq8BVLArMESLg4rGjxKZU9Oi6qLDCg0DHR0GnQvEZW9PB/v/k19apDmjaFiT1GCYy1eS/mS6Yd7EFSwJEhUtE5ruVApaRNNSYvBwNtMKQ7UmVykUkOAoROlsXSusYwiGkqu44LmBKJWvHiKPNoNqEiwQZRklTWiiRNpTrkv6YWMpM91QmI2KjYPQQwlLjD9PfsN985n+P1CKrQIgiTRRDfEorJVOnElrYtxxtMBpujcYynwyY6A2JiGmY2N2ZLzEigOomQbAa1kJuEUPqhv7W/deYMuR5dqdrXelS57FgB92f65S0uBTD8iWyIBj2SFnskLyYAA867WqdtrGN2DirIoCf0/g5zg/htbaB75adIurceOVJVHZxoLrPxGI7bTdoCvcrOV8hTxILYUYqY5ZjCvMlRnT1FVCRs7kkMiJISfeT+EQezpBxMkl/I1BZ/XgpZoXK8o5SD1zj433b/FGTOKIt2aI+6NsBOoMHIc3Z0fT/T8HJN4eT74dugYgo2EJIQYM+hVDMTp5OUDYq5hWNlkDDoK1ehR0ocVyogOcXytHFUd3EwlE81gUkF5Ro8vbqmWi0uEqDssMUCfuMNBe3ki/TLxynaJAGFgspCArLgruiWkiShSOHgsspdVaUoQRAkyS6V0Yg2xVJ5QnG1NGclkKRImvQo6Wp98MOfHj7v5cwxEHWN7Rnsu94vtcFMctO7pEdwUoBSgL+T6lXcD6QD//eWFRA23H4bQvACJJ7lKlAZaYbNaqVO19fYVRPZgkhUD8YVk0+Ylmgj7i5tcBW8xAqgix6fKZuKgOrCAkMJOjSRBE4NdESQQGb5lp6HYAJKpWiNu1IPuyq7t4lCX3gafDGyFnp0VlnfENAMoIrN9AXqDPCD85g85c5R7bgc/9R8tH/lMJmuHKQOAXIFLXWXwX1mdXf4ysrEclXii/SoPkgf0Z/oq6xFmyuxCivgaxKIg4YVoNWP5dF9Jy0gmlAUQFSCSl4aagNaMFhVB9PjHFoBaqrUBATnIEsUCM3DM5ZniR1SczJDJEVmQxhcfOab/v3l/9PLKbcu9eHg8vyBNkt7a3WYWfqcfLE12xUg9e9scPsIpWD8q4Bw/NovDD0/34Fff5L++RP454//3y/fv9/p/8r8Sj9p39J+Sv9vrA66nqQwBIwTW12j6vj8gJbRzAL6gTEDgBgy4VQJCBVDUV+ZO8mtHlQ3gPk6J0nRGqJEbuaskMmsCoBSm5xcqrdwWjm6mIH5YOWhqqVIIS2SXbOV2kJ6Ahvkr0wprGImhkNkZvgGNCk5IZooiNgF9FwW6+eR3coHW+Xw1RZ/ZZc9fYlWgTMAgy0szwe92mgWL7X/SA7VjablQn6ABfGmM/XLyZP/eKsKyqVFI79a7y6/BuM8ylZ+TRrrXzVapiyzKtBqYRVkAmLnUsdlL99mjt0UIEUC/D/AQXvLrIRpDK5TOzyUwXFskVVsTFtOVRqGjUDvPyaUqZTX4ayFGw8XVAwOnFd//ff+Fl8f7rc0K9N4IXFFgg/OOltGBVi9PCZxMACgFvg7rCYe9lMw1XWfv0MptvEAv/tXX9teewTKnZbC/1BMVYVakERkQ6TYq3yK7CRqAovqnSQdEoziybGYJmEELoCpkkCGeLyoT6mTCwmi015ElX0nLZHNEhZIj+Qjs4PGQm5mlmA8BX4WOrm7JNFwFrgn+wuDEw5bHrlTazbda08sjSlXRrMoCDpiBzxBpcFEK9ykdDt5r38BtjPBYTf8LfWWPqMLrExP3Rr7m80/D196WX4Vx0LgU34lnEIJDspscxlK94Je+PsK23b7/fF9MM3kB3VXugpmAN1W4VQhRQGaQAxrLXFwy6Xi0EJSWMgU4NyyNFaeDspWl9+339rOH1tRy21u+2GU0mmQ4ab7u3/4v32thS3DXuWc46hBp5Aq7lEVJV7lu8uNgQo4Af6eUN5XiP2b/88f7q+bdninPwDclx6Du5afTC1gJwA4/DK80/ommtNssRETx5yPCy9/lI8YBgE4cF1f+8YTvW+3HDYBgM0s4Fc1pAtPlZSqF1rOw0I9eDZOVNI2/XFVALbIBVju5YkKvF115wY/ZCr6nk/zFtBnpjfkK82ie5nd3lKaW9jXSjRtlp/G1Axfu/iV/jvTsl5AA8H17aIL3ObR+am/9Rlf69mB8mmKxEv7xeK48u2szPQsy9XIJlsGKju9tcnWozDAO/WWNC7cIz9a0Og0V6Yvc+KhXPFD+tmWwlKhVtXTlfItbhAJQBJWiYaYvKT1hEoBJDI5sT+tUoax3feguq7NBooRMzAAFwJzJ1muGDosqqZlklubZz5Nn6udaKS8sGqEKsUEJTl2PPj5dz8cIz+gBSKBCx9p7BccwH83+APBuRCs0lbkAFAA6Dbu/I9FMQPgQ3//+C/fzt3lEdDRtVn51DZOE8wVMcAgdYj2J7m+H/nlvkQAV8h017odM/Pu4X+xEfnYUMDJD6/f+jEPj8/r+0IKAEVuAGiNPknyufsoG7TyvfahnbDQiMX4ejVUqHxfihbjTzqhJVmfiouYuo1bdwl4NBgGVXj3MWp6EoHJpmukIOEuDeFppxq0AYMN997tUVVvx+HUOhz6mlfXrvaZHsNfQ0dkxt+S5YHhlbOldtEqK9uY4ZmqFbvNCOF0WxuYtpkeDa/mi+qT7gP1M1QRl7fTaOoKsQYmnm8fPXZOSyklWAkJptBp8v16dNKCxG0iNDLVUoIIXeNCYSCGhTwGB1YIgVVSluRpCVHNEKcUtc8Jq7TJjK7BcQhLL2Do0FEtP12VAnfBRKXiro/ZThpgNX4MstwcqJPySLB9AVSBn8SdzQmTwX6DCzcm+xc+BbA+2Oxn8sJQynMwDc3vh/JTv1IhFUQVmOBrimYVQZkK/+51X+1Yp/FZhS8Sgnok6yCAT2c98npcB+l8ACAaAABRM+Vp3tEWhPe+SIipjlN2O40Bik63RxlzjAobMlnqh8PyOo24DoJE2TYGh72oVkRl7NR5qqvnvTgLr+qtHDow2VMy24KtFPfTWJuK5RiU5i6nWqRic0FpVTmY6W75sd5TXmtjyxvaJCNPu45cdIhZqByeKU80MB8IYUyhVBstWaGMuaAd2uGhyWKcWoKosHjvwUG7QUAiiV2w6sXBZ89TIYdG3BiWxGQ1TDIkSXd2lJ1WumOIA3EQciEI1FnqWppCuhxBmpW2zNHnU+XM7EnbGG4YGzS1gio391f3n1cbPtnasbPgoUTDMD3S9JgtdjLyZE4aZLK4QEYAiIs7B74NHEfcef8sYJBu2ZbI/gUDAJbAH052il3bGWwoNA4TogWbhQUinsmH21GL5qW9PF+3LE77wW0OOb3c4Wt5LAdP1N872ty/DiPfu0XrDSApPgeAcdhdljfTfUyiUm6FCw29P61IRX1Gu3tce+36FSAQx3zGE0hiEZK68TWJ6Dy0W2akHNfI7pDdHEQilQKRXeox3yYAszWTcg2bU6f9wBkmS8gaFzLjLsNgAvSQYIFUDY3Mjg6eLw9SWOf0W8SktLd7oKqYFMgxlUbPGrZDtu2yyRYKI0kxQcU9bUUBqGNgJb9ynvFxokONEl21mgo/d9c8FlQjBUpZTYsC2REJUgF0K7rPhYyNiFiySAjIpyZVY9s3uFhajPAoijneJLzTgoNGx5sgCVgw6zz50/pqb8U9DK2IOHSuZSxV5OkwUAxeCvGCVbNKMlYPAHyVOy9rzrhzPmDBaCYG+6hm7jui7NDKoWeVyZ5WQDkEUInjzHWhdzSBT6Y3yRl+UWDIi+cS1a061+vL/ZdF7eLWbssA72/dd1q1zDlcOPT2Wj/tfuvqWNeCb7sDAG1iAbCqa1zRO3soa/mJizazwfBSu2qbyO6LnrO29sv6yXLKCwrWyS51dA/lUYl3rZcM6vQBG6FrRno0tMCn0ROle2ui8Z2U7r6RVx//upb4srypCa6QTxyDZ/tOIaZiVKSrRj0zIwpsynWz2JYvoqfcI7f4oq/YQIPpiVDUDtjc4UXTRNtMxFHJli48B/Bq3ZFmPITnp8/eaHfVyKiwUshy+4P2KG01Ey9s3WTVRNB0lNaKVSWLs/Xlz75lR8aMEh60U8fDH1t3rVntipK4BaKg4yiCk85V5G0+4vgK5MBD1un1xT2evh+n9s3z48QHLyiAucpNQtDqV48ZW9iVqAmA5f7t0ekm7lxEmGJS6UUvQuQA4CJIMamrgDBJ5JA0CgAwsbZDAAGs4HIhHjzAiVqVvzQRCNLteZ2PC4M2YpSQDwQIT4gAQYrIsGKKSQEgzUpirWfgQKAANkxXSMCdpGIRc8Kwu6xgkIhBIJpz/8Cn2XH3NNw04oLXoYeMpGBkZLfMCaa1n/Gqp2mNaQGAzRaAIUWYAYb+NY1bds2x5JQ5czRoJCoES1POlOiguom0EL0Rccb1sFRsX5MxKkuWN7loNmad6mhS+CR2HXEOtB//Sz31jOuay24a2OCMK/Wt0to3BC118tA5ISdbVRSbAKkC28kbx8rrOv4c3gNlCiBU4SG4lLDSrIq9FGtWQdmKFyurC/skx8riWpPDCA1MDey2Dza/2e+L5wyCEwVS8eqR762zLgaVBs00SKDJtutAUe4obOPLXUx/+8hEYg88YHlQIo2tWEYJJprVcRkBZZtQAmBs2o0nngwxSztP8dbr2zzSxMqmUGtjnENjGPzIa3bgrgVDOI4joonMGYShCAFIAIY0O+58/WbFnatS0iDOcoFubF9UkigEYA+W4FiEm3j48awdAOwzLcdPAgAASRs4IFwAJygfGp69qDUwV2MKbJCi7HOTm8HG0M44l3pUYm6rqvZmHSeZz+O8YCtzcCeRKN/FGpnLD5+/9fp8Yv6tAkHqAsAgYq74B/jp8odZ61+5N1ju0d//FYcqdbVdczbx+vr8zC0EMBuCFbGp11judF8MuJQo5WRT7j0kV8cZeLSGWEDByqujBrYy13uwST32ArKpyaWKemufIpoSNpGn2t1jUUlbY6kmYgO6RS6MayfOcjwiEx6pFmJxmWLTbCNGA0fqaAfX8Fd3dOQo6wsqxdzOYLAtdDvHlyK/EYefbSsxeL3oFHl92FKCTVOB0WDIqqqEgmT5bJX1NsT5s/xlo5QZjxyFJJcCK30e10wWZpnGarltZoDW2Iui5BWDXaXJDETM4/M23LuPieuinkOFRA6CdwUnzHc0e6YP2/1TnX/Rjy++2JVGNjuOX8OdY9XK7Rz4zGN+zrZpto7v7IEeJDH49m7mcsFuND/ltvbQOsg6MDBjjEkLL7U04JQ2Pd9nUXsrADfNvOxBbGAMJwE+4g5ROzA+BxHlY3V6C+ZlYCSzmcbQ5wNblAeYy2wuCcA12xzmcfNA6oDTEhFitde+uDciy1r5YDXZXcQOMJkwtCs/ZyN7jb5DLfOpbcnn9lI1bipmY7muqfOZ28w5Utds2wGQ2cgDoOAIqauTjbByCYeOBNZz85u/Zq7uopwZ3St17RPRE+eIaBQMSkw3qmHM6IHaT3VQBqQ8eFz7rUOvqxmHVZ9PDcsBj50c9kjwchnKBpJbHJF1oAAUaQRW4Cnbwj9CGyqDw77IMfNXihvw23+6VrtgEWEbZatng+w8lJxsypzcq+9iuuqmPg+DiHWpwuGOdqab6yvqoXTjelPHHE6Wf5q9GjrQUFpmP0lPjs7RQE3jtmEWsa0BTdmQn+XdR+jP+Jt8/vtff/PPv1NXcily0FPuiACnqNzmbKlOdHGb7+111mfRIBEGaxrWkDfd3gM1+GMsyvM8UB9ts2K4aQ14VaNSmCiqo5ock6KgpJP1veEbsDK7SZCv4c6Dugs4e8GoEqIBIUSXvQqcWx0l/pRKvFmrIxy2l1MCd1GHTWBTg1Jz+JgbF2TgnJs+sLyEEDEa7dw6G/g3F3MFs6/zFZ2XiEh8bgBfRMTsbiALBzDM1eKlbvLZ+vh4faWBE987onpdNw6nlUwD25BJ3XgVvdor4xa1JdjHrS8tgSlDmrWLYRl1+T7hd+YbAInJAwCX4VoEke5gDQGKZTcnEQb6wXGvqqcDTqhoBJBhrIlt6hRRQlBUQSJKYA4AB5MSAlEU38PrdJHQgCdQpdbAoQBLGEZZ2dJSEO4IWjCKhI4ZRQIswALiYqpJD9gNE8GYdAVPhjXIYaFCzZUFMp8fcalsuoCDKvkGzyIOpJl8hQSkEV5CukDNwEP2YSysTUjL9BJJEP7p16t7k4sEXN4AQMIYt5LEE5IGIBPRnuhoUf/Ekg3SSgIlEQwAAIHJCgMCJtQ9AulydhnpwIwQPxr+9TPsP37/xX82brHA1ksFK++ZWGXRpEZwzABxZOHjgAKaTrGQkWbFL5UdlosXlnQoKKzAwbzIT6oKKY5MMaz89NKTeTIaB8Dm67gz3HT2mtjNNM2gCVENDDM7UlzOkxljq9sPWdx+bTHE9waD2y5EA9Pt63Qi5uWs3oetBbGRt4l/6wVMQojfGM9PCOgKRIhiUEJt/caRbMUOt/6B2BrIGhcOZAomCG7Gb7k+lnS1Wmx9cSfL/YjiGsBi4vgD6AMrv4iTe/QLbjTD1d7LAomAlNFiZ66U9MM/fD71oyyAnLecF2BydDmnszoTQOrR6gS6TBo9XgJje+155gjr21aaA2YFFhBnolYkMoI6glGoUakJM1EEjkLUUD1OAYMaZn4iK5gxcuC0JST0mXIuzjwlvJg19pFp1GvzIjwh3SPeQylIe1AFe0khjrhl5kQsgchIYVT0LLpqt5ubaB6qxwBezhR0IcMIkYAjOh+wVFo3g0aGjJOlU01WNpB2P7H4l//l5c9/bllGkBIMkggygCVWzpwqoDXOcyxsXdafZpdCTWps6qEpAgSEggVHUh/DozPymJDPyXkozGG3ztv+/OR93W7tcy2ifLXsMKxuWScCrPl4Fzs0EMEAj5vvkUfBDimnrfB+5n69uEisWExXV9kFmnbo6ufVRlJPp2wbM4/hJJYpZ7jOAIKfyJ13xnIKN13tiCkCmLZEzB7SIa0lYisHnNQ7W1GEMkQFfQwmRHRxZwC+jCgLQN0S84ECPHF+5gE/I2o4NAC/xfFXNuBLcuaAwFxEGxdySTqamCUIAQ64vYD74l/F/Ozj6SV/+8lsKXMZ9rf4x1P6pfsbYhGb8vOH7SM+3b3kHTXc3V26yFYYrEsx+0JLWuRR6VzI63wqCyBKIQBH5quLl5hdpGStc7juCchg/1zDcCaEoFhsiwWshChGtOQJ3dSMiEQFiRln1pMHkDJxQdOQoITRMSuAnmQLtKVxB9MJOzGRNNIbgjlplW9bv5ocioZzU8KUzBB2k2vxoJ9onaaXyBzNWTfnjqXP59m0hTeif+Vr6RieL3K9hpJCd5SHmN9IefP9/d7+t/nWLttddE9PN9bHJE4gssI7ILCfH8hjMTZ3/u6mX3cYaQGYNLI29KYQbTZyKz7HJAi7ThIK4ziNLgu6GFwSDGjAIAouWVbgOicv5Zmf0JEoFxAB9sV8vqjXvkzrDjeq21q898T+4RfcSKunydQXa2wVLCwQGq7khzj46Z7/+HS68Zs6ngIDhaeZGKRoThwARxm4YutQH4UYNzhL1VfmdgMYgK9y5+2JIcTMwK2nI2LSArgrnRHvJvdHC+ITQV8gj8HA+ohWbgbgS0TbWrKWzkJ+RbTYEXaSGiQ+xWLkgBfI2JVJ/AgcBmzCUXKMxYIQcE3aEGMYh2jlEgepOBEjUN3dOsVXwK9t/1RLQlmT1qXtjXuOcKoUlZOsUik5POC83NLdxJHnf6bYQi9tGQ9NCqKUD45f+fa/aPuL55cA7EkKwO15/WTeN8vhhB+ynvbtVGPCqnyum9GzD6kONAjzGlgR0hKFgczYSgiNsAvT7Mxigu7RceiDzQSIMFxRHkFhUNCuEh1mA1CW50EuMzTNdNinTjJhdjiZy1blEn4Hzs6fw5sMHm/5y89ZmnZ/lNImyCb2PvXTvn9nTDdVj9nHh+zH/3defpFiZCIIwjCIFqNP+2+yj0/JW5ZMSxM9rd00R/dX1M7s+Vyqo+7VjTb9oNlq9/9RfPv8LBpUbrkhGkVUBRk5OerXiZ5wtODkVDqQ1k22roaEhKZIM8gS2ayho4uNyd02wR2mIDcA9WE+7X2tfr6VtNTFrVOdzS5udXG96lsZWbRkcgUpjzj02GONaZFYp/nyi/XrOJdMVI8xHqGMmEYw8rg35g4PGeaMfGv7uJRT1k71sTxcAtKfxJ2fr1pES47ItVeHiakL4NbWjpg+yf9qQXwN9AF6Ax8gxFTgUGAJIorDAzdzxDrcNSA+AXpjkkwS9tKQ3+1ALAYGBX4GHJYcKCQH2BLxA99hOegi0vDgABgAuUI1vTd5kK1dvazUyV/sr4VfoeT0ZO6+0VrpFJW+bYpemcfshqhAUqBGi5efvh12TWliAwNAmWYKcIEDf1ZWYlUfd4mTcJJs5q/7+/04X/WVzr5oD1cSLl5oAXKZqip17ya5a4izmRnZIWGN8ChmDCdJr6RR9POEffLryX8nmLEs4QkHTibTnBBMk85pQgNuvePzxWNa1x/vf7Qu9uSy1Ybww3Pl8Tp9jfO3izlvjeeiOpr+2+z7adT/jv/yt9Y+D7+PC3+Dpfwlfl9IXfn6GvaT+/Ye30RY1uRabf1lM/NrZsuTeCcMnDYX+rxe9ZDKbq/PtfM93K+6v6hxHoZyl5mo+BOQA+i0yl6/BroeyUluiZNtTmbjFpqwoAEARxnOyFW97Xn3ODuPPfj0cOoLAAU5Yq+Wd+zsPvZLWTpXnhm6Iowy852HUnvuQmdXrFMUcwkYUqWYReZ9Ju1+4RRYVrl0E2ICiUiAF6QzdFrnrFasI3QOO6uODi912wLA13DnCPesi09nxNsD8CQxxNut5LREfAkUUwQ8QhdiSSCd1IJPEM3c1S7LqFzFRVyPj+NVv6yC+jZwmIcEwV8R64CBBhtwPicxBuQSAqYhWlsL4j0gsAE4ZqRZAP0PGKBExBePS2VUP8TnHd+cwuwkcJfZEkXAyaK/8vKnFNYPs0I9IwCUoCt9KLJN+/v5058nPQJwzACQoM6BSILstO0A7Asfa+qaul6SmyV8PTmAZ+NMasWf+1xuZqrkhIMXcwu1Txp8K/WF5ucl+ELyjvxfvhSfbCntvk/e/uHq9OyIa/0SeuO3tHnYXzZ/+5yJ48fvj37530Xtqs9VXe5cPlj3q9bH4+fv1objl5/DsYbP//j0eFvnW+T30fzDzZvdFGfnbLQpOMsLW0XKy+BnZUmeomAF3PE1Gsqe1YNLf02vJbmlYuCtE6vbVvvjcETjvL30cU5Okb88275dSg4yCoC7BJ4uhRAFi1o+Ss/nt3EsjuMPOicvarB1sLSZhKR0WH7+z7PDBc7x9HhlprMdvjfmunMugBba9aJg4QK7nFXIXB/CJ1AVWk437/N1nnMgJ3tKwdJU8qU8/3zK+0uh3/PTB5pC6awdp0leh2gugeDBUGtfD2xGXn3VlhzbuAvb8TwcBeDruHMXV9vlV4eJ7wPwU0Q753PsaY6F/sDpXS2ijEPeDtqGeEcMPIUQixrA6dunnBM4WfUS3wgKt0KGcwpuwMAgBCxD7OUFg6uqtsAAKAFakEsKMLK1RogWzhEc685YA5djyACAhXZOMWsp2d74kOiT/HTmq9g5ya28FmaeBBhjFDD1dAzmnTpERVu/Yi94U17BV8vab//yef2v1/zzACQnIkAI00WIxOth280r+RCnwcuFu/7qQH0FvrvbfHAswUXEuBu+vNb/5qP1UCOlSnF7Cj9PYVHpXUDfzs7N+umnYn7NEJSh/OX/pj/8ydBXgnay/Tb6hx3ZddRuYnrUnM60vHD6J1t5i/c/b/bwibx2cBxHE+rLR2G/TeLuS/UvP6rxA2+GWpYhCUQkFCrGaqVfcHqAMQE6qJiHtXDj3GaK7/aqOlcnVpcvfN5TyouGxnIUl9Nb5Q8k4tf564f6rHN/kgJAJAMACejpoAJEanLo+eAfzs8LX1z9zu6rl3c3y453DPPy8PT9mLcHiuqYI67ljPQwr9P5nDlrDlZoirTQjc/XO0c5jhv9rIaLl2d1i51Ml6r17OO89DxJcjae34Xm/Mn+f5f/4ZW9te3WRY95wRy5zsoP5MD9eLPiT3aJ7e0M7Tiua359WWLCI3nDbDnA13HndQW3nE4Tot6qJMT3wDlmjxwIrECIveyxFlptt10L/BghavmFZqyLoKQqEXvzh65bV582djII8AGZwDW0ITpnu7oiLBhjYmIAuZgUDGxEiPUGsDqxmQDYATFCE5zqWL12jyZUq4QRbl/g+5Qr4k/JNrrduCZtHWkJQ+QqZ7KOBSKtUtxotMnGJ2Vy7nyYrC/MNQCsJgOAGzCSfsb81f6HJ/10wShIeg7GiEhxrXDh7s/yl5eh+JdNOvf0iZunYl3MmUUXKsavm/PT6i174+s5sNfza5OXTcZzsq6ECO7kJ9aul+E/bNHtSvprKll7/geYL98X//6Ld/tpaX4bN13e3k1Q8fTBHYfXP687o6T8oHP6kGKDtkXpR86XgssaYRPDCQptQ42CTeRDn00njJxWVDhrycakI9puqLYkBcvP13x6pRQmEQv3y9P76drv6AXH83u+VjrPD1tDiCBLxjgYIiIcAJKBXLzpspOHNn+yLzfp9eawWWrWtfno50w+LkozYHAW172S9wjOeXX0ZCmcE3qweFloRmfRTj7fsD6rguwW6VhlqiOsddIQcJZm85R87XOf/+//9ZrMF/n0YTyk69prqyxzqe/AgrdaisdQvivw510xM97fOL7o48vTT/rNm5UJ9ixg+MnceWmGXHBzOkz8QG0T7azmQGDYqU6Mj4GBwNo58cTETsGkQzarxCaiCLF8ziNhYAJ7EeJOd/URTRwiSChb63hSNUQRG/Q7lqN9elqnhUcd5ABhYBx20iL8bOLdOAoBCIAalu/4s3lc2Drfv3L2oP/KybbTfZRSmpg6Z0URi5rkQrBCdFrERlXGQ1KHqf/J/Zir97V7p3kWQAiiBKDtYZyA/vX7lU9/F333N/+TT8rDU3Cl/MsSrw6uUg6yz97++TqfjrFw92O/gKek3s2nPXlpoL4y+GBvkqdXq797tgn9MKpXugcO/xj6r3/W5ebf2Pi3fjR+aFmzcAqoSTXAMdWHHV1w7C/H1u7s19L4NE0fvsCr3Oyw8vvn4+Ndyptnaf/ldCP217jWzZXe7nwOdXAkzJiqJkBYvKhheiXahLDoKI7wfDQTnJQ3PkpmoLGmpXgMcWhcwlYkUh4rJ635XzAwTxxf45vBMAgMcoHZuVfHMeuy36IWFA39tg+S37xPv39OBmhTVn73z3geDPm6+f+u9Ca33HvOfO55j1oWQxBxESCTqhZSPV1GqqvpKePLs4kLLjBlOCUbP8yiU/bvl/rjjXi4S9ebUyEiulF7DasTHnYMylehvD31ZzX+dqNAXNeL0fecbgRC4Gu5M9x062jiTeA+XV4AAUtyJ2vEOvgFXuAIvjczm6EGJf8KHwDZa3MTbxdAggKB8zSah4FHlqgIuOUFHAlw19T5BeWINcBBnD7DVrEAfAC8hmhqJwDwaxMvj0MIoWwqiw9l4yx/AttftDgpDOt5Wbd5OtczEPw8FSI+pU1p6FlWtBJkaqJtSJfFNG7+em0m/5iuI3oDSCIQAB4q+JOdz5lc/2LtJ+Xfe2R+g7rs5qlK+VDz9TR35hny09F9hvyu8I9GzxNhKuUFv4HkuzROJ8uc+xHKe+vh7ERoHU5SZ/RSzIa8tsZB9c3iGH9YkdlO37eX759b///e//8tszqunyafPlW5P3ck8mVfxx87ea2WxBbjaovCpHcPHNFCn9PRA/icLDYl52J4pvx2+JXIxUmBDhzJhv1RxyUblrDTheZEuRGjcbIBrg5tNH/MHrox4Yo7/7y6c7eQj/LadNYoSElmEZ2YcrNuobm/okiYvAn1dicb6CKq6OuQk22+5i9CQly5FZiF2m3H5WXZEYUoRchXKqG57TGwoBo7Frrexh70SZ0ltzx/nfviBgh8LewHPOEQOvfjNNGVs8gX/4fdraV++3O2/QHnd9dHPZV+2N/JurDA13DnIvKAG89eE1OWrQQFiFO8uhUYU8ikcGuaJq5gqPwxcCat/g+rsBAG4APyut9ZzU26Tj8gxNQ4WuYmCcCI9VjKI1YE4Eo6ZjdHA06BDZo5al590XP35BjeZbcbYPuasa4vctqQVAEU97BCe6yw61HHlbwMUjROVq6H37vmOz8IgDQAPBtdAJXLpnxC+vMNrh8SW1f9f6LvKNQblz7lp3eGvQyOPHlaSRw8rkye6b3BCvj68/n9z1JZY0xROw9F23TyY/XhD0EH7JP34zwvRVlrYnT6MXv/v+XtbVgfqS66ns2lxT/+/aVjDqJSXV9sJQh7Bk2Uup1tQsnAIvnYGOLc9Kwn08gyn44m5hRjIxNyLhUbU0RLqqvZ0oRIsYCOEyFdDMo7D8KRKii7385na4tkbAmKqFoCeQZox0rpZC/UzJV455q5kAyyYDBjNbETG+bMyF5Uf+Y/XsTFwYJiMSjDxOLn6HMwJ0tKGcIhBtCuNIGyXq3DdLsqpZbS0iQZcLbOCibDVGTIxsZ8HYF31k9BSEhAgxBu4gaqsrxQ2kM/Z3GPnu7udMy+/f9Lt3+x3ru6vFwY07UgMsDXcGeTDMEtR826YfcjDRcABoGk4AUAEph4B8EN4CZVsBkhJg/0wgBSVESWQXlVM9jZRyUNuDSNOOpTPwRSzIsdau4DfI4QndwdgMkmpjooAixACWh+S0TEOMWopgkVJEi3nMwOUKNXdW9+5WP77n2uJJO1i8FjFjNAkWcD3az+1ZxfgmefzjRpBQDP5ZTi+OPq9CZfuNTJ749uk9gZrm8sID0u8ROmDy1+7Ek6vPWuXx3hdRoqpI/k/bn1y5+zCekChNR2tNJvdH/lIff8uyXY9BGnZukyMh+0YtOtoFHozZG2CsniRKmEhuG8BxvpciiqU+cDR5ZsMAN4caPZRbJqYx85IAFxnF0gzTFIz2TOWbm2OMlP0pAXhVaeSGL8Q65x8d/2ycz5hEmKQVlzfczySLbSFq5dLpce9K1//+vZNMtsfrOX89JVzOProfRiADIAw+JCHnO6ZKLAZkE+B5+E1/I5U4RBA1CQl5Q6EhvXVW0s08tkJousdgG8eR0XUoWpE5DwlnJU2YgkCzAbPrI6v776fH/wuOesh9miS1CUF0+InUTd6lvC8vaSm0481rDVBWFDhEMPtgNMSUwb/VqbYgA4f5ZrvR4HsumpehsAjql5lNrI5ZB3DDzAuXWWIL0A7OGsfJQt/MnKjAHiUlmDwDvU8dt6IVAQCNsNcS0n30wApMHh/ZX+8tqMg22FjHWyiRtpVCd5q15xO3XZDkIVkE02nYrab7JBSPHZB1evtzvzV8VX+vX6yTkAknX0wfXFMzgl2QdtO58vVNbs+MW1GaxfjNND9MdXmE/L7ONlSu/v4H7rtl/tL+eQe/F2nz4N8g1CI/GZpY9+aep+lc4/RpoKYQJ1W3HIRa9jKYlyIyaALw4DkcudoRCjitxgLCpAVZC3S+RZnIjoHtFB22wdhA8eUForBisdF63JkqYLZn32BfHgy8KqaCVj2Ku37fpgd2qeYjoEFM5AJpi3bIif/lg7OhcjS/fEXPQC+bxtPle9zJh8rzbBqQVFxKLgxOH86PLMocsIp0anRAxDIidODPFKS0gkOQKtspa16cMzOxqiQq2mZVM90vhod2xMAoVqAAyjyUVDw+pk9bwmFIef8XWLl3sT/QuLSeHmnU7s9wL2kOcX26qDuO4YLLVlT1M35eupaVw90WfQY3OIYf5xcvCWM8Wku4SRLHx0I+KGAcgVmAAkYOCAhwCecyxSPd6BEYOhhSpSKT+/zSdbxKZ/WcLX47LoaKpsKT2NM1Ebt7M1Uxon3fP0bvkjQD+b19cB8Arnjg14ny6NWWJ6+wWquHKZ/v4zXxcS3j9TOZ/uPuHpCdzlKVORuQXxFr5+a3+Cf9XLxKxw7xtLbyOYpbZjsnzHBRpsfYEuoUZ4gyv0zRjrJpU4RURqpjCm6QG7k4mNlVbnooCJhw8e4VQ5V+CA2dKP2kmxaz/xdPKJzy98tsHbm3lnTbz9ODoCeeGk3j2Xl+P1CVnSiRQdsfSAi59uh1haX3OV4W0Da26k7i55dJunH5N5XjaGJIM4sTwLp9pr69l9PcTtIGYdhBBEKLo+kZF5nubHeX5QSqhJcoRU/IEJE4stl3RBTGKAkNgelc4iuhVZWLvQkO7UU2WVQGHSYlQA0GQgSJ/n4cx0sltffDpzDr+r1nn4WU/ytL7vlf1leMGsDut7mey6XEQ7RJcbD0O4exiX/Tar8E9goy6wwkkC/oYlqNiKSZxuroJkunHIxWSTNEGK6M5DexZkJF9gAC7ScRGnmiH4STPuifyC4i8j9fvbBgAA+JPPXwD/H7+X+78+/WH+/E8LAAAY/U78BADgj/AAgP+fgbD+oK0v1GP099YCXYm8FEmExrKAU6kD8RBHZnO5u0wNmCLE22nCctmf60foj/cs0D+9XeXF5cx1EUbcszMDL+CHS6ytz2V+yjjfk2UUns+layykrSq3lT7QY47TDGqLWrMKNSvuU7/0SdnfHv196ctlYqsmsEQFgZ5dmvXeORiXS1IRitz0uCgTGeaETy2IzkhRAjgXDXqcm2paGERoUuy2m7N7+SS/hMhKrSwX2dadxShSQakUAB9EMyQc0env/9Mi+Njfn+K3h4sPBA+ZtU2fnOtk/5kJCekyKsdYWm67Lj/W2d5zba2Wc9y2OTz54Gy2RkDlT4KSTboP//0fBbJMvLjZV9AhE0bRYhNDNJn8/wSBIosOpCUKsgWgACAIVAAoAKASJKKjcWDoOr7gSEIzkAmowF4QBpq4F4RBAKkYDdwnokBqhARCGkVGZUmUFBKwEDeiACVhgDAAxQEZyAlDxxKCn6TnXcFQnnbzi5+8yzJZA1BlukSRI0RkArMOkbw+WYbzrhlLKTvU2O8PeQNmuo7o7COy+7DfY90ysBJjllWaw70k0THRk3mLWmP3XJ2r75zSnnRpHoM9/N+klj590rMNr5S+GK/niX57ysIDD00sSdVLbVa5bHu8POpzo4GhVxc4s0kbw0C9M+bMjTs4XXM9HLQTIoQxmCj31PZZ21kP49CsRaHnLM0CEaWsUa1Aybi0uBEEbIDgVvOXPfq58+fP98n4RmJt/fB2taD5wpflR4c40NZLz7l29PXE9M8M9WL+gYnjcf969PICX3uaAKbA3w36t7Nu/iFb496g+E/C8asTDy1kPsa2Tpim3XY39Ba59GxwKrEEider92lwlTj9PrwPXKvr1eWWdzZXfoxkcNKKzbObb9HG3XuSFMqAsKrrUAdgWSfrsGl0UpTZfvsQdmurpRMlqPagASwM5igXGJbK9TrPWegu2vB8ZYEhQDb3p3fSUe/99ZhuCGoxFtNzGTdChx4UTmK5nO3ZZ15OJBpLpSY0kaRzrMICFMIVwoEKBWHCEThHI2KhCJ0AKqlWwMRWhCJAYwoJnB5970f+pf/5f6b3r0Pzdn7/8M/XwqWKf/8h/UeONEBiLz077eexL2Ipzo9afkq89kZ789bzcnLSRUDyd8s5n7/RIdRFNsnsF96QZr0pxk8PKGcrjW7gMijox/szoWF81LS3OYxXruQXTAr8N/ul3cI7V+nsQkYiG/q8iDDTFOdejTrZzt3KJ57T4GyL20IjteZhQ4344ZFGmtW3qTbwbuUk+ohqV1xUSPc00umL3aacUzzJCAimJDPZSe8fOJnjaMs2ObTm7YI3uERnRf5RC6esR5TTqQgw0JF6TYAjEkCtR6bJk74hE3uckyZEROB0wiwATfhCOEyAEBAgmCgOtoAVquqEVmg1iLQISFUD2IkaterNuf/cf/4+u3jWIou6+XejSET/zzr5TcGJSo4gIeU3PwbgGznG1sPv9RBZ22O9epu7DW3YNH+XiAuAxPSYkXcAAuwP4kn0JJQIBm4DSCUe5kDh40/lSmVTKkUDhGSUptqquWXbwWSFzenObZEVTN6fVF50pPKOCOEnnAgDtlVOgtNt4DYJxceZa51Ehnu4ykUcy0u6k7KdFblV9p1BnqQLQkjKqLJYKRR07jKzuI7Hgxp99q6kFFwWtwRy9HYP3lWl8NQCItym+GutT+/F4bCzIxyR3tvRtWcFlylXHHURiNJE2cxYmYBsk8xOANqETQUUFBQEU6ZApliQ6kxaQOgAFdDQ0Z6YMIyMLpah7S4vEv/7X//m6uO8guesjn/pTxy1Sn6Rre28bNVY/a58Rm8S7bvYDk4fvpDn7RWXk2N2QyvJdQR/d9x2B17Qw4JEenxAH+EsIIW/j1TgJj7O/IxgX8feEMCjulKQqnhXDrn7ZA0lVJg0UVgRp80xDjOq+O7SAt/YnwjfLSc7LHtDJ+gpSLlycAVeYz6v9fWzD1a5gFFZ1+YJHj36PPQJaTqy9aYzLx87j3qoYseDm4LwGO5rd+Y6R12eI64x4thmAdEwUGHTIQnKiVanO9KTihd2ami01NXpKmDPfDfpxG6u6yACOqLR+ixWVZapzTYzzWFOKIcQEbekQc+1BA8Sh6rMEQZIcKD2CKFOVdoaWNYj7LZLf2iT46FZLg83481Od+P8wfRaXc3j1PjgxDYOFRj1wbGDXfSgLKUYu/Ol/vUXLK2r0O5tK+8XT6MsHK4YwlKb01FR6N/Gss/AAHrCwIECrGZixK5dkE4Puh+DQRHw8YhKjgKS6En6okl33G16E0eIuzvIwogThhk4qq8zI5q4BkhbBg6YC3J3UJQOCsYwAmdliZLlyVH8266ZWgs1iZlHlrtwRMhY1uJg+07V7ibuWk1ZtgI6tKwBxx3df6j6xabGQ8f5hhJSLEXxdOgadNZPVODOMQhKRMAtk0OnxGL1Wmfg5IxwmMvkZfBhdcvC1kKh2pUuI6g+Hdg8up3zsBOQIXUcDyMsrmDFYHBTQ6jIpQoTw6QpU9YxQVggmBNSpSoRVKwiAmiuppYaqHYyo2f8Pbd3L/Hqs7eynHFcnx0AAbvZgq61DQCAaNSoaSkoRIOJkM3CwxnRLO2X72/liCYU5rJMwybvCA6mivWeFNGbbABy6E0aAAX0Jpd8etMLA4tA7xRh0IsSMiiYIEEKcCQRFxAmiDOtJJEgIYIrhH0mG+QQJkRxcjAApg9wr+oom7NJbkHAADIJEySsXIwGUEgJGaRRbMEJkUgQWIZoZjiQjJtCwgQJEV9sPr3JIYsQvQjicBPZWJuTh0mhwRgTHXabII+QiikYAJN8LC6ZgtDAh4gObg30IUw2AImECAOhj8Q8jljyHmM6WVpCfFQUyarFqM1Og6z3rb7wuY5imOie1bc1pNsvj6qlKoRJXdY1lXaMHqVz4WJg5Qt5Tq/0gz2Fh/IfzuW3GW5OOpeqHID9HvWrzKXSO7QO6+B4sJQqEMxXSiXRNc5rnmkOYS4aLuQxRA9GHU+9+o/+02f3mcdVIwdm5OWsoUzLmShOECbAQ2VOIsQCzXhO20JQFhQgsSqZKX2UVh5llQ1Kr9afy3Z3+QYvydVwE/VmLyHYjFAa1ZSAhABBFTUci0RuG9rqURLvSBRYECC97fq2xDx4SB3maLXtnxdtT1dvarFOFxWgX21FJmC7PzfxwYDubyJZmEAiGcSd4ZCJk0se4MUZhraGePMCBTg5mdZdUx1gdC4JpJEUZ/zU+dwL78RxMp4kwCAfJ9EgMNZEJ7cJbBXUK6+yidtEn8ETuXIcM/w49kaWa5LrESiUFgA4Mxq0ZLhNz0YteEGmSljunjlxD3J/Md/XQMx7FpXaqzO3KVIs+06RaKUXwou8mZCrtV2Zjmd/PdIX3MeUdlQT6qtCyFANV2IDqOafrDadBaYWxsSlp6HL0ZZTKuXkAR7jyjLFVEffM+7SL1W54N1/lrd+hZUrmBbr1bag8ExBknewwUEwTCwpyokFmEjn7nyChem0Ck2IbNDIEymZfg8/3JfLgyu5rDfflern6RZatrDAQqeDBFNAICMoFJAGhHIgBS80N6A/kRsgAcCWdcWOkkIlP16XVy8bqaQ3XAlvpmNZEg3eoFTABeQwKaXtPgE8mtJ2LQAv81F7wUazgPFAEvBqPsyU08dN1Sd1U15lNSt43SBhkgF4hf/VCi3QtUAuacCRvffrxyzPrDqnIA+Ah1cpS/NJe1jgN/d6kxk2zd5jus2wOfaiQdHAzXzCSr6yR4EAAcawgOs4V1+2lZmjQ78BPJD3GE+/AYA3szjLM4czZesaBsnAa3zBI7qVH20N08vz30ESqcA9+Syr2ld5KlCAjTuBI6//Zu5Mwfv9ALyQb2xl+zi3Yo3cxnTeZ0RgAnN5FIDzmG7/XRcWTPaFt2MjjVJSe4sBswzR5DuRHtOTj+GuYpEip63nsMKdnKT5mLrtymnbD9aJtW8Z3ss3x2NQdWhmTfg8yhi85T5HZ3uoDk218lLBXLYHTRWkEDsQeL6gcY9GF1fhTDgqedmu83hNkY16H+EMpz2Hqi0RVdieCGTBynnltX1Obddq30TJpfeOMS8HGgKRMCWRESkoAVotYBL4z4f4vGwdc03fievkn98Xv/jx/+uLq434DX2TlOx0FmQ0JBLGRQNTACqUAUSBQqsRAUS1R7wZuKT8hBZIkURgn9GTiB2SoJHn1RsYcMYeatu2isYfe33A5oj1APyGWBronyrEAvvWxF5GDgxZjYjNQGNEownLFgAFC1ZiE2jH6rpzeSrNZtDUHjCAr3CoFaWC4GmIcNivALxLh2wCpUA/q2qirLUwbA2di+y9zwCGz9Xs5ZiBorYuNp+G2L2NXS0f2FqiiU6EEOuAcOBDohHC1twtdLU7BaskLM0EvotNpZPZDeBYLucq+lnK+/9SG8k/2T8If8U/Cn8NblzBiC6GEZAb0NxbZOaIpHjORkddvPW0BbNpb/rOkVxUOJdiKTjfPWzJxSu41dSL7M1z+NzlaCxc7F/d8BCPcFuJ73MFK3HT8hLM7EvRLgbBuGszNFFvN1aNsxcvfUleevPw16e8l5Bnnffi3gY85SsWpjY7ZrYlr8uzghWP9hMG5gtvcNo+vixMXtAYzDBwwACSBAClSYMWWjWhkhADCAA3CiGJVIrNztQgANp8JT24e+T1xe0P7L+88fOHvtnSrEtNAAtt6hmFhC5Qbs1SigAIAkUJoB2Tndc5XN8fHdeH9QF+lP0+vII34Skj4FlSP9WzbZrQK0VT1RRSllABAMXAjCZ2ABekFbETuDxtiLt0N7FYYaqXiCLGAFURHXya8VQi2rkR+CwixjLGs12iQ3cWLEdU2qPb49Rg8RwXIZbUs9tmE51cI/iEFe3HfEs1QrwL3EsX4o+ZYGuaEI8MVCDECia2bcBgHjHoCjRxwsA3EjG+5R1qENsEiebB1fKAjRFiJaOzqYSYArwgIbYyljUmxH8F40d0MVKfmRDzAjBbQqzIOP6MiPEEEAl0JYLhtwv4P/D6s/8PXEiAET5IOnCXUwNCunCHXchf5cc+yXxCm5u1s08cd1lXgSXR2LzUSKPkC+MlSlVMssaEJAD3FqPFa6Z9VHWuLo2CzXuEEwa284wa6QqKk6hB8mgHw6VKAi00xNJ5RyGmNsTJ6KKRfUkkYU5WtRdTR0+KFngvJnYf+4DK98aTXs5MOwqDUZGKkQQUhHCK9lpMk4iuAkogEJCsE4C4GhnNF3Qrl5PXP+X1//Pp7pf67g4iRsbVaQyaRU601kSKhLDgMSpcTUZKQguAJEu/QAE+r/ORdqGVu/C/zd19/XV23QUUaDUos/Iq7/WklEWU4Nu2yTELaAMYZAruUUSdHKtxJkQXV/JcRCNHLthpYm2DhRKNHEvibZfEIgAeIoKYAdQ1sboBnJsmLB6/SmwC4BI3c00U3MvM9coA3EoUMaEAAK6iGbEMgGUS1QZ2wH6RLGwOjFrjFMOkwIEJ7Mmh62gaJb5pALfsoiuahwLZcWFjRwDCXfWItcB6RBX9G8DvTZQB40y08SUxxP+AIjxrp9l9+46j3sRPDYwBAwPeDBwVgwjAGs1to6fpdZUhkMDCZa+9pD1wMI9sex9giQywoLGzoWXj97jJcSnoPd6Bsq962uO8a5d1ib/57MQU4PaQrll7oneUTe9if3BM3VzTEj6FODVDZ7bSNDMA90MDZTm2x0nOytKsmDhoYznc4b4e/VXqPjetuaLMp9V2vaQMQSR5wNdmLfd2aTRLPT0vKETHEdOURBSkdIsxgEBoJiiIAiCAYyq3gz3kO0+En/2Q9Z/f8q++56NDGpdu6MgySA2AaKBBFLS62gQeSQ8NJuV8foFm56zVrXjRWeEX6Q/O3eOEp32oDZoCDREAyte0PgKCvCOncGIKQxEIAPAHBl01Ec9syyTWRUzSDBMbZDuEuvw727GE18HsQnwDDJqBqWvif4xMV8Q0g8OALYjfgPkmRBXfM27AlnbG8iMb9CcxxJTAwS1Rw6hvohzfl7El1F+I2nzNMr6eqhEbgHLE2gK/1z4xA3cDgD0UrnsngtjENyzmeyKyLqVCHChLnxwYWIP4HdiB+DFwjMGCiKbk/HtvbSJKLGJXIHvgbFoRswqOAn4y8adAgfh/w3IxEKJaORaVl2Y/Nn5vPnXJiUSm1cn+/bkkY81QTLIMyl4Dr8h+ubHxuU2aS575QP/E5yx/cPiFKWnCaOOspN2ySJARUT34R9ttDLS3FVWBCdTOOX1K5IOVzRK5E4cJn3tJPkY2/Vpt5zYfycIoGnc/iZtbm2avFRz2iFIIBisWakolch+pmwTj2ZNydWzQWwM8lm7f+Ps90opzb2aATokCg1oGnAgpCCu7sts4BB7HGorSB2DQBY4CdMZL35UBALWYAFEANIAUmwk2qkWbPmNrLRNluFE9arxevXh+BTZYQmJSWnQkzOu85rZRJRIVPd3e6PVb5qelx2oDgEkRsDqi1Cpp5GaJ1e07xIcA3KcoXUxVC2I08K/swjoRg/S3yiaWcrPFEBMN+i3YiNg2Oe8XZsfujNzIEzu4zCoREVVQg40BwHpECzcAIVJVhuPnYohNsrA+0O5MEGjZyN49MlEUZ+/jcUARDpRb79MLC9uSd9sxYmHgYGA+oplD8qaJGEKIdwJwaWvD8icHAD+M2C5HSIgCyIDLlDJrCF2bijAERWU/pge3MyJxe7rKzQyWQh4wQxgbKca98DblyviJZtvA/NbJO6bYX3n27YCyRYEACgnZIaq45uTTBV2CcUhGqbTCc8jno2vd3ZqshV6Rm/Pyc681JNXMeOf5SRgTH/34feGVlx6TnRGTx8bHQT+QBNTl0ZykSAXKwxTVCXyENCIHSUI/wgXprC8i9LZdzpxgGRwLCgNiN03gjPJXHpnuSPbGlJ5Ec7nssCe3ASbX0QgQAIYAAW3SxWNo4CktqHAaW/zF2xUnVI+yc8QzjbuHFzThkt69vYEFrLRNSiQTw4vWPuAqCFIuV8uRcyilLu91vMOxZtQ0sQrYSSd7EI8JioByEw0S9QwFStquiC8AOJ4WxKcce+2NlQRyEPAnVmhqqEHJ9Uj7gHqsyYsRDdwI3JkuLEDpEmJcIKsAfkdsy3nbrXarXb1dvV06CasMC/EpFXsIrtuJRCywYXt32c1z6dwwJwFeHJO3AQXALya2BMrMWmoI8JWJeuDtEWITGyX2cBFwmu1BfBT4D7DZxG84donhAL4X8O81IkPLQ8tmwFampqo09CEo8ZSvkc1gOtpKITaKLPdKMNdYXcx45xEZmX3xJ3p89gSryRfJFXCbO0VOBmjVwMEVCH05RV2mo/yJxpdRVEguXvbGydErRm0untYqHKDAaMX3Zd+RrpOmSkhcp5XmDWSsFWYBkdywhDa+nIZnyQ4+CBNwu7Q9kWYMZ4mX5vbcfCrMAtNhdS1/sT3a1fIilrnM0zhVX2O069PKkwb4DP5HE0WSEMMIvMk0AqQeRZPOzCa0/Q2s8+Oo7aTqIIN0aetwXx9hBz9izoUuREoTK2X0w2m1vT7vSWZJbEBBejr3O9ttVAkokKL6hIyTyxfLpum9Ldhnxs4TEVPNcrainqMM+mBF6GNYbrRgQrfKiN/t4AafRojXgO0R23XsgVfSgZjTYBetNtUAShGNhNZGie0ATMQ+V58hglgmOHoOmSOAzxDtvG0Ad9l8gzzKsCKwQOxBgt0cvlAlooxTDsB0ngfyAJM8YCNiN7cBL6UD66Ja0kQz9wNXW13EZmC8iQjX5tS0IjYGYCuiivMbPNHasGK2ZgAMmu6vDtk1tL/YDg8CG4yd9YJGUB5QBlzQhn0fU7sFiFRyNwTWBYze99lFbkWhIr0A+87t7hnvOCN9E16P3UlqOOEcKjeQCnu9nVSMUm0L1HM05tdhQGwXS9xH7K0ODxazmdrtDtGgwsdzZWLUEYqptVHpeEZe6SvEXKWUnrLJyR2adIbGpHdxvD2XmBMMp5AVplALqeHhjDk79d9ft1fXp6lz9Nh/hL+8ngne3Q/8U0M/OyGiyiwjowOTLLgIIpPRkQk41RzvPSoPhqMIWGQaCq0jHO7X8+a8frGSgqzyIkfppCLJkDZd2bFOYrpg0kQtYN430g7SaArSwssl9QnXoNnn3jGo+IDiU9NEKxcEnk8MsQnIJ0twu7oQas8AGYROFUK0sCNCbMP3Ba+aELXaTCeiMkcHVka0s4SFWHmH8GkT4nfboBhCvA80NCGarXmard1+NTjeWUT/0K8WNfG6YAdiQwEY4wLMBi6DZk4E3kaIFjaxA9FA7g/wyxqxSo9Qnk5Ei64ARtKIaGMje0x08lBggokI9wjmIMSswFMWQTSyKe2I+pwTiAHgAcoK/rz+GfNnwSGBIxIhFxo3aCHNuWjMuahLkMMR7FyDFDUvB++AxTbG3nxjg9l2cSqX7YufipXyiBHXoZ/5Ne/cDDfgIrODXpcYUX9CRIzm8O2Jx8ZI8X31X9dbzqYSD+1ndHbkas4nVCI15WJOmey/oruH97QaU141r15OxuOihsb93ux7h/9m3bMgqqSylB5j/JqhL4bTWDu/X2LQ+4T6lt33MzzjGrD5nuv/+1f/2z/9qye28T9FuhTJiEQAzmgKBOpg5NiQuao47tPYFcTtSVmFl6cHGSt17iwxSqRnc57Di86EUc4XWUpQJkVUlR0lxcMEblNFpUP6Ys2N1IQDCDIE37j6jGZ2bmCgNoDdUtvJMo5hLeCbIapANhMI46ZI8CtiF/3iNgi1yogN9ieikwqeZAYl/MVYLpqsgmj7cz3NLAFukdfehOhkDacN5M9KiyDEj1aJ+Mj+4fzLusCaAba9beOw+zS83wt5Mn3HC7SyeN3fqrWSvqzQEQajeAkfU+r27fM2fFUxdADemioUIcrXc0AKBib2yA7WRkSo4VlBP+BW20YUIXbluQF4w9pnN7cWwGaLUM1lwGtVhRAR/mw3ATDLRFe75waXsJ0gBh32ff1n/LzcPbn393lMztt8nvX6Vuya/fQanT1gg+vOy3gFMT5LT0ve36uP++F1v/7pfoH5trQ9n83cHLw6+JX4iP4e15H7WJ9NnmAy09MELRv6rI4P+jg+Dm/o1fUi/t3/9//6PHJeLZ6s/h6HjcxDfX+zlJO3Z5y5/njV437wxz3cPvm84xurxzbuzblfzsmWHbLX88ujpc4Pf3zZ/3fbT9f7f0Wjnz7yqm/x8j+p9fHm///lm3fLs/mnfP6T//v/e+5eVv7D3oOePvzKvNoGGc83tam9a7SxLUkdEo2VqESHXy3YVCclrggSmhFpSx8p7vvLp1muu1ZjK50UUDsUJNpkKnXfP1U3N26rlJHB8HryQ719uBmWBLw38MlDFwcqTLmBP3DUjFihAhOXAWzCup/0BkL3dkV8DtyVm2rSBhk0kJvq1Xd34cmw3zR5IJNW2oEReZYX7aIGduh0VF7LFQanbRc/Z2z/TH+dzcLaAjBue7XMsqkFrmAw7bdFz1IH3nWkAtRnuUHBOgAX27LVDl0F7eTxLcgzyOnuz+u5IwCJgD2yAWvylbkrJVhs8gC4Pa+3+8A3FAj6rxFz6ipwLoPQM5xz1hH4gNx6MK+1UQEIAu830cndN7DaY6nbQhbqPFzPxu81fn5/p6+MEyJH0Xd1IvriUigGOZ9LlRV9o6t2tec5+Pbru+n58XP1wd/Q30b7v18eDu4Wv/jYX63fbMrqY7zer6LxQIXfHN/1+Ho1c/nlNPdE8mJYXp6Je7e/xxA2aqJBFChdNSxqRV1iEwuvtY0UQRGxgBt7RZrwwT1k76w6t9zFp5kfIHLxmKOPyLHdT/k4wLOf/Mk/922ln5PdINMxgAknccFEMCTDJt65KUQ89Wi3wE4t+C6qQi/h0aqDkHSqcYbqzLfXjvVlT31epyAFjWpJbCBrYCw/fzxfETEGJjFQdXK+2pUJmaq1AZwDgBvwAPZ6ubpszSNKjIcNCoBgdkgsBAAC+KjHQBSwCwBIx6QeSEzay+aZu1KBJLPbx/lAt2aYlIGLWmwVpJouuukK4MFJoWDZvDwqAAxsrEdsp+Se41ldBpBDEs42tovuwmImjsZ7pmAEo9Z6iZacfSAfd4ssgNypDkBo+41ako7Rd7L3MOdXXyKr2Hf6Zo92NtrXd7bVnI0sobFZr22HKac9aLdoxDissSQedCSrd7MF1L5yel9P57ltP/miamWpLLgElGMGLgVsXGaxNV3AamiYkIjQpkmaNPZEAyq02ekRlc+Zhsp4mROP0y/JJpukHA3AV+ySpNv0x8MqtAEyGQCcMqf7DuYY3PCqbOVJoKhFkBXtGFYzlGJJizwTrGM6T7B6ZTzh13qWarm6uewkNEjNAqSU9mb2F1/fDyjUuAodq9ii6FR6OogKqvYr4N5HJ2D3F3bjA4JddYRY3yBnJQLh1CGWGAwig2a6sIn5lRLX6mAPEcBuOOdZHqmYAICLDPJJxyRAmiVwx0cI7yBKGwAukkmwmFqtVQIScdNJO2CSOEb2EsErvyWNw7VnkU9Wcwg9rpa/g62ISgpaOrn4cZ4wmeSThS8Acf2VfTh6N/vIJp9MQgPTTFhtJ8hvJl5ScdNCKwHMaUrRe39bjSBMkBQmTbANQufT7fMr+xSdilCL9wMnUY2c1MloItHBJou1aVND6qJtNifJRuoGmrqoe6w0yJ9bJAxASsg0Q4F05jQnHltCa5rEkGiwpLqoaoTNNGTVq/Gxenz9Kr60HOx22cuNnDmHiSR3TB2dZC+VKN6bZ1je1DQ+ODKzCxa6I2y1N32hS9Uk31W3bpdM5Lp6HEmw6KBIttEUEZXTzrquFVmJYzD3Qz/5WZesNEevJoZEwGBUpc9H27JNDTu0FCpYLkttaFAwosC+zAuk1zqqWcZQQTIeIG99o58zXpCPgdh31xIDg78VUjGAnj7I1YhBHK8MYI5+zhekPgZuuiHK9EjrNMgDXmtVVPBt/gUkEbclJjFy+DspagWTbWYjzavB84MZynfC0kKnsEzSRptsQgMTaTKeenUhrU2TpsFUMqaGXOhiy+BB8pZ/OGoVvkdGclSqlrBCQk+iKrIoJRBE2QgCKA5yMYwARsCsOR+cz4c4XTmsGatDmqJ7qZFe0qZd1aE2e/ek1OQSuqHu6hLomd1uOMrc13qN++HwxbA3AR+G1apXPmJDezqVBKIch9Kfan094xvM/fC97ajWrFNlFk3XDa0kGgBAUOgW3g0Pk6XTqGKNqCXL8qBc4c5yYPyTBXx6QgFITRyLBIN/oHnZT+yMBQXJyz56Ynj6PPVCGEGgkUaZEGhCPXUNNfxuzx8tEoEgkgHgZAYoGQAKrhkBEwlUCBQhAKTMokkMawmNQw5VnCGLUSlQQ0M1ZUNAs1WzOMl6gWowJowHevHh+1ku21Ks2MEdUGQtmRoBCqchM2W3rUIbeo04SYQJaj7H3aAxO46/etKW11VmpULo5cle09H0qk8HzaKErJq8qt2iA/dcH+lEbyAkUJMJUdIBEDWKBQ21LPP9s/sadpd2hqO22xpnnWIJ82rQlVRToEhRB2IRhhB4CSjBEjbvuOUuT6CIFIGBa/N8zv25ov8p/q2c3yT8JfDnEv9kg2IcRzRW0TvXZk7kzvfbr2f8n7mXBxfez/P//yUkCQ++N/9n/s/845sETTavp0pBO+Nxv1+9Z4TN2AjFo5LTMd+M0V1XH5dnPIbpxJyxmRa9837m/cz75nnzvxdYXnnG+/LhH98nl/y/lfS7hN8k/PaTayHLw42JOaYZMjDGxMTEXC5cuHDJJZdMjGUuc5mYMjEx5cJh5nJhyosRtwsquYxyyVWuAsfDSWJ4d+/ExVwAGeYGLFI00BArlALa0mYJNrNJgkEmgoxCE+aVLEZaGwAMWITcxAAYVgAFxV7oypiAgpiepPW1PX9sc/7cX/73Xn73p9/f/+1zOXpyTrm+RFYgvlvbr9F++pspPj7q2OXd6UnkIrqjNvToFtbMFkyBZRockj2swEBHoCCAZAsx9f1KSzpXzbbTVDMcBjWLEyi5co9zMnfW5LlvYW9rIsUsZjioc4O5kBwBwG0IROkikETUCECzsHh+zcy0BD1C6WxnuhTGoyuidzLvbXSprUC8mS2egLHtn6el/j8wo5z+xvXN1a/H/67PmcslV3jP4+73B1jHREACCLqcZnENaDBqSrOHxPIWOMDDWyPWx310Pdux5u//A3389qtCViCNMLcEEF7vfz7i75rH2BG9upVNvlb4Jj7r0zLVmrY/G+l8/Q8+73zJby/XK8v2/+7//enjvOf13+2vpXc9z+2aZ2O5/eztu1m5uzJrKPzRHW5axbgEAqNQSQ1UcAQJoMwAjEAdjVCBlh7ZsuV0D69rMjaULEo4d2klSzP3StmEHWPCKEc8tHIV7GiGMGdBwQzQja9BmKYlVaICAdCV237/5uToPvPu3B7BQCxLnE2DUDlcVMOK/NI6UkqB6AioElxfHN7A83dOJSt/C/l8eqrCzjQZ7niNSWIAI5IBcdAtql5V6as7e5V3QSuSYJwASCUWiCRL0YahiQWiFifk9vCwMtEz6Vxw8T39F5lwt6Qcbm9b/YeLDss/UDYvIs3tqDRDXLqqtSwy10yeuRhUxGUOG/x0svKR5QNKQjWvk0TAEThwPmnF4FQxfCNcXnlqtiIQ9WtarpK79FzzRvcT5UQDUTCXbB151lu8jFKIR8ROPHLz43r8139puHtF133xwwViR9V5bupKd7IIjzumLB6+FJYBBpgpKEQp4C7PTNcZw4KF+kBt3VswsJsQQKQp1WRy3e/CCRgX8zG5ZnEbT59//83/Av7//wb8nwAAAHCLHwFeax2FVA/jO+3jTeQYnt8A3gN8lLat1n4tFTBtchqauNInN2WdpdKEhj3I9dXph4zIn3/rG19aJ0PBg2GpjKpWKdW/PC//wCgBr+r9X15uVNdeDb1necnARaPIuSAAUnztmBn9WS43o73M9rqdb/piMj5vJz7ip/q7rFgZuHP4+j2Tkc2oD84KEA2RBsIMupIqgqA62BwMdS5wR95yv2i6zcvJHKe9Lk4Y7S1Fx9e3vbU+5eaHEtFRr/YoCJKas1M0Z4WxxhiHEcgmQTOlDbYA8E7Ne2KPD0K7oRtCG5Q7vlAHGpB+y8ZPSZUEUYWybPiY+bg+vV0jwA/CLvPXllH5cE++iYwLmbeGpyQmiLEYsVnSWQpslZzDQAIrJgGquKgCRQUjVgwNsJJ3jlWtp+PcrquBBNhqLMuV1ur9eOXFM+BtnMyplBVfmZnjnL8AOyUqKsPEkY+1spwjv4n5ZJyJMwx3h9kY6fWdke8sitA0KwPogByxo/GKUyeElL667TXpJO5JuPdQ30kPV0V/G24/QBd1wUahzfmP6LBFy8EG/TWLyHDj5Ze5/09/Ldk1r1zr5R+Msoe8CFMa5FQ8w/HOeUmbBXURZSAQpxCgr1fr2ckjahg72no/ba70Z6ZjbeJfjn84vibv7a6qmc8cvv7dZ7/9z+PYHR5/vlfdckx5fFzvP5f9/2b/LG7Jsn/S/Mk+khT7/DTprOA/b3+asivDX1uhA4xAIJrQNPAaQaJccKJr96z5TzR/q/qr6X+QMbuPYg2nP1jcJZoAiB3ZJ5dNM99ybgU7PZ4yirWqCtcJ9XbIqOQ9gMJqolQIgDL4x4EeZlESuBZ9oSAvmplPzRZVGzE0/uCQKWbyTiwHaindJsRGjr0JAlszx+qsJOE2f8Pcp9lJ39JAL/G6mMPJMMLzXus819VbImH0wLbuTtXqBPOQjFwEwymwY0Nlj/gWmCWMjGrTGPd4+vhxfGdp2+imA5wApBk+oTddWVVXDQkuFBEDYKEpSqP9FmZkCRB7hnEc9c3X33mVTuiP3bxLCp3kqgSljZ1hiWFHTNZfZ/0LpG/UlcqbiuhlK72hlEy20kBEMyUcwslcaD1GeGWRTLERkEuEE63zNU0jPB6wjxhPSsomkzFqB75XiToEr5ypYF17fhCqaV6YMThlokhGCCB2JHQYLMbE87SjDZaDWpNwssrVIAAbaVg3Ypa1Jv1x0t9n7HhD45tzXU2VXbGjtyl3RjAORqy0FA001YAMb3ifPBbnjg4zfB3WX7RNjhf2YJ/IGXu1j7TP7v//z/jlY3dk+OzDPwO/ry42f9PjsDk+9WWH9XqwOC6rxw5mles4rHt36+o8AzPM9tKFrhUWKYcidpyomEcODBKwmuz6rqK1zJCRj9wafAEUUpFQlHjsGLsVxRR2BFizuZ5PWQ435bNyCycbbeDwcUgbIDcZRE0/YuvwkvPTg38S9+VqmkygjE1xZRDWJoIRYBgPE4xJ1VUdet/4sxEQJg5vABoOnLfakbC+PQ7RojWSsUq1T+cwGGJ1sjfoGnE6wlinSA4SsC6BlgoKj6k/MGv2D5c+665thSoozAO20wmNFprn5BadewBimAwHci6bUhyw1pNtSWVQwPO4HObr19esLmadQ5kpJSQUdFlGXOxpsZPMViNRgIxeRC3iIIP+yu9FABDQ4GLnfOfpj4wlMKhPgyg5KG3VihtYPbuss8I/TeR2aP/9pJiNjY3TEBNdFZmGI64M5RAIMhcZ8HC+k1q41ldop9mH1yXBlHPFYtyYkRkREIPkJ1BABgLZ8otqyCkmdq0WswNOgWOKpeL1pW2LPoInnWChAFQMcSTiLoc4x8SOFHAUiF1qbbur+t2WD6xb9dpoZ+1hZKtnmh7Sb0wtpmAm5DPaBwlpRB2OQwA4oBvPTRiMYWgG0QXiY9l8uWJcl/y3n7O/TPpv/3Dy+j+uf/54jI/w7Mv14JGTtUfSZfpjB+2zq1ClsJFUW7BkJQQWFODeXoSJDg4I9GgBgQWddx+9m8UDJx3DdPz6ke8f+X9I/2dkd6yEyonpMKAYEPkuUEisD3uj0q7DjU9BUYC9KbEgcKphtG5DqQMo3ZbL3neMv81YlMZosQATyJGMAgkBLQgTWQwZZ2TMQq8yfjfNp4eREwUBkDjTgCR9ijluwRtk4QSmpCIyvE53yii3MarjNJg37V9RaLEPFgAAAIBdz88lq0JDWtUSTBiyPMxWEsi04zicOWCFksyDoiTqGEAZRlyBwabCADsiK601KPB445o0pGggWIxAMo5V9XFS5DMwqliailVBRVVUgv6BKCAFyFBRYgIR04qxagncVuwLbowaZrHfPYlWsmLKXd8XPp2a3gbb0zjdav3d5bevt/u9Pu4Olli0yXZbMF5o2TVkV8yYhFVfgc4tnXc0XQWbbL4P0sVYPWBIaT403YZP7E9r37MYT69woruhjOagTNR7OY4fPqEcy0gPqQAGoBSvND2769nqt8f60WwgNA7M9r7Jc9sL1qvj3mJcZ99kI/lefCshmwIcxIeBEFlsGApcZBEXmEgDdKT3ZR66H37STz+P8FXvvzz+t9a+ZtvHo/jLimcZzsUEzypZndvF6kMgEACWABsPThRoHaG+h9ZLXFRbqwMtgAkIETJoO9vGPeyIQWSTMxOYjJKWWPLzmK97/Td2/k/S23VyOtAffEWBaBm8bDDAjoamI1o6o1SU2eHVSAOZYCzKAgfleb/qGIz4f8pDLe+AoAAhCEUoIww1YVvJz1NFeMoEwo4wUAxdZv7H1L8svCLyOpMObYPekASTYJSCSZBQsANE8yryZb+Te+Y6PXHMjnhUJ3VzUJbJGrukiWNFJkMYlYpyGJTtcQEb6cyowcq8EGqRWGdqIusaZ4RlaY2X2IqhYSDz2gEygkZIziZ5OUyIURG0sJZmbm4/LvfvVlgqxaosGVIBIMQatBTYrIgAVbw0w9w6/OVyXRXy3JMykVyAd77u/GS3synJaw6FKbPeF+30T8xztgpyy4fj8XmSezjsZUEm20HEmo1mEpaeFkgvJo2ud6BQRun76FweTH5TzL1Ll8ZA+6R60ZK0q6MiNnDyarfmrf72ku+ToPpkf7+izYZPEUXLYIT8iD6tDe7XIvYCv+X1cPzcce3rjL0P9do7AgUevqacIysc5VCAgUDAhBoMgQgYzH1idcRll+6540+f+MbR6urz63RbR/uc8sxz5mRqpsMaeF/tcx7ff7I7mQcgWmiGtOxQAayDWBDUaHGqAQDDAAwpqlJEVAiYTnU7XDtbcgyNlC5sqWQADSSYgTVeGMXsoJTGT5btK9RPNiwb6morM9PiFFCE1UkdsWNb1iADgMjkhphYBzMyijw0569usfhvC/LpG6ckFCARydHODpw7P8+LW383K788n6f3ghIJkQaoUlX8eMID8X8UVThkdCiBRMi0clKbTt1DCTpVDhEbPtT1dfKUPgTFrN5JZlHdhMKpkFWAFAzDsQHUpSZO7WkUgyKO+TSBNSCbADRXrsjVQ+toChTQPFCzgzQyZc/Spmc0L+UCBPvynlkNvjhSAYRowBAzjP/sX//csDweVVf6CJZAABAgsphYggSUAFLUNV6ennnzhf+XHxIiqx9+Y22kN1WPjL4e4q60/t84BUm7GCVh1MWS53C+Lyk6JSNShxq9fsgp6ylyU0YEuyralVbKTZDJuezS3byS/jCVhXK1thIvLVNb0010qsdT6XhM3I0nLS7f6AP54ey2C69HSMvETm7pVd6SkG/0jxyL7/wyfO9nh+txiJpf9flDoBIRNG8gQAw5VCBBEACIM7OMO+OPQr9cwQ3zP71n/+T3Zx9eJ7pOiyPPks7kJCwYjcMSyAEKBiiA4TmEkw4iSTVgIAFoAVKJlcqAogIUUIUaDAZAIAwDcHOoN8mbeo2TguvFUbqUGDAoSw5oIhAIj6OMYsGos4X8tTod4/909J/NY5tQxTNBRAylcsZTeFg+4DbjxnL6SE5zEpB93sHU+hyV4bzvr1/e/Plz16Pl98xbIARC3tgbvNt0Mezw9dfS3yqe8zf2xuwWczIdbjtiwKdPJ/5sZ8H5fyUUHnmbnDWKZsbVZyoCPXASqK65vubN0cqJUCQA06tLUE/Z2YF99LgazSog5JBgl5WS8gD2uMw2AUTXtBbrzDGNLnEnVy3aVDghLA2qx077cgqABxthzEtwHzmluN/PN7omDjdQqtBGkNVDwovO3WjDZlkop4gg0dEsCkIlBWEFGACSKqwmYOwvaT6+ALd5VuWs0W9V/Zk3f55DYNrRxH8ure+wMLPQNGCqvsx0nDbJVEeuxg6Vc2Ev9y+2Wh4PcpBHI6p3ziAfbmilfwN9mcbFz1m8c6QPJ8gPfyItpKhsb/iyP1RRRquwRke05nEd997GPZXJuGbIfvnBaxUZzRby8VZGBJ4CWzCQ33MuBNxgB3nRGuhE11Xd+w7/0xdzlHbb9adT+XOvLVFYssqykmaZCVJbCTmLEZAgoQsATGLAAMkUAIFUzREMwFA0UyD3ljoRAoCBggJQEJCIIMByu5/e3M/lO7d2Xi16lB63G6ziuOCQg1qyrGyMSYNRNEVOAwLemN77xquuFP/WMv6Ky9Wxvy3OOaoDR5SgTuPDGfj71/efvf/7eNG887MXd8p991uSrzt9s8K+/PP7Fc5n4N+SvkZLhkhM3Lf6err3v5PTHt/Cxb3IqHN/HAjBQOeEBRFdV9BpDc3AitePHTx2txsfhPxFv0I/QnXZv6YDcz8eqFGzmMrgavI3Nvn2nnWH56jXkoGy5oQwExZUu2KHNCnBYNRQCyPtM0KmgxgnwrtnpT3VRB7bh+4qZyxOgMHBom2whobWWgCtWuAh1WbQXgJVEVDEKrg0389fl672BvFGjYs6g7bdlzbwNOYCkABAt8BsjpPevqbzjZy3C/nJqOdIQS/H3HW/Po86Fvg4JSoMRR5LM+bCV65Z4wy4KjPJStyuDkWm22bXDB06LHyAWkSKwaRtdv+bgzwr971fYAsrDfxxnWpffWCWDoSVaZlQbvti8X5Xzvmnr5vDg3O1Z3qje5/VtOIwXUFJFU1xWC1j3Ck3Tubd9uM9fRr/mwf/733+fD2rz8zz9vef/ujz+/1nH+aq3T/6jIfIZiweJpRKAQCXAYK2Jos2qJXy1Q68CA8EgggAgDW2fX388v62Ldvms/U3Xa1UmOqhQRwbCFjZNqyx1iiLwBKChSFg1KaGiOG8ROm6FC2owx042f1xeDLrZ5M4x0dAKjtrER/n+m9pWUIRFTIFH17wQWlWk4qMCFGTIqdEMIFlcKzsGZIA1LwBvlbbbi8IXJvW02NunqN8IhP17s/zvw3nlQr+kP6zq43zv7s9QzSoOwzn1YGrhu86DoXf/0//7T/wn/3bl885nLAp2CgCr3sJpjaqXLzBYC4o3JYN2jxzfi+y3CaQrsDkmOgcv2PRzjcg3TPlbudWHs9+88efA6dTBx4b8dCstSQYwBAGVHCej/P91Tn5VkiKW6fK2lbLfW5djc44D2aJgRBomHMjPtusGcplCqCzwsVwiHHf3LwdxjqF8ZkNPLjr/YAMgGi+730ZyV1EgKMRjnhSKBDzKAyiV5BxM23cD3DY2KkXOX18TvlBKLQZe2onOd2vpm9Rf9DTrYABW5/25rez38Jd7unQdsZN2rSNYZVhO+19qaK6jg466S6iBRFiKI52eE1+uPz/77Yb/72PP3z/m+/gE+etF4+25/QY+2xPeXD45Y84K9I574PBxnTO9/LQAQCAAKESKZVAkQhAQgCAIBYAJQIA4F/q2nJv9LZ2krb+Zk+fn2dXzoU1nM0aDwlllpMSVihDMZCjqJQZmVrqsi13PYmP6nXcdfp9+eab/+IFSZDvQb0mibKDNyMoBAOEuAKCs8pM6Ff4hFOUroyrj4u8ttekRV9OK2lf6PrrBi/1FefC4QxYlo8jNpIymDFxQRJZKRSrFaj7Od/0mV7Vq4PmW7uv3YPn+0gmai2zfGV4cD/sa2BAdVaas7tIR0BmmMfnSPsGQ0nLvN7A69sYlhwYE5BLrIgpGKVBlR2e7XC6psILgpqi0s19/ay3g9cIDDDYYoC1pqiJoSHGgDF1aj/gfkBsUA0VB8W8luvdKfXBxgsFRIUMhSLEE27P8Nv9MhRAGRQMJidm82ev4q62h4OaAjk50/n217OX22jvSVt9RFnFOcgEWcUIxVSmDi2pGIqBxnMc1hk+2RYxTSmzHIDKXF8Cp1tdXsPMaP8ALZNgP8138PSRbtC7t706tMNiojTaR3kXPQyPRiIGQAyLnuDd6dwrPzN/R//mj/UvPv27vMN+6Hk7eaKP2rNxI91aCpomJYtALIYTxAQMFrQGA+pHpA0RgDK0qAwJVqnEaAFJKjgYAACkO1bev7zm3tdpk/cUT7ROeQSr3UEVo0dLIAQH2Eo4C1T1AEipYRnHjqVGCKTKkDYdEnnX+B/i4WhUfRq/+ukf+U812UU4UQYKMHLxLlXc/RDuNn9ikZUfZoM0kLkSxxlHc1/nMEnciEWHe7nKRCEDMqiaiIvYuJsSmWQqn6ASJnWxuh5o3ROfWRkx5cgQRh6btZQMa7zroMr0SJPFSAyA+ehh2q/xqlHJYptStqWb3r5vkBtvATCrxYwVgw48hQME+GIJok+gJJWE9nXXvS47xeU8ObM2wQgzi1lrrZ2lsiekaSfRQJf2+m3gqMdFAGruoOrUnDeSZd2oH4gaIXqOyEEwrhrxWQN6AAAk0QUEhmDe5po4IeLB0uJl1f/67+OjjiKm43y0vRPjNFh+YZ5hpiJTFnpF2T3QFa4CJ6tv6TGCN4ERRrpJBzh8TCPfPF2JnU55Yg1TcnjZhzPjSKeWpJKlKKyaX+QiNmkB7kp7WacLen/Mn7N/pft3f9T/fj/5Ox/vPOYDeW/xbDi9e7o4OVYHAMAm0UJBKYAAgOQQQTD07vyE18tIPkOExATgGifr5xocZDRVBIQhtr2mC4/xqEmd+Td9mnuaXSJlY74zO0brbJElEpaKgZQJMVOcGdsyv3/2otbjrX8f+37m3+5vO++eiieUN7weKy24V8dvL7/5FY9tR5r/z8Z1dzQ4BUvAFKYhZ5AFz0ffaNQVWeN4cEwkAcIADpHivouXGZbZhWRun7/zWfGg0KKMwU0wE87BRmtYUK+Ttnh+bl98gG3+vW/8RqyNTeq2nVTHNC4zshsHHyHDqbLQK/eoBKZKU9RKz3hkIULBDOYLb30Lbrq11dYQpmAOtC6lPTPK2+oLv71e3ERop7qgqbczPQFZgYXAiQUJbJm1kLSzNEBIg7KJ8CQ/P/39L3z+ih47oKAP9hY6wnnPWMUZjlxWvaERELiIBjN5oFNiAHNQspuesjr2zorvg3ithozpdjPh+qfv8Ocz04eUCvIxPaVHxR48h/bE14odYpQRbuCA8FBpTSjpZGXEETESiG70gr6HyHisIdBC7x2YNEhuTahjs+MqHiXK8UAM9Vs2DAvblJepw6qLb0/8dk3fead/fDj7rn1Wz9kjXXXLUSLqkMqFNQSkBdCvWuJw715/EhuhNgqSzxANhdKp5XKdvsOt00Ja3ZMbc6QPcchhWm332nVZaelo0zEdvDoXQU2QxCQLjTogXIGKWboktc8fVUblo+ILcFvcL+8Ataitcl4MXcKUqmSDjDfbL58q/o3ycT0/PMvnOjcBRAFJqLtWG38pYqnSdtw69J7htld/JM6ULjSlrhbPwq50mmkEV0/+OpKC/4dwmqQAreJGqGGoBtggS5Wgzt7EMJ3G+6om6AQK2DjY9XM7vBb1+5l5tsStYjkx8oAEIU0zgNARtGGZzElB9b6y/bIPCFy9zEYHXoOymgxL8RAM4+Ue+SRfsF735yN/vQUbfs5C0FoBCEgA7FJLAoEMJM2+GtqJVN+/4fe/xecv5Jh81uNrnS2amKNZv2nWa/NyzA4sDAWeNjAZG6yQAezV2grG1I/oj7yjH9Igb8Go/elVlteyRRbopnLzpXJEFpEFrtO+X3AfCaAEgRIDPNyAsDwGWayJHcuO/OjYPZ5LMXUOb8F3a4nixDUVa4R+AFb2BdiyPjMWAcT0dcUvnf6P/5eTn/3hUfzhkXiInjJHwSk70HiCAkxTUgFt0RCrWvQeM/3KKQMAgF3DhEmbgAhkBB0dxLAkd0fehP+reb29s7Gysnu7McaVIqydr53qVj8XeoK0ZKEfdeghsJFRIWL3nZ30831eGP364oeYY3QQP8L8clWuzmrRoq1GNfOfgXleMnIC+KK/yNQWFVr8yLo/nkUVTDAH8Rv+vdzWTHcO/N+Mv//0RX34fnW9swKgwERqnCZDTpU+D1XJoj3+o6Tt9CXWHWOVK22HHAaph8aqdh1bPIFblQ8/t9X7JgazFAutRKZZbtVfPSjg/uypck6gS40VsgcJtJgsyJJcXK12zkk5+Z4jjwdxKsZWHBVi6IQCGU1AjhgeCMTpqVMBogXMAAHBAATIzIIjHNhIYMutgBmgWLzfCX5iUYueenu8JndJ9AY1pGPUhXe10d35IpP+RfuIgVNks4ADFEAikfAdvcxnuv1WT92Swbfe52qOJmi6T509LjOZMqKP5rhUCJHcNlMhFatAZTdXpYv38uuyGod9o3fLPkfG5yd/+7XRS6BWLRBBCbEFDKTKJK3MoAsoQb4215r9xK/98OfHXA+Rk3YqJeB9MJMkxpICFUZBUWhWQQDhnquHEXCiKYD+SIGIIEIG7GIiKIDw9Xju6+PXdy/3vJFDWnPO4pNvnmY7zOVSndZOi1gWjWr0IPeXPMgPGgJBHYILQUAQAb6j73bfZf4L5G8yv62+0QHnp0Ub/tp2rqaghCrd+Cfj/6WuCTIwagShMv1hOv9LUf/uyF/O7/xnWkFX8h/s9aNN3+v8rR//pdXbf1v9PEEBICFIBASkDTnGx7kdCGO1uBlX7SCyoa4ZfHKqsulT2lW86Nk6+HcV4XJnIliNFOQDpChABSRFjHFYdq6jNrXe8xyEteBggDdBauP21sPw5GREKKqooRxumtiPSshGkGYiOAWv5bAAkcZw0SxgpPAKoDPPAR14brqiBEGwQMQOZqFjBIxlMNAqBv15/9OxDzLs2fvvVW2j7eOYJPk66dRnzc703htzmS1fxRxOyEjfBK/bQJEBwI5z8ViHVr1ayIuvd741IRCWUbUEKqWOt/bw854HU18hglJXAXBqOamDCvol2lcef90v9OcretXb1U927uq56/jgDHIllSgyJdsMARIdDtOMNFUMVSMmdcObjJTf8q/h1wejkAM0u8lkghIAIFUBMoFCMVABqAGgOKqggBFAKSgU6IA8EBcnlLmtlUhA3t6833i/ol94v+FWe/lxtnzvZ9dpmS5rdo+++HkPMZWi1VlFFKpBJCAaGBJuKO5DD0EMb2gEsJft0/qP7CLnnTpYfigFuWv+TKG2fH9dNjSINPgp/Puav4lbGJEYUk5pQyL6LK6bm/5y5V+r2c8QE+UW/9m3r0c9fvGf/eufsf+Su4LMYp3IEQ7GHkjMKETBGMf+SYxSlATHLUi3woAZnDOGgsFj/crfMz/0P56ZyAaziFC+s6oMEy8r3Itr1EI7VdiDFVFnw/1MdF8yD1x+ABu8d2eDOvVFj0mGiKhIeEzmjst7UNlSNwdwRDWzDW6StQlPg6LDkxXJoECRUwS5IQuPCotBYilJiNEIS9fMiGenGfl5PfbXv8n9eBtZy2pqZ+7NYw3ASB3dUId9cp9y1rPKVLLNZsaxJqRYGMBasrwKA+iS4AS7KWb1QSGLH9EGuGUUpa6f9xjkYEiGIKeAIIiGo9vr+xa/7Oi2rs/wN/U/fq/ne9pPETcXGV0MIzeuB5GsRTu5g771cV6wFk3EgrqHBQ4Du0dcBNiIQPH99bKnAuv0N5NWjUgENDKIGURAQSiAg8r956kABCnE4hQUKRGAioqw67vTmu3qa/jy5tUnt1Kbk9Oz07Mn/bLI8XRzP+CpkwoDwy3DdMfSKSFi2VxbRtR6YgvSnN58UuL0fellrCflUefTzX/FeXJWUhaixWYEv08q8AEFIUyGAg5we1wsvlv57//pH1Hnr5flepzXN41Z5+/84ev234CZ8eMUKxHc1mXmi/MFuGQKAVfN5mrXBRyVqlbvTmdjF2gd7M2v9dfL5DtbdH58Kf+2xqY5+KWhjrofWrPrzBrcFJv2jr4aSeGCljawjPn/dv3iqW6e7mfIP//2cJss9GTuoVpVqOEcM5ZaERMSKRQEKwKMRFmYIaGaC5KRUOc50AdbwMOKYCCgWTYQE1Ok2nA7koQQNoEEApQxzgDwqHJVZz8ybNsIVavUWLECjxmSmmgGpt8l7OvdBytLYQpRSA2DCEMAgL32hScPuwECTjAuRFmqRdb0KXnq8cU8QxeTIOFORbF00RzYg4M+DQx9ufQv7bfv7AuVmPIIiX7AJ+DFyqQoFATEvWN//IvvSc/pKzdbvfxu46BKkiE9+BL03Q4E7rguRqqm+Xy7S66uPOknP6CgTcanFE5xVOsEUPujl1OciBEDkgaKYGGQZqc34Ut8BW/ev+5I+XIefs354TH2Sy8O5+7sbhh12WDllUpQMRigGaLTITEzH4LaXb5SV9Oypivdzsvy5ORxXQRptckH28vtf5rzJHeBLdFc5PZ73Qz/erYQhCDBLIKAOdeh4F/8V9pnfm/bLe4Ju9vLFvRQNPwhwMnhRLEevXJYgbqm2+UpesZrpidEoKDixaohOBHTLX/cnkAJczGV3/3j3OM7/yxr7y0pxoIvDQqmA0EMBAKGiSQ6d2hc+Sln3WY5aex8eU4u8g92AEAEVexUqz5qvtozvLbMB/wNP79BAyXWSBbeBQAAAADYuUsBtx1AVdDOBgKWHORiBZyYvWnOs6mthm7EIaCySIKJypiC5JilGYz/uHsL+PV1HmuT9VCvlDxF1ZetQBJgSaPEIaW/dqEX1zEDCgYEc6VX+AFAASBVTB9a+NBFTXlpQmyC3HEmZtTdV9pMdcdKbvRYkMKuZBdru/Vg7eF3aJp1bhlwN4HsUENeJDJ3yGWWrRL+p3l8+LXDD5H1F/+bp/i/cP+J0ZI9ZUALHBjfG8YiPrM/2FUvOssS844m5SeDF/Mx42zKjx93AFScAACUQgwLBAKEEid5mHyIj723P+7911/rp0/aB2GzqDYXu8V2sWcn2pq67zhGUByg4gEgFAOOgzNKpW+xxYXd5uVjw1BDhQ4Od27i8+wMNmoNoz6iZzv/7e2rlQHBhtmfgivwN9EFNQZFEqs/ig1psDST4Gznr/zTS2NVclAVSoM7gPUwvQousSp7m3pmeQfVQQEKUXVSx2B+YVdf+C0oUctYfnk8hlyqsrZ/+oZMX6DF+SV+5muVgu+CWXUClqmOkVqnyNs9DtemIHe30lasJM7tYTj/H9mvLwI9E9yRW7/Pdo02KZCi0w2zNuAUlZYAF62WYWDAgzxqOWZEfrcEafen/BtibAEAlCOkWQPUaMulTdJMTm4VaMjBKmAzIsiQ6i/4t9//vr3y8/fndZ4UpHAO1RjFew0Ng7DIYLLI0mS+7dwe3cZmB0PSxlhgJgAQBAA1URYsUPx2fNKCvQSpUpQgY6kyOJo7TTBir+3tOHes4ZcUgqZaIIUQgaBDXXQYBkQEw2z349b1eoo+6f5z/7dPj3Ucs7SVn9WJeoaeySDYIxghEGHACd5UOsoPg36TpzQd267LnqX8KPt+FXWBDbz3A4wIAojKAAC7S+3Hx+Tj9FGenLTOCq/dB8euaRwsJ/u12+y4nGOacr9LRmpOzGPqDJwExAAeEAFG8Ypv9es637P72Kf+fO9dEyNKAKLM2x2cHsbUkDTblpn1p69e3vOfjF84H5LP7EXv38ql6NYGnxADOWJZWZgTsabO7IcY/x3qfd7/xfEYRQwrSa7EmlImCL9miSrtQxpa02GqY90BBpCl2MuaEhRhrSy/JB+PFTw5P1ZyR8eDIDAPnBkHn+5W9sAkIxmMrut8Df2b5qfk2nT1iuMAb8jRV+rQz8tCmQtv64snzws9RlTiSCDMUaQSs1pQqUNAAG8E+RKae4UgrgPwWKqf608+6x0x9qQFC0JWElkkAEQ2EGMvx4ziAJAG7ihJksh7/tOTK1fqISvZybhkI7UadltUMUxmGqxKz/evvz08a9BGB/H5IxIJHABluHlfBggAEKXhu5dGpqPCn/PUQGaIFoakEUeyD63adjDrYZrNJqmBCgEDeCEEgyCAPaMc/viT/fF5cP/+wewHj/14n7ORKkwzOhs0QcSxZImjA9leQgECoAsKCD3XovqaIfThxFtpjjum5EeN939+tCFxKtX7KwieLA1pgDpCnTpIShUAXN2TK3IhL/W1Oyz446yre80umlVcm6u7Z3dHR5mXTEuJJMTKBrABoQAAwxPkAAiXvnt9E0z61E9+emvLNudydwxR+dFHudx0T31ME4xqgzAtXO/hH45/POd+dsfn11IfvsbZ0AwkGwxFrImwC/6gPylb+8q5cdNB8yYr/Q1Z3UmYDBAo4+u9P/1Ns/X3vfz0l/b4c9QMcdqefmxD/UYNgNumpWKQxBSErrwXfedhOF8rBBNF/dWnZTpQGtIPaaHi3aELl8/ytbXfwvU3XnvDe15GuyoSIteC8bf/AaxRsZjeTBNgH3SiUqoQtO0gxWyiluSMZnIGHVw2K+AhcaYqlykoWwN/PT7OP3/7vLZ5X/ZAAdOIDkZpA3C42MBysE2p3tAOlswYKtwm1D/3l/CpyQMdaosLMkIp3C0lk9zJxDIqAL+wnTistbEUnBoAcPwyn+V+fMe6ASDKAeVIU8lOEg9OPzdxjAfOYow/3kyrXFrXPsA7qRENAikU5LkQIg0k6xF/XEc/Pe9UPuR+x3nQnSUaBQnCrHTI6MlhZBDmoV1H4kQMxgGDdBB75j25JhxcdqIpw4yw+IMjfpPiIoAAIAsCHloAbaJQQEJpO3t9U16dfvY8r+nEDvR0nXNdl65W3KAsZtgb9rJgKFFVigAWQMUVBMQaUSoKVDltXZG79V796PPtaYfi7XuyEC2ngagIhhLTW7PiKRg0oFQAssB6eLbzYZ/vKktcOs9OZatUjQ6UyHJQi5ONLz3iT/tPz8zmjqWfgCZrS/lZQEwDBKDGJN9tTZ/PMlxEwIMELmMBGh3a4FasQEUApQSZRSeEBdgwQkCn5EMPlN2xuAjWUXKFWWym18+fYnzNNzBfPx/XY67umEyS7r1erqFsYxyi6oMnaoKYhNYGVGZUPYg4h4KCvvqLUm9q9jxSludDEoyJYTYVOHvMe8vuuGODAT0xYEBpShGYjVDhlLdVa3HahCojRmX7s3l1TNk7rBQZngth3YVlIzlckhEgPN2//unXl6UL6ooOP0FNTXGYob71nZ/vuaMpAAAtiLcmHkLDMdb+0cx1V4K6diGCBaFVCvDa2BAbSIBoN/l6k96X1aatWB57PSFLUmUxAmhUIwOAta4DDTAAsQVgkP/v9NuhQxtMpZMg8hDAnJkxZMKQKBhQCal40PDzQHGwd+9XDIbnJoczILDs3K28gRe9Xm4vnlnicffBec6WJ3vLs8vqIUzFsja47CGVJAlERlpHgOIIACADgBoAxmb6tnb5gmq3tf0xnvcKsuO4Yip6DiAAQYC6OK6hE5R7zqxDtQWHMsDQ3pjt+FHy1/b+ZMszj+C+hbx34VQy1Nq9hH/qWj83sj2wPztZ3N8NlxEWLfwRVINRZQDpQPvl6x+HjbMpX6vWIyLRFumTlV2f+qk5EpIqtGDGHFI2yVHwFoIwSGDPyaZKyZ7j3GJnPPAxWd7u667bMB/R3zs9JUEERkA/OQBs0K6R5eRGZLdQiyxj1ldOzSxW5lllN75qB7yHpPNYytO26NGROBDRNM9oBqthtwcOHLhDNCoBgo0o7WTcRAARN5Yt0MFcCAyRUVPrFOg2bz1LYXEqHl8elskwRBmnAD9PfvJkdPs4l7bMk32KfLwv/337q7d/KuddoQD508dBktt4jcK25ZySEKlYiEQBgGVyY1Bp2XaLX1/wh2vrslGetkZfxkM1dZNCAiDyhApaIigRZIoWLSQgwAAFI6MA/o/3zMM+FduAkstEhMMIs2jWKCOmuLANcFP+93scESIkFFFWxDzP//z/+5d/XcQXx3lJbouG0zceHvcJuw51dZrZnmwfz+HRtqoAqLtEYQkoAoI4P64KrBYAMFATGjbaGo+iRXPtbm7lAavV+qaw2GUA9EgFDmhXARqi1m7FMrnrvB2GxWq1Dokju42X5lPu5ZWn02+oL53r5nTvu5szHp32XFrn23schH++ftj/sy/thTbgZfYPQBIqZ4Y0CYMh+uXtAx/nYb7kMaInVym7tpv4MnsF1UQSAQKUkEIKUtpRmQowwIhACMRmKJFT3JuB9/D3qswkmQ2P0X7ggrn4bx8+mIO8gwS2dPqivvZoGllNUJkFhQ6MEkrlUIkb86JYdfiZ9/gHWJoOpo4ZmIBpyKchSNU1c8bUqWFgs4Y/9IdddaMxLiEoAIRsMIfLjUpvY1s4zEOBgAC39C3XLHO0MKqNLprR9quLfHw+//jr0eP//qdZCB6UAAQgyPvt88aujDCKygp9rbMjI7vtnfr8Phd8l95TcUoyEQOEKCkt3TqHmXF3+/6x+mV+/sfnL25+geuDZx9Bv5ZzTFtHPEwuA5QMUJSpg+6wAQCiUD56/vG/ktVFfdsRehwhtGkOLjEAhwoNBN3TcDSz2RE3gCAhAYkAKAIgAGivMDgB+80dx7BtAdWd5+GX5+HTo6/2D5RO4xbfeE/e+pM0m2qYlBMuBJNSQhInCoRQumCh0Sy3eFvb2eQmMJhZ+9osThANEAAeOABQILIgYLALf9AjHzPhclt2BVOb6XUPtd4979ullzCoESCLPoei+3zY8xbXIQ/hwdkhzqheQF3bnwP/2tM/wPz88+I/stsxlghaazpJgWiQMiFAvfwHNilvhxeLbjlBqZOP1Hmfs2atrP2evD6DEiEqiIBhYCRekuMfE5PSJfikNdb1x2qGPkEjC3nePesDVDXiX//j7fffPv+bD/27hbIIokmnedonkfYxYQUNvsVfL//64vtk/0RP3m//1Ha/fo7XB5Pf0DvymE04emb7W/OiTCYEQogYECSnAFCyliSKMGUJSyvoDbBkLTeskEr9oMPi2tee3B6fwSqTejqAQyQJALg8dAadXbYIjIpeToEWrIkLSrVVPtnIGEfe97w14ssRL3oQ1NeYpTAWQggNsQGaxd3p/3b8P3nyS372zV9JfvruW/t5kJanrDBNBUBR8pMnpSMe9mZZChkpFGVVVo8zfkTB1N03f5XWdkbbcTviHtbfSBuM+F9ieXnM8xF+kBGAENMrPegHh0OdxnNwuM9sh3Yua1Exh051Scvuw93BzmdMbQQzZRIUgDCBpCAcBgge7xcylvpqwIrGtrG9FYVwxoKdKS3GvVgQBAXChQMeKFhwMYc72lGSyvyZVdJSJQSwmg72uv1J/rT1xlUxdqIACQQBm9PkFK+lT45Rnv3I5nTXW5p16zryj/9b41dMK5EjAGaGXmUyWWzEE6uohKqhVQBGzCKDU8zkpzmQVMtzvPHc1NyOi4MKMplmSkwPRiIL3bADzeSipmboJD2Dg6wisQAduyk+JFTg59Ppv/72uXXO2nbNPnI1/AT2dFb2+Ib5ZZ2/Xvn5zOs5xKTxIZ7Du+S0dxgO7pPqWwq4N2j2NSZCUkNl+CGnjcjSIaAYAa5SpalqSaUNWhIImGoTJhIhAgwjTR/TtrwZXjRXqKeh0YdD0eDYf8K6OvwDJwCoLTDR2DBrg10VixtMUbzi9nvt76crLS6TBiIO+DJ1AKIjD5RuhBW+hPA/zPef/uLx/gWen2Ify2YeokM7tJStCgpQUADefRAOoDrW2J/1AQpVUVQSUDhMBijoetQRRLjQV8hpSETiJlVX122inHWON5x1dXqddva3AOtuTqzPrV6RVzIILHCrZ/Ce7LOZKpaDUkINQQyIEZDFcBGM4orMVnfevzhKafo73UYT8vX0tDXyjmMjYeEZUWTr568Q7AvBu2AodAjmK67YRbNlTzKoyh6zu+9Bp/qTsPYVaPahFCABVcVrqivn42NY2e2dl/VLn57drJcIGTnSMtNppH7ylRAAEB8gRGJEI3KhsXKuIANXwaOHIrSSJOJ2+sDR90myqC/urDn7EGwWDgDCEUKQaQ0xXJJT0uIG6QAKgMgUEHFGmnw+4U5RRP4KTvokPtm/uf7SgX1X/MrkW9Nf1fwCfh7XmoU8JQ/3M/d5Go+VuO/DdWl1mATCErF21aNmDG3iqUfjCZlQeKYA1oSikASYKk1D/vSjAFQQUMnsIMk4oAjQVfFNouC2duNWmKwvHpFuAgCuCU4kntbtRgliTQfjUXy6YO4+8n6d8yRp8L4+99a3MHXYA9tBhGIHQG/RDekdxv/tjWduXefajPfhybzLgmE5pahag0p+sk8dQWqA4+nRZxg1OMk1HFFlmHQxhRngvj/yM+SINNogaZHjLLPlWuWNIGaY73yLw7cM1rflH7OxtNdOVrPYYEw4Wf3M5sgg6sWlyGXoYQxAogNVGwCjQQgCakwqaayuzzJY0Y5LDSY/+eutq9Hqz2BUWOIrLmQWBguC9sIXLAqFxco28eaYaGJMpjq2erBHVeZ5aGkuQ4bw6P93mF5pzOv4skkaahVliipCyzbqyFwNr8cg0WszraC5Im0EQAAECMmCQoQaqJLn5w1OsbjUhzNVdGCQgkaDDXkISxiS+iriMxIjByWnRTXxNWijuzMRTVY5aYUsWwWsLtrQNQXdjLT4+3++n85etoZ6u+k8B/bj+kr028xTcmaOOoY5411yiOMIEiMrU1gfpGNkMRHmUKCANp2DvgykDdlwUAsqr8DQWcVWCyzFAuPSEBZVQxQQ0MhvR8kfhGm4zhAiBLOefnaDDSAdhS0MlcO2/SJCAD4SAuAl0slKe0x6KcKu/P3zOv/68eIH1pWywhadZlKCd2B14mn87s/07cKZK5MqCj1NWNysCQpQYnNYI3dIgChfI7SUi87rkZJLCkWA3f+/v/Gr+Sb6CLnicV6Xc3GZdq0gGCkfCkeds3lx+/P/+7WWcuxtdYmIVCPiqOCYOu14+O79f+WPAFeA/fXb278TjOc5p1RXIwNCBBRAiZnafLfuWyyHbu534200uOHz87vGaKS8wYI0bqEwwxaltYU5oSgIdB8znqaY2sKSnA3qrmLDQ20ePH+lllKuJGzQxQbG3vqFYrnmOxsFFAAgMMlIKwBl+tIlLth5EJ6lI1Kah1ICUyCQgVJiJWZZVBEKugVLKDXGh+ODVKpRKQY0YJxMdGMSJ3q7nuYYD21dv8L5dayHjiux9cISTWSDJUXUoLQkOWNH3HCEtP8/XP3gUs+ox/0Sbz7k3eN8xTx0NYzhXfI684nMqFAigS8FPk1Xa0wxiZKUGDVZjgG80rG8TbwAmXPHBgBezTtRO4eioOBWMmUiP2UUh0i1bFxoBAVtEBWE/NJQAgJt7h2HUcOCoxgCkxC3nJ8jT0yP0/ZziySE0+mOJtq35wVd17eYd3aY8Ix1mswEGUMK2J2oIPfO//jxuFAniwJFNEyN1IQ4QCSIa5OACAw0DBYpUUIAFQcYwWirJXxa/ihUUo90NaY05h/5br2tCmpgU5defAd5vMjLdqi3HBd3jqB/7ftsi3hVDdiq0DSPo/69+t3+6RsALLwv9cMAcoCsftu0xOZymBgYEqMl5hq1SZPfb9Vq7RXmtrOdjcWQ5TXaOjAQhVEkFfWyS1pxHl+pVO7ktM3tmmvfkonQae9hH75X3yl+fhPLyJZCMhBUePCSLXsXXd0al66ePNoIb0agYiFwpgwAMWpBRRa2OaiCSChK5EbahliBIDZpa8/1IxrKLNHa3imCZKL9FtowoQS6qKmO9X2K86AuVR58pSArWnuv9wX9oYg7GEKEyYNqpXxABVACJerttZRDztv9Rm7XrLGho+DJf/1am+bX0KXt4dZee+46bcd2lYDSr6oXarVRv0JUdxmIoErqQYJSIJ1NukFgWgBWJXvWZQGhQS0FM5RSmAlRs5N2ZhWKaUJOC0VlbAoskYM6bcspU8Rjf8Iui6ntgq/sxf23to06v6MdABsHR4N0O3v2+Tmzvn45uI9msUcjAgaYjizkCzPRHI+FhOxb5nSyBWmADIBBCAIA8AIA1ToRWNQCS12SAl3XGQoMRXkmJyqASjjyfKicC3xx8/3y/56zsV/HbjkbppE5cJtvD2RDuTMD32p5BNMQRzSCj1z2gBWByase/yoK4Psvxo1PtKK4LCbMVUniC7tqQwcmXBuPWZpp7UR80pO3s0umXzFtWa3zaVEaDQu4SBB4bElkOK0kMEuFKmNtfC/bK293ejQ23esWR974/DKbfZPyfkLBPMENbmwFy3g6XfMufblYgWgUkTmGomwCSkVJExBNgQI2GZqgcQVToE2YgWWwdyjO0Eeurlpq8XPJcsYPJua08SWNSfMBf3AHGPEIExmCeNjih2KVMCqAo7+Pv7rl7/wwy21fbbugZSUuFaeuL7tVAoGJ6riD77D//LtXJGoeU497COPfP92Yqwj1nj2yjzXARKOJNMFzCHiZ5MTUHE5GuJkpjkV0BhmUTElGaDVBoRRGFUiMi8pHarRKjfSgUG/nTLlW7foau8utRuTCqtlJ2jCLEiscyj1yBU7R5AgwsjPTj0/FWdZF5LrzicXRJdX59GxEx/nT5zx85KPbHEWT3AjHjQA4EkboIsKaHA0pTSsTD37vYQAAyAFJQAIAAFCvAKKAFQqKUmZiqVQAoDimeHCkz/HeAy/Gb37202Pm8P8cfHLMqzUHMrdJLERiOGw3k3uzrpuuQTLr+Ympq0yk2kKkWg8diOOQTXjmNvrPv41aa7PzrlZHJ2UKM8s88MIb1cERc2cpM8weuyVbzcb22/hZ/Gxmi/rJyQCO3heYYFlJ0uatJ8fMyXsWDI3rkmsudpFo4eF+YF/m9ryRxywpz0uDObrBZRRDaNbybHl2xZJXmGTskGCLHiw0RECenKxRn4/koLGILHQZWpX2yyxhI2jMN0Qmg1F/RBJkO9ev+NVHlZb4C8HjK5SSVCyo4DROoipRHaXJJBWrz9JHWAGN0Bk/K//95I/PeXbC6Yx4aezq4Olrf9l8v1EKKRYNnP4547/QJW/RiAchcTpeCjfukQWmxBdaz5mLcCdjzk4ZJIcLQOwIpCvnK3ct5lBkkDmmsIQxHsYlJswQd+Myu3SpsVo7t6KBumRsLZdViMHqjTLmd/5aZ46U5WlNOlIdeEEAZBUAhUqUFCjAqR3T46ZfcfrtRwlv6JY2Ie4rVri4Wsff/P6xOGN3tzyRIIqFZfYanXfW8+7BsRB2YT5xmhS4rwQQer+6FwRAiSmsA8Ahx5hEkodAlpYFjA8PfslxGNVCyYUW6ZkpcIiOvPDNKnbyJ2u/nnzJseejx81nKvrbin6eK9hQn+KOWXxTvfrDfvATRycaM3n+nd/5PUuz/MNv0zee9pkOMf1YWejJLQNh0MUOFhR07kW5uVwub74zc4NCyVUq+027BMKgI7e5bezDHClX9m0qinKnb9Ggy8frxzfXx3zg7Tb4ZekmGm/jiMIMlSAJU3eivjos4XktkCFKGUQgcNtlngbnwcj35vvfe+bJ8ajxFvstmLPtz/b6g2v++O3r/QO/PSJYSuFxdhbBI42qu4xzvRpGqGAJzNqZEJ5/WO9/PY0M7UouZR0uyv3Fyo0phKu0DBVYfhMbOt/n3f/39eu7z5bcudzco1zIdPH69I4bxB7ePe7UDU1JffSLOqzT1IwMb7IEskBBqbW5i9vTIwl3uaKF4iqaUVysmXbWijSrY7hjpMjQKBUR25EZKIEMhTSlIaAYAA2Y2Keb3/rgdfyDP/58TVQFdyx8meG+3RyzbCyl0Oj153desjbVGTGjotD341v2ZNkeu5un7DTH1bbtAs6UzT1fKKgjAABQBIwQABiTSEMcY5IbjsFcRCc78ku+UOfwoF9kGN6iWJuRGgJuJg0ESDSOSXy4fH/FffKrrxeiSWxipE/MgDBuLtVD9fLLknwSH39lvxzHs7t/7rsfvhSpnz/1eUO9vHVOivOCcdSAQbKLXVyBSO4Z5y0omMN7kRc9WYWlNnWZiAaqbWnLtmFGLuUVnhABCVavaLQX9/L8fMPvh+2Frl+jwYQ61VWVVepNiVijN6IBEQ1qUt8cAnnlUezFnmb6oHnK6HN3dp6qzfOcvxQ/n/f7ZfUqzj7/eNkfu/+0/D0+2Fy9pd4Zph1QN83yH8WzeEEWZnkRmYJRCQShISobKE4OCciOHBQSI0dpTsoshIQaXDZSYBO3Yv2dVx+GzumxbKMBWHAnTS/t81QSpY3gciLTCvt29y778KLtsQiOw+0YgEwkbRdY1VpZLlSUyQqSD+tSUYIcWy1i67vLwa6UjeotaHh8ll771EiAIjoGYVEks2ilroXu+nzQ1zH8AV/PUWPTo8Aw5bWZmzAzyIzZBXQCdQ4+hlcF3+M5E8ODw7m3b49qGneTzZv29mvsBUCJBlXABuoIBTRQbVhNIY0plmmaptOp7IqzOW7HBAbvXInvTRXGdkyNyCN0U02heZyTZcjISe5Pypnv86v/yP/zVz68yrBIEcVkm0yqDRUIkglk8jcXP/X484Pd9+F98/bFEZK4NHo1s9EiQgNBQBJaw5uT52JZLvai+R4QOkbuysqciJjqtI222XEMR5HcVEJkCIBTgGhuH9mnfNB1v+NpvFPVrWq2UROl4uEBMS6qIgYJAQVI0zBxlhf1+uXKufUdlg93Nb7ed7tWl6m0wfASu3XAu+VzMJ2Z9ml2LLl78DXWGSZ2yrmcr2NyyYzP7w764+X6Tv/n/+P6BCFwASAsHEABCwC19f3kY7MGO5/up48Rn3p/tAHAcERjt4WYAypJFFkrDE92BPcm9+DMUMJ9z5f4iZ5jpRFfwKlnFRUAFTXYVE6FJg2rYCioboJD0Q0kI4q8ndUlJCzkITjKruSttz5gYkfYMXHbHqmWabhEael1hRJQrSlO0GxnzkfnV5E8tBg9Koq3bZcY1MRaVO49ejqvE3mkc5wVUZPdfmHe1a6cRlu0Qb0cCaABMQAYUVBD1qUuN3PThixjnIcBu/KYHi/ChVe2M5tk9URHpuNySTDOt/l+2RPl3HfCCKFOTrlb1kk+aZEpnML26Wvf/VYLjMmz6PDtaf1O+jave52fr9bnln1WfbZ8Nj3JrEFOq02zWGGcKKCBJEiL85ilrJyUeUFhcUMIJSpRmIB2SufxOA7eOU8DXS5hqWPDfGE+4X3AT+kWe6lVM9swbunYq+xnu81OjyypwTfuR81GEIUBkMvUZIE2JqENvJyuqq6cBNrnursUIdoM0STV7jH3J2NniTyZpShKBQZjiiHbgmmYRYYQFzHOsxv26ey2vBMT27hARhJ2tpEE6/1yAshLy8ur88tPnr2eVO9T3TVMmtbYKwZSICeHJwsyY/EZB3QQjt32HGYJnKzcbecnx1bXkmRJEGoTXGSQWrxhPfZQRAhsOxAiRHlKWbRJntvDVNxhC5dw7RGpiVYYYZg71a8NhXJwTZVnOtO8MBgACpIKj6cXvP+FD8Hg3u6ZaD3nAiqFC6hR5B2usvP2mb+ec3u8/XjSfjm1a9ynYai1JVZcu3MFGBiBBm1jmCE33pnHw8xhc6NH+lhzqfJKXWzd1aFqYVyUCbqiW1lUln/C+fR93mxgPl++nmGboMgUuAY3yzLVgi712PvBpXJV63pMo207u7PNcm/Wtq22orGu1AUFD40mGIQYKIaWGy1KwmxhTWE9RmIiCoFSZrkrWeLIDTvi0M5O2PNL86QkBGRU6OH+Ba+4f4ib7Yr1Y/VNhfMA8J7auPYzntVevefO5bKXFoQwqJoAisUCbLzDFpyNtjKtzOZut0G7bNR6KkV2uQMRMRMX3d7i4yvzEA6MoKps4QqAAlCAgpIcVEmiA6xA1i4hWTG+ZZorYYIFk2W2iSaQ0MjJOL/W5y/v+2sjYbQJ3DrFNEvqNuZcBEegA5aGSnQNL5BOh8TUbTYG006bbLYNzA1MlAOAsk62/t/F0fHZTrPi57HylNGqFBSAwkMlE25VDmY52DhvSIwnxitIYeDn2flMr1elLJM3p2KjKqHa1ICAZTe/8jf/Z5uN3Uv4fbtqUIwzEZGMwW+857j12KlI1m5LAnw/8Uiu+MbRYnDNKPrrvwwl9bBdhoaqOY6Xt/oGXjmXx442cC3X2J4qkczkdsqgjsvkkiWhBlLQQD93t49wkU+roihVCy0wXP9sa8yev/YdRTBRKkgKsBg0P6DfzyTUlEqw4sKjpMUuWQTdoD+6BQCmxMitxwiCpiAsJUETO65IueSgqZ2nvbdNZ/I+hjB5Lr/jDhP4637w64JwNrH5fE+8p5p3hTHAUYFHRa/RMCaguehSZZWYGiQEkHruMwiw5xOkJpKGUgp0UBuUFIrAAMDIMoMPgkhb0n4gAJDQJIzWAIxaNDBEAAVEUYCKEKmH+ql/sH85/5Dh6o3br56ech2qDVqsm9M0AJAtbBe0y0a5h4I9smSaSIDg5IG3szhJooOxY0/dRXQFdoT27AP49JrVmgEQJfgGc8M5toZPhUwHvxF5u7/Hqp1QtEJrSQE8U6QlT2pnM+vS0i6YqVehAi2GoPM1X5McDkWsJg3UZRdSADRb4AjezPsf19/4f7N7t3+d+XJZpmMLKERh1/KJHYCJYzmsF11HZJJg14MlS0Kqs8uynP38zOtfaauMh2Fbr5df1MtjD2eOpqdyOvaFGGS/7NJBLIalKpSggEYstCIBAIhYAueXjn+qZ/BxAEBQyj/b/fyXrqoSSBEpAMCB4QKydPuMAbqLEAqAAQAknAVAKUIbA63BENeyfMcrlkoKE/vjMvuaLmvtNe6sujv9RoTEr/j/0gdv6CcFb1HOLyinZf/NqlUzy0p5WGGwYg8aElQATQiTU6ciFTF+1JW75pIud0YTv7/exxquTP3a7NSh14BoVI0uBWVkgAhSvCzFgE4K3J6wNRKoN/TOgLVahuogQCpkEAElC0LNqBM5lj+e7afbj86fUUHk+1sr186979q8fML2GXFlAP0Tzu0/T69W2DA6taQ6hkCQJkEQxARJFjnibJi1ClC3I1ntNKhGCxY25dk1s84AS1AAC52/fbNw0o6NY+658UumAsBMDQ8klXls9q3RDeFIdDpWMT0At+e0eJLgfcX8+NoZwjdGdfhCroZWqFCbRiDa7b3h/W9+uvueU7G9zhdt153QBR0RyMs0qeudM9FlPblPhlkCFGuCocVIaMuRN6vfenF49kW4q6abzMNwUvt0qVu5ClfLHU01lEurCohAgIGjOJCKgxFGkBjAoqq4mvlDvs/BWxAoKEqbQxbcICOSJQQJhZc753ZpZFaoDJACFAAJESiCFYCmgRpTs9KiFGdcExu9aNMY68Rx7409fM897wAY0ot47veH+Gmk5y/ktI2NtXLP93fNLlWYdNRFji5sSGDYYSMgAQNghRAtJiZEUJizutU1XP1AUbWtBobqG98r6+mezKsirgzQDIAyUCICaLGkVYhsjHb7ZXJHHqivrDA2VlKDKgva5pnY1dF4KMFnljuXP+2eM54sjDo1XcGa2M8tr09uPuPnL/019z/9uY8v6BfVxVC2vsnPmVQEKc4mhFmKBytMhCBPSANhsr0MMgglE8TBhcUUPPOiSACWC2ZCB8Doiv4vUmcLQkJtjVX4mtRgJVizyy7zXsHl0gWvrhbUtbvKjOn52MJFmrECNR3k1SmFAtWgicn2bYQZVGuzVNPPXvX9V2b+6q/+L3X4p5WdP17CpKEMSASBMhS17rwyeQ5YbCZumQZRBKKAHpQJD785WX/1yWKj5cyUfPX96ulL7o+eejYxeCh9fGe+8FHhOFD07giNljRRLe10UloR2VFA1Zxzz+VddKmmixdwqG3qvc3YGp2hNaK0NpmASWiGYP8/BhRsY4UF61GmlMm1YogYbcsmFTTEYR1iCJClvJlSd6CabkIFYLX2wmnCApVVpMvn/49MsnEgwmMQ1vTOBIsT7BZZAQxFQkoRHGERtYYGHFSLJ9SDLTxT5MXi0zy/+M1u2fY2ktXE6LSnbDZtMq8ESYYyL9EtBap6gBou6ECoRk3R8iSUw8puzd20bfy8oAe2DZCCqr4gJnven1BeKoPchSxudP5Y2VgYJUzJ/r8zv7178WO9z0svFqSkRN7Mgs40OXE5r/BUPRt+u1ONqdpiJBjpeS3UXuytbrYLS6IL1ecDSWKliVMra3MMKYLLBezYZB1DtcHdPI/lA1HdZysN5Jeh2gVta29B1g5vlBCjXEeJgwhGCGmOAMAlV7TnyWC2f3liRAlIQUwJLBN/8RZ7mMxcDqPShFyxJiQFUMgWeKU8+UcvruVF/b5zlexjPq9+/gyvkideuZkLpeMtHJ0qHkUiAldNimRGK1Jm5+rVBJeaAoqAkZElBZhtG1z3MHYLLmIF2ixgY6W4gJttogiZFYhiFGKEStkmOYmJndemkFSEiPBYwMG8eB3kJXtzKjQsL6GTcYt1pnGmz047ikCGTGqyYQ5rD4F0tAHCrOYqDlcVCkbiViKYKFIiqEdM0NF37HPsE6XYSA+qQRDoev6j45r+8PwzbzRp05m0kTETTVwxqHWMHUsGkGwkhAuMVMUad2obHONkHs+d83GHaWGyWWUD2AkjMHfyU9GXq1tIk0t1LAxVFAS29yUKZkFmYuGV7W957ozXrsqKJFkKZaM8LbI9HXSqZZZFDHnOCuR5PbbsjON5HgESVMWqV6/kuHqm/ohQNB0Auo4AJ29ltdW4rn3OjRfpt4t5gtorc1O2AyzGjnRFOna8bR3oIY55pk9reeZk14hseJoRssQIuTGh3PMA1X7E1xMmAVZIhMSESUP1YMsRlnlanx0RUGlzJcoGywACaLZt+X/Bx5zlS6tbUSEIRa4wriAdh5s/R9GB3AcABFICVG2iO+xdObd2VyqFErWLGu9nznm+2bIedDEWm72ZnJU0pZoaXA2JRG34RMRSRgMeizEJ9e4Uxs3iZq9QqKCjB+Qil0GKmwPKl0AFQwxC1JSPNjgzMK+yDG98cjiGkPHpdjnpzlbPcX8Th8mKG9j1jnHo4hkiUb/fqsesg5GoRBNWZ8x93InJmAEPCBA4JpxhPvTkm88c/sgH9XBjykyx1V4/97J2FNdoeclQC5YhuQWxVBIUhuWxOx6SUztBYsFhhJm8WW/CmM1tCO/sG9HO1rmNrm81MBdo7DlApipOCqap34L8Wo9Wlo87FNvEjqqJDijGkhDE0LEcwEYAa+ShAg2GXo1hmlViSrpg4HsZ3WR+Oig/70BIRgowBVUprBfkCFqtSG8+18O9mM1hNzBotXIGINLBmqzCYHYgd76vHU/tLQGDByoRKdPUb59nuKYP3b5cj4YZASIJIUMGwPd4uPV9ktOFjnwHiQnLXPRnWWx+lvTPm5SvZeLVH35tJcRGEw05NpIuBUwU0S3AwyDuzMFAYbvb+Lng2qZvnN0fHtadZtlBKZIGm41lX59CeboZM2ZNWMrhyNyaNlDNakpTaw8DDh2Oi0QmloxqLywasKVCCargGMA9JKTC/EiVYfGCeDHdvLekzXJ6nsWpgPz1dPt1c0yJTZ6raF52PYczH6+eUGAb3he0aH1F40nsADuiauKKm3ez9nbWF01vz3LJ+UefaUbB3ElPl8l8OOOpcnAnQxu/OFk7BJ3TSYeraRfDioJeedOdHpGVRShmAxZADUs4j8fm3FmkrKVasopiTFBn6jFh5HqEWe2iRcoSAlN2otD83OQj0jSPEYO6s3rAO3o39iu4/AEhJ1RA0rjYKNWh63K6pdMqMZ3qQKltQ7kKCTTxAmHhQQUBkS4pzR6Ti7l5XSBPVtbVHZR+54ucutJoRxS6XDuGOsVxKSLte9VgXpdarYCqjTWxq/0f2xmKWgIsMgiy7pgqXWjd23io94W1tNgBDlSEGqSDmHSMf/4un1CWMJ9BQU9dAwAooNCerpO64t0mbY2naSgJSuUyhyxOHXuaJHelun+9fO+yXdimGrs1pztqmSZ0cIpCWqKLctEaZ5s1IzPvZV00R2DBA22YMbYrzsD0fWjmYTeSh15fwYx4nJJiMQ5BKlSKr0N6aa7UF0oFdkfPh7h0pzn3bLVspxfNBAtW6WF/MP/Axb6MuP1wutzf/+Ma/uDiZb9/fJsuLAXyfr+SXbdNyxFHWs1Xv/KrH/89gafKy/Pn4h+du74+k/bhcH++/oWf42+fTk9wTE728EF5YVZ32mu6Wfiy2oghAVHQLFQDqxJikWGJyDNJCaFjj+lZTV4wSlKUkUBTDFKZDPk2m22uE2AWBe+KrhpSpT5lmHaedhb+PwmJ1KPKvM0E0VjpLZ5+B3fGb8o9IRI0RRFFOQUQg4Ay4zIhDg4YeX32COZ7iTbdPCTGAqeKZNkqZJ7c1XNdEA1J1BhL9AwpB8rmBIhS+fazTu7xc7ePF+2yh6606nWtDH5cKFoQr6LnqrryycjaKsVIrSBBgBdP+vbqPVDP73QCv372gCgULGQPCrrqHtGb8PU7Y9OOk7zGQRgRgEZiMTHSbmVelS6VaaqLldY16H2cFC8mReUlmu+/77qwK6a/9axt1VP3z1v8tmVKXeysSDm6Z6IIZJXBPW3mec/3bG/03OY0B3S+zT2nN+1IvepxizeXF1eubw7buNXq9JXJy2YfXsBkSImcG5NyjTJ1rEmbWwN5mtnVu+Wl6Jaldl/N/PiBO4+1Q+8yrrdf3I+hTnEot7L93L6krGYYUtbEuG72rxSYXPXcgYAf3ozdK5SNKh4P2NIiw36VHN/z7Hu6Me2xvs7Upg0VeuFYhSSQEg00HkwBErGhwEq1uQhUms4e+p7oTEGFJQgq0OjWnhZIFaNpPjMe3o7Z6vQ4FaIh5xSmOtVdkLGSnVGNfoFfQWBA5jA4bfPvgd99WuePUyscWzEUABiLEhUHEsgtwTFgOrJxnFMh1WtgsnlhB4exEOaO1phbRhBM5+IhTY3xdL67yTFROqmNrpVZTUvK1yxVaovq4+zO87FRsUKH8tqKRjAi2kpAJXnArPKjjYAlqIr7odVHHDvtMy7FsmzKFEOZTXET7ilqyrUe6bu69/TNxj5e++43oMuK1aqEmQnPkhu2gGkzrhaXhKa8z+bOXd3qmtxGGz8vbqNY62wP9kAfAxNPkkA6C71x8dUGDmmBToB+z26+N3padsvE0A40Gcd/+GPj+vHl7tXu9ae7W67UpteKMaGLeMh2iqPN3uJ18Q8fhL1+ez2zTipqXAmCtYrv+eTMZ+1Nm7q/1H67eYH84sc8Zvw4O8ywnXOlnWty51vi8aG8198xCVqyABBGWBjRKkYToFiGlsI56ugSRSYsyEzKg1K0JUApVm4lssJdkQwSKVAXddWggDNW39r0fJPBt96+pgudjPvVuVSgY0YbtVI00k1s+Rj9S8A5Lm+TXr3pHpITUHRKozWGGFBBh+AEXtRHdCWKyPBkFbBaO0cDX4BKq8KjlWJF5kgEUghO1BDgi0KEnPlMzdRtPzX4wTaQVNPDm2qWQr0geMCL0fUqgFQ6ULwrCZ7Uza5zCVo8PllFbVRNu+rxJKljsks6Nx+ypJDM0mFdFme3VWdKWVQI7HN+/rWslv0oZ7o+54gtT42tZC8xF3mhZyVBCwirf3lZlz46he+cnU/U72yHxQDvhcZtbnZpmLokbbahmxx4G9+m7bRfGwqk+TnYwx29tSLeU0Fy4RIgECCwiW7Y8WlcKBh7KJl0T2uYcao0psueVvvNt67r+ft1uKcOHXZbltIgpUqJspY6uaGd4vN8vPs4JTp8f33o6SfXFy/Wu6rbxX+7+At/7JP9rpzc7hZf2fvP4HzC+YMH8MrLF9tbWxgxTLjHffqn/lL67RePX7CvJMHKPZeCgYtQvtVlUMeG1REhyl3eg8kqEImCRSkjxyJhCoi64gGAACAjKKIqoirS1ARqjvpyzvduvS/66ncObFxeq+ty2YczoWcczjrDse/cfr27f5nl8mgevNfc656eh66pdKr9WemqV1zQCqFBoUYYfQJSFhMZq8BacCWgVqxFhoIMykkWUTtaEQVBLe8nfMwYF8KhBNMpmIhKdv7xf879yJva1KBqTpEI0BkwjTC8HSkiWSwSqWBBF7ZpNR6I4+RUJ7xa0tYLCC0SC/Q6p94dVaUWbZwWECVE5ulynpbs6iBImKf7pR4z0/vzw0toZcChVy2uEs/nuACUWgmjMs07qy5/6eCZ12S94g0VlZ1TrVPEXcbEeSoh+vTL1+ob3yZNttm29mfAtN4dvSdvsSVr0AYEzbgwNYGAFChgVAGQBdSROAFmNwOExJkMStaLsv5a/gDwwAPLXM4P9SOiLCApJDBCpQEMJckMClHkBndm+zOl158ffFLLfKa+vR+/7e9tv7O2C1dJoGiQTCVhYvx7j3+U++xj/uyeRR656MOQ3YChFlqO6c/xoOgYdlQu6YHFz+gIBpCeySqxeoMQEKlKaiJ8tlAA8x1zIm9RwqC6tVIAi1EqVhx0kagBMyJKOpNJ9OU8FqlWbcXPamCe2JxPH959fHu+WR6gS6Cz8NyPx+yvMJ6UWQ2M3ghgFm95+RW1pvNUZ/9M3HXWggPh8LZkjgFzORpA12l5mmf3b95PCYwCElvYGZZDg55SHZi3h7WmjN1WpHSzJKvT7acLn0YwL+XRCO9meR05THCiIF/bvDxPDFxq6woZ0nQyoD2VDea5dwvseD3sA2UMqOEhWTm4LEJdxFK1tQQgjXUCwFDYOOzTff8tr8j0tn+bf/kLq5vKajvHzNIE132LT9vOz9f5+Snd/TYo1FkQxTMLxEAVasvcyzptHK+Tk9xI4/lrp6t2lCffaQfv4Pf41jc3kz6UVChbYyqVwcUohtZIEUWp6AEkM9JX9s5MookSH9EglUvNyxYPJUk7KY5K2VqjZwBBxNIGFFtoAGOJEEuELANoIjTUBwJKHvqybV++qQnPBJvGa+K5JJOUDh2x/kL4Nzf/fDpgkkWkao+t5PTRZwioNZk4AaQO1YizBEhWFoQEKJ0CBTQKAkoGp5vN4t02inJYTbF6MAsJlJGI0EAMQBCRznQOoZKFWBM8WkEkZye/53se3nN4ZnwjQVWMimsgAVmpEEzTPM8HD3E+T3aT4M3vXv2urbsqzUTUL3z847j5LsWd2aBY3K+r7uP1RAio0MPWJU+P4DFNViGwYW/naBtcwGSZxzGGQzVrHMBSiidtqSUgRVPSVZBsv1T1ZX3cVqFgFLXKrGNCBlNnF06Po2bVZ562oWAqq5I/tM/rgvEgxIEVWqxSVSol4DQSF7G4xVECtjWrDhSuv/FcSZ77KmDfObAW1UCluCd+oR7z8zX3i95475M5l0P2AGURiHangVHN1F2aNlFncIZxz/Yp5N7j0xMnWk36Hi4EAG+B0QC4GqjaWN1QVEFUBdU0B4wIS7x6DAPZAIwu4FAzAxr+1CslEOxN3a3IViq1CkiU4pYh2ghFAjAgiCzBPEgCW9YIvZ3PmLKJLeCDz3f8/mN/4b4pyWzRWB3sPDa96P49SwVfNtPAg2CSoQARIkGQA0WwroXCZMGx031aJQoGJJmIJhJBcnkkANT76b2QmNBkOkDuMOVIKhMASgSMiUxmbHqTDDbKmtI3eoZxgR4O8qxzSUpQQu0oUxx2ixUVwDSZc6VHArOT7ZwYJnrD7MbZJG/ylRsuYGpCJ+KnYfsR/4t5sFdBRDMgFDxZ6NPjLy0s0bG1xrzDQ885R/ixkZkAoYMlC1+zTWSuFyI5yt5u7G2wIY135UJBaT1mUWiiXhL9ZUxJmizEmgaH+D5QodzayJyG5RheSzBRr3pp1opsbEZaSxLHJgoNI3k+d6lBVxpdcIbHP/o6jpRPfrqv0RAiy30KbBqHP1/7/TJe2d000JUpB5YZUwhBasZW+/Rjx+kXHZYgWdZztCOnO/zJ+yAVSMJoNhr3uSPeMWjVQFFxowGlBroVBq26mpVdhg5iQKN/yQYMoSQyzA0ojaatoB0qpE46LmBuq7Gm0UrCxt0ALQtFkaAEAChCbggJ8g5bKQ/QelOsYrm9vOLf/Ha06/QqDInpjtGaHpuO9a+s+eQD8ta5xkCHoiagEgqSrFFVB9DNyYtXtdFHUJClZjIT6S4tCIdooYAGp4qEKt9jozBEAQvREBsZJ0Z1bslBKyN5LHWOtUhjMiiXzhnHkAlXlFAIwJJns4MqFEQQCIGpQKrTwz2msDDK6gmThFKQJZQ05kWuY9+0EJqG9578HD37qylAoADAzXZkFuc6q4VMBI4NSiDQcupVTtFDTQFs4ogbnMvm1dzve3XvgWCoLZvxC52TLHVFuF6FfBqt1biSKB0o18Gvotm1g2VFb1psTbl9F7FlKWGs+vZsXgDS06cREKgSj+l2fBgGIe1NwIxBbcr0iy/X7/x5VoPqc0pR2AZPxYNiiHnj+6I3GjwbGNykuiSMccIjDc46xjldHty2bPme7NQutEmc/dpP/ZO3dO2XRKEw3tSv+RcqBAVUDRpVNFLUjaTikA5N18pM073Xdq3h+S7Ub/T3Ni6BDM7uzzK/pvaGe+v7U26sLBeQin2szmwPljgo09gVWIMqYUGlDqmMAnTLPXMtv7Sf9fwTX77fyiYtBIsRosCGYyKemYJwaDOkwvBOWXz0ZPfZQQE1YEgEU2ECpgHFUE/MDr02+KqwfXzKGg3S8xUQkkYBkUxdNSlUEsSDYCAs4sIA+J0aH9LSQCht94dXOamW5Cuzk57OOeNwOmsQSVGKoqIKFMtecFBDqRIpxpnBjKtxtQvCZpEcJNCMBAhViWljeA7lEUchfmCToXGi8ssz9gz4MDRSxyBPBu+/kade9GYA0XRvcA4xNUjqqsdiOq0gzaMZUs7podk8tsdLeuKOdNUllLCtKUCK0+R77Xu8GiUF+XVnOAqdsZ6jNpfgZdmTdrDKqhlu82zMmYqYJZgsqBSZBGLV0jcka2kyGSg0sVt8+SW/8f+eR9c1OW2iFU/VIPSt6fHwMbNOhDli7GKPW/j7VKX32oI8AFwbzOjOuRc3m6bNGAHeX+6Z0pb/EoQckEp0A/DBwVxlNcSs19Q+FdeXA9RMqTnZjzfkZjzsFP3HpbvinJj3iAA9S+A/oPV+q3MWU6WzHA42tHlsjq7TJPq5+ucTy6BgHDiW0tcyQmXwbMrX9gv5xd67IX74+Rz+uR/X2xBpCQWrdMIGCZBAqckPzrSlBBUw4xgiS9qZLUUoYEhEbp/kKQsc3/Ujm19NerbBJxPw5NjojCDdyHYAXiqC5ZXnV/u1UpS/P6jN2vLpEigeQYQSBtqOa/wgZU6vdtPLzMzAfZHBfbSKgkvgsq74kKIjnlvqC0wRP0q5WE8uQ7dWmKgOqoGInCnzdC98S8aNkzaTs9pGyWmX+qHc65wqNeVl9ZVf+WeI3hEP8h1jHz2venr9PKnwKGJGYASbkyY2tZYmIhpsmMootVHmmxX2ngn3yERPewrluzLoCpkKyhLX2/EMme0ikLF92tUn+dZVLzg5AkJCK5BjWgDTAGirusO+0oJwGAUiJAIrdSCWgoIVpQc4fveXP/LxWnENQqvpY+7y7lWnSiBuKuoXIEUFBXv76xaZRFSimwyHAnZTloQ9DT21MA3Zzy1FOS4Q6C3iKFr25Ar091O2A/QrA1tI3udg7uCms3u53NSLbqYDngQQpFR2dDXPHJPZCt1TcQ5q8Kuj7i2eyCZkjRttqwnVSONIhLqNcRnvdl425+Bz+ulg/XOr/LVBmj4r9u2ZX91+JOvY27oVJskCMcCFwLAXSsBInLAFOuJchg5UHAcsCGjmJgFKSUEOGDX+Z/zyT531dPUIgDmSL9OjvjZr371c4qRycjpIvz+8FzM1+3LTfHOrh9pV21o1Mw97uKOv4eLmMkarZuwEl3p+IkD9YJdLCtJXd2mdsM+81GM2D7h2/1gpn/W3mwYxKJ3SQbGbvCetM8abF95cyqxEBErk5EgtowhnzJuZ9dPxPduXyVqjBngEGqIPvkx4dw93i6EdGYA9B82gRobUPLdq5jINHcMt0mijEhIf0t37TcZYQgBlIfNLkFzVaHMB53PP9jHDK6264kOQunJjuF1dbWMqNn5Mq7gIQDRDFOc8NwhrkLzFokq7nVummFDU4OmrM7/2q9udCqNya7+Qz8Wn4MLetHftpMmjjYUa5qymxxeZihBgFJABJk0WbEBpmF3UyK35EkMXt5iEEVfxqqZd5vJswA7ifHKfeXI33PTc3a95w20/dpPaFFpoGaKH+HhhcA3FF3Ed8XzQETq4QVxZ0tyQAEgWpaQxUYMBValb3e5nrrYv7ffIt979o+P37uXH6XjPxnuRPYb3y/vI8fLheHpuLxCoRzcUALIgAtUI2umpAg3isuhIPe1hNgpohFwV1EgRKMACsPXGf7ppZmSt3yVNq+v0b4u6msGr3d4GN2dq6w3b14Xf7XmvZ9fGPt/7uftZ24de432/ft++e5XnlXyxvf1kPyc+n26v9qP2kQW7YooBlQ6oowQGZIyeD5/9yW8N5fV0bf4Av9zo27/5c/bgw8z5UVEwzXoCh3KUN8q8UhlMPRQTgkIgwNNylBaDW9/8Lf+k3lLq4k1Iwq3Xt/m3dF83EBISgttyAMNLBN4AkBDDLOZZZrCCzOXc3rtxg7kJUW7YnaxEf22RdxfnuQvdsiBEsVyublU/7goumE6C8kYyG8AkVeem9K0ngfG600l+17sK0l1ArGpcRWQ1CT1V3XQ2oXv9xV/b8LI+xdeRa3jAyUaomjSsRqhFwDzrKRuoTVl+YMuBUZLCSG0pu5/c5y3MmZtTFCciRMEUEBIcINFBMZ51WVNoQwKsV3pw6BxKtyYXvJYu5bXKa9VTbbTVskA11KBzlzqLOpAReuqdd/dnGQ/DDGvsOnpchEo0M5mwqegjGGRgOSJbcL7yxbl+lpx/9yfAffLqY3z9gD/QH3ffbs9YkB1j0KRS8Yphia0Exkgv5nH7o+2xtfe47o6ypZOSOEAoADMET/KEIdwvl38vbi9raw1MBzT/xpnL5YaEBowULLhQMKCYL2DExIiPWEjNKaRbnrHrtC4Vprp9zdUrh7rT1cwRUvhwSTFgAAloAlGQOFCApRGcqrBWmMpPHmfZqKLMofCb2+Mvp61MSoQdfuxJOHXn1PCNNABgfFHO+hvcP/PI6ZzbuDgMOMEnM1yzqK9qPdlDBRrZztzMA5BrVt+P+t0hrq4Yh2WuaHWOMOW4FfI0rFEwaDt1Lck0kFKcN43wKpKeOKCrla60hspaYm2a4HwplWAZUZO7+/s94ruT8tTRreI8hGbdStWvXDWVXMfX05BVEGyrdooYKk4VbYXI5RUwY5ayL9wd52OrrI3v4+d3fAyu3vTJR1yIm/3WNmiZMBCkICsiIQv9iz2R2fhzdaaQNaNoAQBkEIgQUuJTL22rKmJTbVpNZShTAWZbdn/IHMM8DLAV3tGgQEucQpRKidZogaJUuCSRTHX7ah8mvIFFnnmzVKjuQpU63Ic0vNC1nT3E2q65+TZf1v7eL/8WwP8NIu/e5i3nPnufnDCf1ooFiSgABJpAYICKtLkZoVEJ1bmnC3/8xR8V7ff4ilPYowFEYAASgAJhgAFtkN1ms8VBOJBKM4dBIQdkMHKDPvfcgoM+8IijO/CillIGME2eEfRx5dtknBl7pp12Tb3SExGyFigCgEByiAsQIu50kKOJhq9mY6bQg6x+HkbyJNFkrQKKiQOPBR2gBkGiz/qODACApF/IXIkQHZ74r/f44R/H4udo5yhci9O5CWicMl5Ttzk/lSycpGeokwSzJYba1d/Sfyd8jUmCw1bDUo5z3YNcHQPCI8pAipacoKfdk9Qdpj7TbJamZuIenIpwrGPReigFoBiYTNMMO1zvgqC+Cwyoso3SWghGqwHF88lAR8UWYBgoHEWG0Ag7MkuphK2qQhY0pp9nHYGZ+zxenbaSaJGfrRih+K0N7ySjTFB5Um+CyEbJuezvOKnx5NwPM9/gHS+az2h1NMEwRseWQAuEYv5kNrkEV6NSyYHrbK6GL1ezVtFIQQhblKR0694FLdDSp3SVi8hOMbM46T7I03RwAqFoxbVsijWVBCah2TU+t5ir/nohXiqA/579cn/ljUfsgz33V059JkgBFeRcoOHw9r6tHn6bu+fJrfvCQhOv7vd5L+VtXJUc5/QvLv7jhTaZsjWYkoSiYUJBGMGUYkgIcMVOsEQxE54/5QsmpkdUpBheFpZUZr21fOqc+S3TZttCmVUZdmMcmYtfeHX/aK+P7jOhRBcjJJkixJJaYYg6JRIA0gwnZCvhMOPk5NxwLahyzgRNSoM3aNMjDuwn/RXqNZYVLDCVsCooEwNnDOjhUfAvGi/+TT33SM/A5YC6OlKRMZUoMWo95OSa2abZFAowifut/zjpnbU00Yy2KaOKpJnXDSdG99QDWDBLQLVL6IHmZY7N0T0rBSIBsopFNTEgqSDyzi6D1rtMxJhz/uf1r5ssFCwNoaSUjFhFoInymEy7aHkBVgqFcPWJmhKIbjxTwBSr78bPmDo75jVqqjWagTd8npBZmVH307NQrDnjReMoCRTslDSJ4Kn7Du+m3Ycd+SVeDqsqhnSgTctYWUQ0WMXCCKVFS6MgqGl5c7b7YZ2c9+q9kcVkGlN1FatRjUqqXOkSHcSouagXcRaZaqdWaqKNqgLHYu3aDXu7erX4ZH8B/isA8Pn6hj/fw/3Q1wN2ajUXI9DHIr1tyRtufs0B1t7KrlqzD7lmowHYqjf9XF8mF+XN4hfoZ8zk/sebf0v/D6jAvM6ZRRYAEigjMYGCjAYj4WdlDZ33yDLPXviD/vixBAUpOMjC5yc94Y36AQsHc2DdttvRMM/c1At5xfnyg+3rRWWUoBQdQsFhlBtCgAw4pMmRWwWHrrVTAdY35tzCphHSGpZoTatOjoHfDj2yMSfRYGqYfWBF/BpQpJ96nkIFTMp4L8ozXXYbwqQwuzqbwW8khTUShbEkKX3qGPYwlWyZTf4OCgKKXkRaWaE5FhgtSdXwAM5GrkjptCN9TMiGcDIXU7iK4TJNIkN756qRqoqnAC+sqgiXqg3KM3UOSeAc7eZv2quqsAAFbZZr513g5hUURaA1zGqj6STJLmKLYXZsBVp56wX7Oo41UH26KcqlYFBs+IsXcimjxNXYazX+ImBQ6KAW3rFDtbxoxmTkzPXzWnakYbiEoz3BOLI0ti49cXOVKhoMohEKLhZQHCqbHz39U/5OxcjvLWidMssDjnJAlJlX2/oL3JHPvIJGGDSBMsEzrH1rrsNX5Nk5l/uvAPjH9d7yTB7Lo55JpHZiZ4DOdWSUyKqw5inDT7iy1WbLxMBEiMEAEAI1KNGj/Eb5CRbn+/BMOYR2zJ3Ae4WzjwkAAOQvi+EThoiIkoE2PoEkgA53DeHJcc1d5tK8QkUTpoMFiBSUiJr2228uZj7XV7uXW990M+sk3pZESyQaRIfllt6Jne5gHVHbpOibOPs+caqvVlwf8UriEkpOiKNOqL8cXcEs6PwoCgRuoP9Qdk3IkmHU++QE9WOCx8T/GxMAANgo/UcPVi2aYpRw2vAty7N/1nkgbqlvKCFC4VOFKUSKaD2WtURRk7n7i/gaF0dI6rAOOQxG7vHkBjUQRFPKm3RLIGPBm3xgFNzT5q3agxZvtSwRliwr0wrw587qMVGtY7U1KuI11eaqS6hmD2paGqVdz43Gqlvp6hKuhBkIQmghsBwWMukmVdXNyY8xurXq2ZCv6MWlYo6JKcF6hYO0lYdFB9FFyZV5Ycz6ptGAT7IoD94v36befN7aVrUv643/FG1MFzhpDn0fnVMYiyJU1jLGWMkYbpnNyNXFu/+/f+MVBcJ086jckF2yoLBVL37mbPGt6qrp7dw5invmvPgi+GH+MdV/ubrNqc6CzOxElSGDHuZrkqPUOjqNToMpW9uSUTqcJYiC5hQUMgrmKcXNhpJmUoFQSyULXsS9/BTbuFSsouKQS3cVB+F7UQ82AAD89GH9vpGXQxJlBBBQEoF7AMwJT+YgTX3ZLulzfNqfcfvq/YQvvcv00BmGIQyiBLEtQENXuuyji4MeMotA3Pxi7H/99WPy9fN3QR2KoOrDZzwdITMW4YLMJnFPAtCZ4O0BFQ4SzqBniJtKJHUc3Dc/linmd7/Qt7WoGHAEsnjQ5a6x2+Ph5a0g5wUvqO5Mv8k/ZbWd5rXV4UzlZaHnzGwsWgBiY1nv218tJ/OQFBYFegloaSdjzc/9YkhZ68xx99x8HDm/NRyRomFpV3vgMKnUosLcsqpqyhLN6lo4ngTU+J83BXhMFditFZhv4KINgoRyIELCZqqSGC6o0EKzLtrcFZfoXLWkTSeF9lMCQEMuIgcXBgzL1o9Y1mEtMZMZNpVct5VVFkIUIffBd7d6f+vvb2y4X7q5KU8TNrg3u8/uP7O7bF5xtQizHXCg3bXL9bhcpaUBd+h2Tc4nfDsvv67H7/uELYMDaa8tKKcAMJRK3ZT2cuYr+BH9YeXj1cnLjwVtXJ2CSQp3WSNqVcoCOQpnpI5TQGGRTUwEjvGutRZaRLfB1NMyTj1nwesKMxcEODbxhADgqlEaqEWK/zt8X99/2Z4vZM9nlLJlBWaNg6fAfq6nJdlPoQO4IyB5atnzhEaQjvnSRpwU0OM3PnS/X9ufsiYbYkkDTBKpFAq1FupofDCtfhM/geV2eBwBk7nWOPuk15Oeio9A437wD9IBgFzN54+aSeRkLhMrkVxwIp5J/fcwMP+IaAXSaTt4Ts4za2aWOIHfFffDo+Y3kOVIvgUg18Of371O1GzzRDSzT6M/12thWbZB9CEKVV3sZ387OlPeaBQZ5BJQjnBjJA8BhGi9IPVmrV3vBa1XFqljgHLkBVuIhavikjpW6cpfDrIKS9eQJVYcVNpOSPQPY3pXasmXXQONywrZK2oAloKFWUkJysGG2KVjlfGMxMQ0VK0zn05GHAxqdqaj8PUutRi2aDHPWr57os36rixD7PaaC/Y4G7HCRGnwp8wTsKBYI2dlBA3VkFDCB+ezXr0KL4srrqNsWLjQRmIIkRzKRbF6c7H+m/8tOzuXWm5597GY1C08fir/PPxF5/LX6+t1RCtEIY7ElogiqlaBNDETHO4FMPFEEGBCcxtppgyHJKeclUYI8cSJkgTCxGNemU4BU8oXKWw5MhaZ6CQncbk8Gvxkjz2/AwAAAO9fX4+NE8oJly3ebAyNgoRQLSFnht1PssuWegijwddOj7RztE2aTXLQOSdM29DaG9OGFbh7pd9OZ/iZh48f7OA/nfvP6/3Vr7/9azUfgIb+D9H/eP/Le8/fNHQ6ec4TowhN8EVQEQL6CfC/tHlB+2bUmbCoXjbKHbSwLCp5uaID4n/jDoCG5uVwZDI9FoMpHJMDV4+82HBJcbk02JzStvocHf69/6D2v/OfSy2OWZkvX/yjt/9wLr93EXMRZUaEPE3gGmYY1kwAHHZejQ5KjNDSforsyRvU0MAWSJzl7GB2yUK9q+xY6Bu2ahNBXcnGWP05f663e3iaNVBkkmPSvPMZ2WXTUmpQDvM5AICEOIq3q8RQMXjLFa9///vPRyfNU3kjTkB8C7FuJ62Fay0KwRZcz6dj68f5+AVON3A3QUqg6vBxYQwFTEXSfcUlo2t80wZv/YonpG+TasYdDVMfXa+KAvgER5IVOkgxxrIiC6Be4eX2B/v/n9NcE/lq8Uz93BwetfvYgwVymbwvok0ZpQlqbOWXmlBf6EldgxmFLXSzf83evF148yp7n3zZ55nXGWMcv7mzQLMQMKxUmG4YhGAEElWy2plr7h73/PWhW/eKrzjogePquH3Otmjr88u3n8UE3pjzskc4E42zGXBGGeQikNEAEk0GkcDJRgngeRLKtaATJ/VGjLWeLT4vJExP2/Z6fC5sBvcN77U0VKtpqKxOxlc438r68TBxOebHEjaQU3QFqoMxfzSvv+S350ldNOnxsPmhzI+my3P+ZivzMu/n+PFxvMLGWU4273RhwFP8LTSXNlz9Cz+Bt/ydZu3dxfk6wY3tw9d2//8P7xvjhtmg94qPnrejk5hGI0CCNzfwgHqAUAAE0m3KNfyWIJWGxJtbYOCFmUTNAEDAeIHtENDJ7LtZp32ro/P6OKrnivw5VFfQRv3uBFqYOikA8tpB8jysNKfozNp3keS6o1ysNErdRbxLJ/00AjbucSJDiZGhMSEjzLuQt7ODx5BHBqagZMjkf/s/f/hfIPJiBhssoJoqsQLSgmOrTV2n0fHC6Kcy5vl2z3HPqIoD18edUVMkMGCQGilFJBFGiXtYnZQxLXJOfNvnHiu7d37wp/dEfV8f+prPXvr0ypZFPldeu3y8CUwYC3Mg1gSai9HTgjHMqkJzFORf/yY1YVKJeD123nxN7zA249oz3+IySpDGAWCwGgoz8kySpyRv9bu4y6fM4xP6IgOf5DN5hpy0tNMUP03KzFPMuwuFXBafg87ToIgEkCyG0UUPQW6Jw9JMAApZYJbxbaWXByyUnMWBKjR0aIklQQDbTj54ruPj2m56vRhlOGyPe5EJrQsvafmCI/AvOUHKXzFeGlUyBxLH5g9LUyuEwNdiAAAA/2bSNQUCptR77oOIOtS2uh3jp2v/gtgfnPU+1fm/feWc6CauPL7I1o6OLYjBHcnXCD8YuuHL49e+hJsJkJzm/DR6YeYRn0uRmBIq5yk7qbH72jbTI86IXYHYG11Y2CczDwqAeD23kCQK56BaLZj7GqPQdEt1Q7kkMH9rr3IBVgGyUooc1rl2GS/Jq8bWaBvkYVUQRXMDO8VOWjv0wy0ZSnJsBAKbcIuajF5e7UXhRGSRZQbGHFj97/8XJgW6iUMMWUKLnUY0GStVKjUqsYPv2lYnmuiBwIxSskCqEh2VYgZk1BFGpuHho/yzZNW3mnTJ02naM0Gnmml2ZjGnvKJ+XC9/0FBaix8TbaMghl74ONL85OMeubehoYzIlrywCRHSLSuxRBmMZztvJ8fzGMWD1FCujgvmnYtLYivFLWgyFWxda2vs7ut9RtEXuTBgqIpEKZFMJeqm0DumZR7Dr1QW5S39BWg7VSc3CFKMcJHj3EAC5SiVXeCHk7DDdosPr8Tba0Q5kDY/87iTVS1HjhgrpmrZ45nDgJZhQeICHA045A51t4ybWL6oBwa7oZlwXadG3d9gjbqf406p1zR/GcOyeGK8C11HCcARo1kQGRaTV53QomsawYugQ+4AH16+v07Qx5B1twatADjKvqC76uSbghd88PTDR0+iWa2GndsZHkxRoyE3ohvTI9xY4IAielaPPE+Yb9BV2wuyy1FhyapkLRGMQ0HiyrSxuL6s5WdaCbKsrvOYS61k/ewquYRXhXCy2vJYRwJYkpRvS8/U7MXmmC3QxXdHzjZAF01MhdjCetZ8tWJr5SnWaIQaTFiwyZJtJrT86f8mBVpXEVMaGTJEJNgPtCqn6lZj1TVCD5IKIpCjpUIVcUaNSQlhboeZLnO5GWFaKaR1Nq82drpcrflWnNWAlLQEGBcOg6Ofx329zn6B7jVfYup1x6IbRTOCvHTQDpiVDXMSAi4hxLglJZaKKJew4dnM2bOMIrmsgZyRCDKHsF2yb4WZFh88y7W0WJP5sM9zxBA0ERQqwKwGVFAkhoJgk3rtWZsl/Egs5I19XkFccpnIKC7lH29dS4+5kY9CGrmIAkIlRKtPzb9X51veTp1SYizewSzJ8hvwMiyETtx/K7EMXMsFOL8Lvef1U2hXdw+E1YycoEn5zhD1bg5DcNfHT1m8ESXTkVIlfOB/dDx77D+536tUzcLcg1jONnbIlo5/nO8AAAAAqvVjG3wAYJnpjEsYkxFJU0wQ5f/t5/876tlDiiD3O06u8IzDQZMkoJDDPSemnKGaYUEC97BBIdQMdhF01n5f91b5ss0mSsdOEQualTwJoOzlPNPXVRhbJ//VNc78VIJ5QuVYCVUumnUEwYM6zLSzS9gxCIWkVa/ONBttgIzNvENnaji44eF69W5ZyNQ4/ASxVfdql3FHN/Lj/5q3X27WST2R5R2Np56py5paa0AFBAlFSI3IcuTbKadv+3Ju5zgpCLRS7a7KK7kOTVr5+EBLikIPl+6kPnRghyYpY4kuZKiqCuaI9u/cf8HKRYtwC/xeP07Zl3fKentewQsdAqCSITAYaXEScAk7eI2dPZvK0WxNybgIm+50xM3lWtMW2DNiNKet2VDznMVmfeaFJYfgg0WmFHHQFJAAAWIEapStZbHOwCX6HF7z7MT9WEfkputZMWFGEEUcKlMF2PdqMQZCPuO6lAEYQCd4HDoPvSyI3WfKPcVejM9GXIbKlBw4obRjhKLvJ87r/CBX6cgNhgm9wRJRJ+D3LK5kP8t6Nm+f7W3VIw+RHmGPQfg80DTupujkVwAouuSkBBUHi1yUCCMuUICAgAGQTwiwIgC8j/KXiKh7GlZl2ZY1Ao2oPiZkgNw5q5rcwnM7oShst0ZAVwrQhtQk8qQoVZncQWSZkLgLeGVeV66P1u1dnueYsi2ZO7cCKyEysMOMMVme4aIAzZKtka9J7gKJolYg2zBypl7jjjkysqmt7Zl7xhriy5tWPHYwez1c0mdoCWY1GDkc/xUu/0EsZ+ESNEYTzIm0NIEEJTyMYhwmzdRZ7i7c+Bq1sr7uulwXLda2ks5RgpfQEkUPUwLdoYwa9GRQXUU0nV2DsByvPYAx2VvPZQpYF3lpxj7mlaXAAPizXC9PZ9xiTJRRQQZRJDJZ3DEl/N2nbdp5DPFIaiAhAQriSIXFUIEL1ruwccmWa7TvHar9tAEhq1EFP2lYmzWnCBlJAHTWxLJhT/pwa78kq4MHfPYHv6h5euWBx9d6r1tM6Ep8pev9ugEAAFtYdYfM8UzjTalthRW85/kO4lTuV1J8yVAIe8hdcEJeJwqKJOKp4491AODXsz7rlsItzd7AkaNuzim7yrPF69AFo25IrE27+gMti6b7MGL46RUAzJQVoy7mSQQGhBO4+IRZkQYNVQgpOpxIoBEFADoxEGChL2peRUB06SWPMfllKJ85gMYwsm5AhT0zaWVvgrN3Oro1vDPq7Noh4a6Sq4Fl0TWTH01/7joNeLs/NjGCsLoqa5ZLjDqZSwzVHYTqsF6BLKxYXJOMcNcuBhgMI9yfOowNNiZFwuxW3hw5ZQnHtshrwfucA2vXRhNEde32vmTP+F7f/9y/8Xz6/85EWQ6yNMjY264VL3LGPFu3/qIqqkVFfGnXx61jjSpUVIGAQNZwqRBHHGCAtkBOUg8fMywycWdNBAEiz43skyNHK8JMoJKCFSmtFIru6t84vlfBdMbeRv7inPMn5Uvr64fPj5gDJG+YMGNI93c7Js4YRUsIx+VOqxgSMGxstdJYQFQVLdzoC9+DWjMihyTujXvsXkUv3LhmzSlEACVexfVa4U6lJnYz+I8+fCr+/uO13zFf6SV71j7PzCfhCY4i9CE/YSGqBuoiRBsKztXF/GNvNIXFw+RYoxwBVM0ZzME5SRD1kej39AAAAP5DwQJxYLHLvM5ZA0JHi3FXyru26z7mB3Md9IjxyM6ODnCm3s3hz69AqKqsUE4gQJgMaSc49ojsgCk9VNRFRQlIMjBoIT4MgPJBBgpLJs5M4AMjcdyLCmIEzEaepx6Rd2UCFbL33D6N7DFeuosJ08JVet0qdz00llckqXLqohScj7lnXn9sCVKgrNZ1EYACW4+G6ypuTDHAArwckFWfXQLTAAMhGwEt7bZp+8xSeFBaiAwpICCAmcZw/TjH3qoT68mvSYXWf9jsKeP5u/DxVuTf+YffXX8IkKgIR7SylULSVfb5sM24gVbx2vQpa9x7iNCMmioLih4QOfIxBYYQ0wJaQdEjKdBYEwF6ax2V4pjHMTPQJx2dmMI6SIMkkGmAMBCqRu6u1pHX77n34N7WDfrnZ150J6SAnos57l+YY4ZFIM1mO6N4TMubHTYJS2EpYeVUNYwq2E680W/tBx196z0KEjj3oVAAQckousRJ+OCzCo7L18rFOKXyqAuQIak7t5FhmEK+8inCO/j5aCk4gkflKWRoUPOqI3gsQKANf6Lih/7pPNeCPGKG6gkeCG5JGp1P03Y9+k9HmYIBi01ZG4BWD6X9j3lcyL5BloILPTVH5DHtPjUdNvS3+/Sx9a5XAFgpLacKiQIqiIixoe9I4wAIqXRDSoRtVAgJhqKCEKmB1wDIUqJAoL1YYeJiXBNRoed+ZUv9Tr+GBA91xiA7E6CPI6ivu2aZvWXkruzn1UZxnoK2L5BgKnC44kOzdbL0rbMAWw2wLDCroISAdhGnXaVa8qIKYN3M8DCSJBGBCZ5S3WAgjbZH/0zZcYxQhAmIObpX02AV58iJhUis6/i73/68mtuWiR5eg2ssiPyP/s/8w3/nv8/u4oAu5Xp0jiJbfZ75paY3+mv7z8q0v2Yb70J8f573GaWo5Zi+1Hvrcbob1+WgaUzIGBekIiq3PvehiT6X0isr9cKJHxBTKT5fTFqU4MmH75z/4b3hvKp5mv1/lPfBiCmFSCEMM27kQCJEh0glEhSQWBFIyCEAAIQTJkALIKJCoeCk9GCv2XQCQpRMQhFlYAVBEGnSFOqFxEpJVygGHmd+u96vcSnSYWBRXSGwI3QRF0dkglPhSJipZbFCHkugwR8yLAQwjKmx+H84Lel2fRkpAVpwObEc9Qy6L1QRahh67Uv6FRejniMsQwQFRE5hiO+Af2D16jTWBCvRTEvWlLiGR+ttOluz/VqDL9N+QlqOB7yfzZzq0LTxllymL5s2n8Dwdn3wmAdmbUVU5rRENCuimnCoALftv/psCzOIBaUtlCqJBouAZJGI3XWYvKHlYqoUZLZzK3IoOu3W6XcHaE00wOxkm5Lhwg1o2WA7+a7Tnuu7xnbmztMGWEzocwVFIbWy17oQJRooeU7SicrMJZOzV6wumVJO6PLfVzVqU6lkjeuacybTNGWZlKFQFciSRUsWbuRnVq/87M6Ll//xt66G4+PZD215FrqVEmLshtiwyQmw+uKS/mPcV98fvqlq25y4vMvjuq5tgJmczmE202K5htlhMcWEAm5o0Kk0BKlfY/fexVZ6uIeppWZ2qHF+yS3uB9Qmojx8e/p/eR5f1Dn03hI102KaZYLCkEICCIYoBEUFChIECRsaABCFRiBCCbCz0rNH81F8lGOxErMCnUgJh2gIEVAFlDEl6CZ85+JUiOiTTCBXjHTuSuScFlAHFwUh2B46B76TDoDTOudaDG2k5dikROCU9U1TUVQRfADlE/I2utQNwTWCDQ1EHbcr+A7C1HndrIoMBXHOUIuaFRsh+I7kP4kDAL/JeCGDEaEDsWd/ROvgqaGp6Bc5D68gq3hUAVKVw07SG/mSvmqZBxi+frxdnl/nIa6lxJk9kN0ol9JwKwwKpkr2crubNl8ZYxyy6kvnToGCuyhBuRFTSfO86KE7x0ICKluroyhYuVlGp5hdfWO8rjpn8N+6Y/MKQsz7S4ZXXrBtBw1ALK8Oqs8suoQtCOSYEqTB02poTiMLJnW0mdjdZwcSLJHEXtn+bzvVYYMAVBF0dGi7stKOVIhEUxQqAC1W7z7/s/jD733b/+SPfvD+xMFI+3EITt59oZaoQTWK0FBO5YTOClvHl793ck2r1a/mfF/60oQUWs3RYlgMsQKRMXx/gHPnRQ0IGDTyRHfzeCrzdtotIxUQGRLkMDIFW7dwcv9PPvzpa6XimKAeWHV6KnMXM0AQgLIhQkkIoiAAhWEjUBMCOcZwEo+LOzjSpOis0+Q+PSGnUXQRfThlBhDcWIQq2jsooRP39PiM5DZsUhCGYSDphN+PRqMM8aEug3FdzMty2AyowRzAoiJGIQgkItZtzO9JATz8e36rR2BHV/kdeqK44v4IFLMC1BXPS04Vpae0Ymqstvo/+LQSq+dUN3Qs0e5Q0x1GFo90D50Sh6jjpwvAr6C2kjsfYYQ4QSKeEV/evuYbwBw/fz6f52l4iieTvgloMsNkd2lniDLLXAAManIe1z/OX/2BEjRkA/HyqqwU1KtUuw86q6ilDB+gYMAskFYXGOJiPBxrYogDguNJMn2YN5gjvEX1BunPu3oVW0mfqqsATpW2c2FVuYCPVuMlddfvWcIck2pkuiVvNSTaGmKpKLi3/T+TCSnzqLZrmKdCKUKLmrY1MRaNJhyvb+pyvubxe//4T7ydzm2erJaxHXGxm5cCFAAatIVbGx43j1bWSEnvyVFCC483IGQs4O1symhYwIAEwSRNGBjnxR7IzS/s1+nOySCjXmXUg5yHE+Zoih6KCbnwPfrb99+MNzR61RMn4B3LPmjk4kk3QbWqpaw1QcqQhp6x1rt5X7K33mlYCpQQSUXLIJIZBkPnhufBS7+Wu4g65eP9/OV3/uP8BfBf/zb9aFQrZaKaM+GJokHUHQ4jIKeoFiMVHMX+k1MudMYjFLEIpmBfPKg+YgB6zkdDcClKkrhr4btXwDTpMf01FAB+lrlKVqNMwKfOgweiv+CxLdHP7Lf6tdTWR2pGDoiImBiKvy58IgcAAADmXmkohnQCETHkh3vk2DcAsHL+vJ5PH8njctrZuHREW02hClUDCuWAEcywGrHsRn/Xz9efl/9oqp1krttLm+iEsQ20qDs/zoCyvnR+VR6qzADVdPB55/n9apWMDVdcjsRgfgYH0bSNYsIQWIOFJ9PGylArXYXNaozyq1pQOXdBfRgWDBiHolbX3p2GRkocJWUvmNKt4tXJH6iNNtre27zS5G2tDFa1EoSh6UJ5JZV6uBnMxXn6+Jrt63Oyr/lWYZUuOlZr0okaM6YkAKJOiokAP80MmSBHFaMZQKZSYSzNZmzlOlNoEFYq7lE5zLoGDQsWBIVc3suobohINvVsvjlKj0lokqzoaBMySrq3mUU7NHnFsrEs7kL3jzlJrZeyCgiFtRnG0KF7vMYr3qQc+sIUtckgzQixHFSGZJTZhPF87eN+fBOPDCMhQjPS7dqv/+bhm/s+l+9nd+Y5BFbszzjXuS+ngg0IJsHrec55DDg62RcGi5QP+oYJw+7IVeTStMN50RogkyNxG3hU9GkbAHgb+aWwG+wkbREieAa1dHriZ95vHoNBLpcS6VuRE8AyZ65Txp26AUDTM4cSgDxKC3KIFJ6Sw8A4DgDDeirTBeKpfaCn7aqpFVgK0KJLaqMJ2MBqkRLkKAc8iMHvAH/GkAu8V/tqtjuJMyU5o6LGRPetXdLQDYYCSv3Qymyj9vyT8z6x8LlFO8i6ocASRepYkRgHq3iH4IlUQqG2Easg0gKo1GNV7iphVqEToqJMFC02Xp3IJRwvBLNrlwN278ToN4JdtoEqAZcpVEYGDCkKXdpF1KurFbCHMO+snmTMtNwpcR4aWFtpMB8AuRUUrYACwCK1+tZeQOwNNu4wIjYIaBQpQ0yOSgtjLY6zQbXX0M0iNtrLUUoo86hHfghsxXIPOO7JnJk3J6Iu8YoGSoooIAMleAcF2y3dVzQGCqwW2xcv98z6sX1VZ2++ZH5Qf3veYFLkMRLQCq/HWT5vO5hsNRMSTaWo1Lf/ivgyY4rAMzZXkajWoXrXPPDpdHPf0+94fGtoSA3mi6uCMIidKuFTmc7bmTt+LKVedNaDzGDOgqTJJOZ9vCvyU5DKp33n5o+/tL+u75hzxwkwh8B6kP3fhwHQUKWjLwy+FbPQABEjjyiZJA4Vf8+c8g2ojNRzVhKhgDyIg7NAD5piAwBY1gqqHKgCBkILDzU0iEsCrDEhhkVlJYBixaICMEo1nOzT35zOZ647MClDr75nB/u92nUM52THsCsE7cLdbu6nA1xmmdx2wD8k/Sju00Yrj7LDSN4BK7DcJBAZY+Rdx3B1bGY9NlN0gwaGhilNsKAGENCfberTWn47gufThIUq8qZREH0KxLWF7Ma/lsQVFRUiUawFIETroiG11GF7rOOUPu2pfysvJVLHYRmWLTSgQQPpSiwmpTBkTWoNRX3SlRNYWnJQQkqTVAqoooZGnRKEV2Z3XrgfGvUYgISpmAAIJgQYUFj03NOmB2dnLtGzATWFFkyQQ5GIrINAnFgWZO7+e8te3RD88peH8Xv3+WLxXfg4fLn2evWlv91LNaHT4LwhOrHIz2eQfhpg7/WXRbklO+ev+dTytq72OxlAoqIC0eJkodXsqZ5bdSlJesWr4x2f7vxq/P7z8ZfCCOIIExR3MYFT3gZ3NMswDGZBO2nAGwAAaZ7666/zMlgK5sLTHn2vSfUHiU8SXva4TJeCligKT0Q98A5IXZbRBtshqU6YwBJ5lgIBOkycBXuUazsAmKVXQqVAQWk6jYAEMiBAiCaYZmTITlKJi0QFEEgCehAsdwWUoDv4AKQzb7SMvTgmgzQ4n3NXZ9eJtv95qkOqdLFKknVuwtWqQzoF/7QOgnTVutb6hGGKccfVjPCc86OgaqwsjEMRoLMpEAQN9aC0z10iUAMK0ngSaXG9axUDEH2ikotchlEw9w5NfsOi6YTTMKLZBqhzuxQHh9QYn76g9HDSfUQJ3sNsFsvTbJJSrCENrbSfff852J52Iq3TcsDapZMUaDglBDKFQTPm3ETS3LgYqF0DFCiI3KmzHzLssSUwcUlDw17I1cm8zpkBS17+LAJQW1E2KUQWNmqPcigQAQgyADLwhzh42uOTd/3uPR/jNyevF7CKRz5FNFMIBYsecr6YSyIr2F6r8Yvv/PLtN6WG/HSkXRwr/pj9sWws6rIFllgbVIK2KFNNrImimDAah/ExH3zgd3dso10P6D2ZYBwg6vOMry5hmiHMRUWVqtX2Eesdi+4cM41qkztWB3NQmVshQGLXSmcAMxLVqGZoCAiZHfG31IAGJecPmlFKgPHIFHb4XMLHHQBqPRWj8oF80AIVSIQ5J4UoCFmUkk3EtbqaZBFtCjSlIMJYVcpZIdFJwVntZecWq8/HPmmW1Tq2mK7zrcvlKDNV0OHcml274GAmqD5t3i/1wqf/8pd4PTu9HqJedw6VkZoAGgBBUt04Y06SeaF2SXQmVjUWil0YuR4Pcskuv2wH0XraJbSshuIQ3bb63NmCJbRJsO7IXy/NMkxUBFUgjK1op6G5iMN18/z3RzeHF+m1SsjAh3KIcZJ1MBiUBIWaJP3zZwThKAnOrQNNGrKpbIwp0wYQRtNosrPSce73mTSuxUTbVcCZFrlgRMxJlyi3REQk5bSGN8gZU/ISIwVEkhlYUGKBYFBOa/axFoWKFaluzYlq87HDu843k4fsouz7ad4EghG3LiByOFAQ2oT1oM4tsGKkHDKm/zQv/cU/8VA+2RYiZY0VVsO5+RLc1/qv0krmXbTwUCdwiacWgKUGbFl37rffX//z//67n/7lNbkUPnrRCzP6BDstc9yD0KDdbmh/RV1TKERq6JufZR51VpK55LLlBWEYoQpTn7u2D75P/hKes7wuefjtN3D50f46wvWSspOb9jMzzie4/Ovf/8x//uHue/Zt9x0uBG/RWC4ADYIgKhSKa5gZGADAzZSdBFHxec5c3d5G7zb/VfoXe6imva1peDR7xJ4vPGAddRSqSXENv9/TLe2OjOacd1XquUnOgduvUyhZq4pRDiVwQQELRIDllaxCjWpbpirlcXEkRw56rrs9Uc1tNWEniuEApe/uqliUHbXkkDWDhj8K4szICkxQU4lsJQLVxmM1Me3qoK6ZFqfFwPj3v/qfv47HjXeQ3loMSFBuqFkeV+4djBeBJ7LgUCWvfGvvd0HP+FZHikWc9AM970pFcrOGr7m+D0ayBqtsrVBqXOgHbHiNBowI2TIlBmXUkVYwkuKCbsWGbS6VhPCk8eNVV83Icbl9fPiQ3J88YpYUjJVVJIdasJHKzi0AYIKzo1un9xoX2xnAyD1qh5amfFnhGlqZrDQupnLMqZrnyKeuqa6atd6ukFjzct7b3N+0Oi1Ls4IwkMjePbwn/fD6H/7Xv4lTpOKJajCDhayBz7kE5yh0HCFxbma0hd8vqjdeDJeUWxnY8dUbaxYlMARixWY73zPjjtmuZj1HtrJcLnRHLuVzpvVP4pPjehJ+T9/jI/cBV5qBBmrbWgWRtlZWK1hquTwpG0zMXlgYRENJhIHANedY+KnzFP1Xj75xb4XbvGD1aZhDvEZBlsjufL090Wy7tyfKRb3vZUF6bUQo6+5yvAgAcbCKSgUXEZUVwUoiOcSKUrBM+7rFREACCXVwsLsohxhycXJ6WgxKqKNbaFP6j0/NKViF2uosCjFIs+WoVMvWQ23VuZdu92v1larz3K+z64SaLBYbhamQ1PZXBMxywzTMsFzp9uF0v2cagZ0cUiVCIo3QnMFUIVhUNd+bvIEtg7YeBk2Zelo9B8Utc4UR3FMbLIA9MSUhsi2Cr4AKYIidmDfq4dMzp2Z58nX70MSBLbjGUbJ4C2YGCwxgjmBADkGgAhn9C73sU93yVeJlHMQOgZIDw2yijHUITHvqOxe8fO3tp2B1gGyQq80Z5h1mpw2XKIKSrUkTTQa+XT/4v35z7z2LAkcZCS87OUaEKYKmKFT9ni6OvdU8fylb6cpCaTAzatnhXO8A6GBXc2RvAN7PmSNlJ1lLOnOrvGzhiyNvH/MoPLYn5kF5zX43+oSNNvxAg1FYOBfIKMMIelI4TwpyZxclYRGUAVKRIVI4Ayji/DooXvV2YmMQzGtBMurySTQy08JEyUNqVLu6bStlwqKI+krWc2skVIAVXD1CIglQQOLlwLIKmG6Ci6YCIsbctaRT14Mb1WdeUmHnSiQeB64aT41EIF1r6ecjwCYcVo0GQMHCzEZH09njiRZ+N3zk9BFu29/Lt2/PDgRpPk4nLESFTZwkq0xJkdwnQosQE7fz1xOfDjZ7yghDARrrIQxWU52MDDcxfFtKJNfRT7NB0ESpJSIE1DpnAHCUIgpPUUoIiGrQ9fgHfBN7+uPHm4ekP9yPnV0bAOUoSenkFKEkE2qHqEGW62ErO3szOCxjxXbuaydvFtOxYB0oYoaFucYnH3524MkLDGP9w+rwPmn+6vo11NhUhBqo8byAJS8LkUAixngiYYnO2/Knj2ev8fHG4Vz54GLPikWimGqdCUYSDXNN5yCj61JGlIBM4Ih32Hr+Ji2LCNSsCqqCxys9sq3eeLb4CYDur3fsk/IIz8ZNs8HBhoqFq4aZCOayNcBpS/aO5hIoViw+cwENh0cFEAVDhUCC2YC9LX/nRt0e92fje+SjAd6CrT9bCqCH5BAKMZewOO0Ruq+jU6PGUUxcH6Oz1yy6AEU4g8ra1Q26Wpi21I6apQNY4Twas+mDGTNmJSOLAoN4x91Dx/LSgmrKopJCKFFVKeWkbsHfnxkUgjgkFIqaSJERNCTVj/a7WenB3IGQp8OP7bxl9WYETghDmmJ70c0yryhGEQEDBAL4MPeeOZfYKmkDBYgEpaJiv/Pt0NgqTYtOO3vQlo0TRoBkPXsZOdAYUkjuBTTccc4Te0NPuB1OnsYH9WnoR+d1nlGgR7gHRsdUltQJkbmCYxYaiDOud9+Mef3ihIhLhjhbZHTuGUOfP7ocw3SmbKGRy1HyoM1kytSLj3P56SdffLT+EhOHYKFTqv1LOy7xSstGgwSIeDP6IDPDWZzDrNp/0WPjwyI/sGkQlBbZGDCMnIuTSic8yPwLAIwJAAAs6NIIhAxOjFiBaIe+1CvVXwBUx8cpOgczc4rH2w0Z2qISqAEvjJKLFyRSkRbN+apoUAqFgoa7huU+K4BimG20Fk3AmqvN36u88zxtzSadGQmXchxHrkULa6m3J/dsuz9hNvO92H5rvvapRtCUrTvgo3AdoutXAYUVRgPoJLs+w8xcqqLMyqHy2mASmbpu7ep8korCzFBIxzryo0NtTFWFjVhpBgli0Jzg5zDzMpBvnL+6unOM4CW4gtVIZ4qEZ0OMo/qxNEuthIQWwEAUgMECmX0yolO5JR5BBY4Vp8Ev4+CGPTiKmleyowCjIKoSkyXGsq5gYMO1Ybm1lDMWHu64H3pcYVEAAASR3Ms9fL/lh07zEe/SPpJApqVSanWMd3CtUeRu4ljE5Ij2tYRwUWrlHWZXDLqXCPptYYpdtieag3PDGZl7TkZ/hllOpoOr5VhgLYBZA62B3GKymMds8ouKMa30ofmF8244+Evmg5LEQFeEQDOIJIMSp27Evbi37Kw8aHUuGsVQRa5iwd0weGBX1AqMs2Y51TjylCoQARwcUVNgqJG1G4D59rECSzNhG1NY2bMqA0oUgESJbCAzAhKSC6iDwayAwydkGLGwUAvQMLMTR+7tTi4SpRrdj2sV50k09dwVbwnT5q2zi8Q7PXMY4J0EgZabjMlSx9hi5zYmvMts21JWDFDVknF5eR0I76JkeRmPZVyFNJuiweQUJ17bZSDFfdk8qrNkygG0aztERU4qhhqW1YqQgaqS7h38Y5FRdDuzj5kjL01tCtpZP8yaS094mB/nYNEAzEUscXlAWLS4yBbCNrjZq9ksVSgy5I2RcfQUfJPQyGxxFCxLVbGnBGoiLOpzdm2wjW1ry7yChcayUDUG92hDA9nkQKIb90tb+nV9Pb6+13c/3e90umihsqG4YurRs0uNjuPZj1LFhJZuyUEgCoitoVgkbAqt3L/DQV+qJm7IsxYwU7IDd1wDzp45q6OV//UPfvZnzV3RPLdZIj+KkUQBKRTY1ETb2CGO2IFn+/n98sR3ufHQsd5xgCKSjkaZQHAlsfpUOuHLCN/c9mUIHMGdjMdycOldat8AkMtL3W2QXCCiZsSY6IuBkQloOfL0MWnspFtUhJUR5UOUqggVGCSoISRmLwmBAABJbnFIlkQtYQlq5y12zKOeeLS7Z0UgJU8fPtz72xq6vG3fcNhZImJi1X7dz6HmA/MQ5wRsXbBdx4be+Rm6IIWwM8UnHlnnBgXFbSrlutbDFKmNEKzacx5cu6CmQh2vc0OjJE/0XPw1TX/D37K6WlRSUQRJ1Mong1hqCCi0kdIPCmODRn26NsR3i6Oz/Ey4Z3n5DUjvOcetrgNMIS0U0qbFFYrnpAVFjBkf28jVLLOAJhrGeWusp95pu3JoHxyxQYGYZKMMzqrKxF77Y/RQsOi8DyY32ChJB3JQsNSIMsn78a+z2m6v9eX/3eu788IN5/M72qQaopCQhjCrfrg7jRKUksb0r1vPkf659KCQkqhqTQF0sLd3s5TLUEYERByEPbLmdFGvbJ0z+RtfPH7W+EsbZIH9gImsS1SlCANcwuhnwQFL2XO8d71vqmm/y5AWCmqgXJZAoYMcQIJKlGZDO0zvaq78w5cJS7hZEZmPaQgEJUzMYM81Cg5EZNzZfNITTKk8bUJauMLoLvMIyNlMASCRBQ0UBRcbY/FMeGISRmINVDcHAAReUYAFD922O2446MkhPRQNC5OJ8h8yxw/urtxiSXP008E2Ww7ba3zNFvw6Nw6P7oXJ3tSP6lzHetRBgbd75vn1GQXa+3xfV7ekegxUBrg6x6rmsCjVREJwshZ9Dn4WIKHozIrAXFWcHLbzmeA/KzLvtu66A3gqSCkonerftJ5H14iVW/Y0RsI2cMb3weVP3f/nYbz/v22eRwgk0REAhAWhENRaDjyjxo858bhof0ezs999extlo6I6a56lcxpba0aUcue7bsBYONnlAhICGGlipBpEFEAUwaUKZsbcA3cmzWk44CvY3smd7rH90aALLYLDGVMh6Aq6cvdODw5cBRHYG23bGUS4BwBzVmkCzee1XKMgl6tOb8oZoVdbG8X917NXbK6JzuscWqEBkCR1s2Y9gYEHBNhTyqQmZ7VFUFmzpntCnR3ihjnS1W4IYYuxmycLQqmLvuF0rf9zw6aoysRmkqfqw5VjfyAXr9+d46PhfDzbnN6zGlcz/c5zH3szAjC4w4vACbEBiAcEQIAQAjZBMjXAomaTLO0Bd3Kge5IKKEAoSAARDONEmi1DHiKAggP3hRViFggmpIquqwabUYOiNdNkZBbozYkNZieffU+ASHCYiijlQ8fsWsIifpVUB1CiYLAorkWLYNnLdyMeNC3n2pGAMUbXzGYwwiYaFnQ4MhFkp1o5l1PLq/C7z4xmEqAE5YxcYWGezijvDAZUnWw1yPEV33/67vtfawp4MCCzZ89kbBbF9WxEUYpT135x5w1jZVxmkceSqoVB4pWm1IWBY4dBAmZUQgASIgZE9hQWBCWmY0/omQV75YAPcMxwLV5dxxodcsMySz+dDeaKaWKzXgOliNtKetLGxAFK1F44IOtK1vSPq9j/7Q33Fz8EIvmqyoJyDwB10MF6rti7wETsmT0adsEwj2CDRRWhp0ogQpdqlLpIGAhBybKjzWDsbZ8z4BEM3VpTwE8NAmafnAXbOdrG37/GV9N5p19JCpLbvlvcdU5njnY29/Q7tVYIKKWwPqapI0FWaScmoEpEQUgISAyAoBRzIrMRp/QAuzLGPVgtUATCAKJw5qSkIlSIq4v8Uk+qBwcMvBsxK0tZHCPaahrLUI9Z5qnnCKOkbW4C9fH3sTMLhvA6rEsWVPG1HqahKr1dFXRQwEnAddNliA3dEkH1AAlLjLgqVQJ4RD+74L/6OsqraxuqAtgVbEUBgc9b57+NShi1VDjcCxwXiSEcwEAgloXApCaeyXz9+MuPR78CACBIFSUUmptODDFIAuWv/ZtrSNdZFnGZ9uCgk+RLQEGn5hTGQYiJHiRmBBC1WDHkqIk5qkQehpPDO4djNw4lX2svbUWN0CxLoBQKUDChQyBCIIJqKjxJu72f2BvHTInYRiIl6YZRc3dR4hpZ/nsd5FbFMVEoZShpPqVTQy0AOYg5jmkT+A6R5GEkAW7eVYWXKYgK2WQUMIyUTZJVoyyaaEiUrPBkyoCMM0hKkgrrMA5IxuND/172rz5yfv3x+3/77bOb+sSjDZXUsS9GoJQU4C2jwWmDIIyWsNbVzDEFAARCAExS2Om5PXPTXnYyi2EBLYCwBMAgBjlIE6gA7T6/9nKEXXuhgh34TrIDJCX55NHfmKckQxkWA17qul8B+3A66VKld3xPitEtq1tWJBK5M3NdskVaOSN9cxjiLi5GB7iLEU52LfUZQVxcAkeKGCoN60DtMsyumoqqzIQcZMl5/f/7j9d7v3tejyCtiY36JCsgqACTvjF3QFblQse2JY6f/Ry/byC94CePqJWNoawzLiGQSvrtNVJUZK0+lztH2YQuA4BERo7gSaykxcFuvAbBNKpHn4GT8HD58fF4fHNppUovKqSVHHCCj7CEhUa0YGuLgB0uBRKKl6YsEMOr7r95nt+q3ojAAkEOYNJj0iw01lN7eqkSJV0NiXahf8/d6KSmk7VRsyDkDkZOjTACTw/OVak0S9AazCpVTUWGOXtywiub3iABEkKhMrKCkWZSVffiWEKjdCd4JbYMIDEoYlAH9wGfntQZSwW6WkRAmyKwAptnJ7L5OsyIWyohbtAcCDMFIiHUFjS7597uuzctNkeDbGpYQ4NWWEoJKQpeEIeHhnv/xm//m//hf5UinqwTg8qYDIx3ENxiiiPDpm0Il1yEDa57qJ1D5cA5Z+efBtnpFWNE5Xrwsa2jgCAhJSqqZavD1dj1obKrup28xFnV2IQsVmMxVhCwziq4WaWAjjFySxNxkgWQhGbHW3Zf5zdrfuXffDskiZrwIBMggFAjUhUuNWdIIGzKbCjhv+uTiN47QMgx1KuHOAgC4CmTzBWOWauK6/BdZ7fGNhQnKK8gMGdsiNBUZfQE7/CboX24+TR0Z9lof1lqNORKFRQYuQLnpUm+BopaXbiJAycxjHFVEGRo4dkcWcTf8BO39wD2eZrUGZITMCBuBnHQYvBG2vuOL0MWJI+7w++X6jQ4xTH22UihI+gCP2pCCDmQ4N6GGuZIfuWd5pNS9RnoFK13OifN57ZAig22tCUJKUQBCEyKo+a+ml2bfY/gAK+RBUWBx6pURsGg/EFgnYYmGEVVBRZKiAOVgw6QQyAGlkoVcDBRYzHjQQdu+Dr3XZDERDPIttAmIhs5EiGQYU7D/VPL/nJfPuGXv503XtJtg+VbpZi1bqnIh0l8DW29JYqAVDlmjLZvHyTZSYlml01+LOV36ZwNAtbgoJwFSyTGWiURkFDWrKlOUPzuwKK2gCrkmKu4MDQ9gdTzmdVwDSSr+777IMTsjgAGQA6Wz6o0Nmqn+8+7Nf0GWeUZVEvu5EYcC5MytzJ8nOa4fJsbSH5N6/M//9igfTQY7N1H5Vqe8cw6myhGqcSmbIgLGWRUTMNvyrdoU2QebUYtWizidGLf4JslOd/c46diFrKfViEHXZJJIqFn8RRmZIdiXqIWp7kmK21flVgs/bCL0BwaYSCy2ntwoFDj8zqsUZAw4hoLynAETdF2l49YU6vIiJJvWSf0nMB8q65NkXAMop0Dzo9qHfdL7vcb6/iF7BfF+S6uCdVRt1gI27Vbqj9tNPI0EDRFWmtM9bDY4c9jvaW3ZmtLlSLJrBh6INFUemw6CNdquvwtETsbyIL+2BQWFAVI9tueuyBYUAwsDDJ36mh3e9uedF8HibEAguXaGTRZL450NeObixddyfhfRvl8X8fTgtX1TfO/YroL7+orxlWTQrVl9Sc0pCY1p5wBJkzQ4jJHHo/Ux92gN9FS8l3PIWYklqzZzcNd5T5akqo+G2CWQuoteN81ULsau2pJriKYqg7QzI4Ka4frkQgTAXILe9e7REQoRbxStYAQVAP8nKf/ZfK5TmOWUOkU4tnt50FnQbG0AuUCrZox1zMBsH8E2kGh2PtL3QWsF6IUpzAF7GmpiJdALMTN6NL0mJ5/Xs5yTor2z8X1X3+O4/vi6/Z+ZPPZcKNUFVVwaQaOSLEsFJRoSkk016AG5gojsqCKVbbgMnqqxA8HJG6hCxutU3IKwaAAQTXXFb8YcQijjAGBdYC6VaXorFzfYeQCYApouT/K6llOo/USt37Gys5/+WXLCyUptfyxAWdxR7/JKbGI/e1S1fhp6Ex05QsJjKWGYuPu0Y9r/ctvvdcIkaw4poSwjPDCSFRFIlVwoGG1muz/rbMd1+oikEQxAI8vIBj6k4OvI7C21lE33ObGnms9HKSVkc9dV7qunqxdL7m9YV/K5/8kH/3h3yznsbr/bt5CXmvuG3MrB5TrtLr1U5rRnIoxSnn36yuhoj001W1zLG1BWAyQq+mwINjPOGqX/7iphlU7bGFLHzHJ2JyQ1aZ0GHSZlkU7CmUfL6BDYxpE+lo5jFVzygvQkbrFc0zRYYGkXi5YY0Eifm0FIEBDcMiiq8EdM3aOex46v1LuEjzi4qhRoZWX72GIic/zMo55IQAkCABAGeQ6t1KOw2AuIMWwI6a4qFDKSsKCSg5kqV+uhRVOx/Q5vZ0Xh6I/djowWlwf/KSWvnCiIg2p0FmdKhCLdaSaVlJ5YAuR5NrcKfdk7QcFoiym4V1YwuG5JiYdyQyB1AwgZAAIFMgN6bgiVamoWFxfuNqan9Eo8MA8GOI0Jx78xa/KrmbMDAPnFqvL7izSbB5VJEtxP9eIDt3EvLILX191aBhIfd2b3z6WP/+NT378DhUlcggIYEYyQR4qiRhQAIEgYp86gyv/aX9OctKmugUFATKjmBP8v7jFwNd+6X/tZm/uOfcnWxdYJqaJNfPdjo/2CVpcc39eP/mbef7X/t3Pn7/99N1v9NRvVt/CbtZVJjHtiDttQ/T4dH10g5ZKeXr86SJV2kIJRI8z6AHABSGz9HiZ/dDXvOHFt4wAXEd7eG4JVPfVdsXH9FyxbtVcDbpwAo5MqdjUAEtH2qxiWAUpbRCFRqyavK67flcz4LsUqAQmB1iUaPrRAGzV9Yn1ONghW+cXzL/18b+duSvK4OOTIjXbR4fj4iTQixNL4N1nrNMeYF6WZy+USA0kmAYEUbA+TBBLYJdY7J90m0garVRAWPNSQ+a8Rpt+9d7aIzP/HGmNQEdNOGqoCq/bFO1kZXxs1jWGEiQMFkCMqDTRYGs55EEP2Lx3u+//8echfN+VXy31jA9v7cNDGDD/ilTHkmC7qrpllqvo21EcSPbT27+1Sr7i9JOk+8QQmCKzk1jcqClIWduIMx3noTW1LmyjQajJKCc03+VPT//TfPIWDwLN9tTMY3ZrjWwMa6iskRMqVGK/YJr/BbNBCqBZRhFNMAOGRphAggAAIBAAEMiQZKAXu4hQiGEAEJCQAKBhSmKSBHlQc8sCpPYMg90H+bHwL33e+tw3Pt0XU6+10D4mveX47/+//yfz8PlUcf4hPgWoTECPfpgkLXjc+3JGkjcCMILR5LKsE5wIFDj0JJm4Sr8Vr0or5Nu9MCYmKA0UClSEtVRlZUk4AiUqBhPymEZirsKFp+hDqbQlAH7dtTW5OwrWKgAqK7MqQGJwChCE3CZG2xOijlCcNfLFv/eH4veZ53lv3sz8dyOVWVjxfCYDZKTEx1ggBw29kdbDQGx+/zxSBlFZtyCgHr1RA+znN7+XBrHhJ91o+f4YD8Z08fNLYjao1Hb+fMRPx/5MmjipZ5AICk0oLUWlrHBFHayCJzXX7WjhMZIsNCU0Yn79l94f7oOtWZG3Ium314+YVIftV/2slqI4wlzEDWwSsPtq+Y4X1/Xn8tG7Ilrn9DA5kSYmG8qMAUxQo01lz3n3WK1SbWBReB3O4K9hPfDDr/1P6/s/NOpA9rkyC1VLvUKn5lUpAiADeuqYCVp5T5sln0VfmitfA8JIiU0EQaKAIgIEAYCUJjnDLGc52+yyQmEiIiCIIiABCCAEVUISsOE42Od4dFqKf/NtO9+Wzn1h0nzI+gC+yT7QcR0y/rN/t1efvCgL5jbqAIkes61jMd/Ruve+9ufKs2WRCaQBHeepgSrCiyY2yYCjS8ty5CIVCcV4SRoD1HSg6oLCnKyDJa85XiQipqFECk0HbNRI6FhesDRJJwDm4WFeiqwitioBiMRiRiVweGeVZb9vFi7I6vT2+fPtL0cegfng8098OLTtOsKWulWe80hM4B4mD8OgtIyVekMEnMv/URGoVbo6Yn9ThGDdlNNaOieAGTPs0GNeb8D54CLSKVRcbypO2kvzcXyAZeQeIpWwURKMqSAMWsAlukiT+omxa3blzXh2XBLf7v2q/7zDqo9+dhpha63Ni8BoddlKbZYZ5bro21pvxKrsbhZ21TGzyaNW9iTkRYJQmYU4sctBFDgYqwpjaF51VEXlFkWcgPF98HH/7Gvj0T2zsi/3x6I509SxFRMxZsqIEcI4vvBkuYWYReWtfBudDr6m514BYQAAgggDOoI9iXSuLGrCggJigGISAFkmHeIcWrKawANRoBe1/7zG/ywujV+vpHnBXFkj14P7gPOu1s4jqJORPB1Zvf/Kf/y2v/fxT2RNtaHSpYzQL/qT/O7Gp352Dq8E2tBxa5t+z//0e7IxiYClmi3pWKAYJvK97lUFApQVtmy6n3030RmdmpmNeIkEJovLRqD4l1KpGhvDGQWz0ETmIu1alDwpZNED7BKqghJXY+myZR7BFBixvsWeQBCi5/N/0/t/n2N0/Te/ySMCF3hCSXnACQRpiAIf8xYQKbTXCKWRCzCjMEIAhFWOnoWu4gSoJbRJDF8jSTkh00tz3qJSKJjQQRSgoHWco2aBctEVT3mPzzkMfeSISp0IWIAoKkiJLBG0N4xY40pDKmy1y7fWYU+77lUTPfNds+CtWUs6SqTeu1s3F7QiW4A6U2wgcU19ugXjYUAyAAKCQxSvMPCgWTNU8aKqQXsrh7SKeWuAfLJePWgZyOxMxoasYuqmoo3ZB2mFnNTwdGONmO3PzDWjXCaWFokUZ7ExHUhnOTsyO7FRb7M3ebLCalFoACqyCAkUZEhNS1GzJDbbvY5SG//z63Z8XnOtCBcPW2/ibpGs6t104Hk6yT+/MZr8CFvwo7Pr//wOGVMJUOpsy8qQUqzpKQX21u2Dv9LgGfQ7PTTm4PvaTwWiolDD3kzhQXMihd5FDAjCWdkxyt/raprAWBlg1bllLXWJCIjXrFkypSoYuIJaAtauG0FDYFEAAGlh7uGyMkiEROKSvtQ6sAOUWosIs4oUv1+b336ccHj2ze9/Yg8P2w0rmupJW01tKfn/sc1wsG0AKHLZEGcQKWBdiRMIPKjTOC2lzK7roX2Rc0jOO6vh4Qo4w4YgxnsQaNALA2BYgw48wlm7o6uVmSTGi9pnn2YfMtOkpIR1qx2QSFFGlu4XSAgSGiJOWGOrVwFantd9tVdymhra+s6r213elBBShRJ7TakEEJg6vdmfqh0ZwgoBB8Wswa4mR0m7qeOq2Wpmc4yqRq4pU+iyb714OiY3zAw6RfMOIiq0I1oj7aFdSbmvs8vKN/JeDduOrRHNA3U9YU/zKEV6E7gDf9DfTOw2n3WeXnWsIBuUPBRZEvvYCC2DJ5MoB3XC1v2bj2v1/7oo62pqS7vrX4sbzW/sdp5Unn3mJA1SDySN2UNKxievbvV6Zbq3BlJ0GKNDGRjyENu0J8Mt3x6S+9QnmNi05f+8DPs5nw3OOn0ubTLI4MLKTJDC2Si4YiciNt2DH/0+O3vGKiGYKQlOXlRc+aXrwDER3ZbIUKTQXUrMKFihCoyEkmRmZQEplFqH8CGqto0QUu9dWLlngeQo5Bf+vLe9S/rpb/7WMomswE9YBO3GcP6VAaCYgjRWCQ9VGYpCCBECQA5gqDCowsu+D2+HE3ht3mMT7hv5AtEZFwYdr8S5pKMkL34/GrISmGRZ5RUFHMykxIJ2SLtK8U0q1HSohPQ8+2gOytDiqBOHIO+AiMgEAWnKxtyY4dIm326oDASkkCpLI8pGhgp0STcC0ax60rLfsnea9r3xiV5wvPfqlRfupmqdpnZn3FgZmifD2FqBZxBjn949POzhogmCadYNiejg2/uVVrnPixS7CMWflPf1SllM1cmdq/BvKL5NmOkRCyKjaMinv/3658ZvZ/UA6ilKBo6ITU8L3mXjmDum45/f1Z5+eQ7cpOeB8oBskRwcDB16nJZwHgdZdpAFu6CCreQyWFE45o/AxitBFlvq4UhoPQ20EVgjy8YZxJ6v+eK1LlFq6Z79x48C1WRUS1ya5Pucs7KIlTYpMZM7O2AUoPM7AwEASPjdpIhdtzCbFMJjALVlGB6rJjUUhHHLerGya5aLQgnmglMIMnileVdpvFHYUWHnmGjJbwq4nP595G+uRZDiB/zdp/2dgnJ1h2A8PVKYekqCAIARbRiBBuChXogYYkIAKDTF3+zP99Vp+INnutu0c3gRWLb+fvJg852CU+yHYS2BF7ngy0tskqugZXSsqtXcoyYFlLIImlpgyp7NucHxQzKP4mnybnoi7HknwsYEkja0W1yKad46ViezkxbXhz90pwqF3Aq3Rujo1NZcEzVDCX4wIJU7nz2ZJYIGIrDKPCzzs7l+3K5+99xrF19U6Xl9MWE9nvNuROH5dMsbLbClIxHnhDEh6lnkeTW66KkpDnj/GPpa/OQQFdHcL/b8s1/nqWddXnoGpId9MIiEXYOivc6n/z68lce6skodKebivf/gJ//un+WfrpfjtkmsOOcH1I3xzr7pGHG4sP/nwaadscgoAslG9lrQxeyGmbPM5/a6BoEPmzUaikdLY8T2PiFz4jjRqR4tvPn5puTkQHcY/oQgNNNyTdvQI25ww3hhnBygNp3NTF/MnGt5M60NdRhiFdajcqRCsqxOcLM0mKglTDFRbWptql5KiKJYa9cWGok2hgoVKXCHmzCCwSz7O9/Sr39DbCF+gN8eJbzXs+8/tbb/PuK55lCJYFdD84kBCgKAjRliZKzaXM2SQ/5fdwdKc8X6IJVXVrUKDk/2f4s7eR/v5635aHlXKLGBIsrh1Yc0IATKBZmCVE4ZHA6yipGygrGe5GgwA9IzDCaOl5nehGSSGRxEQkiJBGCCI1hGoGqGDfNL/SD6Zb2cdmi1XClK2bSuvlWSJyIXCoYhANCe5bd4vIhxZ7BRkArlJM772cwvvrr6vGxloeMzaXFHzox+8KytUx74q7VBJBK3Zk0T28/08zAbNZGx+nHtvZoXF1uUBlrN3794b63Pr48tRbUUyIPonqZaXV0sWqiHv1XKfZqUmT6In/3bdX+d7/68v/TtGlhzGDvSnsMDx6MdifpnsHIIdJIiAnlQqAUSGQFoJkKggoTP/Rc86e+pn+AqGjIWjcWbYrslRzefR3/8n8a3f/lKvdxbnyvKNLn089kMARBWuzRKchcPi2xLqMwRSFTWJMs01WhBYV8SUq5DXFnOKuADk8XTca7q0wpgi8sRaKyKXRaXuRwXBFgVVaCqPK4QiIKwxKLFsi1Fuj/lPQEkn2PvWZz195fOGDMhvCIHO2GAKw0BAsAAgE2HiKcMVOi0GMdcxLmYRODnf85qdTjj05Ie7Ywf+d4vyt8U+uNfS33a0yxQwQQCSjtAHSRi25Bwpsj1Tr0JY6U79MNtb8/vz5P9dv2gH+rL+krRvbtsOhEpu/F4ox6cx2aUx1v3RAwboKzLLem1tx6zCpBMAZMHxxYBgKwmDuDtPNRc3b587/gRYjFYEdpwszl///nb4iDrZ/GZ7ZrO2ZlmZiYDWTpaQCjAMaQQCswxxCsxjgPTqOPELdIyyyxKuXzwvf/gcff3B5i9e+1rrMG5kcmU0IqeNOqz9f7o1d++BijJPMaq3DaOXIi2eFTpZnh6febFmz9/XJe36E9PcSP2FR7LWFF7UbZKCgDNbTRM2Mw3rqlX1s+WopxdZgxRa7pBfjV7jZFDv2f33Vvpx3Zrt1yL3+bOOW81p8CaUGKGCCcl1AYf2ZgEC4RWrcY9O6nUw72mTGi7dIMqKFktLOax/aLEtVAaD1NbP2XEiIESUKkAihaXtFwMgcHKSBDQGGIW6f9fvpNRqNuaFULs9e9+COjIpCibbvxkTsnPSVQEIMBvP4l7pdABUgEyFbRYJWh+5tkliZ2lzJOJ8JVhd/jHe/5HZOab3aPwilVoUIqZTjU0LU5Rmdaaulvulz3vEvlq3IPfXz0+e799vyc8O6oGG0pw4CQjSjRU8cZlOr8FyNXDsjLF3DJlUsx3iSIJJiEcAiuSk8mWcWZqaLbxU92de+BhSnYtCrhtq8/9/vyRv82I89ozxfk4Tj1Gt58sM4YGxamGJltpADUzjtaOcAFrngtJUU3oDUR5phNevT9fSRRxIwhEyaafSXQlgmy9z5LExl93MqF5rqW5zzeXbmBbTMMnzT9/Xy+OYZ860WGK4YwXous/oQ9lqVKeUFmm0sJt2AhU3fnrBzj2T5ncFsnRAe5asxnGN+Z3Yml0OhF+T97kJYxXi8cDTqRgWM0TS6XbzbOsDQaAhYkqlIJmqFhYAVCIKxDdDoSwjqO81ewxbquwSJxEBkU9HKRo9ZgbWhWYlRUET8nFlULaDFgpL9VAp2hzZCHz27uKlsyn/3CXWgOqJXeOuRt8tq8THmOCEQpWMCk0KRpEkEvSCEiwJmqWbRoru5ZYlomMsvHhw+8Nf07Br3RnWTdsIZj1DX2VhOlqOJfPb7+9d8bubnjELuhY17bzppncjLawBXXg1HaGRzYy1nueTQx0h/DNZRFNs9kY5c1gk7pO+8guUqi05eN41tln3uyzPsNOPbjDHtipW/vjbs6QOcCtnDD4/ca/z3nj0LPjNKJRPi7gUyX9KEQpGYMiKtBgtvKns2WosDnHl6pM03midR/H9J6vzbI/RF6ElTviQpUQeGkk2JiruEBO4yso8LlkU3zw1PHUuZ+S/jCnrwjEnliSUs6ULm4pAgFAFUXJ0ghynJt4zr706dPpWz79Msu9g8W82QmtLIfst52n8/SRzIzq2sutco924kg672Cn173LPtQ9wVbpC1l+SbMva05C+Jx4vqOsi9eKuZygdlswMIyCVSA5d3EhSLPf1YlcLjNEnFzdQihWNRIkAiVwmhiKk8VwDloDIkHOo/POPQeniPzX2PtnckiIaIu/9qDs9dbvSqEA9N5E5tgMsGdBVUCpUpqWIBRTxUREKpVkEqMqlBTN+Kl9+pvwJ6fK+6oeveRjyJQX1F3Cozj0gPq5ryi4VERB5IAmUGgGAQMW2wp1HVstMZYa6bpbZgsdobd+GZnqi2Cltnu1amV1TqnMtS8/dYObHT+8MpXoWQI0Uw3PqX/eY3vERgDMKCLWedr/YXn+a3+0oXm9lR9PL+RTFJVRIqo8bQVP0oRjpj+DN8uRqnsaNtag0OKrjwmLfZrUYrwg7AkjaS1Faauu4lkua91LTtWrOMQpduDf8Zb/PIuVIhilNF1/yTbkgEUYTqZBI4EQEQVVucz+qNO3f+DtlekqYY10xNksEcM9yRtKv75o5Z7QKE47ArMlrpDXgwOrIIhBN5C9S/ve57MWyR22280PAamtb5Li2Nr/rp3tUdtxiJkxhMMha1NFm4URA1ptALKdLqLb1KJkCIEsGC9uAEijYONQKlEkBqp1FQxjpUtFpVrUTMjL3/06qTiCDGtf8K9vdncXsE2+sjUYmQkgXLRRIFG1tkJPElqkW0KhqEYQgOYkOEk4hJ9+fDq8U5ov6VfZASnTF2LFqmHhA57krCNSswIEMhMNiDWBEzO9KFhbJcQkWKOFmZGx5ioiwLE4FyzhKrXNMTmzTEEuCAL1R1khECrdzAPnsjQImmo8670HTgpobci3cCyfn41fmb8jf9cYfOnJMfS2qUJYwkySg4xVl+DFGRIY56Q6aHL7JTyc5dcfNnKe4WQxVmjpADKXeZaMqr2hjamtOd1mIMySkMiQTWyd/Okjds/FHYtmxoAiNAAlAfRBChZtEWhKlVX15zz/J7+jOW7o2zM+evTzddA4NKDZ5AZIs+LCoiHBf3ZatpfKTfhgq02PgbC7Z5Xx3FHfV6+qgH0tgqxEN/BgZdXmePrufDV7j9MqNaDHncGB8RrJddU51Ai/ciiy3R1QWyt8RabqJFSxSycjCFhFJSqLERAAUIoOKjzxCnDv+lYw/t+8/K2BYYRYvXiBv9GF2wz8SDAk/Fjc4NQogfQNHE7CtIGQwEhRxjLFuMx1akbThIAUP1ihpE36ux9+GO70w4/gkVgLLGmiCohmIDJyWQHAIpQUswHFGFjsaYAgcNZrilfjZ9CBYUvAcGFL/WVSly0ps6AMUqlUBYDgKmY5GKisOABNQ2Zq1g5B9OfPymN1a4qZNUjoAYgp2/hB/q79R/8m/ZyvjalKnGWmChGLnLVb85jeCoEH6cvVkEpM/nwimys6ikfoSBGtXJNX+Ivmb4IKIMnyokzDhySbR0YSahAL5CvRxN7kR/P87k8PD/mXo1iiSCTRbFGyAUMZuYvf4//eq872edZ/WK1nRI4/jM+5qcOoM5Es1Pmme9YzQgLHPwZdYxs/T+vCQG1uH2eMM0f3yBBkied8hYxp9ATkSIktCEQmAmzenKZVeV5gzlgXpuPlVEAVYUUnSplp3MUbdvDWX5J6q5KKQ06qo0PTp6G04YnAuCIbZbOllGvi4Rr3+8NOj+fy+x9V4wjAIIvqm/prbeeW9isakaBB7+0lcVDYLEgARSJESgAhlbe4stftYqnQHrtkmBpQCsbSzDsR1Gg7C/t4d3zytfPu7JBYMNBajr2VHnM3H7TAQcPEDJBWZBRgoWImyWVkmrLIvEhZk5gtk1HGmlUrklJbFEoKxRAoFQUPgSERmUJckFt4Yd1qhXmCBcfj3Gtq9NY3augB3ICxje7R+/LvPP5x7+QPFUMwdAgIBURtJzkqrTNDv6w2IMOb+1/6CV6KyITiBJmAwDj14ck8c8cs8CVnTE8RroXNi9mXwgIKqnBgcgiRaFH5ipniR6c/wbUdneCWNJNBj69Tvb/V79E31dFO9BPDVKBg2/5Vv3YTMwAVh/eEzrogj93Spq67Pjt/rtvw5kVcUu19qeDdjt4IFQa0B3dCVqfNezN2kpCRlIMXkT+89oJ9oWXHmigzRuoanVSzSEEBBRBSdoG5I3IiWh9rhmrSpFIlaKI8VEgclFdUVNQur7VhNxU2KUTy+twPv0Cv+7uIuAwlQgCMaG9hS++cnidDVCFgoTSB4wpgjK/iK7GqLRJV0QqtXpmATgfa0ZopgClpIAm5qxVrBURo4Ph42nXPj++Udz+ywmqzy3b2M2ixjSbYOogYHekqyiJNFcwU6/QMHQFi8kj8egumkJ1U5tveupZFgpwEARopoIqWHRIJYeUJmJn1MDKiQRY8HWpmtmz51mckoAh0UJ4giRD73uV7f9o/f6I727OCtWUGFJ3YEMR6VGF2rTbv6N/Pb7+c6n6ru8Tp1cELsYiz7TJdn3czP1TPy/eqX6uMin/T8AKr1h30NRKHHsxl8GRkxFXDYIu8oT8Pb0Vz+ejJO49nJH/xx4FpKlhxqFH3BlxHAzm4Xg3NblFiPCis1KW8n/Tjb43ZsEJJxEd7rV83mvoA13NAnzoBErGXtizrOoydIN39HHclXyCON/t+D2+4M7uBsZeaYOqsVnlxCKSsHBpB4PIwmOSKhI7yau1NVsq0uQoSbIWhgghYlUQqmYiawYuuz9vfpuvf/pRsgCQyiQQ6t/wrllYAWhWBioANzbTHZw89yW9XqMNCVkDAGHA+5y+UJKogo956E3ZYEYFtddFCCEDx3dn9OLc/PpznJ9AhSDrIEYG2CDMJxI6cAcQYuGpVKM3svbXtxQ9JnidXOWM+Jr74O/4nVDRspr7NEfcabqK3Me/VdqdpEhJPVQWmAqAc7HmpHs5rCA47kbasYfUjCstg68PczTSimQoKBSQ66Oqcn09+KRgqQ5FFCmhMQzR2umLDi9u3K3xYFlrCe3FGGT9vmb9enMeYf1YGyrCTl4Xozj28V3hXJVmnU/AM6kL9EAXmEorJYqE94UBnrefKi4XDLVmelIjqCAEQAm6WZkVPcz9ffLRjXSsKFFksJt3V+eq8O3MIJahqvxeW/JADQd67eqauV8PAR4Hyoh7lKJY5R8H3imKj1Mr07clzUPbH+uAl/Bl3ESPKUQDcpApZANsutqiaTBAeyq0zYodoqDEGbQ6Yy5NbUToQGmQYrto0238ovv7j0z/XvZUxGiHAcFdvoxWxWgyoUOCEBCYAGggGt5hoTumMSZIMLFAxFhCzjMAFW+uVUgrIRAOygKgQdaarnsZv2h88Gc8QEoQDxCSDzEln4QUrwGhAEeVt2d6DycWeKSPGlK6X1F/1TapW1MyCbijGkWAPvC3XtlvVrKGKsTIZrECdR9XGNCXewRpGtWXB+UgkgiSTdWFiU5sBQEamWFhAOMznr81TNuiSFnAMXnBIkiRDLl+rEafBb07MG5WE9CyOGif3S/Sr6HW4LanIslp5vswRCbgnOCDHUhviGjAPgggXDJt4J1b4LtsodySex1VucqojkchoSIIgmr0mpYucFnYphgE49btfzR6f8OnTbniqyTUPMOyde/Xr3t7cVt6wG6GWVjOTcu/eGyXuQeFRDtKLS8DpBVLFdQeYQiiI5LsIpcBBRSBQSFSzFAKZQ/0o4nrru1KUNoeRVGtsKbCE0qalIIIgkzKtL39+KW/RLz/fhQUSGYLMAOCvUxtTFVoBIBBKnrnG9FDUuDpXUZQphgCXQFtmAKbUhBlTWAXRRCI1BRIAYVZqmIbXoSWcluOzh//hDw5ghUVdYMBE0AmChQY4CZah3hYwDK3JGQEz5CzzmdEp2S/AF8tH6zr3JKXWdrMtCZADJRskGrJu6+xjUUpOa0lK4gK2wMxoiQWQmUhyk0RQTUxmKUVHawtEjI0aOn8+HUkmiWqzdBiJXWaFqIybssQFJoOwM8ojH+ydfM1Znv9cUpRTEEjBFa0qqdwHT4khtCzeIC0Qh1qhEFERmKxciAtGRJSjd6gzYs/DScWkCqiMTBVD0eqFLY9mMEdtZ3qRoJvugnavjxqGXKU9k1CzbCvYZAJn1WnpPnWdPoSIPZZl7JTCbtUNCArZlINz5gFF7RosUlghk26JJqSWV1EckIGgkEkyo4C029KiBNSQlMYbRZMlwQtNVQGgSCcZr/7Y0ybfsd9wkzLckIEQ3TUS6mIREYkSFY1Ha7F7QQJhmQZSq9VyWqiVBIgA3cxZPu4jkhbMZUpisokFBEVAUBk9lDH1LNXX4v8a/vBx7n7K48qEAQM0ACMExNrMc3Y9LbxarykeSzxL44QvxFbPBWX2ems17TXS8jRVEebSwPcurWKVE/Wuf5lj++mMKGlIbCxwGKxhALE2QBOIIAO0STCSwuKdxuVp39Km/bz+ymJ+L3cBHzJRwAJqcFYomqbr6DTDdKhsTGgkOPuG4ftR+B+f84qNGEc5nE7MGPBo2zSb5gZizTq2aIIBVFasqynphQaBCAoDnEiNSiCsPGHd6/BCXEaqvoX2YgtmXqRVKEOhV0QFNG8byoMG9LvfM8UcFNNcXF/U2EGiGYf9aoYruzJu2AOHOaAC6MAmIpBi8WQAZBTRKpGStVUQhRVejI4VAlPAMU2Am4MU07r15pgi/amX4exJav3qgJB0KEgCUIz261/Z+WvafvnLvxEXWjUhIYMgej1/Yue03ZkgQjUi4SxsduOZjAcig6lBuZRvkfR1xKYhwfIbOThhEwbW6BJSHUpTN9m0fVIbYzrObOc8KSd7uTbrLfeYsV7RH7zLf+rjvKoG1Jj1koFLm5nTx1m+rTSS0JwhBgT2TithqxZVw/Zv7X/sBBISqAQ1EoPSpGMDQagtdhVEhzIyRMpCeR2ppdOeEHGIUWy2WYxNV+zOXn457evd/oVmLzpqIUCd87+6f5UaIoESnwAtUm/TPo5KJ9m8AGEFVJmH581irv9Yd7Q/SzZbg1QmnCeshuoctGU55zoRTobkYDWzCvc89qHjQEyMScejWLiaS25RMilJWa5b4q+OdE4Rb99WPgMJApeTdFGSQYl3nXq+PvhprBnvTBugTgDzM72azzvOb3QXXNF0L8S0KV4zOLPZw1NvNjQBGYbT86RQIq96mpPVeWxZgkvmMFheWsQUxlIkSg7E1SpXR3IcQIeaGLTItG0wVCShFMCMLljG3/zp2Je+/9Mzo2RChiCXQfTBCR4W788CsiUtoboP88woMZ2HJCoNbCZlG40zkwoWMX8uwECKzkmoDjftlX3ndno9brejM8MUIxaVKkaqHY6TG7sfJw7Oz1d+cuV++/zA9SmEKhMT33LdTSYJgIqtESLjwFWZBC2OWWstf+lqaA2aoAHSqxAZe+WIbI0pELevkyUGRJKhYfCZPzX0b3OnH2IGypHswcXKcP959Inlba9LV5oNrpbb8kOJEt/4+4//wr2wT9ej0IhNwQOHSloAl60IV2z9Nk3npd4z13++/O3KntB+iZNBVFWV1Mz1ZAkp9DYkxmpWdNEVuo4ER8REGeQiIQm4LlwSsghho2sMS8DCVPAMnPrhC79QKtLHHl2cxpDN0P3c1L3NGYUZAo1qQiJVtFw/6kjV1YDsqbuwg4wTTfbTE6XJGATtsGTbRfPBM69KqrA8UDBehTDiUxlWQCX/34F/DQaoVOW1RFXQw+VAukTMlFYSLrZiV7KUuYUsG98f0+Nnpc9NSjHMSz2Apv39/3ZwSoCgjohQTVmJhrRdbjcHRsNc6buQSJG4UimwgmDF5rfG1e5uezW52uxv50ZMVLOxUipSVYkZiVhEm6inph/Hx+3LZm6qP+n5P/vNcVVMsy0LhsVhROkGK4chAcyqQAuqpG1jtVHaoDTNbIWSaQlKwlWt6mt9F4Xaqn//779dGcsKM1vCiaHC/r7ivPvys7t1Xsa3pD/XPz9PmFWW78isf7CzokgnYQkEy9DsPvvn+a2XY00lcEEGHnAQQAkyKRO4gIF6u2j2zBf/8TN+qCz57StpeYzIaOvSAkswLOzwQEjgq4qQ+pazV3c2205Gka9GzXljOqiJB3DGobOV8PHaXyvjhRxlxZC6XucAygYgUUpQO9TIy5ubMvHUDAvIsgUgzszHyJdZp4He3rxdjTUf5mpblwIwvOFJvu9KpT1AMPIUjWBAmYRMs8vgSCkRk2WPV4pZwwF2nGifW1aKQq2xGUxqnQ1KAwB2pqAwz5CV7cbBHx/9WAuEGyqg4bByAsTzfeas9FGuJdZCKzA8K5IWKiYrKaCKSDnS/xF6dvyfzlZ/1bY799h7+FNL99Y9K40vZhzrTCXI1RzNKlT9CCEowitGA9c75iSdlCcwfeVn313+ev9nX5/4XLFlhWksthRWaTYyqQTzzglAUbqlRBpDRFMaojKbc1eDTW6l2C2KQlnVngq1/+jEEM5I5MwoUd163Xg/P//29395///4uzzkXtyoBwzVT4sLbiTKLFdKw8t8wXGQ7nL9ivnX9qevi/smYulG5ca4zRRlFm5ZqA1+/4z0kj3vlf/84Z++OmoeeTo0b45ZE5V+XAAKhoqx8TLBJH0TaNcN5elLzAdedCmhzJl1lgVHoR8U3xZdVP+wU7Y4deyNUBIFl7AEiBMqeZGzFlLNPaY8gKx2ApyGHBrag0Xsc4zqXbB0KHJK32/iEllTKDoWc6DNyTwGwDQa3xdiXDXqqLNZXGp7ss7NiaLwBsUIm0qMZy90L22t4pGFKW0jm5ScrePXlmNDoGuRyUywy8dwUqbEGBrUACF0QLm+tzuu/cbxXF0gQKrwRDA7FG4Jm0kUcqnRhJYYmJz/8j//o90OWNFc7oqSXGs7unUflsf2Gr4xi2XRvrlOAyJ5sI6zeM/nYZ7M6H5/ERnLHvWcMqQYoCgSIDAUSWytwlF//vySe6eEUnr+HxdSGIK0gkxhYJkFgIwhw11EI4IGKTeJegKGQwH6qGx5k4mnA87r7rOXBfh5/1e8tbuKnN0evaIZkTquBqGlxCxzyZYGtsmymoHYES/ZfK2tX7Acium28JlHiXNIA5y5ZTaGMWYH5eH0XTfIDLflvXHjfhe+RkxZHZOQcPoa7nXM9jb71wo+7UnXlVf6KGzv2zw/8tryIT1fF0z8mHw+nk/Hp9y/jo0BzhqxR404vM0rQVgogbwrMol93m/qndzWUETvNAiqmrdMBS2bue9c36tbCCmKGE2EMvBqRkXJscpKLv6fvhgG2V/rlvjYr2RM1UJCFrYm1gfniaXmUTzMcOtmmlEcnPawVhHVrrhHmwqdt0wAHmhBMxz7/saHRf7h+2u/w4gEA7KDi6AKVRcoabiogYwsHKq6H7ySkYBGDZjfAZq8alVj2zL7lHLXG6yaoHF6QoIoOLWChP3kG4rz+f35X//NikQCmQJCyFBoAUkBCAnB1ffUE6dtqZnKQZQkILE2Nhjet91Sf5nYoHMVGhnFFt2dh5FIACAAHEJYy7ohCWS0b7A/vwF4nvzSRzlHucuwnsoTNtoKO6gANCfTopYMCgpyiSW3i8HmSAUz6TaDPzi3hSbVYczmG7K+Ya8rbcJ3nPWp7YWFy2/z284XJ5/s9PGbPTPb1CJ1nh2cAVNzEyf94zMEy9/M+4yUnG5IpIA80xHx7gdfC9rz9cl5m+3n83w/ytOvtX+JB5r3JMcEuMs63+vcEdyic7F177173J+qWVrofWfCTksCO2mftB50vuGsIyg2SETIys5rcHZ3lW5F4YaFuDqb4JjN7aTMy896FS7imEuVDNWEKp8YU1bdTpY7KZFcHzzCZLYCRXV0P9gDcjMK2qdLZyLNasjiviG393M4l/eqiCgRJeRQypAKKBSGcAA5FkzO8xaK1u2UdwYv0WuBys6GB5Y1fkI8DA2xsKmqijjweLS5hbNSn+dhfkG//GXnf3yTBaFjpkABilKUsraJtGFfusNKYgsLQIVnwNpoFBBSIIF4m6WmRvhUayUCRNEGSZC5yQoKwKEHeH3uL757A3j02bdfON1Ssdrotwffw6d5kGnBMAUMC6iqgiMluCJJZIWa1GFGQWcgmg7trCreuU1E4Pw2v2/sjW32we1bjHZ4sijNMq44pzkb3oQt1j3MN1qGsuhWIIIW2t8RwPL7PEbQGXsueq2RWZzRAPv9/+jng3+TidhE+/FcbmdmNX2ppLkuYzianJGawJCwKffId3pGN3rB+dA8551jpKHTe9KCDmBP+JFtaQF/82+gJ4Iabbsqu8YITiMZuZi1S7DBADk/SykXYYw4drZnk6UKiZxHZ8iZ7raSGQirBYt+nW4KBAGAIsYofo5+zLKAm7Fht0irGMJpEPLweiW678PKMOJoaZYlXMKYAWkkFQkpYTmwtXNtNxz2ijeRMLQRVbxlJw4WiGzBCPHZPDaszW0BZ1jioFN5ho79xT8+8O+xPr7O2c2CPZAWD4CIoKgZCrKJSKIAKm1M09rjESSRSS5oLm4ugCMMYaoSyYStgJMTKzr3eu7nnx8AT/66j5MTzbxaTtQqnc0MFFgQIVCWDnPaTMUyIOlI0G4BKPEZ1dIQkumIfo+zpv4IMrOT81ff7wZC+n1TWejYrch0sG0PCVi1Cyu5Ylbsh95JuefevaWX8jlZwyj63OH3G35H1UvVdGsGe6NNLGMPtP43k35HRWN5G5v+8Wv/++fMWde6iR1TJIoBDLPsfHqg5/YUoDWoNebezR2GTGh75tNgX8ist44Pc/oe2u9H6fC43Vhare0AjaASdpWxkhacTaG2iyCHhwVFleeTQXOQZVO8PEo7WySjtnYboHoYpp1hyRYsTU0yVA7+ufgxrEBmTMFaQVtTGtNg7JLPpuvJZTw6duDoYr6lKipLC8C3pCFqALGWLq6X+iWNHEJCWKHRa7XlGLHimcDzduQYeyi5HYgSIsDMIShP5C/3k/vh/PqPf1f6928pb+p+CRcJlDw6KJy0EEPLhayRNkmwGYFUmu+KDhsPmzpnwNALQBGGZhibO0JNZois1dvH1/l3BfD4n57HWid00aec6io7C8+CAQo9nAf3Ykrl0uRQKqexbGZpBMrXnNA5SpOPx77vNe9mzqUnyTKLJZHA7dDf/QZ9yS4jxYOLuQKpPiYX96w3pTkj5ylpeu9tljKmd2/iUnudmI6EgxP+vj7Kvz8S3oQ+ccE+zhGhHq59/ve4v9vNqEfSb/PsP/oqopPojV3n12HONiJTAPZ27oEpLlvnZSulpIAO1eZ6szYcMW+hs63ZJFXFw5KQF8GqjOvNl0HtImY9R8O1usm7aqhgKlhIuWSSYVnJ3rxVbr0w1976WavYauvWpRrruGzW2GAq1cWWVgAAHCY2M3DDnvCNCmnUUq2qUgACBJ4+04liYhPS5DQhrRKVYGeCrh3nAmjDILVxvh1o7jMKMjNyUpArgRVmN+bMUpNSNs2tMEAZTKGVgj4Wubh/YItZ8OA//6H6NJ1vP6ruQwhAZdme6S2tLYC2DKKepZzBwVk9cX/f+7v+P3QiKNXMOjOK0sCiBAyXQ7iO8/qn9+WvC5+/vXt8nm09do4eLZXiOvwdOslhDBPKBQvQwTaxECQQpGyplkxzRYebjfrzK9hhene+vxLvX0RR+eUIVpQJYgM2o6H9dPnx7y9zyN5SY2g9p2FK0R93uz8QnEYBj6l7OxBoGoka3yBOlCf8To/Cb6dsgc0oV9fU0wkdObPvz3f+owids2hUF7/5K9ff/xUxKIMLM8bXu2/iSoHTXeO82VmNSPdT8tv9Dg/RkG3kzrzHvC3P6b2ZXRxGpYJneI+pZuV9/8Asx98OlKlDXlpeUlaSqqAK2BVgiuCgaZGLp1lhaRlUQqwmQYo28+jTfiOMSVvLZztQhl1+AUgOBl9lUTkX2M1wwSeXyjRCgkoBimSAzw0Sno6DYT5WGWpFVRYd1VBITKXEDG2mUZrnXJCRAQosusVbmNyLuxyrcZJzNoz7YlEHi+oKkDhYMXEMJmRIGsCwnE/yUGYTbi9f/QvcOQd1PmHPBBHWVkFRTAuT0EzjrP6u/+E/933IzdJgNgj3yCHn7LT32Rue8/0NHz4+en3fT4/W59zX9JnyjYQDBkFSwE2As5whN2IBQRyI5oYWrORz2yG7ZU9/hSt3+unkZ/jNzrTfZl2LBllmwsRBjBlMQtRBjYMtzrGU3LSQo9Y7roTqcaZMV6GsvaEnHJKmOsnUKGhOqCZ9X/jdsY7olSBYjV5y646yB1L/63P3my8uGif+/XGx2++Phk3nRwjD7CQ7IJN50fVePw7PtSZ1qWw344K9GFcqADbbhZtUm0PpbpUIlVhxpH83A/V7DJlI26zjUVsqUisbntF0oJLFw7dScJG+r1VHaFNJrgfz1OOGkRfiKOJMkGIfq35OWI7LBlDq28ea9yIDONvYux3EZT41YiUAM5jARIXSn2eZGEQ+bSY0TZVzsFFWNRS1ocSBboQLyeBHERVFFGoBu6uuGnTebjYwgydkqxLLdrqxA/Ns1Ltkug2tiABBLQCedSEtjLFcs93BDx6ef3DuXuZaQqkgbARqj8xBiRzNOa9+9v2AQjObAJm03fd1/Prx5WP87u7H5wc4J7uV3tO6Jj9UPLTGbOholpFwlLoCohwN8xZcIUw8aZRDPiumqaHcafBl/f7kE7j89kvZytcuJTBblAQkCFDJICCwgTgh2PX4X+8w1LyJE6iXJZ1kh00j7r0QciO11P0SmTXvCfcR0QT879xnr38XI7Bja0EPId14juJgjf59r5n2911trf/24s6zv5tOTx1n5vwxTsmcXKVFju6hLB3oOTTrDjqKPasA5t6xkaYD79gmayLCzNiRuikLFmvTxlbSkpzWqLKCygJltQJ2EAgKZXBuVWxvjZmwq5TZO02bZAOhDF/N1YxRrfMcCzvK8oMsRICiIPDH/9cq/34WVI4iwpvtRslczzYFomEpQtQFnvuxIVOe/Ot3f25UFBY1Jpgoylo42wyXKOeZAABFWElGhAAAAE1NACoAAAAIAAUBEgADAAAAAQABAAABGgAFAAAAAQAAAEoBGwAFAAAAAQAAAFIBKAADAAAAAQACAACHaQAEAAAAAQAAAFoAAAAAAAAASAAAAAEAAABIAAAAAQADoAEAAwAAAAEAAQAAoAIABAAAAAEAAAFAoAMABAAAAAEAAAFAAAAAAFhNUCC4AgAAPHg6eG1wbWV0YSB4bWxuczp4PSJhZG9iZTpuczptZXRhLyIgeDp4bXB0az0iWE1QIENvcmUgNi4wLjAiPgogICA8cmRmOlJERiB4bWxuczpyZGY9Imh0dHA6Ly93d3cudzMub3JnLzE5OTkvMDIvMjItcmRmLXN5bnRheC1ucyMiPgogICAgICA8cmRmOkRlc2NyaXB0aW9uIHJkZjphYm91dD0iIgogICAgICAgICAgICB4bWxuczp0aWZmPSJodHRwOi8vbnMuYWRvYmUuY29tL3RpZmYvMS4wLyIKICAgICAgICAgICAgeG1sbnM6ZXhpZj0iaHR0cDovL25zLmFkb2JlLmNvbS9leGlmLzEuMC8iPgogICAgICAgICA8dGlmZjpZUmVzb2x1dGlvbj43Mi8xPC90aWZmOllSZXNvbHV0aW9uPgogICAgICAgICA8dGlmZjpSZXNvbHV0aW9uVW5pdD4yPC90aWZmOlJlc29sdXRpb25Vbml0PgogICAgICAgICA8dGlmZjpYUmVzb2x1dGlvbj43Mi8xPC90aWZmOlhSZXNvbHV0aW9uPgogICAgICAgICA8dGlmZjpPcmllbnRhdGlvbj4xPC90aWZmOk9yaWVudGF0aW9uPgogICAgICAgICA8ZXhpZjpQaXhlbFhEaW1lbnNpb24+NjQwPC9leGlmOlBpeGVsWERpbWVuc2lvbj4KICAgICAgICAgPGV4aWY6Q29sb3JTcGFjZT4xPC9leGlmOkNvbG9yU3BhY2U+CiAgICAgICAgIDxleGlmOlBpeGVsWURpbWVuc2lvbj42NDA8L2V4aWY6UGl4ZWxZRGltZW5zaW9uPgogICAgICA8L3JkZjpEZXNjcmlwdGlvbj4KICAgPC9yZGY6UkRGPgo8L3g6eG1wbWV0YT4K
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAYAAABS3GwHAAAAAXNSR0IArs4c6QAAIABJREFUeF7tnQeUVEXWx3/1unvykEEko4ISdRAxoCwoJiQqQxQEUYKYPtPqquu4hnXNqIsCgihRBiSKccUMSBQkiCJRch4mdver79SDwWGYofO8nqHqHA7nTNe7det/61+57hXopBE4gxEQZ3DdddU1AmgC6EZwRiOgCXBGm19XXhNAt4EzGgFNgDPa/LrymgC6DZzRCGgCnNHm15XXBNBt4IxGQBPgjDa/rrwmgG4DZzQCmgBntPl15TUBdBs4oxHQBDijza8rH2ECSJGWhlizJl2kaqw1AgEgkA40abJWpqU9JUHIAD4NKGvYCTBgwII4cnKqI/MuEVJcZ0ANE1kJKVwBaaYzn9EICMw8MPYjxE5TmF8gYpYQF7dr/Ph2OeEEJmwESEtb4Ny+LqOlV9JDIDsgOReBM5zKallnKAISD4KNEjHfIZhWq1Hy0rS0dp5woBE2AgzqMeshibgXqAE4wqGclqERKISAF9ghkG+Mndb15XCgEzIBhvWZVzHX7X0BwSDd8MNhEi3DDwS8SMbGuhyPvj2540E/8hebJSQCqPm+kXXkYeBRICEURfS3GoEAEcgCXjATyr0UyrogJALc3n3mdRhiCohKASqvs2sEwoCAPIApe4+b3u3zYIUFTYDbO89OFnHiS4lsFWzh+juNQKgICMRPMke2HzenS0YwsoIkgBQDus8eZhi8CcIIpmD9jUYgPAhI0zS5Z/z0Lm8Hc14QFAHU3F9kHv5ECNE2PJXQUjQCwSMgpfxaJpa/MZi1QFAEGJg6q7EQ4lOgdvBq6y81AmFDYJuU8ob30ruuDVRicAToMet6gZgEVA60QJ1fIxB+BMReKen1XnrnrwKVHQQBpBjYY05fIRmJIDnQAnV+jUDYEZAcEsIYOHZap1mByg6YAGlpacaWNSlDEPIVgYgPtECdXyMQAQSOSMyh703rOjXQhXAIBOAVAZoAEbCmFhkwApoAAUOmPyhLCJQsAZzrE+82pfgPiDi7UDQTq0Cl2mDYdAxheuHANsgM6SpKSPBJdQRTsRYi2ca9CNOEg9swju4LqS6hfCyQR50i955Hpz7+voCA3g4EPAWSA4hz57ledkrPXULIgL8PpaInvhWCrL/dg6PPCxgxsWERGagQkZ2BGD8MuXh6YIgHWtBp8pvOePJ6vELcdQPBJj/HZl4u3smPkfDNGyADanthQ0IiTFMa/3XEeh8R4wnovUDADVj2oh6CWQguDFsNAhUkDHI7Pokr9Z8YDptGgKxDMOp2WDozUO3Dlt/riCO3xysk3DQMRMCmDIseptfEk/4vYuY9A9IMi8yghEh+RtJVTGVzIN8HjJrsRR8MPrD16rPhxOz5AkbHBwOpa3jzZh6Akf1h5cfhlRuANK8RQ173/xDf+T7bCKDUlfNeQXz4KJhheaMSAAInZfVi0l9MZXIgAgIigOxEAkl8jMDWKxBmTBLu294htm3fQOoa3rwZ++CtPvDLF+GVG4A0UzjJu/l54ro9ZCsBcr+ejOv9oRh5Qd1HC6DGPrJKvuYoN4m5qKvSfqXACNCHdsBngK3ve70JlckbPIn4S673q5IRyXRkD4zoAeu/iYh4f4SaOPB0e5qYW/5hKwGyl35OzKg+OLL2+6N2JPO4gevFZBb4W4jfBFCLX3IZg+BWf4VHKp8sVx3vvTNwNroiUkX4lntoF7x+M/y20HfeCOWQCMyuT+Ho/k9bCeBZ/yOON25BHN4VoZoGIFYykVju9Hcx7D8BepGCgTpqrhOAOhHJalauj/nQPJx1GkdEvl9CD/wJr3aBTcv8yh6pTGbnf2CkPmPfdjDg3bYO8fJNGPs2Raqagcjdimkthlf485FfBJBtcVKT+5A8C9i2959fIXeN5ngf/YK4ytX8qWNk8uzfCi91gm2rIiPfT6me6x+0toOF0z4HHLn792K80B7XDnuxOA5ZDoIn+JMR4mt8rsr9I0AqVXExQc2v/LRLRLN56rXCfOJbYuLtOQOwKrd3E7zYAXasj2hdfQnPbXc3rv4v23YeovTLy87F8dzfcGxa7Evdkvr9M9z0E+ns9VWgfwTozdUIpkXL9Wdv4/YYj32OMPxS3xcGwf2+eyO8cB3s+SO478P0VXbrO4i5/Q0ccfZdy5KmxPz39TjW2rcjVgjO/Sj/VFPweT3aZwuSaqXVl9FguT3xmT9Mdj2tmMzWw0i8a2RJFFV8GTs3wL/bw/5ttuqR3ao/MXeOxJGQaKsemW8PJ/F7m23yFwLqSHoskxgsxOkP6n02aNmHBsD3gI0T7pNte7jLS5Tv8ZCtBufPdfBcOzi821Y9slJ6EjtsNI7EcrbqcST9VcrNsvFg8tTa7wGuFJP57XTAnJYAMhUHLv4B/MtWdAsVnjvofWKv7m+vStt+gWf+BupE2MaU1exmYu8ehyOpvI1aQO6CCcS+a7NNTkXgn7h5XqSjPMoVmU5PgF7UxmAOcJGt6BYoXBpOPA/Mx5Vyrb0qbV0FT7eGnKO26pHdpCMx93yAI7mirXq4V36B85UOCHuvQxTGYCUmncVUip2nFksA5ZOaPvQERgH2jq8FquWNSSL7qeUk1VMzMxvT5hXw1GXgybNRCchtdD2ueydhlLPxSjSQufl34p5OwZFnb4dQyBhHgCFM5sPirkkXT4DOJJPECOA2wKYrl6e2LW9CRXJf3ExCRZs5+ccS+Oeltl0BzkfGff7VOO6bilG+qq1EzDqUQezD9XBk2TslLASCup76Pke5T8yhyItKxROgH43woq461rcV2cKFVzgb843t9l2Dztfn1+/gX21sh0Y2vApx/3Qob+8ehWlKjHtqwqGdtmNSSIFNOLhJTGBdUYoVT4DePIzg37Zeey5C46x6bUh4zr4LaCdUWvUZ/OcG241tnnMp4oGZiIpn265L1pNtSfgjCmxzMhLKk/RjYgov+U0A2YeKSBbY+uilGHMebnk75f9vrO3GZslH8PottuvhrnURjofmYFS130fZ4dfvoPySKLBNYauoxzKCdmIyp7xfLXIEkL25FcF7EH0RXnJueIy4fs/b3vD4YSKM7Ge7HrnVGuF4dD7Os+rZrkvOhMeJ+zQKbHMqEh4kA8UUJhb+6RQCyL6UQzIDaG87ooUUkMKB2ecVHB3us1+1r0bD2CG265FT4Vycj3+Gs8a5tuvinf8GxuQHELLYbXc7dfwSwS1iEmpn6EQ6lQDHHr0ot4f2TyoLwWU648ge/CGJrTvbCeSxsj95HSb+n+16ZCfVxvnkl7hqNbRdl8wf5xA/qieGJ6B36SWlt1qd9y38WOYkAsgbiaUCTyJ4xO5XX0WhYsYmk/3QlyQ2joKQBLOfh2mPl5Txii0nO646zqe+wlWnke26ZK5dQvzL12Dk2vw0smgk3Ehe5BDPiE/Izc9yMgH6UgtQfj4utR3NIhSQiZUw//kjjlrn26/etCdg9nO265HjqoTj6W9w1W1quy7e7b9i/OsKhM3XQ4oFQqDua3cXk9heNAH6oOJZq8WvvVcLi6mBu0pDHE98gVHV9kdpMOEB+PQ12xtdjiMZ59Pf46zf3HZdzL1b8T53La69G2zXpRgFMoGBYjIqDreVTowA1sU3J/MQ1qMXn7dE7ahhdr0riXloOo6KZ9lR/MllqgWwWgjbnPJEPI5nfsRR3/7rWt6Du8l7uTvxm9Xl4ahMEslneOiYf0HuLwL04lKEtfdv38sKH5jlNe2A8+4JGMlREJPv7f7wvXokZ2/y4kQ8swjjnIvtVQQwMw7geas/Mb/Y5yvJJwiSbCTtxFRrOnSsp5eDcXEU9ZrhDp8CbMsg8F7WG+OOtxHxNt8DUh7Q3ugBP6ndYnuTeq8kn16EcZ79GwMyOwP57lCMRVNUq7IXmNOX/i5J3CVG4z5GgN40AWYjsH8zuRjFpeEg9+r7iOn7HEaMze/ylWPcVzrDyvlRYWT337/C1VztXtubzLwc8iY9TuxXIxAKo2hNko1AFzGFNUKmYbCBu4AXiWJ//9LhIrfTU8R0exTD6bAXWq/n2HvgtX77X4qovlnDZ5Nwhf1nI6bHS97M/xA7Nw3hVT6qojZlA4/QkJFCplIJF+OBjtG6+LVgdMbi7fkixo33IGxyBHvCnOoNwLNtbXWKVbBpZQycRHL7Pra3Nikl5qdv4pj6CHhObLXbrlcRCqj52TzcDBCyFy0xUJG27X1S5AMmdQjmHTAKV5ve9gPqzj32GGbLSvt1AQ71Gk2FTndGhS7u76bgeG9ItB6GFcToICbXCdnHeu/7RFT3/sr7WGJV8oZOJb7F1fYbOi8H/pECO+31CZQPxMFur1Gx+/324wJkL/+KmHd64cj06ZLHbn3VKPCsIoBycN/Vbm18lW+Wr4Hn/tnENGzpK2vkf8/Lgocbwb6tkS/LjxIOdXiOCn2V7wL7U96GpThf74JxeIf9yvjWYJYigPLuepnvvPbmkFXrw8PzETUvsFcRVXpuJtx/DigP0VGQDl/7BOUHPBMFmoD8cz281AGhPOdFf1qkCKBcm0XXs8cigHPXbgkPz8NVOQpOgXMyYHhNUP9HQcpo9yDJd7wcBZqAe/9ueKkjrm1Lo0IfH0psUgRQVkyKdm3zGl6DeGg2rsQouKaUfQSGVIEo2erLbnMX8UP+GxUmdGdmIl/uQsyG/0WFPj6UOCpkX+to2OaTJd9YmRd1ggdm2f8YXqmasReG2vsIvSBinqsG4Rz6rm8QSyCHihkmX+2KY+XcEigtxCIEOWoEUPEt7XUq40c93G3vwnVndPRy1uL3vrp+aF0yWczL+2AMn2hrkIyCNXWPGY7r66jxE3o6I+xXBFgD2Bhpwr9GktF9BMnd7vUvc6RzqYXeI/Y/QMmvZl7zLrgenoEwbD4hP65QxswRJE+Pjm1ZH01hrZoCfahcSUe6zYQqP3PIdBLb2O+FwaqHigrzRBRsxx4HNavBtcQ9MR/DxiAZBe2b+e0MEkd1D9Xkkf9eME2NAH8Hy/9PVL4BsFAwHJiPfYnR2NbglH8ZZP138Iz9TrHyFcqo1ZrEZxdguGyNXXgCH3PN11bEGKL5Qtyx66qPCdmbKxHWVYiofQfgiauI+dSPxNSJgjMAZeYocYqV3+KOVE0h8cWFOGJsjJhToL/O27oe4+krcOac4oYn8r26/yWozZ/r1F2g2gg+QxA9k9pClXBXqIP3mRXEVYqChzBKNxUd/rWb/Yc6wjkPlz+fpNdW4oiNjs28nAMHcDyZgutQdJyUFwm/ZB2S64XsRyJeXgdujyYnuAWV9lY/H/nv1ThjomOIjxanWCdGgPi6JL61FkdcQoSp5p94T54b8VgzHLt+9e+Dks+lnOaOw8H9wnKD3pfeSN6OJjfoBTFxN2yL66nouHtv6RUlTrFOrAFcZ5H49kaM+Cg4JDyulPvpdrg2fF3yTdu/Eo8gGMYkphx7EXYrZ2NanqBT/Pu+ZHNlXD6E5LvfKdlCT1fap6/DBPudYuWrmOUoT9yo7Rjx0XOgn/HWUJIXqtASUZlWYHCTmMjOvx7F9+UupBUPwL6As8VgldnpGRJ7qRvbUZKixClWPhp5Ig7XmN32v5UuYJ7MKc+SOO/JKDHYSWp4ENwnJllv4Au4RTnmE3SaWhkjomhLVBh4bxuJ41r7/XBaMEoJ0/8Js1TM8OhIJgZi9AFEor1xwgqi4f38HRwfDAflQCBaknKKonY8BT3yfYSe7BmuF1dhWE6DouDK5THUTFcCnmGTibm0S3TAqAw6+RGY/0p06HNcC88bO3FWrh41OuUtmo3znT4Y7qyo0QnYjUmqmMp3+UqdTIBUYojhQaT1QiwqthRy4qqROWwmlVteER1Aml6ylRvwz19UDkmiQqcc4slMW0XlBudFhT5Kif1LfyDx7W7E5UTNy7AcyzdoFZ4XbxbjG9Qa4VOpjsvyEKFeWdt6ucSNi2/l9ay94F56Dr6CatXt3+XYtyeLeWP+x2VrHucCsdr2BpdNArO9vdmXMoheAy+kSjX7+609uzL5cNSPNP71DdqIz3Bhs4cIgWm5/Dd5sHDEyKIDZPSjGh7GIbjJTgt/L9szw9uPo0YFGjerRv/BzalcxT4DZ2W6+XDCGhZ+u42zzc3cboygrlAuZuxJyivc/8ybmG32xu1I5PKratKjX1MSk+w7L9m/L4sPRq9i7eo9JJmHuMUxgSvFl/YA9Fepn1keINLZVViR4mOEpVITJyMR3FjSrtLziGWhbMs07wByjs/EDEPQ8rIapN7amEqVS/7WxtGMPGan/8o3X27G67X8sXGeWEc/YyQ1xPYSnw4pjBabVzHNvJ2s476MHQ5Bm2vq0aVHQ5KTS/5axIH92aRPXMvSRTtQQfNUiiOLHo7xXC6+JuavmUdJEUK5RFfO0IeLj/7yCF2w8NPHCb6Vc/Fa8QKU1+gSaXWZJPGl2ZH/mR3JJPkkoBxOg2YXVaPTzQ2pU788ihSRTsrXzY7tR/l45gaWKMN6/5r3KxLUERvpZKTTVCwrsaH+oKzM/+RNLDBvPNFB5OOgMLnk8hrc1K0BNWoll4gPJdXYt246zNyPNrB65R68npN3fhLJ4BpjHu2NeSRSYnGE1V2fdBw8w0Q2Bhwn2FoPqG3SblQinlstT1pQI5INbp+sxiyzL8vlpeQWwzdhCKpXT6Rz9/O5+LKzcTgiF8JYNf51v+xn5tR1bNl0yOr5i0rlOUh7Yy5XG/OJQzkdi1zaIWvzkXkrv8gWuIkpsiA1EtStX4FuvS6gUdMqESWB12uybNFO5kz/lV27MpHHe/7CisWSTQuxmK7GJKqIiDsTUC4pXiSbiczkQHGNX+noVxdquU53cAUGjwKtweqaw9Ly1GRC9frrZTPmenuxHeX737dacXFOrrq6Du2uq0elKgm4XGFRx7KbMur+fdn8sGArX32+GTX395UceGgultLBMYOabCWW8IUJUvv8GZRnpdmK+fIW9kn/dqkTElxcfX09WrerQ+Uq8WHtLNxukwP7sljw+Wa++2orOTkeXxBZXWotttLJMdXaQFCjQRh30tSwo963/4DJC3j5Md8F+ukU893Sjn9tjQb9qeT1cO0Rqgx24m6TSIbDILiDDmXUA7IKv9GYZebl/CqbkhXg23zlIfHsmslcfOnZXNSyOjVqJhMTG/zGlTvPy+5dmaxavpvlP+1k65YjpwznvqxcSezjIrGYFLGYeuJ34skK2sheHBZGa+WFLJNX8JtsjJr7B5LUtLFO3XK0aHU2zVPO4qyzE3HFBI9RXq6XHX9msHLpLpYt3snOPzOss8FAUgJHOV/8wsXGQhqwFoVZKO0oUyZ5TIwFSeLQOIeTL/jg9L2+X2uA4io0LTXVsYy2dyeLrH83NlbGp4hFVBc7/Br6VW+v9qx3ypqsli1ZIS9lr6xOLnHWEV2wyek0SC4Xy7nnV6TlpTU47/xKlK8Q69caQc1fM4/msXnjIWuOv2Htfg4dzEH1cMEmB16UkeuITbQQC2ksVlpGduK7l7QwkgnsoJbV6H8xW7CPalbDDwUjNUKWrxjH+Y0rW5sJ9c+tQGJSjN8YHT6Uy++/HmDp4h1s/PUgGUdy8RSa6weCl+r51ShZVeyyOotmYilniz+tduTPqKDa0S5ZgxXyMtaZF2bkyLh7/9Xk3g9EWmA9csCtLi0tzdiyJmUIglcExKuV/VliB/XFb9RhI1XZba32VSNQvXweMWSTyG5qsEPWYZusyy5qobbwIpHUqFChYhy165aj/nkVrYWgMrQrxrCMrQ5y3W6vNa3ZteMomzYeshZwavsu0J7MX/3VIrCW2GxhVIstlOcQLgsjRQgDN05rzbOH6myR57JFnscuakQUI7WdrDYSFBGq10giIdGFy+VAGFg7OO480+oYdmzPYNPvB9m25YjVMUQKI4VFdbZTW2yhhtjKWexQx3vEkGeNDmo0VJ3AXs5iK+eySTZgt6yRPyIekZhD35vWdSqoC87+p5AJcHJR0toJceI+QQC1UPPgCqn38r86p+ZUhIiJceB0FSCAcuOd642YMX3p6yIP9U91EqpX9+C0DGnadO5oYRTrwOX8iwAet0lenn0YqVFAtSOFUz4BVDtSfylijRgtBPBlev27RiAiCGgCRARWLbS0IKAJUFospfWMCAKaABGBVQstLQhoApQWS2k9I4KAJkBEYNVCSwsCmgClxVJaz4ggoAkQEVi10NKCgCZAabGU1jMiCGgCRARWLbS0IKAJUFospfWMCAKaABGBVQstLQhoApQWS2k9I4KAJkBEYNVCSwsCmgClxVJaz4ggoAkQEVi10NKCgCZAabGU1jMiCGgC+Aurev3kdDlISoohIfHYs8zsLA9HjuRaD+Aj9eQvXz/l1kW9zy1XLpa4eCemaXI0w2090Qzlja2/9VfPQtWj+HLlY4iNdWJKSdZRN0eP5qFegZXSpAngy3Cq4at3sJe3qWW5WaxYKQ6n89iLUOXvR713/Xn5bn74ehuHD4XPpcmJhi8ENWon07pNbS5oWtl6p6x8GinfQ+oB/r7dmaxcttvyqnbkcK6v6gT8uxCCmrWTubJdHethfGKiC+N4+Yp4+/dmW54eFv+wnYwjeQHLt/kDTYDTGUB5Q2h7TV3adzjHevx9upSRkcfHH21g4ffbORqGhmA90q8UzzU31Kdt+7rEJ5y+/L27s5g3cwPLFu+wRqZQk2r4VarFc33H86zG78t/0sED2cxJP+YFLzvLtz+kUPUL0/eaAEUBqRqf8gyhvMg1blbFb8dQqkdUPm9mp69n987MoG2kphvnNqzIzb0a0bBRZb/lqPJ/+vFP5s/6jZ1/huZKUJV7S+9GnNOgol8uUJSSysnVkoU7LF+oB/dH1tOd36CcPqMmQFH41DunAgOGXkStOuVQZAgkKR+gG9bv553XlwY9JVAuWQYNT6Fu/fIBuydUrkmUg64PxvyM8skTTDq3QUUG3d2CamclBl7/4+VPeHeVNT2M8qQJUNhAylFW/zuak9KqesCNL1+WWhArV+iT31tNdnZg0xG1yB72wMVc0KRq0G1HrU0+/3gjM6eut9w1BpJULIUh912M6gSCTWok+mze78yd8RvKa14UJ02AwsZRPkNTb21CbAiuEpXMzKNuJo5dZU0J1ILVn6Sc097YpQFdUs/3e9pRnFy1Dhjz1nJ+XnaKa/tiVVHz/A5dGnBj1wY+5/y+6qMcho0asYyNG6I66rsmQEFDqt73kbTW1q5HqEm1+aWL/uT90av8XhQq/5t3P9zK8lUajqRcjo8esYwsPxelyhHuPY9cannHCzUp0ivnt++P/jlUUZH8XhOgILopl1TnrgcuCbn3zZe5f28Wrz6/yHKl6E+67Mpa9LujubXPH46ktmX/+8oSv3th5Qj3zntaWB7xwpEOHMjm2ce+DXotEg4dfMjQBCgIUO8BTWl/4zlhw125URz95jJWLPE9DVGOejt3b8gNnRugpkLhSLm5XiaNW2WdUfiTVBSdGzqe54+XeX/EWeckI15YxJpVURPwrrDemgD5iKhGd/dDl9C8RfhChqpp0LQJv/D5x3/4bDCxcU763t6MK9rUDnjnpTjhajE6e/qvfDr79xOhh06nyP2PXWZF0glnmjJ+NV9+simcIsMpSxMgH0017N/7SCsaNQt+96Uoy8ydsYFZ09b7NFp8gpMBQy6yXJCHK6keWJ0JqBBEhcMPFVXGE8+3sbw+hzPNnb6BWem+6x/OMgOQpQmQD5aagqgFaDh7QDUCzJiylk9m/+7TJmref+ug5qh1QKBnD8UJV41eEXD+7N+KDdNU8NuHnrzCCo0UzpQ+aS2fzvFd/3CWGYAsTYCCYA0cepF17B+upC6JjXtnJYu/3+5TpNqCvLl3I2sNEq4gfmoPXoVn/fqLzX5d1lPnH3+7tp5PXf3NoHaCRr661IqaE6VJE6CgYVTssNsGXxj0AVhhIx85lMtrLyyyAmn4SqrXb9O+Hr36NwnbLoy6nDb6jWWsXe3fIrT132rTf/CFqNEwHEmFiH3uie9QAbCjNGkCFDRMlaoJ/D2tNZWqhB7ZVU1/1qzaw5g3l6Magj+p7jkVuOuBlig9wpH++O0gb738k9/bkOoKxj0Pt0KdBocjqd2vka8u8WsBHo7ygpChCVAQNNULd+1xAR26Ngh5GqK2QKdPXmtFQ8wP/uzLQGoapNYB4ZiGqenHpHGr/Z7+KN3U6XePfk1oc03dkOuvboSOfnO5dS8pipMmQGHjVK2WwJD7W1p3YUJZjP66dj9j3lrGwf2BXQhTcbfu+/ulIfXCqvGvXrGHt19faoV0CiSpW6h33t2CqmcFPwoowi/6fvuxu1BhuJodiP4B5tUEKAyYWoCmtKxO74HNrMcvwSQVAnTc2ytRU5BgkjqR7jOgWVBTMTX12rTxIBPG/MzWzUcCLl6dh7RqXZNe/ZuSlFx0QG1fQjf+doCJ765m65bDVtT0KE6aAEUZR8XIvTClGrcNuSjgRvDntgyr8f2+4YBfOy9Fla8Woa2uqGlNR5LLBdYIFfnee+dni3z+XsIrrIMiwcWX1bAW5OUrBNYJKPKNfWsFu3YeDbr+JUgYTYDTgV33nPKk9m1C/fMqoCLMF5dUr5uT7bEavdr33rHtSMjGV9OvBhdUpmf/ppxdM+m0t1NV+ept8LrVe63y9+3NCrkNqZGw6YVV6dLjAitk7OnuBx0rPw91+W7GlHUc2FcqHsMojDQBTttSBJQvH0vTC6txQdMq1KxdzpoWqWsLKuXmeDh8MIctmw+zdtVeqwGohhjOVKFSHBddXJ1GTapYb4PLlY+1QpNKU1q3PNUaQ5X/y8o9rF+zzyJiuJIiYcVK8agpmXoPXKNWOetRvHocn0/6A/uzrG1eVXdVfpTP+QtDowngT2PJj4ebmBhDYrKLmBhFABUU2mvd+1eeESIZP1j1xop0iUku61G6aoBqoZmb47XKzs50W0G8/Xx24E+VT8qTX35SuRgSEly7D031AAAGp0lEQVS4nIY1tc/L9VjlZ2ZEtvyAFfb/A00A/7HSOcsgApoAZdCoukr+I6AJ4D9WOmcZREAToAwaVVfJfwQ0AfzHSucsgwhoApRBo+oq+Y+AJoD/WOmcZRABTYAyaFRdJf8R0ATwHyudswwioAlQBo2qq+Q/ApoA/mOlc5ZBBDQByqBRdZX8R0ATwH+sdM4yiIAmQBk0qq6S/whoAviPlc5ZBhHQBCiDRtVV8h+BkiZAizuEkK8B4XF8439FdU6NwCkISFBvVwe/l95lGoiAnu8H4b9bioGp83oIYY4GQo/AoA2qEQgRAQkHJcZt46d1mhuoqCAIAANT51wthJwKhNcFc6Da6/wagWMI7BGQOnZal28DBSQoAgzoOrOeEWN8AZwXaIE6v0YgAgj8LjzO9mM/umlLoLKDIkBq6rSYZBE7EUgNtECdXyMQAQTSM2TurenpPfxz3lpAgaAIoL4flDr7Jin4CAjM41MEaq9FntEI5AnJzWPTu3wcDApBE+DGG+fHVk90fyAMaxQIWk4wSutvNALHEZDSJH1Xpqv/J590CCqaeEgNt/8ts1OcTjEdKcMXkU7bViPgLwJC/OHxyO4fzOiywt9PCucLiQCpqdMcSUZMfyHFf/SOULAm0N8FicBeKeTfj5p5H6Sn9wjMdXY41gD5MgYMWBDnzDrS3St5XAgaAuEJSxIkKvqzMo+AKSUbHILnPAnlpo8f3y4wv/WF4AlpBMiXlZaWZmz9+eJmOM3nMOR1SOEq82bQFSx5BIR0Y4rP8RiP17lw2eq0tDQzVCXCQoB8JQZ3mpvgjpO3IuQQATUlspxAqF2i8IQsD7W2+vvShoCa2qjFbYaEP5FilCtHTBw9t1PobrOPIxFWAuSj27fv/HKxeZ7mCNlImOZZUhgVEbL0jApStEJwSVmZzkmQArEGzAWlhQESkYeUB4UQe5BiXW6Mc9WkSR0CjxTio8IRIcDJZUoxePBo58GDFUugrPCYN4mk84Rwvw1cVfq3eNXlMLnKFGJoppmzPDwIRV5Kk71VzbSv23oDvdwWqGalplEGWrFQ8w/sOacFpjlaCNGi9JLAuhm53mt676nf9OcF4Zgzh4prtH2vCVCsRaS4I3VWC1MYr4K8EkSp2t2SEimEWCEdPHzUk/NNKFuF0dZow6mPJsDp0RS39Z7T2OGVIyVcJUrPibfq+VeYQgyv12j5T7rnL97ImgA+u5PjIwHGO1JwcSkggYqpt1YI7qnTeMU3uvH76OF82l9nUGGUSst0yJRSrnA4HA8d9mZ/p6c9vhuvHgF8Y3Q8hxS39Z5rTYeidHdIIlgmTGN47SbLluqe3z/DagL4h1N+LnFH6swWXsSoKNsdkiDWSMnddZss/043fv+NqgngP1YnRoKBPeemCGk5BbjS7sMya7cHlgnBg7Ubd/4+LU2EfD0gYEhK8QeaAEEa746e8xp58Y4S0iKBTTgKiZTLDMyhY9K7LhcBekQIsupl6jObDFc2MBzUa36KabrfFZBiAwmklHKtwBg6Lr3TD5E+MS0bFju1FpoAIVp2UK/ZKXgZIYVsXYKHZSaIZQL5f2Ondf5RN/7gjagJEDx2J74c3HvuBV6POVqKEpkOqUDyS53SHDwmvdvPVqh7nYJGQBMgaOhO/vDYdMgzRiAjeXdINf5fMB1D35vecaFu/KEbTxMgdAxPSFDTIdPLCCFoHe7doeN3e5Ygxf3j0jsu0tOe8BhOEyA8OJ6Q0q/nR42cpmOUCO90SCL5CY8xZNzMTmrao1OYENAECBOQBcUM7DmjBaZrtBBhmQ6pOb51n3/8h50W654/vAbTBAgvnvnSxG2pM1s4Qr9KbYJcjDQfHJfeTU97ImArTYAIgHpcpLjtljmNHY6gr1Krac9CE3P4+PSuP+uePzKG0gSIDK7HpUpxW+rHLRx4A71KrU54V5qG967xH96spz0RtJEmQATBPSY60KvUUt3lWSi9PFi32col+mJbZA2kCRBZfE+MBIN6zmwipeO/Pl6WqQXvD4aX4e/O6LxaT3sibxxNgMhjfMp0CMHFRdwdsp4xeqQ57IP0rkt04y8Zw2gClAzOJ0hQ9EN7Ne0RP5pCPDD+w05LdeMvOaNoApQc1ie2SAemzm9UwO+QusT8vWGKYWNmdFqrG3/JGkQToGTxPlHaMb9DcowQYEhz8Lvp3ZbZpMoZXawmgI3mH3TL7BRcMHZq8P7tbVS/TBStCVAmzKgrESwCmgDBIqe/KxMIaAKUCTPqSgSLgCZAsMjp78oEAv8Pd6MIoKe72RgAAAAASUVORK5CYII=
- data:image/webp;base64,UklGRnyaAQBXRUJQVlA4WAoAAAAMAAAAPwEAPwEAVlA4TBGXAQAvP8FPAE04DIA0bAopNRn4/8FJuxci+j8BLLur27b5WZZUorq7SqTs7gOP0qG3rn6nfKf3N5IW1/qgg+3+dpZIEgDKPVXN6u6O22/eSEpjrDEeSZvbm/mnrF5rrTGA6oPTu/9w96LW2FRVRXd3V1X/w0VJYwDQnKfEQfvbIqtUAEZJPUkmsWn80XJ+6gakIc650cc/2lLtY72wuzvJHxJPvx692VTvX+KtJOlX1d0kt467HYc2jqa62wGqqkWSto2z/aW7s7pbUotzbrH9Jdu+1G2JIuecPF6Or+uyffm6LlKanaqqJZGck4ANGMbZAGylqtGqNDcSAOx75AZuG7AZDybVPRKTa5H0dV32dZm5eJGXLwZkcsc8a5HGq3E2zCMGaVeRa8ub7QQYzGnvqiZFMrav67p48drNr7B71SRJwzaOxm673ri4WF0iHSQxADtI4mzjJJJWTZLZ6YRns0hykDTJdC3XJCMZSXwy+nlM2qYNJJhV+jFxkpjHMYDneR7SDs58fuqfT/HhfnY8z+2BY1Wx2kyCLacbeI4Du3RYroRAYh943zfwPM9A8MyqKpBcsjvHF9z389wea/Rz3zgUWdN2goR7kfdd1UP6tfoehLFAiszI/mbAWUu/UvcNEIBMMvgCEoi9JFXP1IQBIKRx9idKS+pJzu4qxDYBkOCr5INU3WLdUhXSJv+g31QlqcinCiBJAC8O4GQrHeveqmxSL8UxRoxoc4tTpRvbgpJq25Ek6SA+TlbfN/tfVQ1VnSMM4Xwcw/kIYZPw2ANFU9smSdKRfuUzUvtm32fi/q9n9jW1VEIK4RVCCCUV37Ztu2m1bVsdMtjcOW7d539AOWyOO1prmYUHtgxTYkrq/wQA0ABAg8bCwo0CXSF1aswkQMfnAQDQwIbPC24UCUCXbuQnob95SwOggRl0KOpRGo0iSejU5cq1gUYDAF0AlE9I9VDwnilNikaSpE6dlBoZAYCRtMwWO2Th8S41Em/ZYF8NegJJkRQF3RgZQQFfu12Pr+sxuL1ct+G6PdnZ+weKwltNgcFgTNBJUpQuUgMdzY7vMfedYZ8vbsfrdlx5qn2o/cncmfGpBmiaYWs0mk6SJEFSqtEAYW2eG3bsDNftsO6HdY/zi1g57Hm37QD4IwBoAAwmatKNRqaiGFNSFA342tKy0LGz7jytHK/bYeWw8rRyLEcPAKkTMAANBeymVJNuOrukKEqnngDg6/fxxy5gx06s7OseO4cddRwqPF6+uFNdAoCiNKBBl54ogJGidFFMugGxvZMIti/Q17MvVlRU1EY+0GWXigIo0G5NSUWBYiRB6tTpWky4YdlIvF05rVhROVYOlVXuXUIB6FACBCY0zVSpUqYkU2qpmADLOwmSBgrreFqx56HyUjlcGeSeSnfwABAEAFRR3ZiSpFxHMDEBkC4L/vwmfZMA22KHD+/1bkVlMDfwANg0IMbMAoUOVwDo4M4dgKyWST49G1988Zigua0MlZ+uPK8M9vsJDHSoTqeDBpA0WmqpoXRQw46NHSwlV4ODgy/kF8ppxcrh3H9SOVZOO4//eIla4uB8GMzDcXjd4+59MMQQuUkxRMbgfOhXd/7TmQD7Jmcp2Ha9f/misM9jReWntfy0ltO+PcvWWXOUKFGlKmpXoph7rH+iLlEXdY91jxpRh6SGWtTVhBGAtb5UfenZXClpqKjjp7X+Mt9P5/tQeXbTyThE/Re5xGEfIl/l6rG6i8M+3zz2qD1qj3lGJtZrzDNmzB0AiB+/G324yNeP/cW893XPw56Hmn+eb6dzP9U+1KLLzDCekYkhJoPMkIlBRq4xn3L+ba5xPvbjjEzkEbn95u4PJ7Zum5npfPz603d15my+ep29fljaXlRO53FYOVReVnRZz6hXVdYvUS9RL7H+sETtMqrVHlPUUCNqqH/sT9RLjDd0upqYQd1M3Ll7vTI7P6wP9209nOF2fOZY54pnYorMMMQQ8zzMM+YeecQwZMwzpsjEEFMMcolD3D27bsaoO53OHfhyvX1xCyI362pVq/X6UsfxzFAZdMt1GDwSGfPd8XTnTub3c9+fiTuDO3cx6B25RUbyMjOycAdLWEL3WGSR/kU3N/PyWn5Wy3DuXlGvx9Qy6iclStTFuqlnVMnE+iMqUVdV1nOvi3pTD3WPlAnATAHG/TZ6WMMWxLbFsgkPr03Nh5fh3H46LRkP+10M+3zGPGM+IxOZGCJXU+TuIYaYR2TUx5gkqhCELWBhCz0slhbPLbIBslzW16YOe/5p2fVKg7bBVDSwKrp3pUs3TSe1UCgad4RHgKaHDUHYcCPyiGXZ1vPY1vpiYmg04EWjsQB00w2ULlMz536MAEWDmoNmbdamh401QGwCnvDtW516bUzlBcCjeTRbowGABEX9+VI/Osd5+9bntZbtjc4WNJshhkZgWX185/1Uh/OXD2dQVG3dVAi9WZuuNBqapiEV4PzxPKZ07q7Ptb/m7bzPTFzbEEMMMbSjvhyX11LjWXPUHN+Py7Uub4Hly632rUzQUABFURo6NYDxPF+fztM5VZLq7uuhnX1tyxL22/EZ63dT5ctljpqjugL59G8ucpe50f2xAaUNDTUouKDpBl0w/m+86mt99Xb4liq1ZPD0FstrX66Hz3n5frj8BTodkrp8k7v1AZXNDtWD1PSmBNCpG00nSapX3vTE/7hO53Q5/Y9vczxzc7l0iY8dXJc3l4t1gQawRGnAk12gE0hJpaKrNzUBlHqVn+c3Jzvp4tpe9T//k1122ekyncn9/sPyANCiESVANA26qVFll9ClXa78jw99wvZffHS+OHr3V3TZpeuZ3M68SwM0Q6MBQNEANZoS+qK7Ls5Ro/FtuRYQgPPXznLWzuPh0d26//OD4kO2nQdSWXdAQbM0FC0lU5JS0zQ9UbF9yqcVigQQXxQFrqBo4EO+ePAAu+p0umt3naCakhoTKF0amFK17cfN3QmJE8AJFDNsYpkAXG7eur1TqVQBpgQAGlLmlLpcC2B2Ts47kOAjxYQd9vLodFZuwt5SpTL9ETClKWFKNZdW2lC6dLkCmLnaP22wST+nAHgr5xVYj6NthXOFc5WuKyVJJgB6SlGNBo2iA4DnHQCmAsCdAhxsIKAHhSklSQJddrrSVANIttPp5VQHBwcb/PeNc5KNWgAOFB+ARUMIBjAgBkAbthEgkJL/P7ab7YSImIAqXqVSnd2tKpLdTapFQK3qJsHzV9UvkCIBUNUSiU9VVS1VX0WSYlfxCuB2V1dVxXZItQ4cJOpbVccG4Ihdx138xlRswAAMijeR/AvXNozTuID3b5Jt2LABuPV/jathw05V8SrpW9NZGARsAKoiDvIPpHp3Sfz8wk9Sb/VuL2ybQOkC4INUUjnduwI8xuV66CxJVWobjtO0D11L9VklA4HHu7mw5n8FBKGza8M2bu/MvO87M++87zvqJmzsrvFpZjKftWzYZmz4D+dzewKQsWMHhm1W3veded+pvPPOvPVOpKYSZ3VDze/M70ctkQQkwIDtL1+rROogAF9rJvO+7zvvvOdMHeJx8pb5e1WLIG4RLhSpqqJUd3UzBMiDBGwUrhRUV6XYJH7aoD4YVF1jJzkI2HZmFPswcKgqziZ2AsBOksnkoAmDRFXVM0lvK7adSvI8zxObhSvBoxI46a5MkjxPPc8zSZchFUFdKtqcMzPPzwtO27gpqs0MuLBuz7CLsEGYt1K08u6K9rHKUTAQ8oek8aR3G8AkmQSoigEYP1RS7N1dgcx4UiWrIqlU+iHJNy7J2JLird8/SozTuy00KDuign8o3VZpQBo3+EmHRJKztbtkU1IskPxLyMCuPdIUtQhA8bFt27Vt20oufZ37BFqD9T00FrH5JongEBfCo2ytNbx39urVGGPuI24EfAuSZEmSJFmArHW//HPVD/fjvU3Ic2zbrm1LktT6vO9/xaCmouwoL0oHoEGryiLG+sAaMQG8bG1bJEli9X7wg5l7RCRUt5g1CN3rSodGcqYsxoaEiHA3s///P5iG5wCSHEm2bUtEzSNrHQwoOhcRhgFRkJY7v9O7V2W4qe9ItlXbtm3LI5U+9t6HQYUjCClGeqE+5xvX7DVHeBIASZIkSZIAAJGIRdTcw2v9/+fq1Fsu7qYqzISI0NsjPAmSJEm2LUmArOf82Fa78YhdRbxjQr4lSbIkSbItJLG+zV9N/Vl/2WTMf1UoxwTwsW1btW3bVSmtj7n2JTGTrxgpEAqQAiNfLprMjP9fOHut2Vsx9r0PYuBbkiRLkiTbQhKLud8vPzD//4HdPVWh7FuSJEuSJNtCEq+sS3e/9fde//l+ceWYAN+SJFmSJNkWIat398z/f+0aqDBZt4+gGLaRIMkBay7/gO3fFoK2bePs/Cm/EZoEAFIkyXaMHAISChpm5tFnZiZppaWOoZUuowvoEtprySx9ZhpoKEgKcnczu4YmSbZd27aVaK2PMdfa+9wn0RSG/K8qWmuqQRaSX394995z9lpz9N44ybat2rbtqNbWx1xrn3vuEzOFFJKSwJQtyZkSxOyJYI8xw9O775y915pjtAjN2rYtc6M71/2871dVAkvNi5mZYURhTkY0zDg7kD3IkT1g5mEyW7Mww6Je/ttuu23ZDW5LBkmlqvq+93nuQXATtNm27dpum40x1z73PRAMzvVxnXK2f7p6LkP4PiWClAQC792z9/RcbdszSZIk3ffz/SJmDhJjjBEBucLJQq6SmfQwNUcJd0lBEpCU5C4pCIwj7YSbu6mI/N/7xAT44/9/vZv2/26P5+v1Oi45qSRtknqq0OLFoW+GjKLFYYKU4TaHN27T9wd3n9ApTtlwd6i3SRr3pJLk5OTIS57PP5oUmHz+9mzbtipJsm21PuZcIEtEVA18M//ATlJu70PZ8xGcZv64k8IUMweDm6iq0KI5ugZq2w5bkrT7fr+IzaNUZWVVFsa2bdueadvdM41x28b8tm2MbZtlZGZlHm7FjvjemADfkiRZkiTZFpFYzH1+Yf7/7+63tSpDmX6DYthGgiQHrLl3/gF7WxbDRhIkyQGzV4a/3bqpiJAcSZIjOZ7du3cHDgWgBP9DTEhHn3hyMp2PHkAG35Fsq7Zt25ZHbmOBAPzJS3/BNvMevZckKbZt11bGvPeTe2jBGv13njxsoCGnFRPgcdv/8438/9/Tbb37su21bds2xra19tieqY7t2GaVetTUbtNUSRlN8ERyvUTJjSRJkkSN+v83Z07dPUtVZnqEu6lHbduWJdu2bd52Tq8YkLi70waMG1uR29PAVhSw7oFPOfYt8j//2/9Pa/3d65/t/v7/+6XtD9kMoJod8M0r+X16e/36Y67Vr0OzePOSmKl62nlDrM1Sbs3hJ7M9nCNMj7Pyei4xtCiSs3bLhAvQEAPULFBnIIENANRgoMC3ffOb/PP9/8/n7+zzUtHMwDRO+//y3/iWWU45/Mi/7v71P3XpAgDbuPp1+//sx2lk3IiBzP6Bf9h+/Rx+v9Qy5C152ixOWSJ2XLJytihch1O7ftP+z/w8f2YnKoDF9o/5n7z/5T/euSWMTZoNj/2+931+qL0uE5MlBm8CRUDyK1/KhUtZLA9TAT9kY+KvbhuvLDxs/xR7wrf5MYBXEjifez/DvH9tMdi0ckgwzmOuDYmbQ/BNBEBk6IR548TDGEYM3/nVPo+kz2mCZXTR4Z241z+/73sTGtyFAAi225o4Etoup6/9cXGrZt7837/b//nbPsImJGDVWAAoCC4y9dkb+pxVD0zTYgAhoBkYj8tmc8eK2nonCxdonu3T6okCAgUST+yPSn7gh/4CTEBDzcK2BP6Y0sY2MYmpDBWg2hYKBDTn4J0UAOwAZJbFrICGrioFhWRYCRyHVIiIFFUlgO0CwADLgqdMQGMQGAA6nglKowKmmUJ5OiJOhrEgwaCqIo6PKGb1r/oxgC6oIkRdw1h3s40cf4OYDtHCVFwCmhgUIU0INo8/jn8BRdDEicI3XmAQYXP3zENLK4ixktzQO3PXHuqWeiMYnNsaBESNIGJ0YUPiEIDiJv40bLBF1pgsAkgCDuJtwBP/6LGt4gJBAIbOZDZgqnoxIY8T2RNXEgtpDcMKuqrTjmomnemPspDg/7EtRxhqRjfSGABAcGYsbATophwZjBgABJ1l7aQ6FstSKvXCkNkWNIizocQyxiI2mKg21UgRcdyEsFaUqEUFaNK2biOEjM3ArGwbE0WtujKDuDQxCo/2CGAhgKAcZp+LXMIHIKBsVII5vlNUEtKNYYwRwtseKFUYy5uZ4y0Ag0DNOK537oEJYGzL+NWrZdx8eUMRIpOyFDjFAMKZwIh8CpISJDmt9Hz9z27plrYG5nAwlgBI2Touy6iExDAAY2ceztshzhYhABFFQiYAI/71u/h5r9cWusiCqs06wGrxsEKqwRAWg23UdJGVrVQUgEKkquxJzXyeT5Oz/KG/lh3XxGKWbbM0ADWGxT0Gz+bCVhObVWEMJrNdKGpKgFPIXgjAABaIAIBZLQVqwyJMnCJiWSLukpUrBQKsGZbrjFZEFZRYDQBZlslisJkgsyQwKCmlClBi85XXJFh4w3vGGQqbIcvYsBKXGOi4JqikhkuWRIGZvnWGiSdQIQR6T9vAADV6wDJJdiUoEFCRmYYfQoYBwlnVZHQqiAkiXc7yHfjPf3Vvv70M2UsuyLgMxNrS6gQUzChQgdusU68fTyCr6mzWgo/BH3C91pNcikHlrMJgtdlGJzCKgXFWMcVdP19ufco6RWhz8VY6AWLmyhlM/AJgmLqTJk++TGQHKs05rkU0g+dge7x7/owARoECVjTOj8dBRO2klIgABCvADDMGjIQHniYiSmqZq5YgpFydDuNdaw+qJAIdikW2GBa1GmPtLaMAEgjIQYaZefnFsJhIXCoQ2exRIX3rSLvMFUoZgmH85EzTmGg8Y2OVaeNFBC/N5DnGdFqQGCaoazdAESAmpIppNe4QY3buOTMxDpn0rZA0HLJLV0YiYwKYY7qN+/1W89IoBAhHQVluOoNVVimpIw5bBa7nnBgAJHgnEBht/otSaU1Ypx7WY+YI2IwxBqhYZ/0+/3lvpK/hgHGtrAnk0s+lq/awS1QcwHFsbz7ZmryeU/Bo7Hc91sdz27OkhdnqGJtZ2PaRnztSaQCl1CCLBTAIHUCllACQGQxvxhjAwMBEsUqElSzDSkQwLayIVpJagQA5M2tGogYsuHUNAYTIoGkoUMyem2XD5QAmUCQIdNq60mCguYpLCSmwQOOqerOoTbVtIDy4iMVyKoZzTm/E1AxkAHADALhK6Uv5TflGxGy+TD2EM1fnKIloEatnNs6JtFGPSEQmTU+bRyzUQCYzFFuBrDNVl3I6VZCylYp2Xs8DnI0kGmAJi0ACSKwlBBpumymaWHs9GayBeVK1ENCTHyt6RJQVYIKQAn8QBKys2SwSpOgablpvMsTceubktR6u7fZ0zg1bNVeHbMEbeA6yGQCsSi3bAICAzlnhs0BkbBgA1FAqVZBQjJWqEBE5VcUZEVm0ABhnACQFK2SxuomBZwEQNxKoImEEHQAgkiA/LYgIEmIxaKJCHELhVGqmZFBBRXRFgWJgSc7gdOto+RoclHkkFZOAQYUIQYFFJu9rmdlTxxuUWhULaGb6nJsZoFsyeAJCYi3QRq2SwE3NSGGLvQvEl42kpJZVxubm0izVpGNNw4DwWJaXCAACRuQkVr/RAJPaOpagrNZtZEnQblMUFuEagRRwOsPgkgRhpqjOhGGoEHjnbf93zC/1K5Zlja3KWuqs72CDNaJpBgGgrCMMrKiQlQcmHwYAqymEAqkKkN3FmJVKAYuCqmjSiqi0FAEEWCQAIMeExswA4wUDc2kyS8vFpVrJRBRZ6OQO1nXbs9Cl4iUFCpOpALVtDFzIVMVIxZBR4yJiPt4oxmM4w8CiZs4IsDWbA6tpNY6LvLM5Q1tu3uJe+cyVWMCng/Xp3kexSmkzkQgQagaXGiNKHh01Qc1G/lLrMk7KHIStA7RRnhoFoJEVkZgIOsHWlMT4V4VgNDOBeXICYpu6DYRebA4VZrkxlxBjY3Awh5s0moLSANdYRZu0ltPWhA6/LSpiHT15ts8289uSa7wRY1goXvvrd2dIGDAYTazuiVKriiiFpyCKGrYQmHISZxpWDgyooEzVVCqKGsrSJASlkxQaLHRkBBgGzrivUspjg5gxoIkoCjYXCWIkk/Pr5ZZJVuWo0ZSqAssDipxFQaFLRnVlWRezIBQjmxNxlBmqt4oPohWE/IURlXMmtltmxgFZFoTbfT3miEHkTtzMs76Q+q0KAn6tZ8Ab3iRCo4kw5a5m1LyaVqRJQaTEOXfhJvISm+VCMeYe8Moa9JTK6KQQ2SIEQJLKtji0ZM90nbe2Zpo5SjYsQ3NnsFgbVyl1HFOulNYlbbWau7XmM9IkpAswqDASuQStbepj3xSLBfikKGLb+dLSMHjzluV2Zo8DCQogiE2X44Ax+bIRAOJQkG22SsdtQSBr7tloak6hQlE94RQDAlEppAgSwOqCPiUJIIBipYQAYYwxAzCzfezEEwoIcfZcCdh4peJStFgV2xQqyF1XXQpDEDTEU668jUFi+UTQpsQBc9V2LkLFCNhcU27PNDzBqdYaCkqfqJynDjErQuzXLukgQgrZd/sn7OD+Mp69D+/hd8332fufblm8d+wNoli1cnXaAT2On73j9+Lv4koknACZ7Ld5OkvuYL1aVFJkYRQRuEqpE1euadFO4e1pT5nznpnK7V1LLBPidM1QYtGUZV5u3JOm2hqOgR/q2/k4uVLeHCQmd8wYgHXEi1/zJAw16al54vzrKdU21TYMYGuuZ7YYjQ2eY7ayCCSHCj8rg5FgmJUooTg2ZIkgWwUIUJUAogaLBMpc2FEXgACZ/TYABIAMAIA4nnv9490eur0Cp8IEwPEVsABBKlYt08BVOZqDIgrCKDE3H1MDUxgVMquQEdJLwuk3XrlUBjCWR1dUMDUv8UogxclJFpkKrlgUWQhjgkRQ1ubbUJZOpiGktuuXbjQlPtfHdWBc9ahH3aTEa7NX7d+m5swQAUOWYU2eOkNlqBkYsCiBSOTMPo2hFVaRWLE1qCbQsZLQJmyCOTW8ZcpVZCik416sZNEaik+ehsZ1rTyDE7AIBQPNbYZ5qTOGUfJcVjO5b3rAhAMc3o6d4yZAmQdRT4pSzLlODm8LxiYDpJSQBgAOFRYUUgQRVCoKOmkVQCRgZdkdIBkG2GpiQFGlQBECmsMz9/fqfqlQSmVmGHJurLAthgEwKKoECSW77gCiMKraLmkotw/9hQmaVRSSFMHl1beaXC8tCHBpoxTEWPOQGSKwwdEYJMUCioYwwBCGANlS5Dp661jBt9fZl9HU0k23aUucarKiJtZ7N372XPzCZYYxLH1YTrd5pmYbHRigrAALUaKKhAjZJR/V2giVvdak272Zr2VGGJYkDs8ZcBAKFKVLZEBjVFC1zn1+exXerWeFOBzEYA4GmwsF43TWaCaAg9geSrJAF8BG4A5F6sB5YFHGAM2ZgvcA0YQpg5SIOJuKpiaiVigQQVSIAgAEYABYugGYEEDGtkDIAAIAkK2fp1VFt33rAVwDQaw2aQJokAOucBVjKBANuJCiKupyuaVeMWb87c+Nt21U4yTiFWGahrNrRRdoOVHcJqjZOBvqYyKIjJoLQ3I0PjEAEA5CDCF7GYWY6q29dff53IG60Skwet612FVsN9nAiWlJIRiDuHDi4YkCh6eMDanClThoMKqgVJTuY9r+W1/Gn9Zytjo9Yw9FrqQ0TTJ1yIfZk4V/FQ8WleVAyPk0weuVB69+3VvaBgjBWgNZp3fbKAmDAKdDcoJctqdmFWRtHGIuZz24AQ1+/0X1aqGX3Xml1RsKBHGwaxnj5dkCM2gqU43NRopcKsAgLKogIgUIVA6lCETB5j4FSgHaAoDNspH1vP59a+VBVzaYzTWpJMiO1zDTnCIKqII1vRlU4QJsypXID6qNXv+QU2IxAG2wuFm+dRzcBVN968aiuJTlq2I0I/BUZAIRDtAIhwDi4zjClSFNqxQ3RKO9Pr2ntDyeez/60a0lsbbE0oCUazLh4U2LIAJ29tIdBpcHqH2ZgIBSqiibdEH2Zx+7xhFpBWr1lhuLcj+2jsapzZdBaaTVsjg8uPC2gg4nyScLw6eDLqtVj/6n1cVGMMJzWFsQwwAToDJAhoDAYFhEfsaZ0BwIwNDs0hvANJw5m+0DYVsfGKAxbWgDDNSoaiOVgIRBJaUUqQEJAFYQYDVN07RlNgxZAECYTqVjOPu3vYVQwBuVCXJ29lIxAkCmEEQxgdpAGRJVUWWievwuOlW8oCfqdIhBZmaikVKobg7oBlIx2lASxIG9zBBmEYGpOJJBGDLxBqiEkQLCXiZMsSdW3JnPTGIu94ptLkGklPCanpvbFKCiWYgmABgzGx1EgTqGKFexUdhWUVMpkYjTOBuGmq3FTWB/WaGuAHUGqf+mmgHQ0hVBjvy8FROTsIsXI7MobE+e/91U8Cre5nBztEVCExJCw2iAMUAWxmmAmfrQVEnw4xKrRZergfDVavjIMJkyWCYllkGjHNqAQigABKAAgoAkQMEmTit4moLJgtKyAgUw5nB4RcOJym5NgCuSA1Q57BTC8CKRsRqIOhRSFYOymGtbtRKDjZCEmIJGmdjEFA9QWJtdweA0mCQqCB19zIi63LgIOgYIrLEefZiBmzWtFLWQYqMKzoKBNDmLRhsIoQxUHlFMBQrm3IKMc3FwECwfbYwVW5tnQ2QDZCAwglJRV2VEZjvrm25mQwh7e7etydSEYsXQsDunxu3XLsYrr8kRvp3UAYkVaWIiYrHnDofPk5N5u0MiC+TI2xSkMMCQYcIxT4rWo9eJRcY+hwiwfk9FYwNGFmyV+pQBo5wEAkDgWf1/GQBMeAYEIACQBPYAlrUlI1QVqgoOB8+RZY0mr8+3fMuJAZMgK2Tl1LRGSrEDoLoBpYaqglyIi1pVrl2TfKesHhjjl1Xa/E8uPzeOSkYPcAtpUwpCBLF7Ti0K25QNrIoJ4kTioiJ6Ud064pJ4zrr+lbU70o57aJnDUxibFuFtyqI+/sm3bpWXTSAmQHO0IiVFJGLI5GxbbpCwtcwZ2DKGhjLaTtok8l5Z5zx/jYcFe5qDrZqmAIfInau254rM3OlI+NJnbNKf55unHxA1IchkmE/TEbn85OJMvY+/uYD8IKOwjSGbFFULAPS4Gm2HKKUAOBHEBmVE19imKiVFJZRSoCGVFADGVezax42AwXZGpKqCAg2jkFzbRpvAmPGyGUQGsAyksqJGrj7+yXdtZiyUIauNYN6zGhTxcJE4Z9ZDxWp1unmzy3zzi1F7oximdMZOCZdACAopvpuyDvW5lLdiXBQDplQJcs4MMILmes97fXt9ONZeo2eOZhTtBMKRONpOf7r52t2x1RpAwBykONGCGENG0KVRhNEwNJLLkrzCLJceVzyTq3Kq3RZ3eE06Fx9BZwpuUCjR7elEJin1N31hTp2p2D7Nk6oDEWxdNDOaEeILEFCwqc/XFgEAlQxoSCwC1M4l+MwsAwgAiGIIAQtFlSlICJECVJVgQQqMyyUygcAMsTxeHQqDULja29oGI9ZkK5lCGTCQR4YQSTj+4a99l1JRbQPFHqAi2sQhcmeK6ibikpS302ysLFwd02wVcDrMkWABwiCTwWElLGxgTV4WAB2bFAVVkZEheziQ4jzOhNBJholhGUBcsRbgVyCDIn0TVhOFqFCYpXxEmsZiQCNKymUljhUGUbkplIul8Q8c34bn5FWe1R4SKs0Oj9N44jXs7O18VUQ9ddqGOIdUZCrMAaeAcL0XTwiwEOt8GkEAUBZUMpa+ggirc2o/gREBAEQmozG2ZKqKCaAMIiRA8CpqgJlQjQBqmNnVLsXoqlIbwdbCTPFkm3e2pGwqgqCNZdyaxhEo6sevdK02CVQVuqIizRJkV1eVXKLY4q44WLWtSrUf1W1heTHmKLtndGZOhxXLVEZbq4DWiscVoICxHAlV7THeMRiEpWiicplxAIA2AYrb0AXMePOr3zYhqwIsE0QWBaiqsgG35d2c0WxEkAM3d7s6iXG8Q/iscQFvTbBWDDLLzzrYuokDWVw9yz3HEw/R4rXOT9r6Ftu6+7mJFFiamppxmC5JY3tp24MXwJx5zlwgYADAYWNTBIY4swKIAVjKCoEIqFpNAJROYKWkVKMgoQikmOlRgKAkDciSZpktM61SYBUgsDIDlDQYS8pmUwDTsqxmmCKC1OrplzciUZmqAnTorhR1JTG6KC4VdW6i643apsplWhVrnj1tNWpiDcYDwJymnzzXasXbWnFNEIkYDqXRtebJaTm6IxopC2oYIQpAgHJyDio2gjV7C9yjSYWZXNUr1iFKAQBhWMvFbbpkQwDktqU6xgBYLUbh0pgHkeG1pjOjxMZnxCcpueVNDtFpfEVOfMqz22vd7UqoGaS/4PV3vMUCQI8UcE11QlzO93ANDkABwDauLZBaI7UDAEYAgrVpO84ijiZLKSi+ikBgg6BgDGNZjZeqpZIwoGDVzksRJAS6X58f5YVcqSt1XQMKABtzdNrEjyk3axtEAgyAyKBMRilFVVRiqlBAc2mKBFxULqVTyleBaZOw5w69Z92lzLn5wrzW0BEq5DkzXHlTFw9/hpQ2i9HDsHARsvSXe7lvKEFUITkMIgOAFIKCvvN/tuf5848YSg0YFVUoVTq9KA9GCiKiizcHY7T2jg4AgL1rYXMzWk5TiXXhdcLNQe3hCaEpmEgSSVHZTj8nOobyQZt1evz80b151yxcK0fn9vlMeIcVs4CC7WZVbnuLdKN5c0WAMogxVoQgy5EuAwCqKJhl5bY4TkcW0QYCtU4JKxUIVBF1ABpAkAAEQIcWELAIFttFCFvZANjE3CyuuU5NHizWJgqsBNjbFRiAQdU2FW1VXLUlXAGIUqKlVaLK10qJKrs0VwhcVduezN+niNcA1AC+CDOpWnUVn2Y+DqpDJTwIcBhtWlEENwsQIsMAMYkKMiTCObf/4z/9X/y3P72OXhhCbYclUZgRAKUTiIDAWMXDdllaAFjWLFnVD3sE1sMrFExMw2JEbuoyiRJkxgUuzwJvzOrLTdU1TF3Xr7OJg3JTKX0+f/ZNPsGlL0Vi0YpnuxmR0VTyAhAWAFVKBkBpwzEAkFgBUxaEDAbIJmCc1iUQJGSJSqeUUggBCwuggKV0JDODxMIyJYGqIGkgxzJbXGNj5shvZdVg0DaurQYbI4AKVaAqBRFXVcG2qjCr+riCS+6UlkHzFUHF5dKp3bXPpRE521ywKIAECCYYqfOkzeArKt9UEIIxxhen68e2EyNAIIMIgizAiBcs7/Kv+6fyWrwWrMzFQACCYMJni1fQr7GpaWuHhQAAtKiZ8znlw4RiiARYKCGwnXL27AIe17OqPd8rxW3tVuWy/dwy9ybE2eylmAonGjU935O4dwqmsqClq6Y3FBwAME+IoSiiHZTqmhWsmmOhVIRSGACxXQhMkBJTlIGSEVUUQrABBYjABEEBopjZsKCKkgiYGVBKEYtBmbNOTgbv1OUqAlVF00IIguDZNg0gABRWQpUIVStwK40osJaiCAAOnjogoAehSQsY2powFQ2CDR4YCFyqNEqSpw4BaIisY8loP+2J513/emVRY6Y/MJQmeNrPuedkNEwQUADKCTJIOc/5en2e17f1AgXWVZQumFKEwcC8GDRerDMoD5YLi+FYiBan+dx+zphKk0phqwOTXFEYGIe6bAtQT56/q1dZav28Lz/duKJrEstl2QkBiYlieUxMHdW4CE5jHZwJSwpIjvM6AgZ+L32jULBCHKNhwRJAyNjwKgADQGcrgGBICSDwuQCQZRwaTxwSdmGytAAATWGkxoaTJweDkJLGIGDBYPgoAawAgACUMjGYGqFKFA0FAPWBYDWeukeQuiDNNqHUpCQxYtIkUASwlDqopJJAAlCIDQxzOw5TOs92blSABhDME2iB/P6cHjkjM9YMVUy5KLmUAi5y5tG8nrwwF7JFIxYQtaA2C1l5eM1NQ1iG2Q3WNy7ismlR3+0ntx2jpAVjnPoTtz6cGJWGSW2RYT739zuTr+t17a6XUks/a4EKvCbBwxihK3NpxWRji4SiQksiRAEp2KIdxjEAYAI2xpaOI0w11WDMAIAJa2sAiACmCQaBDFLiJEp1SPQoJRWgqMA3KG1na3qiRMKGxKCEFUCRyDI4wKySZlqirGkC5icAMAAmAmUDkWEArCGKhtotIeQApTpmETx410q3Ji0FTEnuoHHic1xBUHRKACCRSAQGwxJ94MYJBTLiZQi2goScOlXMJoJhzEznkgyNYggkbJhmHcCqniikgQwAYRA8GQAANmIDZb0Im2VESKupV8FKEjERtXE8k9UlqpSxqGGM76j9+nIZ24Y15x2uMDfxkF2xPBV5XGgh0FWIQlvbvUbDc8HAOQdAAACqFUbcCAkA+lqM8KoAZHgawECqUiUSQIrChI9js8GTOgWrFZ5jGgCwAEi12BAxqlBJQkSQEkW9GKwAEAEQZBgYQLGBAu2U4tMcfR11e7VX+6LzcuW8uj3COS0JJwDX6mruJ8esh9ccIscIB3KEgK3V9+1TaYgWJSNAEeAIDXAB4FABZcRbnKdGjlBgJsAAYYMK2EAm5qxIx6UkhBKnEjEE82LmQhkvbzWusZZIOAKMRXl/MpAmE8TS5FgWZkBiiCHsuB+k0fpaSysLle+WbQAJbYptnRu90AihbeMtdGjlFL0J9u7J76EzuKhQphkoDYy2slWrUTqtQMMCzwAsWdUoShEpJUMWkBpOK5BMKAowUVITUgAAATYpNts6QC1rs9qjCC5wRQ0yM9OVqpJoIDVNRBMAJEJgFtsAEAsmMTChAAgoVq0Qb688eZ8/ffavH1y30+cZVCySkfF1/Hr/hO7bfNszb8aL+MD55vxsJwc/v/r1+6+L3356Z1JsC4ZKUIcUSw51/IZyDLDZVAYlQPwsIpacEUMIULnEpnQKA9BVIqgREemxulAWeDK8CoXVTE6NnTkFll0K5bCGGIbkxisIBaiuV4Uc0+UgyAB/1IQUvHlLwbBg8iVSEhC5oWEBz2d8VLLqdksuT+5VRhyHUsIqe4DrUggGwFYFhBYYAaYqVg80YACJKlFKpxTZEhgIABBBWQALSCCtBAADCKuQGlaIratSRQCAJTcbEU5AVMTUoMkVZ4sqjgUAZtpsmzG7swq0MbPZbGDX5gh0Kq3X9db5tP4m/c328iD0OtijWyPZtX29J5YEo/FIcp1+PMtjC3f78FLDaf0LiT98ff/JzL701VPhWME2oSzNxW2W8Zuj8tgMJSlg69t6MSFbzbKEQSnqHhgoGlZCDZRAkizrFERUx5vkTQ8eL9O5335Ov9MkX7VoZkVMbIAuBiUcwC0Uiv1xVUDjYRxDdl6LtaFOtQETEwcKL8Z5bvbIQ+m+LH4U6y/totZh/U5c/YYGHZwbDL3XPCulis1oAGRjgB3HtEqDiABF2kAigwBUCrBVixQRAJAHWEgASpFIKEVG21cS5FAIQXJvVc1ZUIBaebebPaUUAJI1IyVNEGywBjOrlawKvjWMjTpqdYGsljHuhDSdMw/Dv7r77zi/+eNx+HrdJt9/vhRPJA1XWU5iEVbHw7nz2kGo0eKxYCOCRWlagvIGt/rtv7y++e3MSde3szIdx4YOqnnm8hsGFy+/GZdLliCTmG9LLgHVZrk4KAUdSEFCoIysyZTEUE0QAAyBpxiA2LBsdz1rJrTUD658sluEwo8AICIZb6aRP2MqnolQOBMHEpE1UzTkpM2oCBQUWkCwtW67OXjXOIWQ13WM3M+f276ynfk+/Ezoob0yhw1+f7JtrwKBTT0EAAyCRTWYBAQwAsDAsmBGALbaAh4ETAMMAKjUULBouDKLIAwCEIJNhIAx5RJBBFRtwMosWAFtALCZmMkA4HKZyfcfv+78rebls0d+S/7z7v0Xvuscxhv80jv6PJ8LYHVK7EoPuT0fng+n5I04LkgSGgDUpiYAAABJvpeXxH/5/Y/ufXn/ex40EzW3GB9PnwkAw2lSjkUQhMRvz28PAHzx5Z0CpZQCoAwlheV0SXwBVamPACqAScoDnF0CNRR99KgRLVvIhB4l5n9gm3QmTkxUc+KrQAATJGDo7ZEaJUI0RIuoMBTo4wDuAtWXi9Sbk+tSwXPbp/eS7aRlM3HCJRdcZUkMDIOCaVUDA9dWAgEQgDCXkREAEJMCECYQpg0oahIFUBmAxtAK0+aalMO0IsK4bK4KEAtKdicrICBnXIhTAFDaFNAmACuVA5IKkQBOBBIUgODBwQRGckrlm+Nf/rF/9U++Xn/X9+dRHvJqHLAcn/fj+Tmp3duw9ZTjcq7Yn/haJjYpJ4b1JlJkYoR1CnXUi6g0fnv/yzfGA0J3GTVNHVHX6gqM5B1fx5ABEFI5QAzTqfmyKhFjBA4BWSEWdbXpo5yIlDsFAEUVQGBw1qKEmThZpTIZ0rM0U4orRCqwLk6CIsOBIYFpCwnSDLLQhMOO9n4ZJOY5A7LmHd1pLXgJbHUBIIJuT34bPx1Cb6la0n/lkwYwUFQADBICTHMM0zSJMWAwbcLACIwQAAMgnWMdMASeNQLaQiYGrJbjCjRmgBIXW0AEALEIEDnNQBRURQOAFECDhKQiYROqiAokEhTAFFJHwOZ8Z/9f+f/9YpRe8Da0RtKlbXNYOBsmSbGXFXuHJbb0cvAsPVppo7d8u7XEmWfeO71z4jDbqZ3OOtv/9ffsf7l+fFxPHC0lTZpigFPWXhEgI6w2RwggopBgpCgjsRKSpVGuFMUluNAplBVoCqxKKUQoPhThRkEgLuaIZu94zrysiMD00tYXiiEEwQDjeAQTazO92Tcg0TGLd82GgsUoQdauV5flJA6ZkM6cZK917pnf3fW+l61awtCv+weLQUAGUJsAQJxkTYzZDAAwqEQggDIgK1QCERKlAEVUBjkIAGSBCFMCKdWQhQyzLDAIDKTYbJx5BFtMqQnFZQRbwSy4lFCmKiNACNp44llILXUNzPFzrpx/rv6/3J955TW7ULA2z3jXDbQ8Qkncw71IfpL63DtsZcWafToktuzHbguyeL0XrWKhd/qf2Q0VDVQR+dCX5fPLc52urtRNaZNeo4QMS4aGhpzM9VyOg870ZPdbAFIVjlK2kMSkLL06odSHBYiCQoE4qqIaV0JNnJIGJMRjmE19zvfIqb25FNuUC1YhiIpTkDGS2PaCYNqBYhSNokhcGBAbKhVh5UnjlYU0nokp07yrbiuCUOoJV7KY9/UcdUGtgNUKw8ACoFptC+FpCMapMTCgVghERQKvUQqiJsBiAAwQRFan6bACMAFmCDLBAiC7vBVA2MCsQkyIGYi2lWYiYIyCUggIBWShKtqCBx4547fZz33Wr+/lzfGjd6uFTMmLVt8UgLI+rTPPootMuCsTq1yo1dYzhPbE9IP9HOzuqbPR3rPL7Xu9HXQcNTKgSGNw/kX4Cu6tYkKa2ljveQNHk+KcDTmt7PEGVy9Kji8RUSiD4BC4p1qhpOL62xgrxGAgEFemECSW62nPIL5RKWoCt+G9n+/09uu925UaHio50KCNHSGEtUQxBHLNNtabB5ImY9ygtqYMQaZ4RCRqGLXl7J30+pelC6K6bRcjjeK7mobOwCACYxSFdDapJXwc0/A2KAVgTQwTGJZ4WWEUMQIUBSCAwJbVYSusVllNaJHACghg2txkQdqVWBjDwlACQEBsKkpJxigikYA41gi0YTvnVdwe+k/M70sz909bMW4sluOm5NawfrENxWy6zOvK2/gqzMg2c4A1CfdUn/2hnF253xn2vrcvpy3XkpuyJUCJgpJVrDy9+Ot//u5N0y7atXQd5B8KRo/UBMKyeA1PO1O0Bl74OL5cLiYJ2CRxa01WqErCNQBsAoSKqyiggcP2bL1Q4jEbWS1o1mc7VQYnvYsrxttJxSjCg/9RJNhrSaJOsMKGsoKjLa9w3MwRbDZeJ3P6qq2b71I9iCz0bW/+tfCviIltT/M6SV6mGaiGACsUgIZTok2yQ7SxF2az2caSicrAEGCYAAYYAAEpSwFUFrECQDSt8E7ZMgwIBgAGdrYBGHqtDWgXMMYLCCspN5dSDCFOrI6VMF0efvniN3UWvdPX84XZwnH7Y59qeRRCcTQ1QAcvLR0CDu9lvzDV6v2mPH05fUH97ZfbcBfr2ftV1tvSnsO9B31kL7NaJIhSKMsomnJUJ45/+/39v3oe+NsjX9esQZ1HAlIejqaaKkmKhoHKYSKFFGBrI7EwVaHIkX0lhBQlDIiBBIX43QOiylllLk4VtJRcGG8k3vbLTNC8HCxL/0NkS0JplGnewRvr6TZhfr42NtqjoTk4ESDq9Nh8vd5YYtkXf/3U5bckV0M1FXmBAGMERAArZUZjgcgcYQICACnBeyYASgSFgoisMIoZQajZMBYGEQZ2JlcexCbbBYVBsGBkanSQAjQnsijHFEAxhi0LhMRV0yQjsdZg0nA7fdDLfyK8V9wjvS8/9JX9Exa7T4YihIRNPnqx5hkhZFJuy4wUnFX03lfV594fJ15P2zRYvgtW7KtRWnHhJLdIB04swtXsDqqUsNVYcW/+8yt/x3ur75ax249qDylykDNP84YEeafFCTm7EwUJjciZSaBEqy7lOKgSUUkAyFKJCJfoCi0y3KrSwAzJzay+90qysSxZ0HdkLTCDemkDwRCI42Y6fTR++5w91yqmsFUOJ+bKS6x6e1QantojUJy2HoSUYCtJKIAl1687K4OcOVOAWIQWJZnJAoQKjCEIKikAHAEbJbUsAERgWUoYnG2hYwZsQQKZsZQVFMBIYJYBFAC4LIUpS2FUAJUuAtnAZkxNc1dSWhMsUKBUj/0S//vyG49z/ZhRe8BXre0NJmm1q86savMA9Lm4dxsq+tB6tyzscJzteEualnvOz93eQunC73OrVZLEmG6zhp27aeBEtXsyVDuDZq5xYzngoVk1D76//7dwbqZZnz9G0CGiuMqqWSWhYkCoL1/LSosioohgCilfNLn8DzaDzwSAmD1pAUqBans9sf20GszX9V/qda1nwlLtWXVEVralKGNGQGB7qq3bWtfi9Dr22AVOzwwHBcRMVWOcgCmnqJND5tKl3GmA184vVIC1Wk1AGVuIktEqIWN4ZaBSA7BiwArbBpQwmAVZAAKMyCBuyMQAuLVEwAAEbK6NAEYYyOzcPpzbCBIKlmM7AAAAIMC4yLKUEFBUIECIigpQQWHDdw//7Dd8dyleWrkVE7Mf2L6E27n2MhntcN/Bc2O3sWKWtULP9M0PPSDKJFcer+lEE3O81BU2Rxc1axVVMSZOMtFsozid3nVj2oizuIdbZM71/vlf//y//r//+2/+/f/71/l9OqkOAFawos4M08MOII+CRAbZYI4FIYRDoAKHLGyGd9jGUCwwjdUOhb0xARBv+5Xqa2asJSmEQvLvXs/qduWyEoTIQJJsl2VGsx8bcaH83rSomU3iGT32AJKralwxpmgDTK5nO/U80ra2hBeROV2c4fXuL1cACjAAzEyqAFgA9EYFZgIQCsOGEQQQBFJKSUnBrKhEAKgFU+a8igUATM6mRgzArGQYcZrzjEZYcD4BSGkBLWAsHIhIlWoQFVFUNAQVIMKVy8U/PVoqMYGcshLjXB0s24+kDEM1qJDb6BMU23jnk/hm/XIlaepZztKdvv5dGm7TFw/0fdftKuB4HS6sRY2Odtac1zFGqm9lfxTmmXwTLTLt9sKf8lz8/vWLmb0y4+qZoTq15pqaxANElIGS85gL4aBoKDSUbJog0LYRBIWCEYdFqCKWF8ITRcEww32tiQ2iWXjlLm3whuhBBR5laWsBjZ/2M80VGgLWbHyYiObEc/K0mcWras0GHBB6J3mtb/VNE8h2LmEMAI7j3NbAwvvq1iphJaz52rDgo4XPmQhDhuehOtdJlCJ4TnhnwFnZg9rG7GYEIAxglsHlWJM5PmbRAy7lJDk/NRiBQ8SxppIIABEVJiEASg3El6eLYGVvd3NnwbILd5mYPmelJGOQwR59H77dlIttuxE983o/SUyHPZGl0pkLNrOTQ0WGy/TiJDKVva/Ty6wUrmBDvGlbgLklLlEVV11LdLfA3fW3/29o71QoN7imW2qyAhMZm2TMZbhndTJnMiCQOwJx7doeuKemQTk2A8hEUq2I8xIPJhajrtU1nqIFfd/EH/9cxanf+ovkoEjDyusaMn4a4Ex4xRPPKr7XsveQilUMg2cAkayhJ/JVuRaLbzoGiI5CAczIiw/k1J99VSjTGKNWzNmnb7IAjbHQZGkABEwADIAoymAFKQtgwzGYgloALSCjVqomkLUFGk3TtGXWNCaD5wbjRyv6qPGwANpdb8vl9la+PX6nnDaAJCIpFQ7as4oEgloZMqWyDEl1VCYaROcWpW2JifJpB7F3QIJl/PgZU2HnvNZX3dUqt6GJCPSg2t9nv6Xc997N7kSDSRalA6JM2cJmej4SZQVd0EHOlhWg1qw6sQcFyFU0+ouLDY8PUXQrWIMOQ5hLjRUimTe8z6n5fD0HQQBStt3e1qWs2njROl0T1LQJBCtRL68azozKmBzBiyPbiLiIMZyAdKY0mZSnM5uDEDFlU+2l6dxAyRYsF8r0jGqGLrHXIsIdApDDsUEAYgOA48h9zwqACLOwAwAMwCEDAAYGBAAxDAyAAQgACMACrABoAEIAgK0YfnLM4kWY+WH36UYk0vXN33br3DzqOCBRFAAIgEkQRCKRFaoQHPSp7VZPdjYlO5unU9cAJXG+q+ltHsx09r71hYL1/N5kGWeciZFnWe7n9JOMRjpYgDNuTpadSNBSmY3eU7yUUMPLjtLdPsSOVjAx7V1TrC2TmgjXI2c+aE7V7ROwwYbT3NDPr53DDUiYlq76bfd1bydhFBYD19K1T32xISym85zWnKHOGCsgKwDoJX9GI2xCFYRC4GORz0QSI7Kmqg4zSShkgItUAqSnMm/R1qjbMwhAYhIw8rR1Gc8qlRbEJBhc0x1bip4pgCJ+k43zNAQAzErLqtZRSM2ZCSR4HRBgbEA2YEFW0CglWJlAKQCmogoAFMCMdCxeJMAYCAaGFmNQIYmgedfpw7fVU7KRlQLGQowhUHCkSJQIgVZd++b7+3I5+3SU1ai+KwTUFTSxaWgcneo0wqGRdG583LwaW/iYEG7rZT+jd1/RJoMNGg2wSzsIziArotpWblahcGLFAhcB5IAlkKhWobCJZWqvmcV1Zn4EPt5Pj1Qxkj1JTc7n1jXwtNmo15Td6wkKHgpEtqm+2qeAC80Mk3MdpsBJMQyAEN6peetCudJUCixmwTlvT5tzrUuvkrWGp8S+LG1Og/IwYlozmNDaosMWRWEgE8gc1MRjAACwDYA2nI26PDy0GQBatZayKyMACl7bzSQASIXPwww8bZjwrIlkGQTLgo+BZxYEZHidALMiMEgIuyqqdLF8QyWv/PIZj+S4dF1RAAAwrjCgRCBhEBBaePvKsz9lvVZLBjNHtg/rDILjF7NucoqD3SOoq1kUzBGi66jBo6ZWQhcN/HbP+Ie518myKyA+wmDZE6xVbp4Lds0yS6BSoIEFweEUBFTNFKGlIDEi1xeaJ3kVW03KT/7jZ6aliX533LPccIMz8r+oP9YFzjNMAQBhhRk6l0R76ic9DgbN1msUUGBfLnzEPPhokawIHDdupxLU89T5Y13/s0spgYlBEQiyTmoGWBart6JOPqtIB/q0fMnGLLWgwGp8uDAoLk2DLWxhi0mPB4blmnxef/vrvHoGI8CIw2hrisYgA8GAAIRgE7ZtpAaeBBOCAibyVsNTQKrECurFeLAaaAAgiN06Z27OjKV6r3eABlNpIUBRAkQsElUI4Kuaojruvrs9+e7Y8XIoqzI4Lek0j5iwr76Jl91Rp5PdzEiksitptp0n0KbYaidk00565u3ZP9+TLftV9fYosmRwmKbTHAVPE0ScMS06KCRkeJqiSUl6wx1GxU5NezVvSwmSJZ4TFJnMa16ffd19sps/ifid2hb8gWtzyUKEGkVX27FeMr7M1/m079cMipvCQdkQIYLP4RRGZLQB7dmmW7MLDYU5bXU5QRRbErEYZKz7fjJNRL3Y7HzBeZZ5U1tvlSwK/oAAMyEGuOAn/JUCYNYYzAwzA3G5wWxqf1EyUMwQjLmMFROYOFfgI1EUKScZXg0mAwCBDNPL9BCqIYDRwWsgzb4ZC2AWifLdbo4npCg9ME0OLwZwsbSIdUACZQlKGIyqrfus+zaXUTp3gFLcIag5uAEn4X39FCdWC3XT1WZKlrqnJk09waKKjXAEJC0AoZpBlkwsNGigoVlgt7tP+0Tq0pjURs9d4Xqesk++39s1Pxs2EsBurATRsgceeUxH4/fp737mz1+fmvQHQ01S8rTP2jFJ0YwymjQ1KCtGlgWo2U2rvc/RMw+exi26bCmOMZifWCCiQcwUhsEGseX1x2ulT0W4TJSUUJ0Jd2Xk2BlfgQM0sxXN5ZwlmTBWIySATAbjhQwAwDo1Vc3gGjAuyLqWkKpsRlAKLrYgwFYy1NjbMFOEqlQEgA2QFUAwMKEmgKgACgAIaJqpY1AABgBTGwAwFlwePlpzmZZvnwZBghMIYHOjg9lsfSs5ebBmk4u71Ke5Y+l0oqOAnBI/Kis1dOWVdPEdkDQdqgOZZ63qbkbOtgraVvuYl4pcbOpaxCVJW0F5VZqpZZtNOizyFn57Qs2qFe4q8hE1ER3rnT/neC3lxKprJrY09kUihDWITTpLvxvtOI7GXF2OayXCTEyymwkAIYmK1EgI26bGSSkOroDwK0ilVGZMG37SyBRUjkMzg330uMXZlk6M+QL3mW3Rh0xmJtEFU8WAkravs2rjBJVStqCBNJwAYlmuY3NEM2LArFOPfeyx02YMF8zDmgoUABsyQJVuGUDVCvQiEAxASk0AaYMQJAKYAARgBO8UJWOTNwAiKDDf2akKATDLQGyxZVTwas60Ot3muKJohnWDVIxXSLMFhLasn1Y3h6PORkBCdEHkNDuJUZTJTe6HQRBBuE+vSsf+7jHE7aegbOtOnGApyPR0VHciRLUD1apNQr+Chcs13J0Yk7lMQMP0sD8fithUOHEVZNGFRZxkRCSoxg4UNnrvq+4qL5ir5/lCryZPJHWqNZQQ6YhaqdiRADajAdFcSiQrK990pamaOSUrMQaAAABzaUYpjmLLoMF8G0ZI9nIHQPApnHl644JIJMMXU1TM5s7OslzMH9qEhsEgDIpx3HqeMqqn7V1UBzOr5pPvq/AFA6DPOTuCAEhBMGpOcCFap6zwaoU1RABMkAwTslEwBqIIMABpsgyAAbCZxmwBGIAllLmMYYNAgr5q1U700GFsOopbrzOdyJpU6tNxOn50ihN4eEPrlMfDayPn0aDYk0GJSk0LosxiU1/MId3TYoYQzVLnS3rvMN2QEe44q9jK0EXdkTImGutQhgnhUuZSs6e9LWTxQm8YqllkzpaENSsSC3Jze+8S1U6vsyCoEUwpsGdhn+TaAp2P4zdas/VH03Mlogd0OcKVrUKcGAk2bKKEhhk+hKALkzhRIIZ6swEEAKFZzMQ69tR3QttILaesLd71uUDWLdYZWtUElWMkGXSCSNbzzpJNzbD2iQXAYVpXB9ZhgHHmnBwjPS40AMpqDeiwWDYsbQWsEBWtkwW2pQYTGNkbCAACAEKswYSJYEAQAAFQtAIgDIANi4sAY2CtFgBjMSZKhrPJ4gAYeljXCkmsqkHX17O7WMdx3cfH8fPV3/mMFZIX1+z3berjoitIRNpPlbxmNM0wVaa1WbNTVD3YqnPI6aDQ7pOIeBxNNFtZknho4yn7I24MeUJAIzvi4Vv2go3ZeTZTe7WNEg7Yxloec9TYTvZon4zq1SwNKkZYtFt1KXLNGTvdwajbZufxQ9LalVkv8Vky/Tv8shytvhUnYANi2xYhsNnqGnnhUpM6lWiEwFYAtMdGRDzQ45X3QILlYLdNasMfnDVBz4YoMSwyDuAEJCCJa9nt1luVkbZFZ38MrPNQcfVAsRZgzsODBjVAxKJgbdgc0xRbJ6EKYGO2ZiCCMHBYw+ctFMGrpQGgLSCEAkAGwCACAAEQBgCWCCSWq6UUElnGCgsXgPSigmuLlZMniMqRuI+hOywB/+LzvuHenHt4/9idF7MmrYM5Go+xCzHXvq/6RIZZdRqHTklDjhEPiNhui1hhN1aa+TYKyqy8JicZzc50FRiv94Luvd1oRnruFxxso81CocJ1Klxg0OWeMNtRuCLgJKO00G5EGWnNDft0YVNfOuDvlW2WTN1MZ5pTr4q9+eQbObFSiQA4LG5gFnbz1Ur91l98Y+bMlIGFTQgAzIMBb8YpKs2Cwlbtt+p78y/V1eOvq2NxUuqjn5DKNy+TCiQWHM5ZNZsF4lLl/hAA3VWpHW2KxlugwjzTjbvAeCYcmTAVG6bF1WVVkSqsVhiXAEGBSqIPzCBKeWEGQKkBKDUxeBcAQgUoMZABGqASmmtboFpmALDZxDAitiWRBGJNKl6QDBwgTl+/n5/Lf2NvdshXn0h6yshab9Z5nJEY1FRmnYQFqqu9hp5AoyDZCRJDUbaA+NNdFbm3SExi+qSXOSBs44lePBv2dFtpJ00XTjI2Y+bSOhNb9LBJT6u1ZQlyXcV9tCeYE1YoAZRITU1jl/v3Ne02WkngPq2FVqY3Ilfqt3PPvrxPdpQg7y4DpgjIADeLhcTipaEQXIhGGdtDATDVcEsz3oRz8ZbtJ8/D3ucD/KNdvPJ/miCRy88OwmHWck1waFPE7SmyA8JRAc3CkbkCYonRWgyZY7MWpDmn0UkF1qwJZdvtCFitVisAcpEVAHVugncCRLAZL0KAlABgJsgHAxCYAaaxGsEAGAaxFiDDSgBmvqvH44UVyk1gGI0IqSRCQAkX5+76x//441vzhOv76Mf7xTMH5aj2Tt1pThK5DLsk88TEAXoBISkoEhC0rmG3G3wKPHFodzyqVmzxKXnWcJplTRjGTUw4x3vJqSoIE5MmGV1Z0J275QUuvPga/fTOrhsrbZFJiWjZ3J9AjhE9ew/d+qRNtnEhhu3QMuFz3N9ue5++x4DCob00a2ZQSiZSKCdMFRtnUUvoARjeZXjmh9i2NlkZx8Wd3hhnojlg+3b9z+b/dLfzd0PUpTWShqUZnJn5MtB+pAlKci3D5eZTQtFiXcpNoIK8pubNaVvXNUNbr+DrZzutYtZkCjovaxgD42VWwoKxWmLV2wzAWGUAIgKgAqTNOJQMAIoLaJ0RAAwkFRWYgacAEEwgkAGmxXRb6zcZCNrDlMIAs4QjqG7dEoZJmXpe7rImJKG3yNvltTM4aoYkOo6FhoIKEiVHoobqS13tlhskqW4rseXmKSMqNkzDKcy4S0chZrAlPesv3cOxE5tuseg0MFFThYun4T3tkOUKSu4UwPNpXUrLyWqSJ1MyIU/o23isrdl23mgb+wa0PfPciT3vzt8/JXP9YNtiGRqpiSGP/+K9W62Itp47PDM1CEu9FsAYCB9ZnEJ7KdAVUA8PbnA2Fxt75PTtvlOnU/lJrhd6Q0IhF+JW08mR4tHhUinBLJ+6PWrOZ86UjxId35IRB3YHxACUAL5Sq2JELw7sebyO8BQNGJt1IIh1KOwBEGDwGwMr7BIAhgGAASBgMADZTHo8zZhhMQyAjMVxze1wBmoz0TgSmwQQIUKA0ZPsI1VbYU3wk1ASmQNfeeEK05V78OxTB3GEruHd8iKkfQ9S1ILYY2UrayXG3JbEIsdr8koEBpEXXEiB9J1m3BrjxOcYsShIgA23tKSD3Fm1DRWHJDu1Pfl2Dw2Rrvpwizir78v5ix257ldTMw5qnCFlaIT7a/9kllR34/Nta2YyQV2hMqCMIaFFicECHQUFMBYBA2HNGMiDOnxpVm2BUW3/1KPfJfpUxd/42Gn7l61yXGhYcCow8RkAgWJElISEXbJcZ77/gJ1vz/EpBuIghhUx5kmBCgRATBAEGjbcTTWxDNMAYwCkVVRlZYYr4VlSDbAHeSnZi6qAiFIymRaA2IJiQBBs2K0LAANjxnR1JYCQAAYzOO1oMIgpCxOOgAgIAAhoaomPpFJi1CO1PopWZj32u89p69F0+3RUq3SRBcvORK9wIkF1ANNbuzome6PyPFPb2rllenMUBEQ6DbdT5qWu1/YmxOFmT1xB2W3umQDdySQ6eZOoSEQQ0swGJa0lku16ahkatcWDqhpF5pYzz5jQLdNjS3+bPnxlCaeoxrF4XR+uRatADUuqxKFMQQkFThWRCAggwudpcy1EErZTv9u5jn+jcC0xuApKd3V5IQrVi29mGKwCo9IVFSiAlSSeqcMcHmYKhkyZKSpHASwxhRjB8CGTwSU2Gj7r8FotdvhZY6nOIVkAGJ4EMAMA9PKzGcAYPgeZ7Ejwni3esyHAANv4th9sU2eEjZRVAOwJwADQFU88bhzwkQqfQmMeklQTxl3ZFysNTtXs02xXK7IHl5zTcqpMYOh0leZ0ymY/KytouyW5iJf9R1gQrngNmT2qkg4i+0ZdGst737ViFDvJteacLYwiSrMOIBWvV0MnR7R2b5yIzESpYH5RIiLyNnmehcBucvqg05eN0zQJ3KKtK00CaSUGiFfJlqIgYdDVtkkbAZRo8jAeAG1ba8wIWJg5+e8uj0CWwslSfe76XU4MdhrmySfKMKBcGFhoLWeWI1ZQI8EfwCi64tEvLk5sqYgjrtcixu2588ZDVAhb1OpCk+t3+5deky0QWVZYvqF+LI9FlZAIMO4JMMDQQBkbYAxMiAlQBSs0563foqiTw9uqsNluXZVSJFJWsy07CGDGClcXXk+MJAzNKONkWTDdgCJobFo+E3t1dXU1CROJDEXAR5aYxhlm0jyy3SGVJjolimtiYgBu0hXlXCaz5qLR2O3ZXY6fHi7kFIuCr7is3EMSxTa7udau9Xf6kfL4lhklhXGhRu5UlTNsJWw7e+x2l1tnuW32sIg29BTbukbz38DcTd+ZEfaMWLHXYH0mP/HLrbacCy4MnrFtvUAESbj/r+ambm5IJGAtqyRDG4DeHgyEbOu1pFPYnNlFP/n+ECFm8zkbMOIA6Qouhqs5GKdpCMMVIHHE4LC4IsZXFJYTYtO7Nax8QsZD43qzM2qap6ZabAMhXMT2M40XYABmAUAIYOGEVgAMgBjXVsIggVcBVgIEVgAMAAZ5A2SFmmSGAcB0jQHAAiD74tQsgHjXUAGDGAYqFiCWuKn7+H5Hk2IXg5JIYEiD+Ka8U9F1KYk7vAgB3T3k4AIKmi8lPQeNa+XrMsoj7pWIhxI125kXMhW7ECQruDOYWu/pzAZHeG01K1ZRQCTKkDwtGvTKndgXwZTy8uJDaVbs7ah9/O6jN9dsWIlhwMG43ahlGpqRLX3mtiphRMkKpSgFMS06prhAu/dMFQmtAk5ZC2QmVCKwEryPc9acmUan8v1Z+98IFdXElJ1zuZe5OMvloGCmR6mJY24zccXEpUUIoweFRDgmpbcRKmdfSb7lFXnguLK2xip+8ylVQ30YhmmG6rn4ioAAygIXU4BcigSGAgEAQhZViSXi8ToAZBE1pTDFGBAwhoAZVLDSADOARYDsZgww9ZUH48yAsAHEhgxy9mYoODqxeW+zhRDBkRClCxFAKyeWPIdUX7LBKVnHTuxJGEF9qx/1eme0cq36TjwWtFRpdpUvCvjsmgRBok1NsHYFKL3m1J7h96NZRoJUcQvhIt6mj5L3kDqF8+SThZuw7DZ9yrOP9r+p/1ndLrB5/7jPvZp2SCazjb3bJ7Lrd9RM6zuOAvUE46N5mWfewNJW/v3s94KIglklMkRAlyEAkIAYAdRFHmuZzbWMEEUlbG4+Z1rwETPltl/MKiDI0EyjBtXeokgQi6ViMVlCAzUiEXtCSDCci8YBQBnmchrp5LMeesBAYgFgYJooWAAlweqcAAAiAFKAKDD4TFHAIkSo1BiDADAgwAZjKwavbLkYwcpAMNVOZoIEAJpNuGZmjTPInxcfHYej3fOIuQLtqIBDDIAgsWLz1aSw5ypUI8mZmOgyMhLEhMTI1DI9c5IOMQ9mrazlFBpkiEspsQRXKtBYw0CKobizeSZsa3lmhXiS+nD2Aay8PFaR9fYJuUMxl/GC3fXk/9zJ3u7Cmymui65m9tLtLT/bZrl9MuqwOwNzy0DO5qwGX/YX3ULWiVSlJ+C8/96/fs8vNaVNX05xthUAbVMMwLNHMSUAQ/x0BSKicgUCszkX/dxQKEf9cTZ31+36z1EREzjew04nhvZUiiQya6Zjk71qajTrWSzY0l4AaX7SXIMijJ5Ubqz+8Nu53e2q+VbHf85fAGTAMiMwYAZbWFEAhCHGsKYJxkDkxWRjNgbAdsDYADBCwRIYTDIupZKgh7HdNTUG58kMsumbsrm5uSkEscg28pB72XdGOvfy17YPAVEZn8XiPhP8xrYm8Dw3kzBxJNlP9w+j9xj1xHvGub7sOq7rY97zlDtiXbdJ0lS7824pvYMW0zYoWaBzBfA5MstQP/y+vkgz91Zm2fXteT/sZMMPfZEG7FydZnIzVNRiKUhjQ1I6sRufOnH3fNRG5DE6YU+6ENubpNwh1dS1QlUzDqG8Xfd4jzSsRwIaJoLCBdeWzZi2iiLDJjITgAkMMQCoUQZEQUBgKJFNgnU/p1sb9vHEaMeI4F2s83vOTBXxNM+gsBU5QpBODqo2vcsInckn91vXikpBMFG7rogy83xeY9DwBjQgAGwszAYABJ3gSQwbBljGRAUDYFwGGIwA69qMZfBqAwgKQVgEsQIAg8EyiIUpC7BbG6aUeJ+NA1tVUnbHQyo/v753/onAjjwit8NfCesFHXPjubV/VKzyJryZgiv9IWWvpcHNEN7e4Ca3zAUAxVKnTSa3qw4fK3TDK0or8qq2aPZdtNLNAxYNnTrUvjvZZ+09K7HlEIYlsdiLUMRLXxqelFOnHtehaAUzohm3x+rEZCaGpGh6kgCtu5tiTLFy4QmBCL/G6BrCxoAaOJUAwDCAbSGjCQBmMCEmkj0andDMZIJhiChFzjm6GvV2JNP7ptdhHKw5fKRrWD03Q03bbVNs2MU43FQiF6O3UV8Cy8f5uZ1X1zZiTXyAaqGqrWMAHz8ebgUiYZkinbF6rFBYSQAKgRgiYoVWYWKGwULYMSAhEQERADAYYlCgSAGAgMC2oYBMMI3popXiJgSiAmypLdnubxRh9Uf7q9EGEKFHycnkeytsbizJ8Sz+QkpY7m+qUDCS7pdE7QYxqJnZzIkPcdjp8tt83+nlG8+6bfmauXtgMiB2yaPNF61IqJknN99i7/PEO2p7jfPjuwMu9rb1ASMtw8I3hFcmtbsDrYjd+5SnOn27PyfQMbvMLGk6po/FruE5H/U8cE43mmALQj2hYKX57jq1gggRoE4oYQspAwCiTPgYIxEnZy2UxykxSZDHLipuPGp771tWbTKcJcxAavNFQ6bqt7t98zHXr1laWRv6Bk8Mr71BNS1Yf8GeGC6hVbdPugiKFehsDoTh/NekEqIGAHF0xQQAIk0QAATEtCkYgTVS0FCeUUqNLVEAFABlgjBCwAwUBBhEZNowYFgAbCvUgjUMsIEImMHSndmirbsgnWMEEyOJc8HWJZ02f5/2dX9KD3M2v8qfIhg73ksuI00Lll6YfebT2guz3dUitKt7nJTQO6ZfHVZXfXQeCtxsLsfz+NrhW4Z0RMJxxqfqhBajCduodMhRCZJpFPkWmgKLcZmW9oc/3HvnBDzNvO5ctLKYi+kiqC2IzJy6F8ow1GWQaIUCG4hGGDEGK2VZMaCUAjGepnkYBaCM1Qgl5CCWcSRPVFJklXZHA91KTcWrzTIO2ohom/q2H37I9PZmlcBzq4Vb/ESXgMbjC5nlpcwx5yrq27mQOvGbKpMHAGxXcYMZWw+Ma5YFrEpHNfg4IU2CV0OAlBKlKEQAYIzVAgiAAODOt1CwwqvcDwARPA2yiAzcNk0YAiqtqc/pX///9UGUBGKlY3Ljxp6caNPgiXrCxXJGjpnvyyWNT+7UEyZU8Nr5zKc5xna6sBdsJ2pGeTrbuT23N3qZ72FlwNfNDC3x29oDt+jh/OjMcpr29Np+YWXyAUwf49YdxXSKY4K7yWyvNt9GPJXf3j8ax0dh7jr1Wm0GjSmD2IPSbWhlEO7QanRaIimqtFeubkgHRKIilc7aUgArIPPyegPEslBfXTlaJi4M2mIL8EKiF9parVHX2IdmqGaNCYkPGxayNm3ms70KtWyP62SeOlgK2Eo8AxaDmuV2Pi1mQDgdUpVEIhVQd5/3kDEYNABjmSkwBLwSAFgPZjFxCWCQAMzMCgBOVEQEAQQpxRECA5BMB4MAELBIBkCLwC3b4WGaZgSRcgWaLrX724Lck79oiMSxiEipECTOLU+ZHHp/aUOmGcSUnubIP4mk2urUqJAYG8qZuLfuS0PO4mjSgkY38773bh8ibl/F0vFBAYkrZVpsR3xGWW/17dN+RoKexr1ZyOpIUxxiVnrS4i0225PXIRc1e7SC6jqDu8hsOxlihhaSUob6Vm24pAiVtNo6FFlwSfZ01horisUJ6jhcKWqwmSAlY7ywrYBhDU4IhzNY0btSqnDSNutUWeVM1YyXmcPxg2TR5kUzASPjRDwjgK0ZULWYZdxSLA8goDLWgECaijeM1X+gqap9/YvB1iUiLECwAa2MImDgSxMAedC2TUDw01KKDZBlBcKywjsBgRVADAADLhsCEQBkyxVCAGAjsjfCxrQ1bs7ReU5sAEipgU3BAoKiElHUhHGGJIDnlkaQ7T4/akdvcM8ET7rOmoT5NLkV4VLXNLovey91Pq7k3Ro90KQNLa7YhfygmcIsV7TTjfiG8JC3tMHVbPsFW6I+Lfai6Nh3psVOOcT33Ho392e1aWZEw6Ls16BdZFKqUt/4SueStVQqJbLBJYd+9FknoINqVFkBsIgqspxzcizDu2U2WyqAFRThEwaXTPtfIwq7r0KyiZ7UzJamwmBXxcQ2M4kYgkFB61pkAAQbnc7D2+sH6iIhAFzcTFtD4tmPZiqHctxUWhgAsAGCFRYboxhLGACoWuBdgC08K6BCAFmYgQnDoA0GJh4WCoDJmFQCr8YsA4xhDIxv+7ZlCxyoSklm7RLX4SAXN28tx6SoVPtqCTFIAEWkJKFMZM5FLs2IOM60c3r6IRo1EsDIAWE0r3xeZ4Xmnlv+HLFrvftSDXaKiuMKLPupkLIBvCUmmWOv+ZDalseAseig1wmrulFlI4uyO66it8HquPZxIyOElawZU+fQnrIxFKwSO1KGsiF6xGrTnB7MrFaL3ZKVAohSNwxNlEPBM94AyIF4prwRwHhy5bXeaF31dtpnNx47ImKi8vHtPBARggIek/yplV9aEKj0zdF69iQJAhDsJTndGlPdefMVHnXbnuXasyBOKFECWAjgNqAoMqd1rQAQXuXldVFdFSLABhZIxlaC1wAg42Y5Kcsbrl1D4HX84Idd/YbEquUeBKVICojEChg6b79dFEOKyEgJZ+GZ1BhDQKDHr+/0OQp+dPe8WCx/f5n253pv25I1nypJ8XXU3aBOVaclbx/v3z0z1Ru/VZO8cefb1RSvO8/7rDnbbmsmc3Ia8Wq1mUcUlFadhCZRXPTKChljTZYViyRFHJZ1uqKiY5kno2TcaVkeZ3wiNu/QsLExc3PconrZtxc39IGLBhTTDQgEHIfGT5jzAEj2HBJwp6Z7aXvXV9nP+dD9wnJk8YMSaFp5YUlrsWCkUrMm69JLy8Zu++fzk56tly4lHIBsDU2cGVBw23IXiMa8LYD63jYBSJEoY7VlUTmEtL4oBaiVAgNlsPmEgJROJw6xLMtYKAuRAlNgIlFtXE7h47KgtnpD3MJjhjtRWhRAsZg5CF4Ah305FoUUDJBQggBNitFWsV1GuWXfzadb365ay8hVnqMgrBa6PUOsvtsGFRUoaQWHkzi95m4c/D3c7FiGvCzXD3d1cRE1oy7l9Gk3th0WM7kT4nbaye5mssnNikexDTF5UkBQyWjSQweru+zGJIlPybgdd9hKAjzJocY/6dMkc616Z9wtq44a97IRQutGAAyMYfETANDGSA3QRMUgw0zV8/bcTJOW7xg9EQgbFyBTsCFlkChkT1jreP9h//48Ii+uCiww263NZW0YANTZwaZg6ENos3swe4QIMAECVb6FWE2A4Pc2iENxgDGMAVYCAAsEr9OWwWdzGcQQL9OBNiludRmFYAPAoHDDLuySqyGrGAC5QyRbclcbRAMHOsq6je4coXSGcEJQYipz+2CWN7GiRSPLrowimLRXCZlbfB+Y/YlGHNHkYr3V5QUTTLhFqPeO79q0Nj/cqIu7q7tasvCKShlsJnE4e3bJh5JGOBCQjU/TZ2DTBFdWmz642apb5+niw3rggtYiQi8hi6k/Ir/VdXNly45hogBsangSoIABZAZMYcIAcWJUXrNVenMr4Yk2igjFb4m7OV7HEtcxopWviXPSlH34nv+ktbUQKFQggAFEQIyOZAmQWRu2qRRjZ5tARsiSwKyDsSh0yLzFQ8UKQASAwAiD5creWAhRC7zTA9qIFwMsYwBYPb5hpRrHX8kGhPRV5oXy4JLQrG+O34IIkghJgrScByKUyFJlb7jZ9w3sxDvp+BhjhXSy70ZdHllktVdlQBf3auJ47nNdfEohIlZq4/YIC6OGOrswN6++4+5ypGp1t/oG++z7se9DnaZt0iEpz/IeN5vbprjNQ0jCYrft9oQU0O/0jXdYKO2xk0+ZkqSZI18YisglvZmZ7+acCyNRVImIZaW6BggARAJAmTfiMkIS0MhmYa/Txgd/2g/pjWVYJEavsgdCPIiufGk5VgtW1EFWXlswmuEGVcPZrQcVsIV1lsoQOJhbFsdNMatimFhMCOYWrQwEX5yGeHmXNqwgK0AWLDBjsHUSGQABEDB4ZVuLAAEIgQaAAIABVKh9ugTwG1zDk9q8EI9vpYxbkkgxYoBoJByfKEBBAaBGETp3o9sEIHgZYcpHXe4re7IBBkqFqyksv1kpNx5K4tc95lOh/UhkU3hskH+fg5DObIDSxgq0JVt92qGhVXonZ8XxWR4y1cBicajjhgtKWOZzhNgUb1ckjU3b9GlTkp9BVL0IWdTBmMK88ylyjdDLRkarNRFMRDRRMQYFgohgzU4bjUs4EMZtRLMbs76Gz0kYq80mEbD5tmbiKZZe0QIgkCcFoa/6mrym61gsDOMM0zVOgYU6y3JAiUMBYMzFLYpYiwUAQ0JgmZjWbj4NAKuSiWE7bBiU5eauzWBRMmC6AjI8icjQMowqC2AYZhsDLC+zWxJIIW/LTblyQXPpxd+htJIObQPECBEAdIDAQ+oTgwCqaodA4qxddvq4vzBu6WKi+eA3k1p126CGSbK+yKGy0uGQxJBIiV9pGoYHq7jL/75sCaOiAlhuxCtNZTYR9pY75V135zP2PeswLRohJe1QWeMFm9WBjzD6d5QQz1t0UG756LG+lUk+0fuYg8cdkFgNMy3e1RSE4OZyAXSVHQxg4JWIVrviN8E7vVldXhNsmCntkQDkfOlwbNIzoZTPhCs7RTOAY3ASESKLNdcTkKY6AGAAzswaBrCEWGepGSErmQKZEUICBFgNEwsxSAQZABF4t0kzAdgFYQB1E6gSVIAAVg8RTZSxDqeyVQYIjY1N8BQwLFtfKizP1rasICsAEmLm94+lr4c/JEVEVEGi6gLDAQHokLiAxpIuTWjekZHHHctyY7qezefMReOBHQAdfR9fyRacO/MSUQDZeLNMMUzv0fz+WaiSs9ycJTd3gpU8cUrd2ozP6L/vnIjhyu3DtxBHSrSsqwqtLXGuNLWa60037WzBRtY2pJZm04lgL23ulAvzLrpY2/36rDu1tDmzFEDcFIUKKUm0gQCW/bLU2Om3do7HNpk1bfaklxEkpqBgrSkYhsMFG85EXq89ga8ZLECa0YCazoujh3BQsNmwVwHAJjGH0WgMGOesKABEsACwELhMYJCmJigABvtQjLSB4G0MMiYzUpUiAoAB8QAIwKV0VhkYwEr2XcuDWSJTyNF8iRbVjBsQ4jnft3NvfPkh9HFwBSlQU9yqWHyUgJxBw5bg7NLc4SziyY4QFs6nHDTc1dk+aAqc1RSWA8nMPKYUGRcMowaGUUbVGPf4fldnmDx9l7TaScSQu4edntTfd8ns6Gh5p2mVRVLiQDEVMLZpGvsKlzauJ12Hz4lIWk+WEnWyboA7LGulW++wlzM4PUlejeRjEIK4J/acqggQwsB7rAAX6N3QxSdkXG7JFW9n1IzzqOKO0DgcBK3NlSe0uWppKHM8Z5qTqd70pqzKSSRtVrcaV44ZyOxjCCEEgC2WtWxiQ9lgYAEGY2YjgNaOGrwaEWSZDcpARBsTBjBQmlJgAs8YgAggYW2NwTBNACysDJ4TsmASwGkQ0ql0ECUG3efr+Ti/fn39+jRLoK6KImdFlGoRh1iUr+85Ynvbb1/9DVi113Rctp1PP9s98bN/7d213r97/+7Kdb20Vui6XspCY4ITsSd3wMqiOQ349vHJRrPMqJsTpovw9uvt9ztgtNjQMl+5HESMKGwlJTt8bNRdpzLzFBCXyxlbsoVFo8vu7nMrRDztIweXlBxAAoKCq3KYMROIiADRkTsurU5R4ab7eM9qeNOrdCvZkoYyv0cIMFhTPZg1v/Sru8D2wWtyAia1eZm1rrUr0IDJVJsXpmRriBcPoSCAhWwyF7iw3c0vQKAZDCybwkA1qmBeVgBW+ygyJQxebQiUFI0KABlhBF4tVROcqgAQgGks1gOYNuPyzRxYxyNhJsfcBVISYokunl+58waI7IeRKsnxcXaxOi92FuHynekIjUIsxuLGG/Vzx9v3W4ETxuCJ0eEBj50MPZXBlgWpmNMClzJzpUbzWPbMUKXHKfDYcm0sTzQVpAM3MK9CkdjOaC57Nm0tVY9qQDe1sllvtZFQsWfbtbd1NCvGVvpTGmcQWLi0SAMPQgMMDAADEVE5FmambXCWKZfcNRln0m5r1J7zs/2kx2ObY8/wilnrmj3Bw8mDYGRQkfZmZZFwnG4Gw0VzB4NmaxkOAbCRHdJabhu5VswAEAAp6ubiEoPIGsgLUAj7EnZMABBsGoiVIhnQJgCpAhTAWACiFNAh8MrGFQrGALBMP9YPQ3NR+RIJs5TDxdHaeT3oiv0j/p+FIQy6aqpWlVIuwY2EzVN54F1Ia5hyudvTrFtvs+pMFqxZHr78rT4NrMsH40Pj2HPP2/Ius+Y0GaO20rPb9TDPXf9O6nI+r0x6ioCF2X09I8dOb/1NL3Xy7KWPb+o2xv7QU7qzaIJ3cbbJBXjmeWc3fUI0LAjKKx0JHCWAvEhP9ut7eEoMDMw2M0MNDWIr2kD8VBPPewNzsWuhzW8PPzzNTA0D3vZ2taUlxnhzplk5AWsXMatSmk5ts6kEyI5k9VBpuDClAhVDaac1wYqLKMAmJBgYA0Bm6BReBwDGACxgYlghGosCDN4ZgAAgAMM0bayaTAgGAGaDAgABmt02aFKsKCUm11KgwkLFjUeN+ml772xbI6hqnx1VYVUndcOQpRPntoetxheNkJ13HIvhCpoIot+V68/5yygqaSmvQKWNNzKz4KPOuzCp3Jc8bbJTadgHzVZ+al8vabYNwou/2WsaTfqgKZDrKpxTyjVmTztJpyDLg8JOUtgpIbeZzh6Zmx2GdrGrXVLcOWTjyrraj7+ceryGYQYM5QchtN5NupXV0OjiDqFYtTM0WAWJzZsBsV6KiQ2dPV9YWDRIFclFJgvE9tDzO+JLWZKWszQ26ikdyPcSH5ZGEKYRF5wABMLIBmyQsrDDyzCAGQMoBSoEpQab7SCQDwCEAVAKNFkbs0epApAFFDWWgYQQzO4Ni0OLLkfghMUQOEmGixGhcZ9vMwoAS+XqkgqVcktDHDefW98iHVopmnp1tlNYbUBiwOnDm1Cw1qOFcdQ2Tgk94d1Y+rwXjSoIRml96FTf3EWr95epkDBmtJFr83CimW58xodOW1eJnP/snP2mV7rtCm5PlQk1kp1dvVdGZ8XaXnRKCjIsYTqJP9LyLUAdU2TDzvfwNDPADACyDYvhGxILmfVtExXFmgV3Le9aRHwt8jHAavVelAbpHAOarBWILFIxU+vheHM922118jlgVDat3C01rNk9mh0TtSf1lYhAv/Y6MuHjAAxWRBGPpwANjAEEsMGQgsHTAGhjzEwADBgaAFMUg4kJMGZ4XRm22TIHSGDzFcPQaQglUYyOIkwj1VBFVU61I3NODe5M4RRLbmTfdtdGotbpplpEzNpQa6khXq5lqphIjgKyLmFdPfOLKmLPdkYju6s8158S0/Ia7++jd+HQkRYx5SknPx17ecKTP3Sr2+69HtutUXGzIdPZ2cLE+KU3TUmtq4y60ZfdcpFZLU/Fti255YRGGXkkSi8wbDAbAGzrG3dYZHXaHlWefpbKvZqkxbB3BFe+xZKIoXGDCIKp6YMJ8QEzKu5i0T0elVicBOIATOORHBkkApmwete7oXTnKGNQbPNAScTD7EuoOtQYxiM6AMQ0Pb31ZlAKlIKciIAW7OwMPAWvhEWwmaWYAAKwz/3cvNgGBJ0vcUkQEDGxWFiMoGKhFH4bO4MAw0ptUVWpDlURNte5u3PzuzrwCR1w9g17X7AQB9E0lRobQJAY2pSxYvr81LJXSSzO/JYOZRMl+qIUScJn12cha+MNSxr50ogdXUyde7turOjCcxs6pr+3/539mi3FQXfX7yDaDvJP8enxuvbOeLiP33yFNcmwJ7XIFcgmczmXj0wBcy8MJvBazSqc+IlzOft96rnNQuo9EFA0u2dQOLaZqhGCAGCrPDOseB5c+YrBPF6bNMhiiZ09M4jpSkxpmhdVvHSwYvFYb66nKmaVFAWpFQwwagaAoQMYAIPfaAYDYIBaiDEwWDcRMD0YAoAleFoQbGYELCiymkxouITgcDBQGMWwE4Q3Cmf25g6gDkNIooR0JFGaOumK23e9Y9UIZ43qRFmT6utg5upYhOEghKFiAuJr2ngVzJaiCINnDZ2/Zq07RiWdRBr8jv4S7XhXvlbq09dn+lf05Z0xc32T0+vDXWl7k41TDlsxpiYiMZHlKClo3tjckStFhYZyfzgtB/LO1kUXYQAxgPGiLk3RdMEir5VMHPlOW2DlppdaKKgASvtBf2GqDRNlUqARVyeXDnH1SGiBZQDRqtRKtMFN6/LjUFt7Yycbq+3JCQFe0L8DYAwwYQDMViUD0JwRAjBG7ZDYJwNlWMKyEShAAEiGQAYREGDM2JyVGsDAMrhsCpAAgM1mbKPikEHuWVJpqiZlVWdu2xlAHYA2V0aclLiovaFrHZugotZsRDAccDZ3Uqm0N821lTkZORKOq1aXCSqDA5e5jZKtLCiNbANkSWhOmaimKnpYBT28MwcRpdNpQjOALvNwU9YDJFNz/drrSqkwFNlWQJnhk4gIQMRiJXwKk9YYZfncEp9nbu6GG93izTp3Xx0wEt6XuCmGDgxw2O0ltrbIXSIo6VnbprQBirCwFWWHKUbNedQVyclZ8urmA2ItDnW849PRQCZFLI+leEMvsrahap7qnYJyg0GzVACLweslAwQQZS347VIYTYAhAgADoA0MAIwBwwSxbaplBQgGxlgZYIHCQCypVkglcvMOVCwSotUZdaBpAFBJqSlVqqqp1Lp5xKy35Zk2ysZgHVJ9tWD4zAUnyJ5xwHHbuHp4g186AshoUN04V7fYw5ki2mutRJLclgDCTX4QPvBCKyHQe25b0nST247fjcO5rrWR+3IPiuhpDVuoTD3JwhVdDpYYWzWmNKLeKuzJQCS9cKk0cDAzAIwPVvSmR5EkYjAmAcjFxJcQKC1hBShDpkzludimgL/c5grbP6ot5+Ajgl6gpgzNC7v+o7UnN+40Ht6FjRyMMJXO/Yd1rflzfPBJwxIGDACr4YdcDSRihAClTJc1a4GmlABQSTAhlaDGGFQCItpAiiqgdCjYbBbLAEAY2DYFCBGCVmXtClEgYmggpKrLp5vydAAOiQEZNNilkiR3DioXem+OkVxQ2QLsDhKhVS3L1mNQWMyc18H61u6xbzFxQeRH3pOXFBjDihDrNfkOxuLBREsqE5KCUQjJ85q7uBdPOz5EXMbbW5Kwkiwt4gooZIkSVo5PKr76pzKdZs5SlCrervIyM4+pS0E72rExAGBvK+lNEZpMFZBJzSGS2r0aEwUWBSQHoSxbgEuGEXVVqIiISqjZfBRAGoCpzmb8dTYcPmvJNDqKVOaFANGGTvNcGMKwCsZY1iIAshswBkGKCLxbi0GUAiCQDCJ1JYSqqiqASQEIMIAtlcIGZzWwAEBskw0CIsBo04SaoY2GDZk6sgiJEJ8rbD9HKUcQlEUWKoQumm0uc8lsAaook02WYVIH3W2JmOgO4MKssyeafBcXUiE3RiqFbvJuQAxEiB3RTb1yfxFE34RDa+Mr+MoWeviiQc1s0iTK7WOe3gNfL3gLXsmVBUALGE2pSKQ0Jzpf1mrqJosEB/Te7QpfyjKG5LjXvBIV2Abxxgww0iKy6FSz7uvkpkStdlfFjuQ4mlJBY6dJrsOg0qQwKggBV2eCmYOAHJ+ZXlF6zpqau7VJZGpKcMZyIG2qeDpf//yaeE3OWAykBhuA1UWIBJdxFqYPzwVPhUVDqiBqQhIooAAIIADEMGBoBMxYwFju3kpMWgAqCjxPyBWmIg4HQ4ooJSPe/e0XcgMAERGhpUuyNuxccbLhmLLBA0oRxcYNbBQy0VdEdjTW425eAc9JmiUhoZLO7uxP7JOZFq1kgsiL/UUsoVBbOqfmUzx16ljoUjG5OWXFbP3OsN09vnef0ColtOKlJYCQPAVQ+N58eGfORo2YlZNwYnD3G/cSPmeWHqd0BBjKMAECwADfc3LXkw5mvViwB54cRFFvzSq4lMMnT9G0mEGfqEtiLh5mF9ccQlFjTYdORscZkBVR7rONsi476neyPktaJlHFrLeuyLW0uYYQZ8kkIEPGHTBVIgKj+WQWBAABkCyAGQnYlgZAVRk8BcyaSDCHdSvAAAzTBZYsCYgWS1vc552NEpGJANMYKpXs56agO4w9LBQbVZlSp7pqCdWyLSYokgArcofcfrs6JWWeS+soU5hfh0ASI8uxypaol7WDVzpYgSBSIKyEMnYWnEydgWLY9MIVhamcbEzS5KTYvp7z8fp//1fUP80xy9FChAQJ3eqVawoK5eZ8gpbmHZo6nUdR9pAiA4qzLXdi4VSnIjAAAoRUdw4P9WpVpta8doZH7jhn+cRq16oQdHKoUVLejmbrus66iJmL4UYZTzBluu4myTBkVf1CvnLcbcNayIkLz3ryy2CFrYrNFawd5EfXWpgGYGAB202gmJWclfCbW716eoywTZUriYIaSsBmuC2OM2BAWgNjbMgAKIxbCLYjphIAwOLmk6/ti26nXtvUxDigMRmp/O5j/+5d53yXq9ZNK8zGuJqKc8NUVJK1xSyA1hY0qEdB58pCqKIVhIGXpbxrifAs42pjo03F0qShIEnaZoR7LkqdaMlDHmlR1rmletSJJMMn4ydffPLTev3Civzj/+pv19UyRntPWlJJGot+iz/40a/5S+e4JThivqHKkCQejDNjaSxleaF5F4QZABABsDVj8Ay99TjEywI/d+ZOQbr1q8wwrYFZTxav5imhE8U4Q9N4WAhClY49x6mf69rqF1mBVVi961rT9fmKn5fyt8p45tdkZ4QEvnfP2njBwrPBPRDbMhslflt4M4ABkAgxYdIAYCOyWhkIQGAYmxFmLMBkAcNbFACYKi3NEnsjSglDoKJHOl3VvvK/+6/ev/LXzZNYaoa1mzELOtquNqdkINWUza7a79VZ6atk3Si2626psDXqjFC2btCpfi0A8RR8gxabA4EeA3YYOoGZybYEo5Ri4cSS5Bknx5H3DL/LG62HK8O+Itt/88uPlr9e+fqnW8+oKBWpZOlNfKe/579ytybWEJeUXtNGniY2LUo3Dw2iXHHaJpu1EiQBgAEAoM6cfLhsHOE9x0GRBxiWB2IwdILO1iqQJYMigHIm3CjK5RChFA+XltEsXVoEy5NFkplYmtvUlE6GbMRlU7RqHAaBQYMSA8PqZSUDNIZZEiBv5cMzDUAGgKyGSQxQoJAKLGBMl0+RCAADADa25XLHggUDBQuIM69SCJTakoolYMi0e/0HZVGKdsmGwaVLDApaMYaKFdrKV6AuFJXSCp9z11Aci6JUMm6aF0nEw8WgwqwAVo7Ayi2ZN7rRNzuda3m3Xk3Gm1J6cyGtzDMQjhOjeumL8HFR/WWYOClNpzVBFFO1ytmP/+b1wyu7xxbTxu0elzBSF4u/yxIKyqEC+YjNmhH7bJpzlFgwqtYaNLkXlUiCEPyIHU4CIoBAHXuINgOYspBSK7K4hUSyJkZ9gYaxtDCqQKNocEmmOSw6EyKRWaZpMx+IiBvgmuY5I6LILbj1akU9ctoMgM02DweDDMYAsDzFkupUOq3gPVIBKnooq2DaYAMDUniWogKsQDGonOLGrGCTMoEMVcZ2oykNAgxgxgwPz1JcIWWpsFi35ii+95HEcOXVfLh6+zALRjOOKILaWFFi2tAtVVczJdWqTvblakYAs7VxbRFcVxDvCMNAcLaqMiHL3DKRDOaU2/Ptbac854hoULba4lS7Gy2uAAks4oPxL93Ew8SQdtH3kFePh1CUqEZUmcreoqxhLVojc5vNKMCnmhCeafPbEvZWisRMilLO4LbSLOclC6jEoALCqjLXSMnsCgi2mnvPxEYnQ3DuiCSZUiYsRs4KgKPlNlm1lisqRpGAhpcNlGS4shA8B1HIXW1M1qYlaDb2I1/p1QtBSvNmAGeCax2ACCBi0HZzSyQXQJf6sKwNACBAAMAECkTEICB4BgEgAACU3QhvWVlgCyi511jwjnxmAowpm/dZNjFubq6BYk/BL5yHYtt+2t12eU0YHRCrtVRqKXpXVSJLvJoodWLu8hWm0TAr2Wy0RGHGOnEAyCZVt26xoERS9ogruepJJCdGJDg7GyAKeay4OTrozt1iqDPh3Nql8wk3aemWfYcirhPoRYbJilUGGBYkq7SjJqJpgHWyZaCZ1FUuX2OJi8SegCSSfvmGLe5RQhpTrEAKyMKYzLI1u1hFcb4sapHGlldGceCsCLa8INB0cDAihIK5SBCoC38EKkZR0uZsxmcAPZF4q42BReaYqVSa9Svu5Y1kGDI+ABwL4UWgRCBgRbeW6kwDoDCYFwwADAyoVIcmDEQn4iQi8AyowFODBNlX8xXBBOkg2Bn3LNkKAcTBNpfNkpXV5X22JRdm35lpOzKaEvERO49xvt1n2cLSiAGtNUERYqkO2dPdFGuVyHWCjzVoT1ARxGC1HYyTCHEK2YIxCkEkJVCnsy2rQUnNPWvel57v8ww0pS0alMEetuE6ex7RosdWRTGd24YqW+MkzqFbai6tiNauLa12cRzj8zHIpcGNKi1uq1fAP7Y/uraxYT/tJMGkots5vsMXNzBAxSpYHYCK6WwTl1IqjafCQSNOa4Td4i2NiQmm0qhhclAEJYInJyRJRX8IIWKXgrhobmlMG3pPLFxaEluDOW5FW6GCSww2KIgbMbTP9rklMMBmA2xsido6rAS/dYVnBgSAYQAsEBhAAVgBwxCEAdt2n74zqwACgFW3jI0BEAYAsm3LttjcbFVooIOCJImvcfOwZg9KR00tvlkvu7xZLJcSVGIAbcbVX51UqSNVbkW5SirVjPGiOPb6PqsgFwhYhCEVkOeNuCR2Rcr1VqGOklsudaEM9rA844A2KPGRYbXXPNDAokakY/zs+4YmHqu0Zk+/PP7k8cGyBAuOJxphYz6LCCQAxtyWwgmIxaeVrhZUPEVFqKHzE805TDGAQEcqEFjtDkOlEZdqz2tkkw5vYwVHQaIpN6CSmm4SYbhkIVtdBCeerMlAyY8jCjFA9BLqIZegukVBkrIBlTitXtmQD3lWVo4AEksbQBiKG7As0wD8INVYBmQG8qheQimFV29osBlbgDFFUDJgsAG28GiV7Ont08YuOxwDC2HDPRsCAAEsxVe+uLOspcWcDHImQqUhDtr3dghNadXRV2B9O+9Xs2+u2S1TUVer44UKaFClKSWxS4UVbtua2nU4tjr3MI7DBZLEYRkmEcRj0qrVOWbIhQejDiCheUQYtgpV9kUo+vUAMQulEuqqEEBgBkpO6vrizy79j798vv/Tl0tUlNAkkjlWt3EJ3fPGLJfv8TZxEXMtIuXX2NLS16UzReMJmywFKgasoMIAkhAEzUX0BJsUS0mMiKfSKEwUCFwGY3THHfs/JSSNITkqYmbgD3AGgEw4NgIRKVkQ3eyEnmCYQFfNiDPLfiZDcA6xK5e3TZQDYCzLNlYYUFDKwikSPOMFgY8CAcAAgcFzhWkMAAIYbQ/v8VUKbwQasmy7fNe0AkBjIrv5ytd8DlZi18IZjZWVwKxMjSvvbWRAtisqOtzruqJfMTv2ItYAxTK3WEKFxK2pHE99io8wtImNvMZWCcDJJbe3xSQyM0MJh/Y4x00IjSWeB2iJKjyTk5ibWB4FLFgTku16Ts9HyTW8G6lhVwajiXUn45/7b/+rD/uv/8fHTJACio0TodpTUrLHLssrGhIRv679LCsELZwkQWBUTqt3tyQSWRIWJQAsFsDJK2u0MB4CuRJNRZ2+/J/u/2ekpIkJS2oLpbPTfkj4X0pEpR8O5czWpRCLlF3mBgePzLbxWNOAncttZiwLE9EOXiiHKTjrxQg+9rVYv//s3za9+Yutaaw6AMu0WMqR5gtkjwzPg6wFqsfRwIhixja2LDcDY6iA3M8Pvrln38DtnjJMrX23X8TLSBsimzsXnjFAIhWsXd58nRxq29wKAjeywrImI8u3DqMZMC6ny7r5Di8tXuW8W9aiskKY5fKldV0pqhyRIK2wPOrVbjsYi1TO+lgEoRxpDwqRGQGxac8z8cSjfJGSYmUsEgY4iDq5M1aYkg2xxhNyt9ZlbhjS88QKR+p2mnPDf7/n7X9xz5s/cGuk9CpbQzcsiC5GO3kiIsqQRVt0sRvfg6h5lqMdOuBar5VQb7oAEoDh98qpl1IaggB43BTrVa//fvF/6bKGYRStootvzm40l1YgYNLYsa7BEizROWd4rC8Dartv55w973PzUDvB8bVLCpHY8v5enhtzXzrW0ApsxlhBGgDVZBpoRkSA/PAHWS4MKjZg7lf5vn0/zPPMOTN0xZlDKBYNwoC687VHHb62G/MV7db/brf9he9+nicTyhw8N992TQHAgNCCm2VDEdnaxL3IlEt12XH1nl4FqooDSS+W7aKz3yte63Ju1GElEKJphMUyCcdIiHM01YVLFNDbawGUs4TUskaLzgwEjiOkllogFaVTISasEZQIALvpy5aq6HTqvoa+PQbFefXEmsUCCypHS8msc32s6XOl1894Np5X/nr8cf1jvP5Nk9uOCZpAAKlKHMGBW0OjQERTnNawqW4zeasE8FuAaWlQWDijMkIAI+pFiJkCzuBB3IVeD2utNHdaTqHDYR5EfnI8XVg04fSamRTH7HKigJh0sN0HCAar8RTfpKVJ0PKam9wCEip68JzEE/wXaYARKmMCDAOwFkaZElG5bPCHsaqCwFTAQG0rl2tHMgywtW18BwfAMFHgzrsxk3c20nDiIlPPxoUBDHDn/+Pb4hHDzAwYogJAgxBKkHAbteT0ollb3EQaRKhZKpc6bNJek9LHRADBJRU+ywNoj4Y7V4DjCqWOugfmds3ozEGRTqKZKjA6oHSJcyD6CODShapqUo2IwCld/mqKaL6cDlYfH6DPikI2LNhuDlkT22ajr7//k8TevbetK39dL99zKnd7NsmH7UgtRqC1alvxEREzD8kmBBdb5HhSrU0ba651R5R02pLkQgQ8LUv7AdNseW1lY21jMbxSL0PhIncYnPVMZrbVRRSXx1upbHC4nCdHM2qJUWKBynBGCb4+18svh6WVFje0EIRYa3jETTJOR9HdxahE59gK4LYDC0PZseJlwACIcdAPlMxAGk4xIKqA2+p96ygobM2m4m3B94avChMCBBgoUTbNzs3aPT17SnarLZptl/sIPg5cbA2Zdbs0TAatJKpkmuVyNVmtbBefnrs07xNzFlPtIpucl5M4tkfNKOIioXhPgkn41OM5apqACNAGoIulZJqHlgZka4XUQWtwypFGQwTApBQEAhCL60RcEJ1Q/akj5hMVX7xYhFJkg3lFOfV4vj78N9fDr/T3pfubcf3V/e7H8Bx4rPmcOaGOIC5Co4GKmBgslamBJ3Ex2ZMya4twiho7gLxz3kSIFNOYlrE0a1klxFbN284nM0XLDCBgpgisOYYoSDLoa71NTWYzjx4bKyMhc2ZCAIpbl67IiHUOQMa0dsQYSeFMs60eTcvfow5vnc9N1p72dv2KAW3z6yr/CdMQG7EJXZsBwjikw9lb01ASGmuzLGtxy42SpjRL21wHYYQ4Dh+VrWaDbS3NPvfA5m6x7Cd2ri3ZXk10Y1s1sRGJAtsKYww033X5vm6jk82COApdBmXTw+1roxOx7kyL4P1P+/2Jxw8CFiZLuQqH11p/d967e/7t85LMg+UMSRqw1XveQKuprdYRRkgWnO1SUNpBwo5imjbCbE7vtnvILohCCFVixUpAOyXbldbpu1n+QjtFh4hXMYfF7nJ5z1M+7JqVz+/z8/3f9vh1OT/y+PRrXg7jyrj9EcTnYp2i0z0CKCu4V+zP5HhCJcaNdn3K0sWRg5JJbzI5s3cFrTedlXvUYAPGrdmlzZguflXMqouKNwKm9XZzNyC0RT2cVkjXuYiqVBmgzVY5O6CEDZO5gBXVx5CCQT0ILMDJ1qOKUnQJd45p1m/ShHJCUCCWMUi8rX8T/bZqhDGBudFABJDtp97HuvPm4XmSJl00Fshzno8SwoCWgCm8pSx27tf2bv3gfu72HTaxrWpps00Q1ghgKbIKsohoSEYgwXO23O0bBDnATdps3jeFEovj+f7WK10KVJzLw0+P85d8ftfDw/k1n3/x+Rc+/3Jhnenb9/+wP/9//tm/+xujlIsUCHPBnCq1RaMRHVhz8zf35ODzsNz0WHLsS91TjqXVTMp7zOkz7z73w8fRqq42a4RWFJFcxpToNP3lfHXAiOZwXVveJxigBq8UVh7cx77y+7FY5gv2+h8k3FnxzJrEY7jXzFIl98Bu2k2sjS5KINoeEzkNNCKKYpFHrQTWYGFvUCzvCptCAGKXGSAzuGxQpL1lomI0Pb+9n4uzyas4VB1g79qazGADECGeTjdojZKEzBlXUtwTLbUH0zKhl1iKkjRppXMb5vcWZCqrWj2snl4YsUH/5n3s5y2zQdDO4RQDKKWAVo0+ClMgzLev2MzFWpb4Ttut0hYR0VQ12ADbFoDaQmAkIGUXc2gAUFaYZq8aW0QwUMGziwxWyDCNa+CAkGXn6tatRxFrgfZlsB0sz1k3i/f1yvGaj32XK5fX8RvrLOrjbzP6/Nx6/Pjjf1/77U7wzMcsOXCRxQTqTrqsM7ylNuTnHO70sO7l6m1135webraEz27zuM3F3H522WtY7tnjKkFR2qogMqtO6e5qrhB5Pp3EwdAc0hIX0s0N3+73/dr1c10XaCAEXXWtnn71Yf60e+gri8ylSv0BuwKSupdpZNKI09koEZ5ooZgoVSC4YzgAAeCW54u5UIZw9W2XMuNRa/Dkm629kCrGZYbf5597Xhfv6hRteRZFh+Wtsbx96sRqbsR9Xq9FAI26YZSJtHlt7xIUAC1aYglRiJSq8aSme4U0MUEDGsbD+etVJKrbFpCRH/zK79gAALTFb9r/8i7/y5M3JbUtrg0qGuXQAEloLiKdwiaAALOsEYAlLJoVjCXAYAPQRI0pEYgNtluAjDZMg8lg86oNbN7nzi4y3laZJ+3urgWlr1BOvTKVnXZdSPzRb69L89Ufjbvjb1aE/t6PxbcUKMTm3OLGcHUzfSbUwuNuAdvss2usQoeqLTVkmLuXnAu1dD5exzYtoQjNyBDXzOS0YtMoisrGlF0hdVfQ33KoIUqFw5K2xW4nHWPRiPrFzqznX579+ccqm+Hy7ppkrktT705agCJKkkEF0bitrHmeCMWTDo2Nm3AQwBOI0xFzBIcdamFsjW775geTAA1WT50KKSoUbNJm/vn7zK41eziucOiBpmi1nb3HfloFNVZLobGta91JjgCpi90thXLt+tKlJUpMAAgcEwSoOEIuh3fOQcabz5z5G94mn1t859tmnn+0eV8NOwUME13D8j0QxgFRp0gIkEpzCgADBBhSMBZAs4iZAVaAtsUwJWyk14a9LmhhUSDYUrAVGIAFwLjB2IOgAIlby1htXHCrfTcU4x4OEvZJr4Xi/c7pF7/8aeVy//RILWENvNfrU21cyU095rvS4c2p9uhZmMbiQ5Tye48ecZmOE+nQTROkBvNRncZR1WWZe06X8E3p+3LW2ZTWqJU0Jq0VJRW+T39pjweC6LGzkHfNWrJ2+2ThsOZDVdXWymS9wwF7VjKLZVk1p9MoZ0UGL6MSifuocR7Axhi+cuJzuFGD0lYDgMxFnVMYSV0wF9NRtE6AGECgmeEJYo5wLk2dh1U2Xq/rz3OuD36uD+DNT/aTfefm1MPrMmed69W+rgJUOJyMzQXIEAZkwNtqttxc7lz7cTaXX7nbcofdr+9ju1Bpa8jbcvgCwAwUcsRwYYUAccYBOGa0FYADjZVtSQAQuDEjBjAwAyaGyTYmJhEBEQs2DGAMqgBZ1kQ3ZaoFiABuQFKAII2MIfcyw8jhkvRigG6FCW/bH8+1NY0c3lzJwAAvnco8Tbe2MTJPo45rWlklJLqudZ3rVEyYpAORxU6vUugsRpbKYJxmaSKEQSlhVAL8zXzLKPF2e/Wd9pfFta99+uIgQHCgweqH1WZ9wkpmelY5yv0KHqqHqAd59fp27z3Ra+WS7IEMZ0g52fLs9nYVLYhwklgeUWORJSOwrSkyzkoTB5fQ5Jh5YUo6rAIAhS1GIoIxW/Dk4RglWHbqz6y/4WN++dPP5Lo255uGQaD0EGIdLONRJgjQLO0eRCwLs3ZZrl2+zz13xs3lMthiFLyliNrOBoGvx2WqA2AEBABsMVB4Giw4ABhYcFQNLCMBK9ZG45YthhHbMjGzYlh5sAxbSRkWKYN7vAECmIhYIs4mJS3CUgIiUIAgpEwXGjkytJxA8F6cABRe5pIvHRA9lYDrWe107cJWKrRbsbTwko9lUiVOWrcUA+eP7+vT15/cI7pw0UlEIeBX3UrRw2TW6nWnCJWeuATxV70qxN4+3LvWN+Kd5QFFbDwQGiOWTMMgoOHIUnIVXaaL2Q6gOcHSae+0H3YYa8LNOVYynXoPY+sQacVSNnVnk2V8CU/7DmRncWLjeTRxujXXnBPV/a2xBZapBlQjCCCa3769h3Icia3mr+yKkQkyNtgvGMA3FmilKtEr27C+cxmXm28bd9Y290cLa8qGAhEAECKoYc6WBRYK9LaCMBAJwKgAEqOEoGwcKcBSEsaqGEkDYzGQWAFmZRODxQzYVrFgAFtjVkoLC7LD1gy8IgC8a8yM1HQ5ddcLAicQCZnSCUdFDlymZRZ/kBC8VKZMZGChafM4Yk/azl6gVNtjJ5YpkKAZjCgatAEMy6P4i/01dJ0uiIr0HSGjpMEgaDVao/S5PA9WEcGav9Xf1sGnRru3r+fthp5lONw8FtFMhIHyCJeqa1SfizoZ0bNLozrr2z94T1Iyn8sXz1I+VSrhldidbuQkNdMbBTGNN/pahm90aSJmnZLKxXtk+UmaLnYtdlO4qh6xVNVYm1VsVkzaqmqfX5/20qIoNteIBMYVET8pu1dg0Cw7S2e/3cp2ZdsxYzahmACQPoIhImzVNDBsAjFBgQNEY4Ta1NYVrq4Q2SBkKtujzGJTGWm3ZMumgEOZBGDr2jAJI4wCYFoAm2BjsBisYFvYNDwbLEXEWhjbwGrbhWFYpHdtwDHXrItlOJvmpveAi5QKH7CSZxPrEL8/WN3SIOZiSr8gENNgB2nVJU1BhzgtJPbIj/2coA6QJlZVWIep3I+/npqqN+eZCORlrg7DfXFpNNlml/fUppS0FBA4JmQ05jyP5Tm6oRIsgVWmF0OjSsaQZgdT+Zy9hiz2+6rnd70/T3GylWkby/6ttxEdXdVRKZYzYiTZr9LlQ9qx62wFW6ROlKLTjCeFGqIQZ7pwaAPjsz+d+vm67e6tnhy5IaNeP99z3+e+k7lvdLv3bd0f97PPr3++2bK2swIsAbYpaEYBAIcAgmpBCzTCVFplAIDJFDAKBmoqW50NVu8ptCRg7mkQGQEokBgAVDYggQVRgAVGDFQsOySmrNgwYvC8yBLrPGzYFkwbWHYCW9vJqDVm9xqHa7CKWC73tvfISmFxGj7W86QZ9B9mk8rmadpya2TohPjWn35LIBeJEB42BDRSDIGi2gopVScJM3Iy5yqyMKCp6ayWvuR1zVy5/1eayFtUt4i3wYomsEXzknm9PfW16pF0Qp29RVg0xhfO4uqqXHVaLbA1s0REprMwghewm77Zo4leTW3ojw/j/35vPzd7ht3cg6Qv7JmtZcoCY5diG67ZlCI4wfYl8lw5nt9uwY/MTVZYPyddsbLhVGf6w3Q3xInqe8/fYLvDb+Yf/wZves4Z3NBsxnk954YKv9LNrnK/oCdoicB5ozRIvnEoR1UANAAEABBDNAAAxGTAKlMwNle2ILBCZiCmOb/tKjazEjQQA4SMBqhNIsaIhDPZVDEAVgEsxFDBgK0AgAB2AQDBZgC4S9sUJm2aYBabVmz6RfelRczEPdcQJThWvH428F/C/ORAiJXIjKXd1vpbjc0kUinyYgq+MmpDaGwbHUYojvOEVWODpRM54zqILKFaCdR5t96mkdrd/Do8H7Xw2JG15O/NwF7mt2k/9dlU+5332xI7BD/3FOo7jtfuuHG6pXciihJG7QcZtD3zm8z9k/uPtV/hPDyX/uA/fZ2c9nrMmkluMcjxsmynTI+MKNPKyQ2HYVKAYBqxRdR8i9Mty2S/A/Q5mcVDumBCWaYolXjV1feratZv/9zf/+NP+CDAMAAMAA8DQIAQAAIABIABYAhDGPypMgDE8JEAMDACI3xkIIY/MT1+EgEgQACAAL7xk/fYIBG4c2Og1oHs7lVKm4NOaZJJEte7vdWdhK9mPZdKpdLzgAICJRSDBVCjTEsyTiQZEkhdupQxOpHtNfWKE31VEFF419m2Lhn64b7YWZYrX+orrB50Lk4gCXgQw+HcPT639XVrX6WqJbglItO6VFrWOD7VR/vyt1+EXt9q5fd8wf7fv5+fOZRnx9KOz2RTDlf69NymLV/gjjyvM60YSDiClC6cKK3MzzM1I4bfOSuPwhJKZDxl5QlSZ1q13QDA5O/+7e/rJ2hphAGC3DSNsCpgJQJMhQEDQAABxqIhkEqgAkD2ewgAI59e2wBg1fbhJ8UA8sdNDzEvBqACDJgKsQK+6v98/dt/HDBRb61G20eNQkFbkCBpCO2O7iutUIcWctGWmvdKaamIVIRLWBNRiUphhWKSV1yZgQtHeTIBBcIuCcIILJymSsQSs9qtnHXYyhiFzaRrqwy/6b1avfbKNonIOZbxuDNdRNuNBtwS1iFqWok2SI/X12770HE9fLy5/G7/uq6n+A/f/uKbX/+FDUQgWo/JvrpTTr3ijjj7Ngadbt08Ipq53T2pnIzH0xJTc4+xqIOo3vl57YmTpOouKFl36ntLv6zp//pP3300dwFfHSEGBBDA/2/ala5T7EsgBLGk+3bb9D63Zxrjcf7wrfT78vtXfqeoi9LQUwmRwhZsJAIVQBQEMxuYszBYUca0g5aMAyiVsZPJscKCay01JRYMP3yqi6LJ+wwXr9MP1j4TY5eO06mmHuLXHdKHjh62K6uKcld/iBBdAZxvTifv3UGYwvecv2ZqpvO1e306Fkhlqt9jsTG0ZBKDNVDlL6cgD1FTSHqlvYHWRSB9MlWOZVpMU0QquUSHIEsklu1gmQD0YEYYBAIAAEQIGGkQAAREGmkQAAREGGksBhgVqdP4QKLD2IGl+E2BHQxGeyyRXzD472GkU41UirversA3g5Eg3huY/KrANwUAAhgWW8iamsGNpHvGeC/za3M2lt+q87B1vaaXcY97y8t0ThsBnABUEhDehSNCpXUaccAIaV1ZByYEQCSMSPlc70mhzaB+cblmhfBGpRJpqJkCqWxLm3xf3nmzvGyg7bt7r4geyzoA3bGaVvkYtqyESUYlJC9f/jEpNDlUqTIU20zlqeqqktMK0RbUKp0kqL2RlBSxL1f2nU0OsoYIPfGKSiK5SJtVZCi5zb/CiicSorNWCWAGT4Ohrjq16jS/toDBSI/ThTH5BSMNhnucKo3CgkHEKDqN9raeLsEJFPHBpPfeTwUAQNvYmG1HYKh6H7ymwL+DQacwUCf5ifjdstZ5GyK/EYSSmw8dlCnXrrAowTcGJAg2c3K613W3b8294RlikRrdPsdCzfW793uujq/zvbfywr4NH1RKFAmalgg86F1ppUl2sENSGEQNkhADJwMWZ3sribKkfWlnBwnYZMWUNqeDhkJLAs95WZ+HR3vX++p0BaYAMxgxIGz069UUXBQcHFSkT7zBSVlyGUlss9VpE/DcKycFQbDwblu7DvYub3mVirF4MsN38D0kdllnJ4VQFukjlyJxhHLLV3OImipA1GsXNND+kAEAg6qj/TyDDtqKy9akTh/tL5dhBW3F25FJnGrHyxV3WwLjLoTQpIgdEgMtp4tXtYcOi6bo+lBrXuui6r36DcDY2JBtxzw3JxNcflWayZcusP8OoUrnp9hvvXGTf2jlzifdperribeC/AYEtOx54fqMnjy7Tv97yq0vzCHwTRlZgokYmzx9SLwYmQsOxGBIV4owuT89DU50w72LLq+fBQBBIJDmCDz6hYlIkvZlmGEcrDUXF1QiLkSiceWQh/bISJKQPOjlWAw5zJhCQajwaxbpTzcWVkdjslWxkAC4U1ZeHryWEBds0YxvxSnPS9SIUBoacK4f1Vn9fH5ukHCUsIHcDx5vahrtTFP2Wvb2U+x6XR/kFb3lIm/1dhkpchIqZWXPaQIJMbmRhAsCEwASWGQeX/NbZ6jZLI7SD81/3Nx4vHSP37EU2qOcNT8p2rrG88Vf8o5l+pgSww3t1fd3/dQrxVUAADCxkrDYx7lU+8D57Rtg6xQKq4j4SMsxr8ydm+PVSdpH23OXl3fMecbgUwBAYsZCYr4KBrEDBgEAAAaxAwIDqMAqQv9g/cDC2F/vMxgEVFGnAAIzBgLAjIXEAEDmkPXj6un2/YhEWrf+2nX639NuXWETAyAxYyAA7BgIzBgIDZUo5gVIKShBuRFHJhyR3FNxhQVY2psGXd0d8xBiNQ0EcwtMa4ySTWwlCQDUuzoTCtit/W250cOh1EjGDEOYopRAAiBDMWagVMS2CNf1yug7+6cojQ7HwqeIceumiqcXn+dqUNAWbVkrMkQ3VeIyVIg4tdWfcu5gC/qEKNbHpSFG6rxm8WEPqvQqi3/IU16wh8u+vTIDju5q/T5ccuFGmZ6LVBNkPqatKBkBAIPpcbNxGqWjnaHRILn/8khn24fh4FKmx8iT569f+sL9CnQHCISG9/drVbfTkTVLxMgSIsKV5ECiAE0JgZIJUNymO12TW1EChnKaJCMg6REMSmEwPhgtaKukmw4vYAyWjYbCQtNgtJrPCGyyw8gdBLI3SrMSAMY6lfSAQHaztKpEZkqRgzN+apcsG5BgeLe4KiLWE61oqcDDkY0ggEjSAmmasrezoCkQG4wWDIoIMLs2OkUAIlIjNgAuBhAveHZwEQBiPdGKQQE/ya5ijYdITEgi0UrLgrcogiRRU8AogNwWpU0BwEC0J140IBCY7IpuIgCB5KgTalSQ38gviNhBTAWxEXMANiYtmHNR2Mslixqv2iqIIEYsNZRs4fglQolQDLQcp0KJ5YJlqWmCLcQuEAVMejKJEYwQIhxJogAFJWAUc9qDjt2VZgLYL0e45+mzqtWPzTlwiEWZU1cW+88de10NreAClpi01mVY7CtsIKmsM5tjXKv2yg4pEDhd0a5NyqWWHhJZSA+4ltzn9ft7h1udLC83kKZLjAXweRF0Y/jo87GKBy9NvEpiU1Y/AmAMgmtiAOK4j5Z3jvfuuz4yCQEH9tZ24MsOjMtVMG15tE5juH/rlhBTrgt3s+PlChxBgVMFgAJNGj0Oc0h736+ehynX9vr4rz9vu6mYXKN/Un3ttt0sm2yYxrCAgArTmQ9GZgR7vghL2APgGPaghSNwB0g4qAJvBXAGu14LHAJwUPWW2vR8XsGQ+thLJlunKI0nMMB+1bvRjsZThTMQEsYzbmON4Nn57Af8wN+37eCnvSnXk3Bx87QLZyAktDW3MLa4l1AdwjVbzmvoocIURnAM44pvU4Ppkc3TLpwBAIym3TZ9t5j84b560+7b431s0N1Tr7/Q+RiajlfgGBIA4GDG/drwUyMyBzZPZ3ACQkI75XpJ2+JKuDPc0TytoAMhYa92awfuWAEACOgKKRHLZnU2ApOC4DJE0UqDyIhITOCYAoU+XFcVIEpATW0KTwcr4UpVk5PSAhuFCBKrHBTaSzhhRMgRAAUQBYCLYFcMTgs6JpyiaxlZTdzaPFR4hyiNllNQ+KyeLEIRBG5pyWidYnEllZpsPR+PecxI+vD2qM9WpGgOSPcByStnTUxusidwZvngH/XsPshblbk8+8lrskc9EsPQwwptZaHBNYIVhlXIFgCgmA1MNwWedORjsYRbB+q0XAUA5mXA6uDtpEICrZwcvZbz6wdr+zp/ebX+c2itJ+4PnqYmii+4uiSgMZo+kT801QfdOnus/c1bXUncXLpNZuqKgxft+UAt857dpoMXpcdwaWJMB3L7AY/fFCc199LbN7/WU6aXgw/zRtH92TQfxvCuRydG8ZRiUFgROFG88J/+6k//aVUTGuyEE7f2zPhQI/7mv/lLGSof3H54SixHd+qvPh7zoI3f6yVxj16NBx4cl9BdsM6P9r2TYp7L7efx6E/5txWXUeZSj9UkzuyomKQ+FnZx8zS6KI8PZ3cyTUFsiNWlfpvYmttyuI0GvnBXfM/evoPgNe7v1/Yw7u3i7Ibv/3lqsPU4urgtDtP+RErBuY7lj8rbKy61/9VL9u0rfmgyk3HLtcce26FDf+T+6Jlihhol27L+waysd0+73bKDxunwDN97kj+zWhdd+tX83eX6JXEz9Z6DO4Oful/mNy/malyjbp8+e//Tp+Zrs7bZ0B1VAARNkcZE28JgBEgQSFJaCSJZKu5RLxs4EMBRhyC3uz4EAIE31CzA0kxmCSiCYYRCjX0BZC2bdN2d17XyXryPiURERAIAl1YjhZ1LSq1TwLrXyet7HX5r1FNGXd0dpYSpbLoyl0/edtZTfdi2XVQjEpcVAcOWFmXS7jpRqxbbZ/f1PM3xm5v1aRzofoCI7/vGEXb1GYTa2419/5du/te6c9UiyzA3ub0YYcG+ZucWv/H+9IOTMy0yolYLTB6uS3gZPmwXBgGoIeBoN/UW5EhgOkCzBydpC9RHOhqOcS5TnkUHK3foTi2L00o9rmSFVoEDEHF7/emzHUtUziKeHv7Hietf586bWlbLPUBaqzzIOGWYAuBwCvCS3ncMLwCb/e7p0fSZTGkQmjphOxqv1iEAnAAA/Lb8IazCXXgtgbfWcgwiJSFnY9bf4xCLrpSvX9yrBPHFsypfN14zQwAAnCyZyqRR75uJLd5mX89D/b3eexqtAwAAfMm7lrx/T6Rj4Mv5N/W+JTQAcD0xSJYpuiiJcSWjrZ2ZAgCgaJpD9p+Es/3VnlnuBK7O7x85nl6R9EoAgJ4asrvyIePPTidUAAAl8oL+6x8/t/Ka2wIAcH+89/b9WY0TZdOAASABhm25AjjA2ccno37z1jPXqstIFUlwNNDrC199mMqUU7jNaTLj47wSnAQE1bNMQzmGRZqsivlsj7RMpLFsqiogRwRLA97ML72wf32bW+P+3X40r8oNAT3lRsHugAEsYs1eGz8laMuKfJJkgVYPMulj2zeA22JiZdjQCUIdaeE+DnLQXRRZsqBYv3+k1XTzD985nicl2a4aib2qJZtQbrmTd/M0hSu9wKLe5TDiESRT2o2PD3f3AlAtYDLTAm/JLFRSJt+ZRWeLktzI9Pnx/IaowEyzz3ID2AWAnuT2cm9UAiEU5fMePlVqUSl/whpOtaJEQPJU+Tr9tK0GuGrDxF4edldZSnNzfOB6f4+vBCrCounPGhDb90nBSzfQJkpZ5Es20cXyGZ+mPkpxx09m3tcyqkwSjhTZ3JIgiBxVNrckCa/87T+3A56NKNDSuv7EuQJY2pRTTwm4AIuL1/vPcuPAeuWfS/xPyyW4u3ws2uX+hjvi7y8hgE7yH9HMo+5PAJ6y/TibstsAZVO/7mdxG4B78kG4FQjAIz2A9ifcCT1iSWcprSHg7FS5fvrp9RV4mxtH3syQsGOq7OycClBcSae0t8bUXlA+6sC1dsTI6QCMVGa1YlubTBEzbi4RRZYh6isI2+RIIX6Ltlqd59veADjgNOfLzAwoCOiLDfulJ3V/kIGNpLGxi3rZIDajuVslJS048MHYi/y53/vVD+/Hh11vHa63JjuwiE7fzU0d3feulrPeOkLrWO4YQasOhEZ5L+LheZSKw8fWjUs/ySlbnKtQe+GH/nlwrfBEk00OBRDsq1z3hoeLj2T69YqKGC1dopVlSXpZuMTshANf5yMgg5lt7/sRA8BgOCp0rQqgXFH7jGoA3te2TxkVpw73TUZgK/meL8HkcyowkTi4nOy93JyGwAYD15UEArwlmxPiuxbzfWskMCdj1i1chUJIbZVe/iR0l0xkHs436n/MxCVOWAkC28TN2fxJHzfn+bec9v6wn0GBa6/5vx7AlYLqbfHnHw3jWffMLghEIuX6YBANIV+dCYJoQ87zJVGSlN7hJBEW759NGcjUNeD4DjkWAkBC5GP0VHhneJVfAn8AH7bNf688ykxXODvIFRgWP96+8s/9ZehX8+8WSSMhxu/21mPtFHmXP8pbsAHT2IGNAkBQg8r5Sg7XT3l770hP/n56AloacrmxCVZ9thelL1dlU+HcCbnvaIGzQ5blT0/f+yVquSan1oPiuIh1iQAMApaAGQNQAG46W/R73hpFURcCRldmtE323KNUlMbOzAy6cpChDOvQNdoL5khurwmRHitU2cduTY/BvYs31kqIjUAOCJ+Fh23eO9sf+OGbng157qwTzEbk9ti8fSmumZtjk4hbxBhnMmPDqHihFuSrPFJaZp/H/Z4SL6IWVKQC19BDUFovCwFRVhdnNF46h/bveactPiobnEEZjO7TrVRUXHklhWOirfQMAxo8S25gXKcCZMhTdX2iHCZ/PX5cGwHs7axEoJvcdJhPuvJSzLKgxD7uj48nEsLHN9TArrFAYPs9mftsYb4pKpCUBwzXihKA5Ek5czehV56czKsSJCUwIRMmWgJd8LKuzn7+9Eff7q65PlA9xEf93gv5XxHA0/qbB4bNgmftf6AkUHLI6Nu0CB9vrJVgwiuaIUaulQaV2KrKdkkQrpL329bJH37uXlu9cZ/V19eWPBklAMD0ye6j4eTO+Ecf6R0VHmwyHgUwEg4yALThn/sPOXi98e5wuaQAjJj03slYLudPOhpVJ+tOGgLEAgAAWEbHFg6nnZWMZsNwtQaAlha5ODIJfY27Vv+6z/Hvv4fPf9YnfOZf/OwMORsxoKlxvMXR4mgRAKpyAoMDBlWiZZvBeprCJBFUpaj3eust9Y+dTQMKo5sGv0+1dP7stAZQ5gm3NCLllgPV8i6UaG0mzFfmpscAb74LjxXrGmiX7q2TGhERU+aBs9Lkfhl/D/Gbre/KXd6x7KPoJLmnVbhTdT3cbFjZhqbBEW4ziPmsWplpbvoC64y2+JrWiQQjKrFBlNRNRRM7FBmxU83KRCtLOx399ZBxyMQJHwLQKitN6QEvqHKJYN5gALB5KTVh+gk7eYWF32IdwnYSrtVHArtkTEagOYChuj95brizIRKopdk/BTqdT94/FPYMAIIx17rpNtAHQMloQUsQkqbKdScAAAAGoSQEBrBJn13js1AZwqW+pjuuy5/xBfAB15b7rQufsWVGSQAoNuTjiXsziBEp5oiMq6RLYmf0BWL6astpSYKob7niPfnL981Vr6GM5VomMjESAKDfbb3+5+G/zCaADqldBQETAWFTAU+AIx5BWiQg2PNp7957v24SwKN6NRYA7qAknKz0uwC6q3GaUEFLi1xk7hn0iLvP4Ir36JrXQKZyKxcTp2sD/7MpgKMCIABADKS4ANnZtyPdVZIav/XTb/b8U19kCkJYVPyunoA8BF/l4BQ5b/B5OIqkYMRqIduX7NCCdYsjFTxJnLG/QOHeTpUjE6WlgcugPdr3yd3t/iLn5778CX51lvFQHIrcWCZcBkVt7YSkhWlMRieaVGScjjxK6WmlfF5zEZ5jtjVDK4k/lUEa2XfzIRCsall1mWC5VbxBnOm8qEIeKg9ntVj9hSJj14ooQVkSSecPjAAAPJrJ748+M3zCVmHD4iKwOYDJGkZFMV9WRWA2KWDs0kD5UAHMNXsrgNVk7xkoBgED22JU9TiFTYwAfNierSUgIbkpg6ZWcPP+6U6aNpBXnL99saaBmQkAI2HQNLF+uyquLN1/uZY9TLvzQL0RYt1hJ/WxjmY1FuknV/4cyFMNRJcgln6V4fc84RdEN/e9D+W6OEl0lrxf/RrK6/CzNvd8jj5r8igAKIBbl/n6bCIQvwmu9nfCrC/fP7G0YmCVVwOkEAZPAStXAQjCYfpUiNVXO+T6T98X/QKMAAAAmSeXrh7GJTjWKo+ykzcBrha52DcJfvHYZ/tXf87l7aPdmX/+P2o6757NcAMc9ezemT7tCdNd3p51kZ/9uB+Hg8G1SGIkGzxRZkFPq+eee7v5yngWce16bDYbLiFEE4/Up2qxZk+x6xBSuW+BXQCUMcgLuiK+W6bviVyhLS20XGDB0XxInYojkAUgajaw54CHXe+P93dgLfzVfFxKkfv5/u/qbq4D0NrrgaXFmmgnTBlPsEZ7m/0pXbDN7Ln9Vi0I5m0VtqyQgiu0GxVTFPK4nque9NRC+OZNfs6a1U5GQyaKUCUwf8QfAvrV0lRUEgzJYQAAoG3Z0JtYdFggYgyulXDu1e3KFqotbMiKd30OpkM5CS/jZ9gfgIhICA/f8BjmUAHAURyei67jsOtjvacFtsu/9B8WcxoJqVOld2QqmKyfmZyBP9wePcDDSbwYOgwAAAJG4Pqr8v8ROXi8tdPu3fSKL7Y2+mZDpJEGb3zvyvWBFII4L19bK/LWKQjiDDKSUXIQNktOyumHe70bON4ifUEAgO1kBeBDPQHLHy1/kIwCCMKiLQKYZh4uf/8H+azj14enBIAgDMengJ+ndk+Op571qAAMAABiSjBP1UFIbZX9O96D5gY0tyV337YCbJ5Ghnd+dpungnNSBk0FPXL46cq5DPfjYFHuP1e3s+4bfxMAJIEQG1xlcVzd3FAIRL366WkywSKUoHg+Nq+3v9kTZJVAijI/ZNCBGsgrZPZX6uQ5r9vcV/Ga6zxAktbBqiMOnKYza5w6gA2I+dkp2uHVvkLxvQSW8HymED711U/vb/oHyUqvEd/yCiUerzOF1ESaNpQ2k6CqsbAyIYe2YvWMkNhcJf3Qy6RxqDKQNkKEYDvBtLfy415lJREpEGnVkKSalV76uFGhBcViaAdPjEGwMQIQHFb+Q7dNu5+1ncftAgD6xFuHO6bfb5b2Zkbeeme4WK8EgHZzb3zUouUaDEoAAhfU0qB/8drx309XAT6JhJsOKAEpU+Xq+dPzNgGayxczQeG95d2X5ndYAlCgIVn6tcPOCr8OAUTIn9ZqE1pp0zwcf32F3zH77tACcOXPgTx9ec0lEkRlQiZy70gSRLqU2+s+5//8f9gmwaCy4WtARBl71uRGEBCE+WoFEFZsIVfxn3ZBWwIWwOUn2R0i0sKITv+98RFhBARgtGISoF2eVQ0BkGCABAADcfz7Mh/yAGHhbPY3ANrHlZ8LGVdOAza15QVg3kk5/7JhtYDRqG5pmzy/fPT58TGn7OPG4yjSVwQAAGCbFcYYUNytyu4ys2phVFRiEYWiIPzu+fe9/rHyR9ZYJKKuLX9Unef16gHIJBMPS1E56spWdLPLU0k5wihv0tOousQSERZ1XX3ttozwEkJZccNy3f/dWH9jX6/E5aQdMQNDdcoCM7vRVE2rEif2YapSzlKdryQkIt8atsiO2esmGFmIVKs6BsOszeFHKAUJ12TnupvlPmUFjRs5MKf+upGfiYw4smkwL0Csp+W086N2dH18SJxYG0/swY8vejZrps19et55/gRL8Sr3wyYSqTM1wOwdoUEpVusYFiESLIHBFq3btTi03gP45IftsUPqO2F9oaa/9Btjah8rv3NR/kOYnrGVa/mM2rzoqAB56ju+9UQb4FyeBEqwu16+x7r6so+V+dYj47Y8g22VNBp6V0OoAACcYs/Zg1o83f9EZez9Ub/1Xf4xtL9cfuCK8dNKDNfy8nu1nbtYN8Z3Vf83PnYW+xYCvaweyr+9MdZQVuu1izhY68NF8ePAM3r5kVyNUYBPVcfhTEo9OVcvBK9a//wn7isJkZuFxjmyRR5w/96e0/gV/dBhvstRA6zlZkLTGeyVawoHGAAI2ZYX79JDF6tOEEAHdor9sEics37RnwYP2fr/N7x+Vy45BDBI93fdt7y8e+E8rB3Lrfm8c/Qhk5iLAtjC+jH/xT8fVl/XpV1LAEYB2K1a3r7IyFwpykIMguR5+eIGYJwKw3gVc+9se5koZAO3pjSijf35vKoTazMjTmOjWDmVd0tgFAEgJVrX8lRQ5XlTw9AMciuVksIlvFgIAMAEWN0iDphQ65u65H41vimZyPLCo66Z9Iy9f3Txvd/wz36wUQIJI1BXsoRUaWHvkWiIo9+yKCBjTOcy13SjtAiqxJOiMg3T2iEbH0HbK80MRXTQVJNgROtiZ7ZKHKv63d7uE+YBGNTpXq8Zo26hftkivaVnykbmlaLkZmfskQMzVomBWbiZBVFxyVdiCTtb90h9eD/99HAr8c44Wc5s126yoW0eZlX2Po6QiZG5Q2OL9tzWp5XKphPQnTvvLSjzgn2n+Vo3hb2Ky42r2gtO2r4vi19eIxI5XMbz+u3kIFAA2gDGps835z9z/SYAAEoMTGX/GKUo69fV4IZdDLZY/FXffHQ34qqbiUO2HAv0F+7MKaPtbXjiVjs/OftBT2sX99uUYghW3yPc2f1alq7DAY66mKO4f/jp7eTNjP423xvUMvwyh/j++sdW5uPTnQ38y1o1m5Wzef60W2098f2F3cukjeGOvh74dEY0eQldMQAAHcDujYeDBY+HTi6PuPKFx4Vnvvx0jcrdZfLbj7tTE82nOSy/t8aiMhoxL2b32SGn3xlaGD/aMDX2PrmCvqa0vTn8bekbp5z4vd4GBgAg01ZUyz0asWx1rkLrCxw8bJIBGNe2LS9TaXcNb9nuIY1onI5PlmOnsktVMzB2yya2VFNnK/WIEow7oCCYBzgJMm7u5yrAS+GTGDU1Fm8VQAkIoA5OocOjXVSLFCaNtLvnzvYe0GqevF4/td0rRXPbu0019KheTfpz6Jci6EAltVWi6kOhMRBuIsT7VFRHWdE9J61uzSZQw2A1eZlWg9s/uLmQtWOxbpBESidvb+ovMyzrEXqxa4F3CXs/7UNCmfTWB1aBh9u+C8j0O2XLIdH0vt5z5P6XVy8Pn+si0BT52LAz63Gam2u8bTdppzCNIWbdDxsPQgejWTOFTX/Xx21fAzL2iPSSfho/oETzCdiAMJ3zvDm8EjTe7C9Chaj8dkujJfpez+sABAAAgB7/8jh/u9UBBQAj7aD7s1DHf19sYVBVej4VYPL7EDQR2iYOCbQcR9BBGf+NzMjAs9hB75c9qBCV386A1EjDaQ96uL5G/3YhzU/3z/tNd3X+MzdOd6zTuyzyETlURt/15lC3wPMaTuCZ85+tZzefJrCGZsa99rvJnT18O75sne/NecAnu10h5t+Purfdwc8X4bGH9Z/PJ1+I5nh/0dx5f+BuaDAcNp7GsIEIrePp23pgRqROMofIrvR+GkMPJXOpcx4xMAsgAaMQXNqy96wchEmFLZ1OZxceNA4XgBB6SHukq0KQTa6sbaKWnsf5eeR5cz0gd9GruDAj8pw3BFJQg9mOEKAGp+QEyy5YElGGmmf29/veBblzqekwBmggxmoH4AYcqi4rvkrvFF32fhnP5Rc/Pv9Evf6Ln8i//y/V3bpKE97db53b1DjiJLsFz2KrYzAuVBBRrKYJKGB0e7hGr5ISD3r3KXZnrZuu60JM9pESVqKlztXpdWWO2zDynATFnIuMWRBy5w/GBwGnC4EA/V0ERgVOBfAzfGL8IXU5+6M/cGbMAOC5ABRjZEBk5sWU27E2uaVGRkKBmxZXDQIShCoIvxFYBCBBpOAUDJYag3NigOr3G6qETrwNpEEntIoYJAAAwLKtAwr8r6GKCK+hLUKCUIdBdxcDAICS4U6nqJPiHn4TwDidKtSJlwLIcKW8d/Xh/Cf6e/vQlOCNcClPWfZ87KHpp8dLAACA9XDU/fuLi5GKbyOdoUJg87vjRjZMeSbjs/MeAFgXZ08P+7PuJ9vXsEqM77s109X79PcuhkBuUjnx/g1Da+MIjeEuQgVji6nXAAAAsIqRoh36trQ7OCMAjJou4Xa2Cki1dKjC7FAch3u8MBhIoCB3BcDBhrs7tUieb549zy9DfR2cxsdFc85vixeuJ3IohxkOgmxjrIZCDa89V6WlUN7hwfOPLws3HwahUBZpKGAR+MD7wqvXz4Fz7Lay25mVp6rR+Zfz7/4a/3hc/zPOM74nzfjy9q6+h81IwNy2IV/k8kkkYQkBRrWbpo2UUkHXoVXBER0u4nIf/lI2akPIU9qQETHI9U7zpthrVYEeF+fLXt9LUAGUqDovI287LeAjjPqi7ZcF+pcjrvELZt6XQwsCAgFR2gAAAIEBdhqBAQAA8BrAV0SB/79IDLCzkd628+VT9r/4ca4n2VejWc7zYHTk+hc/YDXXGadup6wqcV6+FKy53ijtCgBIDJA8ROMxtrLto/ODzSyvnF8C01LDIKCECnvPV/9e37cHtdmc/stvDvrGIQMCQGKAMZEYYEws21x4tjRzQ3WCEpLhQLgN2JNcfKiIVLVTDUQuG9ltJHzm3se8/qK8eZLbFtP+TouuUDekNi1zVqV9b3tn/jr/lF//Vr98/OOi50n3nX78POy1i/DizpkbQM2RBAGIVaKT2JR92vGzibSbwmrFz/b8lPmJR36wHnevZ//rWmfDV3d1bdfV28sWGzgYMBOnLpdq+kakVraiCVd9DQCrO6e5u6xYWwXMKmaTj1n1oq7IZVBMk60UL6wHOe/cCeWkwinf4RRqZpDsuMc8gt9zaKby2+PX3Z924PrNm4c7oZt+v5GdUQL4z6ox2tf2l9tgAYJV70slOl4vwxG06Y/F0OscqL6vpVHcGyWBUZG/uDXpE0a0Do34oOZ6VFqREMBIRKFMhz7tgDAkbjW59doiga8RCYCAbTZ7ZbDLGCIn07dX2OOK16UoNL/dH3YKQe1agWWhrdv+rCSUzfXwrfj7b9efsO175v4lZM+aLYfuXn/w3dstXueBmxTjY38/v//ZX38/8nBtdcgTMRrTNaePO4aXALFCvRHO8ckZz86nsxrmOcC/4vtXj+F5dK9pfcUX+Y5LNXnW4pbdt29k4oKLtLqNiF2KzgB1iUQjSBKAvtLlap0ewLRMS5ZwTvc9lsQ0LkDyRIbNUXxcXa/s9B64E1yAg1jZZ3u8tZp9djz4XVFoRXo7G7zmlNvjkZKDM0oA/2k1ERuGSKkejaJm5xEy3NVk15doi3uT6LeCQ0urUyQwOiYc5m9KOPdRc83ShoQAABhpBamhurS2am4xIASAnTdJZDRcNRYAFFTcl46AWNxqpNe1nZ3CtxP1zs/zl2+7mHUNZzvh23918cfMuSSCGNr21VmZy8yDvN+dveaEa57X+fzps/7z1y+3n7/OmrQ/7mn49Xtsg3bm/XD/2PcrHQ1NV38FBSfRufXBnjsUQCGiCinTWfOz//2L9/nqYWaYX3/t9f0nHxz8/Afer42GzMBd1mCNYbkmaG6G+9o3XYVrcBGkARtpVnUsEqCFGjGIOhZmccyEYKMfxHScMZ2RnqFWImQzbqM5OOarvsnr3JvXBUoIQyekFrMFubOW3wcQ0E6nhtfq0IwA8B9YpIAmAAAAJBQwaBDYWWOsKmZwxkiRwKhIRRo0EviKJgkNpf00hx4EABCq1dpLXO44nXvzvE906+9xb/rn17+8/4Hvz5Pza96zcPj1r/oX/+JptUU/WvfC+7LeVmEIf0i5gEw6MEnXPOg/5vqNPrjqi37ZvAOztp+vxM9D53FG1kc3d93DuXtDdVFEIV9/6uMLJaRAAHHTn2v+6n/47O51/xjvyU3R2z537Qd8ecJnvfHzIIAXOBhbpexCMm3Nm5L+EPX+biB0oCaaNK6k5Whoc9r7BYGhs14nr1BVxjJzPeSb7XloEZ4NC5D9WCcr5F0Q6TJs8dE7pnckpuQrHHuFoEDk9ia/z9eLwPwnMAiMahLgG8RoiQG+6t35/Fd/cf73x1fnU4tL2SQxD56C0oAEFVImT8Zsm555tfbo9PVFOjBePCs8IJXRRXgTvuvizTgsJW/T0zmt0a6k5aPotM37u6SRpl1XrFO/am/f8fNNX91D3o/Yj0QdNg+biyqJNp+vPBsQKAoEgRAAnHrivauvr65+lXf1OtqB9ezn7iBTDcvLyiPZ4iIDQDnfk+8UdRbh6KMpQs2KM6OOxAk+j5q+UgCGuok7KrdtvxImHjx8lO9x3JotIZjb3SQFUKqTBHi/7I/XPloynTybWTUACP6sGCnEevxGcVNg54y0i+MmJkwZ79GI3AmB6EC0F/PNAYDG2ECyw+DQWooriQOJLo0d3BpvQ8KvxchQJVwtbnoOga9w9/DnZzi+uV0WOti6YA+L0Q0uekFpcEjg3JatDdWOesaJ7hUfr/2iGNccAnCIjGLpFovDCKkFbNwQMmOZoexqc9+lO62psBXhfdt07+sLzsMyXAPEe3caQ385METZVkDqzRJA0cEDWpE4B2AbaF/v5U+If/zKFHy6yvhx3FEvE1KcJRc1n0tyL3C4mYhBIjHEtp6qSVaGa+7e874RvMssT+W8prCWG1emJEwfltuSByi/cwLcb9VSHAoKZNsFCxSpDpNXzlfRLZOBGZamK7UzS/MnwYiwRPOUMJpyzcIaSuyMQbtY6Mfrp6b5pW75bhbu1GYsY+2OxmFoOe4a0PjNaYx0tJ0P4ASAg2mPG63H2+AEhIPJH9f9HZFfg8FQpf8wc4c+/U6cwTcid66imeZBB48WaRxtExmO5OCgzMVhc2s8h7XG1HCecPP9nj9P3XrTv8e3wWCz8DEyKV6RDAVlS+202+k88nFr0iU7vXMgXbpvj91DeMjj6CMXdZbNhQjYLugh0iSiNGq+QIDZQE02YmDCGDmhObwZJ8ohCGJq+biW4EOexQTKdlBkae74nPXDN0vOQdAmvY26eN5hTvQJkjsalkmy/bDnjX9+KnYasSUuZb983GyaYKJ9uVPFbpdquKau4R1cAJICThZ05tWHthcSwm58PP4ACPxZJXAd27801+ZQR/e36KdeLWwhsBN2sf9XLtSMwx/8hpf0ExcMseVXdqNDjIFxeloP+ePWXZBHAEbgG4sNtp33LlkPj2LXE3/c+Htcvoy/W9KNXXy6+YLurf647qVfQ7ij43XvkP3wpvihZzLWHC5W/eDYh50TSAFAlGowqHEzywTDwCNm1s97q9694cExKJNdFedrBS4hZO7sFbP2d/vgmalYLYgoxpnoWaQRkAoFSNnzeKi8rRkZAgNNWhXWJhW0DLFsAjKVhiBBYm9LEDwYwByGzqFbAH20eZplHatkLHWpVlHWFSAl55xjWM5GGTxssk0kQ00AxQ1ZaCOoIpFlptycdDOEOGOxs/l5l8gYtieMnWCi6GBZk5YSQhsI+nRJOZl2+u2a9uWmOoHSAzBi/IxIIzGjIQHMDhgEAAAYxA5l41B36J/1S07Q3Vu9Wbq1L3dZc63uJoAAMDsYOW6k63P9R3n5Ui5f2m4/fz1qPe1HewEAQAAYID2xsW7uat+g4abyr8apQLVKiBwDCWC+FmSkAItFjI/x7cB1+kZ4Yp9STuwOgJ/F10MX6hzZxOwUEgMAqqAlxEP935/D/FOOYR0WeTQIIAHMGIAOHiyuSBwRQ3qu7IX5Uyp7dCeb0QXej0XGKm2e9773QHEiCi+Bbt6mty6tScenCCJQMarTsAKorjg2rLFCo6pQ6QIXtDbqWAZpDEJUqRRwqhYD9rtNsA/8OHSnE0POjHoFhyZga4UjCB8KNEKzAgbZQCK1aFKYURZq6Kx2qgfKI1ACgbIjRktcadyh1/otTThRUS3IgyRlE8EGOFfE8YIruSscLqpQxHJvgtpCseWh8yZ51wTtIICDp8FQb7pLg7lmrGKkJYtJbkEkYGSomuxAAkBuw21oTI7EKr4ZnNUYHkhXXBx6qjEx1HhXowKGMrdA0uOUWhgUKpEcsYVGZSIdBgEgMdL/3e6pCqN/ISo+AyydwCDGDjIjAhiC3Iq/o6lJZggl78/7b9e89rEcWQSMDXcmK0Zm94hXVIQYj8guAAAQHYgVDAr4dmDODEaHiFdiAYxcJeCBbyBcEvAgAMApWtJgdtVPjUyNhgMXszNITOJgODCow+JOoiZy+1yql9OkWiCjMYSRyJBIAAAYzEaYEwNDqMFF1alFkAqMGKHbhlf3gn/p2oZ7+v24YFLVSX92a2kghIcgTNyJAwzxMgBuDQLZOq581LqbMQkctCohp1GzXhhAilxYOgWkEGUBIlRMEhTMrdmUPcLYxk6n1B3dyCrc2FQVtxBCTbOg0aks2YLoGdLCsyktQcIBzyoUMqYFagdJCPN9i4QrwYkTH3OQnibnciD7hc7lCVVw0sQQ3cjGJxTj0uSqcOVo3L0WErrjdKXZr3xRszCQNgEABp1q1+dzcAQBu3AKCRV2Zt1j6AmQPNgbJX/soIKg1Xanzidu2vk6gzMYV3w/szu6XgMOYTr5bWyVbDk1cAJNZN5ZEm+5K5+0zusVdTntpt8I9zQcNtBBQG48nQsVNSiRGWk6lxPvhyH3TSmsYlFVEKBT3L7GpqkxTgALo4q3Wn1tj9B7ZuZD1+Z3C8+79xETv22yMyZxiv1fz8ERlPS7Q58KbAGYTLuuR5YikD6weRrBGQAJ7a+Mu1vbQdkUjacDOIEGrgkCoriebwBEAiIlAkr9eDscQcDBpG8rKdH9CVjDqPLSBTZ9sPE0gyUALczhGJz4vZ3jzrnLU06g+QMJrYtxaP2Ng6A7gwQgJv6YOy1tAl+w4YA6Y8qG6oZ60Vv353mv1WaFvkpEwRwDxhCs6zX8xFFY+mEM0WEOkBqstGiIwQtrnK7eDfufFd8uACG6MC6uQ6oiGpeuOgVqUgtQZ0yL0LQkUlorzhr0vDcH4FHT7AMIUTXk4xGoSjdxMOQkWrtoDQI3A8GwXOFb3DpnhZg1Qy3y8BCg4eyy1pSDmaEcZToTOVEyiZ0mbeFWYrIgq3O/EzYsS+mOL4LEA5kDvREjMWkuKFH+p3/nNg0NlgYAEOrseN0/cz48Yztwgyfj9Cymc7k0RPes/vrO4WjmrdXY8uK+Kxd7NksTyCbWT8TyzfEieP18umdc6dHpzflA98HTl9HpfHhTuXX18q/cvlye/g+Xsh4ufr7rp3tNs7t3XFi8tfV3/EruNNyR372Hbo/SdPr01HkDHYCi5+vstPCl8oYf595Kve3MGr1fZiOnHSvo/7w749o9Eq+Zp9tsbM2jx/y7D6mBPD8XK3mwknnDDjRBKhDq7P+6f9i0PVrnXOrdy9GZx9li7wLvcvxz3jbllkq0Hrlgj8PjcgWTArmBY95+/uNHBGDxyN14mp+13Vjmg4ybj+vCFYAYowAEAaRLwuGlcXYgl4vUP+cjb9MWpuY2fe9s7Xeyuvb22knRNR5HV6+rI30QU7NaZ6/SnRT7HjyQ6/Lr2bc1i2p+bIytNsSx4ffmS/7r4R/+8DUz36aB2PQrq9v/qP/wj91XhR1xUbG0c/Qe3axcOhP06eZakz2esSgj4uJisdjcLikOPgyjoGhAG78zFYJQJGDYiiqBhqh/jUQJ4GMIKkggJAEAQZjrEV0H2xIGuVSCtPc1cdnlHMOQGWs6i84SQwFznHqwuliA6tFQACBWgauZSALJ0eTOi5hmSyY6GpK1EWxoAYITzTysYXPL1HCDMhZZxXvED9QlQhGdttpb9NTIA9z60A5b5W5vji99DV9uS3cg69LzPJeWfBBgAYCupnD7Ud79CQFek3cFwBBfN2Qib8On7ZUAAN2NCacrJ1unISLildWW8z0pRI+4e23C0Qm5WUL0Qu78xOv8q8NUfGJyrAY/NzW/XHzBe/dQAADgr6mzKFOZHG4AAEFkX0VeLlvT59e6CwIAgH57bvuLx8vlA1h+P0b/6f36P2p8/tuv+PsP//2P777f96bmz3z4PgIAv0K/7fyfjOU5zachCIIgPtOPBhUFqgAAqWloPDu53YAAgC6RwBZiwSAEDE5P5z22i9mcpvieYoFOC4cC6+PEyYpl+Md/9mWUfD7jBQD9rf9yfuy7f/L963/9Z//d/vRv5b92/47fyvvIu9sNQRBEQ+KAjbbTKNw5iqij8azcm7SAlEwdHjFuk8MRp7PnEstm9EMUibi24QAUx08H4XggAyE7GwonRsr+kK1JKaRROlRrZThU9ASFW5uG49DX4f3tXtf3bD+4nd6I9zbSW6obD12HzViAFYdXE0tFnAskoZfJp4bcNNkrd77Xbj0AgypXaW541IRgeVGefH6M6kj2mJTp6zA+hs2GseyqYHzYMFBUiOhQ1IFvmLUAfPGBM5s7FNvob23BEQMQeFLAJWtIh2D/3XRXa7igvfnjnxt5czUhVLsmt08JCGgvmQzZG0bEE19dc3JWnyRsPnn+CkwWwEYBNwIBFCPPXr8Wbj3yq/9wDwXwnmikLGWAziHjqZ2PK3C4Rj+/dwiCWJ456Z9Ji4iI15wF4mg5UdY5ofMUwI/th8GGifuVBk3ebf757Qn59XACf1jlauzdTQiiWv32muVdDbEXt90fz+h43aaGCqiC64DGVRAl6zQnpzEE2C1IWIUcgIIr7Y/6x7ZLwHP6FgA8EnCFjN/Z3XCBT26demCaWCv+//wn//cb7v8P/nGHH71eW5pEkO1xKBlNEjeVF8JRoo9RQHdOJ+8k4+kuLGkeAOR5hoM18Nxzw5QS5/olMlaFiBEA8MLTGIggpsC8CSTYjj7UbskIJgBQNo4GhijiYmrvPLyf71+/ju9HcPt5Ht9hp4Ji2CAhMHeELQwLKEDBZAFZIpEe4HKOepXN+yQ8hq7v2jWIOkGljEmsKrh40fe2ZGhtlxlhEhrHPR4VcLmfaiVKcGBFxH4/vQbgwLXVgdDGD5VUcjDud6b9vKDgF2a27QUAVESAf+z+S/yTHO2fT7AZNauz2wZImyqHcrxuGoAlk3LXDvGDeuvqhSGIvVfA/iQCqBMwQQAK8ioLl25vCvAuHMynw7B8Pm8XzJy/fDffgCU+P3+Wrtyvzffb8+34z/LLay0iiMNXOT6+BVyR/5lkXEbscdGXwEEHBaABgb979m+sX9niX+3//Kg5q5fek6Hv7hbWJy7/PMufZBwEqM092NoCiJbsOPPjpdoNONiUvhz8MCDe0kf7uP7Hd9VCKuJV1eXtxSkAhBAEAEFAoVxs6QwSLJ6Z/FN2d05FCyzhFH9ZcCGI76+QX8kPOxLEQl3ZdZl37MWuAgAAul3jue70Tmq3AkCGeZ46pgBubhLlUqNnfrPpubBKAwaTsObxmUxNixNoU6RqMVqKzao52dfj95faa36czAowwCh4r1aIM7w/3vz8J97UDPdHaRaRIGxPLaYhEiPAS6xuBaStdAHAstkTk6cQF8qeldkLK4qF++N+wFPkwSso3NAkcygRPRllHfp25JBymhlUWVYAKTINUwIQ6ebJixQv0JvRnUok8/SffTgR3Tj0nfwpeQYwQMQveQEEQAH8trzPOSvxBnx6llPOJ8RqwO79/N/JP17Xr97bwQbsb8hGgSQyL98HUYlJbfLK9Y9SsoAfawa7hgDALKMD4zCNQAW8Gr8XJi2HJWBdv7l27fgKDFFVB/NlzD0vAxnO/2olglgs4M6F6/VfrZcWc8Oo5KdQ9gdq8VHVOkJ//52x3i18fyIBd38fyFguv79qTrKC+s6MAGwFYCTCqcJmbkwhLr5sI28yXd6EeEvU2auySQkG8pkyggdtAMaU84yp0Nu8a+3cce/LKL0AgBD8b28QFkUyJ5FxRUUKkWRSW2a5k5YEAKWA7anHOcdtcnvIBRp3I3CG59fBUBB7WzDjNTzy1a9NXGFWbWJYZrYJcNzQtEprFgz5yKmiFlH7+/VsX96xnO4hrSLS349NjzXpxb2e8rq2xAZwtyAmpIFqoURgLVTEPADgbWx4pcRuV1XKPTeYkPXq9NqGF5Oa8S7JTVSAiu5yk9+kmBVvfJXc4mTFaXZneWvSTnUdwp4hh8TtUGoG2hy+ZqV22DvgbgGiv/OUqMIpRv9u8kf42Cf8AICGzx3glNfpp20XfHVsef4NEd7c2/Lxq9/jx9egry04NEV6yVcQVZHTJL5OtKhhuW8WoFf1les9MDUBAGiMSlFAzlEAABAXkDLfyPHoM19ZsQKCKFLkduHXHJFg7hSo3h7N5baHxg+DEXQCwE8KhPM6YfACBW756f/yz3UFBOFN9aRaAWAAABCAdNSCNWY+y/Iuo7WTYIl0cA1f+oYSgBynClMdAoBIAEQAgFzk7/+Cp3nz07/xvSd3W+vx3J85Ih7E/yASBKQoAMBC6N47R+W4dQYUACHIMNd5DgQatlUGAHMZ41aNtst4/C7bMBB/GWyj+d2cEI5b0kSVohJOtSumbY5gdUZZR6Imk2l1L60T1W3hLggGFA5KJEiJQCJq0JxpYmxQqO1Wqy0SWygg9hNuq1WOO92HFk8mkDzhxLtG4ceOWAklt9KiCyNkJNmgqKzolKwsO5HKmwJO1YQiTC9M7ysln5UGMTPB2Yab1uvk6pzxCa1+BoD5ia1A5X7pmQHMPMurzwxMMexsyIu8DtlrsQbsbMrJiHvBJCbDiRAyPZEk+ihAs9z6KwIAAFgiS2iwxUrl/WV3HuuSHDzzY89fnzvrN6z9q89Axh+cpeXzpTRBEIvyzcTnbwmIlVcLttk2XhwP3dL+vku5pXycgZ0BrACUigTI88avhrBY5FOu//E+8QVgAgAAtIGS9QYS4utTZSyjRQWW0AIuJCUABBKqsgBQwtijQucDAMjZ4YJgPbPWf/J9IVcpjTcLO64kTDE3deBZn/p0xjxrg+/OD/2qVW2d+rC0AQBigChoQVpLCEA55+h58zDQlDCGYhD2qhGpiUtVsBhsfc00OOttorLVbF1mlWbUrCAlGtRVxzJTUTXosZdpFtOJkm9WNRUoULgAJLISjAQ0QNFebw2RtDJsDQPAUJCL4rQZ67rXa0gGSWRO8dwY2KA1BRUvt1AkWICVBJmYRBIiMpSkTbgM6pYIpw6dnJVoRj8n7hbFBnmFRVFPrNkj28y5VaPJgp+0Aj/rFXL1f/vVBefrid0bPh1TQH6rPMpDZhNspk1HJn977bUKgiiVMvg+LWSFElgfCS10WMCITPSPDB/VyfuA3YhI9r/tr0KT3rK8X2T7cFuWaGz8/N8D+euVv85CgtjbkJFPECUpMOo6j9/yPzxUZSCFYhCYzMs6BFBFACgAyP3BK4nzvLu6cjjp7kYDMAIEgFIK0w+9jjbgVMmz3Ge1AVMBYNACMCEW9ACww11q5qfDI9bHKkkAkOtFMwPIUGV88R6faQVaxHCLn81eq3YQBao8ysXNn5P9kWOzbiAjjAUAAFIKJAKWgBDgnEcHtoQxWwAUGKZ6vpQ46kbavomGNTO3ibdg5Wrelt08wBtUcWmxRVFJhlpAOSgU5TDdNbGDA4ODBQcUAAgCDAoEFUDLUqZqwgh26dKwDKrgxp4RpW4bHfTpkugA4BtmwgyZSu5s1hI0G8idmKAtmFCooII11mbZWaRICokCIMK8cqzTiysDFPfEPUvcbNq+DFcnRHbeRYkGyAcB8Oscl/xXbytAxjQykuesVoCWam4A5J+U0Z3rRG7yUggiTZWb++5eL0CeeNv7k6+b7hcUAApCBs7+JrCTZRE26F+XGYhM/v2vxemdjzfAXRmTriAsZeY9L6c7FYJo9/s8OyMC+EwJD4YM8MWxBzsAAGIEAgGhTBdeDUF44mxqDAKIqEAVAEp7zH5sV4x9YQG4G+0DICEUAIKAZXQIO2+z6zoEvhfNBv/bZ7r/Wy0BBVe8b+S1oRXAO5+BVkACOyD4hYyzkgTRQ2XCD3GVPgM24apIAABAOmNVB2JvKbLWU3NpEOARgiqxiprFQkzTfFtbVOVJ/valum7yNeddE48zU0mXFkMNVYyJIQMCmiTCxDILFQWAbqDsXAezfE50aL1rlIB2WWnVsbyb3A5u1dDeNga7G0tP01ucZH3d05jTqsfX4cJ6Cdi4Lq3VVVph5fzmbc9lpAuLcFHEiqxmuTS7hy4DQlo8sYI7bH/Au7N2hRrHZuXMFdWUKlqMeORn3dWoD8J+QlCLz3w6J3bLGLnk53riAL2l4rJG9H0evRYvPSDPRylAifyoHB3/9nJdmillvXFa3aOnXcBnDrO5fP3RF9Z++GX1tl55CB+8TtcX8tpFz1gznT3vHzwmPnqA9fc/XvR6Py6N2zun55w+f+hEzwWAHpZ/jvt+vSx6XsqtPPtsfVgVMwDoY7Ui7rvK75/7GOqO7bN62eG+N64GKFLf09ERvBGO7o8fO8/33nouAlodreAil8UHC97N/T/T26F7029aogvtuVr2eMkXp9GLevkRviekAqzVYZRRLbtrOVqkH5l+o7ipMdRlx8t47/XWY+P7F7CroEB9kycO1HlH7Y36xd+Mf/MQLz6bT3NjuH778Tv6JWyf1kuW+UPCKsBmHQ9r2IMLdZzuOb8mP3n8Hr+KV87SRUvRz6LVJ/uwayLOnp8EFgVQAqjT7uPWoy/rhQfp7iQtoGFTPPHuN1/48HMqAKiWVQaGbhZ6br65iYkmwFSldRh10Ww2I+LFEBBrLRW2ATgAc3jOod6Aw4moMMMyKQNxAgOhUBhFWhI4rnTYSyIUDihKbmmzDSa2BKKSQMHSUWIlkyzOLEZWZs6N2WfvBdkhCKebhh4N14nzSZlxdaMuM5kob76wlQoPS4iml7Putmq/6aInEuA69txDXQBlU0eOuNBhSZpDwHGVWjV5bZd0m7IN4PlghMJ3Oczw0mvm2qXhqZHkdZTOasLSFlt/Zb3ssd4HBL6EP5/mqQ/S6ksbREaLiw7jPPlWR8VtyFZrCzNi3OV+DVm+ZTZifuekaD3lOhhZyQw2vlp14Sy3k9T0un/0Xrd9l5XfIjHSeAqYXzivqlW6xIpnDn7O6TfySzpddL5y+ByHBmH58c7fpvmEb5BZ9cJ0ctCHfbz3u8vdu5Tbd9798eU/8v+nFxTZ3Oy6F782C8dufJCHNY8k7P2U31lirzLudv/rgf1nZ0TjUT/ZyC1hB0YajAy1/XwA259sx5PJ13DluHvsvBJFvbs2xXxnTRmZsCG7vtlUpe1lOGWOA+p4m+stg7s+ht1rk6W+d++lsfVrBY5dyyyN7+j+7h/5eiCgbleF6RXLcyMwDGVvXTLStX2f14et00OZRhV1rXt06rie/ZOfP0s2LHZ2wWSwpeMqunZKYYFAbNINAGzeJqceeHSuWqdThqKBSccZMzQQEBZT029MFvYCnBGsRJXzEksKIlFCgZCU0QA0bdlOAdM7WKkgEAyU4I0wqFJ6OZmuGLMPfdZHLUyOaZdIcDddm3RTG0n7yvsT8+tTNvu19lS1EY+IRoeV9kQrpUsAkbu5I/uqSFtCdFCuaWO5Uj2AkxewdZzflLacJQDaVi9GaIlJqIVTmAOzbkOx6bZAOIVEX+tP52ANwHj27Ti/6zZEAkb2fwWi6r16LezIbB+5czpbTLinn1jBlpfidxWc8PO1FWosGxmYY8uvFeihVFwyPTL41MjMgeHNns8tDFAqLtv06OAjJVQyNVh/2oEVJExnP05zW+h0eJyMnEbguz+yLkbEdQ1Pb7MvM8jkdRPfOoGeLxdggJj4bW2J+GjjcQJraGbca3cZFQ8JTvhlqgIGADRGe1TYeppBD9Pax8nm4wGQuRCFgUMUpgQzF8JGy9RYG08jWEGpvkV+c/tXocx6ZOO0/odfupuvPMrv1bM4mjtP1McAbazeHGez7oevDBegQlRebmlrl0wO1B9bWEOF0Yw71defjQDoharZeBkFXVl2Jq/IsgAoyW4wYFiwc2MdpjhKHtYx1SYHEAwTJfKKg3GageRkTa69sUcgJcTURo8jKMECpYUxCFOJMV4VbwHO/XzsJhoIEi4pOpIQizLYwfcR/9M9elvWSdQJtbOj4zTY9qnVe+8LQtf7o2inVjBzHtw/k25MMe0gzcrSjSmU1ZEsmjFpt1tDFdEsJycXZRgMrkViKeslrU07bgEIAAAS0kEbkA/xMJRFj2aoRbFpEAAARLgSKgqUrLulkQCAUYFTMeg2AYxVdQIf/B2EkXbBjjTS2zESAKxqJNIKA1tsBBkAAFiFcNEKA1tKghQAACBUDVcFShmlFhiMKjgFynw0IgDierLrVAFvRyeAXbWKJnGbADJSCVUCm9+0i1agwd0DGFWJaK8VlnbcRqiCdJsabaVdAdymsQgg3Ge4oG1+V0knMNKI9lNZ016xsNwOAACwxZvfxGMwCUz19VAJbbwGACBChXBBhGdLu0sjOJX72b/jTW0KfBz0eLMf/+qHl5OVN7vObhRly/PNmSkDxS89Cnj929eKxclhBjA8t88pCAntCWueej43R2IqxVKtPSDhxIwoXBhlbKUYqObl3NNx6koNmGgoOAaBDYT0mN8PbvHN9Hg61fDiupblBLOMzm7Qj7VcL408v1FlqkOoUfmDhJlyuYdNLM9KnmAvYwcw4QherBWyKixwJdnn9vpSMIXZcSX5vNzdTqyFAR8xvoW2C9fkiai0AbQzroxsBRgdCWCAbxCJAUZHYoDRkQAGGB0BAAApBHYaiQF2HokBdh6BAQAAsIrZYnyvt7w+aW/fkYlxztvNHD6gk1eH8zNux8MLSgBjIjDAv1MhCQwsUVyrHZcjAmV5t+EUqUVpa28tZgAisIEYDeHGFGdGtJuaIFcAkLbHplICwsdYkWFP5rl5Vq9aSfQWHdHerXTGIIy1zkFnWwFYYUkgSR4Hnet5vXs/0HFn3ZyeV6JTuhCMOgt45Cfb47OUpkePeoCmBG+FzrTmJzqXNvT05GVXYEYXWYfT2YmJYyWoNLvH72KdEQzhWol0a79p8MRJMBFgD6CwOent9IHhbjgFYGfy26Gfihjjv66xVjGA/k8LMH1rhk7ABs7NuN3KLlgC+HrNiACLZZCi9U0DF4C6xLmmUcjG272CAgxm45kyuhg3B2Rgar4W64SjYaYVB/FeIUjXkrbEj7nP3DSHZOmiSxOxHNkYhHltCmjVBuQglsxxbU86tKGWZoxwzW5b5yJ9onJYCUoEKm2Il/psa4VGbnns9Bwm2Wl7rkVvHoX0QhtEihk1B4xy5VpJZ9ptPWGlFGP5ccdJzMxOtSHr5Z75K+WQdHQjAloeAoGper8V6xHI7+HuigD+a2OsIHXQmNwWkS7DYng3t2IJYEyMiLJDKoGBwAgeiteAmYEyHnWVxUcWEQLVtdajuWpZurl2CjZCGQxPxFSb8bQlr8tgdFk06FgZs901ekzhmZdoq7eHt2DtQX/DpTFZFFFczCunGjEeBtUdWExarPdoOUlXobWqus5jrTFDqO06yqw5y5xiyUHs27SYv6F8O67Jo3OUqH1uZ0i3eJKnOTcw8XUl26F2pnVZZ9DQhd60oztYAn0RXnZczSALZ26N3JyZtFMuhm21CgMAgICfDi8CRooE/quLEGHQpIAAMCZGAhe3f11CBc55xdefHKoqZYSk6viuq+hCX521dz31zU321du2z7y3DoZVhOXgrX6DqeJrzt9xFrY2oNgeylKX9j++1WXIvVjyqqSe926vpIP74CZNPNpzc/t+n7c+SNjy8HOlbV986jNuXfdZ7iyk70b6kj1q0b4Vx5Y1vZSy/UoDeMQhCZCdttoeKt24uvfcxCroPHNb2vCcKali3s0rXlKjVpcuqJod0jV+CRFHXgaYToog7thsNUhffVZwUzx8nEczGVs3vBsExkZg/kMgMf9iX1UVC9FWHnjCr/kLr1/BGxqBgeTr/9Uv/51/7ttsg8mqMmyxtVqycJyht5XMDDZcZY+nix8EmQMzqedZrzqF1UcnAm6GCMNavHNdonW7n+XWVcpsgHSzuJkubf40oC2PidR7//Heh2P/zP9x/qP1NscDkStI9zEXva/5UyDOW0FzwgReaT1rVZ1mzk1Q1g8juAjkvgbp60jPRWlIWW4OxQ727XLoy33xSoWnaYzGNaKzq+5wtR8DIW9d0aNid5mrdgL0S9P1WZZLBehCLzdPe9118fY8R6DUdR/GNhjuCMn8jk6Q/wGMtCOjnW5aagr8G9nB0OtuhfIU3XkKV07ndgEEwN9f/8E/7x9SmTHMwABjjw2iYMPWA/bowfCa85lzrQ8GATBHNOolDkadcMgd1vsCJweLl9Xz/advmJu02bjGwK0J5meXZe/OwSWALZHQ2VMpT377+4Qfs0NoL/NHTWigZEXkJQt1qUfGMSjQrWRsujETy7gJyO4843GnKfe5PJAZGdySWZZuR3Hq8S4vr2tXMSBK1RlMz3E467rdNskKxfUHKSGRrF189cij2uqaFROW0R9efv7k894zJjXYIZJHfoOx4Y6mQ3FzPektgcAK/NsZtAtuRtN5DtPqj1vupoh/H4OgjyUGLTyR2K0zh8sPb/qVqiowiwGApkA0LtRsWwsM6XO2n4ODa5jyBe2tNmNqMwx81a+7+9h+EZObfrN4aOCu4vruFflefu90T6u2lWPFiN23FfZzICsCsOHKxspavmStnDgZto6NPceslkAMc0CVkDZVuEWciEq0vJ3MLpfwobwaToYhrFxL85+UGABAY+kMizvvTycujvc86Z2Tu/QdjTkh3sz5RxojpKvlGz2Bdj2VSdb8yDvYFRtAXMPyOpcIkYvT48QvmAZW8POYSJ+NB0/Yry2K2y9t/0WcE+5ngf23c4pdny9Nvd+8UT/ykZp/DlemfFjaRPzbAIAYy6GsINCoEdTra1pjWQRLwK5YrsheADN5JRZwq28/Yd7i48GbgUVyBueKYIKe5qUx0sosWNPNXHxpgc3SnB2Nau9lWRoybw9yCeNqFUJN+YqiqXax1En/u5tHqWLBIU3UoGAQjFiVCmSeAiCv5GkrkNn1U68DrxGGBXlBji74DkkhHHDWDdi+h0/NONfdumZtTt91I0SKsNrrCSnRiT11m5yPB23jzGH1LTdMVUHZ1Dl+7MPX8sdTyitIKRAav8Hu6MvY63F8jr8EsdiPH+4fm30fhlYxAIAEMAAAIDFjIDE7YADkWBjEDggAMxYGCQAABgkAgMjIELD44+m9B2i/jc2cx83+uYkFfgNAAJgxEJivhgAwYyEAUgCxA2Y0SBMBAIKDYoaWZlrebBOAsRMY6fTpq8PTxuv1Fbjdf/s5P2wlHm4YvhkCex2+8/nezK6gHv9WG+CZU1/K2IlyzfWm33DZs+uJ47ZwLXI3ULa6S/k894Swh95cPAAFdHXYCMytnFNbnh8aKzhtHHWcsWxT4hQJvubEhUnJ7PHx9FRevn0ZajZg1bRKle5KZuiSdGE1ynPPTDV4sH0kMx+mWlUh2WpeOi6hpEXIVBNkPYqi1S8h1triUhfl0Zyt892bfuWRQltFelwMhHeNsYFExcgd2Nm6kVRoGkyG6V68fP4zBbQc3oh3KoWAmw49TY5ECsYC2VWvKQAIJA6EhEbLWUxzSxh0iukBgewWpTVEZg5YcnDB27GCsoMW5HZGllAQ6kl0YgQCyC5ogwQApIY0RBK3OfREY3wk0VtoDj8BEiPxWpUCMk0DxGmSleJI+YZVTPWIBIDhDXdTADAYG4gVNCrwk+yCtrZIjyECAACMiGKSXVRCBaleSxoUMdIsLCrQNnUgEhQTX8SLxYYKwoXACAAGUwcmTJmZEIkBAAAEAABSGTzrFAzDZYwIECjBDJ1VOebktsPV8mZ8poxjmm0g2sTMIevKr6hdQ84L5GgUpWscsIhr2CcegcgGF3ghJXCBKLawMAZjmCA0MMSRi9xS81GPZySr4npJUynlIqKFpT3X4nD2+dzfc/GLNwyty2efXZZxRY3OUv3JMCtPRUKwzs7XW3GBMHTys2eVu7mtpshbJxBww2pe1g7EPqeTUf1yAmGtLDJmc7IMJa41MVxyUFFByVrtBABojPS2vRzACbiDD+LFJ+r+Mv/sgpy/fW87x32vL3AEJfUR2Vehh4TpLsty/bALCxBMfZQU2+IWoZrRjqYJ2ICQMKt9mN+i63UMhwAcVL332vR8WkJvtXMV1yw1tn09gy3sV7+XcEfTJBwDAJSajx2giAoALSPQ8QdTWMJ00ns6hdbjDI5gp/o2YJrP+3AKY5iftT7z3njs9fDz4dKUa4h0G3WHBQwAaLX9qc86PAcic8iGCTiFgApl+j11o2ssW3RsnAAAgIaEpuajCxBYPy6gByFhb/aDbU+jlc7XDpawAwWOYQ4VVjCSEMi3WD/N6yZ6v0Sxa0ViAAASAADQJkgb5GZIA2MwFDAl2naKN7Mg3T7nZxP7goDGMQMgAKhaAdPEEUyfJwBQ40AyMyM8i8hUZKCQ0d028P1AVkw15X5pfjNmREKEcAE5z7i6q4SOntkObx2chAo4g4XFROdd7jnmxxPBPRwzM+eA0mtVdbVz0n3N+HryPEKgguxCd86d/PQ+7oL2UuJ0t2arsdh6EYEYV3inJMqM1xh+NQNiXb0pKy0F9bzcp+u7G2B6EtC9LgEWtQkAYgNtL/sXPY4OYs9XFSOoFBjE3/N3379Zyx2rWSwbxjeN+Z11OJbzxch72s3v19292A/gdU5ujOGSLMezm1HT5O2v2mpVd3HqbZtbyraveYuftZiLGUq/t2/rxm+0sPfZ0a5nlXuVfSYfWtGZuPHbw3dkNH24/dEbXS64+pPDx5bF9B3fd0d5AvqlbfI9PnpqHLjkOq5dov8EUfP/jkooEJFtv7/z27/yijk/mzfk4mq91+2bCxmW1iuf+PBWKnD1cmNfplujnuefXCbSmi7JcfX1RGTbqWYuPuAn7cply9Hsw0f9Z29Vp93CjmyYNsvb9FjdO0nzHP2X3HeS/hWUAy83L8hPD6vVIKgQ0tFoLfddkP81/e7Ai3fHl+3GpbCaLi+e477fxen8ebJx5Bf53fN09Qs/0KXrF/nLNvJgv9ez444tOlKhGGh+rdc8q7fe+/raKdMweN6xSgCjGkgApLFLR8AyxrQIAEST8dg6OZqRbW4rKhk2AybGMC7n2syBWmaDEMdTBpKuOF9GWgo/t5JIqNKTIO2xmfS4HxB8NVUvM5InVihMtbQci/mfPP+T0hLu3QiJrKigBAFIYk7OrWnhenZNNHHGbHvbeYqE6A47GMBcHDgMv0aYEFz2STOHyb2djo7MkTEkLShGcckEwRoyrsArfjsvx/IhbrpnuWANTVOaFxkeazeneLyiEyVQ7YwAAJIlh9viW7o8QTs2Aex4G9tr+cFhvzshPmvAt37G5z9Lrc/pdygAlORK/ctvORwBAOupMFz7PpdJZgsAQFzsaZG7l/dqqGDHhJx98Cwaglh9VTmdda8QxMIr5WyGrq8AAMpr4ve38rtOgEyUCmcLNT6G893ccu/KlUMQTXH550oeTlN/nDyQhAeOdX7XngoSyvuze7epAQDQVQP3mnzI0/IpUQEAkDshd0PPIvx/cVPO7l/HFRMAABGxbFIm8ljRejx5qbaWHCdX7ds+xVFlpImTj9c7P11Z8Hjw+3gCHBh8eri3cj/cAGQADARATcISDRBtskBAKd36DqzN4S10SZUEtm1KZzMHzeecxxw9C8mbhhO/vf8VQ9bzel2OGJz6amsC3CA2VTFUEBm8SaqiYMADW6v30oknrd2VPQyrvrX3+VhPUN1X84qMjiQcm5095/v9GVbt8aP/1v5M79va0hTuNMOkS5/BhvR6WbW1J3R3YihhQ3tK2ymp2sslpG7utCJhtCbhmOB6Ov/+/WN7XPWwZIoElLCp6XZg8p7rAsKC6USANAUAFDKgWccTBTa+0K4x2kWEhR3Ob89PCg1dQQAlgMuAwpAz+o/kI/h91RbfJtYqH5JHkNOJBSrXLH8sJ+mtACW1ZkptASyYOek7C4onZCdpAogiVbaTrkr0iXtX/8r30NsAX3PzcWLCFPDIr7xl29dIDQAlCkw+1ImRscSAZ0WmHRDh+OCel7fxKsAaVeg8JVBShkrKw9mpYHCktjR8BVWTcjNgb4RbwN1Yf8qZSYBle+4ff5/knihUCkVOww8Y4ovpyEl2A2yyxsYTnlaINEbsNblwtgITIzzc4toZ5YUsnnXkwarw+IndabkK8HYkLOJluP8fgGB4XS2ANBUArCKWWGAJbwEvhhWkQx7PAYCy0wBkWk8UtjYgMADDIj02FsNYFOveHIa1IFAizLHMkKypUloSkFTFFmdZScU2j5RsCNgVjUFVv8Kts3NaaT9dbtlf3byr9/F3Z0OtqlarBx0hLpOvvevfslivBX5HdhSI5B3tscQZxi+zEGebImMYswI2Azl15fq7b79/5nt6F+2ycpYmEjjcJjV2lYrYLZ5gjLZsQ77+YAKA7GzNx/Xz9N5XeBAXuPWm/+FimXfcmuMNh5398wlBQFkoIgT+WvqX+Uf42fv+N9AGi3g+PHjDdqgjlLM2OjlvGdAg5UEubv0+6mpA+aRs7ZoC7oYMiyYIoivkJiOVqEhKf0OBJabvtvxOfnFiwG7shZfJ0BpWUGzA9K10mC0x74oBz1Icgljz9eXpT6fSaLlWATsAIETTdGnw/kcM2DrkF/LT4pNgtNz3GmxvQrhl8LMhxzJuPAWyd0uu5EEeZGPF8yUuYNepcvba7vmB/JKBnI5+VsMNOFLSK2sFRpy32l/GJ85bH9vUX23xu4AFLrDd14NN5uSrjGEvtwcABjDzsKEgJYYRgSJYYAAAito8PJFs3iqKCt4YAA7U0bbrMCEBYnB6i+3YzxOXRGA65HkUUFv9WrGezE56EqpZtWKMtMRi4aI+AXTdaq0w40apCBuS2DIZprfOEtXIjviH9mqbbbdyU2MUWoTLm8ulkgh2GC/tKwSeIRGWnyGdZHWb60GsB90XaVGSouIhQgcQbHa//ZmHP/d583y6WAwKRgJjFSUVu53Xi8Ur0K5CRoDUWQGAEoXVKdebVcPuR32szL+PBJ4yD5e7Z99rkQLsKDDOWfD7MAcFRhTQhJd7gkhNArp47ToNN+BoU26efA7ktlgDHiHjWfNXOC/e3iu9IoBLEpPuperMiH0a2cg6CdGGo8XRcrJRP6Bc4wO16P58YIW+mfk4fuew086a2JyS9DVHlAmiQDM31ZID1Ld8DuY4AUFYr54ZJMS5lsyWrJZzBfDp+btjEtrqT6+bW9fp778fX3064/bf3tidy+6Xu58DeZmWBaMBZ0ueZPL1NHEB62Ymo/vvI5m6VChvyqFTBbY6fxkfXflxU1I4WUMCUxRHPBe1CLSorhg+tPbxmNvE+/R4zZo4lo0zMwJQLRC9eTOMjiqKWWptQNiYYGzPAG4eASoAQKyuXfvymy50ALgmKm/CvFsWNGkRKVpLG/U9mwKLTlqA1CrU6L1cmC56YrOCIILR+7mIm+vV8uyu0TTqeHGxbUprLN+Hm48rHERjev38N8+PGhzEwwg8mQe3oRR30IZ57LOc82oMUxI7V6cZhsIMHtj9BX886quVL2ttKgOLarc8mj2urG67NXSMS/ZATmQrAAAwmOx4TZNb2/drwLxjLo6n7rZsG7crc6YHRnEE/ooDDyAQsACyNHLt/geCgBYP7iMT2HMaubt3HctdQSv0cVsP7vps9DfjpO45KNZsvBrioKYD4suQo4LdQBz4nzhsCQkYE1ZC16glka+UQEz+/MUvPRxKAG3ig8NVGJkIAIAh3X8hngAAiAuY2/8Un09olTfu49/9er76dSVjuZLnK9+nF/bjtn3Q2QLdjceevT//dyvPC9okBI0l+1Oern+f/ek5bTSDeo0MSiSgYObjRn6fehmw81o2Hibk99RXEMAnEgabavDDc0pY15y3ptUKOgSU1cIAbJ686lXGT856A3cagKqwTTyf3N9wgbP1DAMx2ECNJuZcd8Og6CY9GBE8G5GO5u6uu53U6F6eRloyLIS9mTZwiutpiW1yrKRJE1XP/P5Mt9NgasUaCyZTZJF35JHckcFMheOdRLi5u+3no8/fq1ed4dDdNWC9KZEx5LFbTn6/OXtinjOlZRJY66pxUOxisT/i42f8ibmf+PZXGpIJDTactUGVtx+HYIZqNhyBAlSt8EwMfKr9ZfufTeIcssWrQ/V8GG3icmlgr/bwKCqODgBACxgJgAAA2Eam/Q3IbMrpQ8+RXJY2wT31qteO3JdNQm9B0jV7Y20khD8sfDyzdmV45ASExMzdHTHdKdMZPd3B0/3p/v2tu5nLmdcASg4YryprIoCR8CKXZ69C+CSwWQkVBAAAmiWnAqSefPtsTpv2uOkOmu7k05aXrAGexi//jK/6DOV1eJbmPq2RWfr1f3dyf/oUiCqTpyv3V/4MZTR9Vs0WSJlGLm9bA3ntKDh3UnadKmAUI3urG/lWpt9v3Fc+ts0VWKqSVuTgZSawm9sDeJ9qAAJgK0q9tU2BmHFEZBPXpuXQqnni0ah242FEg/maNNXyCjs5NUEIxgFkrEENHcNF5uzLJZYsZqSTMarYplrjnp2dRGpwGz2xWA2BKTOKFdJlE0/g9jxV3O1oZJ4l21N2K9ISB4Wb153KeemIMJ9wPuGCmL6R+55O41S88Cwcg6XKSIsBwvNoduUWNzKoYSjmK61fzGHvz+vj/87UtwFSKApBWffQMx0vXulm8Apr+okuBmDwVIFv8XBb/EPkMMNjeX3WsqmOUy2nfXSBAhIwEqBYrRQAcAQgAcAERgA2yH7FgF6GnHUZzpy1EJDdIg/yuH0CINYc8GzKkxuCKJPyLJPvB0BGU25l+PSzc+BkRw71x4NEqQaBUkM8fd30QxDZIVvJXy2C8OXnamECFQCMgPkzz0GoAfWt16+vMpSnbZOzpy39DVPBZsUhZ28/G94JyNkhvR27AOzeLXl9eh8+tPt3rJOf//vsaUDjuPNzJJcbTo0XpJ+UXacKYDCASaJRYfWlE0gLoFH1ufHeOY+HvcZo0+YOxoTVBcFwAGAGEZASzFds+nJFFIe1xud99qeFzcvcKQs09fX723wznMSJieEkCjbnPFiMFZqMCaGIskVbrWy8wlaCrJLezG1i0eSWwa4xTeCVRiQClhO/0gpWq9bdR61532QYKfOKwTDpeWi1kaGmmn+23anLaotJR4a3w0wZ6SZ97dqH8xx4vOMxe82VQ0hO8YB7jwCAQ94/exrzddWvf/z9l6/fiKU4RhOCoRdMNoShVDq7p/Zw1yMW5CUzsrqUv+aLkUCUuKbcY4NGGx9Mr4rnWQgogEolQaUAEAAoCwCClhEpIIPZ0zHagiCVjWiBvz46i/Ih05nnz3ZBQ+OCvsrd8SsJYlcaub5jDWR8ZhLAQ1VLqAE/8WU4S3QgAT+pfRx9OI7LEwRy3jUn1wPu+QjEIPnifrn2cR0GBYBg7XxN7ndMBQi0VLZ0F7S1yPs/f1+7J8AQVS19DTDFKAvvZdUUAEHCBMOisEX6SQOgu2rKBlonb1tHcudUAQWSCQAjrYWdlz0roSDwkQCFNHK0wQwQlw1IUcelKiyI0KCBPWuqgOHlOAzn9bm5FLvhPl+/M2D45GnxRYgGG8vHYWFmA71gXGxIWxaLgkWCNpNGzeny/Mzozdq908ZZ2BDfkqahl4lMGnPY0+zqdW09J9wqW2T23Yw+0zLNSoKrQYBjMP3emtW3OhS3LnSIKye+iZMyJZ/hPhw50+lKwGyagsRkS3GtQWztkPO9Hpn3deVvvt5/+f8Sz8LrQAxZaqJosXjDo3t6K6PkS71oFwCmeHzwkY9f8hvnP/9AfvmO3WuoQQM2RRSQBSqm6ITiuxboQZ8EgBIVKNEDgJeM0Htkkbq8vRvaW/Ws8/xhlZoBBtpj9X/xV/f0w5xH7fRoVt2+OL6zhp1n4r6TeCNMrt/8eX6iFrfEH/xqyNp7djOJzOu/fPe2fTkXUwP45Dqd3hHXfj9cqbkeuTsAUD6xaSor9OLT+PgeTk/bfnTz3b4v/Sr92G7cXs+yfhrvsXQQBQCK1IEHyT5bzvm0XnoUd2cYA0ArJw/5xi/jPNRT2s2b4+/N0o4NwBY2v4uHfuxX3xg//NP8SBOItdCEBiIqn/Dovno1NE/pacf7o9KaAD7ZEMfXb6/4e78Ly4/16sU6VySlFGOA0sb8+fR3ZX8t7wEGyOc0UznP7QUYk9AogCLBedpMiIgot6IsS7bkbgpYXQgjlrRMLKY1rjDrr3P3zb974D0xekwfMblAKhWy0NEffSEQWRVCRQYuOnCENE4x8ekw52rPyJPDeg8s/zP7nygF2GTm06XMnKsuKVgSwVllm0kesjMDreob4GQ6qXShO+qyeQqJ2GUQnPrgZCI/2p8yT/JbVzsR6KRFhnQW88i+1zHnRbmH+/c2eb36Fz1P/08aghQ18pUjd08RFr5Mxb6M5/gmT+MBCMEzZDvXH355fMvoYlMFMNISbbvlF5fzggj2J6H1nhV+5PT1xwWavB73/ciEP13es8w/NJLDxAs+vrgsz+JVp/oVHdltynG1+oZjVLyXc8ZSUUt75h3DCLaz7sPgE7vowaKjZWrqVDvWNtEGQ+x5QsyqVW8TiPQMMsq+cuy82j/Sjlht/zjMYVTzcVraFQkAIovR1ByyVuMBDV8sNWW297FrsTrajkbiZt/T1AfXbS9ctv/AiCXTDiJ9tp66vebm6GjLIpo93Ds20FV9bJ2g9bQL/YX7SW2NwcafWzQcnX7DDucVIIEgxJjQslnXtXPNDNl8Wu0/z47SOFaaOm8fHYXxjNu6n3bvnmX7D4xk+nsRCJoCG8d9eMxXAnWRr473zH0eD8yOBahERylhEKlyFRTAxGZNbbs8+s/tgwsZjXIY6aRIczrzAjz667ZDKJc2CzP2e+9Nebk0VMh+vGO42BhtAgQRCCOBarKiuZzlLL3igChPFKArpSWhBaRHaUTkUbpicY02crsm9jQv+C/n/sdNDmcr3JR2iB3LwTEapqbagtIA4Bg1wZtdXZvBp7m50tvJGjfXvSo79U0izqOf7yZh9mK/1TyuuBO2gxompVaaNB6BYZwnsfqjddbKPBLJIjBsL8YmL374hUpBAAAAyMQ9E/vwSswgoUy+0LaRfU3I1EeJ7QBvHrZQISouGRJdc7wQPWR0jrJ562eUHXNwji1fgQGa6g/ClewzVIhRsufrDgyZyzZCDQgFvV/HwMRvWwHAYKgS76k/noM1JIxnPhZ+Zn5VCQAAMErkawx9SiiTL9WzTmXrpDtkZO4z89Jrxvfte8NFGCAqLkckItKH2lrGpbGDAdqaD0LV7FMxsRGRLccd6CAyl2bCsB2cG7fG4OcAAQAAIKFUXgZj0xONh0aXNVQYzbhtNY4s2oWeL7swQFR8O0KSGTnE99vNw5ntQgO8r4BGG8zOpASkhEmLcoSUAHAchX21dzOWBHHMjF4QcSpPsw6Ipbv1mcu9n02sWS6AOChVcMlUvYMKABkrqk0ke1iKP0IpCMQcSjq3nM0zp6BsU5IliWAkFGnrNXuHtWKj90n7qFnKp5Vt6a3X6IaemQ9YFhdBg1RNlom1FEU6tTnNZi9X49V+qojf/eqqq+rmejfNjveB2Sv3GcputS5rlln3j/WT//SOl0OrWMejTj0LYBO3j2/3aVjOD6/f8Tn8YFq7MfEAjFNoIwUFAADwWuhmzbWTIMjwknjLKVcBr6EtUP2OqujU2zU25pxyS8Bv+A4BwCpGalqhb4tNnQIAADhVS3pJkIEUGSoAboZBAACQ4UKoKuDa0o5BYFQj7Ui7qsHbBTB2hy38xGuKDIiq90OrqBNvBwAApxIuqMBPi6luAACgRLjTKeq02MJPASWcmsCoAfo7CMCpRAoiPVva0QhgnBqqqBNvxwq8XZXbX+ofVsYUaFT+1C+aen1keAtgp5BSmiiSNBGtCClkA257qwV/IGqbclHO0GGMJIODE7if6XqBUIBwNNvOAAIhOICkC9V7DGOUT46NrKxbdWStdhYIVazJLYISEGUOFhZGVoxUWmGjtvSWAR8Zd5Vd48fMpmEXyya2e1LviUMUQaARCigsDANvwVWnGW4UjxyqdrAxtz9Dfcmm6fOiJdpDct8WVzU3i5e8umykFPZ73giq6cJFLeK25we//uxmvlF3KyKXY4TFJvjtCHcPABDQWNoFAATgJQAAILQtbQKjIzHA14sEMMDXKAAI+A1gTAQGGB2JAb46EgOMaawqkZvpZr3VXXNws+YgCm3HMkAkdTSNQKSTRy5HhONg8JUv76mQVUAgFDlfv+i4SISSXkhE6dJXeZ5iIbiqhHbyAkyVShkuXoYBBhCPiVGswNeaznQRe6yGlmYvWOKqbJS8B4TSjLn15vSg6lSjV9s/IwbwSTsqHc4yoW/pOkEXa4FpUJUKCKsARWNQYlZkbAyn8rTqlPIOcfDNsj+dvtdDGMwpWos742D6DVee7zl09opBCzxz6+GeYbgbPjyWT5K4uzInNmFk/Q7/tXUioNUufb64rM+64QLMp10fHllVIQYAIAK0/sX7LlYUhFRN6aYhj1AAwKzBeyzerZev+MqDE8df9/Vm/7RkCfXvtY0WvXe9tp6yuN2cN5yy1+/hvWvkkpU033v/2ju++QJU/vCNTvzIU0w2XTZPSLn1e5WSJgscc+5xK8YZhEA68FTpin1NX7d0h9MdN7JIndWOkqflspM2REyxhQKBFbOgiklDs6mWsaF5P58i7wbJptqMktjmYDN78tb6MFnkrGRlWIFlefTdY9LNGpkxPVeTRMTbM02ncxj227SgFivIP/fXfe9T2QAA2KgQsAEEEGNhAMS/DgYJABjAROAEkIIBGKGkGABAYEbRiBxFGZE7g9nBBOAokBgTAoCYHZAAAIAApFgBs8ee8w1XxbPjjwBiAAD4yj/5z89/H1lWSBSE1KqVV4tyiQBAYbt86ONR8tGcwngd7jNxEcScBCr2WFnmwxKxVPcMTxPgPY2Io9/VOzfAO8ODbeWPrrUkJ69VgWjMFbHoAFJToyRRgiOiRiqZwMyIwXD3oOF6BL1uzwooo8s5k3gJewEBHwQGwATpZEKoLLFqAaRzXHOea/ZwRuqgMuYh3bbrc5A5WeEcQvUMw4PbP/jFb/b1E+c91TVknnhHNzi30JwdcIEy07dCR6Bc/gv4xAAAANyhIABAQo71Lw8CIAhAQkIDAQMkMCYIAUACAADCAMPOACAAAmODIABA7gAJ7DQkJLAj8ZlfTcYkgIBJtVJFa6oKKZlsdng+tBZX1QStrs93ElkVisTGHBIJQ0Q/rvcWU6JCnT1UxtP7P3xxPJ+GBogar12eZlrJkqQOoGbJVgoKSlqcN0aVZJypEXddIrENMJ8mGMWqy/Xa7eFo1Zic5/5U02m2UACBIhK2UW0IAoUTKV99ZrMYn8ey8T3HeQaDXENfbZYHrQv8qMisIRmAZcRd1R43zL0WnMTss9mtOm6Mm2T7Asu2zO5pg7j83fnP/LGqVmQqXv+1f6wMAGYsAwCCIRgLoWFQAAAMAKj/H6diI2AxmcDQAEIAYhlGwQDAMZPBE0T+P/e7+rO+DyZsCSBk87sScayY/Z2Pv/VpQQJLxBaMeRhsFFoQq61vm62aFAg5i8AULEFNLDn6AgWVA8vTTx8WCBGXywUIFnedGD8soiKdalZqSfNuHVJFQ+Yzm/GXW/VsRmE1HUiR8KRAMzkySyrV6Ewn3bDbe5U5PSBEEx9+OITeirwPtmVhSVPhwVM1JwQDoYVloG53vPeg3xiY4J5BmwBtLTcHoQWLtWi4MYVn4g6geoQXQ9gW4ra5cq+SG9K3915vnJcdvtUqRgnXNFssikB7AdhqnD1ev5JWZN+YFYNrbHDKaRQFRfDoDdXVv5C/VBG4I6y3f8k/0GBwlga/f449RjsEBgBAAID9/xAhAP+0P+P1n/YX/HbHTJuZ5OT6r76/aX+1PmQgoEBr9G7/37czfKGxi1/6yEfC5zKThYpZGqzKbMxGCgQIDFMxltMZMGeSAwD+XgOAm5VkV5FdBYbc5wNv82+9jBrDuM09tCjWWB0H33DSTpHDab9H/+ZhsTTayHy4py+nFenCstvF43lilHvUFOXS92orm2gr/GiZqJtPydY/+bPqey5vTiexla72ZwMpjTiCQ3e3XWXk3N79bH7VG4LO9qlupU9O17k4+kbESRPyzMyC0fBGTcEkNB/KAvGSWWRJRA62P0I65dBJp032T+Vj2uu3wGfRLhJiEl58bznqNF2vWHmfDpbgav7MnrWwfa00kL4YgPEPUKzYAzjeoSj75MxWBmYaoLJnM9K61ubiAsANcEEwCENYplKSbOW5OZaU+RnGJga0BhiEZqA1v9n9Tj/5vPBoW8DA5qyv6//3zuEAmE63M3AEAgNoNmcIAMRaZaitEiYImntgoWRQbtPszNG5TgsAYGu3SgqUVK4QGAFHRIYwDOOcCfcqGItlSKdEByAHAaAlvQdU8Qw0rWTEkF5a9WoaaaSCpL63fQWtWScqh4tCgUjmBm9eMMJRBk4sVBRWOHJXD5zTQCqhLWIoXCFl2DoUB9VMvLWseI7jB12NlWDMCFDnwuUXNjsORLChihWHKTOy93nHtl/fu+y4EZOesvJNU8jQPNnG9MacuSL48C5XlM/qHgFmlzOR4aZOQF3OunNiDwCqk64TCxAeA0SXbAtAJ7bUmTeBFgsh8CwaXi6HGwsGEBDY2tqXzA2jLGt+5jmb2rphJNLRJDbrtAcPNRYAZw2ONosPBIndnZwE3qd6lwOwBJaY6k3B1mU0AgYFMcU5J4uR04bBc0bBPcWVzJUBjiGpRCUiDACz8t21W0SQJaSMuL+nDg6A3rhsI0bRFT/QmSW9UWt1rfM+0qFCYmmy16or9JOZQydMG5gpdYGaXiSzK2iBzUEeUyGxC+eeC5gYFZ6qvL5feedUKOlPtnFPt8wI4FZ3yhF4MQAEM3yPTHjmyZqf0JxrVDTSUTY3Vdm9tsIoIzBJEqYb+ngWzUKeVys2yp3I9NjIfHV5Q2UpeuIWtSpkTR9DuGI5ux6Pd2aCxTgUrEWBo2EbgJx4GIPNoRlnxiixAMqaPUtbtP2/9hfiFGDwm8w5vVky1WxymZ/ACCC2whQXJV9WAYAgBsXgZ0fBK1sXjNiqhdeYDDGCnJgBjAJAQe2ehhBtKCJGbIOMZSjDFL33uv68i6efUUYxU5f7gVNKjS4kVmRglP2zrstrJyXuZfaLfjV3A7ONNW8VaoO8XbGNoZDJ2Jld+7oulAVcSdGWlgVJEiIzLufEsZS1LPEprttbu9tRiBfvfayoZpXojr/7M706AAQzERaXVY/e4SaItJcAwSwmrSTtdvZCd+aZGmcgYdxTo5WR6qSstY65nbvJTh9YH4RRkthkkJusHJlk0sWOOBSKBfoEHYNlAbG1bWnzOiBMW6KxFQOmq62s8UoiywmsWth4Pu26sa/8/folo40CsXoshlUAxuzXOl6PS5sSoy432zkAABKKaYYQAIBNJ2XrHgSIAWYpeB0FiIUEFmI8JmDATIeu2VgAgIsNyqanHGorpahIqx4vy2pnoMAZ1S/i3yrVFqhaFFiCKRsEAQx+w2/6Fb/pmjPRC+q9YNgv3lPa30/eazTJTezSk1vlsMRg9PDolEJ7hSF1PUajYGt3cCJZb3kZlclq7caac7nKGGOtZkGTfsDt4gwUTDI4nW3VGmMT+ye+3c2/XvxoaTdhN0zcLebxw7dcufvSuI97nInIhCRRJlu2TfGibkXvGD9pbY70HfmV84FqjZ1t3cshWCHx9JxkwvGYvBwArAIA5fnemuusO1Zb2bR5DYhI0TDuzuKMlVfraTVV2r23y3YHzG13SvPVu94/y7U4ozKCbcVAzEBQCLYf1/9vz1Z4S0K8rlnPakYqMAEa1QD5PdOhrMHC+zDqDCO2wnOVpBnQKAaeCoTIaQNAGQAAyEWYjzsPKwIUUGo8xlpyUPvja2N8PmO6RkJqQk3ZDQowHg0XHi4feN4RYSUxvWnP5a4v5nbt43k2ShvNs1CVeRNeqqC3WRjQnZ1t6kqIFTCSljT6pqwxARG23UV2pVvy9axLbC2le1K0pJvBM4UN81aEQivT5iEv9oZYnl6fdrWWbZHWU9taxp74CETMmDhJ0i14XG4f93q9gN8GrSXrRJ/3rtlDnyANpZIcT/a9c+izSgBg27YhAAQAsJi/7ZO9VlufI4iiISMqdaCfbsO0mY7XZN5m8Ur2PA5rbr5sO/bu/Et1k76UDd4EmKlcBrITqWD7wT9w6PcqhIB/aelt1EQzbBUkAGi1CABQsSX4hFjDswwEllECKws/XbMer8SlFHU5LsNKaRahrUnXajWYt/ZClydgOVKcjmWVHLIAGNjEOgdGhonZG7WMALUzSTnxQGrpeXYkVcn8z+sfUfac70/f8Nv6t5y1nLlEvI28SlJl0wpSRzdqhdC0aK+2DeG/PQk9KsqiDXqzSknda0nBJPSF0zj25I7wmkfrr4sCmEkvl5CKSpa+9CndjUkyFYlIIMYSUsYKx+35uV6fxT+zHM2s+VotZjx0XXA60WyrLSkH5wiDIluz1gI/OdvJsWSrUA9EAKhB6IFDgdLcosIRlR4DpUY6vRGrp1yhhBkKAOe70EcdBA4AgOyS0cB0FgAwq6Tz1BRxOdlLUW/iySXeGOFrDAip4Mcx8EyxswAAPZ4UCkgFq0LQRIvywQAAA6DOojUARgARQstCgjQ1GBoBIUSKbYtjV71+4snflmK9LX/wYBGEG3BgTBlCzgFle2VWd+uc6ikvrUkUyK7xK73jLLJyr20Kb3a2nv42naTh7Y0KjHFgfQbrxV4K5AgDSq+ccSLq9/RVLrm3ahqBsYG5Hp1jGSwkyTBO5kaLVkLQAZw7MRGEBQZFlNzgLQPEpBCsLD4PYNzqFI4cyeIAcdBivG5f66Nwgjqs1/X8+uo7kA5qOS2zKGE+anvJKNSaKid0+VnAggUAUqCs0Z4S9b2WcVEBScRByagShtVLUq5UscJVjmqmi++6LgzPOOXEQ1NqRbb0i37SkxzJgHCGEUCwSQICgCVJoBaDcUbGzVbwXallRoBBP6gCsQhgCHycgBpQkwyxABgYE6wFH9nogmIBgFrnwBihBkDCXAHaiLdz64+FzYoAk+HrM+iaqxNn81nJF4cDwwYgYFIkEqeMGAnZhLatbdnI1NyeBA3v7/XRK5xrXa3b4OSWtmAycMKLPiYuefVW6619U8i5Z7Nqm7ZaDLnHiSXT57m/5bv6GdTSuLQaZTtolBgD1uDUgxrA4GRZNSS/dl4zP04Np04SagQOKcyCkb7Wa12KJxAOgUUBjXgisBUXy5ucr1ueh/1zMDtfB0rqak2mspf5uNN3/ngjZ1TalJ0dBswAAI6awXAWK0zvV009bgAqHfUDubyW0JRPrfQUZMOz9yYdvZOb5nzSFGrfqJtyg37Re31wEwBq0UPP9CKLm5cAAIQlDV3vc53cxa8Xl3sv9h1RMlQgGoFAKVsJz6p8AhgtVQU6SETBymBYQJgxACB0IIlCBVKBQAIYaRUrwGr0YqE65+PbHIC4JtD1+V9bzGsipgonkxXpDwIAACQbAKSZ/KCTxA3b+8Xm1BD0Pn1BoXdMfI1uulUSDjKCpp71lu0zBsJoTI8NXInSMk0cs2cLai0uAjA4Uk4ZPl2f7zp/tfi0C2Pltw2oQQmPSVKYKCgsZEDwaNRjkXmLY+ghM/D37jWkedi56c3u75cq3uW7AJIQrmaZsRH1NgigsXB9Fn3IjymIfw7iYlgblVB0W9yzL/fB8bvfJ6ip2XLgM7UI6wb37BVGLa3waRWBY4YeU8rWwbljf9lre0oVibN30LG/M5YWF8jptvW1uxvbSTHWExdNBi5pcp/1rQfO4s8qrp2ptoUryZc+t4tvMnDOvdQ/5l2c0TviBgEMrGCtADBgwHphxgAKAQbArFZAiBWBABAAiqpr8Zj1KWMDgMD/mkVgBWJkgXW2CgAIqNms53QlBYJXuA1qCDCEAyA+ADOqbPyturmstvfISH1w+kiGssdQ7FbcKE8axdzSMnsu0a203KLO09lyff+0XWnnOtpxBb0pyxApzZUCZ6K9svUuq6xbrY2llmbENEoIL8GFVAlx8C50m9dWMTWIxxqLMLPI1Ejo0u+uW7XzsjWMFiygQhub0zbrcmTEAy4Wb+XCnaZe7gf5gxhQfH+sbjp0h3lKXvr76h8Ahnr6dDPmEQCAzF2rnF7Y6fehebEzr3DgY79CRLoGTYd7l6GqCjbasHD2+zmd89O3K/Oc7On56/5Bf1LqelVPSjDikqXLmvjhfpio33w00WKL2oZZ2Osb+tcq7rfx3pxiNA85ALBlAQGxbkQUAKxeXpsaMQKACEAlTFrpCCAADVFlRSwQAKDW/4UmBAFcHBIcPuZwK2tLCLv1OxsSFsX0BXhJg5kyBhHhJXIPdaev82NKtcaI03n2mFi3F220bnRLAYNGV8hb0dob+oq2RTldU5LTNraaNHpGYRP3qVKAkLTI68KTC473bvv2/phtRK8ve2Jngau9VYnQ6H34stnWqGplK8siVvHB88cGQ2N+X9lxFAN3xed6FYhudKLSPxCK1laUg4LNzQjKsFiWFon3vB5B76jvkkv3e1AwCSibHv+x39fTL/+/M+lxQeTwmWAYtnOvcI32N5zmjTjKs1U54csmXNuzkvHE2DS1bava3Eu7+uPjhrZ47+BnzJdz261Qx/d4s9pDJRyXmxT587JaVE/L5YLNvm12hum2ahzyNq7Qgxtc1hlVKgp+NHItwbKgTitvIhkYGOG5Ds8OrpjBR9/j2r/zu9/j/43W0ahCNQDQCZiiUW0aikQWh0fgaE5xhNnCGBRD8Ay0mASb3zA8gcgiY2PawPTQKl5pv+1/1GUDs6K01xbZoIt1YnICyE52dzfK8nIVgyZtMJuA3WZfvLdZJWi5yCLAtZTRbNWzvdENne73K8X6XZN1J/TFWpxSUmksstVRn7rf/nn8ouy96qvvz7q6ro98nvUWjYjkqZLMLTqnU4Z4bJRwXBo4mkkosMTYjOm456KPqB9vvr4FL+J918/9GanqypFLZV7nth45g8rHTwALZ74v33eboVb7jR/nW59dl1zcsOojrXL6VyWv/dW5fif0+C8Z3emOEne+bLnQxSF8x/6c59Srrmz9jXpMgWkDEyjs+8vb87hsKrOccz+8xbIcn2/T7dUpvFbuocEl984ZLmAQIQiYfe6ntFq9PMelN4ACABgAyUAFsrXFcDWWiIAeAF77d87n81wtvm6vYJskGI2q/iUTAQJEP/Erf7YWp03ddReLVJy94XGDMZR/wxZfrx/9U//s1zpS5/xo24zNU5n8vSwvI6eLu9nWEypPYwRxcpq64WVFLdCn8xTrbcOKNMzWVrPSMbdMetWgYLaoXOtZPkZajXt9qptV5piT1+3i7SP7+5krlvZUbSmUoi6VA7xt/8D9xtB0a/9RuXlqXq7dNrrDPmH8VkibdraN5T9z4g5fBj/+4c+bF9BsTspCAhBkUNTCk7bE/v/uvz+Ebx3voO+3Wt8+vwLp5vFOiZvpgAWxJL0EAIDM71yNOpmN/dQ9fsR2HkuYz/LKdS9KjW57q8s7e/upK+Bpb5v98dO3/i1ahNHsn5Bc5B7+2pvYp352f6O/2t/rHQfCuJd51SyxkUDlAYyphp9rY+qVSk3uQ4MivZDAugrAsgCzNjAjpdQ+ZcAEGBtgQAxA6dCkAQtAxwaUxusjb7VZb83z3Uf4xHwl13Qn+36nP3idX/6duCpBGIasijFNc1fE0SaOBBA1CEmQeXvXsl731oaT5vJtYqRTmVBZWm/sJuo1E2rE04lVrCY0IzHWwXWvyyhokGUUlEiDrO4GGV09QMak6FEyoih5jaj3JX1JF3brpNrwFq+J9/Dt9c/237sW9Vm9Xuu13Z/8OvIivAs5tp/u0Yq6dVvX1+V5f/7x8Ul8uQ+tKcnZS/74g8/8Nd/6D//t2gOk3t4nOSjQESEIEq3TZU7Sn+P9J+2S+NX0KOs9zZzZydwdOJjWpIIKgrEuA0iQ5i56sOdeJu7Wv7oZCed+40Mn3xFphqEZFy5v6B3/ub+KxFJBBWh5C4OxVF/oyx6AXMEQSnSSTbBJDqLn8g5gJNJlC0L0uCieNE6UNWMOcAR3vjg2drXZjJlMgNRKqYjAk4CgCQCUwsIgxwwg3SSAQBMKYJQAgEAJxqTVMR84k86KOyxLzstHXzbna5dv7mUZydeCV/znkxR0pbWi5WEBW9kE2SIUQFYijcgwBgPBNDzNul51+PaGCG6TrvEwwm6CwJoxOF6WrMxTkKr9tiFL2Z3hZM2G280FAbOzdF8AgXoGy8SWeK9EAAoNMRJUkHAP/aBg0oIIlCy4nA+FoRyX3aoRw/zxLvzYzoHz5vtwjeXS6ymifcKUBUzxzPwUD1bcVqmPG7d9aHjZT0+72mmg4rVGByTQqDFQaIWRRkrhABAFYJKqIt1WWdbYIbx/RZ/olTWw3otjBcmdOLrBORaOyZ7/8JsGAAsAUHmzhN7nZouO5//hll7ezu0DfkdSE1zxwe9DmFuY5EpKrknEprqlRRcVvILen+Rd8Z6vxubjC8ghkceDFKspjbzSpOClYBwBGC5EN5Z2GIRyZcwvAxtAgDFYrgEGwDQBIIbXDM8ABQkmQIACAiMVFQCARAPCpKugrRXfpTOcFc/q3uHF8pzzvO++vtv2cZfsLpfLzKtar+ir4DUEsFqVRJkiIFoVAG0kEgBYjLnqS4/97b0v8GwPrwO+c0lOTs2atZdegaTbFOtEX6ETT/rF29UT7FVPlGptigKjpKm9aZZEsma0ISy3y5oYV4owIdiiDHdhkDrnMudGjjZR8pBFMR/RcI5eT3pwPtyW230i5uweuL6bL6YUzYmrhCInXK20VEWIhpDPZ9qnjt8/tozLvvtIGVmY3/A2NATGQGC8ZglqObNMMYhbTUIQZQ8zeEv97vJQneCFXNe7uAekh+iQk6wp5kHx8be/QURDAGlU/lic33lv5vDTCGpGs8ZpBF48V0wtGyOreEwEBcnNVLC4W9qKi8TaKdmv6Tf72CA0p5gl6+bieodIsW7kFetSy84S9cB0MSLbQiAfEoeaBRT2dVaVMQBEhtlGRlBYLQDKgoIACBgAVAUrDBsjm7CKFKMTQXVBFS0GSAGgNKF72xIHJ04wid2hk7UoZoaPuW/3p3dmGxaTrMprzevgtYkOIpMAVaEgVICG4KGpIUzWVP3aaw0n6hdS849V3F/v1vb69yvbWnSVKbdnaFIcNqvh1Z2fef6QflCkzkhCABfa3W5YDT2htI26zdN8eo8uDHfbMTe6sgxvbkRi2fCFsrhXZIqgysrAFXMmnMWyOs3e+vc0ZibvX2B9oN80dQ1mV64lopKWs3WFLzovlUKUFqj9UqZ95jg+wlqm8TIb2bIO1x8Z3tM4pCBFq8hsvqx8NQwqFwRQLE+HzD5cU/fP4OZ79dppa3lzqZ1tRuSN2eFKMgT57W9+s/BciCotX5aqV1K783vDO2mWDVg2JrXiKqq9ZL2DqlVKv5DTuA6wvlivTu0sCyJ81F9PH3fN4oDS3S25+DF5y9r5wo7BiU09JvbaedO6vFU6WhxAllMah/pFCxgTAAOgjLUZbDAAEGV4TiAARKQYwAwEkWqoSBfU5PDK7blDZ/9DMgAIsKsGTnyP20VtazMLifSoK9SzCsyUz3nuS3tXdsxOvFLzZJ6U15NP3VZFoVYkQMCmoGg6nWfvxV/S0lmffTngzY61l1fddEOxMUwjIW7GXIWkF4tXzUKKJTz3H26INEYxwtkerTVdnUJnCj2MsU81hCGYNTCy8IA57Gh0yRWt1AeXiw1qdctryavmq/FSx6nUcuIIHANHdx2CM2jXliN6kYuqg1BEVRRkUe1Dk/Eh0f1SqO5++OLdp727edPQ9kpVVNJyscKDbX/AtT7ff17fWzoV2DqUG8l0z63pK+ol92OUuGK8Hp5/pA/zUpGdty5IrAT56Xe/wQAFAQBe7LatEWe7+tv9f1hhwc/xyKglSaPYzW70ddbkXGnihcbGAQSEa7bNJAFRQb73YX+bNLhMEWh1KkViySVzRmvPKJN63LdbrFm8wvTggBk2pc32LuzOD2tmWBmGtlB4yqROMqDGGF5r+GgIWCHQcKjCaFUCK/0be6Jv5Vs7vkmnsVortv8LiCCq8w+3295pNyiwcBiiC5ddtJWz3NXnhTnoXubDGKfkFFVVAKtA0sMqBBsWt7K6qhklILyYuL5q1KU3bGILDBoaaTeF7MFdOuTgqqSMEUBr147sgq06t8NBu1GhlrswYq5vXd9nDYwrlpBNs96gkgSWp5rwzVv19Lin9dX6Z+PWfKEwxYUhaCsAN4ARz6A3pOy7zW5eoyuq+5KOIA0AAICgbnt5bmvqJ7eUdzx6fWCl27LtlbEMkUhRJsqR867Wh5ZiSFEY0jOHp54b98Yqa2Vnyq1hn8/L6+OwioScPR4RNJ3ZPoYBCIyJ+NCV+P7+8HMMr6Av/2Plf14cPEcDc5wjKFH1KhBiNzyM/Uo6CBSoJuF6O88p9oI41Fb7xcGC0ENLtNiWoeFxY8Z94qIDVyOquURi8NK9GGyo2Mu5JQDbvoABgAjV3GsJAIYQ+Hn2BjCsVoIAIFWy+yZf/2BzX2q+O3M5f5RzDut5eH58lbvzAb8o0AmTs/3LcLnqruYRq1QjbTTNlVmDppUGY/bSx74sHu++Xl4+OIbVdrWRoEoUg2GrAi+9nDJx8TAMGaa9UMtQCZ/+/nTVFz1Vq11+TzTSGkUuMjGpqPvTKNrcLgRr6aXdGsIi6AkC0G1HlYAqz8gyjl23yulKvpg+8sKXP1zmt8qPVrdRE64gunDqOqY3SEDgOIC3aHMdYtgvG5iDYmotU2CkgCBkTkN79OuIT/fD5y8/mf3Zu4bnt5XdX5VM7KIUkCAjGAqfHiFia8GasJMrUdgkoKiTTu83Zl3el41D2IPq2cFdYjbUNwA1YFmPurTe/oxkvp5x5Cv/PiG8seSt3GpHAY3nd1hyC1brLXJKdRvcu355QNLF/XkGQ8+opLuW/X6vp2TbnjXdpripSOWGak6fvSct015Z8d3QOEbJ4abYMlGAlpUZBiCswLyNwAJhXeMxTfQwoA8MyIYNQTha3/7gZ5PP77enh916ktLO+5o/zNrVf+qgX+5L1MVrpCY56erZ+5Tru563x4O1oyAHAqJ24eHmMDNyygZjgeuUl8frerZevIln2kthDBvS5/mGJKTQRnPNBuI8N4IS9gCnIODGNefv7e3R+thmPznLovL/Ix5wXQh/sl3TkVa7oW8VwFm8ndx9JjinILvnSMUpQtHphNrL40zXqeu91nuqz8an6jZtrbhwAdyOpoEck66tgNzujb6DywQJZpGgqQKkWgEDIKjJEtkbw0by84ym1dA73i/uCvY3R1ptm95uq7MQYXBQGLUHnJEEUKxitNSOc6qjGiFBP3DfcdO48vOtXg0OYc/vUq0kE7/EfQGY8KTS7u0M3kfv0Uxzzf+DN7T+3ZftLW4bY5zvZ72/XdesmXNDdct7z7kPuTpC//B0ZyVlLeoJ+KiIYFC7em4NUEVX0rInXRJ76aai7e06p54+oycq6kyFIZD4GX9r1wCKUMBqgoEpkNPwZIw9hD6BgAgqJ/ng5sEnu8/5If6QbMqIriiQbxDaPAqj4rU+S/ZmbT06TqgfuqbN99v94tXXF6+6tq7KqbmTWgrpCl40Yzua4YGZrIg4Ih+s8uJT9vl1nJT6Y97NFJq1jJMwLAIIOEEt1CszSfp6vcbk91ojAsePY9gsiaOmVZNfE1euoHea1pEsd9iSLjxzZdUtq/2e0Wi2U/dpe9O+dZ1tvS+PnyU/N7+MlytAzTEBANSFq8Y2xlXjqDAdVkU3u8RgljEYPTotUgBYBULTEdUtUduVa5IvVvR7Da/pK3yhAytfPRw/IetPSqO0W0jv9ygTG9toQ1QAaMsaNDuvx2qBdmoxVm/TA+pwoBJlmIv1EXR2bx5//E4qeI80wIz34E179ubCudc/uqFxWyhFS70Hvw8YG3Iw6YxUER1ajI/cidwsyjy8txungkHn3uSEdtu44dYWtN4oFq4adOSk+47WDx1E9u5fGnYvCrZKnaVcgGl3baewwmoXgHFIUygEWOox4TcjomQjJbvq+JyCZfH2m9shX8a54TX4wPNye6+tx8J9+3jfKoM6cab3/c77yzwXsN8f6SFzo6/oZW432ctU2VibdJwgIT1Ig4ra6rfWQUkI3NtmepyVm0TXq/EfT+O8Wvt6Jf5PrEBigy5GhaWNsJs0GHFXUWxAa52mNJsmFlq7YFd2l+1N5QpnhCEKkSWpIoArDs9fofKuGkEqrix4XWwJLx3r3D4fd/t5Ps/uLq2kEC0OzhlWBGotdjrpI715Trm7jxaDhBWroVAKAICRgkIYyKv2MHz6Mh9n7sfrXzz9uXVSSwIpTW+N8kd+NNKcJ8O5Glo2+8yiJUoDCcSCQBSwy8RjvpCh6UJOVFUlAxD1sjFrk3/d7VmOnMfQHAX3AlAEWKiXNPZ7louAPRu3v+r1/fhod81q85/OaKXsprcHt7EedNa08Jhiuvpod+ixKp/ze0EPCn6dWKlAuO6kLKe7VWyT+6SHrT3hbu7FJZw2X7ML4UoJk4EMKqnfzT/mIGwBg4MRCPHNpKpUQEUZJXqDAiAKAAAIKLkMJVFVTMw5b3hzzfcyZ0RZusWK9up+/9673TveWK7pKoUNA04eR3zY5hYzvoxHlsdxCc/2/RWPsmCXfFO9QccFCA5IvK5mq3QdzuE52O/Z2T0eu3u3K6ezgif/B4BBFJAoGLdPDEA15a5tdorDjVe14+w31u3tdlBabyeZtY0Xn2CxCdY4SBJAyqRah1qWU1kz0k6uu/WD53DSz/l5S/e83y2cIxTBVV0CGWiA0GopOrgPH/hwHmF7dtjARoTSYAkBAACEEPSVI+QW6mbX9Su/V64/c/oH9NVBuKCyMJt6Cw1qLQNbVx99rq6NZVhqYYWsTRQQIWqXqWZRPRYyRZ+q6fL7xM1ekOY6pOuuut6X3OzSHU+6DdkAxpjWkAa+a+8paYrAHfvCqRQjyJV3K8Gqvli+Yfe897NltnTnEsWu7cW4koxhtIPzHncrBgQ7F/nhPSWBSFsCbvQ+erOECpWW9Fn/4yy9tDDGAZu1CMYJzl/WmUSAZZWKWRtjCMAggDEGY3gHAYAiKgEJgJIqYYVcbx1HSL6MuYtFI5FbzhibzooGlcBbY5FE0eY0D7xQm/d1vtrknNbEdcyX//x5PnndRKt4XTDlglScxfmgWcC0ZXPAIQyG3pbe8CIOpn1/0ngKtdJKCg575rIZiyVd5PYlrBvrD3e69+XtTWWq9EDQ66220jxzAqAglzVGJA46iiEpSe32K3m1bk77ftH7mh/r+//N3NJrsYZHssJp0Nny0hhI2aIpxbZ1HpEH7hakDcDARoIAgFUoAmjShSHVbobGls2bdXPkLxz9Ht1m8SMEjgCDyaApBT8j+sbqLFn1TnUiAQ0NA4cAHYU6ohiNBdJC94B+thrQkFt4cNktutOQm/j+ZjWcKyctuCAwjDUL6MEllySc1kvaDiL0Vje36H06M2cLBXcqb6v9729pUebYWJf8RZvoarD9amPavK2emYQGkfQux9WaWI9g8DLl7nKjXxCTeGSDK1EXL1s1zNu+blkGFCZMmSxMwwAKMzKUIwMKAAOmFyMgEAqQGkpAOgXJVoxeWVW9XyFtrgKFpi20IKk2v/bu3n2aYQmgIS4+WVWZhQHgrLRcohMcl/N0VxnJbc+3xdOci7Udr6AO+ZA2sRlRy+qhjt1hW5bswe5VrClrDtlaWxHcwckLE7Y7vrXudbbs92o3bXrRW+l2G3jebjfR/SvMk2lOvaGz1Tk0NbIaENJuZdTravLFmvt1fV71Wvv/r7lbPele5uo2eIjdZeIqkCTJ1OzMWW7cPWd3NZGlCqSBQik95AZETIds036yg2zaqJtpfTZcM3VPNgsciQgAEBCAAKuDZLKms2tBSm56CACbUuuQgdaYFYkSm4C6Vi02t3irqbomnjI/R72jlvC73DwEf5NBjVtTBiwgABh69+wrN5JrM9mwhxh1sE+ZZSWRWqu7ezerIIoUZbW1mcqZs42OWXa1rFU6qprKTbR6JwVttHPqAtmcUfBaLgU+uFI5wMKaEFbNm+/zhmCQhsoCLAAMOGUBqAzUEeE3iwriHkoBwYkO0WVeE39o9QfTGi2YYAX2MGE8/prfIk7XwQEMK1VtKjXtbQiKiFQuNFNNvEe+9uKoK5rpyTfP+9M4QTVQGyXnIow5HLDlci6CAMviLe3FfHH7+sAKxyE3BoEHDR7eYuNULZraR0ozPLoSrBeKziA66TObq1Ox7tXEnM1tTaW5qM8v//j/zz5r/3F5/7HwqtrFS4Xlhhs2IEyIXMHV7Mwuax+ycrBdmjaVBEYVSAEAAKGGvfNm5ovHPEkbZhruZfAeyTntp9iAMEhBUAABEAAAAJQiWTabWOZi887XFxagsITUmRlf3c1kSiQ0RfLxyHm3IrgmViXr/Vafuac72ZlI/FZqcC2LliIYAFgAFMWb9ixyqIRtGetuLo9gDoo6WkUmF62TfrTfvYeHtNjVnvClPFVr02FrinR73NpG3QJnc4Vr1RqBe9MlJ67bRsa5RbfKCWZTkRCX6667vthQDBAjQSyAcMNmMwmwRdJqeWHsJyy1ef7nOZc4x1Z099afG/9PrM/odogu95A0iUYiczHPxluRLIohogAKSAGpYtgIvSoLJ4OqiJSTee/yddR9sNGP8+V3fT+1C0srusK+GFrbKCwBEu7KY46P/eGD/uTr69384ZHXyGozBYFPP58+dBFwWjpuDc90gaKxzQJGgnH2idugJF72QSjOtlseb3v80HX0a/uPM/G1cqriCswuwPlkvyyy6qHoWsQZPM2pVBJW2mzXRgFhQBAAAAQFg26nl6sXq4/tg8PTewUfJp/KrrY6RVBAAIiNEAAQhBQATBiUiK+xyn3vtv6uH69ESqnROmSRHbw+e0BPgLFyuLobOiN+NH3f0bscmz99xEOAXtYrepPjaBGsKQACAMDRenPsjRYIL2TNKrMqA0ij5r3tz3mOm8SkkxZN8rClRSymOoYncxXnc/HiVrbdbtY5sXS0GJIYtDd8vp+42ttsq+GsRRuGpdUcvB5bpVkGNpZWBSu1VngSNmrVjIET6DrEg/CTBsvhZf+dv/75f//xVz+t+8O31/T8qryMhxMkE2w8G4R2mbBj4Z3vhqHYDChqMEABKYCgAAA2o0FW6sTRpPoyQtkpu6f7onPsMef9+qh9GjZwadNWp9LOkogNKjR++pKf3O+PH/vFFbeSKFMw+5V+cN0CRpVGuxnDWEVBQ8EgAulpYqpKpUXTZV2t+4fuLxtus9O9c3+sepo3pYFSRG2XRssWKc9BCy2RkZW2to8SQZNGA6RCiVBgU+0ufbXmy6tP0sfl0e2Lt3XvU1dfxKGFqQJYAIEgyAhTVKEoggWMRAQyudUNheat+8X/Zd3DABiMpQMray+3ECw3uVCcvCTik65zN4i+Zx4Dl8wEytY1iNo1CQ6iQBbAGBjTVmHDc84LvSC0xqXvKnDVWu7bWrRKk7psycHcAahjoYvaa3Zmgv92fv/TyZ6/bavfRw3oata9wmSBwiUcoMrXjKFt8kzcq8WAmVk6z5ADZg0sDPtsM2n1PLDKudwEWyEAExER+wAFLFjdHD5w+yf91//87/w7/sZ/rL5st7laD0RVkgsCbTZkgnUIOzILACxwKcfFYgoASAAgDRVYTUCPjiABXUt9mQao5I46Y507574W7etU+5N6fVYSR12ZaJxEGnRFN95u+P9H+/svHj+er/tqskDc5turTzra3jZfgOp0n/Vqcqu7RVjqxjG9N9pe5TK2Pk3PV6mffo78uJ1i/ZL0q8wFlNLIMAslcBqnquk981gYE8aaQxK0t71tY++EAtFKgwgCaWe5zX7x8NnwiTzGR88jfsX5LzSs4sZUEQQEWCyAIKCqVgCKIhQIACyRpg8udRWbP/nfX73/dhjBio60i4IL7t1LWiv2kHpUGMgBUd+740GJM+EckOS4Y4oBO0AMshKCQAJ6ctF+OFthIooKuA4VF7Qw2Et7urBUFEdJDlmRbHydXMPWlD5fr5Nmk6vPktbgiXjNbVyv6kLZYHyNdAsXL4NiMX668zbVNrIJhIS4JaVlk/oepGnCNFnBbixSAJqIyLIMHwmm6nmw3vTt4xecw81VWrRE2800F2NP6WWqhzJSCFUaAYoASgBAoMTQbvVuOp3j0jtDSkWFXv2du7tTdQIvZZ2dze7mp33/D+us7dxfX8879rLrabtolg1KF81702b97r7+FOffqTjFrtz1bdO8V/Xs97rYTYwlQQAILYDNJgzTDy3CaLHabd9XuL2/3D/fbGVkRac5Mr9YfpSP9X748t2X7/63/ue5DfYQgkNrWp1MaJBmggAiEpFGku7CmzVfXn3iPNx8zPHtP/4++eeu/8U5fqmBiIhLKQNnkITlyhFxAEPmftf7jws6n+2gEBKAtmhUBbjNpxrTaYSUI0vOVbi6OchlN3HwFRYHMxiAcgESEVK4MSff/Hi949oupVFaXNSX+LHKk3sw7y7xAr8MYJIKiYoJST83VAj0BkSZnna/vfi0xdytwFQNG9cZN+aGJy497JbiIYiRIdDZmhFQuEBnABWwjGEULLAwVmd9wUxLlggw/HxazLlxvf3Fj85zXz0N6Tod6c5vjqsNy37HvtOnmUNnQuhRgJWiQqlUII0EAOoqSc4vS9JUgjSlP//8na47nbtqy1PAuq1p5ojuXM9WT5fM/XbdbtPDSQo5wiUKYdPZ/GKtI3+Or2pNQw6EXJMqq1OdiAowBvTgyOX4oSqXO83ag22xXLnlD7f321kGO1wdmwjtmuxj9/lH/70+3++f9SXLWNaRGtq1kQjCIFIgCNUyw82arxfPpxf4sD56O/qvOP/FfO3Y+uscA0AcUTYjArSqxIHAGJiuu189v/j88WLLGWIBJSFhHZqtOl7jnJYdyTGDr0EmAQaaALpDgiDP3CFeigYQCYmDAR/vZ85Qu30t4RjZRBkuYns4HmOc4RJZNC/XGFWpimrwrJN+ZiRCYoEEDuvsV7NZ+I12NAPHrXfjqoNBbT74DVIXD8wxUIy5Oe2kwr21hUIACvj6UmFggQENC0xoM0rwG4VUXsc8/XHno7bMu/m9c8Y68dVSv7Mx7vlw+6AdyyEGIWyJIwKA0qYNQQDNi+kuUeXCqlJKZZ/ff+5Scbnq6CaePeBybhcnBtkVPYZ7yfE6lPvtdZs4Nh/oJCdI12nepm+twKTFsFe/h/fa8FtiQWQ8EMSyDQBM+8sp67ZGt8sn13qv+VF9G0OQDvRiUzTJN+uL+5/+o8+1ryYGB2NoQ6kUEAIAdch29XLxcvGEebh9cB/zz5596updY+74wS/CqSOiDIyIuGKJCw5gYCQ/z/evV795vXi5p0pIICfSiGgNNmMoI2YE4xlSxEULI68h1UBG2MnzOwvGAGkEQkQK3jA3H2KlvfRuNW64pqsmu1+cxOlSvqJoRcKssCn0EsX1vUIX3/AVDpABqEWXIe1r4/F8XvL99P7GTa5QTfvetX+8jE9Vp4Nhcbm8aG2dM5/dexX8KZ7cGyOCCk6djLUAqYjpW8tKsGAY9htMYzDKu8Rup3QPbZQSqm26y/HnYp0PrvjsrZ/e5pptrG5KK6o2ilIREQtErFKLL0P36dDVJ5JWu5KqjlOKJhjK5jq7FIyN1AZosLJHzCaN693Wq0Qt2CvyEKXqMn3wup6Hmxzt7PxjnDSDepa13EUCLQvmOfuPc/5xrc7ic9NdfUA/WLtzBYsWy7CIHXzUl+6rvtajUotQ1ABIQ62AatE9vHzZL65+AY/bR8/jzWen33L0GWqhl1wCDnyBAwEEAAQiMyPJ6soBBBB0Pf3yH9eLxzr3NJJCQ5qgJNnGW2qFxmnonE4xC8DRU1AYgSD3OceCcuw0Vg0i0E4DmJyLZM8aM4s1Erq63/neD40o/bVvkycGjmYtOKGHZdCmuICWqVgIJxpgh12HgL2Fyf2d+8t+sE3ie9lbex/WJ7W5YJCfUaes1HbPXznC/1j/Ki1qlGSrtZkmAouIDJZpYFiW8POsGCB4tAjq0NYY6bbhvgtHY0obra4m0+V+Pr3pJ9uGjicOHVQBaYkFjChjGbpy5Kp6rKiUox5XoVNXEXB2DHg5ioRpikhsrIA0iixjlfarIGn1UoC0RV8f6sbKvfhweolfSrefIJQNRuEtTsnK83zqlq6dH54vyQexgJoMuhgLnOQOI/e5r8cEwOEgBUQsBqnrErbTF1e/WDyiD7/y5G1tPrH5Y9uta4EjUUKkwCXAiQACMeiFXtgNYNi8J3/wf7re9KGjgSCVukQF4Jp+VhZsFuGgEUmBAkoIKLGscx9YbCwgEE2T0ogkoLw7D02YZzmUnDqJ7ts73baZKley4wI0Dyp25CUGjBjddC/AmpyC3aYtjdiDS8pxGWH7wN/5som367XbizkcbIYLjM06db/Vovfj2bR/+Xv/u058pQRbKQgA9zXGwvB6hk30IAIyxMCwG6Fscc+6Up269rYY2qvamHo5vRN5aq8fm9dv+fTV+tfrUtRxGjqGFoGQqTbVtEjUokAsOcxaSkojgsjIlUyaRSRSKeJGApS6JGQ16Ajw+gxri5a6lK36un/PGJ5HwLs5DUA6orGAlBbrc6P3pf9P1R/AsACsUGxCcuKpPCJbTgRh0UMUHAAAIsIBO3izeLF8mj4qD97W7c85/pHpS1w9GqwowCBBKVACgUAEIhAFDKCq4MGp6ef57jv/7sPPfUlrD4dYRRSRukLC4fVmo03OYVzuNRxBkOoKWhI/P3ziaGI01BSmQxHRyNJsxAtT0KOcqCFVJiw2WpQCAweM3dT8tkvYu7hT2QSN20jRhQiWMs6wASJyBhVUGKfsud8jeXN2LYM4lpc7WBJU7/mZxKzvFq32Pz7+Y/0HI4T7zQkKGKyxDNpqCRpFCmAAKACQAtGWIAElu+kbZMLLLIM0OK1F5onzBHiIK3s+eeknt+ejg5T0IGxFVsV3RUnTXYqqpjqEIXWVVq8iFDAC0FJFGAoOLUBAAAUKEC6dsA6WXpfpa1sPYPf36gfTInEQhkIFMjVpTv3p6/mPX219FH6Av4qp3M2n6lZ/wSnvCm2GgglHVuJQEEtRTZlhO1wuL7o+bT77enn2ZfU/cPxbdKeiBysAEAEOWgIIACERQAQQERLVriTHePMYKOPN+ETNhvky58N0//pM1FnSSF0DgMCJ6jyXG/PhDtd+K/MEdzC6JNpi7eLEsCQVRwIiBJpmQ8VQdLBJD+cEzGJ0lunH2FIjsyaev+ff8tlQ/8vjFv5Gz/dTqevuVgmSpFBUtDy8cuYAzlIDGfrhKV+J2h2bS5vcalHvxh120eCxcmX3+sXiuhI4CFy2AAACpLTCICysDM4WGX7SRjhtdGgCU3U9bGp12yseg5/GMhe1qGMuUuaUe7r267K9Pr/k6W7PMlpjmD3U1V9dlXKLQjVQUanr6BIlTRUbQErMRkRaMhQRgAAAAIApKFAQEjfN/1+qrT7VO8w3mkWQK2SaNcHY4vW5P/3h69vf/H/m7zWX5qqK+st1g95cP0GpLABIZClayC/gML65HV4uv0qe4cW9Hn25vv50ufeJ1Vdrxw+MVAQACERVVyKAIAlEQeBAAIFLzKUdqzIG0uuCiAtAJvyyfruXt+sMqwNggkACBrTyyCz+5vv840z2+dL26BQsFW6n4D8TLI4EYwJLqQEYgJgDJSVAXJSrru9XG8t1xYNbUsU6cejYuzYGQ/DJ/a19Hm93/4j9w/S9CqQpKSYUwF/wpEVUN/Cn26N4tu72w1nRhW3lN3Cj6qE0NTVttFEISVfnf2t34/DsKk2zAooUCKwVYDuPMQ/2MiEew1B18NF3Xp7Hf+NQ91zXC9V+q+dUT09rqeoXBcpu4zv//t72//2T93//QH4p75ghEwlKEywpNlgAlFGUSEEUAKVC6Uat1HU4fYm4OvfmLUUgIAAdaFUenSv58Pz6lQ/zy95HcmL4bn4LIZ0aJjXuAk7tS2hytyh3aYgUAEIBADACEqm0oSHhrXwRLtLHd7/xmZefXf04J58bpbS3RowYA5BPgMcE2dMyxgIEMAIhG0yAOJL0EgUAHk545MrYa3pDM1ABBAUQEGlmOt1ufxP/S70bPKEiTHRlXvzX7q1htqkjtAKgCAAqCD0YAA6gEnUr5cXcYNYLDSwuATIvygM1tl+n8+hvf9z3D7M/o5uUYe82hZrj9tPvN9/xQ+Ifj69/PpzQ3fZ7+8zJ7tabdJfzNa66XtXtVDiEh1qZ9ffcgwt7gOBpYRo1QCAk6kEvAWR4t9Rx9rzg/PzVlV9plkS1rlZWhLXnanqs+YaiwM3eJh08l+/v/VXODytv8IGMMywtBUVLDRAQDVCUmAAhUlDKCtWiEkr1heKqJVOTFADASgu75nR+9tv9ozN/LnHQbLWwN0IkxqJJo+prLa5wwoQJMUikEiMgAQQoRSgZsINr81we3/3sk4/fXD518+vpBx8z8lpAxAAwAhBEoJRKsjQkAkDEGOwOAQBBWgOMXeHabbxnQb20ACABiSYhQJ+cXts7nyIjAFCjpRre2J67lOx4ACgYAAALLhn1S0bQiqCO0DnhCwoELXJO0eyl3d0TH/2e5M1tQlqxF/enhtHRumib3QSUEnfV3NqOGhN5Q6eB1xqTfd/9tLUNNom54jYUkOVyAHfIt1fR0+3LigEgGINdVWIMs8qKEYACICDRTFm82NZheXJ49oW8mDbSF0QtpCiThXXJ9nKzGS60rHxP362kShJfnPP96o8r74mFImKwYhBpWIwINiREaqRyOq6TRaUrShRXpwRVvQBSaV07uZzmDz76+Mv+cazAbWlT4+MFza6KAVccWZkQKQBIAMAoCA0Ulr2zN3oZnh8fffHxz37+6Vj/qke/h01dGikEvUAq2DcXAIRErpQIL8Y4EAAigIGoZraxjRjhKcLz+L067d2qiQqAgFRREBLYErK3NiwHnzZtOoPNprq2OaEQXo0hJR20vChwgoJWKXJcmnEPvSTjCNVua3PaTu6kDxAa3JLQGjqOxrZzJTGItaqqqL7KZVtx5T65yb32Uc7q3JM9u5/HyOpyq1/xxEoR2QYSDg5zh3wVZAcwCKwGoIiWABhA+Mhg2IvTlPlpwrL2433Ma7fnCmwaQSKgRA1F8xFb3gIEBxhtaLGMbbrP+QG90zFE0jEqACqiIGDtGBgEKFcfcS7UudPJIhL6f9GsxA0EAMDKueTQH7/YfR5ZVTUTStBOkFMiRSkSMQT4X40SaVRo0t3i6sNcbJ88efgHv/hx7X6V45+ZqrXQChAQgqYEAGJgAKOMwLjItASgN4gDwe4xIrhkJGkJ+nbcs9tgG2/4DCIBJRJAGhpH5M7uVhlxUbpEIgipNqARm8ZQwEoigN37yR2cN/KEqtVqJP3EuBSMEBE3UW3F8x6bp1FqrRUAhnSE4Z3Mvb1V2ZbUqVvz2IlfpAeu8CltydjOTmxOVu/DrGdeqPa4VT4XMU4uVB38x1fUAiCwWrGaoEG0ZW0YgwAgJdDNkilChERim5vxxqha3F19dr33Uc+6LAAMWYCkxcX9PHMWi5Dmo0UYPGK0AwwNrsqbzaFkQFpEoEIJohjgYMTGFS1OUqc4naqxaUqahCaAhNIWQ1BHrj08PsgY6SKuSNSxYgGhIkVVURqAodpaaYMEZJmn1y998eDJ1c9PP/l9vvrtOvlVp8/GscZaIgCCIAREq4gxPsTAdyUYCASepCoFMth8iANjBB6Pb8YAIutq5macFPQgT9asmWuDIMoWtRFKqVLqdVharIUuN7vWieDNZenx7zK0AGUVKYbsTP9jDb8wt97KgvWorVMDq7QsAoNBCGO1Vnsj26sRGyoISBrtUPY5kTSyC9SucdrInFzUCMci4OGoMJ7sIjchNzMeheMS1kBJyIxzGgpeg1CwEhs1hJ+fCGgDAKDo2IxbU61O8c3t5x86pQcoKGoAALTFAa61AtgggPDEWmtJgMAT5pg9rvv6LU/XdbY1tNpQIqHLpGghNC9bN+0s5SDuRERX5SgdcvcspChKmrQoRamiH17v39AYrHeMlHu00hBEiABMJdLi6FZM0iXcXLx64atHH4cH9LNf5H/m7Md2rGp0JBAAAGAAGBACAAkgFCSAAAJX5aJPAmMgEI8HAiMiRGsZaUPQRXlr395GPdqarGyhFRUAkEgSXmXmsTCnPQxI0Czw8sTIVIcBAwReLZy76P/gcZJE3io81e/p9jXdqTbmgliBJHTp8ZLU0QFoUUIlUcERoFWTkpJlYxHCQAIQccyRp1jy+sl5gcpZp4bXu9bTc1puKQI1NuJYUNvquosAYkEpwyipYWGKgegRAZgmANsuADBkOza5MYD9kjUPst7wwmzEtCUGK1LAvaCEwTcAB0Tr2OggWdCpvnLPyae+Pt42V31958cHs1sZEtModQZrIj1dy13JXCr2VOAUKZALSmbVKIkQQcaANsVuz2ufz+Nn/H1v1+8b5BzGKIS0QqWBlNTd8PrKlx+4mD7pPH7L69/09P/t9We4GehIRVgyIABAYAAICIAAYgBxEiOAiKlGiJg9PS4AMAYCGEAA4xEYiISBDEx063uf1D2rq4qRIkIUBcbhrc1VDiQVb6giqOS9VensuE1rgbYJNskQzuM9t0+byE59/DZ+bL/dWx8bhMKiYhceuCSCdFpK8NCAcABA4GKrzc3JOicUGBEIHAAxCZGGGVAUXB2M92zbU6cd3huUHACwUXfcq47PaQIEgBWZW0EAEYCIB+GjAABMi8lDbgo16KLFbfo7ff/s+n8bYU/GqW0OkmMVKLEaDhDZUlwHuB9kNU13bKf7qhzoBvt89KbHV3y6Pa/2K8uYK6EKqpullFXuKtlNW9MlOOSARCmdFUOIogaR0Fy8eBwjXO794cGK//TdT15f2aBPCFw0jcFQgWXR7cpXjzwfLphPb57/ZPy/Of7ttNuCOiCMXHCLcElAAAAhEBAA+V8AiI8AnJDV2vhleazEkAiMEcH/C4ERWnhbkHx+a4a0URXQE2oAiozNK3sYatviLS4BEChxfVwk4nRIJSKCC4USmjJIP8pNJ+nZ95xzYirOUFhuIwlQyuMNgMkBEDfINAZQYTkQhrK5YQFQUvAdWiR7xT18eu+4XvZHgixdZIQ9WGO+yu+8rDFgQuhkCZisHEMAQEQAUGPgoyklU2fQpq92H7zeTmAAklRulrc+19bcbjTqb6H7f33p+webqRptfErBas/+7KWX5awDx6bvvqU/+Y6vP/jmefPN+80UQ1WtEAVDETMKWImSCM00IxfUClhRqYKKtKJaSlUrkSXaQXa27ftf/KbZ/xbx/xn+X8nDf5z7/btS/n2xEFOMpvd80DvuDeUsP4/lEvysS/xgFbr12KCEKRLQBMTlER8EGBiPgYjHeGAgkrEsRyAwrsQSRyEjBBE4DgB4ABiIAwEWA/jVCW30yhSdT1AyNQBWAPQ1jbVfFhBu0iY2gEvZU96rXTMuVCSKEvG42pjmE42HMu6a1OtHuQcuKymM98OokYE/rrmJVTIEsQwyq1aqADW9WWev993EQQpsSNZ63DmQFcr6vjFH0Ra0wYSYLQBWFITXlABAAMA8CAyAD6NEzkP21cdz/XbGKWiVg7npkM/V2qX+/+4vjH/4lYepp9eq9y5K0e5hyFKFe/Lk0DXkvG+/vT+exzHGwMlUZSHiIou1SDBScYQiEqwSWaMIXnEjYFNVMFLaXu83+2Jf6vyAyn+5Y97r9r+cVb+yc+S/Xc3776PkbRRou/V0rr5e7bpftn98Gvs/D5a95bg6GDASQBgJmKopQgwUxHgDxADGiIGIiFKUgQCQxBhDzBByBHDMBsAIYEQIALFBFyHD0/oFl4ETgSwAUGLhve5CxFfHOTaRWEVby7Vqc0gF1JSCBTA1EOYwlGT6CDBtne8hh3MoqqRKbBPb73MAgAxgMhAALIAwXjUtb6ybog2MctrWr1PrUQZg20sAUIrJPudkgxVQEBjLBkBACpABuEzAtPEgMFaPGQgBEgEaHujHF/fO8911zPHuuyYEQKK1xXpXf9l097vpPKqX1vu4j/1C2NpDSRgHA4WDbwbO5HI+u9lf2+LBNAnsNcSdsiAYSVUDDoADkQs0QSHaulmKNHnNRnI3se4teyzO1Vn6bS/yMfVdC68b/Vumx7Py2diaKoYSXWdt+QHhEfpGMgy9dmphpAgEgY4wRZ3AgVEwHgvGGI/HGGwwHkMUgwEsGIiBUWkKgIGBwDiAQDC/iAkREtpJELCNPyIHYxu3iJUCoB379JYGXh4oVSgYtEridanSNaAoAIBAZlfyQehMKGH38ui563zx51DJeaCWCsQQAKaO0QR+XMwqUIEJFumUVTvU5l3zXlo1SqvS/qj/ear25EOAVQDcIpZRQRADKsCaCFghisErA8CsAAyeW3OACiggnvb0cvubl6dzH7LbsrMwohlVQGNlvi/jSGhnLMtO0RXuO+NQYABccsupTrtP4umaj6/2q1t6Z1j4YSttK0Ao1djBFGYpVpWEQltAaQjaiPvujHly5MfxgbP77Tt7xa7DWPYSKP0d+q28dtQaHLY6xuNuh/vc/9iaaP6Szb8R9b91oJ9t+ppOpinoQDlNldAUZXw/hIc74oExMDgRR0SMgYjJwEtEjMcAEGSgjDeIpwkKjhEAOD6MlVCgqEMvoupW36M0ZVdruwoRAxWI4a5TybWUeutTDHiMPoQ47noQAIAcvypQbIxOv01nlKCbRIh7odwQ6wGCH3dX0KA5UBf4bDnP/Bh4NkD91vZif7reIszxetswYi9pOoAhrGLKV7ICwxIwdnZuutUAQJEqqwcARiJgeBcAMKpsXekK1lNvr6/HisVlg7JTCIKF5Un9Ss8MEoFL3VTpsqR1cCkwGAyGqvBEnhp0XlW96dObrBs7KjENUSAgtbHQWAyQwmxto4wq2Zv5dNFCrZoKdlOaJzTFxWjwG65SKyU1Qpc0GqKKaWWZeon0uEmVdawcNZ+bxi06yySyEH+mIv1JUUrQE4nySQdQMB5jYATGiAAQGChKE2MM4ABiQNmMYHcBMEYA1zQEqUm1CZzssPnFR9m5ZVwN0ELLUq7LDkbwWBOLKfCSpit6qdaMKoJQAm0vH41vL3RrLna9Sn/VusqLSDjdmOPeFdgqgLS6LNZZzxsBIAEMA1wUt/o87765/UoL0ZNo7nb6k+3caKmtgBAOAFtsMSjma44mTJCSxM1NHKUQUSuB7MMEKdgw0/awQSF6VFUCNLTtvO6/Cyv77c83pgwTTJQ3LWAYwlAAwG0VSpVWKibDMSHB0AvbpBKjeQWvej4OsyNXfHztq9tkeclqw30J0QGQIkZn2eZ5sc6vTqjjmtwr9zRRx6FjSIS3prcOIn1wXT3wnS54YJBt7Fjb5zOFsouZpFx95rjo2IbevTYtblaarYm0xkTS0uNy9fSIDgADQAQwgAHgACLIDTAiAiMGgCsRIyQQAwMA4nvHBC3YoCFN0OtI5uzN/ejF3mELACPFZey8lis5UNNMjGjKnVbvngIvHShV0oTkchCZgTmzetqyaZLei+NavJf7Nk6MmhlAQFibT3YOr3rGAQCJbRUrEIByr9/3bf/md77aek7zbau73bMvnTQlSwNg7sxwMfEsJ76fMyeAAgaQVsMCVkuA4ZWAAEwUwgQgiywTI4gEdNCmD2/rJ/vln//jP18/P1immFgiDAuo+1CyPhhcgCq1GwpN0KaQTU5raDdFjQCKio+VJ63XE9CnfV+/JvvNnGNs6iUtbTHEOjs+x2n+4n3+MtFHvIxCMVJFVcH4qbsamBLpipLTd7ropxi/hL9XkyFgKcJukirl7BU1jJT1FvUNS61rtSs30qa2rK1fRolAueOBGMDAAAaOEQAiRogydaXBMoABBAECFwSAQABffPH/ZNegQQDjdpG+dy39wYNNdgAKxSVLHy73uuhaosHGVAgA46upmAJVo1JkIhod6rNmvGybnMpIsbYfOfMAqVupvSBVVaXsPb/muodf8a3YkBvW2QaWb98uunJYo9Nr77m771ZqvaFx/v+2gwQ3+sIDOHPN1jrrrXa2nzdrc383QVHYbAoWmVkskKZS8HoIgBhqhfDcKOmqzARAIJANtfbJq9t/889/eH7+973dFtK2U16ABHyfPahPXQyCKrVbIAAMelo41uiI0KYf2SeZGBmF67m2rJynVqUjx+uXz7/O0/UL83Z6rkk10vff9S++5fzVR+9/avWVqBisqqpI7dDWcxZcR1y9ho+BCFS10mqDikJazPSktmQ4EU6pVqkF5XAOXdumqds0RL9d9XJv8oFRUY9yCSwPyPiewm5Mr1DlAQwMQWVaFlmhrjwiRlwJMeX4MA5gYCCAZa1ABQaRPvDwP8nN2qqu1ip50tfs8OF2ThNSTSmF+OeWGhWpDzBlmCzA2opyjKJ7orcbhevab5Cd8662Bs2EwBGX5J5xq7cUxVR6aqVxgKiHfu4SgdWSpIcBFaY+FBfyLhU8AeQ5sfaNNdXdBvcIDUqek0BkHNzxtE2u/ph+9efP89fgsk0JJsAAVhizLRqAZTasXp6MMA08hwQGUAAwBpR/h/n5Hz7vmr9/M/J8oNCSgkRq2ezpReT9h+HBMIKNcwf14//v999/4WqdiXYWqFQLYJPTSYZbmE4Roa6yp1G0Xi8+/Le/7/G/9t3//NPP6vjuQ0yed+7F+VCtEe8/OAtkczPLlqaKuH9M37Hn9fxTL9XOz+ZXv+uv53e5zW6wCIfR/M//4f2v/zNwwxQRgyvuQIAALBaLAMMoRuJAnIt0RooRASAgBGUoCOAgn3wCHBEYAMaH44gjBHN0nnz17Nh0r70qmKIhjdROs5V35wQQN8uFjczNyL5y3SgYmuBlEddv0WsI0TeEDmgNXs/PN7nr8KhvyredKgHJOeflMFmnmuZ7zfrqAIIcF2YLpFUgCsejU2C7glfHoqEmcY5zzp7zBnKIiETAucKYqj01LFq/89fZjK16qRWXyACgGGb1/zO3RFagsQJ7HB6T4HIpNWQoiTCWEwA0AxZt6lkLPHy053mAwZDUMDlUhEVYadoAoRqQS4zX3nf78FIqLbpIWMp42jY2eAYwYBSA1aMXioe9V/7q1774Z1/SW+dmrpa1MmxwLywVM3fLLhtG4GEPM7L8Oq/fgUIf7zc9+8XktWg17+Jl4/zv//N40T3qPk588AABwAgAjQAv+BGMA4hOMuboMStZZBlAgJzISyJxHJcrnxxABIAjxgNHRByB46e7X/3nwbr7yi1pCiINBKhLxbp3845YpotJxel8t6r+d/C+EAqsTFZH87kKV+nKKXThWcf5yGlr/faTUni4F22qvNgClh59k6p2v52AUVc9xIVesCiEEMQ0xwjHTaeX08XZWJypoZhZbAMjpDpHPdgQZgg5U08WRCoGAdzDhNdAgQGAYHhO0wTAAIJJE7yvXigDo6f18Eb+58d8cNuyQtMCilUGFoQBgOqkK+ComsB/Xf4fdGwWWBIGxFTiGawBMUjAX7RHxmFq26o59Kzew5IORJ1sqegFxfJtbmPnOVXyq3768Tba/FEpuKZVYJCn8Atn1+pnXP7KIEbYKJxDFiwCABA+1EFaDmnEWika+as5OauTlwcixghZIkolIq58EgAicLAbQATKJ/L1gPKuxkMaJKWBxFDyq9/Xm8cYGxlnu9xcrsYlMyMaGQAUWt7aA4xbWErIwT1StjX31DGaV/eV+2kwY8scrKpjtif77PuAqkj5uA0vaS7TjVc4hiqQZk0Pb5y3sp6aWisbWGiCh7bToM1ZM01xALfNoOnDjlcRV1YQFi/RXhNgZIyRGbayEViTzGOMMQHYihiC1csYlCoAA1p51QdC4Vf14uWycqeGGOTNBkZGIEQQZWUrDiAEUiot8YLu6Kzd066MCAPKalciMGqt3tRQiio6CnFjpC3DEAE1cbSiLBkWGRkzT/PZnpmNjNeeqj2tVTsCnFHuxS6b8Vmz18ixf7nXFWrBHlgLAVhQiDncUeJUs2a1/hpxgNXDwAMDEQAeJ8lxkErBoTIoPTlyAggUoGz9ruqZHwylPdZWAIEwqNxc373+Tje8MRAGeycKmc6OWys0ZDcDgIUAtLWvU3ic4GlPKc3CEPMtGJUQ5gseSxrnBCym2S681+gztohzvKVXTiX172EzMJQgtE8OcvcQ5TbauRuARNyCRTdNhXeao6qmYkzEyhuEq1QzwJsnJQQwUkpYfYdkyWCQrR4fDQAQPhYBGMCoZ55rzMelpDwI84e3MZs66AjFcrmBKm4GUqkYI5UhlxQSQMCmuior90o1AocYhaqJsaqp52Tk3JhWrTIgTaiE4xqmciYOCou8lDP3DMBmDkVjbLndUbeqPTbJgKAwEFdaNEdr8MtE0jpR7wYAnmJKR3zuyyUiSIUVKBDEeIw4xRUBPiRxBK6Uqc3uZux/1I+/PwiMMRCBCMQXjx9oyZ1VM36XqihCMNQBM+4QbGbuMLjCkii+xTBmK6CFdfZE1d7wjztBDm3aVy7IvAFLO6G3ZJ4bewZXyVFfkqCiCH3/Ew92YkImPvvj48vKMFThaQkmetkN+cxONDoDAEUkm7q0NWc68vkKVHIg8TmiIfdPuFMVt0x+gkg1GCRgBPY2vPVjDAplQNtjTFFkASIytixrAAwARqsePpgUicNmOdtvXH1vvjiwhxxX3oHYuh1cthHixAUVxHi8No2CBDQgFSQABVOThqmSSqlD9dw5t8EdMU2LKk5ULGljyJUcMXIRKXQAGgzhADNY1iB93Y7kMC5JACITQ02MCqULP0JPevEAd+uB2iLgYsFq5YNsQq15aJ1cAohAfPTMGVqJJMlxAIHJJTA949Pg7/HNY6rIN988opIkuMQpdU2oTN+y21ovUtbG7rXa6Os/zefOfLnwxgdVZVUrOrF3QOMCwmBv1aYbDFpVYVvrxBZa3nPY2sCJsLzFkQGTQ+deRxLpxm127X5670+fn9Xtj293r+zNZqei6moJU5DpmMkUShOk0MR0gkLpbe8lj3l6RaYduwObYXZkDgpsAsgzq4t79zEAJpAYADBYNQvhM+GdVvgsXGwvXkwAhMIIwqvtJ9/vUx/FOuy5GSkjstxY5cRlIkJRhmu/OW0QuEAVgIa5NQVq6oKFyjmi0eFPF5dJUCsOC8SpwEIHbIDY2NiJ0KWXiRcL0zLcIGizS6vbw1vfWWxACk4grTbtUGKE7/oN3A1qJnk5135Drk4HDFw2I6l5/UlwCUTEwMkFEhEVsEFEIcfVkwDN0ADG9BotSZJK4Jeo3DYbnk3LnFLSdCoXO9xfrmljU5DLqFs1UaX0AgjAmCBIS2Em2DdIqN6IFq65g2+okoP6uSkAzXlbveGoV1KhyrhHbTGt4ueq3Pbd6o89rVwJWoRFiNvHaQHfIs0YiKursuatWrqdIUyUXide6fuLp56J5MmsoiVB3mRjmhRkwgrATYlAmwHhJ8fGNh6w2YYZtnFBmOrwwQn8aFg2yNP0+bePDUXP7tmHFZ5zQC0XCKIUMGKzGMbg1lBgoFhHIVWRKrCbbDFlmxyiabXOGRQQKaDAwpAMIRtD93hoTvtkcORfq2RDF4xACy3Hr8F393gRodDIEemtAlZTLX2FPp/hN8/0YYpRff2d5zN/+ahOMbwciJFBdJSABGIgjqhRPQAUZQAI4FNOj5XjQC6apIIHOVjCUgzAGUh21m29W6vqFIca2JsGUlhsMpGWBcq8ssCCADCtZSLZAxrb8jkN2IUqEFttfnGJGWDsVbEiiDbyxNSmUwGSk4Dcopdt2yOiBg6Y933fy6+v8/6J7vXtvfbrPieLjHaPvl+YgF8hYxCxKouNc8TiMNtPHuBhDidIGFiAQcQAIGBd6WeAzVrCwjAwW2KAhULrax3wWhq0/Mt/7pf+XTBgQDISgGIQi9zxGACBC1HEiLESE0TEkR9tH8KDf3L/7u7qT3R/2k0KrvEcS+P+Kt6vujFGyBQpYuy1xRoVTPHyGAfD8a0+fWKas7oy1AEQTPeM/+b3fdMdObSP5RW6N0gIoZNzqc7aMn7OGEAgcJyeC004AuNxutKM8RDgn/sQt32RZFV3NXMRhoAgFABgpADFGskcvVzXW7LagdS0gvdf+9NANOAORXQVKUKBkhKAyKpVmkpvzRMjpyDLttufvx7Gr5AsgYPLUY4hkCC3uIiPFVWGKYIs7s229quHyUFIV1V28at+sZZORJNu9whTFLzvfPv8+ZtQqi39wL5uHYpJtBDVW+1hoMLDARQQwLSyDlisVTowYJoeAUCbstXAIoJxBausxgpVAFiglOZdT369+xf/+T19fEXF2jYNkSguW4/dgmhIKkaEAGURYTYByI4g8DHh4/1fno9P89X6Deih6AxKz23YwG3OQyd3mGopFLfVbhvezmKVrdgMPQBR50+fuPWsWKC2w7ZqHmzDPQ70Tv8mOPZcEOxaOJ3f8hQk3eDNERhjDEQk6RGBwBgRgBC+3T8/5P25P4Eoq2QIgwAEAAAIACaoZlrXyoX6JSRRXVoyMr/7LBuDASAFdWWW0wWEEkFom602UfaxHz4JJlbbVt+W12gLEsCy8dhkVWS8uJVucXvkYuNuF/BB9/Z1BaNAjZJQSeTbql96EwjJBX5BtDGHSJV9NB/Vjfdj410mdYIVieguOShKc9vTY60UVFkB6uJVbVnABATeVQeESdlkGYEBrMwYxgibsCyAAmGdM/qv//B+bz7cZGYSsDYtBik4Sfd6YqsWYHKF4QgB8JprH2YBsKa9idz/+Oavv87Cl46ISs4ogNTG1lZpNtq6rRWL2w4i5QG4eYnIzJ4+gx+YjKHhkAfoJgtqs+pRrOtMsHwJPxBIPdDH17jjm69lSj8cBUcxAyMCGMeHIyIARAQAfvr4qRxoEXNusQIAEAYKACAIAPit8uSLOozUrSQC+yf5yRwXRIMyELriUgEK8GaMq/U5azwj1x5CoS6lgmQXLueJQSNIBSSqNBwAMJxaefI4E2YjqaHSntlFKJH0Qm++XBihKFi4SSZ0pSm2dC8MVIBbdK+yKJoT7RdalAs2Nn/QMICBAhPfQQEizmH4bMCwAgKCV7FAGMgATBEQqAme5/Dm+3dRAGBQIOnmnKEi3U2e9lukVxcAC4zhDdtZOQIGO5c9fyJev2/vogGqbAhKoEbmAhlXPB69U4ci8YTGrIWckY0LjMZh4RbfPFWuiZ9gjzMaFDW0yXZneaURGuWU5gZlHd88HhJjBGQMDACID3EEMACMAPDxRhCpjjFJiTAAIG1M+F8QxkQyGdjqLO2QmlAXr9+vMQ9wYapTlcpG6wJIYeIQhMVopX5RIYJKjCDvBl3wu1JNnRDYBE4jV7EMgglSR9yyeyt2r2sITtS7zFpJbtErTLXfXiUBioOAotwtS/Su1QuirWkbAUmu7CtuOTer1sYZ1vofdd6sMQ2kgTF9PyIAUFkWAHksjJQRpc4cZAAG1AkGMwDLYpFSQEPcHezHrLXNdqaWpEu7zRtalY3ndX4vpvJJyTXt4m3TGCDhJfP6tv3oH0v99EgWBbKSIxVKMlXXfux0am31O6EUGq3hiO1+EQKFYsw8JXy7aq9FTAlM2IjEwa1VuMJYh62FAXoZ8XF87jDw5g3wzTDAAICUsAkEDnY+fgiw7jbEWDBzOISCKFgBgABEspYttflcDmBxQRjP1gfMmPIwxQA8LnMgWLkTAIxIWHl9PRpBgAEMwsTse2w/vXf8ZzwNi88uiYSShTxrTxJgGAL4BE3E49DQ0mkXOG2ecsabDURdJlEcBENWgi+AmqiYWlU3YFDK0dHpBL/bs4c4Videp6IEsCSrzDbJekABgIUiYogZRIQiCKACIni9GkiGSArzVZLrm/vnco97UVMo7avrmmNg9L6Wj9/yFx/hRXjdtztAFtP4q/P+9no8dZcfd9N2FSUKiKoCOgoTZBnqxHWBlgWUS8HkcJMWpwhAEc/5wR/XH68/rWHCIkgKiGWBhpeyaXW2aMHv2Gpz/3z/nu/KYzweeGC8AYBpLpX8sZzNOGIEwiKc70OelCcBocJDTlIIAAcWbXl0w05vta3jXC/+d8xqtbpW49TOqmvzms2dy4FVpaQKpQBmGaDNWv/lMShsA4yhFu4qx5r7a/23urgS3lkSMUfzmMUlXGWMPTqZ4xjuQltqNDvaRdpLa53aSphILMJxAOCtUjOF8MkmilbxVugUEwdRTYK7V182GLf+t/lPsS0QYCzLGOpWqSrldCB4VkeNzbbHCCAiQMEhRFYAVlgyCWtiSRXpKiDs4yf3r19cWGG6CEcm8xijbTgYX84WTNEszmUojrbJT+ta/CpvfQYESpQkStoqV3JYwriB8dOZDG3OIOkDHhaok2OE48D1C42sjxXVXktTJTJiGSAu4ypM9AVCdOhx6u7Nr29v4+XN9zzGA3FBAA/8kNOIwJEcRh7HURhF/BsLoJOb9x7fSbO10y8uAMU1rG4uvd49n/nIt5/LB/7e6bmjE90EVm/hK92kXvP55M6Yg4MBTATJHQChUi7ivb98huMYOVgSeorONWzuDxd1kHu5S1FOPVP2VTZ8FDFUaRknElgYfq7LFyUCkaTpQmjEwgAHEJhjVAhTUS2GwGFSQAdjgyBh3MSby2E+Fm3pygBIsMrY1Axjlh2xCRERe4aByAAQxxSQCggfmxKrCqqAgAxw2bfvDH/y+b2FGWFtv58CU8acXDpHqd4v6Nrys3NKAp7tf/3vL1/Dte/tq0Y9AAUKOJVCSPEcZ2Ao1Rq6pce1SgXZsQ2SZoSbR1DInC7HTb9Ikqzl9Ai/IQt10CNlADp6Q2Ve5Kt65fmfPo0f/7ry8jUDKAURiCM+BAJxMgK2uB45inA83/nNoRj621c/pr8tzjxPY6bF0ebg8eLl5Avf++Hdn/zu/Z/n/aunZt+XUUiN3xSL8V1LbbiZ+tEBNrB4RSWn465SAKVCVlCSSaRAAlBU29rWq0ZJAkgErMOS0lvY4Ks4O7mwQkB6JzsV/ZSKlX4XhQQUIxQAEBWK8WIDRCwFts1LT55zDn4L3ihYwDCPbEUNNIIsNlexmghSmwaebDNLxLZBoigzAYDDgAmg2UIKQKCVAgpAi3l9frJ/9Pv/f/B/f/zNv29cbgMPrjRowEMNXrqOBryxli/bQW8MTUurCqlBpI35Lmt/OX7vt05/8y/jPgplUFAATd72Ir57H7u5uef+vJvWt1/dqBM7WACW0nacpIBFiaZIkQhIPsjR/qB3WDpFlIN27CiyKCMSqv+/YGJ40m+dvfYmpBZKUIKIAACCEBCLBoRCQRCCBQpQVzhCCi1CCiaUAAAABNC6K8vBcX3PmqF59rp4bn7gz/6/L3/5G34ofNjVayGfh43KZmbrWGPkjI66EBwslaCxYdEbATAgAIczOHPmbAEglUStYMNGUADhKDWJ0uCbnH+a1lQg5I35NF19szNOvD1BiYnVD+ooMKhFqGoNLuAXADRX2pJ4mbyPvr1PuBAV4TJHwmUAWaCABWfQxpAo8B4EWAwUIYKmFAQYagHXFgAlVbQggIm9Gmc/Y6/5j/UP/+VefVkPjZPy7MgsCkN4TjdFYUCIQyjY6gGFDpX0UruIxUNJ0+P+R3P0d6+GKQwIlJEGUUVz+7VdOyMx2HueXo2mcENbxBxoQYqovlxFhqlwLCJuiWsaf5LGM5qbxjfQ2GfvkdPEiUQenOaYyPeRL0GMdN/QNZSCggEhAADCgLSDQ17oACACBDACSNqpCgBCAiswSgNIDALpz3O8Hpt22ly/Hm978uTXv37xq/JjL37Lc22MpbaOYVlJHjHc7FjToaG5jn4RySUABsTN4SLGlMjaDFqtAORYpGJbNeA7cbu3Q2Q3Y3GJi7g5f77942m2tDve2HIrjm3cF9b522aarE4OjbUCgREARAEBzLJNjEZYNCEltNvNQBy9JIDBRFAZYACzup9b2Z6xgKXDJd4wu2ZGoYxChqiKgFLFZKDaAYDYF5SApJUKAAPWt9zv27YM7yYv/Xpu78qEvVNQTF3DIqaVPHNdfl318LfnF20zC7GWUWEVLNzy0hzxv6e5w0n9yyeH+6giEyBE0Q007dkb0qqE3ukrVxiXa+4Rw6TbNer75pTWEUQ72cfgJA1u2vq+dPIgzYwT7S7zqP0o42fciCVh6E4PdKcfeNNchgZAEggECsJAEESp4EAALNNNBUGzBGxt82AAJDBFAZwmlIIBIdenm5vDY331OsD39Kd/nP709Ls9zs/BXllKJGQo0YKAcGmxN7kLx9xBx/qVW5GGBmxliqyBd7GZWAgAEurS5X32Fl+1dtsimj3pxQIvnmnW3z3yp2zrc6i9UdVZn/J829b5FS56nza9rVdaSEOohSIQAABUajuDvGfJAAy6tJwqt6UXArhuYmnwyqSaYcFvHwMBCgEgAMiyY0BhFZRoLdjGBbUN/BiATakgaNlJfbfkynOztXMCS9M83fzF/mX3/edvzWd4fenROk5bWTXiqoMekyQn6Pyhj6brOhnvLMUqlwxIC1wSonYleOt3tVJiWrl2rNZLhHnNFLlYZc8pZikQOYgaEGQrTDPJ524lBWokuinJDCPBCdIV02DA7WPwS2s7pA1KAFwYrSwYGCgOKgSAgqg4ACCAKDhFAClQNEaUhKFtiG5DMIye/1CEB3/hxy9/MX7f8v1XVnXcq4oCgFBsAVhaUraQJWsTB2bn7LPnlhwVIATbaSO7PcBm2xgcDgBAk0Ua3BOf9enfpLvxqhG9l+8jeF9NmqK80Q+/BxG0p2Xs7C37zjYjjb0ZqBAjWmNBUUPgBAAEG/vNU7P35ovAa4IV6xXgunb7CiZenxHS6gXGxlwGhlaQoj4EXgkRCwzDqhRRVagDpFubpUgNAAGGMFRAA4OKsMBX7XK+n+3LL9ExbdbZ/+b//7+/JWB+ftCrogxuwsM0tKzKnn+3xUMzV+f8MNfON1s+j8bR0kBGJhRFSkX2cvGy/Cq2QyzEw/TCEFAHtVhFtHLL3EpRLw8YIS1YMsplQAzHwbiUeTivGcsZDvbYp4qWVQoZSu7EwDgqeDzMtN8jbWO71CULB0cEIAAUhl7yokNaAGHKABBUpyg1hl3DmVtPs/ywZuGPfnr7y9+vH370W+rmrLJZXagSQEKxYCmwRK5skaLCIueUpuloi9+kSEBmw82gQcBqlS0QUANCE0lUpx7ex9Pq1Xt63xRG8v2G6EfPItvAIXHhpNOyLYXV8ZXuRnUp95iCS9vBju7oQidonbVZ43jYhtv77O/ym/XOHwsF4wyadc3DcAAXzFlwzEsDTD0LAMQpig9PAiYAgpW1igQJZvIz96Q02VbJFiBAOfB7K41UhClBhpUZRHaRH3gjz5+/Rjjrn9+/7SeUYYZDSE34NWKxiUGorsNMVl1G/a1LIgWggVGjiUbLatJpjt8tNyc8reB1wyQLCVEoVW5XylQ3tFGD4IQoOZaDxUSNLdO0zIoXLA8tTShQEpoiFWGHdk9uwh/7+e1wznRzOVk2t2dvySEoa9WsFnFZ4qkDgUGDQgrQQAAAaEzsIOpqKB1dsjNXj35r2NvzzHfNOjnLJcekbSqp4qoDRhRQsBXAwbLBMnKkYxRVbefZbVR6dIFIkIYtWoCxJjt4S7ICgwiVZHElwpv6yxj5ntJ0fM8d8Lk8bV5oKQRCJz7kKa1N3x+8uAciECdk7PR3d9jTrb059bCO6z0bGu+sXLvfm7+Nk/2G3mAHph2Xb6d+2+8ZI8Os1QH2MDdtuG+NGWyxFcH7GAMRwMQIYBioLYt1putVP9dJYQEULGJbKM8ChEE2CECIVQ4lA1lSn9dGk7y7wlY77hn6CTXMBAyBZGvqEOotfzBotz62ciUbqagdAiIJ9F7OWK24WRjoixdFmOtKyOmKANmJW+asxS5wrDzBlVYamrEIG+mKH+WFeRKjssTQTicGAQOlDwaA/IB6qdN/pS74Lhy49/V4q3fnuP66b/54e/lyLJkJjznaI35Q1heS/kTFgcBScT3Xd87PDvTtYBnoONpnS87O78wQSqVmsngn0EwYCdQSlkbUqIAtIGOQMXECY1C0unOHTTtWFqaoyzRwZue27waANe2ZutIAaOhCVJaSUK6ZJvfx3GLe3v7s+/yo2Y3BueJUrMbUuGmWAnWpaONak0AKMthK3bMPx9u1334zJzv9Xekrr/Xyrvolvf37db99jni9JmLWc9avf9ZjcKyuJxgsPAWDdq0BKwOaAChFBACDMQACDAQmStj1l/qoSYGKwLAxlrrzflNe1rkBKAwqSGkCqurVYSg3qqvRaDyZ9K7ZbQqWvSSKlBJmz1JrYnQRpqVW3T7saU/oaosYXLFILTr3YamJgH2HqyiURoTgKHPBcTQVrAuFOpZQbV3ljZbz5uQBKkbJiRTJrYVYmXiiiTikRiOJ9Hr9cx/7GpnztH/zEPcb9n7e+Trkpb7O7X1/8+X28v321C/27492c5TLmvij8wtaVIjmxPfP/PDr/uCz+Xp1d3jqoexxtDrbmNWEbwhE2SogQFijQRIglbgoLSmgjMUkrqCnu/uKgdM70wNPpZERzDAAWdYwEYwWSAxQwMZqAICaIjQNcGk5EfObt74+NqslTWL2ClFUT7uWbPlWyNqRe3ruKam83zIHU9hHr4MO/Oq1uwImhSv+3rM3vs3u6Zl7Z3qegdZkF1bvuiE8iOEcizAvBkpsAQAmgoGaJkpVAWxrM8RiWKGFFRACRy/OAGCgdhsM3dtlnyXzGkNGgARgtdHE0xMyvbknBWyzlHWqDWRrPeO82lS0Uo7fxu+EX01njdWLo5Fu1WM8baWI7appoNab0o5FbSLBoVNGICozUA47OsGpkSSXjG6ovsZ1YecaTcU26fX190nO/NTvZFUzROgH3q717x9N/0Uqa6gYBGEyMjSpsaZP/fhfT5+pb6bj5ed+4E9+c/2Jp+tXLM0dKyiLOqJxd0f7r8Sxj9Mla/5w1oeN3o4hS0oJDTuxhABG7ShpVLux0WWrWtfVft6QClPjKOe72iqJoDQCQBELw1MLJQAAY4ExdbE1YmqIm/1VlTJw/Mb7IiWxWiLrwYykJG4NWzhw53rnewIc8zWK3sW5kRhg54jRiwkv0+Wu7BSs3b3WRpUufGsySovXrrC2v/Jrp+EYkSLqIYDtG5eMkq3ykSYEAAhKBUwzwJIRrQSayMwzY0ADICKrAAJiJ5Y2oM4xg01llbFUb62ANcI6foAf2wYItWM5lQXRRdZzDvye9Kv8vnqdk91xZqPK2GyoO1BuJWBud6cAUHJoc9sBy3KrGKx0ACRlEMLSJTFxB/Nd3c7V12TiuGDPStZ/vVgex9WNClOwob58rn/6Z2fDjYnLKFJnzmE/XHdizJJtVK+43zivNs6ZK99vWd+dZ+d1d5sDJ19Z3volsZkWESGAwx1vlZZIw4JaBBCIgzowVbCADZgKZddAQQM5bXFdt94G4QBgs4EGlm0BhplOFAHAkrBnbnZf3dZ1V9oPYUkkDOaS+nXfzYQEhISARXzi3vY1ZFA5Fh3cg5vFRhC4aC9VOkggqykj1MtT+rNdCU293Zpuq7DqGcdLOyXA/Ll7dwTp1ORY5mHAMBkE1rEgrPA0IKgqbsYAAlGWdgHDWYitphUUgCUIMBCAwRQAlkQVMQdncERjiVIl3CcOaZwXjVmT0J/QWokvpH+hl+GYnGBvnTtu+7zL5fJO6uL2LYuhoNLpo9XR8R6dHFRrWVWElFU0gTEjQIlYtqjYMT73132KKQvqZu57/Ne6El6MwRBBKYK0s+pfP/G2prg31LS7sGsfzm2Zz5K1U8UWbT1Vu71fNbfXrvPo48L+v7I820NtGZVtpmsUGhp8tK1Vio+yFIVRaQ0WE4XKKAAzkCBk622kkvCEtOex7pMRVAJUYnrniFRjmMFCABoWumVfHj7fXtjWbVLcfnGciFhhqfmyX21JyUHYE1aaaMM9bU07ITKrQ797H1zl8w5RgYi0d9Jl32YQzJK3P4+/9VtGHeeiS9247GzzOEq8iO8kLgtrlrTKjEjAMAlxDGLqmYSE12jCFiB2M4yCMgEbhkEGyAwzWWDJCAUAQ2FgSUspVEkwwsPkTVwPU5eOyxVfhjqoVn9WDYGuX7BfMMP//2f62sSIJagBvjpzN3JmWnk1igOrIM7trNaiACHSwbKFbwJO73pWG1ppfCLEb6MtV4hldXW5k5ZSp5lJD/7f8cObYkxgGqDKtizvh/93XqevqFCVxqKG2iakqiTW0BxMfd6bshZtH5ip7o8HYxSt2+lD+nOrW9h9pYU2Hi2UElNEclcmGzBuBgExOjCoYwuAPTeQOrqriNMaQkEI3grDiBLYjBFoAADgUF7DM/ejuT/os9VXJ8Jah3Q/OBS6yN6Kv5PNivnljrq6Sr/7+5qa4yISUO/gnvrI92nUT6vRrbFAG2QQcdkJMazS5u4xN57zWbaroV6mZVAYlEyvSjcYGMhVppoGAEwx6yKIWXJpYEx4GoBVZrkZsJYAh4kyuACCcfkGZ8EEogJbYltdolOAzUYtLnRqbyZPE13G4HYTy+Ks+Trr4596+uWarj+D4L1//3//L/Yz4/sROCSNAJubEaFyDLB4vUqt1nsnnKOnEoBSCkDhKTDNs1wBFJIEKbsbDDYPfuwmvqKuRBq0mRMRC7ElFCrTRWClCIQm+Oev1nPrkA7bUGxDSSiTKUpJ1TR3FYXW50O5z6yLh1+2y6/NYubq2UpGAHFwLBrVtAaKBTCIm2bFAlgQqJgutoBYrHBOA1fbUocRiLAxMrTQYGGBGMx1gabA0Gt6Qb9hLx7HcTd1sk4aTeGp2eaXsSxXSHuAy7roz6vf5rgXhh7B/K7t8Dt+dl2WX2GFo89BgxAvwlYKeSBlXNHzccZ7S+86SjqKWL7Oo4ewtybW88wATtPEwGJrgw0EVJCFWRBIeDUAtiYMtmAMUzFVBBMVwALF4WsOAFAgWlvZFlMKWwGUCsX76rnOMF/yrH3O/fn5p5/XL1c/XsLrL/P88/flleGv/+/6+JOXb1P+5my/PB4vQQICVlXERi8rqo1VWq2xeZN7qdHpY6NI0Ij3/Eb1bKIbya3CzdFDjJztrfx9WoQO6kyRBEgdt1PcIynIkMB0Ja2giEVQ/aM3ON+m8t6wjSW0KOGUJArSYG6vLnVaadRPtHKv/XR1O+neNzVlHjQAH5W6AlALUNJgYRawZKtYDAQMthdTLf1ub800n9oWZiXi/UCT3JR4zzSmEgOBgDVQ0Gidy528vrIcOxHqttFK0nHjxyVz5rAsMWo+usny3vYUp/xLiy6Qh52gRlfrcb7pzopltiz0k/AbhrZ0r5UCNNyMEW/BPB3IuUYjrf4pi4qdlPO0WQDViggzMRgAMrPiZlxdUe48wIoBwBhTJCyGMoybsdXEJoEDECv7ssMCAIiyXMU2RkqJAAoaau71yKo9f/PDBNSFrGkNzZR15u7qC9V/+6f/dvl1fhZCgS4gpIREqwVcwg4FtjU9/UoV0op+iIKIpcPlsXjW9toEk5hATpp6UpnLe/BnebqPB0GxEsJ0OrENBKWDpFPSaSe2mVIUWA61jOXvvU4nfjfYe7WMAEZSgANq21idBlakpk7Yq2joj6VftsHSqoAjYHErsZQIZABmgWE0NGNbAaJUzXu9375/2uwbqQ/krLvmJnqf0dy1s8apbA1ZgWmaMCRNgAqQlISYMoYZpa1AA5E5EAzkOcHbse+alV7cHtvpnQ0Fl9Juz73O++MrLD3qeRY9jxbbsaHiCpMsQeiWszQ72quBNtbjTeIPF//D7xxIL8SFeEI8JCJmACzP3Yt221lee5N7mhZep2kzBsQQxHxnIxEBCACtk4AEAGJ5p2QRRQQxGJGApZnEaa8iQaOQBEwVi9jMljZw9Xyl/g0jJBczSB1cOkk5x9/HjmJ/gAFrvPuTd4/b1n6NZvbLahRuhUMimrtbAgEScoXKEz3lN76H/rLxWifjQgPIGtPxyd/hzP32U7ZSNGIrIQgiIRWx3j98Y+kegQ023UiaxLfiAoDbnl1pDBCK4nQZcpZUC2uoUDupUACwGESBQWuG1gbMwoZZMUQwt97ta/s+/9d3UYTps3Y6MXxbA3kdFzvt+gZtBcuAdas52M5VkNJok6Pxm5LvM+vhZzrnXXv7lsm167AHEt/0i/rIz/Qr/dnuL+jRJRPzI/+v/bjdz/h+LmNyvl412rpku2zqO2M2fpm/1+u680Ydd3jpXNeVYLh6a+Piwns2fQsikiHO1rCHAYArMxNKYuHamBFwABAAlAg3AIA3Vxu2DXM678y4CSAM0GA2Oj9gIsAGiBODFhQhhhkVbehf058rZegeImyIGqYSVYuWJoutKXZKufmOXV16K5bl6WVqsohdBkWBCWBx+na3v9HdDOUvVrCUVxqpP+sDhcLASTXcixW74fBMb50RBgiiqmSTf/vZ+KNXPr/poNVH1NZrNncZs4wYBlBgCKGSfSakSmQTwERAaiI2DdsqsA1oCTDQWBYamDg2jgsoyAAU8KZ8F2f6e/ubdzzv9dPGs/vKDCPB6kyTAMEk78F3jTdpG17uaMN6MkkHayJl8q1+8TzX0Td7lVliYqybG1d4vqsBr4mJK4yZsGCGM4epGwaoESCgqcvpCsU4oCoBWC1GbHm8FRqDaLACkAHZAEYpC7FBieTimAYQuyIFACyXqDQzNSVQAGAhzuZofelcgZKFVuY2dMWsCyv0BNo6aSN+L3wH7kuUyEEFABWh6Egg2GS8Y6wT+eSLjaxayUNIhXZ6BTMLIAyXOyZTu/zkS5+w810krlQEeT6A27R0iTZjLJFM1VbqabywDN5UBfpPL/V3/3r3/t7XXKaP57Ip+6mp9H1QOqRXkWKJoyi6fX+839T+z78sqE1gkYIWAc2mFdtoOoyRCkbURFoSUiYoCAAsZUkFyK+VicOt2rs7iOqaINM2A1Na0lrjhHP6HWSAdLCK8TpQZw2nrQIeO/LSwLKVhIFdyIKkLIDCUAZYDAvhKaiAwgJMccjBsLBQ8DqywMqwEgAyGAABAVYzoGJJBkBqOzwAxFJWAQBQAowAFFCLiTRxUpYl4kBAQRxESDWnTRUtNB1wFW2nHfEt9RU4LFEiZRnLzXC2tkX2isVMb96iI2/fToHgjsYpna23e450dQCD6FEytL/Rna/t+rXv3V35LSoUDWuqP74GEUHBhrY2rzAejLFh6RWClFJV29vxwd9//D3nIL/IO0wT8H7I1N9Q4h4Ksi5EpF17rP8y6x+Ov37+uFv83iYIg5EF1YQwlgaFaAO3FTnEqgkKEU4RiFp9fixO5oVxoMPiJZbJChuIRpGwkxyjBaAkG6KBAsoNAEjSAKAC0CoA4tGQqER1OVVmZHoIqUBYFQ0CANRt32JNxriAzIBzq+ixOYPDCkBkABBBsC1mVZKUIULj9hIqpQnMLQkUAYDSUGAUwMYBy+JmK/qAkZWQG/wRG/BpjO62TrF4D1PowtF/PMJECpYYAIh0s+kcVmrxbk+qpt/5/TUlFi9X4knRAFMIUFhWD0aKKLo8lzPcdvmMqNQiit7xmYuYNSHbo/MzP/Pq1oDZijb3/C2glYA4UUnlnz/bfHH8zcGfJow0EsUBFFQgosNA6OBad/rPUf/ofOf+yvO+ag6g0CggBKmwwWqebrbUAAQtsp76bXkE6RSCjLNmd1+P6lm8y8PxYxg63wDABmlJDVCrIArwf48hqDT4oysAQogCgFUbfraCH8nJ33ihVhNbZTAYO8tqu9paCQaD9wwAlgFIAkBkdKTF6l6bGJ49B0AACtyBYQp+v9uS1lZc4xkoWjv3DLTrtnWaKaUdMPNyfZsbv8NSBKCnBgXRA0TyYSptRitm7+Eo1jSm2IyKQi6L5UCs0YhSi0QWSOxWLAo5aFNWEEabTFi5GC+/ZmzNnZ+r1dO/G8emtGmD7oBKW62//1T+7L8Pf0DXcB/2uAYczEaHdBgAmW5tmsj0+/eXN6OTsgJDLCmEEiluW8AbhzREaB0Qi9Rr52mlVXG5hIv7c9BXt+QPFFUJ5anTaGVToF8MEECEUCsgAQYoCQCEUVrSusANqyMYCwOQZqVdAEiywZ9g9YNX2cdcQSUqaBHMohBbw4SfzqTgAowSqxIVHM64AIbRzCClaTwSsZXB1KnfUwJDYGpb1pPqqChSOTQKkHEGdOY+xWjP7f1ur8AQjYCDgUOBKSEsTbdUNEnRhrgEqmDXqiE3BMy0zBA6DYM/8sQ3FtWrXy+7O3z56cEKshcxz2cMFqQu28XyOny+zg0WJxYNqHaYpA0aIo3n0uf36v/6m10hnxseIaXVA7V16TXoUEgpmVJBB2f2PHxVvHSqWuwAksBsFhSn7YrUGAvFwaCSWHZg0SjW5Ln4MfG92kyt55mntTm4u1ajXTDAKhBEFAQBKAAMZkEAGPgjoxqbLjFg9YA/0R8gcqNLxqIEWmAQnU7QRKUCYADzgEG5DIxioIgjs6iSImQCALAYCKqwodMmCACrmkC5H7e21E11LvyyyrI1ypWk40J7Wtb8bcq7r08qgdegRAUAAWTdNLEU137aqG3jybL60vllJ4dqx461xYtdBLDAZQGXgx6TuQN799s9R+4BY/GdKsPOnBvFbtUaKU58vHXrG0ZXHP0dzoB2CAhs0CSOU2n//m/rP/sfup+2f6PWN9HLPWq4wAqLEDCu63zUytvze+yappzXS0dtHYwhMpoEYbC07C28Na1UYJIwY9gCufnh2/3qvoS0wlLnb4qFwdS8hxoG68Zkm2gpBlNAFEQAGAMFkPZHA6ZDgT8K5oB+5YsY2xJjQMZgY22NWGa7tQKMwcfqsm1agECrco1zAJiNOCUANmHZAMEwNwVQolEbyBnlw/48+8wVu991vNZ8oi/r2y2/6F61vvENPrL629/+/rpxYxk4SAFAYmAl+XQLTclONUB6ttt93/m6A6wrOx+GhVIXpZCHcXnVu36HikahvS/7DVwpjB+GEIaDCjT7tXc8Lr8bnvPcHGNz8wxGiIgAagxp0/Cy/Ke/5X/234ffsl1ggzWoQszACIACykv4qCd/Hn98zozzmame5zVHS5CSVSAzpsO2C2TLhIWl2nbaeMYlq4PpZ8R4YbhqX8P32uJWHRW4IAyMzTq0rABVgMDvHPjjuTnP7BLYmA0LYE6WTTPZTAOA4Sc1IEQgABjGTDMspmqLkKFWl0RtwUiMAABmJtBcbAD0/R5HvN25lzUVppvv8YRZORtr4fVMfVulkV/8H959u66GCAKoLDVBoda5mFP1QBVrz1oryfFxuUblgEtNMV0LBaxmJkuRBHbW1jxCgtGSXWLGr/b7qEji1Rx7KCbC054bE5kyox4lg9/ivrxo0LYV/Dz1m6cV8xsXrgBNgL7YBwAdK7++erUIW5OmIpoYrdSzPi6/MubpHoVYZAIQLh0T3WBp6ywz3OhW9tvKpIOrWdkHDikRgANSzEbMclIpFMC4AMxOS7/Ln9AYj7l+DFgBMJBhBdqU7ASBPs2GBRQCLDMGgJlACTgKKbsy0MMx5JxMBgDAdHUCNqDo0tsPvv9Z1nO9DklwhJhuQyQGUpDq6sX79zrZa0MbIAYOWECxFHWg1rHVyea3t23vGBARL1yDqKphpT1FNKlY2zRKyHy2po/80FgFv6xKPOxIQQo1IlQiuPtbxbAJPOyRFMkpnh1jh/Wuhfr0unr7uG/746anGSjjbEZHlmo/6Fx8c1nPFDhKK3HihEB18qE/+9tf7H5Vf6x37TtdzTxskCEFNEphhRQNGr3JxHu8Ri2dGyEMXCrdVBYjmRS8MsCAVX8ljuO3taHAUwCsgVZ0vKEKxhgvYxgD0FEBViswrNWuBSo4iSexizwcBgEAVltbGXNVBGpFp9gMATIdYkTEgASFRmjbDDXCGrtDccmQWCIK3aWmMznJ17nYbbUg0lIwZbt8J/AYaocbqoggjNXUnstc/sl5JKiUH7/Zch6VcmSi0PJAiRmf5gjPWL1vXg7sRNpxzRU8tZvo0IP66PxweXvO9fx2EpKwbIRl2n7z3h9/lytJWgrYWCpJxLCcKC/FV+y/ub1WXpPDzBwwHJkkNoyANsBGbcalCnFluCg5FzBlBNhMdqBHJMBiKL9f/CGAYL7bHG4ABAAGl5vFmC1zrNpgmsYDwABYKSXAbjabpiAAc4CEkURpRIEAAGBDKYE57NaCwcCQcDh0u8J2cAqAWxR+uoWl2U/a7coGuBp8ME2FlZTclB0h1HVXOstZNABEscp3/tTcNb0Zpp2I57WRjXCaqzlJ+eYUQpNRlh3moTrYgyYOYU5k+n2wpVDzO+9ZcY3e1ZgplsMIAsZH8JH1QX2cdZ9yfYOpnerojguU3eU21/0P771a7KkxwdQGAJSCKe/zPf7+q+Dl0v4bF9LxYjPGgwpGS7GhqnXksABPRGFwnsKbNLSq2kBY9UXVUyHwh44/hHDGnpMLBSAUgMmuDFZssiawDTC9jRljILtQ5Z61vfYsuzUJIMSUFWVnnhwGgQIUrIUt6mT2KGEwSDiZZVx77qjKWRhRoIMUO03ncnVMp3tJUYtLERNJarp1lTXO5sEIxwvmQCHLXe9jaFzFIe+8Zo1BOvYg+zMRZwwCJfkWMsN7qHPfv276161+Yli7bIqUuRnVlnL53/XjA49YGNcwbXSiY4KACsgq6Vn7Q+zj+Am9aagWPT6JT6n3w36wW/jVrKlMAoLYMVD6ms1UNRjA+6+HmxzzeWyrCTQ0A0ILTMvQEg6NJkqoLNMVw4OBZ8BQDgzPAOIP+WMxztQPCjYLGAugwd7ACtAyoADxhhwApsGgWTFMubMEmcRACapODQAgsTUzFABh1CU8BhVro/VnL5wa7npsHOhxIOsSxiZqk1tJp1C3BgOtBGkl97UmvRlV4qzsWg7cdhhxxdsW2QbZmk262+UZcdGTRCD5DcFNXqlGRGrpnR/tKA+sICjZwjPIr9cLfuqpZ+o8bZQ5TR2TvYCCgaBbHeFUflf6Tak2rFHhYIiRHxH2p6+/uYXIJo5TqRKJGENBKV24RpjJnEl9dH23Wgtkxa2tqFA0l9kK59ZmZ5wi3M17c16tLzs2YQlkNXz+Y+KPgDkA27E4ggYsBmaaTJpshLUjhS0gvdUKgQaUwspUq2hbyVmDjEkOFAf4QQTq7jSziUzpEKsiVLoqS91jpsu+cI4HExXMh0Rj1WFFJUYDKGq5KpcEkQo9qt/Z3nZM8Grb99UxQPlubmvP1taGLIRizXPGjR/cuEEhvMEx47rzZXqtbh+kkqpPdiQGY8TTS0JaNH4N/dRajAFXoTJP1Tj1Bb1CN/S7xidRo2Vx3IBBhNL1/nJ+/uremt6tlJk0WjDIBCZkz457rj79Oee++cJcrtVQLbUtyIAc3QoGHb1sFk3BozR7J69y35423yqu2MWcrBB/ij8U4wBzai/ggsFTuzVsstIIP7+dAAMBQFTTYl3tUB6IGxzKGYnfQ0z17D0GfgkIAQCK0Wbz8dg/WS78GmjovNzWtOG2jyW3/O66pzRAIBQVCuLIrit162YnVZfe67e1taC4ZVMi+ua9JUFTGEQ2lTaiuEklZXhFR5wQdfnFU1dYMTy1qTsFhdvyW9jsd141svVh2HuSZAJFXoBx4YIU7MBV/ymygP/+ty3WywZVcQBBvK74+YtzP4cqzWyIEiAVQ6Ab1gGzIZXbPD+b81JvXz+yHWa5pGaotiCxlbePfPC0KbjVLrD3Dz/bWZwfTLVVmdzO2FYrAKthNpvx1zFlMGPLvr46XmMEAKHBho2nTXWJCsPNzc0NgrGBaXa5awDJxNo9m90Cyi1gaSLwasavGX6hcvOqadUxioeAks0+Vr3N17vKfTk8h6e9P5/HN/Xnzlmn609dPh5frIOtFACkQVVSe1bikoPTlYK9flWxTqqkVqGUxz8FMBZOuYzIrGeGCgG4M7YFUdREvRyBnF/nVnqqoxrv83imYWkl1aBjKYkoW3RTM/fd6mq1rKrEmpy8c17z/z/4SbVuaS+DbGinO5RidaQN+f//f989/tRyVhcoVQlAorqWrkVFgwwuR+TGePfTtHep+cNb0XPsw+97+5nD1SUcwiyf4RPX98750o/NsOifcv+UlU5vQetAUEcVniYApD8i/gAYAFV+ZbDYAoABcNMwEqsUFIABwM0NYMCAHQAJcdfl8sXbCgAwQPNYgOWXgc01q0HTbkGpSDCB7180L/OeS/P8qTrdyi/pD8e8H7d7+cvPHq9KRWVlUTBBwq5d2bo65ILcceZ05Ips5VzUyVCmqwOGUqWQZw0ekE3CODGqRCOiBknrVJ6RlWdtgiY9pvUQ7CgMiATHiua3GyHlzgptqTHU4pzRZmfeNL+s8lRXdZiv5BhGmjbXM3/O2iFO45YidaUKVNFcPUhcRIi/9ltp99Wt4AVUUSHk4dbu12x1zjyM//jP/PU/8h2Zes8R+Cff/uXTTrqrG6ayrLZBEYDV4AGA9kf8/gEAgCdchrFWshIg4W73kjVod0dlAsAYABAAVWAAdhtYhJE7n1vAGKvAcwGwOXxt74h4cbAAiSGoZMCq19PqzDn77Q9sMS570k3kx5HMh29OXIJBMALAhiUE7hKRRFG+T8cFSkmFbsdOUSyMUgTzTs2mUfBcczs3wDsLzijoR1WJ5kuhVCQoydUJOmqGT9pt1IiVSOLEyu0rZZpJZBjIjBRzaAVX/Z+ovyEbXl+KUXNZRxwbF1QqNCWCBwVPd1TUGaoigQLR08fes/rWKBTlUGuW3te/ONCd3oFXr49vJWdvD6XfPWvp26qJXIXuoUZkb8gJA2ADPf5aIdToPrsAAxAAhjFGgoU0ZgPTGA9mTYsZQAGOlBEL9qoQAKCXZ5iLCa8hEpoGyFoolrFzwm110e/VKWMVXxArrUCtulwSBBUNiqHQNlXn6tSuZNu1KNVSZffH95EKWeYuyiJRO12nKCFbpXi4nb8bW9/OsTJuFOOAdJsQx7SsJZNMXdSn+QlbCb0j8ShnbAkhTZ07U4bCVrQHRZpZQ/DNVLmE99Pqf5CvmaXfTuTdrHP96G/+x8B5HTqnKy04qONIb0JL4NwhaA4aPXJfmOZ8MGQCvIhExQbRiKSOQxaLiDw4ILmkMRfetpt35nRjYEVEkL+SAQgbmfa7FwUZY2zAsrrQNGxji2lYETFgNgPGXWNzuQwMFCEAKJnMACITAMvb5V6MMUXTxjZGIBhjWA6NAwdUrM6Hi4yaTrSFKwfHZwCjUS0ClBxYpK0KgkXQ576TkGP6zvtOSaeKsQihrjmlRGvX6rQoNIfh8FixdRvBnfLOeGdnZ7ZCSAjFOhJar40J2dlgnDSswmSCLcYoh1kNcrPMgvBjstoN/1txf4J/GYaU2zNLm97b9WyVGbYjt1E63PZxFCqSI7HSEjPlvpcm08QyYyhCYZWoKDFYodJ+mi25oJxRogCIILCBTidgACAKf70uZtbeF2VgpUQgzOw7tklrw0Q4BF4HwzJvGXiSxQDARe1nE6M5tAELAJgAQDQt3Ro+bgAAZQQhgjzh1A9lVuVJeTMRKE7jY2k4AYwUI8UIMyt2jlpQk8jVzR3Hh3jX9+0uBQ4lOjtjTJ89EVDt2pmShOZx0VxH37tMxTDONLKyhkmm+kTtQtrmJHElJq09IpocaQOiwKK+9F4lKGe1WaUAtdJ66P2E4GcOLZFTa/bcmnd8evV2cVVLY1IqVOIIXDEUGWUUh4eqBMdRwaxgGBxpOMoyNYCiquyhYJmSEuQFTbYJ2XeqBHrAGLDxh0T8bg5AFX+SMQDTasKKVXe7FzNzQ04UrRgqACAADE+zCH6Um5uFKSwLgCmDALc2trRtxQYJKzAACiorLdR+hi+1x87RmQUwrFk2D9+DAhSroRQqpCpQ3RoKCnmd+y4v+7s4vV9vCLq9TMcJaDZFCGWdidumddNh1GzFiXCUjObRrqVhSeOsTrJGV9AZ05i5kcHCiIVzHCzWfYXN2lWZCVx5pPhOP6vetvJB+P9k5AcxME1wuV7P70+Pm+MjphaoQVNUk8IRkQZLg3OFYqzVz2RVhpgyUEoBskQiSjIBJyJO6AWFUKTFYpMKJQNPw/BXi4GBXqf2MQACYFxgZNxahzhdECaSCsAAaHosK8sywYJSdr4ngMsdABOABmgTiCu2bOpaUmoKBAZtQ2xGj57Bc5ZW81a51bXdR/TQm9paRaEUg+mVSJEdE3WEgOUuKqXI00qhzmx+a4aOnXff14wZrOcZUUMIklBbGotQsGyQomOu3HEU1pdkzdRUKUvEgBySIzNCR4a2a2XMNIERY8qYNHUKisN+j+ofmPrF2kXhts7+u3e/GM6QRQAcn9ouUPIRgAPARUwbvZzi3ZaGRWxgUHRRpBgkgGIWywBce/tMZ9SLDIIJqQQM3rO/DkDwaZNTmAuWBaSTcWPMYKshEwAYABnAZuNiABhg22QIQ2wo3va6KABAbsQB/1+OGfoaJtib9Bx7u4RDoLHBG0yPuERb3e4+GEbqoLksh44z+zH8/kpuFStSspCVqJOz52ZETC5ayrnzc0Ogjt/ze9+9iAXEEEAUCfDGY3zjLcTFRWO92VJxde0+xyzutnvv9jvhmmsKHZn3rHnBpVm3BU7say4BWFHUezhx9YVEtB5z+a1P/+Tnv/z6TCp8ZfwlxxZAwVIKFBcgATbQ2C8mnz35JrhdcnAIAE5DAEzlSMDJAMC6CvjlTHNANlqVpTDYGAAm/DUGgpn5rF/UM0CoJgAw25bmYzs9Xi3De0RkqzGMAQCIsmkRCApDy7DlbTIVE2Y4gAAHuDyVDpirrN5Y3GgWxmcgAqMnWFrd18ixV09zN/Vrkz9OYh8rhpbDItjcFFWt0sSo0gFw4rNFYai/v9tDJ1f+b3e+dlcFgI3SWd8CF0/cVqQptxVhKW/sFqGo34OR293XSUZO3TaTuUG1Wuyufd7erfcxkzkNMKsV22o2qmtIU4ojunyYz37ID+e1x2clLY9LgQo1VRCksQY3OObEURwYVib9bl76hj8rkei4UIFW30EvMamQ69qFZAJEpNnamFY4p8DYAhEA4q8CQQCuGQCYJmCBuvpWtjbGMBVbALAxMCwAWLEFAEQTDAEC0PaVX0s2MiTMYMEYYMjQWJM2VFGC3e3lbA43ioKR9XJqza80a5SIrqKk25fCM9KRP/9/5xJE07EMxSp0YkOUJeEyOWdrw1sO1M9C9B3XZ1cM4JLpRCQcNSmlG0BpJQqCImNZdimUr3XtTjk3H8So5V3Larcy3LqHZYCBqLCW17AOYAQ2tgiH+obd63z5p77JGXdfRhyjTOAYgYKNIg24cGRkPrHxd4qpej6m19pFpOQUk4zLY51mtySGiYiOoEqZmLFUjUThr9uJeM/nCgDGFmAxzd1mm9WYDZqWBWwCxrQC1KrZAShM7OyYQnMqLH3f+9NdixBCAxgPSp6FDEeTsU7NACuObJKrNjaIcz3cdMtoaWcMw2oN79XY67lZnIs2XfhEw6KpnCABxRwEhDuv9OqJZZm533cEEPHu4/q+oghWIEQTSQjTO8xchhW/GBQGx9UF6uUVCy3OXpvifGNNUdXNBSo0UBgvgYg4QXfQM7PCAqqYDnSJGPGLP+/bv2N8C+E61RBsJycUtLaANOEIgQyztUe3/FTfni0v7TgSy4mc86PXkZDCWWVB3bq0HLEaNYxLNobZAJgeYwL9+UaCavkLvwcVgBKzgLFadzXbGixbNWB4ZwBgS9EAWyxsOG+dBPN27aU/dwlEADeXIcQ2cjxPGzjtzca85XxnbTHg7M2J7pIepxBxkbeYfmjsWP6lRGTt933171sTvbVlI1SQqBUYEOouHjVYx8VmPr5DsQOw6ujV4DVgXArKGdXrWR9OQyBCzEXUVNQyFB8lHFS5//BtNGaRezarMTOpbhXZfLVbO0ggEQ5B0EsDADMJg/7dI/3J/Joomq3Bgksik5FtoiXAwxNraEDa/4653/wWv9vEMgihQsmqbnCs5TCovj18JsLi8jCGHe0sjAEA8TA2sD8dWwKYNx8lLViAFc92z62xlzc/XtvHdYzBLEgRsbY23Wxml1XwYLC1U4obL2baXvcH0tt7vZTA2Ru54PnCVgSQfs+dXmevXmNfteu3xbyumIW72ciJMJmSWm6sLFO3MmnMTzZborubsLYPsdipY22ywQpUNdCwTEnHNUu+G4NoxXg4zHp/Th3hy0LmHgvLc/7z/dzdf7W8kM5c0cjLqltnsEAUaTuJQMMqHmo0kkSh/XZjzSpnLRfcE2/LaaLUVmWyGjsjbX9an3++fvDVmGzpJm/TMgiAyOhwShwd55zQxV1IEKx/lm6IXChCgBSXQ3WMMmm6iV3gsxwF0YCuggj85Gaz+bNRAaiGn8XBACuAIs1sDGy1qRQgNM3GGMBlXO66YbBuqZTOwtNh3FpuFjO72adRqh3XNv++AT1J93d8WxaENCNH/Or33rB9jNtXNYKyjbCF0V0jVI2Xmmsl/GymnIdtNf19AkSMprloMrdQ1rnVbTZzJiGvQ/q+vq9X7vc7PC8vBNJZ54ub0+rw5NEx93/tfG/WvEMBMCCym6cMFYeVxXQkZJlsUWjLVHsKSwAdoZrKFtxpZMpYaMgySgpUGqf/9DfXhx95G6GstMgblSsDQiAAbnVHV22dVTMOay28kAnfeYhiDT6d0u7crDIgpCjXM4vd2BqjyglQ/QQw7kxvAwDFHwdAaY6+qbBYKYMx09Zd12FcTSulzLCZZaxWK2yZMYYH9ipZKnv152uNyVU73mfX+4+r3VnnNTMz3Txus/Wrvov98t6+rftbX2Hi3/59m/X9roGa3/f36r2WD58RFYRrWDRmFTWqDnFFkIZ6vt9X4GJuU7AlotQUE7z+uoNW1SBFXQNq93XHhTtLNBrdcUYgv/rdIdr6dv1Zvto/+s8/ABcKMG92XqR2ZRJDxbX+UispPl+HPCILPK26FykltgbWTZmakQGzWmtw22iP0q5dtgl98T/+9jF/9X0r4NAA3sRtZVmuAllQpoG813bMJtlKzK6tkCeikvu0h+vQwPMcUo5xli6yXbABJ908U8HvHRH44xmA5fq1/WQurAIWYIVxbQKxcd5sJKsFJNjc587Y7NkMDoaKFSyc+lIPQbXRuP7d8dU66ZkUVUNfxTFOB+Zh3lHjqTx0iol7RJyapyT+NAr1jiLYkLJBlQIAKcdaW1M9e+cy7BBYp/taoiqZ6QLUdXapXTsSqN25Y0KE7cLd/XB379TP/lV5C+bNogMwOOOoMq5Qf41K5Qi2tEkrC1vJnVOvyyx++N/wk2v/EEwEZWrbbm51OZmuBsRdXEtFGx0RixgqEqzi6Vqx592/+muv84TdaaOEvRpCoggkwkRM9jTGc2516ApGTbitogKEMSi1sKgkymltHl3IgLTLis1MsqttoUppTHvKh6APEfjdif3MagSQXxtMIQEG7mFqyXjTspmtx/R7IwoqABUb27bLtywA4ODUlDFG7drXv3NgE+NgQ5wuz3h4a18lWtWpPYbmO7Mp4R4XIMaDMo6+sibRYMRKnSByElTx6QyWVWvXD9deAE6/Voe32bqaqCjk8VIEKQbllDV0KPbd2RkvTePgLTOQscSj5TN/nhuXtE9B3NRZMOUK20oTVxXfEnM6jXzilq/Aqcu5p1sxaPN1CtPluIxR4tqJs7bdMzlbenouDNr84RKoLUhPL8fqN5Gmajqi0TjEUF0mz8l04uP94KxXTmU2NQaf8046QIKLzKFYMPCAVTQUTkZluGIaO6u2AUAAML2gfPjzFthyPtShCoAVYBaam43hPUYFEuoAIBPYJgwDoJajDrG3BuzsG19fDjswNWVhvE3zqvXcnvLYtzKKPsyxNstZWeAkpAg8x3tx/uRzd5iXvcglLySIsUbsl4pTVI88l6Gc9SXBFmEQoECI4SJHct5yR0sA785141Hs3Mcps1dldMwc7Rjfk1BTDlviBD5BQEDWSqejoKXhAIgDpmCgWtCrnkaAEnNNMUwzzdnAI3na6C2Bn5vHHG8xvlC5ucnof709N6eRm+4lGxhCqQAAQr7IqSHGKrZAwe1B87CCI2XKpSVgCOnROVxFjG4s2ayYWDgN2IzLQAVkb7YPq/hzMAAVt17DA67ZYGZaYS9gotm6CiGIloTAbDABABwJcYhjbISZXYGx4wgy1elrmLee2lrn9iy2ZUJRIiej1amRi1slhfCxEdwBEN/DbV9nKPoi2Ca391QYNd1iCHK0xUhJg1LGAmz1XmyP9PL71Wo3uc8g8Kc7iliULovXfp8gxoMPb/MxdDM9z68CSdA4QQqQ0pumXSvXuWgwgH/N9lBXX+6A2mwQlLIiuqYiDABkr0JcR3fKVxeJavMukpytUIgr9Xz88k5cU2nQSygQQGHHJMhgY5tN5XvsGM9lZ1i6QNgJH67KyaTbztEVbWlKtYIYRJcgAANM+GzeAn/KZRgGmubjYABYAQMDAWZbzctJiImGpDErAzAgioRRECKt53UUgwGAjgszb71Xe7VVqtVW3nNqUA9VaG1cVLFoabzYKQmQhKM8mzAb8o7b1O21xzAE9rRiWW2plAdP6NPUpAmaxrJpN1itx5639vOUoyGajvMuH7u7+fF7VmSFgOe7ff89DD42RGs4M2uApBVVVSSKaDl3r1zEVQF+5ld1nfM5n6lNDLdDqIATcuZS4iAokC2sdesI568N3IEPKnxFg5G6jPrnN/jqO862K+3lqHQUdhqi4r5qYWSMSUi+SjNauZxs9dijtUDZoiInojaX5VIYhgkrfFkAMIxY/AQbE7DZBBYC4mcGYjCjmp+Lslsw93xlXqnUVmwwbOHm2ryxhk0epBGZoJaZAdtgDBWCLznWvgw7jkkiulAyBThTNc/UHCq1qpWb7lV7Bjqj1WZEdC68EgmY3kpQITN/UJd82HKKimiH3fIm3HsnQM5W0xGGtermOEgQWi/tcGiC1btelztsF1OmrqvT59QVt01tYYrxuvDDBXJFkfr1eKk6USOQqLTQYDXNcHWvNHBwweYpzeWalA0hGqjNOaxtrmGiMGfOsjVc2sNQnrYsVVVhzZEGaAXN0z/723vvu3tOqpS2ttWATVnGFl5Sv10r4+e0pDe0opWiR7tCUXgpkirCigxcBxITbiNi2cJYAQFsQqqqqrzB2GCAFZ4qfgpg21KO/RRoBlb2Oh8JhpVNWCWUb8ZuzLPtXgITqgFqAaMMdi1DB2iuVrM8j9udeVMYS0KhhG22vgPVuj3rPh2uOXlwCKqkWG4rNGGi8paL30orYg41UEvmBkET86DLcn0wrwXv7hukl/397vUz7/Pl0XR1Q7GqcohAnS9UdYFqkb1jeOMJ5Q4q7kEKWHVJxMePV9QKcEp+HgECpiGgIMDZWUortzWpFHzhTDnAwbYdjhZiBsDEUbomg0MmR5vDZCTvEG2PsslVUCCRpQac+21/18/88Ob8m7NpFCv2WguFe7eY6aar0UP2fJlJcwg1uzZKul2363NPrnUcoKnaWBVxOmcBC9mUmhiAAKKWxQcAEwAJAGjkJ2I0g0EZIGDkDVExrd+OAMDEgAW4ML+bli1bAyQhQQg0tgLiTLuNOuh+d3931yzHxElvbR0O8J4xAGc+/YebXvFntQB9km3bMuml0F84covwmjU2Nh4YXEGOr4WI++LzxmTNc9EneI2TMW9duozx3d2dBQEkCtLjNgyLfhdTSq0SW3/Wn3fvtQbEMR2SiNWL9IlSGVBiCgaEiKqqRcrVUWPdXEIkLp8pF3BHbSiLDBZSxdXlcql4qlDEcMZYh1DmdWG9ScH5HnPEBWzPa71981+8/eivfnz0wjTc267kAMafblmQ9uqqJs877kw2lRXWfUq/7dRL+7Z+3y5E4wBrbEUjcZ8CAEVYSUaEAAAATU0AKgAAAAgABQESAAMAAAABAAEAAAEaAAUAAAABAAAASgEbAAUAAAABAAAAUgEoAAMAAAABAAIAAIdpAAQAAAABAAAAWgAAAAAAAABIAAAAAQAAAEgAAAABAAOgAQADAAAAAQABAACgAgAEAAAAAQAAAUCgAwAEAAAAAQAAAUAAAAAAWE1QILgCAAA8eDp4bXBtZXRhIHhtbG5zOng9ImFkb2JlOm5zOm1ldGEvIiB4OnhtcHRrPSJYTVAgQ29yZSA2LjAuMCI+CiAgIDxyZGY6UkRGIHhtbG5zOnJkZj0iaHR0cDovL3d3dy53My5vcmcvMTk5OS8wMi8yMi1yZGYtc3ludGF4LW5zIyI+CiAgICAgIDxyZGY6RGVzY3JpcHRpb24gcmRmOmFib3V0PSIiCiAgICAgICAgICAgIHhtbG5zOnRpZmY9Imh0dHA6Ly9ucy5hZG9iZS5jb20vdGlmZi8xLjAvIgogICAgICAgICAgICB4bWxuczpleGlmPSJodHRwOi8vbnMuYWRvYmUuY29tL2V4aWYvMS4wLyI+CiAgICAgICAgIDx0aWZmOllSZXNvbHV0aW9uPjcyLzE8L3RpZmY6WVJlc29sdXRpb24+CiAgICAgICAgIDx0aWZmOlJlc29sdXRpb25Vbml0PjI8L3RpZmY6UmVzb2x1dGlvblVuaXQ+CiAgICAgICAgIDx0aWZmOlhSZXNvbHV0aW9uPjcyLzE8L3RpZmY6WFJlc29sdXRpb24+CiAgICAgICAgIDx0aWZmOk9yaWVudGF0aW9uPjE8L3RpZmY6T3JpZW50YXRpb24+CiAgICAgICAgIDxleGlmOlBpeGVsWERpbWVuc2lvbj42NDA8L2V4aWY6UGl4ZWxYRGltZW5zaW9uPgogICAgICAgICA8ZXhpZjpDb2xvclNwYWNlPjE8L2V4aWY6Q29sb3JTcGFjZT4KICAgICAgICAgPGV4aWY6UGl4ZWxZRGltZW5zaW9uPjY0MDwvZXhpZjpQaXhlbFlEaW1lbnNpb24+CiAgICAgIDwvcmRmOkRlc2NyaXB0aW9uPgogICA8L3JkZjpSREY+CjwveDp4bXBtZXRhPgo=
- data:image/webp;base64,UklGRjiJAQBXRUJQVlA4WAoAAAAMAAAAPwEAPwEAVlA4TM2FAQAvP8FPAE1IbNtIkKSTa2q8s+7KP+Du2f8QIvo/Ac/T8S7/z7bv+7Z930932+M+dP+b7/b+dNuOlzzVh8/Lx/vnc7A3r8jV/m6v3f9Akr6SVTP99bH9bdtu29bJNwuSZLp76+5+abd/XStS1lozY3v83v19awOzwlr2+LHdPxzve7O7e0Zr9W132+pu2/f94vu23UmXvexuu+1ud9/++fbm7rZ72zd3/3Zuv/jQ2/9un9vvt+2ZE9usX778YHeV+2AbFgkQftUhKXSdkiyFhF+jwyQoz8deLEqglf0vz1+0Ei3bnStSRqwQCRBJgDwkQDLTCVeqKijo5U5uAZfygLRmIl1JIi4hRbKSlSiRpCTRCigB1N3XBZESUgSgICEBVt1I+lyXQUASYCkBSEWIJL3qklJXnpEApET59U9JtKq4AiwlpwAEQjgGkgjlc993XsJ55biS5BR/9J1C/jboGyWPZPdupySp6islETLAfDRqbXZ3t2qJpB5/qhahZoB4JNkH20tKUvXYT6UYXiUJkkfqCQVR5MddVTCTzVKkbksSUFQiXbr6oWYGsgZAkqNPEqBIKiHHWZCqZ2AuSUoBG6goyKPitaoakALbHiUAM6l5mO3X4VXsCbWqqvofZuoNbVVVUIY+dBuoVfxeVRTYT/c2dENTVfVTVfJUFUDv9G7eC6itKqkqimvba70UUAVUVXXqzPWtjYUOdQhUVbXqSODy1kILWo4kOZIdo9aan7z/eXgAVdRPNgKFQqMwSORP9+7jEWgr2x43kh6KXtSz/rPP0aDDuf8L2WeK3vvHiCAKY4QxwTRGULet7Y3T7NHIZvACfXJ3eugdBtN+hfu/jDedzusS1ocj9PV/AjgjSdBvTj09DFRWABXPJwF3IPGuAQh4kiRvni1cnOBk9HxYeixX9+GGBKAAQAAkSd4IuN0U7qh79NKy9Tg2EC5QEHiSxDPpT5ywgQZgegzGJQSQeJo3AECSxBMAFpttc0ONSp22jAm3g7v/tTCcIGLzhk0AAngDEOT/EjabTTAosCQCSOCG4I1AEMQNcSFwb1yezL7iDUml4koQAEgREUoQBAgCIHAfAOs55yiGN1QqlXp5JikSBIiICBA39yQA4kICBAAFniQIPFcASRBU8AbgzV2AoKRCocAzDYpwAwzwjkzwDK5hyBBC2AAxAAIEASTCC4ZKpQIYEkDdyf9tPAA4xzVsQnw5iaMwCNvENETEEJGRkZFhqFEjAq6SbFK/Ziw/3PEGABHCYqfTtAkxrqscjmI/HsS1eB3P42XsxkG8jIh17MXjomDGInz4+dt+NtGc+u5cesnhBSfFyQHUShX1Uw5X5yzrGqcy5zBnmcpUYj2VGNY1rDnMWfKsxEENlSoVj2EPbfZCzVZbW+e9zL7zi/H/Nm/UVFPNSJIYKqLEVrw4PI0nP44nc5bDTtw53I6dw8s1t+cc5xxjeFyMpaGGGspkueiNsezh1blV2/L9p72zfbSfqJUQITJEqIkQT2Mdu3Ezbsbw8fk4fo2jeHEY40b8FjuxjqM+PTDUoFHU7fM6RsP7q2OsrI4h68J5avkrQsSQRIRInDajrKvMOc5ZYljXGMO6ypwlSpQ1S1yZyjROO1sPnQ72f9brzHG196+PveX43VqTq3+t/uV8e2Y0KsLPbBWOFmMMh2uHMQ4O69g+jM7tqcRxjOsapmEap/JC/7ABTF4tnzJkfGozM/VL6nCkoQy7GZ+cn1WASk2muHk4jvFwO0qMh/VP40E8jWtxHDvxOg7jVfx8GGL/sBu71DfP/vPsrSP64AG+5VM+PS6/sBoOhivzrzOVmmqqFca0rjLnuK5hzXEaw7rKusqaZV1lzjHKNMw5zlnyosT3c5apzFn09uH9VL7hTRe9ebN5YfXG5qeHOuad74ad2d6LqqZI6gu1ulh/eH8Y61jHtXgWd+NwzhK340bsHnYOx3EnduN2rOMoimve60fxRojw0IaL8aPBKHJs6ZlzN8cYNTJAZPe2h+7Naz5zsLdqrXa1q87YhMHucXb9tuvufRq92YhQQ1T91D/noxjl6/6KX+uHJmldTQcAonaCZeUAAH1b1hPcdpIsLJ3fmxpqqPGj+vlvF9Jg4P3Fp/nRo90BIIENDN07yfcA9A1QFpdNv18qlEmZ1FDz0+Vs+LKfrUYaX/n0/akOHnUyNACo1G60DbdLWtMaaOjOAtsGK7iDjddLBYhwyuHNMA/nI3nw9QZCAPoBaJpA1fStr0FjNNDQybpRq771QG19r2qlUKlJVX3aT/8Ew/m4fL0Q3gAd0IBvli2tyKLp3rp1BhpA60Vvuumhm069A6hUUoTgvxN/tL+/MdgmD4DkeVgAwGYDja77QkfT0dC56NeLSp3LbvrR+x2+DRFUkWpVa2Px9+fpl/u3bjTABgEIwGZgaBqAZmn9Vr9d1PtFvdcNWoNfKxWAMsnWzziMvdVsjQ0N0G3O4QSsAOh03ciFZFdrq1vX77t+T6XOgFrVKqrQNJ10jTuvm9kAwLB1m80LAgBI+qJzUUOlx9b122U/dv2MZ7OgUgECTdLpOi0MGqteyQbAWBmADa6dyx6d28aDfg+iQcBFhe666667bjRylhoATACwwXW70suyUmmVBEEQIOZ2IYhZndVUMKEvE49Na031DreLgNsysurXXWkAIABiFgQxq1VNRRVFdY+1k6qpAwBD5RIACQQA2AAqQCHUCwKYIKgUXSiqq+yt6km9pwCg80wnkCSu3TZqbxugUqWa8GQDPBqnGqRucIFQve/3PcKlto3uUDeVi1oVqO6GGYUgaPDoPeoJgE7MAvrSXVML3D7WBeroGA4jSWocjvMm/4CfBSmEiGDgSEqYOzFIEU/qK9baa2/64uuQmXEfn32LiQ9RDX0O7Q0C7lQ8APIuGfuQKPdnBIJQF356CNnIpE2bLryNccV0/A+ZQUmLH+7Lvz7snXuLSOZD+R8e3iqTAEmLUNBL1KNJsAyVCjuKcF6Movh9L+ag4qxKUC7Yr0fJh1ESp/DHwtiPDfQQcOQXX5TrLMZ97wna8Qfvioj96Lq8HtSPtgkd5qLHU5KnP92DcnkdIxURYhZhQRJI6onphnR4JbT6o0HcII9mLaIGBi1Kg3/+waxftImZuNCZJMhlh5hg4MZHtluuXJ0ggxgOOOVAUIlFG04gZK5xZtNwJUMdQdHGALvqP84wV7aOHtfsiL5GtvUVujqEMvJDZXdHwwdUJHC7R1lrE+kO0BEYNqgL+8SuiBkoChgtUlLt0TM9MwGc4EBrMdrd08xSNRkxEz6REe4e0XDBaBPMbKmPbXPok0mu6T6W0C5j6sz5Rh3MTaOkpIhQEUkLs8C9PpPFM3EhhmzGnRkqkjXXxYYYIiDPF4sIW3e2Z+VBVnHODxoLMPGRampJaqnWE+FopTHdPUFJ6l58Sr3S3FVFKt1n4rNxSnetKq78EFdN/cwcNXhMEHtmlqZCoQiIgEkfOMW4J9exTCwAsoHHYU1Vn7GxrMwqKvCS5tS7h4jCk4lwH4+UBGOifHiwBAF5TDU8srhEhGLYPcYVPPVwUBWuegTHUPHHGLcJ9wEPgn7sKAUJM8auwqHhSZJk2bYlSSLk9VS7OmEdpoH1bA42gX+kcY5aOQGJYdsIkgNqPv03nFtDCNtIkCPPF0/5k7tNTIDv2rZV27Ykq5TS+pxrX2OmT9NfDlOAvtlMg0trjt6MWQDfgiRZkiRJFiCLZd+7v7k/cj5knmcilHxLkmRJkmRbSGJel8f+o/t/1eWn+5ZuHBPgW5IkS5Ik22IiEsvq///aa7r+hm9BkixJkiQLgcTyt/O/6+LKFBtJciRJ5jlH/l9pps0LORURniRJlm1bkiQkOe9rPf9Bale1p/AWN86Fr1OQ2LaRIElUzX3++d7/tx22bSM4VB7df+KeYwJ81bYt27YkSbWvI/IlKJSPslU+SkAB6Ned7WOuda4IA8qRJDmSJLVYzMfyzxi4N5x0h23bBhKV//03vjomwLckSZYkSbZFzKrmHln9/z/X33C/R7iZCs19fkFCI0mSJJnnvgCWP7cDchUQw7YN5IC+7j9xP4oJ8LVt2zFH27ZPalm3/TgKSdunddm2bdv6Bdd1cxBjHLXv+7Jt20aftrtzdiepVNVx7Ns6UJXkkm5t245NkqDzft7vj4zIzHId7dLYtm17Zsmb4aXZnVmzbXvaKFeWExHfe/vOtm3ZHk2S9uN63ldSUDIz03JuaQJnLqYbaQFGpgtpQJqQHvB6WsDMAT8opO997ysmQJcASIokSZaIqJm7R0RmVlYPw/In3mP3bu8Q7xDvm/mPmbmpqrIywN1MVR4dwrckSZYkSbaFJB5V3Z/dn9yPdQlX9i1JkiVJkm0hiUX07bn//xfvt6oMN47U7P+TIkmS9P+LiKqBu4dHRkZicdXwLDPvbU9z3dM+wD7VnpjpxHRiZobmLMqMCAczUxWRSz+E58i2Xdu2JKm1PuY+F3zD2IwQK79vLBgx2D7+7BiqQw5+0RiwMgb33rPm6J4jSXJt27YtM8vex1wb74PPqZ7qIQJfsjBi7RJwKcAlDNdac4yWHuG3tm3btq3aSqnU1id/6S9u3MAEPEVFAg2LQNp7w+ytlsT/D7JvQZIsSZIkC5A1s/69vrbfu9yEPEmSJNu2JUlIsl7xzWwKNv9pGNh0bAC1beWYAN+SJFmSJNkWskb9//91f0U/d4YJ9fUfIIRtJMhR9vhzKrD+mIIkSYLbJmuOerhCz7a5HRPgDds/ZW7b/3u9Z+am5ZW0kkW2bMkcQ+ykdjhxGyhz+2FmZmZmZmYIldIwtuGY2ZYtW8xa3ptm5v0gUH6uC9s/RXJj6fv9IyIzC5rFsi1ZsmXZmrF1PB6e9TDPLHiZmZkZZvea93pvDzOfYUav2R4zCCzoVquhqroqMyP+umjbNm3blkppvY8x59L2Prg4V/HuY9i2jT/HX6T4th3x7fiNL9u29Wy/d94993hrcc7Re40J0L9tmyK5sTyu74uI5GLuaiaphZYtyzLbw7N7hmcO4zIzM+9PzMy8O3N4mAwyo2QxNUN1cXJmkB7b2pZtkpxzrvt9vy8isyklm9GTJZvlakyNY5KHtkyaATNlVUR873NfviPZVm3btq2IlEttY0z+XJtBki03owhbDMYJvbeSU8Q/37+tCTEhWg1i0PayN809frttS4/NhrGteV7Eq9/1t94BwZvOJilnwnbP1Hy6bB89epbOLT51Kd0+19WvuK2j98ThO2zt/fp6vKj3P//+z/3v/304XTqXTueuPqfLVRbO5dPt3uV06naKuO3idpV11Urto/uK7HRn2ra1eGc3m5ttlgHbK8EYW2PVxrqLiM5f14c7cSS30ol7u1NS5qv4VGzfqD0xT3gZxpoZ78xupOdV8LT/4d3gnU1te3UnSif+9SnYZDN4Vxte1TPj2Rhku9n/Kz7d9e3zdW+eZfR7Y58es0Hk+aL6kK2xsmEZNwswgDFMGWZpZiszAkAsBosZAbMY/NkZS6vRtgbiDXhMqaqQRSmbTdNshQFnMwmxvbOURSOwyRhGHJcb7pKhwrgqY7dns7VVp2RWbVsknTiENtGIpTWH6/h6ZKPKUtUqGAUVrEKxmdJgpmZKa3NRVqGl2chCVVPhpG4pHCOpVgllQVoKElFRSqlQaY2xiTG2VqyJ2DRpz7cSq3ChLZIUWCnzrUkdYAVV861pVyuNLLsWlEUCEQF0fEvaLqZqmogILJHJiIgxqnRrHf2gvic+si9fmeVQsCIFjiiKYFOIgkYCKaJEBCJKE4goberPLFnkFjQskmZOIRAJiTVDVWWJjpFkWwELwTzvBnp/LNDWpCktiy9BMSiSSze3SqiVO/UaRGrS1dmCTETDgAFbUrBsqFqrZt6SkIisNmtrneK4gB5es69tGFR2K3bisinpQihVMtXsapQnOxVpiRVx6+xGqsGyLlkGbDIWcS3kVi1TSYUkwrFSkDTUpCSXEGFoFaEWEYWZAQMVW1YQFqm0kGq3LlaqAwlUvXPGnc41xq5NWFnvGrkVFN9RGR1w+SvBKsBNKKCIQikREiFSbiQES2RKSpSiAoJDRAAgVglikgJSKlEQSUQtGomqSIm4YA4btX1rxFkkSB4HybXsTKexCHMLZ5W6pNyprcGMLS26agmkTQMwPFA7MtsO6lZJLE1TjOwoEU1cEtE0sRSKnWZHdozSSNJFckbFbWLZQiNOqlpT5LbpJqSJxmGqgBChKdHD5EY0etqMJg1SFSpKKrCyVIoJQR0INVE3Bwo5RVAcSNKoUlJKgSUoToAJhY9lSsNJ5VCIIhLq8Pf48UsJaviTJY5qi6rWF+gCFQLAlEAUhERBUJQoEYglyp1oCgIAS0BKCCVqJqZISpVcVSVJITYUbsIbUruaeDfbetjBOKlmc2sDjWWY2yWzstrVy0mksvSWGTMpEpXJmMCGkGq+nnlaY621SQO1jB01ZEjaKTDiKOXURCBSTLWnLSAhJSRC5gwIjKBSUDZJlFoCIQaiCMTJSSXKrEE5aCHSQTdBwraqJpUyElqmlWK74l0gaCYRBYv4AKDipppSIoz0SBGrIyvR9h1plaTKaVGrRk2N8k8e7ixx8Ui3lqfT6aASq0IFCkkQIL4RTWSpRAANDkSBAymQCMLPkaqirUnSIELlVndEb1bbIbOCKUVoz9awA4Rtg+cbBxyHV6lDK2KXSrdJ4b6EY0XBuSoAZDFkNYusPYbsL77tNwuXZHxHiiAQSFtTGiFxSm4Rw255g1ZF04acBtJWYgm3qycoS5EpVDTaFGEG4FYUJQsgDpOZFPhyuVpVhMp0O5u1qYdardKtaHPRqNpOL7sAEBEIDMCR5KtWihNRVI3QASrjI1oRtdXaaRVKQY0qmR3y0PUHcvlBXr06ksLxr34sjR+25EismghBEICIkKpEBNpWkSWBHIgoUJAs/QCAFGaQIotSiJiWxXpvxAEmEA57J+sCbWXjWVDmUt5ZLqFUGjyHcYVr3RhVVpG6MqIRERpS9/zh2tjy4nJlNGQpRgTJqYqCuLmmHSmyBqk0m2rTKi1NEcQWtKhBU0UgIppKil0nghVBEADaQRKZqbE4+9hSoKYgAA6XCXAQRr2oKaR6XFFTIRmxhBmVKEXZpAKkNNJQpmorOCVLXYtAYUyQTHpilyQOuCxA/HL5Xq9Aq+Zd95LT8Z9z+KDXzs1NBRwF3xL4DoVQBRGNCLAEIqpSgACYqUqRZEmEiBa0NT0Ba8WsOoFMwgA14thcRVOikHEY0qnO6VC62ALuAUskXG5EmxbJ3Lvetbu9vFa7b5KqkGqzrZGdqk1zqggFkSJNrWorawpSqxSWTsICC7RjUVtLiCIKEQWylow00RpmCho5TuxLWMVarhNqlBVLtQTQuHQtDGeWIIkUEoVKVJIYRLmhEkQgZEIUJaVRZ4Tk3AlxRYKTkKnokRCxU8IRN8qFXn6G0uzjfz6GevzRy8dCrzMFiRXdSKCJKI0AiLYKaATFICQEEQBQAgUBp4KzqxQI4CQN0QJExLRSVk47TTOO2WgatZaAnW3bdwWYKI8Qg7iBNxdnl+yyIQQi5euuT/Ha2VHe0OUKZcMag2hoEz90LqWIcCgCDFig2SzPsISSmys1VZnAwqWlFAUIJEESbuxoStaGLA5pYcRSQbREqmqGalSkCFnXLKCiK5fsFEEIKhEpTNlaqXYv16wVEYgBcTEJaVZZTA0kFKhSQIKTXKpT1LyrkMplwglIl+Mt878+LeX0Px8SUlUiBhXJliKqUI0ACmhCAqUUAF8AJAo0AlK6pimAUNmq5LjQSSgu6ZpUHS9LGNuEEIGEsrZaEhYwmVlqK5I5rbEAhO0aHKxDSfVtvTFUfSx2RTRnrLc2k5IMU5RTQnRCKd0GoyOUOOBgTKPWlZrkKr52xF1xWiyAFLsVVAXY3rtpUQg5ATloXAAXmqEAxgpUCqSgVYhKSU4JAQqQRGa0mwipNdpNJGkqAgFIcQrEhOoeiVcaYyftWEmYcpVGUSCpJMFarCu5CqF3fpZ8vHpaNZFeNpeQIxGRTolERUjcqNtCSUQAQPkWQFwFUsAK4qoimwK03uz5DujaBdew3E1vDKXbaVIcY7pNi7bGJm2QrAHlF6NhsAp3xZNRZGvFgRKOOdIZ+UGpq7ZmN1leGw2r9q0Ut7KPZVnEpdMpb8iYjMFeiIpaWqRhZ7+SA9cQSHURlCGBGWbvZjOlaC7Qzs6opEiXKwtC8wpmBQArVUq0FBQgRSEiAGkbEBk7iwCiwhVCGOwKToGEE0UBSGEWGr4cAFXsAgaYuNxIE5VJxbw0VK1uXo0VMLvI5QJIRaKUMAJZuomIlLAAIwIsAYHhXAnAFEBwc1FoIBUydgEQNQyDcUVrUhvmpjSCjI0MQCoKNEBAu2Y2RraB9A1kRTqitWU2cvoTu1e/kxxWTQYJUyggUOUQEp2lLMvam2jXrLEslaAigGShHVFgSeDgii1QUgQydhEgO2oGXOHKidSsQE2srNJBdY1QoiMRK1IoAy3W0irm6Yqaa0CjIsISyCE4V8CsSl3RoEQzVGmV2dpYHpPsVgWokWhcVKuEktstxyUgozJFUQKaEhEZoEgZRaYaaSr1FQiJW1Wi5JQKiCoCgi+BQ6Tk3RsE9Cgl+9o3lwhaJQtLtra8cbi4bcYwUrkwK45WA+y8itHMIlutbmod4zht0s0N5JJiRUrN3xuz67BDgZzTVTFQF40yYoyxNE1sb+i97HoMBYOk5VylglpwT1fn0sCUEmU4MkSKJgmdWqtbQrkqBFGIUFFUKKCQSBgoCfERoKCDyhFZlFaM5QaUrh3nFkNClq7CCTgIiMpUtFWrEMEO1RIi8Rq4EFXJlEPWDAkUGQkMAIEUoCQCBeiQiFAtRYBS6VYWAUIBABcgoXMUHMAhOBiAELSdncYoiwrlolYYWbYIGM3NBiBDBFIWEnos9757xo0gRIu0IE7NAYhSPrUznFVfjgYaTuWjHAkXiqN2o6xWSYnTXM4T2+xp9TQRQETSrFEa0Lh9TFNKk9qLBpUjWDTqcqFWxGnzJZQSxGitVmoKSgmsVkWyKiQIToMRAUbAstsu0zRMSlflKo4AQKowI5BIKpDGyZoii4KLFBJQpAJcToUgtIBcQUJkllgZyQCgIN9ABCJSBJXbKNoiIlICUXGBADUq10hwpNVios1oNmiQK9dI5ThOlZTyBkitdigAzQ20PAokjZhIt6THYvRQtuxOKEGLDcCIIPdugu7v4XLFXShscaqEIo2gxdpS46k6Za7z3Mazbbz6iUzaGlEzswhqbbYzlEgCqxy1T9oheHtHdiDSdOXa9lUqSdhNCxISkSpqUwgdxwHOUsqoEOyGhpwk2MEwENmtdBHcii8UAF0FBKDZKQWjSIoYLa2IEU2T0lXerQqnVRoAzKnTIFqF4GoEddjIkUUQ+JGRAEQRlCVFrSq1VckNFWg3VIgSUwBGa4qCDMgE2U1slUlpYTsWolyI5XIhDNN8z2Awg+2Z9k71mr2pseorb5cFayWMkHBJ0boh293ahO9+HPwzViWzdMKuuCXSJgXS5mV5uqzOXP34Hjy99q4XZHu2ZpQms0nNlJidoSIlh7qeVW4Y4pJhK1UbpXC1tK5GAwVIk6BSCtoVg1Qd1ATgdDqKNVcOlQKIlALXTkpOmsnocgKIgiSOlASRIejWigApY+sxntGTfHBiVRTSUKWEAoAcgNpcjWQWAFlkzBScEqqEhAAAISJCQCylYDuKLg5CjVSJA8YYBAjFGQx4mWIwxmtuhNgWGzAiqsbLVnUtk0cCgU0rSuOSmG3S2Wy2PCJxblQwC0ZD7fNpelWllpLKrUpo07iMHkQpy86VJE7lPvdpWLv4zpWETDtCw52Cgii0E2IsBOIUCATw3j6V09JQLeIo+OIqQZxxVAJNOBcpoMqRyiFyR44KkARk2gUZTi5TQBFBVOgUGLUDBw5EAiLFVWAJk0kqkSKuNQMSCQtKBBo5JRVUJOImSaGCODuDVESRuJFoBiBFAgBCJxUQqAJC07SDzGEtUjuuAkS2wACwhDOtKKA4GLKhhYh7BqfElq7pCCErAhZkXMRvFBUdq3I4jcOhRxPvwUpDnaNQlkVm21olheYCjMWIohRZcC42fiU7SzksxuVwk6Rmo6VYpVBphbGZECKhQKICG1RJTBVUFmC7qQHMsogIhKScTzhO2QlHUnEBxalcgMNcg0SVTpdGRSIAylRICElhJcQpYMSoKbJ0wUIqEFROtdZO63NrLWSldQntBlW5AjMSspxwJqqqoFGqQ5mQAKKUADJVSkgrEFEIiGWUkh3VFXZmTnLt7JiVkckmNQ8myhBBQDqLJnt72xbqWxshxgIgmGbkGreNAEBTzu1o3WYLkzEWN95VelVnbh+634wGjGk7orjcYBDmjpKWZVTtri/83BbjioX6uEeMgNZyM6kcsqYxQVVO6pS0W0skxmxN7RaqVmBJASkFiFNFJbhHNRJdHSjlIJAilGipQAZAjHZKrcTOqoloRSClDqQIHCjaDcIoFbkhN8W6WpDESpSdJEo6hVTMBgwcjdJurLsdQBxAFipwCEAQEIHAjpIAVDlQS4ICRESUUcJJhNBEZAYAYEgtIwxvLjFgDEUMRnE8fs3Zc24UIMctz32NICNauLCtXVANJ3YEsfpYVcG6CTtNeT68/h6OSGKo7DCKAstQonNZM95dWi1/uZLXXXwZZZxwlSIDgCEhtbZZUGlVoNkBxo4sKK2aqilQR5Y1CAuZURZHAtRVZcxaIxVarCoiwEDRBEaAEtE1UyV6uSmUxCapBQWRw1qLuMSNEsGFlhKt2FYylJJSyrK0apVIJRCCU7ogIILsyFDLACglylTQEYBUVI0qU4EUUTCrRIrsXKIT39pMkzXReoZAEcJgLgEyAeEiso0zVh4a7vbORGW8tZcXw9OX2ca2K1YOccVMx1QOO1EliMLAS7jdkF2XvhKjxAEHWjNFlwhl2d5dr6vPMb72GtzxXaE0oXACponQePbaDpGImGBRBESg0KoUCHBdNZQCBwAFKN2K1SokbGjWtKQ1LFXiEENVAzEF7Fa3A6QqsmgjRKlUjUYVArcIiBpIUW6YYgITHrGggBIZTE5bbBVpihFKCUDDbDeQqB0SEQQCQeosCAgIzTAXgYgItwoASgClCKRgNiN6Z9e72RDSbEopQwwjnC3CgCFbtm3TG159sa6Vmhf5TgH2bBsOaOy2RIg2J6qtXRZXcPgNqjkN3wbbau04vnN1ViogkQJwXF7dfOaan++32+7Fqy9ejeNlvEAhGiKqyKhlWLLzPiRQGkTFD1TFDUgqpqmqAgUDmG1CSlixGNmZOeK4EiqQkwRpNxADgGoHgGKNRJCJqEyhEhWKyAziMKQSIEaUKqMspzgUtQRVQYqimdIoym5OC98VXGO4yAGThSVQgEiAiohdV1T6oUIo7BSGJIBzgQMCqwgcstkUBQaMhqwNgT1stYnYDJEtPlz3Uch43qp9U2/vyYrNL8JaCQaou7GirkN5qywH0tGkG3o2OW5ubUoiotpht4yOm63Xq16t28dd313TF5O6NQJEImJosvMshai0uBTUQEpMpOOg0LJWLZURlK4MakytUolIVQuxFoOSHCA5KC4gpCKRQJWcKghAAAJCuI6MoDqKpCMAIYUTFSMWFWwirCBRiqVUZELM0UmukgKgCgGFCsAAIgRUKABERBCV2VUFMoeqqhQKQNVpiAqkQKSMsTOc5BBDJkMZApNHjCCMAGUjYtjeeHHxhfZGtrMZuNZTEy/aQvGFZrSVTAwJyuHFcXmDgLmQveqlnNq5JNtJV+JAZlS0pzPP1xzcE179VfWlVAle4riIlgqGYz127Yg4So2BiiGlah93hRapgGRWQt2kSFUxJkDFIGFJlH1EBE6cGywXqJwKJIIWpAIgCEiPilabokIBiZJBFiRAKgbUbu2ITKLW1I44FurEiMQwmkwizBWIksYDANlmRYZWqmqGIlLwI5ITA0k1qUQEHEktUihuQhIObByy8RhKj4A9xGALkYkQQjSjYevAG0WBd5tlM9uQ6qxtm3Nvsu2x4lKKQaUxHm9k9u3lO2ylU5bm9b7vC66/4mmcvCyjWI2Om8WgThsxzefzdc3jvv8+z59b7XE41MKwGAScvUqLCpSImEZDhQEX6nxcXmtGszUhTfGuDSGNIgZKDgkWEzY6FUgBATRPACQ4qBxSDslOKaEyJRJChyqpDdKqAKsl4mDHwEEAaadgiCg0qWqKTbtpGnEVVF1aaSXfiuMkMREScBy4MYwZlCqlRKmpIohohCWgAoCqcVGmmixUyd0IStEoYghlMBuwMAKEGEQWorzcAzDeLBrNhttQzGNXFtd4QwP7HuaVRTGCTHGos9m4+TSkd2l2ZMa77l41Pbt+OE6IKLDErhXu6Uvnqn203fZd5qPnQi5vhBi+0MYCLktcO2aBUCNFWhiLOJKYi9p6Q8VarMUSVNWsAgJyEmm7hkGLqEhVHAGaAbqIs5PDz9I1oFIIVK242tpSmKIYNFaUIyKwyk4pKEBBQKSUEMWKVkSaUpxKEjNFitSUWFmqiYaIBGAAz8COieRQCAggUCUCAKNQJdRtSqm2KhQiGgrIgmkMMIxNs8QmLAQbmhBg04xsbJuJbChAhFJBoUKXPjw4GkHdmC2xjcjgxDbPDhB7PK85Tre2zquA8oZa+xLlqqxuzbe17tVPP83WU43VMUYMtUU4HMtLt21M0xg0RDmkGdn0WusJKsVBhTRcKL0aREDIJUVW9K6WqlilgxEKgFVOKQlac6lqNpEZRKtKqKZQSm0oiaIABMCFn0ogBZAoMEZoNCIV26kGYezWSJS1nCRViqXQasghAoBAAGM2skAIShE0JUqgRESkQESAIkKhCaqamBGMIWyE0VyAakiYmSZiGMZgYLNhb1EcnQjyKybGSjhUofIV89tcXjxMYXp5Jjbv1+F31s1WWOY8w9bv0K6JbbDsIYcCjvF0c336J/9a39vNd7vjsollbKHt5RhkWYa12ghUODKUOKZpjJSklQAwgB0VRw/JAqMCqNFsV+MTItWSwpAAKVgLRUQYREQ0oECoFUkyWlVVm8dpJLmRGPqqqjEeS1WhNE0NtKgmhAqhCjhSSSmAU2siq4IQIVUlYzxkjIFlJAQdgRS2qsARoECkAcwQCUREIDISKGVTyCZ+GPcMcDSWDSg3EcMQG4hgDAFvigKLwt0lONbww3jHMNWhIR0KR65rpk2zTrs9drdj7MZ4vankr/PUxNSUsrgUmWV5TqkvXl+Vqb/uaz6ViMd0WoRwGWNrCNQuNcYEtvOYjBSWAgVXGIyARaKymphC3ZZ2FTWTwKQ6F1AcXQAcM6oZzaiWRCQASJdbJRRRGlAWQcWsABLsYGeo2Q6iQAKtcW9RjNeOSSErcUPlqkpHmiChZa2UhqKhQDhwIAOzMTAgCMpIzjIdoyjhoAgAEUfKpQQEiKCQJqRrm82DwJgtIhsDROONDdiAUDYPTJ45LoqIs02FsFgUwVGWq6DLt9F/EzZxWOxtKcqM2eJxHIOGs4+ezdscFt8oI7yDhuN3OPKuXzuuP6J72uKXbeONy+MKEe/V6VwpvONGUlWhKoVENAjWpKByClTT0lqzUUW6RyFQajW1ZgYatIotSlOvujTEetw0VCIOKtmtCswqlKKxaHYhWyW1ilZDDVEw1URjxIgorTWKoBCBZkowlvJBChQLNM5OCxIJjWST0nosFPxOH2IIgACd0RQCDChhqCoAqCJCJAQSQGSUccMMIMwAbeNGowiABqabZgxsCEM8Rtw0YZcFs6dYe1FcL5RCcv77PO6fnzPrbJ01XpZteviygUfGzpqFmDURU0+JrVEKyte9v16/spBD7nsNvwvHllmRDNlfKkrYmc0WQYmCCCqhQiQJqUCGlCJdVK5qVohLK6UomVUzVZxaq2SlFI0NoEkFKSq43CQB5FZKEWnZIQiqyYKsrJCjKkB2UxARac2oCwg3qnZko8ooUQGiBm6cXXCBXSVQFGsJK2RWIgAkGmMAJSQQhPgdMhNWlVJ2qzLCjaBEiIAi+A00wBCwMZoQithTqFPAEAHGhrHAlrEB6+LGcmVIBtkGZtli/PT+7ve3//6/zqBo9sw2oZu9betmCTpl59xrdd+X8C6yLCwPt+rr+rV/fvz439/Znxzk36fv7uAoX16Z8Xg6vhnvqikLg3uxZjsV0KV2hECqAMWp3AbNoOAWRWxVSMmKVLXZGKpyKlQR0VcRU/lChUjByEERVCVYlcpuCdSEpDbKIlOirdOUo8CUYlR2xNkRFOa6MaXAWFqXlm5UVYGqykkMMa46SDeiQI0VSDszAYoMDARDMSEIVDMWSAEkBICQADU1QkSJQBHqhixjhc0IIiuDPMjbZuIsm62FQm6vbIabrRTfkioewngsM169+ntXu2+9fXvfn7tqcuZAap8dmjpqJmPMAFSMuDG2Lg2MhRLtzHL1RsnM6Wd/O3aEeBEuihAAbpyzPe11TSlqa+UoIrQMRJGFqKlalfC7cgurXIqcSikwshhjCppwhKJqWpZaJgikaTIntVRQRqmq4FTUyE61D8CqOJ1KEq2rOBUB5KAGUXAqp4qbIjOBNiqRxKpK0CjNKlXVESSmal1LSkzFqQopMUoEviUiEGdEQBw4YjqjLAGIUJPJlAIkAvFqjctR0a0aNtiFLC4Px8OZOMazIUDqcUhtb56hK+bDY7hZHSHAZa2Owqvl/UCMDWguJmR0ptcZjRp5Y/tpI88YBgmIgakNFrRKTUY8dx2PTRkLbEAmn+20oebjuWeDCCLYGYWoElJQVCtVwSgRKA4qFlUJuBiMEWsmQ5USPohIUarbkJOBEKUikqkQUGMIqRkUYY1QibCWNFlxSLpmTAWQiMSRHchOW9CwpCVCzk4xSFrFKkkhR1wxqSpIlRRC4ueBQEJkFJkqCQgcEoIIikBECmmkCoikKCgvK968ap7ONMOMfXFR3rbcGDIRL46HsMcehxhvQ/atreJk1PnkaRqLuAHJ7tTrViFXvMLG8hUZz+/XyyZmhoVgWs0qYAPNoK5GzIuBKFOZzSgvhPZyXLzm22Mfm3TUrbv4npVCLBYrwWoqcYqziJRQgBMzAkNVgGrfXKiVVkuGYCY7JaJQBOByisNYaoy2szSrTGorkCME2jWhKkqpMhuFSoLT3XCSQKpuilFUANCSUqqEHdr1PmNZHioGxMAoVpJIkdJzKekk8KgzBxSNht0CEEEkRMoIEAqJAwAUBbDKQEJAIEJC4lZtTs2rTJtmCDyZIQijxkTj0Ahn+PEAAY67vsu5OFRmiJuWZcag1o2PVrzRqDtrvkzCyI736pwZFuHbu03L655Shq3SUarc0BcPGtRk5HcOgo3j3Xif24+NT1rd3R52u1iLy1KtHFQRMhiqVmqldAJBCUCzIxXDznBMM5thAQRAFdVulUhEENRiOVAiJYLQTFDVQIWp0iBSilBIgECqEhS3CkQSIiLFCVYVNxTsaxANM9SaeEKtSVSxZhmxRWUSlBTJXCtoIqgEC4aUgogECXzshBJABAKBiAglNxIUGWUk99JqWyGMZIbZb5UbWHwQjTb3RHshHP76jTfzRkuz+toHNoQAaMrNBXLPba2zhh9E9+GyAueYDLoZdYzGYjOOxeY9+lW0Tz/kZi6KPVTUYFGZQweY1em8nqn97PbT3fdBv0uEUiSSy1JjJqpyRm2lpKQiUslAWZs02k1BCBoUAARDzlECFKejjAUQdlYOUNAIWUhtFQ0iAIMcRHG+RFRIQnESqwpK4zDUYUZRQgRCJDtUAZFMVFcFYSBWqSomoK5kGldbkyQogBkGEG2pABGIFBGIQCDkp4gShIgIwjZEbq0IUGKr9VP5HhRjQ9MzXp4nb6t3dl4B7aHMxkYah7HHsDIwjNbr2pGFc0dHxW5JKzMwlpMKCHIVZtKezTxZsdCLpFguomJqDF1MnXa66tZr399d33YuF+qdzrIUWSmEUclOVAAJSERdMETAyqUpIrLbTUKanaQgJZQKyHy1qaApDHC1CBGlAEV1g1QlVQIhSICqoKVISCJXGUAJiGpHqsqRqiquUnXBTFCidqSKKBKnQBWl4Eogp5VTrYkQBUWIMFSI8YyoQM4UAoFAfAUgEQAQEYQSOAOpnSsH8fEww810hU9v13r7/bLZtrZdS96WbZyF2u1XtxbHFV5S2DQRETbm+Po2d/taE+bp7KZ44zArxgyFh2XMjoMFl8xZ7Sae4tWgY1kMqBbVsddtrql7Pfplvb8v3/yah2KxuhMEhEspVSVi060urFZUqBQkAG6QElQ0iMQ+SRyFIiI+Je0Wt26TFZoGoLqBSp6NACFuJVGYQWHA0BCaR5Q0pJBzEpVTFSZCjFAgQARaHSY0pKoqCVQQCSscIETk6gIlLkgFBFEkAgSBSIjSplQShIgEgPgqZxQjCoCIAB0UD7v4QozsJcgsixbNLfds0jRGaXePwDVwj3C7WS0XBpBJXmbFRXk6d2rXvr43ct+7ryv25m13mr8CgcYvBqN4XMQ3yjee3vazY61IhTJUGWIN49krb0u3vnt+4T7aPVOSY0qpfCFjBxY3Dsf0FJGqApUCKUU0NMFEIgGYkWunzTCtSvtWCDWUy60Zml7DkrCYFJkJMNC0FAGoECAwVDbN5plJMTeyFFOUUwgAqihBjJoalSK1hWzcSG4VbqnSiktUoVU1VaJi0sriSGFEUKSEwwCwEtFEqECglGhLjM4oApERycgIRwSACFBmmwAkUVUnydW1uOs9T8ND2++Z8WHMzU2Vc3sYs6as4O26l1c/EQq5dSXTvkIfWxe7pbXNJAMgQWCsFdR4KjTbQbuXn1Pit/NOR72+n+++63WhswoqVCUGpUUKxIipINcFUmFXAEsQSCmBojSRUQg7EKSqNUalMJuNOtpxEqIasqOIJUDgArlUVYYkSgkCyBBXYbRLSuM4QHxFqgCgQAJtpZQCVHAI0MiRio1SlUK4kZ3RkJAG0A5FWwRF7KLbKFMiEWgiCpQkoQOISAOBFD8iIhDxFAIJRyJ1rtBdYRtCzGC8oGHa7jp6Jd8bTR2eGTs13xu97eWvzzu/7sdYOpao4rFcpjWDAQCBgUQQ0AjO4+Sde9XMyHbdm++7f3h3u3Xnbd5BdwWVcpthZyhgFBAgVaoCJVQ4rColOiklFAeCqKI4SFWKEma92WxGBaNVrsI5VYMClSRH1hoNDYmoacAlcACQgEpCQoTmQgRAzNHwnZGWokISrQ5oKexGUFVFqCJUA0uwAwFABCpNIJBUjaBKpGwCooigQQkJFIkADgQi8B0RQ8JCUCkIl5N7H6YhTdwmrhXNLxA3H7gcPBkUU+w723TTMhvFfX7u7b3247l3R6jihUOyhjIuQGALNRgUZNdTxyequ7Zv9/f8zHXnsgwusTwFAZQKJVIRlIS1qmg7JAGkUsW7jUExqyIKwBSQSlKpClWkiNIKoKXEIFJVpUhUDhRVl6Y0IDWoUhpJBFxSVKSgVGFXOQUApAZAFSGSAHullMYRGUMMEoJBDRiSlaABRKEqiAhShwgRCFlEIFYAIkIEBUXQBBAIZCl+REQA91CUpshNBUeoSsFlliErMmOUJTYWk60RZtVW6o6//+Te7twmhSzPZ1/Lzoa7ZbaoMw3eDQCIGGCGn8Jqq6/9zPf1JnG8Sy0qZ6SMHRpq5qIqUKKkhNbOWHYmUwqAITIIVM0Sdqug0KBRKaUqpaEqKLQg2JGAEHMNKBHpJpgJdrV2lBKaVDXbUSJCCIDgQApp5Wo4VwDAEmQArO06JrIvrSoiAgIRqUoFVYGoYYCY7JCCMjcFaBCICFUQERQAAtFINCESKAeMAoBGEBFAvNykI1Sk4po0qRVnaBg0xAaMjUKGQVKxLUxqll1xc+2eL9/26euQQ/G1WZadB1uYCRBjAIgauHuhD9uu36tX39O3OReLxapDGAdTbT2NN62tP+JUMICg2dlZU9vWtLXS0A4KolOBJQ0ipkdEupIqDgGizUIQJJGDJAxCQKRULane186wzRRIySKSFLCjEQvKYNmWxlmzZClNm4grEsJWRMotVsGbbYyBJJUmQwWK1YhhKZICpDENiQRktQsIQoDaFrVSUgKR5FCIKAVNBCQcHJGRlBKBkANoC8lUFg6kDbvJDIktwIZnWIgwYhCwKLyajgdG1Nhl4W/fdXwcycvQPdlshFcGUBkAMSPEzna999yuOwUYhiSUaVG5mQqn3AtN5WIpohRYThJUBRiCISIpZLmyiRSt0kRJhUroFkjQG1hKpVW5UpMCEQmYCQYwCYooUUhDqdkuNROFhKoCgCKKVbOqDa3iCiBaO1chbuEAmq1CpBkgBRZDEyJKAnWumeUUAYpEhGQpoEAoiGgAqIhIAYmMmlIEpUCiJClxs6hAAKEaCRUOxFRoyRCbEdAwELOxsSwAjKELzIXYcJFJcZwiX2tdKu/GbgpGMwBAjBGqGSNZa0VhQNyAEJ10h8OtWN4pgorigCXnClKOIqJVaICqFGA01UyQCqSRWSMAKiQk6rUkhFQVKgfzdiiqgFNFQYI4IqqUEgOWMQpURJISUsVVABTAKW6VoAQERgTFKaVBSdpOcVI1CyBJSMWUNBIBoOUKDQKKGERQjVIhCEQYKQillJKMahEqI0Smoi2VQEQgJBCBIyuiu60i2bFJlGHzRkQDTW9jPHuMbDDfBYW5KsLGqNCuRIpvXb0nncqdFwlgcDOAYQCypkTVlAJr6qx7rAQI2RBjJ6BKIicNSYLATcmyFBEJlJJQtGikrIltxloyA66ohSoAK1VpRGGISsElcGEZ0wAFIEUVzYgqAnERUEXpSEVJBCIsRRSFoomSnVRQdmoVshJCqnUiNkMuUUiFliqZKhESGCVNwoBQIJYaUHajJEpAAaVQxG0qQhRlSSJTEZUEREJE2hAJ4QhKqZg4kJKA0oJUrRlrSiqjRAmLTcHiIgzlUIAYYBE+2NaKDcyEf+tmu743P0Dacm4d5I4e4DTA2AEBRhaaHxxsgVgUik8UVLDA0okRulJQ69SKtMQ4Iudq9ySoaCRKsyuIQGFZolFVUFAuhBLIxClQPRJoJYhqIkoEmoiQFKrUVIQWKEFBTkEaWDmlKbKbAL6WMYOCiECUEpkpVEN2QFKp0lAgFAqipLWkpQCAIHFK5fhQtBgCCYGIaKtCboIoUux/jogY7ERSHTAZRRPH2e0WZoidFMQohjAESBqvqVBN2BFgUwiIjgkGR74SAAUlO+aJL33Tyyx27WzcW3gfnl1sOvPGjt9hpes87HxxbH5Y2dxrXdc4sljb1qCrMpaF+upddCLOaEdEqtpVkbJaICKrgFlZJPfvrKKGkmVEVYAaAaCwWmjIiQhC1EAZwTQRjRMlyneIKEjUnFqtFWEVt1IuFiExlISC4mKqYBlSqUq+C6kSskRUImk/paTdBJ1KJEqRWQmg3FzVUKrqqhQBAAUJWVCURIJIUzRXJACioSECpIE0wE7yCGAMAYqNDed0AHzjgwRtXDPdtQDeNhulFJAADBADBAaYncOl72i+7ES8Y79Tu9eXO37ri15hkd1KZZtMOvZyU6K57iXyEPF0wps9xHUJlDgDEYwIRNMiU1mqKTQgQltpkaiscwlXqToFpJBRlhBWKABoJBoVkU0SNSWhKGoUiCIRiKIimlZAxK0kYSREIgBhJw1DIgKoZufdqEhpRCSTlhQQUkEUOFHNnCpmDlSJCAQcQSQgCxJEIAIRUUpWmqoBuUXFIKIQwjBDqWwVcKPNGgwBACN1mtWWXPvRVLyucybjXARQAYABBgACA2Ac6Uk1ihFCb0xTszdfMdIsjuPlfdIL9rR1y7jV9g3oNlG6uBkLb3OdmuK1Wm1cxjmrlZVqS1Un0pVIMhIRsAJWkLJUDW59nSnpykpxiQQFQoU0FAjVhBJJERRSQoqKEAo0KqIpVWRcNCFKg1OikXBARWYT0OwmxRHxVSoI9UqlCASAItNIoDKBSjRUjpQqHJEEllDGVcKPpGoNZQkClCJoLk6DMkuonBQtTWZalYDKMCZAo1jLrU7YgNNOSjY7wznMzHbq3PL0tQcWLGCTbYaBBKSEAMAGVKf1tsEW3vbvgwB/uZRnFtAUbcRxn5KZqjMYs82h/dWhrFmabYwjoK74WrhKKUWkMUYupaCEhJxlbcoauG21CyWcDuTYUt1UTRwpCYEGKVOiojSlQEoTgXRGWUTQWVCm2gSoRTQqUApqyk2gsmjRoMgNEEAYDmjsKlLGKC7ZrVWMBBAFosAq0cxgEgmOCBADqkAAFATtJmguobIqJLKgkIAmpQJKBaBhqDQAlYgIaCbLktz2woFvijOZOjkb+NvyNW93++zLutdOtA5GbBUDmAFgAAIKMLb68llh1/G+m9bOTYtp55oI15mKoQ0MhW6oxI6OXjr3uh8KsFsg1Bei3YtRCiKBNCVNTFe1yCJRwmUpoKWoTR2VpsjqVqgmqkh8SdwImttUEZFARLQkEI2iLItARMFtJQIqMoqQIhCqpcTUoOFTJUAAsmE2zD5QBmjep7XPEKZKEYSENGglZ7+luOXjOA3gBCCgcBOFLKFESBSKknCmUmSqC6IEUQ3XLIwUYFRry34c2m2ngogST0fkzNR8nmm3bX/t6339dO9a3x4aX62OKWeAqsWctTUBwUBzdiPEhKUXbLW13Ne/z19Iet0uud1rH1bALBYQb2QFu+6ObwoH3c1SSTLEKIvTQisVjmARiJgbl1qDQAChcMt2NQkhmkMFMgooiQm11EoKSEApuSkIlYUOTqMytSNTEBARRAVtChHEUkFgisZDpMhJpcFAaKr0YK1UtsozSDO9mp5i9lFaUBQJ6QDoKle1E8y92kSqmpRSiaYlwAGUVhQAlECsmKqVqYAtsxZ2S6yCAKOkmQh6zBqabdrmz97+fa6H88tT127nfV63v77dS2Jp0ttgN+zA5nYoRgAlICAYQGA2kmmXYq/CBUPY1slMB/FskLZrMTPYOFOz8YVuuVHqalcpbOkUpQB0ru2YgEiRRqQqjiZVpiIipFiiIi4RK1VK1IIIQSgCRdJEMFNUVggBFag1KmqC0ChERSCyCAmKWKWDUaH2CAohyibXYVaBqkUwlDuzL+zIrrWdHV87IuLalTJQFISIBKRApBFmiq110ygmjfiSUlVQlWQTEIigmxJBbiQ5OAqIktQUNbxFKORQM5Mpt6Ptqjffty1p1mzjedvn6373sILt3FW8JCIXDB4wdoylxlKeLEJ5io1mFUYUy0AE6mUS8N4g1ASIjcuGSpuh5l7WZmomwikRt5UTMVJzldIsiKhqorHPmBUCQU1IFVFaUJEFLYC0WMv0Z9kplFSCMakkiaKJgpSiqtKimCKjrKWkpZkrwSELuYkUkYhKhDKKiCnCkLgtTo1Rsu00NindgiIjiGNQChpXW1EarkqhUqGEREeKNC1xqlak3VA5GGoHCLGkiIgggUoEAJTYp1QQIkWA5bKSlWp2o7PGYrllkjLnDCTbG7UzlrXZsmG5SygpiDAKCowdOw2swXIBCyBUhtmUUeKG2ApmUjoFAy1RYvHIRS1xxwGUTey2qEVV0ipMWzpPcQRS+9ApERDcyKKWZgGAIBEpqjFNQwRaTIPZxsjS40AaKgBVKEmrVJemGnFMYQQgAkkAEU2VErKMFraVqohIRCBSIAg1xdwkauHSfICWpiqxIkEcNL5QxFd/2xGYkCunlP00KKp0TDQQkSIOCksASCKGNE3V1sK2FEBVRASBcBLTAGgArJFOhccyLI/qcvP3YuYqzPL3wciuJw53o2ZpdA7PYhHZssjAiCjJikptKuexCqqBZWwIYCzFJgk5DdkBIEXrjrWXRuo44+aQSDT2rANRyKqZrF0n5VYkSqtqS8EtMkptt1lpliVKNE2liWgmpNWzixhl7nZ25GXRrCqoQJVBkFRUGIhJaIpURQIRVMSGCkqbSUtmJTwhBsXIiFsSKgtkRIHFyVzVvqTSqgYIahkJclqu3iL2sU1Np1dHaghxeomgyopVxFaJAFHArkuAI6g0ExGlWZUKKA6q3VAVt2p0nIah3NMfSFCcSSmeyX6Zmpe40T041FtrzyY+U2G0sseAxqEsC3FaCgwrBIfCDb4a83V8GRTTprViBwMA7DGv0lp1jZvt0EUXi4CBzR2v7hKXkzoAAG4izbKFKa37pI9sWal1q5vGHTdJO8au/dovV3xHWaSUclVKKyw0gn3KbUNMob6c/pTN2w03zZHiqmrFSLmKUqQKSMQiEhFRTKmuyslsatc1tZZNWsXIjW2nVAZTxiEAJ1KAklakkzJSUkORQIkiTSuKdlepLbJTCQTQoIxCBChgKjGlaYqNxKBIiAWRJCyJjIJAC5dSNJBgTailUrK8wnv2VjzUso282hnAwGJ1yTap8RCkEWQoSydEEEJX7pjX2ts09UEwAQBpS5feM9hC2XOrKsTUvNeBUJ2dO0FZv1/XH2TDWjRADTUxEKkqdwDUXG6uGrU1upiVctOgYJFDADhRGsBURZQTzt07VIVa44SrQWQFSIIuSZqkMCaUqWYJx5JRSARMiNIiNmKtbbZtSwWtNSyL4J6whAIJKy0iHFcRkSRBjaUkE6gAo91SEa+xGT1HARygnKMM0iiQCjThoACiRiMoIaiYZUJgogoUVNAEyomJ1kxXC1lqo8ieHVYH7Ty2eZAXOLCQTZewgUFI2xAUxqWSSWWoK2C96wS0DE6FzGAxKLJqb0J6mzcWEACiSkdFaegoTueWbDt/GP6oDwdyhwZDIIKqXVVEmlutZNJLTRMkFtutFCUiBCg3xUCWgDRarSbH0ezjaoI5aBlzKQoUcJkQSZqISpJCqKEkEaUUrTIiEUaGtSatKALxyEEJTpHyeUiIkFW3wZUAVFC3EQQraVBaOy4Kkd16GY+4eoYSsCQZrBoVhBHs01SsnWCGlgIkqpACqkEguKqROGVAEAVdV1clsBXZAiFkMV4LtfFYiPjGLGSossEMQQwQZY9lsVwdzQpkd+1ZUaDcUYYQTu0eozInZzGSGWbDjkUOb6tDTYEkoOuc2ENQPi0q82mTT2neQ6MTK4WkCRUlEPG9qO2YqRkTSWjSikAEAhGQ74ilz8UJEdpCSgWVSxCQdWVCpGJKiJQw7BSAqIwCEUWUwSGjwEBKpbFKNKVdHSL3BEVkN5RJpUWDEYDjE6ClN6JaCzP1vPK+aZByT7J5ksEoO52ertJDTWStpWGVUwrQAquq3VilpZDGiBSt5URxSstNKgSDimBVuUQCRDiKEEALV4dCBnExvsEgCKk1sCHYZinVhJWj3lW4fbx2fREtOwQUF+nQsQCsP5yZVdsm90buZxq0zVcMAIASiR07N1+znzp/FPP7xR+HT0k2ZtnqlQQKVFuqzM2tUs3KstuyYxo0myYlRARRgBCRIqXIaAQgK+1WFeqQliQgJVDRUhBFSyLVlURENKpxIkIETZQCKQZipGog0pyWcBopJWhHdoWDcJKTAGlcO2alzmq9CrRICERrW1M0A0mBIl2RnGaX9LYvAaQKpypOwABwOdUwZimeRqTlCNRulSTRWknry7QKdoIcuBosqGgMJ6jcc7dsOwsAkuXFR5alWKgCeWS0WOdWYX7pr7/46u/PFc9NzuXc8O4xtrbedXtWrZglUCbcy/G0swMRKkpHahr9W3+btqv9trCAUC6nrJpVaG6l1FYWkV2OIrWRS2ZXEaWEwJSmlBtjE9l5MgBQCxSZU6qCnR1HlYoaFEypRqvolF0isjhyEioctHiBItEUU5pSHIEs3YiKNKXUrspqKeSbZJdax4hIupLSeFqlKVVaa8h2L1tzIzBV2ELtdhWl0iJctVuO7GZ2aAelM5NeO45xUicaZ5/oQhCFQa1pZPRmEydJjAhhLmA3YTK7cariCJLjdApBAGkUqSVAFApNgmqZDd6sv5jn+xf97CVEh77XLWoR0LwldR6xah5CWWwAkEgsK1LKV7XubVQpKp3htidpgpCtQJpbRGFB0iiBEgxZQ6eKiCjFpkpN1dLynMXgCtWIogvBLbGgMasEAlFdAKF2JndLHZSEYiGMKsgCIyJLJaZTpKAQGdmGIkkQJBopShCVJCTZxAWtahWUfUqpXJoDpAKflq3qKsVIB8ZPxRAddFohBcMp8JSrrlnF7tX0DOybUVWDCU2BGzkiGcIBocxQZCZMYdcQVKiiELDCIrIiiUlREDmaDkyZT93z+fLvSaWMhaJ1u1C5m8+Ea3NiGXkaL8rNCgozpkW0SkNux0jVXSUlNg5hUJVNQCZuBBRMkwqtOM/onVG5VS4UZw0ikgypAkDeAioiC0WpCkDT5s2zNRSQEqsVfUyUqFaSYpFdsBIui4wxJgmpRkI6BZKkJUlDqFUIgjRRlUTSNKkI1yE5bk1TUGmtUkoVxThVkRQiBSKCAggEibl2gu2ypYgr07NTSEs9UgVIgAQFQUlwSzIKqCJNFiEUFFTiSEVwAJSgOSgQhFKkFolZuscxhzNW4oBqNamV3LQPxCrY0ra7MpvlRRJmKqUCW7mUziWl1qWExriQoq3jNTEB6bmRCleSddGydmDtRlFVgAACgWYTdgEADABN2lWiKXIFKQAS1mBrJLkVJVHSNREqkwAgDgUWZZXWkhZKJVMdSAgQkZgUQVAjkGgMKkglIoHUBpHiOMWF4jhlnypLhhUkQEXBTpc4QMhOIWGOAhiaiFSxqia2VEpBVZVSUARFxDBUI0FYAmscudptpwCR5EoFhcgXMoJWJJZYFRCpW+8R5VSVsiw7ljRa8szSqT7JxhQrVuAYh0WreNM1Cs20XS6d6pBL6qYtV00bw2FgYYDEgQoWCEtdIqqoIABkBwERkarcFXeAzdA0CqrlwimkFBE0DeaJtAglnLIDISAlWlNbyrKoQklIJRVF6khGEihlEQmDEBKRJqSSoqUZUqlQtpVl9GdnmZcArasHJTFEFZKkCqdIKaWBS6s0l1hqhgZtpQJT7xYAKCCFJUQBUFoJAREoLbnNVCMQmJaxJWlKEbvUkIMohXrUPn1qZyLSYzfP0R3UUJbh8rO1dUt6BfOcvvT9D7WqYcswe6MNHp6oTItMj6JNK5To6pbUbh3vXN6mjWg7dq81IXqKRLVEIbI0RKuK2y1nt+HCaL4iFTxthh0HwEpFzstYjZAIxpAGg1Ij8yYqTkfQkdRRpZtMGysRCywlUJFoHB1XFtWAhDHGRBzFcY5ICEkhLbnYDJWWrZhGg4i83zTsmzTVTMpVtExnp9Lkci9WRSCiJFSNG6HUUgsJQyJGBJDApCi2JGNmYClERFgFxSoz3m2GkgZRpCjSo4KAQjXl9rFPfk2pOHTtGEULJ6KyG5nVLh2fm0+36x21+/Q7dWYWKDUH47VHm3C19bpu0LCQmhul0lXS7pUgLTkWCxcou5a1HQMlHAKpFVFSEQmIlAIUpUlXkYpIjAESKESBgkTACBAIALRKIZgCKVKkwNcZx/Ll2eJwPE1pHWGqplPMpKRGIiKlgQQohLIksyIiSY0izZr8pijSCIBILuDKaaQJJaPI0Cwmxsja0ogwlRADCDYxwkzWAMS2JIBIUWhG7BaXcIOsSXFrGRSkBqOc5U4lRTFTVYvyq/c5yGJ1iiqVCCR4tWPWbQAhR04Jzq8+XVtTtYJlcZJ7fU6Y4EZEtNkySK4qfaqiahAPjmm1ULpGBVOtoRU1GqmI6EQpLU1EbqRcRTQFpxIVGGQAQEAoUmAQZCQwV6mkEiEKJeiglFLghKAeivJ4rK5iTNlWTGOwkVJClEgYFIEEAipLqbOtCilxdyWKzcs21ShKU0UpTkGFTqnEm/JWNagyYGmEmbGgVI2gYikFQruXkUYzsrZmk5nssAEgMRaQuopEUaXIRbRbVxuhRDSUOI4xxIEWO1YP73be+qzP/7v792F5AxY1YseyMNkVxznH932v2/csKytYmdOGo0RieXo7axmTKNsCTUed1mRH25HXZCPY2mzYDK7cq0gSIYlyXBWUUc6Kypw2Wd3mIlAISGKRqs1QEDUlAClVVaok4RSQIlCzggAoMZu1ZFa5FTiVJlXNKqJKilKKVJUxWirGaUogIgGxSCWdVim7oWUqRlqyVZoUQxUVpVIXkEQU4SIamjVUBUZek65OWZyqYD8BpbVpoxGsavAsZhkUQcBuY0FhURMhIlcp0lSgkCwLyJYiRIhpFsYUHf+zfP7c/fvgMRxgiAMjy6qZmI5MsdtXbTSVFZUQEdQkxPotem5qkdplSOUsQ5gjTIleBwDTYkxpiKwgstqqjnPllgSHC4HYhaLkAIVqSBoIKZMkJFQGR8GpGCqnoMTMEZJ7nLZMUkCqppKyUxUp+C4ALpJKKRBMQSLLzdhJpUjMXCUaJcUWFA328267ZuWyZmtJZYw07kq4wlKU4WUB5QwsArEi4lNVKUsDxymltaM1DgSaaAo2aKbxpRVZRJ6JSsXm5aBBqQ2igJayrFagCJi9SMNpd13InuCvXXePEMpl7VGCaes2JA2huc3z1dXzbpI0WUnNFAgFh9c9FSSLQFw7q52X3aRrgoiEikVTTuqaEK9eLeIoUUGJBhCnAQJSrpVSbitQRUFADVF5kTicmjSpSIylKlIEjUjkqVqtpqIqDMapdpwKAJZSJABGSNBSKahVIhKDY+hTralWs1aFrRhJTSn7bcgoTWUqLAhVVKOqUDpj9rK4LAshEUiI2VXRTFQXqd3LJi17t9aMSLNmyos4hWL0VLZtzSINhICxzHZUEUdFAAwrGIihhCLixyG322fXu3rVBZfHeAwCkGmtEw2Vm75yt3WPtDPLCkBYBjJFtZpyMq1WKKNMlhQRnRpmbRUC06MAraWslYRAl6QgUEGiSECwRJF1BCismpAAjkaLhJCBCklKYFROwCBCKIxMzjzsNKNyQ5U6F8gJEQ6EImzNWjOkqdYaW2+LSaiaKrEKFFGJjEIaIIjGiCSbpFAnlaRUY88WoTqWZQFVagpIU8azbVMFlJIhkEUrSkRhXmAZIpWriMxEJBhBNBgpM4coCETUALIOIaEIVfjFQ163v9vFT4sgY2NtNZyInGqgGrFr3uzumbm3nRdZc54kIBBWNTUga4VosQhVrYKiMQmJAJYiUq2TCk6QKAJFBCJBBIGCSKPdWItaVhABRQrsKGCFAgoESlJFSukEgFJKodOouqniVBUrYGBVKVFQsjrRSlQlbFJGI1pjSqlwSoISUkppZCcGGmNKiIQgKlFVtEIVZHF1LAssJbLebu+bbWakrZKqkqJmkO+Zwm5SiiipFVW77KaJLNAaALtmaDO1mnQKBZVoC0AMuCFKa3o7//zfq7963bm/22l4gDKUAE5q0ZKqIc4e5doXQ4pTjLKCZCmKTLIgidSFpkXMgCiRCrWqJlHQWiWuYuDQhKQWCKlygMopjbQpI1kklxBiJYgSEUeL3K6BpCUMBIRUu1GgKpJVQg2JFyVBVSvzWMlKKYUxXkGFCmstrSXiEdO0GSkypasbBxVmghNTYqRnZ9YSYVUxRcQpclJSFdUI6bFQIJKiYhApYso5TUQCDABmENMGrYadm8GuWGFQmhFMJTULk2LZhHZcsUsFshtALK82I45wYt56b2d/+OPDr/1di1/EZhnDaNQqJEGShVzcWNtWI2IKMtQsuymSyCTVHaqIvLbzrqLtuKBChYwkKiuRQNCQdRaJ03GkrWhVW7ObkDQKAcXRZFZKNSogcnOUEIdCWiGNJg4J1CIKQAVloqw0s1usOU2pSRGfZlYwKyKoSZEklhiprGXNErlIEcZKBUA6UiyBDAixKsHBWpJSiioNTEmVF/IQjpfOx6yHIsUFkSuRjWhra2trM5GF3cAEdsqoCsTBoOp9UEKTTASx08zbFYVKaf524gUw3mW+cchUb73m956NPUuLN37E33zmfzOUMbZbFAdRQonU/B3pFbfz5pjCEhKyGm1duq2wQqezzs5qX2roZFkcVTJF6QI4wr2AQEvFXOxIPTe3Wk1br00rlYXVBJVajZlLIFEhpZGjUzr1Ai0KsbR72qhiBYAIgREgwgxuSjEl7TCQSEAKSnFjmtQqrSlaEkQlYhZzCa2qtJrWnIoJaTXbBioN1SxcUqFpopSiSgq1sYDy6vL4cO2bkObQDEcTRaT0VkopAJwCwak0KAXArEq7HERqIPieNEEBUNgfG7YYQhkLqLnN7eR5Hlp393v3LqlWKnQiN+JCRCkIKWi1s9JNJJpslliALgJTECwTQpaIyLIMmaQmShUFsi3AMAKGWlYhlIlOpJuqNCCMAli4gkhUUY1ZJWUIiooagpAiqEWhEBEDlQJKJCUFKFWgIJQ0QwA4TiMIagu5t0LklGAUESEVgiVU4UpqGUMEpaaiSHVT7gkEJLSUYttGqrKILKoCyigFY8iOpq2hAhwjYFWJKBgsAYwqlMANslJkNkCVUoHiCIpoG9jysnGNVWPGc3D23fXt7h5QyGpFgd0xSGRlLLiwgoWQcjurHEeJLKsoQ+vWFEK5PlOWhmxQNNE0USfMFBABkKlGFewuVQedHSpuq46AnOVQgGZJBQmAJikVEZQYMCRWqBiIBgjsqJlqBauYmhEY+SrJR0oqWDWIEiVL0QAmdKoRyag4CKeKPgKnFIoCRzRNZJmVmkjcqAAwqFPEmHTapqQcyjYqEyJxKVVTq25K06BVVQxDgCoVhIPLCU4piTmpQK7QYLeymxkyEUMBozLTKmKiaUR55nbOMZWu6+WrISoCtFbSpioIRFjVkRbGXi1bv/JViwH1bFm+NURtTtCqFiWmRu0SkCgopSAigoHQVTVSRZWJOoFQUiJpCyVMMiC0oHKwQxCQQNyolAAKoRJEtDPSqKFauw0RgSxSrUyBNAUARU2VUIZKBJSSuFGRqIbSOFVBFVHglADQlJmNoUSIHGFUw1qlC6xaq4oYKUAx0rVWxlVNAA2twtSsxRjc1AwgVuBIYhFRZmk2BKhKp8FasRoGVYUUOJVoKBULR2hcnNKZc+izda+FZ/6OEwIMwFYmd1ugSMp1K8CMhrvUjlpEaFQA0kBBSGQ6OrLO8s5ah0I2YMssANhEDaghUp6EVQARilRKITWyFllESSOGSADHod0q0yqibVcmAygioMApwyFxFASCcARRFQZCiUIBkBIIQqKtAkVk1LASSZOQ3W6VSykla6RAZIcEgaaQoBmlCJxqRpAYKDJCBGIiiaAAMqQaCAsRGIIqUDVBMVzazloXkjjVTlXoj+ckxTSAkQAoIIcl+9o3qXWkWpd4GOTWiJlU2pJWRK9EtXbh8kUBNQaplaL/NqmwxTItIkJG21261TLv2lEIwUBNssTKAoigVEzbcUpRNCUiAEpKQkCLDAFKG6UShQogUqqFpIQCighbhearEAAozFBBShEIKnxDZQkREVmStpQySE3gOAWJOeyWZpvHmnmmZqscpVw7SigQQMHOiAoJLZvAdDlNI6YxpTSmUwCgA4wUTgqMGEDgQIrZqYx3ToJYqqhm6ALi2UokCROqJMAglYMiwoTTVC2eFkJKoJSgRhKSBDVVK4BWWrJsmlbTMmbTtgsQQqMQU4hYI+sU1SuERNHk6hYIJ4iwRBMAVNYouFwBBA3IbanFkUAEzIWGQkgIgIACKCEE7I7MOiuaRgACSgy1m3JbhioJCShVSKMylUXKUkZKnJZEhLoRACKquJUCIDHMKoFWJV6sSslIojglIRJMlOTtVkEBpIho9yoMFAUIAEgiGCyhBKAG0sxqxrtVxFQgGtHWtmyIsRs5ZqdBWQqwG3IQlSHgq9WLd75cQjkQUhIkQiaKSBSw2xXNvKOGaieBXiukKMQoFBnLIYxVdoghERSSoC4pRUIVoJVIBypCtx0BAIHV1vPZcaaCAGtVqcoEodg1A6FyE8ouqhgFyiM6gytUEQFJBVQAoMDSjgAlU6WRVEopikRKI5FRRJCMnp1GZgolHGFwYKCJ8CD7Ji0VUmYtBKA1qUQpglKVbymVQ1VGACCjgKlRrhonWMIMMdBT1kozIEVU1gyzZ7Zi7zaqpiriFKacEkMyA7bNrauVi4UcG4XCyUQldQMpoURTVUmFLdO70VavSCKgEoGaapSE1xYYWYs4qh1AUohKUaRKrVPQUalAQamDQgAsGSWNWtEaXQBAS4lSV6UyqxAqqoqgKsACGqUkQEEptSwNA9+VgqMc5YK4QmEVZxQRlElTlVKCAKegQEtQTkWFKRGUwSBurOzEbXMhNzUVBeHWghatUooUVLOTSKl2A80SRERQoijsYOyUUomgioJmRmU2Smvt0102MqTW7E0rTePmNCgpRdkNEpWktJpWQhHrgkA9lkWNQlahQBqBr0rGsra22jWRiBAgpKyUqEWaI1FUlPSc9TSCVCYqooQiqQrI8uKod2jCiRURTfOlylJUCSJoQqcEBAlRIRCQhooITJAA0maRBBwBU6EiKSQkBSWkAkpaKo6ExopUSYXKqVAJfiIIIigKAFNFHAhBIRqEIgSK7AKkYCWStYKatFtBUtKCanbrAkoHkFmLLQVOBaSCEd7MKIJSXTRCw21tWNe29DTGigkEKqlGhZpIA7ppGpcqQRQN0FgFVBcJVG4CEeOZsdgiWxYpAkjUmYoCTKMYy7pbneWmzT1WihARoCILrqqqskx49fRUpLKwJlI9LbTmAEdqqqhkllpVOqmpKgSgVENZlYEiBCoLKxCQdHvigqFKSKWUqDRV2xkpkIoAmqgQhkqjCgICkVKUUgFEATBLKkQWCUizKqrIeaqUQoGQCEq4jeA0gUZExAZp4DRVmbU0JT2amFtRytJUMEXMNmnBieQEHwq5uZSQmJEIAGEKQFVUiBOBVQRlIIIqCKoplCAgoCSCZmJLisxeHTECdArVShkTaEwEEm2X2butdUHMWgmUMoCSTIOuKJUkq6ISygJqJSQi1CWlrEplWRNSiFpUABFtAqyAQJEmNTUVJUKFigCpiColaaIEBaDAiFmASCVFZC1BBIIUQRGZygDSRsUoE5KbJhpEREBKpDZNQW4kMoosk5aI4LvSUKFIJQLQjIm4sXIlzcUxcbW2Ldxm6A6n5ZhDPEhoFCmqOEXARHZTqBwnE7EpO+qZS9eCEJGkzVhKhQogoBRjrgUiAaJeGykCdF0LqAlbyAxiknBp1HruVdMoZbZW3rwoBSaRVQoyN9XNmURbAFRQJJUiNTWGrFKuuVc7xAq7GkQoUgDeCgQQoQw1QYE2RQYFRqoEIUGtBCFuEKECK7lChUq6qvgGIhCQKFIVKlHECahMQUqNIhBZLKJRAgRBJVQWM1YqBplpQ9zKTaVpBICByZFwVSNoVpsmsxbeDS6wUyh+CUt6QnYKGgHDTKkBgUDJrgAEVCWgCYIqJBEhQGTlrFCwqmnusnpSBa0SZCTThJpRKGImQkFHMLdRLYtaaKxSaKVKcRo0ipRUIbuCIFJBFQWpYncdKcVKXMvCKmsyd0CoEGCSUlAkpFVUpm4T1Si4DByntVIQgYgKFeFEyK1AiEglFaTCdwQQUBGBAIoMIBARVCIBEiHAbQoUBUXhAKWoJDnATAhVgoRLIoUmGhDELhWDrWGLhX3CdeXQCWOvLSTZPZsoEDCwSkUFB1UiaQrIUgRk61SRBjoiKKAAUYIKq0h2ToeRrmQoI6hOCAQqK5CJEdWsYlFY0iEJaxKgCSs4oiYUKAtQU1YBSlSmWiElJgWtIoRWREgqsFJSgqh4TAQKhNoyFQGzC9E2IUlLNURVKY2KULUIpxgoKaWMJCJVBOJ3lqWf2EBCzdVEqAjUlDQREhJQjYrmxpGQpFXhENuRKpSwpmFlDbFGIeyqSCNMTAkp8bzSaqucUnoM1IKKHrqLCCNCtVsVKBKFRaggQXZGE8qNhIoSSpQ6JCKrRRTIEskndhZXN7KSgXQ6MCWKTEVKKVTqWg3FlBxXTQUxKioJKanKUcVNUUkJOYlaZxEVFVopY6VsVbpEZcRR3CghIOLIHK8iNSXRVkSCipKIRqEkwkUpSREqlCpKqQiREk1Uaq0qBV0Vjh2FiJuzFBFR7YySgHDLkIJuU6O4MpeTNSogkFotphISRRAaBE5jau31HiBrqx1NtLBJESlFlp2dd3bwMDdrQ+sS2+x5iKlpLlVTa8Buy24KQyBMIFFiQu2sRFzOSq04IZLdnB2HiqyECrBKNCQUCaWzXB1IDQVSE6VQBAalk5GImFUUKpcKuqAiCjKRlLK7kFMBBUFEXCCuEEyUCqWCUtVNKSVujssR4aJunb6J0ynKlwjgSBNhQiJUOFIXkQjlLEOJCGqyJDIVkSIkonYKoHbUTVD8ANxorcwpFJ17sgpRAhGKQgokkzNZBwQQbldkJIptWW+ZtSAyK7hXrRkoOCQY5FZNFpHhpnZLRluMGN75Uj7O2IdmiFGBqESVFJUIIFSIQCNHpASr1lpAVgAhRMUaJ2m4pSogU3SIK4BQSjBNgluFEmqcCqULIIqqAgBqjqZE5ZQFKZI0UM0uqzHWaCUKTIFGNRINNIMKUjFxxEnl1qxAqk6NAlZMIq0oAjCpNKYFAISIzdhsKYVKEbKrhFQMgoKiiYhUAGq9mbVShWCnSkdIFER0UiBESjREjAoCEFZG7XGkYxlLOBHWhtDCi2zRlsRV48I4nLCsvRwKKOB4iWdO8vjmq+/dNY+6WgMEUkQREanoFAZAnBAF6bGJALMGAhUAJEqAoQCZagSh2lwiXwIz6BJBAAUmqioFEgBChe9U3AgoWDELRFXbSqyGQE1MWykECAIkWqiCSZFFAIxAoAJSARxnx8lISpHhVIhSSanVSqlqVbGpiEzCTRVIKSJCEE1VAFBpItKbNFrpVLtVSLFbFUAglLAEBFD5cjXdlEaBNQEtMV2LY6mkeFkKqC1QjeKKGnJZlBE7SbNgq9koK/Xy0njTunxyEwwESMmqlCaqVERhESFRICglVeQgRCREQrIqMhTUOV1O3EjBCuS6jaAaoUSEMUEgZgUEJboqqGpSHIBYi4GaIk0D04RTo4imARSCNIUmCFIzhJUgC6UVVOFUu4nT0lAwo8AViojKEiIIpZRIWaBy01hVihQzi6pIYVnUsizCKcBo02yzRmuaRtMaEQFzjcpXAiFjVRGRSqsIFFFQKhcaSUPClAUAeHrKPr50lREu1SK5liKSjLIzyvJVdVmVZQlOWa5u3qk+tpao0++VBw6KU12xK1ChCDUDKmhwWAWWIhLiyykZSonIqJDbGiI1TiAkIkKyFaENoIkSplBtq5UyAKod3GqYqwWgqVpNUwpYSxMpisoRoNIciVSmKKgEQUlEESkQKYlYqkoR3AgJQgaqWTQRjaSiVYhSSsFNKQ4AUVU5oRSIAIjUiCxD05jRNK0RDVojjHYqJ1UlqlRVWlEiWhHfUCotMQqlVKVWugwMQKx6TrNkMFayJFlV6eyjfBGvLo6hOlVwTYgvS4FSitdQyixzTTtr0xvA5CoKKqISRUgTYRJRJEVVIqofKFChEFBZ0tRMBG0lqpIiFpEgMasVrRQKlUkKVljFaifqUKERRKk1VSkAq6pQlVIZQhBNkASkoMcUaitlJZkSyZSGNA+AVEW0iIoyVdgEUEQpopxorYm0ZFaVwMCXdJUqpbRykUoIkh0ZaixrBGAMFHwLilOijoG5VQ4gkXarRDSCQAdFq5UdUBgBtsljWnZJ166xa0ipLGvUsawuZRFr7ook8VJCIcOLdGi08wCQFTZm3FIFoARFKQo7ig0khishlLiUgisUNHEVpTQqAMVE6y1plXWJiIAAQiilTS1zUENBBYUCVghVDUBSlKgEmDmBW8EEEQWqNCISJLcJiaWpoolqagURIaWUqlQlY6RdCosopbQYxJapTGmdyEbZsaQ0BotaQwXnpoqIU7erwGxL4bmbUgHwBmmtyQ4qEZkpJHKcm0iMmOtWKYUBM5jZ2hqNITtqsgNJNXAX07FQUCqziKnCGgVREcYTUsQiqpQ9RBFi+VTcO47ZNnEQDVq3CsMJxVUFmbKg6k+z1mPrpTU9phiZLQImEEFkkVCAEKfpUeZGGnxHg5orayJiRQABG2lDUBYR2ozwPSAaKsARZ2hSIstERdaiEk5DwsQ0pSkRJQIRlTCEiAPM2C03VCAGMBFRpRGpuiJKJcR2xlBsCTgfNaiOO8sr61On213i1LxrNG0tWSvllls4IRDIblIYkwTZGawlgAhkTWRNYNaW2Zo1Nk+bRQkwxBQWlkpKKYuylFXj8niZUqxK7RWWpaxTXa19AxcFvY1GB883yHm24+2CW9C0YmqqGHWPEBRtgwggZohntmzWFjFKUJhEBqhydo2YUI3ACIBoquaK1ECVs2kIIJCsACoMSiQwJSI3rJRwIqHarUK1E6pXc9tYdSul4IZ6S3GEKmdNCqEjKKOBAaeLVSk5yt2+OazagZNmdbsFSTQxTRiY0UyVkEDrUzf33MTL3H/6/Yf+7e/7996/z39z3R/Xpq9/PX+Zz996/nyWCmpHsSQiYE5RsAkaM82UOGCsbaaVUgpDU6I0VzdXrpSCmhg1spWasSy1kM0WcWEr2GLAJES4GKsS5PFSsl1/0/mineNz6OeEM/Ta+GrBim1mk1kRzKzRmZRMZdcqiMLIDWMlIrIIAA0FIiJgQiFNhAS+dnMkAkEIpwGKlKpWCLcElBJeGUko+oaQYqATBRFNUsFG1MSqRIgcJVwZUYBSBgRAKwCtlNREMZEaEUAQshJNiQaxAtCgQURDlCiNEEVsSqzJV335r8Xyi+e/+LsafxDm38STB0P/fa+fbnY/2Ox+ZHn/z+N12VoNzBYUBAEBBQFQGkRQKjcBWkydKRF1rRI0IREBCEDYWQyJtogIhFYDYOWqRJQgCCgBoAxsMQwgDDYuQvgQMPNFzg5bq8wmhiQe2aUnKLSbI+bo1Z2aUojSUDQXsStABAADAAHFrJQAJCKxtsBtVUZApprASiCBWBWU0omCVmohRUaA0QivEyRAAKHq6upgAtXIMxfGQiUiIU2RkAAQEQZihARmoUVVFCtkhJAIRFMiqmgEICMAiGjQEEMMrmaNrJ339ZH9enZ4zNjbG9KaKWcHV49jKZkhPD6q5tCMxydrPnT8rR+uT2w1gwdWUYqACoqCKA4aQFAKChVxiUp9ABGJaAQAqI1WqGmr3QopsQAIUuUWcUFYhBCLWESIi7huMLRhkACjCOdkNLlhLi7fmgptc3JYQICZEh2UKevWoppwS6wEEAU7UiGKsApwWg2rSqSEaCRdMUICduTAatBxRIYCYEUFVaugoggQABgBgVJC3SgEQHIFWIdSrDEwlRWuBUkjRoFACGST7FIRhBAKVVVUqWwSBDIlIiWjCNWIggQYMAAEMIFLz0zj5bK8vPZVA3lX0SHBTnOICsVkPMrscE1r0qQNbNx/px23f9EYcCZ5RpeuVBYUXUEXkRKlRKA0ejajyeqV5kwNSLAYyXYBApBCLI5gZWF1BAFAiUqViEopQrNMsgjVkD3axrXaz8YdRjyeeXSeKxojnHNmt2waTgt6xg4DUBnOcucCqogDACQQSGEDkCgJTEotUECRwEqwBiSBTAViFREAsEtFR6mCqkLLVSW8Go1AAHB6WVCSQkUoNTWpNgIiVFEKkFUjRkAAOEQ0rhAVkIrKKEIEtBWEQlsoVUpARZSiCBAghgDGyovBxTfyHtj6jqyNVjCWKrXGfDp91jvan5OSGIjYSN1EaotxBLSbNdOdSRabW0s0JUBKRKAAvbVYESOqSItFhiRwARARWM4QNxGRXiGLJY2gZMkpgCjgFioBx1IBvte63GrxdQek4vfS5spy7a2Er0fnVC6wBBi3AVRVwV4KcYilSEQgGFAAhkApDqQqKHAoOaXZTeS2mnZrn3tqsY9UJYCipA0rV1FtssrKCgCqmUS1IRQj2EEAr9IrHGpV7bZIzYGKJqiYHVHXVlEEiBWpKApoCpWsZDERqxQqVBhYJFSAAGpWMdpCSRALwYQoiXBZuOYw/Go55INy6dCsT1WYX1rbxe02UZ2mkhXhmQ/36r5zBZdyJG6CsJGtzJ2+b/Cmc2C19IBQQcpRtIY1pYiTCVS3UnOJRCkWQozjSJFohQqlSdmBRJQIiVIYh1PzsrO4cSpvMLYFHJrw57kbt1RoJhH2w2e6jm06szrtZIEFVQicpiWEeImylFtVIagUp6AUFDeUEhpTO7cwErSmmZX2CqGpSiiptYDVTZYCKptqq6IKVEXYEQFQGcBoQkjAolCuU0NiqToZrSisIiJdWVnVkCQy3FYEsZJMlTYlCnOZdCk4EBGJiJIpLAGVqQgJChEpFAhqYl/0h1//waC/4eB0SUNyHdNczzTkY31jPixw6wZ0NK4/fltzd2tlf431KEFDcoa9b5Y7stv324u1zTuqDIiIgzaxGRSIlLnOp3WkKEgpVW1VJHxCSmOqdG+NFlWgqFoR0xhDw5aKV+VFpHDCw62FbKa53z3hdhCXqsV1ljV0pkpS7bQ94HKqqkjBTCXKQi2LJAxIAQoKUOSmCKtSmlVRERxpUyECXCAIhRRAlEYplUEplAKUBAWUSAMHNgHSgqxI3ZQKC1WVHEqJCYuYwqWU4mDnJiSoHLECQpogAQgBiqpSVYXbKLIjVju4VpQKVBEowK0aJqhMqXmZbj2f8m1iSaZhIiyXyVp0W2r7WFdDZwHu1oetOx15eJcOpAZpGureOyT7z2t0zq//7mz8cec7f/+41pi8Nps1YKNBcSNYJVCUSFBILWqlS+s01NQoIlAo3aayUrtUba3ZgLClq2tOKZzStebpDKJoRViwMVOKbVfv1rC5YEQGBY0Fzla0GOvSBpSYpAhANVpOARMpod1K6CmsqlUMCAClTWMNgAhIFhFHhKiIiGIkwlVFR5WBAQGAzySgiJQAVZUdoBOSQpGqlVI6u2pdCKNWUkIZEOFbGSkUYrqqKi1XlRSlShNETbkpEUCEUbUaXMhLLwnCy9+0vzTfyH/8Ox3oEqfy3UI3SL6zIc3FUUCGmdp8uWqRTSUQSlgxy8QUN7Ux/7P9Cm8nbLmMefbayxpaO41BqdRBRWVFiqxCIisRKIEG0rQgIU1RmUREtNiQgWJ6mzKWFRahdSaNracRH3YY6RYsxLMMdwM/Oqb3OmTk32fXLSwKKYoTAUBWwFBmkgEMNRKYYGv0CSjCR1GGFJRRik+xSrKwreocnvMocMuAAJiKqQQGri0GCGBeGAG2CgCMVDbSsKyI11gW2VhlSOsE4KO9ksDAsawIpSxFTACVqUaAFcKUoynhigRBBTAEwGyRxiOkmxrHesUWbSMu0VUzMcZjdL+7P87iWminqeR/DvrLel9Pt9P+qFZuBgRR4oDCqYU7/+Vfv/qX/+AFJwE/EYR4HqdEIBBSSJIkhSCDAoIIj/BIJEFpSWQRqErUOQJHabod6QvOcIqIFGNMqSwFlZd1KOOF5Xl5eWPT3Xnck8xmDIXXg321dSx3rA4MkQ2Hs9rRQBiSRQIAkKHSgoQV5JmpjDI2CWJkshEqWwFYZlf3J6pJqzZaTjEKME+UcVtSPAosBgUxVQgVqyGYcFe2VVqAYgAgACAwjQkVyzyGGKEApjJhJhOwAKI2YG0xShQZEInUIqQUgFYghjFQZq3bNMLhtjce7vWENbNN6n0d3icY9Y5PE8vEopZ/7rlSvqGv9q8A/AJZB0AHzpRpBmUHDhZz8eXkT6+fqRoGZqFh9u7D5fNb59CgOk6MC2Syy1HRRJSQIQQJGLW2SioRA6kyRdi1nyqiwClyJWute0ITi131iGmsFrGK8nSbvbX3vDw/1q7kBVif2ISRSk09Gmu9bKt1nnNe7XZtcjq0uhLsimSoKOOVRBiYsJowZBoYBAmj0WpzSByBPYylNMcoRNIs5ggqeCaZ4NOWVjwCyjAQZY5HSAVTPYgBIKY8VBhVYPqqbOuyaZSVyZoRKwQQSA0wCNZiKUnAiIUooVSWShiR1EZnFAQ0ahYFpbQVIoRIY1ocKmeZEyfTo5H6Y47NCK0YfQMsg3MtGffaT39euAPo3xtBAEYGoTBlKzNh/EPv02bDk97jwiCHz+Wb/9wX/uJj23+9r547n/lDIaYoiKB02OWqyAIJ0bKl1lLBCBKFSGuwBECCyo6poqTK1roSkTVEwEw8k3F/37bdUeOF0yxU6+reeKueZqNmrJFYVpkzxVOYcFxIx8BqRTpRAIuB/24UTHkkAzQQjDRM02Y151lb2j6ggG3HDE01Q9AEkvaMVWvskwKzAGkEG6pKtl0IAmQgYQHUABBppRlCQGAYsc60lC0rMxYDxagyJIN7CzsAIqBIRASiRAkBMYQqGSKkCABEKYyGOEKjkMv0cT609ugCiH6yTXiml6vntNS9k5eq6vrWx9f/K3MMteioJx1USGLj8eErr3lC+RB8lCfdNoMa+8aLT/rZ7/7MJ7/3E1/z4x9/9fD7rK9GGcJhEEUhSRKz4EqSSOXcJiGUZVEapyqllEgdRPHYTNFErRmixIszSXvTkFgSs4nckqrfDDIc13kDajk6BWzeSW0VIYCBs1kgA1ZqE6JUhdUGRoYaAwBiI9NqU8VP3tfnc7U3boBsVFAAgIpoNDtZMLFunxYrGxArYETJsboyFkxixJRpxahgBTACTGIQUw0DrbOs4OXVhiZWEMMigZmERh5NrxesVsqyFBjmEJGpNl1EaZRNqVqpIFRKaWmCLTHEWIGUEMwVL7e9ZCI9Wjps4vNxhpRkfHabkaf+Zn6ndhYGHWXMnXnKqGhKcnma/QkPNehEB2PJ5OjpPPD2B41Xt3W/8l0DP/cdMzc++VN/9Ce/cjoT4yVOCFOkJoJCkyy2i0qVlKY4oJKJcmVyVa605pJcpWhFM1dloY1ohJBalQw/Qihwu+VopNfpC9gQ6tZrYGt9Q2Tq3LX1/bY1JFYAbJTjNCmruesPJCSAxABDNopdAMkAikx27XDjwhRBAAIjMfBdyAa4Bl4FMAJIsQQAAwEycGySQUChWQ5gBIBBhiC2Gk8NNCqAtTQDII1V66//766JosSBcgCRVerMFWcTVgwKZGkkzq3SiJTKzXQ6UDOPpBKpaszM7D0iQJDICsCm1x42f5SjFYotztRpmJlatFfj3HGeMtPUSn4qpyJKyCNOiNRoj272nlm6jq9rq/uV2vrTzwf/+//d+NbXH3nwjbnVohqKkCABoy514o6oEg0OhFBUCSwCAacUaPdKmiRISkJ0I8UbP8OC1mYIE2C+7R8d1DIjj56khlJdbB8thV3bIhABxKWbboqQ5rHf/6u/hAGMAAYG3wkA9loI4QPAMPh/DcSk4RHACNBADBAGBqgGxMBUWKpNNaqRhiMG1cZ0DVPt8aBjZJ/0yVLMQDVEkgykDXzy51d/9X9seiOOoppQpRRli1DXAhShwMyqCcUQnZ2Uajw9WQZkdX+vm2q2q/nSMoPSCJOLPS2ddfwEGvsKC0hxCqCsZOPcab5mv264U92XIHwus4YiQSQbLZS+NOAxXLiS4s5tEgJXHF5mSf6dGVnC3XkV1dGDSUVRwgn//6aSVtolCJSwIKHSRIpINSs3kLY2mzFN09QKD0fd+F071Xd7j1qoZciff7493/WV5t1bazuuYUXjdotx2ztWU6/FtKHNSiyPT23uJSHKR6+/rTIAEAMIvxYYYWoL/uMMWGUjRmAE/qNiAAgMBO8GEBgIPg3+Ng3n/O3H/8zL2HjjeONNasUVIhIJWLVVBREqUxIRmzWStsIZryFwHcP7FjQ6Iu3bTtdY6eC+HkchRm+JgBJLL9isgbc8x3pTZtKE88hrNT5uHl+1g0oUVtbssA8PPLBYTnmWHRU7hM2Iku7zVbi4ebvH4s57VigHFq7t7+OiI6WtgEIFouXccoCyUwoaWuSWZowFWtIA4iCzGvnWb99jcB/fr6++f571Tx/x7sXzRClE7QYzs+ja9kgC6T7MZdRspWYUKdq5X59PJ752J0mSeEuSZL/8UJZlwsJIFAQABAkWUKNVSSsVuwICjswooxTFxqNUVjHr1Lr3FVNHu7NUlEOiUjppDRsQYUqaK2QaIkyjxJp13S7KWbdVOWI3A55NwsEetd1FUgkQIFBAynwoqHErBt3FXJrcgRIKkrNw6XlSRx1+vHDPZ3/6O7/z1D0HnxJztYNmRMJ5YYQShYvOobO4I+UitxoU5brHL3Oj/NodEMTLl7OXyxiiGYQqx0BfP+cfrzU9JycOdUpQKuKGIiKWcHUk1khD5BRiSUDxhRL/kxQktM7Xih0ipSKsQIIACIIAAoIkrqKUpnIiFaeEAHF5bRGUEoeiragEvNLShVBBZ3DUKmOSAyWOx7bPap7T4Wahut7o9thu2M7GsMvs8Sr3peKM5IDSFrFhiSLSA3DgpOqfNfayG/LW9ikqcn6XLu+RibeydOPaCjscFbaZU/Nfvu/KHdOjicook5w4MnIOndJrIUMHpMFNrVaaBvy6tZm1o1wA4GKqblBS68QUtqRY4hyfnde52XKWy6EnqQAgkkWIRGmrJaY3QW6qAmWgsBMKnV9kkPlmNktmsg93eKuw+7VGlBBEEQAQhiBasSIiFlVEapFScWsJWKgKKCKVGLShVlvj7kT9usFGub4xpElbcxbz0kiHYjUG7HyjLgZ13qeTovY+qxdmMx5rpS15n8rn4/HRZ/Wpvzr4v9fVr1aMjmRJpuOswt+H3se6aPWQbmVc0KZ4Sv9wQ2TqxT3deOFSJDkZbpw+9Lnn9327tY+EbzGoFClqyUSUovMjK42y0BSlA9FqU85anouPAsLCoCOTwWyZ2o6ztvaErpOH77zX4NSNAwQUMlWLrjJkoBPQXoDqXAllIMAVqHzBQUBPMNdFAwoAAAASDoLeiZbs0Xe2XJy5iloSha8BZMCEZzs24lAuIoqgaEbIVsNqwQSlQk9TGjPWlssNBGLtIa6WooUF7uY7L8jGJzRPmZ9Vq+imV2wM9NN/OszufKK8x6V15muzba3dNr/Z1h/zhSM3D6z+CPj54D5OnPdPPvR2bu7lP2W0NaimkDYSbw+pjnCXN9ZU3bZrxaln+HcsQ+ePbNW6spi+qC43zlw8lmjmyPm//rmrz/5B1Z/MRD9lhxL1yIHRnX9jR3HMXsRd5aqkLYWCsfPjjY2LBGOx7rJNPmEO88xzbMh4P3sZxAABYQCITBHogmUUsWcPFwwMVp3V9bEwg1IE6nyJQOdVDjzKmCqxEAIAhBCExnn0mkPn6n2Nbqln1m6P/CTZ+7SZr3oQ+kCzBw2llmijuDxKWdL6MCF39Z3pMDY2jmpAxK1tYkTEVtKMZgqcQJb48nCUJ604/eb147SaMdJcyvkZL840HXsdt2/ttZvOpRk+3WoDast98o4n6zYvo2a5dH3n3f3iwYsPg9uktGhwsf7t5y8tf8Xvdv9sBFoeW2Rnxuaf2lhvvaEyzLbFFsSod97O+kcGOaLEm6fHZ7mfrkIaXQdt7sj53zzxB/mTfzLkn1cYFuNyZAflInuBQkhJNKSiJdLicmcTs4eRA+6dzsc+oZt3j2pzbikTXccC4Now8O+qgBVFluWxvMwIsAmqokJhg05BdRXfsqL6RH3scxmlA94YBYCHLgXw0E4RhoywywURhADYArsiQgLAmBsAEDEEAKzDCCAhDDZtAQUYElhaBw4ZQrDJDpnkWGAEkIiAxI1YoKhQ4EAw2gIciEUjBZF1AuvAgUNBQRgZhOCs7ZA1jK9TZbkREKEAgC1wUSSiTW4+n0251ZX2grHgFQhQGaif58/e+9Ge/pTVeBOQQuOBVk8REUGiIhIGxR3yePaV8czFYRDMc57JPXlyi3L65muXf0j7tWv3px977bXKAERT7Tta18bs2biuPryHE03KOXw9f+HwuTNfM3j9nbQ5r9y8o+Tx5lPVvu1urqF0ykI2Vf/EOilJGJoA4YiS5ubCfR+++86lNVfW5eGuPlibQ3VOO5yduO/sm1/9xfTDW5fS2bGMGmR83c6zr6tboEBFKV05KTbz8HyN51zcj/qe3Ui1W4198qT3yH1P3MVinRAAsG1WgDEDqKo0SYosZshY4YyRgiSDlcUKKcEPMpKJG8+mr8Y4EAJir6HgGAJOB5qvZ+JlPrnAiVx8w9zDdLZN3tI5hnOIzgsCAMF9OEu0X1bPJEeOWHljLUqL2+R/lhcACO6J02hBz4neUPQE74QCnOm8qRgRHIccjeFlRYc6Q3oJDvqncELYNNnpd/IyfM3gat0IoEQk2iV5XQBAJDLvCIHT7J3mHzR8Y2H+/dSw2XsgwcFkRnJd5xBqROeqzom4Zwi/KwEAAGDKy+i1be/xpJi8O/VTAPDPxx0CsTpvRVV3rrbY+EnTj9OgALTByiWIzPrz+rsKi9tpNF491r0dp6mHz7RRlcSEAKlAaoRF9ppz/vF1HT1tm7Kb24GfU0nuF33fuV36t747u9aY8lY71Oxc9DibOjenszfbRa+LbKZxCnddf+7+R00aheraHqoex+PrL8TWWr8cb6ru5eNQuG6FzsRIAiAyVFW6S3N3f/B9z3XYm6Hd7aj0BqlpsGXo4fLNb/7/45efDz94KPp2Tc1Nhx/3/uT5cW/5dAScgnQrXHYbQs1fn6y9NJqcHWxa7jtt2kzNLQXR4wxYWAzBNQBgWyEijuq2IUOKlACgUCMzOgPfVBPpfMGhQLxtfLnIIdckMqf6t1wswJp49hXVoSqdaD1NSWfoLq5+hx2POkhbtVye5I5HqxtDPNY79x33fWxukGRMmz9Te49G/6Q49v63e+LjKVu14Wxy7SZy5OBqRqdGKSfNKJs1rn0i7TVP3FumUMnZ/oxJxfK6/ZuIwvgp5q0o2K3c6zuirn3TdZ3BzbqBRvhqbXhftkRykIg5cvqSlPQz93ttj3dusBv1wEzbblt7+JRsmo6xRQavu7rB7CEPPkH9Bid+tnb96QAYCcgEiXbN19x8V3OYf+k+9oK3a3d1ODdj6eUqnMntD41SFkDG47n7g+2epgGLubJp/VP+sfcPvsp7NPK5RNw98bpztwX/6GujtYioIgrWLtIwyuo2b6/jjVjjxhWu+e3QE8SxPNhGrq3dy3tuxUHsPqKSEEVngTPH6SFTa7KJRa1b3SbPjE8/9BXrN98nVrcf7bQ9Obg4s5KSHRJv43hVN67PhMlMIAAAqYuuhrcRL6Q76ZI4NU5GqlC67UWzm//79uZP/jH9F/rzqz+wZtNs7vd5v537/fgdFi+rpgCO+8OfF4X3Xudv7gz7Pt/EVdopLw1wnFVD2SNDAAB2AYAFA0CUkO9SisDULI0GCn7UPs9NLb4hOOsfMzgda4qK8AU/cJEyZZ1nD6KnIllouJkG39TaV17d43B3M60aqxmAtXE79+wAwGvM575KcKayh3nfsaqoAQCAmDxdcuTLlUvupQEenPObv78+nWGh4T8n/tbvra8wWUTOkwv3IcnzykO/t8LYsZx9jy93fHPpzSRTBQKETGd+XlhkwYIFixnL311p9efcXlU/PVI8lyQA8L5zEISvzs01e/HGxAcOsUUt7qmvsnWnAOQA4AAArzGjF8k92N77cI15AQCAGB9ta3ZzfXuATMYMPvzJ7X528t3iAOAJsKiJVut0d3PPPB/MLB3oqZ5QxD2M66LMwKlWAjoBg0UDREREjLoigmIVUw+qeYaRb2LgqOub3WauE4p7ndJO2NazOK8+bnz9loCQgqICggpJ3SqXLjPz0QySa+vUJ23srfXAi++tLZ8xozNefesL4ycb5qOosDAEYBhaAQIAAGkVusMHDm7feV1b9jbX0LIOloLggHKzth8f20pxhPCSCRlLhgom9ddXX6Hm+76/H4aF1znXeR833zv2w73b672hJ2kDpI3lyY+kGAEQMQCGgYiIVLEJCwFgQIjF8GqDYjPCDwAE99iiqql+1zv/jRtogOMh439A6f3VvqZFAyVTbZz6BKN0J1/j4nGhOdjgF7MbdX+taocq/0A1fpSP/MmqqBlxztMo7gqV9wpl/yNcuW5L5KjKwF/+7O8ft8mCxbMlv/Lp339Jk8WScexbu+/6zB2gFzMPJN5ynQEo//OqgWrCCKCB4RFjhcWFMP976msKCxZHxSe/WloAfJzQeKrdtg0c9D5M7TlLe7UbAQisCthAvRt3UfNtOMiSnI3oYASXZ2VS3XBPxrwAlzSX3B1miWoo995cn8JlUaEi+MGDl1+sXXlr8wSgAm2MLdZp8uHNpW29BpurrWsuvTYwrHUJMUkqapVoxYJIEQqiIQTJiAbFlCV+PSz4k8HDYBZKaAdeEFzAd6pfFpkr3vOvni3//EvcWTSXDABFGYXjtFRuXF069UAtBjyNyZTuoetbK5w53GY4TCwevf/td3PtrlmXH+YrBKCBEQAAAIQA6RcqMt0tNWvZ3LqnuxySmjXSNFTK6uBqjSaTUCNJAE8iTDtswO7O/tr8vBjdsXXbm3vt3vNV876aDkEDoyELBBDcBLCECjAABtGyZggaARleMwAYtrFWdX4AAJSMNtn4Jx3a2wMWled+bP5dZTsJgKQCMqCCqT764dzwP1z4Cx7zGOjy7If+zptc84Lf+hW4lFfb95E2RAecY37id4ucXR/TYoCvMT/79aoRQJf5B7+6NhQWLMZjfue3l2ULixU3HtWUAyhhz+G0ZvQ42X9Z5ZrOWyUlXGGGB3X17mmBxefFL33uD/zW761PZg6TRwreDDiAKvPBb5FuW344LQWwIQgkAGh4rPNffpyNR+q6ZnviB4vC+try3o8dKgbgxZLJr6T7XTVGAS5p/tMPFxtq17kriwXq8czDz93/3odeAGLV1/7TXPm/r/Y53gE4aZX9do/uKdZ+qMnaCCeRrktYrMPd6NH4jEZkAMkQTa0WACR+M+gMR65a/GBAAaT5f6/7H+XD8PR6lpcBwqGvzmiW+dQV8BcBB07Dxv2LuR8eiY0OimJxQUQ5Khdk9o4GSDDTolivKzdSdG698nZj5dH45P6P9P/7HWteTC0z6a9xPGYbWUskAACHghK1tWDWzKlcfriTV05DhljvsZmalJvrjXOK9QklySKEAABLhpJpE1O3M+102Aar7ri+rsOsue3NvRTCMmqDIPiMMAAGGCAYi8JYMcBAgcULC2ABGoFW/gXA7HLXvStESp6eSLWELAFv6BmoaHX4rdHV9lmYa/Vmy8tmCWDFUBnrIJyrM3PHyRyrmavWDUC3aVJbREBB/t8CFkvQFg3Lv+9UrLCY6aqwNcYnFYMnX4BW1lH1/t3iu8NNAeHIRJR89gwrCgsrFiynLA92/ubv7/74J90/FpYAY3gn8Eep/7hWNAGBDCbDSkCIly8j11u6rWosvtv6G3XL2TtIwBk8/JsG76jSKjkaoEB963unkiRZAEqB/C2UABDs/RmGX+FGAAAg3qmRma+nWT9JLd2YdhywpL0atOlBp44UnfYy3WrDYb17kmgaMpVyP+2DIHvN03V8PxJ2wazX89XtV69zaDRvv9zxseOApM1r9LDY673+rSs603gBCk6NmZFExQAnlPKyitaRlFblYvZtN4/Ltw5/dPAPbzvy6vC5W3e+O95uJxNBnuxhAMAhMxGhDW+2yKW+pqVnL6VhctZk2IyFuxMBpBLeI1uGDlqv7tibULEDIMk2UJ6BPoztfL9z83KfX7Zl9ZJy0VdywVQLACyIDwYUkIAAs1KEZZpVZQaKmSmwKQAMBKAB0PkBR9bUvs+7/3mHAByB6S9TfF+ZDjIh3wCAiVS/wCZBkO8XX6MAADsqCGDQpWDaXkgtALDyZpnrABS8HSMsnnHGLSxezrHQhvlblXskC0/2RQtgUKQOoLJjc6FKgQMAUOLYcf9luy6HJMCCBYtZ8U832+r3hAAQQpheDEQBIFSiAAAQeqMCEJBVa6vWfyDbtsSbcwlO/nYrvLfCLd0gWQF6aQAAgBGgQFeyBABy8wYAQAlZo8ayaAqAlM0hm47JDFrc68U+7LqaYDQJOdIwGputahnVUuBzj/JONgHZ3fhBepaWg0XR8KzS4RlueBWX2T9xg4OCTseaV0+7n/7yUflm90SvKE48tHvqQdPurLj7yIQrm44mYJzcOJfeXDd1/VOTfzc8uDl/+LJ/u0/eymowY1xZRNbdAoCCqdNbrVtedeLwXf3ISfFtGl4LV9aetCsOFnfpJfkqciPJQpVDdmfkFk0V4bBkYMfNTM94+cVWyTmH8YP1s1sSUE4bnTvKFCCWNQCMABjCL4UBy2pQadZQzYCATUB4383lOOWHSLYuec1fp9DucYMptud+g+DhiqYFEAHOQr4RRZGAAqAICgDC7PTCIavH2qlfJvveEo0ZL0DqyJ6l3epAgYoIwz9v13PAoqmwmLQ0n2r5R8LbXu0BDKKVgGKTzltKCQDApShV/s2l9sff6v+27WMllwyjsDiuPPjVIgBYkWySOQnv4ktAIpJBIwQA2IED0/bKzF0nA9mRz7613L20mSKcKGuIUp1lPn/d8qraTYv/PWu6M3cbKwAsvTEtAEltk1cV7RTSB1L1QQ7dSU7RBTdd6+qRkhBV0zYvihQY2wAYgmZzrrGDkJ3jdiyJc1sPomiYKw/MAffB+Mbf+6arJVQUceKs5QpEsrU2nr7hc+LaGqoefO8y9env/vorJ8uL3X3153c+v2KjmxoY1rzYZIrM2dh06fGVt6s20ESWO+pVSRoDQMhI29BNvfkyd8/+4BW6l++UD71//uk/YOOd/6O8oRk+FwfnyaSv7M6Jr777D7/67IFXl+pCDyDYYbCZY675+MEQSlO0ALZKqZUeAlsKAdZalsIbBCCOGGrGmIDBQGKrdbgDwAKAmQRGL2CMF98Qtsfb8GatEBGcvjR6P9CcqKUAwli9AUrgWbLoCSgAABaqrvnrhgC4pjG4WK3Huf0xsxRgpo93tOpvsgrDKhYryh99o//P1FSwYPGKpullx7vI5e0WgS8BGvTdoYEAAECa7Rdq5zYpqWn+864/+9gf/O3fWdcMFlcUACEgT214JxO/554/OisUoArxqEECAAAAxeo8m/f8xQnJePiAbZus/6A2mz1ai69bNQBDVvklJr6MrLnh8y/iUsd/fK46CQAOtFfq5xQLFIkELSSJ4YU1GtkxGSCoF29eXNVjqY4UeGTaIgbRSjDNBtnmHisQpETlqvWVJJPrpoRSXkWUnXy4FyiLo3iarrFms7vfL75Fmm5Kh+bK8smRh27+OH9pIO/C+dmf862PRB6+b10W9RkLx6iPrgr18JxXPbo2NVtGkoEfCAEADb52F2Rr427n0q6wfvDs0mnp2khp/P8uvvKtlSWML8tbfepGqjceznzjy07ZvufcV//8yYdHbuKW8oRnqQu+2W98M+yDekMAVMROsSmFMIAXWQDC60AqpQYIABi8B9LaBfQIADBLpKZJ50tG6o97159vEADXvPutPUk4AEhy758ldYQKAAQoAwBhQQF0JRCggtVnOKkABml1iKBPDTBvOf1iZe6q+o9ZkAAWJy2//2vLn7/cFxUWDA+2OnfBvc6Ale/0BQMAWBbNnVJRuABG5zArR33+YiKFRdVywjIZwoLFsyWyBwDwkbHKLKqkTPHERH86AACSABFtX+Hav4KiASDedjXXnh+R4eJZy4N/UEdaWBa8WVgxXShR1u154HbmuxdNCfDNVx3Xk143/UmxABBYMLRNqghlNRixzW3nBLbS1nPxVGOJtphiBNfECYNK1QhyNG8jdYMpUGLJhKnYOFZVBHgyKhazVebe792UH4aykhbHbCsGMgVRZeV/96lHwal9QP3u4O5kzg9S7y/5nfY/ZN/1tnzfB9/0zi/duXz7ol89wyisHpJA2E8toxKEAgHAkUneOakMRv+A4up19951fhtO0XmNVbwcZ9Fn3jw5/ep02/++7rE3vTueoq0b649O3PI7yKM3xzw117ffm9/NZ06re8XmBxmCQEs0IC0CyAEUIJsEhJtwhGExtLwYKgz8ArgaMAIzBYCbVlXdSgSUizP/fp73h/a+bnOrSQICACRrbnMx2tUE3WUtDXfmV0F/oWus6sI2eW4//Nuep55OfumxT/b+//02ehJY1fRdbz5x8Sd0FuVWdKZsaq7e9Y3/Se7DXa6+TvICh/5E7Vevwr1v465iQUbkaS5qAwCusk2/l1YANK3q9JVYf5zbXt9VdjoAEKecOHN4iZldiTUANZsNm+tzZ9FWvva73936tNEH6gTdVRRj6/946G/YJ9IPKeTkcKgzcTzy68p72tbzddCqKCUFaCkvwoU3JJlZqQ+s2UWtZq5z+ncxAIAiM4dwO0VhzXMtGFXHxkl1UBxdgXGvj+q1OIjoB1Sdq9GSacyx5W76SL2HHQNlgNqgI6ppmc5a93F/OaGhpCDT5Hnbs9vNuQ49qzNrr3zhl3zin//0v3ztP/+5soqAe5M/sLN9Q38tLbPUz/m2z2q3EXtkKNnQH+tAt6bqyIGEKmmO/prZdRQlvYRKdYuKx/LpmT3SGjutsQeYYolOmtVqc7qK4rq0MXtXRnm4Ve97+ZOaar4fKqebY/oHu36rgXH11Ktbmi6FdQYBkIkQJw8CoOB7XNEATJgVbPEwQKnN23cAsEkCAIxna7ciAghvoxujezKpnAAAFBufI977/aPYmo4e59u/yDv/zKNO09FcTLeP/JZ37/yD39y6MnoL6Zdf2XHL2CSlZfP/zqGfeY6d21StPpu/NNSJc5XgAiQgzxHQnAhgVJHcuNLe9gyKAnRve9ukAEiU8Vn0QhQAWOVe83tFE2RgYLUyIbq45NReIHc/rdeFA0iNex/3//PmBpZ23Pi0lReNf7rv/sLn///Zt3U1h81qL1buYwMnoEuquCeaKeuKrmNuef0nvE1tKuTBF9U3yJwuyPRAt3L4Tsrh9k8a/0J5AgCAE6jcAFlUUbjaNG6ULs1jLKWlXe8cKxc2ZybRLfSt5341HLJLazBMxGsISU1pPRs2nWleC+uog/ujnv3qZoSSImxSXHfddp092q1/UD9t/6U3vn6aH45Ly2jsCPqvL4+h7e33bJxfah/xPhioQVIkyq3spu1uS6RVDpowwYYZuW4VaRjBUjoZNxOnHBznWWdevgFQMmJoH4lNWappW+HizL9XuVZCp9ajNRslK3ozCWc9vLf14PJW1jvGZ6PNTsLSdQNwBn4aDGog9kEJAGsSs1kT2BZbojEDKL8qGxQwwBQABlpb6XwBkXfyDgkAAIvoluvg9HuoMpruVstSKoOw7sLEFBPM6hRSWQiIpb8z/yTfUut7r5aBXUgAwGQAshEOJLumRURFJcAW8svu/hAHbAUsxrn0A5pLNAAgnOJCmAzxtMweNNBdRSUBECwABN5J5q8UL3DWXHlRllYTspTKAJK3ehsZLAKAR0RFFAVnYPVHeecXazf9lTiPXRXS9KJAQS5GN/Rjg28qN9gAwInUukykGbuaxAHlEG6cjtGoJlUwqpNhFhNmJXUEdxmvoUVahZK2mNNFvtdPsjkEXMpOr67jOVJe5ToGiiTIGM6N2XLsllyV+vrQBw4zXr/jx8Hlk/UPes8XK0y1urhr73b1wmm7y1JLkIDDBdfSA8NzU1/zoYEehx7GoXMZBECS0w3lSEDCsgoVJGUBlnTi0aZKK4ZXzuSR1QRM2qwaOabf2cXCpalaa7dRufb7y++Or3V5IDt5rgKATNIGBgAwujAAxDRIp7J6bI2FgCX8pXVsLY0yjwVgYrASNecHEArY1g3aG+DkVGBQTkA0g2DzBFq1B7AAQGgiGNgFvJ4EgF0AAJIkHEaZqD3hXZ+pff0JAHCi3+ioSrBIOAEgyCSAww5LEcQCBwEKLXjLACwkBFUgKCcAkhIsRYElQEQ7r7DvUe+gAZbgv5/CO1acBUAKk/DmBgBAoJB42biRF1G6SKpAxnjmeBxzj0PViMLVYJJTMXUlWHz0pBZVMw+KwpEd4cNYjoURoalhYt2NmaCAAAvIQdE0u0xag7FtcBgx/Xx496N840fX284mHibqmtpdVu68e6Spkd6+niJbS2HNCly3n5tuCaZqTEtL82KySQgLSOGtNFtoPLy7zmSJ9YIEAFDQlnhy13Vmt/OusrahFCvCNxBQaYvuG0m/wbET0bcLnP0w75s+5d5c1ha2Z8oW4+X35Vqna90EAPQrNFoC4wEwEShj2ufya+duAODJAgBwAgCgLPitM8pEQ2kpYZgn2S48QeY01pIdkimPMmuZj3PFpnCsAwcAAE6we5LJvjvuZ9CY7h2/pKhFAfAWVSxbNlWcRaHChE14k9TIRQDbQVFhhogll2EEkzSgN8Ub3dF8nEJBOR3mHI5ndsulZ0DREXZr6a4OEgNlwyIswnqwC46uH5+699XCxharXbK546Me9Hf9g6vmYpc7oDTnpnz0lrelsdqr0GWCCkUD5o2D3UyHw1RdY2ykMWmEXHjckIoq7KQO4VKBYocE0/j01ved1fu9y6gxZEl9L5ha3XqzfQEgPeEPp5M2J+xUuvzUTWecImeya4xZBgBWbEi/CgAGACVACQDbxwBQTBTDmBggAmu0m8T/a5vJXODkW0qZHmD2CE5rM7Brd4Xnnyv9BuqOuEeBA/iikwzfMtnD3Sj/pHAAb5FicDa6dg9GJpG1uIH+w9eWWBhEKo0zqYpV3MNxqFsJbGt4tvUEblkNJjOQeJQx7OJuVRuyCcZOPX/cdigBMbAAQPOc1NB55tT1wX/0G/7zjovHtf64P/DP3ZXwM3d8KjMhNOc28O5a9q62MLTCYqTB6bicq7tbXGe72e8NmhwTdqk37YvwxiarBCkubxvPrGktxc7SWkiCgpOSfDp0De/edqZUc0xDoRDZLrJdWprucCqCMX6K11Q23rqxMvHkRzdfu8E6p5YMXSyWgRgDkIDxC2AAEIAB2ILB9MFgQSIQmA8wl/Duif/ncFSCpbsKSVuA2B0c73By7wsy1gF8CUWQgpy1RcBbJrAw+fEpHC7qLdx7622ffRfCGK3YGoCmrpFssErN1BrQWTNalYiRiiAVPcYyZmk6qeKgw2qwMLYAsFkAoMpjKc3L/7zn5ice+4rRL3/rI/7Wz/VvzKyw3Fy8wkm/Tz/STGXX6b2LoYHq7UMyWPrzXPGivF6vWvdMgmstBt+p7feJGytyh5uTW++k8s7zeO+AQRNFWxdMQgYZ2+r2uufErT+OSbF5CbpjUi/GmvUioSplmCKWIii4lnLo3fHm6tlcT86EMwABDTYMAKBfSU0JEXEA1DQehL2YMBqBmRLYHoArbmvv/l5f/78AjBBcBHxROQv4MoeksQAyndP4S7OECDSAcqosqOd1FQKrQJ4KrsvSzKYwxapFRQt6yBJ4rbaOIQVVVhskzstIh4EFAMAQ7T7XPNhv/Fs3n/zAvrJ/t+nM9bV8gBuXZrrl8gjPtGZIsbMPu/OY14mM5ZWctZtqmIWDdSo//8ZnrvsfP483zzrb+8d+/Pzl27ZTCbcI11xw5ANn8Ty2aXKOyIUgB0yx3HDxu1Y2oOZIXRHYYal+QujYqUglJEzsApUiC6526/Ptt6jCmdcqS1koK1bH6Jr3NTcBiByn0+mqacL0sNlsLhbtQDD6Wng/DMSoNLPI/7GvmmxsnHyHO3vbntaid9EhsOd6YYCgBtE1JKfEtakZ0KpuNIKZRzHjjqN1gjWzKBiaCMAYeD00hcs2n6V/3Wd/dEmfKHeveupLPx7aXQD5wf7We9EboLB8kyNXW/nGy0vauuP68z6m3WcPv5LV409fPp2946TBvHx52XXmybbjPQpjIjSt4VIyC9JsxZCJM1JZM/n4ccEvaP/DN1onMhElMZxpWhQnCNdUsP270/vHpX794NX6BttTv4p6AwWHVbIAAAgWZ19Qz1lICT7n4bdkGFoRL4ER4N4YFNv/VyIqK0QQzpcHCREgAXhDilSi2ERBBWCb5Yp1rRLTY8pqEqDM25WKlbihF1hp5gYLgIxQfDSUxiKAiQgACKEihKPElZxPbeTJv/7OyEuXXVvPvTkOI0qDR4Xjp3d0l97xvjab9SuHC/395TgO+PqtTLf4PyO2rZxMzy8e8t2xy/RXh80XLR09X2rLVJsjnRDXejZ0QIMyTJxE2K2bD855TTxAlGBy8kqQCYnOKyuQZbNXXwyoQzO+N63BwTmrMQUHElx0LVhkxMYXQGAxPn7PqlSA5QrcFCHcyP9TEK0nrT5h5xJkwIH40sEhYXo7V7BFEm9AovqhNHAEgsPizMK1CCpl6WkswECV1krq5RUW/B5pR0FSZt2go8/UGQCgG6ACAJKQBJCCxcTxsqiP3yp0rye6drukTUVDLeVUIzvI8e8WbpfMiwkvt/h6J7kB8s6TZVXYmp0szHc9tvTFQ/ewoqpWl22klCxKeDGedwlAMiSKDJGM7l5WX9689yIXWEJilmzWjH2hZuKa4JTqVJer988W1e9kfXBSAJCAnIFtf5WAwD0EWLHfGCCw4Ddms2LgfzUERShK4ssEwvYc/Lzv/mLb+x7TqRRg/NKRoRdmltlxIc4A00liAVRpu0wtRaJ0K4VzR2uLOBu1IwKEdV+VxynoTA03uMUjXuO807jbzVJywMAAKLhncFBgYEXgasnnlmZXfrHujUnphVLSgUm9kgccs5Pd/gvb5R+UWbr5AdpvaBtkuKWd9b7RvKmv/7c1uemB8YvUdi+sPtp0lvy4ZcKwJU4gQ5TvMupATVjEXi3dkz36xjz4t76jJA0X0LWYEgOoZNy4NOk9aWG5P165vX9gVs92WS5AQWkE88Sh2OjBWZjFoGAvwACwLGMX/p7hL+kVw/lfBcFuctP4pqYT4ssCAoKzu7Tfnffbwi55UQoCvuQQbJJ4j9c795Z7knoigkusel4uYKCZgANwjiUzKUIMV9JQPUMPNexcl220Ah9sMF8PhyGzSsqSDF0d0RhAgQsEk10ZuFo4ufLFgHPqSw82r2uNSau/9FDdfqzUqbuI8r6Wj791MG/r43jltdXVL5JF6tM7EzvHXt1MOu3S8rMbd4QfppAqGlhUaX6PHwISTTsm1sRM9+Q6+NrE3LhdLAhwx3KlALUEBvaHtXmNDnboV9lfmCUePbP7VPNRy46qr7wr5ayTm8GRTQBgBOmjhrvYlr9Rg5aP8cIi3Lih/yhCQQlByAgACEMIgCZCWHkCAAhhEAAAFtkBwKGoFIQQMihAZ7sP5WPv4Rvf57Z7ku4pIgAIYRAAAJbGLoBAGACDKABEBGAzKMCQBptcoCCBdShgxFKGBgVwAAQpAWhCFQAhyADYAoCScDgDoFWJGEDEQmALFIQgYNcWABDCIMcCFyFICCEDAEq4HoDrwAMAAGdIYMoUJRm3EKsS0Tv3JYxROuUYt8famQqpRml0DF2ekNSP485ANGsqGBmoAsD2cQC2ySBzLffbvftLcf6O5o7Dcx2gvq/e3D/63V7fZUHXvLfsPfM+/sKPudQCkldWvB9u+NwSj9z3mUp6QZOq7TCz8kbfXZgWtoUhW5EDIVTRIZ4KNLW2mylDCRuHHErOQJOU1ISbAC0gsF+cRCi5pZvM8NavN6/ZuusneV6W/TQfM76pPfPdzT2sI8O+nOgCQB/vA//5r3/2q//41Z/3jb9z/h1CsfXu9J+BeLssqiFw2QxfqmhbGtu/q3482PKi8U/jHaUF0H5V0woAeGfwRtgMiWTP8PWyQTZbrzdEwldKtw6o9VKeWLtVbJJBovP2NDMAAO/OxRtgKZONXgQYPBApWHaekc3MO0OGzYTPFohzlvR12fTOQjG8bf7fzv7/tr6IAgCATUIAIRYIo7NtekWbDO6OiIQvFsA/HwKmj5393kx+HFSt//8L4F1I8rxssuHcSXAY67ATvlQ24d2B2wROWozetPFEca/teUB5bG375CJyGeTAIpXBBgCERlG1JQKYaaiAsLCJZ1IpHkypBYp42o1zXgUglUlJhg6KgrEBQHbwyQaXJtM8U+afHP/NBT1KymbCgSMiV/vWyUtvFzh9Zddzmxk9ffut+9+SxB8YefUzhVfmxZV19r5jY/ns5gvvbak/NF2bPXi886MliOfDtuq+e5DLauFkWcqhQMiZxHLLuWzrDCmIVFKIFTBZAST2JSYVKJhM06K1IttsvIrK5J5QfOz/vNmYaS+P7JLAvdJMMHLxsgwYYwQWIQMZvyICMOgv9nzbQ4J/lzD95907e+HbDW+N1Lh3zNWuRKNy99/MdrSn5v5rd3dVrun+/H/M4KtEfZbt2XsuQzsoaDRcWGbu1cqeSjJzbJBdsnAyWObQLn1Hw2P3HMIIwJDVHX9oOBV6YbLnTl4M3Xzl9LM52l88+Xhma+eu2tVs2w+0cDrRmOIk91kIjzrJ3NxKdtdALEKv4bhXLaqs8XjkDzzDPuDVo4kAvJ4NeYr2TbdupG+uKkyMU6dueyDIjI/JE+2es095fx/8PnTw+X3aJ0fA2VnWjxzGWJ7v5/jTzT8e17Lzmk525uicokiuIyM3ueXR5Mbh4qZxynLbyiSTzSVOczOVFUEPWgVduFEkl/wtIVLJU/1b+teSv1X+HrHoOKaVskc1YwKojDACWRogxgDCoaHowEq4fWElB7p/luabzCDWm6FBtOYnR69iN9d+UK06ju3H7274mVfNC1cz4cN0cOroScN6QdemQtkcWPtosjyamb7WravARmIz1GDFKwhwVJnFOai+pzYmSqFuMydyrCaVJApNKmorBICKC43iY4juFtM2oQimpZl+saJQ/JN/8sv/8l+/c41m5V4Mz5PC6woEREQrACKIGJbGLzAAwZDfWWFFakljYLL5OjKSm97zCNvUAAAA4KTx+Ddn6Vy7Fl2rECGxGelu3CHdPDz6KwnuLRX9/F92jgEAABDwCr36bzRvuGXgKL2jaZ2capa5Y5ndlECWm6g7YrmVOMiH7ne9NQAAYOBF357/zRr9RPYh4MnCK78/d3yyH7ACfLq1+RpDq1yntl8N5m7ve2n7mzJ7xtdqdN3rteylZxLpq1JwSbDxaC772XtXnetglMzf6v2rOWA5kFIZp/+i+l33fK57zG1iFeMHPeRyA4QiQAAAzjPuy7+7XPSbHo8emn62nvP/MfH1Pf96H5Hgw9r69jyQw+ecmu2/mOEr+9+yzmefDC6FoUA7CGQNl7sgGrQRXnd6qftRT/3Y4uLVai9+8umWAAMAcMYZALJQEY0Sh/HVldOgvVdtD9GCfKlGV00qA8FgtTfuxMmT4kBKY+WWoG7+eHZfeK945DJO82J+kB6cDYdXOYbTYn2/qH1tjLI5ON+svLTDm8Nds0fX9JPHjf/2zTf+5jd0DhMCAkiVB3lRmKESacKqmCqojevMdaqq9u7uyRWDNWkR4MX58bA/ZHS/kD9KHJkV3kmxHrhuQKOwdLH0CCvAZAkMoGAThsD0BQKkwu8dR6GHvoBDDgAAEJHOVbc/nG1qgFfDcXzXgyuMeu32+nTL5KukEuDK48xG716rgtdu+tp7c+r/+YHPMcdovOse69lMtRE4+zcy/s1mEJChGOpKQ/PMhNPASDAhnoPqW7ntHa6n4IxrzDs7U+suZWHzp3Lld2oZKqo+I1xeNtQCABvqdFZ6bxSwZpz4slMhgC5ZPp902+EgoKmcv4b/cLiHWOjixC89z7i5Odgw79va1Z4FAIeFkQwe6IEuKG9d1vEi+Qph3CMC7EDhwfTn9AHdpBssfYJ+pOLUBXRoAAAwxPp09yUo3MrdyFth5taGAayeZuFiF78aeNZ38SHAmPPjvm/OuLwUAFiwiH5I87gO/z58zuW1JA5jdqbxsDRvjfFgen+gtdaCdoltRI6IutHFvQtwc+izH+67+8oc5zQ7Ob0ItzN/eRRk5Xh6N3rI3eSD5p/v+kez9iN3/jd3/tfbwMbzX9MtQgqAihVrK/bierZXJGDmeCmKBPVMzenc1+fc76HsYDEsaiJDZuv8GPVbLBL2/UW/lPEwwvVENrv0QQ49ODgGHSApAwkQAywkTOOLgXDLL4xpTOqXaL6YTpgAAACGuUYpAdBkcurZZ3plNJ8HX4a9YlAAwHjw7B/0MvDHuPUtHXfwpVk9RGW/AzyUr/9TsSz9fXMwzU03GiMIIBFPzI/jP23+4TR+5NHtggOYKjz5/codrTEKcFXz/l+XzaFHZyR8uMioH6lVCShZBftjgAAA62R2Z5ZMwKqbDOpqF0DWq3+N4Cy9FGBeqf+41ABGACBgqBd8tbFC49Fpq18zc5cMkIQEwCZAIggEOApPfHVPzts/cQBk5Geytz0aJZDcQIBEgAAFLGWimdtGL0snYK2drUpBQYGMk8bFs02d9QlnwdwpYyfvjwqDFKDsQlrKZeN4mj63+lN6+i1REXHr0nJ1aXqObjZ3qQcnOrXRFZFriSvdkdxlZvKmWJ/3fPAH+u6aa4vdsR8ydfUMNNB79aoxd5rXuAbs8Wi+UvP8zbuzH33TMhkAAMoIP8TzcFf+mno2Iy6WZkCskG53z1qd5zxUx0SORaWGCFkXbkZjw+Jby/Oh1BAXCF+Qhz3lSaIABgqgSwswIzCQArDBZwGAgd+T6/dtAp4HNQQlAACAC94DXJkSCw9Tschcds9MauKHyZ8gty5LgMFiiv+OOv1U5acjS2UwOF0AgL1T6wvlvz29f88oAlSI6mAJ6JBLz5Y6hM16D5AZCgC4oTK7o7yqj4DZfqqO8key8qSrTEAR/WlmM4C8WP/e3kOrCXYrOPwhCxRgriezl6tbNhXAQOXAuZlDwKUu8jDIACgAAeea4/uCE6XGv9lzxzW3IQC8RQGwsrAe5xDT82ZAynIkb1OD7RFsS8ycdNzcNXKVXK+2GDfXtsmsquiIT6hqDNhlG57Q3ntn7LybDQAoAGwWRsQ54cf2iC595PZ7NxXKNF4KyDSoQ8why+Omn1Z5RQUDnuHkMlZ2TNxvK5PT6x+68TzPP/fommqmpBEwIGNx8iomyptxrtkX79mT+DCSCDLealvd6nrRYzQIVSUuWJC2tdde32ev93MKlz2J8podELJlTWUIavyGjAbn2dt0Iqab9bzl3dKb5EySJAAKdIUAYEa4x/jaApAq6yMuifPUcZ+rfckASwAAwEV3xMJz9dnFtmiz4m2IBgCcFY89KwAAEKC3odWCYa2kS6aMBQnAR7hVH/ClAAACsodNAKF3COOS4E5bBADg6KoUCgegBYaYXgwwAkBUZpS5qQYCaus6Sh5XDO5XbVsmixbnDgwuttr3MmMC+ry2VwIampM39O7UFgBLJQK2BrsfIp1Lg2IrAIAAdB1pAQACzJ5cYGElQCIACF0wKS3seEqIF9l0WNBrhlyvFnuoMqW9QWjUolvBoYDtcHOEqAAAMqAwkcjL4zr+8+GkdkLzNRSEQpEWiSRk7gXbqA6WQkE4iSNAUUaStCKxHiTWtra+dpOHz6jXDdYDcSoB7MApkJvOizbzQlaasMvIGTWo1ddNJuQ5mSQRR2jKHNXCes65e3fne3QAEbGoAwAiqupF3FpD51zLg5NcPu9N0XHGvbftPJtObRlgmRoBqKhWDXpjtMF3ARj+9rWwvappyuKXYgC83mbypzP/Vv3vT1h3Pp8rx82Jfm87qIc6Jl6WEKARVWGSYFnViYLJJnP8Fkwc5P8HMFC8DQAf0kZyACC2CAcOBICtANaRPVGPlgDf1D1k4ICMC0gtPLa66ZpZoUIATHVlsoAdsXm0mrJ6FdUoTtREK6CH2kIDzCqNx1VV4LxRF7/Ko4sy3nbn6DyHHEAuAKCpuGz9uMoCBUgk3ybdNUg4LiBytACkeIJTV7tgUpu0hmuzQlZJfQhEWtqwtVQsjQO1Tfo6QQnN2XLDKAUKQRKc1JTH1380/3mS7Mpn08VI/WBpSV+mkJZGoITscQo98YhkNL2DoR24DK5HqCIro1IeGZvvLWIqLJa2HJIIKd3RQAoAJ8pXAzITwAjHhHXpSrP5ZXs5GLR4UBRLJdu91zsWTJeDFo+2jFRGGTV4EVKMl6wiqlWXj309+Qz7D715+8kLnbp55DzYbOow4WYIKCGyBaEZfslYjQUYwLQrPl7rbFFSugHA60Wi9SPf8yey1duc5v/8ukt31zV3TyMkVUqYvRAAeqV5t/O/6g0XhQQsF/m7+B8tgJNJ4+9k+K+5/E9SNgCHK5uAN2SEJAfgmyJn6ToNBGy21vuBLH/f/V9M2Qow7+FdktfGMgICVQcXb2l6WzJLAZah8xIk/RNOXrEuJLom4NI86iTsAgAAlIHbcv7/X15XeQK2uzs/SfNaMwZLwLp6Tv5/+3+BwxMAqAjAsPAvhN3ddSAMzE8b0Qcc3vmMJ04sQAFgtyOj2C9WiX05EymyLQUn77qa9Wv1kWteGpZdLUq3lNEUJghDQpQSudRIqMys+eZHHr20ZvcLSxeoDiThZJtYL51NrBIwfXcUN9SG2DrLPR1IfSgrpOtoaUwjHRSYGFEo1/UpDQArDQAohTLAtZIQE/Yw6I7S4Pbcj7rwj9p5BWvLBTNHVXFfnnelLUI8DBqBiURRZBxFLGOd4wJMFiYdCfvPH/3qP/1Lv/WXv+dH/unn7RXPi4E8D1VOfwKAgjEAGQPY7q2q41KMsTYfDwITH0FQs7s0jkBCwAEAAHDESaZyhAmYZy4pA4akNE7NyjtakIA+6p0vDXkeSMCKqP4OWx7ySBuABgmpHzodomP58D+b3Q0AQAhgg0EOaC7UArC7+J1fXPIb9VoW0CXbpE76aBIbmkevEpwjfH3OZgGAZdF8I9y7JACAOVeY7MrK5jPMAABQ05y8Uv6x2MLrCCVIHXxnv/p2DYC8pUrlQqY3ewSAa903/UkHNJ6BCAACMOrVAS0KFGDSWHihxY3TE1xk7oxWBxoEAhAAtUxSr/JNvKJRwBUdWF/X6t6n94oAMgZCSFdlRDYNgEEYZcA7zuLSxFcff981L31d750l5RAM8AdFsQsBn8aLhO+IQtW65y03b1vHx9nuzI0wBmhBA0sLEiFTAZUFxyXJQBJS2ASCTKCIUklImXA4aaviW9c/++v/Pn75oX14Y3n3XshotsrZWVuIIFAUSqWq6r5kTwYGnSttbe6lumtr4totOlfXY//3G0/9z39zfv718p9+H+fUc5yll90ZgNX4GACMgWXCJ+G9DkAcAq9V1HOI9TZvClgUgc4rXvuRvM0rRwEAdc2X2zn3uKVzYQDM+qwryJFj30Ptq052/yFvDzxa+9hlvAAM82E8uXuobVEe6IHeUshq7+nc8Bba9T/aEQLu/+L1+OW6acX93rMUgGEx5smDufIG3mHTfUpH/fDKPuP1HLdHfgJF9r7LO/KHkbUHFp9YvV7OEDKTKcOntxoH9MSf9rLxn6YcAAAY9bZX/puOv31d/TPOR38a186LOWRd4XnbHvhy3fjJeTPNRcCamIBNKu3AYSs4CidEDxbQiFnnyUvdPY6ZMnj3uHtAHgERTCqbVCiBKw4HAIAD8QZUtIE7wB22S+pUF2zt3V5vLQgU8CYVSzfGZaMMIgCALoBiJ2u232Sgv/QujtlDTd7fcb7AaAiBSYJ+SqYiLSxcX9a2e/3N1F97RZudnHFbOgBSIMiQqFEFQhjQ2CwrBawgQvfoqjtv++v57wsHu7yms7KJdFya3+vWdV+8tu4W1ADRAQhZoKKZAQtBfK7WEOvGogWxyyANJYRQDU6IV86a6fnWnae/9aV/W+wfGm12asYZAFAYBIAIyAYPdJ0igPEC5gIQC1ItUM8rO6efzOjZkpbAoUTnFXNns+5ovIpw4fzVijcNzmIzLAGryt9+8vajP/3tV7/+fu3DvEqNvuln3c7TFB5m3SGdQOPAuRcUS7hjhz/Vtx575zx6eQgqNxjJjv2rlBe2IwsBiM4V8/fTfyhOpDmv2VeKBnhjbAEGO7mRymxM4SKbEvJL01DNSSMBCaf+/Nj0KKn7Ze7+ux9b742OFsDTHtveNTtMiDALC+sIQyj1qeHV6j6bvg10YfItReX/TTC9+kACloDJ4rFvLJ+cEfXOPd+ddWQFjHingrUMH9/ImN/qrRtVuScoqW62ZK8YAGyy+TqC0iiqtmum6rT5bu6cLS9vkckiGZhkydZ1a4qQbAFhCRoAEIQtVBaXvmt2MdrhpMDZbHyxf9357KhHvWXksIpEWlo6bfG+enJy+ts35P8O+Z2qV41CEqKmUDSBueU5r705QEISGCMAKW3W48/8Pv4+kgCz0tKDvnL7CdqqrFymJlAomGOvvfZKhQBFCaKQ0G3tGJ1MknUibgwJNoTjRySQN8fOLlT86sFnPtJ8bbJoibtZadIYkwbRICI0DPN2BAWTL8YIQAywABoAi5LhvKwlAICImN5kC7uHWMPbILgLswCCJUCJK/69mz9R0+AaXfA2/pmJqGmJt4oXqDXdNeBwNsbkC7lpKhcAAKBAMjfdVq7gDYAQpulMNrFz5CG91QA4CwGAMJ3sqgoAAKA7SMoaAOcES5ZH24H6Y+kJ1+Iq9sLyujM6KkGRoReyg4JqEJF0YfI2lMo/UVxceA1ZywBgAXBFuuPka51d/2RQ4CKAkrYjvi73eieQDelEdit3zus+vRWLgNjUL5t7fwAAsGqtO2omUaqy6jqNC0G1Spti2u6ySoMIEo0QFkVX4hwuCexinR7p3De020jRiTBqqELwFtUtVQUdoYRAaTMxws1Hl37zmZ01H0HwgiCNiCCMaPTauclHMIkAEQMgsqIICiYWQJIrmbpysnxjnw132nAMASQFAkRLQAUYUkVaOC9nDV0UvBBlaEM6bkHlLj2saapOXae4E907v8ivvTa+wXnHYLNrLGMawY00kdEoz6htQSjAprQFIgADAMWYgnA218akgd0GACEEDBSsY3sAEA4CJE6/PSsvIiwCIDcACQpCsMNFAIAqB4KyFgBkkETBAgAAQwgIdrkAeD0JCEY4AAgScBhFtPXUYf+n5iE+BBzR/X/ey+T/TlxsIwjKCQBkAOAwAkhQEGCLAHe1yCregaxcFygEuf46poezAAgAAIYQAC4wyor2Zh1am/0IAFzsFeuBAwAUKWOaB07QnYrLoVRaWbSwaDmzQVxBta0CatEsAEG4oJH6oZt7A9M3jk7r6rQ15iQ9zvFmIiGwg+8rk1/NnBFkbF9hddJo33/33k/uvMjw+/fFo+mSES8IghINIo2wokdxIwAmJAAAddwNEmuGqZnGIn1MXl2vfOV4+Xdxc4zKjhgAUCgiRjAVFUw5LQ+hbS5RQgfgeAXflWlQKd1riwSsckLj0mnyzg/rl8XVOwo5KAEA3AQQGANYxmEjMEAxwAGfpgxzYBU0zLZZ2CUEBOMUY87GUsnm2yQKdmnB714Y4fW55aHtVvs4CTUkXsoFv3Uukikq4s4r6EK1U90Z28lFwFsUBhXXjBZ0jLPOqSeW4F5sLwAQlCLmMNvonW3plnd1q6j2LKuLYgaxARIEgIERAL1lcyOaDSHNXaSLSud3ZkHaJUl1CCUMqyExVatEH+mFwdarbLrNx/yXr11f5//C/1vv3+wfj/3IIlMiqEokEuEZalQBxJyHRLOAwADjbl20sIQEO/64citlwq5yL9Pnb3pNTEiUTiCAJAogpLwvifMQODEA8rkhTo5Hpzvp2IwWsb2sCgZxmsiw0PSiPn/nJ962Vy8+b5LDaSFuxnITDxHPLEsDCYPflwEWwTC0gaOyGzhk6o6HvoO5oXMfLvhDhLQZ4dEL8kMU/A7ZlYPWuJUHvhxM4p7HO4YtAt6yt85TL6/STKaaTTL3hYsAAKBY8mk3PHL1oyPVhW1xrTiO2KRC3gjGIgYax6CMJzlYV5Pu/srGPOOu7OJ0V3i9P76lmqWYTqMO9iIJZNRYpeKwGVQtdvHaY8Yr4yfFKXv6H7+drzbt8ss3makWe7CPJlAkGlGYFhIIkYhFhrV1xwbupA7A+hajNKW6KB0L7SzGpo69zNukn+sKECAkUgBgUGq6osdAAFC5ZIgx7MHJ8gELfhSHev4w+eWhUiBhOOyEj//s25v6VVknO8YW6K4FxQ0CA/EAGUCD1yN2RRlRiwMDIjHllCvSLgAAiOA0MLhA/UEAIOGQoRX8TuFQquz9HcAFdgFvHULWMHprIdP2At5AI5/06781fszfCE79lf+Ogw98GQv+n3QzII8Z/RRP+H0/NjQxz+76zLZ3wbRbv/QH3fGkiylSmZQxEKBAVc/+f7/3FgQz052W92qgfGGffoJs90HVv+zrkt+QiYUKFDA1INJN0RidHgcSScKn5iaVrVQKjZSiXIr6sswkJQ1gUC4FTvn4wrtgEKnEVCLReggJOu5NgIUAQjCT2b3Lu9uxyy+3ntt339+chnRR8aJsj8VgmPzw4kfPffKVp+XxIsDYOlEgbgLANlpiQLCJF80AJzBxwBqxtUT9kFTlRJF2A7AZwFcsJBz4HcOxvYAvHAUCLgLenDF8g0AAgAAACPy/CTVCT/Xvmj2rz7urXvm71fp4Ib3N5c6fH9OikrJDd0QtYT/Ukirx9p3X//5IhKp773Z08mP2hx+dnT8kScHZ+AuZ8t1iLIoXTWXYLdpiEYBhGivQpPUwTXMeV6IchQ7kOt6ssCkIKNfJgtlzwdf8epfIPQKJAALJ1+s8kQ176p71LLW4RQFtvHjdC6/cbnzHMrLRjBMdaEvJgAhRQvni0A89/uxnt7vpEWFhLaAsmXIzZBvGCAy8H4YBwqAEWDAkxLuYd7eOgf8/ctZmAV9Csui2qLPJ9uTo2aePfM/06P/3lrcyixNZDkEujVZKGlUjWuykk1+5CYTqKu5t44/f/93+59f7r/Dkpnv/0ISnd2hUaWkkpRZgARIZtFjGSOi7voIJpndurdQOP3YiK3/f7Pgdt3U//++fbClkwWZmFbWnlsVasTAYOdXSe8Ms5O7kiuJMFEIAWZqJ1Z0/0jP6s/2sRM61TofhMNaxYLkn70epW6cbqqGRwzkkgPCAokQAAZQCABGyVcMdwEkwAAFgMcPxyH8nSkQowK7tAYgECVvkDMRXFKUllgKxKwhRKSsoCgfwVilAaJ0vhCWBjVwef/zond8TjfDK3tiVVBRxy0axBF0GqBSFtLolQMcO2rVhAfzmc3ZtZP+KYoHQ9ljejp6W3xpR4mIdQfZyRAGBHtpz4qzne3fKCRjwrOh3E5b/fyfP5oDJcAlgZXq2uHW/vXff+InREGEmlMwtyM1AYolzhREgJbn+U5nZny3badpspDrWIermH25CC3k+9fXI4elM82CqnyIUA9SEIBUYwgCmACgFwBl8nwARjDKwlGbmaPLt4L8jgQ46aCxotF833ddpCM7DxeaPNUnvJP4YdiG+bIgY4HLbBaVl/kVb3+/Md8d3iF1AsNv4idX/b3wTCsB5MzgUSGbaBf467H4B8EilJe47+ezKoR9R+cSko004wtF0QrxUKnYvNYK0F0IUPSMMROVM9pfbc3fqfHh4GEtTDUA/Kr2xjUaN66JmjXWVMCQIwV0s7Oc+ZJHUOh2gsw9d7sBhfseV0tIggVV3KtdunUzuPV3bu6iMNMH0YF2VwwrJtiK8TAyHOFWtXaURhw4GZZYVWrIW8xYIbEOb7x2VZ9sRTJqpUgOSgGoQRjkpAAqAAsRbGeWAUYIFqwwhrLi34b8Dgc7O3pvZu9M9TkGBRv9l+//Q7I7Weo6/Wu4ot/7RmREzPRfQa8LulwuRW/duPNF8Q3O91s50mH/Wha+fy3iKs3KRJ8aOIDjjNNz+mO9+rG25aLItRd6MjGTf3jv1E1Nv6iwB560BIKjENsomrMbAUVOvjjUKlY2tZMecR2vRYRf1pt4zNrIspv2hru5nYr3Au8jokBbdMranL2FlyYfAtIWE9ZG5MCSsapswtQ8/bCGdjk94CKuaNR345pYIVgCqqAqFmNLsOP3G/WC5slV0GrsuUkv4OgqVjFMIr5nu//0Ty//2T3hWhaLvSpGzCHFr1dFDUnKas1vpjx+44wuPgkghB/CmBpAABgpeowSAUUvBAoI9VaDkmnv/DSgQ3Xb0JK/5ZV7/y+cBP3Mn/7+4Apq6j9uh3ue1RvQeTnJfXlxxUVt81dLZGPfLRMv88058ax93XZN+4fnTfzsrb9mZVvNvOy898PNXD//799U79UzsiAyb8RL7OdnNfqxawsuI6JtQINm3/7Qf4MTDF5qbF3+H3HuwmbcEB0G9aPHLr9OVr5FH3rVpmrBSbJ6tysLoC58QZayLsqRlsyyF2e2Q/6zew5R9kfk+pg3hAAARFb6FMTorr5d7t0U24yqblQzOMnYS6d15zNqVj7MU22YduZCqcyN0i56XH8pTedMW5eJjpSeubh3ZWtcpD55rpaMvoOl1D/3FeZZduPfHK/bnu1JRmjCFS0wAolEUxQSDpD+cw5X/sdGvgBOwam+CvzsMCQSQIRLEzNJjwWkx/xqBCLDJGQoKsBIA0BAGAMBoM3DeRGB03b30464jut9c5TkGQIeUAFJBUYZEAaSSCgA4ZAgJALC0LhwAAFIYBAB22RDAaB0SwmCTCxQE2AIKJChKDlAZ1oKUj42X8/cFP7x66T5OY1lQgiK8ywK1PmB+fw0hFUpEAIAEJQkALLkHAMGYGAANokhCJhg5Q0kCgEVAvIUT9RCQ8bIREgAKxiyAW25LAESs8tzPvrW68vHBv/mD5cEFyrW7mJyapy79TtAcWwMNJx+NEfS7WnnWrZ8yuLKmefMbTxt9CAABAAJQPJYH2AxKL//9CZSFddwxQXgWtDcxez1+f4HcWXYabw3KTVXDo88JrDkqV+VEqVSMUZPAo+NBNqhUa5cMjvnu923F4WVsl/7Gx4PDvyymf7bcn0mHkYqUW8+ARE3aqEoZkZpg0iKrS189HlYIeACGfaA2pwUWmDJQEAAisHYYSAEAt83q2ZB/BYbpjF6CisE7El2yPgmaVxu/xDsiptmT4lcFAOSYzLnAYRfidQRJse9BsrcXgMPmgl9o9igdAUUIIIAHIAoACACbwkw7o9fhIEA2ZE7t4TCS4NA6L15aFcA9GqqNL6vWCQ5Fd0ZvQOhdIHoBQHABZRgnfK5sArQb/fRtlywCAFiSGkW11GCRICZfduaHA9B+0/grwJMANQhqnP12Z74zm98NKGB7Oi8UGwByggdQNShAEAAIAOnc+k+UFf75hE+VjQDc0/HWgTP5Uu4P19nghZfMXcT0imi86+w7ATRfM/4mb9QCS2E6DxxG1fQvf5X60a/MriNzkaGIa8UlrnbSp8MgHojuHbf8pMHDS9Ifo5a+dAj+TWil6auh47L8vOecVqvLaNYHM9gbMgLhtJM3dPeUrDWow3ZWs8yUT7lZKqZGJ5OKHPp9uLSgnCEOd3Fy4GLLzk+L11+/6Qe/+O7f+GWn/sSXqme+rIbSdCFJkvrWo3cMBChalgg2i34aH1HfZ7uDCRCClMQAVkpiABYEDrgDYIkFBcAqI6CXsrkL/QsSekHXMtummMAJc1PIRT+6nK568/w6Rg8XJj/o/DeMDcyjJnOZsy8qR1AShddRNHyWa84JMbdb2Rj3vN/8O8UsAAAAAQAAAOQAhGxv0n2EQ0u9tIcOzhybZ/yzsioRsRnbsce/b2D7Has6dybAkeusrnLCa2Alm6+TJM7jnkw2+/wS9WtmDuUao3eGdPplv3zNmU8avSCLAKAICZhgqctP3Of+ee4Pd8xkXBNX/Mdr9WesCgCUuk9b5UlznnaeR19WKZ6YWcn2lJ5OIaqJs6K5XSIJBwCATAYO3lF3/okWwqmb7jrMOkyNc87VV3VWLN3ButgkDN3jzGW8FdovM/xu73nVXma6Onv5f5vh18BSkKTDaw6jy+3qL/3C4GjUaPqYCSdBOHFtR6FS9MqZmb3sar52+/JF0o2o1gl39DRMAwwAAAoAKDLY5nDYdJY/f/V+lt6mBEQF5gDkYTq5WSOWmgXYJVnGX81PqZzU0zQThcy8mevTMPz+RDXq5avSbL3hwVNXtTT4/s0v/6T7t3/iv+98oe/xny6bj2S/Q5FiSAgZEVkjuPiMAJ9JMS04HFab05hJgtUYgFlElAAwcIkDRgFLwRBIuKMMM5oEmeogFjTTfeDITQ/TI81LX+tpxwAAgKd9Hn9W6jj4ibrBlWoAAGACH3peOSrI18GhQY1GATOigYD1xcLPxHSKBOCzEjLamlvf1d5e6yMAALgiHnpBgDngPQ/VaCkAALYYZ+7QxifX8Qf70GZVSZcK8O+37TrTPnCIEgIAgHP421/4wb8y/laxAnZMweiSd370uFsNAAAATilPPy8tCwAQMJpb3HOo+lWAZ5nNJ/N/s6UmWLBgwaIp/ne2zD4ZDQDF7LnO00M+ulVe9cYcyABUPv5sT/5to58cN0vAKyXpm6oTHPzo8YagpAAAwCnmE9/VP1vcCwCy1kjX5H25mSvf+NT6M/8tOHnLLNwPlg5QR79uR/O1E/3gQG5SLN55P2tTAoEBwGj9zP992v+slqFN3Um0uFCVhBYEZYVVHO+SsgZZSbVwsmVEAUQmFWqZxoZQd3wlFyCiKCZFKxwpKCcpc2oZa6JojfxBtxOvfuZJX9rH66cT6WUwX+9+4OnPXLhuTlY5PKXFFAF3YIbpcjJjkwPF7a3c/9vP72XvM/77FdsCiAUgpASM5SqLqWBdLBKAMgCUWGFKOrrkBEu5mmwGVjPfw5Pbvbu4M1ZymdFPeLM3wJw4vKitNVupTfKZzOFf23LvWQEAAJnJPv0foD8HMFOcnxegiI8VTn1/yd8332zoUIXjdUetj03zFFUObvXaSL0Mj3yTuz7iaCnAYuBizwXLxQV9ir01AUHYxI5MFr77hCVM5Flnk9/U1649yp/7t/UnCYlLVAsi0X629n3muFsNMOtcdsbMAW+7aM8xn/l2IxUATqf1PX+i+lWAF8hLv2XmbFsSLDriqVLPi0iwuGr0P6EAALU6oGTW45vdQ0f36BRz1ez85gIYkNKYcXD4wnajFOaKcc4ZMjd626X+cDfP/aQypwoAgG7aebvlIpy9OfCJdB1PnFbbH6Rafkra7K+ft31ejY/lHFIc4UYPTwEg3FuJV/tfbx7rAzvdhroshijRQaXWDHcw2TE5a/lOlCQDuJ918rPchaQCUdiA45adQFaAEMamKAg1aTqGyjSptOBITogFxpZkHjP9YXn4Rlk7etfVGpvuHBu2g+26JlVc4bGyHo/a+tFXDspZ5vRPv5Yhxtrfr/3sIREs1thYngwsA0CJwBpFMJApYAkFsFXApNG8oK1o1BKKJMFXzz7z95bcb/ykgMAre7409VqYUfHk605uLwM6djAjK4aVJAEAgAhGL7FlaTqqVM7MauV6qykld3OCt4WE87Fqry3bN8igcT6zX8dfamx1mWymRgx/OjZGAS38xFWrP5nN7d7Rjk4AANKJ4HPPY+aMXKh+F3Ci8MjXYPl93wdw0/4R91/9Pfs/PPG4xNMCg1hjRwKwBg88s7TfNHPW1UB3qW1Wqg0AoOWN62yjA05YXvg1Sg8XOc/jy/j/0+UXv/DXfvLP/LVxyWLNWPlZmw0BYFVQ41OPXf5PGzzZN/2RgVUzeLIMhACS0biuGUaYbfl/LzGz070ZC8Y6r8116U1gAjgDdHv6dA2o7omLZppJnri6j5xMttnfnLbr50lLjyetITfnYvg179g/J+MkkbaRdNqFEbZiOMQpy9ruUY9O+oaVs4MemaqSnauHF0/PJ7igIjLhwMJFRqIRRY61SDo5RqWJ5wTW0mJIXCQ0AdlXZGmu7qMzn8ytzoo/uXTif1z1ITGg395cpl25qXEhba2tq36YqIiyb2p5pkf5YN3XNc/KqJSUSC2LMFoGSgTAgMQImFURYFXKsNo4QJOaIJRFS4ACqmsHf+qlt4gNABx/xPwrJpfY87l6xznzQkhHAuCQw1YAAMBm/XO1EQDzcvobPRnUFQMwUKx8dLZ2pMQHyK2YAB1q3zLf/chIVWUE5LD74SXwAiwaze9vPR9YJu/Wz8AidXmubjGT9FSSyuLVA0qnLZ/5///hBWZ6qX6iApZSAAAYtjV/euYowAKEr1bvB1z5DgsOIEvlT2AR4HltowNW4fFfTv7dZbOA3/jyO/+1vx6T08aM0RIsaoKDA5Zmyt2hn133mblApQIAACz8acoUgMWh+3C9EjNwAXl07ykuAsgCGTLT1HXAkdKOCjInsfdzk/uiem2sf71dsbhxHvoALIC9MbqaIPXE2lwxnmzt7ByHFSNcTB5k+/0OLo9s35SKm4U0It+3dv1yvoHv/vfr3YvLlwdccBHKqxCl2MuA8Ob4YiwpADwkmRSUShZlVWCGKBfmRs79NOrED2TrI3R+jBbHjUsfjo7O/3ujb9G8RxMzCy0CQIlCTaBkvPrECkgEwwRDIdMyDgEgRgVGQ4wcBQpMQADZtJZEg21JQArqY3ZXAgCBzXrr9a2ft18NUEc2hQS8oTCjLTecmd0uoIhf90eOBIFg6eOL4sWvLM5JvshxEOC62xAAAACkK+siCUgkVdoWUtgl4AZFJTocBDDYIhdjS+wKUGPJ9PNCpSCDJEDUkgCkQhRMr8jYIkA6aiwcAFQAQJdq3x+to79D4X2t9XJeNliwaIuVkFiwqAkKAAABgDL1ab6lDCyFI3sVAHLuDnUAAACQLlUFD4AzAMqJNcry6qG3tnbtLG7vuudfuzM1pJvER0gTJSkHdki4eQaEhpxyQrM77Rq+eN06f/zBu85ZHF63weSy1qwmq4kim+wrv72Xvk9+W949X7/lLh0wJ8ERGNQwJfKqtTEAJTISKiJSAdL9iB4REs6PduOCk347enlyWD88lTdlI+0qtPuxryhRVagaBowDCA3ZAiwu5+dOFKCkrHZSgYA1ilijjACAqQFkQKRiGBUGIqMiAXYZAOUZQIElgDC8yrXvs1/N4lMLjv3W8B9avv0+AXBeR8H0MlvqkApQRMDrNwl1DFvqi80YARHcf4AuKlMXtZUD4R5aAvIF7cVW8/+lpmUMyNCgdRAgzE/ONZPEYz2MDbBIJpafz5jf1N2N6SSHRTJRIyAj00YKlTblBwGpGb0GSQDBpOKp1nm7IVb3h1rjbbofarHB4qzxZy/c+9VP/dXzgkVVAABQWADAAgXLIdKGRADWjP/ci5eKIEUW5KpGdgFkgZrdNbjd7r/9/bv+1XtHnv6Xc29+4/b2V++WaT/06j6tr7UOs4kliwX0wgCAEXiGWVQwoTzaFAVW59NfHfsf/sbh6tlS3GSIzRhvBMKKCBy5fOxzYl/Ju/db890JrZXbrPfFW202T/IKKmyM8Q4HpjCpQEGzM9nxTqzuycU9UuXTfeCxx1e/8rfXFkuUTmvVp0+XsjbjYnXwueIowXC6Y3NPR08NF3gEfqXIyHH1/27vAFIY0pGJLICFUWAJAGKdeVALmFVYCqCMavYn3pyIOmA5BUABJAAAMDcoGQAj5icVLvWhk3gSwFYAAACmbi094jAA1uTnrBSQk+CoHPKqFIfuHeNfXwYMUMGIwnQpQKA6Zjz+q8OG1v+hvvuQh2/YfHGuCcA6r2u/sJz+8jjvd7dPgADAMw912E73eJvbN0VH7hkggssv9sf++FQE/ODd+nvmCgACAAY68rN274trvAhgLHy9rQjAELXlY9ulr7PlIwyVAqxBIzVSAYx45pZupYGM6or4rz+gMNIIFi/IX/n0X/3zF+7PBlhUBQVYAAQAFADdBTYABGnjAgJKuH6ZF39bwNgna2TIC8+WsyQkADLN9JCH55JXzwP+xC9kP/cdp55to5Pf0zV8mZaR1AsCwhIrDRwnhAVgAAifDAwUYaJ6Cacq5vfSf//3vPf+f1+zV9pOlSaVEBAIUB4ytz66No9XMLxrQ0vT3vjS5mypLBdCn7kUMP3FtYmrZWE1VnO6Q+lBcutH/mTZRaiNnkzbHde2Ttr9quOQTTsTWt3TVbk9XyXxhaq6EyONso6+kYU0PL1HxAjAmghGRpyAYTHc2kgLWrUFaQ1Ia7QgAyIBDOUAMVy1i10mSCQlQIYkANI53RZ6AQ5VxzVYT0kVQEXYihyAMMMnGTs+8i7gvNfj39uX5oMndpbqmg8c4Uh5OiQe1S6sIAtKdmeceYM5GFBd61UTHatKiaM6DZ/8/ZyYaRxlWvz2z/cDRAYECBAE3OqOav5r2zkB2IRrosVXG+D/Dv/rF4x/YKwAoIgIeKD7294aAJCMxf9ca6/sVSICkcByoFLKpbRzeI57EEgAi+yQi9/wjALYSD1T5vHHaSOLWEwEaoIFixbEQimBkgcJwpKAUgYkzwAEAFhmd+aRG62uFCnAiqFlXylSPee8+tvJvasBADhFH/ve+HDvLzJ97Xnpld98vd5NusRRGQZnQCmDCwECQGD4tAQAyAFKXJbPhTTy8cb3f9PQ0e+P7J6TNwHS43gkg9HQCSzLqZ20rL466UKONk0oa82U09j3i3E3s/C0/Zhc/6x79VIOMW3TsRePHJ1mRLtSxM5Sm+yYrtIMbFhNyf1J+2CpTylwzSJ1f5q2+84u/do6rGJX0Vo1N9yLr6KEjIfxk6nQFCglxQUwAIj0AEEjCzG8oRbERiNoJReBb8DIqV/rVQZhtrd79HLnS8+ry7v73vWZ1tRDB893vfhMFgEzdw5vUZXNmrlr3HdWby3eRUy+30s+2Uu+e5vc3w//rufabe09FuTp5Z9eRz+bUw/3/2x3CboLgq27gDp95set/twtq6e84+K3r/YM6nJlMJ4vtCcm22w7l1sOei4LmFNWoVvFghzrZcDip3/h88r3G78i6T/vyd17/fga3Ab9cs1Xnl94qH0JJ4Dn/P9f/dfP/bc/UwOUpmn2A0+/uv0fdc/f4/F5c7AXwNqrz2/8mperqJ/3SD32n3wwvdqP/OLn7Z/U3vTy73Xkk9m49p6f9ezdyNtpuVKAprFic0Numjzw4GjiN7zYcgtPn9rupd0zHje82OcXbipGv0B/0G7kg/P9B90tvLA6Xn5K7w6KKxxyz8lVEsyzJz2//XbzJ7QCwCIox+3uT3vkt7/11vniSX5o5faD/tAMGVsywQgAGOjrnSWZBgfJdzDzG9eFpRdcr0MUioHVbGQVtSNASXGFVimOc4dVXlcGvNBd4bPmmcfCqIrH/rg4/6r7kOXDs3DypnTsqOpJJleFokVYkXQNR6VorcEbNUOUOm7YnRtduvHWoS/v7Eyh5/BW0UE4CZWorJeTCbIUJ6yLUixYFhOHhiVGADOF2JRYeqQAxgxAsQIAO2UQS949ZqwmUkj1umT4ghtvvOd3P2Hj0NxASRDwwMgWDU505bDudO9epJO8ulXFI8kK49a92ACKZd+5Uh8b0qCA8Gl83TBUZ/TFX3He+See3WifM08f/R3n///kcza2TnGoZ7P/1bFfvIestKaFJ3RO4YzULegiza7jmJ6Fr+Y7/tQlIDGdBVe3+N8d2N2k3wkCJv+zo79oj1px2tz6Pxu9tWVxIwDxjy/+9SNPlwEAe9ef0GH6boPnO+9bxndNLt3M/MvGL1ZPg2NW7mRsnnLK0/BihYhpVF81f5rBQ2Fz+kbplp7jgdP0ShfkK6QbiU6HnwiMHJvEoX2uL/2Cfefvf3bLyk8/KpJtJBF2xi0ymiwwNzzxS/fA/U3ufNQd/3RGv2jLwQkASEzTdPDtT97aR8zGuvVLCXIBFozCTfhbBoADSGCb5u/sHd2wxnFtXXiGLXMKhGJwHPVqgW4UIDBAUajMFBmgOihkJtKUjW4asm529cpNR4+SRsZGgNpMvUjlJnLavGhj/2w1mXhs1wYtm3eenxq/oW7Vld1Uf3Qz9sF9jhlRqSpW59ICDd+ih6CeZINDkUMOugBXQsKosCgDdgBYWsAMMwogNdIaTaT+qsoDcsNKgeB1lKLjVIIyKSBt0RZJyiCkEElLekuxhL8ckzWtFFAJAAD0J9BUFgoAiNxyo5rDRku0KsPclUyMWNgUWs2f6R/F3TavckewYwsSPzK2HfOqsM4H/rRdCJjpITftWb0pZDkSAESM7lndh3m0L1n9Gby5EQBA+vMvxQgAolyBOMqafVh+pjxn8FyRshjeapPiikok9cwqB1VjOuMbIsc7CUX1HhCygUzTy0IEpLBgilJcqMS6vGkqC7umFx4ZoSgKFCE5+7z+A1q1X9HelycKABBwtt/12DuxX0cuQrPK0HXG0AW9gP3CCG4Wwu24a2pDiyreemtpNJubj7j9LNTuJcCQBFKbXvqqEMpSSosKtZSFNQRRIkUk+CWZrOM9rVdrZGUmR6JfUAFEvUAhbG6ozqynk+mptJvpfE+5/LUjPynoR/W5LfG2/VStbS3poAoYDI8uBycoTFHkoMgdAACAARsso8KQZAQINEEDMNA2ZSREo8BSoBmLNbHpWjG+DihN7QJOFIAAEg6rAAASZKJggQAGHMbXCYJygkVBgFUWgnIimlmCzRMAKJTAsEuBdGblKB9adN8BAACACeXwi2Te07joDAQ4UQAACiUwuQEBi7Lg3Q2AiMRgy0EBEAIsAEGAExwSFARwgSUZAEY4JAAs4UAQgAXQWIJyApABYIQDAAC0KIE3C5bG2umjXjnv7jMyR1fUobCABUCsEQALYAC73pEFImBF4ry6cT298u7I1ouyX6vbZggAKgNgAFpox0LaB3DirquAFRUtEgs4ILKy4OfAkKZNJWxNQ9OVrsJJjjoBNtWil8KHSX+dJRZMt/Ly5fdsfecfzr5Y2F4LcTl9DbaRre1ZaoUT9ozJDwY04Ct5KHRyrRqbGECUQ4UFSLyEVrDEQIwAYDYiIQCGMFWinrDHRThvAJQFv49OAABOsGMKJFPLR7M3UsklsVOYLJx4QTkuABx2AX8cneC37T0nZunNRQcHAAQgYmGjpRICAQSMoMsASbEiiznNhbTP9BUsmPYbZY0sAICQRrD99bU/FGBY36Y54/2kmlgUpjO+xQVSmpQVoSuLRRqs7UKCqlZWEYaTCyo3I/O+lbaDU7rtqFVWqPn+Tr3Y/fJ3Lhy761uc5gybsPOelJhk74pbT+wry+UsHXk4e6/tvHmxYMHA2DkGbGVwEBtL92gAUgjKRjMKCGYpFgMZb2VrokLVHfAVDocC+oDwlVInEaPonwKZfaTgsAsJ+KpOyrPVl/dQCxtZBTgJBIA9BhyWCcwY3IzYy4CFpfBqea2N7nZ2d/07DzvlcpDvVDgEgIO9UpPRCOlTWTuXtv/2naNk+lKCKI4UAimEhEppUoC1pDnN1IpSpZ2JURKtSrrhQib2d88z7U6rYDNuF8Jf+XiBjXLjXjZh+JUytMa1REP3nDjrP72nI8/t7LHI3RosDFI1LQCQwErKUFoDcqMBEAC2FiOwBBlwMzHb6ty42sgahQYBARR4pW0HkEB4yIRggKQCB+Eh0QUnFRCUJxUT0AXJkwpyoSAKAAgAUDMGAACwKQRF2EUh9/4C2F44MAAAOEBQBHhSeaUNPG23EQIDAARYAIoA8KTahgQAgACQIAnxJvDAgSQAQJuPgHojctjMc8GJAiBUOtJKI+/ac//s6SgQYIUzEgAwTKDIKPBKeGcAuAQMJ8eBXTbTNVnoaq+CciggIQCI6fclX6XFGMPN1y87F6NWCAGBilCEZJAJoABcK60tweSqy50+cV+PhrtQhe5Vy/rZi5ES23ftGpvKePXN3d//pHrmF+3qaG1CxSRlArBCWfuTVzl459mRv/X0z178y/50r8MkWf7ktMESEoAyIkqKmJaDNdiwalMDSD5tIoAO1JXTcVNVwlfeS7dvaD6ojRoDgMJ6pR0AAAmAA8JWAHLjHLvQb7TAGYAw02qKislF1Iooyqh7rYCp3q1WucUymJQyZnvZPAm2RGHl4x28VHuJPZAAOCwIAQBIOAAAHBaEMMGhRsMSNAAgAAjQBjGlqTCYsJQTJQiQKIog0aU8YUkUUAaAkR0U9CR6S/SwQS4HABykAkAOpIRd4Kd5Aa9AGxaxCQCQwyY5bJKz+rOvIs3GVZQnunmafWz+7eNMzqz+TCLCqAvLB4BabmHyBoARgxEIAKMKoxLuzgzfXhn/byc99N03XASYIIICsAUPqe8vxOmLXHbfnjrDSao1VqniccsqvWmbwhoEhDA4dBEbTW+6vVZOfWLhxOr26ZqdiNF7uycnfXlqL+7wrSZ2610XJgCuThDK0qwifIPUsZDpm3jOr77xv9y+/Yef5X7lAMszbZHOteAuYStxQTMJQ4sBNmVDVUWD2AANs0NbRy8aex774kpmcZakp578dygMKqRdBpCQQGWnOYhUbW109TSo2rm+eaFyTLbqtMO+m58ES/xd8yV8Wv5KdAx+q/fV6i2j+TY3tbv5mtcMeyf2K2zJjmvLciQAZMvUiLpSsSc739v7D/9tfX30szqSSA0HJNDqQgyoppghqFbVQi2tkciUCxICATW7xCwAlFBCdhSVGcxBfdcMRZhGQV/yXj81wSgltmQ0dVqJ7pioMg0nAoDm0BlqmvfxJuQaJNClEQnZoqzVS7HPvU9SMYEJwJICxhpKTP3pp18/lTfTuw/O/OgzrYnjau5de5+7X/ryXDyPIlc7OziwcgUxMALAgFk7bdi0LwBKQKCwJIQLw3q8QGb4bC18q6NTyi+fpxDhBMPhsIjMbTZGd9i3z+8XvsRFce09VvO/9WffP23D9vX505fRa5aE2dd+lNhZM1yoVGHl+OET6YNrtVNwvk4NEPicZFE1Cw2VyQKklM9qe+eGWXv9o0PP3XXvdWvFxAJTjbQhQJCiXERYMCuaQIw0QNKixQBECpnZDPU9alvtWDtLtdtue4634+WXb+q2Rz14cxeG0g1sryXaU6tabholTtWqa7Ntkdq4uiTtOiKSfjCfjY5Hc1SyzZ3tOXNi6si7vCnVgyTDTOVp8V/1tRG/fHBWQRY2kMZKjMZYy6M8fP1/8+D/lL0HHxgholNRFUhCAQ0iAROFjuAOy/GbF/LKMn/k4OdqxZ6+pfq9Wb34CyncSnhV7p4EUk7dWg87UzKk9dIu65vv3/DXhhJ7utQ6dfviHEjjFhWoq5CIc5Ym7syKdMG9NICilLAoytnKkwZV+Ff/P9xNC0QMAAYeIFgK+/pX5398Kn9y92/9zqPeeXP22e3sCFZjfzraMzaykqo3htSAMQIAYsDaYDwDgAEAEAKmIMAAwovLYB/sNH1tLq4MR6EF5ZXQoIhHQhhjyOuNPYPZPIbPVl/nE/M5AwVKpgbrK8djY7MaKo+MerpyUh+9u+OFH91e2qgkNXqUGxmArMpIQgEAmEzO/s4vTvLr69++7A7bdPzEDu+/uF3/4D0mAOtoFmQlsqLllQmIjLEopG2SgIA0mhVJGclaV6h3eFto+/x+zR8kAk+yykGayqZUYn0Xkkr0HErBDPoVxFYdnPSG3LUcNCZ4LrcIFunU9Gih6xtVrtS4rqePUYu8imv2s6cMjnTF2IIMJ6n/LfW9cSvJFapBrAqrG/Uz+uWsiF9980dG32AToLmDNWeJQxtlCJg7kIoLPVzUefv3h/qoA8CvMkQQyVuUEF+yJCWrsYRb92zRa7Jrfbqvm73TNZGFel7Wvq4P5SsyrNEqsO4G4btFhrboBoDLWFf1RagSV/cej5layy6dItXFkfWMnUZn9A8+aUtfKCnpZQkc4L/gn33+6/2+fnuKN8c/GfXOrDNAt6omUAkluhAAGAFgMQCWVSXLbIwBBAgAAAAk2AUi9Jb1xtCwBtbgm1UHCJTGo0glkTIRt+7SlHU7f37IMHFnufr6u4tFsuzsmmed+wYNwdGxnq6etGj3PPuUbFoSMz/mxz+S58uxpxwJNdWAynACF6//v3g/cX/ZH777Dv+vZ5feFKv1C8ZpGklLOA2kACoRECkLg5hZShRGGkgD4MSkxei6YCtUlwh7OapSJ4qgihdtLghwbafUFjdjSQuW0TbN3LOyXJtCFbVqkZ6rpZ4QXTBxt300c5/1S9/028fgkr7V/tfsvzp5vEGawYKpMK84Yg5HgMVlmsb6weiglcSK1k33me545/8/3iQWudVgOXSjFKmOMlU34vK5qxdO/nN9kH1IQQ3tCJPSErssmQQobgaHpVyu68CGWsNLpl1qFweF0zFraJ8wFQhGrGJZKIyFuBU1qZejdois1ZDBAOZELQyVTuLQZcW5pe3rh7MroKkZIlVKwMj+j/wV/X36sDwHedYNg4HIklG3AJGALg7MgITPmGhuMvZseTYABEgKAySQPaQBgsDEoB/VO2EzoYVtghxA05TSI1CgVMxuxJ3rGnnOIcNrTwmXLB/Oq3I2O1N5j9CNIi1ee1gZLlsvvbF+sROlNITymzj+DpkqW9kHA6oyilXgwfjsi+9f1/NZ6j/abddFXrhFQFsCrSpokhtBKlEkxFAwEVVVaAJDGkg00itjKoaVBnYWO93QsaJY5AWvGE+Jksx5UZGidIRiB8WL5TpUtUPL5EZpeOOcJfUFapwRymw9Ql8mEBfUvHxCZ8trOsXftV1pwRElVI6pOrDfKRNlkojhDrKmfaoST7yGvOLicuagwg9FBDAIqTogQmElM67z/NXOxbtf73/6pk2u2XrXn8eO2Pme2CmgSMlUUKCw291F38N9BxlLV+8aeD1BxkeoGuDLuu6h1+5EO3ZhSTPrFIVMyLVAjcoKNUrzTK7U8bpU4gkVO6w1ioABKyAF4DLgT7q/jn+A/c466JVonuTCYBGQAAsInODfWBiPhQ0AAAt4UBQKbFsWjcpILg9u46UXzbKDLoTfMSZM04j0CCmhzIarufvkV3Zfnl/+vQ9fasSo1mrKLOasSWR7X017rMzloduLW9/+zBohV5ZKyC5yh9eU7QQz1kSHKCKoIm7f47XBr8fs82fTm/VZjwR42O/TehhqSJmQJQXLq2VBzCmMSCKhWUCkjAUsqU6YozZaCtW4aS2P7BjNJYccG0QBcFZzN3MGTBWAFW1z7z+fGwbJ1lEkokKVRzreZoBZLtv0IVPoKtjFVH53Dettlzpf2ZYWpgobsGx1HHY7mzXJlEJioNvU0m71rsACasrce+XM5q+xtoZDqohQ6QKayMJPfHzi0JfKe99STyrtUcULJK5ZswuVgAwmLMMAqqscHIvVZM7C2/WyaMn14dD11Oux7zhtUFnClc1Qz8K7ot1ArllFK4CyWBjn0A2c9pPidtVgd3Z7fUSvl/basTkWjLWfyXwG1tvXef4s/rbc39UKpVEAACiALhYAAAEwPkaAEQBUhCxPSHaNpgKpijUm4/FE/XG9fkf2a395aNunbf8+qVNLMeIRaBAlC4yRu/rJFd4fcp191ac90dVjbfESZst33z53f/3z+00uvHOYig6jsvPGwOSsXlBhi0qdUz2jif6q6K23tyeTi+BmWa1QBOuwud8+23/x8eknR3kxVbZv5fk60ECeEioyUZBFGnlhIkjthAaxSGvRsEiB0YqINnbQEd1uWc22qlQAAIBZF7tBQgUkUIQDiDd+45fpHxEHtXvWuufkSItSqpjdt3toq7eldGTcekITtgpQ59BbTCDtlNVlOUfeS0qCQQEhaCh+21IjQQEE9cja1atQeU54qgNYVfRFfrkUPmeY/tC+/U1vo4UNnbfszbTe5V2JyhyiWkkImORmNwkRkMh1Db0DGKz0CK1kSMgSLNh5N3GgoabW9QSAKmvNkmweja0di5rKRBEc8zAKHsNDHbFAokDopi6I2i1tuWeo7+Kf7r6y37NYSSIDAIBFClh0AnXxy8AAwACI6JjxqIIKVSNnVZf6Y9y8ndY/FPpH0t9a5BB2z5Q6E3YAUJiQaISUUBrPM/JqI+fC2OtrdKBG1nBaLF9/6uuP+qv3k8tmDdTleY+52LzzVBfkJ2KM86UAI9ZitllMVV4ZyhBAIwO0qhVBuWXbwO5y+TRgDHxhARJCQbWGEIuIqHUpV0EApMhYBKompkZni6NL5dPX5Xpq0c9PUvSCwwQdgdhRNQZGAwAAYo29+iV+45eQDZYQ9YRVR7W3UMPYJmlu66CuSK8NHIeulT5cIKvcKQ7MbFteKB7HXxysP8b2DqY0ASQhVEGTtyRDxYgEpQrZ0KMX2Sf6mI90Q0FcGuPlGGR/sNn6lmJH0oBUnVfuUFlozKEW8qxhB0XWKEMBPF0GmdHlBH3dshX5uHoA6Bw1DHOcsWydHhOFK9Zrq6pThCQ1VkLDMI0cJgx0Bmsse9eu79sYa1WoBva7GMD1vnm/bdz3j+f+qdd/vP/82z/+vz+MnOAIOLOwvboACRgXwwjEBAwgTJz3l5pxGkfm+6cK1cF/KQ4vS/VDtXgv7M+03Szlr9d5b9jDAwAABExHcCCTUmiyl/OP59MvzAtQ407PuOQr9Nz39of96fsJiyAUd6Zf+3Y/M3hQDWextJYJcBwDoj7vTcc03SwGbUWHMgYaxO0j9uy8n3p1/2Ppf3/P6J8B9mqCycDQSCyhJEjGwszyCBRBigjWJK1C3AABRBzt5kWmT2Z/4Zep/O5wgyaKgwJQpCMCAGCtu2f13MhghF9bfg1UvLxDiR+WTBYqoYftEJt2rkUr0QLTmlWW++H4o+dnP7y9h5IKBHQsFaz7lmWVSrmWLpZuxlEHoQpUYnBPTH/v+NOvzHdOKdwOTjktx2sElnAbbnWkWjU6LNVvJ3PxspSTpqa+cjjsFF+5Ai9eDF5s2B27sadUDjQFCnfddtI9DgpLe9we2wDUXkJ/yGuSOVVu+fHY46oBAPCwsD7dbIfHb///5L99/LVhvlLSCAuAZQGy6x4DnwMA0gBkZGngQZehnq5nBt/aWv4bXfZBLr+RljQGJ25VI9fq+mhucbPLLmTXH5cAjFkCQADgIUk6dpdDoB3mbTzaxz0AkcJDiR56qclb/UA/BHm/hHfKTR6UP+tjt7q3Pztqf+f9Xn9vTGfzdmiGRzumP3jnwXuZ+aOCr+lpgVJ1yvnV2X77X/vTP9z/C5Uwbqm+53ftxRaiBQRgyMBYZgpAyCeGIK21dsOihd0i4VaGiP8akX7AfjDV7575yd/9M80r/Oz5skoUxEBKOhQY0OnNJc8u84S08rZ8dpmZe9cS1jJ4SGFgQdPxoefJc/3uHWrGmcVrTdlt/5bP3ws/zlAcAh3XLhGdXvuytd4xMsLVZ8/bEqnmliUeHNdt/d/L9jDW7iFAi1mRWcWSjMAAuAktFDzBd3GBc/gat7KGJwL7ySy3QopmrMwYg2DXdMru7icFEeyQ1qjdZe+YQro5tGqsU43KTOd7VQCFjT+G1MgBQAWJEuVVs3Xm9/7l33VKTraUyAUDJjAw3CwQuBkQiAAY0gDpARB4HuM2WE3/v7f/KG9POF5ZP8pFEqcj2v1u69Rl1bVJN4GJAPDwAwMACBhZQiOg++Gw4/8nFHUTLoX8UoSWQA99o7Fwh/mBtEc3/MlhdGfN7gV42v0HscXuLZoZP6bdqzsHzwr9uvvmE8/n5oz2OkK2refp85O3589Wqtf/ev6LHml/9J3aZQi8AIChBpShIGStWZO0MMESQwKThJtABA6rxKOF18o1HI/9Gz5YLwR8bsw1K2gWQUUFE3E4np57Se356FxVmrLChrTgXFhBk16TBwxpnXZm30/1PcJb9Z31ZxaLErqK3/78eE2lAsBOwykWBmwGywUJLME1Xjz/QonjlKBct/Z+Vyw0EAJ0817qbX53V88cbmS5Lm2BsYY4LthtDRucNMPtMsOuXLROfV62ADG8ZRW6VWPbcuzmiulpnaeUxduRSgHrMushQlhVHZVR9sfqaKHj/lPRK4MwAXCQtSOf37h8vH+1PpfAXDjW9KI3UJgxg8cA0ASMABBgAwMYgTQWQka0sGt+8HwKm9aG0ZEAigxHLjPxyLPf72RlhV0IkwbGwHggABBAUA6Fkrop+QObu/VKSJSkHPVNXvCgXwD6YkOT1+8ycUnX5GLgdi/shro0ir/K+qCNOgk4LpX14/7/tvY/9Ei1O3XoWWxkL1snulLQa/Oc361/F/ho/fQnlkpPCICBoZpNW4woGmKAtDKGaAVKaZZncQsRgTiQUFz8xJxPmkIX1xvJ/QfrGrIVsLSzCAAKFc/TPn/ojVf3aW+9rPtaGMFgWN92r/BBYVQDAdPqFlaWdpXhmciKAYConfbNjzZshwJQ3NVS/nuspsCsdRsqIpmSqob6aM7Y1dwE4VsIQGwRFhgFYM7kZE3Nx0NVUDzAsStVssAoAcRncAumAsOwfFweXy5JB8vyO96Y0krglVE1Qkhgjd1wPXrqnpFeL3HqJliDiuoUx7BjBzgwQeDAAyY7PMjnm/cv+F/3jzlmHzgwlgwAAESguQlgomEAiABSIAAMlgGULH1w37fPc37/S7+/Ud0UAFB5CkemCTs6WrodoYwQYGPXjAEDD/9AAAFAMNnQURnK1bn4Tj6TwRc55EUDgdE3OSTwJt+w6kPPbB2+3d1dRLcp6yepB22M2gptS7l9Q/PiPfa27LZb9daheFL34363CsKCJAb73cbF24AhDoowgMkAgmkmIiiJCVoZGs2gINI16wVxA8SBSKG1Li4LyIATDkjqV9RWMZXCYSSkUVjAmF5WOU87iaABowMS5+737q7Fb4AWDilwpLa4hOUC+ZDlLCIpGkzc/RgXEWWUAT8uT1JwU9SibGMZobmJr+lI8zKRoQ5LX1MiGtIcukE/Zu4YQDAJaExhXAsmdHAEQBN2MMvgTAWU4BABQkLiVlKGi4pkUTVOBQVYLGmjLFHYTdZVZR9ngVawMMu+K6qdUQjJMUxPnl0fn+fvvVe/Qy1T9iaksIILBoDhldFARAAYYAzAAALgkb5pDV5+6U+E+e11fv81d3sOmlRw2Mu60FGG2XsqA0IWYdBjYyCAECCAiPQdhSbyEL53us8h8/wMlzxAWAo44LCCt/CWfU3rwe37Lu02d7ZJh6xxmVMUwDpSgNrOlwuhlgdvPeWe4pVrp8O9BoxAWHBKv8X7I77WUIBFCJYyAKAkzG4kGJJm4vTsU8TSxABLiZ0QcUzxA/zm+Xy92SGh1kpTst1ztTgDwYkODiVTRjJlNNZ13cCBIDCWUIZHur8C35GXnDqrIGk+kW03RW6IC9Ts6imwDHayMiKFTOD13hE5hCYLb9chAyBAZFv0Qne/pKvcAGBlIgBCExOpA22KuGie0ICrXmfn+BS0agxJ63UEiSi+SpEdZxQLcdqJd1w8qGSvvZupQgiMWBxKq1SUrCFLOMRpzsgEyIYgaYaAx1TRUiBWceUkPAEfjb97+452T1hEjxHAfg7sBdkZMwaAEQAGBhCD0otNNV8b333xf39ZP/97elBk00SNlVG3Xo4KSJIAZAGJMXANABAgNFXZIV/lJj9pePtndudheekhMQGMTDwU0aHN9Zj38DV9FDlKpVSWkMo4AEDoHezL02+f6n3EvxjmqxUbRV+mTtnjbJIWG3bT6w24Oc7PyhWUHgvwgKBIKSUAdpIQNAlZIxE4EgKPAOKY4iPwTCk5gTsL3jFaB5+lybkqx8oZG0lNSRaMabjwejkH7YkeIQB6HoB1zSvDk8uYX9v5MktfYMvttOR4xs4eUXAVVdG3RRAATaSMMMIGGyFM5JFjKRFq2/GL7TuEKAIQiFAioJsTCmBnATNqOIcgYJQzNfBa5FZNmiCMAG20ho5Y99RihSzgG2QSgmBApdFgTIYVViIGZScxcKdFSpgKYuiIgCURVDUycYx541HW2xlbnJR46DUhJCEh3M/R22AIDAQwMIBAIGnI4/NELW6739f3XzNH3j9Vi9vilqkMw8GtboUW6w0jAISQtcEAAPMAIAkADeGECyN7P3d48+evInOZE12KxlwpKOhMBibEJa5oQsADNOC4hX4AFLNa7u0J7ygfcfz05/vHG4xNVk7H6fvv2vPGWQhsS/d0XmWUC+6ImyFWMjCwIwMApNKoRCMmMRyBEfEp4njM0JKIyOhIJufyzsZqPVz/zP/7Tx/JB3MFOO9qahIQO4yMTT968+61bQ4WE5XvtUT3vpvObmBpOnFpMPy+tx8n2EV6n8wVb7uwOBVFgmokWonSkUAIFAAIQks3dyTs0cByF/E+50f/az2jASAlmWB4vGJBBdZYIx6f153nlBYYnTvHqGO5e7yFGm4uBrF+0K/TN/H4SIhoo+C4vPzC4ntwIT5yVFJBQo1yJYdGAkFi+VxJaSuIaKCGULW3WVqUmqtxfFqnt3HcwtQEEqFZIBiBXbBkkUC4WWBgABgxABBNYujp3/tRcY80+/CBi9w3Bgir0Cv6Yh/kp5VmYRdCsrFLCFlZgQBwUnQAysrcEEpX15n5J9ZPfkpu8wvtTZ1LDaY2eQtjXlmzlzlZHB0dorFrhAUGYjrWAEoDnr3t9zt+OJPfUnaylI41pUftuntMOdPWZY0qM4ueF8r4djsMeIyQQJLEAEyk1GxaWQQCYUqkyFJQ+disNTQQkdLlliyOkZI7703nmso7B5SRg5CUmHEyoFNtgfLPNhuTRvfNLiRWYXwmKryz9c/+efb8ZqUF6iFApx8X+vTxV3vQtv6BFChVhQq1uTBIhYtuFeiSuRkQBCVrTlKzUIISXElNrbpfji6ICgi9oz27BBHiGdat7u604lK5l1bn9Vv6Sp9trQFvejeZ3NdqNzqpVqV87a1V+SAJxXEBCqs0k+OYqtyxbu1dc2XAVRptY3JcxIlYbu6duzerd9PN2iobbWB0eTftw4wNMh4YpAAMMQIAygDKpBkbWRl3ZBw+o630O89/9kvccaVyRVJyUu/pXTtH+aBmEQiBAJREipHLsnE1YS91G5TbTuOsb+mwo6BTj4akxo307DDu+eBcecIjQXW1Meu3v88vvb9f4g0d9pdvntTn/tV/zPXlqpaI4p56a0EQ6UovOAyG+HD83v2vLh9cHc1GuFxugCQyMWI0p4H4BMyOUwROo7qJrcD2ApSO0/YC0gTHILmBcdP46mjZz013JAbDYQvgpG4B8KhBTjExwDpiBRMcdj7ngLHDcoD0Xvi/e37bUgn1ykwoM1Vr37hKABBqJFR8HStRDVygElAUgBQsN+P171qUmeigrMoX/6Dxs6gAQipio7TCcnIpOcwuDrHs5sw53TSI8zjX+nLru4+8zG9znyxqVkirfFXsgMsqUAIpNpTLraKOzmQN3nnj9i3CvABNRG3h0wC03MlwF81oXyLUpEncujFDYZlkCBaADAMIYBQCcToJKKA82boTt68vmV88Pr9a97/pfOXKQUlKpHrshs86b9U7YEqBlCAArdmN8yLCynrgB1c3C9xyhcyYwkjfM6Mqz339WtTpuR+4V4cpLs9X2B04/7/Z+Z+U/9v/vv63ng/mv7U+f98nqt8ErpNqDNsx7jGprLSluJ9ssEIFx8rPM599/tOaZyomky20qDWiOTbNDRBHAgI4TtlpdUrslmzbBFrSyKmtZgSCiNSU5pZw2BMPj+dzZVTauTmBE4ENNIDqtvBeQ5Ifr83vT4DxRd0V85Bl5tpDS5hDHHi3M4nGaZl9N19ebe7qTVqvWKgyuD+9Hg5FUkE5VSBtKgoILIgQGOwLvjYpnBPdPPbzXvzl+N/LtPJknHAIQj11yiHsD16U81wbntf5/PyUW13zqa41Vmu+3bubgWODqdTq2qGZjWbKyq5U6ALZhFQNQtFZcrOuFpBEnKXaZEmW6b9O9AUlCUsOvWihyJCBlb3cbtoJATMIAIbACAwQV6Z1zEE5A9prsJHdd37v/v5U15fopWfL3TrYh5BLuXWp9zpyKQuDO1Si01jB+f8fL8t33UcoLLbcivLp5fhBI8QbxikajzPSGKD/N+DyXkNmtvCUUsEw2C9nmVO/8enfuPSX/mXneHd27r2jX1PqB6qZ2AjnLd8MbcVZjjLTGtIJuhGXNZnhSoyV0pYSbgwiIiElAgKBOKtLV7mN1tLCEiAC0bzoJXGw9FMq30a3pUujY8yeVZIzTg4SqLCSyrPLPz+n1Sjk//tr/7frPz/VL6g7oATNcDdz75//3T61wSp5sMrxfvnsfpyHH+JQOpJbrR44sgXbrtKHcZxmGhoNErJKtgDleatv8dGsyysG/u4Td5nRmK2JBoikZpcoqQA2FsHIOdj3DA0or2Iq2fVzi6amJtGaLDX8xpGGilu1puw0uQorqEJ5AWrTtls8RRVoQuuoSkIr0/FQ6UVilsCGbYo+wlYlLNnD6ygD36NYYDYsyNO5PDmpk9dzrp9nSzHl3jzXuEuXXHIZDUAIhBSoO2LFG0eUd2vskN3E+fkE0VVRUpnCmG2GPhaOcHkMr8L7LTMVaNVVOqT+W+YvU+DP/8ovf3my/tQn9r+qZ++9WszWvf+vq9fb49cCpqViNKYg7Em8reXDb8NASSUrMRUYEewEnEAnjEAcAxHo7tytInLPLDWD2ZWzTVNe1hyTs6Ilq8LDfq+Vstz19N6M7nIcKiQkABjyzuyN+2pvZp9ZuGf+eo9uxxtHyNV00/gX/3iX3m26urF11528vtiPn2HX5Md97Hgr9kcu4cB7qn0O4XjnSvNu2NVBnWgitsPm5DYs63v7tptagaPIQK8BWu+oNlruplFOYhga5zSyEg62F/dWd312fPcpoxsMpGAgiJgYaV7JkR30SLVaMhUvyfKqqzSUNAGUGxMES0GiRw5cKjJ3qceW2cxmMwCWM+JYtVhPu1lSBqnj7GgKYBKwZpJgegBzBoQgqz2x9qpjxsf3Zr9J7xomw2Wl1CvxDHJyLidKSBFVWgBJUphYhtP0KX3QTpFBEDisDhgNfM1jTRG823bHog6gBagkiD38LabSnW8f8/y5HVbC3btSv+nQp3578cAufuByPgAA4BSUGN4/UN798HzcrmGSpFKxbDOW5iCcaHwOIxIQEafBqvqpzk68FgCUABqk6IY9YMUZzSYtF0fv1ymSax/VZn2mnaQMAZiQRO3ObZ2mx/wg410md6Zh8i//rlYHwXDmCpVLdg4Ktfik9Z3T4GGldt1vq49tCORVQfdMeabzZu6m+286t9kt9xvwigx2JvN8utK+bdnS5Tr8MBt2/Gf+52+PRkyqaZ4aEAaiMd6CBbBlkc3Vo40BFoCsJHI5MmWAGnqpC+uziFCTYy5fNjeTIlksdVwUz0yPLrc0lnDm1ivsbfZV0zYe1rPZTZAQwjMYmBiekJsVLKCuAhKGgLU0jAIAss4FkJ1Ybr16fPnpv3X5mnvHahiTVS09zhMFIEAQUURdopArqSiklD3pNB9drBaZ4jClhZgAceH1jw7IbGz3asNHE0y0AtWt8CGAVIPEHw9tGqtOvxWG/mG7/pkODtThVdE8Sql/dX7y7v74+O3do42LoEYhyOGsmqOJcZyAA3FEfEKOnSumYN1V1hQzmtByDRDQWqt4AVy8k+yBpW8y/cnxjq/n6ANz1AGhLhJQACBJMkCXPn2a3Un168h/9fe1orFKSiY03EIFOhVLf9d8tHGCmVmF231ehBoMEOoGlnB+OVG/Gy+zNrwPb+HUHd7vLvOD/lcGn9VNgiSnO6OmeHwkNzslyRoHW9sgE2wxcDVJiNUiZAPbMZDBjgDrXLKfiqLh1IGGEjkY0gpvvHVvu6kwiFFrUOyiK7c6XqV4jGYSrFGMiOWWnzmVq3dcBkBFqkahluks2pNFgAGwRGCWwCINwBqQcAarfW3c+PL5vG196b7qd7nLxIhJo+sK5FzOOCEJBY2IuhPFaEHzbmHwcfTwnL51sVIICcokFXlyON8sm+GO+yLD0RCmBFhtNAVQRBgpGoVqo8FOWiqFmwvvBgZNNcNsLc+wHss+LnWvXujfPhl+4t/0fLOttbIrHXKyDAIpTiPiQDolajQVVVvotFT1sMRSs7SgJbS0UeV/v7YcsLEfrSf9pq2PqvpxbJ5nZ2KVA5iYmHSii5ZpQFHTNbWvjA6leNYFpKpwvFvVVPrNYZTWapS7Q3fLvLTsMWzhW1rRSgWgZb1syAAG8CL5qvtk58vdf89+O5n5G+e/8Mv5NjtuS4sV+M3GHREgvA3btGAiS8sQjMsZdwBK0NYt2IsvC+OOodDAaFNNosDg0OGwmnMuddLZ2mqiOlIqVaqgrSZSk5euIlSTNoPF3IrG0Q1tztZK6GIpog7GJxUZkSc/TKAKyIhgZQsiIs20Vg2LsOzyer8TV/in4fpeZwykeuuyukmAM4AwGOeaCOtC5aAgn6WNgXl/iUNNeONGobCLjC6dc/a173wGPPbw2EM5GtIEkBagGjVoUKhQs4bSakaxQcoz9ViTkR1CEwKbwDDZKnlpsfvHOY/2+u6+6784ed5nvbW9Gv1zojUAHAM4kUoQ1XKLWxKtCFNrsVgnLa0FhlN7/nJeTYI4Vk4cOhgbZ4v6zo86rwOggg4gBCFSTa/MfHr8nsN37McF+nnuBjvL9ulW966N2RksxDKb1IKpN0yudN+0t+HX2N+iBzBDGWu2mQLKP9pDe8Ms/3GJfIi98tYfd+UPx2O5vtqEWVF82YcIKd25I26Kt7JUSzAylCJjvJciGq0qWCFEdUGwFQv2YmPZnlQfW12MtsOibb1MmVlvVaa4IojhEkNEAlu1LHcbZ3Krh7vCeHrtXvu8Hxb0x/3t4L48dxNtSmRUzFgAdjiDgQwACNAAlKZsRVrXPnDXUc7XB69/bM+972J/s1mjgQJISU0IBtd1bAA5EQgsJCBQAik4WQ2iZ+MbONmT+9NND7/YvAznxWCx7XOZzAWgiQOcbTDWBhYnVt3Cec/Tl7b/t59H39t79//n8N53n5Zvw++7/sv6R/orHvj3X+wvf3n98WogA+4KwaJAAQCALhql6qKMbjVg7AtsxbZ9bHHDWtGIENlWg1nyQkcWibEkTFLqyDbiwiLXry8ylVeElQNJyKKuGHcOHg55dstEL4ULXz+9LzcLXFrpD7qvl0PsNkuEwJz1mnxtklrS6iQN6u2+zkmN5lZnk2RIHthfjM4f9iWshZvL1/N+bGcNham2c3HY3KVnmULZG3On8N0PMU+kzIamSDmRTJ9os8jijZjF36Zt6EobEAZtgy2SzEPHtqBVoUeKr66Y6mQdPV8QekUsj88ICr569Yk7Qg6+8nCT5z7P48EVyw7bsMZb9cZmc2NNOcrIGDMZoMTYABBAGkiWG8PQG/Mei5T76abBPFhfkDvZnAJj9Rrkgv2F7K97B6EqCFkOCSAEQrLCkhd5xKf1o++vxF+d+C+3XJ/+avoWVRZmHbLhQTRnVVneNcB4khARcSSWYlr1hD7XKeLE0hFSaOpH/v38rfmr/Q7++J5n66K34FsLdwXVCAhVVSWKSoGilc1dgojWVhxpdlPINlCbbASIYo6sS3hIzeB4Mt6YWvj03TmpgOqoE1Qyg0gA5d7LJilNalia5nSShNGWy84jQ0kf2rfo/Xz17F66IzVdqCH3HGuCPz9faoEGyOqxRk07fYR6cWgHZVaf+aNZg7YpsKxU2vlAtYlLDJAeqSfdq9Guys6IFFRqpk/aq0S7jZdHU7Vdxi72YHTIMmt0NijTxMiSZQQ1Xg1nf9dv3dttftNMmWQMHQlSo4qsiJJlOlbm4Xh3Xx7mNA0BbClil7GnxJIhT9be8E4AZvSGA1AJyUXU2z2yLE3v0Y/De+UVuedeb27hSUoMjvQ3en83n29qQsYpknFySBhbDFiWW1j4IQnnJ/ej9yfjL6bXJ89X1eKURHISsxKt+v1oZS2aGoKcIpbmCOCER4NBdATihAhjqIDa3f/kn/GbzJXeF/f1BfYMbQDrirnCVShVARRFFCjrmyuHRYrlOMpWIyOt2RRsOTETXZhFV3LIRgUB0x2zOOX1ORwJ1QqghQhRkiFoo275e5b71gIbhQIpPE4/W2z9Znu9qfS9g6/2ugOxJXNLPswOzDlOhhOSI4VrYOEjltKiZHKonwkrzU6W1kaxAItdak2DDFxZko4vG2Htl/BrckcSpt/by4nufYO8JWiGqFO3sVkd2nT3WJVStVrx7OzYOtSsPX5Qb/6c3nOdmyVMIMEF1bG3xA4AADO7SnYz1Ho5GNegYc5rjcEIIIPIMMhilr0JMcIriwMDAUCVhIUaxCv3IdhXHbk2z/cKCgUFmAgm/UF5Jx+gPKycQsgJUdEP7co5kmShMPSEJ+6vkCfPx3p/++LbbzTH52sVjhJzeSZFrMm01mdxFrrsVouxQGIJEcQOAxqIA3GKgAEUMIQO+LhN3uj8cxbgl/b1/HZpbpkFy4WDQk2lgXYrl83AdrxtV32W0YOAbVpFNcLWR2wADnCMSkSCnv0nspQf31aZ6IQAgE60RSGGUCA5zl+dPTdLRadKqeam4NIo8ZDpsOvu9j6XwjJA25Znd241efmIsxmomMIWzHRKxeagpV1OOXM17IyIBEqKlCGgBUtn8ia2ooRpbfrxC7gcbGDASJGiRJWTeq8wLU3GkWo4HcHq7q12ej22HtvNnLlVI2fHGngo1VKhC5TIyhoxalApkNSxLNmB7diPggVCAqFznZGbMiUTmcoGYNRGAYSbkHiM8F5VOTrphrV5lXnvO/msWd70t5msDHnIAB5X3V/Q4/lSrpiHiVQGImRL7+orGXmSIyEpkZDnif218MvL6z/U+6vxB3RrslcYunTJaAYCxFoZa/6sI2ep1EpgVWuWcEZhjXKKCEScjgBFAQBMAQAABPY7d+Fl/DU6e/m769lpUygqykUBQKzTZqtyu4JdazA3Ih44uqKMV/24SxYb3BE9E1CP5oc9hzxzB9gIihUAARASBKhEYjhha9QJiFgmbdzGzkDjbtEmJkIldQc0wLBV7ot0vjuzXtqtd32YTKdQU3B5kNY21MXOIOVMCDWggVLETObgQp9qX6JMPeO0aTuvbj6rRUrrdQtKC+mm2SjYNJ0fX63pLLtTluVoe8WJdgVBYakf3F6jZLFt4a7bTZcYLYgtlSAFIrE+lG55nSkbrz/GsdSS5rTVJS+a9NW7e92cGRsUsZYNI3zTyDgAzAjYMIYd/cHk5fb6KQeXYj+lRIuCIEAjp/KLyg8o9McYdkVWgUtJucJdvUvhKXeSHIESwMnX1a/X7q8f3/5v6Rt/9ZWzlciljg0ZhZyWsUkk0r4VixmEjAJILEXToEqIk3YrEAcAKGAACgMESFQASCCBQ7we3+2+A58kj+t6KCIJXL6N943Z0j4korKpiUUyq4KwW1jcHqzxiVcS6Huap8+kr/Z5QHGCFSsAGK1UCGoFhGq8z6kfn8llpjkKTKGHAWxnr9ISnXMNG+XluEZ7qD/UQ7Coh1/ys9u4a5GmygKZpTgNZsd2MRohgTTrg6uBNAor0UC0S2O3z93afriTTj/54uSzu3eBbHS0SdKYYiXK2/595vlF9+u8o6YAubPIMmVjLZLjHbveDTnePVbdtTs7Dei+C7D2+AqqoEs0Sp7pIjlTvg67/98DT+5LH3zrVS6xNNjYZj/ttoefuvPctBgKALDAUKRDg0cNUDGeYQ//z142911+vf/8B/qoHR9XzcjqUI4tx9HAY/qp/nLnr5En/UmucnQuQ3uir2OPUFJSn56ERAS24OG9fkDOwn8UfsO/PPGDR8YwhQPMpbmUNvt+IRjMHj6BlaAjBQJhgsknSJOOCEQE/q+BKZREgQQFBBCkhHUH3of/+fOvy98+P7E/nvZpr795+Hq3fZ9otFUyWlpaLCwQZva17Ryyhmeq7QqlRs2rS9/MxptrMSNaUFTaKkUgFQsACK5LKw3SEiqBm47VsldTLMQpTuuj/kwzUjndbH15iG81eQ2UQuPEPgyTiPSxjZYoohHdCkTk9XQ3tyEVRCHFbGzilgwSGuhkONOW7aePbysrE40pWrEKoGDXvfOn//HvP11/++1XOwtDjCKbojbEoXaHEKKwp/3gEB9k6tmsXWwhIboagwGk2oYXdr6O7keXbZU6BhHVy3iNAkjxkmHx0qUSFBDAKIyJYWfBnQBsFNCsh95//3P88Sf+1f/8x89//oVePnBgBVziSPfgQ3KQ/P/60vPV+DFeQEgs0Xxs6Qvz1HoWW/oSHj6SlY2k5iyZLOn1c2X/6Ob//jj+/J/ip/+GUjdaAGQEuebVEMcZGz9e4IGgiMiaNIByuokmBQ5ERLMEwEKwEFOygEqiqQINWnTRggFqXodw2/dvPHNtfYLnz/UL+/0/c73f26/+d2HbrLIWw7EdbLsMEIdOuTxHL7SJWWjFtZVPHpdswoElAFpBiUIjpCYLa6ogilVJGE/srrbH9Dd5IkQhNMZTIe1uQU1K0sBu2xekv7KaVZc92UsCus/+LqNgwpiu7Zq22+vQq/YeRDLFRZYip02HOBQ3lsZyUEaXmkQSoUBCNCILAB4CyquXy5crKV1J0QkUANAaosiVa7stW1mgaxMo2wyao1qKtCEnqVffyo2BKHTGIbTYCSsyua/H6/5rdKfridOcKnJ431T7Pk/r09rJ+7f8ZQFnp49SFMEhpjw8zFjYMpumJYBZgIpMFHheoqdTbNSHTPM46S7JgakYKkoSQZL54YOvN9w5P238X91xQdkoa4//zMcXjy84tM8oq7yEUY4FgRLSverSu63l6Nx0X0RkjUWe1p6ZmyiO35VSCrn1jdRuIlqlnbD0aeAADcQBjJSIpQR2QkQc2S0xfvet9vBef/3//GP7W/u7/xbHNy+2P/rbX/vhrcWePFUMR03AErjsBRUECzhsRRcQXU/aC46s9OH3S6sSOLWLU4d2y5+ZqFsFpiIoJRglMTVB1rhckRV0L4fRemE4pjXuoRmiNTx9VRRL6zALGTnLFWVT2/D7V6AJ7sMVulWIfDwKPbJrep4VYGgLrvv+2T4BdLqkDWJKE2yRnlxe5ff5b7+Z2/c0LksZIQCyAGBAdNIijhkCjZOnKoGiRYvWouRyWUGW5VRwiiA0GKh0xIxszQxx5BGvkFXtmjn2jFFZ5YaEl+21Y/2SP6ifdy/1PDx6Zj1oFklW/vY6xtKcUlxbV4MEgKoyqOgUwMjUAEZ2WZB3RJctSd5T3lgHW4Tr1WEJk0B6Zb5Xj/e08ylERmFm2VDpXptl1Mj4iFDeKEfCSg5czuoatQY5IKUZFSiioEzjzWJsPcanj88igPjWkQXKJwBxALfoARwjpDkFIfsIRLB0c6oOoEoMzc3bm377auZk3y51mdx82TNet49OR5yCpmiwivHiIBGWAIAzDgxdiuQZRGgTlrHMniSzXaSmjl+eXX+lSkcpMRpkDEVvQhqD17hpQ6qNIbnk0NE/QX9XQfn55lP6DJwpdblDqJ3rXjVbnY+5f2w7plvxZXpto9CcTgmBJT7B/OXQXg5lE86dR1BCq0XDUZIUYpaW5w498+3fyr51lDhzKJEcADQoASwZti3eigctvPjluKKKFp0goK2yo8xqVZJsECiSMkwOpiKiQmGNVWnMMat4TUprk42763Ym/NF6fgVNZbv3aDDt0YRlYCxNWwcwrvE1croWwIAgWMXCBkaGwgQAAKsIjSTlCpu2Pc+vHbt1NCnD3mWeqkDIstwztNgPWh4yxEl6rVbj277ZrwiHUe/kFQ42MjpzRzCj9HApSdWQueAFDwhjQYnDCNv07EFnkbKY2JfvwVUcxxiICBBLAxaiFVMKfDriBgh2rlS3IE0FCt45qRMuG2lf9b6m6xpP1J57u//uT42p9bdbRnAVE8uaACJRKifwBJ5ILcXyrFbYMlSotZqNwMmXbsDvMtNCCoAaQgIIUrEwXt992Mx2se+yy1SW9bJYzjQ/43SX+bOnUcuB+e2iW1P34SP9Xd1L9jdqHT6obSnZUBwdtvWwh787rDbXcUuK4bHKSSpWiUGqpyY2m87h3q87807ce+YagqSMkicFjZiawq2kt29dE5GT9NK10ytawCBAAQqs4qyUQNCEGpZZNQGJSFCGIEvkmECM7nuXX12nK0NbDMOvu9/e2Xlk8Mhjb6aZVpgWCkNII1qk9oUorGMZYGJmTYmtzQpUgLUBACCQVLswrXcc2wtdimqSVBajjqwr2Bo41P1F8i39GUSu8Sn5yrN99jfi8T4a0UNeyMFDCA2a3b18U20OcYLSZBXTLEU+mzY2A1YrV2uF8Xxgp8A4vg2X03ETK0vEnAgUCMRAOgGImzhIUqSkBc5BS4lRsMNYwaexghcyibV2yzR1td2i9q5/9WxTn0qnG8Ih2vCMUSCSAokpsPIY5LgYTrKNg4UqwBJerstPvDN8LlWFjKlZUrIe2l/+v/vPL/YzhUoaYDWYNVGuTkqvjaJKOVyDEk1BYwgjc4ElcL8CKLg0O4LN4+mL41ZBrhEU6bZxawgZTt2HULRTMaqJQgOYxS/9OSU+0svWVsiUEVCSNCI50qPpevkd9tkyunr8Qr48PxQmChEBkMC0RGCliCxZRGKWcGElKzZwnI7ihftibbuGC7QW2Qg0NVm6lU4VlDrtksOS7REAAJRGmWNHw6nAn6zA8M0QAACrKFFVremO0hPRFIciACoLhdImh+n2F/X83EFZ5aeBn0Z+HPnJ+KypfTx58NiB8iqMhMHSV14f1uPUq9u4WoRiwDLhsWhVCywG9uz3kQbCcJw10iCL03G5dTS7ABAOIHAgTjkKIEICV+XWwNXALQkpN0GJJ9Y0KvZYaSVAGNSbdtTU5yPT01vd1FC923hgSTNWcdCiv/z7nPkYoDbaj7BIG2RJn3crXbNCmlzkg77prNwAxZo7gFtgCHvyy83VUC3IZppHoT72e3977xYjA7MjUoeavRxy+SFWISoCDFHFoBtx1qaiYUUS/OF22+kx9WJSWX7sfrIchqhS08WQpqpni8Za1eFR81zfU5LkLIkMFEZTEQXYyx8O389VSlY2XFrrl8qFqhVgsp2NpZXIxixWQ9loA0qGLzEktHB76uKUWcQiUOWSC07JiSKbscRKsbAIHSe3o4u0R4IRQFBc3EASqGD8tCaVLKoCo20pwwAA4GVCFjwJp47dAiAJBCW9ZFi4xHZmygPy3b3OB0CdnVMG7Re1QWYb0GhYuXAkqTkfykfT/PfFlShN0RcYDIzwMKqCaKUG9SWD6WlabmktdjlOlbdv9ysRwgAQOA4gJWkAoIlI0QJQJsQJVXYcSBqsNCoWVsUErui0jZw2mUu0LVGtmjNiNc9M6vPd6mODv/wHMVPvXTqxya7ADvoKtU7P29mg6NEdGMCm6w++UplRqkMqEACN4K+FAUkwZgE5HDofwC373fB99oqoFnVTfFmbzOnY/ifmiW6ZfoSZ8HI3n//481yCQx3gej2e/i+6uVUKtN5W9Y1CYAaPWJeJyvXuU04WeQquOHPgul5Mjj6RIZhJq1BQoAouz9LMiQd7E3YGF+IqEgBUIpRTq3VOnPXaGGVkTXtt3t7j8mhddHWezu9UFxrzMZ3VFje0ARDjXnF1rrWDFbasZFTSh1AAphUg+RIQBMwg9LVGMIMMmCUJNwi8WVh0hKYsB9veUgk7HAKK/UrlU/fgNZtPN7553p1va78x6dGOda62AABt+kWPk0CCyesiL33/b3FpRdDSQKCCJCCfIQ/k1Xj1pojA1GLxVSMfuC3oq6/6JBcbERgHZudyCQ2s8S0sN6kACKgZHaedm+OIKt0ISystsgBhg0LgwkXpKHCcqjTRG/es4antxuuNc1q1ewWJpMx8M7Bb0IQSKjvdbk+4yeC3vpzRjzCVQU4iIBclwRcSPvg2sJayigA8bP8nXqlB8yXzX/bLPQj1mL6BPbiLV2CONssYxlCBFlr25wBqSIAy5PFH7Q94m+RIG9sF+cPkzK4vCz0EbTYUFI28BRXbjUulSUShwUmRLBBgsPb84i+fL+NjzDi5U/8Qh1GHVlqhIiTgjWxU06R5O+Mi7vng6w9/8LX7532jWKNORTZV5epAG90AQAHcGhx3vtWIXaiprVAsrsKFJYudUBHSLkEAmC1sZYvBekcZLQwANIgZFqCCijzktTmlwPuZcJlvyqEp1oBz0lVx9lUrt18P56ujwzbfpaT2FcCJUeJu6HrYh9KHZl8HDhllBL5ta7645LPfRpia0irjWse6ls5U7hTtqLDzfkRxhEDK7zpS7zeOKr7unvDTApBoxK1vxxIORMQmjnNaKxgOs3DacZJvypGqSMVKlvBYKxA24VKGrcgmDORikwxyZPHcOGcbThnOeMZJW6UxyFxnFbLSXDVGpmxDrDRuG/y/i9ekdwjq6GQMI7Bw5bnk3TcLqUZcsOZkX5E9Rc9rgAt+fqd5t1JZxIyaLJeCHKKP2+QJ/WK9BAUAG0/DkMyyINl1HMdtHuePV8NnbRu4sa3bNmRRC9SmKabCtRBQUMCMmMyrUs4KSEDHE+8al5XT2jFp06EbXuwyAIsFVAOCQhJpJQypIUmSzk95/NqztDaQl3L16l30AF0AnkWb7w7NYDSttfR7p4HdrhzQ03YPyy7ZkWIDWGvCMj7WsqEgMxBCgAiN4rgUc8lq86QrMw68+HLw5uQtJUvAyOLazvGPnnh04e1Dy/bVlR/08gUxBXGChLadpstl90c+Gg6PXv2YEkJqMhJ3wpYV/W/flo///2vep7+vioglIEBqXi6UWq0jscakE50Fe9u3LUS+IqNauZwywIN9Kjc4ENGcWKrK7ZJgIUyHvSth7fhLKKUbtJIaqdyKrdGAUiOBzqYIr/3748aXrEgTWq8Nk+mJ9jnr6V6Z1EcT+h5F+QQCNixZvk57Wpe5+Om0IKmbOXpR5WzzJWLCw/JBpkjfJ9pedJrSAlNvmgoZKgoK0BqWLFWjpKjlin7Lonz67x7/j1r/o31WxwCoQ6A1oEQVUgqIJPJMqKkfH/plBqUEx2Ct460AQQVgMAoaA4FomqlRkgupEPESUG0BSIOdfIkz3p31r15+73Ixhull1tKj0bHaEu6ynmKAYEha9Fni0p4YisOI/QXUeLDVu81GhoyBAUa8AWDArAwCwFrMBqwgxWFuhp2jpH67/vplcDyIhTQTP5C3K/40HLx+v370YX5OrSrKsGSEly1E7RZm3q5+9QwCXTF0EkCjklxE1RbaY/7Pbfz7p96WdyrTnwUHyzCcDru6UMoaSUfUka0V76XSu8d9r7oxU+/1KB0LqxYIxE0EUolGawHGAWYTd4ehiciyJdVOEhABgBEScLhKzAiLSe+GW+y77B5Wmnrq0tmzxdbv3Avu2/O/zNEtu2u89Rp6JfnSzsumS8StZoMBaiJhUoUZ8GETZnsZrLKZlazfeomAm4xNuYQ4thpmCwFEqu6xgwv43Z7EzW1OP+GZM/PBCH0YuQIjVIYqAQWVvRZJ4xcqUxg50TlPAESAUqDJUn6TJCEESqrfiWD34tZbIaRSQ6o0ydN0q7+eC1fPXF2wRVVhhOFQ1BLggZsGUZwciAIDG+LFu+1TIwuCQFw5MVBo5yw0ACAbAFQsge0TEMMgGE9jgRSQZRGEEMqjWs34Vdx59bdSi0XLUN7PtE/Aq/72xaNPf/fVl9PZie3PtcWorCqhReoJIUI/+7OGIwAAjSble53+m3I6o7x/v59Ny6g0Pf2dKB0agzyQpVmklKXeYMWmLuF0rkuqOjntVgTNQrAUiLhB0qoGSQIQSAsLGBOJQFe3Y5HAiCHhOwEYy9I0Qc5+96EkKmVkHxZRx6TCqdS7eHTdU19pfHX85WP1q2vONNVZBrrQmEcxwRbFIXHdZO/aMjwGTCaq6Ufbm+z5cQlm1Gf3HYUFkGYFXAQjMUgNMMmlYnhjKGvtPLOkgO12Xpr1bZmygEopCkLAVnL02uO5oa1mb6hDgKMSDZxUX69uYmqYPLC9dDd6jcd7nboJlPgTOaneKdwu3XsqzCwyHsnYOFBpi6AwBAWAAOxx76g3UBReU9yGKoyGoTRjid0Sxr46tCyCTBYQABKofcJmBUCOEtgAAUTYAYAdObRGt6z53uXPYWEXWmTKO1fePrD4f4vN53uaBvr5Bavb93l6IQoGGC2FcJBLGDsbGVJTaWN21Squfc77TzvzpQxrCYQ4vS1pqpdtu2pQbG4DbuFck1qcXRTA1l7cCTlvZuTb1n2zBEQ0iTHVCm1bqoBmgbb0Wuem0ZxWWvCJqKrCRtJMwdppO6YlA2AQTaTd87Be9guUjB5A7Mh4n6rQNpMwc/XzP/X5ex77oqkGCVthBzOJKRaCYhPjFn2zfUNfbRg0aAYla8gmE+gJmGXntCOKGtBDW9YqAGIYSbWBTxeUm2Xy2WUOPK3OdVwirmC0OSnIKje6ZA4aEsX6D7dRgrk2ACoClEDhbSl9ll3nzi9rm0JdwTK7pBtW30yvOfnnPy7YLpRclkyabU2lvqkXcqE3UQ0LpbSjJWGs+2yQBHdVvsOm2ESUigmCgX3EaZKTYQ2yC0tZS9kMkN0TMI2BFMu0kRK+GVoAoM8wnpv3yav5ddTtfeg8YDXMkfTRhsGd3Xu7WTBlyVaCbXVOWLoNJcCqQuEEEUoJIejChlSr2tf77KhfjVE7WqctsurkE65ee5cMSwzz6VMaH4ge3kvVGgBy3R4CuUhpIUwRiGhptPRIM4BmTcumal/bYMo9hAYlqDRS1UjDMFqGYdUIWuJYUHNcNm1MeILaMqbD9laZwqEu4iWzwli6MjyfKYhRueSjsEVCEgyjjN9nuOdOIqAJc2xJhbRhUZgY9rKUgDSuLGOLrtoHnSM6DxT2lVe3ce0UG+0CNqjDGlNjlk1x1MDSAC3cZRVmJm7GxdpWuJv1v/77R9GN64cU1gQKMmj46t0xQtITriEajVm4pkbf709//fVP/+5vv+u6lpvLOB434kwZPCoHH9Wql7gAIjHaos6i6LnuRdnhh/iAUgPDp2+NtsUGjnO7Ql4A9meFAGbDPR9ACAIRADWtDSADAaFQKMjYSzqK2Wr7pa+tzr8r4ocdG1fy03v9R98U2Nkbd2W8SQMwoQqrDaUbjS210lRCs6DNskKnYTV9vU5f6umXJlyrTY9GWWiifbuvvu09EMFGve29b/e5vu2ub10svtjlENoEzmBSwqrBJDdw10gTQ0ysAQtw8+TPrsszQaRGEZQijCpZa2llEANGVUtmZlIkzcg+EHLeKZQQfaOKz8xKEeylgIVWVyNS8ZlxaB4mqUicljIp6cVbcoTzTlIe9eyDsa4P6ynIkjSqAC5mW4zCNhXp/TAnCIPBtJZ1QGLmlLVSTIGqEZCKZTX0yWSq7ahA/dDea4WZcuye3/mZpUBSJMcjNCOpFjLj6o15frz2n2SdY01QlzJd1Rdfu3aX2BBCooN1wL7yEqmi1PDqq1ab1opbEa/YqmXTbF5O6dvypXFTaxa0CQIV3CUcyMqhhq1EEG6BATSLwJgBgADQIMOP9NAHPWnSWgeve+fVn9az9RPjPcYn7+289fI7/Xg7U1A5PYj0yiuLl/cru721OOH2/v3X3B9r69A6aktLLSi/8vK55/c7/RLbTMVpFpg2FAM8m5d3Xluu3nrT+mF1aV1nq2thDFVRfNdiR5hpEgNgCi1HgWAkt3ArIYsxtHbgFkkKk5CScGZd26UtiU2xdWC2inA2SxGIUNoBZPStch26+jjOOkVwSKL5OKSTCAkTwFQcKOEM+kmhFTmhvVJulEop0HUobk080TMoPuraAZQUJiTDEtMmil7lMWxby6uJXLGhCLgtebEpUwUSc7RS2yIOdNsu91gghMNBVZDgPn4UHHyMZMWXDLu87Ghk3LEvN+krm70rkXbrCVhNqw2BNOvnfWDSpYxQE8MrJQzyOsE0lEpVPEswqYmyZ1cmJuMV3sGXOBhfREvQoYcLDk4CSxk7zvKYUpF4AIOBGFgQEyVdZCHLmqlpvoxtZqorwwYdm/dz541+9+ufK1/+3B3r9xt9WmpWGfJPtJykO19u4w2PSXXdaU8+//l7/Gf+uBeV0HVaq4663b7sj83itFnoiBjOPHlRWtWMl3Pdnau1ZfXqMtKnHOJzsSxM99HYKa9TYwAYgNgkjZJbiJaWgE8N1nALdViNHbHHYiOsFUflbnYvabupgmKpJps6m6JypsbLZZmSJ5qYviRdPVFbtFartNzaJdJRhmdSjRoOHlYgmoQmhFzH9H3r6kUcyoim8M10r72ee78l2rFNMw+BeccO7JNbYm5p3XuFuWqfPRAaaFqn+q59rZeJUhQJCJGMBoJCZbqtjnE1h3XmTbuHa8/Itp9kl+x+iOETuMbKcUniYpUZBz/pGacNZw09UaO2mqpE0mmaIetEJG5KaKa8M9lGJ642r2MjQmpVZQ0zzTyZVbeJCNRsxaYsXbUiMIBlsmoYSAAgYEQCg3chvGuwUAADCgB83rtU/2/C1G3DdJe6f+prDScDca7++kFveP3g0qdK5UdG7d4VY2D1zZUrjN+4Hj22y+mgUYMCphIJduR3Ofsc7T3suKhBkeVQxZ7r9i1L9fYuttISABCwcQoLCXlz2sf3610zGWEAIAFMEljjIJoKJmNsbJQ1M1vZxLcqYcGgVBrFrEqvlZximwiaBa0OAGEaxvNotwRhz2JFvc1eaxf0JPG0xiaZnNgHzU6pojRVdpJ1XYvuQx+55ok0DFDb4EMJuvVtnttaSXw5lrqpOLvu6+7FP7LRRnW++Tn4W77/4olZYDPeZDgIW11BNiFA3eYAoGwIlSIL1IFVkmOt7ZbzasucHT3+50N2jz2hGflcu+M6/EpuNOl8nRP34HhSZ3hsb3apqY7aSBpjqtwNiFqLhOKU+oyN7cU0ashVrbZhhTQkOBOpbQUjK8KmUFnuxraCBgSwQWOAlIEAA4ARBFNYVACMOAHAgADYg8AqLIDQqKVGI6SdKttTj/PlxfZNx39dni+9q3wYhqWKs4yovOK4Zd46PXM5Y0foqqYNsAwDwlUOSmRbiS8UpKLKkurkxue7u1No3a1LZYUWkAFEQayoLRHXiNyzLwEAsHzgTbSmpZRbBMNKFapic0TGnnvez3apIQhEUDBarZ26ubkOhgE12lu7IEedLRvSKM2Wob3UhG49hgPbYk62lOZ1bJLMlLzb3CMldkKPxIsqgCkpIQA19Oh6d6EyfKBHMOsdYJu2o4LFYACQ/T/uM0UiorstNxc5j4AQnvbdnrobId/k479LJKoIzEAogRJgQBgYaXZDlcz3PtVtVZ1bfvHq+u9OYTQUrol2R1KdPPpllsBUP4jaThzgUYu2KuE2psFEVtnQKklYBJhaNi7NBSWPNjEKrZRSjwEto93qLpJASLaubRWpDYAlNrWpX/3mgQEzseGVAAwqEQQGihOAhbWbXb0ZIAJuYZED4YJVVmh3zlnr6i+rWvQH3viZP/2GUz4/s7JGW/st2lXs4Wz6khy1zv6ZXr1+x7H7A+v4pWwa1nZWz0Z23xqcvRm5bjeFlVazXi9v69d1bd0J7LqttLt1XcIWj0ahVgxUDkPNqKWACBRwTT3GA7h1BmSRZbA9W7UBSsrpPa3dVgMCDoMo56qRu02mZmaGslphUDkXU6JRUPFQYmdTiIuti82EdtuzrJ8YbIRbtV9iTNoDzlHnrAqxqQ25XI3XTWLnVRmrLrQIR6ZPHi0bnILs0JKd0XpMy4oo0OqwAX1u6dabmb5cyWfWtu2T+jXP3/xGCWLNdByZxB1CECZEKCVGs+P25vgGQCQMnrr6LfLto4RD59nhRVgGJDty155lzhWLCgWqJU8yN1VBNOFtukYyNQ6ZAc9qUfJNt2g+UwxUQDwUCLDaRtmX7yZQBBIAyHLNwNCADcAAiIGhN0BMRU0hoFWGxgImVrshZggFgS3RznHbQ55N61O32tbbfXbqNVe5GnaN2/+lyfV987Z3tKvb5OYw3p3lQ+7k/BtTUp8tTqcHd5V1Nq5d0GDnzC437H5KbV40S9iKgp7Dnu/6/l3ca/FlI8v9SLtFLUkLGA11ggBUjkKEDRwSOlOSMZgQKYFOAREBiTZwkDZQJIUccVzmpGuj3DGduTsGD1aFs5JFJBGIhJGGMtDT9A4UsVDN4J0qgeikofs2fQe34U7zzuF02i6MDPAGWExfvtO3oR6d6ER3YKuQYrRn6pJTN03J0lnStKbgEGuAFKbsPL6t74eAeB16N2FX8QuZNg3hIHLMBMEPNcuASLkdTmo4Yb/J5+fxc0eCDGT41OHFGXHvox+XjiI8uOfeUcBzYXEUXt0BTHHkTRPOsErXnA5HH1mcl3qDkolySbJFf//3n/7oyyecBnYREFtGGic72pUSZACy1AZSBsAYAAivjNjFAKskyFSxKKjZIgAsYjEgAhCq4qwzhX8/cnH17L2xZn3+19+WWXXovL1/qM+fbGy+PtbOVV/x7jtHdHmru1cYv9NqmnXr4vSvlj64troaW9tvmu1qk4crPUlVTeFn+8A6X+bDrCpmXW19/o5cWQJLFJt0gmFBaqtcBwqLbMEq3ayZBIC0GLTBNjIUACiLMpjRcFYUwBoeclo71g653FmzxYCSsTX9KIOyhKYgFK3CApi63dCEoLVXfrT5RDo1pXAhdNDsHtBCLNI8YRhCNZmXJnlmzqmOwneWh9aHJlD4rJd2DMZMa1JFJ22UEPrmQeZttoYfmjPltiygXyZ0WnaTN4JsBenJy62GMIThg3AUEKzCoNkmxvHoqbWZMmo7DhMEfX5oQH68izeMTB6/XCVu4CKdrE42Y0AwUXdzGM34SrSm85R5swEJQwOxoPlf7V/ia/fHc+l1ftbncrGc/TILDTIkECp140mhIRyiNvg0YISbGFgJIB2tRTJZMETBWIAyCltsYdnwrr/qHQwLHvnxf7z4/nwJq+jkA2qH6lmePyjb8PxoaKwduP2gwpAmdZIWBNzuhG/bv7jQ/pgNerpztKxNak1bWNKCtJBi1vND43fvs4eWFuyt9D5uZSMbJ61r5EahsAagxlmMmxVqpWQmiAEmAi1dMRjPYIgC6IZ3t3eeTU0mgilX+b6ylFynXDYQydjobSLlkIgAk17XRtbms/QAOq1jfKjZFL67GdUP1xBrsMLNnIpJt4MOpaGg57IxQEsRtiCXstxq9pWoZ2c6lt2nU7cxpNUOWrZwi0v1Br2f15DfAP5Aj1M2cZje5v7/3r+/H5Z1XFlesS+lvypX7H+h37cKiM2EFrtceKKf1eWlH+Z3SuHkbnss2vtPb3kOzOr2Cdq4UTGHDIPW32jiFjQcjtrYoaEKFbCn0oKYaAOpIhEF8RX8DzOLvQ/2gq9POKVD1ayjHndxcJQlZW4NI7FSViEzFTGbagCAoAFYgw1jJCqBYLzsAJzAFPwQJwwTpeA29/0Df7n+4u8rh8yVrfD6dbwXE2j5rd81J8zlnXsfuOc7yuV/ah6SjlDnKrKFItxhu7CRcreRe9cPH0f5STQnCznRyYjOjLQQhvZ8WJrLyelRrE0XP1WqcCZvxVAZwJgVM0c3Qu5NlbKIlczUlAIDmfU8W2RAIeONnWG9+mp3MQiUlBhy6+tuXZ/T0hBpiGRBGmQsN6owQDFYhNtWpQ3vNbXW0wrbiD6+tJiJBsc1imxt5IZTuxq0o1DvaQgVsyhFez6cot3ykD7aWd6AvONnQM8mIQKrYt99HzYJgZr96U67nGVuS8eqJoWEnvSr0O3htk2YI+eO3i6HkjPnj3Yzfp6sJjVvp/eUbpbbmTuNp3m5h99+hhw7+lneC9GaETSjQROtEdAlhfFWyihqrENdmCUjdU3GAFI5CEWgjYd7ztfZ7ffXuWfTJXA6z34uTuZmk+Wuu4kdp9shAI6FgFlgZBgBjGDNFlKIyCmEOQLLzNEaTjs8KvEDomSBWSVz/bL+ev7m9WcfhbMid8vaduWGp2pOyuD1k9abJxfbp2SPBUeimxoKqgUktUP0RTt5ubrt9XsrPLuaf2CQ0Y+hlyczwopQEaF93ubi8lFnWPtZt2pWdbt/y78nMl28teEw8B0ATIYRKhKqvcVITDUvgenNUXZ+eCTPvrV5ArBzX68tKQYdQtm5Diq+borcGHYxQBAAADTBUIkoaQk94dpZi7vdPlwPqQ/HJMVK7/lyqszXWabGYFvBuPENxWG9uwTg47jECKXUvtC9bJ6VTo3DB+6DnTLGRbKl4nSxLJVxkscX9/3FsUmnnBl6Kryyhwmn/2F7teR6wS24D+ZJ9+dP8fXRc859TuE026ZN0PCkdmc1zE8Lg1rvJ7cCPKw8dN6nnrhGhjQkbFKj07hyEhVfeVnhpb2ZO0oVdaVWKhvMgIXTUjgRHe9uz5/dM3Nduy09Idu8Ojul2yS3jllQJq01QQDhJggqoGIJgKxZA1BJAOApLZUkU5aWAEiWkCICVo0pvAGHnQ3twfEvfUPrP/2kOs1NLWOL363UV9CP8ryOvMakPidsTUfFpshJBk1pJFqtRqkdF/yrnw/3z/V1zg+LnWWnWEEtagMNlhTVgzzTpMBFQ7IVi+8w13Y2KTYsdjHX1yZG0zqObADrtAsqJFwyAACwUiAGi3FBlNfVb/eHXNtx+mTDtCryvKdC2fUEbESoDANGTMgYsglL2zaO73x3RhsTipabY0rbaYmtAqKEKlklmYzbQxmQSXMT7sCoapjUGI6aAYqwwF7YuZd7hfcNbEnf3mVv2tAm5ZvJPah1k+Ed82L71WlMU3DpNlHFldcR6Wo4qen+8kvn28WTmRPXIz6bLkkOaHN34+eZCebHaLMLtx7Z5PyV2fuULPEoG2poE4sdtSQlLKGDCyte5q7M2XzuDRQOIcqmd2m71DYE0bSNNOJK0t5rWtdN6QD/In6tKt2GimCYAqDNIGAvzGDM0qmYkdpmawFrRBwAQMbmRHWhQEpCAiCYG1SgSm8413aE3Nsm17r/7es3zj21tRvfbhYFUoGIGC3q6vJKtyYxFJvIkGta9LDleOnrSlpNLo5xeBW7M5onm7IRaFKNBYVtS3czYr60O2m5FIgXA3+PD92MB4HYm23PvlqrAiJ5p4FgFkQdKSUwArg4FGQrgViAqjXWgz85d13d1WUJ5JX4zOm8rF4gaEApBSMWVjaZwEgyjR6ba3euS9vOwGOCpXypy6JamMRMEvTcEyZAAd1Nl+ukVXImnpGSPhouSMFeJaJEZddutt/veO0pauJL4d/fX31xdX7bwwJ1il97llmaEo1Q6KaT0neaf86X4/DH5qw/zJ2jl+CQLyrBmc7l8tU5Na6EMd5EdWqa7By6I06UGzKjbQhSNLCaQRJZUhfWpGzNGYfRzZDWoXWrCWxcFqlgOssGoJib1s7bPp3JDNqB2T84q+/mgOkQDDQADGJAL5AsWJW2VRgIjLFm8F8ypX8DBCVKGLVD9nbdQKooe82t5giuloNyvU3+6zeNVGCL/LCYaZnWTMuIm9vVjee2vpH5qPaPxkjNsMfX7e3dvz3U/8ud9dxrexOmwDUlR0YIlJsSlEVpq5oTFCdajnwQ4EvhT+vifI/x1DAgwJC0s7jqNUavkHgo2hOS4rg6WpkSi2MAkMyxHutYcz6dfnMAW6D8GS2lXmiBcsgaMlJYYRxCI4txDBg0LncJBDlq7HaC00JNiIJON36TMAE+cEM6F08EG921DgukXdeqD9vFK8+tinzPvEpXyAveifYkhlqXn/8duaZcQB4YUqjYjEY4aaQt2eQYmGsq/bVxmPuWTkc8RB+0kQnHxs36ndYuuSa4DAgzTaklTlFXctEg1jEcu1jdJtJpVW2W8Up1khml9doYSyQ2vHabKQw4VMIK9b0xggzMljmVPW6GmbZp1KBaOmIEAWAYJDYYxgBAAYRiS0LApoSWmybDS0FYU5r9GCNBwXHW2bVzj3ercegzVzf7ZcxO6QA552i/m24XpXAuokAEhc60OQof7dy17msLd6TZyfpBrNOSXp1ZevSqLHh3rc77XPOZoIISmLrO2OgWywSMhVjDKKUztoyzfhxjZmeXWTMbmsjYrq3dQKaB482BXYsGarEAYgGqAA7QYD3qPvsry5P6Bg1aAqSzes0Gs1YCJAu2kG2ajDoSKl5GrFlUKigU0Wwr9CTNnJjmdSNtgkCFR+U+qrJIOhtdRmZkNGbr1JRhHj7ApKmvgxp3j+oIajoDDzHHoQG+7xG+yZpyN+6EQ7m9fc6uuPJgGctuD8x+en1irZr80d+TZ4jJpXpnbdId4rhlYm2X9baoZiIzuc2pgGQdJT6YKDQtuFVqmsY2mYmM23ZzvCjU2QorEgoKJsz1REgIkdvnou3JDDINlWieSGKVpQiAWYAaABhAAGBmEOJQEjBgFVucYhmsdQLMNTf83J06CkxY4AG3GnWJO3ad3usJ2205LCbhX/734//zT1Kp55NDwUtQpEaOWBTayi+dn9i+m9OF0jSwZPuXq7h++e23/3HV66KePelXK2KBqqosSlALKecYgkXUdNLbIqBQKiWZlN/+vaeVYpdUB9iQGCfKHdgcX1CuaV07VxNZiUFbISOBCl8HD451MHe1JrZSqKtyFROqJoBUWxIYAMrUZFNVSsO4wPdHA6ZfKUY0WBwwQUMaj+XhMjeWaCqZ+LJHXVwjDuZQ6FpsppncKNcw10/K4jYHSimdBxCTLnVHzV3cM87sTbpPA++YlECpkNv9/DPzXJz+t737+EtPnvOpbuT3BjvyQJdMyD1PTmdvyRBrVB3TKgWQQUvMjCqAtlOcaqTOUmyCllbAMEYsz2nLSsajcgxs3ly2UvTYkXiEQx0KA0raBICaxUzKXUAOySlrCqJZJoD9CAEQ3iPLY6gMWAwCTMlKBkR2BiBycnOU5uzseerOPbE+lpdD6/6FbxMy3C9TtZlf/PV3rf/xu8AqKgGxmiBEoSBbKNjx6131F6v8xAVR4/RE5POL964p7/6A/eNFfyNjmwkzCTOyJCoGgXYXAxqcak0lo1/AQVEarOUAd7JzNYNydnMrGeUCeomR4jgbTWmbM8t2XZZLsrUwqa1QFHjsverxmpYurXZ+UsAwo0GiXE0gZAQGa6xSYLaRUgGjANEGVB5IajumlyxwJuLDFDPM60zISrRC7eIM3ikCUCUWsFSHhVNhlUBpoZKhHYUFLFMTjOpiJFrAnd33S9596TaHzIzrlEEGgKyLj9eZwU79o+IEDRwx8BEeYPnstbNXohcQnWoS3ZWOohGOTG8BYhy4SrFAtwAxxImBxMjLdpytNScfYpuCbnSzXbdkc+/wWSkUqgVY2pgYABAEQBcQGUAbJGWYADzZVGKxiwnDVtiLihkxQshrJL/HESxrL4PTMdTP9qlLdy5w4rzf+uVipjufv8bZKSaWNUys9WZ+/RO/+d2RrS82qspajE2rAGCmVYXj26a/6qnOz+r6lebBcrz/xPjuO+1HZez+19X/887h5vppYoFXmwrRpWZRpYhFsaHJkHXWVVvZsz0cPDtu5XJpyqrn1PQSZsK2aWmWo4FjHOPcWtt1Xlkm020vxAq6m/Nub9SrKJXz1JQgqjgSteJ2AaKWoLdByzoblqcJ0mYmZHYmIaPAmqEjsqGYdb1coT9s3kCiujXLisySGszAecaTI9ihmQw1EhNk7ZIyehDKcLil/4veohJZ3WCEoipI5X4/vtznAi3Rn+L9Peawv30ic4Fn5Xnd+fadz8nW8AM3SqRK0ZdYe075YnRnw3pFggDZiCUw09LPQ05rmGx7OXYRFAhQJzFjubgz9UwhaI01bXmhDdSUKj7HZ1zVMJRkQJlG0CAAHAogEuFGBhgBGahNYW0SQwwAy7IsTqQAOJy3FYqlZbGNRSsYa+8WfCRn/q7mZX/tzvX9bevZisnF/UX9SVfCEPer3d7w+Vy/q/dVuW9wd5LpLftkC0trJEOTZRb9y3tO/Pjy+Iy5O6cHLy5d7W8fdtvpXP1Gc5Gcfay1WItTyiul3SKUylTN0tBSxwWEM0zsAM9hTyrGjPuUdbB0ozkmnX7MqwWZzx5Kx+69rmxrN9j2PpchuWxt0uT2ujGxs9UqgcLgZQBmnfekchSODVlD6M0UaWxb2C5StGoLZVEbIc2U2fbNbQQMjO9hDm4r9Qm6IUMowEBv4s3ObeC6RtvqtFhTR9ZUa9iOFKxy1f7DzgvXp+uYvU92WqVW/kFey/2ooaS/t61RDgT/a73c9+unoPbesgcrFKsGQVWhykLvk+3vM/7K01ATodhIEjE+CBCM2WoaGI6kJscxOFK9UrjsaCVlIJL39pi92ordtZZ+fmofXWszJq3U0tKJBRgAoFAxyFiOwVCUgAJYNWsBgA2B0i1sSSws2OpgELGMmyEYp3ptIJ2MjpMUJESYgSbqkJSxDz8RMSq5++MwhhKcYaAiL3r+5L+sfPf6L7x++vU9WBMe2kV7pNMDV6QbPR2mtpjDRx8Vhs4KDfUM/DSf7+7jq1/i9+6f30t4hE1vksSyOcTIaMNKpUU0AyvwWT/JmkcKyqr/XaRoY48KoXDrGBIZnYyKzUJQNE0g9SwlQbGm/rX9mwMgcTm3oijWTNWouy1px5ezFHVdWVlnKtvLpgYD0CwtmyiL0VZjaAdDYHXPrsBJyNqW5lCmLZrWgdndbm/6BeTj7AmoFmlEjZaUDtsBlcWAmBjw167P1WVLNZapyV1s/8sk3H1GFuqFcyPDng3Ihdf5vXPLTZYgLKFKpYOEbKx1Wg8LO3MZC1N+iTspBpipqLIYmYwmNV+1Zc4Y/GtOyOK0llg0vkwhcWp1FbsW+6n3w2qU0gampVcAIIjFZnULgXQoZrwR7IABGAtQJqpQgREiS9kucIiWiF4VBoEZU+EClbRESsLZMsgxxwQk6CY8OWpGTswdsVQnmhUTEpiMpOvvOqn89I9O+YfSar1OjR2aWdq1s2He4p6BYXUPvBS5kPt7wzaU59XxXc9sPVEuzNd/Mv4TgICULAJ4rMkWhRCAiSq3xTQhCgpMYYzdfKNE3CUBYWWipEh0NklPJXxC3RjQ1TrlWFd7HFeXxYAwciRgWd20qnJT1PFNKay7rptpxDBZyJiykTAQKFrFEO2C2MhAkrsb9ml6ZFlJSVuz7gShUCJoI5YpgqkKcnJsjqltSsrL5nbT0fSkFrsIZTQrp8c5NPk6d3/yuU/PP5jbyXHaCY9YsyKgJkRNyQqUZmjNe3I1LxYGCBiFwtKvYWoi3WCVkBnM+Ae28q54T2Wc1dmpERISNFyhYDk+v+y96Bv7MGIqSTOtVpQMxQbDSSmdAADhgKEQBggYuxGwLBoIUC2mvsW7vKJmzEwGYFzGVlUUEraZBOa0HTS8KUgj2rQmzSFeh/vtqJTTT0mljCQiGuJilPDK6r/c7x3uwTcOIbbqZIrVzA/IDlLt28DQoh0mUrLU1hANgrm2eNr2KobLJK/EyrwxFRsJxNZjTTL0W1Nr1doDVpexClVDYKx0DoroO5OtUFEKWGYK4wkstJZGQEAo1y2HcNOMstKBOEfMqpkbqamdKzfVruOI6KRqDpk0t6nNYrJdbZtVqhmNNk2ULDmFbTzFVUIoLlmJpdwUIbY91LslF0w9FCGjw3Kgh+yo1RhttTkdXwwruy62eCekxxA4dGmnCOn6Rmh87sWjf4iatMqVtrmiJIRll1FAAKkcucgd7FhooEaBQ3s8MT8YDSdQJjVvnaQg6UysLTwBdaMv4pA0fNFVKUcZX/r52TwbKaYOqnd1G4xxMEjxEDbdQhCAU2OdUgCwLHgQAFgAsIFbLDA+78/smmhrb2HqDdFkylXqceOuWuJJq1oXap+ETNvDzE57u70DZrfBcWrNno6OmK0pBPzq/8L8zx7lwlnu+2ePIoO3HLCxRCSMBx0y2MToOE8i1DL2OWVVp3wdY5VPl6xgwWKKYEsJKJkKljksNsJJBYTQRGrSLj2pZGpWqGydM0OJRpRrypUASptiltArYY08mN4mVxWsVckZpRgZuZ92U5eOKEdORWjlikbNAiMzBBkgCxUzaYG2e7Eh5QDBIVVEklGDtCAUqq00AUzbTlKh04bIBB5gWvNVIgNuinVuLUIHVxqDre77bb9oSKK3KuSLXPgDHMSqQKgpQBvFJS2LPTDLkMQVkSzp0/BxREesvx0jW0VGgiopURgSKKKFceF2LdZaHcMriWv08DNxzcSkrbHmnBZIm9nhLFqHMQyolJWCpAOQSeTUISzWxpgAtwYMYCQAMACaglKat7bNHuXuGglvupSpyQIlm7eMFvRj/dfv1zbuYL/1EbWExgJickuhxZTbaiRisQp2svuu7LbvWt7ffl917ppFpgzESCjiqKfDNC1HjXnIZbVyVitHrVliiDRplOpaU2JNbI3OoWvDxu+w6qhlDVwUsoabymW8RpW2AmjVUDW2wpTRMLg0KnoVZOwev89Mu4l0rjAGzk5cKTarqEaK+qZ1uUpDnZ3tKtxoymhJLE2cyaoNQWvU1FJgWw7OsQFzyqjKWhoBvA8ZcPaSKbXFYJFiO2OnW92Oeops3bKYVZdZTR7jloQ1DA3qthCqdEA6P1CHMUceJFWoKlAylr0eO+483BcfgbIIuERU1QgbNREx/8zhk00TEl1oDTpYSIOPOZlOMDn56slYwyydXgNHhQkek7C20nnTKqZAa0Z2M6u2IRUCMmWlgCcAgCDDKdhbCfA/MoYEHAKHWkQp4LEUZ7fe0vRb3e72HdLKRDiDYhYGRpV2bu5H/Zv513NdBXR3khJhnhVGUlga2qUtdF0qShR1rOyx7x8HYTSJyTHzNRLDGlrUAyr3DVKVjh52tLXY0pFAKVmNEBOoZCaBll0b2nEgfoUErJM1U4ca2iYz4533eIcdPGMWtmCCZhSOxXx9qaUiKm2klMq3facKy24iemHqMKMIQwFSV1CnjxMuAbmAuraWW2t0FgzqhlXpGW48r75kccNuZmFofkeYauf0LBWTQXh7R+/TGmbYas9GhL0mL3dJzLisy+w2uw2DGja0AjY11TEGw1b6JH4CH/rPEatqdSszNK3kUpStZcebeJMbC2uyUBZTdfmt0UrAWKjt72mu7ShrHyLDiyIh8S5PwnqoXQEbOTFoGJqjGDttXe62xTKyVcCd3czGIo7DAZmBaS0SAv/v1JBtEQAKEAYgUiCAsoYCEwaYsm+qY/PGRWgKuV6t4F32zhoC6ua86bM+c6/39cO7T2Owhxd1yDopN7+gTaNapAS1tJS6lFKT5VEaftfWJcd7mE2IDiakhBJJaQpzMiqt5V2XaNOIZnKVGVuLrXk+DMkg3DbtrFYZarWSf4lGgJprW9YHK1S7uSdXycviAsZZNgvWyp2pfvp2x2osJkqDVI1dPRHZ5CjUYiHj4wAkWXZZ2ghS3bpq1UuCilmuxErzKotmNXcZwebOMgsfjdzEGG5Xjr4mrcEqsi2Jgk5HT+/XBKaFalTbNgQFTTppONqUtiXaMUchrSPZSVI0jv7HO54be8bnkAJbeFYHduuylugxA+PsaI9c9NMm6lSpVnVH7S/xkiWTOnkSwvBk63FrMRs85uA76ub0lbOlGuUlB1knpC/DmSSZP3c1Uw0EoNWYmsyQdqMJcCqkGJRF9QgAIDYQS+sUAQjhfwpDCqMkgNVYzQBQ+BlkWz99y4+lvry0tazs7j5f9F/1z/jvu9/0/ErBD7a/wn12t98/RFvYKGCooAhzg50Q6rAGRaHRoIbI0nu8dA6KY5BwKIZSTowCIsp6g80EQzM22xp1VS0uSnTng3UHPZ24TpqgLGAN2pIDhbJYRTFISRVaDosICgVZwdwsbldxdH3NauIlq/sOMSgaFcYaryymg1ddMF9OVTpGYTNUuT6ka6VZVQlbWkkAmgyvnqZVMyQxM7uVndJrQyVZgF22YRxq1qLl9OwwsXu1PHA0m+AYHEogUFJsnaFCjtSiv+rr6srto6UFXx/sfz6eH2urLasX2ozDLK+JhtgsnOQoktLEI7JqSCfQikSPLHTBujIt/CBmNCUOrqKIS6ozydkwG9RlOpzp/Hx7R+9CZZ+2z8stxOczU0y7RzpVT+YUAycPo5XXK8nCDFPkCawpICHrYeA1EYiMUBcARQDg5nBcQAF0UQCAIlUBF0kJC4wmSIFyyPAYby/Xcm7ujM9puCfTTrEqzzpAhfRYlLUjssdL7EwLSZodpe8XE6j5Q9SqPbWbe/StNE695YOSiSK1QPA0XpIBAKFNYfG2ugZmIffXPK9MwfRt+HR8Lh/XP7l+I1P29lCs9qa3W6WDmomiUJZlcuWeXZuPULSuujDrNGHBFTNBw0JY2LBZlk9n1iy5RszMeaAhTAtcBbCQCaxVowKqsa1ZdRxtUc1osOvPEk3BEmGG1pIz6yUrPtcMGO6aozajpgq0YCK38CLb0mMIEpc+o7FyP+zZeb1uSym70uOyMMA+0vjYUThQyjg0CSwnJwi+z4D6n2RTjToxm1JhiQiZ0SIVAImQtHWus3FlPdQCM3mYQs/z/fPxQFP2OftkPg8MmKy02z3KRU2sUnrqcEeu2YqpEBgzMLTsamCgEwI+E1ApQ1rQ5gIwGLCA6qIFQBcNGqRqYSyCrqHpt9vO9fIRc7fn6MwjvruIlNpVk6/cDKulBuEFNjTNs7zncJllPxW2E4MZ/Hs4Cgz3epWwVZW4/Ko7a4xEFiJiWdYSlPOIig1dNUro9L1OGyhq8dbd4rEbULUcx5bbPbk3L2Q7uy1MvZUBoVmQlXsyk7N0Ekp2wJlrGrZT2bG1vMZSmLM3Q7eumDkVOM4sRxrG8oUIEx32qyRTLZIZiVkTu8RNltbSa1tn1P1oKZsiYBbcaGhlqxhd2TKzvXlgEreqcDMqBzGgG2SlxjBDsXzXc6bzs3bFggog9rKF17P79l7fX4kkcko9oSxcLl2Ck8qg3VvhI45AqbHAWWFMt1Clykma6Mtyd+3OKakRNXJv0uw7W0lW3uKn+XzlJkhBCVh1D1mzylTonLFPwWuWgjAJwDAmSwuBTABaF00ANHE4AAgB5IpyDoBZHICCGQKghBIB0CAgkhCH5hA26w388Z7bef+OPutsUDNClkITp5V0HdJgSd7qanecmmIpOLHtd4cwIUqyLIkXYit8bCVv+VEnu2PsVR2gkiVKCa/PW/2KC9BUp+C2Z2GlWABwD2/hlg1mCo2Hnpa8WeQ7LasIQpEtxAWHRTAGC2tcr6vUejn3ngxdM7AJOpEhuzo1HqBLo2ORrb67MXCoDmAWoyKiCAPL9aa5pBuXE5HdKhim+5zNzVJFzECNAEIREpbswzV5ll1MiR4uoyLQl4dpbjY+s94u7uW63fPuslbpwa6XhMzyHLLX8TP9MfumR69StxEyRXs6A6rBL7uFPyMrFpUwNIqK4pIuIkOo0gRm04s5XfECxIz62pvTIwl2ukuHl1XOZQkNWGBVrdvVobKALZmkFpsuDQGmBqx0BTPIogMhEAx34FVSLm2ebSY0kJWqmaWAQ05DmMpRu6sPmuPND/26588A3vN1Ix8rego4vbdBZLFWJFvWWcqUICVARKWkAjKOUEmYLFncArIWNmOqitnymS9sarUOgb5gW82IjhpY+Nx6mkdvF7ontVFsoLSWztiXcOgGGDyFsUViygrOEstURwAUa0LcuYwzmEqu2Cmy9vl8KmEK0oU6RrXCOgBhu0wD1yz83t2NwBKbFYbgiptomTPjChlzpbXYRiVrrtKzSbvVfUtTAjEbLUGCrE4ZYmBouBoX2EcFuwEq1CA6gw0/8Y7Fhds+R5rhAV1nASz0iNppdDVcsRbDp6eQUvB1SpFdg2Tc9EGu9rMQ4Qo50A0SQVXVg76OCPbtZTi9mjdqFmqQc6hDyThzdKG3aBCdkROwwMpVmtDIsEG21GxYrZahoqkgIqGGwoBllRAgAIiJALYhnEBdCJEZVnY+64f2HZ/0A5/WNdd3k2FQD4jtMmXGx8lihUlwT12it6btaI0WJNgSrEUbpuDATEu3uaQka3FTJEw8tzJTrxG8ZYkSUM2TKUzNlGc600yPNxgUhgBMLpplC47sc7hAz9JZcNQSr61SS8SmTiEotTyzRT06WdG5kgYwFjXNbKIECpQrd3THdW/zeiKn5ikEc5U7zjlXMWc6DQUWMFOpxOXyiCBolhuVbZMaMjMaIZEQAMzoWirbdC/jVnYdtHTzAhihEjB3pWcIet7Uo3swIBfsBi03UROu6Zo+QodXBUoIYuVDMndIioRiOUAhpUbZPFrrzqMj6T1DGG6mHxzieoACQEJUSBTYgZ3Rkr3OZfdiphrVRGZTOb7mWAwyuzSPpoJKQXBpdQPFAQsmAmBFFoEUHXjdBxJgkFAycBqK7RVE1UIAkQjIUDhli0TphlqdTJ/c97/u+Wv3F/gb+P8/l+djkUpcv8V1SPk0Jbs2ORatd9EQq1sFDQ6dMUabmxhsWqAZ9iErJm0bGoy0aEYwsNTA0OwypbKyXLVMxpoulVXVEbGEC4jkSw1v5U1nvGwwwRRDMDPCsYb4Pa4lioAClBy5h2X45p1LsZgUlpmzywZCULDqphtK5vUpMzJXNKfKtpwSar5OUGQOjoFsdfmmZmiUjEyGDm3YFyVHI5SXkiqbMIMcBcbGfakWRksxYrDWAlWaKmUYA+lZE8MO6PBEM7cEJ+JRL/kqVol6AFBIULddCVbUA3UXKlrBoFtUAFEv8rKRGJv406hjFYI6wAQ3svi3Dbumx7diUxw3dIPLRqE5jMwA7EmnLbWGR4mK0ErJMh0VKpY1lUjpNTGqaAxiA+z+G0QAAxYtgggTyv8AYA+ATUZYVVD0uczzDfzh/vhMH6bW3JOkiPQ6v3fooODelX/nL43nx9rs6kPDHs3tL45tRAfqxVMbSkUDVYCsAGSQap3t0rIYAi0AjdYX9AZzjVIyteUalNWeHG2wothxF0vSmqyyF7NpW+ns2UADto7YNHR6fQ5mQtJVFECTmjURi9NdIBaDGCqcGdNZAGCK1KFaq34bSivrTckqHm41XYcZvjCGINRPSByHJeN5ycBMmoo5p3OmjlyBUa6EcdBoGGa9iQc6LaRalp5ZS7NkllMXASCxgYHUcd7fPVc7m3zl6J2rVr+THvQpgJrQwieE7g6p10VWYgQWqCI0WZESs07DVKbMqABjgErQSISSSfnVs3dOOZUyGSiUO6bmMbfjGMy4WF+8iqgEujojkoQViUGGZggGBHTxktpQMYgpCAMqxAIaJmtQCRkjnZBlg4yBMMboAHgMwIz0zd6eOB7Ue8NDtcolNS7DHIUXlk85mUX6fe7NPYVgsK2sU4u9/cCqS6kp4Az1oEQdNiaUEnXEApsWqUUVKOW1e8DYpWEHCIxSky1X2lw58zGYqrn85NssLQWvZZkbMKlyEjrkRC4pxDWpsBJktYAhergfcj/QYOS0Ud4w5OC0rRWhCIIDsWJibfakS7up1NvsHAGL2aBDYUPVGF0TDJUdgekFs5NmhWynlFvqM7oSM9Zk1yzi/zu+2QAzw6a0doIjyYNmyECXZhUnAHgGw6vS4q8Oi0oSKUmh6BKZ96W1rCEROL3iHqUvp+QJl1RhBFEtqlA1VFGl2IQSrwnmoIxIdGRX6q/8Ur7/9rf/dzjf29wsA0oX7FZftK9TfpITlZLI2b6vHzZfs6JHMYMU0yYAGG5kqQQsBBGVdEHMZHVIBl5lM2IIDG4FDfxX1bpyJkiLgrxluIFcWVQcv7hRdYbR63+Zd73JaMGecybUXwtG23KTsuh4GJcuc3amAAie+Q2/4MO2shFrrbXO+J6xXilxAYsICxWakrkx6i0JAJooVqVyFPC1j+vX9uHdOW1rFqe7c07Ebr2B67pazOswxs6XGqmMypmOKDFse7fUpCZrvnKdmgNPRoWhumCROTO7ojFu1BQANxeaGosZcnXfyZTabUU79UwIMjNljTn37T5dPEQby0q9VnFpjVfbSatqyTmwFLE0SpCUPe6k18RqwCxt1eOLgyatraR0nWav9ba3S4Nv8kophSmFOZagAhodhJFXNcDmDTnRp7CoStFLnFh/M/f2M7/L+e5e8dq+smeFR5mc9UK7DCkyn3q2T8prvSjBNhjFWREAy/p3O1xUnbI2cwo6kclEQ607WgcASmzGWLNwGBiAGAKAElfwge7RkA4RxWCzwmqVapwRR5486YtV0LwP1VrQEJbIKuqeaqNmJQ7LjRKYc/YFs2ScVI2kbLflaic+dbi0RR2VujnDrLlnJEwEIEwwr10iyhZEsapFybl+Ngqvb7/2XB69U2u3rpP3xa3Rwkkes3ux+3S+LvSUEzOpOlFrtbWxtr2G283KgcEOmv0htona2RIGwTEvdbddLkyiwVqcbjmbsdEKk7a7LEhM/czplEsEYbHaRb6777IM29qqiFZyXd2rFxlNIJBixAkwg011AU9SZaxzs4uHGHauGQF8ViKTsI/LW3kYn/QDXGlebBcJJEANSTFEtInQDlVo9CI7GpBmxaSl2xnTiWZYMzJjcGu7UMe5u6ilcGGOM23wiPZ6vVkmcDRBlomdYwOj/mkzv6m2ag8moxITizVglzoBwgQyIwY2y2EgxgIABARwJkWzep/AugyEC1SrKZly0iU7j1Jhjth8cTlGQ8LjnI6JbNAkgFql88k81sBAEJjqChBZ1V6L2hK+qHNl6uREXnenVJWLQkbilRegRFAIdIrit/ZOnbnIrwXZlnXO3daizTUXu9pbroUvV+9aCFAiiFWMKalnL6fFdooMzY3V7Ps+YLveVahUOaesttfF2QBlkUP5hJ9t0EyW0g7YFLNDzrEx6iyv9m5lGe+P1juxAg0LSHRKhsbmESkhJdVLO2HNWiOogS52d6947LmlKw+GnY46sK2yqBItvsEz+zZZ04fNEKC6MlGJiawakmhUqqrRGx1oyIDMSKfQFgaDSkOIdWxXeRLWmQ1gQExW2p6DQ7Sves8FjGTAmmKyCuDkehj5UlXrxEZSO3rsopIaKiFjNOlKNhiBx44wBiCAAQC0mEWAFkDpkNnRMKnaUCWlCqfPnJ93p2FGQw2dJgEz49C5uFhmpIC2ipIVYSgYCCgh3sUeoo6O37wB72AjdeotS0GdCCRZpNyASkCm9jBrmGqhZ/iTMc/2fNZaEsNm70wp3hclGlX7bnGx3CnFkgDRlOizZpGyEmZiSLNv4xvKdyWsIqdGyyvkVjkZaVBVbsd7egJkWXjAMB0YHaTbrNEqbyvYVvd9i2uCGS3DVIkwK8tupHM4UUjKpmY/BCOAqa0vL3au8DX3l3SlQAqrfKKsGGFLWAqUhtJHApswwZSuJYoSBYuRrAoRGSRy9u7jP3HilUXWCACsALnCiVFvurEAEiFlB0fNmYmjdaokA0RgbQg2NULEwWDhvVUhpjAZLBbZE6ogwEyYtCh0ygZAjGtGQAAAcJsUIO+RhLxpzcBqN2+mhF5VCXEoqSQ2dxbxdCxggXZDB2vGbDUQ4CTFHDgQdAGBm80WCS5g50VVLmOWy4FAAOqILIjOXbxDmbRG0zhSEtJp69ufrl/Tj+XNJQOWYNqikmNXFD0CDDAsmhZq4sRLLXapDa9+N7d2bEw73jn3rGijgax2n7uxVbArbE1VYHvr3SxTmoixiqnRTsbsDsS1Lrvv2pe364bXNGRt1lFR3z6xVrqFzKg7NQmzFtAsTZcpDxth3vqeC393xutqZQ9gKFWqRQEuYKk0CXMxvGqL+qCsn9NSOX7k1015nBNTi9RNqrqFaTQ8/dq17eyskwIQojGhgRE4lImxhKILXWG3yQg51XopWIMJnVpQTwYAmGlaqxoxAEDDQMIaCAgwBBgqIBCGKZuBjQwsE5g5YbDA5AM+PurL57S5mkUdrbFLTU2Q2BiJQbM3BX4FeLHffCm5jPVqRwZmJUUpIGMF4SSH3GAhDrQZknVbEDDv/B4xIIfcxUp6snorYs7nfjj3/8n/YkksN16C3bhMiYdu+3KJ3FAiDJ1wkb6hhnIARYEACx/TyCoaOY2lkiywpcepHXZNyx2zGWep1KJTKRaW1oogr5mFhjkuSBMAmrHJzCmVvQTad/vaFmrEtg6pytVJdQ5jUKBJqgWkRMCItGSDOi9vOrz85XUO+bHoGIkQDZrqXQAiSKGOY7hij8TAPh2HV7mfw5SroEz2sHRIocK1eXjuvXOvGEgnJJVsSiNDsdROBerArkmDK7jWFMvZqomZoWpVDdTYKcGiGRLVBpQAUzAYWFuBACJlVCJMIGCBMMwYQ9sMDMr+EAasSGGT5y/8+Ke4zO4lOwAAf4TfwP8702+f03OwbuaxQilAKyOlxgaIUqzKSCpEoAZVJHCSQ3WUxI6KjU6dPfakvRa1Oj1Wmj7E/zv7D2/8008vgbtvL6eVRQLFgnhQUHo2k7CLTcelThZL5DXlN4SLOyYqhg2xdkmhKK1m745g1pC3db24UEq8ICjcuutDqK20moIY0CyttZaADEpbZaNT9rSZKZRdRXPXrTYZCZOKSSBKBAAJ0SLCgpQNGEI3grlKbzJ3oM550EAyiEoAADRISlWroLiNAK2px8OnjLnHNKuL2lxlOQZEgTB85uvt5EzzF+Qoa6oZWKWITgFwCOl6hY2hDFB1QrVbCktBlLWBHN1GyUJoEcLxwUAiRmTNMkCYhBEsQxjSoIKxMOiZhwcNA9Eg4lTGACCR2Cwzvo/jM3r+WeZ/6P7bemOu1l7t5/YrOqQJBWO2VDUgaABKEBE5WBUiSEdwOWrQNDO85JjDFIgFVWHVHgyzoxbXl9l+/i9+MPffvp5/eD7+Left/XyT9jPu0qdBgzDD1i2lAmUDIxRNYaICqzIX4SAQ5K/5Sc0+Kxa7S6Sgae+emplZMH3t6xgdNEXxdBBi4XCphWDb1bwGDCrNWqItyYxS7lEHsR1LTVpq+zRbm5nB2dNLtGSlACKNUyQiGEAIsCwBZlXgqko7aHhi2TADFRABREaMBaxcFicqYCEtAEIMxo3sNhgoQ250Xon112RHsfGId/eMPJLrODJ2wYk+1kziHOxTdDYp+5pZZpZWS8BFc9VMzZAgiKFonioHEIsUiCLBGICZ5RKKiwAIEA1SFgxZgiYB4jrYlEgiBbViXf74yPDMoGJlEb7n+v1UVl+bNYmvvgxaBmvbq4qmQGFIYGywIg0vvgdSqKjcygqkz14P71192ffEn1eyDUpO1ZKbPOn37NUFbZ961V1IBgAAgRliSACEUqkbBBhSVMi1xazSMDmTANhufda40Fkj9KoI2kqWVblQi6Elluemlp7WMTo7KbVhNo7SmdceW4OZbXKrakpD1uyRwKujJBGnW4RESRkQtXiyjhOAAQBUAHA7nMwcN9Vtbx1QcoCqr4hQv22OcDRGWymQFSuKHTRbaA1Psjnq5qTgMz72dNvqbcj2PkKxblwv3dYVgFm7zcIcOVh1Qnq3w0islvWlA7gQz17D2q6baEDAgAwgHMcwQAIIwEyBiAoyGUopCCRWhUyTEBaAmFE4kZJbZGaEuAAITRZxPZw6fvVM8rxu59RHa9V1sHj4b69IFAUUVYjvkccqlVW8YBoEqCWHm/L10Ot61/dLvrwuAxyTnmgnPTK9RHs76lUbpaQGBInQBJFEFUmVBaGAhBRqKVYTxJs1IaOJLK9psxm+4K67Yzdrz9Yw8GLAg+4+fasdXd11u7AFqT62frhz2Wozhmqs8TAoyFqLx900t7agJQCaq0SENUMwMNgADZMBAAWNUHHdFlhCjg03H+4VCAoaAJBmPLUNwv1rIlCohV+ak7nJaWw2+9VvIt5GsCV9zv0fr25zDruXQ3I76WKGYxFF5mDUg0Fa8cJZk8NunLRMICCnrWImzQraCgCAJUlVA3gEzXIQCpMMUIt6WEUpQ/ViiwuCoT0hACQyiFDy4fS+3CIR8yyVKLgMCBDk4T549gCnbS0/dlMxggvmuE5QBUqIwPJwVbLBSMlSIEtaX/Xz/0nx+q7YVWTaJ02kzW1upVTAKmNTozbtASUpGkUqmECibXlROI1ISaKE5Qa1jZpQxyRSqRKe5saQ3t06W1kHc88pFBFE3lhZCjLWrEqqbME4G4BKQ9aLgdYKOVJquVOGKAYOJCAAi9IILAbGTImtAAAQBu71JjHKbgru9cl3LR6hQCGaUsAKTcbxQYhKMmJurSHVLPHtYe7cSKrhpY5P7uTdOuMyN7W87G7Y7XDs1JNwVCbnWjfSOqv69Cpyk7qAcLAqnlmytlRtEQMrmaJiOIw2yjgADB5MNrarw0DmAPQKMSBkWZkSJMAgBiXhzqOVFwmAGEYogWKoADKcTLJXVmri3dgAIeCimCmZWVvt2yp0VMzxICWHBWKXG6Dvw7/uncsryShkzRGn5w53BVTTMliNXHuUKCWBigJQpnrQ4FYPJzOqdUnCBijILNvpJpxpM7F1XXfu5LQzLas1R9syg6nuBYpUhSHTamZKSE7pgZFuZDXLIsaxw+ykIUVX4nbaDcQIJJaKSWkkJBgBLJJUEhAsAbju3LqtC2YdDa51FyhWgTFEGk2EKtJ8YoppOl9Y+3pOJ2Xo1Qf4cCEr79uHHGOb15WO/PmXU1/fXLsKjYui9151Y6ixrjkIzrasFKyrQgAIDMh1MNqqp6FoxnIKAwwGAAEh3Kbe2Q3dxtNZBSuxgZTpUVkADNcE6CIyPAUlV3jKsC4akP8WWKIACEFk6nAaXuCOHrPGsHsH4g5ikJbANQGxuXSCeLnBuIDTdgqS8N/c9/JDjQ9ciKLuXq+H0ZnOqIeyEYjAUAOhjFLZIjARUq3FMnjHEDj4TNmxx82NRjnEdOCGakvAsiR6epmutqztZFBbkAggBGMp2WiDEw0rZJxOaQQZdJghDHBLa4VT3wgaJo1IQCMlYbRAo+AxrBh0q9W4ACuo2b/u2lvRzTPX7Jxbi5nzulXEyiho0IaCDqXxXNrEDakP5m2yPfqUfMY6sTsBSMqNoV71p5ffH7yU3VCUAhZYuCuc+twqaKZpWnBxCaWWQUgjmeNq0wkZQys5BRbIYBEZRJDHvNu1O/Gcp4lTZCiAGNBlGwWaVCV0wqkbiFUN9cnDlU2ViCQmCGBBFLOUADL1cDLUm95x46ZNUnYLrHEszMUIjB5Gg3Q6QmKFNUR0cqAx+w/Nw33P+E26CedLe/9/YeoRCwAE1QUFEdSUFIRa280JoEab9eBmIS7GyXq/bu0bHcsggogAxwQLwqJEU+vWbxGVrAFwVURah2QwVbSqdA5EQCDFBCmWwsDaQZSmWa7r2oxbNFJKIMlS2dbcTCS0oQg0EGVZvaO5rXq7swuVM0dT1r32YYNJZwNGGaEESFKMTupKObjZe5lbn/Y/zQ8zrVuEKMoc6hCblVxPTAk3VkXXDdfUtENAxUazQmrTini5YefEoIoapKkPZAAwsCoyuc+s87QCNeLgSwbbfMgG48kCDKAYMMmUyZ1OH1dAT37sqa9nJ0Q/517JV1YYK5iAaJAxSywoLIloh0/NtMoe62QMYFvrxhmmWURGH916cLGwup3duhZ0xdVuceufRTTFcL1854hDGdsP5aa7shN90AhVIwACCgiFkDKNu0XDb8zXPfHJQsa9Nie7zR25TfctW2vLjk4EFiAHaRbadTbGERy3i9fsXDiElEJIzTaoyrU0cXpgNFcMxKYJE4vZ6FhrTC9NUqSYbdJsogBQNW6W1iOYLLJGRU2kVp37unMKaruvuM2ZOnls1na3MuZkfmzEFLKXUGWTwnDG665363SOUeWSX3bes/CeosIWCeEokJBTh2liEmIKdIOrW7jAUMVd2RdrwgQEYwFGC1XeuUirtmReLserIrB27pmz1GVUNTuVwWf3ah9YpmIwLINIlTG7Kkttn1aisgzr8M2Ti/ezIA//0rRfegvAEqwCkwQxgSXihY1B7hrWLKraYQqLuNl85TZyBXPso5+6O5Oss8/ldrdMFWrTXEzT6pajAUDDkAZP5EFt4BRcbQhFCwqgESAg1IkGHgfykJ3eOXF5sXEpRFRBhR76G7+r9RjM2VzbKYTKnnbrQAxEWY3T1fGJiNIQsSVE1LOdENga0gwAjtOIE6YYT4/Oii2t7iwANFc4fgxBPyT5ryQGGlovSItSjY7LpVy7aBrYeTfXDfzIJ5O9nKvlfCkNtgig1YbmjuV44rKWbMrdJ6rN4byvP8/vZ/njx58fFrDIOqclvJUdedieSdlCpzHrPcsu5G/27wrJglMxJuBUMCialwGVBzvgPEvapI262Z3SafvAUhgLhkgGFMkRr421Ag4g5mBPsbAg2Yo7B7/0dSWDJBhaHmJBLLHUrDL+kGUAp5OL9VAdGDoIaMdFKilYzZzDHSSkDbq1au0Fo1hgwgQyotAI1JGbTPHwo3++u+mdAIqIABMLd0RAGhACAJbS6lVFn7YAn5/sQ+sV7aef37rxfd2+X//C19u+vv39w/3f71rMMtFUgwYNQCnAzeWhFRbFoYWkRASwAAgj5UQigWiNAFCCHIyNDgOujpuszwFxioQxWRSjnNgtzVRE626syRC10O7b5dJEc2QAa+fR5yLDOydqs1TdzjPfxMU1gRkCp9TilZYFczTZXsWH6JrF6W+uj67QUioGLNPMlXXUzs6eRFrocQOnASJf06EFmWCjiMvbTG1RAZhr5OCmi51Xp5jJ2W1P6jynbGDSWBpEA2a8HLbVCZQGg3Ie635oi7bHgcAtw5bd2VrHGiQCybJg4C4xKxGBMBXWFCjYKODYwbBgxWRwsFeO1NUIDkc7PLrGSJkIdKA6CYQEBkd69Af/snOisZFDRA6JRA5RTAoBJaMIQkqMY9i1xzZ3FACFoUJjG/TddD/uvnvfX/ZEOwc8ZIEdsdBCBS2+5c7HAyhgY4kYiR1MdkSRqtRRMKHoNEoAJSBAShAiRKqOEBgUwFIQgcixWGhQVESE3CmlNGiLgKYUXLWOTp2r4yBqNoJJUdxUmoVktJUc5WPPTBe9SeXJty+0dZ9sVXPlBhqKazJ45KHRMJ1lo4xX23paceDSO11o5pDSmDTIMUIz7c4UbKttIYNpU0ZoQ3VWirk5bbVU9plEW6uhWEYN4qCOvE/WE9sAYr3Xu73MSY1EEhijSgUysABItRgCU6M0loJOSIvKIMiZrqiZHPOYXRPUotW6aId7VMrxhEMUFJUjQGRtaSP+8J/bXgJRGpsUBSoRSUGwWzIBFvGAq8cv4t2sh6BEgGP7qhotzyPcGggtNJZX2BntHHP2ebyH5rHn9Ej+wnvmhgooV9u6hqvEDgolBACVGACt2hKTFLJJaEihgOHx6XQQrtIjBZmbo9xitu4D2ETrpl6wVpEo1Y1VRRYmKpCYnLxIhsaVbW5dB0IZIQiIbstJR8RX7VYmLT1HlwMx3g3242rRVedo0x523d7bWGIR877tEJe3oiJC8MQgZJ7UIAEBxcFutaLOK+LZM2iLlQ0Tq2XBFJM2kcmVqyLfbKtAAdRQmKrJsMmq86IZ6m4/KvJxNhkDGx3MpSYANbCMAkQsKIgHwRCrBoAhooWFqWvUw251u9slXeY0XG6ZY3fvxqriknNDSRFj9VRYai9ZAYHZqHRaBEQ4ShF1HoSXYXeCxJJ7HvHF3N/nKefJ86VQmuuurypow2vrWxMAFUOFSYyAg1UApzvDfQZ96t92Baoxu6ee+yml4mONDFFr3NuNlTQrJUShqgTTxEQJGzXI5sS2kBJyCaWcdnKpkRE62+x208Zra7Iol7NchBAQ2aCaOHoK5xZKnXvt2grX1gqxipMogyCHr9OQE7ttLYutWUxlj7ROaGpfY97bu65lem2zbBolOWxgFWObIMJIWXPn2aaFAky1h+4mbaP0GcoMA8tylYGuDjGEgGRso6yLbVMZC2mJqaRmdmybtqFsZtRtTU55GVAiYNrRalc5liySBa8hYZYyljV2XoGBIECZjN8mD950BXVZFy1S1XhluztvVUCOxU47mqvDYKQVNtwkkAIg6Khgq1WLmnC6f+N3vJ0/Gm5CDszi7ttWuB9vu5oSvWnZTrZUZgSwi4FBIBOD7FsmhHpElaG4rW6wYfXesKu7r642WYaEb3GkR/bPwS8JG2SBIloxAiDNDEHVREmsEkUSCwKkXHXTtBBjIUiTEqVb6aREkgBoTCMIAdBqMWNXt5BmKAJCyaAolZic+ZjtitUSI0KoQt2ydKxZw/ZMpD3Bwsm6VJYRELbddkNkhDCQTB6bLFXYOyu3wuni7DYTmLaCqhqmVX9gCSvgjLYjbdNhcsvSFmEBMLhnt63OEC8Hs+eh87oYVHCYVCamhR1Nmq0CQCzXoTxGY1kAECQADMDrqEM3biFPc5aUlErQuuvA2MMlJ4qawy6VcMiptctW19ZzVFUKM2PkaK4EDzbno/Rizs2H1/iRFMSUkzXCzKXXbmvcdaJth6aINkSYQuMM5t48RrGqkjG4YIMGpLReY65uyzbVcSKxqxDyDr59+rfhPZxWBkoQAmjUAKQAqUFWCQwEANLNSTWtaYpltCDJzJASWWSiJDEYYxS2ArZmLma5U627A1nILQQiQqoELTsrLXHBEZKLFKtYhOGskaKo9LunOueMhiTFbT0UGFewrkXFgVOcs6k9S9o3exYWOKgxd3OgbRTP7NpIjGwIrKZVqQ20ajM4Wps+jIDY9jrmSKszUYaTZxpWsBhkCHeIxwXICdNa5JKQHEIeXpaBBYuwIEZYIp8gQ4OhWK/rhYYBRCOCvuJEYS0112PGLjVrLi+sgODZrYYmDwQTUSBFgox+vMv9SHa5xU0Whqtuy+OqCUEALOdyKaYyDRIAzE3FzUmNBjQ0oxGWU7MSAEuQUK4iFSUgboCoeM4eZjMttx/rf9qvfwinsDQklVTSlI2C6zSIVTiQCKaVqqvUajNka7dCjJHYOBEgwJQEMCBCqDa1Ml0JpLOzI5ZZbWXCQKI2LJIEQGUTiYis2AUxT/JMbpNj3u3d+7Bc7MzIG/f2kos5VX1WRWqKZqJ4Mlqkzva93VyzEuWZNjLhLJHmJEhXLAMTLkCEBCt2hvXZ6MDQaR58Yuc1F6lZzGxzofp0qDLChZt3DhewAdQUQEQbLdPTyigxIOYlZAxypn7yF3u3Nzd11kl0KVOAXgEILd9r70DWsa57jjfsqfPCGzW0uk0fgGtCF+1QEgS15Bw5fDXPc4uQ8/yqPDsCiucK1zVqZw7XeK5mAxRFmMaVzDpsmaw92Dok6SNEoVXQAiBiC5hFU6cNwhiVlu9nvY3uPJs4Wf/J3mdGCQmiQhLtelDak1OtdVSiCM+pzapFLsiiHK1IEYBluQVIWhWRgDEwAkNEKt3pYAMEwKvSWAxuJfeyaKtEACiEqHy3aJvKsCOJmeySBYYzi9tkT7hoWKttYiajUQ2R21SgeO4Zs9pC05G0Yiymsewqh4GuzgSLNqvQblGrWnsOszbO0zAGdnRf1rsWFhjiTA6YVy5yQIolGAASWIYyFmCCgoaITQQAigMIIEZCvKqGXfm+vuPQyV68jQQEffVpkgNEkly24QZ2R+fd+hVOTj32w85tOLv5rm+xEBUw7nN/x+kzzbDFaF/XC8g5Lp+/eWNw1MPybBYzFwgjmDSbNXk41uoMkztadblsJjOWVAraSwBLCUF3gf/lnt73cr8/7Lmyfc/858/enfeVz82SkBjMuWMGIYEp9OWjGdamBZl7QE1UmvGK41abMUhSq5hhmhjFGIG8Agwo2OFDiAAoGSAxQiIhYCGgwaJEEVQxE6WqwrPMbgcVkKTt6nSK3Gb3xsf8WhmoVm8pDAfYooSnTDSGvvCwJ86SWfdgINqSUk6BWuhTmplMyMKiWKPGZHWtq4mFDbKSH3ljqTMbpJjszdPrZa1Bg8RyC0FEJXsyhpnCIApZfxInJz+zNuDiEEIAAQjWyJVP/M/r654Xe+7djABN2NJaeQAEQRzrcGPzGt3I8t4OVmXss51CXZZvfXkDUOH2wx+aXsQt68Ky7d6hbGnHc+7RJFyv25ONay9JO1IxxN4RG9veapCBujWpMBuU1B7MywoLLEY0u+p39nH7uNCeuLaHXubhfkAfmkIkWrIuXYAgGbOa5RgbEiKaVk9PU1oHlRK8NokIg5jHADC4BbdAU7IwHH8MUfKCJUNBQ6GqkVqT5GA2GSog8jqCJCJ1t8mIQcZgG91mzYZc/b3lWoTAe7Zsg3MUEOOIymNu7HTOWyMhDRYxYw5GttXoVO0M427NItpkTrFocR3KWMa92t35L+7m+b1+XsHUHDmMs9CHTIKAMswKdoShRQ0QHCQUEOwPB4MtjGcMIIQQh6u48yWf8tl5/aKdrdFstYhoK0YxhALu9NJ7rGJS1qqtYCm60W+MOIW/+EMcPRFt+B0vn896FHBoeK0OIoN9qYdIb2OzZvuaTTRYmpzaoEmyTTiSNZuz2bAD07q2SHvqgFLqWGpp27XdcCdN+0DnnWZn0vbK8np3B+nCddYlwCGTSRUt2IzWhsWtsJKdHRFxRJgRITxNrxARA4gBGAgCAygK2G5xvICwYAfNCCbJQ3iL0wrmiQLQ4EQ+SjIiESE1g2zJrJq+uUCPFwnT5iJtCoUxE8csMHVpm9xmDzkjckZkC0vHbWx3HqEWnsbrh8za2Oy0WMmYpKW7daGwbABUYdvdZ30+L/PLCTIPO4xbp0MrTIFEFMCJrG0BgLCpWbWAMMhKxsA9AACEELDnU360B9BJrzRG1ukIrmhLmgFDYAYN1Joc0m79pB89y2os85vvmHb+lPOcPxAqleE13MeuWRtmcUT8X/X1i1fL3VuzrrVo6gjfxaBhKqrUQRFEYU5FCbODk7ImRbnNZso1lWkhbN3DPet9xyPxdZyD04QS9NLpDjJqOSY4JhdgRLEue1GI2jXNtxJadhURJhSACEDYDF5FwFCnBgAFEcNsh8bmtCwnJRiKVCDx2ZufB8SpyZ4amH8mYBJFiHUkEtPqBkIkWjK0bR0ULMYVNAgzAZl0QEBth3ZDd96bzCo6J4UlDx6kdbVFRnu4nC3Pq+XgANNZqiG8AIC5MNCD67qX62feiw0O7yC1spjJAtpKGFAMiIE1a5uKjSQAlmJhaA1lUF7g0hgiJp+vT7ku6IXLauXUqhDiWLBGgxSTgovFLjXXcp6f86iyOZ2tjSAZPvdCjl0U4gOfQ60dAgJiTUF8O0qdcdIKZCyvNQ0sWNkwJCQCTUV2mzSLF9stZxVnIsuq9WaBZfch9nBkjGUx2JvWRpUXrGquM4NOaLE/UogoxneXKyMsgma0u12r8XDWUlXFYLR2apKYIgBFZqhEKcgAgFSatJgdq+JDLQtQVkCEcdyvr8JXu7FNz2piMM7LfLtzHrLkpkiUCKNOpqloZqjFNAgVEIGBGQEBybKN7aBYYR2DnNbmLT30nrvRVrWtdN333rb28qzNdtScqPP0ElwFDeWFskFzvuzed9ue189vm2XlmqE1RcdF02ZlR6qGsGKkDRWtIJlkCmgKFiFDZQzwMAAAjl3Z19tnve+WPOtlWMNIuVqZsBinCjQjWFpV4x4Tq9ac8+uUFmx0IXWxNUohffoixzyKLoNOh43bNUtADx2Cjax4pmIUuFfTaihXdVpgwK0jJdigBuosra3GdnhYpmBPLEBqtSsWl34lDIFiSBqGFEkSNsCBU8gZWp9FRWHX78PEmaXlpk07bViJICHotgvSSVSpXYwAiYpUYKNOt9FxnOI2NKbYzNlsVjsAeQ57CrzQN27YyezZgz7D0JsBzbFwJ1l6PaK3jpESOVsMUHlGsK3VIJo8Go4DREAy6LZvzQTNlqVqm/RYX899c06zvVPvmz4JtydeN9XcEtXGShsrAwgAFFaF7z6/5z+09vP5vfWyZu3UtGw7BcqgYIBTiD4TkKRWzFFJ2EahYEdhTaA6MAVAjIFNU2V2vs+14vXqfenWSY02gZWSCq96lYRWtzgKd3iB7IY3Ps457ZGDYmto0UNjjrV2ZbO5S+/ZUgMFsFUDBBMCHRVHLCDYehddkIwnp2irgeYpmzaLW2zLtlmbmnkSAlPRom4Is/6CtHrP1ZhbgMhOOxYgyRzUglatsGCt91Qf2HSVurdz4zpQFEpbLUrVBogBRQqGJbElZo1KqwBBNWa0AMpGFpbJKFMMeAgpU+HkdNM9LzsLTg4TMxuVEJBUtY2+7Jv9w9bWMhQaWiYzB6yoYiS3AhBiPBWGdD3te/5RH37xsm1GhzXm3t7yeNfqmWW71WcH78kuOvfJ3rlUXas1CmAAlwMCU2Byz3/Zfd79qv38KNccK3SmL4QDPAZGk2HKDIS2RE7BsiLDFGRKDJk17JIMNIJaAIjJp/f9dp/ofdHTWswqq0owFa/MBNHUcqR1unH5qdec+1rz/NFuMJg6TjU9Fsiz2neusa7odQdLOz2LRRo4CAXMpEg0CFjB4UAaM09mpDCFD4lOlolqIjIZMmxBTRYdDAef9ge+l/qgZ64VnDUNA2gVR0QflFdlYxtcek8stGguVz2305sY1EqlMUNxNGdkWdUIw3KlsWVRi1ARQQQ0CFo1kSi1ifRzPQE+BMwcf7u3fe/hcBBjjDEALGlhKkAjeFnbzrdB8p9/qdapNZF5hNuiKEkGOBkADDAeWxoAvRsE0NfYmelujklN2RQQvWo05p23wr2X9tFX36iS2rMxAABqZgqolCTF1/Xv3p+W1x9//r/2udWxRTu/DYGMZsUCZEbDZM8ykCkBYKYeOaEGIIKGMSptQCQAwUKAzqKe6X86v+fj5/fX3iZsRVVUoooA1ARSiROMKCiqgaS458Pr4syhklBauDnsjA2L6/3xYVZXu3zbPm5lN3HXCDAkdpitbWaQanCI46urixzUay1126oyZQoKY1JJ0EabsdBGG8Otcb+t93P2CkqqTVRO69pQgwmwxQRDpR6uwwUfe2qJo8poUCBbLTqhNlsUsQhZvUxjkTasELKoVYksk7aUhQpFigLARMclBAAg0MMWR8n9Na3DweHIaCrP8n0Dq1GkxahguW7f77/7/YsyBUmyKGO7sgBxQ4HCAGI8ieJtAKCRrBMPS2cnCEuExsrQzdCacGMZbtk9rXZvtK7W07QoAhKEARyNbdiwOZ5b3tf6np8PPp97u9vK7/YtT1PlZFRbW2w6Z0jWYFPDwQEwDiHZMiXEYsCjcAgAkjMXINHZhd6xR/wFP1/NJ0MzLm5rQugw6TWKaCS+rBRQRO36WO38fNueg6FCaNWeqodVKDEKBOVuty4X2zHOBpxWQAEUevbqJIYmNbmcJ5PUsfLWpcpiXmydAABNJrgVpgoAbAdvvrzngfPq7aSKziqO0bpSmExwngykUoA99CI5Ait6XXeXJsJqhS4k6joMLC6gGAeqq2Lpm7iRFdBEonU6CbNSxCEUMhptrupzBIDSoKZgh+E3wRe6TZOiLeyn5CFFGtU6hBBss/bv84/fn9p1gZQdy8nWLAKAVjKGA8vkqnTSACVVICAh4AoLd62wMY0RNMhtWqhSUlnX5m1XI3oEBQAyMFCYzD47HmQ32zrnCtvZyXlSDwMwkG4omNmoTjg21Y1axOSpw1NnsiESUJGBxKIZQpKRVCkOZ3ikx76GfX2Ur5febLVBwEC2BWYWXYG2UcBe8VWh1ti2esXe53SreLotJhCqsNFlabdsaSlXt+9qt1XkeNowHPajaqLBiERPIYXZPCVFbruRl4XxsJVChIEgVU4WQTjAedSdsV33dfP95L2QNQ1DEGPCOIdTFHPzY4c9KZFS0CmnisBmFK3BiuZZVjSVRqBCrHZbYFVO526XLpluYKXGOgJWW7RUIkOJCERQKosBCBE5AlZevvzld47nzqrRnqi9KmOKdgRoiiIGltrfHXs+va/Dw6gZrFADjuNxACczZphzlsYY4ol1o6Zrd9ZYkI1KLE1ozRfs8CUFLq+8fj4LTeoBAJWBYYYsnIc7w/rW5O1Rc1hnrIf3xsaTgJU9QSWmBgKhb3eeuiaQYyOAU1pC1UALQ4gYQQgoxpVwe9THwr5OUOnl9hwxT5kFqxQakKilVVtde2oFiaAeJdhy7esBN8s67ibstFESdZYh4DWprIFd71zXrHO2uwGcnh2rWjWsGHDGUtvakDQbt6kP6q04TDAWCExOzXzyGCY3JzYAzM603gefX2u/ni2o8aYIbWFp+1XxgLrrNhT9KxNiSkqpRkwsXbnNJlmP2ACKjDoLRVkA1qygYGDrDUsrpIqC39dKJQBBlFFGyAhIh4yAEIlMM91TDG12OKyUar6gmq0CoaRqdDjg0Woacl++3+NJyRlkASQZgKEN3ZMs082EghznoXe2exy8VKAnSgSdlVjjDHzcDruSHrtm6eJjWjMoOQCA8EYR55tjSU9U2cAW6VvNyIG2UzUwFQOwZzIzKQs5M7RVYaTZAGDz2vYWVYwEFVIW4MyMYCJ3vdl5W3mJe708R1V3AADKZmLMLBCgW6kiLRaKvUJctwy66zvreImV2HxhNFyj3SJ77JqL11iytHo5rFx4Z16d+5W3eIsU3HCFARbEzIxnaEI219SOBJfKdGA422NrveaVs0TJITvvE7uI7BueSE2CPm2DzKKYkpDNdiyq8IKwADnJIgTVkrq6STqNPkyjHB2lK8xklqq8qFsPEtXEgJAoAtwEglZEWVITtXVV7NXap6ACAVbmIMdiBxRNB2GvWFw3B3lrhaJBqakZpjoNLbnvOXbsYJGVVSYrM8qFMY+2yyw0k7wFmfG+do7eQwVqx11RgCKMdSgh9g57T9OhpcukbtgUABaEAaYqI5NnPnblN2DaPV/LmCOjPcxc1lLYgGNIcbSpsGA7xcACJhLYxmYAhaBplIZAATm2JwkozjWf5612eNPzqjONLhQMCJtCOBXDycxmd+m1FlVmaJ7GIou6g30IcY1t3frCsFzVRbvlzpqIzSsYCYsLtdLr0ugf8saVWdGhZ3XODsVsZmiSyZkhy1QyM+oECg7HpLl4sWcTA0jmQcY2dk0X45Z72RqycmZWQmROMuyQdNSiSlAKNRwKfXm7Ygv+nAxlUsS2lKzKGC/lkKY5lw2BTYxZoFKoaUERpQSgXAOoMsYr+qioAIwAkIgZcWc9ReoHHxzt29ZiAAWgGmjdQ220rSrx3uE5njl43EjKUDKqqFt7SJymR89dzNztvQ/4vmHVe+61JZjqjWhI2OibsgeatjIztUzJDLCqZV8CGI8NBR2GmWUXp342S1vb7t2idThJ5yxRaBwAOMMxeHM0De0tTA1OSYZjthATAdEGLRZvcm/f3IrRGvlkbx2t2aue1wETEsCSgcBAyTjETGybNYsl7cj14NrFZ4d08OS5zNRUKC5JgrGe7+eWpbjjFWtUSGgdBHNmdBffvXCTKK5McV8TF0gvEUd5RKDMMsvSBdZp3/ZMWSux4sWEeG7sBNmq9zwbVVBHGHqLQghSDApKPanea03AYiGZgrayck4KuUVrdE7L6J1FENZm1uV3fj8+at3rsouv/VRPk8DYRlHASrUI3xsFySpML+kPGmlTWAoAKFAokSQqUZLxxorVRgZaCeQQdZmwWTVIMtmzHBUZASQpu1g9favljs+7r69zr7Blrj3HdrnPz/rZto4Ne/W6lUW2KNSBUqGDRtUFgwWM442rwl0ZcGVF5Ycf43ptzKw2C8IsdAkMqQBMxgatScZGbK09wyAkhGHRbU+HElGjDpJjz/akvFn2eV/f7+sa3tt8fsLP9z5voQGULAAgMdgsoKHNKoQgZG17RIN5dRJ3CCUTNBhqQZmMG6BoL+1379fePOUoQHRwFp3Q1VF2s/dTf/zPuxvBHKoJNtuYAydpNCMRThqKOjDMeuvNSDsIgloyciVZkBbOvWWTQItjWYwAmBoPR86W3vAaQFKSxNG1bRf7kFW4hRtvwbUoSC4M3KZ6LOof/37c/Nzt4rNrFzrt2lKtaatZkNIR7Acli1SX1+Hp3B+2I9UqMDWSCkaEUQk5x0B9HD0Gt2W/1rt8ACyRhuFWAqAoG8ywNFkJ1CyMjQiCJnP8ElmoNoIlO0OE+z2HluVs+7g4hyKXn18fducOU9gAxYBCtaC0KiMoVkoQRvvS3nITpnRQvK3MRG9dYwFMBsbSlu2l3UhqAUcxAAmlZKCCKaVGVRAwMwcm2pQmb+/+5+42rt+2X+ZJpgAaS4tGE1fpiIQgYEroAiLqynPm7E1NmnU0gRgMHboUenaewxt/5w+w020hL4niNUUUsk7Hs7fk+yvDzEGCHGIX12Q+dic0hIGhiAskKLIEJkp1OMHNV1sNu86uXcti4TmTiaxVkjlpxEkwrDaU5cJAVi2HFRc499Q9dzKFzlUigaCBiBo4xjA6PXzaO1EP+lQ0iMwJa4CkUDgMFGIBBQDA4hBFg6bGRlfbRtOhhAFQRcCaEf2uPq7yY/YTuajhjpeiQwSY2BRWcRIIjZARwOq7kXACSCtrVEgsYd9TbYALvIdtqbAiIWs+tqXXVHlkVEVWk0WwACijgFZSEjO1/2tP8kTbYIm289Y5ZUKSzUxmTAihQ4Yhqok4kMBMadZmsdkBMxt7w8DMGEewzD5z4xnuh+m7383HA7I4TgaBdpAoWCMIsSwRx8S2WBsP1kfO2MSaZSRNDJEYKQFQ5GbPiPedgp8re4K23FIUHAJk+OjVbmCxPTZIOJlZbFrDw0y3DiAU4QBYSAsRQMh6eefUKl4kX/nFjrxq1SAgcnK4DWOQwiICW4mUPMAadu05OfGUbo/zCk0WXCWEEALAu5lqTGG07sKuJk8zxRnzOsQIQlNkVcY4MknL6pgL4IUAhnFzhlMnWysUBUXSiqAIQHR1FgpM1h6+ecB1IkACYGoISXEb2d4sUyYAICImUaxmRwEXQH1hlbk5NHgoLacsgRW2+3muLdHoMBABNlfhIQQo4UBrImnNjNUqc1myW8bAbVoV2axZBBkYEkoGCMgQOrFTIgEEFh3QoomvVqqqnYFO47ARz02N93rT9fbL10ePWiIHbLaAO2ihwJHp6upKCgwwdqG1Sfp22UKczbttKjbCEpmCAVxidi+3DNB685XCF18T7zpbVYvis/RWS+4nh9m6ClwpSnua9a6tUxMDOIhQASdBQGkJ304f7vn2OWvb9uJKrMDEBAlBnlGlKoFxBEggkh3eA251n73e933ovfcWE+gCFMxKhKAsqQjgGPfEdLyTPhOeseHUndY1lOBTMgpBcxEkscIqjlU0KIZRo0ojo0bUlRUwhEAGiGQY/DgyorWex4cUMICY2wNyW9eCeSzlZXmmoUQigFWfpCNwGZpoE7IR9gqXjtSws1HN3XmeW6QEMCgubFUwQ2izagsAgfjb7Uh0HktVa7LJVNY0DBJgGNiG0jkJa8gAEoocoIhDAhSRjukwxc4IwEzL5LzP6OZ8qVW/t8+ryRUwAAF4wfBUVTKPTCBBDQODRQEn1lO7/GEx+DBLU3EolClqUjN1F0x055nGLX5Xu3EtqLMjMCUzUMAhHjLoU6F2Rmrl2IejbsVgAI4xiZBxhMDavaMHHLM5O0GvSUilyWECXSAzZk1wZhw8rQgMY4phn+bH7kvo+Wb92ucG0jlzFVCUBlWFCwcOgRMTtdpodaAW4nO3HxfnNVGhi9bThpOtwwLKENOtmzoOBIVRUynv8JoqV0kmA4jUJmgGVQGTsRkv7FoOitdL65TS4NgFCgM2WHD7ufcvOAgCkmWZxuLUW21UJmjTNovSWgyY+5rZ8TA6KeUAi8uYwuHGKnIziNAoTDaDjc2WEwyCpYYoJ+8KA0AQBFIrGQNrCKaGzMIMbBQIZAhAGULHzByURQWZI9J65Zay++mmvIakCEUHA8ZUBegMnyqlCwwjh+46LJfr3D7uJ+7lWc9K7EUEN5NUCIoRyNXjGfTROSj3JqnDiGVFkWsC2EsorumpT0GxQwNT7VoEIiJlBwVHEMe77z0/k+puy6z3cZdjRkAOUJYl4KKWWoZE2BBIcCNzHdnz7j5XW7/7fV7amfws2QbozKMoNbRBJrDEZlBzpgQFViCBNn1UT1was6OLaONAH3nedJYLqIGlVKKmiVACkMNlpebSdoKxqCjAIqLJKhRTjKCRwA644rvlXFfW8H3bYntyJsSQB5t9wW7GDMKA0LksdERJMAbZsphbjnN2i1NfhSEFA6MHm7EMDJKGTUxPjFLMGbFjp/Ycx0g3cV01KhQ0gEY4NbMdFIh0DIQzshIyJ4ea6qZiFEjoWHvvUx/YWi0gB8Haxnwp5Wyb+ybIBIq9dMTAqiu4RDgFItcoyLKGVSk0HArOYsHCtjVjT4NAhnu5ZZvxkntW2tAgQpLjRCbT1PI2BcySy8bm4x4cWCCUZ9O2TYULyDBsw2wnMFkAGXA/V9s9TsXmzq6SFeGwyMMkFlIAWFYZHo3WJBhiO3Bu+z4WwCyK28JZosDm6mBkkOhlkysCBs2AMZrmamk8n1adJ6dJ2RGSsbqxOxjWbl+jLIdDhQiApCiUsGJerlmTbMnKYoQAYlRNjY0aDgAlCqoNGNZlZT8YvkOhSZcGGWJTDGgt+Bo/FUaaGC3fiUhsQ5qhFZtoTY8yKDE7mLSUBK6qGoY7krq32lTbu06y1xe6j9nRJF0UeIGqsrQuAoUDjIFqNZkwYU0ZhhDKMECQNckwsKVCgQ//sEtvXpj70KDBD/w3T83H2YaZqRFtHzsYZbKAlgrbA1U61DC44JpFoSYmNpVCrWzE0gaAw42dCOitPlv2brievbnNyi4tiGvA3ZlmjTOpCQCLt8M0ZdgwGQJ0fdmvDTqYDLM90V6zThgNKYZdfL75+e0IdVE0ICZz7Sq1lZVh4lDh4WYsE2VNcoaOeI766s7vzpsTa6tlqpKsiaHVtAbrNSmkw5HwnQpWQbDcrYYKLjoMc6NZ4piVmxGd9raOJwhrAyJbncGUX9tqxAlTPLkpa21RAGIRtFlBxiAQgemqoIQEbtxO19MlEKBUkm14jOpmHq0zfDobzwhMgDs4EhVcnSEzWsgyAyABAOig6BKNi2Y397oLYWjck9+vr/WtDl16f9YHaNoAdZGCsk5iEmODF97y2oJYAB1CTs52DC0CDEMmJCEzGUpgzJm/B37Ha578MPhRt7x1e13aMxsg4y3ojV5Dq2BltKSKJ1ksU2FycDWlKzDIdesZ0KbbYoLiBghlM5xY0P75KTzFXgy/uad+OBYUpJY328ZBURBAq4vC0ak0qPjozN42r5WCoIaTicRtisl4S+Za6gNLP0MaQAiYXQMH8ew0mIA5fHIbBDntzvfu++xr12brjJJXyGKtPW1ZZQNUd1pbbKVhuy9f3fuUY9RiNW2ay6RVLSJEgQAiFEA5xCR/XF0Pj1RioyKIFFGOq3f9L5AKZKh2La4VLQDYJFCTJBFBCVUUYlUDF5oxaFse5eJtcb1kolnlNYRIRHiJ97NU7WgARVhJRoQAAABNTQAqAAAACAAFARIAAwAAAAEAAQAAARoABQAAAAEAAABKARsABQAAAAEAAABSASgAAwAAAAEAAgAAh2kABAAAAAEAAABaAAAAAAAAAEgAAAABAAAASAAAAAEAA6ABAAMAAAABAAEAAKACAAQAAAABAAABQKADAAQAAAABAAABQAAAAABYTVAguAIAADx4OnhtcG1ldGEgeG1sbnM6eD0iYWRvYmU6bnM6bWV0YS8iIHg6eG1wdGs9IlhNUCBDb3JlIDYuMC4wIj4KICAgPHJkZjpSREYgeG1sbnM6cmRmPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5LzAyLzIyLXJkZi1zeW50YXgtbnMjIj4KICAgICAgPHJkZjpEZXNjcmlwdGlvbiByZGY6YWJvdXQ9IiIKICAgICAgICAgICAgeG1sbnM6dGlmZj0iaHR0cDovL25zLmFkb2JlLmNvbS90aWZmLzEuMC8iCiAgICAgICAgICAgIHhtbG5zOmV4aWY9Imh0dHA6Ly9ucy5hZG9iZS5jb20vZXhpZi8xLjAvIj4KICAgICAgICAgPHRpZmY6WVJlc29sdXRpb24+NzIvMTwvdGlmZjpZUmVzb2x1dGlvbj4KICAgICAgICAgPHRpZmY6UmVzb2x1dGlvblVuaXQ+MjwvdGlmZjpSZXNvbHV0aW9uVW5pdD4KICAgICAgICAgPHRpZmY6WFJlc29sdXRpb24+NzIvMTwvdGlmZjpYUmVzb2x1dGlvbj4KICAgICAgICAgPHRpZmY6T3JpZW50YXRpb24+MTwvdGlmZjpPcmllbnRhdGlvbj4KICAgICAgICAgPGV4aWY6UGl4ZWxYRGltZW5zaW9uPjY0MDwvZXhpZjpQaXhlbFhEaW1lbnNpb24+CiAgICAgICAgIDxleGlmOkNvbG9yU3BhY2U+MTwvZXhpZjpDb2xvclNwYWNlPgogICAgICAgICA8ZXhpZjpQaXhlbFlEaW1lbnNpb24+NjQwPC9leGlmOlBpeGVsWURpbWVuc2lvbj4KICAgICAgPC9yZGY6RGVzY3JpcHRpb24+CiAgIDwvcmRmOlJERj4KPC94OnhtcG1ldGE+Cg==
- logowanie?id=8h1b8R4U9O7b4K8v7x4k9i7L8y3O8m4W
- data:image/webp;base64,UklGRpBTAABXRUJQVlA4IIRTAABwBAGdASpIAUgBPhkKhEGhBIZbaAQAYSxtwVqM/QvZOjL0OyVbNH3itnlC9ff6H8me85B55v8kf67/1f+B80ltfyn+A/VH9//8Pwq/6Hjf1b5p3MH+q/uv7r/5b5lf7f/n/4f3cfqz/k+4F+r/+w/wn+d/8H+C+ML1nf4H/mfk78BP5l/af+n/nfdU/1H/B/ynur/qn+Z/33+V+AL+Vf1v1tv+h7I3+I/3vsEfzL/Df8z2cf+Z/8P9t8IP9V/3n/u/2P7//Qb/O/7t/y/zb+QD/6eoB/5fUA64P8PfMz/M/138Yv2l9lfyL6B+u/3r9Z/8L/tP9R8kP97+SHatf3noP/GvsZ9V/s/60/3T/n/5z54/x/5S+l/qS/Iz+yfsP9hH4p/Hv6Z/bv1o/t//Y/x/uq/1X4zeePbf/e/iN8BHrd8q/sf95/X//DftJ7a38R+Svvp9nP8D+Uf+J+wH+Lfyv+r/3v9lf7f/7vr//e/27ycvvv+w/zP5jf3j7BP5D/Pv73/aP8z/w/73/8vtx/of85/h/8Z/x/71///gT+f/3b/Vf43/R/8j/F//z/n/oL/Gv5b/ev7Z/kv9x/df/3/v/u79gn7P/+b3LP1R/5H54OJ0bk19fbcq2+B3U6LbOfQ82UXlPI3vZdqajwBWNW3a+B/WKeQXaLn8qXaXqDptrITeHyHA+BQW+vH8xk+FbFqtjF5Rp6h7vV0Br+i54VW1sKPf0wX5Dw7t2flh2ZCzKTZS9FLs7rAX4FZskHpgN69+KrzEDnooiawnPi8iX2ilRKKoYKk4j4OwzGcfOkxtbuO5xpJmgwCwQLYNkPt+yRUOMbdfA/v2xnZhzXghNt1Cz5TX5spRpY5tPyWt0MUW4JLSH9ZVJ3maZMGP3IbUhHJcabImufm0rdhdHgI83JcOS++HNhf5Uu94QO2Ron8NahFsfzfQKhsOqInZ3aowXt3T2MegKC+qMuloFvP/ZDpDGvulWPimMnrINpuAr9WgWbLsGleYRtqmnAA4DGjOR7k0WFdUu1GHOqbgByAcrI7pKG3D3IzkSqBKKJWfmRjOWE4jd3bUIbKfMx+zs3ekSGFKssN4U5l0jYl4gFMYWsQr+6nsJg9HkkGlO7B7LwwYxIjjp9zw63TQn5guNd0rvkyOvlgrG2n6YHYIRo4mKxVpaNo3xQcEZpMKJilUmgl/I9WbH6MqibTf/HFqEJPCkekoOihfsKmdsd71ehn/S5GoNP7VmAfSNnOgM4JoLM3WIHFjmCEGJ/I/KAr3lB3fopHEXfSaN05849h+4t3AOD6E+6elgFZazeMSkU+Hre8L5w0yHpzGsqDFX5ew3mHxzU9jL5hLOpdpmOToFNq1wRliV1IDmf7I4TCiGYHXUB2nY+VrGHFP1D5+EcDMnV67OrIi3rrU4JGPnydpQXcUvGMNAuNZHn/lcW96GfAv9zrZAWhuw5wKGcrauwSFxmpedLEba8cIw0an3h6wg5GaoASLkUnEz7CmfDav6RzcZXIsnyFJpEmfyDmXVU9GdSZ3bXRwOxUTS8XUHutpfKxfWEV+DeNod93ex4mmCTvBtiawgLrZH8cYD/4LSaBWBDjBpgxr/Bk8Ozg2qDA5nHXSHyHbb3eegOu0+xr3o7iq+etoKMT0Cdvt9XnfxZyIeKLQLBLLsxehnWbw7apNHtj1LRj/XqOQ8qt8+mrDs3mnz0I0J8UxMUSuLGgSdPV8z6JPI4/tFODxjJz5maNv2gPSf8XnC/b7KlVOybbNgUVqfbV5JWb4zYx1FScpxoTXRg1+IuR7U/N2+A24zh4P2eBorWgh+fqFBYaDCzRfk4TXtcuhv/qHIzoc/fS0jVvcnjkW39IwrrMLa662vhpoO2klRseAY+ZfXKd3qxAorPcKuGN1aVodrNzX/ZiMS6JtdNWov7DNU5A8iQdZH11SwIupVpv8LVPOhOaeRrpC6kGjyFd/EOEuckySCeX64uKWkSU0kOzGlWqR/4TVpJhdkovYjkw4/r2ygB7AySvTOK+UHCMV6oIrdqvnjY+qKgDLKCBgMJP5frk95inNb4qJF0B8Cpv/bJrLi1X24jDuMI/NdMLxa3Dvf8X79CNKmL4f/AcKSFpJWN48EhQDfaBDGfALqzSycdHTKC3I7nUoX/xSygtqme5mUf2ST8MbwBQO80PWOWwM+DJnWzWoPMybkiZCVMNE3WH0f7BCZbpI9MTDvLudXfP27BJHN+yYfM3Wr+dFVzhLVlQMMI/SO7TGSk+dSBib7GqBuXQT9RGIz0ExACzL0DMUJajxxoScfviHZM384rMEWTzshF19FR96WisSMx0E4BqRBMhuQqBLzsqXXRXFsVycqBAe1Ai09EQ9uOTAWM/n+i50z1vXo3zj+xLIs6RHqFWdSKu8W/exW1oATzrLX8QtC/KTnhin5qAJZ7/BtXQahq9Wk3VwbDy4qK4qyhYhcV9mKIO0QlXyiqobrY2zS1gxjBnXfN7lH+2PueSyLwQEPoTO6B0amj7RMgdwCwK6ZVNxzaLfKFRVGoa1+2xEg3XdDYpLSHARLa4UHjCaxu5uPxY/Fn5Bqy+F2CVqZyKBtAilyrpF2Rd7fN9NG9APXho/0FIZboY6iVMhm/gcoMNPgAs+gEJ0rqpMTc0C3YAyg/223SQj+ImkEKct1Qjp6WUujqHWEnG6vcdI0daSNOayMH5zf6SKYgzOJ1qxC1hLaBgCvQdwjV3f/dtQ1h4QL7RfjcdeEoMtDJws2hyIVrTa2iJYSJNcC5P19RmqyK7GahWpO/kff7JNfoUAAP5D+g5m4wKzX41t2i58NKSFsm4pJAvfExHjMpT4fw+oLKecYumcwcaAhcM54zCYX2tuzHNTINh7ZkboQqiXfzhvoBaVvz8Rz1mXkL/MP4v9xyyiZ6rdhrSVmbRe62BhNLIFkddNBpUZBSiz9l13iVyFv60ItURN3R9CFM3308IYM37nGKvWoKxm4sJAnuFu77ah/nyTcH1/SM/2B+RRkEOMTXrCI8LHgjX2YM5pkkMHb/BdkovzolpnftV5+RhPpkdB1hBcUm0oeZNllPSpruWCuiUAbZ+8l2azpZelqNLVYANwXyneM1LT+lflrqm+qOUXZuAa7cyOXlD80S8bZ4KLM1yuOZnDPhK9m3gYc+U6KnJjPZRspK9kf2TyYy2HOkUHcH/SiXE4G4mng3XID2W+V+a0M5BtbVwCxAbwZDoqVSswVWKuntUe6MGDfDDa0M1tgcZdBQezSRnNu2RHoA7ILXkkkAz1qTBYjXmMVbDmY+8iFCuXmfA8QfitKHGgFxPCU8WUtajRiKLFYYtUmztW+vEmj9Zr5B29zvqTlfVdICYBmbPgLnEv+rxGuBcswJ0g5BxXdyCpzWPYrNHmk1Oxjg/sBOlhCo/3ydSA3PUv3VYaK3rI71E9mDbFgMhelJ9o3FW9w2k98fdQ2+/M+B9H6tTrR+tLzLnI/CxmzNxWjO3jopXoq0L/KmA4ZvtDRA07aY0lFl7hAGXUVF0mI3g5PT11FzMUoXZH8c+gup+woErz+9moduqtyzXWaD2kNNT9llV9BGJsB0A3WgbJyUaAWTRWfDmecnirTKChhTXWgFvfC+YrF5PJmbw/e9ryO+BqgdzxFthdAW+uITH1IKxhQBVn2ykK+TrNKIjHAX2X8wOluNTEWcpJCrtRPE08wuP/WWf+vOCAHUoXZkM+jSsla8vwXmcuwkaEiIPrpvl6eLvsqADsIzRF+sMsZDKnGflvgHGBmpnxZhwTSoQnuq++ynNs0zLx/dRPe14DLLZ0vuDws7w6lnZeQud6l6FT/V+u3ClWV/CpjJcWURDCVnUDAN8YDAplSEIN0oUgSOg5CiPY2tK3RSPS2J2Qly2wdpkQcrXOBOjuJDIwVppozL69hRRHPNVIFfdDOFE/pGQY1iokgaTHnQwOFrY7xRulHnhCdeVlw/ZOHkxCYxrjpEBuIP5KGqUYDROwkr21Tpvyz6e6qlH02nB0U4LCHG27b4b+9CBYLan0pBh6Iu1327IhuqM/+ExokKVhFfXMlx8khbZVWCkneoiMOrLYji4MwgBntcokh8b1IRPPlfhIBaWHN1XjgDLTWR6WR5n9Au+YRb5nn4MX/Hb+m3J56w7lIwES7/y1IUCW70F7ooMAfQQZstwfvEeNiI7vm3QK6imeQuqt99J4NhY/WElROlqca1E/tzTnTM3CUVPl/sNp34YMqMYsacqwDBrkJbx2z1oNkkvxZxAmbnE9EtaoYsg/wuk5ZBxnhcmeviob7vt2NLqyR1UlmDNf+giUs9CIZ2N09trIVGeuwiZm+vHfXHWzmB7LT0uVKh0VtUGedxxqgjyURvaquoxwxHLnF9wIv9Z2TZQ5sFF70sw7b+pKsYhNdh9iJmPCVr01JTsMPzKDTj6SngKoCLrsF8xQOq9QoEYfzy55oL1wqk+qxTaC+unOa5a67MTJXIzhv1UKMgPGX0hGNM2J7Am8MIdFiPN9RQhL1IZ8eln1ZHmSR0yfgEEewEXcKLQiUbOW5ziEEjiFFpVxypT61z3mI/YW/tg/RzabluCsxf8biQnnfhuWZMhwv+ORtSmPguH50c9LWof5PX2ycCKCvM3p5N4DQmHW/K1qrElLd+q8AbKgEL1W+qMuEJ0s+im+pD8mpXD2PBeHynxqDVHCHctDHoyVnpLX/PqGuauh3iABP/OSVLa3RJUeSIOFe5o6x+vMHvbYZoxStfO6Pv769Bl2mUuXBTn++0d1MaQxCtG1GsTsN0ktXG/9zo80/9+JpWKDh+Z/TF5UqFX02pXhcB5TvYecP5p/lTlOM3TO0Lg9Zg1GXxUMausseNZ7KO/Y3aQlp5uIrp55otgOIUJGlmQgvi7Yhsx21sAJPlnVOK1CNlga4gyeJuDglDWG6mENncyzPOM9wujUsRNZB0RVAo3UakhQOveIhnNdzYsEse0QbDHcPPu+Tf6UDF9Ipc+NY/raIZuyE3yWv/9T/VV2HsZqr0V6fMbrDOpx1L0HTqcIV93DtZ0F7gkGPkMpm6OMIqM+UnhfqUTxTEfGcghanl7/uDrQ3cIan2vSynvgHAOEV2olBChKA45qGrQxRNiR4vlcy5XsaxZ1p6Z7CBrZBMHA4gTk+wgsp7XOKSWtd2Tw2MNDI4rRCoMew15upI7FFyaMwzAMPme/X+qfveyXMZ1FPigUoWvIL2Gj4Eb1IqNWyIWt1/6/JF6C+es+RD1Aj3x6oEWltYn3yN8d/DeZKivoqH/faKJiRaj+l9xvaXLj0Xnfodz5I8fJ0XlwPPSe73ajDhDgqRKGZkMLsa3QYUjnUGG1y1QKAUy9Zfm/EaekmBgrgcBe4A0hIEhwrzXMecn2foUns8q0y3SaqYdeEGJmZG4SB//o+XWXPh9L1xUhgudkwIBIal7ZoQhrDoG2vZYjRWoZaEQpN2t/SMJyDYoSx4tCT/8REIRpF0X5H3/InzdVVNuH/eR8wrC4nXD+HyEzDVvn9hf3O+lHlGXd3KJdtrDR/kTUC22ajB/aMCgVGi9oXphhq+l786NT13tXkZ3ewd48j4OmKGGIsGJkSH/Dj0sJOwr34/e0SQfYto98pUJkwQkRX17qrOFYMV3EKZqzl2oPDaQjdnTf7cB78Xc+mc0dgE5oyL8iwUybP5JC1axj+nIHXfIbOZtNJoER8ebiYAeiDn/8TkJqCUAspqNP0vvZj3O2nX7nzC2um/sIdBUTaxqsDLYKZJ45Q0fhp39ZV4MzViiy+iYB5C5kLco8ABSlM9HKzVrSTQtL3A42TCQ7nv8U2Lp8AE890kQZVVPnW/sUxYfthdcEuL4DC9+XbZGOIQ/7+XutVR+ytzd/2wGuLB+YTW2EzNlMKz2BFF2uAj3NCZ0RaL8jdX0Z/1H/sPHpuauKd8p+3m8eQFGdsCxJZ5XnNI/kWM6gqjz8yotNqep/PqXA+RHN5RS/5dhENNBGhv+xayvZgcxORLmzfT4KdzENSfM6UiyOBKDSyxlbmx8k0xHD02jc8i2WWrBj5TDrw2ZrWMlwiptOj0UvE+iTza6kg9i1gmYdPE1bH2WkzxJTB11rNkQTADNhdl745QFM/gzAXycMjl1fnWlBbZ5Pfs58yozScGLM5Kd575pnKg8li1gD8mXjXaIrpfULGCd2fI61JTYYIi0Fazo2v3D1uA+o23k8S3lDa8K9zQ2e2lOfCgILt8TW0K6BHpH5NAx5Ffi3MV/JBHwcdwQ8l5IY4ogzX/S7wuaJCCWrkdO6NSwFciHr+RdP2HPPYVo5HBxDKeZkv2wZZ1hcepxjLB6+OEwKxGDMBs9ltb9CFalbNI9BqfA9gigbYIP2XqqfQtm4Xy7L3DDV/GTwtjezNiBDaqYBcmZUictFfP0A3MWglKxiDxZvN8Slie+z2vXGte1gxDaSGbUVZRbK4UCLdXgNcX+mxhYxmkLhbr7RPGO4XZ0fULIln/nApCd7gNJci0trAzCkRfFD0H4LC+X7yaxzD2AS69imBb4ehYWvyw/CL1zhMdG43F7PKVp5+E5MUikTeIE8jqUL1/bd3G/tC6+bPN59+nqhtCJYKVEzEVozC/Sy6rjmSupRl2yPqd6vNNmqs+NFT0Fc0SlsNo4HMmMzCMPaPWOLbvc7cv3rNUzAG/Tt4n39l7k/mKwincVRxCjEED2DxGK6p/8V24/IRedZhLkz8dKJrC/Z6pMuSainZ/mBZh5UYDKBDyXggTtgDJFO1azRwj4ISH5z5s4Xt9/I88IREepBKd2LbeHH1K0N9AqpPH6FjEAbAWHYbqMCgNjcq4TKjLFnQkseRTTzWZ9jE8ztpByxAA+grxW+W/tZaja9+sFcL7RlhJ0Da7XMP4Ib9f5Q7tgHOd9aIpVBQGncE9UaRbEx9Pj4Q45ygAVaQZ/WzIQHxFxrN8ODkWBXUVD0XPstlFSsfFsNeFd2FCttwprjywqF3WvhFmfaudpUebjqgogbVPtfxKzcylhMhIITl5I9NUIOWrqzUbmLARmdkGzS9AH3wGJu2wACXjcx9Jojf/kXhd13C8QbsawcUGpz94xOn4SKRiJJCQiLQ0uVSFGUQI0HimHz+M8iqjiDa/NX7VsfGkrZ74YEnhPDrz/2Cu1QtEyjtGQeWe0MeOaMf0Sl6eRnE6Venxe9H2YvC9ZyLKoHdW2/3wWyRVMhkJpKAgyqBGDtyhE2ChL/DL94XeqhhGyn9eFtb0Sij+GNtVnYfPMCk47ppBS/Qdgyffgdj+POsQ29Q0/BNW0zbmoBsqbuoqUhjrFv7Y2Oz+1sMByc8wwCrc5REYHMBw83uStm/AFPAdJmTAt2og9MDA0QRb+3q3sv3CwWUmIX0jH1uckm3AKWI2GWdm9I8KNgXlQJe2nrDSVruwUhIjyWCAz4ql1a2bBWLx/TFHCk7WLfGlU/UPtdOhNYepJMKOR/OlAoUzp9pSDTXh6FZkHJQPbo7EqZpO0/rKKLlJND26ZWnkCOUywoMLorcG/bQjW5JJw7mSWRvE9j8qo5pcsP7LskaWOlxkpT7OqsI80YTCJs889yqeltRraadOFjW4RMkl9sJbvg0ssz4pl+32RQ07TCLr+aLH6AZRe+QbnvUo9BQZLcHPPZ/80u+Zvz7+76KU+DdfmsXVKXND2zBDq3OK5hzCCbBw6STNEPakgLAADV/1p+nPaiIF0TIXxV/R/rdxkVqa21yOWDgXCx+dNt2OxUoaRm+1j7O/znDcpeo5qzEMxG/E99ORvsp3LzGSLv9IM/Vpxqb0DpEmND82/F6HwFrsDTOjbAAQGgnhXq2Ux5trS8l3mFKPAsnCzR5xQmT8DPiYAXDprGEq3RBrdN3ieLiLuLwEJIPI7uGAXk0PdqA331AuURjs62edfi2nQp5ZXd7YmBCBFtK+y3poQa5uEOSEG5lzqBY4/z0kBL7uEjnW4/qN6PjxuryfYKaxFRFV/MDHMV8me/xkAC2JpsEthcnRDjEpIoCVxhPXUGGXaP6cQgDNvsxrDCbAihVpSq5qbKIHec02kcUA5tC8Qo7yxNd3I5tUzL9buGjfGH7oW1yGctSsHmaNirmo/zOpmuVryCfG7i4ImFxGA/MaKh2vJBh/xdxc5xLq+2XcpQYjO0okoCQjgg3KgBT2xdu39A6Ch0Q7EdVdQGF3rQY4507MIWJioVF2yKWU33YpZScUFxORbz4lL6N0K38oj4Za4RnAJ13Ba6M72GZPdYo7MQ7R5S0zqU2Dwpx7DlWScn9qg3HAp7xPVLVVWL5iZInRsUp+YbSym9VjPPFT6sK8DKlPvphmogvLihcLtkcj2sUrk8+B66SHG++br2y2Ky3OAlHSppaNZuwb35I2sQ+6prvZXa/xHrhMkyjF0ioBVAFea+tak5bmZE1Qs6jo2gnPw8ka2U+hfbxyqBc+M8NR9s5yoSI1r/6LO094AnauCmePJ7PFAIPFp9SS8Ezw901yLo5s1seWhk/WG0el09CZGsKg/5ZkXAShKNSkBge+QKNoEQKQ8Qyi3GcHvWa0mUY2udUJtCDU3Nv3DtmSPSJ3LhERdIYr7kfoKxrDfxzrdfGC1pZpJXxtstF14NhnZJOmp2r261C8TBWgQ58l5zgM9EQNHo0W/s1agWLx5KraqIPvERDlxDU9CVWCEwGagKoz3WpPyAcd5QAF+uzX6GvomltNeOMCiJTZRgGEYPrXXVUCGRU8KupGF9hgdYxkjJ2rza2K24V8CIGyIkT0WSMlPCcI0MGlyILrQItj4F4wf17PFBIGtjlwitVPzs4aVTKWM3nKN+SMIkuGSKNElsqHULgCrZxBKq9pBrfhW7Dc+GIzJOoB1Xw1BuIGB4RHj6GNFqusUplVvjyWTgtxhLmIjdhd5VW6OB+tW2Uj9ixi9Eo7NsnCq+IeSxprw3IMKR6NVA4Obu9BSch4w82RzeMEE6K+KMffpZb0I31RiDqbBsZVC9KO7p8aqedD94ofVlNPm1Uya6dWThjd8QpjaM1+dtTS97ztY7e12Igx2AhG2zSFu6J/5SQ6EkvJbeBVWFMA+rPzxJgRTP8+RUlj5pe36+GfLFMcTFjs8Se9vg7FCUFFmm/q/Zp9FqDNGH1rggSOaN7FbXVRUC7zlHuuLExyYWeEyokKBzehO+DEDD2o6dkeXtEPalNQt64L9cJOnMh6TiQAbARf4dOIjqQ+6080ctzw/7JLlkQSvqv0ft9sxmNi6dgtLVPJ0N1UDfHVs8pws4dvb2kN2BcDDiU6lvgvspvo6skl92ejYou2AwDFYBImSCPhepfYJNJ8veASMjclNzNPZzcxTPpbRTo8CbCZW+F1eOYSUidFPIz3LXTVqHAYcZ4O3KrxvX33KCJUFuqMVbCoNxz1TrmTdLyo38uGcT1g/dO4Q5JV8DPSr3zIUDlTdC3G5STkJmSHXN+IB8vmXljYEalRsOUS7WFgq/rsExSnUfO7cgP+kKaMEPjxIRG+QJ5Sj+05TkFDH38OkhRF+a3rAaXKlFrP8kQr4SSqZByzqRAJ/wfksa71+RxBSCz0fbSKQxO1MPGgkUpptdWej6vYf71v+urQC8eogH0ld/OvpkC7cPMu42AbtmocibppSPJqn5fOczfpPXe0YdvmhJl61rYv9aKRQ5iDSK+dnnL0ZydI344btlgwNo2ZvgJ/ELQjG+ftcAWEkRqerBC3RKhmtNotPiNuJNSjA3x6sHtH0AnEZCv4JPC9O+Da4DrWInLTgkhz5dQRFwJIlyjKMiBcf5UlvXPfOCapRXPXPQCHVy+qnff4OQL/NQNSJlNxocpkav0olBDU20lkIK85cuhGZn3CToEwWJPFhOr7HOmemSE4WRXBXf4JzqAYdAfiiTdgqbXLC1PyaorxiAmeC5DH++Ih+Fz3uHLWrfdLR4Bkp8K4e3+ZxH5V2KtU2VVdE2u1GJgJM8uEyATAggMg6opPbGayw6hQByOEXIpnX3dZAhzX+rK1ptpqq8SmsjGxWzRGJc4lNxVBqFxf1gtXt3kemmKUd1+UfbE0a5VcxVGUg1p+7jTC47Vo6NdUvcqML5Ndk5N8EDZJdQgyGkVtDiM+ZtRm3fUln5IvkJpn+WZUjKfSHdF5KyELI3rQOi/vKyTVnbM+r2gUuIp+220qQfXLvJRjV0fGPDpwMBNcr7RC/ZdCNr/n/zYTVcQSqjWwVaP8evSJpWn7oYX8tPIVbZqo4YGEuqf/7yw6wlvLzcsHrmBV1J5+Me2DqumiR6w4uMcY1d8vJE3GwqGGBEXhzIWq5OTj+F6EjmUi1rTQ6p2fdl+VvYymA1OBZJHy3/J6athnXtbNJdh161Q0pKNtVKIdg8Cof0FkUgDeXV2DtpSLzItTL3n/BXXynt5L7y0XStourDEd7J1KsCFSFEDZMpK1a/ssviOowI7KmfwgGmxRMU/as+ydnR9FeKawdnP/Lzzn5Wn0dZSj+fYAaXrz0p4lcN3rJ7hMEbFdMVai3d8ODkfupTwrAbUSt/+TgjUSrpQXpfGN+n1Xfa7btmr1Er75LDGGakzysvxRFnQ1+GiROpkIsudNj7r+kLtj2ZSEJryDGMWYoiSB4jmj24+bSzTeWrRihpWc4P+cZxg+nuI3C824VDy29tqgSSXzmDhcnJbs1Nj7oRZipSdOBE7fFcxX8oyOZkSuvelsJ1PhAGwcfAJwyMkSRxVJT9VeFkEs88maTyIBLzpfW/gHt/ns6V6TwyxkaZ3U4iyEVVsODipsodV0mufa2Uckk88EwiXXvfcX9E11cXekogJYRZ+ZhL3pfoaAC7MvmBAyGsZTnlnhwLXT/hnaSg7deKa6JGwZi6orybsC9ni1AuL07/urJEhnl+REKhv47rykR/UrYYsVlAQ3L9kJvvnmH1lIKIt2tvAVHqkGsYax0Jel4izF9A5N42eNi7a70+uJ97q1yghoC2lNESWuJZ4lu6HQEIl/J4WaSMFEy26wOThZbKed4hBr3PkrZ2BV2s9HhCk4tHpB8O/XdRsWpJ+9LmOISMNJdd14cg5/NgjZ2FxVbkL538RIsv7iYnOZT/0NG6AVBApP+aCPkhAnkXUQt8Y4x0gbASAHqgrJZHJOcKuwoeuHRtwuOaFfxtfUb5TlPnm4nxXhYs5DsYpBwsLZBELEibzQMRtGVGOoAARd8CxoTPXVuzcpigO+iLibfT7tCoHEWCsiV9tiv3IPRzCWhMquIDnl1Uo+7kOIgWxTPMtvExHfLP6pd2GLW59oN7pRtEX2hAsvm71hy3Zmy7ib8+/KKPOM1hokSgG7Ex0lTdWNa1SrH9AQL5sYzE6F2xD4oqlJjFrpyk5dFm3FISpbBlpz+wN2JR1/TsLcWv+1GvzYcPxW0D7ivDMLNZ755Hd2GFZS0nP6lkK3e1S2Kcg68Y3xdwsaSx7wXoAeXZndQpyoLvJQvQ6EzUrgKZW4sUoeGbya52ApZNS61cpHtOr562PJInLmIZHQz5fh/pE43ibiaEdT3mwlVsm4/uTX/4UTj1vAtCMCbQIs4v2KOwBL6ZYpupkZnfXdrKomAEFKGSFfBGNyq3ftoyzCxaZjpIFHvQjisISOQrtJoOD95cgPOcYXSo/u4rUPYRHPUDOBbDEXR2ggReKixXsxxcK97wRYX5f/6Cs43Ecx3co76ot9MqvLtplHljJ+Ympk4ZbIhANUR+bNe2BqnemLSinK8HKUfWt57oQzkae4/Zb3tUt/VniA+eS7qiXHJBdoIEIMH9a2PfFCIes2VovPXI1OH3jzfy8pX4JYPoob7NZ/QeYAGCPiLdrbnqkXbrxwo5nY8lvmu+waQfMdha1TepcQf2Yhs/dDSOZqUL9e1GPKgRQi6FNTZuaaIA1A7KueljaibYRjhEQnPaOUEl7gJHOc7suXJ8jvX9+GzpOLOdtehDoxlztwQcjoZlRby03UG3JNLw/AE9hO4vqjgRnca82TzD6UqmUZJVFSYu3frkcvEcTPoseyIlfmZrsqmW6lIuU4E0FnkE7PbL0HkyxuiwPRmSiIVh0beiICJuuJmLpiDThpDSB5Ft1WnlfFKYvPafM6GrkhQ7x/YM3ejzP+ZwRXX5kUP+WNZhmah4pBmHq8Lj0BdJsbH4l8XNjgzXvjrCbyArc84WG0NJMhGFFwU1nNrIjJNI8yP8dV4S0BH3yCDbuuKhF8kpJ2cQEeCLNHoWTM5bZvW3Xkk1qj4x3W+uHNuRbaj0G2as/YkockcAZKUUynW/IpOuJU+Z6BFkMCi7pnXRKitJSMui2SZucpiDq/3YGmMUmOcvRe6OTnZ7DutjMHdwd+K0jd0r8ugmleGSBIUi+JF1vKMG3kkdorbwLlbqEs+X0lsRkJmVoR53EAD2ZDcoYXRAp2UDlpbHTnyT6yNU6tIwAFP4Dp8VmLYMt/kF74srC/tbheQR+CxwzWeXqx7lDu1rRvTgupHu4zuxTJiDiQvcsb31WfZ9WZURVBsWav6fezud5JtgDNvl4cTmq0xbefgicXCyPZgfjw6Joa3HhYO0sxTYrYa2w4FW9iCrvzqvcHLV41sleDAEWLYNaxiFokmF0wv6PzMBQTtabUMyF+f4ukXR4viSj8pjLzgoB9eiwH5PozsJEDWzPSxoFolgR1lpMP7VzDsEbtEhJuH0MIwzk8umMObSez6rb6xBddLkU1EBIT8/jZIJ0ZBUjjC5oaHbQRsjzaFmfQtM9CO1t3Nl5B/wnRZEINoZV0aHw0FFHY0B1XKnRS+LFsHzcuHB7UWBQ8Gr2z8JLWFGilN9osa5hRvpOBDpiSKmQAAzflXPKARsorQbw7kxhVUa99vQAb3wxQYakeo2dl219LBlfyrU6vkX5DyzCtq6MstyXfd1g2ligPGdeSewLmWGpm2EujV4Hic3l66/oVQmuq/INKsLw8cro+GW8sq2UsFnB4qlsPF8jaall5W93VkzYhP53pYX8KMR2sH45CU1+RgZ32jAk/L5nX/NxinxN0V+8cvUd3EoU1B1mrZazblaG0hrSE+5Ak90adCy+2Jc/ATqHTx/no0VSEyHe1JIdEDlAgq6Mpbb1RRqdtKBVAloA2BniUK001Bj6EH51S9NNDKnIIIfx/z3bUUTgm84AlrEn03msRfA3duvqou3be0NbT+Pz16F8lEH3iNAnfBJVnfOm/hM2/uWYH/gbHPyldXgH7Rq9qQMuMnoiKHP8Z0ZkUALuuWKXiSQcqp81lb2PlKWWno/PlxthEDYUrGlKo8UdWhSRwAqu3VRwDanktJAyoJX29veW1OrWpToAZDB4x8Ke4t+Q4l/WBW/pnF9pmg8ix3PxphYG3AxMCBSQwaBXIGMFCSUBu1rSD9k6pTgQsPpDfX3gpkg+784Ob2LnM8wcYgW7VGHfseXyOrrmet1pMqJiN3OQZE1mRjr2SZrhtQbFaVw7stGTwnAEv/hQ6rtcautfAKpytl4XG4k6Vy8+gtH3d8eezEL1l3WoJUxMfuo/ddfAcdewVXWG1ABqbiT984/OzQpV7vTDxhY3CwRQaA3lSL65kt4FZC3iSJapXwhlzg8E75mVpg526RgAWgDl3EgvyvaGyYgPOPBXf31VAOs2Sd6yyDcaqDvksfXABkUZ2BXgykpYOjb0hJR695lHs4cSj9ZCVZ7B0ijK+B5eVRAbpmqnDd/qsMEefcSroGacy9o3pmfIvy7XCQnAZwZUS4zFXsbL6nw2ImjBDB0qjfHOfgG2yBGEGY7Q2Q6lNT9ODWx+Zqeh9Vk8sDekxSoaNmzwkqc2ev5acoL705YQmQE93/4OlJQFc0jZRzLnCuk29qOpg1g9B07tmHhvxv/fi4yJmOiU7mdUfZq5//DY92j+axLdcU32N5bciu3eK9/cme68PBUmrpRsgw7Qp/CsV/6yQV/YT/TyA6pdVL2mVDyGlei+vJXo39z91qjBllqDHDmY0oQhp1JY/U7fhbD00PfCNAf1uSfFAioHS7kmfKmo8xBzvewXoM+byJ+CTR8XAY+A63cwwzr/K5oaRuXUDksWSghfO+oJ0Nuvn0vGwIBQK3LGS98DnyRiwCN9kXdc6OS1veUhrpDoiKN5nOcBlyGJEI8lhQN20P/4lz+HpZTZuq71pAuNUuJnxRoxJRaSPwbBMYkq8eTDO/d/P2zadro0ufl1Z/xjw58nsM/t145zS+NHaTJv4gF/tHlws9K5Ym6s3efJBAZRuXunrcFayJVyQ/5zsIcGC6L3ox95/4J5B2LKspYthduJ/UN2aLuz1qCFSrHhp0Rz/qhNgK9wukJHUiGscRuaib4B09djJsiFSlwkBAj10niRqGKL5g8X50+oLPKyNnhpDyYbUan2wEDtGFNNu5lq0Msh4Ly+Y2eEa0PhqKdW3AOzGr1lasadNJFFH7EWagJhVCkZQXyPeI64nXPi5Mr9GgpH3SmzP4+SPasqH4JdfwN+5a4zkJJUSO/XuDmxpu79ugx1ufIwmW5xbOjAR/UuGyjmVoNdTP34jhCvP6TL4ym06ExDCofeNIF6d06Md1fPhzLjA/MZ8nE0tkK9/Vh1DmpRKSag8OFe7DL7sAhK/xLcREvmrtfuRzA+S5NbWImrV1wCEh4xC/Gfil589qKouXis5ikdW+HZjEfaSun0E6Y5JGYKQZRjnoLl84foNyxSuOIWAiypaz7gFMowJ2sK6/Ie2DoUH1qjJ5JvlWLqQpnx/5kKJBxxqAXeg/E6xO0PLdpGZ3vF/NB5UX8gFLozYQts8Yu5Vu5UG+TwZW6KnB3r7/Ek3Otzuj/imT+w5wbKYMFsxlqUUoXDPmvyyq0g+6qCCnQwwqz+LMqykqZrYdEYKioZ00RLJJjA3XHLtcBe62fv3K1EkyuYQAtApuC1jJkjC6F5J5nJYTqrZb4gyukf7/MN3s5qG/UjkS1K8RLEc8Ek8y1WlwsN5J4fBtLe08E9wW8lQ3Q7AqwXxroIINHi4F1xGXcr9vBKJqJkvocHxSTcnaYC7gp27ol7v0AucFgxWknlc2Ss+zQ+5vgqcU7odIrDcpqUHIASCsv3jOsNAnL6KADMZIf9Fcuh/Lxtczf4IE88t+p0m7/428IvY0eguYGXqWzMUdONVG3xPgVtc53hy7T6iakrFEoyjZC7FjcrAcZbUIyDdAFscpS3MaE0IvI/53RZX5XKAXzZtYHDzOKiArcfqw7XjTN7uQpZJj0v203nSf/wvrZrol2F+ZsNp3DbUf4Fd4SUduPFuYVHeHGTm2IfKJs5ulGpxaCnBY7NtYBsK6qtpOd9WJrm+5L4ToR9T8lMc+vUkPb4hwjYPLxRsASQ/hdSRKjiIgOnhnObYc5gXKmf2hRWqcESZ/rmVFCgI119wq5tbEPgookNGL5rmp0YrMCmYPUgCOMlcl13+nUiM7Cok42qceN+iHXjzZ3Eti17DTEfZssziHCFNLydYS0gLyWbTqd6xU8iOP8fYn4PmeOpotsHhwCrLwryvMGSCvWs8h+9n7wB2DN3wPX5hqf77sWdBR1ilL77du5UqtvHSC72Fy6Yd0P5F0w9b2+8bB0ZcZFUiFyKrK0df9WeNIZFs5sJHTABGsG0rNxkNFocDhlYp2ipYQAYSzgpNP6fkMbnrZox5C8jw5j9oaVEHnH4E70YwZsJWFZNO61uExc1h0yr/LnF5LvrKrUYqE6gktJpsdslwTrE6+lHhwv6J8eM6n5pKAUnRhxRvz/LvJWUkYa25lraY2LL2xbkN7ZgNzloNYcxdrMOFmk6wJLaVLtGzkc0uBj1bzENuDdantqCaW03DLF9ZnoZwLiUioVX5Tmrw216ZHQPjEVUZ2oK73YOeaK6JUWUWteuJn0Jn06WSBve2RpipgycujJHoROHU7YxnITruJFNeuidlH29sbsTjxVYtPuj5wi8SZLa7KL12FKxs51p0sqWLGDWkux508L1ZRAhKfbnpCTmns+c4X52FkRMhnL9A19dlRITlzsoFxFdjG/WjJ+1xoNswFqpMIdhaaB4IkH9Gq5k2a5fLPKRAsMI7+6Yw170wUwZmcfa0GFI9FSyzE0i1yTDjwAWRIk91HrczfX95oWagqFzESXiOWxJ5AK3n27DvoM75RPf4syCEE6t3s6A2AGJnYE+4ONdFUvuPwP8B3dCQeEqli7BeZdEymePSl0ZMJIuXfx2pOJMuQ6LI/0+T/wEPHAkK798rfoLplMIJd1qOtNpr3xGOt9AeC0HvEmIQI1RYU5iT3zmD2Wiku3HRFax+cMXMZ6+RGacBCaRBhR0SF5BLXIJHmYExpBRmcX8XTQMEaCtX8iMxn8iBVm41vI8Kb9iu+dwgFwFWxfvSqKV1GXdTzxw2bitg78j76H/JZovDPfegaqzlep9t6nPhRuc2mIdQ4MZFV7dYxDylOoMfOKA/GdVy/8ehin27+6ZM3gZ2gbuDHM5cEejbHLu22SFL89Iqt6pSlZ8KdPK9hlb1xuj251z8JetI5L1Np04Tuf3oWv/vZdESgIoZ0fCQqMqT4ok2qD3B2Pe3Ee4P3I3sRWD/Fh6KkZ1ibTqf5+S/NYpufY07NKrLVPOZtH39FhfEyfpLaYVLBHq2S+XLyyXytV6vKyeHfvkXvDNLXOQHOGE3O6Xd/w55KinyMXyOY4i4LlY6yMo/8GquXF2urlPApf97ItEn8KwWI9kicdWmGaV406jKGvNd2Yw7wpgJDhzMnieq33NbVkmAcrP2eDjV7JdMQ0b+0JjR4bl5dvaALKc4v4t0HsGI+Maq0MpvGDaRH1HnH8RMiOfivMkHdPSLxinq+b5/XGrbW7VwyDQZhbyY6xh8jO+0tNQFMFeH0myQsqphBlbR2+3Tl7hSBX3GQL7tHHLYnImUIBxgeMWZoQ62Y7yhSXRHy4rmuwZJNQY1CFoJOELcO1rQK1gIOgXej9shIQmVh2nSwRyjtEy/HlnR9n5lJRW17eqoroDvE1LndpSgOUpG5J+wqNMSHGwoiLvcmF9kfYNHbHJ+9QhaK3KncFJCcsQqj1MnfUK1FGXh5eiHT8rDsUXcqNqvoXv8l2RIWBOxwVfAAJPLEuT/1IwIO4Q2gc0TLp9XocWmzNmFKbSMSkTdPmppPmyl+UDBnYJboi3fl8Xcj+HvisCJ2oRTIt0I7BfKTbBpz85P1MJ9R9V+bSWJYdWLOf6GPcEu8ydZBe/IY0XV7huBzMSBM1axcFSCiypmecEWovU9frbntvEU+JTR4cx/+hqp9uA59Yw5BTEFOF2BXVXZJVSjcBClJXuvqd18L93KPYnJ/0LX/l/H5UgKMopKynCqXq7VWSRnjrh1IB64QnZZf9IQonlE78kKkSHNNs/HATy9XyicndyhG6sX/hIh8xHCKDOaSyNDuIPA3oDqa3zOBamLrHuJ0ZZcEOE6ZHtYVw4C7liUWItP3xb71uaded5XgF6olZnDrvstgiMrcUdjAdBDf5dLTq02vG9vTcfebHkwQ3hk5D3qDkx3LjFt/p7m+ApAK5cvSSFNC23iWWq7McuJkSPS9/UjdxZWRCcCQi7pVJQ1hFCGd5tAIc/qFAFMQQcY6eTUm7TpAnw6waLlYaU2O685qMArPXtZQR9o2c2DrIWXHDyOVzvLFEUgebLawV8xLEwQAHnfM01uFB92oNyZkmdC3vGW7PEMVeEXk0WYZMQFiuGI+Dcnq2KtCFJb4jOFhePX5nFUEIPWbhRMMi70nnENo0L4h6hTsJZqywNrlfEt94p6zWYsnIoPt3DU5IyrOSfteeNBXoal//1U+tHdjGbdDawXye8TLxu/A1WPqAHdg/Xj7bXDuHPIPMWPS8yF2nyXp3X6EcvaZlnzQc/05g0z0xx38dlYJ9ZhuEvFQH6s1HE3MoQArxQ5ise0BtNyIXf0H/pfM2Fl6tKMutpTPJsfaK+1sMcCegOKdn5DMapIsoilV+Sw6jnEBHeBXaSb0IN/xGvR2vE/ovm/GI6aa7FZHJH5j4WCnElit3IEvJ6iA2SLP/kWgwT2s4TtEN37hnEzgduqOaXRHP/svkcLhGPOkWO/mZW1ZZGUebuQmRL3INTEQVpOMy0Lz6FLGwvFpM40WktIG7ARThyj2V2tiKWSbwF7N8xhQ6A7u54UM0K/qGadBmnxurP7kMhH/q/BZdWK36yJxv6i6DphZ2YCuruEQ489235U55/5UYj4nvrA8JLrrrSO6pmT0xRC7saTZs7ejupWhlqUjdwINvYBeFRHgIXg0MBOXsUcZWqVj9u9k7XXhJaXHPwTmmPoXltUf7bvl3qIH8s+Pie/sTQzh1Y9xp2qclPw14HGUJtkERwz8W72AQ95aIQcbYy3LPTewufkP2DMAHbb0w3Agm9UESY+26hFRLC27zVgFdZasAFVaIER88Gz5goWjqkDqIrkD5R5+6RUyngKXhynNCiiF7CzHxtu6jIGOWfUzTy7cECIG4xSlNM8Vk5VrenOSQHWxz+QTAomSjFORmkfmm8kQyIu7JvbLgJ/ORXegT0bGDixXk5CpzvfCNGPIOnzssz2wlHxDecCn9zHkt64v5Cfp0dju4RBsF0DBAcK9G/iLOHFVWCNgVMLYpdR4ZX2SxrD0HbZg6dUMgEO2XolX4qyoQ3gS+u61PXxRaoPdtgWxokqCcqg5y0YzXut0fZ3em+1/j4jhDSPJCd/tSFDjrt+htMeffrWCscljUKVRf+MxArKzd6aKrxZWqRPpjJSHu7FmZrpqGKB5kCtqv08qq8Z1bcbKo1zfYMzfxp9GICrp4PpRmCZ/wtSf2vFiiiSdQEf3szQ3rNNjoMGgzxz/L7VyfhHaSFkJ1Rp+LrsJOgqeoycW1DKIAUenxcExdpVGGUJ/5drS/CKZO3j0zdxSBPyUG6/1mjp1ipyLheIqMkYFK6l5vptIwdMHeYzJaFz9HaPcu31IzFYITdNY3yW1tZW8DnQLwJ0ekBHUFu+6p3ckL6OQ6a11VR9XIGmu+CIRDzBZdeRIT9aFUe2iWsMbHmikyy4gjs9oqBvWiAaOyyF+yglM2QHYOtNStxM/2Qa8MRv/WEletEh4/YgKDab1JViXx73GVphgqjtAM0ui73f+rKqq076B/U476zfvy6TDPW5S3iSeagVXDpAWJdyYTr+UWTCrXhzSsHOObSvRig4U/ZBfsvtyFOnuOqRbXmNkDRtRzQrBQKFPfLCihI8o+WrUEicRJdFS/agoByEQsNkMbgmmcQjlNtKRGnC3HapF+TFOqzs5Gb099w/fMGQdfL2yRocy+i1Zc2A3OwODIUDfis7vOAhdb1vvNQiBjkH7EajCX5JaaCll/RYpeRllGtDbbQGAi2/WHCHM7hhVDof4D2zB11e8U9+Yz+VMVvwFHbPLOnXk79Dz7NmNKmiFxam3Nppm4g5lI2bni50qutgHTCHH49ZJ0VTI5G+LQ0Hcp3lYusGLEeXWScXEKLnJfcRcTXe/YOcggKTHrjawcAbwujb/5sRv3sbnSPFD0z6otHQGK1nxHACEjjAnSnjluQw5eD7wumwjoV8rZHe/ZmlglpLKpmnD3YPWroGl1RiYf/+3jq/bZOEzc7+LafJASvaRiPWWL1jmEQKMyHasYu9XMvcqdmtLYGRdtMmaBnJDdpp+0cQ4Wnm7UJSNwPRB1GjquAQ2dSMi3gYiWfRn9C6fyt/RLbkDTSJyYXwHOI7BSzZoS0NfsjsOtk2bJrFspf5RRrHO/8qa6t/892fGqWmDxTFD5XhAuxCImYAbvAqQj3AMmrZXrBzyVOVAyDTnoFoIrEHmBng1U24A9Rv4Cz2AR9G6GDbkL6Eof2Gru3dg2Ve3VmlykL30pIfDGvIZXfewYHrUUdMiVHYsGXL/KMNGqK8r7VQir6k6QJPKpEYO8k0t3PJ3aglsDtGuh+CqvNm9ESModxUJXRtP3e4DJfkiWVIBwQNNo5Dm/g8e5eV6CEsx2o++F1dAdZUwX2e7YmwjAuURlQyZcyOLWguFMMp64M/zFKNGT5tPcbwcV5FcQdcnvpV0w7DAI2coVhgHKpHhKMS/qa3zHIhgnckwEXmPAsFbyODy118p8cl8W0SjgR8V5TFvlRO1sxBebghdKpcxtT+DrGWoDaZ9SJ4w8ayGDkIDTDDgbzj7HLWcrEBdpcWEfdQqlPKhuO26jOFcTRYcIuJh+R4DEIaCTdY7Wqd0x3Vqi1SHeoXorxT7nuWPK6FGoACHxEW70XJq/uaPr7yIupnTmr7XP2XeGira9ocgopaKruUiMlUUmb+H7CTjBPxgfWTI8aen4NWSch4EiiIN7AD+GyXYIOHn+oz1kZc8W1KWFZttxH6NR3RQmWAWqN9K2H9aWtdCkbMGTbw3uNtYU9PEAr/OIyEuM/Wo46+Fk5/5gNd8wLQ0wWWiDSAA9xbHJgnyX5PMHAWMo7JeYRUDzohNewK4ZbQZ5h4YM8bnS3TuXYLcbnpTBwTzlWHUQVQ1T9Hnsn5Y57pUAPyg69XoybSszGPy6/ASyKgZaUXgQIbRtX0MHTdvolbMkv54bBIX/EukMg2OujKNMiXbA3hCcfpm+YzLm8qQwxK49fgSwPvC00XpttvqxXWUujWDVxY7IoXAHrZBkfHLNixfjT7/Iln3+EF1qTbwKY/CQ+SjyLBddAVHq68TrSTaXpxYmUbp+KDbgIGBKMTONYlVjwtNrcgnxUGjdulDWvE2PMuL4Wq37o2GEBH0vK1F2IKInYo3NkTueY/N9xq3scnv8NAHO0tZNXT/0zpMXajhwUaDEtATsm63wezHb/FdbDKaumhv72z5qYvZYPALtCFzHXlFRJDpjrXvyUI189Lx28dTAwJ1MrrVTna2YZz1GVpkKC4+tRBav5a0wAoJFYRAbDfxq/LkuL5JLAnGCd60Knkz8rhzvKNwcnG4eujZ5kXgwP3UmZdT7e/xDN7pRP1bexyHVc5kRiCWMp33zH085FsHoQFSf2wEMibDdXWekxL4UR74ISlLv/VSv8tpn5geXUSKKXkh4YnWSncShl1sZXZ9zJoj+os35IEOexhsA+sPYMgpIibmirNTOY8n8RSQqgFa6a/wYnSXddKOjUaYchDkAP+3vkF7HVYbegjh+3uo3z4Ej1HpkuX2Osh8hHaKgft3PQjMazAKgyjsD3jd5pyja1FImpv6RLDaMTt72k3rASA9oWRrqV4SynXLK9X8rkCushCB8DYbYRJuHylVW1TASfkOGSbeiABtdtOhx/uzEMbcX5GbmfvHWto5s1U0cYFsVYIfTxVJJmcWeWtTFJIAZtX3tdvPM7sPF8YeBsY0RetM+HaJaicEHKd4SH85yguqo+5rEJAmtngpBL3bxSM9gkEYuz3+hZy6Ar95/IYo8roEsw0v5fXPGC+Ac/sveXhlQ9KdE8Af0teMqyJqhkGnNNYo2+13ufk6MX0vmAeM+fm5yMpAZCSBRyIquhMn0dZ/gAxGsutkBf6Ehdl6BBGcHH56uOWWchvKis49VO1O8np0XxwmJJiRbxeq0VmkHwAnLOgqH3QLs21JTN4VeFTHsE99jYojUF7BwSWwt2pvPbnMlaja1pv8X7KuP4IH9eHNDXZZQnB9qr9cy5l3Z9TPbkvjWMUbOWLDaVOmvAHvhgjkLh4FcERe8U/fXI2SNOb3gmTPXaZiJsV+1MqjnbWKoTJ1yPNa9Ug6+RnFYfK4CEGihhT2fU2VAaRlOhEA37Q5m7Oz68e6OiaWQ9i/Vor506OA+lFgbbq3O4/T0M7Rk4LWcvnQT8hddptyv/3BmRpmUuozDZS98pe5CxH4uffazWRvw+hE8Mxp8jj4ik3BARvh0z649Dx+hjh6+54w1zjsTf9589mZg7GJhSfFILgeP/vdorDnB+KeuqD/RvcaXZq41IDMJumXtj62/L0TK0XYOyYEvCUrf0RfHmqseZuvRoq8kOkML87tmmfV9Atdyvd/W8zkZjJUEq5WMxtBLsbXDXwU5rChEIMjJL234IxjludXmqSMrMpzyKffUDd+4cPCuxL3qynenbIF5awcx0Co+9qJbNbSeGhDNbbh7e+bEsB82J5FELWhT4uccH3vB8HsmRqqWnIzIjozyZkNo/czo+rRCeA6W5aimOvxyOOFD2eGGecnvZvrI8rSBBp+Y9/v3kllfQ8w4C3oPaOiMxoOnjQ6YaKpRr37GQILldyfCqvOZJOBRHx0HDUtON1V2uHAmwjtmvVGn3vCevOiDsa18psj40RI1YUXpab8UptKfbSPEaFhRdIx1cyrWSQ78FgFokPh+HlhnQX8mCslYRhFeCVeuHo841hUFBkDZSai4bwYaqLvP2t2gxQ1SnbnerKx38WXRNKmEFlskLYRlV+jVVMbONRi0OF4BB0qJRWM3LEMSs3IuXcMP7a0jgLTwszZO16Bd7vClIUl6RTNoHzz3nwJTdxsTiURV/Irp4TaiPFuTNGhlSVjO5o4nbsxyBAZv8G4NbfdX3b0EU/0vnLicRO97Q5FBSAtpdIOuunlGK5//Gt5TqXu6B14ocIC4MM6e22fgdR48mH8qk4nGniSXnO2I7yH0gI6DWKaCeJM3PELCPfOF7wYvU2ViGc8uq6fWs3T3puL8gwQoNcPvuvIE6/oFa/y9Yq0Axt2HtEi6RH0+x9cCvm7RvMUpzFIh9mzz48SEyvSs6ZwyRlSLJyj1ru99YmyrOUHZ5AANlx0wc041GoLhTxMXGdenQztlriUZ17belU5DGIfeW/vOvKbL4zVFODhhGKgpI71tTLzQKDXEakaNn9AsL64fC12JpuWVHwGQIcqExw1ri+65TcDeXKjT3wYZyuEm34T8/V4iiDVeQ1b3xBLQFTHv5oyb3K0xgRCVXGPVjgF7YJRk08lEh8XNIHFzL3CBt+YjIyDQf7DP47Z2VQfOFrMM7BtBowqJC++Sk15vnDktGgIvVme08vTyHZeRi1O/t1dsiuEQKCeAb+OSw4v9DZAXu5SIhI2MvUcbDY3lP3GLH6j6j9WzQ2+VMCfNWCvVovEXryY/z0UCQJ9cWLVv5hSFB0EIg2QUIWOW2UD1LlCRcyjc6OawXuRSVe+H5Xv4lGxdg0wo3Gz3KNgIUYPJBy2+OYOrR/9Q8cTIN6qFDqV401OFMuOqZ9v0YsU6hE9tGXwPDN77X8q+6d77nQjWXePOpnKJzjcT9r/C+j0u2I27gljp0EZNz7uFS3iKrTGivrSDpiS/QYGmZPEHJL68ZUyXsPzxClTBLzrNEDkU7R2ejmZNAhitQ+Tza17SiyT24UcfBNb3G/LqaG0OhLkfwmAYf/k2xXAD4OFXyxoOFPQhRdLr+n++JNV+NmsSkUaan4JTfzMReh1xcvZfqkOFYw5s4DTNmVl2Ih5O8qxqKlC7L6F6ttQranM4P1N5Tv+4WFw7kPxRTmrkehhF9p79y5+QgeGqcmNeGjiYkk0EsZE2PA++1Z8eg2g0QlL0+gluJ04PmzSouhKpjwv5suBU1bQBVQtLhsPLZS05b0bPc5d3NmJ7G/BGXi9UL5OUgsk1cpQ0a/nTHacO2jvfSOX6PbEnqyfhuciIAM/tFZqD+Ow82brLN+zhiyrKRxA35Epj+D+VyVXoe4KD3NwpvVC4wGInw7FYSfTFH895qPl1K33Dn060pkwnGafoIgLsVH7VPMBOyEDqUf8sz+wEpSfRFXyQCHQ9rVp2Npw6jMspu+kENKXkYmkZOZutkxo2LyuokvGuanj2UKxBhsZkO6A8LBZ6Fbk8B50+g2hNJi7znG6s7jvi9MvZXHdCf+KJreOnBgvK1kEqcjcI47sSp4TMw/F2969o9ut9K9C9PDyAJun68Ns+gcIInQGBkZwrbmrPuAZsYRg672ua36KqEhfjBVEXRVgG6ID+55Lq+lcHCb//jV9z9Y5Ew0TuT/kWUKQl1Nmj+KNoNisxtZIqFumK67AS5cCPkTdkcK49okcW4knVD51Z3K23jhTRP1JLuVDabozqtwnZEtStzbZR8Qts/kNyi3kf//eJUqscDqBeIlFzERYUTGh7Dww7UtfIO6pnI+N+z1UVbdJZTJYQd0T3E49UithTQpVASGOQAy8MjJQhGTd7M8fDUzKtEztV1Yet/rM4vRfE+yotU0xvlBZhYEer++IBC/jMFsR6SiF/op3s6fIF+iAACHfHkt1iBKotg+nYCNuWUtB7Q3JnP1r426QUZxIjfKhRiKoxXYFhldLQLDMLTias2l4JxHY9vhZkgVuKjNoZ6hRzotXQUUuA/6QUDy3sg22O064uYrNWH/Qqf/Y1bxbE+PJCVothDNge1RTJf/nAytnOEpqYj956/7rXbo3yc/N1gDvUhuAa6z0fLT7pOiP9cD0T31oBI679Yn7uV8TYZQlU+GnVM6JrKEeqoWAZQ3gOpMvosnISL3BhZcQHxft+1/HkKcNNynJgxnvurCwRHsLts2J9DchqKNbhHBt92AQr37K9MY+G3Ltv/IAT/giR7Dm9vypZDWYWcQRHJyUs5mQyC02vOOSlLYqrM4VNJnjPQ1b0SgRIUT+yD09rpeH0/YG+oq+wATfsSfY7dcyyoDuvEKI9Eb/lX5gMpm15CtNtxRvl+4DKFFS8+TdHwgSVKP9XPKHB0kUrIrNbxybOyVokyMW0liT8M+M4cy/4I2f6kreHL8R9vDI2++kJMW0hUxqTLyZ1VlGxqhlv5HFoE7JjBt7ZiDlBvPwEaGhftrW12xgi1xrvFPhbWgeUmZvemadztcMTV1X/W3EwwweB0K+kdb4XX/E8YD216EcnExkT1wbXUNkEHGuIFGgYyQwp0l+LWxcNrkXfVxF26dVJnR4jdqVyxRGuoQu6UbDRg8rIObAcGzUrlVNwPssp/7r/jx2DpMID7naoMJNSf+9+mGA0vEaBJqS1jADT3yJH7f4m2Sv+t3Y6CzpZw4ffaxxXsBQn9FRChLwvtyFzrTJorlv4V9SczKjZm/RnL/z7vpPvMT0vFsKRi19uz/n12cYE4NwEdNSlchQPYEj6kMGC8KeCfalbrtfMXFpbY873an1oN3RY4yaKEWx+z2Vdm8hjpbas43M1C8ltehOiNcYVOAmCL+u4yQsRfz0hQhDGmQf6v54ic91juA5L9EAFTJOm1QpbC+DcL8SJtcs8EIo2eOd7sThn+CoX7xQgmIv+Fmpc2ZR/yy73+I7cdTydCOIr08OTJ2vj7qA3uHoOvrvxx6Ae4D82BtS3c/HvKwb6OKlR9xRBGpGZqjlQZXD4POfQWus/9OvZOEOLAFDxsAtKN5KPKSYr+7v6n6UY2oKQXXnGfxLbwH8HXglbPpj5V59ITSkkG83fWKJDdOq24Bx6ooYm48vsFV9Iy1PNCCZLO+eDpfNgvVLaBd9sgaWCWp2x9WkwYCDIc/tUqcU7KDPaLGTIqezSuqBvw6Bgv4F7ScmTjJUyNIkZk3SmtTSLhBA1lv51xm5ID3TcocbzSas0OgIHiP2ROXzvEJExBoN4oceOmhicTRXZJ1P08hzLXZG4oP7BpuoSx6pL3XxeKdHjtOEGAYlvdgpuQrIh4C7KX44ir6jPkjTfjVIOZU2G0ZEH7cMgS514penDxish6R+51oAcYx8MwV/LgnI3ukB02tmK8SZe08LHvUKCwXvpqquC9m/OgldJxJAsAawqwdsEa2JTAogYIG4lF+VwtVtMGtOu/W2fVajVr1RjJpFVH0ByoB55jTaSsEjK9izZX6HLFD6Z+agvb1AJ12K5CZeoJ0eqrbboP4BxUKMzKIRceayL46RWKOmnK0wdaP63MVcxvZkaGfqTd4no773UQzfO5Pt7ejeUmdttcHXjjlVD+VmiAGWR5g8XEqtd03p4q/TE96FeTRPlJD0V6s3Cx0YsrxfVRPy3YyHwrDzqJqS1PySD9byWNhZR84g7nk6jr2mnArv1IAGsWUGwiMWeBbGW0fcFqxKrb2bcjlK1gjqMYBYWQI+OJ6xDKKLYs/BYPfJEKLAvhF+SzEwMFfM1IdTl2BTFdmFuH///jgq8xT7Z60QBWHR+hhSacBfGEYnITatRutXBXVnuyywWvjOPfZaT6WhiSVWN8BcL+C25MdhL1buB7XxSkc4sPMSHRmsN9Q743E3STzoAlQGRQm4lz2/ewmU++Q+VnyQfJhx6B6O3x8aDU7pXdxpHYEcpQ+aorSUmJPiZwyg/otwcaFpcXNA2EN3JrOyU0iEQ/R8yP7dEqjmayEPmCMTwqblebDLNwOObBVRgweH6QF3TiFnxZ4SfeQjYnV/JK8zJuHdP0LBPfxq6hfl87A5I4Gg9uRNbT/GrcMo9xoMZcR38rDWyj9DcrqHAoHRZZXQCIlZQMu3l3+Wtzuq9g+/s3tQDSee7MrQLtQmNMyfnjI9tf5xs3VPhc3aN6gbFtyXvK0gk3+7nAfR3mkR4wtezXq1dDbkVvKajEcshPRHZJ89b2zDJ+Na2IZcbHNnr3l4PwqvS+n6NSTnIDKHZBXRKAzoXe9lCPpZTa2pS/LxZ6rKT7N/Fcgpcwl1pL97PWzUwXP/ZeYNY1PdWcxd22wWQ5WQbMuqpgV9G7Nq326EqK8AVyMxDmY+nPZanBDrYbklA0veRnOZ5lgKzHZ4llcHToED3h8/elkGf1BfXNraJOf7t67j3g9CHD7A9jpXasrHwcDcTzr6L7UeXPUhl2kMnfAfZ7xGXIrhZfnBjyYBq4m0OYLp419AFm8AzAsjwKrpUkqyvWrFRSqDxSYHaJ08RmXDzSWUN7eHp6V/9VRi+2cPP01RmoHD6izcf9fWS9WfCv9Niq2fQ66vbdHSH1FZnnvcEKx+RNwFYZw+oHVGVbVRpPioW9zK02MoytWTtaxZaJ75HQrq+4wc8BAszS840NviztYJ+ROuVdDTgqwP6Wtmzm4vNZYlWZbAqYQdUQ2e05cZQWqgoJJ+HVnX03yLGv1ft/rz3DjJaF9yVy5q18KLalwU8WN2DK9JS1kiFnk6A4Dv9mclPPLgV3hmFhCUsV9g2N/uWFTTnVsTjJCVEpSSDmsveo6eEpnIyRxbmSIejxuqde1/1CzzH/baWtTdIqTWpANw3N32XAyZzRYPGYF1z1SRVl/23D2nsu4FvI7tdpaoalI4iZCgGunGoiNLguPQofKZtEf8jA/g/Mw27ppS9OEGf2a7dn6RM4JBJh1uMhH3sj+Z4ncxThbq1f32NRupsUoER+edkpe8Cvye7ENknlmfbuuI4DNRXHY/8x9gZw732uDuiXhrZ1dOhex+GZIPMU8A5ekWHG568RjD/vmyBL/7HwamrCCtlO+eNyNtqeUfSeQJOrRwepFhOtBnCHdDc4hzuGfPV/gNiHJ4arLhWtPSLQlM9BYVu515zZN85f2Mrn0HNuTUA/pXxIUDYK2APNZC/8S96qm60+W7TEH+r6q+Pwy5g3w51gTSg6/cI2TbMovzQz1zgX6lqDAPs9YfBzpnzDfVZfJbNGTxvpo4cxpYmEEvf+gjbWHb5dqxfc3O361EPJehXReeJNt8y9V3VUtdkdtxOq3j543I7jbAR+JY1t03+yb0pLLuDjjo2L7uiHUp28jKFlVTO3GC/onDIXbzB1S1RQRUHJ7+Jx46NNU8viJSdnizFpTyQnowzB3457p+dUh4LsXOKDQZkdgguygONIksM4AUm9IJrpG/D8X09Fw0i2k9F+VmFJECvGb36EfFCGfUEJe1/PnQmejbNVjOoNvz5HKZv1lWHub17YvMSixpzg9iuAWp9sMyeRu9bdGJ3ga0ZGauNfa2N3UiQqyXQKtLadf9GVC7ICo5HeHzM5Qmlt5/eA+1fwv9mmasAnZK9Onv+J5E1WyPEm9paXMb7Dp5q2ovjoWRiNeMxyKMTIeYB/PvImX5IA2XqLlnRPe0L8COPmApNmOK8MZ0Yp0FQLDf6DgFsvYaBuikRzMW/GkTrOHXumR6ZuO/vU2B33n8Z0r3u4xi5zvFnwXAKvDNVIV3AWJGolQz47AbJEqVAgXGXBQhzF9Wr+/7KY95m37YEYjPl1BWYwyCmzAlw6jmZZrcwWr9meDlmct9I7WssDtA3aigC6xMg+peJy4LTIw02FVsHEeWfPQRW8LDWGGaif8XfvLodUZORFqEpsRkHfOWFgptYy0SfsTKygAI0JhYtPkMQeZVF7zEmJL06R48hJgy54mpPPGxGVdjSusQa9SEvvGq7yYfE8uM4LH2ApTXhCp4YrzWE7hn+qeys1FppOqifbyBLkjiFCFomVXCfx3+YwsilO80vNy9fjGmUajjOamTlrEK315jCUfmo1osZpXMsg0OJaQZLhXBs4VxJCV0eDVMaQGZ7ikMn+eT+2PVf/VHz6pYBpo9AkT3hG4O/3sAh0lW8oedeSI5wUgMvms53E3TtzirIvdpJum5YgqlqKz9/1F8aFcrc28bp32Ew1S4eDCLT19aZaQVwm7frI0dBv+J3QJfzh94R8sxzYXydwAhaU6SVarPNWqCkQOb0/M4IAJDG7HBjG2wvqAhwWuKqChO2Hq9l4fM4x+NNrJ6VKRECwLsrUnq3aLpnlU5MPVCqgwbpa6n/SbXeAvhm0ZMtHTD0wnT/FRyqbsvJzOujq0oZD2Jgt0Yj85W4/TYeiXbSfcOGcpiRYaiZ/xrfF0H64R8gUtwiBBYPOAAAAA==
📡 API Calls Detected
- POST
📊 Desglose de Puntuación de Riesgo
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 3 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 15 technique(s) to evade detection
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Allegro users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
Form submission (backend endpoint not detected - likely JavaScript-based)
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 15 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Allegro
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 15 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
allegrolokalnie.76748219764164.bond
Registered
2026-03-30 12:30:19+00:00
Registrar
Global Domain Group LLC
Status
Recently registered (1 days old)
Hosting Information
Provider
Global Domain Group LLC
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for allegrolokalnie.76748219764164.bond
Found 2 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.