
Phishing Analysis
Detailed analysis of captured phishing page
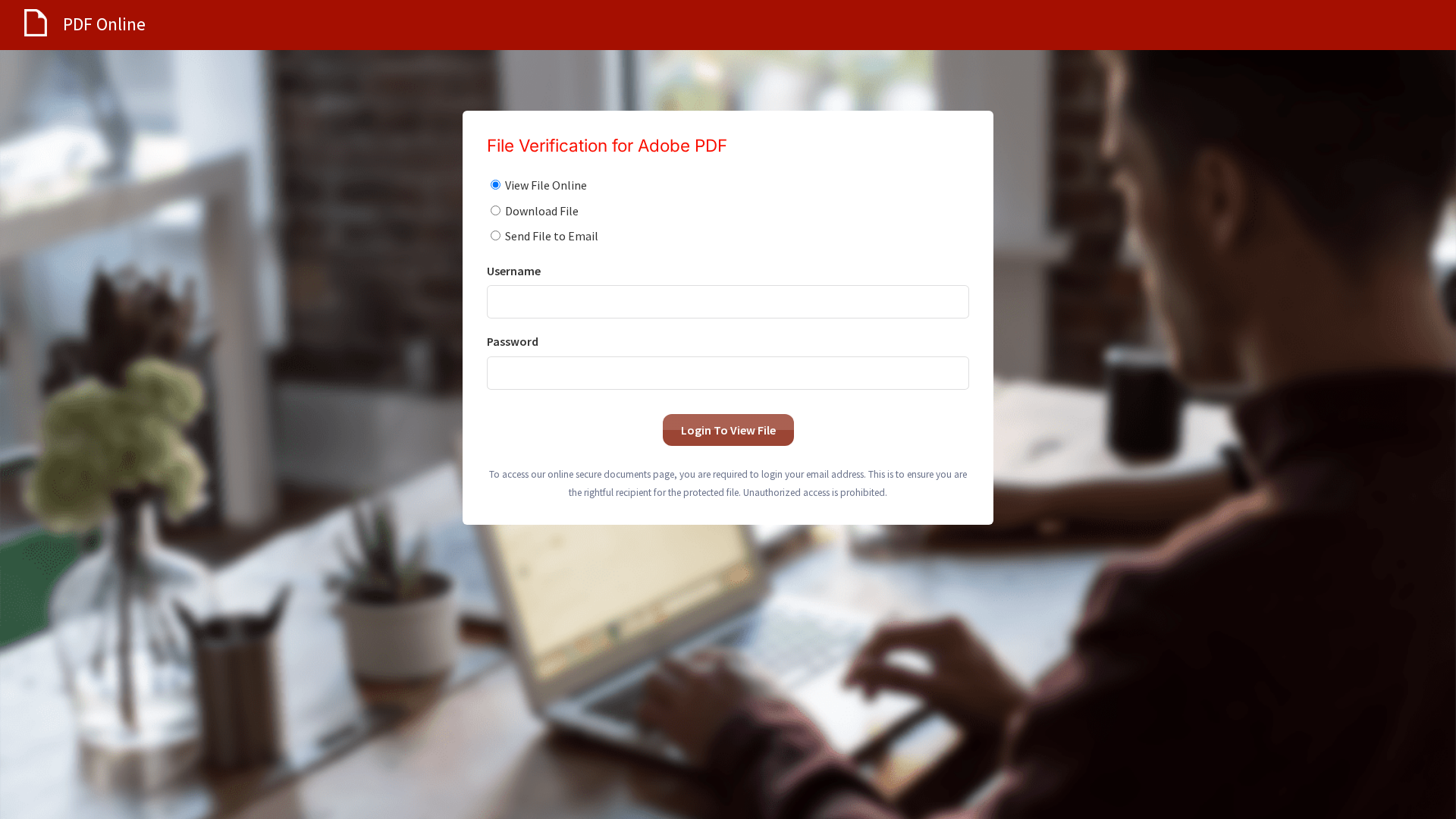
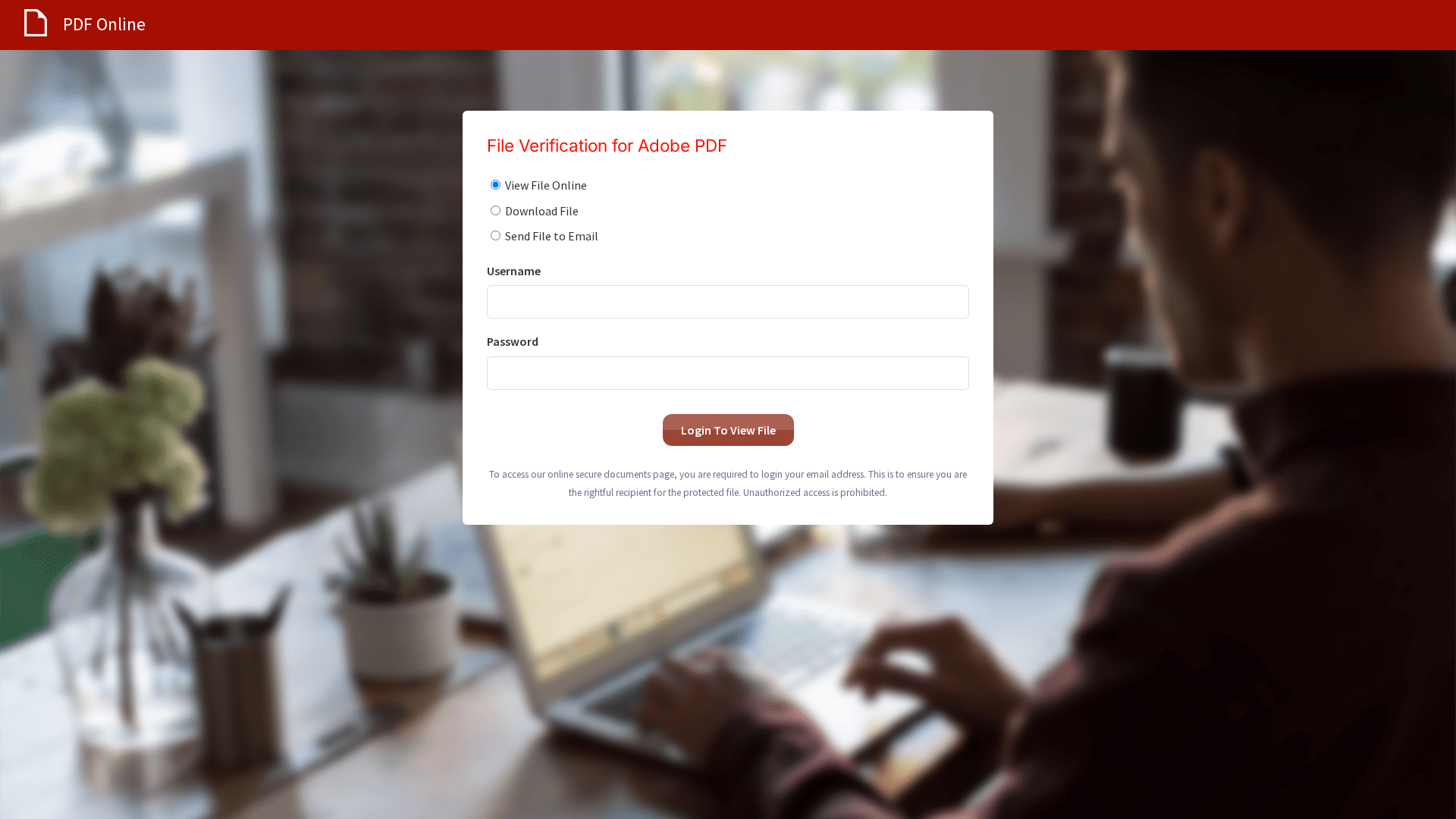
Captura Visual
Información de Detección
http://mail.amazingholidaycoupons.com/s/63BZGFSVBWSFCDX7Y9/85201f/8681e9a8-b42e-44fc-8482-459b41358d3c
Detected Brand
Adobe PDF
Country
International
Confidence
100%
HTTP Status
200
Report ID
d61c0789-3e6…
Analyzed
2026-02-18 02:41
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BA61433590459C7B6252D39873D6FF0461CAC2A6CB0E6C00A2F4D3CCEBE7D20DEA65A5 |
|
CONTENT
ssdeep
|
48:nICYcV+cgNstRemx3YfkljfvHg68SBF0YTgl76214zeVb8JoaTokg:nClckkJfvHg68S0YTgQU4SNqomokg |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
de9c732427382537 |
|
VISUAL
aHash
|
98bcbc3c3c7cf8a0 |
|
VISUAL
dHash
|
3038316868a02949 |
|
VISUAL
wHash
|
18bcbc3c3c7cf8a0 |
|
VISUAL
colorHash
|
0fc00018000 |
|
VISUAL
cropResistant
|
3cdcdc9909e9ddde,bc3438b6f4d03464,3038316868a02949,8b8b8383838387e7 |
Análisis de Código
Risk Score
65/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing de recopilación de credenciales
• Objetivo: Usuarios de Adobe PDF
• Método: Se hace pasar por un proceso de verificación de archivos y solicita credenciales.
• Exfil: /site/submit
• Indicadores: Dominio no coincidente, formulario de inicio de sesión.
• Riesgo: ALTO
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Mismatched Domain
The domain doesn't belong to the brand being impersonated (Adobe).
Credential Harvesting Form
The website includes a login form to collect user credentials.
Brand Impersonation
The site is designed to look like a legitimate Adobe service
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Credential Harvesting Kit
Objetivo
Adobe PDF users (International)
Método de Ataque
Brand impersonation + credential harvesting forms
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Adobe
Official Website
https://www.adobe.com
Fake Service
Adobe File Verification
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by posing as a login for a file verification service.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
mail.amazingholidaycoupons.com
Registered
None
Registrar
None
Status
None
🔬 JavaScript Deep Analysis
Total Code Size
88,4 KB
🔗 API Endpoints Detected
Other
1
🔐 Obfuscation Detected
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Adobe PDF
https://federalnewsmagazine.com/s/63BZGFSVBWSFCDX7Y9/85201f/...
Mar 15, 2026
Adobe PDF
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/85201f/868...
Mar 09, 2026
Adobe PDF
http://current-news-alerts.com/s/63BZGFSVBWSFCDX7Y9/85201f/8...
Mar 06, 2026
Adobe PDF
https://site.applerts.net/s/63BZGFSVBWSFCDX7Y9/85201f/8681e9...
Mar 01, 2026
Adobe PDF
http://my.webshar.es/s/63BZGFSVBWSFCDX7Y9/85201f/8681e9a8-b4...
Feb 18, 2026
Scan History for mail.amazingholidaycoupons.com
Found 3 other scans for this domain

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.