Phishing Analysis
Detailed analysis of captured phishing page
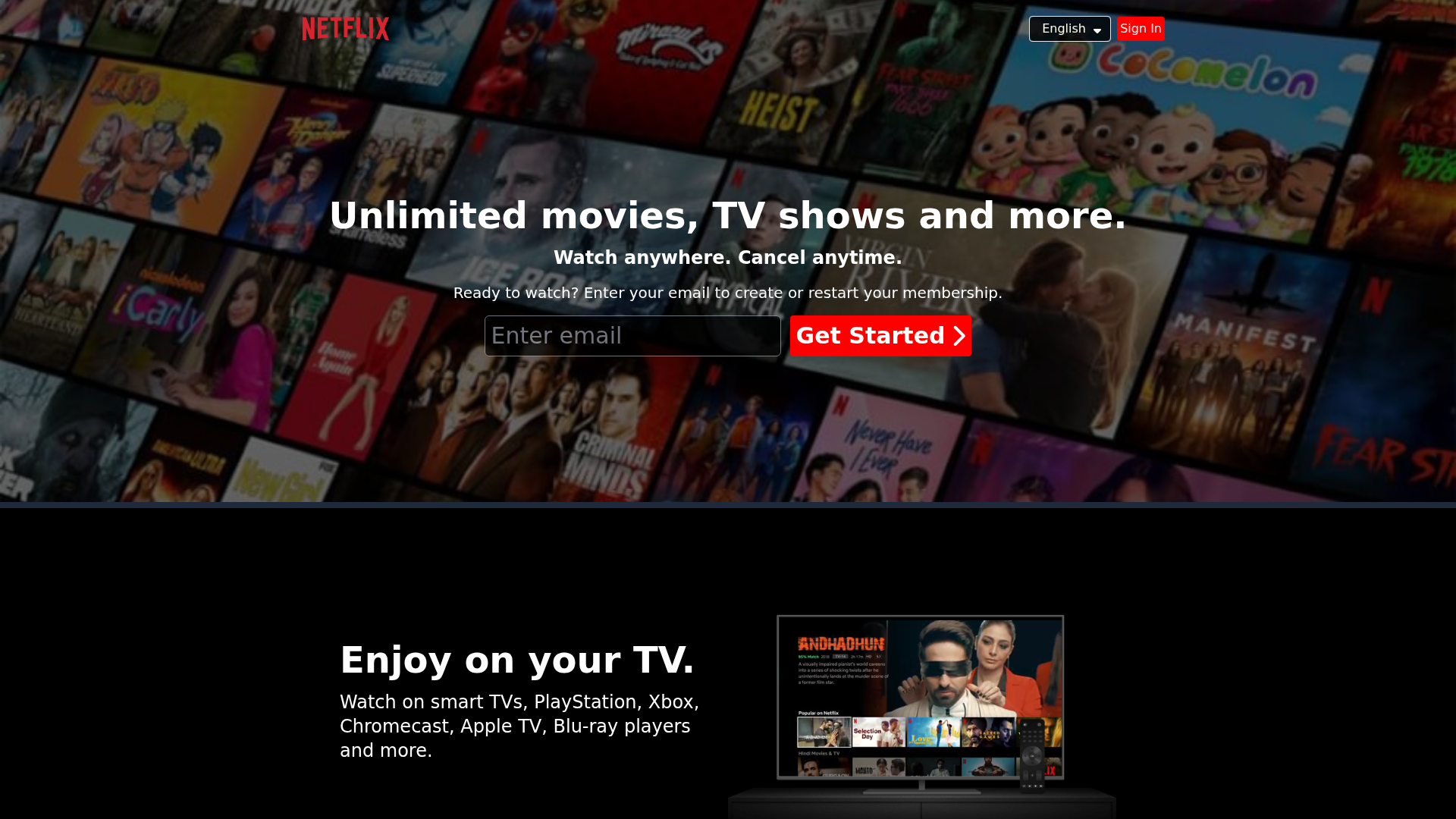
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T151022E6041529ABB05DB81F4F631AF6AA2AED385C71F8B2832F5C35E7FDAD24CD40254 |
|
CONTENT
ssdeep
|
96:TlGtlFZW6gDZP8y/4XW3fRo9BRgf1gN0N9jpKQylsXrvPjW9mr+qAKb2ep0BNDDi:4lnwDZhsoKJ9mLa6QDDi |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d3e5326439131dce |
|
VISUAL
aHash
|
e7fffe6edc00240c |
|
VISUAL
dHash
|
560668caa894e9c9 |
|
VISUAL
wHash
|
eef7be6ed800240c |
|
VISUAL
colorHash
|
39601008000 |
|
VISUAL
cropResistant
|
560668caa894e9c9 |
Análisis de Código
📡 API Calls Detected
- GET
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for netflix-clone-puce-kappa.vercel.app
Found 3 other scans for this domain