Phishing Analysis
Detailed analysis of captured phishing page
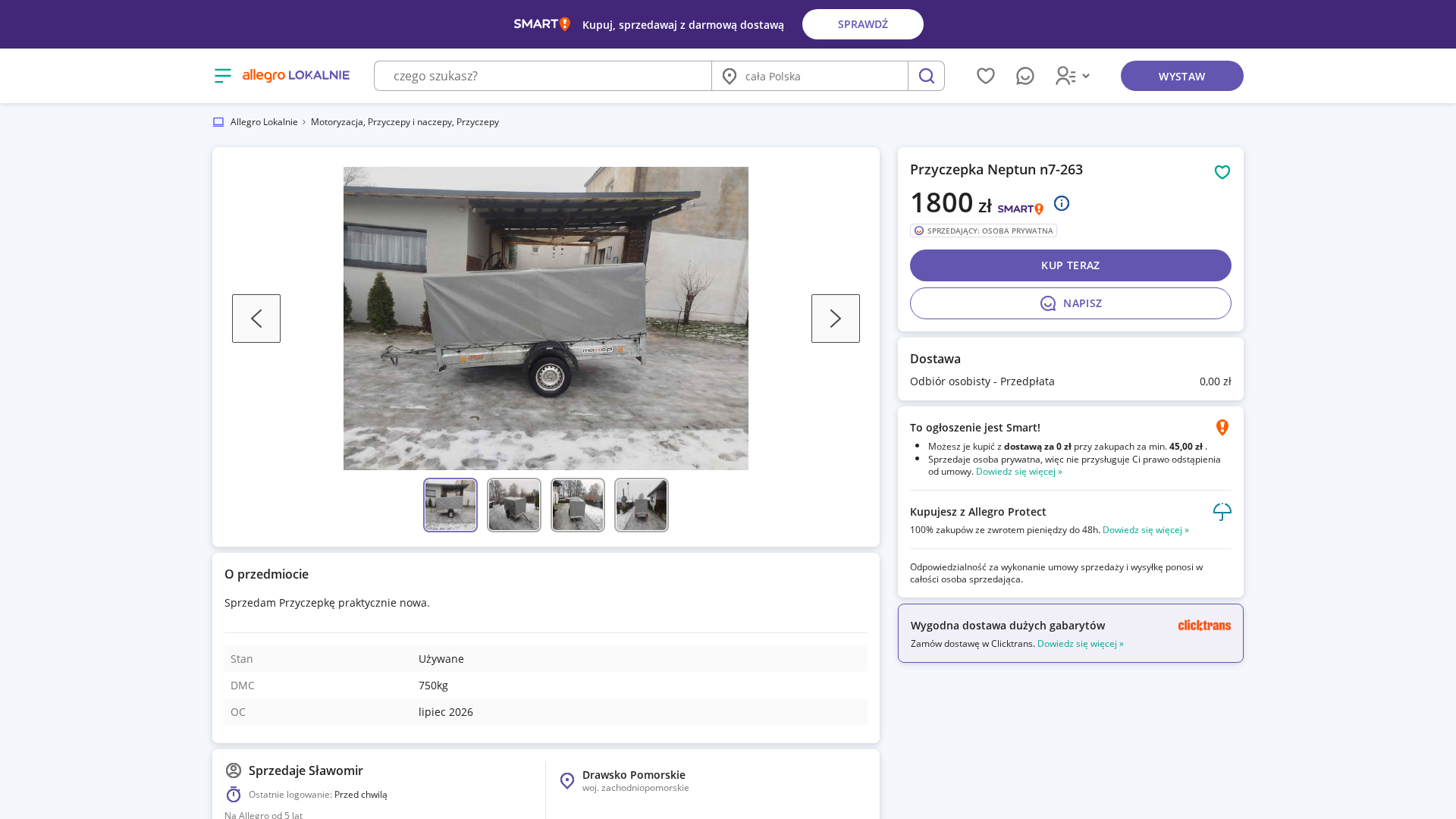
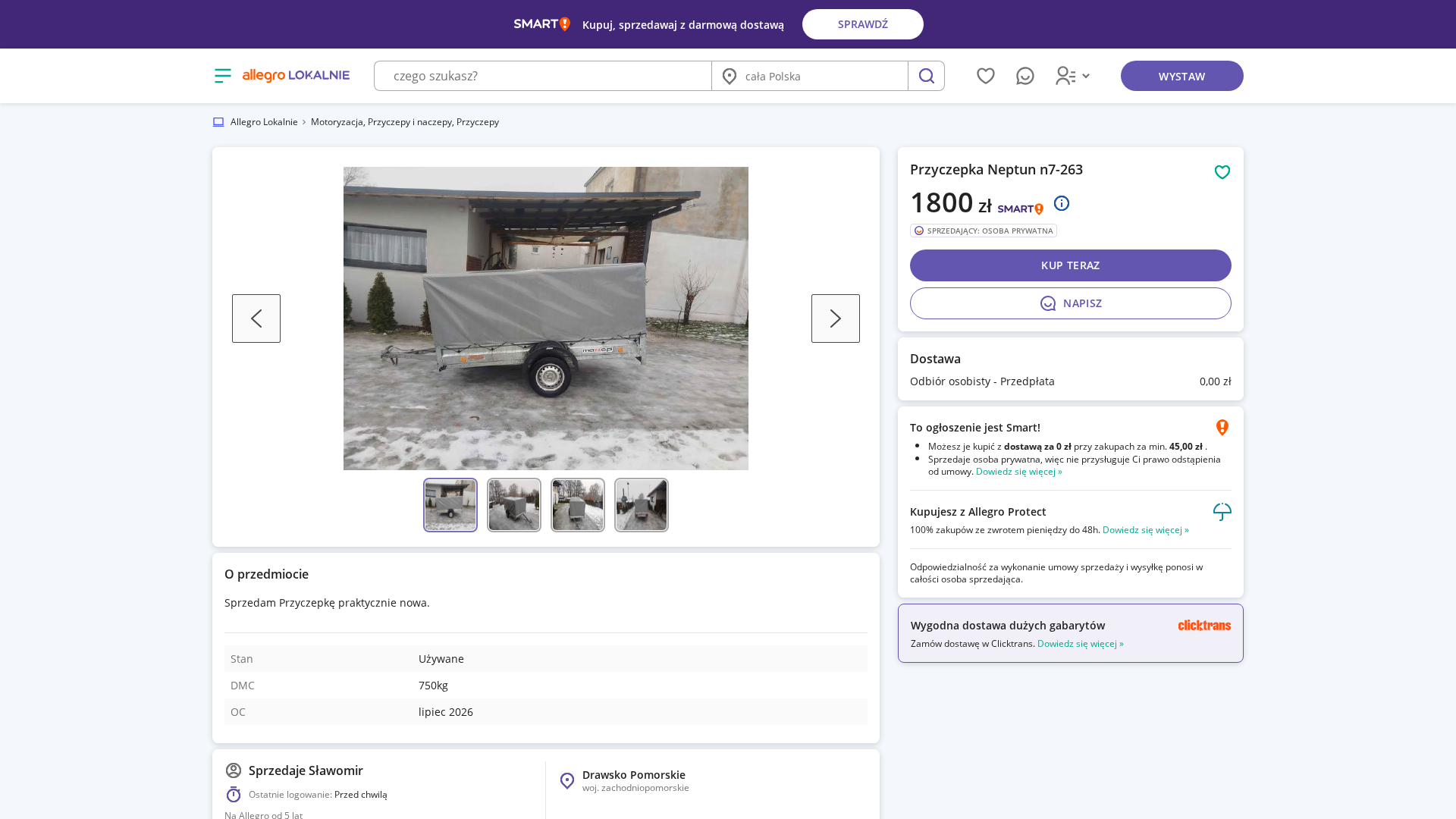
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CB53D7F1A1F166BA015FB3D4E2257B29329393FADB864BE181D4DF845F86C08DC6B484 |
|
CONTENT
ssdeep
|
768:6QgfXWUJpqEKa86E67WXvzNfZywkeLLXcpX4/cOdll8lSL92ypt:6QgZ06E6q/hQwkGfl8l4oe |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b9394747121a7979 |
|
VISUAL
aHash
|
00cfc9cfcfffffff |
|
VISUAL
dHash
|
791e9b9b9a13e350 |
|
VISUAL
wHash
|
008b8183cbcbf9bf |
|
VISUAL
colorHash
|
07000200030 |
|
VISUAL
cropResistant
|
691e9b9a9a13e358,041a5a7a3a1a5a04,f80909cf4dd9d95b,ded6fc6b33038583 |
Análisis de Código
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUgAAAFICAMAAAAFypcBAAAACXBIWXMAAAsTAAALEwEAmpwYAAADAFBMVEUWmiPh6vjf6PXr8v3k7Pjo8fvl7frp8P3o7/vm7vzR1d7r8frd5vPn7/ji6/T+yAHLz9fu9P39twH+wgLM0dvcewL+1wLM1uD9sgHH0dzj7PrK1N7EztrT3ef+zwL////CytbeggL+vAHc5PDpjgLO2OLR2uXfiwPJzNP3rgLg6fD9rQHm2tYSmR/+3wLUhwbulQPklAPV3+rZ4uzmhQK8x9XbcwPWfwTusAP3tQP9pgIZnCb4lAL3pQLTcgPm1s70nALtnwTV2eHP09vyiwL7ngK2wtDwqAP4vQLgYwXmbgTtggPPagS/xc3q39zGZAXnegO6vsXy9/7UgC3KiR/X4vMjny8LlhnXiTXe09LUp03Whx7b4ubKyMrPkifh0cflnQT28NrXkQn5+/a/sK3TmzH49eX4xQTUexjnqAT069DOfATOoGbeghjIhgvbjyQEkhGsu8vx37rOlUHQnlbWpUHRXAfgrEfdpTZhvGnijxTam0nqvqTv2Ky+q6W1t73gsGnZrljIeCLv4cnglznIcgvbi0i/WgbttpfiybTeninxyK/VqHnv0r3YpGnbnBDXy8b36MTbsoDJhj04qUHavaNJslLmlyIkmyHf8uDoq4jju3Tuz5m1hVPydgfMkVTx9+/Mv7XqwoPx5uDeolf4zwS5pJvckl7loHqwOwrKoXe+SQzZtZPb88zosFl1xHtFjDamJhHSTAfiUAXommjjwJDTaxrQp4rzZxLefT7LsJmIGg/uvQfmh1LI5cbpqB3qoUjjbySxb0i03rhSl0oxbBOsrLDm5urws3ehssLvwCBFeiVepV3sgCe5kGnx0nKzdBHuw17AVjCEyYnUbDX00imsWgzxWAvy3YjosTLrwj397wOUzpfL5aiVQgem1qevylmx1SG+nIPE34jENhMuhBLPeFZvr3Dy0EpepDa83lDC0c/UsQ/OiXJsOQdHnBebm5+ZbgymSEH46qWrcXJJJQVGWRR+Xw+ktB345mG5mA/YUyiDnhFvt0etl4+Qqlidbn0cAAAgAElEQVR42kzXYUgbaRoHcBsTa40zNHsbgnqBpplk6NzCJJnQ6GGDjZb2auGCl+1ZIkFCpZU05oOWdhJusWCFKxKLTZN2KysrgstSTTgWBCndQhXKmfvkpzsqWoq4uQrhvuxJSej9n3eivWfemSRNIOTn/3nead3KZP9kqn9yMTU5Obn4vaXt5Jdt3U1Ngabv0xO5pGiz+VByOJEIh2VZjrEK38TFH/PX6n7sPqs/4ozdpw+MxEawZK2iUffwxeHhwcHz4pUrZ8+eNZvNoij6wrnI8u3lnOj29nR29gSDvT1BPPH29gYvX/6up/PC77tcLsHtcrnPd3xxUfRNV8rF0gaqXPq08d//7Hd0XDxzpuMSqxuXbtygh/1KdbecVTPZ/OaTrKqq1XfvtpaWXp5qsSoDrKxOh8NisbShWixOh9PqsVolaWBAGbAr9oGAdQAvJLvEYwUs29VyuUSFx3I1r6rbJ3gPx/MmE2cy8sdN/DE9r2s93tqs0zX39fXVLQJxcfGnRThOPWw62dLyJTk+nAJj0mYzM0dRPqp4GBWPx31ms8981uyHpw+XWt2PaZKEKY+MjMhR8EcT0cHh9vZ2YNr8fqKMJ5OinEwMQXJaELp6ejp7envY6iVJUu28cKGr67zr/LkzX5xxy7ZopVQtbJDkJzyUQflxf7ij4zeo06dPX7r04tKNF/uVcmk3kwVhXs1ms/lDSIsTkB7isjoA2cYg2xxOC0Eqkh3KpImyS1ScZOclh0f58LZYpiLIcimfzW7bOf6UFZCcUX+M4xoa9I0nGk7oj33NICcn01Ppn9KLk3Mr1xy/PUlxdDY9X8jlBNHHSsZiBcBwOBGP44G94TfXIhnTjpjPFzsqJDImAzMaiYRGouHE9DBJttv8ZopkEpJiIjq0fOdVVHD19P7hu2Av9Hq8vXQwSZfL1XXu3JnfnTsv2rzRj9X8XqlQQD7W10ulSqVSxvmR1f7+i7//8su/Khv4uSog4Zi/mlczLJHvl5aeWhwBhRgVD0G2aZAWh8XhdFqdBIkQUmQ9RMnzHCfxvKI4u6VWx9u9EiEyTkT8raQ/ZTEYDJKJa+YMvMFk0Os5jmvVmwgyPTOTTqcXbz1uaulG4imO6QfU1T4bU2SYNjHJKhFPwBGJjJttADEjjf4rMXS3n3W7r/ZxOYYpgEDSERkaGopEItHpYapB0e83m21MMkeSd92Cq/dvCGWv16s5Msmeri44nutyeW1ewf3xU7VUKhYLxeL6LvqtQpSog4ONXysHO/9+v7X0CW/slmqQ2Uw+nz2EXHI4Aako1NkWS0ubpQWnBaQONLZTkhSJAhmgRFI20bw8etvahnjyJzzbe2taJkslVc1uWi0WQ2ODzlSvs3M6Qz1nMtVzRhOnM/bVpX/4dmbqh/TUXwNtJy2B7m5n4HEKaWTDUa5dRVEQ3fjtcTriCbrEbSiS9CGMNCGJkiWTJG2UYFLEdSQUGbq9MBSJRqODF9vbf0786eZZn6hJynfu3cm53V2Xva7OHq83yByD1N3eTsxIl+AVvYLgjn6EWqlQWisWEEvkslyD3DnA+X5ra2mzsLtbxnwsZ9Ssmn+Soe4+TKTT6cQMhJrVQbPRQZCURqvHA0g762fFarcPkDbSyPHNOrtD4o/Zm3m+VdkukmK1hO5Ws/nXbbyB03N9OoWrNxmAiOozNXCmuqmZFUiuPHQ2oam7m6zXZtgmU2tqmEAR5cKppfIfAIUli2VtM9LGo/9wQBIkvBMJdHU4EZLlUDiSuj0UwbicHv753srUI79PFJMYwsmR5XuvkjkX8JBCr1a9mqTAvpe+VnBPTw9O7xQLa2u0CuWN9XIFhO/eQXJn6/3Wy61CFpBIIwgxHDPZzOZnSEqkpGBrqfU0ncii4nF6PNpUxOZiRXsrClQBqUcg7XrkUk9v8pa3ayyRtOVk1e3meiN2HIMdhkZDfb3JpFnWAfHbmdVrTZY2R6ApYH2YzgnJWhAZIwJBv8YtuN1uQWvvZOKokrJsYx+MMU0fa3DNMp568yw9hFiGQqERHJFQVJZ98nR69ZvVOb/NLeZysAxhTE7nctiBgmhinEGSxBOvwCTxvYCMuoXpanGtWFxbK0FyY319fQONfXCwwxyXSrvZtd0n2UyWsriJbTujbh5BWrAbK5Q+gkRT45dSGvFP9mbpsKx2DRR7DU8zkxpcz9NrSXesjWZlKVutqrR583qFb2zUI42ANNYg++qm0jMrj6+hp2mX8aCta3HU0ujqcmlpJE50dw41kejvn6CFSz+7K/r/0lAh6huamRofT91dnp+ff/ZsfHxhIhGmjSs0tnr9+o83ZU1SHnqz/ODBA2xC5iBNCy81OAXUKxz9/ahc+2jsvaJaLFBh9ybJd2hrctzGXU8RidxVMwR59SqSs5k5ggTMABwhiCyiqRFOhBHNbGd9zdOyevhDSOp0SS8hmTwv6XQ6xS616j5sFtmtUD6vbn7QNWCL4Y19fay3+4wIJFo7PfX4K2cTVSDAHOXaFiPbhK4LLoFGFftNbhiySqVSk6nUaGp0NAXK/gjdEbF5KIfluBynzcbXPxELpcdCo8tv5mf/wmp2dv7N8sRIzBceXb3+zeojWWB/FnlhfPnB3Rxt5kFzMGgL2rTepki6P0sOHpTW4LiHTK5RINfXf63sbC293NoCZGH3SaaIE3ePNB2ptZFLdUeDtEp2DxLocMJRm4y47fEotFnXCmBWKy8pmInshV3S81rp9ZLua7ByvM7z+m2+WkIo8/nXXP3xRh0QDTxB0jLWkSN6uskRCFx7PpFzI49ybaMWiLDm6BYYIwxTC2NzY7WaGxsdHZ3EOQrOEOWRMMVw/ObCzPj87Ozss4V48tXyZ8r5NxMjMklefx6xsYAnR8bH79z9Z5LdqaNsR7OSdbYLkoPuQXG6UlDVIutuzXFjo6KNRwRyvcwgs1dxz6Pmr6qb6p/zeQ3y6dJTRbFSCCmSDroFh6Pi0eah/dCx2YpP2ek19CT40YIjp9c12z3N9TpFMtUf5x3b+WJJze9tG44bOb3BZDQ2Mkiksu7W468GLAFnIBDonplwuUVZCyQ5CozRRdNeEHITt2G4sAC+W1is6Bmejs3NgfIRWYbC4Zv0H6AEy+H/qDKjkDYSPIy7ycTLkpmAD0soEliZJjlCwWbG2z7cw1Z7HFhfinuU3VRsE004gqtHohjtuZg7b7nN2bhpovHWVFuRe5A2Cbi9tsJ6uRo5ITnx8KEvFrOVILkWZCkc5a7F+/7/ibY7ScYk0xd/ft//+/7TYDD4MvPBRx2pzbF4PMgo0+nNaP9o9wMmyZr0ds+Nh8Ph0Y80UcLhPCJZka4TRb44ZGOXSjMnIKv7+5qz31RqisSQnNmd+fkIURxJZvdriiSGlNJ4qXY7SjjHCvlYdLIG0SWtqg1BTV9KGkI8wJEGpigLkipLkkGW39dLz3ez2Z3sHlqSQAiNBjI2dFl394xivwCMXZ99M3HNpfkaT8pqVOLz52u+doSXBmODMdCLMcGTY2u5BnVhIZFIfJr49JNffxJiDQZfxoPxeDz9qP1hRz4dD8TBlWAu5vtT3Xd7e29eaXKk/gZzD89losPRppomm4gkgzwZkOD4moxdGuHYZozFwtER9AiQa1gMZ5MIGyR2cmZHkyW65M7T77//twbSaiNHs8GdeK9i9rEQyb14IyuKYm9UbPSFzLOxJkgo0iyKZgnhI0l6SVaxIL4nql2Np0TsNfoGwSkLGJWkybozVOixZ1LtOU0cmxEVzQ5okDAyR5djNOqLxEAvFuuLMcnasby8TK/lZ3gsAymxDC0sjG9m8pnFIGHEEfxy5cnFf27iTZA0ClmOXxntnv6iN4YpAElO9c/NDYeHU4zxEmcOMDZRWvNxmickBFnKlgo5LbOBcqdYLJO19+8dVWYrCJvLSQgym8WgRNRgR9xbexckuRn7iirYG22q+YQigUSmy+BobzTrOHAkWldAkrq5BLLAZa4JVWowq05GZzLW45+p1vcM7O2Gui4rCj0UCY4OBzYSekKOLpbjeRr3rinsJkOhUOQtR1JkDAw1lgRyefkvV8/0PuhbiN3/0/3xzxEXoxn4OR4I4PTtypOH83kIlNBClenMldHQnd7VJfzBUtGo17c4Hs4Mj557q8imliaf7/SJIl8cFg4OIMgS6mKFORZ2itWjMqo4FaDqbKWQnE3mUCSR15epk+OtTQN5j4YiQKoyQFrNqqURe6E2Gsm+8LesyLLNJloINRVJ4igxSwkQzQawhDgFnc5s1usFJy6YyM0mnRF7omSiHkQgoUirtW31OnHUDpqJZ1vPtrbSpMdvGh4acrvdNA01jLETb5MM+Xjw7MHq1//46Wc3SHPBePrL9vmOS6nFYMBDLAObGkmmysMyc8U7CJLXiWQ42pxZzCwthlmQTaxIPBJb3S6ekvhLvs6VsuCI8lOhO0DFXGG3uPGGBXm0Xy7fPMoVKuBIBZKqOIJ7JLkjPq8pEp3RaqWpqMpWswKQCquRNYk1hgCjHSmntEZOfj5GacCMRD8XGCSkCnA403Q06TsbRFHi9YZYmuq62uQupW11KVXDeI44ugDxLJIHv0N0iDAOguNgpC/S1zdZixlQfKtI9vbW6tUbNwgjjcbN9vb5+Y78WCDg8fv9nm9AsuNfcU8gTiyDwXTG652803vT14yxkY9OLc4N3b8/+kETL55sbcf2rT4vy9Fx7b9k7AKVyNIBO/s/pcJGjgVZqpbdZXfkTa6STF7Giv2bGU4aKHNd0UDe61IIlMq10WqWbejjToaoRTS+FVWrIisfyoTUyRGDlyDpkcxmyhtytWC2itQeZb5uMJlMDWaA1rIbH+psbV1WZXrpXT0iZcCxFRy9UzU1ulmSwBfpOwF5QhF6xGlhMn0/PcZzEbA8Y39feQiSQY//dk+P38+a3Ax4IEoPiTId8Q4gcCYHml1T+WHv8GIm8nGkSTta+LF9ayvRrDn7Nco4L4g4UxXfyB1sFKsw9dpepXpQPCqXy5VKspBMZi9fJnfPZHezOxZ7TZHwnKrVbydAOjWQsrMmSchUJ1hVUVR+hpaJ9VpHN4AEAxwsGYGMhMm5I6iizsBvTQ2iQnclOyWRdht2dkOdFVFzZynlbcYC5yWO2CJqcnSQHN0aR0gyMujui0z+GCSzfEbPxMJmfiKVXxwjL3s88PQjkJwHyZ6e2z1+D8/JRT8u4CKRHBr1TfeuInBc0UzUN7fknv4q5WhxOI5hbt+6dWu7X1Pkqyz0CDmWeKvZKB7gdQRno/lUDzYqR/v71cpsbmZkpAI1Imiyz3ee2xotZVbknxWMR4U3QKfilO0Wu0WlGOb80JGfRVUHsVpE1QLaWlrDtMAIy5poWNJXxnqzjkYiVNhpljvBT/rQ3qDXszihSEzIr/uiXtKjF0Hj4PEIjuTq8PV3OLq5gtckOdj3I0lSZscmLnVgT6aiAzeT9L5buQiS8R46PIHvQPIXaT8wAjKFt28UY/IuxqQ3mvFlIhOxM5MA2eSAsY9BPt7+A2zhdb14Uxgp7XBoFyvFjVIxt1Esl/fX9g4PC6WNw8rR03WUyWQ2RxVoB83Hsm61NdpPQNJdHb7PozgFVbHbVNnM/hUEkbKcvE/uNquKyHctzAZjvRHEIDfTTxDPglQv0RmpTWA7JR3R1Z0SjfWyUc/eBsi2ybCXtNit6bGVbc3T0e1mkMcY+afm7kFGuaWVH5x+e2NsbPHz9ouX5i+h6PiJpMcDkqTJOLx9+7Y/8AgkUy/pgocG5djcQCp2p3dyotk1Ojw8MTe8NH016sDR1OJoqYEEyW2vy+t6BWtT/ynkipiRGJCFXFUTJC5s5HKHexfWdqszM7OHMzMju8nkusVqPWWzAuRTgFRlRZUkvlum0P1vFHNFoszAAyCxQMrIGvK+qpCtQcwg1dfXG40NeqNebzSCqpFxiqZOE9GVRCw6nYL8vkFQsdsQ3Dpr2zQZm/5vhThCjtdoPE5pKTN0LEg8Q5omtfPgsSqBdGsSs/H3gUBw/K/t0GBHJqiB9HhqJGlM9viD/1t5Mp8P9LC9yd1DXt/NO6uxAe9UNO8bH78+/nHEVQPpaDlHIBOPQbLZG32DDfugQHENY+cIXaFM9yGrOazfG5VCpbS2vra+N1Id4SaZReHZ/aWq1kCi35m1ezoAZZYlq81mBwxuixiR2GpQJEURPQhrIt3Z5cQ2GiUTmBFHI30CSCOVHQQ1F0fg6zTJAk8AgyDVYUBGiSG/oEfIsRUhg87jdi9pGCPajxCeNZhYshkiVu1EKAGOCBm0nECaEoYGI2kSkzHAczLjIXP7/X9cefJkfrPGGCTT3VHf9BfLS17vaD4cnsssfXVziiTJe03/71iRtx7/8EP/qxI4Hm/ZRQQNC3L/3g7S5wB2r1Ry2fW99TWw3NndzVbXbeu7uzb7W5AqZS/dcFQx7QyyxWKn+2RAKYgig3TqBVnU0QfUHScjJn7ojQzRyIqsNcuGzk5UcpNJaDCZFanBKBn1RkGou6AZe2AAooStr7WihTNHdnXk2NgsyZA7xMdgSMMZSnQnftXvxgINRTLJ4KOVdhLh/7k0/5A28zuO2+R50vTiEwjcCE4fvPEsKX0YdE3obf8N3YHU25XW5cbRC5kaEqjbRdDmktUFEnSjjb0TvXbdEXsTOXZHaTWwulrhSntGTtBKoYUyUOxZQnD+IWXQPwrOvd+f53GWPvHH4w8QXn7en/f78/k+OWEXT47eh8XAY3jflfyahjPOOJSUkiylsoW5jUsD+HuZ4lTpy7FSESX5I4H5u88I8tpDkLy2C461vaGmJns0Ws3dzXJluQYLL6NEd3YePVoFy7X11dXV3UfzRiAYemaDDGFSxkSCVmlIdAz4g0HFMFBdGADDiJmm5kNpMg6FZGOByiNGw+vUtINuIemyErqmuOg/DOTIR4f4HbebK466ufQIOMaK+HCss6Xzp23QdafUY9rieMZuk/2C0rr+RpL9/bH+WCwVW5yaWhxHfBwUkvQUsZgJIZl7gi8f5OLJOPndYS4f5W2yhyEoe75wae7v+d7uYiZTLOWnStmrhwXj4cOpa/YFjrVlcKxYW8gayOGWyl7HTQ2BEuGyWt6Uw9Pp1fX19Wfr87rRqgcIkluLqG4KSBCT/aMWfNMfMgOGDypGVAdCr9NDkEg9ED9iI1C63IrhVVWPU90vSB7PcNWjQNQ+n+mob3rfgfbpYjiqO3cVjt1d5DlAZ0tLS1sb6tFKjwNSkuf2UuQZrswSsVj/S5tmLIaCjEXuDX10vvfeoi3uHnFn4kqKWXddINgHfUmSjA9KmuQtXb0vN/lhZmxu7noaeTVTzJS+LBWQHwTkzyIWxm+ff7u7u4wGCWgIkAsAugRl71DZNSobsr4MnJh5trd3drY3727N3/XrraFQ6P8gdZ1HgwZthaM0Ju3GBjP4luHBuBdq1FWM0phNkL2ZG72qjDSK180wDoqyTdMEpIfHCyAJMTtVxXC8fzzo+KGL7uRV6rLHECETRTZICLutrbP7X9nEnl1bDK0LLTJt43sZi0QivOH7wGEet5y/N06/QWskySez7XCVeHIC/fBrMZwepsl4Myecd/4Tt627bzgT+WRubuPTBLSdRUkWJjEvSk0e/WxlryQ3dsWvufRZQJBEiyyXn34PZcNyUJ/VMhJkjceLALm52ri11dCgt0ajIT20BpCfoyKjDNVmGH6tgWLQ1AKNYX+TocJ5dA2kzDBk6lQ4p0iGdKMQZY2mAi1KU/qlysAIVfuYiGjrDkMNNDkOWAs3tW4ECbI3C5gUdltbS/dIJmE1x8I+wjS6I3WdwEvoReQlPHt/cOrtt4FyaNIm2WXV5FSXdEbomSQXwbE53hG/A8j3uiySsJvJ2JXf3p67XkBTRpecLMzk7ZJMgaONchcgK2yPgFhZ4pDIqebZzfVq5XKNDl7+jYTJ7e3p6Z35Bn+jvyEYxZyhh9dsaYvXeBGColqYxwqmHjQa0ThVLRhWObyE61mN5ChDocx/nAVVNEB0SzeGRX6TIOEwTDuqT603fMbx0AFFcSCVeupo1pkiTBscW46AYzGdAcPCK/0RHBGE0v2JhJAkyggRRiKpgcmZsd5fIT+eOvXuA+4oADIOdE8sCQvIPhrOu+PiPs19MuDEJ+g3nG9K/TOXbmzcTkDb2cJkvjSTpXH/+HBkZa8in+/uUs7gtYDPcBdL2Ws3a9VKZbqM8FPm2/bmdhUNcqsxFIApywMq5t3v/80ZsZUgYR0BqBS+YkRh4N4A7lQlgMYIrWJ0FEUz/ACpzCqGA6FGVQnRbe0lLJCq5TodPq/Z4W6op64discJkN3ZtAi7EwWJHJ49UygA4z7JfoEIjAm2yJiNUa4S3HowdwvxsR0BcmjcWlEkgQ5B58F4UkAmrTZpNc1mKH32qviNNSnGEjOXIO5iIpNJT5YKubxo++i1FSG5iwBkc0RFwlgkgEuIhLI5MxIk+me1/Jftzfmt41sBPRAMWKf9Xnsh2WpJOxpko5TR2eDhFmiYSJFe4PHqzEXc36JtAp0bJFWmINUtQVJA7qG0QlBHhxcTjh//Gmib8QeOnRmxG+SRThh2miCFpYWSxZhOJ2LkmIj173NMpUo5K/aM//pEO1h+MTQsIOPJYZbk7L0+aZPJ5C0RdxLajjcn7+/7DTdq+dTM3I2N61loO52fLIxfzFLaKQsk3/7LcYZBHIayIHlHlL22XgXIBSL8a2W5Wt38w+ajhqamLXQ/gDTxipq/lIq8GdWZsb1BQwv7dZg2jFtxerm74b4HIMWJTMYdboQ0N4O4T9YWBGeg3shR81kgAY6h3QOWPgP16JSdOkBms1aDPAthd47YHFmSdk2mRdV88CTxsn+/HFN/OsPzhMFBjnt//vjEk/bZ9m9yXVKSkr1nZ2/1IJZPJJu7/mllICnJP7Ik+9glofrc8HhiDF1ypVAsZqYyk6XSycJ5sZqVDSF5fRcMJYljoKFhoysu7Dx9unZzFVYDssuVapkgK6u1+QB8pimqt4ZNPg8VNVutPdrnrQiIHjNgmsiPYCe7HE7bCOFsb6ocN4QV0jLr6xU3pe2kf+NOVbWwQp/RZDhE9YK0GAwX5SpMivsiR33d0ZFMTBJk55G2Ywg+aJB5vPalbVckH+Ahxn2QKR5woSIHJT5+3P4E+h4CSUHJZc/sg0WMNxMCjwGSIX1iIv4N7qcEd9doLnfx3LmT12/M/R4lOVUolQq/uFhkQW7Y0t4FxaUXCy8WlpapbQukLH5qlWlaNkMksk91umkr4H+rUW80Td16nOcVkH4EoHBQCTeYIS5+pKaQGr1hg4x4jzLVGBJNw1BkJMQoqHoOejwuzecwpDYVNE6nU7MOvL0OrSOOUVHt0OoR2l3euu5sNgWjOdvZ9vNOJMhMwVb26xhfb4+RyMCFGZkNuTbrGf3qH7PtzI+5HnFry7oliVPQIu5JUXp8+MTs7Du5PZC5fGTs00tz1wcIEtq+crLQffihgFzZvcZ6fMH8yMGQARJjzJLdIoEQuubMwzA53/AGXSYUDJt6qxGNCkt7/aM3vKfz6B8aD8lhAh+nQCmGQ0Hv3irc9HrcLowr9YZy0OVyKfgdRnFEIZ9W75Ii9XncKgKmqskRhbOjQ469YOA+hNC6IguypQ2OfZZJvLB3SUGmhWNiD6Rdjimx7NjU0EAeRdnXw/2jrHpI8tYojTue/OSxtEnYCvWcfCyxfELsR0pS9ho9aJIziXTm3BUBmS+U8mPf3RhJPWeLXEGCBMalF7yWK4CJZlmpIZRzpTtfri2xQyKrX8anZb2hwY8xBQkyrPtpNeY+yDfePP2ernm8UR68olVqYYI0vTrypOwh5PIc4nMTCiryEC7V9KrIi56DqkdxcFUmSx4VTuPmHhORvAMlKWfa+IFyoI4dsrOthcJm9HkN5KscQU+e40lZIIeGPurtHVqUvU8PoIw+RvNrh5y7JrpoMRckTS4mrZIctv2GSkdJfoEuySjJk7BCIpO4cbs/iyYJbed/cjH7kNsKVqQFceTl84cvyhVWJv1l4am0SGTHKuoTjRI1WV0PNgZ08vPraJJ6GBnnu32QW6dPRz00ZdM0dEN1kp5igmnQj2qTXY/qVl0QL/KjW/ZCmCnxI7fqxJcsxw5OhRJ9vIqr3tDkiZ9mnyx1Nc7ayJCcZ9oYIa3oU9hvkLaqLV1bz0Kl9kB+8AGfRxvKc6KRQaWPJGfb749bbbLrKxH3uKSeePyO7Tc8ePgf1+Yb28R9xvHgu0us2b7VDghXWRbNJots86LYEoot3DaZovzZoG7wpGFObpzI6WItruRgbLVY88k0IoGQJVW0jZiIhUztCxahFk8JggVPTIlCXZhWRBcVCIrW0iZC4kWdCZCy7/O7s6E7ochGIKQP3+d5vs+fG7wzpUyBIhEkyelwMnzq8gBVGzk9mR46kEaR+ezsZ1ubRPFG8XG1yd12q0i9zY2LtKxZ/e/a2t2tZ8+K/6Ax5cX//OvL69drfrTTxa4g69HUQJVUa+x2dfzTvP5bAqnuFuxK0dChydtmranXsHk4tdM86ofR7tRqFYXqXbzSZGs5NbJJkoKWHDgKEjGk2QWH+o3vFcnubkBssrV2kyAD/xfZcbVcjwa7FYYqR4AcQEsDkoXZLOuyAe/k0TtzeWIXYlO0UB4kC5dCYEeZ8RPqdpgk61IdU3M0aguFMrHU0LFAMnlk4gj+dRbbucUJ6PGsgrGI2B41tZps1dHiDbI/iOctpMjbb/f1Wa48efbN15/+4fr9+5/e/+nL9WzJKqlXzqjafyyDlH6w/811Wv+xRQ1FM8eLRsS6i7fX1NNsyEBjXJ4mZGLtNp2OPDmN0GkIiYSoqeJYJqTmW0DLqNcINI/s1JEkRd4o8Jy2AoI02ZpgIRnHACvYKsuyHoExGA2WQTKSA++9s6NEkgYWJMITHxPIqeicFhcAACAASURBVGtjLLbrTj5FmixMs8lPqPcS0yeTZM/VDrLrNLnIjJw8NonYvnxk9PdJmWJ7/MBQeHThyaaaHIubbrfXZrZVj24imFFziojsFbfJZHGbqn+8sfXNxS/X999/eWd9Pd3Vs1pNZ84SuwYvgQTJ/fV29NbkIWF/tEaXHaFqIBtIs3Fy54JW1CJ+8Z3n6KzCINDxnlgpcrzTWslxRjWX8rS7MVCsdxrxF0Sq9ijbFRCkqbWJrA/NzuTnGEmQqh6DwVF/tDtKryqUIntAnjm8w7ejP9/vI01SS3OOonluLj+FNEnkeusUDxRTQEYYYzanrDvZPuW7FimBzMlyePz0nq4kJclp+bXfJR0e863vFI7FWyaHw2t2MJJ4ijdWVzeumEw2h8XtbvvhxrOv19fXX6qpZSCZKOmD8klcLU0tmn+2f79EGY52YJCl4LR3orzQgsZKFxUGAR0MnZYZRL3TqkXkchxv4LTUbiNvOmHGYSiVwSQ0is/s3AI/ORp3aHiA3GOytUKQ6A0TcaXJLudHheQocXyOkUAOzMwE/Yf37t3rA8f+/qVUhOVFtjkEukI2QtHdE0EXA1seOneOeuul9qmpAmu563oHO/CHABIN5tBEajoQPnVhdA+S5Kw8HRiSkq+3eC0qye9GzQ6zzWE22ywbm9e3bmyt5e6u2AikiZ62jT/V7ITtqW0uJ8YaSVIuKeziWgmkJL305nZl0GgndkKtplO0GvR2Wk0Dmo4cosHI6apooMtXok808Cg0VIl05HB0rNCAI9VtPAJnJJACx1k1VTysaUV3q4UE2cWG4mCYYA1NmaJqH7tVhvS2AuQ4G4/6Z2Z+3Q6Se/M+X/8SSZLgwfQgugtXU2wMVHdCrTesUYzMlyXZM50vwK0DJHLkRCwXiP9mIon/SiTJaTm3KDd5vDZLlJHc7ANIhwMoHZa+8OTk2tpaasVsspjNxNHsrs7VNzfXN9c206BCBEtXjXKRApovgpS2b69lF2h2XnDZBZeGA0+NKNCJDwjCl9OKkC1oKF8Cp8B8JM9GGLQEU2o7DdXoBkinI+8jIAGg0uhFQ0VDm5sEScNchDb5cWLJSAaDxJGMD70yo5C8FY0GA/KAn/rs6eOv7u3o8HUUfP3TlCVLaRIkl5TpRWSemckI7W9CvSdKU6C6nsiHhQJSaSYTGyKQsFkT8q49zEnKpxdzTV6Px2MafVQsXt9sBUg8DpA0XVneeLB2c23ZUQKJ5/YhiW6XSJFg1wx/U75nFksjcrpZkST2Wo3Irvi0Gr2BLREFqj8CpT+dHtWcJhS8oaqKWAnaKpIku24WlB0XoYWP1CDotVSyObY/47UaUVvRZWnsg/3pWkgm4wkgLCsyHA/6Sz48qIQ0k6Q/IINsIIUSk5r5a3t7Rz7v6ziejbHoDkWQJvOQm9p0H/uE1RtmxEORg3OFqWu9BLI3N184nkXRHhkayqXGk4H4hVO79gzPphPpdHj3UJfX6/B6TY2PN4uP+pAjGUj62bbx7d1v15ahSIWi2dTW9sUviST9kiSrE0VZotgW4SNVkH+RXFbUH3YXqdzXW9nFPYeEyGqSwU6QrJUIcB17dQYcyQTRXBd6hPJQcFwKR6rjhk6yT6hWOt6oFWggAkW2ulv7Gvu6Fv6dTCYSsgyO8YRqxINMjgpJMuKsbAcTAXLlkyl2SLpEJH0+X8el2JiSJmOf38nP5QszMcqSIbVTHGPNTs+Z9gK8ZB2BHDmYn0+zyB7KZSfDgfj4hXd3NQzPJmbTwbcOjXpaHNCkwzL6eLMbIImiw+FxOExtK2urDxpNJZDE8vZuWJ7mZrpmlhZ37z6waN9WK1XSuZ79rjKQhL+ETa9llz0suJEbDc5aNIR0nYuqa7Wisxa3IcQ5u4unV5L4Kq3OoGGdOFMkTXkJJMyPKBgJJLIribUKzTgn6vUVjTYmyOUFAomHGLKW5kUn3u33H2Z+PBqU3/P7P4gOZNkpaSo2frQdKAssTZIrD4VOPIUk83NLGXLpvZl2Cu6l3vMsoBH0U+kemgiFBj+fv5aCIlPZ8dRkOB44dXl4V0N3Qk6k35mQkl7P6x5CaTZ5vSRGT+lxuJdXnqggKbjNlrdvHpCszIu/lr35cHl5+eHDL3YDl1QGSSTZxbNVveYjU87bnXZ01iLjxFl5MAQjo67WJXI0Y9OSOed0omLFDVrUFYBE+kRc071FJ1lNSNgAswTBihUQJEA2Li8MM5DxBLSY+F5P41eabNbWBJEe6cukynEsNqiQnPoVzccpT4Y++jj/ND81nx2LQKA9H6nLL7ZTXCJJouOGWC98OD9/IjMyMjKRG5PDcfn05YFdDciS8fTw9GKgyeFp8ZAQPS0twNfS0rKvhR58trU12hhFM8N4OyXppUPN0lvZfy4j9k1ms9v95wPiInt/pgyS3pBzOa3szpkdr8CcO0UjTxMdtlhA1ebQZxvJEdEbSdpKOpICYZ3SZUOHHKGurKykYSUNJ6Fh/FmjEU0OWqCKNoDs6mpsVEEmEuyMr8zx+dAnWuLo/8CvCJLdQqYOEsl8wTeYzShpkoL7Tr6wNBZiM8eniiTZUVoMkiwssY1N5qtLB5cyIJk7GYmHk7I8frYBsZ0AyPRiuqkswZZ9QLiPPYTzlffv3WuAHC0WQrb88MHq3yYC8Y2Vh243lR83BbvldojVmkXxBUU6nciUvPImg5XWs2KtqLPSkSiEBTNIyVBD2GDM7QJNfvDbnTo9r0xz6dUkAslemjPCuyN7avUuq0DXVEZk1Ao3ak1X35W+BXBcURVJWfJ77kcd+pQ4+qdTTJHsrDR79WqeSk7hEnOTYHfmaP7pXGE+y771nGH1JhY6j04xNNOOag265yOhD766OpjKIEVmRsLDSTk9/vdbrzS8C5DH5cVcF7TX4imJcZ9C8ue/eOMnr957dC9abbI0vf8/Ks4upK00jeOanKjFJBKlQZZpFo0zgcxioxFbB9tRSFnPUWywXgydwY0OKmYZhewag2vA6bFJjZuGZC+kk2ymREOUzgg9MRIZHZu9UQRxFmprCyMLK4MMuxeDF4P0Zv/PexJ1T2KMHxf6y//5fp+Yfg8r393Y2N1qIaqyw2yR74cqtn90pQDympXOJcNFImBr8/EFWTZnlStoGK3aCG2pPygvp6krKwURj0t7dMUIJ2yEg9+kDKi8R8MsGUzLyoxWTkdVNx3KL2qhTcubGyN5QXpkkpebFQXLLnDs673vvbhc4Uep1XVeEHLrCZd8aA9JD0hmX4QXhpzOhX7WT9uh2PN0KLa2t7dOEV1cSEjrvohrNpMRM6FAAKXpP36ZNJneeFY8491TodbWj2SKd/IUW21dR98dNdw4OnoVqmqp8x/5f3j79uaHH8q+srry0tVSuV8O0942c/nDz08QahoZxvx+Eh0Y1TQiM9expWEAslppbaYR9MzaHrMZaMkj0lkAecBAzR46nobaWqVD1kTttDK1GlUNp6OMsox8pMOxcVMG+UY2bVyePMlAwbDxMTHeywT5t9g5RUgy7GIkYd2bMG6nCJiPpNfwjMIOjWcXPmdjBwrc/RCiL7eX2+mnA6fBHJ9bDCJmu74MhQLIH//+66sGE7Q5MfjxbChvygWSXVfr7vrvHr0auX70Q5flo5qm2/6Hoye7pluUZBYA1uYzouqWQ042bRojsvNo1sIytlZ+pE7QNavKiByGo70j5DTU2immYYNWaTRCkCqqA5XyxItgKqkG0rEmOZtVwI0Wc0g0NT1QpKKYgRwpgCTLpptHlmSApT+f5jneH2cU+0ajLtk95q+wK5JavUf55KqXFd39zqV0+l02PpOvHF8yqiwbGkpAkj6EpSGn6HMLX8SmIrHY4DxARgDyV5NpHiDHglOh1stXXHq+1nXb9PDVH2/dOPLbed7WdsPffLW9ZrnmFgswhWyolsWg6l2X2kzRhiuARMljLTAsRG6r9X2tWQap1LACRsNdIZAw+0ZOR30LleZcj0y2OvmpRq4SEXd0qHNoBsYZP6BgQyBDjKOHGE6AYUGQY32f9g3IHAcXWYO8r/fPrv+/wmFvKpVa43OycRM877t0Ok31DR3g+21EgiTXWdGISJTbW59bwLfFJTffPJ1JxKID86Gxiej9wV9g25MouAe8UyGLHF5kjvyyOy7U1PmfXW2qWb5qc6dtdx767Z2twt3bbSxQM4i4ZMNu2deoKfnZ1pBpM5C03s5WQmSSDKvR+p5Wx9hAbWYdskIzAkoZDR/o9BSCNwVkKsTJCZarUH+ztgbHzmMgsSxR6kpKS4qVPTqlzsxAMhfpmZBN2nPB8fKQpm9xkH1+0Ac1imGXiFsBZDiTSvlg3F+k5kTWmnQuwbjT2RkaQ3QP0RAxK7BTaM7+1Mu9vQQ5ADGzxgs7iVhixhQCyMiiw1JHy8cAGcsELJf0KPDPeMltty/740Knv8nG8513/F2tglsQ7t69Rfiq85qsxa2j+q2z2GxWIJHMm/b3T8yXtg7hKBWN18y0+PHetR7ZbpE44pnKSkU364+bqY2mYg1g5wI77wPYKorZTI34HXYQtaSslOOuUPuip6hjxBE6jzVE0TN4KfHpHZATyN6+ib+MjoZGDCN9XqcYDothkW0n0A4SmflSKpUjN7nDBg+ooddJkvCSSIm6P1+SsqziprTnm59e7q2GF5yiOAWQM3OZFZOjoWFyIvKlo81iajIB5FgmMzN/maObF9wS714WeCnutsd5Pt7qttuk5zbbVf+NanpbCxkicays7vD+xvxE9oTnILX5Xbn8qhdA0mza2ghGT2mGrUbprFEhyFBJzcGqlVr4SDDueXp20q9jQRtJuZK1LrTMsuEduRI8aIshWCUDiSxyxFNIxsGRUHoozAxcjAzHJ3pHN/T6pEF/FnaKwCCSFEUG0uuFcW/61vi1nI9ak3TNSURyxstyy6CbTRSR9fQ7g/9N5Xxz3cggZ+FXXwSj86atSQdATje0Wepq4CRXxhIJgLSxUB2PC253V9ezOC8gxxLoRLAkxEHWTsK0NXU1Wyqr2HuEyHqsrNz1almquE2m/S8Z5Gf5bRAWt9VGZtp0tkeR94CI4fCRKiPIIMRQu5Fu9L2ecL1+n50sVVITjSGkERi1hdh5NU6tQMVYzBW1tJ+DJJSe8XNFhi4SyNE/TQyOhvTJpH7YkDwjUMy4SZD7J2enYPrIl6LInVudoxEOfk6SfE2Bm77cTGdz/A6QLvQvfL2ZymXwQvxhbp3/JBF7c93RbtoaGI9EJxnISc9KIJEIMEXabDbiiOsZfywcp+OSFJeOBSF+LMU7bUKnva2uuctmqa2qqsBF77dS23HiukLtCmbIZd+zFvmPT1BAs+44caQ1OauRyhsKy/ljKFq25GAsgw5htOU0mGGTm3LdmV5/8pSMF2WiinHkiqmpgbKmjM231YoSxG7U2u0saF+UNeODoVAo/44eshofFARpGNYbKgzJQ9o7EhnH05OkXn9w8vbUu5Ta5NOoFdmZNOD7iiTJkyShySl3Npf1hVnCHvFvrj8WPxZngyneN/XPkMnSQCCj0VBbmwxyLAqQNnbBrnnpmeR2S8dZCU/TQlqSskI6DnPnbXxrnd3d2tzGQBoMhoqDfe+21nzhEc9BsgVsiJFIokCkjRAU1RouD5Ia4kCjLjPCR5aqwEyLNLG8XFt6Wo//r59miOQ0ZUHKj1o122xQ4A7HqSy6HLRZ5hPagOo2QgOFSPOAPOTKYO9Ah8EwbDAkcT8FSZF84+GBQa+vMOiHD07nfL41kBNeULyB4IIUuF83w2lSPbgOseZiJEjRu+aGbaPIzqTcqzBsS52lYavBE40GLG11TSZT4MVkdCevyE473CIuHviO+fiyxEt8lpeyaelY4gG5tbPTbePt1VUVVXiBk/r6M9dnClp9paSRI5A///zvb3/8Fk6SSLL9TLNR3gF7nyruPEhKDlGvqEu0LOOhPhrRVakWTuoNyQORFrKp3UPRWh5uUzNTBY7U01Sj6NEVjbQjaDOQ45T/bG106A34i/QjAwMXihyf6Ou9TiAriGTFSRikwq7w4S58ZnIYH4Z97+N7OYDk93aC+CFgrpIkhRkIFPXNX6W9HCXiTufvRJ+Uyz2ajSQii2tfjZkaHCYGcloG2dQUCJimpwMBsmuA5O99fbSc5qVlIJSk3PIynxbiUKZEPlMSOuEz7YKtlkwbJA36+pPTbrYIouW2t7lLIFmYoQhDKBUKNR11NnIX2TYScsRuZZlCBskhueQ0pYd60DgYorYQ8ke1EejoGceAyuLUKqgHpypyjDhaNkZC+Sbaf4b1xGVYX18/PDBayH0GJ8b7Rkfxog9XwX5wP6QhgXh6QPbUUUVKPfB6fTmeWXMsyIw7+A4kX9unREp1gpRmbord0KrzMWx0NTYdTaRSL2oQaUztjq2GwekIgayBIidNiytj8zYi2Snc+2b2p++gPzf/XJIgeAFxJs5TxJGWhedQ5TEPZ9lGtp2kVxl/+MFh9/+oOMOQttIsDFdNTAaNwYSIFDagZpBY6eg0ZJvFbRtI8SaRTrCzMCxSo0u9q9AW0s6tRANtI9rYSUWLyI5Z61ovTrhtobGGdptiZX9YAt3gYGbTwtgOlSGUsn/KwPhv33Nu7LA3khbBYp+855z3fN/5PgTcZuJVRKcWGwJZ3lTaxmEDpJ5BpBk1GjyjXS9qGhG52spqLVlGCvpPmsqiedRXuVhbo6FvckiX66keUW9TyePRqN5NhqpKHYEUCCQ3iMPrxjpRsB4GybrD1qnz+4JEZF/MiQTSaMVHbyzSKH2oKBpFq1nAN5AMCrTIC3TeDZIkAfuOs+TDEAk0uiLBr9+IRu9Eh2bgZMbX1lCaf29xEMhO9/rU5JWZ4RLIufDyMuVIkFwY/8c/txU8SSWVkh5Iq97AApIiSg2t3T0CU9+ub8F/ou2PIClT1jGqKFsLWZcJufund29URZa2FVt4mrzkgvj4Avw2QHaTwHiztRxktfA/+qpFgy5nJaOyZ6CFNNoHo9xYyUNWfIS2ho6D6cs/N6AWHQgGg4JAIF8RySkQFMzyYSP+rKsrkTxz9fKXN4emMyBYAil+6JuOFrhWCvSO3FkM3diQVokkrddScEcY5ItElMB+u40k+S0TXpO8Gw/Xri89nwsEGtrdzQDpDl64Ml8COQaQf6Yc6fGfe3j3NuwjglpKpXzKE2XBE5ACHU6/5PRKqY3UajJFhdx38uSJelRtgCSU9J+nRTXBZMr8tB/aCGc+vk5fLXwmW8PzUxoaXjHUdqMM66t4+L6CywrR7A4hV+AfK+jYPtLCLkGEC6qqoBUgNEE0h/H5p3ylVzA4yIpEbL8cHp4S6g6LjfhdBIpaVZNnzl69tDYwEMqQxSiB3Bua/pCHezOaXXgTocpsIo6ej9g5aR6IfPkKYhEOKER1PPbzdnrjIYp1tHcN1WZl9Mr9Zw3+gCMYbG62l0DaCKRtbHJy5DYp0u9/9uwcMiHq825qV/IpaLM7/F0eydlhcSp+iNIHirupVclz8g/2YlE0i/TJ4rdx8f6i4Cpu/fpRkTzyzAOn6kGajw/pi9eAamoNNbrKSi0NQtKIbvcQlVJZliO6KrrmpwU1RT0qApPJeZT6bU1l9adHQPIjSFB8Ofxy6qiVJGmsowJtrbP208VHF+fpJNeHDLKQmTBCmPnQdE6AczMLpkbQBEhxKXRjG8UV8MYTcS43o/i717vMsT3976fbGyv0/d7RdCr9cHls7pzH0dDW3tbcbnd3Bs9cnR9upyu8wpNjk5cujc3ZPLawLQAL7k0/RZnxJpXkgy5vwOkPOB0B9NsTHcoDKaWs+h7t/rzkrncVmhLFfDaLcM7iAxYEUTTK+eJ7WpB8++O9SK5wqnRfF0838nUVBh5qNlBoV7QYtOWLtHpBhVxPkV07UKRSWmfND31CM+i1R9DBqCDL9bV8/piSKs2s0jjRgfYSSDTbeKYGycwI9EYkrcbPzp+/mOgbuNO3WBBIkRzOwFYoZMVGwWzGh282Co0EMhJCoabYPrcUj7MD2gbI/7y4gdiOR7/5/unG+Gi0tzc2CkV+NTb3V0uHx0GncNvs7vVg/9X5y+Fgu8MRHh4bvj0ycgG2iNwPQL5II7ClnR1loqsr0AVJOpzAqfgUZUJJeXdXfcuJ9XpXttDaery3tbWnJ1TMy3X80B+ynM/ms5nMVk8T399DL9XF8NQ99X10TrastjaULX5YhM2B/mgr4S97gIiXXKyqpFM2tHRRQXMDlSRPvTouVKmthAFqQrU60F8C+V4FOSWWJFlHVsdozZy/NE2tXd8AgzSqIM1iriigkzDTejRoQpXiUiJyfRskIcNnsInQYWgl9QiCeh4P9cajoxOS9/RMPB6bnb0mbZx78UVXQwddPOJuD9qD7mD//fnL/QAJQz42duvSCBQJjgvUFHolH8rTzg8TX3Q5/U6H02bxOAMeSQoEYIoUZdXvCbtNJrur2HqE7jfs+VPP8cReXt5/xEwmky1Ee6gz5IPs6kULGp7KreItbW2NJgJlZIRMvrDYTWFuqOjOgSMFpfxBRwM/fAkaREyzGHqDekIRka5lR6kByOb2QS426jM5lcEPy0RShm8Es+z0InV2A/8P0pwXeJWAshHJEsG0lBiNrKRIk5BkJATHHR1NeTe83pVI/HgI8kxJ6ZXZWGz27vjGRnpCcjpOehwlkJ0McorOxlJo/x0gKUcSSfKLyJNSUpmQuixOp8XRYLGBJjWOE0lfUvIGOjx2F6qLqxjlayLxVl1+Cs3rVjH7/v2rdwXUm5ayMjppo+EUSRMTdAyEaNCEj1bbUrEnZ4x0LWqm0E2DerrFnGjlMiHmN8upYeRNMLgiOsJJTQ912rTPXcP3NpAiATJDAytUbi6fQZKkUrMf3EZZzKmnWVWQzBE5nXIjrRLYeSGQ1gKzS2uJyHOJk6R3eTQWiYdCgJfe8KKNicZ744/hBcdHZ2fv3l1JTwDKMRspMtjZHnSVQIZtADk3OUkgw356OLTpK7mDH5GkYw5kyAaH09PlkLqQIZM+RXqMLGByEUpX8RTfS3qEJwSO9GyWvfn1zdu3f3vNRlK9QM7AouQhcR4BqOLTDS26PdklWkGyMduHsl07QBzJBchi4WDPwUpWcS2doauiCX3aCNPA32t1qE7qZSIH+vuDwlFVkV8P0yQkagnUaCSSVKLNIp9VHyKQZn7RVyMvADba600lWTa+SqzNJJZOSyRJZ/jlViIUikRX0tKj9OPrvfHj8dhtdMyn7+L57gdlgsLU0+FwAGRb0OVWQaLwNLeD45e3RgCSFOkL+Pjgie/BzhMl5bQ1dHZZHBabBVkSIKUk9OhbO3Vl3QQ9uuwmV26zmva4mjZbWsoixeJW9v27N2/u/fgvKttUYjiiObL1nOZoj4v0BJDwKTLf1DtUYai4UxSp42RBDlWzkrXkvnkKCCFdQ86yokZTVn6QT8fCpxPIDK/rqs9UfwYfhVpvqHKDWX6aWrs+qtKqJkGzvp4FeYgFSbI0ZZeeX75//ytwdLqRGcRsDnnym+1tGPHnsVg8BpAp6fTMzMzN75Pg+EWXpa3DYXO7O9vdpMgLV1WQ4ckLk9dujSwzyIDfV3qSO78o0glTp3nQQvciOo4dg9VK7TxBhzjyu54tlwt2ByCF4nzvZk9PdctmJFoQXSiCsvzu3uv9HlFj+O0mGhYkr5UxyMJh6jcAMttnqBh6xXEt4yXm6FxIuYanWBDbTTo9qk2FnjfDqgzo3mv03Cge6P9s6uhRDu2vh4fPnp3sH6QaI5OPpOCmKN7ruwOSDJKto9nYeIhX9+31vMpvp0289Wdz4fCcI+XsbDSjngtyMRKLrKW3t73pkRsxPCvIkadv3ly+Bj0C5DGLrc3W5h78DSTsD7kfupZyZNlGgvQv7IOUJn5JBlydhzrNnUlFIT16vUryyX8X/AuOWNNSvUmAIu0wkEI219rUUx7KurKiEd9Fd7H39jWvkbN5LN38UaNRDZBBDXWDLoEeBCBFIdddFcGPsrmvk435/xF1fiFtpWkYV0/+SUxCEloOvRCiQvZ4lo22YnOCsckSydHIJGgXhnHWsVnao84MgjtrB9uA1aah2W2d2aEIq2S7rdItnZmLhRZ2G2rvCrnJCmuxgS1zKXuxN72ZgYXd53mPu3tsjDElnvPL8/77vvf7sgGBBs929faCvBJ0nHNQkhz0ZUdBEKlTL8d5XUpbrFiMxxeKAvLy59XLs5sc4qEkgRI4wxYcMCLwxnHoxLQBMqRLo4PMPIVk9knv65MN9lIyWq0ZeHtbO6VfTyNWD79/HRzvPXryt1vTu+9XyBGWPXpqgCCzGkFqALn2ua3ImaXVrWu7Qww2bCo6Ocb/+XbESKpZzcqiXlxZmai8nRh//rZWqxV+d3YHiiRIkOwJ1Y/6X3U1A4YW7rbY19tz+vAfL77p7zonO0zh1t/hcXW63UgOfR2UZH9vMNj50U9QZlhhs7E4tRO3R+Vg2vCQ3JHP63B2dPn9LsXJCQa3m9U2jNwrrX1dHdC6hyBjCwISgpQxXVuSpzkW0R2QABNqvVteXm6FwieKDIRtKWoJ+44gU7LnY9puWsxy0NqyHtzeufUngnx67+nX926t/PnZ9HS+UnlNQdK0uesDFJkFyMHLawQZGVrdmplZre6+jIwkIUghacvy7duUClQaCpbJJ+PjmbfPa4XHKzmAfHn2NoM2nwVO0zqGcbe6LSMEFUiH9N4hwnYH26VOJKgsHjWPFhEyOvzIC/39Hm/7w0NUG1ZP/d39nYZh59AMNYeXpOXZ4+v1+Lv8PrcHyY/CvlT2C0htGYRZd7HTohgrbsbnqMj/2naRAet0QCRp0SX2GAelUqnRI0P6hClSVENJdtqFVFJVh3DNfToeCEduDR4INK8/BUimjzx+Xy5PlucnRY/gOBpJpQZkoX02PqcVAbI62BcZZivlFAAAIABJREFU2lpaWo3evFFNjanpQqGWs0nWJp49W8kAVUhIFp48HnnyvFabKNRg259+8YWhyiEkjcP3fnahEeg2jB4JiohD5uHfP+yXjZFoxi6fr2lZFlLG+452p8Qdf3tprxspXOPdIvJji1URjHsvYL2b4qS3x+Xn6k9/B9XoEZMOygytBHEF9baLIGML+5vFTdi1fM1e3j4O2JK0jRvgVKP5tNmw50bCqAul9TOk2yA16V4sTBRSbL3DY40ZpmEGrIMHv0XOszIJz3j37qM/Psrn56crJyBHR6PJtA1Si6cNG+T5SBQgo9Hdta2+saya5BaxUCU4DueHx3MCiqzCr5/nVp7UeORqudzXP3ojGG1N4mRfXYhDjchuYU2MQ0jWX/nb/bIbigu68h2bFgz5aEqSH4/P2f6qtRe26sdfHtVZW8IULYaavR+8LrcLikWAdnDsjXvX2M4xOOW1ax2H2+lyevzOts1YbHP/DffuYtAGxuVL76w9YUiSYVbUIb3RPDBDQIhiBrekdH0mEwIS6tTV1HAmkZDfapJahgwUjmvba9PMm+e5D+r067/m59fL/xPk+T6CzBJkdkErXtu+UY0OEeTW0Oq13S3uQ66GBrgbdA0kJyvD46fw2ipJwhU+Hq8V+FUgyLs/byFmSzOqZgjJUjzcHTBCPFl6T2SZR2ck95Hlb97SoWXCaBqLQW+HE/FC8e7UA5TjQZ1qpBzpI63jSz7PGZi/m7tWwID9DpfLHVQUe34WgZzrGdpdLifS+rYFgtwvSiI5O7tW4mRMSyQJs7akug6H9ESjgdM6Aakm9QTUlwI6nLyAHMhI86KuJzWZr1fx/+Lfru2ucwpwfubiEpxjvlyez9ND4qfJ89HBZDqVXcimB9VsNh4DyK3o6imCjFQ/u9qXGRhLpvRQWrbSrk3kK8MT4wlojlzwLhnDNHigZNa++wcoUtfEtjUVya1xCLPuZq4LkGBvqFrj4RkHauRO9uxsNAJ7dX7IQ5Ob5Hp97d6jhmkef7ncMsOCMSAZNFJICPAM98rmZgvQop/LxKQvzStbAnmDeNLt8im955S2OEC+eVMscqHcjRKnW5bvMK0/kSQHHIkOV4DyRSbqQrjCREJlsyJ1SYPWpXNR1xNJ3XZWuITQ3NLMTJ4cb74kxny+PE9B8sfy/KfRuSwMeyGeZj6evfjB9u5SlLOx1dXI1btXo1BkIplK2kGsMFGpIHCn4CDxPoGkJiRrBdu0b/1li+egib/Gd8AkyLAkuYbwVbUjGYrshGkrPyAZkU/LaNz33fcpyo8P6vXWuyvNOhI3GYsTww8fLrJa5PiOy8Fg7Q32c/kc8x+FU9xBJSgrIWDo53odbXFEm/39/djS7K92OLO/8VHpTqklI4+WycEe0wRIMhOI+KeniFBnuxggjp20g/J3SVIVb4UKfO58ZHBAvODCfmsp/wx6hCDFtMvzMzPRdDadwpNzaSOtLVxEPj6DYLNa3eqLbt99GZkcGAHJZFJNFYZyheFKBTVODiANpgmiyaETQeYyq18NSHP0/0kaGmdxpFvSkFivGY2NM36Hwoa+xUOzmyANo7HodisPjxpWvfmLxZbZY1rMNsIUUNg83AhOcViNYzy4dXUgMfdzB3JA9HoEIzsCFYcL2ZPL0bYvIDdjlx9wipXHndJtSFIYyowx4KkgpYbshgY1MTKWGNOT0ncnjlJAJoWjfsIRl5uGbqkS6tgwYvmlmflyXjwkOc4MpoWjxuzHmJvd3r4amxuCIGHgTz+rzn0cGUnZJLNICPKVSTZcJPF6ht3HZ4TNvoLU47lMoZxJqOKfmdTyzxu6ytOX3mh6SDxj7HR6lG/+/UJRmhZB9ghI73KzUbfqO1NISpBpECQ54tvxIsKyk1JkqFaQLSK0+HEnbYCKvauXB/W3A8+44SM3N5H/7BdvsP0JBcx7GxsXSqUdeBE6R9PuYegJCUi7v0YfyeCRnhJF6mz1PhFkiq6Txi5uUkuKEnh58bgRzlbKCDUCcn0aHFfFsrNxxBptDkF7e+1mbCAaqW5Vz1/9zbUtI97HcCMvqg9AkKNQ5JMojdQ46Sc1wykqMpPJFEYzYgqssdjIi590PcwgyeSHGlUN3Si5P/zu+399F9zYo+s38eYa8eZxvW4ZjeUrB/WeEGUDPYZ5V29e4ScxODmIi/TIicisyPIGVIQuj9MtKx28isfJgtuvuNqVtmIVkvx2h1WglNSLXGqwc2DakmSkpq+xQRKQnsiM4PISmbGELULAGxshRy5EgCSzwhE4dVw17coQXX9cnl6fhxrL6+vrAFlMC0gtzaBtFH+5vXY5NhiJVqtLFx98crU8Z2b7BsZS+DtwyHp6tILYslKpZBk44CdxhzfV0oYAMpeJnBqAbQhJGUshOZ3+nC1+dgQyjOb9F/xMgu+9zT1UbWGTHONW3aw3mg+XWwb0yBgghQSOo/sy2819yDv9P33lO9er8GNCFC4U8Tg9MjjJPjUOWHR2InKjstmPzcoQuDSUsN8WJG9vN1BQ93DIlpYJfGMjOs4QgkuM5QAyMYZzB0hbkHSaKXnMsG2HGwhSpyQZo3DWgYX16fV1UlwXRcKy00koErEmG48XP3hwYyY6CBd5c/ar65/8h6vrDWlrPeNqEmNIo6hYRFgh2YFwbqAe22BywjkhgRxir7JI9YNUsLkBa1JtA1rbi51QrUHsxg1tKftQqeIoo91dYRvrygjrxw2/GAeea4Urd9/6IQRCCbGhH/Z7nje2l53GtLHU5vzy+z1/3vd5nvfOekAuCCTpx4JuUWn0NnLLHl8XpTAqxVck75koUbLHKwmjIp+W+MEEeJiQDSh7e9+7/vnp5OS/Jyc/7lKWgSR8SM3sHrzfW762vVPoAh093Q0cOzwHy6IU0glH395M44kvXqCEiOa3u35xhsvJAazFaWMDCv07Wptmp+/N8zzHh6LFSCC5+UpG1OPp6GIXg/dixJC2EPt0bdQAqopG+tbJWYfgFoyI0Qh/hNuG+5YJy16VL5idJGO4WlxdTYOR2QEwEoQMwtdk1Mz4vR34Gm/gdw/WHn+3sTKdk5RgITig6IKUOrXHJvtz6yMaBZK9n4t0hzpUJTbaowTc9M509jQsnF5fV7eoiVYZ393lPzEfP306mkGSMQQTiYDn+rbz8vbykUptT3SfHpY2vu+C2SNGtrssF8/YuYfOTj2e5KdbRNM7jWWg/BJIOhyOVkfTg/cfDw4Ozh+cxfPHj4cfvhFjyzbfqR0e5DIcXkM1Buw5fHdIN4ZHySLGqFSeQskQyAp+ktBDn3H06cwj2CYgGVQpPcqOrY4LRo6PTWbJRMb1uEyZdkbNw9csLg14+9eya4//9uRKv1uLAUkV/kjXCUr2Ot0zSa+kcPzTq55CCdEkB7yzgVkv/af5SrF+82aQ2kB7WdiUg+NV4fBHxvGkVELGBfPY5RkKlu5ftl3ffEdLwrhHgrKbvfbhts0K7lENPsD7yuqgeow2V6Po1Ek1AsDTTgqHS2/lq8XRdPbsubPnz+JxnneLnh98/HCdulY33yIUxMfq43VHny9mAEigZ4wOgn5GzDCIh0xIxtE4xZGD9DhZfxEi0z5Ed0d+YmL1VNrjbCLpUjMDKiWIMJEPlgYQgq0tbP3671cCkhaLSXFVjROSBr6oMD8SH5qhm+YFpy+shCTlJOgKrHWzVqFfu0Hdp3pUyruAua9XLf10UgKKhecIe+hnDKmFUv3T/P39t8GGaIiTrOz3D+FH2i3UzgnWWaw8osom6sctndzVYLfbbZQsIse2g42W9pbWltamswyjuMTW2/ODw4eAcj9O/rqbYxkYR81AzEi3EwaQIU0jMSuEI1Bt4Bji4JxwZE8Dj92wkd3db8HDnzESJjJOhAQCbCIXn65kl7z92cmJhbmN76fdXPgjRcHmKBnJCLOSeBmSqQuM10p+VoRPjoVW0fRkPpkq1Ws/fRvVe+Uo3m0Ub8QXL5VKGbjnGdryZjejHtFhYe8QTpDFlUk35A08Mwcftm1U/GNxAUg7bynYuDBfJNjsZCiyRPzYStOLmx2Otk4aBNTXxPVlBOAXMM8RlNfvv5K7YSKRS+NNQ8Ua5S9GJJYgRsY0CFqL/D+OomlQj4QIRso1KGZCDJX/7nEufepsxsYnU0kmZFBmZWemrjy9k1oiZS/cenn10ZIEFAlJQcqoToYiYpz2gHHs32ir8/lEMHHKUHouLJ5cyef6zXIuGjdN3efpDz6n3A/OuDsYhEmRC7v1ekZWZRGq80omib1wcMjFuZbGEMT2r8ipUKOIrZM9tFPMDXC2OdocdFaD68KF1r5mOO52h72JcSQoCc3zDYlD4YfX59/JtKUg6xT0+EIMZCTiToQjmiFxPxZuqYEj32NI4EinnhGKMlt+KEYO5B6v5saIkEByPH2q7KCKKJJM5MK9p4spr3syO3Fr6x8bK/6YEhNQ+hV5CJZSYUJCuvSJ6YYu2kbwW+S0s84wJHeufwC5US5RzJfAynK5WivXKpVivlBIZSj3Q64jD6SKKfz1USkD66NzYMRgyurQ7v6HbxBhb9Mcd5p5QTNMabCKjWugO3keJ5VkOGnJp8/R2ma12C7+0tHcYj9jRQLZJOBjIgowBZLnZvYebr6lFQAPG76QD3hFIlokPBJWNKpLpuDR0Iic3KGlG4KPIT49LiRDuJzgeDxJih5z42Nj6RxFkSDk5ADyRvBRJZ8dD06RiewPpLJTE3NbG0+mhxlEcVCiG1CrcpTPpBOMDH1uv+GehxjXUSIfvzFpFlPm8fFxtQYDWKtWa/xUrWQKlWrlZiZfyvu9Sr5YqXyq1/cnw96BZFRYah0J5PsP15FBOl1iCprFyZmhBQ6G+djJNRjWtrZOZwskjbQQjrrdyoM7W1osjlaLvWlopiFsAaC4wNGOmffz/47SSi1NlIAbQUhHh2eaiRFNk6hWjO8kpGhCczpFlCAtH2fIAQubMY88u05HeRKAgpHpU2UTIRvK3lnJzk6m1rK35qDsLLNRGo75IW6/242sHOaP+Ag4jS8XgchwPxt+Rp0Px8eT5nHRLFeL0VSxXC2X6pVqGY9ksFStVcZr1ZoSTgTrlVoNvj2b83qzd17t7+/v7R0uP7z2L1c7152KLhoLl7O0ceEk7KPIBnkgg6uZKqko4uGKLCsVpOGF3dFEpoOWMj9zkes0aJthZu8330ZpnTbCqWBE0hW/O2Dm/JpGiRmogGCSJE5E0cXqT0SJCBx9oo+o17ue4NP+wEjk2oQnKTsTJAOpIhqXM0P56XtP746vTmXXQMjvN1a8wkDSw53LIacM9/jphKLI5346wVfA96yxD/H1aNh88XrQNFMBcPKGtlSuleulerVarJfLkdBNsLO0CGxvhPVSpVip0cT9TGlnfnMH1+by/WuXO+0O6vTk8YZ0EqeLVypcCHQQS9KKuI37Ee1W6tlGBN7H89WsVLZLMLZamxi6c6LiVcDJ36D6uJmnCzkFzsYH7wxVDyruUSVwLCGSjBl00it5HIX4qHOCQzDiW6RCX8P6K4n1xCwLOg0Ewcd0mnBMBglIVU6CjsHg1PTOvYWthanpibsvt64+mZYk0vawFPO7103TxD/v8YvlCV6lENuLfPF+zg+XLr25DfhW11+HJa9Z/k/6z69NCLgARYOVxewfeyLlaqW0WwcTZ93JVL1UKZv9ejz5Ng+jqtAI+3dHe5vzv3LSaAsG0gIIW5HJ0A6iy2IT7SFOWMi2Vl4a7us700LDMKyUbDcDR4ejqQBpCxNJpYXkeASQhGwmMTJCSCqRkOKXEoFYj+HOKX8Z1oZ7BkeHwzFhKw0RTiKaFDBGhNPp6tLdiURaOOoxhJHpHF5QWsOEzKhqJinLma78xOLOlYWXBOTc3KOrj/olvwRNQ9tuwGPmAl5hMdkQft5U5Af/ia4XMI0jxy9GJbNcvhkw0+nU8c2ZEtxNqV4210cUAFkHkrCVfn8yf3RUKReleL+E9xql/Q6YYHywu0d787/vtFtoCdflpHIAa2ennXewqUDN0n7GaqPOGprH0MyzdUHNRqEfpH24W+gQIfl5wUSueGmQdCARXu/vCoUkzT/YE/b6L90eDkUGSVo9xsg6G3qDVywQi2iSokHZwndTsuidXV19fGvuD3TuEh1hBWIiBhqb5AM7mZDRLkRycDVPF17OLdydvvvbrY2NFbd/WBqmEqpBUrWbD0JlGMVaOV1vwEM8vcHzpR8u/fXFi9vrZm428fWoclwuDniPj6OzZko2/0fWFYS2cWZhS5YVi8YJsREYHQJKBgbVhxmxYjQyHqEBibGkgRGOC6aGzXTW3lgrexYqdTYktWlcxJDFtWlE6CFhlbrBrKxloQmxSxMIziXFsMk4bGZjH3TIofRgBGIRYnPa9/6RnC772ygiuSifvve+973//f+02++O59urQVqFqNbVvA75MVw31asHR+80a/qqvhFmAUlcKOFQ2PKHLz+9R54Zco6MSQ1N9XvO4RUWuHuID74YIMB5A26Xy33G6zx7YNAzMOBz9S3fPXiCYxUncn3eOWqBf46MMLLSLI+OJ3MRWZFNaiKbmjBGU3JOjlARYQw1Z2KC5Eg2izmTTfRgDLFynJm9en99fX2xVLx0afpSBTu7q06GxAVSw6PUzBQ3b5R2q8XrM+uL65dv/9Hvz0aAk1lO9kdyTsuRzFOR984IC5LxX2kM6nT6IQApG7bOMAuZutm0mFS0PR2yl1jK6nQ29ovtdltXQbupVMHOH7e0QlRvzf9yfGy15otf3bxzVUwAiFgLkWooJPDAy+f9uNuFl+ue6scB0ykyqEKugB30uuGty+124bju4CBudcM/ubx9dzfvHBzFulA69Q8hI26lgZGVC52mlQIAZSPJTYwlTNOgUnVZrue4ZIJNEe1OYf0BKZM0LgTBuRRFEMZC3cXz4OCKN6sQ2rMLDiHzSEg1xoPUFL/Y/Gx7t3q9WFqr3r58S1+IAo7ZHLkBOUOgzDkgJkloI4hAQwhpAuXDh+kHRrq2ULhmPwY87aTM2Q26sCQ3/IJlqfutTrP9Lm81p+O1BXvjCZRB+ZalQyl5bFnvvp364Pnyn8I0+h80/vADUEr80d3vhnx4gLMfbzklKtM79eXFGbQBr9vtxnG2U3jLRf/AmdNeXx/geHC0L0FFer47nOmwkQz6TF6QylBJ2MkMl0ymDGMixckJE2Icsl/drPlT2WQKn55LFBxr5G7VM9rt/HcPrYLXju1/vlhWyrOzTDhPGAk2O0RqHygii7vbpdLM4nbp5s1SpbK64C8oppHO4K3cZJG2I8KYdvKjAyOQEX/TaaOu0Eq8YWbrjYhcq2dzkUbzlRws63SCBYluW0+OO/ZSXbTLMat1fNyxtDDP70+X5z/bfPT58vLLfJiiCB8l8ovfPIT40ACKDTbB8WwsuaeGHK+BGPf6MEd6nend0/1el/ecp+/OTwdHTyH5g3WKXek6nC6S2HYfFgHJZrDOZYNBv5GMB+moSUt0tFBWajV/IpEMBiGDsSx5sLiAkyyjY86GwwmMDpQjVzYURS4wvcDm1fwwLwEhP978eHEXwr+6W711+W9V50rYZ5ac5jJcF0UnP2a49Ht5SSMXnfVDuhbPpg1zL5Mxcg17L8N902yDSsEnNZO0DkDy+VZLo21riRJ1/XWro9O0dDhLF8SEqopP92NjYhi7IycRBHjy/MHyvQG8NuQcubsLmOcLBAiOHgASGAkJcwCcouu0zxfw9Xv6fjr4+yE+jh2PFqgSGUI730USEQgJtNXSgXmRXFCgIoWgVChoZU1TVY2W4zI1RuWwpEyB5xknVOxubzsXnvQW9gkunAXaRKH0cZDMqyDbMb5HyOsz29sgNYvbW29hbb19saqQC4V6CwDkMrkeHXvrIVLygVFPp+vpTC0tG0sQPkBQcDQNXb0WVyKmZjWWBGm63dro2HSN5ZTXFgAZpFmBi9MJbOaJJKBFISH0sOQJM/mj5Xt4kGmKzFOgl8HaER/NAD4bsqTXQzq6eP2pzxvoAxyf5lG4cJybpsFrnCXCTQZzgVMJqmzREzuQIeVgUDGZsiJKWjhEHkUelSOpVCSLJTIrOCA6YoMdDEzhsJy2AHauJmNRhglLvLPgS8vzhJClxd3q/Up1u7p2+RE+oHdua2sLoHxlpjlcwETgJsL4q+In/fA9mg8e/MX4vm4Y3E4d1Kb9+B9LFoh0Q5PslmVZWiFhyOP5dku1mt8wYjgY0qbLhRgfpChK/u2bl4cifk5AMkE+70la5/EFoDxF/MzQIPoXnBMgB7XdngA+3O+i2+cs0PC+I8CR/M+kfF5FLKO0dIEcXsDYHg4JkbitRHIJv/K4zhYUUQxLjAbmH+yyqJgTsh89CPhwcnMUemGsJBMifrkkup2NEDLfdTYMCbKHI1EakiFBskvXK4trxdtAyJW5uW9XVgDKlReKgSdDCIhIRoCRw9f0/y3jAdjD+k7t8d6O3VzdiUPdY+k2RTeanbbOW/aSQm00Oxt5qErzsUgwodkFLcRGRHrm0Y03X785BLctSGMC+ysoYwhjiEfd+T05GOsNDAKQYB8D2Mf1+FwfgXC7XISRXpcrEOgj/rCXFHGOYhg3W4YvOKPiF2KJiFKry8nUaEIxw2VFLdOarkqqmi9omkgpJpcETo47HRiCYcoZCfr1hR1kNnp48smG2uNjL7BnindKa9tIyN3q+uVHiz+uzG2t4ILXt5VVhZwxxlNeaANJhDvYIS25EyDrO6bJmd/vKLXGP3eUpWazo+nMAqtZrbYeszoNW3vaaURDG3ZDj0msoLU0gR1lmOhfp5av/vL1J3cPJRRtgaUASwIlj701LHYRyn//DjcUTwFig2fcABmCd8oH7wA/SJxgF+HvsB/Zi2NstnevG4PIxO0jRDIUUbI1bsJgaaUghBlJFVVLU8PMhqiGwXREjKQZIQYYXXavihztpsnekFgM43vyyiTfTZAY2DwGduWLG6Ufq6ViZW27AoRcnJsDNq44PwDli59/rqyu4qwQ0hIw6+oNRvcJjuAjFQOEZm8vZ4KPaSw1OxZFlR+Dtbeb6rhitRvak9YsKDNToBKiKb62GDosqnSu9Hzwy8P9N598d8CPQ1YURIpihS4tcZcROyuSmD/6dMo3cNHT7+kfOuMGlz3owzrIhcUkJEmfywMp0t3nnJs568w+jow4Iou7V0IKa5lhkeI4SJDgs4I2TRdUjdF4phBmmLwqhcPReI1TuCRUkaSIxBu3xk/QRAixQMPaiox48b2l5icxsOcrpTslUJr7ENiV9a9uVXfnVuYcPm7hgjdv37548eyZ9co2TbtmZHqJknOomSE4Pnu2w6Vr3E5tz262laxiW9GcbYOvjy6Ug3KCaepjUPpEakGTiZhsNAoeO3iNjYrszQ8/HPjy8Mp//jC0fChhB7ULpdSFksROHnIeKPhHUKD3fzB42u3zBAIXgY+/OQ2hjZEe8LhAe/qw9erMAYy8X2Q6BcEUEqaShERushPBqE2HroGyb2iaZulMGSgphhU/6A3g2OUjKSDHsD0eErpmYbh3wD8UVv83sP88P715A5SmNFNcq1Zu3y1tg9LMOXG91UMSocR6yAbedQU8xyGSHIlt47+0nW9ME3kax9teC/QoTVgz3qUvJCPjNrpbmerstC7YKwleoW1s44F46JFuF4SxpXq2TGI5GxavmXghkl3MyQZwCf5J6lxMJNmSQHNGNrEJL6CS2Ih36Sa82hdKsqfmwr243PP8pmVBzblvfKBDmWBiPny/z5/fzPBDjgtptyiv5OXeofV1Bz+fM/dRvevw81agJ7G9670cGzc7+SP5OqavzuxkGgNBn5NhnONZTVZ/aTWz8SJ76ZELfeM6zFoB5V6yfI9F55BSPQQoO9XAESSpMcHLUFZ20GDCNGnSauGgManwZqId+LFj97b4gFxw/6jB4/C43U0838SzPgnahkaofMFcLp/MhcyNNrOZ93s+VWbu4t8yIwuvh8mA80Hpl4NZw0WZNznaScXubv2CCHKgMxwe/eryIJbsxO3/EjkSXZKYXVsjWy0tDFEEI6k4pXZS4Zj3unm58EpyFF4NNUgFqyflTa7n8iG2IPUmKVshLrJWycc7C0MuSJ4s5bQHcxzNesyDWaOx6vyznn88yZ6eWFTqjAt3Z0eU2EweIiRJPH3yWWWlSW88VVZ1UK0uh5JtwHJjAlWasNjs2kySyrNxmVKAqAW7y2rzOWgv5UgW8qFcMjgSAT1Gcv9e//HHSCQyEonU5fOhvQGbWdnfHqJRUCaXzNaAfpRTOGYUjpggBzo7pgdm58I3o2Ds6OVvY7MJkiETt4sgiR6JuUGTC0N0kaO/WMh55LgCHBdWvKKUmp//XX69IIqy5Pf0SslCJMl4QslCgWby1xwOM93HOfO5TDAy0sgm7wsjVo7ys9bxrDFruvisZ/8Lo+7MXUFpIV1OfP7HBe9dyLEIU7Av/vDky9N6tVHXpsbtgAykbqO/satU7Sg+U6pEZuyNUJEP5UC+hZdqzKJSjf38EBgHz7kIRuz9m3E2PNs5Ov3FHeQYnY11fnsxHJ4jvlYyZKl0o7XXngPIURvnKVm7JEhFj6BVaV5ukSWxsJ4XZ667/d719XzBBp2vM1QoHHFK+YLEMJzUQPuEQEiI5Mzg7STnYFiWAXef0k7YkWTF18v3wdD2xVX73kZcpXQRhytzWAYP9sziD8sTR2G0rjUcNGgMauJtqNkwMaqayd0axYc1d/UgoW1h2XIsfrVse7/9B94WljGoukyjQDiCYJGj/Wy0dRDMfOfmQHT4SmfHZTD57a5ECWSiFHNEkWDtk5yHIxRBkX7Ij7zbCyAX/rUAnytySpx54G4BkJ4Wv3xdegXG9vgdXtpBg52OFAq2jxyik2YaWGso8yxnZsxxH+OEMYJlpjVZjfGR/dbjL7XG7JdPEeTyImjvN6qZAAAgAElEQVQRKoAVUZI+I1O0NwBtzjw9qq/SmRCkkiSh/YEvKtJ4bw7EmTHVe4ixJMXgn84Q0NjCIbyUjQkSWnFoIcHY0ZMdE7HhudsJlGSX0kkq9XsOFLmEfyh/FDgCSIoIstgLiUSPL+EliTgkiqmV9HVxXmxJrxccvR63N+XlJFpywIFymnnWamO8jM0lBOG9zevA53zYBuufNLUmKDi3Nj7TZqtPL6Of72P/iPsaWskNc3aXvQQzAz5f/FhvNKn1ZQfU0PWYSOzZAzmSXKNRuu/m3e8FpGUsxAS2cITf7MiJ1gHQ4Gz0ZjQ2HDsZgeo9R+B1KTATiZI6sWgvTQ5BxwokOcXcCJJXOE6SHAkzkDgjumUw+Mq8zKfnfTBG+MUU2Drlo2gf63McAXA0SzN+c8CadDophsPnfKBGX/tN7b7Ki0LPzo1stqp6asK+VxkPcSkIVBlAloL9p8gsZ/VaXa36FxoEqVEbwNxqA+RIcq2mFD3vR5Ej4Gu7kBEIRwE4tnbiSDMHeoxeCZ8NDQLUkgy7upQXosSpWzE2Q/ZB9XMEox8F6ZUWJpcUQSZBntCjyfJ8Wirk3TDq+D0PYCLy8xwnQX/m4xjQJUPTgWDA4aNdSRvN4+U0KM/WpqaOjw3GynFh1/4XALKy+vwqDoeIUlAcHlAWUJW0JDydPgrVRa8rM6gNWhyy2zQw4kAfuRtvUS0VnF3vUmR9ff3PPLkN5DMs5dAH4P+HcGztHu8Pz8U6BrqHgWP/NEAlMoR42FUKODOngGw1cxxBCd4mPTlPOL6cJJJc8eK8LabkGdmdeiV5ZPm6mBbviU0tKS9FQZ8jORzzvTzFxe8HA75k0mV1NFG0EwUJJFnmq9pa043+zM7H542fV1dVnXkkIEmy/uAqlRuU4urTR08uZcvV6lo1PhSr16r1JlNbmwZgGtQqq5204+RGrK058q10LO3n2t88237unOWdIEkDoSzpBiKtnYM3Y7PhgdiJK8Pdts5l5JhQOKIcHyY2SWKKnBxFjh5mi7d5r6+4Ry8c0i1eaM7FFE7lcsrjF+XrPlmUPJAlJQqGMoqn4ynctTsO8kr6bNDSEVujJJsYhrl2uW2f7uKzW/s3stVTlcayG48El/21aO55/OLMVPUxHY6EBzT6Mm2Frq2tSqf57SfgbaCpwr13hUzzjtcV+TZkluMXLvz1TWZXL1y4avn/IIu+IHoM1AHHjthcODZwIjY8gAkSjY3YHhJFltxNBm9UZCvDNQHIkrkpUKQEifPl5EvS/Xh5nHLwGbOW1ExaTrX4G1Kv0h4evc2aJYqSmcYUvKMctLUxRPXRNMWyHNvEIkaAydz8/UHN1Liwc/+L8mOVWqMpO3GfrFco7WOxYB96/IRs6KCHAdtUpq/QaT7UaI3ln/wRsqThgEYVNMP0HL0T7l+1H2reVKTl+PfffV//Rit09fOav7e/ptT6c/+sqblwrv4dIIt9Ovi6LtJ6lyyK43XDgWBkfDCKxn5rJLDWjJqZJo4pkcRwSJNrygaUoMkh5IjFZ2ZmRpy5dy+dFkVfyudpedDCN/3al+IYP+iZO3yY4inazNHK/QYcIkSKjJWJ/23PKdOlv2T2b9wAkFXafVXnVwXX3uIcZt8cMDZumMpx8RFAlul0H/5Ko4WmXKOHdrLNpIoEce/YNRjNloZs1v7jxbbw+FTN1PEtIAmn9qtTNd+9HWTxbP32f/ATSKJHZKlwJJNhNynY4+PR8JqSHRPFDJlQZm5c48X5cAgJFjlyHAW+zi0tPSfbJmKKHPIrq7+8OAO5MiX7ZSg8aXf6QUqk0l6/j/vUI3Ie3umEjAklh6dhpGGdHEcoegjKP//hl6eqpkdAkscqy3BTuoob4yOCXShSVEj29DQvG8sr1Ea1FlciK9oOYJEpK4cuEgZwVWsd7vbevXSbkPzPpiKnar7eBFlvaW+31G8qst4CsXm2CFIFp+CMpV6hiO82WY4p86YA/U8wEum82w+N+JXY2YHh2NnW8eno8JqSHxMKxi3VBpfSJhdOMvE4fMbjfXHcHavv5NA34W+eLy2RYrOwEKKgu+Qpcm1Mvgd+lu9BvaEKKfl/bJ1fTFp5FscRrcgKZmazuBsehrB7E1d3WWlyc7WjEExoXCstTEAgZUKt2Hid8i+99LoV2zqKOJ1hrllAW9QG69BSxG6TpmDsGneMSSdpYtNd22Zm1oxJH/Zlu8kkferLZs/5gbad9VQKXOHl4/ec7/nd3+/+rlqXy4F8aV5hsHSpGycVagWtULRDrTUaKIuRkMQyeZiKH3+v4txU6x9ee+S1tU0ySV2N/OJQ+U+/bzdrf3z0SaUcV/RBw0PacCUClQLICqUoBCT9kNyP/4sk/QeCdNiTM3YgUwapsUOIHHA0aXfspTYc0jjwY8jRIUrOJB372r32qDTEbh3s8zdPDZ0JLXu9mQAHHM/OzYeElUvlzvFNSl/eE+aDpXQiEAhEIuGMIMTIZbaxeEzwhkLhMJdOpK/juQw1rVaTZp2/B2rsyv1jK28e/uG5nvowZ9KaYOzY3sjwtG7SQinUNEN1a43dkNu4RgtGjhQFPer5/uM/OzF0eO2ff67Eu27Lq+R10tOLn5dQlmSJpx/WvpXIa0qTC0olDBRhvC0Fktj/iApem39fk9dfHgBSo9lOqVQLu3YNAakJ3vV47tgdyc0FOLqzB3JbtXBhEw5sA1rHhTselWc9WSapscOgq2Qz/uYzyHEphBzDAX+ZY/9e4/NwHyE8X3qw5E2nQ0K8gFfOn/ryyyv7cerUqSvT8dEM53S6fD4wZEx6CgolWDef+yuTY4d/YPUmc5HRqc38Mf2H3Uy7hW9XdwNCWqEFfAZKTfQIX2uAH+Gjf/9mvneq/nVt6VpkvFX5ofG5EsqSMgfqb948J5GTqS5lhVgmk2LbU10NaKFSityL8QTe76fvTPrF0qObB4HcVeEN+eC9A0EGLwCuZBDKpScFKHccjjJIvK2FSqWacTjgE/hyoezlGlAkKY9+v39o6Ix3GXzGzcW4gH90PuRdeQDmTGR46+0+EqWYFuLTV66MLIMEs1EIJ4QVI5GIZoXZ5cLy8nQhnom4AWYD6Iqhj0F57Mrlu/miflI9nM+ZGYW+e5Jn2nmLwWLRGo2UVqeFZtxIoyRRjpQanhqowIPjH49/1zv47HT5Pol11VVN0srxuZcljhgD9d/C78gUTQU6DCgR/knhUJUSzGYsXuCaAWXflPtR/f+DbEMs60k70NwNAshNeHgA1rZKdTeYTIEl7Smy/KmdoB2OXrDf9ah2y5K8toanT/qa/X3nT7qFFejD3WGBcDwPHHF0Tfj9WCqVl8GrvRznjYMOl4V01GplfQpf91b31taWcasclg3fBsNardHs7MjIyPJoJuJqUIMuYVQD+X3sXo5hqGF+8m8Mzxzl891HLUaDsV3bTuG0DJoNSpIuS5KmoU9N97/3zV86e2++er8Wd/IBoQEy0Ob44tBUL+F4uPf7ryQ4vS1WSpEgztv04BwOJLdEKbLaJkKFkKul5WzfQP2BICFhZ4KatpQq1QYQUymVB5odrJNtds2mypPcB3kh6JhRqTaDd5GmyLEOXyjXyIFft6LNQFpzML4+H3GHhETf2dF56IJWyOD6IRHkjf4fUYtAUSh8ARCjgBD5+XxbPouP9OFdOBnGMHj3OxIbLOtyRkG5IyPxDKZ5170ucJxcbquYM+f475g8YzjGm4xHjTSuYMBlljq6C1px2lAybi2kOJYF14vjTYuDHYOvcWEfmcCurpGL66qkkm/OLeKU9dTU1Pz7dcoabH9kFRU9PRIJ9ONKpRJSHeiKnozZJrhFwdbSslZ/EEiRZh0bIeTpSdo9mLPYSrY5krspzGTVWyAdGgIS3qcg3jRQ11p/fmTK7f7TkBvKIxd2u4WQuw/roze2Uh5fY3G8/PBW/6UlL5cpfDESDweIQ2+xRZPZbDKxLGt1RkuRSIBIIYrF4lMrYAbQ8NtobLkwez/qZIs53LeK4fMbRZ7mIacZUzsP2WzQNep0CNJgog3QkOMDQGobiCQbEpd7xl929j77pHQncrz4g+ygVgeZXHfixPjFi7+XysVieTUYNgixokcsqUHrVkLJrAKQCfOEzWYbnbO11h8MUnTnXZAqzOk2x4xHtbC5mzoIJKmpGG9ANh6ZCg+FuaWVNBdxcwLngv6xEAohRxzKXCr79AvAfD9eGOVchKKPMU2MWaOh0XA0HA5/HXYGAs6IExw8nMEIO58WwU4YFCegLT6Fuln4LJa2FvN8vsjnt/g8w/KMwWJqx5KoxWVdOOXeqTAZcMpGhyctUJxEkrZbv6j9O3RorwhIOV4Xi3vbKKuaZE0yMaayRFxdpZRKJJU1PeA20EIeApp48gdEWSFKcGMTfps/9D1ZQ7X2NkgY2UBzSAgCSBQmpLZqJ4UugkdnHMF3U7sMEl5uOyDz2+xvUrtz8HM3nn4Mu22Q1i6/f3GR28vrkmdfhpwOZe6PClGfTz3soxV6PeuKZDJfRyKQsi0t+N5XDoZRsKzP6gSkYaeV1etNxY3VVbSh1exsYVZw+iZhqFjMT141M0bayFh02skJreF3R36lM2g7OymUJNiOgQy4O2hiN80vfnvo4mDr2uta3FSOrCEX4568dU1iWVNFnayqrhpA4hRsZSVkNHhNtfQQdpBKghL6yIRzYsLlHyBrI98BCUUQAm1lx4FevV5ybSiB6xoRckVbOQAk/JdKBoPJnb0x5rXWzr4+LhbzIkev1xZoti3OcUJspXyiAgV5YyXEZUZJmRum1QxwguYRELLsWVavKANkS0FeK1hGr9czLqQZcRb5SXORtRKY2dnZ21FrLn+1aPLlfMO8jroaGXs+SRnwwm2dwdDYweghsbUdjfDQ4hbJFHh+g7f/l18NDbY+O11ZBknWiOOuzjIYTYtxwY+0iszB1siroP+BAinFdZLIERryB3PuRNQ20YsYBz54O7U9KRJJsBnVOjaNM9jzbKIYVduYv+sgTs9PQIKtk35oYRO+sbPn2r0ByGocFNo4IWoL+LnFT7nYysqtvTM+4DAhZySTdbpg/KJm9YRiACCyLZjkLmspnAmM8hvrlhXA+hQKoByAfh0aI1bPbECAl9/+7HbWGsizvrxZYaI6hlauP3l+1oAbEOCiKR1tUhg6AKSuA1IdaiXVcJiibI+Pfzw/2Ln2SoJGU423ScPFpWJxnUwMICtwBzSxslKmrKo5JMUlaDhrUyHDDdIgRB/dmDtp4/D2AR8M3HynRpYD8N3B5wXgRBpyTRKh2vFgah0Z/lSRbZodUkvX9/vIM0IMeseIzcZl3W6X/9PFk2kh9qI03UowCuHReDTQPEzRPqYIVfAqkZ+CdbmsY2PQNUajESiTmWxWWFpa+k82m/5Xwpp4CjRdbIuCbYE6Cd4NaQ4oixvW1dXV7PT07egYoDbTOnWHcOvxk+dPDjf+j7bzjUk7v+O4IIJUWqceucXE5VBSxnYGUSMSrt5hTSDp2oSCLS1qO4MpRhATWGphJ5Qoicy1RupoZomHcXghhj6yBHJG0gfoLpmzqVkOH/KguWRr4oN7TPb+fH9aXbfl1mR+MT9/gI9efv5/P9/PT2tspk7SX8q7ejov6fWXlAZqfTYoWMI9njJdvXYw2v0dG5PEQJ5no+/pLA1JYlUVRLMSrqcalrISkaT4Ar+/vZrT7YpAoLDxMDr8Jxp1c+JsKnQPjteNitaKB69fP7hBuSGV0eBo8Oum7sHr5zfwwZObT44vrUd/UHHzyfPXz//QelyIe5pK3b4/OTK07PVYIioqUyzPpTLHjSnA6MkHV1bd8r5OoLPmp90wiRoNKbE5upzKZNa9bp8CYaJMY4m/Zc+CZ/uKJJ0ORtzl0nRpcGP1+81mOHPYyq/XFxcXwi5bj1wv38olSy/3/qYhkFpq89FLpV3yS3DjSnb8vg3ZthoSORUYePYP/fdfiWpECGmotZQPiBegvMSRJxTzBBJEOoIq2Mkafj9fWNf4sUTEOAKkyVRYD27VNhhPOxsq4U7cZC+Sqgm8YVULVqXU0Xc6rp5Ld3Sj46q7rRMTXLI9MXGqnqkDxsjQsnN5yO0eH3r10OOcS5Xe7RVmbq8G09M+eYyRWGUYpXAmDisg5tiKWli2vQqzmstlMqlSinVfvHwZ6qQzTY4XFA9pXEcxEqGEC1+fvTO7YLV9IVffT0yVd/f2ZvTa5gYj633EPwUk9cp6LZ0t1avJe1viJfvPrz00bH15nZ7VWS1k0/Rp8tkFXgcVfPgCgZDSw0ZRY3WdqLEFd5USHuU3QlLtgAnx20FzPTd+6XSFnFvHb07Vzbm3R5eTD08X1nWnK+xPi5MjHi9VH4ZG0ksIt+dSrAkgmSwkM97JdBAY+zodZjeE0cYJo9nqnVtftNOOmD2RoPGdCwtzbD2am8NdJpXaXY7HbdBKMFC7EFQyLwRZhB3A1QyUs59ufz5nUxgWTIisIJLDyubaBi1A/pSi8B650tDczLorAFLf9hj/XFPH77cMxV+LRWzIAoGU8C/w6cnkMI9CAcIfavYRN1Zfr5NIuBqQgMd57QCtQnLLeM9oPLGR/+fNryGP0+txx9y3N54FPV4SR7bKU1Mp/yqkEbmvCjd5CKNMwxQ6Qx2nQJhYzGUeecOwhZBX14nzNlthE8PhGMIXNW3mt8kV9HEXfZW1htfCsJP72a/nB7ZnPe7EVVMgGX+5N2OgycpapbJeL0OS3aNXahvqqRuSHbaJZErJwE9alkZHv6POUnr+M/nsX0AoeVQpE1L9jJp0K8WSqjphP592HSgcR5ApPgYJkvXUJ3lGIOPeqGXksSX45YbXSWpdKhPHQjLnn84D42d9Cv8fN4LTkEZ4aJhF6P0UCWIG0bUFSSB55WBwCWtlZWNlZScYXKX4EercKQeDL6jzSa93m0nDu7qOUMLn7L9Zv7V9LVdKDAbs1NSm1tLkdK2y3iCDUZSNtSmbG+hkrJL6KiKw2oFP2j+fHC1eqxG+A0maLWgkpy2myjhiIBGvsbKOOnhJIoGXMeZABgqBueI33yAlPhOQOh3rdEFY6vE6U6TWDKQ9NTKdd8vbPpO7d3634repNCpbKOrM5AhjLpdahkt2TefT6Z2lnZ2dpSBbSztLCysbbC1R2Amv7YpFtrb0avXMXogljz2/+stmGLaShDKamu3dni3ZB+0QydC4obmWRFKrVVB7gGbmbnOtkRr46JRpEVbE9Elvy0Lxr7PnRdycUgG17An4POor5bQaZlLEo/GTUHBQFBBEZDZi2MjAnwtYganSrvegeCYgj3taWp86nfDWZB3LgOWFTXRBHmX+Z/DZhNEcTVFRbQoUKUv0xSbz99P5dD6f91NciaVyqGj8kg1eKbhANBdWPbYxh2t6NT8S2tsLhVhw2ePY3MxGSb/D4beLd1o+TSYT9lI8uqcm3TZqtUa1HOqsmBnvbqgF12bqAjiwJ0yDH/VKbiW+qjlfI2JT3wVsV4HXSOdBIIEMWSMVKWgGA7kdMTtxjE/eSSTU+/CHXefT1oozXE+dHMbkVDmZ87jzPpdPfkWa37lPGN3WqHM9WbYn7Jk1s8YXi+QnI7EIYko4IOr8P1lj9MICzodBBtPqGDN7Hznj0ZBNr1fAir4wbwLjGuzkZjgz37udKCUSu3GIJI2F0nYb7yqgzPT4dSPpejPtJ6QHTVcvN13s6Pi4Q1RZJyKIDKSQ7V/z6QIdrxLzhHyBiCuS87gjDdSzC5AmZiTxUy6Xf9BVnCnIEtexhytTa3CUOqYn3Qqpxm31pHLzg4OJxTmkibF8cStGy0fYsGQni72R0tL0gKbF6g+ug+UQ4iXvmsenbNarfdDwEBBmYSr3w9m3iVvb86WpHDgPa0m3u40GAvnYYtkbra0FSGpHWro8+FFTe39HR8vFjmp6tHEVnSdm7biAyIoTAvIutI/IgxSSnFbRGeNGHo9T7SOQh4eHhcMbZyqRunLyaKWG8vlhn0+hsU27FTLNsNu6nBvs7WhPPLKp3FBmCGPMpzqFEL+lxy8GsUtK3wLmzMyYxbM6txD0WkKWEf+WthvOJGZz7JvDa9Hs2tp+NvsmN99xK5nLxENjeua365UKaPNvduOW4XtsmtJod/fGucu9Te0QPZHkIp9m+iACgrRRJi1pJFqUwpCai0FYVC3mk26LSbn7Jcxrm1goCYjlQ1Phg0C+34zxY70rrbpymfmZKSfMIzjKpCSOGiSCy3PzvQNN88AYS79C+E6iCHUHPhUYSmXcrgwdlb1y1HCB5ERKZQuIbA9gOqwwmqtWi8MW+RZGsN7gNu+b12Amw5v7+9k3UO+BZAkkVVoKJeFt2pTFXDIV50SyodtQvHMOHCF/whZev+R8NSJJiJ2ANhNob4GIUoMu9QbQ3OfKaqFIQlU0kfB6U5MIEskwFkgeDyGWHwKy9f1WlYn/1NDynkQyjmsjaeIotaUjCoQ8Lqtz8dbg3+9khlSxfLpYjMBkAqFCRmmhjKNHQ9BoyEUfd6LuSucV1nQhlfZoenpwBcuQn4VFDtWWscFgUEZAMgz1jm7uv8hm386fuzYFkuN34V7gbRT67leDcLDx8Xu1Wmp9fTXQ3tTUIqQKD7I/NiSSziyQHSSQPLKRRFUsFHGPYqnhtyOWlDSK6vr7qxlIEkeGsmAv6P53kK3vtar8l4aWf5VIptfeSDoy7PZp3Gk3YQwtL+QS9sSiRxV7dVDciuBDDUutO7nT2lf6/m0xuWSy2QmVh4JrKE4fs4ysBh/6rTO24kG3QVn0ml+wICibfQGh/O257VwpFR831NJwLLX+29lBJDy70eGfGQ1abfHOQEc7MkExTyLgSy7SKF3aMGRRDnXmMojchY4XV1Wfr6xu4dGfC+uQdYsrrpo4jmQj7YUPkEgdFSafn7Sq6LgNG92P2sicdzrt9vl8jun7CumYymV+lGMFIFvs4HtwhE7LFOCoOJbE9xAeHYKndskrfdy+NGseoKDI5Rgf8v+Tr7MLaTPN4ni+PzQRwzJs17aEEmmKMyFOLd1CxuLqFLqMjK2OMY5pHRKHFaproWXraEm7QUN0JBMatU2cTkwpk/g5FDIJOhvXVnC8qcWYmxZZYS5ytYEic7cw7Pmf943a0t1XGsNrctEf/+c55zzP/z0Pls69Nxa3Xk11zi95WxjkEokyP9FAwTv90Hrx4rmLF7/404v6U1covfzl4b9/d+7lq29NOpNJRhmPjmJ1RasKpzFgMU3Lq2Q6QgZzirhFw0+/awwaZYVKLVMoW3U6KYF8/Zog3uFgc+ctRdrefmv7vyDdRZAW21p4zfY/FPk5czT/cXWVBnBvdyhNBfXEvT7X6gvieB9iJIzidCjSQz8VsTWN0KIGnUNYj5UDHNvpojTzquPGkOPqjZuPbw5e9QY624PBkXgKsSZ3iOR81IWE54tXnQ0NDYQyFpt9udXZ7pTx4YkaGR9EgPZncsyGCjyPpIW3uQKPFiOMI+FBE0klGmfrS3Vy0+9p5EswQb4uhpv19f3/PUwpogPFYrHYsCRmg0lFInpS2iwCSP4gf7wIEoYWe9gYlgjOFv7+gSI9NK7B0bra7zph7WuJzsc8nvmbHX1bL7Ze/dNqBUYzb5QKBIsQxeY0fFV/XP0RNgkIYXUlldoD96nSXL3rj2xQ8Zh8PDhIJAc/C823nzrVHkilfEs5kMxl8hPtSCg3v/nLuX9sddY3lDSUnyqvd9YfN5Ecq/CkAp4hpmitalU3l3KrCoVaquDIjQlSeNKLLjQe1ygA0iCXauTS060UtXlYX+YMiGbJ4tC2wZQiOlCw3zA+TuzoxrgEq962Ntv4pAAS27L8cbsIkg0tAMm/bcL3i5aL35Y/H00KHIfMVmvvZz2x2PIyBZnBqRdbL62sRrbjfMJtHg6P6GKjFeEJ7kskxsrq6gGCSXXP6uLdH/3+e4FkMrnhe96y5ItGBwd90dlg+ZWSZW+KAjeVOLlcnNj+3PVLcHlq6tuw03myvr6kxOk0CUeYV/FT7VIFH1F8UtOMhklqiiwoAzkHklZgHQ2pOMnSoCSOCqnaINfJlMqyY60STsWRA61jhIsgbfCd7ezCgWKR2BaMa9vu6fHrkytuozv8FTwpk2G3cWUXIIWVcfr47nVhn2GbXrfZarG7Y3TTp+1hd3FD0vZbz9Di1YEBF8K1tbevZTYW89Ds2Pf3qcX+jmuQIzZTBDGKGL8T+tPgB43HL10SnhL5RMiGBgaGKO3xf/31o7HI3WSGZkNsNjzHSlrI54im66+UxwopKnF8IJlhkh7n8TL16dMUW06eJi0KB4uUcfcZrPqg5eFxWbO8VCGXIwOiRLGCIzbGNteGWpWO1KgmTRr0lGrKy5qPHhVKRDF00z/bQeBg2wk0F2Y3in3SLdzZ5i0Hfkt/3dnfq2GQkGnY/oMR9pVdRJ82jkHC5o3F3tO/OEp67FgdNZ8Y6GgZG+n6fnnQOro4tdgnYqytI478kKgYnQWGwgEYeHbuEo5ZukQxnf719g6tJn68fdsfCYzdC8SJ43PCmPrz357mUtjicXhJlOXBUIqqnDyTxHKQJ9asN5lqTDU1x2tMFGGkKKqFwyJxgAAON9WdxhxJIMENbWkQzhUqnYJ7/KgpAlFNU6aXN+ulakotDbJjh0ASx67DIKcn7aBiw+ZXeGfbvkLc7JO8b7hmNO7Yx8MHiiyCBLvp8TYbD218U3S0FHfBbqyOuogj9GgmjsEuT/pLa/+jqX7rNeuH5g9ra9E9SDikvDig+byGs2fPNjaeP0sJOGWMvC3b0YttMYcj4E/Pbm4WCgVfMpnxZSBIROmnuVwOm2XezVjwD8EoaTKT98VzOV9+ov7n9fbSGp3TVHMckdpUpitTsSEAXSr4UBC9Xlsjk6s1BgXPk1o8oo2Sm15Yj8W2AUqDnCdNuVorKHKdSHJWvr4/tJmMBMQmLd7A7SEAACAASURBVMyOfT90h9huW2BfEYPNYZBG4wKhm2yzscGFEnRmGD4wCD64NTpwn+bHUZfZ3BFKE8cxl2v1EeRIdyov1KL9Wh3k+BFT/JgoEr1GXOe7G883dndTeV3cVOxuCTkcLaF4dm/myZMnM9ncUoY0mSleS6mnvng6FIqVXGnoQZUT9SVpnsxPfFDvKSnTVVXV1CDjofwbh01hQVyPru0IMtj6l/MZdWzi44qbVMnr4yoFY1RXqDToRw6zpNIgPcq19mWh4IYqD4Nss7VtiyRs7KXabmOp7trZttL2DpBGMXBDkRSd6M7OuHHfTGWxfwmOiy8pSySOse89AVff4qNFlzis69DMil6LeiQtnm0sXqnhxkZ0YeqGIe0qQEbnRyI+R8tSdi6bnZt58tNPM7ncAcdM5mkqFa0PPnw2UVLePkvA49F44lkuHh1xtnc5cQ6vziTTKcpMMj53SUWJjxpNp/SMkqpEA7sEBJAUcBC9sSIuhd9CqpJplQaNplmj1alkCoMOIC9zmXinC3PkG4o8BFLyFkii/C5F4mKLFX8HvqGVHTj9ipYLF3F8vOgyD3TcSAfB8f7Wi1scrCuFGINWkRcYI8R4/j0i2NTU2ITXpsZh77VhTH2sx2hPOj2W9Dl8SYoj+SwuAppdytAQp+id4Tw8vxms33wWay9vjxPJQDQQyebjhaAz2CWTmnQyGcUYGXp+qHB4aZleWYqOrxq1Wqspa1XLNVwMYvlReJaYECoErMRSqkYRSWm7ju6UakWQl9+lyOt22AAmLfvq2qU7xHNHMm1csLwBclx0WLh3BOsUgVyAK3rb6J7eN6VJLA/6BqyDWy6ruS+UvuLxBMzEsd/Kw5p9yNXVte8zRxytTRMiMO7/kCi7iWOIflq8oejY7Gwg7nOsZnzJSCSSyOdy/5nZS+xlc8nk8wxoZjLPlxLpzWUTkew81hkN+cbi0dl0NlOYDX4Qi+lNMiFaM5dSHOSuRMBGG2dMmLoKAqkipjzqpTKtlkoc7DdgRYjQ8hxJwUmtVFVoStUSQZB8dd0p1tosvAU7nBXTdjb08WilFEiyAssA+wIsawDJHj7gFKM23iHloTmS9AszJf193wPdYR7a+MYMjkFwHN3aGhX1iL5yaDJyoY67AML6wyO6iS/+hbZ/RBENzUPx9GxPIhn3xZNxcCSSyUwuu/drYY9QZiIRUuVGhsZ53F/wtEOTDcFQNHqvJzQ29iwenx35NFaOsawQTz/V6E00TeJIWE61SXQanZZmQGhSgUJRpsNKroq3XmlWFKSpNKBYxLaDXC5hPfLQRtA5UCR8FGthViGHFp4Sp9cWjDCtfCW8dRNIyHBlxVhMf9pA+gfwdq/sSGC9OjSyJQ+sHRv9Zuv9EOI1xjVxJD1iWJ9BsCaKhPH9I3Vn3hNCTFORJC7vsNfhBUbSY0+hEM/nUk3EaiMS8fv9xC6Zyc7s/ZrN5vNpSog2eJ5MFm4XloP5hyMlJSNEMtITnQ/kiGTs05iTz9hUVAGkvMqkUOuV+lIsQmpQCapkUrlcjRUg3FLAn8u7M1JKhypg5COQaP1M1Y0axbewjCaGmzdBhsOwnYjzHd1Gqk3XGjx+O4grawSyzbLDN6eFob3G06V7EjOAcUWgv3JQvj/468Yt4tgSCMY8Y2dIj1wTVvJTgVT1cYypPXKkrvIEBDncOLyvRgjSSwNb5BgvRKPZubmZmZm5uVw8QRz9t/3+xEZmLjvz5F/P0oWE/3Yik0kkE4mE/7+0nXFMFPkVx5nd2Z1ZWUg3KYmdpKGGpngiUdCERGBdOP2roMF1Ye2tkeP0QuK2NoGkIUzPdoFh1tlBytxSOu1lVIyzwEZDy7lVY01p4vnXGRditGlyyWXDP5dNLpv9z8T0vTezsHi5Sv9wzOoKi398/L7fe+/3e+/98pm89tn0+51prKU2tBlzwzTzyfj1L1i6sx0SbJav9rIYQ3p/htENXVLMODgnBwG3m/HgKDSwa+DIcCzLCSzFQS4P78HrMEJOXnBWVpAcS5IEkFsbEF/13lkbwaaPkZERu83mztrabB9y6ZtdW/u0lbbR8O1sIxaxWPUqjbNUvEJfpf+QtV9vrZG/vw12HR6enoa4p5/02FR/kNwMRj0006rhSOAYGvYEESwTJE6iDFrTKGOapD1fgKBnYSG7tLzw6p4pi6KiKrK+sp4rrBZuFfMp5Zqa0gEwoMwbmvbl/vcjCcNIJDRjBmJzM59OTnN4KEMs0d+4rUFyNHIKQXp9dMuAm2GZUMiLJBmSI9XiYwQEJDmwawfvE9wE0uJIfnsrIEdbtdvoSvu1EDpSrYpdk9JXYW3s0lv8qF2vQsUr1gca+76CGHTTsht7f3flwMAl4/o35zOXwM+8PFBPHI/9FAKeAOQyOBsDMhvgaC2PE1sYJ0/aGCfopWnopYHl6urC8sJybiMlJuNjqphKPcwWLj8u5DfyR2vnQaUg1pWUqWnG/c4fnYlKRjphTCUkPM3RkxEsuWc5F+aIPJ1k89ir6UaSoEIn3g8CobijOhRy1HmxmZijqT9YE0AgXeB4XJ6qShdTZYPssbPEb8sUCRHO9jKU8kIUeldWz9JaXrtiv4fo6U8fbWsVm7tQPzCupafPZy40PXvxEvTYdBBLPts2n58fxvnEaNZI8S4RhF8Tk5Ox2HoMYOI4z4mYZJpgteCrs6vF1WV8FtZTiqqOgSrlh8vF18Vbmfz+2msiWLye0nWQpDb9TeScIUXTU9rUlBQMm6Z8fR/NN+Pd1dV0RMOzNkRw29UhoaoSFkEwdAcLILFZzsu6HW6QJZ0/oHELdLoIIAVHxeWecndTniK+ZZN2J1u//8KS08YykAOH/xhM7L1+fxQ4QhiEHHEwb5sVhANHPFuoKfPXdNUavkCPdycJIrwbBdsEZw0eRl/Mry4/sFCaQFIBExd1cN8/qT13/2jtx0CSPgYkFzsj+5KGMZWOmgnzXlAyUyIaNxY5V2H5LW4y4gk1ehreEwpZd0l6sAYA9Iid2V7c5WWwBsgCifVTAgMZjtPj3mbaoMnWnR4b7ARk4+x/7vSW9y7O/erSaeP62U+GB26/eHbV5ngQzRrtGkdR4hEhcPSXOFqKPDkJVn0XrRvtO2hK0qgJegSpoZ/ZQJIIM6uLtijN4g9P1c5nlFpVJuuW9SgY9z5aJlMzQFIKXpLMJ8mIh6liPYzvEI6L46xJZ6hSDzZ+gNXjHgXLcNU0TQVb3L0MZt4e60CbDnQEwelzcXzJtEsgS1lx41sPsnbyUMHftoPtubnenvOZq4/+8uLKgaZ+myOuj23E8TAeY/n9/s2ohxRJD3AcBD8TlCDXQ0E+SaWeEMfUk5XsA3wA5YY6BguloiiZYvep2rG8OibLtFCKomEYZ3b9YBr+SMyYU2Y4OC6ZN+IsU13F1J061Eyz41CM5GvcTDMO/qDODw/j5B3WzAVrjBe2fnloaw0bZV0C73O53NtB9lze3Nh961iAnZ3Xtr5ZuNLYCwvklRuwQNZ3HGwHggFEiFelHT8GyyNx7PJPlAQ5aRk2+J2uk4NB6hC5F1taWpq8C7kgRZAgTIjMCzbKLGgSnvmjcvG8rzlp6oqIFMW0mjCGMpG9u9KY4cxEU0bwl+PSzc/PcNWsx+FzeN20LeGxxr+6wZ2E8B5E2g53OHGorjVzwcE4sJiKBX6CVc8ngNd28d+ryHf2NPbeGr6KC2R9/8H29gBEj7Q+4p1Nmxy7Tm4aNrysNBHgAsYhSQtPLixQ/AgR5Ar6EgSl6/llC2VO/62qqPPXjorF198W0ylZ0QGmKCviZ4YR79wViUpaVE8tpsKD4XHpSXwfDo3z1bGUzmDmRyhBkl5vHaqP90AcxEN4joOnrJFJwBZjcmrcxgMIN+fiOQLZXVomH9te+52CXLz68ikskP39AbqQIICXBRxvON5GHLvs/NpWox1BdiHfDyQpLIVtjojyr0tL91Ywq5HBy6jyqk1yRVHG5uev7Zc3isWiaoJm0QGl1eiQsXimMxI3wlo0kUmYQSA5emMa922dLMdb51oY/VCFGVo3+GqWdzEOX1WVNeUQPTdjlQxY7gaDI0bANNFSZDfl2z2bO+TvFOSFjmdPH8EC2QGhd5vNcfcR4IhhuL+UFlpWbV2P6vdfbGkZDFNPZ+z5cwogIRTPvnr1Kre+AnYrq0fPqUreJvkQFPnxiWuqnC+eva+bckok284MjRrxH3fWpaUYaDKTkAaD4+Gb8S+qmx2VPgTJ0rwPltwJEGJAlCEv+G2v00fSQ2MOIVGW6qY8nMty3AyAdFYAxO5N2+553Lrj1e97F8PW//nJxjkQ5Esw7I73GtppON1xzGbQ0eyp2W7XpEjc0m2padlzMUgcNYggMVdZXVhfB5Yb2VxuHUApGPkoeoHWydy6rI79QT2hKPmvC5QtwiOrSWNoKDodad5vhGMQBFmSlD6fFurcdJ0ceRsQmQNDctw3c7CCN8Rhw5evyjpGxBZEDIAgAhJws8IqqHJgVQaAtDlaIHe6Rvb1veGe+zanfm2vY/lOXcvcFTDsgf7+9t0N6GeOByyOaNilnQry1hZIOluA7/hJkEFsRUyRNesbG9mFbLGYzUJaA39FkrqctzT5SsZ4Eh59NZ3ZIJBpJW4MDQ+JhzojyaFgzEwkpsKDH4AkkxEea+/J1WCW7bYXSuxMgiiI83HgTQCkC7y0xxEKMVhMLqA356ikRRBCDPx8RXdJkZYodwiyb3ZkWykB5Nf2T/Z9OlL+b7xZ1wKKvP30ygAY9u7d7W14IUgg0NCwyZHWSJBkKerpamnZU9PS4kdPE5TIaUNKA44aI5rUeqF49tZqDnz1Qx1SbVVOKWLhAYSUuX/isgnJtyh//Ukmj1jluPrl6agWjUQiJ4bDExpk3TcnQJLhG2e4Ks5Dm5B0YogFexAB4RA+ANnM+5wAkqe6MyxQCWHrEsaPbow7SZMAkndVdPdsQ7kjkNY+eV9ZkcU/sF/RWgLLjmi+W46BIP/874H6jg68iglBBtqONASO4QJZU2OZdtnOmR84IkZ/12A4aAvSXJlKAUtdFlUxXyjuvVxYRpQyKhC+Ng8kc7nc32W8llAV5dXiuWQCTVuJR0//YliL10W8yfDpiaCRmIrRKpnc5+F4HjgyKEgPjqPB+gqWAvNmh6+SIZAuPAVDSXoFL8bjvD3x2e0NMR4If7p7ev4/kK12M7ydQ7faPd2lcQFbbbWtZSBby5zNs0cDTR1o2Oho4NWAgQ+lNDbI0pZPlx9LIP1YbkYrZFAzsfHj4cqKiRxFRVaUjcLr1wVMbAoQ6CiKqMx/VHwAIP+2Lo/Nf/hhXAGSmbxOIBdjQzPa1AmQpBGeGDxtDo9eBEmOgyRZOmCgrR86LXTbQZCHCzU7K1n+lEugXQrG6wBsgkOg3LE0OzvkIJAoyO7uUgy0mdlQmYn9W/nX7HkrI2u9W4NWKixFWtUqs2uI1C5vsUD2laavEMjfNA2Ax94NwTiOgQ80tGMAWeK4pcguLH1Ehui0BwmktD75X7auLqbN8wrzGeMfxThq0mTUKvEGXdKQmKzOZrakhGxSuxtIlWCDGQSUJaFenFG35obabSqIM3vGLHEwCq6mOCITRphFdBCLZKAKJMhuqsr4rpGQKuQ7T5PlXSGhnee832comVH4s/HFk+ec5/y9552enprOZBeIkSl4vtBQqlC4XHxeIHtOwimGm05evUZIbv0jG56YmLgRicSLhfxIMJYKx4btg1Gi5FqdLtY6SBj2P+78I1Hyi5C6EsjpTaw3vB1brxEFNbZto+6SlqfHtWoASR84bKyF2vAoOf2sqWTTFo8f+EjsUcHnXRMnmEWxWJRFKmV8EIwXrVhk07ZgcEU8c1YZbxGMlP9IvMufodhVJ6AyiHzOMB9x2OuQ0nmFUoOIDaKNfa7ZjQtx7juzmWku5k5tZnJCiwnJpu3tW/+eLVB+OEk4RiiENN8tZLa+2loI9070DlG2mE/nJoOx8Hz6/uBI1D7cpTJeeNjqdrm9/b5OxJLzHRWSRsedLcZRI9JF4S6tmnKT9lJFpehoU8LjQHFSU14h7rGBFzAYVCZmpMBStG4UCVkyL2FuBdsrVoStoiw+PkCIJZ60t48lyEeWtW1g0cpKm4WB9IyOX72KVtkMDiOK8RYLSuTrG/RH66WDiWTYv60iywaMuMQOOP6kARPhCiEZSGaoyLyFZBOQoGMmMzULKPNBmZMTnxeLLDGzOSBJIWRvrJCnGHMx3Ns7QeaejmdypNqplP1b77zX26M6XZnqdLndnT5fq8v1tfOLuzqTWi/Pi0ORKQoXmTdpt0OlRVWCgaTMUQKQkkFXAhJrQsjiTQzk2y0lJGX35tlAp+uJvOqD13hhLY1YpHJ1TO4qrJjNMzO8foWAxOCUGHAZ59EhnmkZwHuI7SulaYvf/5oIWdXI29/fVXAEkjYFSYLRJlcv+BEAHxdaWzNg4zIFPATl5lQm6Y/5oc5DIUKyAE+ZJcmJDIX994Lf5ClcX4wQkMFwMJnLxFOfpVJ9gcHoiD26ZnWc9LrcDW6v97YrcPu6L7ZWwVeDqFUi1VbxQWL8JEm1DpN636VynRifosDSgeKkXgDJkSQFliqHtJuRt0qMZDUZQDmRD7tzs4D3+6yMtvFp7TG5a7jhad/AK5cI9yU8USaAxIvaBkh3wMiZ0baX6KKVgMSdlaQywPFdvmgOIc4u4DCZwvyULRuEJJn5gJKZ7BSWwc6iyzA7lYsTK0Mhyg+/LwDLzdnNIIpoBG662JHb2pq7NxSm3wznl3PBz1KxPve3N6Pd3pNdPzVGO90uV7fP53K3ft39ZY9oOkhsz0RNo1GjLzfV8nElh6OWgMThORxgcPBDpZaBxCla1C4cDgISSXaLkiSWosGEed2SICq1DchtQHlRkof72wqQK6PCaxKQS1g0IFplkO6ldovn5fhSGftI/G8og1QP/tJ4oubACcbxPBESM86HWGxsDCHjt4uPtnMBgpGnAiipiU/mlos5eESuQUKP/Sj4pIrF7WKBRCYenItfmbgx9Ojz7VRu60UYkXr8r7msfz41T0B6o/32WN0vjnY4XW5Xn9PX6Q74bvtCRsr7eC6Fa9+4FNawr/w0Jn70mtpqHQGJXjbJjewjTUK1+SpjCirJdRKQb9NDAHlxJ7OxLJk3Rs1LK+aBdWVvjZjkAVc3ZNPGFpCll2MeC3ddzeZRGUiLgltJtXkXmOwj/3Cipqam8TyuOXzvvbcYSHHio4Tdzvcw8maR1FA0DiDj8eQ3xfyygPL5c7JvCnsi/nCouPr6rSLZc5JiySskM+li5cnJ7As8G87nMv5oLNrn7rQPD9tvrr35flc/UdL9kfe6O+D8u3O+SyMJTpqsBq7t6gx15eQeiYa6Sqvp0j49xz96rUSiTfk2RZ5aLgVLKKSZSHDKBIrCsi+WymhAbeml+cmAeWNF5pICpMJIEhvLkyV4vw0Of8wcWgog+TUcAf0/IGv27weQjbiy8q2fM5By9INrV8g9kpnb5PouhNzFhu10LtyZSyajyA+fpQGkIGWSkhp8DF1bfaMFSAZvhC4Ayvyz33y/sBCGoQ/nMqloJHrKHQj0p7zdPdUfV8fsDS4cdgoEBl9QCs4ZIa4MsDpUKgMF6A6jnoBEgafCIb1GETlPokG1DQQkO0y9WlsOu0aeSECSe7x1S0m4S0AS8RLj5rE2cyIhZyavMNLD0dDAjPCR5hUevCjjOTTsvvCcpSfH2l8F8pdHjhz5FW7hOX8GoQ9vBuBjXAyfzbaLnc0MKMeQrQsLTgDJVTO/X9TMnoOUOSQ1EX+k99r26vYyOEkh0ATJTL64vLhF0eVn4XguE432jJzCQbHoTXuq7l8fk9w0uFxOX+sHgcfRhzGVQBKmrbJWEy0ljXQUG2AldaUAUsWH5VRs2Vyn1NPLy8vFInKNSojN6n9WRRi5E5BjqQXLsTIpsZeRK571q4kxD0YB1j2s2gmMRopxAoiP5+yMOWHZC6TlwT8P1x8+3ogb2qtELC5b9iGYtICR2SnLDoC8Q0DeccK240FEPSnCrvhceSxzehi+YL5bLK7ezW1l/b0Acsifz+cpBopQWvPwfjTV87tP+9zuvpFhe//amy2vj7jcpxpue33N55z+4VQXtkDyjA8Kjw6rtVZnOIq6Wi2lgBT/EGCi2qtC3UKt0en5Vj9dOYJLCZuoACSGTPcWLQgLsl6Mo43LSu7huTIZSLS9seBrHZv8xli1eY9NOxjZJmZaxhE9yUAmdhj5YX39EQKxirSbgDwmxIYxtNkUHG2CnDZmpVgtt0CZzeIkeqv+YJqQjORLSBaCXEgb6m3arrYWC1tZCsUTCRLsdC6zNeePh/2TD0dioeufEiVl2+6qjrlcDQ2dt32uc4PzsXQPymFoyRgMkhZ9BXWloZqbNyZVtVXSvqaWKio0YCNRkisYFCERh5GAQ9BNyLUvYhq/5YdAnt21NkVOql8Rm/YBXsVCAbpFZDYY5C0Ts2tPeLxl41WxsTz4W339Qb4QvubAmfM/K2kN4UictImjhjZM58p+ElpDQeTC0z89fXonnhxGezXoD8bi8UIJSZIclH8ioWvbxcv5rxYiYGQqksplswukN/Gk72YoZn/nVJ87YE/121NdXbUd9xvcDa7rXqc7MBJKPzKajJJk5CMgWq1BMkhGq4PXWNCnoyptuU5is3YgIpcApL6SPCafMTapsRykBSeWSGda9hQtUP9q43kVpQomfsONWnk6hb7I61fGeBtLG4Zb6B9P82PPSrtSRtvV3X1Q/1092Hi86uABDIzvqLZNGDYFlQqONgVIwjHL2SFyw2SSEu14MIny43/lplcS1h355F6ouK09nc4sRoaG/BRB5vNZUPJF/PFwU/TUO8eIkn3Q7a6urtM3Oykm7/Z63c33Q7Fna+o6nHA3kclqcdmKZFQ5DISiEUiim6B2/MjqMIgwkjuJYCSiHw0fgy+72PJjYqQsNu/vqv6Iiqyl3bOzIHZnkYro1p7lXSxctRCFXWV4Rfw5j7eU3qaUItZ/dxj3/h2v2V91BkCS3Bzaecjs5HlxxpO1hhj5FD2a6c2p6VwymWRW0tekQBKNWPaTn0xEio9MhnRmTsTlsfRy5g7cwUioyXeMgSTb7vZ2nO4ypOwNDe6PfLDtWOjZZXWdig8Ra3RcHpckvRWtRalSA7eJoYA3HPJD0lRgwkXPixgQ/RCSStGCYbzYsruMtndepWz3BMue9Su7vuzds7L3bQjIDxtPHKg6vv8gNpVRhrgLSPkQMV8/d4hZ2SyLdpYYmaGPrenZqUlMqxCWybl4UOnDbi6ich6+0ttUPNlRXNya49IuRZC57Fz8yxcj/vn/8XZuMW3fVxz3/UIMBptEzBoWFyXYpBiZRAEUxRnlwWQyudQYaE0I2sLs1ilUs0u74DIzLoEGCII6aaDSltWZYWSJoA4MA3LGw7AibZ1cIrXxw6TIsia1vAAvUV52zvn9bZJue0ozY8gfi6dPvuf6+/3Or7PcaCxxdbjcE+4Gv61FMWxl9bbdNDByIXxLJFDwJWwPFRSJuFZos2GLFxuUiEsiPVhhy7fhW0A3RlMbA1d4cCFMTv1IBpLCzitfjuUdN8TrTuQV5amURQSS9dA4lmTmx0ws8NALY40Vg83mXCKGLEGU87FkaAthzmzNeHfTJCH39vZ9/vNRSNchdA99hMY+sp5MBqPRgLu99XIhk2TDiKdhApzka2607W53s+mMZ9h/C/0jn1vV5uPmMymAlNB9iHSQQSBnZo0BRyQTCiUiIC6FsgZMXCDL4ul06Wob/331ID+NG/RQ2+SplaoUyJRJY6lI8TvFEUybc5GTm4vYQottzsXwEMNsMpRcC0GVE5zxphYPEyFMg/p+8bk/mdzC3o8XG72bsc2gzxfov4HnRJmTvHSpdez1I0dK/4gg+z1uk8U6fCu8IadLfuSIEtMcmwbyntRJEOxNYEgXgJMEAUrFQu6EiFSmqKDBNbz6ggIAWKAr+P+BPHA4T12Up1SqDqcVuSdIejQdS2kSLRvHy1mt2NONQchJQp49Oz8fCy2jswRdepcoLweSa4zkO0tLW7FNTMUhLRq8Ehv0Be7205FbBNnhen/E7RkHkHec5ftdzR73QJfTPx5+U44TxkXUlBQJirGDq9DQIpcczxuLNSxBsuHIQzw+JxNKpZACSW0/th2sOGTj6ZBhAcnyfL3uBweZ6rGX8VKnPz+NK/V1SpVKq06D3IszhWkz5wRpYlnkpBWSn81YDN5bT6DUhtpwdpNIQvHtnaJwgyQxnTz9ztDW+voWGDeuRgRjsUlfwNdPxxyNJSXl5S73iNt9q7il+MKks9Jl93QPdA3cGQ+Py6myUUioO44HwqC+0TCzzswUi3GNATMgDeSTAj7kQ3hmW7LvDZTuwR8JECS2LVCYf30FPrIRb6rC0534k91bFVfrwayLCCRuembs6KvwaEqbaRf5Lq16WZ2L1sFQKJTcnN19Al9Qaq+sxNYowOCmlW1GElIdCjHe5G44uQi/eIcGF2Of+Xp7P2aKNCLI1pHuhjuKiiMtlyAldwU81iuWMYg2Mg1VNrQSK2I5I4URyHPAb4qLK8C4NbYKviwnh6+Q5gil4swskSRHIswR2PLlvGxdQQH5SUzKf2hFljV+1Hst0u6v7Ql/93jny++uVa3G4/FqvVqtUkOsOfwTApkO2IVpQaZNmytrrItOBDkDKLe3bvXsUvNnJbEWJElOXb26PY+LiYln2DUbHe0b2n2SPLUMkKPB3wTv9741TSDLGciGMU/HSMuRlmIOZPMZy+C43w8pOQ6koT0reFzOdsjGRlhIpVK+gIaOCxQaCEPyHJFCKoRXpkgoEgllYjB7OXZ/srNZuAFp1r8cyO/vPitr/OUDc6S/L/viRNWXO0/frlFp43FDdR6AVLJYQ4rkNFlIcxVYgzdcLgAAIABJREFUdn42FW+4mA0ggyEkOTS1vr27tE3GDCRDIeqszXi3t7dxGXYTs57h0dGlreDiqQfRqG+sodvT7ft9e2GhkVNkeYent8HzpiJTMGK1l7s8nv4zXLQR4UhdORv3IxbKig/xWfNMA3FHzrfR9X0CiUa+T6oRIkmxWCiWCXMy98k1MlAk5yN1wDL7JRX53IaLlCK/MRsDG+d7fFVf7zxtM6sOAEi9Sl2kUqrTQZuTITeXZn+67D52LN2LdC46l0OM5JQ3ubK9frGHI4koh6Dy7ltPzMdi4CZnvCdxa8BUsOvU36KBqG/S09s7Md1eiBSNRiOAdHnGWt3jgg3BHWtrpct9yT1gcQ6PL72G9yXh4DgoXCCsSOX8CgEbC4Kuka9BkHIhHTQG/ygGkmIoaoSQCWWC8aMiC7Jz0Uvi+vZLKnJvw0UK5GcR8+XpjXM9vQDyX9eqVIZ4/La+SK1CkIdJkUfT/HAaCD2AHFmwsZjsVvKRi1bnMnAMsjA9M7/yJEwdyXkiCSxnvKPb6CQTC8tQGXpBkkuLp94NBaKe+35fd+/0hyXGNmM5B9I90t48LNjgD1s7K13NY26nBaLN0jhOu8d1WQ0NnRIoqCIUKBTUqFCw+QE5Yg11xtnqF+SSUgkEHRkk5LqC3NpaXX12ra729ZcEyUZsP7/VuazxfqTq8v3Scz0frO7sPGrTFyHIE2DZRcpUrDlamJqKlHaRnFmftVg6rexOgQGrdQ1BghGjLc/MrfwjcoWR3Fxeg4/Aor3bf9gFSSZC1MAYGlnuOhbwBTwn77e+Xf2wjYFsQ9vuaJ1ob/ULMrMuTHZW2ht8HrtlYAKijRxtFzer4LgkhFiRqglJkaxVgfusUJE5yE+G57fpvKKUp8vOzc1FP1lbm1uf++0LIP/7DrPj/2t2CLfh4vm/bZyORG4Ml54Pf/Nw5+tHbdV1EGscJxwIsmgPJJMkuUfOQZ7dn6pqyEXiGcS1EO36gbowNNXvuO1waCs5TYaiuL/5at/SxdMI8hkUjle90WZr1+Ld6PvuDyJKrdKhNrcBRAbS1Trdbr9TqlCcdndWdjbMjDVbBkZOAkgBxGU5zuYDOeZXpDHa8OYfuQw7FCK210omFqJJi6W4IIYHnUCR2fDKzQZV1mZkvADyOLepgrvPhrc3JoRrouPskPSoELy+hlNkWRNvb1vFdMR8YziLgXzYVq0GkHVmJdY1RXn6E+lYQy5yb2AXk2SXxWllocZkAhdJgiSSwYjDYaiq0w7gUuL8wlqI9lSNjvr/nlgA416LwuvuY9dC14etP7u2iqNalUp1dU1NibEGbLvS1TD9FoBsUWz8ttVu7/CNgZMcOxkOE0g+jqehJk9+GiQWNVKhQCKmY9symjMAgQa+ZfQbGjkP5JiNEDMyajN0v37OtHH+RyPd/FPW1Hj9k+NsTMhxfKbUuqksNSqEx66vYdPzG8s+4T5lJ5RqIh8jyMjjnaf/ATIdtNNxmxNkqsy2W1nyA0QHgR8aNXyHmh2OqgMOfV1dV2J2NjG7sBwAH4kJZBIwLiSePbhxY/WRwWHZvwrK1RLIOmV1G4A0t1FxM93bOdFSqti4BCBdvrFuiyV40h/Gae14WRKU2gxgPrNuXMbhS6C4hjpGKFEAQIjYKEpulwAEbqGIB1JEUQJLXW1t/Z4im+7dxEsEGpsAHQ4hv3mPhtD88x7eVIPHEenOmpu47N/0K/pTGpf/u3s34dPr6ZPuvTWR/udAKjGNfBFkyZ4k9/qSZ6k77rQzF2myOAdDuJcPOz4zU6HLSvjPcJjz6mrmgOT87JW/QKwevTDqHQLTXvhi4c8/NRoMBwxatVJLY+pRj8o6kGPJiRpyktO+Tkgkj5SO9XfaywMA0jR4wR/O4uNtsAJsMUJ9CKEmnyjiWyGR5QhRfUJZFjhHMbxkELfFNCVNKsx5Q8bLIJA6NPAM3blv04tfX7FLbP7UiPjo8av36NAwrRs20VlZvPXiOj2y+27eo8VEeiz7HsgqBhLSyHiV/gWQR1OCTKWQqWTcZOI4Wi2m5SA7UoPnuILLRqCoUpr1epVlITH38LZj9RqSHJq6ujWHV6h9cZbuSzA41NoDBoNWqdXWgSKNYNtmc43x36ydfUzTdx7HaX994qmlv0LTkNhpcYEfQh+GGa20lFJIi+LpdINqnRA9UxbCSs7dAMtFOJHIRF2YSJTlosYGfJjmfLjFi4AXkiMxMWbzLidzyf3jH0v25/7iv/u8P79fKeiW+8cmKtNN42vvz8P3+/08kCKHpuNnD9QsqcYPJuPdBPJka6xj8tvKUqxMKiBF5pYWYIDchqxt69EJywAFRBlKH9m2ZTPXC3vMOWE4yGLQDFPM+Xl1XM3hdy5ewHoanoH/Y9t5rL7Azos7bQOH0dv+DV5pBvgx8TL+1R/xQIN3njaUXAxkxqr0uRdSDPKnX1YeMUgngRR9FvkSba0iOW5nj4et7CExs721vmt0Vu5/ZZB/C5kSISkqhSTJffPm9QUnfbyx+yB96l/bSZF3LVZsH3UmSJFQpt0UtZi8ABnKgDz4WVXBAeOtvR8m46nx1K5dB8fGvl3iTe6qAm78IHWqONygxUZl0GtZfYZC2TVylQWzJfeoFzSFBDJMUZtIFlUQ0aKdmdofuUCibf5iZhIIalgwy6JXrpiqPo+tFnjTkp8Rq+vmLwIkBZs1taUAuZxC1FZApkmREQZpUW4jZZBK0F6TjsOy5VDTRVn5DKLJaZ5Lc3+ui46YoYhNDEmBLSXfX6+H7JyfzOGIc+phy91XryRscU3biaDVmra+tNoTFpNpweOJlIfItsm0h6aTqX1lNWVffsYgr+1q/ZBAVukKNJTjqOUtFhSNP0KjFw9DwwkGblFr5B9Bkk7bdNwmAwfLQi2CTQWh5MBdnInadTyDgWsl8G7FWxsgRmwYqOOXrvb2gUV++pqXX8n40lxeNNK+FuT+0HLqjHEtSOdrILP5+OqFBZ9p6nuUUNNav3fm0iBzBMnZuR6HxRIJSWIoEGgIXP++1pkgktZjyMwfP2x5dTNAxmwymUiMaXKQzpd2S9RkSnx3jEB2SqFOUuTw9ME/BsvK1F8eTcY/JUWebI0DpAGPNNyHhNJwrfCRXseNxDqDAlI2aIGzcb2AoRYgyjafU1yEzIe+QZDh10G2t/eeV7bTXM6AlGv4sP3nv4uQqDLXhzKgXwE5DJCFFb+iSOUSbZ0i6bvdStRuZYyxvfGu+q7ULL+3TgLkqZmHPfR/QWoIiCF3s3vb539dcKbTZMCPeh6PPH36tOVzyZTgVbh2J2FMk6u0Oywmyw9Xy90UtgHSBZBHOspqKie/GnG5GGTXIIEUCuRmGnkWmsFAIQYgMeVQi9GbBg7VAqMUsNdGpwFN+tqQm4O8J8wcCWTWtJ/L2zcvDJznzTa8mKoOtVEKSHxZ11t3WV7LQtyqLwxc+A2Qk5qi9Yq0rAWpYFRyyE2Zq0hcn43wRhA4yEE6Po+h7ejS7MN/lJAiJexL2uz3B/zXjzmt2CGT3voXbIInjtgqzCBJlzD7BBYNP5smBwmQoW5X9/D0oSMdlZWqK0dlkF0AeWOfvoyfDNU8JRIFAXoNhCfnioKACX2CQpAyHrPZrMX5EGX8pSrZR5KTLEbcDu9cM4phkZfYcAS509ub85y3sCgg23isCp635SU3OXKN3/xvgKzg9OeRnP54AdLheFORmYcGvHqVJPfy8TB+sj4++wB3Y2j4GBu8P3Ks3GOJQpGBbZvRJ9/SamWQ1q33WugTImgO3ipsd5ooibQ604hsj/50m7LIDMih6UP9wZo89eTeEVftkfH9Xa21gx03OgRjDXo3+c4HLQ1lZg1uJTLJoi4XkUZA1bPWrCWQqEgjjvwfkI+EHJVv4dWEHI/9WGKDotLD+JLH72VAXsaSm8OLKNidx5SAd76R993wEfH/gHQCpPQ6yNVXGxZkPTlI1J/FIcgZ7us6M3Z6cOzE18tRRJZ0NNJAJDc3+Ruat5cQSCxbd9/7z717bovDJzocEKXdSlGbwk2Uvo4+uXrO4wmUh6SQ2wWQ5/qD7+7UTMYeE8gJAtkNkLm5RqwA4nZDdDC8h7sehWOh2axDZ7Y8CwgpkFmPyVQGdDuYzQKZdphZwlHSITFb+7OoLLHBaD6loCKrSMp8kE/OX+R9YIuZgos3TXsotHw7C1LCyUZaD3JrVpFKtIFhQ45JdpBHHxDHYJAVeatPslidLwnlI09DQ/OOJpLk7t3ECsS8d++1+C0O0cYcEyZrmn/aROp3iAv9Hk8nK1IGmewPcp/IYzJtGeTYeIdeZSjl4h8MAsHkqXxNrqFQjieFZoOGbVsBq9WUCmir0+DphqJPTjivqAITKXFMrMje/tTxeA9UUWBYpFxQUV3H9RJyWQVKKQZy5AqL9gt3nt/JFlxke5TorN25nLqlCf994ckvKwmPl0FGHKIkrlekfCG5Wh0AjpBkvLskfulMVTBYRccWhOypUDQNSVqtXndzA2YjNu8osQOkyR5t2d5AGG2i6IAITUh6KJuM0j/6vP0L5QBJivSwaSP9WVJPxuAjJ66xIgHSmAWp1pRqCCTP3BQEjdFsVmm0mUMhJjSgTYR+EDh8I2pvZC3mFecVralGU+Z/8K0Fr67JFFTwL+C2olouq+itVtbXZAsusl1z1W1Xp5ZTDwobcWmx8sTjjTpxRHQ4JJvDJoMs37pajZYpoCJBxuMkx1isq7br7JlgsOPECTLsyVOzsyMhb9pJkqR4HPH7m3b4m5qbtisgxU0BUZTAURQtFKjtlPSk7Rb6CdG3AJChyCaAdNXSEfHQtaqyStWtr75YBQlFGnlwl9L+WqARNGpuqsvP12PGqbYUcy9QTS7gLo0ydR3p05xr3rPHXJgTxj2anADtzNu4vtLijaEgq9M/XiureKPgInsfObWQmjAe+P2y98XKvz0RkUGKDDKAnXrlUGTJ+g8JMh6LY/dcfe3o6Q427EmMqpidGfH5vHacZOj43MAg/f73SXVIHMVVjmTMdJRJEEi7ySfawLEPIEMuBun69OpQcriqplI9EcuARNQGSFYkZUA6lb6gRiugyELOFTFPSWNUWkIwM0TQqdQarQ6ZZb7ZYMwJf3B8Zx6fEzfmbfjgbb8itn39xUJqaOnAlT7vsxc/nftEJDlFQ/QX3pJ5iy3f+jrHkpJkMkmWPRLvro0NBulzIojU59Sl+6MzUwQStm0nZ+hugpP0b0/YfZTtUD6F39bm8JEDJjdp8SEHIlO32bz9fX0UayIhV0QBOZwcOlC2VDkeSzLIPysguTgS1z9qisZ6jRFlAEglDYZ8nF70FFQo2ugLDch9BDmiaygLIo+ZU3H8n3wb2UhnxA0Vx9/6K+LjqdTZ31VeGWaQnTYrQEoiikz5nYFLqGp5Y0CmNrK2JxmLkWXHu7rjl4IdVcQxOHkaghwdvZ+UopTrkJM0OcRtANnk351IyyDxu/pEkTwHydLic1DAiUpbbLYIcVz2EMjO8ogUYZD7k9M17y2V3Uq5NrmuTQwRyLGxG0G9kZuJ0YKEvkSDGR1huP9WafL1dCQs1Qn0PclTl0/WjIyI2Obn7xFytQaYNodssu2KxuK3D7KvM5WqMn48HPnuxUpnp2RyOi3uwBZKAgPYilSeKXyuf79eLtkFyNhIEjtX4CA7oEjKxekzO/dwbuZpp8NncuJyzGGz+VmRm00Jn4kSR0dgG3G0keOwgaNI8cYhEcjIct/wcD9AesrpTyYfefDB0anJyrLKgrNHXC7X7YmhkwxyH+p5SjFNTqVWo+d4jwHFaYZCSonoyI38Bxt3DXydazYjWTdoiaiZyGpziijMkJfMKwo3NhY3/vy2Qf7hdmf/0Q7jx+ORH56tLHgiUavVEsJCwgDWIqEeB4IkgrVZjiMkSAxnr4+NgeMZdpCDZNijc6M9ricJLLm14hVyGwaV+9123/8oO9+ftNIsjisoIAjCvdiiIgFsy0U6ERxbhBG9F0TIyK1V48ZNpRiTDZqtS9y62kiNmKGdwFrbMEs22ZrdldVM0jW+2ISZpJnGdyX1jfHFvtD9BybxjX/CnnMuOO1kks0+oBYxbfrx/Pie58d57C1Y7AQgY7sCmGsY1udDUe50uVyRs0zmcDXvgVzjcURMESgRH75+mM9167SVvz3scXgzCHISQN5WtuOpGbxSt769q0teAwnWiELHIKdWkjQriQcR6YI1Lfq4EnJ3HScV2wjSKAb1X3z20cCmKP9zVI97/uIbn32x/trzZDqn474/Ojs5OZsTfBYLgAxcgaxZZOsnBkkgBx88HXoBj0QCNSSAfPfu+fP78+fRJPw2LBgT/dQnX2hxAkjINSYn4+RNkFwYFKqggJx+vzNytrl5uCmFSM9Rvy+a3E8er8794dc6nebeNxAiba8L22Ox6VzxzT1lO9SEtOOxvb2zV6lFkPUKlQa4qepxRz7ka+zTgCBx9ofqHQM1iMUZcpxEU4NNQsoRL/70q/97QKr+xe/TZpX10tqT6aJO/fbo6OTkfA58u4WNzAoRgRcki6yB/Gir6WI2C/LH+6yA+RqKmp2Tk9PTw/N89vm77Jd3z30tPhZB2l2u8P3h4VFn0gl+zUZcLuLoAsf2gU4FjRXwuyJH4NebCBISdv8xiNBrkMpfrmUq3drmV49TPQ5bobA3FnueKL6pkP0Ryabm683gs7jcpaKe2lAIgiTHGfKG6oQPKSGoFSFYNgHSOjNOn4XUVmOnusM8LoYuoOa+uLgQLy7axI3x97i56gJfi9I3fz7wSMnlZW3H79WxbxgHm3MLcw/Xd/L5bKF7Zvcsgj1qPBH0QWySjTeeeRxVkwSW+Khy7FnMpsAg08jxq5Mf/00SHPNLv2D78n7UGY06AQbLMn4/WmTS52QhVwfw5LLE0UQcIQ77gSOOsyMh4vRFcWbNsg9KaSGf03V3N+8uA8i5cmHv69i3Q+U3WqkRMXYSUHRd75yYmMBjYCqNBhcZFLoGIEbNx+V0jadCaiOrgRCpxL4/dzpCUNYYzTdvdd40jotBGOog6nNjhxX3XnB6PdoqrupQOV5dKVOTiIcEZR3fuLxc4rg4PuM/jfHi4Z95/sHTnXQ+u436J3JaApAC5AAf+DZftcjqVSuSXUobJRcXvbZUyjv5x6Gvbu8cVynSsNgDo4NRk5N1MmiRAHJ4dDTQgkcb7QGXi+ddJjBLyDAoJgNhf2Bh4ejJk7Oj/h8whe9fowUcUJ3scbmrouvSHYD6cTwob6W/jm0PFd7IcRMf+DYe/lBM3TLgZikAacBsguszBlW7QkmdjFXIE2Ikbu7Ddxsha7e1ISCu7ebNYLDTCAjxidCsYJCiUdSr9TgzhLJdX1snuxp6ALnx4f3lRlyMc2KNIfwBrHI3k50VvOX1TD67PNQd3xLOSid5B5TbdkZw0923n5D0Xu2RXOzB26iePYXK8MUx27KPU4pkkdegTAkP++wuKDFBI9rBt4f/2hf1BSA8mvx+Nw8YIUAGgCXIfeAozC709/8QJVWJ82oWXL5pibL200qlopNVtlNrDlu2nJkei20ltr43NGglZYjasb4LXLt+CpjK5dhGW4nRsF2mg/gIBmrQNADXBppWM9AqTt24FamZRT0ESYBI9oiIguYN0XwdnF5Uo1XSPgIiabyCCEz1aJEfLkUubo0jSnygOcITQHoitsx6JpWdzlX0bwFk6Qx9G4zFzWOMBJAeIumV7qK6skh49WwLK+ydqGUfQO5bas7NBAacLSYTG2AAJMOYhu/zLO8Kh01hKBb9gJBxIkcIluEwD+6MLm6nWTUcdhYNOcpGd3SVSncl9CjlsPWkDzKTK7GDxKPihBbbueNKDJ7e7NUYJhRTUNrItdgdVgfFthYEpRL7xdKClxxbwoJCN4C1QrKxtmF9qBfb2ox6LkgkyZWNHNcJDh5Sj+NMJYcrOiGOw5kiPTGkgetlEB4vcYclIuTIHhEjPAp7axFHOlfKZyfLM8Hds4WS5Nvw33QLRFIKktKshfeqwHEsOmyDy6Qfz6NUD9J8D4K0sM4BAdQhC+6NCpxx34ffSnjYz48Oh8MBVD/IEYIlvIKXUfgR+9WAkpGNRgGkb10FHCuvllPwS9w7yHw3FjvIPSpiB1P4oCStlMnApZuaG5rblU1S43w8R9eEa9i0SoOOjZmHQMoVCgAJowNCotVsJIwhKfiB+aGTc2oRSFrJIGlrC5mlZI7k2rj36v044IxjjBTFK+eOHxymhBuTuXI2P70VnNk9nM2UXs9B3kZ7IZMUPESyejdaa8251xb7fvv4BeSZROI8GU1Knv0fggkyPOD2gdi24442EN7uVhM/DKn77igPycbJ8xgvEaMfKhoUQgzNYdAXNEkGq3A2evL3yoy+uziJIDOFzdjYd0+Lywk5QtTg0KqapjAdy6a0DfV0WRXoc8OEqh6qQoOcsnh1/VCBqhwVZd2dNrPZagZoemMHJRGjuppN0NWBJYDkOLNe2tpiJTvU1wYCFcWRS+xBQBwJokjOLRbBt93z5fIeBMlXwXhhdrVUyjs8EfBIAvmJSbZWRRB8XnT0PcgN4aTP0GnSkkwma0ESQbYwYZy7hcSM+oZxr/C2f94d6OsbcLncfTd4qLUD7oGw3+9CkFRo41cG6LFV82TtSfbHSkUdwhBps/WUtvbGVuZzB8v/aKKrQ8C3NVBs90IVqJnqRYjNMrwXur0RDyQ2yhsNwJlmJeWIE6U55u+6pTviyNLG0oi1raPtJ4KSh0MGR4Wp58wcDT19+pQlZ7VuIEhOyjbiVcqJ72bSDt6b2cn8Jv04F4y/PcqXSqsO8G0Gg2TgZyZ5dUTEa3P8rowldi6RKB3jXon9ZC1IEslABGtpp8nO8P7Wf9mEeYdNcPXFYmE3Ze6BgQByhGECmDRdDqZoZ3yMBJIssntm5vN76RT846nyVnZlZTJR2NbiiVckqcHufL2gECeapppBm9+8fgs7eWk1qiZZg0oLoFUYIckQUUti5lHUfRix3hlZWhpZEjGzkGMHiSQlb7JC3GHOYZZBxyYrpEDJEVB4b/xyA/ehk2/HSQdJo7DnEHq+zRXS2W+KIf3uk9nXECSrvo0rBWSSkpb0Sr5NFmnzFm4P3b6dy0GJveoD3XftI5aQde14IpRhIiaX+8bY14OOyEKkx3OjNcbbmdhdrOJdfhpAsgoxWnVy4gjfOv795wAyMQ2e7cgWMqmVlXRia0uOPfrA2DQNkEaa0bUNjVP19b3NU7emZLKpdkjeeEentpGWFrE0rMpyCJ66hjpgeMcqLplHrB0d10M1hJR1oPimPX9mhEaxkSOQVRlEHI16PKUMchMB0gdX9W4xfpBJCZ7JcjmdndwKhXYzs5ul0sse8m0BJLmkJZFkT7XAkUgObg9RgEzknpY3j1iLhfaf4Jo/bkMBkmyAx/TsHo7ZhMjamC0ijMXmA4Pwt/XxLt7vD0OI9NNMub3m3eTfaJwQJdno6Ux3Zaar+OAlgFwtZOZXYn95sVykozNSo4omRSeC1DbJ5MpemfK/ZF3fT1NpGrYU+oNy6ClUfhVIy5S2BxrLYQttzVQ4Vntq5IfikmCQcOYkLnS6llRJIVRjHWEQBqiDISTTJoaCyRiNyV5wMzOJc8ewN+rNZh2T/Qc2IXIx2WSv9n2/75yi2YPBgya9eHjf93me732/78NFytEyfQWDzRzSl9UC3qiHCC+BWwSyQSCbowBmvQIkxZHSN+UXyuPkHZFUaiOrpDmUx/s48OuZUEW5osxJkRSmN/f3Fsee7rA7L1/PF/fnfLyEWg/sNm59F4QTf3OaxKSjd69v8iE6Q0ASfhVdtXU4f1JH0rqVPuawMwyf8WJ5OhEUAz73UoAPBAKCyOMC3UVSIhs6P30okG10fW3q78XrBwfdHWtQIt2O/EZ2YGDp7tbTSQIkWha9wajvdgGQVaNNJkvVF+Swhe4qrZZcuWswVJCLBQy4Koki0qDXwX+dOjxMRZvt9p7m+sZGJSLPK1jCXywJSbaS9Gutg1ftHiUOP5FAQNxXaflUQ9JDNCUpkkJgYz+7uDi2NfEYc7uQl918GENS5DguHBYEhJKq8gCZWekdI84QTXbfyqM9t5+PobFrJYuQaLHhgZh0OPsvOhaWl+RAWJRzcZ+cEOS4JLilTjyXCSTlWfXhiEoHDNtoUIbe/ZYHIKuG7mzDL3Bhf2NvIP3NytrTA72OrO1Adut1lrKykRFLmQuv9asqw6N9ul3GEZNeX64nzQYcujAxDKPD1pcF5wVOfUwRIO2gvm0KjCUczwNYyOKRShaDE6viYIlriBTCh5wc5GHZEh+penJic2Nccn9b3MzcvLYJQEJuF4qrPlkAOywKXAPXeTYsIpgK47hxTOCb7wBBEOMP1/vW99+9FsGfYJumjiY2Ions2/Bl7/KyIxTKCUsBKSn7lnLBHC/E43KigQB58Sz+IaSDMogkNkn2BknOPshfB6M9mZlx8M75zezicPrb9dmsyYjnK4CmQTj1XzAAZEXV6Gj1iJ4wt6alG3SlXkfaNrjBBtNbi60vg0nLANkAkKmeqL052tiuUrWCI1C2FRkHdDquWRL9Y2VP6JomNtmjo76zHsV00wT/KTvm5Kc383uL1/66M4G5vV+A3ObxnvUwGGK0dNgDAyRVozh9F3B86EU53lcEg1iLTTIxRDKbFktC3F2XB35+HuAlkV9K5OSgJMXBDQpcXAw4G9RQLKU0QZEjekh0B1az85vejuobWxkZSmR2Iw8l8sfvMlsWnTJ9i4uOo2XgchimQoMhimcXa5p03WUWfTkO7TImplqD87uGERDvxgq808Fw6uNh6jCVAinZrvJ1pQokvrW02GwRO8pzK2GeQZYKcpb6RgIkaB6P+iMNTKVY7mxkeCExm89mxp5sTexszeXyhaKMCqitlgvX1FIm4MJCqUwmHnkJjg+93vV32PZYICMuAAAgAElEQVR/pkA5pUAJYLa24uiPe+mWc+lcvy8RTyalXDAuB+UcfM45f7/C2lRJKsaGGMS2kORz+Obmbu4fHNw4mB33Ody+H6BEpgce3b0zCU4Qe9j0GElXGXa0AE6mAvcc4xUYOqMGlSOjQ01eYdAApuXANtpyHdpFC9RIeFIqY5dwbFEC09Post2/CrmvIOlB5RMpUQ18/7dHjUgSpJ4JBUr42llDATSWze9lILd3djalV/fuzQPdcG3mKRH3fxHRzImCQt2JLODoHeob8npvv6M0jdyCWHKh1jMUS2zPcP1YEXgHL/lkH6R1Tl5OBuPBmMjfWnbiPAs6m4aTgGyjcjIWlHLzuZsrHdUdfWMLYPEXf8hmBtLTBSyR5dSukG3FLs0IrqK5DAymsA7PWtAY8B4mAy6YV0Aua7CVqNPpLTgaBFl+Kgpkk7LX19s+8zNqobR+vNpiP4z2pFKDEbY0t88qM76UYIBsPDTRPQq+lHcm7CiAeH56o/ggc20Wcntr9XXhXlEGw91mPhPCdW1avDgc7YaQTGQgob0QjcA177ArDTT9DDutUBchKmNTCGosJPZfvnTJ33XF7zjdwCeTcUjr5D/ktzn4XF44vezv7Pw8HmsVr02a3a2/xN97NTeqX84sBMAfZkFFDtzan31ZwejwugbcN6MAaTFZ8E4lHD7D+0LwbESojRCOOqPFoC+vJleeai0mpG8GWDsVtYHZtllxTECxM5WeUpkcHOyOQsjej0ZwXxMZpGTZTxKbxX139z/DEb8UKbS1kXF3Je7k8zS3dx5I+dv3VmUJh4Bws3FtjYIkjna7A2PrCKS3b2h3CBfQzEpRrMPJHsRwiiyFtZob+q+8eO5Mp6/4nW5JkoPx5NG/jt8uuYMizw/gPNBFNbepmjxZ/mmL4ajkm9sdHbMzPodjvLiXDaR7F3/LrGjLCSHjvbsQZ6N/GsGulqbbyOC9dDpyuJKB3AtmsTDkHKByplqH++gMpFlrAiBTPSAhbY04JXBerY9WqwJkS70dUz9qw8aOMrVmLYFGw29wMDLoKfGPGqqApf3x2p4s+K5li5DbaxNIN+9vf/0GIkeorfsQ6yQhSUSzKDjdvvHvEMbdSe/u0NDKaq0CI47Vn8EJ5jrlAbLpv/Di5+ELl9P+cGJJlsXg8dHR8XFySeZ4YWDghQMlOcrU/5ORCCaOs0y9Kfx52+cPZPY3fh1In178dXbIWE1J22DCZXJcRDMBS7eM4vQUnqmtb2piCKWD8tFA/WzSM4YmZbMSKCEtRmQUxDgEZaTyhLNLNrES4jHa2AyMA2oyYqWMQ3O8xN6eiFIj6XOdfcxSde6Z+AlzO5ApZjOLdyC3d15J//zq+3m3IIRaP5zhsEqGCJKQ3O7xLYrj5NDu7u7KqhgimahGJV3cNqOOnJqKic7Tvb1Op7/G5xNFST76A5BMJn2iEPCn/+anyrH25InhUxMKqfWy1vzLwoLPESiuQWYP39qe2bQ0MeRYEIxJhjEYq0CPmxiNy4UH1lTh6V147RzwC8hx0sbRaQ2M0QiyXG80aEcYE5IN2sNGzG2ysku/KQF53noYtdl6mgFlj10hbtZ6AqNHUT30TX1nWcVwe4gmd9zMFzOZJ0g3L1///v1XRVkShKkzH1q5GpLcgCTHCXIRHDbQDOA4tPtw8n0oGMKb2T97cMqMUlDNlxecV9JXHF0+4K740dF/jt9CtQRFPvw87egnZINIquviZuWZUkCtNYcCDt/Mo9lXgfS57e2xdS2YaNzGBYVSD5mq0YxYILnB4BiMTeVleI1IWROYw3LsMjImvBdMayG4GwBIBiQ5AhltRKMdUdU4XZXE13bXeWtjezTVY2u2s6T9rQB5Iic9xCN6Pv25ZHLsQDdre+Nd7vG9QjYzi3SzMycVaEgGn334EArHzG0hUiY5IQt87cUCCY+3b3IOTTbQzTPcn/BM8YZUlCOQ4Uvps10vgG+GZU6Qjv84+u/bpCSJkn/51nBvZwM5CDl8llRIUhsJpmbFY+JLPOB2ZEGNn0v3bs9kdoGHy8kWTQw38IWMxWTSoknEU7Ph3/W6KohKC8DchBu4QUSSpiLeeYMGXctgjTxsbO6x1Z8ISNVru9pdLlsjcHp7e3NzJZ1EjbARhW9wsZwyy6d5rdCQ6hWBbkCTJzKFwl72yUsAcj/+/uu/FGReFGJ1mNwxGpIN3O84vTeEOEKF/B9XV/uTVprFFVneqqICooLmosCVkZSL5aUQQa4vYCtYtGmiixspyYrWGlLr2Aa3GezadJmZWuvGmIwmbZVm2mhMpom7yaaJfptsv0z8YLIz/RP2D9jstz3nPBdt9xYVK59++Z1zfuc85znHuecsiJKTbGss2zer/5DXzAo//WQQkgPBiNDO8w2Z/wAfM+60kDbs/80Dhg05Uyg0iJUgNHNwke2fnzkAkB943prf+X0hFV9Cy8btc0qiG2KjktdgrAEgr1SrlXJaXiOvlsuqqrCHRU3lM0pxpFWySiUAiRU0rtVrtgGMtr7zBzFtbe1rNXmxONSs0fRLhzVS4NZTe2qizMH/w1FKFOF5vQG27UptL6x9//Iuo+S/pm8/wAsvWhwA1ARJMDaa/Pod2DUqSHSQTiDlQU5sZ9eOJPcIvLx8Xt9tE/f3fckB39NIE28RxdisC9cCiuBGfPs3gqEGqepDeIYioS6Ho6wqAdYAeN/neZ4/3F352rAU38rdn1JC9qJUISOViE43AolhWyZTqrB7RSXH9SHKMQUbu0LeksasKNlSXoWyIhqN3osaTZwNDLnVqD8HkizdbuO8nNnL2TR1eur866dLJOyFd3MYhBfa54viBf08WMkJ1rnSwtHaxsvN1+AlZ399Mf3oOVAy1oYtfgHssQ183CHhM+IkHBHI4g/jLrdDeyGALnDE4oU17vMNDAy/SwpPw24+lnbNzbkBSPfTfV8k0tWgK2tHqZDm+OzBo9mzQ9CtQMh8eMmwlVvDJeW1iiqEBI9b1a1M/YxdUmBLFaKlqJapZfIxhYzuGqtqJDYiVdGzVqor7kW9Ufzi7LZmjjN3SsZN9R6NvRPPu1uNtj7WIM2UJPwJccN3bB4qA5DQ7Lx4WOwpbqzyon98Z+H7jZdrREnxdHr6NCPG0g6K3A2Qt1zdQQcJRu1E6dPrBDCnNtfmDZC5iI4hST2++SShiIdgwrDH4nt/PTlosDx5IoixkDsE+brB41uKQ/Le1X4uHNlBDTu3wYJ5Q4Muq9OermYspaPSA0M8nt8a31TX0nRdrP8oUQNVdoNUBCxVtWqcgq9U087TStWYvIPBSpuYWiTLBuuXVVZ4vVQgj0ZtXrBve3M/M2xIdUwAZ10r/mYy2kAfmVmc0dBoG44uL2o663C0CB5FsICN44M6z8UQTif4w0HJJfIzhYWjwhqJ8oPj40evXjx0i8fpQOOnRkCyPfALBZq9Pfw+gnocos3m2/F5yD7gsfBuQXA/P2M4kmVnQ6IgWpauD0esFn+Yxw/wFnc4HPdd8zSFhGAXqh+t7kKIl7HE4KPVXs3xHiDkds4HhJxfHKmRBuGrqR9ShbvTKEesl1XjbnKauQniUgWMlNEsBomOivKiATxF9IJSvOc1e5sBK6PdaGca0mgCQhI77X12jQl1JubZQEIzlxiNJgAwhBDPF2lMi5m+w/9+k9B/VmmDp1gYd0fC4zuPCoW/FpCShdiD268g3hzPikM0Jy1wOjXlRBr2TpGPRBPvLUJWNL46j2cQOADa9/yX/7JAw2oXgVAkOdAzcP1a0BrP5+f8FrfAAyGfvrMGQ0E8UUQhySQPAKol/SmFG60u7bbwlsPd5ZI/vpTfyh0ov1Ip2F4lZBpLuLsvjV0aG1N0yNRUMce/dvyuniZsq9miNTVbtK1iYFYgH+95wROaWkHj6M0szdb0m/SmspzUAyFNREjOzIF857hENIqspOlVXiJoebj+6EXBkuHIrR+U8qJl5vDFUeFHoCQa9+z27dvbmbQjLQ59+qSLnT6borwQi2eSeQOQB3dLy6k5v9/l8rsgzT47Yy0XUuTJ6jz7+8nh5PWkEA67/SL/hBduhAVffGAwEmzqOkcSQzRRU0Ky4ePZmR9L4xkM2Yalma3colNdS0OT2EpEtvBHWX0FjLteWd0ieUJIEjuqqnCgNqOjnC1WU5HLhH8V4CCjYN1Rs8kIUcXM9bODBSRkfzMYrx1wbdbDl9mMhXRAET6UiHrNeixS0oiWRHkd8ui9bzi9BCPrw6gjSubSIlByYWNj8e46M+6d6TsPM+ljt5j9dPk3whEUD732RgjL3uLf10rjc37XvJ+Pxa5+eEPHDQxFSBLfNGoF39KSQVjaDwrxfNhv5Z/GfeFkjwcPY1FQOVAPsJLPucP8+NvpbvHPP6a2QENC/l/yh29soYfEBbsAIq6WU7HaLm5pUEGSWCXDscRK2l1VXV1fVYM2rlCrL0amKSQLB0ZCpPECK9FPwnuwZQ11WIAaqjMaIf9u1Yx29vWbAEf4bAKh9CZGOWN/J4IqkRHQrePoyKHuy+NagHJ9YzkfM8w8uHNU2FjESjkYN0XuzDEgqb2MgQaUz96EE+2adOQIuMiDt8vAR79rLg10zLadk7ERQMw2NmpDnqTP0zPs6VmKW8JPw/zMOyHyvifYFYwgG1nySbY8lHa702nR7X7wyOls7Th4fOKyWHI7y0DI+MxJbnGkRaZgi+dkNHkKL33hZc5K3P9OQFXV4jyLW9Vj9bRbm9Z5yqU5IczSVSrwkQAP4vhPBiXgp6H7IuANwS/qTbZWmxm/gIbwCeQkWHM0YWaGjePpOE6v5xJ0cItxvf8CS6aJimsp0R3P7SwUSoWbGG9ePxQP70Cm6D5O87O7UxSxMcxMII4kyKfWwUfO+Gf8qVRK1H3IkiQvpzdaPMXRNgmeYPK9r8nq6+kyGAZDQtIaSfIh7J/C5gGw5QBeVWoP6LRXXS7exeembvX1TU48Xt0Ct/uXtZVlfzy+enLzoIotFsC9CwAlQsOOEztUEG1ozBwozBZFS7e8XqVoaaH5Sug18aVWM0wVKoraUYYjvUUg6YAbT2mwumaD/MZmMtOnGCGBkfCTCMlJPRhARoo7naxiWaYk6SLwkhIlN5cPX1Ki+I/j9C65yeNMobfYS4UzTLERR8wQnVMTxR9u+udTqZlUzq3LfpAKaFigbNMNvcGA0y4G2geuWUWP77rPIwzElwY9wta3x5Bit8ccePdLqx1CUjY1gH6azfD5za9+vjI5svj4BHAs/Wl52wWEPFxd3FPTboEaasNVqNkqOsBRfQUYOYZqXImVXZnsFsQanKyE3+RsTxUzbrkCfqlAhKKII+TcAKS5z24nRpoAThM92BwE1o90HcVI46Vok2CY1uHZmB7lUDl11H9p3Z11/64rvs2JAlDyxcb97cdYu3j9vfjtzvTtlUzm8Nk6niugEkcc9xiOqH7up26m8LnpirVr8eZwVivVf4Yo19E52oZCHtxwfm140DOYTAaFntjzfAQ9ooN6eLUIJcmebFsgs/Hz5ORkx8GTk7zBkvpucXvVEo+fHN4vKmtxC3RNDW6iq6Hl0Ars61OpZbKqsTFZiwLvGatbqmW3cK1NZXe3DCfRna8FQpGJH6mAPJs8JEAZbTZzdjtFbYwk+n6jRgKSw4AEBg3potncDL5yFN6id+zE9isNdmKgwsTWINauxjKecuxeP5IoWVz5GsUkusnjhwuv7jz84zNsTsFMBlMaBBEjzcREb/EuwjgDr9yqGzIVrDMwLaMNvKGscSh7OdsUilgHrEEr7uXuiThCXTE378BIPeRop4jdpguwMrn2407HlcmO4uPVVb9lbnejtPI/qq73J600CwtcAb0gIsj1coFcVEBniVirg0xaf5RZSrLoTG1IJHaK7baL/cEa2+52gmlCZ00TdruOtTFN1knMVCdNGjOf6mzSmNRvOptM9lOT2b9h/4k9z3lf3PbaKvjjy5PnnPOc855z3vTEn5dPVp8eB3mXj9ttU22qG8to3JhAVCm44CAR9z/zbWqWohWdAdaREYzP2j8EUvhIjaKIzpZNQMZDxsgFeQJGhq1pXPLV9DFmH4INkFxhes6QhZu6xnkO+UguoA+IhOfjgCMC9/TwF8svr22vPt65T4z8/sbjdw+f/f5eAzgykLu7x0xHSrRLk+Xy5sK8ZOTVo9SirIh5MBOXyYukMc+NpxgfOz/6u89/i4yaEumLo/2+CDmCPEp0/Bdk30huPJVf+/qSzy8fpVPpvcaD7Wr0i/SbNztlb4dip38Kmn4cKndEiaptW7EDQCIQORSXEiz2YSIWQOICY3lzGtypgxebtujxeHGEow3hQzl3nEtoJIBANQGkYaCBALonxDaOviv6YBepi+OHmUvkMjuR6bA1+yWKsreFKPmgdj7909f3/l7/a/35JpB8+3Dx4bMyBxpJSOkfZ9mwn2OwgZ/lhVTqTMYjzg8jnouLohLkqXAL7+D5wcHPps591tM7+JseMuSuqdFpcDeCARHiL69OYk5WPP+evbt0FKWI3bi7fZMMe+3kwZYaxI3vREObqjpVdOihh4qSaXubYCR2U1EOSIbu6oCvdLmC3OgH/GxtDr6chRkZi+kUScbYVeZMwzTk8TbyQ83IGlDmMZKOYywjcQae46CUMwW0AwPkJRFoTD8rS24cYFKe9vUO/Jck0Pz0VOHy49v7e2svgeSN799+/e0+gETIJovePZZxBi6y8Xxh/rLEcfnmMgXdxQwgyQ+eSVdEQbJSGeLYzQiiiptHrkmae7j7ouhxxoJujyQlgPRF/vXHo1o6uvS3p/XH0WqherL3etdm/USUZ21O0YjrBJxtTq9SLEKRY3YbSQyuSLMqHRbsYAmyZdsdFnExkENRGMg48UyLkfVC/YzpmhGLcUktHI9riDN6VtMGoHZMrqjBusdASOggE4tlTb1TZ2KKKhvHbaKk2PDQjDhbq7Xz0Z9efPdse+9P65e3gOTTeqMsJOQpH5MsgpLl1YXlJiHp1XIqkYimePtjIj0+JFqp5OksTsjJdDM+X4SEdz7v6e0ajmLLCiHp6+kSjjWCeToEn8MEGfbB/qvtVLTQfXSy0/A63Z842xTw0a2KRlNgSgR1FPu8tjnV4mLQeBOQK+h2WF24qE6mNoqoVXL8Jh+pmSMj0DdIFnEOpsVR8aFP9E2dDxg7L32VvaDp7CbNnGQvYGfPKXSlv11ux+CFLZ2iRZDrbcK4N+dfTBWqq88e1e/Xd+aB5I3yJBNShGqCEop8NlmaLO0larXqKYzzy9cTieuJ6yn6Ev22eQCWEWl33kMAYosFgPNgvw8hmRiMcIsLUVG61gom6nyewK3u7vXGzsv50YlPX5zcf6u2ufnyXUDIPaZetm4nzmOKOLbxWvrk3eVYItmG9nyLzLGZinarCNttjhaNMsP4SIzIR/ismJoe08KkgnT2i4bpJyihC1Ew10KmLjAEdJeYlFCTIZ3emUgsudbWJKesXDZrF3sL07XCL/U/HNSvbl9+QozkMUNQkGXPrrTq0mTyHwksFkhU6TllZOrFCwCZ4u0VQ1gtJQZG6H2+F6l3hDcveEgz5ruG+y+iSeMH8qGZvDhi8ODwkJBMPCEcV6PdheiPezuzrW5ch2jn7lJ+kBWqaLFXlKLVO6d6sZqTu4GCbdhR1WqzWoT04YzGrkhNTowkNsZMIxzXgSQBacRj4TGK4WaMxJBm+g09hLoQ+lkMMxRjWU7GzW6SAg48p1+jXx1ormvBjjAJZLtwlhDq5sbB/dq77om1v1zbJCS/efB2Aw1nKJ4lS7vCOe7CskvJg1r/GWwWEE9toVZL4cV1/D9sErLHJwtqgYCvF2vkkDlSCl7JRyq9Xf3RaZEJBTwZQUqCHsEnUnl5t15PV9mwy2oHyUY3RLibBxrAyLk51U223aEQI+WkjV2mMJT49OEmJlnPFQizICc32hKPh+NmaCQe05C9jJFBx8I5pIt6jOTjmMGU1PVOIElYmyvgrZkTCl2I8hDKRmK6RBq32KIojVtIoK82ni7XpgtLm7fvba7f3P5mi7zjBvNxVvBRBuxSY60fjJRPjdFMMYqJ1C1x0k2usacizxww3okyBn5QwSoQX4QEeTS6WBFIRiqZXoEkXlQCh5TS1GDYO/toiLSLKzrdio0Sa4w04IuXAEPPFL1Sis0KBZb4ed2KjDRs8DwoBhSJmC3hMAUXIw5OEj7k9wwtTFkOUfIsBSADQPoNgcuFdiTmLM4BJNk3iXRT5DedzY4XYdGn/S9ZSUp6tlar72qFtc3bjwjJA0oMOccW+AHHEl6UGg95YZqAcZg/JDn7E00cAx5KVhhI9EVHGEiIIlAyko94en0XU9HEuOxgk6SkX8IxbOQ/C+Qgq/Unr49VVjkYkkPbD8WZOdg2RrHVuMtZLNrcXq/TFWyWeuyKyzbntOKwUZR8xFZOwUo7ARmOxQ0yUNCNbJYMOZzj5grNDM10tnPrgAQmPoOchsw6FBK2PcPxJuRnPp4+2Ww2+9E79pOhjYN5Mu7C2uNrB5ubDcpeJidlTsOGXSqREp8trSaGpwnKJpLywevRxWa/RSTfZCSPxfnQsM+n3ZUIGXcvulEXU4koFCd7yjw8JeAmSAOH3Z9OfHm0/ipJKbTbzbTibj4VPRXEQXjGOavLGaTc2ut1oIzB9V475zo23BXNQOK2cr5oltt8LTBt4mQ8BqUII6VwEhpD5r0SyhnxbBZNGJ3ESQCiEQdzOAwj0ImZMyJug7FG+8dP9qN3kpQbTxfIuLsTP17bKnM3aVOKwzOWkNEkZ9fvREcZPvaT/GpqePgcPk975ElDAOdlPMkkNifBooVt53nPDzRPL0L89fcB0TftOWRS0s9I2acnvlw72dmwKQ6eIrbbxbwrQreXoSR3abe6CUiK2k6rqOwitjssdq8De9OahUguBPF95RZrS0yLjcRJk0MlhlC0pWyR6PYzt5/q2ayB3Jo0EM4PDdbgnG9DndNf6KAj/TArSXnhlIYfMNIv94XpjfWl4VqhWn2ZLDOSSZFcC5tGin28f6eaihKU/ZKFp6Q8NzWcZzoOYcSht4eBlCuogFAApotQAwuO/ODzZKKjV/cnf2XVDlKOo+WH+HoYScBBbgkuBfsIDqz8UL2KjUwaLWhedFK4gtazBKRqL4oshiMOAalaZN2Xv+PANTegq9XaQpGYskSdQjeA4YOHlZwR+hlBWTcJQcRlndIbzR/ykzuNsRNAjIeopFcCyHY/yfoPoWRank5/+puyfOFdorBwIHQ418MhwBGuSUCWZrfupJdwHy+zchpgSjg/Z0XDJ4hkwJ6ungzaoQWQQ00g6UcZULLiowDkuXW/caV05dF7jDBiljMzTqqcsI5M/1Lf+acadKP8hSug4eqE9hGmTZISq5/JR87N2ZSzQnKzCrLY1Var0moTBUsFkzaUSXbQO5elBUcIJMopCwTV+EARuhzFIGIo6fOY6PrrDIXaKelph6kTL1EUCkEZNcfFkJ1/6Bg/BBKURI5DbvLJ0tSdzXK5WTlj7bgrEhrKaB6k0vxMpKOJfmHV0j+OnmFPyP34EVTGAv9nJJs1qBgYgqaEhROSle+KF65caZ98z53nUJLj4xno9ltvXr0+bnMHUerGbUpOitkINSp8JJD00rdUHhCZ8youlB5dfFO03aKobmtHR2urIrav2HBiQwS1ulzWlpA+tkJ4wFpFBOFCb46PHhBVZijVMUA/s5NApWTnf1xd70tbaRY25prfP4zeePcmN+FqTHS74q8YU2FHW7NrAzNa/FHwbrSKILFEK0XZlvphSglddJ16qUg/dCA4GymI+KlLoRSm34rzZcYPhZ39CwrDwvwJe57z3qgzASmk0g9Pn/ec55zzvOeVk/q4aGRgQutRLjKK6pF/HyMvCGnZpTUqcLJPDHPEGLGyDD6GKAwn/rn5t+pyqVQaJiRLwwTmZbL5SzvaFkcioQSbGEhg+F4AGYdGB5BB/BqdfUrlwc9dc6OeiX/PsBAS88Sh6/mhvg+bqx+pKhTIcPjzc43IKdvrCnn9PsK2oV9Fh9yVuCgCHVhN5bfxW36SuJEDICX/lC1GMZJbY4QYeKbhxg3OuJjgCDE5xi1IfGTLH0TkU+XxM53tqTnrMOdyaGBcqiDm42XiFpMHWTN3V1FhG4iPv8HRmBiplArLW9V1ASXPYMOt7b03/owA+UVbEHfASA1SKdjUJHpp3dxLq2kfDqAcJbuxGK05/u3c3NyT++svOxaLfK2kCDdaX/nN/7pcgYAYG+ItLwnNyJBdyEg7pRfJD99eJAm7hSvtc1o+FYcjEvE28DpENlLyRgY63A673V2fqMOEQXAPtR5lY43LwAciWpKqJATR8aW/jApoMKHtzMmTREtVj15VPvJvdBACJ7sIuNqpWdjMbS6xKbn86wJIA/Fx4qCyvpIt3N3aml0plfi59+zw4GDrAOH41xt/aiuKRdhokbc1DQU5YMaHWFnyKl3hbonnsaAYADcHP00sbPWUd1oHsjufh9qKaJrnF8tvKiNOhEWYK9gYEJAaQEY7Aznlku4kvHbSRc7+BAKm5HNYdQzkjreBx2OOi60WfEnWZfelLcsKQaYh4EUVDaI8o4+JidiDDNLKpK4CZJVqP8s/2SmLnIOh7Kh1BZShvErJHA9sGz21uhs46uaCwQmbxzRdhuj4GIDy8N3x7Fq2Z7a8VS3PEJLES1yoG0bquYGNFMF4kbs5zW1/aBKZpyiakzxjBF8RNfOAtYjD3XI+3fNoPdsari5Ul39eXOxtHwgTHxdcET8/Qs6dcfzhEve0vS7MXyVbQizuSqDY9kpYSlVTOwBSsi7aXcJIOrQ+XaerSUCpJRXgqI7rmWhK1VJES57jUN6hUlGJZrjA4ZOdIyD1zvFJmZK6KucuQyKmZlrj1ZQDOjZemNh4o4PBu84wxyYuGpy2GSh4hc8AACAASURBVMeuj3PG/LvV2Z5C4S4d8A/L9wnLQWJlGNTsxWQwX+QNfMGmL27cEjXO9fZmhMqjYLxbBEloyTyWwuaRn98vPVrr6ci++GZ187tl+lcGB8tvXi+4bZEAjBMSOInbrRQhOVfzwXbZ7iQkl7sel0NICU1F2BHgZCDrbV4775asQSgOOCl7h60umVJULQNBoylalER4sl/RKSUTjvzBsZZTSVh6ZSvqgX66Ptk5rkVVUVZfqkYZrz5c5SR6QlZjiOg5bzCImBsyHUWBSJQ0Cchrcx6CcuZ+z9rKerl6+qFcyCJcDgPKmzCRBWGKaru12NsnjnT3YniIqpvuy2zDh5spmUda2iM6Fra3K89frWdJEITL1cq2UwoE+Lk5Fz/yTkj6/JyssbpiiuCx+dISmra2hDfkt8Osgn0B8AhQ1rbbrNdDHHzD2GFx082NXT7dGR3hUCM+xpJaSgEhwcgzLcamIE8NRewa4DM8rssqsjejqCiKhSQV5xr86DVsG3U9p09aAqjTNAzR5uEfNCqgxLtGt396vTA39/Hj3Kh5uHoXIqhw99HD04fldQazNNx6C1Y9ytY3qeoeWDoSXaC9x2KA08xBEkBah9ui5L1sduubg40nL2YIx3D4w/PVBT7V/Nqc2xpnSwnMYind2OsDIRs8aT6inZO+b5jyuqiOccFKikqQdGSInwpyXqGkXaxCrFP69bPMA55nKSrydjTVr8SiFCPh5SVGalGFTn2yRjmS5LIuJ8eh0nnCqMik1hFdgTWaHHxDorbRwYM7TnAPyB5MxpBmmIuMo2hA0s9C5dntpy+MUY8xR5LF3N2YWQGW64Tl6enDhzuY23QsLt7s7cuWstnW7D2rm/bp8yeWQUELSIHkUBulomCRKppiz8nC7sarJ4X7hexguEo4Xov4ffV4iwq9Wm4kOikxB4iYlFZcdnadoVJB/zvhmvLit3AfnldQYT9axM0PhtSAtBaRuxzEyKTOSof0NwU90pK6GktpKg+70bvIKKSMlCuRkOpyVeaICiRRn2us2aP8FVz9yUslKXfmrLdJxr+eNw0e0XSNCEsFV4acZw4q+6+nb++fwL9v/tKYMw9WNwoE5UoPgXl6fv4j76I65WVID0/PfxCE7D764ft7xUsgeX87NvAONYOSSEzn25ubL94UelZK4bUPr48N250IH+jakyrwOjsJRhI8UiJBOdoBC4B4iI5qFqq1E/XcanO7uPsY8nKdzftiLz7Mybp0LJ1k4YhehEZ1YObXr1MpRbcGi4Qjer7JnFhkg7YYYQiJrlLVo2EqlrFqxqj1yV2W2o05mQ0teOpucrJzge17EyJj88EW0uft/snq09lnT29XDkyzc37eJDgph2/MFlqzlMeX1neImkDzP/z58ZN1YeReR18vBcl4LdugS46KJ4+dU8E8hc73G9+9Wqb8tRJuLW+tmhFbghsN7EphIenm2gZL2xM2F3CkE1/PtbTNYQuEphokMVpwCSNkyM6Z53dA4mm/uliMkrQGIGHuI4Ayv44hRMJYRXqcB4y1hrgKilHRzXZJFd/C1Ic9LRqoqMoXSaZRnG0ehGHzPlxr88aINTPk6TVLSMBozJnH+5XdzZl9QHli5hoBJZZiHL5d3Vh/vNaBR9V6lpaW1vd29nZ29hatCHnU19738vsWIYCgf4iR/+UWUb4t2I0Wb/zo/MkMRdzh8MDa9K5HT9nTCcFIm2TRjkRNIIB5Q0CyOwL+2htKyNNSJBRqqPeBtjw1pK/sF3dorXzNCwRcWFeTSmUyhAuPELmRljnLJLUxJUm4paAquRnEHR/6hsChkMkONmhPbo8TP3n+TVFy1JO0oORxjUemRAPnBSLl/AjjONFl9SosLW50nRx87HpX2d89qczMzj79x/5bEzCaAs3Dd293q+Xy48dUcPeJXlD7dX6CoaXl583dk8NtpucRURBAHu3da6kd7iKp9qM9+CuHs19+OX3ityX1NBxnksMmOMlDAocjgIG1QwIcuNcgZglOp7M+YvfapYTDGinwHi9ek3aVikJQeh110UxGeaAT81iT0+fsjHiZoTAZg5gU9Q2iIHEuoyZJbipI82xOJV4q+FACUnj8yJZAca4hlvgCKHESd747DZ4ZWsMZPtgoDo2Jk9vTxws+Ot6Acn+DWPn0+MC8WBB2CGYeHrzbfV6tbpXLO+Xyy2YB5KeD+V/oP+m8hc82AUmRsri0dx1IFoeakXTi8Z7W1tJK68Da/rbdHbjmS6mOCN4i50atuI+AzMEsDSXSboeFI5v5AKTf7ZOs8ZZoVIhLdCJt1w44LsjWpUAnwkEFNFpUHzujs0xfpNMxReU6kTK3LgIgYe6J0q9ouO1wERMZSJgylFqJA/GjcJnDmzCImcDRNIHjiGj6iMYZ4bg9/dXfv5p+25U+PGYon+4/m7790/7uIcNoMoyH84cWrERW81X+KC5w7BwdNRq/tVoZAsjFjo4/ovk71ARKxuNLpdJ0tVyojISooq73RdR+bGtGP9ZtPQEtpq1SoMHuY41oDbcoMtoiuAorSTVk3XyhWMKzDXbnFUUu+eySq65fScZSSVVNCeuuTjDCyBfr74+pwqnGqZs9adrZmIJZN5CHuASK+El6ksg9CszSnVaXgnAUdhZ8tHHz/1xd30tbeRb33t69xvaasdD2kl+ScvemjsgIN2ttXyJUEB9spRMFU8cGCsV0tS01UUttIWa0JV3JpAlhYRVEaRmQMG9GkMJ2nsq+7NCHPuz8BQuz8z/s53O+N9bdW7Ua9cEP55zP55zvOeebzVZlIImODfzUgSEce/fqn3IrK616I3PcqEzVj5qL9Skxy/pBY4/bweb2bu/5YCqXP3zPNbufyxfmqj03vnMzn6UGCSCRKY5fuXz59WcmjF8j54FvD+Yqh3/bPeI0djeoRvNs3ZDrn6UrXB1hsUQbDJ43NNnWd9JoBtg7ERP9Uxm1zBRR0eiUvXKnH/0PAYPyJ5aQQpkcDMaHnvyD/RaQ5fBs9gKoDIcoM2mMspbmhmz8mpA3kaRJsnRJLz/LEpG/szci82JsYblZrfrNKXJsyOMZH8fqwUzu4sOJlcnWYuOgBih3t5pb+bq4+CYoqKFs8fbtvbnf8GkV6Xp29f1Xn3/JqtGoTLbxLyY081/JucO13NrzTJHePX6995v3872vn/+l+Xv5XFDvCgIty5r25AoB6khNeqBM1TkOprFooqZqo+D5gcX7yM/JXB0nkgzdULN03bDHc4Eu83TZotPoiCVjSGVCQ09Cfu+EC+ceciMcm6MRtlNFntAOAVr6MY9sCT4TR9uVMEkdTuuEk4+2t6uFbkalghbqq55k2MogmdSArquZ0Z7q8W76ai43sbKSrvy422xszZQWG8dw85mZl+lWqQQwmxBFVd+3f8uMnq3uH5bnqqPVvUazkk/nZq/PS5WCQP5azjZ386tUk9fGL70bf/fL84PjgYCm68Fu5Na64yV5q4VmSG8UeVtcHIrnDHW6wYX4tD0CiQjAIzEkOQHZpM0LMfzdcid5TRtN40yH53muzapjJK74BtkihCVT71gsQoWpUm4YJ2ImFRGRZEuLq6BDMqP+Ux8jJyXIs9GxONd2grAzcGxBcWQEjF2VmjhxzPD7CI6l1s+tyZWJl/n6j7XDWj5d32ocLdZLU3c3XqZLeNL5CuDcK1fxlnF7zlar5a3derqUQ1L+4ekP18E24wCz99Kno3y+uPPiP0Dy3bXe3vl3yweNQHd/mFdnB4KG4UxPx+TGYk01OCMBZFOKlqRzd1Gna2bblfll4BxfCJwPdANaxwL87exQsht1AimKqMOL0boATEyohchFE5HozWjEjcVsgiutk6Boaf4ZI3O7cvCYSIhvy0FEpN1LqaaVFeOwkZdAAseRqmpPoWdnqmRtGGRGbf67MQooWzDKV5P4mKtXDg8rdRoiwmXp0dTM2suZdLrUapXS6fpbEFKjAd8v5tMzGx9WVzeezV65/Ecgydz60vu7y9s7+8X8wuA8ZXnv+IPFW528wzQo76ZhOeFEkt0S6kpyeHIgEPG6LIuEw6xRnb62m5q50EIzTdaGOMTtONqp7PDEHknkPNeGecWSSVtGwMaQ8oGjQ/aQFCKjESmWyyFE1I0CrPhQnI6djBBIhEUWMaWOadtfEhs/O+QBGQhcObb4swTJ6kA7OexTuxN7zo42FgFla+XV5ERqc3OqsL0jWB40m42j3VJpKn337gaXas+8fCltfo/Xnm68/uuzZ9xMd+XZ47Wf3iNIgnB+3d//6f6jhYXBhcGve78Zf7BcZkMugptFI+Tduo6uxcIKSGYxpnbmWy8+bYkZknQ0zTS/tOPSxzVm2BCU3WZn17Tl07fZ+aWy63ejwbjA0AnPFmbh6U0EcpxHMnHZPsdFVfwWMnFwuR23h+K2za6CSCwBOuLIPIxVCUmlytsaCKwNGx7tm6uODGQHlD3KGZeUIIGkP7CIaBpx545/T7daPwuUqVRp5u3hzmERpLN41Gw0j7YK+anZx7O5hw8H1fHYRRYvBmfvvy3WGuVyufbD+Pz8u/H5T8v3BhcWhoHk8MV7D542P3YFgWBQV8kMTFJzPGvamebdXtImEdCs80bI0wzVAtCu9/4PkBobcgPfnuuGWvesgBJNZ04ZpPx8B+zRS3qAYmjMBc3C+uihUTGyqJoKkyfKScVEgq1VcRuU7iX43BxS9QqqSN8iWR+yWaPk0FM0DunHtjMVIeWM65bi60yfP7XII4hQz425493SZqs1OTk5sTmRWsjNVA53dvbX12CZi3DzBp5mbWtrq1KpbNVqzUMCWC43GrVK4c76p3/Pj19/cG9wGDguPAKOg7l8o8fud7r6g0E9KCaoSW+e40wnHV69yWvdwS/B80FXN4JKoTPBMZXTM0nkrFInRVGAi1V4WNtviT6iO7fVuKFovUMUIykY2Q08mf18TyKs7djsmYyyRikPfB0ck2B1Mh7Fz0sHZULJH1FBdG6a5WhEOgGlkitAUvhk/AA54Ndx6dd9/p416acky+/BjVtAcRJmSRfP5Su15y9e7NSKhXxe8Kw1mwrSRhOgLhbuLN+5s769s7S08+nvV2CreFsYxDM8u9v4eEZ3Pa1fN4MgCd7BCeQsAukkgSdfshgoIaYtbn7lWOwXIE2/zx4mGRZyl9tYAKUV7lJDDyfKhxVM/BJZO0ZzcsHaUODR0AVACNAIbTQUc9x4KKpiZAhxEWixpwX+L7ydCCmP9lNFVVhjOqlKF3YIfi1tkFkFoB8lB0DYfadWhOE/ddEBrLK+SbN8NTm5KVim84XaztKb75deHG4X1wuFNT7La6t31teL2/s7b/6Mfzvby4NqaBE+jZxweKrQ+BgOGEEnYYn4xrtj6RZSGt1yAKujXrVYwKA6PB82OAXSKZLSbI8knnrC4bChBmrUJI66q8qUK1lE1RsGycaFCkT0A3jqtDAEzomQo22QkMfVsarHHNExwXZyNv8lIhGSDu3WB5KW2XZwNe8UiUTnstksrBHipw3iFxzVGU6Puk9HLTlP3MgcH8AsN2GW9HFlmKV8AaZZXvr+zf8/Sy/2i/vFqYXhQUFx+LJc+lwpf7R0h2TiOHI/MdgaOFri2Lozbepii5ppaZIAylIfxeOqXepUlPRjZdhQB7KG6X/CLZJGgNDL7AiBdPm3J6DAYwAnBs62x8Y4EkLaiSU8zw4pz2bbAOV3wh3ilgt8gojJBl+BTpHNiZQUvw6FwDOixGmW2ewtv+uMQPrbg/qk4Xy0vU8D/NQzt3f8z3ppM5WaUGCmNnOtHLQkBHqhUCluF7fxFIvFt6tr92fpzhsfZhkZh2Uz6myhmenvDnqOIweuliSEQMpSaAFCfTppcXzLRIzkfUqG5hFBXr+ry+s0MkMsrbPrpMvHaKPbPkUMSpooIzisYJodLv76RAxQwjJhWi7XCcAwEQpt6ESYpJMEwgrIJ2BuhskxyHKbk3VIFhWQIfuEtolje80AWypGMgMAE5GyHR4hgDKjfdG+k1WeXDgyKvtTOUTfFyWWB7tQ6amJloDJkJlK5XJ4w7Mw3H7U3u1hDiNfvoIYOZWvVb8LhpHGJJN6f0APAkgFEFhFQcm5TZ1Bk/ZnaRIVPRgh3ZyhU5ejHNX72OUPZrMzgMrIUKPIPpDUP92i202mQx2U1x4Yh3ISYAiQcnjABMbG95IIzzHb79VHhgjTtccgKQkk08S27PkCpNprdSEyR8cekbaKEcExk/G7zkb71PZJFn1hvOrWsXa8lMGIvr1j5jYAM3V1YgW5uILzKvsvUuqW3pR6BM/h4dzMYjN7SwtbySBwg8rR2UxhOhx4o3o0NEccWFd40UzBMt2wxDOag1zQiwX5hTi9asDghLEQiTT1mV2WFlZAdrI0yX3ualqbqNMi3RjMSmQ5cHOZBLJ5HCTuijq0E7DKJJBkH190jJWfRCw+5KoipN12al+U2+0cERGyB8pHLdWE7snI+asUxP9L1bW0OI5eUeuzSrJdsnCBG6EXCISEMbWScM8uBVXgVdykEwwp6Ka2A+lNk/8QGJiFYZh1M6uBkHUasstqmH+Vc8795K64XI+uR5fr+D7Oufd+V3hz8isxCNn2tNnCGg3JXO7emKl+NDC/J5hv//v27b//eL39QQMt/rK9333/06d//fA8IkUjCCYpiKMbWrljzAtvMj4mCf1cl0RzFi5DsZ8wWET82u28zyJezSYwY6W/6njn3AdFmp1GCkI7Naf2ROjn8fFbZkOfcdYUJtmx5AAGDioJ4X0UUgqKPYxy1O6QA4Cs+QPHir4t4LJvSjuzGxINR1RIfO49g5Su8TiS+Wyvu5iaxoY1NtMUJbc67PC2apSNLkTzy0/AE7e3uL95+6c3uqzVd2/+9v1f/vr3Tz/+/PLOIQWPI/DZ75MWxDFtlWwC/IlI1MAygVEukYFCB12TnHmgGDaKOLq+cyMiY3oTV+c4tPAou2MzYhks76YiGp+S4BVd59WWkOoFOoEkiCo/Im8gCatIkTcHcHNVw3smkhqxexwy1ojg9KQ9ED8snhG6bnJs0shVtrLjtLlwfPb88f75RX2Fh+cX+vUm9+eaNJp13bfmsaU1X08+8f98erpcgOd/vn79+s9PX758+Qdef/306cevP//wcv9hLJY3EMEwRYCVprC4lDcGvRSikKQnkXO7IHItyxK0SLUcEleEd2sAHUZFOm8boz8GpGJh6JZ3ayv9FqbEiaP6YAVtV7uTYuh4ZO2stwiJcMhbfvz9M9M0dTb8lVaKlDMM4EEavzg0lcporKILSNosMKy+kR/1FIWjKKT1X9+ZuuZtc0WNS6R3tlVkZ57ut+GYz/tPPW3xKx67FRgENJitJfrw4cNvexfI3lybpsgiIyWM20MPpnBa2GRChhMA33EUzACs0FFCWqfK5HizuCuUw4NoER+GuXlvNFWAgkSHN4VuofJvmuhsvEaGQpY3z32CaBnAIqH2VLeoud8nyz//nj82pwFAEUe2Xj3EY83TschEHaHrESY7q+Xq3cm6EbkOk4DV7yhobN7+wVNx79kfdxNkm53NAylgPk1Irvz6te3Kf/qpz4+IoI2WY4FFtHswCdyBzAh+DfvC3xemjI1h2Lo9kjWiJDK2lvkAx4Hf09LBXbtfIzG3tEcKm8DdLQpekpMXOI3P1XzhgfSM3CVRbA0yJu0ilK2PLaubKYBtk/PZncssgSCfybOZaRj74K1g4af3W9a/r9EPXyLcY8b1X+CZ9PfsdJzCYscqENhm5p2aWFLRPE/26LsKl3sr5W5sS523uG/9iKktcc3cG5sSxMM6sESC6Fzm/UgohSSNDDdHh+Zwnv2ZTvhRsQBaLtAUCSeStN96dYtczQ8DVYSiBQBlpqYJzus+NoEY+S1AjuuTpmQTsXGbcl1xjadu7yC7k3Od/hkx4Rwks1o48a7kobN0VdaN1UFdGLM5ssehHUvmbZ6yA8NsjlbY6Iw2CVV2u78FyAdL2ISSrYXLxSS2D4X+/fRmcwVy83+wwgxh/siIiNFjBxorOkYDS/TSKiPvQ2KZpAukE8EJ64RRqsgD5ydWtECaZArrGd1SycZxh5QyvaPaXt/0ow1gRFO7durgIEQ4brNIk5vFunAR9CcM1Z2Hvjzf3p27JSyyy2mSx88Mhsgnctw8H3sWMHILguLe+BOS5HBUjYKF4NPnbAKSSNbZ5Noex8t01lBIXnHc+Q2UYDoTcFOueYVjLhfXhMwjY3Ipv2HBj2RsNASZRVrCyn1RCnlx2BJQmKljrHRM0fjiqKhIMAsOTgRMLySUSbwIRdhhnQJvWQ5xOiUc2+3j93+ESRFRYjrw8MTFbMjeAPyxLc6uXWZtPKsHtQ5yqOkTQR1YaqQLdSV30VQ5sguPy4J91+NQw68VE/GZ4wmIEuVOsaG7BskcAfKBTcP7iyGJYMm+ApXhySzRFKJ/X+Ez1eaVNRqhx32VPWpsy07s0m8GmqTcGjAi7cLcRqBYaEMKDAXxj0QR4LIasd8LSOCdWNHCvB7fktBSuRmbpQtqSJ2AXfblPNQppFeLVCjLuYcqFMdcAr0ziTrnCRhS43MyH8p2pvZLxsTMjhZQAWOsKV+EJ4E8sn42GJDjqN4CPbnvTu9VbcvYekAIm8aqmGge1MU2Ok4wwYOE46ZqJt9+haaZaOU/hDnid/jByhUZ1ZZPVS+bxMMdW+/cbagkwn/gL4bzhYswFh13RC4p2qcP+tgJStUghRdIEF06uAtMQV6LFdEi6+PCGhESLJxY0wg5fhS6hv1aEPiztcL5TTGlzzxK6hkfovpZHbhFXVcHlsz7PB8Y2oVNQ+7IfAOvqtuhgsixSm52bIxJKul3HsfyI+3wwR9+pdSmSuTtwuKjJ44byzcbv693Kxw9wFvOr26tG9lzEDhj+VMqVkAyZSt9XH0bKTkwMYzgFe6hpWmBwfj0W8oYwDybUNcYowaQjkgGsazNxIzgArXO+9gqQZGvCRkTgowpCr8xyZ0Dw1F6x2luZT7rKPmIJSd2RwjASqh0Gd7Dq7VjpaoUJck3h+FYld72uvJIommym41uXfVq98vLwzvhyCE+jt1fiOODGCQ7Yg0woxb0O0QqvYCcm1kyQDKLKV+vto/0EzynQ917ciHnVlwkOstARLylVbGrsGCeCROZqROKiaMJqxJpOC5ZAnJawIckE0kSGgvnXE9SJQvqR7XCAtZ1Qs5PQRAWJmoA5MjnTfVIUM2RncSIB98FZK/aj5rTfdYgFJVVNgzkNFqKpjZDr7YE1HiWKQ0hikIyZp6Ud4MC5O6Xy8v9g1Fx1c8gbp6fXwjm5mnHtRenqaaLu9y5aRgmG6rDamNM1Dd1e4vAKsYbjlKzYj7gOSDdoIGJGHYqEpnyQpDI1m079ACbV5miemzPLPhIFxJwOnTg1ncMlR5IY49IIUWfx2ESmWdH4Eqw3ujmhj0ujgcsQ9lyGE5HZpetWzJ0zjpVuvHwyoYTpIeKU89H5u6GJ7YPPADPs56lqhr1cK6gxnM/PpUbkoqUyNtI8ztVKkxjP2hMBTi+mKLZic2shBu9udrs8KFOfAPbqtpWrCrzJFRVQshwsC3z0bHz5sjbMMjCAIVxbqeGTMpsG3K0njIR2PVDK5vFN9ZkShquIHck9WFovL3zju3HVzSvsriBc8+DSJ9k5cLktRbGxr7d7cLr/khm8iRitXPWMQ8rTDYVZ5+Px+Z4oP5j1ZYTfHmpy6uRmIMSdwN1YiXTzdgKO/h4SQpa5Vbxse4C7ZEHQZiwcd8+NaeK65m2XOJ5BFoAcWPHvdUVeg8hz9M8DVXSttlyDrNckRdkevFGSYtM5Nos1Ia+YBOIk0cC0lHEEEmiiCwT9SMFItM4OdAyMOu8vQ2DwGfywCaBFhzOd5KKFgUoMpm7VcOd6rzhtD+N5XGwUp0gm5lbawilG9jtKuuyGwc+5LEuByM1FddCA60B/l9zS1BVmnZUQ2KqRHYl7VFurODoDZMwXp4/NkCwKh9Xqt/iTtRsiaL2OWjUclPt2BA2w9RAdS651Vm+hohlRB8GkzUu9aEsnG4p21gpPRbqZ+yVksD6WvxI0KqwK2cndgHnUGjYqkDyGVE0jMLbcDi4RWorTgmV7ZVcmDlGsU2qTYstQhtYTZazMqttmoc8jSdFYKHsK8qTgBrLtxmAPFrTNe+6QYpbRlnnPINsQDJHsPdq7swNUxcroL0Ygawe2eZm6TGHaWobpeFHSG1klcUScZ/cc1K+6qEMfoyhNhkmya1iA7Gz9hZvY6uDrQqbIJgjNUQbxsjhg0utdMZSJOuQa1Ya1F9UJ4z/1zoI1lE4D5P+UMinCdWCayWn0tm0hHMS4yyLcOUcQums8/qQ9gUppmnwvCSZYf7JSC+5/qc8Hi0pD9TcXBDEMImUBHpErcO5jK2E4YtdzFk2yRaNHJvxMefJ7wZOuq10NHzXNH7lX+MNsrJks9WLiBULy685JJIdMFQxCiZHRbM2im0chtrQRSyAtyxokCZBxUAHJn3g64kilvgR7jkjtEnA4KCK+dqdi0V4s3b/q+raUhtHomiqrMhyd8UkEBCSSiAQKsKQryr03TAB/XkgAX3kI8wavILZgrcwy8mu5p5zS3ZPujuBjmnaJ/dx7rkPmXlGR4x7yFXVZimI1+RyhiGQVC6ZvSCjTRuvERiReD3SN2yzxo0qsU6I49DUuPwpxWFM/QIkhIDPdeBdGwWy+foX1ni51tgcdGZB8+fpJLkFsfbEovzEg0w+nw06QTEmji/YysPulGfZXmP6eiLL1R83Mg0hBHtMydho80i4ufk3aLolUU8OQMJrTRiPAtZR3Vs8vtqx4QW9fFewCjL7h3Vd21IqlnZd+oLaLh/eoH0aPe9TFFli29xechej9B0LRJBJ4duxw8AoxB3UKVCAJmFwacImtwC2nCRSyttZPQdS5aNDfxHj/WqDXQAACEJJREFUlHjvL1+or4X8KP0Bjp9/XTRh54SC05NcJOGl3myP82m+ubYQTN2qF0QDJxSAZK83nTKQrBGF0UBJu1JnVM/UfejBfEX+kBdV+zVSy+X5x8JJasJcQEkIHSllYXa72EyrO/7c/TR97VS6wGYYqmwER8PRfQEx2f1hW5nF9B+qgbsAHkkCwwWaOQRct+gw2VMj0AefeglqKG/Q35YSI0WcveB474TzXpjnRWanlHvJDBJiLktDDu8hsQhGXsfZurd62K5Y4S4Yb7fwhB2JFs/jSPBtwvM0z2SpGxfXD1Y2sDWoacXNtTkoZdhUdb8jybIHPVgJkzDKQuinBFecQsLBe4mYWFAyu6e2niWWuZ9P5dp5Kym8teZ+b6lhWHbBtBs7WvS8DC10b9XK7yYl0/hocAUf9jXPyjWEcuNpDbEBkrhmLJ6JQHrOR3mxwtgNmD2ffkDxwS+9Y/iq+pniiN6rf6THDjhwg+sNM7T24ebgi2ZvedUjDzZJRqpDg2pUUt0wXcl4CAQyEilJFhG9QYHvSIgglGnkg2a5ZoMcoVKMrBGPRsXe+4JAamhlGSgU52m34k5cv5Y719ervLhtJQagNMQRNCMl5V4nzHWKQGUiVkCGFsmG7NQ7CJEJtBvthIkKJZTHJobOq3djYTFGjxlpDJ/ia+Becv3jcsnSGaB8RXX9em11ed5vQR5R66uFJp6xu3yzSni31+sOENgRIjvE6AmKieeEDFS0BBjTmiCNj8InheYccmQ0ZIWQHinpXE2SoppRILnNaaS0Eb55lDSTEsrrQgWf8ueHwxUp3wRIl+uKQ5HuuNNrKujRcI0Ja4mFTkznOyvgTuxrS6qeJEqOmIKW/2eNAb4a/+/AKD90KTQTohY6NWK9uDPAWw068SdufV5egKMycaXkKLK1t4Ci5YVQ4hIBggFs8v37XW2Ru+E4p8EV3WcWpLo73j3Tqeu+l+9oTQMk6dFxpFxhe1fqdA8NE0qGo76oOKYsohNIy3pRk5I5lsWoOodOVtC8cEMOK1qSSsPqJKyaQ+EqPkoAzg2ppzTljmtOEmkPUj2iccbGr1hkiJ3uvAM6JOUBQ3s1yA9QjsFPI5KP1Bs15iF7jFRhbnJZJKLVaNz6d+J4+fVrYz6Y+FEcn3MVyKTN1HJaTtg1+eZxz6HBndkr/+GL8BWzXKi6hOWC1g5egYRBJhJEauQp02yjqcRkIC2BtCqOq7erDKwZFmWk1JcJp7C31gJp4dNHsUZAKcWbACA5HI/dRZbet5Ke7P5+Vxo9XrNPDgpxMrr2ZFRGC8SRNW0fh3OtVw9zmJc6sE8SLbHnjpDGJcQlL42g6ulyzxAJW83yE6NTFHw+3x5zHJznTHdwn2CQH8v5e4Y9Yih4UaznQaGkgzdQ7wLnYKHRUZQihElcx1oymzGx6U/onHa0soLrCKTNGpFl7nZUySW3V+g3HjE4wJ9BcTsTgoeRu7gGz6HbFXxcV3GequPHg7mvsEArZik1+fFQtvKPty3VjfYOyRlTfUowpGYIy1ln7SlMANzGd8KMQlx48UKA9Jj/mzXdYO9GE3aWfIAhOtqvrAzfHj1zyu2qPr/ikU7zOTu3Xjef9f4sjgbiObbYilwaCnxR/EPKhSlsQEY0qtV1iRS7BawGGSQBmFtVstg+O6GcBuK5ACkVuaCJFi56B2x4a80nhll97Kr71gqj9H6KbXG/dWYrPOSrwBN40ayAcFHYNlldWC7a9o5d6TqwTIRVxrjM2m5Ar3riPU4xyciHLeGQF5c8vRSWHjthyyLufrlohPw7Xwf4HUcGvWG48e8hY1b75R+Ma6nDX81WZ4wattSHmdyhHymhLFrXkI0jSGobkcHvCiGBXWGYaVRaTowlABxcz3a2ZO4d08MRaKLhjSlUk7fAWvlG9fQg6X/trfxDVWWyVPHw0Mo3sD2HJvhxLFypjSEAadd4FyZt/kECUrHb06u3NUOPd+TFuUMHGi5xsRZDQlORoxe4NAcYWRxutaF4NjWfT3a0vP8fiurcs5Q48/vZZyQ3hk/b9SicuPY4ixGOIabQj6mZNULG/Jt2NjoVyN32QT+2/GsVcyGcYfysMqmn9YGG8yEgJQiiw5yLRVbRxwxI/T3uqvJJ6swS46VHtz2QChdkMVF5yHMtUmhCSmoNFF/b35GZsbKBPIFZC5Vc8gISh1GaZm5SH/zMd1qfZrbCYRjomX0p87mgnrn8urwyOMIov7Tp76/mqDanNincHjPqxI3XxJYlO0anFAGTghJBg0sYKv6jn71ScdKfbI7jxnLEle0qlIXTUja3dDTbsL24OnHnGkAjIhrItYCjNRj8ydPOJTs6JZZAjGnFqtt2PD7Yam8o/UDq3edeDZ7cWY4Ca+94uy+tK1w7pKQZp8EgXwiYFg/aggGeLACFHkvRvbBFO7xTM+sxWuWbL+1hX9jn+tQ/AqVk7BfcLM44+izxDLmm4QNLav+NfRQgKTlnQYNykgJVgvCmAPEuW4fmprCFyACpn5La4cjZenx28luAlK/yFhPIkbv2FxznHu00opVTCnFEwqXgUB4cYeQfk8Vyjva66A6V7bESW273I3NDTE8ACdA2RoFdoJSf9Z1H+YIbkkIlt8F7pW/sIWAGCNkGulmQKoZ7daAvYjOxr5cFrYWcaHIxw5YhmM+bz/bos9duERJWiUP7Tb2ckaDVuxmQQ4cAo3t5yHaqRHax6frc0s4km7k6Fy+r/lKDFJZu05i7NrRBI7gmiYexRxl54CwURvnIHXmPyugIaaFslDND0DWrvcO2NixVRbTtQUxINxIuWmsPbpRwcLDxP6dSYgZ9E8BSAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUgAAAFICAMAAAAFypcBAAAACXBIWXMAAAsTAAALEwEAmpwYAAADAFBMVEX/WgBlg0oaGhH///8REgwsIRYUGAsICQUKCwYNDwkkHBNCQjVJSTsdIwtUYB5efUhmcRAsOSBVZg5WWUlQUUJubFpdaBYvKR6FlA9siUxrfA1cZSU5LSJ9jA3/XQV2cF85OzBwiStlZlc6PiBcbwxodh//TwBif0CgoxKtrxJJSyh6eWh8iCCZmBR0fSBzhw2Xog9dYFGPmg+aoiJWeCG/vROFjBqPmB6kqxIxMilZajhmcj5fbiRFRBluh0JMXgpGZTq1thF4fhD1WwNigCZCQihMWBe8ukd7jUVedjFZXRM7VS9zj1AiJxZrhBeFjy1BXTVpgjf/VQBxdBRkWUyOkBH79KRCTR2jpEdBNCpUdkV3jDd8SydLbkBdUENfexJJWSJ7gS+qriqSmC80TSpBGxRTUjbp1YCrpB4vQiVSVSa0tzmvqj1QbiOkoi+CgnLNwxdaRji6tSJgXj1xTDmqsUtrZ0qNkT/9+PJWXi2kmR2bnjnHvCjx5Kc9UGHZyh5ueCz77YdRThVBUQz6yQ762REOGBhuUiFNchSifGOEfxRzXE6UhXVkOSfjy1vu4ZX367xRPC3OwEKHgzqwiGvx12i+vYYpMQ4UIiKbl0iWcFT4uQ5PKxyEY1H/ZhRtd1H98eE1Q05UGBD8klS/eVXCwFmub071zz+7uXGLc2W5mH368cuQRyaWYEOzsVp/YjA2QQ/DZzkdKS6SjCX2pT+nkXprc2jGkGl8OSOGUjslND0zFA3OrpCImlbXzDagUS+2q5cgDgn2pxb+dSu6qB767BZjHxN/c01HYXTlvzP66kDevZiqZDunn5CblmvRglTJoX/3uy9qZiCZk4P94c/acD/qcxz6omXYXRnsiUDGvaj0kRnozad4JBKoPRkkPlqrp37+g0DhrHrm2SeLg1/BUBTgjl781brQymvipliTKRPg9/r2vmD7uoy1UjJfgIj/xaP87mT+qnp4nKbPshnY0sLPjCjjpCzK7PR3jIbdQC2ar6/EIBW1z9Hk6NxxvtiEHwrEAAAgAElEQVR42myXQWhaeR7HQw57qEbSPl9ycOHJyxZm9mWFR2iGsDOUDSQZhJBDAuMpxApajOSVSi1BQ7P2VBET7OhiL85FlAa8yLqXruQwICZE2thTyUEmD8aFvQx0Kb3t9/v/v6QzZX5/fe+ZqKGffr6/3/+NxeM+1LnvHA9fcMo3dT4lKjgVvBXEeXJycn1yXdbiYi7XiuwkrmplpVhwqlQonZQKncJJ6eTkpH7JetJB1Qv136lCSVasFHPqYO8QdYR6y8PR4dvDQ14d7sVGjWYoVAmF5KHZbGDhiFN5WC4PUcfl4+HZ2XBgWQPbMGwrb2vVqpYyk9Fo1OtVFK+ia6pW1VOqpqqaNjBw1nVDVVXTNHHN9znldrm8pm4ZlmW1cTCMto5qt3XV0HRV1U1TMRV848Lq6vTC9MQ4amJ8AjUW340LjiQZ9AXB7xxrKhgERxRBXqNcFCTTiU8ki7UC6DkkCycgd3lZuJQcCbLQqXfqePTqvTd4Ohjr9ZPf5XhIeIdHP7wFTZIkVAmywsUCyUZNgmw0ypIjeL57d3x81reN4cBG5W2jWk2llCQhRr0ACQwaSFbVatUwBhZw6rraNnVAAePUJhkmN6Obm1632+v1tsHRaAuaKjmqRrttqACZMs2oklS8rpvT06vTqxOkeGPixvgNgPR4ABK1D5AkBxnJcQo+3pqaDP4WI0DOU8kdrB+FksXCSDr5S6neuaxfngDlE7HAsdghPWe96b25MtKBiMffJcgLSZH0hJZQkS+PHJBN4WOaJIGwBo7NsuAIhkLJd/8Dyb5d7eNg2LZlaxRSiQqWiqJSSBVLr4JO3oKWKvUiSBN4NlKbmxsb3ujmhtflBkoo2FZJ86MkqeIV/ys0XUlGk8lkdGl6+h/Tq6vj438QLFeFkbsy2r4pn4dKChuD10bKcIvKkeXiZ+F20n0JITuUkRyfMNYEiepJlr1e/Q0Ovcs6Xl0KkKVrH2OxvUPBECLuCRGxZLgRbfrXFBwpZahJIUOgKECWhw2RbSg5HNpVmzi7VdvuGlUzBXvA0tR1TQMuCFU1NANxtTTNcEJLkKlUCjBVVdnY2GS0YakOyIAJKfk2VRVXlqGppkJ3o+6ZPy7ASUAURoLlGIK9K6Mtki1qyqF4a1IoKX3kCgRygdxsKxJKSJYrP247To5KyDjriVPiBYwExA4JvunJcANlr+7kunQlZMxJNj3cI0rnCpcXo0ZDggTHSBrRrjUfQcsrkCLd4Miz3bX7x6+edavVLoDBv2hUQbIV06RVukp8hsGjyv6nwTa0PHBS2TwhJoRkj+Qn+JE2891um229jc/gE5A6FVVEL12aIUgYeUPGe2yXRu6e757HIaQnvhz8rH5l5OK6QDk7P49/UCIkSCa2V0S+gbHYyWQesIDxsiOi3cnQyc8KZEu/xK7DHYuNTmMHh9ckgW/vZx4uUDiOBMemzHa68kj4iWiPyuVX5euikH00R3tw+rLLBpmCPoYZJcekqWCyACVtrAqQmsUuyB+a5gYHED6gaeDo9/tdiuI2FYwcnT0Sb9PbGoU02FfRUDGadqNRF0FOyEkjjCRGzm0fKS4HsyS5jHU3yEfwTxw369cVWM+F1yLk+IhtS9Lc3l7Z3n6IunPnjsB4baTA+DlJzB8n2VfZHkkjmWZkmRgv9i7YOQ94llMaKNOVSCX0CFeJBJWklA1B8x2rDJB9zJqXr15Uu6lUEmAMDXIlhV9ob6pDD2PdMvKOkSCpbOiaraa0rmG6wdHvxsDBRxSRZk4c5Bo9UhMjH96mEO0/L834F0SThI0i22O78V1MG59n1xMPLmeXl7NBorwbzF4r+WnarAdya1LGRziEKo9RkfQOau6LL+79TaB84KDsSJSZTKeX+dzJnoBYwJLnn6SRR2yPwsiLgwNQjJ3icBoDLhnudCuNaKfBMkGOfDDe78qnRFnG3B6e5e3vXyPhAJmssheKbsexopqqkQc+CxskK58fWIb4nSnSLWYPmqTLj2grAOlGnwRDMXI+GroqWLK/4p1JDJylpSX/zAxIChtviGh7yNDngY+e5WWBkjSzd+XzbtCJNp+La+nQdaFlPQ8HwuHZtVbrq6/+Mnf//pckmXnwKyEzzHsPj/fF3zhZoJESI30cEeSR3PscCo5YEDKG8+k1x1A6nY60Iq1KAiBH+PHI2QKVRYs8HnIN7Gf/etE1CDKpca4gv6qG8cxk5y3J0MJTE2FHK2yTsio2N16CpJBulxeTG+1RZaNkuPFFqmiwKr8aTXJpYWHhJp2ckPkei8c9cY8PT3Lcyn4HjlmqmQXGLMJ9SxgpWM6CY5pCEqOox+HbtwPhtfn51tzcztz9e/e+fMhwP7jysdgpZjIwMgOORawPPXHRK0olR4WR8PInCfKIJA9/Rq4PwBEkyRMtss+2mAilI2vzuVy4lUaHbMLT2mtwfO2MHLbI/jBvD4bPvn/WFT3PTBkyypjZnDWaZuU1a4DKW3kOHAxjsbWBbJwrhu51EyQGt8sFBYmPlHX5NUDPHRBnvNgALfmnuSWXHMcdkJDSs7y1jCb5XdaBCIw08irak9JHEa2Q3B0/ZrTD+7f3A7Nra63IHOr+/XsPMyQpKLJWMsVM8QNWMdPjEQdwLGKzxAJEPji2j+T+0RFSbi5jSPeoiT/Vx99bm2UmcEOAO4JmEzbWHCUbTDcw2nbfMPrDfz57kWJh4KjcsIhdi6aKoU0e1oAJp1tQtS1mM0AivLoXIN0wkizb7cEZPorfslkaTnc1qgCpamjAyajXvXDTjxucK5DAtwWSHs8WSMrKPnVWNutMbQEyjGjRSNQOOaIqJLm/DymRb8QuMkeSqA75FVe4Miu8dOoDSL4vfsgUStgvlbiVJ7H/4s4G94ZOi4SOBwJjDE1y1AhVbPyx5+HZALeyuXWQTCRqo0ZtVHsNlq/kDQ45Vu1u1z5+aXeTLCiJMLI1Yihb5Mjpg8aJXOcxuklXa4v9osoMmwBIhPLexm1aZ22CxFbT5MT5KFhy1gjZdcww14zf5efo5nZybCtOlLtbni3SpJJZifHp02+eEiT2kpPn4BiIhISRoZ2Q9LFVeU6UcJLxJkpB8qEg6XBEYX9EL4v/oZCCYg+/dpQcSZLcSAolKeTBAceMNFIKWbEdkLmcUHJnB3eINcJ8jU0QEs6tz7c294/YkRMk86ekePOiEKRFkCrZGV2QxEJGeafC7TbmMWJsKow02yNA4h7QNMQ2EuMImyfe5AiUTPYGOKJAfsnvckPKCd7fjG055fFIkFkKSZDf8PxpIxlYo4yJSqLitMjHfABl+PbXX9/eD4cFy8jczj2MnMx2BibK2sbuqOhcM+Homu+vSJbYJgXKA2D8QewiwfHUERLBbohuDI7PZ8XNlQDZ2uGN4kqthnhjGDX7lf6/bfvbbuqv3f4xmBIjGlnq/1SaQWgb+RXGTQ65jNZ0K41SYoLEgKF1FJUhVEHEYakO8aJQsiCL6BjZ4IRYK5cYyUQ2WLuwCAvjBY97kPcgCtV2KWQEHcs5NfggGFzILJFvOZlFhwh82IOwr/2+95+x05HtOLbkxD99733fe3/pJlKkDtMFKJ3zTazNEAmOfi6nhRj6bSVIhvEQLBskMZ0fHoZNkDMYhExJQlLbmI4A06xy4RGmy4e09F+uXb92CTIQpGDE+wMR5Bf+1gIcE0FZF4L9wZq1ZvGtPjU1O1uvF1V9w3UWFhaWie8KJC9foBv9DbkCTUKVZzRvklSF/f3V5AinkSZi4XlqSmXzqjlldElMAx21BSq0vBYwtu+jsjEu9rbbUtvUEvK4zIa3ZXqBJNuUoYAUR4fk8E3qEhEcVgOEbJT0bAgR8UeWPWLg8oiYDDgydmPuRjcASC3+2fVr1yeePnk6c6XIrKQfuA0wPhBF+uknscj4UVi/IskGafGqM87PslMmEilEoU9QLvscbfzO+ECOcxQs0ztJ/u2jjJeQ5jOJkuR4hdF3GvwrxXoxKS2STdJxarVyqVyr1Up+gPBYG+5919ra2+sdHZ1UV19xIAZMKHIFcUeXECQGU23zM6AURR7SZQ5VMA9pYRMoI2G8YyokP3JEQqKxH4pzE6NIE8Mid2rArqXj6c+uA+Qj3AjyBSbE7ORDFX0gyQcPGH/UXJNEYbM3ypzmr2FEkLzuI4ROAuQ0xsdUKnXPJ1laEJTLpQpB2oKxtFtCv9x4udEnzp1AlLI/Isvvf/2U4zNwlCer3iXGzKXZOLVyLX8HJGvr5dI6QbaG1pfDYetfe/vDd0fbOvMJfDUSCRvG9rttFXbk129XdaNq6GrohkQFIofrMMgdRtJxjVu3MKM6gg/KW5cEJCgPmfB5ccKJSRAwmDhBM31t4skjaPKJUiRIcj4ESylvJUjhCKcpqOQjGAuq4CxfkXjoFPok7oY5PC8ky2WQxPBYKS1XFEeU4VxHebeghCznLssb16jfHz375tO6/mivOw7kWEzW67S7pnRJx0GbrNXu4Ko1a+X1VsEGyS8tb9j6xy97+97JCXsk8skM9zRm7N2RWlPoIkhX3AKTuK9R2DrAEQY0COdIE2TEMDBqU5JcHbFNcsrh3dV+w+SaV1Ss85u4ZyQ08URJ0ucoOwvJkOD4UIVIcCwmFj8ZaYSjT9FF2THOzw5Q28mMgFy8u1gWkrgqpQovcOzg2uns7iiUsPaX/X5/jgj5BXx+fn4+Onv2jb8R+tixC4vg6FjNZJ370txvBuS4CI6AmQfGWj5/x8HTalORnrfWGo1aHve71ftVQJyZCS2FDf3kKIYItMIO2cZErfKLUI3dFleWSSaO7qjFATIOfUWIB1W9ApBhU1Zt9P2YSlB+JI0Jw9vy8Hg8MvHoiRT2q0CQXwhKVrc49oAcEwHI0lWHVIIER1cUCedGaaNJsrYZzoVkZQENQVDaNnLfx84uNLmjBp6XfZKU65xv5+Pzi/OL0YhoO3OlMsZBXFazmBzkCDJKUeYc4biID6jtO04+X8OgA5D/8bwffx6Ntk6Pjk7dNjc0L7QZbSYC7ZzEOJzIjpxnDVw+6qo+Y2LrIQFJiLhQ2iDDxAMZ0rO58sA7pUsFcrfOfBqTxETcGCnxFKTh2myRrzAlZpUiJxVIkaPkxwQ4XirSViTXpEPuK5KzABm9ApknyXWlyEKlAIp4px6Bcecymu9uXHIkxvFYgby4OO8/rz2v1RzH59jMDaDIaJZHIGyS+KK97rv3Iu9mK0Xu/Tw6e+O9e3d65JEk52EuHwDSjEBMxgqzI0ubZalW5KqsORPGBeQNLtFC0Bg3u9x2sGwjQtKAeNlIWeqr+HGS9fmdkBi9lp54dGXZk/+3iPztIKfaY7OYKibWCpVAkQrkml/ZllsHyOxUdACQmYwoEiDJUWIPDduuoLBtIbnrt8m3qpwDQY6B8nwMkAcHF/0ay/aOgCTHHDjW+T+CLLtNq9lc+2ktIyTlLq2Cx/jT+mU0GhV6pz2v9wEkaTdh1jYGbNktIpXHqEpyrPo9DhwjYc7XVCPe/60xGIYNeBTHcLUp532422AboA1VgVOqW8f9pLAlOUmO/Ap6nOQJw6Raj0flhCGXzNA+EpikE48XoSrwEJyFlq9IXF1RJB4YjU7jAZlbqd8p3y7NzYkKBSDPqzpI0HOXEMVyfIpkyIuCPBgdnIuROHlHyjiHus7yOAkYG9lct2tZaNC5JMTabOI/QMtuwbDts9FozyPHIc8cqEhudBEG9QgbnexkdVXd8/PEYJo8noGY0iJHwuS6Am4TUiBNOjdBRuQUB8mRm0p+nSS5OxKXQljCszHxlSrsqeiUOkTkNUBND3JJPulJbiR4SYnaBX9XfeXZrri2moByN29mRJGXHG3mR4zFH+EdHZXLA4oYcciQN76NL3g7Pjg4Jki85fNOqpmBxfAZ/vbbqUGXigRHPoXFpCU7PGvonUKOw+HezuiN3TvFrNjztrc91vZqdUWneiTOcJEGeGBZnV8Nz9NtwxKnCTHul3Yc6qQ+41qYK0z2SYMjD3Rn6nIExqNYeVIMOYsganYC/KgJKewpgowOsvwIjLLH5ZkC5Jh6HIC0S0Kxojj6IDFyDCYfKknicZk/JiRJLqCsO3KjX4Mj5mLbH3A4JG683djYVAB9jgrl8fHB+74oMp9v5slRMDayDfpNtwGQr4uYF1kJgzoSg8VDRG9rb+dstNc7xXwof1e1je7I9Rl+TWqI566MLn5MDHO4jose4dRi2Gn+jXUeT2sEJtkR8LjEkBwkOjToOoY648ZPwbcR4BF/Xj39+ilB8pUBg2jUN8ekOptxnBQHaFyP16Wyee5U8KcaJxAkRqFJ/7xxmsUNQQbz4dwlSGiyI3Pixq6c7gDl5l/HfxpfXpsXmxc8JDsYP/89OeZVXbM5NrIvGi8akGPX+pEMu90h/uh2i92BO+yBW290huRDhhTlh1PPdaur8+1t+XXBUYfdmrdjVBmrM4w+Z9JmtLgQ1CIKn6hSky8Snin1bZjyEKEnz0IYMTOstw3ZrZtcB9O2qUg5kPUp+sGxibpOsZUvwjnkAkhQrFT8jUVQ2cViHRO6dNeo0mQiRUEuX3EkyJ+E5JxYjSx8377dfAuQn1w/jHnOePbP4/5zkBSOLGxibExRkl1eaIqW1egOPbdb7xZdfMVFYdvvz94MPSQfzyPO3tDlsU2Vy1xUdsiUOQU2O78EeDN82QAaIXc8cfrM5yFF9IYKQCEBzFAUoi6Ztuk+LGZT2C2FRNMS1al4gvx8goIEyNmpWRYPeuM0g2MTenTA8N5dWdiSZMG2pUv6c7blSxId8qHk+KjE9+mbmVsCMthVYK5RGEWTymvkdHHjeBMk1Q16HG+CJF9DMO7/wQfpNAESTjNoDBqrDSH52trf7zYaXRSv2224luuCo7v1/rvR1tCTk0RcPW/oxtwYJhgudNHjxHiNGGbDUGRJ05b48gsUrGlqKj/KTlxL37hxg6LUQvJBnXBLUwRIU9qjmrxNbkLUq1dMejs6hO/aX6O2ZwezhChl3UxwaHbovkzWd8t31ynJSqUSzIhrDm6iSHbIh/5LCZQkb90rL5cCSVY40gQkmX6YxgNFoksGJDc3jzePf+BZ7fjPACkkUylkSEixAaMBPTbIrf3X/GRrHyU9dIfg6G551ui/370ZDk8+QIvelgLptnnasLIdY2VHpMlhvuMSXJtB2S4ZBg1Yjl+hSB7UBIlcTBxo/k5Lpy1TkpAgJLxEZcZ0EaIa0YE2Ymhp/NQJtULjJmwwTTFKd2Sulj3OXVKUY0JqEqUtlQ2SVkuRrGe5U88GL8qI5uDbFOT/2Da/kLbyLI4PfejLvS1dbqKFPiSNBKx3DGbEP4GwYGmmnQ5FhsZiUWRVSMuYVmtsyrZCY6ETHEN2tzUFU8q+bNe1YAMVOy918MHlYpfaVt9kH2Q3LFPwRejsvO73e84v2oH9XWO12IIfv+ec7znnZ/qskEyfpRf/m0FZrCnywY+12OYDNfLt8V3EtoBUSaLWnJYkKQwz+UylPFd+CKL96AQq1UerRIm36f+W9ooQ5NYqQW5sFPDmQZIo0HAsUblERZPCS1C+lIxuHWfUhd6ittTrGIOYJTwYMzYoqKEtUzXputko2nYKNigw6qo4pe47ghltpSqSdTu+qRi/FzHidHcMN1OPQ9eHWocgyQ6SvGlaxKW5pYdzIDm4ef7LfT0eY4Y9/XnH9fQIzfgI9Yhmm0byJyk44EiUqDM/jumVDCryLhe4j8mRVzE+tgFkJ8vN9woSGBHbjOfKu2lvsZLvrywiMz76eZsgF7LeD+/3pkqz0OHOGwFJlNVqQO6hJJMk4GOJxvvAKPvBlGVLQEJrlqnW4hWlUYzVC8kXMZk02vi3ChIHXBO2XCPyy+0N0TlrD35Ivpj22t8KSDYxwLhEjh18WnUgBpbMk93caYOkDtFkZwOOcptAOcroMtI+nB65yTsYJJl+zv0Ks6PMwp8aC8mSPcnYHhM9jj0Wqo//vb5+FyBBUkGiakcA8ltKMp+fePgMiVGIVvLwOjtc0XjZuff3AfLZMqz46htaIVHlghSbLJx3VDoTELQcd5QDRFTZQNRSyVkJrdq2DGhZergalBDnxJyzSfptNd74apBEbhQ3H9VqriDtCzVFcg4WiQy2c/PSQfXxHTheBUYoEqHd0dENlnfMJlaMZG6TFzQMR7r4Y2H49ztQoWCEHj+5QvnT06JYcrHi4MibBAjsu7oHpyJFom0GZI8qMrJJSbLS5Ctlr+LlpXZXvHfVne0NWO6FxfX7f98rzb9DQLNsP2OxqW4gS3LEA+OYtA1HhGXIBROA9IUQ01wWMhs20I8TpYAMCka5b+H4ggh+LrqZGlCjAD4hGx3Hr124LReufJbjix3ihFxQEqT67+HhJYMR+bF1SA8U2dF9HL1i9y0z/I/kwpvxzRN159WNx4+F8UQEZJoRzRFa+mxt2rgr4zJebRmZHNdlw5jcFKopcl0wjo0JyJr/QWe1yciGCicqrNoix0Wv8ujV8uo/V70b1eW39+/v7c3Pw/0gtlcZ2/JWQOH2VwPJZEY2MAQJnq5LaaH6sNDyBBuC0GQwwSkkOxwrZg6sugXmJC77MBm0SXQ32FrMKW4yxl9G7SOH9xUJklwWgOMS5TjcarYvBiNOR3s3Wx3oNpLLhcOb+sTrjpJj3Wb4mA6AYN0FI+X4tFj8gGeXHAWlXBFSkuQoN1xqoiRG/A1BdhJkOzgORsT8CL8JU7qnZ8vlV0BWKBRmAv+Yf02OH2YLG2LGEeDsElG4A57negPJJMuLOkeRpI99DnVmMdoR1wkEbAOnZxz9WEyPLyRJ0gJJwNvcillfJ9DtpKxEQyyRSsnAUtynLWkydri2/IKVjBOkkKQF5wCndciQ7CRJxHa7gAzzECU1CZB10lgegySp6XaAVJLPHxDeutHjLqfh+yDHJ9uAsq3tI1F+FJhjirGtTVNkcw/aqqXuwVxFQptqBEt+UJ32Nl7t7BSy/kL1SXFv7/X8+w/P0F8vL6siZxHXVdRtDsMz2UyC0JjnaJw5+hYpSaFmbCNYQfKypViMBzKqtOQuECqO9TW/isMJMk8xb4o/FYOKH80Rs0W89vtrsr6Snar0Ma13PtEjcmQnFXmcICOQYy6MJ3eRTzgcj6MtqovLZFdGRUaRaSZHqpEvXogs7paKD2ocxz+K9gQl3gnFfY5StOnIux9GKps1kBNlDxUnzzy5QUUGfG5grjRVev/Lf/5SrQrInWc7s5IfgTGQncGTlftOCVsHj9LcRa1a3tN6k7LJ2oe6Y9Xmu9Dki3rDUle0VKfDRt1qklstEtwvXb+0PcELAPklSZ6If5UbPMc63M37ZTgccB8ckSRAdktoQ4nhizRLILlJkmiL4gfLbZT2dLo3LRhVjebqPRc0JDk+/lE02XWqiyyJ8+CAo4Js5w5bqnZNkWVPK02mMs0c+cbJPnm+N7X+tvzEcwOQ5IbGdrVamcmynpvVTaLhcoMdIjkIKRSVYRidCyFK/ZBVtm0ngjoFUlHWv6gnSlvUTOSySeOHCc2aPv1ZBO0o/oEq8lo899tz587dWplb4chWtq6fYqQkwZGh3a4gI9RjhNmSgR6PXzsRrxOQnBMNc/4rZWZesmOpdGVq6tKlqSneQCtOjo+3aWgDGVB2da11rf2aY2OjuB+6SPWRCrI8zXcM8Xx1dXtjeSvjzPxrav7t4kTGCwR4ybSwzMGuChJWnXcEUqkbCVQUFFYfxzhRFFzXj+Zb5uLSUjc1pQZSqabLlnwuhTsozhyyDNYHfXaNI9savyM3CORyiyMm3nHwxfUC8uhX3/SdoxzBcUVuz7ERHDK7adEjQ7sFJI8blBcj4MjQpjjDdfG6EyLIk31EeUtuUCKwd3dLu9AhKf4Rj7CkJLXYtAHZmjyn1qhLKLOLzqfzVKOx4xfZaueVZH+l/G624lXKi9Rk+dH2RrXgj05c2Xv/w5NMMgtB8pcZPgEJktnMROZGCgXicgO/85BLGb500exEWbepKpu/z5DPULfBoAFpxfYzJesPp5GWZkU4SDHnMu+xdUzpxGK/4X3Tz353NP5NXx84ih57e1fYvaCrhqsWjiO1qt3S8gWOVBySJExWHcmS12qR3ddNkrDtaWCUkJ4iR8HI16WpEg15mwiS6tOzRpbm085G7bSpxzqZ/dRIltHSQJFwk2WYyILrZgnyr7xH725VoUkqUhwkOM7gVclkMk1NKMoJGXy7UQjT2XppYtLyJXnvmRXJ8zIpE9l2UCWpXbf4dg1ivwuQf5ZfKEH10TlI1AF1YgTIo/Ecvn1yhAxvEiOHZTwjegRkJzjWUB5v//y0oMQrzAco8YRPgiNJDlKSZ4sHcqxBlD/+AJJwPpPkRjlehWm8elVgKsbORuPGL+pUN68o+40VR5RTbo+WC251yysBJDcwo1UuCYlSBhlyUGlmMpk/oSSjNLMl8TtBGEP3pSX7ASS/pJNM+t2F7Azgp3QOGVRbfrB/oP+x6b5DvEKuW25YH+2+OfEAyCPfAST1CI4M5xXi2+DqFH8O3dznCIyNLZ0tckCyp11ECUGSIT4InwHGM7mT5Piwj7LsTT8VjCXF+KszVZyUgo3cSA1ebbzdyKNSlNNsBKkc7+UNx0WyxMub9ia8ndVCwd1evoIcmY36A4XRUQoT8bxgMC6gzmQ8L8UboQ0WOmtGJVOa3O0R4+IMDKQGkoFCAJLMDgzYtWJjEZ8Gtn5u0zyF9JKlDHM5QkOa4AVJG4Xmu0NHDn3WZziu9Oomn3p8fqBIE9qdnY0t+BYNSaCkKHlA8iQT5RmAxP/UB5aI8Fu9COvd0n5UHxx8VnowLkWGLGVi1tx8u/G24WlAss0Wjufv3TOK5ByyX+1kJZ+pbq8WRlcLxb35DwtJX5IzGT8XWwsS2Kg00FhTyqvC/jQkEinXsQMBbZmDJvH5QknA80GS/oFk1p9MEqQuccLHxcUAACAASURBVFSSOk7j7NxSwxj1myUNp5AiarbkFw6rIm8hp/HXV7iB7pVNPg851mKbOMGxBSiF4/GeL3o0vCPU40menAgSeiRIxPj1IhX5f/QokhxnQlxrW9MeRs7tZvNBC56eg20NOIom+/srVKXWb6a1rZ+3t1aXf3k9X1zwWSnHSXJnHQrJvWSwFN/TlMpkbGZI20UfwmG2z6eiCyKok8koQZJnKJDNUpFBnVHGpGrHYgJVx+WSEaXFljFkSAs3fiL/o+N8Q9s6rzAeTBAs965sXKk2ROY6V1/SqwYmG5IpxhQKwsLDpCXXdi4Wl0YJ164SKhzFMkpqhtTaIo4TzXFsiFlIv9hWW8cm0CwJTMSMFDNv6hZr/WI2CIYVBZJCPrSBfdpzzvte212WK9n5ZwL55TnnPOe853XU54MiCWRl5FSF6/SwlOS8AImHDgLFaPsMxx1ESRyJpIhuUCTHM9Lff+B9CLKfOb5/8uT0DSo0L/L/I0fBMZ+/RtlQFGkG2SMYHmrtaeUfPY60glQQMIvF+3glmORaJpfNWJN0//Dp2PrinAIH42qBtbk5xkgLVLSbbJpT4mZRKKbqGp+ksr7YKvr5/MpRHc2BSh0LNkmh9gbmSJFGkiZqLeIoh67e8GkDuXCakYuLJPh66NFHtca3B7aROQ7v4jgvQM7XaUGMFu3QkiQJIymyCSTxwAYdeJuyAlzTjUplBABJkUKT0xev7hSaVzjmrz4SxYU48sHrzsOZw+P4DpMs0vtfonITyLW1QocOb6PXVjf/8nh9/UdLU0xX0y8tXLrJIGnNIpO1XFN1VeTIUDTkBvyq6w8Y1BOKKqJaKFEG9zZDwDsEmz1Fuguk01q0sVEsXtDqhQhxDeWFFgbITGp+3u5Vae25QehxHDmS1+svDm/rkcawLMlyvVQaFZvIJVjp+pmDXGx6msTrcPPbTFEmhRNACRfVHz/ZHwdOVuRrIjsPCzT41q8HudKwIOlp7mlunmjmnxLHLqnHwsZajkCKmkMgN5D3blGFCFjp6ujM4ouXK2jiGOTCJQa5JkjSIpVram4oFFK4m9HFmIJLsh/6Clt8ksj3QYamuG2kAbhBM8kon+GQJedzHD8N2hXynyoPfRhktNHn8437iOO4T4CUGDspmDtpN6K8XB4giqO9eJdo2a5+lUgegiClIg8fk6kV2J8sL1cqlXh8GiTx0T89ffb/pMhRT5H5a7A8BwVFCmgyOxNiC2VCHMNuoFrLwG7fT5osXGGcKxuZDK826xZiUk9XfzeTX/yxqEVcN/D53JxQpE4gTXFx2LU0KDIGCcXUADczLXzS5aAChw26DavgE1Q5hCi3IoYeDvtbxGBX4fimAFda6MSRb3LzlQfxqxY0NHtJkT/H27dHHB94HIe9RZOyuNVGioQm86U8SF47iMjuaYJ2SJJHTvF/wLK8O11ehijjI9PxESiyfxrV5rWCRGwPiupM6VFMcMUDjryowhMf5thV2NhIFbquCKz729szKfcWLA0g+dWp7OQPX/a++NOCa2Rdzbic5SX8TFaANPkmu4bYDtlob2i+6K3ba2rEsoywzr/jBByHbhmj+OA305P+qI0X6g6TFM03t48Kz3nlSKhFCygMEqJEimxgkMMysudpaYxIluv1UYFRgBSL3fXOX7WyHAGy6UjbRwJjWTyz5SfDJMqRePxYfHp6ZP4VkKVtjvlrFyRDGcniXpnYMJt4OJFIJIoCZdcbqY1iKkUQf18opDLtR1M5uuavKm42i9SYvfuPz3ofv1xYS2f9mpUREKnSuFSA3CkTiGhMxirkIYVGPyEPA2ZhBwVmym+h3ji8DaRF9MmaJjobJaLxtFysWImZGoV0VNgjlHGl0bd37zihpB1yuXbHgqQP1mN9Vl5XpeAulXpZkgMz822kSGbZ0/bR2Z9yLBNJcARJKHLk7E9AlnZIogYNXLvQIyfgE3ygIPbUJ8Dw3xNLEwny34Jl1xtdEKQM81wm0577IAdfA1VlqxYNv6y7n325/tW9v29mXX8ky4WGyjYJkt5EExRjKo95CKRFQCJhgAxPhv0ASX2OAzvJHK0/1NJ0Mku4UJn4qJu3xFsUAZJ3AHnagb+rcS8eypI+oUiv0iBDSo71khfY24qkNFlPtja1Msam1qTkuCwuXzHKJ0KR09S637ia733V/QhBDnQe6mmWEAVHXvAAw4cTSwnSY4Jh0rNfCrKQAsijmVzuPTN2Oqa4elq1EXV+/Y9fri8+3bqruVrWEhdsstmhFBBOoc2eQnNow0lSv8whqXBwGmndMSZrBhcNFe4HNRyGUnMiejUtThNhw+lTI69WcWIluyOOFhTp2qNQpG+3IncekSLr4rYqYPYSyV5BEmmyk0KbULa2Jc8QyPKyJ0i+9UskK6jlBHI+/2pgS5AzZwhkM/XTlBnhdd7s+kXx+ApILq0wSVhGPNQRFlMFegFkR679aO5ozjQ/NJGuEK74t4T8mbV/ri8+++66Y2oU0VSt1y4/OA+KUzETENFq20G+OsOTHXHGBZOjG5Npi+/BWoZBIA2kSDSbDFLuqMkZEKTJowxx9MCHC2SgWrqjvp+xIunZs1uQXqmR96d3FJmXWXK+TQZ2q+C4/T06yuI+f/mbeJwncgB5duA1FEmRB1mR7zLI42x2ioklfhKeIvHDEtmdFEkyVTALfbn2TO6oa/4GrYrfVVQ+JIhkitfXx2ae3ptLOYEMmhmI8vLthYUHUyTHUDAUtG18VrUIekNb8XPjomh0iSucpjVyvHSDZheQJH4ZqNYA144yS5saHDqf7eYORyRasj/c7IAzgRSaHN9zcTi5LUpZtusS5KgkKRVZQmy3NQn705rEV28Hdtn7rgizHNxoliowmPP5V+J6QLC8+vEgH1tLkNwMriw9BEUiyGosSpIJYARKs5Ay+1iRqNinYzGe/lPKMgzn9qdji8//du+mo2c5KWbO//XOtwvnM3SoBZD0DiqWo9ohFJB0QI0GFb9e03W9VsVToys3tGNvQJqBgFarwSVCw6I4wyt27+vubugmBdKSWotsxsGTQHKSJE3CkNOgZ3i3JjuFIiXGUZkiwREkkyjZxJJAbhufnW+IMFuuxCsVocgTVG5oMu5RpIpFekStOQcrLjcpjr97/M2udwpF4siCvE9xXZSxvbRCICHJXK7DRKlx33NPx0IfxmiwSmvz/qxh3f7z178deAqSAR12MmW657//z7d3boYj5HtscIwGgzFHUWBqbPhEx7ZVNVBN+9Or9D1uatUaX42zULvRsfsjATCy+T8prfHGwL6GfQ1EUuz9MUmVZ5Ut3b69Xmg37IGtTiZPJCVG2jSZ90D2ihS5jRLl5gzpsQcmMrm7ZANlXYL8pkKPIDkvBZgnoHnOD/n8C2pszj16a/CCmN3io6vrk0LxIR4iyRRljhSKBEozlTE7+gAy94HZRyBPK1SEXS2StazbL7/+9Bkkee/65zr7nqGl7+8sAKQdgiJjdgixbaM827atIIa5vgTStUC4Wl2t1aqrVZ4cGRY3ObBLQ1CkbTuqUQ3biG5IEiAbxAIGqjhVdIXmkNFot2d/xlFsjh070pbkNCknPSBJILcFua1IBonOBu12KxTplezdgpydBcgbQpIjF0/UPZD5EqVaoUlENjg+Ghw8dJgPZRDYhU8KCYGR6ozIkfRpJbHygBRZSKVyfX0p8jXgaKLlI5Kw0pqWcYxLL8fGnj3f+m7r+RfX14aGzD7zSuL2A3wtgQwqABnkh7y44zeUKduvIiVCjLXN1erq5maN9ihp7A2tooI7ZIoonU6G2UM27vM02djdzSdiQpG/ZJDsx2n6c+DAsSOnOL535mbzZH+oO5TFxjNAJZRt8TQlxbzNK9nbz7InSDq7OTvjgRR+VHL8+NG5wXODJEkGiaa6o7D0UIb2fa/aSEWuUGTncsCTunUreyvVF2KQnPstTXOytS8ejy0+e/58a2vr6da9hdvFQkfMHCLrY1OCdGJBAtkYDAKRpTqOrTo0OLMmV/H8sLm5ullF2UauBUcFfwhR8rG3EwhbSouNZvu/XJxtSFtZHsZF2n6I2YWhyUbYljvaD9tGRau0sSMKhWbtDrVu2VtKqFxohCgqkbtJ2zVF2Ol+EOfGtXdqYWobUmiaNvYNMWKFDhOHwn5oNXbdbokNi4SSKthh94Pdr/s859y0ds+9ufEliPx4/m/n/M+x2cRqQoerYycP8kK1U+ES0xkAuWtHebmcRgNIkvSfl82h/Uf9fgGyJMdtmeQ4FYnBKaAmluSP7q3h+n9FilhzsfPi2YuX2knyPxQkxjeSY8931OMBgKwTNQ05EuS/PgVtMShHvMJ9Q6EhpIW4429DcQRmjAo6SS+q4916KrOcvosEqFB4Xii8Lm4UP7wI626wRN7jBUEtgLjt40ulH9RISMG7WrOS2cpwKi6zcpDHUEkdEqTDoUOYyCzhV9kMZOugIOkrO2yiGZUhyMVDvXaB445yqchjVVVnO9lS6m+SK9j+A/3td3pKehz+5CW/Gb+27m9oFHNAlU39d8TUxtpneqSPvAjjForkEvcdS49i46vA+NfvngHks95nFkjO8vyldeyBdJFdD0ruEWOeMB8PDSENB8cz7vhSAGWN27uPAVvMNqiqMbVcSN+9S5CF94WNbDGdziW6TAmSkvQFBEWfz4R/dKqaqauKahiqXR2MZla3tjII3Ls5eWFSkbKxHpi5nUmrEKYNH4n7iIui7KBxV3zp+gJffMF92jukHgHyN6eEcYvm3GZwbG7eLknxlrc0iYS82Vq4qWwESGHYnyty7ZMir3aeqz0cWe9hgQOODN9yORYQhY+M1J1mxL4sFPnjzx+dZEmQgDiPSw+JggaFYTwTDwzBsL2cE3QEHNUI2aMTc683NwFyA8b9vpAtbqTfvHkxZrpNn5dK3OM17Xt8pq5X2FV4QhWCVAzNcKo+E/lPZmtrdWVlpVplUBdtK74KiJZ5kKAupt0YbGwugkQm5Opg6IYYO450EOSucmuUnTpGkgDZsA1lv5Qk+QkfKRXZc+dAc3OztQTmb7cUeW+tdBgUOD5aKrlISrK29tvudpRJzMcZt6+tt/f3YhzotRQpDBsesnWEPlKSfPCJZNf8/OOwKAwDjNcn1uKhADh6HVw0sKuKszqcSM1tpjc3r13bfN8DUWaz2dybNx+6zIBQJED6vKa5Rx+sqVYN1WlAkE6nbqQ002dWK1ELZFQRIBFp2DjOghERh3klqyEw6/gFgjbeyLHjiONLnngIZdp2SYy270G67HeSpOwXb+bdwF0yUpLjH40bINfX+8mxef822773ieM2Qcpg03m4kxvhgwPt6zzip2f9zsAA+HGQowBpcZSm/eN2jow44cdd4ZGhEHwkzBs+Mt4SD6Fw5iGGCLIU2OTcZIEgx4dRd73feJ2dnv7wJr3xUNd1gGSshuMzfb5BwoIn0HQtBUEqpmlWqNGoCDYrgyuDXIRAeungRIh6UKOp70a2rwqQO5mTC/t2ITV3ucoFUB6MZoGUPvLUqVNcvqr0eDxClFzBpnH3SCkOj+fHh/MkCcOWQ5BsEJKUITsjbpTaSyWQ7FzpnOHepRmPONyP/eTBSDAYHOi1RrBu5ttfyWkdBhvLtJ/IsM3UJ8wnBNlCji3xIXeIu169gbgyOMiFZuegYkwkJ8mx5/6tK+PDmxsbr6enp/+Z3pxQDL3Cd3NkxLy5hxz3OFYWFR0eVdWNqKGrhmnqpr64ugiQq4s8XkpMqFXY2SkOig7Vzr03Die+PdIhM0nBkaMcl0iILI5CkcK0jxFkbWUlSfJq5JQEAs64jNmlCUlh2AcESaJswkd48A6PcLQOzaNdW61Y4AiGHnmiQNDf6x8YiERIMjLQG+Hu10hk5uofvpZ6BMgRy7Q/KpKTP2FcoZYLADn0VbzFjfhNjgG3s4ZVjRJV9dEkLfvft/50H//oRi53OweQbzbnkGDbzflk8uF8102ANH0ri5quKIahxUZThmFAsbpdXeWxk6urNciLxIGHUKSCqK3irrCz67m6Gm+wYdKCKlkuunaK/JzrXQuWHvGD721lVVKQIClQehpxcdqWmMTSVymJvAPnKZshhCjrGprxkdK5ouI4TFHViDkLYvRww/FpuaHO73/m/6MQJF/BSHckcmlm5tzfvxYciXLsyWemPUI9honyQgsjDa6WkHuISzHufV7loNeOxCelm8nkxst0z/1/vHtXKBSLudu3b7+azqXTWcPpDM8nMJLJF11jpqmloroenTVisWgKw4CN66aZQtBmmVitaQ4VaMGzxqntxnca8nEVEe2g3Ws/YiPGchsIgiYsWyqxZNY2ibKsSuixqr5qL0AKkpWimBailCjFdEW75HjUYglRNgX7zz8iyjUxfliSGAGyu5NdqR78NU4DC5ADA/7eYERyFCeczVw992eCPCMUCZJdJPmR48jIGC4I8sJXwkn29SHmxAOhODgGBtkzqkYVXU8mNn7avHLleR7xulh8lYUkf87m0huTKePh3FxiYjRRzCYehpH64NNGNBWNzmb4TFGTPo2ZZAYWDkEyRDsUpzpIw+Y6LbcR21U7MnlytFk65PsuUlwol3hLjzKB8aRAWSsQesRzL1AOtLPs7uGehPN+mnWpQUKQhHFbk+SPuN/qBynH48fPMmB7Oi1xnz7tqWsSx1sIkBzXg/JsAHI8Y5k2ZDkmTdsqbca6wHFE7wu9/RsUOdQX+H1fzVLIGwJH94WVGnZOzMY0PZlN/7Q5nO95ngDIbDaRfZV7Nf0qnV6emkgmJyZGJ+eW57LZZDiMSK2HUylwzD/NP52dVTTd9GkrWxkUNhkGHLhJh6YoGlfEnDXIJp3IyO3qbhRFNlAjrgXJcqFcUiy3lCpHWVUtOZ48ebKqfm+tmNmpEjM8e/ESW+HO9web4D33N1tr+hbJ/fuZMPm5ECshnjhx/AQ5nj3b2d3NFkBPXV1jI6y7rklsvAFCC+V1gOQWHYC8fKb14xjrsvLIJ2QIQY5ddrvfri2BJBcN3PHQvgA5Bg7yOEOHcyqm66OJlzeuDeffLRPkXDYxPU2SH15uPn8+2mVERyenpuYSiWJiXtfhIFOx1OzT/Lv8VCpqaMiANGVrFXpcRBK0GFVg4DU1didSH8WJJAh1kGJXHT7Xnp0L5fKSD2nUkqBQqHiW1dZKjhgw76r6+vq9GOC4t54shT4PV1Y2fOJ4SHRISJLd3ZeuWxhPHG9rawNH0T4NkKcJEk+xexuWbbnH65HrQQoSHH/JUFMybWpSUKQiSVEHx9a+tbWW+AXB0c26D0kkT/xAMFXVqZipTybTN67dv5JPZKUiEbRzOUjybmF5IhxOzaamJib4u7n5sGKoMSjy6bvnE7Bs+Ejd1NTMFkCuimyyhgRrKmjlKLLtKuKVYnfYXTtdO4UMBbAF3gsWxo8ohSLra+ur6k+ePCZI1oNevWBZWRryq0YL5KGjh0RLqOwdYxtvZ+dFGnRbW7ytpU00rdR20q5PVzZ6GkCSxt0E0w5akYYkpYP89W9RG7a2btfkCG26S6rxcqvZ2hpaWxoaCvWJhSwvyj6uvgQCuLnslTLDsdh/b/Tcul+gIIvFxHQyAUnmpnMvi6OLsXAqOjqL0ge/KyTmEWFis1PL+fxUbHQ2Sh+paVoUhg0nmeFxaSzF1f+xdb4hbeRpHJceeaNxkay6JadkYyawahr3tGv74qQozb64F5ZCWgldJkSplT3uZGyQghTc2kKHpHeGG2EbHU6sGDJBEOowFOdFUjiP65AznhExmxc9ORTBvmih9O19n9+MMfZuZhLiFAp+/D7P9/n9eSYY2HyNPGlHkuTJu+tsUOSFHEV3rtaiaVnM6UGfbRs1rV0+YhgOh02UXV2DFZBXrIR58RaB7LdAWhvmoUnaWH7D575zB7Xo9PTNCNv742Ot7923biGmuy9dAkgiyUBSfiSOz2+YHAnjozOOa0AJgs/oDaPlQF9fx/23f/3xR1OQ4EiCpNZWfnQU4zg5HovK0eX5ew+Kh7uHJMhdCHLrcP/fu1vbn5KqikBWJamgkSQBEiajG4ahFLJqPo8aKMjzQidA5tP5HRc9nzOI4LY38aHGTmKIMhJ1UICBvJCrz1n8cixXMoK2Ckvb3bs1PpBjHC2SuM7kWCmILn1ztf2MI2uFYcF9hUC63Tfd0zenb7oJZYS6nhh/tiGq+xJtp+wdmfrjFGsOnXr5/PnzlxG/99dfzAz1zVQgLvT1eSqfcECNHo+nY/Lt/Q7a4hggkAHafPIbAgkx2Xk5Jifl6OqnP//q6PjFC1j2LoFEaP+yv7+dWklm02kJggTIZU2ToELKj7ooiqWiigooRvHdhAyJkc3OeH4ny0AGXY12O4yHykqYN/81zMaMa8Yvd2rSFkmw/Lm2duPu3SUKbeJ4mbNQdhFIt3WyGr2HDR8tRVZAto+RJFHlIMlGpt04b0bMctTX29rLJtIvfdtNfUf40TcwcAUo6ZqaGhn5i9/7ry++n2EarDoWwNK84yGKOPom/04g+05BhjyjbY0IbGjSLsgxQZRj0a2HD8rr63uHu+BI19aL1/PbqdTyqqLKkqRoBHJZUlRF0XWjnBSVdPZB6T9AmUbp2ITkGN9BdGfzGOA00YYLqoI6aYkHQ5w2PmSZdu6s0rlQRdHS49ISQDKO3FOcRNJJgV2tR3PU2MMU+V01yParY5Yi/W73dT+Vo37GkblVK63bsj2prb2tA05ng9M3wjiOID/6f9sMjmtra54qjB7rDTdbcHpaGEpa4aeIDrB11UCAGtZJkXZ7VERku2JRaXbx3snJHiQJy8axvz//eD61vbUivUVo6weaKK0UjmbLhp7VS4qoiLK6WNTVeJqKcleJONJEeT4+3tkm4JZdgM8EadBt59uCoRabRS5Xy3wmxz5VJIkX4nqBQA4OOsMc97T5KSPpJKuBe1/Ey+djIEGxxwL53TmQTJE+n9/tv+71wq7YFl7nwACuASLJtlH2toJjA9fQ4ATKkZGXPr/f23zt+5mZNSA7r0iWJnELFPtaTFECHwNJH2g3OM0Wkh4x+Igmk7Icc71SiotzqTmgZCT31z+lnvztyZPU+qGkFCTJMDRR1DOZTFkvgKQiiWJaVopHuiojP8TGs2qc1hKzZDeuBP5ACTuMm2Z+hcYAD+F/xcBdqK2tiPKcJm0M5NLSZg0wEkfHU4eDA0ko0teKghIgfL3WnFDP1Z6r34ydgbRsm4pyFtngGB405ew0j4EuQtl6EWIcIDk2cBxjSSsLXPO1azOMI0B6+gKfs2wBS6BcoIUryooBmhELhGitPxRge+jJa4JBISZpoiyn9aPFn97Pzc29+/Dh+Hh9m3oT37x5P7e9vqUYomZoklRezByRIBVFKen6R12WDSOrugAyHYfVxHd2dkp513ini7cLGJcDJIbcwUZakgiZHC0Z5thZrcafbTbbBnHcrHECJCPJQZIcA9nlo8N9kdYgGMhhkIQiJ84i2+zP+tZMkf7B62EvpVioztngPIXpZBvMcIMe5cnhaCCYnMNBHCmwz4d2NUpgNA+SIltcQHr00LYJ+6gd+SsxilIlJi1Dkdny0eLD90Ry7mQulQJHmkD+6f329rFmFAoHmqQsZspwawNFTvZjMbOY0ZOKrsRRzvNxtaS60ioKoJ2mzlgQxbiQqAsBootWdxDfLbZKqVifO6t4KihttRtmZG/W4Nc3IxuCRHAjPn2DDCQ4miCHrdne9glLk/1ngrxCHP3Xr4fZXyNMAAkb4RwgmAPmDVOQDWH6xATZxwIbof2/KOlfFtYYSsAjl/GE2CcKdOrS4kcDdoFv46Mrq1Fe/WiUi/fepJ6kUicnJ6k3xJGtoqcAUi9oB5qmZ4qGruu00kUcH+plJYlMCasJ5tVSPJZGHZndQb3OmyFd19hE5k2zl6EWk2N9JTPmzhBasU2CXNpcqmngwtxlIongZiAHB6k30836M0cYSMaRJizY1whMWAkSHLuvsD4wZEgv2RX+JyfnJIzmZaoTb5YW2VfjNDuQIIdMPUKRnv+vyFNBMrs2kSY6QigiR4WAwOOyfxlbXcUIulRWlaOD1OPH86/X149PTuZOt3UArKgURO3goFwESVQ98Y/sAd16soAxokwVuZxXy+mgi2aA4i5aGaPJCqEOo0O+jV6NdV9VrIUef5+r8uvTN8qQpiLx61uKpCRJfQqDFkZqlJ0yO9/7h4fbhxHbINk/YU3/9HSbge32es3swKK3wWnFsAXTSU5DP1ovcATImSEPMA6tDVUPbJgeF+A2lCBhN8BHXVuhFmRLxHVHgJ+8P5oI1PEJnv+SX9VeCYl4KSsmS9o6gdzf39/bezdrduvd/tPxO0VWJO3DO6OYycwqBJKehjxraIpR1tMxISGk9YKR5tPk2mlSJGVega+zN6EOcjXRrowWE+JG/WdmXTlNq6EciYBjKIGRFOn1T08zRd6wQFJ3Z/8EoWyfGMY5MWxSZE2eNwikN8z0SIJmh9PSHzs5wORYuJtoHQRyCASt0wL5qKoEQlCvkXFb6ZFiOsRc5z5UIsC7Uf20Tca2liEqVVXFWF5aXkfJ88v+7tbhAfsCF4A8WNHKYlLH6NAoAqAhqTrSo2GgDjJQT+qikIhK77TCTlDOlvLjrDynBe/GoBCi9bE2+oaRjlCd6TL1tecpVh0MJBTZEG62ROlAcBPIiJtGJ3dujExRw7HZ2znRD4Tt7ZBl+9gYUWQcfb4IcYQcyfQdjKSTMwEydzkla0U6WY0lSLromBliGB9V15MoxBHR9o4O88kcdrOI9Iy67vM0+ZUQRhOd8su91eizoBIX4zE1/sPx6/nHkOTW7vFtyI8Uqa2KuiQXDpY1UmSmrCjlxY8G3svkPOWy/s9XK4d7y2KpMxbPZtM0gybQUAYwE3b6wRUcj/MhXgghhDfq2Ukc8bZhqwhyw0ajmoVNXhGjTwAAIABJREFUKLKZo5O7jBdQcF6/O0LNmT5wpAdmT9EzhydwQY0AeXVseIw9meolLRJGWNMX9EgQieU1siyLH0sV5NEOJkui2+xw/I6eEzT0aGboDOXnJPsCo6xfq4PtX64L1AUSyJMtHa5JIRrFiCOEyI5J/9h6JTyTs6KqptW8sEKS3H9xuHU8dztDrj0rrUpSclU/WFk2jjKL0KJeLCsS8iPqSRriGHrhZPtEiiE9ptP5vMsFSZLZ0F5yIlrXFkSutPOTk5MBeHO1JM8fp4psbnY0c384TZMcKTISoR7XEfYAd/q2mt//l6+zDWkrS+O4X/zSccJga2SqEPoSCmkRFgoLbWq+VG1m2YoQcEVJdcrqkjYdsqa2TkfWugnby72lhr3DQrKXFdZV7rVZCRhCMIwlxV1mrt3GVtPR5MOS7jQUbGkX2n4b9v8858a+LLvnJjYqRfLL/3m755zndHV9BZLwk5//ihoqUc+57m7iPTl5mjne8ICXx+O5gWcjU2wkgvwzeil+8Fmj/TPudd5pYfxtL5jSvd0pC2UHPWjHFi7KIPcyRyQ9MO2xsdBiXPPRggiff+Db9bVwKKSj0lMlddsXvg83WfrzkydL68h+Xr4cmVbjlHybqA8r5erC1RkoEQo1oMZczoCXHDEr89GvTd2hpNN851xpaoKbRDWDytChOPxNqHNifa19HWDb+m6IedeykfyQJFmRjTZEbDu/28ONbif1teAN7ATyIq3hpR57vCnx19QDiOSI3/YLjAB57hxLkSF6WJIIMIcFRDHwGg9gbLRzp3M+D6KzV1w8QHPKdcol9Gil4fvwwjJr5OSHhv80HJ6bTcpNBxtCNwferJYA0i/rmmYUcq/Sv0s+jUTyjwAyP3/9+nfzT6uGlMvArGczs5UXLyYWFqpIKguSaeRg2Si7R26Vd6LzI6aBSlHTFd2hK3KT8oUv5kcu3uQ7ijqnyTfc0Vpf39zagZhjGfb7/nFZSPKPrMhGGy7YJZn2cVLk0DHedC2OUdrtXmjtN/780jXiSGrsmTww2eY87TwOtd2wCYpUGzn5JjGh9FDG6On0dFITl0br8gClbQqi7KyhnBIcAy6SY8cpcX8CIBtcDVQd9lH2SPfHQ8nNVFLWHyqLa2+i0eIazR9oYcl8Vq6W57Kz69H1R/c3S/nEzsj8m9s5Uy3MzmUKc7OzmRd0zFC1XIAOt9MG3SEvVMzqrfn5rwtpnryRZYeioNKRFeXovXtHfT75oO5gb9lB7pDupO3K8YNIw6JkkDa8zcYgwQRKt50U2S0Eeekag/yLxRHjIjWluna+mzYcTtKAYR8nw/YECaP9nJNvEEORNZIoYTz4Cx4mabeRIukkgwA0yWeVDHa6+BAdfJkSbpJdo2DnGiab7uBvRpv8A3OplWwWri+Vz0cTm8mb4ZBPy2ZGyhMb1adzyTfRyFJqcymReLoU/TKsVlUpHldVaS45++zFyE4ll/uHUd64809UQjkDnjI3cn2kgrwcaVAshI8krYCor8nxUKGUUsaTSqiGVmSSewTI+g8i9vK7XvJvdZ22Tg9JJQhX6aZWUlZjClg2T+uLhq7c4p4mDH7BIIcYoxeR5jicgmeQrhvHnafbzvL9i/1I64+dPUckiRYJ0sPdkO3iC8MknHyETgCiDJAiXcgqRWXN98LJwPmbGNCOQZCptWw4OTv7tFjKryY2szflkN+hVUYmpmeqO5ns69XI1uZWPpF/vf44mdXKhXhcUtJaNjmXMf+9UzGMgjk9vb1dnTYNlTJJc2IC7lKKa3IYQcznoOIb6Y+s619Q2JH9fQ0NtFrDusUDgh9bHD9kybVNHXusRlvQ1mh3H3YySKDkVivCsi1FdlHUoakXAjl5EhRxud3uoM3TSSCD7p4D/WJK8ixVmQeOHXBSzCajxwdVw0i9fFtabLUxaBsETuIZmJrqhXEHaKPWIapmOiyMJMjhwNjw6FpqZTGb2nz+ulhMrCZSN2O+kF+PmxPTKPt2KuFZBrkeAeVv0lmtYGhx5Y4SDoezcSPztGIgUk+Xt8uvTFVVM2TgE9WJarVswrzDchj8dJp7gBabjlL1SPUh/nRfM5vznv+KM8vvvCCSZNqdQQJpd5+jRh9CkudFqOn6K20Eq3WCvExtaK4xyEnvSa8XHIP4AAaDNwaDQW+Ptcv4AJIiXHR3zcnBmjGyFgVGardko/htjXE6mogXikOTgXEXHfJmIeSUnHcdjQ7/K5W6vbiSer72Q7EYiSZWYJGjIV0pg+NMeacQXgPI+1uJSCm6+uUdVY9LspZGLNI0XY8Xno2Y5SoE+aqc1rR4Mi5R0KEsCKGnAAOnhQMOWvbsQ2buI20iL0fE7qC5LxKhUCJ9/fl7LMUTJOv4/BVgDFJLdickyeclXeHkx9ouIjCyMC9eqoGEHE+QHnERRm9PO23oZJbdQweYZFubk0DaRbgmg6bOqWAJoG8xclN+mP8Uo+wd5x1wFsNDImQTR58EMa6kNtfmUlulSDR/Oxb7KOzT0+WFmaszt55l5GQ0svVkKZJIrP5mAJUjLapQ/BqSGym9TScsTtPpnzMouuNaNhuOS7mCJKkiN6f5h7Tu4DVWMoDqTWTlsVYIsq/eIgnDfpdic+0FI0YKVGdhhFAYJDWUcg7tKpL72dciNzR54aIACTWSHluCQUbJHHlSu5vaMXByxE2B7IKkiDPU+6vFzZIETGY5Lk4SBEvWJC0nhVm7aPs/rckFSppAHA6Mjinxtc3vv98qplKbxVI0kl/pgCRlXcltIEk0Kxlt8TGDjEQRauR7r9JgpcmSkY6rlO+AFyrFmQXkkEamUFAlQ82pLMzyNAK6pBg6EiE4C+RBfp8C9xuixZWtrc0Us8X4+H2ErEXL3peX6+idtARJKUA4SQ1TqOeeIHlZbDvuejsuE8jz3ZPkHr1u/D9cxBEg29tpmzHtVzoj0syhtsk2ARIDGGsc3WzeNstRWhzH8e04k+zthRhPDLv2Htwnpg5pjCkPw8+Lxbul4l1ceehu7RRA+pFKvwKeQkaSBx5Hlh4hL4omboc1/c42WbUC45ZMEpxRMOgmGuqaTMa8BYvOxQ1DSjNh5JgIRWkFhg1FPnzo9yMhJ9NuPdTaTCSbdynu6vGXlpekULRMPrSuhRuj0dvjc1Rg207uAtltkezaPWeKYw45ySsMEqYNiieCwROC45kz7QLjlX66BEmSpJ1tm7yj+wE1/2px20W4AUHrlFD8YxsfDzBJjF7g+9nw3p9QCiRIjh0dnVopFvMAebdYSmD8EEPeIm8/1Lc3ZjbUpOZfJJBLq9HE63A4rmhGTqZEW0ZRiNoH1O7kjLKpZjD4qDYU3zlVRb1IMchMq6h35NA+KPIe8iDklY6xYVoNTcv4m5ub6//HqN2ZBEi8EwARvc3ahkDxk0/2c/fCbk6A3j9n6sJlAtldUySTbPEe8XqPtJ/5lG1bkPx9P3V6B0kGSZKkXvEP+POiy9Ij9fYN1mDit+MBi6SLVOkadYkdrqTLUdepgc3NEkRZZEFG1mKhUEx/dU+/s/HjjLQYDiW/W996tL6ayKdugqCsbesIM5qm5oy4YRaQ7xA5SZozyrQWu0wVTk4tUAyCkzSkgmlKIZrnpTkxn5/OW6Olfh19ZNrN9X94X5DiuUeQ3PNWkScIJHXr476Q+/czSNrZLg6GBcJvLohs8jIpsn+yx8te8gQ9vEeOnDzS/mn739uFJs8QyTPCSzqt0+PhI5mWnTFaggyO4yEU2TL6AEAhysAUSFJe3ity8hiV3qge4TSnsqliEShLERopWiqh0/TBxo9XDVmT1ZeJrW+j0VJp5SZMWpb1tKZrclwtSHgauZxqGHHYeGViYXqibBoSQTSRTYIjUqNcrlKpIDvXQn2xmD8Uo4NaxnwNfR/1kWnvusn65v+nyHHqyOXlrofUyIemCQDyp5Yia/uYvqLyhhR5/kp/z394O9/Qtq4zjDuUfMlCWlgW17WWkYXOjSldSZY/SHLAmIxk1B0OBqNUeI4zq8PuNhRdFittIOlkgpBMI3LHtit5CzQzsyaRme4iGwwS2jRTq2KyjV3bMoWK2m0HMfGY7W9mz/OeK8tpx7YPXc+RbtKQJuTH8/47573nINpwfIdmTY4NZ397ll0rk6JI+Mq7SpI3n7J85CF1HYQ1xDPyIHklR6d9xqksnIpUmmwSKTY1KR8pVCPuUYKMDhDkO2wVDRcKs5nt7f6CNmL8fj1ams4FSiU3QMbhIJnohFjcJJGa63pcRz2p5+/8gSuSiDbB4vKdO9zLAWLIsVh+/x/DQ94Rr40Lda4QV4E6PTaoUbnJXz4uyJ1sqLK7TZA/FoxHkLd8X8zxmRdU2wmbnwTiG9ZNaORogWy7YA17w9kGjDrheFZJ8i6PZLhMlC88RcNmoPkeZr3cZYAABavu2qVIyNRBy673q3ijKPo9/LFJHtyVPbh/ML1YgiAHQHL6AUzwG5lZguzvN0Nh43frgWwA4RwuEiCDoVAwOGQMGSCGUhHBREduHuTN8ly1CJIjl9L4NYtcEHr49tv3jfbOnogMLpXjyzSSPrLWIli7S4uPWfa+GoZsqlFOnmHz92UkgNyWlpu7rLeYFEoIshsgr71ypK2t7YIlSrjHPQ1POuoE4yQkOXn3vChSJHnTKXI8pMJ0PTNJPv0sachSFElBzlgxp6rJjsYuCjMCOwfIpl7fVw963FslCJKReVPzREYKs+FMZuNe/8ZkqBD8ZF1MPvveoDZkmgZA6tz5jutUYxzZoxYy8ndu3FguFlEjokosFosAuSyrankzXl5cXA0OuXpiLq/X5fJ62ClwjhHbJpqsCLEix9p9FVVaiqQgnj2CDPwaz8e+Iu8ZQZBPc0v79e7uvscGQw1AgmObo42ibIBh1wFkQx0lqRR5Figr0QYgDyiSPNKY9zj5xaq7uvywbD/jtp2KdFgYlSZ7G7/byDKnsampKspG78GDt7dKpWgOitx0QzSZWTOc2b7Xv20OhcL6q+tI06PR6WGvFjJNNgbBquEkTR0TGJGEl9+CdwQ3XS/CmFN6CiA/RgTSJ5aL+t/mPlw1Om0xWywC45Zu/U5hKIqsfdyy91UVaaGs4cmPR5g2AuIV7tKQ5ulTT++Q7K4K8rWfvMbkR0C2NTBaX7pwCSD3AORLjDaTECXkiK+kPzuKRMJzQBSpbqmtDrlvHrFuBkHbf9tfiTi9KBqB8k0qkwuVCDmRc43797+5WSoFcopjJLxUmKVhP7ERYhl4Y30gUIoGplMwYTMcMuLIt3UIEdMIappbS5bzb7EbTecAyDIlKSlkPJUPJkYBcrDHFov1uCBKcMTDZnO5zrlsxLjbuFt3SO5SJBLw5yX9vrJ7nD4tF07xnN0+OfKaLLtZIEKQr7TBthvamPVcePJCwx4MgHxJ2iSVi7wLlJdvTqKUdLKydmJWOIJRFWOXX2obCeV+S5T+A8gnuyz7frMxQpy9+IG7OJHNLEFuugcjrvbMUqFgLm3339sIA6R+a2ogWsoGtvQQQAaNIoJIkGEa5m0EWRSWy8iBJhhmdLb3PcrnH5aX88Op4sfL5bg7MbowtzoIPcZceLANNYIiERBtfO3JtsuyrZKxGrf3WiBffp7HPJ/AVDeuCFJpAr/CTW3lIq9e5cquFIjiIsGxQfR4qWEPJLmnTnU+T56/9tF5cZKXJ0WQTkrS+RTScMnAyYijo7HDYkk/aZ/x1VON9T5MatJvFYyYfPZGSNLrbYw8yJYGctMJDXr5KV+3Di9tP7G9sTESNn59ayqw9SFAGpo2aI6gnpko0jMi1ECZQ+NGsYzIwuKQJfadG/lHjx5ijCbS76XyxaHB9JqAxCBLL7NJr2JYidyfC9mtIk6LZM0Pnvn2KaszRS5cOfG6TNGktKt09119o+9k30lu2XQD8isK5AUgvESUl/bU1dURpOohR/Lz0V2CPHtZBOnkUe/EKamjxBi50bJDrjbA9KuIU0+W9T6n/TGQ+Hh78Ykg/QHIr9ymIjcH2wFyJGMKyH6ALJhBAblYEpAam8eLmHCPQS5IIH4XJ1LlfJwgCTa/XOZ4f3FlZeUDngHhTq+Nzq2OxRTJSIibs5JQVgzbtluQv9pFtdUybSVI9frcCXVdCMcV6Yp87rkzZ46xveLk1earzcd+1C1XNlw+coSRxiFLaQ4Hy0NGmWvn5aqgnXvVeEcLL4aU2+yenZmxUkixblTUCiVZgiSFSD3O2AnUcpQe9fWw2vEgjHbuj8C2A7nrMb4UEwoLSMSajUImIyCj09HAp8YDmLaOSIP0MG5KqIkb5AjhxbkhZgSHdRTnemr17cX5+YWFhZU1gEysrcytumNqcN3cG4l5Q52QZI8qrWt3MFrRprW6GkSQLz9/SjX4SH/PmZbDLdY4rB7VqR7/w/jvv6+XGAlTNEmSKmQj7NgRxn0iSmHo8ePbC4oegPR6Iu9ko7l/QpHekOYdQdQGyP57KG9M+Mhcbgr+cyikjcdNusZgnMNk7oNkB0WgTmOHIoeDw8Yw283nWuYF5Vo6kV5bm1tNCEaXFvLGYgzc3Ea07SVKmvfe2s+XNsq2pRn/69KPe0a1Sh1rqZFxGLOm+lOZu37t8+NizcXDFw/v/v/wK//2t+HZcgAcf4jZIdkiTwiQAWdpdzjtPqevYt7yzhdQesgR1ua9vZXN5dJae/vPvCgCzRGCfGIpHM98cmtgILc+lfvLOAK0WRgJaYgxunDUk0lADMJnolw0kkYyOXxfH04mEmsLCy0LKN9Bci2dTq+tpgUkopUXHBlvkA31YDKZZKVYRankWNtaqRP31UjmDYbHVB/Ff2D1xY2W+i6lSIWykQvkByQRcjicDruDmvT1CkNe8ExB8hw4eaWDtv3uexp3V1BSz8JH9vdvmBOZ/C1kkVPrU++m3bc1k7taQ4zZ4QmWgzogMgOPM/Qkk0kjlXS7xxIfrABjy28gytFROMr06mgM4Qb1Nv4eb3vIy/wHGPfa1EeRrBWCuxTZqhT59PHTfE2bGM80f2kgKcmOo0c7CBIhvEvOrWBy7nD4SNIumvT4fXz9ENPDXQCRpLaF0mZ60+1tRyU4WyhsEGQxX3j1ViBbmp6amtpMuNsJkhzD3FFIwSXmuWxBosEkx3hyPDE+PjYGTc7T1czPrSXwX/fvj8UGBzWoOaKF6CY7BSVY2gRkNQv67BoGQB4//iKbSHkqeHdz89UvB+QMsvKOn3f8sePojnX3Ssxx+ixN+nx++aibsn2dPjmYkKq8Hg0MRLObSU37Wnh2qbCkQGZQ2GRLi9EcSWphOMmR4Ei4OJFHkNFTCDXxiTxKRoSacQw3SLrH3WD3wQIwtswvEOTY8H1xkuNmMBIagmHHUOK4WNv0uGyRGF/+tlVycuvZyvU1kWTNcb4c193czXcWuv+vIKt/dMshdq7AsI+qRguQZMTxI9CQJERpkbQGMLZXQHY+yAYC0eifPh02+OI6lyz6t+MTxV9MBaazfy5Focmt63HWgTDoiQmT9WA5X06hijGS0KORJMlxqJIgxxIrC1Tkwmh6bGwwOZz+K0lqphYagZsEO/pIfqBU0WXFUX5mSW3f3poXlSAx+ppP9jW37PyzrfGFcbz4rccUeaCL7SpHLdumcVORdocaPjvmzuCSVvs3ZWGrM9R5nSBB8n7czGxs3LsniixO5aLZUqk0vzW1vr7OC7rLKWA0EblT5YcPuTCeShqkKAiFJkH+HX7yX6ydX0hbeRbHA5e+dkvBOttmcqFLA7tZZvtou92HGdk+DB0fMmJxEbcvRZh5CK4imQEfMhiWkKQTIe6wamLYXK5Ek4cLbW8CQorBlrpXEjFq/NOCoTWEiSGVrdIulD3f87sxdoedgWV+SZNrzMzDx+8553t+93d/t7TBFiidTqn14DhQRoYjWIIxjmvmqdhQzZ5OZ//RLkgKFyQacFYkKs9nAGle9YpVzS1F2s3h/JlQOnPxqPMEJPz5zdtCkb8he04NIJO8xCRH6DE0RMIcGRnpHhoZGgFHf3+3n3lGnmKGfDUe33+08po6RLd7e3v33pJ3kcaOlj9a9oSw9nliwCwzhQL1grpeUHAdPMSI0MYeLn1Nkp2lty/rJMmMWicnSfWGBBkIBBIyjH9vbzuV7bvp+jMT5AnKVpgTScvV5uXD4PjlCUhbQ4zNqN3283B0SxXLaZCf8gKqX7E1B0rOktevAyM4gqY5ukd4V0LAhCoTOs7ZLG5tlhdQar53v9veHXjqHdsBSCOf/Xq5Z56X9g0M6GQeMf9NTcy+rqqqkc1kkn2pvjQnyHSaKnc2+7L0tlR6S3U7m1SNZHD6cXCaCs6DFdkf6YaTnOYzYOlS1opIF36y+XLmzHeijrdbzMg2r1hognRG3ZIY7vj/QdJmP4wVc87/Alk8Afn5BSHJPxDGm7fv3PyCkqQIbihyRmhyRLwM8a3uZbnN3+2/jGfb5L+YZK1WePSa3Q+B9HoXcU5sJ5s30l9P9ITmQ4xyAav4dgGyrKuKahgG5JhJ89Zh6SBgUktTKq2vl9arm3lVzaYfBwEyggsW/f396OopSf7Rmi5pQSv3i0KTzcFHn7WfsXR0nL447kSR0Zjkbhw0KoRyj1w0MXHiTQz+gfE4UUNaH+AYucBmb9B/Z7eZH/MX9g5PyHZ+fuUckTSXSWL1zx2x2IIVOTMyMzMzMiKeGP7LfK97ua27Tfb76d8RkuRsrXbwiG3k9qNdDwQ55R07SmpHhqoPeHpCIPltA0sDRnfLermsqIqR1TSUa6THDDAGn9HL87pGILdqHk81SzY9GHxMIP3bgUTzauRea688+Ky0kb3L5xQpZ2LQwRnrmaa3bG+CZIxfnlJkTIo5KUUeSFLDbotGLZZc1BI1Bw6YdjRKrGy5nM2JI0qsdBy1OwkoQFKp4o/N11bZ7sSZoQvnmeTN299gueQdnjsTIJtDnnkiz+BOEwD5EDe7lx1tftkhT66OTc1OTNRqcyjasX8WQh6eQvOOaUmltk915d4rJtkzOloJhUYX9EJ5P59XU4ampGAhU2aCpPGMGhyNJLnp6fHkk5NkLnF1bnB4+0H3cCAxPMht4uBlf7q0oT3miV6RKq18Skx80FRkS5Bf/qWzpchY1GJz5iSpaI9L7s2GdJBziyHtHUjuPTt9x12M2uMx+sphTNqkqkxvJOSoPceJIWbblKS4HVHdsNP/sHIK5DkieVYskcR6tZtfYHnAV9iWhseTWzJ2dcQWmaxFKPKyLDtcLkfCIUeOx2YnZmdXKbbfSe7i7kJo2YtpoaUpNaXUqqrq0++xJkO4HqQ4WgDH6pZmqIqish2nlzRsJHYbqrMiCWT1eTJFHQ9JMjhOiuyn0p0YHO+nZjEijwepCeqj+n1XUDQJtgZAdrQue31PkTanxW6ClIhMI2emTSlHHxzY8XHDvifxLyUC6WyI41iUQbpjlkMBEt+Lns6RH128eO7KBbEMmjkC5Fk0MwTylgOPmReOFyZHh2vN4XgImKCYkB3+v896Jii8qwJkJcSR7V1aWlVUvXqs+nxqfgIkCWMsNh/aPSjnq7X7WxTdipESvQ1pkppCTavX6y/ruIhxc7/+PJklxqxI/1xgmJpQXoeK9+5gKbeRnYanbLeKZzPArU2QwkWyID8+nSNjUQrNBiAQMalxGLft7e3lKmBIvy2aeRA/R3NFgKSvVXJRSgYHThHa9v8JsuvilXMc3LiD79lvxHKqr7hqC0mSGm85hChJhq6VtTcE0iWkmZB9JEi4cp1Bxr5dpl6HBLl0rIbD1ZqCcwllTw/kSOZoPjRa1pUqpYJ9RdUMkyNVnKyhAWSWOCp5bV3TnidJkqk+JhmJYO5i2M9Nvd/vD2o7uVLQav3O2jRB1lMPAvnr9/eqOLE/UBaZXRJWTkjPjmLDsCgXgpOFaKK6F0m4mwDJYJ02/An42PljIC/+WYDE01zid8nkKP/SMQOADkQypURXwPFmZdt1uU1OtPmZ5IunXrKSU8c6Nzaj95bHqNIsLY1VdV9ErSqYcwwPeEiQMUR2WaGSXfW8qu2L0GZXnuzLGoqiKeR6spqCXUU0A9u8GKk00uQwDZAcZIqDg90ZArmRtjbHNeaH+2JYr1mvsSIJZMfH5h23OjpOcmTT/lRyTO/Qjmk0pLtY1GlDQB/moM09LkYCZFGk1QrY/zjIT7oudqFwnyeG5z89zwv+eGYcIB0Q5IwMjK41F3AG6GB7hWwkeSAsBA0kjonc1NRqGSC//9uoZxaC9K4qc5OZVN5AKclQmiQTNEquXFX0PClyefZIJQsENVJQJ4ljXlEUXclmVcQ89lpKQpJkjIJ/HR4ODgIlg8SlTJH8Rm4jedfkaAqRQBJHjm7OkR28swLvxNfZypHueDy+lyM7Y4LEp0Xhaiy2olShGM4B5MH7IMHwp0D+tkvENi68Od9cYoXTidf/xKH9ZIYD2vVm7Q2/uVz/XnHBSNJIuKjn0KcWF6fGZsuY+3G/7lmlH3CSNhP2TabyKvYOyvjEJTcDBb2wrxiGUp1dXTcM1eC4TpKjpMCGQnU1paq6TkTDYYDkP0MfgYQq/eQoSZf9ZLv2tzY26tPW3qYkzadQ5DUGSYrsMPczvHq6apP9YaN4AhJ4+MBGtsgNMtywNEFCik6bsyi5oz+pyE+6sDyYzCQvaMEaNazHarof+QUNlxiMcm0FMU4ku+W1lbW1hAqQ3olRSoHu3Vc4nz21OLVo9PlIf2TJ+6h9CetPPfPzZCXJQhoUv0o+rxG9bCqVzQIiPevEVw0XiOMCtZBzc3M++gMQ6D6cvSWO4gme/sF+Pb6xgSSJOSCC1ytotgugTUV2nOwLeUqRkJfN0gLJtaMhem8nV3B8yBpFvd7Er0UtrzhFvgTfQ379Aciuj7p4WeuFG+Z57xuXblyn8ftfAOQLX1jxJRLIkZQgKbhXXJQaoUgZc5ABOQXbyByl3SMv/PnJZF3yAAAgAElEQVTx+v2jTEZZKBDIJMVuyqfrJEnPvYKuapj/VvBGIAni+nqe06KRyhqqby6sFhYwX0lteYRITqbAsY8RkixJk/7I0Hhgbn+rREmytxcQ+cEMzQdaxKstjB98cFqRtma/J0AyvCIGusaixPoDJXelyPYHgV+puJtaLDaiOfyShPpDkL/Dcq0buF0qztjyskKsbCNFEsknkz5s6JFIcIZ0PHSsrT10YK89fwIc1wJkye+vTszHirvv3AOLALmjrce1TEot6NRtkz00SJHhqmfeU1WYIBGjTpspbu3s3L9/tI7qQq0OSXKuECaIhHFhYQ6zGZMRMCSWQpPTkYDc37/yQNmn5kYoEg8hzGaMkyKvmnfqw+ZyH37Y2eq1Y9H3QbILkoRlZHVW0PI5D2AZ2f444YL+Q9z5vaaxpnE8cP6A3Zuwh5CTLGWbm4UNlN6U9mrbm96cCwlCIPRciVdLCEjxRmhAL4bo0YJSGDWRzDAy/mAZ0I4SIVmDCfiDUdTjGbUBZWuYMIZGtgohlH2e99XE/qQLe3qGBKm/IJ9+3+fX+7zP0OwcFY2msk/8VehjkH8jiqR3VPwH3sL38Q3HnWPgqCgKL9IA6CX6HBFAzjqrTjrLnsUZfVa3NnJHwyOH3e4fSgoHmUtRlgUFXAmE3rI3wm8afUMeFAkOGTjiApfqLTAKfnsloSJIpaEJZI8MQUYOkKTFEiSNGfCTBpAQDFkOFjfE0har1H+VAmRRr67eYFwlD6DI8YUYl3+cmyhyARzNJBQybHMcGj94oNchdUANUs5YOhwMtgfkX4aZzmDAbS+RzzQGjQXMsAedGfguw4cgf5xgpKp8/OA+bu0Cxz8QkMBRlhlCEgRJ7gIAy7rkxKYAp7j+b/2N1eobZe35i9EQ3Ey2Lik9LO/wQBI44iPvFXybPoWCBC8jFCH4xqNhfiwTcVyPgNQV1ovFX2CYjGSamQjIkQGaaQsWN1xpS8oVhKT7YPHJFiu9rqcIRPpDZUlRXoOEZQ0cf7oGifXIm9I2BpHTNUqIKN9gHEQUCbYQ9XdI/NJ1BdNAvwAdFn4cs8ZTw02KSPVIWN4lILFx9TEV5ESRPVjcInB0rpPAfBZcTgnHsOMZzHbIasu2/I58fiQByJEi9XooOqHbRYcMzhhsg6D5NB7n9YGhgOeK53U80WT3Z1uqqvZ6Cqzshm7GPXDS2ZdMlgqZjNfi8uLaxv0IiwtFyVq2qsknKyti/ETaD9BZ3ATlRJbodGYmGL//Hjj+9MfpCvlUWWzhvar5gmFQI/EjXfY1tItvDJN3vPcF5Akwr7C8MU66rv7cvv2IYHz0+DYSxE6DZ/epIm9RkDwBCc7aub6I4bkoghbB0UBQ6RSr76whHcSV3/R1ZQTZUxoQxxRjQgFAQjxTLEM8I/d0iBxlnOkFL4IyVTVrx2EDLQ5AKgpYTc3ssTFskswESiaTmUIkKQaTADKFVaIxyI2VdXFlZStoSe3Hn9Nh3Kt0gRNFoiDnJyDvfAjyy2VaSAxrtOC93Sd5df/L5UnMyGs3FfLbd6kU7z5Aio8eTLpWiSDhl/WChhTZy6DjXichuRPs4xPTqph0Yu0a4sdaAkBuRt3tTD4HIBt9L+Z+crsMjlkoKprAg+Y0Po7hOLAU+C4vqRU71SOn9uoKpjm8LRpqo8fGPnLGi+NXRIZBL0OGTiPMdNCy5QxuBFxra64jCzZWTVCuEo40ZZwZ20e0kHNfD7IDmfe4JLm03eE620tffv/24PoDE0WOr2fP8Jde98c1tFvHLOYcXh4jIBFSxCrO1Cs9MZlMG3jDj/UDyF7dIy5hN0ZtbzO+nF3t9bsM+BqhXJDBGgoCpxT5YUPpAUhZVpCZ3FUQJGKEFc6p5EleKISsoXYmc4DtLALLsqWk6BRJ4JMWwFpgpSgoOo835vdSiiaTib03HMehOSla3CG3KJ6AnPs6kAuGKQtq+IqdHcOUyUWSn7uIJF9CRC4yODNKhAW9KFbRNjbBCzw3mQIRAIljPmzmBpeo2KLtstd8Eda6AxkzaDCRsgxA1YTE19XKsMfHMGtRQJYZUGQdQP6idoAkSBItJ8PInlAN259xHgsPOQ8LIINboMg4zzUanFKv93gGYqA9U1yDd0yBpCzvjQtBM8iQcgSQf/lKkB9a0IX/7QOf3/CmXnvn5ewizhQOAkawkajHCPyRFiAZYCKlaikU9Zi7fU3XoyFbOeLezOv9AQ8c416yp1AcVrJSD1b+qKKh/1Z4iQepFs+lkcPfApCqhJIk+bXgzRTKMsMy5X5fwDrFMYMgLaxQ7zT0hA5BinL+6tWro900blj8M7D6kSTJjgOAvDOeuIkVma8F+Vt1DpDF/XJndmd2FsKd4OLiLCzsUlmW91OplGXDMm+CYKXaDHncZbnvLthCIVuh3Db69L7OYntUuStDIihlHS3wz3ZHpXJh1kCOuIwhkzmXIFRKdFpZ9fycA1kSkHFvGYwxK8h9GYtrli3wNVuwxqVDrhF2hIFk5/Lq7OrsaJftds3sxyDpiaaZ68mlywjy7783SGojd/CeE7cITFFMeoWTk1gsFUu5ns/vBZlkCUCaZdnsidbehWztTDvq03UCkinDukbd2VuqVMlBpL4ZNZplBZfxMJFVf31dyVXASSWkmKT+AiTBvUMuiefjMYJnWMyz8cSx0xk8r3MJRy6sNw4fXl7Bdba71oX/p2uQ96ijmRwMmwJJBpr9viAXyNbX0x2yT4O3NdsKAkdkGDuLQXi8YdqzCEwJTKS70G57sKXPbS7YjPmKrmFnrixjUaflyPlbw5NKLudw+MCXeHBybKKC/no4ytkpyFi9Uyck46yX8Qo8X66FarW3TWYtHcRpaWKRgKwkDg1LBOTVqyNY3BnL6hRJinIa5A9oIuFafvjFXpPfXJHHhOPTW09n/4rjMavOZAT3o7BJJwZr24Ig49V30dM2HiJEkGat6950YAuLAKE3KEwa2XOOrF/aD+fzudx/3NbvrEZNayQSJKHJwmsAsg5pZB0WN6TacUgrGfBFISsWtL47jQsQVzYPkoygNMKVw+2HhOPS1dXR7hHf9U45m3tjA/kC2y1mfqAcCcjlTytyyfANQR6TPdjZ9VITb0iRYYJplyuFgjyLAciAKRCPO0OedrPQPj2t1UIhn6b58ggSz3wIijokm2D+ymspvHmRy41kG8pWb3BcIsG1cGcn22p11P212DnGQQqkPD3w9HIhRLaerAVF68ndTCETYYuS9Prq+joDf+OS04FpRd770/yLeXp0ZGYyK3t5bvnTSxtS7EPDNwOJF3B0VnG2XpOJY9JrIZ0lJydn6XTAxMbjTPRtEyDiTClbNKyp+Yucv6KhoVMqWOB1OPz2UV3VjcZ87udI12O1gjdqIMhOC+QKoWQL1/a+pHZ64JrixXIBfH2hFnr3rlYQIGYP6308jwNL4RW5zs4oR5PJ4sLTTKurf6Yre54eQyYg6SBXnPY8t/xpRZJ67TcCGSckj9er1WYzEmHJxgnkFgDy/PLy8iTtMgXjae9p820bFFnLdAuecE+7MObtYc3LrEnAEQyjPRzOJ9S67olu5n8ud80ha3QzrOuJRKKj4nkn0qcBWpS4BiQ/vFDU9G5XwPOKwXhx6MiBqy4U2gdbLheZMQUXwYkg97CtfExyYiBfkLOzM3SA+5jjJ0HWaEFi5v/ZmvZZkCx7fMwyOFg4492PrZH6NCry5ApAXp6ndl0Asl3wgKupnUbKZSOANFo37b5uZGttZPfjWFh/BbgpdQgyPRiq6x5ryIgzOsMgSTXrQJB2ewW49rSEytX5/VFY9rLBdJxdi8vDXM6uFzKZpGUjAPG/iU7sQp67u6a9f22skHusjS0kULxW5BySHHN8T5EL2JuCGzWHg46BloCmjCV5jb6BNqpMuaRJ48rUl0x1u0y/far75b9knd9rGmsax4XSm20D5+bQpTSTZS+86UX/h57r3kgQAlLYC8nNwiEcL2ShLC4OB5t6GrtKwV+Iug5JnFNkp6gYsChanExWh2iMjQoaomdyVBw5NVAOh32e951RQ9OLjDpjyWee532e532+8770dN5fc7lI2sfnpdRVUpvrB5DI8UujGw15Len20d7wMy6QcpB2cIOfzHf2fK+PvW5eDgTIbDm33W9WqwoCFJUm7nYDJsmJnByLtQQNJHZzUwNIiVqN/G+lv7tcoZAtlE2n/6OySu3oPZgjQlz+RJFj7hGJNR6dJHHst4Sk4SEuT/yEuvaqRUINjfITqsZHnkyv2Vy6eDjMoD6FaOuNJjiVWZaA9EqT/iX4CaOrXXAqaHE6vGsyrF4Kru3FzkC3m+/m5/JNKuO2kS6zBvLLpGzz8t72wXH78+ejT0fen1XfyHFo33MMj0K2OarIC4WbADfuD6poqRGzWlEGigN8WxVFkRMEAhIbZ0B8DklRAAJP6rdSJYFPfYZc/b4PQB55/+UJ4ip8KxzBrXNWD43Z9xcGiX6NKO++NXzzUMd4yyJN4Sl2tscMzvREwgZt9nvKLPx9SLQqOOHbq8Op9ZgOmcH5IPs0jFPBeBiZmUzFiKZ2wV7YkJ6OHbRID742EtNL9e+wGdrtTlBHMpdZ9ibp9thugyx7/d62P9SOfIIM80Dh+iNzxG7mXtR2wSDPRr5WS5CF2aBabd0Avz0HB9b90+Ghw6GqJQApCBwZIyEm3cA5kBNB6IZxM86DSWKZyJVYJeTZWTK8a32QewS/ESM+n7hFaeqlIcl93hKLfPjkKW7S8PRW1MamVh17MAjSHiZTt/iaTjvix7TxXTcQQQui1PR/ZIqtTmbN8EswNxsbF2qXmLFnpxqXGXbI4FOiQdBuwnf/5i3JPOHYgPgqcnm3x437XyxAdoLpeK0dsnk/bW68ctWUm7SiHt5xcMfH//uZS6U4X2r8ulqdKdVGK6CCRTrEeTxRNYNFqqrIckJTkDknDe0aSAhLAUiTsn58Gmc8q5T+4Q4uMeZwNT60xlzQhiqgjQ0i48VGDbVHq/ZEPHXtdW2zCx2k3qYZYt+FNPzH+BqbhUViPYhoFi5GtM97OOFIJ8Bp8xXPjJGuY7iI1xtQ7TIl9wG+sxnuRTQVwTQcHupNCwD57iPkdxOUkTQEGQq0vHvHgyjdJGpD3C4H0+laO5vlXRun37tqgpJ+o5oP1UC/XVMqeemyMpiO0wCydSEUfPYIeHQlkahuQ/wWVbHEyk00SWcAix4ZQMYCTqHZglDvzINBHm2P+9WXQVswt7THHFnaMBdEITSuBoQbAW5pLdgH2loXYJXPaLAhgXv96W2Q4zAq9sLEIg3Y/GcMPf1vBpARRmu64sjHEDWQDnIYBmcu4kX2sMlILjKR33UGbXNoNNBGLe3Z6l1zBPm3j/5MPp6aTHB3H67ESVBfB5FkJokkJ11w7fTREEFC3bPvbQ6q/1QdKlsYtV2KkpVYGTeR7Y+EHqSKv9gjKuSYcylOUkoRQQoxMEkZdUIluTloNmXMOJ3iJZuyhT5sjwcJ947NnQF/jiJEYou4MM0O1Py449rO/c0NapHa+EgwruSRFOXTJ0vXHmIndVY0UtdGBQsZ47R+AQFpQDvtGU097CPc0UAa0Bjt9XHRSFS/dag+yEUwTKIL661dInWhKoLbIF2uTgf1dikY60RunrSAYwNJWyYL/p7MlDPpdPs4m01kd08/7PvT1TmrOi6dFbHvqg3yc04ZVwd9h084ayWSbyKHaIeVVFxxmFW2REEqUHUTkE6lSUC2WgEAeeM6OO43Uvlspty9it7FsTEa7UAabs3d3Xq+++3+q5NTMMb7m48hZD/QSmw6PFKLJHuukOJmfTUhNzEzEl0gUOggI/hjn30FEhw4MoXQpIM0NXHEBC8m9JE/gCJ3JmZc7ZETkMXbIN99PDjmo1DVlrvnuHqFICWz2KX3uHexH2VzR/OD/jSdsUiS7f0fnz4d15SS6Lj0+dRKul9tCL5+PzUYjUatViJrmcMIKUKdqAxaBGSpJMoyVjgQxpBkZaQMBGdBuCiIMHzWjvqps4vW5Br+5zJZ7f6aVIZl9+YuKuGg2DrZ2fJsPt7ShHwP9PWp1vD5TmKRdGuq9fUViwwzkJg09TEwTCRmDL7J6MFGB4miNEh2dNeGnAafYIC7EDPQi8KYyeOpY1RraGIhorD82iLf/Rg68JajwWA5eXWOC/zM5xKk5bvuoGdnE4iWo/lqPy1Zsnwiuw8lXQRybohJ5sMXIgfDogDOWcWNbQZVPpuck80GHCKA9JlFgCeKl5iH47pfCFJFkGCkQoGF0qjv75wHChfnV1fnFx1rtNy5/v2LEYaTxD7q3/ZJv2MDQH7/F00aSeL1Gi5R9YxYJG4CRC0STPKlPkZO70SKRqrd0dVlM0jIZ1poXgEZRvUPdlvrVN8yw9hD296Li0w4Jg5JNxJvCQwYQ7Tlry2S/9EatLmtwWD0GkBeEMnZPINRNJcjWXFZGkhS3mKR4vzOif0PQGmGAeD1oVkNXBQuBggyAdFlEN/npQqQA5DqaCBwDvBreMkRkBi1ESSQvGHl0UhmRe7Nu9x1gQ0AyO65kCQcsZjqNVz7j/FZkVevTk9PTj33nj++t2KQaxTlGuSRdIcv6trwbyXY1GczInUk6Q9qcOvTup6prIA0YZKESacebOyQOc6IJGhxEZHwErVLE5FGpphIGb4GaZjztC4LljNdQhJsh51HwdMgD/kT/Cpn01IejDQRT4Rsn+2/gk2aX6e39xyVArZjfNuoPJs0Grw/IWO5iBbJKQWniHGakqRT53IJGfsqrLPZFJzif91WazfABorn3eurQj6KExWIsRHnd8G1cQemV+9PTne2dr7VQGoPfiFKfLDTAPD+vIg26y8XY2STysB7dIw06XKUpmHVtUnYxcQQM0c7abeC80bomSRVp4dLtQvkUDNyMA0bvnZtpje3WJEkAamTdCajNKeL4vSBq5aUsplENeXPuOy/2iN74NcvDn03BXzyi/Ph9rEAMlWFMCIHcDMRURQKTow0BCSHILmRLAcuVZJbslCN30gWyHkmTjZwdtUpXxek8nV38gV3x0GOmyjewk1GTk42H93bvKdTfAaj4xo+AL/29hlaJBqitmXaEiTUeTGUn0DW2IvFsLBjekMoZLRqjumhogXGwliYqFNiDB5SYzXRK4nOgqEallW1i8FYbM6acIMY/fLYYp6OuRAkbBUGrQCy2706Q5IiO+/QDDmYyXTK2VrC4rfkwYV5Hp/ojLzAIPgLnlkARABq0Gi0zgLOuTQvXMicTxRloouGHBxcfTSCWDOaCQBZxjFUZCszReKzkDtesWzhvBu1dgrz60kDcrBEnEe9LpDE9TzBs0/++mjr+XOyNsMDbZ1T9Otna3eJRdJknKTlS5Cky0rarLT1CvZXh8jDLPuruiCFnEkPFwoXrUG7ODQt1S5a/3b5JYblZAiAjL/74ZE16KYgz8/Ozgrw53WjQWKUwWCm00nU/BZbtlqVeN71/sPeoRknytstXDONyE2hoAbrLAgJPg4ePBpx8F6JuDZ7Kf6fuPMLaWPL47ioFW5b9+VWCv2jvT7clz4UH20f+7YQH6QIQrHsQ3pZH7aIodiH+xCZbLBxbhuwL8mkV5KQYDIhDDvZJvgw18ma0hCvd+ydSWZDhmqZSAYNm0t3BqQs+/udSax6u932oXTGP1E06Cffc35/zu/8TvzJXpyS4JXkJcl60ULvkpK5aMgFLxW37qlW2AJtiKYmywdNIRUAjCEfFlkEFlZWXmY2hi6BJC/Z27RPO073A8Z+R7/DQYwNImyTPALyXflJ+xMWmO2Wx08WpHS+OJpkO164Mvi7PaInnvndbwLIzec/3mX8PqZmtEFWgx5KZAu1sPMSWBw6W8glAikGrQ2Ybhfzl/gPQHJ5brchYo8q0u8LO3up9Wig4W7FG2BL4lTRBokpoLgEgWIZs5NVi8f2DXG1UspmC+Gwvu5RdLYAQ9sCjgdNFmssbpEictz8PQSe5L3R0Su3ziBGR/tEEfB9CMquy5c72Z/jinxPUUD5SB3UZ1r8Evln96/fmPb7cbZHD6iKQ5aiRLPCIkknDYOb/mWJvp2KYe+4HM1VrdYP/wZRPo5jSgchEpqiZD1DY95o1C2eIu0uICoEdQJI4FjGNC+vgkF63Xpi6lqtUKAR5Ft4etay5DyGUakU7fL5pm4NAMhAYOXqxsbLM6OTX58jXQOIIk+3JXmqrciPAYmazH/u1C7Px368cWPWP8kU2iCRJG7XFBUWh3YBpsnss1iYHPkMcxhTUqz1N66N/8zNJVvAz4aJSTIq/mRiOdl6gdVYEoAEs0JJEgoWBFlGTarbMB/EYbwXg5ZpCgUEqTRv0zVTkrcxsC+FaNeMb2pmeGggtLJy9SpI8tz5K+dGTjuIIG1F4gAHmF2XD5ORJ4f2e0h+9hWHvFy6f+P+rP+Sn66RHcBVvCrEgFeFGs2EszDmhexCSiiVcqlSjM7q1rrHy4QW/5lMul/jrhHKTtsGPcUJgItptLqEdoZCkHEME8sQHO7tlbcVRVVM26csgi7NIvw6n2MKphTZzucPtFhuZsaFJ6PiyvDVFYgSN+6fnzw7fL673+bYDQ+QIpjtDkib47UvXSCgcKX07PX7swxDZ1mcJQGjCKZU04RKVTRrhRpr1CAYj8XYElZDRnOMZnnW/5aFqCf2nRu8mSAyxHcYtY/nku4ndW5T5T0wS1LAkUiSj9QB5R6PHHXNpNoo0Xtvxc1YrqYHG6qSP2jGMDuPYaFvABzye4uLSxsrk5Nnhs/2dY6J7ickcZbsOkyOkwdfCOSh0jkAeXF2doq5xNBNnThAOLrhEcizKlk6wDVg0Av1ErfJlaLRlDNrietvDDaXEywPJniooGjDpF4ne5bdrcYmZnNhdgSZAkhwxtVIHSSpVtCU6bqu2IHOa7TgcQXcHkEP8mUeQdIulw8PjL81MLD4MrMId8bPTA6PdHdOfQeU/bYojw3ta1+q0uKpXYvWdZMroSJn74JZCTdxRMO7gv8v4gOSIv7nuDLLbQocx8H4prNVhfKYusByIuZr1ztLMpSnuNyTbBXjvAiuDo/DFjhiVANzYzkiY88fvHTdJLt0UJFgwWVOb+oiH1EjMpdyuUIukhcfAE1mMgkgOUPTt4Yda/aZ730dlv22IsfImvaXA3lzIfHz1sWtNJbLP0zPYq+feT+TVbex2YRNUxDYpqZVgyJ8T8GhXm/qnNxkozlDqYhAzyLZIowosVEDfC1Rxbk5CLFBoSJE2EX4bEm4PCapCElGiDcRJrwqVVEiIFvJ73fA8TkAawPBUYwUmdJAkpnCvMVC4qfFRI4VQsOOvrW+9kWGdxvkGKK8YFcI3PxgaV7H9/vEldn3/PSxbw26fIlXN/6wlX74UEinZx9cnJ72PrgLbogkVknzMo2MbcPQYJgr6BPpWnRTk3UQZUmrVFQII4MUlpR78BEq0trcw6WG1jqCBEHC4AYfHfMV4LArFV2Wid7x0sA9sOLBN/H19dbj5X1MVSiUHI02ASRu+/L7gaXv6spCYCHxKhFrcjGfA8Voc4S7H0Vpg8Synzv/FyTpk0IqRse//fZTQL7np4/XnTJOVygTSHu3ttJbs9cfPJj2eqcfeEssa5oWeCl51CS4ejUY3QqIqIp46xqSlDnctW55RLJejfkxCjeBUWb0t4Z7bgJBinjSH1zko0hJvKy3ZV4hd42mjf2WSd9+s069aGCRykHespoxsGQ+l7+91DE1tJhZWFjJ/LQUjS6FTnWjFHvhJii7+/tskGPX7ly4Q2h+COT4NoTXuG0EHmGQ/PGC3N4e/10pdPkYSAbMYyjwc3rrjxevX7ebHnrncQI0aoUsKzQ5+NcF1KQOCG+ia6koYIrw/GLAwulmpWKHNR4soKoGKS6603i0jI3nECzPR+BWYeYTPZbebILCESO5NPAPzGSLZZh/QIQIFOF+2xTNVAxQAkIbpH9qBRvUZTJLicSzkD099vb1Hg5wBDmGcySwxGO2/zfIdkqWbJex818f3yjkcIXx8Fv77c2hbZDOU8yM0+VKBJ7/aesiaZHvnZ6eF0wvq7EFO32mHRhZMDiGBiICkkEwO5xewYIyXQcwuu4BX7AIUTUIs0oFY9H6L4+SbsxVYFUF2A58i1SDwJHTCEi83sJsy8rK3vfRVMhvisqBZiBHo9CUuJSgctlsB+SMj3SexCaKiaFRR3dfby+CJCj74a1rzJ4j8b5zYexDIMmubdJRAddRPwHk/rtlwk60GZn7NX+kx8Xq2uoqSUPOuLzPn6e989PzcHlNgdXeGqTkIVw7CK9iDY6hoyQrSFKFeU5WZRXsrKFZRXdybqKIC4KURVmx6LOdRxOtOAm9JR7sC48g1QqrCYKGCRH8YBhZlpPjL5oCTTsLMP3qRgF0XyuEaxWJkyWTJVMkjT1OXdhXLbCUebWRGRoZGTk76uj9qvdQkn221SYXnkh84UTJih3MjNt9ViLlp+PHFHlYtPKumUq7OOVYIDRYjhz7Gcz+DB4tzweQa2urTjulS7vSgfS8d94/P38bZknNoOmwc9VJwxxpGHZKKF8xKiSPi86RqmJTUrH1GJeVAGSx6H5StGL1nZ3v3JjqCUpBUCQKstyQtRoWrbIEIi6yFQSruueOstlTq87aAQi0xoTD+JfUKjxfjU9EyS54mpn0+3NLsRTppJh5Ofz1vb+fO3tltPur3kOUoMhv2ixPgMRqk/EubKeClSUYZmNW8gjIwa7Dqha7xwppvTLYrkzpNFexC1UHO189xefaJte7PXqoyLW1U3ZtCBNm6IW0fQSY1+XNYm4cFxoKWCSAPnRe0dGnpDxgcrAfF3hDpqeVxGVON4xr93LPXDLejO7su917DSxCg7dyRFUbjRyNkTrN0GC3avCs4ZpOUYpcyuLzr4bxdQqfxxMknU7jQOMUy/19U5dZ9AFYiZ8AACAASURBVH/8dIo0H8Bp8uW5syMjf4Z4e9RBBvdfbUV+c3nsmi3IY3Pk+G+4nWsfF1j+1fNrebknnz85Rw7uL5OqFqyo2B0fz8/heN/t2S3bC4X29u2u9mZu8gE33e7iw3aTkfEjijxtaxIvZ/h2YN7/X86uL6StLI1LzB2Tm9uHYsqFIbW3DvRhOlB8WbgPfdkwj/YhiBAQ+5S+DmFlN8yDi8XJMNi7O1lmQeo1mJtiKY0MkW4bzbLhGnpxRBB3NEZCUiokbkO11aGWurbs7zsnN0n/MewcSSLXm3s9v/v7/p3zne9cvk61MMOQ7Eayg0ExI0V19XKlWFj6BmqSymhCzoHjzN27kbsr46WnlBzT+Zfq/trO2N9pwhWvJ0naV3ZNo3FOy9J9WtkAcj5BS48/fLmvCYhTzKxI2xsatPczpAOapJIpVn+6e3gc39eBoz5Ea+YX2LjkHUmRPEq/Y9LR389UJUHJGMlFm3aQs4Fkio2nsLJpRPyWf9fYsKlvShZmU2VxsimHpEOfxzsbS+I3+KXagaSZsmSEV8uwl98SkPTvE4yGBRx1Q/tHWI9dD1+TvtQWygab9iLWlEElkknK/SwuTRXYWMa9pYcrg4MHB2Mzg+NLL4mZnTO3j9JrTw+ePnlSe1KrHW5tbiZrKS0IrHB12adZuiAE9bntpYc/DeHeDqcJAAUB/wOag4C0Tk6sTHrzr98nC8dUdk6jJcpzkO0739044/Eoqnw6ithmsv+Thnh3XAGOX1yxmw0kwRBJxpMRDiR4dxh/B0iekEIJJ4eEEqu3ssvTKlimy1az2sA7QAZIyptFHWzR1rNZwEj7sNImyzpLWrp27cvL+tAc0Yey6kIQb8uAVGbKIBaQXKLxc/iOK9+zAruDt5eWbs/cHTwYG1wvbSefPt3Zqq2tPXiyU6vVVjVthE36GCGHigBUEMJHcNO/1rOMgVlBFbPgJWtZauWqpedONvOF/HFZs7SFXI5VFZkGkBeDikeRZYcjeqqBJDhJjLzSapfsWUQGQwefimVTp4F33Z8LrOQCW/VKeShJqssS6dmiL7Av79r5qe8B2dFW1KEBpMAkWmdTiDT1RbjhE6J9Xf9xCP3iiZ4GjWTDsYRZNTTiJHmO4+Dj+hSN3yyVSuuU4fPne3AztyHWh4CwtnO4k8toYc2gZwAgTVnOZs2R2vrLhYWQAK3iNI2RO9MhEuwoGb25FN0Kr0yxcLL9uGKU61RnCUgusM3YvjojQ7bhAiGkcTAkGSOb7Ty42QSSO3qBBpCR+Pt+ZA8XXT6fuNG597hzd5dqVG2wVe+7NmQfApIdahts94dEEmsigsDogC6zbdR1LXb9sq4x/UhLhmAeWCIye5WBJCU7To2NTZWWgN9UqVDKl3CsVCzAVV9bq20RkLVbC5oWDrE5f1zDyoaHBXNu78GPIVGQBdLOohCbGNbJAJl073odJ0J7GOXNanErXTfqVGYpR5y8OT0xPX3uhrdf8UK6+/spPuxn/iREm2tHfJJD+REg84EPAbnLMyVZmZ/dvc7kVufeLsujgM48bOZbtQPJVm33XOBVb1pAyg4mT1ysiBQgYIilbwPKbwlhi+XDs0MGcyfR00q1RHOwtw/WC8WXK4gF84WCv1gsjR8h5NmnajRUhuDBA0sf8cG9scp0CTyxOwP6Dzs3fbRxNm4mCtCRzuCAj02es+1LyfHH/SxrH0q4WM+wMktzublZ2oJkYmD6XLfcr0iKR1VAS1gcN5Ds4CgyRp4930oQ4DhcaDLyfSADjIodvChVsjPC7PpMxE7wiTTmuT/IyI23ApsOv+kUs3rI5N4kMRJszDaSt3XdB55afMmQxQ4BRlpwUOfOz9FRtVr/D4KaUt5fqFb9hfEjOC25odm1W6u3bs0ukMKg7cZDZKesrBybiP3wnf6JKDqdpkiuK0JmYeBikG5u6TE5S8yt02OzZo+P4Wyl07OrlLQ5O3tzYnhgeGJiQpJltVdB61YBZT8k29kU7fPkT37RBJJy8Fh66UeBvMAqq/DSKrxuSIddMYTyUsjy9LQByatZsRIsAa4gWwNAflhsODmCDSTrMmdfKMsNqVFvARkqp1Ik4pkKDd4U0nDac2Mk2fHjYqVy7B9HzJhOlxdmb+VW53RfkG/aLoq6hWcl+HzD02FYaphqp1PUYyFT9PZe7O32+ILkM/iALZAEe8v7lVQhDld5Mz1LOZsk2CMjlC0wLMtgo6RKileSlNNwggDk1aadufQFfEp/29L2meczne8B2QwRST6phAqPFjdYqZq9Tq43qSyQHV83gLTPJvcHf2T5K48bKc9+5o2bZtNohsp15uWAl/ZB0lwWYyPVKiSjA1llsd4ayPm3sYfjpcIxuZgnpXU6nK6nqKxmKDigOkTybkBJPBV8ypLgIGkGjqoqCLKnbyDoE4LBMOU7U5KzzilZ3k9pm6V8/vE2JHsV3jjpRyrhNKFCRTocXlU6062QK3T6lG1sSE/Cep+99LtWDjllm8zMfFxHBgI8N2UGcHCdGgjwVLMOlv5oK8EGkDxTZZcc8j3bIbfFm4A0TbcLnXO1oUmczDbh5ZJupXJkMMoZi7whsLJeSees1MHKN0txP8V4leLUEUKUOrTa7IIRikkyYegU8U761yFGgSKkGjg6ZDnq9JwbUOERikJQERsSQVapcoJwUbOK90rb+e3NfSrgOb0AIAHmhCR5eyVZ7fZI9y/2eRWP5P3MDSAblISlOXvpytlWZBNIHm7FGRlZzopda6U1jIaIJmkXBqDskx5Wm4XF4BRJPrfzeTiQPYE8FVxBYEjn8mbbGwBput0uN3B0u1zAUqSYkUxMxkaSAWtZGhN3GG+2fChEZrxeyZX/tfIQgh3PF6sFf2GqmgJt65VZLesLQ65NthuxyDfWhK9D81YA0ulQRadD8Q7LoiM6SaeYzNyZdM2TYxpNKxtVcqQg3Pu5zMgIvEgqlEYTsp6o0+FVQOZeSVWl3nOSA6J9tYElKcmWaOefx5lK22jmrPCklLaBXZ6Q0tHzfvYJac6mNSEGkpizYQpWoqUtf4UDKYKMANJlsh+Xk4ALZUUBQWGZYUpOHnx1vmooxOy2FeIxOPTZ1wck2PljBOLx49JRPWOQ0w6HMSibeDoMShOuDlhIcYjbdOJxORXF5VS7B4KUxOMUtExI002YIJOn9NHAZNnKIbZ8vLldW83QDDdw7O1T1UQisaiM9l28f/HVz/9Fe/Hizca1jqsNHMn3aQcSapDWJhAEbZkm70w1vJWbYr/3BJIbzfxdKsgSaVs6Zn/9rRrnfjDRSVx0MTSb0g1uVCoG+T4VyCypSGKhxZcIkiGiAQZI+xgVNC1ARZbuVfbvpTIZLYMI3acoVFxYVlXYhKAnPBwjO7sIn4U+E933E4nuPq/qIHXZZeqaqWe7upyurq4udndjZOLMVzduTFN5Cy0WBHre0dG+5fvPnr169uqXXwjB169fv3jDNOA/wwCSGsBkSLZEm1bDRCKt1TP/V8lnWKCGIWHF+9qCmA9PfpldABJk4QjSb5BAwWdo5QrshZHZp/FXZmsQAGVSqdQQjW7FgsN9fQMDw9N/+v2/h2gVcmboWzakHZNikseTsNsotUR39+jbjR1PLEa7XK7o/Lwwz9skvSaj0agzOr/IDy0uLuIqj+j05eXl0UUcwDnR6OT8pNLt+fnNzI0//uEzAvJTQvLKp2S423UkGw678FtmqfPQroFWQZbDXxsE9kMA3V0uJ0Vc6Mgi7zv+5+W+5b6+Ua9XCsM4BolIQY8Hn7SqEuQCr9DJReo86z97b3Seuk8IPMIPb48SH2v8zEQbxonFeUWNkpi4CbDGtdi5gFD1zHe53V1ivwvOuFv9/JTv82uMkVRe5SqQbE8QYCsGA79t0XugvexK4FdrsAT8pBdVmzzLrD1CSzwimHgv/sfa+bvGjeUBfFDeaCR5ZsjYjgWx8Q1WksKBBZc6YrYw4+KCYHECQ5rLFHMBDYRgcixxY5Y9mOLgClea4jAx/gfMFC6mOpNmmms2gT3S+FKlMja7uDDLHff99Z6exuM9yN1XGv22LH30fe/71fc9vTdk/SBlIX2hKeouas6oSGaXR5Q1JoOHzM2DZYAzsLD+wSwe9jE9V/z+kP8RoPJhHTIan4yfj4IrQM/zKh4t0Cb4/66j3CyrBaV7zxnl3btYcvN/KtcuFrb+t4exjHlkWEXF2D0/PweKa7sjwLA2GvYryqXMU1FZPHhIAdtgQqjQ+mJGIFxBBjLBcRDHCK7v9OkorhmhmAnlxyyITBZyMet6jxyDaOkMLPj/PaeFr4j3nhuUoJNfBHLjf5V/nHgqAUuqnOEoduA64Z0rSMoJIPABoKsQQjBAs0A4FKPxmSbeiyqH4R+48y3FjAAcZreOizpEN66BMAJNkpWMoJmjeK0AllH6Gr9vk0yqcIWleyDPbyNJkC8CufHnr0iefPWE5T5Nv3ti5P4T7G369sLthR96URaGSUK1uQIK5+ICKRanFlYbYIO3w89fpyy8bJ81EfASFRUkGHQ4KW9v/wXeTNBKU0EKwA+wXeYAdZcVyZyHEqxWR9FOUjvNtlLxpoM0J7A5KlVuIcjZWUR5D+7z+e279ydBTlapWJ6yA9u5v583Ynj/0XfUkKFpZlOE+zSu1xd7FJ9XqE94F4RHKVEYFYfDxAGN6yufMyl8laOj6bpdTuOUzHEncITDVRmLVfaWgJyD4UHU25Nw6RmB5BPJGSwSkkQVo6zopJuL5pcrJP1BfgKPL6lGSRv7tp+9twAoHwHLJxuTFSIeTG8nxC4DpJbOHhW4Lcp0AcZH1ADsYr3+sl6fxb5ja6R/nuQwkjp9vmA3pDCfbNEaeOKjpyn5IiZzELoxRZ2YOSoAjut/BX0MAoqz4jFLS3shqCW5+oV710rJj8JGJ2mbLgWNizY5N4mPxiZcnYfLZJAvFxZeksZMNDK3bBX1cfOc7Mls7V98PjPx7R80vEXphtx0o80dxkrH5DTp9RbrifK1ggkoIkoPX4F9CDk3pLsk75K1SeeIQpJuxKX+ohy3vL33PX1HvRQ6eARWu8NvOII4dFz9LyQVyFyen5KLUSa1mkV9jcpKy543kbLdJJmfiVeqpVnQklkcXwLL+sIEyLylXbuCBEV3PuXd/OguyOvcA7keenUtZqnT69V7mZXBoNa5yndEMSouGtqEQCpP54mGNtejC3AYcAJPwCgBtCDkvo/CJKBqOVifRGyTq3RVxj6NuKBPJ3OMJxquOTilR4uy8vOcGv/OSZxkprm2clXa/Lrz9aa54wLIZYzAfrBBXvAr49ahHZjdWMx5wYBjT3ok5l+PepHEziSpZ86dqCZX7ipJrso1SkMVD9GhMZsd4ZdLH4Gw/TY5n9gNS/v0Lcumvvln+RGiniYPvi6SMVp2RkmuhM/LDcq15nzcfB21SpsdGuodbOu/Uy/WtBCN1A17bO3/eEgNwL47fGfV3FlkTtx/KUOjfp072NV4h2fYrRfuh6XeTlar1bhWnMblKmtd37ij7HVLNabcdIGfb6dNo0rWaUTPzKR4+MRmMkHKSvr9Jl60U0uScPv1i1Y8qH673ittMkkc4fe7Qk2L/S0CaTXswe2E7H86PHyXG5sed6y72qZhmsD2FvyQJizvHGW1hFCS+mFNQ8PBLSiMshlNGF1rXVlOnfJtR0eZnTmlPOm6OdubHkDxKVE2NFg5AEudNOfnm0/ff3yd1Ybzr3t7JerkqPOnDvaI225v5q+IZ29uvTkDkCXTjc0hZ436Y0KTtHvISASWWgjzMaJrtdoRTlsRjNKdJCy1d9qAspZk9F1FgBhdR02KUb+bblMV7EPhKM9YsukWpLCotBMh3k+eU5C7mVsc1mp/uNYXfUzuvP1nVHPip6/3WqU29RfV5T5x299rkA+kbxoEmTfsQR9x0oezn/O2hzcIHjDrRgCpheS6DA/omZEENnbhuA6TzJAkOOeonKSaeZ5pk1I2B3/CiNpKWnBtbsr0Jo79tS3X1Z/1Oc984pklANl8upo1SkaXHuNk09S0wDIEbF787fLyp3fcsIe0GHBBra58ePNZ15NYj4BhN2oLKkE4TVI4DKTb+W37KMqyKMpqWSPDL9DA8CaJWOuboWmXWGuLV3xf85V3Mxh5qbQA24la71RWxqmmmCezEX5eJQxnslpQfdoqZ6Wj7lH7KG2nbdbKQk0LMTa6YY8c5Nm75a1lU3NnPTWUcCD96+b0mrCngT8+rIW7vtk5OiKIlMIhoeSmxi9etjYUvk5cuffhF42QKmRmkhd6eRY37eH4xj/1zQtO8SjrNQf3OIDPgx9gDI+v5oOZqBbPvYiSpBQBye5R1E4jTJvrdgWBLfEjdcMe4kdiIzXU+ocGCZBSEJwJ0ZSmDRhi+sW0TJM0asGhkE1iupZ6wy5lkS65FGYLgXXZx+MPMcgTQg+RD3BOKH6hpgi+YYJvSTJwJC6Ux+AoQMRxIpz6sptCuBhEw628UUKREp0bDoYzMRwA63PHK5e3br1yfvMxbM6tQqIqyU2nbVzoTgWpG/bQZYX7Zx84y5Q8Mmo0GikMOEljAIdjM2rEuNSIgWLcWIIBNqBWpqiVq41aIi6jq708y/iapOVQ0BFp+q4rXpNDWWviuj69DboORhdHEwFJDICPx2vjMQdqOTpJ4d3TAxl3Tw8oUE47YTzdPTWR3VMdWR/zIAIbj6/Oz3/51y9XVx/f3Lp89fGyelBdTWouaGR61IiOGjCDe1zfKNT7ZpDSsIfGu4/tAf2Ud70AIAEiwWyQAsKMF4XfkqgkLMIUEDej6MWdNVQvSlmeCiTeSqHt4Wh3LDePUckDHdolxRjlojefwvZTgICjLfo4WKJVntlC4MbyK+7R8eU8aj4en49BJ1Edh6PmTDUOH14CyctX8811eL6lNCIIeKNI1Kpp8bmE07fLumEPAVnCoukHDz6Yl8cNPgNTinFANWzEdE7eigJ8ASVux2zg/eW/V5ohRicA5UDiuWN+9FjIIL/psju2y15OSZcmZTRlabqY81irpyPRcusazrG4pjl/MABr7cQzju+FD+eqH6+qzQySVglv9EiTSKMNq9VI6oMB/UjTsIcYm1sXP16YPoIskFpi0MhYo8MkTjM5DLSzmUZ/f/u3mThwGOTo/OdzuVbhuWshK+oYFxCgmOwO7/j0GnVGo0usbpZTLvAZHeiETGVAGDkG66L6Uh7ERRCQ0QxjsDxgcuhltFKJj9eaUcIgScCANhpGI9H/oeo7oHdbpmGPM+nI9IJ7VTPF+xMgQeVA7+BH6GCectKPzeNKo+zb9zGYA7GVTnM0kJwdk/PVz1dX58fHx2PIuMa7w76vHPGQXQyfo2GlwkbPk1AH6PRgNFFACH96fPwQznJMuUM/rN65MzeDJQ8aP08HSuK2Cldwt1XW4OnoHm2RCWzEIBtHLUYHc2kGKbtWQoBGslwjsYkPbPLjU8lq2INa86CCwZ8+mY+3r2ukGB7UcLI/tEQ0cSusR1ENywK0dQlmYherkXgVV1UUIAGuvoN9vEFWBEcFzzBEW35W3d4ru+5JuAey/Qzj6irA0gW0OEmAiycY/AF3CtaW9p7+8ff4lXBA7NVJuVx2cj/H01wq8jAMr6ILqvLQmWf5/9pGAshuBpYvK7EykkIi0o1iUHeLf6YbG64dQWt5UQNb7UmWhA+mIDBnkx7h1jRtpp2Gvs4+GRvHDUJHYtWO02e3iLQPGTgcK3IC90TRt3/8uTRFsZIsCxKMPi5xU1uJQy/R6A1wKbnS/rb47hM+9oSvrfJAqbjdvonmF9+v8D/4g9HcN+TvRCVLHRtFkFMqRtgtfdgg04Yx3NZgSUNPUEXB63z8GDwZImG5ytrzFtdcv43hCn+MaiKL6Fa6UrqjX6nzt2JSFXai0Hfq52G0ayG0witpLn3PetNX1qtA0eGH9+6DlZ02WumGAZnw7EsKvyJhlXM06RulyXoZW1y7j9vgw7IbyVfVN9fp6qAMslIcGkKIZrtbvJ+J0qj/cHL+oK0kdxxf6ZadnciKWPTAqDNWIdCrBGm8j8A2PjjWC+pEBAsuFoEM4QqHI2quVJXUcnMY1ylOuFDh8CDXubk0acJVr7gmlQvz4IR5kN9v5jczv9mVyeXNSqtd/bP10ff3Z34zIyskc+B9fq+AwXrkoV8GiV2BnNXKpftyKdm9udtdp7PlcrvVIDeO5meD9CVojk+4LPGsQoxVlV8mKrlm1Wm9hopAanKueBWxIrCrZRt7ZQUbUyULbVXRK3KHjREDWxkJbfHxcAt5RS1q66kJT2+vVjPVsQt8zzb8HJDnNV5MecvqpKKjpUYIDW4uswQ7iMqdqeHTdkgdQrxD2r5yo65mO9C8iE01r1h6GvJGhljIsMOBh4tAMdXOai+SdrxOtRMssNzc7Y9WqyE6rDrI5eeBrAgU3lQco8ZWKaCqneubPF2qnrYip/rONL7SKHJr5+Q9UCNRKwLp4dewXuS2/NxzY4bKDsRKOz7IXihchU5zFCDJ9vp+P5mtLiHWbJfDgBn28nNBOlymLfGydCf1NstynC8cmhKFNmuUqF954f7eH8mzlVenIf1QyO3TsZFszknsxvrdN8AHZEVsarpm4oAr9Uoz5invH1/+9W41Rs3MQJG23KCu//6MGSdNXssmvTyHK+xzPKiqbH5Ewza6hkZlHClZsLDFx9jkI9JTjxSeGPWTw9CrfunCmH1ezCdYUE1TxL5ovYHr2jC2mRSgss6Hp6effno3Q8UMq8BmKjo+YClRWeAMy95qDGH8ajtX27iqOo6XT89sOTG0bbo7irrmVyF0cI5qw8uqnhEbfZlhbupvoGbc9CcuqdCn5cExM1Lcs43sYsEqj7GdO+Usmz1d1XThscfnx8dqhba8BR95ID4sK26YlUGhtDSr8jotx8s+y6qQkcvN4/qR/RvsgUS6LqZ8pZ0SQHo0DC1I0ocGKdw0E5qWY42QTR3zBak6d02Q5l3p/dw710GS64BeEj529/j4tH9z+vX+7emkfxT4DLlF5gYStss8H6vN3FhiueZsIDp0FfEzIKdPar7wy/Mz9KQn+0f1czl2uCbiBcmIzc3xFGcmLFpIdtKdZH0/bbSWJ1elVnLMyuG1pwj6ioC5/w4xzXIBOX73n+//Lm4m999OvlWlyUfozAc60lbLmp9rGOR0DCim6gbbAq6dA/R8++WtfPnl06dPv0CDm5fnlyccZlChu61mlURs0JkP27gooCm8BtLmLgaP6TgbaemutJT2NBYHpvM4qQumUjYKIcMf/vT9X39Yvzk7Ozu5eTi9u1/fFMVxcDCoejguFRCU1HR6hYeINK8pz2lvagSIz8+IYpZN95/2p1m52++foQHI/XKjhhAjNO9Q/9aGSWrYQKwxaRlKZnT6A9vpoJ5shKctC0GY2XoWax2h/WLU090ZczDauPH7ODo/XxyfHZ/0T3DyTNQNqlcxEgvdLu3RVROlxqcuU+9VGRCk6zxfFt2NahDWOv27/WSpBmNpnEYli95EB5tpcNMTHhffkdWCrQsaCq4pjolmNOZvIGPvbbUdkNjN+Lf4oX1XbYabbxZgU1jZmlVV8JoUp75h8mYVyrcpXRlFhVC3Msu7UZKV0ODuvFomxW6fANmuBhnKKGTj2GTRZOQxRWh/rrLgn1jUbNPFI8FnO9aBH4LJvh/lMmog8X8S3/3lD8l2s12NF1MTKwITb6uawIyi0DrphvbIK/eg2uPcytAhRHZwSaJuOS+pzefzcvfcwUkC2rSJYOynPnEsWf2wPulb1p2aZ+iSPIFwShS+BceHMkbBvx/71hTpzBe97neOt9vh1XaT56qrlp/nwQELNXwQoW50TDRfb1mNIiixVCjLaSET4Ego1X3PT8ONDtzoJPWsXX8yyqEeikt2pEv3hGBzbF3uzKbbSsfIc46CucBmAm9dKa9yrO8nHcwdZ1fjGcpxrJQYOH+YT2vmbGhMGcksY4/qK6k2YxRL2gxGBXKJFInkBK5PL/2rLkUbPY+KV2RsbPY62GaknhJAYXQjvCK3MUkD0iQ9eGZeZZAJL55ovco6aJOChYrj6Uky3G63X34JOWE+Q1uGhDBg8HInrLqB2jPP89njaU2F2ppLi7GcA8i8ByZdmg3ay9O1mv6jQRqUodenUZ/cKy5oeZEiNSpaAePlOVLW1yPE1ukdCNj2z9VCkfPMVGxbP0xONjgNYvxbBRLaGN1iwIyS3GGdnXdcZq+28tUGLjEr5LiHBNE9Esv9y+RKG7dOJ7VpqyEGaZbDCMrAQ6tKL+oIs7PuTaVJJEO+aIb7AeHlkP5bNqeJS15aWt9NQI/j8+H4enWJIFXfBBVpbDNrOjiLrsyskWq1WbFpA3au8BWQ5TzbyMWFCjIEEy/P+4/X2knq4K1r1m0F0u9z2KCjyi5s+MrargUpGcj4AMhG7ilZ1i1d14bdRcsiILO4uXuTJMNhPjza3a4up1PdVUHPGNRs1UCxDo7vf2WbmwtBU+ASOb6wZ3Tf/uWnn9Uv/SLKyMRuNlol7aoiWj/CuLng4hRp2WlnJ7zlXMyIXf/ROEbBw4skR8xLHKjbMLw7KrZbSIQ7p7sJOsCFwgh59SJoCtCSLH0/5wCRl5vXZVdvpd3Ny6VMBuqoRw+eztM5dLvPN4VylF01bChZeVaG0it9S1pJJHgXxIvXzkPGXgfSWwvHF8WJWMYHAr8P0nY54fjhtLMBSXb6p5M+gswX6BdxFzgHl7HtgAAPgPo/Wq+KuoMRUOxZkr355Onp4bgLIEGT6qdK/HGEKGIlF7YCRrCYYNG6UfzYEa3r0SOpQxnvrtvsEXJu082mUKU1LuTD/k2RDM/7/T5AWzCUQeYCbPZ6sPhVEIERNkvK3gvbaNqNbi/m6mH1DNy93T8IiYtLtSTRCbnxO1tZlKa65uIquUNm3JwYt2N/mgQL2SQ5MilHlwAAIABJREFUXVWjcK7KkhjtAaTxnKZfo9Op9c3Z26PN8PwIOC4wqCwQImxZ4BH7Y9PZeUx6RErD6fWMwHqWom210166ib/58M6Sxt1ul7RjuQ6LLdm2hMgd05oNSfWe2vCToSF5RUd4UcWZuVm9ZUFK6brcpg5kvhmbtlKJyHXL6UtVC9Pui7MdhuxFmhHKlU51gob8fkdmzHXYa3D6341eNDdUKzn8cGsRw641SYqzEL79aLtVFbVCV8lDV0eLRS0FIY0wZEQo9rJF1xv3Eko7lce8K4/n0o4/MJA6jVX1PfXCdnEcdfrb34/TNM3SbDVdAU/cL4Iyhe0rcPx4sYGEG7PPpwWXVgtv9Im937TXwKJtv7fGD/tTnEhQiLitJbnRA93erPpDZRrPEZLxmpzHlH2c/fsrr73V2LFgPck4pqzemrSupusVy/hvqRe2k2PZPhpuL0GQqQouK9hAmlng2W560OlxTAca4Dxwl8VM7zGaJ3L4c693a0lmaooaSrK72VK53Iz6UwnDLApuLFm1U8NsV1o4kLFv9tbuBYvyfMEmiZlKx9JJ3qyIVX0u9eqiKML1yXCYgvxQkbAtEGa2ApDvFLKRcnZf0Qano7mRoA9qoDZ+fpCtemFr1KNtNGrlUff2n7ctOFPtFkHegyRFGHXVEib8L1VWTmUfPhDtjNB5wDhuJDZeNiP8dcJWvTZtknyMh1TtFcX147SEAf8iLtxdd5ZZWgLGtJ/1UZjXsPUDHhbgA1Pg0BQZQYCHrTXYDehwMHB3HoLao6sihw5hvon7f/tw2xqZP5cAuvukLeIoSrZ61Y3u37CxT1t9YLmIK1b4ehReMtRYuO5AkslT9Z0X3gTrzJBdm3XQ+K4h/hZs0ZmmqMjrTPlJ1GWqQDaiLaixxzgOFEYAuLsYmHahW53noFUjqfZa1KPRZbf4+OcflRe9VZLsRmuQpERJ4qobXeX9jRQsslBl1Y01uDRI1G1XNOy+wZKCj3Go0taCWI0YLZtNyKA5Kqq4hCBlkqfpPO2n5XXZB4KgSNhPAnKBPRMlRiys4L1I6AL3F4MLTvE9bITygnEckPHXeYKVt0bL6OsvPt7qvwQ3u0rNLG5DVhEBxu0QJdkupLcEnQKPUNNz3Tgrh+RMXPpBpSlKk8uzoCP9YoV+vVtPZ2ZvKeLtohuFSfouvYaAfF2iIuFS9sv8NDDC0zdeeFZyBGyoxAuz7eCO96o5kgamBjhoHRAnKrKVboY/fvEPG+tbvWJ9c1Pcr/9L2NmzNpKkcVyt6e3uOrtXCA0YsYlfgoLdSOGobwonC2pWDe5oQMKwB2ahF44Jhls8iRk40FdoZY2+gVHgQGDYbJTMJpNt4g+wgQPjYBjGc89LVXW1LO9VS/ZYkuXRT//npZ56uhQKkORleQm2HsR7bZzRuE0pdrXGyRcdg3YsWogGvsfbUggHpJOXOwWS0IlaKFnduCCoJwC3MA12ExDkAKy7x+4RHGSvu2hZZ9YxLq3jCgnZaYRjY9DX1y5JS5lIPilMGmDcn599nDDJquM9p1NklmDcWYlngmH7Sha3A7dJQtjKQrQ9xGya8Ea4jpx/i20rPCZjdZ7Rvo++wO4FatAlF4mN1T3giBdwkzjenB4Oip1PLYJWPQ67jJFNmhFeMTbL8bp2lGMbfRClV9Psu88IceYs7v55/rqj3aRXFbgv1nIO7zUIEhdwsF6exSJqrGY7tXGnLtGIx9EWM26CjGxayXmPrf9QalDXjMLIZkGRsP2b1IrdzuYzkf02HBqU4CHBsA+L3cNVy7zQyntEk2MIWrahOP5EgvxDC7JG2Qg39JPHl424M+kG3fvz1zon6FxNeBcuMG7wkZcQuANcoM3aJi129wYQLsgmuO0cN027UcE1AuQlN7smSW7R7lwT2GZNeH/3IBLO/LBIiCEZN+qxt1ie9Fbr1tMZoROd3XG9oUiTCyE/2feUZwK5eb6OPtBP9iEt794/vNbW3bk6mc/x9L9gZ/iKSIKz3ENdNrrChBt86vLj1qDcdImhW15z2tds20poMizhrIGZNRzAR9s6YSUK5wvdLMgK4nfKGE9PB88Xd7cXq7uvLaNHzzi2bST7DZB/NFykDTNwUbJ2j65VY4aqnfBpKYr7hx8meu5THRer1bI4qfpDMG6QJHhL3GDJ35zR6LgTask8EZWjx7FFi1EIa+C2J81pvthcoqE/5bMicecMBHl0lO1UHdYjjt7poLdYXXy5mgHMln7BjwKtCcZ/p8jrRjKpKMcxjtF8Z4r4lec03nEp9h8exkwSAk51CDMAfOCQjRtGiROIxsqTzZLNtLjJ6e8HJk/cE7W5xO3ME00Z3FlyIEXSIlJAn314FB/9llijRjmuF6vVeh2cnJydtaxN2wjRtyTHrm33+dq/vv7PhiLH1juiIhuOgjyhpDmTTlE97zgWOw9ak5wyVHgfxHQEWdLp21SdFI96c8zLbMrsSUFuCeGNrp/QaZY0ixlC1JMnMm0s69E2B0dxOUiSRFM8PsWTZcGauvFxMhkMWzY8bLjIWpF9jdH87HhIK0kSpKSseyN/tAhrkieWJLiUuoKUVK9e/hdAgo8M8BOMNkjy7E64q16RaDrBULgijfyNrMhtv+IbfJ/P/MK7fF3udPr/ECRt/4L5xF4W9yrECNfj48NPd7fri8VqHnQHyRD4oiL7lWfjrQmvdkLtZIn6x6YeWZFMUkk8PKmaJTWpZ53SlOGA5C6Q5Fhe6eIQJuyXtK/AN7EGSZIR9Uo+WV8YOdWyR25yS5YZNbaMq6fvYTgLRLMYaQofegc/YU7FB5DguX8BjkmKvvHq7uvXr7fIMT5LJoBxkrS0/Br5c8eWKcb9JkULsuZIilRwoCYlXhQqk6xaakECRgDVMeULrcnXmL+yIpOJTMGLvi25WI5xm/v8hNOCp0OF0O0SURQ+Hbnd0qWzYqvPA+Xbl6tZPU8M3QY02mAVvwVUtodJAmS531cpUHwzOLz9/AU43q0Xy6AEfQJFYNnqbE/FObduDE+ni2MnGbeKRJQeCZJYcv2srqJ1JNblZIedZseS7GsvCnemk0Sqt5cvuQjExcnA3UoPjXUva54T8mTq6K7ZaHsn+lxYJCfYXs4jB2RYb5isi5I4rYGI3YYpwjdl/ArtenJ4i2LEcXszj38apmjqSaJBNlNxaWOuBlcXzejGjShO3lPBBSwbB8kSvmh+BEnCm6adJYZveASR/Os1ekm4JDIFScIvq18vX3aztk7a7LIiNfvgXHp3Z2abdW0p7dFCa9hsI7f77tGeHmbJQeAJxXUfi1ntplMRZzPKM6lPjg07LqqqurIUgeMqLoBhmujRknquzXVYuugpSY2RnCAnilzGeDTgISBJViSColIu+r1JJ4VviXQwokf0+hC79+/PP3Yqyi+TdAIck1z2v70s5i+oJRWXHny3HQ0XA+Yvln5z+dpdj43qday6oBlZ/wCSpiyI6rRzmE+F2lsKW1FD+c4XF4NdlD6uxWG8hv/LPm6ZbSmCXS+Lt8hvWINEdyalFhOjxNmJMnVGE5cVHRvzHZ1oKvwXGTdjlIwyxaODatOxhkXqYa7TH0Jm/uX84wRtQKJlp6nMpZz+fLJe+u29LuVBQV1R05Xz+Wrumxw63LYzbqMNxZ0Shrb/GW14tqKNszlH901/Fhp0uLxa7579SBsJRgHuqFNm+9iv/dVa9bpgjDy8JKlQkYyQ1wNoMDCPWDIp7SLpNqcmyRDxB6UdpZRKuqOTkjBT7SK136QKBpLsfnn2AQ0BJJsCxzSXeZ6eDuahH2RdeAkBV1RRR1Zy/rxtFwca3QBhuK2zvu5OCetqHNy8Wqyc00vsmjk8PNhfrIpuHFC3B5p1We5DsnN7d4s0IetZrM6GiTsqSYpkO/SslshCFQnQEgO1KfyJJKk0Tq3F8Qiv/RE9yJO5l8vmSKW289p1krKBZPb5/HeYgidyiLYNksxzlZ515/DK2rhFlW32c7u8feHWdzdP8XrcRur2mZtwtLxZzOq2lMhmk4D7xfP1evAThGvIxGPS484tbl6CF0wdi18RXmqsWlV4YZCNAS82R5RMi60Wv9EV2aIJK6KpFFIcEUqFd+NNDXy5kSjJ3TNeBFNNeKZJKeIP539WHdQjSRJIqn+fPd/P4KW1y+4RffAgb15hF53RxZk+gc112u094tZ52rg+W9ysbELkG7dKlfisuOoV3ecxJT8Zcty9wi1LaJf3ZfH9EOy49o4qeZ+o92TaziDLVDjgK6OyoEaIVDNUdO9YY5zSoYgmRRyjyBxlTc+mFclTSJ1r4h1JEQSfzu+rIVt2CoLMR8Ny2dvP/FC0y6PS7MjgC+fMrHbmmxZTtyr0f0A6nanhigVpGirrs23DLAOzjovdEHPIEs9g2RkQw3nWPfrlTZW8ewf83llFVnlVKQo2qANQTo4A4CAQjAoHi41JjlBz5h6UIxxKjUYjRRdCTpLkZ5L6HbEopeGaG/fRB5Li6q+HH4b430jTBASpVCGybJaJ6B/UGG22NHa6IkUGAYdtOYya7d+uAOtvpF9fmJlLOL+5WZoFhXo/beTYzrAiWvbaIcwN4x/pZJYMbgGIQ9QfUqQvOu9RdGXTRo45XRS+DP5ixrQPjBDiCN3gmB0lgRz14UZ4wAgOxniNrPEJ8InwGOsHUoqZs8w9zpPwr6Ady1ex6EFqPkRJoofMpyopKXkDD0WpOWXlutOUSznhbEkfC8AZkW9m4M2abTNJ5xmnDkyzm5sb/GwI36mQ81lzQdEFatk+cIQssgRtXpbdsxMw5wod4TsC9w5nijRbJEnCkSPInPSocnoV6tHQHNG0RzbqoFTxLiQ1xWM6YtbjceN3ET7Q7pM0pVG5QsXin8N3D0nu3p9/QJKkx/xfKj8Cfq+6tEM+LuHY/crxpROM2YrSSf7chCBonunlrjXaWC9qw57dXNzMiaNZseHNkiBpxd0odrqQQ7bJP8YlZDmVej8i603YO/JcJkUv6QTvVq6HOsgPgOZ0qurjAA6gMUUaMPQ3EqIiYx4RRPydEejxmm7Bd4PeEHokP3ysHS+/D0r/SeAIKbj8ORarL89+T1J+L2FMVfr2u28vS5woUhsqxm6qxQQmYs8Xi1nobEBRn9sQbfyz0YFGKsaNhaLIOa8R83QsT4T88RnwINrHDjgiKcm2q3SQ+SeV0VK8pDyxkQySLRExHhwQExhjxKimcBvdohgdDJxmM041MiBz+j26d6xBkk41RXgk3ibZX/ZrQZp3UGJC+RmCN1iIdgo5vm1nRfnyZam3PQ2o4y/gbbaxYQ1ozMONk9abpymadh+x0fEzv7i4mXHuLezngwSYaoWL9ae7z3dgCXGAf/bIzlyUVR5A/A4OQslXFimAJHTTg6nBSCpDPvn/uDqbnjayLAw7jqdwTWImTDKJA/LC6VhEI9v5KhnFrhCEaiKqadtYkUULC5U97gUZTZHduDGSZQUJWb1lAVlF/APLSCyQRupFL7yZ2fQPSPYsWFiRQAiY95xzq2zmlpvYVYaGx+/5uLfuPRcPucRcGZUvPMEJ1cYtK04oFd9Z5R+J5A/ylsqsyE8cB3GycFCzgQ6RJzuhRc5+hqPEy7bgrT280erf7m7xmDn9lVxXXAp+CIGjfqs3six7bDQ5D18b3dVHl9aC4xcybLWqLMxpKo+SIA3qtfr9wdV+OEi2sFvNMatruTehy7oyuKtwkon/66eAoAPGuGImRCsEEkc8Lhc8if17oQFNKmoIM6W4VbAKcV+Us2Kc8hFwckTKLk1biiV/tS20UkX5ZZzIdjXt8PLy92yOc6A2zt44PDm59/ktkeS8XOPKaFwITA1M+iSvD4lfH6f0twjxgjgcZKs3cvOGPKUe4bX3+MGtFkAOtmnQpJvNmaYtyOycitN21sy6G9kNQNxwN1w84YHe7KIWAKO4EqQ6mCRIWHGLniuSlVJloUEH2TaHaiJZKQEJ7c/Emqwo92eR4kSkoBWnE4YlX4jitGFbtmfZ05yMg6R+7+LnX1eynJnDdR6eDJ7/6YfS+LI/vUoLha5Vq9gGySN99GaCmso7Mk7ppfB+Qk4cv+ij+67wsKOuKmr0+ieDq4sWBLmcs03bZDM2iaRNJG1WoUuSdLPVDU+auaWgHiixChUw/ws1K+69VDIlgI0FPBgssVQcHQskK2LD00RMWrxClmwxQmJn2YZh4KmBf21FEoIEONd2EbxfnSM3n7NdXJy+ga7t0iw637lxuv2Qj0iFbf1aketevw9vNzqThf1jSB/qUb++2kH/4n0LzWP269BqMvcfoaxFIM8RrUtt2ySSG3zYokhY8pRn3KRIUiZsfw5hPlARVKMI6VTJIykKFVUu0KNRGTZykATSIWwl1qPwgvgAEKeYqmF0DNVwzbWNFcOYVhxzwOjOua5d3dX3zo4vPyyBqrECQS6VqK8wWzLHadg8GFKSDA2LXZBPIyxhbWRBh9y5CY+NLCYZzhfaB8c9dessyIt78kFNz0eIIzrWmt4jkKeH2Xa7DcMwYchg5U7ZJElSJA4xd3eObTs7hf92Q+FIQPlBtOJQgfGRpkhSZgSQxQXlSj2MhMlwhNw02ykDcxRMC/Iy3E6n43oos0QSB3elZkvgCIxV1111u9r24eXxedZ1syv9wWFWeuDTszZEyak5bWXNt0f9+yzbX+AoiaSmh/+vpofurVkaeWwju9lT0ZzKu9AySJ7eE+aVe8E/RLT+1dXV6TmBJJYkS9A0bRudQkJrw+AJJfi67tQUBGlm3+NHVAOjzOLR4VNrqE5upUpJVFiveGcEJDFTaiNAKyQ3o9OR00TZxSuXDnq4ZLhky7YIeJYEWa1WO0vQ5fuIvn9+8+JzdbXfP1kEx1V6L2RrvuV7ObsTqu89XNgKRwlRShlCb7GDt5bOv8Xj3RakYnbbnjzp9mBQ1qToPL9V1x5MRPK9wcXp6cWHBIOskS7BDk/Rxy4RSmYJYZpTLo4p0879hA/xr7kAhRRryK/gc1Qu0iPpp0LFYoWvCkMi5RkuGK2s8LOONH4KOQJfp+qqRhAtW0CiT0UcO4tbi3xtMRIm8/79sH82R1ZkrPIoJfzpFJfb3l3GP5rU6FELw8KID/2jbX1sdNJkeGR0zAvXvHtayF/WoEkZbuowASdVE0NQQ/b/t0fgeHqRS9fS6VqtJsps1+RLQr1sUyAyE+b9+6a9hDTidc4MUPZijWIs8FcB6VG0LM5oSkqLKpiwBXsQXYMpQY+2DxIoO2zWbLtVt/pmnN5jM0lJJFmQW4udjpCs7mqh56cXJ4PDJZuka8j4mt2utMc5pZRkSN3Rl6nLe1+4BGp45E7jcLWW3GbQac/FB6/yoWH1OPYRtOA+rNGyFI26ULu7H9ufps4B8vS/7VoyWTwo1tJ8oFVAlraSYpC8o1TiDjhuREJjXXAO+CGWQSIlLOBFYXhKoFqMkuIv5Y2WZ8xOx+mIFsV2VxGcyTd2rjVPi5DlmzcufI5tsclQkmTZ7jgMu7rovacbGds/Q+qTlUQI3C3yS+0aUL4WA89H8hMTai4GzwDV946ojO61Sakq7qiRjmD+1b3beTZ43mGDY3SQfC6VS6YZKeDY/VjbXF/PrLAkd5KZg4ODDFoyA6RoSdofDg1AZZezyTuJRHZXC0dqyXQyYDkWx1xgY3H6GPFHikjVK+FIfo+zGXZ9UBxIWpChS4drMEhcH6HIpG2FiUHid7At01afoKfWOfWW5XzrbHB2SSmlsYrARFZkE8hGo/12SyYHRWjp+UQ+xCGChsdCVB5cWPrDYmNhNcwW+uOrW3cf3dbkZo3UVaSl9hHaZzFPdVIjZNRb6c1/rq0110WSX385mEnNHHgN4kwmCWSS2/xkOvFuErrsamEtQbQDEhNYfgzRKVjDkCsWzFkg5zESkQ2LTY6M1mFH6F8AX3o/MqIhSfkGm1E+dv/8OGEl2ngYHknHHGeW3Ez3vrlyNjjZv7j57cMcxUfK5sCxXdnZaWw2oEpvKa3GpfV1v7TZdk9tSEq19L2Zy+AYpG2c794KqsEiWipK3jHC38o8aWSku/Wuvt5c++23tbWDv1CVp2875dRMCq2c8niC33wymWGVzkOfTwsJ9CO0+0U6EwA1HB40yFPCLaUr6gQbMscHiSPMy5ZoDJSOIYgZt/opDtm8T9Ey1Wfw2EnccdL4FeBkTNNIFBKFwmTCMd1x9q+UANuJ7MnJ4D3FnOP/SD8nx45+p1Es1jc/NWrma282BuHQvFpVgLe9JxvAMk6p4rrXe3X77t1bD2R2BjtGVY8kwvsTRGQjmO736frLVLO5tgaQf4ck0b5mUopj82XzZWqmPpPJzM9nMjMzZSb5y3wy3kXHcjyTKTNIQ/21KnzIa85T6KwXTmwyWo+jXHeNIclpa9gKJEjHT4pY7pYFITrOJO0/DcsopK2EmaC9QekMSJIYOQi1qW94WF3W9NbF8bcPdhuRHRhrtUajUazX642dxo653B0pvSTFG7ztDeEuW/3+IW06TNWJe0fPbz8I8khPUOoUcIEcjW/8C0b4xu8z6+vN1EGTSKJlHrEkG6kmo2w+WcMVXC8DH3GcAdJYLJasfYeU620xUy7jSsAQ4XgcJXPuCEfVOobriVBZq4QOV7lChx3qNPew2TtQ40+BMDqcFfDu3U/xv49lopkY3E3iTmJSTsJCHLJfDoelhyeDs41a+x+RcA+i/PVzqQKKxWLj0yY1yBJEGxzCqfBAkMxbirToMliJx/Zej7YGOOr1nh8+b4VkohnXroNZ8yx1ncc2g7SQtPvxHeEjVM31Jpl2s8mSPP5abj4hkE+e8GVYeIbsulyGJGOx+VhtGSH/dTETjZYh1YDvyASkADJcv0/nGagxmiBKdt1Rrx32sNKp9kBCkgUx8gLnVLEoPrdo+UU5+uLFi5loLAmbnpwH2SQehBJ5RRwpxkMY9hwU2M5+R6K8efl1Z2eh0ahvbv5IIOsHEGX904/wlm+ZZb5H1dTzEX/KfJAnFYyFQ9v7+FGDfk9XRa7CvKYwyB0kTckRNl1bB7ymgCRJ0pcaecnjb3XBiCYgU+weo5kZcEyma8vQ4+taJgptxBjkmxFUCJMM0nASnhrZ0jnDcd0RkG8IuZh2IVmvo38p8dpRGHkbedkEHSnV0+iTNfxCKVBMPXv27EU0GiOBRqMzUTTYOlq6VtmZJcM2i1Dhzv+YOoOQtvY0iksXjvLQSfOGECJZONzATbk3prlNbrB2JMExUzs17xEuDVOGxJu3uK+JdyTgqFFeRUEkCxkcrHY1Mwt5XRVpoItCXWUzs+jC2ZUHsy24kME+mFLaN+d8/6R9/5p4E6OtP8/3nfP9k3o31w4pytXXr1Yeg6NfbjTK/jqqGzeQUsrllc0xmDifYpHtxCuffgt8fyr/7vLyAr61o05JK+7E1wtyxBbnR2fsmITX/QyyK9dj789FkgqkSZAQpDRHtfIGOA7/4oQ+E52AiUcGpne3fy46FWIgEMhMfKcnWMab3R46sq+qsU/brUTCllsvFPzi/K5Klj2QQnJevTcMq7nR7MZ1PWkmcUWSYdREKpVUAo0yU6Bsfw8VTa4UV4p/xdq8hpHxw/nHR48VRyyfqsQNHws3wVLtoQ/e5VK/I5W/qlee1xr+j7zG5OIfyIsgOKIeIZu2Iye3zhJoiqbjmFLZRKUEaaJZtp8T5MeaNEhplHBwmxWMZdB0FmYHEcQRNg32qflYbAAcp3f7mwrSGhdh4pWK2tS5IVWuprxeZ5xWj4cUyQ0c/cLxmzfHhUYtAvn+nOPEBM+Ajk44b4S9jdONNEliZZUmgRAHSWCFPiHNYtFeQRT/dXG9ttJbZyfDRxf/W/3x1WPFESQFoS/vvUajcPx05eyBapiqWg/vqn1g/tL8oaOLn356f3n5q7sjz148u3vlaETOSXByC1IEM1PcRCxG3ERAdjpOu2OOQpLn509o2YTNZYczRiRQKkXy8JxE9crO0MkCpx7KBYGSIImSnJTuCINCoiD7s3RI+uZinyQp4rPpxPNRq1Ao7B8fHxeWa9quAqmWGEkkggo2omF3/3Rj420u7mX1pAKZspOycEcSBW7bdmrl5cXFu9vrFmRXLj/GKq884D7G+flrgiwU6k23obTYQOjzvcLe3sGbhm9lEmdbEorUKwJ7r1Xl8MMzT0nJA+/wDgLSi2qx5TfpKQqi8JMWiCOv5bS5OgvPz7F+LAKg6WTaUs7RfCQQAElkyYV7mPgPb6oZRzhOqdLugVTjiiYw1OnLaUCxiqbUOikbhyxvDXwMyTSGXa83lguFp7gs5zWtd6LuHsdoz6ozKff09HTjbToXj8ezUtusauoxm8xaFiDaVjL5EoKcrFlEVcZCOT8tL3Bz7cPqxydlv4G/qokLV9eHfOp7ByBZaHWblKpRmtva7rv5p6SpznCFjHPr1ghP9PJsrdDsdmkwnxAqJ+mYbJgdAekU15QkDUabvFrAqAU4Gi4sXIMeD29yRrsd47makd8GeqXaC443djW0OQVxvqKmR6ZyIEMe/2MvPrJskUnHZzYTRdZZo7y8TMXYgUpkIqKEGAHAcFQW5JaKb5z+83QpDZS5eJaSFIxKj1gC0noJpxm3dN91G5/W08dnh0MvLs9Xf3jquxBktw5mDZfV6O3v7X1/cLAnOToOOC5k1ikulM5CobmtuS2uubm5UKjU7nT8buOE/+/x6ItyV5YnHHVPhUVGb8fBcN02jFKp3T5TkvwdxJiXk61jsA6EgiGePvw39OvDsbExnvEacxnHidGBz4McpoobmsY5h3oUmDJox2bQBXDQ24uZmUnMj3NSMozx8UTRhX5csPTdRt3Nk2OUlqwAhmkqdGoz2zw9fbi0tJROp6lJoCNLBTNpQ5K4hiDfTdVSluV6fZRdFvHCrcEdJqFHGIVdt+76nit5xDo9AMf/7sEs4p44hlp4zw7qYuDrNoQJGkSgAAAe8klEQVS40uAJT/1zdHU97sXx5tFl9Jany/TCKxlRDEqvVEpU0VBg3AkjXwqAYSygqdOsj03evDY4PHQyxvPtgiHPuTs7Olvt50gmlxibYmVKmUilHwH7m5Tc85LdtPFxY8LIFMPcEcnYbtbKurLqhXqGhZxSpgyChGQSl6Xr8aWHD0lyCeUNkFZSHpYSadpwbjtZQ2H/oWjbFhZJ1usF5S6N9bPD4Wc0nSfyEY961PGd7x0cHHwPkDrAtD4vR6GB2ljBDNUIOKC2JSCfraBBxvEBpBqJZI6TwuNtxFwJNgBXAciQkuRCAn0R5axNhQCtOrq2dvO3gztD24nRe1W1trlmZweUP3CKi80gPFZoITyszEf6II1xI2yoTY2v798vGgamkzDtgd819BWX1WxubJhRJposSLEHZrF0qV1adS6dFo4Ckm0yaQFkWOWfsGNKYcdsmo6dtCzfrTcKaIi+hbDTKG6NDLO+X5d910Nh4/s3U87+wb9A8rSrZ+PQlo436Xmy20DD9Ri1EV51OfDm1LmpNqlRppoWP6mVoiOzrm2G7Ux+IkEFBmIPPrBLvgoJR5YwKVbX/vwF8v22kQ/N9iHeweWbaYyISDuo0fGEej5QbaDNSAjEbCfP2BQZmtUmebFYkwwNvSnp5OL4k8s1wSmd1p0U7COXE9HpxAuUEh3BLhuXx+Ry/Jgu9S0hKGzyJyLRZww/Gc6ylgmSUGSh0HBxZFm1WuxwGPW9+vFR2WQlSzF6VOTpRlP+GjY8Zb9Ox+nIkMwtCFEkBdjyzuS0XkdjtiplR3VGDHuclmmJakYpkVyoNPactf1hKnA2RUNZBLjF6uT1bxH5ZxMo/1GAnK5ufyMwt6sDMhRDdUyVFehx5uvNr8c3ubkwMT+hnmwwKEDoEofgaLEqU1SeBb3FSUYApZc2cmbY1IlLHCXet2i+SUPEx3gfbliQcVaBDKfIqbb+p4vLvxkEKZo0mfJBsuvS0y3HtjJzrO8Pq3954ns58NGhu/29/X0GfZS21+oFa7ND12h5psM7dPZAPevF0Q0Tg6LIqhHFsOpE4SNRJwpfzOczbQCcyOcxQucT3AagDqsiyX+HApBjMDiKjvjV5PWrmNa3E7DSyNQauuRo9d72PQJdlB3yxDgHi4REQ/UUwLzsJxgTAg8xMCWaRGS2LJ0iS7G96SxqBTG9xLd4yjGJFiRR1ariKTxTT6rAI/dleQeRCkk7xbjj115dXL4ruUlLFsYIGZcK9YaABNqk7nfmWN9olccuzYXRr1DvuvAR/Mw8vatTdy3baUtZew7HO09XC8LUMyMC8k6MzPqZhisfKX06lt3vQCgUqgT7kqQeR2cXF7+6+SU53gtq/JzY1Ogo+M5uA+fi2BSf/NocX8B4BhPGF5HX5NBfkAExREKGsBRx32hGjCArq8cFYHJ9kkCJdgRETSltLFwrjsm+Q0vV48eQ7IOkHH2a9DoK+3bLy/IYQQDlLG5Th7VkdW5dSaG2t0Z2vnt//vcfCkg8uuDyPa/ZTGNoirPi9Rbzs5qgYTrkR5zJlIPoYB8KyG9va1oggFRYAg9NiyD4wpgjTNu4yF5pSAsGNe2OkmSQu3zBxeraL7+8Ozg0Uh2dJskSGmcwGFyEZYdCsanYAFvf/YVirUaUCWmEm8piMEVyBAbKTG93ASB1kVoWLOi4cqtH8m06nsQ/26KBU7TQq7gNkafQJvlgPFZaZNLNESkdW9f5CcsQ5HMjK54FGTZU+vF5hK9myQzSxTzit0+Gd65z/l52abwtC0SbG0sSquJZtE4nE233dhbJUDwZ9YMwZton4jZXJwEJKAWcpqljDekmhCtNGiIITQeDszJxf5jUkHL+T9jZhLaRn2FctEFgdi206nZQFQxJmAGJSBNVgzTCUaqVWJTYqa01QiRsDtZHD+r6SwwsxqshMogNQYdSbKi9J5OTDwtFxODDwoocHNo0eA/1bU8LuhRy8CFeWBES+jzvf7RtT/37Q1+Wgn/zvO/7vO9/YgVqWwe/WoB93AoE8nmdKjb4ZFhLvMyiYRKkpD6scrxep8+pX60jI7I6I09y4pBR5aWMOEwKSDV3UM0yAxx8UIwBCyAZqIhOecQLaaZHFJusZFNKkrJ15HCwIjWclb+OX4+3raSU/h3kxhU2MOvsZRpw4dko7SHuazjuF//c8yNV/vLrl7dZvAkSvSfzCi2CgCxWVb5EOUlVWUKw4MuqCYD0w//MUnCaxn4voiuSIAd6+Xw+FLhMjo95NURJ/vTqLK+vabWbv/9w4dLUXiCnaYDM9k3w63iZZfNGxPA9ePCgDpAg2YEoy3Xelo1Y2eRZFJICcobWRsmQxQPBjnDBZwqMGKiIaxQRq9lBr9xUqc5KyninqnhPtJtVZoihjcBGegNICPKmlQVIt+2imdzBYlivuK7rYAGwA+E55OxGg3tMla++fvl5K4vYxpOYoAu0Wgnbnsn0+5bMIWCv0e7FJ+lwxu5NSWx/lIOQQtBhJRhZJseQTgHCWedLeXhuSC4vIO8pSa7p+trBxl10m4OAphsGgOtBZoWgPFePsIj75OyJMiennc5mc5MuGxDraMyvEqJsBrBH4TENw2hxQEuJVcMz4WpYPsVI8BvyXadJjsilUiREjXTmKU+4UoegU0AtMNOieiN2Y7CQG2U3lnWQarvD4SFRuiukxqFRmhQJUUC2u649P+1/8uanV+9ermazcN0Oax1el04nBS8o1SYx6ZIZhvIVL/kltj+aQzXRVVpEC6c/JkYtoPj18qgfPVzk86WakuR3gaVvD2B7pktaCM+qhPCopAZdZQa8+LKuQD4oywh6s9NULOPxByg9oLi8HFxG/wxJzsgchz6LTXRYso7qpTk1pg1jelwFSbtpsyolUSKoYc7IyBIgRZBSZKBhJ9bIouVBfXEaqDT1nXYaZhT9z2h0eEhVEmN72O26aTdNirgJZi5tfaHf8+//HSj//K9Vdto8QidigZgVZ+J9tSGVMc0K64hJaCjIAeV/3v/dthEU1y2CkkBG7xeAJHuAqGx2j50fJfnq1duD736755/ay5lBSY6SAuQ4UJEhUWfIx1NQ8LEpWyLNjsygSbJuXl1UwtcBMpO5gcMXKXJHdxFRQnaA14fz6sc9k44Yb1GHKQtmkMmxOuOBxKqmxHOqziaaiuK602hISYo1IMjfOF1ILZ0mx9E/RkMOiwCxO5IOnSTJ8qSBizQj2Sn2pvcfIsBRdqyoGLFGy5LsbMe9zed4nbMa1FRDuhOzfnlaHPkfDnKzEt2hvCdC6O/x2hqlyDXgtzzLcUBJ8vTK/iX/wDCBgBL3QFYIkmFOnHkfEG6WWW3AEAEJeTTWLTtDXxnnvAOLg5y4aehBw4xzqGlGitwDqlZVK0CQJMmuRow3mp7JhgIaWIoXilVOXfXa4FcAHcdRJO/DQh51pRd326MuQY6oSVx7MRrhASGZltB2FEm323X6t/xA+fbdu+//8j/r2Q8/nJ6ePnv2DBdnp/+9zj64REl+c3bKh7DGGxsb168f85NXDj79dHZr6zO0LHdrn3y2NTs3e1dlyaf+hQASYSRYYTrkAcDhoaBxFHp53u75GNRMjABptRqSzQuxRJinaQCeAZKawVGPaWg5I849CjDO2HYiiZJYzYRliwAgmQ8TqoEJK6jifJBQIc1EFKFdkF6bTgV1B9Ib7qw0uClyH4H9tx0kRwLDxUjW0BVxHg67QzzH4QclSWEyaaYBvVXZ8z/a/3D85uyNeg8seR+s1+Of1/n5+fh8fHx8fo4v3DreVyDHb+S/Z6r3zZJ3Kfp5vf0R63vvBi6PRZLHAzNOBYpl1wkupOUAEgAhX4q652OVYbm2m+DosmQiBUWT4QxLeH0bpl5bLpLexwEStW2G/lHHVtCQ2ctNqfjIiAAZVUMdhLREW1Z2Fng163HsSmwXHPBC8LayqcQ6LWTnxQUZMrrbiuPQpURH4N2dcJRyQ5Qwo7iKZNufH0xPXfL/Yn9/YWF/X73jAwvKI9m2mZK5rnyot9aV/9LO6a56p3M+6RH/OtvCPnd8PpA3LLp+drZx/Otr164dHx9vjI+fnIskl5jZaDxRZEKSEzS6dnAcDCQZDHycJlqwkOj+og4LJg41gk+Abe7u0ucbaIHtuLEW0MwMqgj6uSYNDnuWapU/yGNhkyRjO5tNTpoYVOaYXKi5T9tb6cJJm7iG3YtCtnV//Pr19m30eRcXbYQDys3oS4IkR6bILu4TA4qAdi9Qb07ohuTF4XaOirLH4O2u/r+lqjY8+fsPHz5578qCt/Oo3m118ofl5HwD7/R/v/+KKty6ynJSXUSR8J16qEeQA/nmWxejUuapGFF3yFCS4LNs4Nn8anOX5zmU8RMZMxdYM0zZCGBJshot5EFkwyS64pXVDqNbxjxKh1k1uyjQqnvh6mFEBMs9h6DVPimsfHv+5mD19jo6FxRpV2IbIJkwu7JcbyyCAyCukkPEWAMvj38ngaSRyFS0+Xk2GJWKWUGHt52TKQM9dyAQqNW2tmo1eBt8agMh+fSPN7dnZ3OXsUqDyWKBuXVLXff+MLpsUeyNCfLHnD4/D3w606JwRLFWiuwN7uH7nk+aEFscYtIByBftCwYfJzKdrwDyzlK93kS/a5XRpFOcQhISRIVM0OA4tCq3V/HjeCUhGJMZpfI6AhJonj9/rgbkkgqZ/r4k2wv38/PX14/c1fV+okXBqYAedT3mXReCdKRMdQnSYeOHZGxFC3K0bXaBNg1Y2E6i/0lYnc3NXbhg+N8bsiul5ebm8G1Z+uuS8j93d+MmLUi/X9GU9daXI8Ub8TjKCfpu2nPcO89H5vVPRJIb+VAJtxnOJBliuw119u7dq9XuiSLhVVR9CGeECUEWRJFN7oreubO0VLcQSo2mkVvLGQxu2xKjBJmiqsSGh4d/2tk5Qbxbk4aRKAve8LGgFAmSI7XT0JVMSY3y2s4GLGT3wl3PiCQvXFGhB1IZcmRDRziiyrei7AHhpqJIlASJQ5xIZGRbw4YLP6J3Q5WUqhCRzm/tco5jBvzqmhHwcyT59L16saIF+3CbMNclDyXIFumxg2x0GMF5uYyUNiRLBrxuJ+RdSGsTKkHsNTFMPjthedv01WqLO1RoXNFMI9qxdiHI7ZsAid/GMnkCWSRup6qE7IFMDUfS0p20vpCsGZ0ENztr4SkkQQ1w0v+ZFKmNh7RLC0nVnfCUOlw4iiQeEYz05GJ5eBCclmUleCZTsZhJgG42GU610NpYGU5VeFIMciZPLTDptyOLsBysCbncWkl+d824PD1FkFe2aeaKmeoRQZZEYlBsJKicIVNhSIO51OTemkjyek+sjtc9Ut+EzV0c5T59+N2lRkQtzgBRtXecE4AQK8kzfpfm5rZtSKLQKG/P5YxFbmtVM0dHTXrF8EyS6Yy5i3sgWTWh8NpClh1OxmNpb5ehDbIcp8cmOc9JI7DHNhE7rRMWZMCUcsTJWNqd9IXSGuJHOJgEyErQtKMxRk38yMK/YOG+zAy6hpl+pozARt/CbiOii3fLEWRPPLS5vUf/8/SbmzBzwSIUGSTIeU3GDyQZlNBl66epjKgHZ3TJkm9r+V5JuXc6R3mGuCBN4fVlZTwIBUFSiUSL2ovFEik7zG67zlP5l0y7AQRZ++rHhvFvmq0ntG08jeY0MDBohQ7CyOjQGQnsXVnOKlgyW0810UGZehZ7QQiHnUMsexmyjckEw9I2NkRU7MWHHBJmmZ7mVPZWwgh6KNSnwi5z6KF7y2khe5hbWNqFLcsM+96ntKSHxLHy09P35733faZQbNNdAyVHofe6CB9ppaj7eCS1ymmhtmiLrAE7b4hbvi1q2GOo8n9lqc2R2C45DhniS36JqH65TwlJRbhPajuhZwFJ3kI3C8oSQKJS48h81lyrZZFENnMPNHKz84wGjWVLdGmcROt1qj7ctOuKkfb98zsOgEyiqApIyhUgqJHfaKyNGt8quppAmu+rZFxxb5ZPTePXjTASZbRRDZk5Pto/JBXk5K1BH5d6ewihmOc4NicGgTO4tWARlwUYx/SktRydvH379uXLxspPCRz4liEjcc5ljYjaEL9Hob3drcYNlMMcPdAyQmL/tsmsX1YRCeAYl2goXTqTdMGPJzjYcWXOBbRFpkNkdhpwy26YURukJGdQYVGE/pHYWa6Lt+OS8ekyuaor6KtQfHZ28aEA+flUlSpH3GINes1P6KwhJPW+FEDgShaAX7Ais1dVyXFc4Id1gbJqRHhzKHmN7zeaTXKYGyChT1rHtJW5TImiLRvoOOsWs9V0BsMfh4hIPnhkTk28284RYJzvr+hTpTWzfePw0Y3nmoAUL6/Kc0rGar+r2/X47gUS22cT72zvNyYIwZvRdIsCk6N71MRjFt804EIfxBNJrEgrn9ueUAwkwH4wpQqLqF4BJNS1DkyQvVq9p8sIsD6+KOJ6veeOKiDvLBCL2k0igx37JvWKBuhe61qfDNFKohXuiQTccB5WIRnj8YBc4S2PkOUI2fARoCSOihYDSJRDP0Vq77e8GmKSa2y4kxZQ5WlNbqneWA9+tFg4bU6IaEy1aYZ1u0jZ+X4aJaphBkHNNKyq690sXJicLrUNOmm4iEHxLfh7KABfIrHvkiYd0c3c2p9z7s8141ZVZ32/DI4Pjyn9CRV7cwuBWfJjBshl55xAZqJRkToA0uFnDjLREInrGnpfqeuq3sPNj0dFodQVtRD+8/z2lkEgEylzGo5qSI8RIEOh2knkT31ZU0kMU38n05u6DiDv5FUQ9vG8+rFOJOluxBtoekE7Mj3xn3DbJiUze0SAOGwFnNVIzsrmhO/sDiNaaayB5qaMC/i7HsBVk3KKSxky7rAMvMPzzAC5vgdccdkasDNqXGPxKMNNVf8FElt9P8gJZL+uJWuIKRf92vSYymNmtNRAG6kYBQASRyBkWQbhdf/cTgwCiZcjf+hkOWpkxuUmlD3cqV7XkdCuXQeStHNiiptvn382jVDkkihJNOkpN/pZTVRdCTl0QCdqbdHOZPs33K/ec0lNuV0njKOLfNgHseaaRRwKkPug2gODnYFBYuAKSEUZoW4hoVtiQPA1k6soqb/7JGKgyQ5wg30YQAiWaVTOZrMJgdS5zVfjC5tbwFFFG9zDH6jhXKmJbOFrnmk9vL5+M0YcpyiX0CfMevw9jgr8gEdJuPnONXiEYntgiFPgLA5nsyn9FCgYsrNct2jukTkOKppxXpYrvxRybatI69fIXCdXRiMAaelV2/7Cd3QAuVo5VqVSQtF/qg1ENI4QVSc9DiLOuHUynRsuia5dPFTYXEZFcj/sC5AjYgn6Q2FA8ztlozBISFWj2juR/drKlfVokNdaXuoPn/KE0XBYli0BslExmm662t15+mTHx/EzR90zEHecFxp7hsVZEYA00Yf8iNmETPdaw2fXb34fIhpMkyUThYO9rmbS7eQGnQDpl9zGaUOoWIwDxZ4udg+nwI3pm2d5jx2iWhUDkvKht0w+yuFHRpIkqp2/BpCBb/NmY92yq27zh1sAsp/4vivSudJ87DE9AGmB0uhRkEa8hIrurGjhRxKSL/xw9DvxfceFMURpfKiMR6NPRtSIG6nH5V1xu9vVAIOZuWeSpQNdWSmTkU0qezLIH0AdlRDbrZbM7jqkiQCy3N15cjozzSyf3neI3GYXignBGVoDtHB67Ja6QC/dK8IBmPRTdJoQ8QscUjZ7oC2rMG16TQSGARG1AY9sGaIyjQql50IL4HVwmj6kMgd6e5Yx4PhFdnR6WY7mWHJ/gv+gvjMXdLGmjgFkH0zy4sMPWCTvugQSD0RGWZW0ofbRUUgrJLnzY6HChiwJyli45GUwKQhkHI9HqoOie484Vvp8o8ZFNsc0q97AE8lVTeIoK2UyTmCP6Daacw6LEZBgc1MQx06Htjd133yyu5jtnJ3tp43y/PFu6aMoIrW7nkyOgSuu4A8s+8li5RthoaXNg19dv6n7JvkFKlEl0rjqgJD0U5/t0k0Me4AvVeQaS/y4B5iGXIW3EdeSUoh21Xgv7JCTqInuqkz91Qr9L8ftuCtKQbfeG4MFWmoF5PcKHkRftznC1oRl30QlgIzp7PT6us7GDGQ5cujnn8mM+1+dzeKL0ZiLQHZUjOv3LkajiwrKDTNKyKNIs9Ez/DI15QGxppkMpLSWImCDVtqdb59AtjXnDTS0MkCwpiJdOkfLTufgT093zmYH4PLN4+PZYauVemzpy03UTFZU8+Cs5TuW+81sthVpRZxOXv39zXf7DT9akZOqYVy37SRZ+dLVeOfUDLLZOVArI1Xrx+i/TuRwZ9CgOosJgCVsULMqeoefofTRvy+HL/5y+Y9Xr3IU/dRMlJw0MAwr/+fbMYC0VL3e4xC7uJF+Wk8LFaWIAWgd0m9EzVNH9MV13VWu/8vGHZ1Ev/zqu0xVHvbaxVj5NL5bfHpRpba5SmhE1IDZvOk15l1vjyLJqEnNRF+QNSOwv2Z3+0pk8NqLViWENrDqQlY0abruPHnyzenh4c563WnOz+bLjhg2nSN26mS4WARb/16mQ21xuj479tWxFmXPrt9Nr7ZX5jJAKie6np3fz1ZDlhm069VwSDaNiNBsVwYeXMbR0ZIR3AMDRUjvvbZtmdQLA2R6khcrj0IdtTVNveHlT89+/fH/fr78W3b/8eN/vvoyJsjhJx8IARrZeug7odLLbSZvoWkcdvW0gpY3Q7IahfHRoICA92gfyb7k1+k6v/0is8JxzylG8eusUGIAqYQFgIxWQWPSQlptonVszzfFBUGzkAUjNGQvitqN5VHXowahtO5Uo9cJUn2nTBF5862d0x/X2+Vs568/rDtHa8idjjgVR2BGwWwSIMrW64OpFlD4tSK7fQud5jfrq/XK3PRX/LiAu1g8LiFaqIygUCLHlWm9oqgupxy67Sau3ePONimqAWJ8fg6w3chAtUMlQyuJQ93Wi76eJOUs9RZfPyfR+fjy8j8/P3jw4HI3r/eQ0GPwHyT3H/GIjDbJuL2nx7HWA5rjeq/yH6ige7lG5JkJiFnkf/GO+5I/3WseZJ9nRjjOneIiPNdDOyweKXlebKSoJltc1CzN2pyDKTMCTCaKmgduaEwQooBhc33V2GxCy/35CgA191+iIy/nJz+cLkDlm5vB7PRs3QwWk87V8uSo26imCicAcnkwmWzVaDAtl6v/t3Q9oYmjUbyHhTLQdYNC6EaE2RKhrkmMkcTM1iWbHOzidhtLEMuW4iQe6qySkQxLWA3qVpiDhz24zE49iYdel1IhB8GcBkYGxoN766ngpTCHOXQKW0rLvi+7EjwFQ37f+35/3ksQS4AnciyOS385u34uOMs+6t41zUZjjLxTo0whqitB0iVAcCXE8xDgdgFIEnwhysd+/ZV2KdW2gYkpzDcomIaj8SlwXvQY70iY1jPo8sEPk1GrNbp7eLi5eB8PnTXnIERgb/4D8jXqPyTILg4rEe0CwFL26a/IIkJdB4LwQzgFTr6LayoloaAEBQ+JGz7zhWPoFEFmdCGQZagcDrzSWehEcAXKga7IsYpj0az/8KKiVN58qiBnXlDIkuHJdKEAQgPKLNf9KpP5NnpeQqx73jvPRNNBNm3Anob8hjoTdZ5FCuRPFmJs/1U1nar+bmyCMkUocFIFxyIiB+DFdZmrGuCuxs0aROmxWQU8UX+QsXECK5GalkMdhW4Wk3zBUiFO49H/GxHM4M/Ly78G070D++3W8O1w+FMyORwOd+LJ+c5GfGe6P30eOn8yeTwa3X24cx+vrq5+Hp7bBzqDRV8/+gz92wsknWCC6CLPEMyGCQz05EU4AIvR7XZAypEGMriECRyVCaLrSlLRL8mbLcVicVLQ1XQno9oLQsC05pjByJVUGs2KRdi7qJVtxXij9waIkIWUzMENpDyLrlRkXuQAIQcwXC4BK6/ubMbabedd25+yimm677EKx8ptx1nyxqlp+XMWGdLN0avt06OjU6NgWIXtFNS2qCSE4ex6y+AjKs1FUmO7NlZt1aymwQuAE1T1nIoRJQbLwQFEheMAIUkyQSBEDZCUupmt+cM/d9e3tx9d1525bvLwcNZqHbZC+Vbru/xotLY2XZtMXj5C78O3ZrOPt3E3Pvwifjmd7n21V3x5En9y8uOzYjGD7fpASp0MiYU7f3wdDi/saDerM2hUHdQY1PrhKA2HuJnSpGnIL8m/AxFHIQVGL4OT3dfXaUVrnMKpK2aj7y3rNB1D4+O2E+OdHg9cyPeUAquQwYLjVCzYrjIa6csi34aa9PvVVgVO8pYybTmWyBYsK0KkNmFnx9qiWCubfc+JiZtKIv3L1W9HV1dXVY5K165Qb63X9/bg5gReTuiGuG72VJPKdOxBcz3Sa46pMoFldCayS2gkJURBNMmoCr6Z1EqgBIxK4IGdm4cP97N8/sXP3zw9e3YWWOQW4ey3xQC+yB2fHTPIJ1HH/sshJ+fnk9ksP3TdWxe+XHcjFEq2QvGku5F8f39/cTHPRMExDGxYp2gmCx60jINok13wAngQjQyBvCOYUGWqtLL/fdxnySEe2VbNIEYvFuWBKhpKr1brYcq/JCoYnvp9utkAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUgAAAFICAMAAAAFypcBAAAACXBIWXMAAAsTAAALEwEAmpwYAAADAFBMVEUUQ5P0pBTrmAb1pBnunQv9sCP7qh3wnw7yoRHtmwr+siPzoRX////4pxzwlxvtsoncm3X7rBvzmh7ihxD7riHtkhjoqX/YmHH4qiDlpHrpsJDmihHjjgAQQZPprITojRfin3RpMwfXkGQ0EgRjLQXegg7okhWARxrmkQHvsIJcKQTalGsrDgTlq4rslxjTeApwOgzgm21OIgTipoLeoHyjXzTtq3lVKAZ4QRLZfQuAQQkjCALolQJ5OgbrtpmBTyaMUiLQimLwuJIcSJWHRgyxeE7jjBaWVyOITBrLg1rTkm3McQd4Rx71oCJbMQ+9dlCeWC1AFgPGfFSXVBaTWi5xMgRnORS7cEevbCpXHgLIhkLtvKPFgDbLjE2KVi2tYzhwQBi+ezYFN4yzWwdIGwO5dTC0ZxrPk1ikZj6pbj5DIQqwa0XShlM5GgjflmS4cSTCeCgaBALFagbRmWTVk06qUgXAgEKZYDULPI/RjEOPTg+kaDPPf0vqpHDz9fefbUa8Ywa0hmbFd0jNhjmvdUTdhxaMXjusfl3Vi1u2aD3WmVqxcza5f0zDh07gigGaZj2nc0vxnh3HjVi3eT+rYhameFa9hVidYCmhXR2nZiUgR4vtxKvAfVvx7On0w57aoGfDbzbhtZbplCPJk2S1gFjuz7mSQQfq4dvapnS/jGLSnnDGhWPdro+KNweCVTXYhg3LgSy9j27lo2NNKhPejCbfnldjHAMPAgG8ZijZpod+LAX0zanh08qTSB6eRQXJdxjfrn/Hl3TfmkqeUAjjlTN2SyztrGDMjGqTZka+bxWtWC/jvKTqpFLunjDonT+iWg/akUJlhLjTgB3nrm/nuYfxunhxIwPSoXzLeD7a4u7XizQoU5w6YqXsw5jYxbppQiXvpkTdkxHytWlcNx3z2sjdjliCm8accVNTCgKiSSfzsFOar9HE0OTzwopOcq6zwtzQuKrKale/W0cALYfdiXzMrZq3loLUfG32rjTJoYrMrAu0mQgWQIpzalySh3RhV00roU9aAAAgAElEQVR42rSXT2gbyx3HI2zZaSC0AdGn18MjvGt5h0DPD9pLSUpP7yKGmcMcRnMpbwdmWBjaQ2BzGmkPXhmT8OANZlsYLzpsRRZq3sHrJbiIJC/CUlARBB7m9WLI3cf+9NeS4qZxm85KK+9KtvHH3z+/ubE5WdtL6+b1VumD18blur2yqrO1tVV99uLsxHCkxVEaBMQ5pGzC+Z8QwZTVMBZaI0WslNLYQ2cIhydCSiF8n0fSSqOQVtYgHYgAEQanjFHEZRgPh7kNqRCjp6mV9m5W9PSo9/b1+Xn5TrWyssrjNXspz17GNxbvlcu33l03Nmckp8cVawXaVcc1SJZmFFdAVhcgqzs/nCBjiOrBX6mzE55IhbmkXrf2hAItlfUChYiSOcBNXCJ55Iz6h3/XUuT7xI8dl7HKOCdESjgZFKQpFgixMIkIiaKIGxWkSAXBKNXB6PRI9L89Ozu/s1UpT47paQFzCeMyyCV85clj/LyxwnHzv9Dk9RR5uwQHvGysKXILnhs/FKpIVaZ10StOMmUM9wnxBPa6rg3ULFcAx/wBa6007hOcGaMU261j5FGvJpB0kZUo8DBGdyUfS5RHHL5DY0vGn0EYqRAway1GoyIFjp549v3gx7cXF1tbY04XE1iVGcHKv1HkmhYrk9NCkdvrerw5fdz8iIosXWnsubd3XnQ6WU94XpD1PwPXcsN5i99FgtgobycuT3KDFCo09nYZQpQxSnzfSiq6umAaUS0wpn6tLgC9r5g//kCe+Cbin1ujdIqD+u4uoz7PJAn0iyJQ/fzu6VOd287r84vqVnkCci7JVYzlpTUT4+Sr8pzlXJHbk8eSJrcnx0dV5CIkb6+xHOvxJcgx6OkjAbIBYxrkearfjxQxHS7l0EEASmtD41NOAm9XjFKhAVtL5jECtysUYLiVQpR66aj7u6MeRthTPEJCMAb/iwRcrbse1djxLo0cXGfWGgO/MzvLsv53b8+rWxOOFzOfz1Au5FlZA3lrRZtzRU7cvSrKm1NR/kdNXofkxNWTlByj3Jhl5O3qzssiyzDuaagHLk3GcN3zsI+yvrWWE6Qw/qdBYZ5AMg6kdSHWwC4zoQrlwSPZjgilGSEktCaMuQkR1gVORdGDgKRRy6t70lnnbKTTU6uo9KOEJ1ZDhPaC4gUyb77tgMPPL6ZarFRm/D5IkeVVkNvrdTMW5YeosvS/1DY4Gk4XPZwVQQGNyyEXc84woyYQelwooCPdE4CVGRXmuXTDtkv2Jfd9xHCAWa3ZbMmBBewaB+DeAPmtg70WBEMYRlDiHNqJE4HuhYgbG0uj0zQ1eNen9N645dPT3mnNfvcjSfud/tvzrSnIKcW5ClcwrmdkeeLsypIit5eCcobwKorXUuSc2zsgN6aFM27srZ2THHx3dKpk+3kuI+U3woGz/QyaI3dpKiDzKFYUGagOa6STzrX8JG61mkCT59GYe70WUmh3Iajxm8c1T3teDSH/HmlCJMQcArLOSKMBojXjgDxKc8kwcQPn4+L0VctYJNK0O8rOLu5UFgW+TnAV40SMi8sbP1kLyRnKj5SRG7ORp7SxAnJq6tK4YjaqL/tfHhqtu11+2G5bhah8s9/ez63NY6yUoKEMleLHMfQvpGHIWIMZ+egXjkR7e5EKEwmpSjUKCbxiHWTAJ6yJJ/WHj6FuoKcJij75WiGEv4aAAGmLQHFNjM5kA1iaxCpWT8d67kHEvj6D2pmockmR6yAXfp7xHGtyJSNXUvL/rchpOJYuTuxAdrSHP/+Z7XdoIJBxb/YP80Eu8xxc6fYPDw9zmRzy1IOuHg5iqhhRKIojmR8eExXJXzLzWUhUaOJfyZBAI0kY0x3xGvvHnNdAmpS1kgcwDBlE68ivpwIGJ7gqQKavulhZJ40PFu/1ivShOHt9XrlTLi/cvQxwjvFyhCzP55+5Iqe2Xib5cRV5OUhO62Zj0jIb35/0ZZjo1BjrLJcnQiAo2BxAAI9Iurz9zfP9PG+7KIJAVLlNBvsJ3OdGhjzce7MvdQs02gpDLFjrjz50NlME3v3i+V+SZBiTQKTiCfUlp9mYdMiMgbnICzA21hLvYV3UGcXGkW73RQHzu6gfPR0BynlGVlY5Tp09c3T5ip3N9uasaJb65uaHKfK9KFc0WFrOx/GpqvP2/iAZDg/yY8mN+zsMyx0ZhQpGbkbcb5zLYUFeRmEYoqxjcyeT/OcwCSGG2G6tBrpsQmBGzYbC9eTT2qt6nXm7nhceHPzVRRRGyNgZrnXwGLZGtVcpaxCnqO/VqQfBK7/4BAWwl8Q+FoSjUe+nn+oi7T4LipOxv1eMfevyi5kyy4uiWbX2ZWtvvk+RpavAvgdiaWOtYiarOiZZ3Tk7hPEwjoftb9pJFhAuk/2EO0nTv7FAKfcliNQY2Pu14B3oIx4nWQehjiF+S2nYywSpH8eJi8PMtCiWlsA9gneFx6PfPu6yZoPFh8PkwQOumFf/qv7KwwghftBkYuR5PieRtYji01Ee+34IW55MG4WDTAtRnF1sreTkreWuWWvuykKR20tz5Ob2R1PkOsXpZXVeN7/PBu4BQk2IwTwxI0EJWNkIdt9nOjMwhd8HKdVqWGfcJXGSmJBLn8BuBRFDOsaHetF+BHNj8iiSxwfJn/ecjIdRGDVBv09gZykbfisOPa8BwH5tuQAdel5d0DhPiD6th60WQYzYNEXBPUl3PfixMGkdpcWJ6qawA1+ffG4ts5wavPyutbcve/uaGfleRU76+l1rA8mdou+SxG/KTgbzHOQUzDWZwqIRvxlwKJrIr31Vo4qHpmM554gp1ogeub2WjOW/KLPe0LbRO3yhzVJmBjsIWz8dl7UQdruNXLajIXBLDmIcurYQHIJ40XtEbJLmcDkJJBQUDbJDoj1eSaSVFNuiH4SrDBwtHL50+pBPcdweq+mtNmcXg2F05MtgsO/5uJ+TJrXTpOleO9iIkD+Pn9/z5yfJcTBRpCLInY5sY3YjsrRMLuc64XqGUmw3C63bcrImj0zqEcUI8BlFvwxkFfpnDSwLu04g6zxrmj6LeNCRHV0VOc+PovcbejuWZaIKlQOhHHzdtvd7xbG/C8iBnv3Pxd5Ifup0J/4fRh4BmXiljzcv/OhXzxqVTuAOiVxXVRQ0izC9uhi2Crub9wvbIaZqgh3tZjsbMwjVHemj3KwjheFG1IyMjzWdM22K4iiWotIf85S1Tnke5eeha3NpLWPZyXX4VomXZYV7lKdsR7Fs6f2vVKb6e4HyWWxLkiKrFOWxYDy83N6hmTwBuQ72tirtylasfvf8+f4PjhYVXYD+8OhrEB4vsw+8dmnkiSR5dgCCk0i8PSNPpPBDaP/xHen0jGIgx3Fcl6XtZkOhoXsUnv6lALoWmV5JZ3ETZFLisYegz7k6MkLsmm7O5W0tm/H8nG2ZjKlAlQHXDr8xGMYwGaxQAmdjz/N90+SjX/8mMky44oam5ymswn9qMyVOsRmdQSGURfi4BLFU7+w0xJrO+Aymq9Wd79UiacRb/9273M3IwRNZ8uQ+cuDYtU+q5BsWaokuRl5KnEXHvgsXToWz7159K1bCiMQVFSsC3yx/pCJWJ+81n25uln/iMIxYksubMMNbDWAjJ/NRK8J2Kwup0GchZju7Rt7XDNc0XU0zXcV0k+uWsR05xDKSlutkcqZL1R6pjG/cTWYjxwlDRdxhqLSmgOUj3mY4sU07xQ1KgAQgcHTMKzQLJZWlGAQlR7eRrFe2jnLQMZCvlcX+nkA+0JsjXwnlGWU7kehlZOL86NPj2ZcfVGK9AjkY63WksPxPA7VCUSR+Xi7/tkx0mqIoeSsoNhtbSCQOijFExkhS2UhSFJlg6JC52Vw6bWVS6XRqfHk5TbGmltKM0FbNiZXs7OrdpGUlNdYTaIFbzmmatZENrysCQ7MQihgcOjwSHok0z2tWuQgcTjMlFYIsIR/xtMBCT1e/B5rKFbmxd/nd03piT1vsf33787aM7AB5LiNPEjJx/PZBbBMdfwomi1UahxGuizpPl+hiuUFkXaCUoBEFDR5cmTWL/wwJSKVj+iIbFRGyecfKjU+Np3wtmVken0ovw0mD0WhLt++s5KY+mUqlUtM5M5VMalnHcRmBVSg/ZRjWbqtlM7zt5z0RgXu5goeQShxeylKeztV0AgerKi0IfJGp6m1dbajV+vP9d/tPHe+XobL/1T5y4Dj7nFiUD5y9/gEcE13nrRl5cPHeVhmTgEeyVMQsC2ZC7wgoVmUSOjHr6XGjGBY2CSI8zitSq9CCf9o3HVPHkI74wMhNjafhGLOf/XFyemp5cnh6eDqVy2WSd1bvApQ500w+uZHOpSaXTcOyrQ2IQ5Zmm8sZw5bCv1qKT3mUvVuACIQ4mmUZxXLMesnzaJ0vdrYbuugxDNNu6zqAWt3bGzyNk4fu05WB3rl44qZNLyUPUDstlwN4l7qeZ96fOT5HfLzZ9wCkSAptyMZSQaJ4WYc/VyVxFEpyTL6gaL5cDiVeTecV6IEkshRZSVPGZoTAZ1WFquWX86bv57SlpdnbEyMjQ0NzQyNjs8Njk8b62pd3VlZXMxtrT1YzEyNjKZ/jfFezshtZy6QUK2IVCX6NUstbYHPki69o2qsxCBcjjHRaUnTi2Gpdl3lORCWxUhFUVP2bvLffC+RhCx88qjld+8iBk237Yu929wzXfoVj4rx+eJR8Lty82fcYUhqWg0iCPujYCqpzdBucpVwISiItyzJ2WqHeZnyKtqMI00q+Bk6MnEj6k+uaUPR8Pw+kAwpOjw3NXRs9PNc+uAVoplY21uZXDGvlyZNVY2Vi4rPZ6Q5n81QmmbE2vswi73rWaG1uZBnO42ocE0QE0YLLE7u1qZYUlXJ2C0XopU3EcTSqx79ApXYFVf61f5pADh7Pducx+M5xiuze/3TbzenjnTi0nINz6RwgE4dIJhLw0vfsPQlLPBOUtwMwypjHoqfQJR4YoopUHBzsKizP44uIFJs8XRUYwvMBQRzkIatw3WUNTdNS02Nj86Mzf5iZWRhdGH34cGFhdPThraGxsdm1b+eXZm9dzUxOr6xMLv379l1Qgk9yuUnNSq6btKgoacPKWaGDRRZ+Nl/+sSogxreaZSCmallOAKIDDUGmBDkIiIxKqlCl/9N/ynQfU7JrQz7QvdjtZeWZ/eaAkzDiHc9+C42813eokI+lJh9iDBGSR0rGlgVG0EEdJVvWazUtaj1tIS4DiVIqE2wSB9MydGzHQjTFyeXd1jdJ4+7qZHro6vAHMzOLgN/C4pWFxcUri/B+YfTW3MjY6trXN+bm5m7NryylUrOfZZLGqqENzyVdn0qth47iKkzNz2RtjMXf1fKoc49NDTdsPsY2XwZ+VkuqrNYrOicSolZkeasRiDvPoHm/wbj7e1z74gkUL76RkS85+dJz3kIjAUu49LhZRFipikVJrjNZ5+eI+1wiQbG8WdQ5j7VbhW3c9kNJjYstInseapZtiU/lKYaBThNFkWWZ47O56amhazNXZq51IPwQnh9eASQXFxYBypGhG3fWvv72xYsXEyNz83NX5yfdJdDN26uTwyOT663QChmOddiab9vCn3UhLcifk2hTEsFq6sB7xHDVeoxRqaTX6PhndInIRBbFuJPM988DcqBra/FakjznNvdBDkpcevNkJ463u/cqTenvmG5XSKCLiuMQysNP728SHAUsg51ou1zhlI37/6PUilrbRrNoQ6Z0mTDvnZeBTAJhQ7oUsyUhoTiBmCRFVaaxUb8VkleCyIrdZuQioaJ4wdvKeLqyRVLJdWymILLuguoGk9r4IczDup710KHbsVmnBALF7PhhoL+gj3vlJI2TtLMdodgmGAxH595zzv3ui92caJgKqUiVvCabyMtVnSYpJ2IzK96ZyOoY5hqYWA4NTIwAiMudVwCzw0qcIfrjDwqj7VatVqjVmGEXMzY0nl2989zN+GPBLELBWI6n5QxK3iOpMJeqUwqdp/cCXkpRacicZCBcblrlRkMIGKJoSXuq9IO29+bnt6fH5ccS99GmxfFsc1JxPohkz8cw8gDK+z8Vpfw2G1YkqSrrvMTVAypdefG6EU4kdAu6/IsNTbArlV3brCO+YvO5PAcGRbJo8I9iAqGZlZXZdR/GhAZu3RqZuOVACGQEQEc6KIYcXuLMIPPgFxxvhwDMeJzAB13DY7O3J9furE2OgYM39TRoHASfjC6SPwYSKMPaOchVGa5MG0laZBH7aidPh7fCiOdFSymDvQyHX706/6unN8eGFkcD3lNIfhjH372nvN8faO73/rdc5kUwOcVyldI1MiyA09AMUQvXE5XNvCHr+V2eBtmBpExK9s5OnmcRUpwxDx1GKJNNPvL5/G4CDw0Aig4JoUNCRU+M7KM4MDAAb4ujWL8r/rRWKuGlkXatVSsUsOHRUexxdDUaTXjHhrwZLvkY7GQmRRo0TaacZ7ZpNyXTev3tDk/TdJb9fMO2yhJtcrQt7jXKkFOrP785MQk6cZR45jBqn2iUJ1YvfqW0ezqyfaTcDqS97xnnnu/taZD5bR6Cl6SwYHQgztB8nidJrs6Km5ubNIWyJm/nOFYVBE3MiQlWECobELghYwcCkK1X/RhecsBbdgoZtNq5S4BlyLmd/8PtwgcxZrH9S5Rpt0uAZrvUhhJ3ueIG7/ZHY8g7PZ6J5NKR9bo3ycFzJf+ZSmzvmKA+snhhx87nRTWLrJ2KpUhkgrfytCqROl3Uym9OBu2zJxn5jopd8v3J+5z5+2cX71LOIZK9fadJeR485L8sSH1k84+8zNGd2SDHg91w9k+c1QopEEbg7HJsiuQlSNc6SoVTic1/bKQNMVJPZdEsgzsiPTIy0SnkUhvH8dF2Gx/FcQDMKeuO5gCSmA9bXC54akSr5YAJmLeYNrE+OeiOrsaCmZXpmTT4Si4VBIeZTssst57lNPi9ABLtfJoH5L5XNUunFI0lmza/p8gsn9OL3cb8cNPi7Ol55CfH9fvjBKdnn5Ld+abvwA/1HTbHQ625v/PsJodYu2KxKVoOBxyDyCpUPSzZIgDL1gVKNnRKABFKgtN0BrCG/Wz7cRJSn3cWw12L1zpoObpSwnGihjEYU6u14BUgLblC1zoV7tgg9xLIUeubVQbaJIAZAtK2C3H3MD6UNYOebHbcLT6LBhMoYF5C+q5MCcib5S1+L5Dhxdy2WG2YiFJktQFPm5LorWpRpX8vB5xFjGMx++wpsTlW3ue6JefjliaPMfKdTPd1U/LqZy9fb9KKpcm6JiRkKhCgLUv5EeRGIUGQVSGlQtARIAZbOStn84G60hSfbedFbybjnRkbdMg4sDyyLyvgGDHM7S74/b44/GEMAVYHH4XvwDeWQyXcvwZIlqLRAkHUarV2yBH2VrxA/Oni2Lq5FJwZX496dp9ATaBsTIayhjCQ0MG1UigJD1rTiiT776KkbklkXVBopdGQpET9sLgPETy5+3OEYPcA4+NK+90pzvEuuQ9jN5BXe3r3cnY4TBqVbZLNAWIqzxe3AoiE9p40UJ2SrKZFprLi7rd53TRkROr5Lz7nIYp4M+P9g65Fx+k4l4Migbl9fp9v9Tbox9LSbVAgtxvAhBKHtgl4l4jVR5hrebm29qBGEK1CrQQSvwgf3Fj/xSGvGYwMjUWemamkHua8XiqZFNRqPbmza6hsOoKqPK1uZWVwlV+XFUkI87TyQ5Wi/vof6uWnR87x7Af2I4/vUp0MOB/LSGiPvQdA7kfCA172XP3s75pRpKplrVLRE6JO0aRoWKx54fF2jhYyWUoy8roQVlVt94UhfM9JimGIkLGzscj0xcHRxWtgdBzLXcIJMIaTk76l4FIwFvNc93hiweDSqs/vLxTiGNHGofYnoPSjHqY0skw8fxrFWkyh0B65BZJeIuLui8P9K+tpz/r45VmETBnVL08jWqfCgYyu8RqtyUggSUVVZ8ympKiSRnk5UMdqmS4XlZ+gto9OEbvnkWfPnOtyPu8G5aePws79BkYe9MduRvb0vhTSZpFWJNpIi3oiqzVF287xevPxrq6GOYjTtoGytEXz9gUZmZr1NU+XqZX1R2uT/aAxAA6YnWuhUQIbmvR9denPN65fvz4/v7CwMDe3MD8fu7G0FL3hWQOKxt21lkNK3LPG4CPLuPvpNwWGKBRaoVudrlBjsLFhv7keWV+5PJ5VDDOAZsc5JFMNYSVQ5nVSchYK4RFaSbKxJ2kqKyNIN1XIEJa69eZtF5BvP+3a/jlzSmi6o+K538TIDiv3DxgcMvbd3x9X9DkW8g/KlMGVi6ycBF3mEskvbN0gOa6h6JZSN638rm2b0/rOdxuibnJ6fnNDZBOJbCbimQQ+AjBgvIGNODM2CSj+7frduwsLf5m7eXPu3r17c1NzD+c98w+fPHkIl+fGqg9Qg5aYjmOliRDhvnPneY1w+2uhjmdqE4XnjGtIDy5FMtOXZe8KktH4uMCZpICmvaR2U9lSAwFe5C051ZBoSbMtQbB4tWxZr3akV28OxrwdFPex3AfzTLf1OTa8OHGq+H+QPJinHSp3X9/xWNNTzWnsCs3Tds4oUykRYjOEa1UB86YoSBZFA1p9Vt7ceAGSrjbz2xt8OIVQJDLUD4QEHCcGlkcJZmh25iuA8fpdwPDeTQDxy8419eXDJ1NwXblyZWrqycPYJfCbAwP+tJspTZQI94M7D+KYOx4vOWJVardbGD48MzM5uYQux3Q9YSays+NC2DQzqRWvjCh1T8hAiUig5c2mZlc0KvU/ys03pI08jePIWjwrRz0oFX0hasoF/LNEvSNiqaalJWnxhtq06exsxmbAyZzuaZQZIjFbxE1IupOEav6YDD2YLeOLJJRgzeXEF+ViaJb0tkfC2VYQJNCwCAv38qAv7/lloo2NXXozmUTfhQ/f58/3+T0xpgijVdx9Q2wU3p++i1+jyIaayv35P3ZoOpqay1myqQrll/FnlqAATa/kp21zRhHIOYJ0ajcqQiRxjBTlqSDOMfEoa6M8pCh5rR69xYaHlZ0XsYHxGeQGB4CjRvtHwHj722/LUgSMsz098GppQQxbWlqam/tbem523fhmYUitGF9ZMY0me6FPWlpz5xITOVdpGtmgkgEbUw6poH7bhWtDU0EqgNPDEYfHizuMix6/n9xgfGAfocQEfdCXc1zKaHFAV8ERhGMj8+53VV3k8doFtD8NtRTra2aT9dVj3k+O1j7Ed9PxELLSQu7HRSNlMab4GEtacIKV/H7aKjLQcNhoxybjo4xBi5H0+3mr2b63sxYQFvUee1inAj1CY3hpa16hVil1GiTH7wBjRYyzALG/v7+jv6eluaW5o6OjFZ6O/uaeK7fvD3UrDLEJU1YxbsCyS8vuw5zrMFeEut47P5N1jU4ouydovdOpubtIeOx2PKzzMQEfFbxmRWu/rJ19HSVtlD160I42XkWIG5vNkXrg+Pcr1JafPXH2deYURTZ82Keq/7/GQCcOcurkxFjOlWh6tvqCX0OrShwXfXzgI9OxvT0vniejIrPx0mKE8m0MCgFR3Iv5BMFo3dmbsuL6xUh4SHUR61ZPDyi2tmbUqiEU1pAcjzD+DBhnEcaOjmYEsaO1FV6tCGZzS9eVb56rex8tG0aLCvA/2dz6+lLOlXNlTcVk75Yim01MDHcO0R6toL+mdUrrTmG40+6XKHN+UeBJjvR4JX+hACp9/Trmc6QoLTpZcjhSmf3Cm/dHg92jFFkDsqHW33y8ofariqzSpFxtKoFdt1pgWALHGZGUfkoHmG3pZpTM0xzLcuY8sRl9Ep3L+9n4diwQzAek7W1vxBn2BBbG1MiwQJc9v9WbVJXD+vsjjg+7ZpEgZ8scZYpwXWiVL1Blz5XvdZNfSS7TAjZuUmOm0evLhzlgmU0UkzPzl5LFMahiKq0V7M2w0u+0C3rVMOn30BvByxob6SdwnbDhsNn0gYODaCZj9QTSrHHOxm2K3Ktfzp4/MYuUjeJpObKh/tSlqs/R5AmQIMZyXDf9i7MSJNn2Or5D0jgZf8YSFE3B1yVtdmcAEEKFlrajO1N62kZIO1Eir41JTo0JXPTAgBrr3bo0blA+15aLNYCUOc52zcp6rMBrvVC5ZJwd/VfuKcdzy50LiXFsbAArQsk5DIUOcwlXNjnTCzUoO6G8aEDbBeZFjVZvt9PhRSOFU5aIPsJLjINaDNKU0Sb4o4yNxqfs5GaKyxDSwVV+8/2Zk9tUlWLTWF/fWG1sqvYla05wGj4jR1a8TROEttyL1/0pw++KuCP+5OlT3ogzT/cYjp5LpUi+EPRIccZiBpix7XiahdaXYUg6Ilzf2xk1IZCTWCm5taXo1D3Xyl1PJbB/RnI8Bon4DcLTLqMsf7R2dN27270zOrpSmhwdmywByWduQJlzuYrTUL1LWOKOZvSyZiqMm/+s8Ugxb+zOsJkO0C+D+kCUtGwY85AWU5TAp3x2vXfER6d4iJ50mk+9OxpWVK9AI0U21p8W3w0nPM7nKLLpN8cgkSIrDmf1ixdPpAdvuB83eT9DmIlNMGBmS4Fk/JTFUbCy4KrFdHTHKnitFAn9G0dH1vZCBrW6hBkwzFAEQQ6guD6uM38pc+yq5McHZY7t7e3oOf44B3+03rz/94Vl03pu2uQqThaLidCyO+ReWnK5smiIBJq8o1Op7ng86x7dRdzrtNLDehuokKOHnYTRJoYj0J5t4ngqrBX4aDxiYWwZQPtqd/f92aox2pnjZfzGjylWnT0c9eQ1P8D5dFgjb1j5hDKDJFl4yhDgtlAsE7iNYBwvBcIBlXqR5kiKZyNzPJuOm4P+9Ou4Hyp3wLseGlUnsSLcBlNpfmtGpUHt4w/3jhJkRY8yxtYyusH29r72tr62c+fa2+C62tbW1zd45fnbWOJRqIS5XBhWyrpC6yG3ewVIQp5UzCuwCZeue0L0eALCsOq6N0DrOzWkFYxW/hpkIoYWCrcAACAASURBVIJ1CpzIW8MMQxk3+F0uz4r7hXfgzbhfzldGaFVTyXKObDxNkJ846D5SZcMnQZbfVsuxXU6TqxxkHJogGYkhwX0xZCFI8F6SN+uYtViAJwWOJ9lWi5B+8t+fWFyvj3jXdZ3qZLFUMpRM2eR8r1qpvXUisIFij6zHcmAj/fWhG4GEp+3q1barI3AP3n674B5bHzW4ltBwKOtacbvdy4cuF1SccnjnFgzdEwSJU8Kw0st4cf3FMI1bjNRwmCEJgsoDSCYg8LY5G88zOM2S+4UMRxo33levnco3ypGNJ6O7KleeMpj89GaVHNirlTd46pqQIH/7N0baIcH9s36rzVjgWMIcoXyS1WH0+Hx+IQLtJENAmmfSTyQeLJtZmFoYwqYBZLFoGE1MzytMmlv/vI8q9ne3Eciuch9+XGhQXPe1l1G2IYrAcORr+dXWfOuulA09Mo0duopZNZbNhdwrQDKXSxTBwPfO5BKm7q+mpDWnR7isXJvC8fBlmsL9XrvG7/VY5vR2kSEseh9pFJnUm12c2Mxkfoz+h/vHi9qFNLlqN9affjXU11SbX1MkkKtDQlytO/oHYrupwPjTPAMmkLAELQRBOuaIDOGzmaldxsrN6XERvq0jSDHxPZZz5IO085GyM4lAZqHdK/bOT+rKevyhnCIrfgYpUuY4KCdFpMi28jUyIlOEa2Twr29XQi531pALZbNFDCvm3JAml1HxBsFPK6azEypVdyLmwSGsl+K3vQHdNcrq9TmVTtYHrtAuicRGHhLRPjoA90Yy/P7mwTb5svD+/MfbfbIi4W5s/KgDqqjyy9rfKNYqsrLn98HZ1CGaX5Rb899zImmlIFtLRIESozxH4ei3GZtzOM/6aAslin7GAm52l7VSQT1NBRbAIs8kS9kSOrYqXbqEaZEg7yFF3nh442HXw4fIFvZX4vpCnxzW52SKZUGWMT5+DCT/cEu541pOGBKh3P/4ON+QNvI0jm9pl2jlqC/KHeuL0lQhbG0kqN2KxTWCkrS4bttoOjvOeA50kppemECGCaMHIRdJ9mYyqPljMnS50IsvYhaCmsvBchybZps20G4j2LIglOxdXgiFfbcv9t7d85tJYrS2k5A/vhG+fL7P831+8/slCxQ6quWNYMy3HSuXq9XalNPpgHxquBynZJoxT4ZCIVEcImgLFxmOu0XK77dE7BzjSvh3XQQdyhSWXCy7V3jzi5A/FFIZFs+f/7hBZPtJhVJz0oboJpGaY0LCc61t7ZT6QOtA6K9fnH6RdO8lScGdSfq36GQa5dodIbnHMiT4hUpwZPJxCqOK9nCYoy0LmccLw5PV6zkHGBuELOWuX5lXOvZdJUR+PYaI7O2tF8gBCD0DSEb9Ob1KowKkgiNIOTvb9e3I+krMW616URiv5rqr3g1fcBuYLFnhq9NxzWwcumwkxYi45NEtL8gJg8hFMF6e35Awvz9uIknCX0Gp7BnajW3jYfLeYb///uffDn9M4OO6kO0tjxPHnL53znueQCQqkei9fssGtOxAerb97j/pixGK3XudtLPFKAdqRfG8200RNhdrp1wMJMz0o4IsAZ0cXZEzP/3PMzLqvF5zADGj2blq7vpt1dkgJFp8HBu7pAh5USUS6agQeUHf9DUYuy4jOHxwenrCG8tCdTxATHY7SzEfukDJagmieb91EibRUTwiy0btshSBJCRKIsUML7EEIUmmqItgGIuQFDJpVIB4fvfpZ692dv/bsmtSXbY4SuQRe8NL3/EtGO/ZWaUSiYDsqAN5SrknBt/2w5SLp3mSZP1+LJWW6IqwtwfFEMwcJgjansyg4wfLnATzYdTFhaYNCMjatVKtFvCMwmR8GaKPsnT2lzt/VoTs7W0SqVRIpOKFc+dahJxtEvl51ze6iZVgthoAIaFbO644AkGfLwiPMhBf7XZMabXD2ssLE0vigsEjU/54vyfMQcmc4YqSHZfNLhezFU2QgkDihJu0kzwLbtp60uJtNZy/l8gzxzT98HGHBpFtqoCgJTL56Y4vNC8+ZTnXFvu1wO8y4UxaoCoQuwmXjfbbv5NkKQletpg4KSTxlQQnrcfH52u5K9AIoEQGpketjm7DLWUJ8u6XiMg6kEqFvDj4CcwzkCAhMuq79O8KCWR+3tVp9Hg2AqWS9+DgIFCuXumeWkUy+oLBQGk0W4MJxzqk086nwqF1eXymErWMGH9ah1E/McTtkDw/bOIJ1/6iKHBiAi+k3hRYfiv/4smTt8fvb7+HyKNTd98JGy+OElk3d6NGtnWoVJ4+1ZcX2B10HtUdxumUmyQTMs/9qciIJA61iBBSmQxWYUj7GMljYjizaTJboXJVnUhIT2DU6rw9rDpb1fHGpTG1RHYqPA4M6NUKqQYf1GsUYz9XjK14e+CB2TPhLVXLq0jIrBPMrSAJ7g5ks4GcY8o6ajTrluQljI7OmCiTRTsXZikO1+lYmoOASTMuXrz/5lVqYUdYsAsEZS++KO6/PJ5/jhH5DpaaPlVpzYc2sag6atbQp7V6hVR6zZrm5Q7PYHieZe1piXQLRcpC8DjPY4UCyW5F8XQmRBHQyyWKxkzLoZRHa4XkA0xCjQysrACR98yg41/VGzQA5Nilm41eoxhbj/pME8iuQyDVCATd55nOuLqRhTAeO4AAWb3i7PdCAIKGA8k8CzNObn5o2DikXZItNBMfkTnx6kyikqCoxNDjdBinxjGXy0+aNzNJdpfcSBTZXTb9rzfCy+Y97rNqND+ByPb3LVGeOR6BmlQ2mg0QCVgq5xzWlAHn70XIsOyrtFvASZpMs/t5Pi9wTFROulO4y4a716noov3Cm8cMvbgUWl4wWWvOWq3quJ6rlkDIyXnHVyZFSEVHpUTeBGf/Wg8/A+o8o6+HH0VItdU8b4jZNXhr5P4m8rY3CEpmnbnbCEmfb9sXRDMO/L953ZyhZ3pZjIS56WFxgRo30jaGss3ESYoi44tbxBazaMYompeWTRjp9xeeF9z7b3873zxxowjZrlyHNbJFxvbD3t33ofMOHepUU9fylBqAEJtrHU+KPMGzDx8WSIIo7oT5Cv6UC2foqP8F6XbLNr89KTDjEozaEUyOhCZM4z1oE1nNiW4QrHiByHvaW1cVIO98qeoIPP7ai5w9qDhbpVHftHZriURSdj0a+GbGuAkBHOZDxGQul7vmjW37FCTLgKjDWZ0PTBqsbi6eIU09y2FsUSsSCYyJ6yBHEClzlPK7qOEffkiICT8PhYkt+otPi7+8bRz2VGdFdF67/RDIFne31z9ozpycJltX1OoqdqhEtqEqiYrk2loxn991sekCzIVYniW2KtjOXiojySwuUKJAFkn7p1QUW3KHQjJFTtw3j1incjVwdrci5OrcVP8IAPlAcfYNxdmoZ/d2XuxEIfKCoqNy6VUZu5oZ8mFdyC79TZ1hI5gtZb0xJGTNkbs9CeZGQvpAyBIgaTUMDfdMc/Gl8IJ1LrUsGqYFHKPCumUOiwphjON43GIhsITNRcWFJL9fxFmS/PnoUc+PFBzV2eYQyEOjg4x9rXfD6r+8otF0NH49BD3VItkkUp20AcofQcH93d8npbAf43Buh12M2AWMxuJJNzQXDm2RJSqifXM9FZI5+6a3Z77qqKHZrRusveqdACF1oCMS8k5TyJu9f+gEHQchjR/BUbU2+Pl5I/zM/g0A1Xde/afHFwhMemPBg9hB1lG7Z12BMLkNV6wMcTI3ZTWZRww9IdHEkRHtakpa0Eb8okQPhcgkRkhGt12iIjrgcp8MDUUEdndX+Izf+lHZRn62sQpUt7Zi74a3jxLZzD99mmO/1NAQEz7UlUREgpR1f3ec2i+k8wSfDJP4LsazKZISkxGuaIviuJ1kbGhg5Bk58+i79dCSKbQeDFir1xwwBDudIKQ1tjoxd/mrf//xgVoib3xbbzXoZmHnxcHBT+pE6ruaSgKRs4dEohwJRRK8bd0ueyfLICTydq1/as6LiiQwWY5ls1O1qSGT0aDdSHlkG2FOMInKTJy3Ma5xkYyEaFwXESiKMIVxF8NxOiN0z3/wEuF6cvbIvP3RmfYWKdvbW8RELy1HHg7b9pryVFVEb5pGp1FFbFOqI3i748x+OsKCD+xc1EbssBKM1LQcek1wr/M4S1j8AkzZmD2zDQnOIi5PrM7PT+VyNQjhMGtbrcHVidFrWpMSIu+qzn52qfeSAmTn4CAQeWGgS6/y+K6Q9QAEQurHjP3BWLmUXf0/IecT2kZ6hnHqTVHcXHIImO7NJFQ0YGEcpxaCWD7YWBVC2SDv7Ox0PlkDHcmWMDOgYczItKoYV6KSB8kjKZKIU5N6wX9ihGStCy4+OE4Ga0kTh8QlYIhF64Ogp71syB5a+n4jyZY2bvsJS8YHH3563vd53m9mvhgmCS14yJGMlGMYJJaoVjl1GseNNzxPIEJQozY6nwn1MzyLciP2lTTNzLlkmudHV4JMMO5bmZXi0sutd0fMs85bodsU2aHLlpV3d1wIa8iyuXSSV3SWhqblYIi4SWJxAkiTLCIk/SaOXnEh5FMFic7IzHwwmBMEmA4LFFKYzNOEui5yrtz9r1I5M+F0Qu6ZAWetwHicWhgZuPPZ5BcBEGSzRdrt7SD72qq6rxUjW4psdEksyauBPxdj0agVOiOAq51qQ2Y3tMhyGTplHdLkKYRyx4i535YWRC5HzKcTaWNCZGnGMq8WChTlIkWWz7kkCVHqEczeJenokc9barvJ79q1ax+B7D5LQ42XSddj9wUXwgDgFUML5eWmKgFmc/MCBpuf8awEtuJjSjz782VVKG3TPEWyaVJiFClDonRwmfJSaIHmQrng+rytHytS00EO1LTk2IJ1wHh7EuT4RTNEQmnrdwJgjoO6ZZ91xzPTHj4n2UAJtf2Xm9lqtFiNlbECK0Wn2R3GW7ww3tSz4ShMo4THPDra6+IYcS0aIqGck8sUxxeINONi5PH5ZXofWfhjQaB846wgx/EO0NY//w/I7q5LXe3hEv5i6tjjNWGEuLhbLDvsZvFyq1MufvJ3CaTHsWA13/BB8Bev8KZHFQSOo5WdIOcVxfQCmaGR6H06mhenbTc8IEgYaWYqznt+pzU5dt86ZJucbHJsCFJfVwevtkCey7EjRj54cA5yuM/+2ZdVnL5j5Sw4dyVK9LuT2RjOQJFsNlyNAkjCOBr63Ma4CgvTIS4jhyZE1yGvGEeQmOcKOZnnJZurxMIwcTsjICkep3n5RccjnjrILlOHJM8ItqfLCxJQp+U099FwbWNZQo/85E/4jEwZXGafF/8Iobwgbm1sqGsiu0/dTySQT0EkmaCYNO1y8ex0CCobmmOxMuN0/tpfsbpT69ahkck/NAq7YTYH9gN7j71V2g2Uw52C1OeZDpKfDo7dcOCBMFvO1mOx02KNcE+lsngbSL+uWK9VNMI4YrHenEMsB0M2SeX7FRFiT6F/PC0ehsz41CVlXPGxMp13yfL21pvtb7wvOg5q+C+K7LrUIGpq9Elc8AZDY+bGy3TZ0NJkW3k3w2QrTX5iePk3gWFhwOpZk+g3e0hMFwSf+iRYQEgUGUg/qsiSjKKK9OEcJU4ZzcRp5XqtWPEPOQf8A9ZoeN16c3wygMfsXy7B6/HBgd2Of3owSMzxlq7JzfY43lgtkPru7nDfgfFmPRwtpsqReiyiFaMgdwyyDIKsx8JQ7TXCYR0Zc0yQBZo1Kyhx30F6aQZtpMwsw2fMCsPLkqsgMcfb5HScFpaXt0uvX/z449Lu+liRjV/a94VaejS1i3KxifKyYfF8M62xT75oON6S92VpC6lBhvFtCLQgSeDgJPnTjRWFyVNBlWFFtAxByJITp403CZgPZ2qaf2BoaMB/T0sm71t78Z2Qd/Ete/pNe3cDY/AOLJtNEtvNZntlY5Twy+bwgzaSv3o0OPVlFCQZhuSYjUS1Ktg2gIzpIOFVBbfxGG0jZquaS4jGWSo/bia5DCsq6c8LQok1MxwtsKM8LMY1F2RpuvSKPv7rh2ttx53+L0U2sEKD7DZ1XMLpoNhSI35vjoqLlxtd8sprCXpL3Lex50ugvaDMc4KqKul8XllD7CEn4cf480hhvU/vzE3PGnsJGNegRfor+G5wvyM5u+7onZwMBJa+LwPCqRSMjB7C455ITo09xih32kfEhmfD2uzb6Rnc2dx89OjR8+fPh+EDJLmEa1sLQ+jJRqpa3emYTaUAJDabGMDUTgmH2zja6wDDRtPmBJMemaO8PL225naxJbaf48nlNWNepsnCmI2mxWVh/+X+Pz60HxzbCVJHeKbIc1W2hUlT03NM523yTJH6k56LrWdmF3/0e/nVPrW3t7Pmg/Aj8t58cENVSBf7Cx91zHkliuEP85KayDztnUvnXB6CAL/WYBYGkPdmtKT7yfvY7UAgcrL7XdQdrWo1okaAdgiPpkXHlux6dd/Ckmx6jt4s+3befrX0GDIiuPJ7WE/KO307g3YjUa/WqpFyFiKQFoOvAyQZ010bk4RQrmGQHoZkpZx7ZcE3PhIvMb5gcDxDU8id53m0Fg7tS4X0Wo5lhHdH8dLvXp+fxPtDRXbpBHVFXhCK2u5DNf3gQONFfYdy0dDY3dUViVE+25Z5eu9IFSiE1sVjybWxqfropwXfilo6LNBomRo9pEXRV7Ao08Z+p+acuX5arDixImeu18ITJ6u7728Hvj3ZPdGKu6v/djqdkKadhLPm0ZKBJfvVZpbsa5Ic/nRzc+ftQWpqKouvdcF4DU5dxb2wHIk6o3UNQALebDGiEWDbTZDYucG3HVbP6J1ehvNSCxOKyITMNMeiNGsxMhKy5V7JDJ2weHlpK23hmAyzfPRO+PonZ6dLXrtIkd2Xui/IliZD58GnLZqNKacBsfGM57kiDc/wA7tHRyrFkjwMhUJhLqimDzOlfUQf5hkBxdk8TZOMGsrPJa29TseA/3oN5gx879SMnwjHVnd3T5LlXQBZ++63D1dBN7CcOPV5ilM6Sb24b7Uqu29np+dxKjwbDmv6I51F/BGNVmEVh7SwVgSk2UisClhBkfjSbKReB+uGlA5GHrVZbiQg1y7Y5hU21Mu/4ph0wWZh5PwIohmaSltIhpaQhWXSy4hF9NdnemwHedYWL3V3XUAS0zV9hLJDkcCycbUBK9IA+eeKaesIcfpBWTzEILSiuEikiBwvUSKdGaUEeA8llHRi4s6ckrQOeQi/f6ZWq8B4AyArzuT3GGTk25OT1ZN/rT5cffi+VoPydg7h6nZMTN3VGyU4zq2zOHmr53EgMBXFj9cUmyB1jLBOT6NFLYZBRuqRKmGNpsLZGE7oMTwowv91zE5YhsYRYLIZVZQzsxyARHPTqphwb2zT9DayeBlOEIy+uEz7fGDbH9qOsWlXpF7PWJHNuu76aOBpPYjTMh1T+7iIDUcP5VewPHHLvCStxSWaEiiZl4MrK2+DIofgm2UFJEqc6z+UnV9oWnkWx4cQ6Hb6kDwsKZ2HoUnDSjudYp0WJSXVBLPaIGYarb3I1cmFuWrq7l5BuXINRJwbFHIVjZpEGR130cUk3RUzaRgChomzhNhZlkjbRSZQs0tm8WnBl4R2H7p7fveaf52U3f15g5C8ffiec77n/H6/G8IFDaKFXogm1WLVlFsmGUOHczf3JAYDgLyyonXv50v1OnBs5psHaVhNCFVzgb+dpNHI3fYR0GRnK1GitfZJ53BqZMgLRUmjCfshriG6C5VGBT2bK4WCBoGEJBloQG3xer3gyRtoDtSYLWyOadSKPqmIpHAwkeMZWux0Qu9lnZjayEyMRVHBZlUYY6wSnmDG+t3zqAnfefV2aLedqjXnz4rt1qDtxslM2d4K7Qt8fKOiPdOykfCD7E/7znMXeoMhvhPHFmq1jY0gvUHjVBzDjbhFiZticQ80N1y8TzwVdIvGxqSPVlZ296SGPcPemze7kjAPEkTZLDXrCGR9NnDwOuC1uc2wAKR95DHfLX4imMmPgeNAKmUHTd622Wz2oSHUBgYiUExmK16/tuDXoLMB0N4EZjUac9gbno2UIYOiX1QKGvmESNHbTVgIIyZSYy7PlIngYqGEKBvExKodFn9mdMcZtogrbBnjM2ZhAXe8Onto0Xb+COEZxebELuONs19/OiMYIB4lSpDgI6uZL1+6IJAdFOmsOQlw4dalDBGvMrQx7jHSsXifOxjh4spr41m5TGSQPEK7sFJtYL/ZzOcPGgf5HwBkHomyBBwn66/r+f050Nz4bbRsAHJrmA9v3j62QI6kwHeOgN1E/r1cq62t1crl8vLsbsEvb6AmEYGUa8z+sDsXQcWHbxz9BY1ZodJcIwjaqgovenRKjNrmYjQuU9GMSg2tDfPlInofjGkOc5mMDElQO+8Aef6UfTx7CTTP/eTdxshQIjWeO1QkqBSB/Po3Idw1bWKfWu9uWB1JjjJGo1wCdwXphMdIcPF+xfxEcruv1z2kkGmgL9RKdg0Sfwk4lvKTpYMSSBJAIppIkaVS/nVu63XZN2S7/SkC+TA1Ck3jRR7k71CGHBgYTY2m7o2OIo5A+SI4SrCUsNbKBY2/0EAeHLg1CnK5OQyKzPl4kI1Axe8XKeYVYpqhl/Q6Lsgpk4RjesNJyhQEMT9RdeBfL7mJKs6QKoJ1FJkXL96pyPNnxfTbefLGkSyF3numXaA4w+dFYbB2oeV+UNV2rVYZl7GIL9xdszrobIwmWFzJmYITniQeI7cfzFNJLtl3LRxxi2RayYpWsqmVNEr1fVAkiDD/A4AslQ5B5kv7B3/+Ef7y+3pz2a369DP7yMi9e1sXO3lF3gWQPQMAcQQe1E9CKwmm/Q9r/KqVzWP8/Mc3i0yPvyCAjKAJ0HKggfbB5GalUjxOx5bcSSpGyxdp0pTdyMhUHDs/z5K0ERdto2PlquR3pIXNzsX5w32tnYafnwLZJjzt/1WSrcOTb+2IzbQeYWsW+aAdhsWLOzu0i45Gs65qQhWbtjJFTzQ7xyUxhibj/R4Ky0VEsuCSX6TRQooEL7n7BiTYbKbz9TRYHj5JHoKE+j2ZFlbdtr4OJO0PR+8NI5D8bKLzI+A4+sUIiPIxEuQwCmxAWbtV69ySi6GA8xMfH9IfAulFIPlOkQepUIt63dYgJ0v8luTMc2AkjdGQTMWwqm6qSLAh95+eUZRrPskSRZczQzCvTv5PjPfOkJ7QI7adpcv24+p9wgXN8J/jGBds5IVzT0wuhmWZ6EJ0LmSiKfCO0cUQrsu+iBE6HU6Qlj4PN84lHoiTMYWoW/rokWRltyFosF5PlxBJXpJNAWR9Py9QBFEu2/XqdYjvzx6ODrRAfnyps4e/mQh6TAHKAUQSibFWu1geTsmvQXcE1QbZcLTpZfb7wxF06iKAKhBiq1CZN7MxkpLRJMGJCMs2FrKGxCrckZRbSQczOBV/asGrukQVd9FGyoguwr9/9BLj987/n6tVaw4HGCc80EwryFsmCGL7ySqDO9jprDOYdYaMxbjO4aLnYh5uDqPQmAXb7p9aWyQwWTeXVMmuQX8t1e5CN4NIwgdy4uRkmuda4vE14WuyxTGVs62LROsQ36M9PMi7dz+8BKGNOKI1OmSHyh2ZHcql0OBta2to7PNCRQDpQyDlZig3uWOQs36/WiUuZGnS0j83jcfU3CoWW3CG+pMmNmbO4CzDeRxFYpXwbDvY1elVh6V6dCXxfwLZdoafFDZzTlbtC4dDtZYhusAnzSdVtgiGvMf6qzknemFSDGdwLqEMLQbJBEaQpE42sViOJsQSxbhCZpD8WiKVag8QJxTMpfQkVJxJFNwAMo8CO30oyOZBKgVptb9Puf79FwNCjvyg6/LNnns8RftDu9tti+SWy7Xysi8CTdDjlM1wf7NS4E9YoGtgFf7SfA5Nd/nhRSDg9cvVYhGViHHiGE4E5RhFcl3OZB9GVmlxrGoykfPsDs5QHsphjUKG+sffTryR83Cw+26M7cfB3XY6uE/co22NJ2eORSnMhX7JohvEC7f4S1mXL3V13cxE6YQyEeIwJdon9jzoT4Y4i06iVonEvZL7Wuha9t4095tIlHnIhyUQYPPgR5AionsU2LCW7ZGwWQYkvwdFXuKnu12XbqJ7sg+RkdSjY5CNRgUgHZTLNr3bfrv3yqa/MMsfsgigU0AgSXMuJ4AEWeYiYb1erqYwGpMlWDomTlq2kxhL6oy0yanAitZMCI0uMtAmEiGnMxEv/oXvtd8/XbXb//6uSH7HCEPYfTiO7JljcfI737wl/wVrZKJA8WpHx1VYHR2Dg4MbENpW2jXvITBK15cgaSLRL9WrNWKZ5HODVALtoUHbAPeTz6M4zqdL+4GXS/tpgWO+BTKdb9jsYbPmQf8fj0B+2HX5o+HH4DLtdrfeW0E3vK5fv/5oZRfi2RfWiLToXQwNBHIZXUwEB67x+3wRNKJcXg7kfBF3WC9yk1RoypylWU4/sR0nMEzVT0Y3rDKMJShP/9NvQ1GF5Vsj7nrOFHde/WQX8Yawefi2Mg9tJfo6XcpbZwdaq/1wfCG0OPxcbQbt6vzsBss4ei7f7Lg6OMhD/OdXg4NfDQZjzlsbC1E6FB3vVuowLOnp7taLunslEi2A7JUapIVSXlDfZL6Z+Rdaf30JzU3+iGO66TfbEMgHCORN6G0+6ACQnZ1bqdyI/bbCPCa5cv3ON9/c+ffe9TvXVwqVSNhwH4Hk9xdQaBcKIgAZWPb6DhoVXzkwuxgIu70aPYf9h7Gzi0krTeN4Y7rpuL3AC0MHLgjVJqZVjBRrGxsBCSzauGrFjgxFLFmBsVo5jS4G6UhQB+oAEUWqpJZqpB9KJbJ219rKdJldoths2jhNbUzUNGpcL5q4F5pxmnX2ec85IEzbZI+A5EC4+OX/fL5fdqd5xO7sr3vYa9csvzAVyOUyaYF6Autobf1TRF+dL8WUrzB1JG7S7meCzSeKmoP6O66pltDpPdwTL0yS6dHsjI0S5gAAIABJREFUH/VKNi1vmZoneC9AIAUez2UPTcPmsDi0TFtdf75YInZL8k9kGPjHj59FfUh4lp4q3UeiwwXY/At5aSAKEXTRByt7ipZvWs4dvySsqSjMTIEikYFWzuWGQj5fWUvGqdq1tclfp6au7+9nTV3Nyrq2ag6nn1/z+/HS2mRBAzhIka6AA0CaLSEwbbjZDdm3ym7IEcuskjPyu4uLw6873Zj+br9kQq6SZWg7lLLec1J4K8Um1M+/TNh0Nw7ku8OfdZS/yS2PJJNeMmrb2TjKnoTYjRT5SmNnUk8uC9jIsAXvfzr5zOMRUNMyafgSN6nbatc5OyU5tTlixfETZ8FFIlXC3+TuDJEthhDDDx8+wOvyDK5TXJYP9tdKFADy0qX7CCSTw8E50jjTjxaPiTK+Pr26+d9rk9enpiYnp67/upZ+Pv3a5NXzk2GekQQ5R4DcDLhMe65NEyq5XaJuRY5B5RwTncvvr2vJUPWGxnqlEhWm0xThjV1F31K1rE6IqZR6pfr588fxx4vEJ+SHP8kxiQgzSdFH3Jdj1k2K8sjhmKvEw87hni8ey9I4FMHyM2ZjXh5F8O1fQJFcCgJJozJoTI2uukFTqOmtV/ANlSdOIEXikjw9ubaP82qb+UBwxEluE44TZUAr+7u7AWNlxqWCYE1xWiYTrf6C3+SwoBhcVJwo/Spsnlu7ehW5SLQP1era1azz6aBL3hxKdiC+zIUB5BX/HESZXQTS4rrlddTxEcgRW/7Ay7qRSvf3t+w6Q457wKkRvsRUMh0fi2iXDMIJcPyy5qXIPxM33T30mZwnPm4nEV2MpMQUKHEh8kE2SQRxhDL7yHftTOQbb3tuNH5LzdvIQyAZ1IabKIQzqOzi9or24uKGtMIGeyf/OEp+0GrY1c3dbdxB3mm7hxCSIH++h0CSkRtdey1FkP4QIBkMDlorwhoefjTtQxlkvdGIB22TC8336TaHJ9OzstZ4ZosDTVWxmFf9JQoEUmTZgwIxZHJ5Td46RaXNaRuz8t0qWye/T21v0lRmWK3NTrdaLtNbByaW5B2tYgz7K82m6lj6OTU1/nAwEmR0YDshehMBO4koHZOSP6FIclZ0dkyXPaS3zE7uQTcWCql0gWD5xW3mUCN7Y4NFWX4GeXN7cQqbJNnVpWtHV0OvvfsrNHpYu2baXpmJKm8XYfyFVORrwrbx9Adl6ZYzQWFwqwuBpOIgmVQW/fLwo9xjxyDmiKDA8foCodDsLBqA9Jon08+X+s0mAuTcKqQ/V/xml9eyawKQAZfXa/Equjud9pFKl/2lSlzU0We13zUUWXXVlXa0F4NE2qGV6yV9ehkmG2tS9f2LPK4uNVGRSZ/pWyTF/cULlZyGGm3vklVOD/6WdJMAeCKFIVi+LPBc5lYM3XzbSD152UNn0LoqjmWykYpo7Iquqi64qtCEFBv/1NnTF81QZ68QwoNs3EpCRNfrFdy2H5AgTfXlQai3qwrhtwiQNJQGDU8vzvpmZwcHy8pEZCsN6hrfqMtfC+HbjLLGEITtsJ9nLvGb5wBkwLgJOZADPmmptNWNvDB6e50jiqI+qVXpFA+omkb58g6dpomvndBiKokckzfLpXLs8ZfRgxIJkoeQzghHCGpMOkD30fWJIic5OeHEDKL27iHGGBHWdzdor8GawZ65nPmtITaNwvUIaJldb9HsPKRJGlt3pqamZt4JIH3FZYpTp2vPbu5sE7U1mDZI8oDk+6hho+Qcahsc5HxZYRqubjzYMBhcLguRHPQhjIP4ePjs7GwoFBpsKb02yVOgijCEVtn4ed1o5xWLKBDYNEKR6Bi1OIzfWG11NoVEqRvpdivdNpm7AGK0IgPTOh+OnVODi5S3KvXqiQ5soW/h96m/OxAkBJskMo7EVzAkSeJ+zKpjFh7XCYpugIFHbwgveF8tm3SRRxduMt4vA0e06Pc/40Mb4DA99NxjXfNokxRkkBRa4/zW/EBNe3tFsW+wqoaPGhfgI3dQvwdAtm27cdPGQT5CMXtnDzhv7wYgy6kpD5aX40GbSgGd4ws8GWiSwPT0os9n8qJ5BahbOT09nbs4K1KUXgSQqGmOZo+HebxuXhiBNAU20TCtw2QyukatTpm00uCudhYp5c5Qk0Es02LiVjWm1LklETXWoZRg2MSSXo6p8emRB7ucppKKjEHD/WD0zseqTEpsqWXH7akfv69+NtLk0WwsE0I2AsniMNu33m6wqXQPnc6t+mGo/caNm2zqSQqVVhy8L5mvAtsuLqsvL79ysTbnnLDSaMJJtrWtdxKShEfvNrLpnb29UABE5oO8u3yrvLyqOI1NY1CINJIkyWWxpsE3oqkZvkK0i80FeC/qht/m4Uu2AyDCMC+s4KFWrxfKGkjMTSKvyei91enUdYs01upeiVZl08nzxdVKtwHfAUYSiahVP0qFE1p1R1OTPPLHxCN6SUUeaC85xjR2P3bjN4rMjs3Tj84YILPKHjJ2/+EtEwwbahkKldk4FNzaaGSC6d2+7fvhz0+G2hsaAQAjN6X86fgWOMmKQSQxYU6GsMi1tzODG3Zb2531gAEH+ff1qH+cufdiD8AgkDjHzBQa2jiAim8OQmWwULd8mA4sp3MRQR/RmQzNeltOnYboQkYbPy/M85f4/XPegMnkt5i8ItOow+EV2W0Kp1JnFVulUlu1W6hSVlsNMrmy2SnVYnK9XvmPCPbqe7uKHGdIjW2Tn3ooQX4xk/5/FHlQ48R10qJj3ih4f9dAE3ieAUcau3HoyZvxBpAkhbt+78J9RLKBnceg0DkpFU/fBOe7UM/mTHB8XFjA21uBchDUiJ7w+mCn0/3Beo8IMkSPbSU0WFHVNV9eXg8ckbOlUklBgrfAW2po5IFOB6BokJbF4oC1o0Yaz+yAbHwUChkzj6cwXwEnCSZt8kM6Dv9Fjlu9I7YitdZtECv1zrreFiEm17VKm3Vyfb8sAkbd1xqJaJsf/lT9ciF2JCp5qsihOG7J70hBxpv7R+Em3ktGJ6Ieiemyh5DmF8i6F9KoeKgRUBrfPin499MbG400Knf99oXgOJBsoOUxBFw6MzP4t/GB+rKyqprg+NOnb3KA4w5qPLaRzzt31l+EQittdw44rqz44Ou4g0xD8R/4oT1qoiDxiVRcHCE88KVhLBSCFF+XKIyjJocXog2UNua5khJz2BHAQTqMloBXJBKNed1apZIv0cqbXtv6JWrt/1g7/5i00zuOm0svPZNl1yXkPEhmnF2OGA9TAxjTaSm2xmLYRGwPRFokPWgbPCFpZ6NAGcqJiKZUfqgVe3SilvrjMJd8oxRw5C4RMYvN7cK5LiEzqRH2F2tmb/63z/N8AZG22R/bYxX+wCZ99f359Tyf5/MdbupTX5VMnFH+oWdm3dGnViiHbw8/92MXmf+U2aIjIR4nV3xclMU5mMVvPe7OReyMLuHdJ9LKUgQSNFnT1ZRMxl/p9qr1tNmpjVAgHL7eRaVWgHhYJSIikBK1iFQ32UvxK4QZOB5k0kisymm8T56exyQRyPRBIrHYIoqlwLABJAAEH4lqzjJc4ZAgGbleIDwwBIiuNd8k+HfvG41mLyptBkmQnfeNZuPyvtFgc0a8Xu8tlxZtfvdty8Wm29Z6h1w5flb5reIvrrObUtcTRdvEgHVSItE4Nj/OPmE2+wDFokJSOc/4FgsvVGT2EKfqZO4IB8Vu9Laq+OSXumqkyClUX9f0z8XjYc/O3h51aksYDoAk9yAbQpf8S3jxeMoibGk0etkB4tcHCCRKGIOI3b2MeQfJXTQMMngIJCPgUGVCiP3Vp1BFQ0O7aFiTpTTybDa/r4rsw2C56/mX7xp9XogvTtTAa+B3RjsvI5DRFZvNHPE1+lzaS5MOuWJcrND6vtK2yeWS89vr4m2F16qUPL0qvTW5KVWr/X7/d+9nHgiWfRA3pShPiDl6x94UZpOFh2FVuV3e7B4QGXB+7ueCVLBtdzQ06J9fX5q77tnZ2fmJFVsKxJdiQ9VUWkcHg1XCDcTDFncL5MkqOtFuhIQcUvL0wesDIHeP9JUQZxKJjI9MBA8jh4832CjSDJGWXUqDlL8UT/SCTAA7SVKSeauDxtwI1V7jQCnohWxnf3lw0MDpHORz0I3jKDZtX+OMr6lPrLaOozbiJzNXJhQ3RtvWN3skTXeHB3qe3HCY7GKHpnfgzvN/Uyh5dQ3lSJF170JZYNwFiqzK35zEYeYByBNV2VUPPpE2sz4iQT5qaKjo3vk9CjGrq9cBI5EkYkNlH8G/lPGkkldLhPuF7sN/LahC7cmkeevg4NCrkrET93AuOf2z6XvzwXvTuHJELjK9weW6RWwBW8jjZkFOTSGQpGmjW0s4xOTf8UR9uyVsOofj9UEtGDE7B6PLhuXPBjl8yIecGKRvxQuKFIt77JesoEqxlq61j5kmB+TSq5etmt4eibRWi4bp99750z8+puQ9zpw8RcQU37DuY6uuUJKFDb5VmR21Ew8yBQ56/V5XWVbagEB2IJD6vZ3V6569PZ1nKYlWqpwEearSdjoZ1gkX1g43WlJAOGSxyGKwVC+zgkQg4TuBTyASWxEuT+iG5Mci5KGxDGVlzFJax6NzyEmyqNhHYkWSJDuyl2XR9U5VLZ9j87nQSbYzuj8YHexcXgaQTkgknZCN+3zoaYDi0aY+iUPR00b3jljt59VqyW2X6eoL6Z3njrMTUolk4tvtAfLxdAWKrCtwgkcpZCHDI1UWmvfRwCWobapwgVgl5ZaUgWmTcbvhw5ruva4diDbAM5AE4cXKyxjnaEwWt/zapwCS+9PaYrNbQBApmWwVcUyp5tGpDRluptGBNg7XhyuLp9BJoUwQgyS+ixwnwCTzcXQXHuIKebsYR2xaZkzIVOYKGL2Wc9NldDb60H3OwWiUD7kkau4bdJptNgDpNVnFWtO4Qzr2dOz8mZEb9vEmqcI+qpX6X0gkL9RqpfyHMbVf+f37lCNFHgs2dW+RZZ4e646hfKPoJhuCsi2TaNMC7PvrfhALBjmFQVaUVXfvgSUCyDDojoh1sxg0KN94utrTySVPefPiVsTNJi5aLK8siGQqlJjGIMkeiwRuWQkGDxY2hCJRi0UQwyPnhOREAfi78SygbLTJSRL35c/OYpI0ZvP5M5z7Lq+t0buyv49B8pc5TtQNjUAaV3w2k2nmR5tW2uNbjJy9OKEYPq/tlVutFzV+eW+velstnRxzOZQDWQ9JyXvmcVGhBde9y6TzI3lxYeTOXP48SVbboMeqdSG3OqvIBjDtCr2+Gk09KtethuNJIu7pZtKYa1tbayIimQyk/snbWCtZEARkon6LxQIcw4HBdG7zEUpDKBmxh4QaWwa5j0AGH/NYPP08Hp67wuXpeENQ5FCpkDUy0d4FliRS5NQsfOGLSyU3z3AuA0iI21FnNGqIcvgcjhmcpAHNTAMP6RsxuXyNYoV9pGdUrFYo5JcmNdJhU9/6C4V8+NaEWjo8alc41in5HpJyZNp1b5jwO/RYfKwqz1dkpkMt4yw/qDq5qxFyK1kIJDr4QoeINfpqtIZIkAFdJYO2tjWbXmSDw4wvpV69eiXSpVL9wn4gGUvNLc2FQqgrMohL7PnXmCSgdMfYIMhUbNXjAY4eNFFS1zXE6+IJoXyHKge8JGQCrOytMAxydvYZAslgic7wr7lczkZvZN9sAJLXOq+hCbz7NlAkBukbGTE0jlitPeK2qzesfm395qbGetGxrhmQWO3qTXgZUGr+nOcgKW/kkXXvvQ1nbkvtaFv3vTfPwE7kD49F18JOfPClBwSSSX8aKmoqampq9Hp9WfeQzhObixPEEoBkLc6+TK/VAkgC6m1QYSqGpmH3Q/UXQiCJZdDi/mvA+Neg+xCIAsmESqACUcbg4yE6nx4SefCEKtSpIhR2lVfjAwcW2lpjgjJJkFOz+LoNjUEV1tLpjS6n04s6+QAkFIkcpw8E6XSCIl0+r8t1627jqFUst9arFV+N1F5EzT59m+ugRWubX6nphSTyO8ovMMXsD0ouj8xfu//j+iP+s7urUbkWmn9cW3x8DnxkQ40eQNZQ9dXdXR5QG4BMIZAdwdnHEQIWmHpgCQpEEZcLJAFkGHKk1tPfpBNRuhFl54mWw/lDKHjm08DRLZIh028//ZtPWwUisPD+ftXvvvjim06BbqgbjbpgNLfwKk8xmeCFSZCz2EcyqDw6vfOmywziM+6bowYMMrpijoI+DTavb8bldd0dt9+wgyDblPLhkT6H9PbYBNTXcsmofRsSIblf6fg7JZ9h1lMWHVkv+rH78P+2Ljy8gNbftp5NPfpQrweWkOkhkKGlONQyum4qY+vl1qIxiUmiFY9xm5u5PFCkoG0OOLW2thPxJhVqljwUHcynV1bSQSN7AdXZ8L8xd/ZXBFGfwhvsLWw60dp6Ohny6Mqry5iMNbcISKLjbhq+BPYMQDbQSlnloVr+5QWzwWVc2TfuGwwQbTgGdP0dBGlrNEa8PtP45Lj99ph0Qm4dHm1T++1PTY5NjVwundxe1wz/MAOJ5G8pb1tFxyPL7sNfvnMV5X/914V+Ab1cQCAbkF2Dfeu7u/pjc4F4IBDe6aYuTr18vBhNIpLtyL4RR9ThKJIByCutra2fJ9vrBaqV4Hza7U7Mp/FOhXvD3SKyQIEYSglSaJKNRWYRCaFUF4To9DmHBxwl8GOJRFzUHsnMkHz0H9rOPqaJPI3j/MMmm/RyvcQAmmBgbCRSTehSIgGU7XYbbNNLK6jT1kKhaxXSnq3Bq8UiDWOD1LbphAJXYveEo0uopQbMbVNIauTcRBhzu0diULb4x11O7noQOdAE9797nhkQZM9kY3Z/wLw0pIRPv8/b720QZI5YqC6pbghHXf1RFiQ9o2wERaJZuwIQy6ejUbfT65Y98GlMJr3O/Xlv09Ppqzbr+OWbul7g6Z/8562b/3nzfpBbvrHqYwCZ9bO2TZDA8B6IUkRYBjNx4Bi/P/ii4Pitr8YmlVotkITDfKZWkauQSCQcyHMHkGNiSm0OT//QGY599d+was2QkkVjCBJIAkeDAWM3KrI2HIuBU4BwP1jLx9J72kwBST47mZfdSgAEmbNXyBRWV4ejM33RCdzctK9LWVLd1QmB5gYNIGXT0X6fs8UHB12b92bPiZDVNxbtnYWipi1UZ7LaeyKjN9u+3QaZ/Q7Iqp0of3aQWQjyLAvy4r1r11iQwDF+P/msXXh8aF8sob2bYK17hJTk8vm5jxAkEyqsBJDnWJA4H1wVexpWqcyp5lgsBvLzmA2GsrIyg9nMgQSSsUePJPIwScr5ObjXxWTYQElwFxEu4OAuIeBZhAaBUimL/ssVne4Ec6ZnqguVMzh/qo8OQHqJQdvum376aagp6PXbTwyYhv1FdV+YhvX6EChUZwr1fjf727y8d6SYva3Ityh/OUX+GmwbSF4EkMxIHDhC/pJcXxOVnhIIzoARJxJTjBwExM9VyCnQVd2BSyhI7XyF2oCPtqhdUwE/tRpHs8IcSFylKFOhOlGRcpxWqlBgiGGnXIgVZgPVjbl6Kabln+HcoL0FhCGhVEK0memcmACQfZD/NAbozhsuGkFCzO5vcTvdkZqQZkBTX/Od3jsaqZu1ep9cqNP87bxeb72u0/xpT94ukrt85C+nyFtnOZCH7lna258le++PAMcQk1xPJj3ksfn5f2srEifnMyBIsThXQbAgz1yqREFqIcE0kCzJ2jXSkCHxyRYAjzSbAaNZpQojSuTILj7mFnHjHCB4JzkU47hNEJ9di7wfp2LwCY+gsbGhP9LV2TmNpk03KBu7AlBo0zKXTIYgfT5/0O33gnn31Gjs/ha3zWb3ef8x0Ktv0reNW23fZLMU894D8m0SuQ1SKuVO2zdGxwcqcgvkoYvPkud//zBzfwQECTJaWzeUpebBP872Hkh5ahX8UgApkZOe5InDCBJc5CZIlWoNYnmqORyO4YA1sJOhHNHmIypus69cbrks5DyloEcxXyHxwHvK0bz3bs4MKhB1ewoLlUWRyN0buE7WRfc1KJUsSNc2SJ8THyf9ZNjZZO8ZnfC16XX1vTabzWr/2jpuG+dC9ibMvOwf+cgfKdJhNOZzJ7wzIsSXL/M/TJG3tkBi0NYwmYeZh8gR8HjKUse0Wm1CUOShQJCTpXxC4qcYRnuJUySATBlIkoRyhyTVKdkWSJUMf/CmXx7uh2OPRIELQY6M4Yo6pClWyM2pFMWRLBCzu+eLhN0GgaCoXBbpckXBnl0zEG2UuOzTFUCQ/Uiy3+lscfrtdmdIY6+/0tLUVn9BX3fVar09eucyVtl5b+WY/Y6T3NmNVrUD5PLqahrSnKWVZVBVenV12bjM480ZP1SRmP8c2l8gFHa3g+V62B1oIPEGkHEINdqKwVq5Apdy8Fu7awd7yw9XVgJIIDw/lWJ7J0CDTKpZxXEMbzV28B/aMLvaBmdQYWHIgcyNqcriGSQpEYr4Ir5QJIS/zgiKlSV0xNUQncB+CzqAK5foG5D80DK6PwJVYssfvEFvsOmqRmcKuq/arusvPAmGBmym+gf2v1z/c95HrIfM+8k+0rjK47105Kc7eB3pfMdLHm/11U8GKd30CluK/ONZHP8CkJBGEoSFGgQyZC3q0WBQj0wByLjHwk5yHBoDkFSyBkqWXSAp0pBSs3MnVNskWY6468qd3FxxKRRRQ0NDY/s4lOLcR2FzaoqhsNNSuNkIi1pwtKT8VIS+2wcpOT3jutKgrG5gs0gg2R+RAcigzmsJakIDTaPPT121tvb03HaGTMELfv/4F+Nv9ux2kNk7QR4ELf6dq6jfgpzj8ZaMQLADeHI30qU5LsV2OLZMfOuSzdYdmy4032jc4U1RkexAIlaJF18QRDs1SJGDKEnsvzUwNacTjGfwBVeHHOG3Sijm6KXDABJjTUIAIHEHcpLMpLg8CBu5BgFmTRXGrVfYZUmlk6Vjx88+fswNwyJKsO2YSl0x5aEoSzf2tRFCorubSgmKC8uLwLYDEG1mAq4r1SxImgMJ1u0OuvuH3cETIY3GPyaze4ef37nZotHL63vOf9/0DajxPbGGU+THVbsViSJcdhiXACTwXEZ5SrnIY5QuLqZZ/5lvTG9eStNSfDkL+TnSc3Nzi453FYn9kQDynug2CDKpCdWBn8wwDAP/JCFXD1raCb54/5EnYw9yie5nJZWV+BRJBFmcmEplDB5WkM0YpJEiBHXD+joJ8XsNm3yD/RDGcOOFocdAct8RdJSTfEW4+cTpOMjZIpcQGwRwtJCfJ4oF5eUu2tUF0aYrMBNoaFQ2BGQ0RBuobCIymTsYHH5OO51ejS70qcnmD+Ija222r03js9Zv3+TlffSbPdsss/9P1OZQvlVkvvRL3kqWAwyct+LIXwEDB6ho2vlLCzxex2raIQXP2QGXy3C5wlud+5LHWwB+jiV4ET6E3T7yMwB56Nq1AhFBaUIhJgS1MsM8s2B6QpCglr1s9yGAtJSdrDx8AEiew6idmB/BAA/VdxmbNcogB4LGrEO9M72xbl6HBjA3Nl5PciCHhvaNbXtJdcV8hqLw4WDsowlqPRWJ4qPK8lMAMjLR2dUQcLkgHeqiaYg2UNkgR6/XN+ysM+n89Zo6m8lv1w3UmZoGLjfNjo//Km8rhURhZu9WJEA8yHZcHKzaBpnlQHjSDt4Cr0MKp5V8DmQ+ogVUCxCJVuAEVFeyshZ4LD24xN9aWF5AV7CjsmFHv8C2RfcgB+kGfUF9F0pS7RZChKMDhARext1dS/mtF6iSk/i87AOHUZECzH8QJKNmE0eZJ5OBIhubGcwcKDIcybVw7PUPuH5zcpJLJksnIQOKmVPHwE1iN1s7sIQ6/1ix4JPGkmqaPkVHOwMNXX20UgC2jSDd+OV2++xev1ej73neqrea/H59KKTR6VqD31vP/3UPZ9nbNHeDxO+DVe+YthSJLC7yOuY68MRbNjoQ5CvwliuLaTD15Vdo/CzYlw4El16E46JxtWMh/WoRye+sbLZAXjuUI+q21DJMcpBqJ4QikTgnZ/+R/cICthf2gfg2Yak5CiB/twkysRltyEwzYDSDHOMjqXgmzsIE18CBBJQAM7yB7fXGBugTbB1TSQjcRVNxD0eyHfIF9WntmU8E5UX/Y+1cY5rM0jjebDJ+clKbEKAmNdQ2IRQm0UJpY5GKbMOWsIUiLYVCuYRLL0AhJqWziI0O4TItKUM12sA405UuosWI7NTUSEazQ1CayUxnHBkGxA/ILTiIIszwYd19nvMWKGiy+2FOA2/fN/30y/+5nvOe4+hqbBwYsuI7dRIACckPlNotoEm7s9t8qbvlEpTVtqoy5xfXwLAvVxXev1pf/wPBGE3JMeQrw2RJI6Em1CVP2Ul/MMAEg/sn0yfxsj9oIYpcQ24QSib3f07DUD5loYGbREXSLGuUJ7XQwHOCktPDFAnFNjrJuObbyc3xde3541/iWQHEtX2E86fYOHzsfpwEHtLIFSrwyOxaTgWQ5Pq4x/8x3gESNurgI1gCjHefANyl0BgPkQyxfPUqG9QJNzJqEVqvMePY3SXcCZ5wLBlhF7D5QpEoz2rVtg21aUGSrewsrVZKehZ6qdQp7XSecjptxZ0ZF0xme+enp1yFatPtiQeur6MZFMkt+94TcGhbMw0pu0FaIPNZXoas5+X+l8v7z06HTBsNnpUOvvPsNDrQsy+Wp8tZABu4YaK5Us4KviBmvgWSUmQPkWQygoypk9V8+bPscHwdeT0Gh/tgIp6zcP9AfHuxSCg0kOOdOZQiuUoAmVsCIAWCnBHE6KPmJV6/ygXfmBn1hggR4IE+iUY7XpPvwBJASgV/PgaSPAMoIe0a/wuC5ItEEodVaz3XJwH3aFWptBIAae1DkPYWu8tVqa60NV14VH31UGehuay+7EJ9penRtxH7EOS2Kt+N2ilhn7ASkTWJHnAejBkukzQaBRJdJisds8zdUlZEAAAgAElEQVTpchrGHQzuYSDX0EfOL+9RJFnbdxKidnMcs6697jAEGSw3EoEhbh7lTsUTAhKZkKAI+HIAaTDUKhRU+uNTDo7ny0oE+YK8DMS4uAhyHIfKW5Z24LffkrxucAqY+Hj9b95k9r5+ZSwZD2m1IxviutR44tjgOAryPPaLY3lg2hUqlKTW0XdOImm1dpVytVqrVK/rk3Z1Qcx2Ol32AXWTuspUbS+GqFNm+l79qL7+M8Jwe4RZd7gidz47IJEL4prGy8vydMq0UZFgviQSTbFY08FJykdugaQhwnLqwZYioUSkJhKxJRlTMxcT/3N7HS6QINPOmPtpUI/XoILr5PLlckPtMIJU8DHY+JTHcgBkSTbIEVdoKJ4Ax/zrmbljfn9Uphu8xkeJqTiX4E7V9LihOkqSjS+N3B0chJ+VYEWeJ4JKkVh2fknOsYKCUr5CLjoisTpaL/ZhWXNRwisFqF0OqbRJ39LihMTn6nVnmams7KvCy+rKC0XFRUWuW99E7xrv7/68H6QlSAwU7RZzyRDIeYww6D9frKHBr60R/7kDEhzCCwvCD1Nkj4ZkkqTeTm6umWPGnAGQTNLeSg1o4A/nU6AShsJDIZfzaw2zRJEIkst7cpwCKci46/MtchSxS7psqX/ihj8QmPB7Zu55Av6Ap7//udvb4+lJSgr0+GW92UshT5ojEOTFZozg4QSYi+ZAYV8q5EDcFjmsrV3SVpVW2+XgsrWN0hYA6dDrbXabzaa+VPRJmRlIFpnMZvOnrnrTPz8Ix8gIU+X/VqQFQjZR4ktS3VAgy6cw38H8cQWj9uQ8WDf4zx2QGMBfLmN+tKsfSUD+CnE7svn7OWbkXPsXR5lkbQnINRXSP7f3PnBsP89VqHgGBX/WYABFYjeDXcA9vpSfZizp1eX4OAUF4uG8rr4bA97NCXdgZj3g8dy7N+P1PO/v/zzgft7v8Xo9Hi9UjfnGpSdkbnJQ0CjRjZyH1CcXQGYgSD6nolTE1lpbrVaHStvqsGaxT+RJpTpQZJMe4ozTrK5ydnYX2zIuV5Z1X5koLPrX13/9MDrkIBkhRb4jSloKNRBjSjhIWjrJBtNRfsQvklqbNU384tkg2HfwLPW1PNxHruDDF4jXEu4jyQLo5B9/ijt6Zi4m8ugcE0CSyXuNBlyk150YU9de3Z6h4KuEfMMwHk3KUfAhait9UNt03Mgu6TXqRhcrFA2z1rahB0ObZE3++szMjIfsL4AbXaw+778X6Hnu8T7Q+HsfGEeyFNh4N+py8nNk7e2gSCcBeYTPUaiOsLMa8Wxu1Wgrxm3I0KU6vV3fBHmk3ml3VdkH7nernS2VlebO4qp6098jPiTdipAeI6JDDjNckzRkSAXtlJTdjd2VYBAbQFDyraC0psmthbYyPx+cwnS7fCqIX7HBhr+gfmCZml8Ogm6Xp1jheSQFMjmO3vzxXPOhyDom8ygBGQAfic2GxCjgaGZXCLn4Fl0IJChSCSn5SEdabwmEDZ1qMaFhdqFtaGNoczMEchX3v8BNBsgSK1wcNLMa8KxvBtraFhIUvkXJDagsjVAe1pwPKVLE53BUbDZb0pjn6CoF27ZaRUfQSeqluqYWG7Z+1Hb/QLXtsquzsOhjiNi3CLR9MLYjTThCcmVg1E7ZFuUuRW61JLEJEXZLg9ty1nZ7ItS1tGz/AB6C+5xfY+2J2lfAtHG9xRyAPHQ0hh7DxKkUamNCrzfxdHVNdQa/gocgwU+GQBYolQXcwRJZmrG3T2fU+irEnJsLwGjzXNvG+sbbdbKScpXsZ7O6gdtWrZLVlfgCycaCmOO72TsGFVAueA3ZeXMHgOTxAGSCnM3mxoIiL96US/JarbHsWLBtvR4UaXOBjzR3nnaWFZkyXEWmT+qrvvmdeMV9lCYjdkL21jfGtmn/KfS3R5HbTfJ02p5r+k7D7J0+OvyH2nx5ZVceeeWKRvOUjiB/vP1VM52ezKTHxRCQqeAgU73ea2nVNU5lQQWPx+MPy+XDBsMWSB73eI4s05gNIHWxPoW4IYFjmB199qzWUCvGY5ieDf9n4e3bjY1/Gxbg30YgAFoFwJvrCxyubixzQJomy4w/LMOVMIIRJY+Hb3IPc7nc0jwg+VCOGylpj4gwAWoiINVql9nsOnWqqlJvLjRVFd36jJIhUWTETpjZZdeMCAZtS4wUyv9rzob13q87gxTc6axwRWpIlRhHp0MKFEk/GRdJfxpJJwemuLGJ6D+Q1n7mb1whn4cvGcuFADKBA3kkhBouT7mUGyXNzobKJmdwUdzQ0HCn4Q4ZDQ1iGAn4CB7egbuG4YejN9sePNzYeLsxOto7FjVxtTctLQpB5uYjSB9PJOSIDXIe2rbDYVXh218OEfuErkWvb2lqUrtsZgg3TvNll8t+u+jWd7/8Hr13MHacJaBFwAw07ZRw2/6DJr9YK/MrtN2KxLB9Mo7+KyTlhx6ffBx3UEM/BHEGQXoB5PXumhwlFB0USNz8GYptDNvHlQVPRvIz+4zZOp1OMBKroKBRGDkKjqJCoRDjnTiBkwAkG+6IxYba2tqE2Yc3xpImJsawQR6fBorEeQ0llysSJohr5UI2Lws3/inNGtVqHXkQbvRAsukSgKx2Vqqd5kozVDjfPfrl270YI7ZYYtBh7NsXgWtOGR9EbCuS4vkHzSKGtXZ30h9IgOJOxtU103F92sGnV+6natzU8E6crv4va+cfk2Z+x3ETcu6PlgHLZVoSyJ5CpD4T++wRD0OHP8AWJJQKCge1p+jQUQmhhq0Q3HrbpfVycabDeUHTrgt1fxglrhkXDX9cyq0lrWuWS00T06lrjEkT00tvNrSm/+3z+T4PiNrLmq2PYin2R3zx/vz6fj7P9zvqdFIeWqul8db3NJ4oTkCibes+s8z5EaR/a8tqP8GTHKrBNXTWw6YVyBRKc5+dsCTf3Px0Jw/Z+ey9lqMgSB5kq1NJebU1QwpWq1S6QJIf51xNTd2dEYoxDV8+P2xKEEVOuS/2fnRuasL99TLgkuynWHguIRwBJCpSUvbT7ww2/1cTtuxgHkk0Wf3XXxvWbzwSNRquSaVduBEuCDK18vNenZJBkDTEGq0LQQ5hIklTjHJB3zN3r+dkoN5f3761pfJxJIcUPhrnChZo1ldzQsHS9IJtwWNXoCgXg/d3kCOAxLMdwLLbfuX45LN2BMnQiiGFXUszEG4+vtpkg+qm+6oKQV4eToBBj/b3uqd6e3/RD/7xbqVQuBunJbwWJYVf0LZRkeXvSSTFPPLdKrIw/QNXYRmNl2T1B0cM2J7FQW91VwopppKZ2Ysd8DNSEGpsWrjwQNLgkIL0F53UgrPdYQkEOJBQ/9nSimBNGndM+fz+/ZH5XO5JOg1B54nL5bLRKFhF7vrOvbwGQK5UEJA44gaKbNc54Z9jg4uDg1qQJNj2yLxtHkF26s0JdJGmqSl3v9vd/9HZ3qnJiS8qBW90j5LCbyQAsVzCSbJEke/OR+7GdH4a7UajgXOS1R9Uq6Vd1xpFjeuN69nGFL+V3nSilQGQUBGCZbO2HIAcHDrBEtumPAvmM+AkA+Aj67eA5JbKmrPdxwTo5et/YXz+N6TnL1+++vTVb0e8FL3ZvZ3fyee/ymdSdWKxxVLxE7BsMiyIIBmlL7gYDLIerZJRdY6MuOZzQLJTZW4ehgTI5J4I9bpD/Wcvhi5cuBsX8ILES1gp5GVYxIimXQ7+UYKfBORGkeU7BGlcwZ1GGx/cKCxacCB/KGrsurYuwqWKrFqKm+mlMprLulYnRTmRJJ6pnSOmjbZNeyhIWfSBe9cDgQhIcuvLrb+/IIs7uKv261eQMb6Gx0u8XmfyO9h2QIyWfEYNb5CmAg+2OtpGxlchjXRSDTY7mHbQ52FpRgWS9ObmXdbuTrM5ZgInOTU1MRAKhXr7z04s3RQcEgpPl4AkKRDmk5ICxfeJIvHaq8i39ZEkX9zTc32jc6zDnVXwFrprux6yuvoICLIL186SyWydmmyml5016WJ6HiRts29yIBd521bSVP3cXOD3/ghokizmciu52zs72yC7rzK4hAYXWSDnn1g02OOu01gAJCdI7J/pnRC0ISDVBH2QaSmtTZGI1Tvi9TZ1N8di5mE8qHPSHTo3EQqdu/XFaUEcZVhZgrKcZJMEZuE5USQIcp9pv5UiZRiTZX1vnGCR9e3W6hqy9dSNG8SyDXhUMyaSR+SQh68DSGlSrsniZnqZ7O9iug6QJAeStecQpALSRWLb4DoXvrwOpR5u+IrhZmuLdGm2eXBEgfm8Ol/4ii/XAccUgKwAQba0tI23OUj2AyBZBeSeg3YASVOq7u5u17yVYpoj5g4zSDIx6e4duDDRf+7WPwTfE8SFlSW2zaErAuQx8orcDTYbb61ImRGKb+7Lge9FVx+uynYVCZm3AVFyGA0ieEEqzzbiVvUpdTarnsmuZFZWNOHJVl0MnCQkQEpKO+hr4hR5YpHEbSVFe3SBufN+P9i2vwdJcnLk5Mdf6sYHD3BxkujSkkkl1VJ1XZ24IEjiIuG9Ujb4ahZBkUEWMiCaMQPInJWiGiIms8k8fD4Bpj1wIdT7t7u1IEjwkQJhaazhIO4RJK/I9/aZ9tsoMoqtrT78ckCSstXHJQuRCNJQcI8iZFgNrtGQFUnxvvRsVlM3q5lZmZ2d/UMrAUnpESRrZ/EY8TSCHAJBgnHTHqd/DgobBOknK+Avtnl+RZipa1i2Y+tre0cMIUyKc0Aa8Y9xBLhlvG3MAS5Sh/k4pO9DihoACck/SpLxgiKp5qvNkebE5YR7YGBi6dZy7UYVgoyfrtwlWY4+cp8gdxX5P4NcvXT42+hBQV4q1oZEkSLudiWRHJ6JpFIRWHTXI5yoqMvOzIh/FJ6ZnQ2HxybvAMgYAUlTWrttBEAOQtReBEnSIEmlR9n+55PoIVGSHMmdZJLr1nCtQ2LUOyTWWDR1mAlge1sjxmScuEjHh/XoIikGXQbUNqyP1bJaqrm7wdukZJiGSGekuWPUPTwwsLR0M376ZlUtKnKvJN8kSFDkfwFZnBwnhIpTKtFoiSJlpS+Tv7T2tDhkYcxAaOENWySXy0VSAw7PJpNgclnNzEy44k8tFdPT0+OTrbFYrLVDr9TrIZPU2l3zm5uDg+kaLPeIl1R6FlQnESS5AoEXPdjcIiF6e5vzlwCQ95t5PPAiRc4UQZAoSPCRjjM9aNk05TrBgfSxCJJWNauoeZpqYMwmU8KcGAVF/vPmD2rj8Vp4CPDEemFpqNkvSFJoY8zmQR7jKB4rAWlc5a/ClAohJYuurhlXeZDf9uHECqkIy9bW1mRRErSNRVeawahtWG8ELeIHuaEtuY67M4s1RIpHx8NjY2P9y8t3WjtaO3RKvc4JdY3PmwOQaTZYAyWKAiSJn85AoJMYNjdg+mGhA/uCNF/JxwsOI5nuUwNHTpHhlhaw7Dbesj2MCwsfqIQg2kB9qW0wmykrOEtGHzNFzLFRd2jpSlUcHGRt1fcPCQWCuKCyUrg3Kd8vSd68i4rc2KPIvoeHuXvOcaWbTKl8sxY1RnFK5dKzgiKfwctPZdjewT/w+Hm0jKyVF96KjFxONjtEOcqleCgpKawfAUixZjY8HR4fHz9zMbRcVXvll3c4kHqwOJ8198QGnpKAJAU3rgJ14h6lPX4yJxA447h+3eEoyLGAsc1SIYYsAOIYMWw1AWkBji0tDkegHSyb1jI2LMWxpNT6PFo7q1SpGKuLVjL6VnOnKTbVH7p9aiMOaoxX1cYB5CEiyT0Fzj5Bvk8e32na2GAg16VVbCH88XFxSoVMpxCQ3NOnUZzBuIQo16IlIGXGlEEqwtvnAGOWu8ES6kG8oT8LJMPT0y1jY5/0DwDHqqorvwHjpvQdOp+d1easLgQ5iBtAcuUNSFLlvxrBGYEAOZIOJ/rm2shANH5ut+EIuVhDNsoGD0z+F/AgHEhyDxRathL0niYghwbTPnCSdpZW6RqsXppmnLpYcyLW0b90+y+nMMqcBpACIXAU7BPkQUWW7yryYGUjW32+9nyNdG1Qe0YcSMMe9+HHZGCFA/nQ+BDnJ8uAHpmxeta3R5EAUgpyxBOH5fCzcQs9oBeQZEUFgBwfuzg6sVxbdbNq49TxO3diDIC0B302q9dlsxGQuGRWgxjBtiP+zvoCSNyqi8yYchOS5PSqFdwquw71SIYOQJFZAGmxENPGUAOWzdo5kJBIgvJZdpDVMjpVkxVSSqc+Zk6YYhMXbh8/BRgFYNuY/aAqhUVFCt+gSFLe7A82x3Z9pCwa5Xqv6C2NRtlDHPchsxR9qzzIb/rKuDGVtVVwjGuk+12qyOQ6tlnlcnImBVktwwfkPZAnhy3T4+NjhGNtbdWpK8d/NvG1Xt/RYLf7bF7vJp4fYleAbYNHC2oRJG3+D3FnG9vUdcZxBFWqKngLXxaGFrTLvbKtG8fxnETX2HGTNK4T3MTEhJsXMUHamWxcZEFAWiMjMQnJa1HaSQnZSFErLUSaxstkqiAYH1hA+cBcPkTkwxAKVWUhZR+IxqQpliJhZ//nOdeOnYR1E5N6bcxNCDL8/H/eznnOOb84eFDYNbWMC378SosZ7jNG7n0m7wiMu5GmUkv6VMtUC2XjXe2IZBFHWBsSg5fAiLeIapLfZutQNUWXAvGLZ+JzJ0mRneXl24RtlzNIS/GwxWYR5z9FbZ4+XGql6a5F0YXynNoDnlZVrUVtc44236byYp0iv6YShtdNAyGSR26oBcm6P4amTkOQF8ZniKPTGUzOp8ZTXv8EgexhkJqbNnfl4fCokGRXQ3ODECSvBamsqOQLN48pwuTfYxft9fN90QINkCFEGw41sOyozxF2F0DiHSIRt+QK2JoUTfVLsO0zE92DN5IJZydFbCsk2ckJUAnJjWHbBGlvtPMzDT0WKZLTRTGnCse49HzJBLlQNVwMknp5SZZPnr/YoEjqof36kDniOMmHcOGWFHk11DI1tu/98XmrnUGmk7WpuVTc3+yHj+zx9ABk2K3FHA6eRBCSVGwfHuw69m7vu3yKLLXp1t/h/r06fE41tMCdZiR5yx+qau7h86qDi6Rgc2D/8a5mv2L4bsuqwSCHZBOkqugAKQGk7grEz1zsHj95c6+VQG7jBAgYhSQtayMXr1Ik8RNPe0lCvkRia+Ww83yYm/ioF+0pN5ab6Y9QJEz9RRVn6KWKnHyb+j5pshUMM7lJQfL6vfrHV0+3/Hzsl4gzaeboTCdq5wnkxfZozC15wgCpuFXDQZL0DcUo3vTf0pu7uqhrd//nEGSlebhS4aB3mpA8RG0bk2LnpBph2aHQlBCkTdcQu2KqIWYpHJRGRuWooiherw3pq67rgXgbSXI+GSSQnW+ApIVB7iwtuV+pSBKi4FikSIouCB6iUXLxXxxL2GlyRzmD/GKBwG1fYMb03fU+cjKTWQE90FzOrGaXhS5rUF2HKNKAo50se9RpTSffuzw4HtcvNkcjmkQnyLrDquaWZZYkAkO/u1/VbW0IN718vgqvMqypKT6cPH8G4ttmpKm5RzEblk2CbLjrUR0gGNMMMd8ju939GlKDHglJl8eDapFsO36xb258JpEcFYp8g0ONGbctPCRJg2cbI7ZZ2dgbGwuyLM4jtz9ZWlp6Qm2mZ8lwQQuq2760xOkP3Z59QQ0qdHv2BbWxrFfkw9xqNsMqXMlmVzOTPIh77/qdq1NjU5/2zYxardY09Gi1/iZR65wByHZbNBJ28VG8GvxWzEETB0OGwcnkLf/dNpIkncIQMo/7KhzQaR4VS5Lcxe34dTVs2KcfkCAb2ryKTPwMLUK/AaSGhFyLah0uxQWQiiYhjSWQE+ODiaSV4jb+ZeWEkUFaxNBuoU7cBKQ9L0Z7cdQWvWh0cace0JFPHM43pAgfSd0ryC653Yq+erKlRJH/fJjJ5rIZwFvO4sotXzePRLl/ZWxsJEUE6XI2gmetc35uFu4KFseKNCDJsNsEGSGS8Gbeu12QJJ28kgdJJN/ZlT+Z81BekVSEEsfTIYo0+4912RSZpnmGDHdMgIxpNPWr9XR0kG27JICU9Hi8u++z8cGZRNDZ2YmsnDJJ4mgx9bg2HvkqRQr3WKxI6j8RF0WXxcV/VHFbyvDC4uIjuqVhtIWFR4uPWhGOPjB/4FHrlhJFHgLIXHbl+nKOQGYJJKUpj6/8buxoyvmW09pILAlocD6Y+NmcjgxFY5DPpmnnYk3mwD0dMyKypt6S/O18hg0HmwrznE6qmN4pNW0K2Lup8zm0h1Of4w3tUsTHE9+GWxYgDYQaFVlkB1Ifl9craYrfhQSou69v8OSpRBCS5PJGKFJoscxSZtlk/GcNZD7UlNbawx+YVxXfD5szrNy/MiwGdquq8s0r/AP0N2j0p1BrL08yyBwcZC67urqaWSaOX96///mnIykRra0CpjOxN2EdnNV1GtdVBEg3dUqyl4zFIoYvcosCrJAkOckKXiu3my9zwwVu3GCQdSLzEXo83tAsRSknvU1TDA4G6WOQmuLqaFLdkhcfoOSHkwzEPxs5kUq9Zw2SHMtHqbAxOVrMQLNzgySLFZkuWHdxN5r5KMwtbCm5pZvW4m6W1qqn5DOfF5YzLLNpZ7MINMRxNbfyOHM/8+uPrnxyARzfcm6FUW+FlwTT5N7g5dSsX9cZ5MCzZ9Mawo6qxWJk3MhVfIZ0S0H1ISR57Vqo/k4NL9+k5w9obujQw7yH5NqwItTC1SFzdNMsLQDGZEMo0hGF9BVJcqGqiaqwbYD06v5AfGLk5EzqVAI5JK5yCjajFjNol/EIUKkid6xdW8TQzybpz38141o6UMk+c7igyIeZHIFcBc5VoPz7SuavX370zW8vjMx8Txy0uBW/rPRIwJpmZr3w+IifLlakIRuaZsRikCQs0mf4VYUlScdEf77vQeWdO6BVUfHj+h/Wi9PfORNn/1hP8XoPnWtOejwouaMCpE+ApLozCu0rPS7X4Q74SkjSBNk9MXJiHuW2lQYuto2+uQ2JuaWQ/ZRtUOQOeqzzkXa+XmcWsYocaOtwwbRX4BtzJMYcWTbuM6TOb3515kQ6mE6nb6bTCX4hkEGkQLMBxavD3iSADGthOQI/GTUl6TAkBbbt/0M3kTxw4NqDSrJdscSwosI8/JQuxstjFUh8eo+RHgsgDTkii14Xtwo9Drg8hztg4gg3CkBKDPLozdRMbcJJSeSbwFhuKcSZjYq07NhhKVYklzYE80evNx1b8JlF89qml3jZSpuu4PXlpUsv123HkqZi2xpMzsXxP1I1VerRpqfD4WjMcGvTQpKyw3BJalQEbl4Jj6ScWIlFhtXVP6FD4OtIm8SRx8727dvfe+RDm6JRUc0gHYaDQfocEXxcLpdHsjUNEEgXQrbf6wLIbihyPjWPrAwp+eioZdQUpGVtaHe9f7QUQAqSjfY0TDv5evPaJXO0+eF19gDmPi28QYv5IvZrqboEj0Qgg6kAnKBEUgkD5LNIJKKxcVN544h6dCUSUfQ/dU/QAiYquHHRLILgWV1dWV1ZWV0RwkuoxewIaGj2qKpKtSANyUGRQwbSH58DLlJ1DeDRBJAa3tHrZ5Detu6+ozeCp1DcCJAIN8WVtqUU486yHZayIkXahSKZZ/L/vhXDt8qYQMK0rcGZuFeK+xUCSUd2Gsh6UMeJeONwu3QJpY7qD/xlgtbL9vaeO3fAvGhXc9YmcO4JiSP9Ptl/HHUhPKEJkochGeSQw4dkSu0YgCQPH+4BR1XxeP1+G0B2t/W9D5AzyUTnKKWSTsoi87V2GWVAm+aQIiE3HaSQ5XcB8qbVmgwG08HkrFcJxCUYXdgwIEnZIE2a8Sbq0vX+iCz3U2j9irepIZjAyZv2QYEft3zcYs68Xug9fr6hqx05gEK9GwIkkp7YbYD0+RxuRZUGOjwDHYebUGbjC8nrJZBIJEd+euNybWo+cblzG6WSnTS1/cpCm3zkWmVjL0jyO1HklksJZzAZhGknx70uPU4zfT0MMibHKE2JGDBuX0TSybZlOYqaGOb91Z/Flj8ElFfGQ5/neMeG80eOHGnoamt3QWnccYCQRekoRe3bMSjSJ9MfhJtsBJKitwaQAb8NwSYeIJCJFD5Y0iNEaWHT3ibs2rJpnW3Jl4j2xryX/F985GYtK69oY/l2Re5FlWhNplCrBbySCbIHFaJDdoejEUOGilS/rkQjtD1Vvx6YnaWlyhO0YWefYPp7fp4HwokuULTBE0h/kyTJBOnjycPYEIF0RCWlJ9xj8wz8m7TzeW3jzMO4wJCTtLD0kkN1GDx4QBhbCMRoR4gRaFYWeCQsZA91CWKqVZfUYFpfqokMMqHIPRQ2EZvgZKEXH/ZWy8WmObmhuIbtQgjKoaCVoJiClyJhH/IP7PO878iWUidt2BFRbEee4I++P9/3+z4ub9ugzfmiqIUwaeRy1nvv7x8iSDab+TnR2oh6/PVLPxytmrDIUd7+3SC9iQR9OV/6ilbD7xBmIUjkmrnTbPNpfcVIWSkl6iI+FtzC9Ows8itNksoMSgqFdZHzpEAJqzw+/uX4l1LpEa9/8wGypdIRrjqg8FI4usEYWeUvAEPGWp+dXkcxxd/PjTZbs7fv2Rw2EuvjiJJWOmc9vrN/ONNGkBQlub+LGPKryNC1+zU3Ji3y7VzbOxte9MKvzrIMLgaZ8MRwS9/7XSDbM4yT889TqToLYw1B8meA5I++VtDXQBK2qURXxXmwWLVajKnww/px/bj07dHx0belb0v4q35U5w454h0uiVLMt3HXQoyYI19zyM1xXQcgeRLRVjmPiWhiGIZm5RLW48/2D3ezi+32bn5OoAxJ577sEV+9bt6YtMi3BTm8OpI0PoPfGf+alHD4bZCIkWi4T5vtB5b63FqJpjTnYK1gu8Q3OxsrHBSr09PTRRWVJKedBUl8EEHJYv2TlzV6iEsDlESKj6jwbe5abAiOyfVZxFvddm0u/KAdadwAACAASURBVPDAu80yU1dVmKMBg0wY7322//3u7uJ8dperFmLtZ2o0sHIz9JodxP8H5MWvQFIGY1KGhQeRrxNmmZBhIcgZgkSb+ENdrT9IIXvasbWfT1wOW7BWQchE7p7WJchIBCSlj69+o/4Iu4P9fQV4YFjPHeVwaYZGlqmoP3FZZK7BrTj0k5x1bdetOlFbu/fwoR3Rq6gkI/g/jdxy2jDg2gS5eJqVBtkaG5F8tY70w+Rohdy/3hXPEyA9z3uluvalDMNXFnmpuZLx+p1+JRMYG3FBz9gJj3+n/NCblGGhRbJNzLabi8+VFAJlKmfqxYMT1xFNTXKde4oohaqqGivGADKyCpOsVmMxrlKqPyokaXxl1REeFxYWiFLTADOhJaICpEjaG08YHnG7A9e1C7qb0Mx7nz90IwV2orBIw9qplQ1j884nh7u77cVmtjXV8k3ymj3ta/a1xzFOWCTnUHqXKDNieCXDp0Cvl/FBhq+mWSq9c6qrhC9HXML+KlGPm7WBXmZ0k0p/QoZFujZBzjQX/2KoP/wVJV3aKa45tr2+wVM0ySoHy1GdR5RVhEigEc7N07PfqN+oNElgtI5KpQVxpUHSymnASZAcuBQT+ih+krMb04iQthsruJpW3rr70IkUqnpkFU1iytq8Xc7lHn/2yffPECTx1rZa+RZXf0Jvtsgb11nkGEg5hzL0Y1xlEPwSP/xQDlY0zqWUQCAz+NLXXPHVVS64f9uRQizhCk8iU4nA8zpcFsp0OcEm194H3oRrE2S22V4sKc9fHCN92lWkbftA7iOiBioU6IJqhEePFUmyGmO9rQjXNox6nRiXlpaWBchcOp0GyIQicw1BInHjXVnXXddUC45rauXP7/7Xgb0CpIKuxtr8aJkg9w+fzc3Mt3fZJOa5ajFW/4SuN8gbb4iRzBwcSWlIkkLi4mU/SLkVhMfeSzx1z6gkQKGVbqYiDh1zz1ZMsAghlowUZ+hSfEWcnO37e7dDyrCMgqcASddut7On8w9SK0+fp4x0uVAsuK6LJMH+sKij7tOZFDjlhwQiQfJjyRF55ogUeS2DYXoBj7QmTFKvFrnO/gQ0kW6mYei26qD4MWt37z6M6lWef0QhaRhffLRs1XdQ/rRau+0/iSXJKTn//Poxi98EyUnHxnmmMzp4zc/PuHsDO6RddQRjTlfIlEI+/ZeBbqMb4Cq5mGsR0M55QJ5TLcEBJ17OvWFjmBHviDcOEr12G9lm/qmlPP8rQNbsasx03YMNsXq4VnR49kN3uJamsKhZXZUgJUc69pEwyOUl+vbyMnCWfd9miOSRMPZHydlp1zZR/ri2bd77+ustV1+LqbwpmsRHmztpK37nk/88m8s35zkfgDIyf7mlLTrut7ZIT+z8B4Sqiudvc1MopBHsZIA00xAyDT1Os3ijIYFBnxIrUmnA6w27PsiO1L0JdmGW3UyAr+mN69lctYjNbLtdUoxHRipXKxeqJ7brJDm0kiwW11zHhVU66J1XVqJRRTj3akSRfo2EXQfIpR1hkXjgGYYJjnhlTJwHe7Kxzj3y5IFdth1y1NIA+S+nUNSjEbaMuMXjnXRu8xZAtvLZxewfRD0+FbqZvylrSQbLt7ZIKQfgj6T4X+j2Go1BcAAn7gf6YnrFy/jTLGdCWiDYHfS9yqX+l+/asNBOJwhv7l8wRIalpMg4SHQ27XdO2wCJNnEFtqFotXK06pquzdaYvl0swCPhkAoMMgU7I8kYQRKjQYMsiQgZx2MpXqvV6OG5ROISJNI/D30mfzLLjg33RtLeAshIYa0Q1SOoN1HJP96xrPinHwJka3cxK8rI1ihrhyTMt7XIzK9BdoKNs+Cwh0jIjcLK0J/ik9MsZxUwFYA6L/0q3KuE5U146Pgi2B8E8QKpszakDMsVyMOZZrsNmNlmc7f9g6VG0STeq9m6In1b7OcXY7aNeujEJUfNJylBWswtRwyR8fhmPL5Ui9fi8XgNJiksUufyOCwSGZtr7eYyMDomLfI+QOp6AS+BZytaySjt5HI7H3y4/2yuxWwj6sh8KJQPXV3XtjdvKsglQd+m5D4C5b3OkDq6HAQQ5c9LoeInn3vUUkLm7nryOwPn530JkrbcaASQtxsUbRHyYIFJ127ON7mOdno68+KYZxKVaG2rrKhmwnFm5TnYYtWxT06ckxM0LJpMIqsiRgqQtEdwBEZyFDwFSLzOD5FJIQC4sXFQXlZdoEzYCYD8bluvOi7XktWoVrKsxwu5nVsf3zqcm5qbfzEjyx9pkZcguSn7mgGB60GeC6UzOOyXfkvtDYN+6qDShQQpwyHziofc7L3klFWGClVe5Xw0Buix45HzGH52v6iIu4+5dpMZO5udQ2tjGKoaVZXa/XtRBR2IvSY29pPrVd01Tftkz04kUGyTUGTVB0mThEHuSIK4bm/evh1fLr8KkuX9z+WEajJE2loOIE+qVdcW6212Dm36ox1j4YOP39+fmcq3CbI1x/JnSgZInyT+TLbav9FrMxd3L67U4jLyNDsRBDkEzRZR6IbAsxsy2Vx04LEXYcqlUYgFoAcjNU/YqCfG1YTkiJBhuQL54m/Z+XYW6ebFA8tAUINJquX7W4moFo1qhaTc9oNJmnvmyZ5piiJRS3APXJUWeSQjpMRYA0WCrKXTJurISMxP2uyyn6yZZcU1RfGTyP356+9+Wou5JkG62+UFBkmj9PePP73zosW0TdcOCYvMi1Vy//q1Rd54E8hw5kLkhDNvrJUeVORQymjRIjzwp1lASNbZQ1bpQ1+IRQYGKbfkS4L52iyUYRmph/zj6bvI1u1s8+mxkUJI0+HZEXdry1RyZLkup8eKVd3e3jvZ2yujShTxD92f6sfIehoWGRcWCYa3P+JBkpqoIyVImiRBJn+qaYqJrA2DTKQFSJ0gVUXbMhcWrBJAfvHeLdTk+ewVyLxYtxjjOG6TfwxdLuy+ZtEi7FFOpV8ZP/BF0ZVzceJLDKigicFr+gHKsIjBlrNzanHK70TMHAmz9IUIS098gnDBf+wGRwtuBDnTnG+/87SeUmOx2HpshWs26ftlBRwSLidDuUIeiznb23v/I+56QttGs3igkD10fCh7Gdj6IGSiYkwrBEZah6APnESCOiYmGk8KRRZdx0QKoslcbGyIp6zrYlzGKfXEycJeNr54D+ksmmswpgSSvYTmUjoplFLoHFpmDnvNYd/7Ptlx0rTTGYapgkmMUcA/fu+93/vzPW1XTdM04CKK+AUGnokYukjUPlF8nG8ms2hnAMhF9JH6IGijggT546iGCFogmVABY9IGIF3PUgFtzgAgN4rFeX2usrmw/PcfHry8RqckAxf6bpK9/OsSa8T227GBD1d/bp0qLtAhlcFGlX5h99bJNAsdcjmZdwmeXR3t3x8v0DUsT/43SBG7fxmbvvbX/ZgYgi/NOzKWvjhlLc8pAick5AgCucJDYrO7R4E0jDzApCsgxiHwgKHv6IRadgYwxOFoBDLKgAwNAxlJGqoIejxpQeAXAMinL/hkwlTEsNgoG6Q1V5zXtFKpfvvmd3fHrgOQM3T2Z4ZNog2ApG5yqO0V+MUy2umtw6c3kw+vYBn8GT975zlLWOhvXMNy0kX85ps/d5sT2BKIjEeyqOrkEHw1UVQBSBy0RScphbPp6t52taoampGPgnFjzUdADGlOA3adWbJriCMDkgpyCuQ4AzLiWA1FBB2ZtiBoC2DaT184adBDIic0yg0AcrKugSh/WL+93H10fRobiQE6+jwsf3wkL/V/GJSBD9cjf2UjLPixd6LzHAxb/eO77mG3GQtlHScVWXElGXI2Gb0WuLNQQhXlCE1JspwkAYxASaIZ6AL1WEyJ6TvEmM2jEi9lgI61pToAuQRecpiRDEjHcdS8hR1YDDYQ+8FHbnuWWVVFkTTKa0Sbmyy15ktayd6YX77exSFJgAzS7VNKkgF50j0810devvIHdRGDw2THaQtFhKDgQljg8SQ1XAqXNzmVU8CjMSBTIS67u1cFUprGbLQRnSUC8FFntQoqfTK1ylIFGYm2DUDqGJBo7QflD+85TjVvWRRIRQenUOls7SUTRhUSKLUMQJLN2Ob8ws3NVqtVXNjfn7468wC5R0dNz7tOpize9ZFX/rB2bDA4XDM+TnN4IJ0f510s2NLClmlCzIbQwGVXcMEPH7bkNESbvW3VQEM2NCw56iyjQekDlFyqVWpLNdvOsGAjgNZmRTQI267nJtcMyyKqleYEBNLubH37wmw0qpDnlMtlQkqxzfrCDwslRScbt/fHAMgApSSiOQTgKBLSR7LPyMAnYuTZ6ziZxtH7iMu7KTxKFJbCnApAKqJpAcTjuNVHssJhFYCsqgSxy2PdEcK1QRNsJCTYNgBZoU4SMhsWtBkjI0BIz3vRxmXZoMdFRRUU3e707pj5tTLoAMikyqZemtx4uHC4fLMI+eJG7iU9ZgwZ4mk+0u6CH7dHBz6SMvLy4OfKJwNSSuJBr3HXSaWcbDYry1IawqkuckaCC+GCGrB5yK+tqlrdg2iDueCstrOjU93TioJtUyDpiSYbo02eptoUSBeSmogDlr3bNtMJ4KkFHgPo3Fjv9cA3rhngjc1yI0/sybn6wnLu+0cT3NzBQRcYeZXO4tOzX7QLhgwdZXy8NPCTn9JHvgOkI3kom3mZ57NZh4cQnUxvJwBIIkAMj+BGtFSYC6VNVW2oJpAwA0jukB2jX/LBxwRlavWazSw7Oss0Oza1sRnpeo7n7U0R4Dmkh5yoEqLn1zu99lR7rfGjqOgNALKiF+v15fnvX3YnxLnm19MUyZkL/RyRaSCqxymMACadWhlE7V9mZPx3mKj4MJCRlIOtV1dywLQdPhvOSknIBhXOACA5ulouJQGkCTVRNVWaxUSRkjuzzEUy27YzNXgt2nZ+lgIpskYDBLHxV67nfbuGMgAr5KJgkkmj3emtt9fL97ZlRc8jkGSjUs9tHk7/KxcuNpv7Vx8EMLkJsEmqQVFy9HMkY4A2EDE//HhGBs8MTJw7ZfHRM5Tn3Xo87rruON115uABYzeblJLpBAMyxMlYTgR00zcsM2FWBQ1iCxJR0wzWYGjhW8xrKJq4IBpjETPtLA5qQMz2Xtwpq5jUqAKIK/icVNZ7653OvTuvshYxAMj7ZK5S2djoPhobaxabG81rVwMX2BERiuMQKwM4YEGnLEb76c1HRO3C0emBiQLb0PmbLtweUjgPyAgACbFmnHdwvxyPiQzoZgQSU+EUApmSuXBaTahVgUQBMSzhMhgRxeh/+wEHDRvrurrPSCA4v+J4rrfbzlsy+EhBBQVOQIhG13ud9TudPSklE6PaMADIhxWtleuOXX3ZfDyh5bqs/nPxgS/LT1KboVTb95Mjl4evc4EMnpmqoMuzC79RPz6j577fBZLnI/CFAUjgTgRVUFhKQnQV8wAkJ4YjCCS2DRFIVUf2YRFXY1BGKZQs1y5lSrQcOQCSNr88z3W222pStnQTtA+nE6Olk6ke2HZvF4xANCBuT+kAJNHmc9enH+0/Dk00c4fYk71IT78P1dI+D5ya/PFN+/KJi3wPkNi5OgOkD+yv95Xxf/bLPqfuPUY/BiaIklzyMHynMHAropInSoiz0lnQPynIHsFxJkxTaEFgweG9Wc0n5GxrlirJUgZ4uVgaAjIMQCLPXbfaTkiyJQCQCZGoRpQQe6vX6fzH40Fvqba9tl4E0zZaG7lct/tVNwx+8m+HaNoXcSQN4/aFfpp4pvYT+BAjUTGzgYnC0WvWAPOnKgaMLJwUNfATNtscHFolMvTom/7whb895PRDbyDYuACjAzISvrPrYuMQJBBQUjBMiDZWIsmDwkyBUldVRTUELVOqZZCH/hXta8lSZhEZiabNqr/hJNbReA8cR7X9ipctxUDbJmDbeWGx0+ts/Yj/V1ZKU50pXOuVzxcf53L7X788uKEUm91HeNjmjJ8cVMmxeDGokL+PkUdHIwV/+Qc7bUMfXxO/NcL24hfiBSyl/cSGUEbgk8LRUTwYP8J9xc+PGFgnS0X8e/v/qxB/8vqU4wWJAnz0wMBdZ9yNrMCvLMhGhRgGwBFKJCSIRkBJGYMuZNuZTIVR8gRIlETRRYSyhDUNn5EhHOrjnVcQ9xv3PF4SFUIEPQYRx7AJuf/vra1dSO9lSdRsBPJ+ZdGIxSBk5w7vxkKxyYX9u7i25iKbfvb52Gckq0z6yc17GImHsvEk5+rrAh2YOgoG43S9OLxnQBaev/UrufHCTzgk8Jo9kGD1yRt2W3AwhjHC7l19M4JbMZ7FR9iZxs/eDOh6vIKtAHCPvIOJCA5G8q7MicAbAJKTkol0CsW6fANMG9Al0Vpt6WGGiiCGJusxRAFF37KJP7GCZxpSr1wEcs3jHSB5HlsVikpsWyutb/X2QP9nJZHY7cqcVqk0TG5i8qCZW+7ui+IXG8v7YzMzF/50kSaLftI9xMiBiwyMMCqeATJODx+x5R+3guy5Am/7y0DYkxqw/0ofZ0NPwrMH2tCtF6v0b/boGzaGQbsPq6t0TgVL49ivWH07/NCbYzrfBJEbsURhjq9sWBF0wwA8wlIokcaNpZJkQXInGGS2Vv/yy6VMdGeAJMVyESi5WFqkzViVASmDj3Rw9iWyV05GHMUSW5oJGjOhluySNvW0t56W5JQsqmv368VWvWKbYS52cHCwsNw9kEOTt/evQXoTeDAcbi71i7ssuQmgmBx9LyM/609anDS63hzRdjY9/87ObtMJSHwPH/3sD1M8e/5/yq4gtI30CtsYctnoENpDLioIiwimIjsIzKhjxEyQxlKWWcmOxuNNIfLEeBONjEh8aMZowCLbqYJruSPb2ZEDDoW1KHUCNsHbw552vcHUPhRvfAnCgbAEnEOCcwgUCjn0vf+fkeQ0droOUSIiOfjT9/73/v//3vfieIGDrfKeDAN7ufG9xDkfPhTaU/+6dd0AQKIGFJDshZ8ZD2twe12IBEIpw8AtM8eoahpdKC6rQjQK0Tk4MzEyMjI6SjeLfW54Q3DTiwYDFUD01haTDRQCBMiN3nRAZUXFgE9HDhmWXjdXHqzYHIdpu2bNJsxFSxejLL+0m8jeuLET44aXbuysz5/1uc3GNGd3+7rPdHtQ0o3OqWNCmzDyzVs6jI4KpggCyKUDaiRA5l7gUJsDHHTRNUVuZenDFJnYEG/LMAiFxw6bzUMyfgT/uWsf720Px1p15CROVcJTQ2RjGM0DwuPBlJg3UAuVTjOMmiY91kI0BBE/ODODvQujZIRsG0gIbWQkXsbmRA9I9BLCo6U1e6OoRVQ2ZNplCO2coku6KT142kijt4VYM82EWbWkEJ9KLWVLpcd3r+0yQMkb35/7vOcT4pLmnZ91k1+Emh4vT2LkkZEh5Da12Wx6jgxdGM7TJF736UtbQI4R+5CpDhmGd9UVJ1OtEP1p+l5PSfWOnPwgbSA7hymS8KMHyc5NTKmaykCBziEqMgAZTQ1iz9LIzAREN1kp3UoyP6rrZGfjlj8sFeyOEyDlSmGDBSCjdUMS2Jwg5qtV3Vz5blMYgvVYbBj1hL5QlVLDpWQ9gcLq3T/wTCB7bWfvXA+tJH1kr9jj627Fto+0iGDOOYmR7wN5mqx0B20gm/ebzemDZx8GskOGQabg0GLotQtk8z6+tw0k7A6LROQdLhIrC3zoZxSlrChKalzFE9o0w6XTEQ0IGkslrczIV3SGLF7B4m+yShLLL3IamRM9IDmqxg8/r2y8CMK3iIpJvaYJomBIjlTXH3x3hxtKByq3DTM1azlVJZWs13lI3buPH9+NXQ5BVTlw3kc6brwb7jM+j40ETMw1H2PkKy+0oZJu7schmONu+YMsQxf8rq79luHKqw4gO2QYb10x5eEhWSHiFGd8b7xVR5J5aUhIPLsIU6P2flUxaopiosaPuO/CUskEIdnEEkm0/8lkqiMWQJmnWA4SRk5MICU9oQVR7JIToP7+55W0CmVlOhqqmw1byAmK5Uh6vfp0U+YCAbuhWOKitejU66Yu8qkYn90FKAOBpRs3977p8c1TIPGr2803p9xbG9/xBTlhZDNO7Cr2yXKI6B1AEX3whGZtIj+bwueY1SFGqYlIB5BtGQb+9WCsNaLJTTZj8Vctpf47TDWozgmTw0OgTz+iqfUBkIauyBHkJF5BBJnLQMgYD0BigxJyEqHLE0aSgdv0FtFwhRak0YbB9thw+PmapiGloZQ0rTvbFUHWHQmCe/UHO4CzEhVHrM5ZejKpz6Z4SHGx0rXdx4lh/t6XN/cGfPMolOxp5eyO6y+fW/4cy0iqtHhFyx/i4fX6Dc5XIVtEWv7gC4gEaPrN69NHgeyQYeBrp9FUBCohr/wh36tl2/AuTFwX+nGXjVXkJFkkw4IBa6StK6lcmlODaHkdCF5mo1E2kZ3JXJq7NJepZiC6KSdJspnAW5s8XSSh/tFY6jYbGYL/4HlFVtVImmWjvGk1vi5XBFFyrKppbW4KQuhr23aS8NwO9S2afLIUYjg2e+1xKTac/fLqzU8H5ttXN2fc40iPkac+xkiUl72GKtD1TaKTbA5aBTmV5x1g0w0Zl/beGtmWYUy5U3BwACVZEVqjcPztQwsivcM6HBsPEMnJyYJtlMtG3hK1kBJlgtgzCEAGINsksmR8+cVLGTpseyJPMw4wcgRDGyhp5ASPkuQG7EVxw9bU9LgWYKOxpF5tvNzOpUwHJ9gsPLgtyA1FcurWgmQruq7wpSzPjjOxLFAywF+7dfP7T9fPfU6LIN8pcrjro/0M5CTN3SIex8hXcXQC8bdUFd4kG/+hN9nmzekmKWDQHeQZwfDZkyfPYOkjBrwtGYafbAlRhhGnHwqOwmnCpmisvdcmupJJAqRb/vRPvrBtXbJrloAlS4joalkEMgpr5Cj2GV/CUb4ZCcogPBMnoU1gdWNboOkmGIxENraKkxsVWePSMqtF2VTKchplYK0l9VWtqrNZLkuK45iLjmPblhJNlJLJVJALxmCVjMWWfn/15s76+vp5XCbPen3wngrId9IW0a0j35tk4wkovP52oObhWxQCHeCKR8aoUTNo1xJ67KipCPqxuH428an49On4WLx9+kOKSBxc0etFdn9BtvM1AFKKMhwj6DmAEfWOAVgjEciLpBP2UqaduwcRSIx1WpO7sR1guI21F4XwZCEnqJyGX7EUK1admg2JTNL1xdnqyqNHNXulai5WVyVHVwKxUiJrpliGKe2W+OHE1Su3vtgZ+NX6edIIRlqXOo7SXBHV8XttyNrHTLLx/gBWHeBWG6IWS8Y3/vZMm/dlGPhe/z5xXJryqoJ2m9g7PPfBBAOAFmmMh4sbWl6XJLshqZB2uVAtFxCE6DCV8g2OZh4SJB3kpBfbiGNGIqskTTdylA2q6Qrg2NvbX8wJWlBjVRmADDC5RsOG3K5LfdboIl6DSauSuShJj1ZtARuOS6aZhE8NKnOev3f9yq2lnYGf/3J+/hNPbtE+SnMVuyfVkSebgXSNPaF60ThpDZk+0of4obcSgd99euhDLcPal19Fmm3QdKEXr6Gx40vQ7Uat7Eho7xXh5DuCvB2KBoPDUOMlZzLYnH3B5SQBkhISngGUsOk2FCEkaGtbAGOauFpwORnpqG5xUVHjNNuRYK+o4Mg0s+qsSI3VKiyYzoPKdi7I8olEn6krHMeW/lbis1eu37p3d2994Geql2xJoN3OLyyAjmEkmfT1cQPo/WeEb9isdLj/0YscPx6eeTcN8N7O80hgIG4OMbYL8IgSEy6nl528tFAej0BRzYxvNQTNsBmG5fkshDZaMFwAWi6TIogCOQJpvAqkBGCBkZW1O9vba2lsd0IpVVoW5BBgqRY0MZeWFd2xRCNlWIaenHVWVwBH3bKeSgI2HwOSdX3WyjFMInEvkVhcmPviqz//9O3vBubne9ybhrOdbivHhvZxzvfvQzPl/5AtyAlzbtov8x852AXwitjphll7A0O8UODyes2pSU6uFzZ5ETUdESQtJDPBGM8nIbQvfHbht5/98+HDi8vLy4AchjYx311uAEPzxvbtl7crW3IwGHQbZHtVFaocWdU2hlRR0WSoqxxdVEQzD0EMWWZFAiBXnJwsCxWVYVOGYeqSwARiyTrE9oI09/e/7u399OO/vplHFfmZTkH+CWvkL75G+P9eHT/muxIgqTlfsdgb4YrFAhdRdVtqlBsLW0MBbmgI9tlqzo4G0FiGTwL5AEgyaPfCw4fLwEGgJBBy2VkGQkov//2fO7e3hRDLsrSLDoAcUgMUyEIBgJSVPNSo1b4ULJOKKdYtx3EWrZWVClHqV9QAqyRN3aoJWjRm8om5hbnrv/nxT3t//Me3A+fQ6/TsqV8f9a35XyA7DMj9v+yr5abSev7hV/n9R7Q/FMhevPoiEmWgJDZRp0O60ajVHAfoAXsThhniNEVkg8FYgq9b/+Xr/GKayrM4vg/7sg9bZ+niv5LFQkvTjqHX7mBvMXAr09sWerlYuF5lEi9NYLVFy87isI1UUmALI8LQCzq9GsysYjWDkhL5k7jZdRlEHRwUCTpxYuK40ZhNTDbxBTMk87Dn/G7r6Lq7p1jR9umTc37ne+7v/M6PranES87fQ5SX0SUbShr6arprUuyVua7VV6+6BElt7EMhWV8PIEFBcowEmrywWfQIiViiV/J6BhImIaIoTicsk/A6L0sMH5BESRL1tBdvU0vwTJnHW9pf9dnyox6jY3bFXVyk0xXhcSZ1xNfG/+WR/81wZs//N/yK+tUPs7/hgB/8F/6f+ucN+/FD8vmPWdtBPFI95AYx7uf5gCiEoCQOJWU7qZcN2A9ESeBgALKEnRu/8rCqSh0Oi5MNcQvnYIoFhmvgjHJJMNu1QoYI4MFkO6RsCGlxClZfQQkCSM7kUjC6FcFjUmDFHIBVUgqImJQSvSJV5ozHo+xNG20ylZ0+X/DJtHHC6jPq8slcJA4b8AAAIABJREFUPPwZQmn+q8ym7Nsg8/ImstY4f+r03rPd3bWHjhW8v0GdnfV6EiuZ8zquGg4y/ODhpUtVVxb+mV5YXX25emR2ZcW6/NXx3++aWxyfta4cP76y8tGfZmdv357t7Jyfv327sd37Kj5fR4k8xPDWHWFsvMM0s5X0jRWGm6dsNl4MRuKpIHs+3WSnRIuFpiy8xWAyEZBKhB0bO7f6l3MPH85VfV1JQjt1pWtt/MpaF8s2HIS8HQqSPqoy9UqSensTD0qIEbjAVGGz3RlNyLE0R3s9ChsKhgSBdir9J05A5c2IIs+nGU7uZSg6mgxF2WcWit7tGT584NGKY2V61F2UW1xcrNEU58JraCOpbN5NNnmZ48Z5ea1tjfs/Pvvd0UPPn7dMTnZ0bAczm83rzOvIkPasrUP7zfpNW7Zs21YVk6Xk4veLI8tGndE4/Xjxfujy9lt3tNoerVZnNTocPqvD1/r3Nqu1db597LPG+VIDqJLCP+zA2R1biRLH1hTsePLbRFsgKLByKJmSOL0Byusy3BKE8rCMeGRDya6Gy2fWvl9bHF87Nze+Ovfy1drLrq5Pg/Hubkg37EFZBWnCMQL43AKETIBHkFxz4ZTdFA3GYumA3lvnUeTkQNRjohRPfz/oH87yBFaVXo6J9Qb0zlAqFOq1U7TelTy8b/n6803lFTNFuTkAckgDBl5ZvTEjyRHk4H/AzBsc9LW17b8KHI8QkB0dWZIE3E8kN2/Gee3rNyHI9wvkmLRv8W8jMz1Go3HQ+OjByEO5486Dnp47GBRGx4TP5/B1Xmy0+lrn54f/CCAtfj/uGPrDakmjljcItHCqySZFIrIQvyxBSUjrKVjvDDY7BVFmcLlc0T1glSB7uufm5s7Nrc19OgbKEbJ2zRk0VJaZNnIguRsnqVgsAcqg56TegH9r2A7Ln5xI3wx4lbpoMhkKQT1oUur6++MJhgd50MQQkiLlGUgFZV5PW8riGz55/t6X5YsXLtwCT9TgCBZN8VBO8eiLHzZm5c/gOxjzrBmOR7Mc76sOaTZnKZZ/UV6Bc6pxfiNy3LKt4JicOLVy/cHMhFFLzD0zkvz4xpLbODljnHD0OIwqyFartfNeNHmybZ62NRVif1Q445F+dZsBmy6aw4aIEExEkjGDyDFOJ0UrUafBFhAEqNhc3r6aPTW1Be993d3X14Cr47VreOs2SPPaM5WXESQqSXV3G4MbB1OKHKWnOCkRgGQmMpEQG2PSkil6Kno+Hg0pHtqgtNftjSdoMcCD+u9dYCTwSZOSZNm0havfXXLg8GTHyMhfL1QsgSeCRw4N5QzlaHI0L57ieJDME/K3UQLHxrbGq2czgd2SCWw1ss1vuuQ6AnK9GtkFx9iSWa3DMZGHsQxmvPHt8UadVjt6fdLYY3Q7jFYA2Xix1WHt7I6ePLm/jrLZMMGQNEOqQz9uNwDJZn+4mVacMUlmn/mbICI5yWSKxj0UFQk6IbLb+3D41E6cJocov2nAIV81WOPUgj4Hhc5i/R1UgxufXABIiqMoOhBIiP7wFIf7NTIodkbpx22aqOLxWkyK61RUoO0cjx1cCwuMIEumUviezHN2vSd5eHnp23/df3qjSPXHIQ0ZMZlz9+5dclvnux45ODjxmmPWIbe/dkhzxboK5Fj+uLyinAT2bzGyt21rKagMnYSg7lEpgi3d0U7vN+rcS+aZG8DWqHX4HFYAuXL80nkob1OCRT1wSfZp1L/CJLzDUDA2Oz2RXiGe8Dc38xznt4sUHYyHTAk54vWWXWvoQ5AbPiAZm4yf2gPSpxZYAkesdfCRkHq0AffOKJwTxsESwRkExtZsZyQmKKdiETEdPdEfTw6HlDqPweBsL1U8nF3kQB7oIW9LMbmXcg5EU08Cdotr4PDy6PRork6n0eRCbGsIx+qh4n+8AIVOQA7+hHIQKIJ1QqKBwP7u6BsLpHm7+d1co66QxCFbWp5X7r2thbBWA9uo0472aN2Nvh735IORL6a1bgcB2Xax1feo4Hf39g7EGJyQSZ6ZFfr9eH4DG5/9QBPnZfIeb4JJsNwUz3MRiRc5mgpEWDYhB52luz0N3+yp3Il6nFzCWdtdo870IihrkWYmuAWndM1Ek4Y2AEmZAgZOesbrJUmKhFKfJ5g0OzAwMAbFocdD11N1rnYn6AMGbxOhuVhvRI5FTLCaLkC0U/0HHuXnj+bmuzVE/GC6qSb24mnxzzf++pc/exMjuuPgRJYjSTQtHW84JPijuaJCJVmOGFWOBGTBsdq9VsCYWSC1bnzLn23U6m59VbEEbgqfWY0rfaePLPtaO9vm75XuJgUHZumwv6kQb4L1F2J3ZCE2m9J13gUhFAMZxKVlhnMGg3pDQJLlOIAsa+gGl9y5E29pUK9PApRZhJVnKtV8g8WOsIvs3YBD6mmOo0yinhfTFhpAMiCgAFRsYDg5lmJTScVpsDjrXC4Db39CG+rtAROzkIjFZUGIR+SbvN1wet8RArKourg4p7gIVkfNUDUexBl6+vTuL6p/QI986zWIwufqW5mGcNyO7mg2V2Q8cjO8yBIJHNXIPtR3UgUJzgh6R6vLd2vdPZ0O3Y3HI0vAFT7wTXz5Kn7uz75WSNvRXXq7ze7fSh5QhP02lJPA0NZcGLbZmwxOl1OKsJy9Sby5kAIHGmApSLyMzIaEstIavJu4FkGSi6hqK7MDEM+QtwxJ8jAtIuCJRHBIGrdx9aLdn2YAZK9eio+lYmwkPjwMxeHcWFyh6mnFVVpm4J8EREuTXU8zsViChTIVxAj46KmP/k3V+cc0kaZxfBP/3CwYJg17TuJsYcrEwbO1ydkfl14HwrSlrUVwqOGSK73AcWW9TTZVdoKsKSht9SQ3XbFFo1ljW3etJXrlSrKEOzk4FvRE1yCNGxPvCHFjQsK/F/e/e553Wn6MTfxDE+DD93m+z/PO+z7vYJTRaBgNEMQPGA3e1nL8/fr6xtbSZukDFGElOeLjIXrEwB786afpCsiDJKwPbamRfUCNa9VqflG2mtYbcxYgWQ5tB8UgT83wb7cWVt48pxj8F33xzkj25mAYQH6jKFoeL7Ygb2vq642gRAxxY++neNTGLFihCVZMPj74fSKuKKMpMegz8V4gKXX+o6OjtRVI1tXVqSRby4u8t1oRJQEJveJp4jcBF2fAKxchVZqDrL+33hcQAoEHBiGUnVeGRvvHMldTmVxBDHE8L5yz2Qz+72NBvtcI6O2RBGRSMZuIsCb25BdnoxSjoZgqTVUZJXCs+erZ5kaptAEgVXx/qeRHYtgY2BdBj2otfr4c2M2EZXN1WY/bkY0cG+suXbhOUR490iMoaRpE6WjwjN+9ueKgKYbSRSlL8V688JtVT3juektE6oQqGUEeRtOu530Q5gDSaAKSrKulRVL6vdDfBGPJpBJJZUQsS4JBryjaTuAU00tI0g0sL+FwZ3VwJEoT/r6VR5IAMoHR7cL3DVroicyQIlnoue2ShEs88mgh6xTHRq+eyaVyqWTEqe0yn7PatNr/xuxakwnIc3IyLgLJRETLa899MRilNBqKbtBoiB5rakCPYDfH10ulI/uOV0CqMIlhq4JEx57eVUNWA8WtPUZzoPqXZUFCirz0p/4+WqcP6+iojgQ2hDZN6Zjod0/vLtCOIoDURS3RycSF2wDy87grpLB4dx9pDNG0PzNgn9OOc63bjWaoFYUJ2ddl8tsjI3FFzGUiWCgbgqw923+qrglnOp/qvtoEJJvIAE745AlGLCTzuCDUJkJ/E1IkiGicy2L3mjk/64Ov4JVjDx7YA/JQNpcA/xo/k8nmRuLgK10sDj80+ewuaCsNLk7LxeK5LDwRyA0t44NhvUUHLBsaiCRrVK/5avPrrY33e0FuG03ZsafBaqa2BUkKyEPNlRRZVuRBNUMCyBtPKFoX9jAUKYBofCBdanpmvl1b3Fhhog8pqMnvJZePrYY9T0RZimlxsmY76QnJ7jM/tC7GdhOke56ztricsp1lfd5IpJAMpe5nAn6TD+It6FfygLGurtFd13a5rRHy5HITmbOLmiSvH/L4YJoEkiEZWmZytDsAsQ2/ufp21iBEYnaoMOX+VCoUyaVS94FWPBKRtLzVZrXxJr9g1mo56AK0/piYGynEE35tZ8uVQUhdYQ+UIQ1V0CU2YGh/REjOljY+3gtyh6Nq2VM7NSQWPuRWueqy1VSrVoORvf9o45mmC9c8FpryDDvohec6Uv4ASAulGcjPrrx5s9iAAW+h/nry7GtL2NPzA24IM2jbyRy+8rLFp2YcjGT0g3xc1hanUzIYvN7Y4/h8RCy8ynr9vA97bQMnLpPhxI3uxrbujrzqOOpyOYZ4Pl8GmW27JSYgRxKzYXGrr4H19SJIcyyiSC5OCo3mRDDsbMadgjyYlM24+G4z+PgA/FevAN+h0RfJ5gojCa/WBoqM0o7Fol6v98ytgusQ28YDtDUbs0v7PtoDEgy7R9Wj6jS7ax9SQlavlRW5u/bZf7T2TEI83acHq9H3WBxrUzqiSAft0FvSA2KJKt18s+SILkYtjvA3UEteHLySDciQvCCYIZzxFAP0bSA4osmgwcxZrecEJxCw2wPKfCGReTWTwI1UvBkng8hY+OCI59rajn+fqsMiyL1cRonaXK5IMtuWwPfb5OASb8dxAmz74V5QaCABIF3O/lAqJ4YSOTSbZGIkYmN5aJtsfl6A37HXKwUCPqM9lM3lko/N5pbRwWhx6tgiwzDRVb2n+LqIto0naKuqtmbf71EkWan4rqLHSg15fjuw0bTLgV1dBgkc732SSyYfKP0vomE9resZTpcWiN2AIMF80j+MvE2vv/zn27UXS9RDZviRpXj/qXv+f+/wTmseJ73W9/ZCIY77aj8zBnkjixxtkCM5syAIspScGcm9mnkV8weDUMTY4OcXUu5GXIkEmI0d3ZebaoGjuyxKcp0afojhxBO4mwpHBPC8lzOzRr6+njcY7LIcwh2UE0MiZEm7nLqaK2TjIxGzje8ESfqNeD7Zy0kBKWg0SEoqN/JO4c71DxaXbjcvMVTaodHQK6WiR8eQmrzqw82367tB6geIYaNjbzfZRI8HVc9uJrVPdUWQByrFeC0e7I/9Yd3hCVuo4QHH1BJNQDIUFfZUXYvfTaefpdf+vlZd1DE9j4pr/znz+wJ8a2arqwvnQIJT4+jcw9hi815oKqDitlldgoFzDcmyUpgcmX91p2D3B70sNM0uZ7cw6nbvxyu/ILgbW7tP5cuaJH/Up6xJMSSBIgUzLv54vRxvgqQMLY4iSaHQkCRM9MvZrN1oSoxlMqDNiGTFV722oJHjDD6vC0DaTbwgSdlMMiGfvHJ2+sXqxjqjq3qepjTpdFrHWPTRqo+PVO17trkrtB/uGPbgl3tKn2OVuEaQhGP1WvWBna4m8zj2OOacczBgNXT4kX7jmIMqKzIc1vSNlJi0I828vPu0qNMMXH45edHzJJV8rNhc5i58q4UDDHtxl9OvcUySljVzOKXL5YJsL42FkpM/F+Yn70S8fq+dBaE4J9pOyKhHcpMAiLG1u7vVDe69jP6NLN3q9XT5XP7WKEhPkewGtovvAtcGkL3GIIcbzKX+kCRIiiSnYr6/+UUxk8tB3hTIKMqg0ewy+DkhIMkBk4kTOEGcT4jd4390f7k4u6lb3IKfL01X1dBHjqR1egdE+PGaD3cUCUZTDuyLqmNPVTLkod0gmzFLqsu5hOO9T466lditsetRhtGAJFcHhpdKUO6UFRlu6LuRZqCxctDTb6YW6IG56Is/n/3dfPJdjJvQduExWARJSOJRGj9HhqtbcX+D1C+FsqnJn+dn7sw8wJ2hUMd0Tgx1nHa6kWMtIVnrzpebHLwuxF253y+D0S2eIC8c7GRGkJeANLL2iCw4BUke/ZWTkxQukYXWOjQKaVJRYq6WTvjiEBWcNhiQAoois10GzDG5XGh8rKmxbu3rZ9HS7IquQeM4XsVgQclQ2HRDUfnBjtGoSz4/VhZ9pqD0OXZ+ezl3Cz8oyAPNKsaDh4ggj97Op662jvdBK8PQYU/xx57FUsPz56okh4eZvn/RkJ81Dlq38HRNd2369ernF+du9EcCE04cB8l29RrbccxZL1lHM0kGM17j4TRr/0/WGcY0kaZxfJP7dDGphqZHdD70xrSdUHO0XujRadKb0bSdoZ2lhraw3dXSC+w5E4katE6kkHJuOWUtmcqZThs360oLZ0HPs4FNXBfZKgdZpUiELptNPInn5pJN+H4f73lnBnTvgBAKoR9+fd7n/3+e9+3zumgBbF55s7r54KPL6F2xaLCKR3a0BemiGpCI5D5/IxjKDgTxoF+FON3or/qX78+UvQL4HzUio9G402mFvBHLCjTDyHJYEIgYB09b+jPH0WlvrliSYh4WDX+m2nEqjkNOSPG8O2qlOSsRK3szR06uXZlcsYwsLVlInbFZN2FB1Y1eMee/2LMLsj+hVTSDg4NrKCAPD+1KtrKktZWtZMkdyVZANpbHT/Z9vAB5ETPo+8mFxOzriXoFam4w5MM92PUnJAKpn934/bOX5PDixq07039MhBg26UGBYje1Wnt70fAFwNjb2xtj0cwPBipkuyeZy4rlKoC89W+Jg+iBNc/K3W0d7PhbkOgOEX/XaNcRlWIjfJ/2KyRL5WJJBelUQBJQrBNiNosowhchUnHuFcVJ3vg/OCGTQSQJEDmIyHY7xeGSGJYkwRVtJyhrPCYVcwdPrt16WNOvb0+YfQZzbenzpYnmBguGoRqn4ZoG8h4SGrV19v8JsumdBKl9Ko1xlePhsrfYN3iWRPpiNIDLmvphqbY9Bw+NoOEJ7PqUGTgafXNv/vr1um3YvPHPB9+ceTI1VZAjJpBR5ZBTb6tS5fRCzoyJSGnSvJNl3XQuJ6aLxc1bmymRkkQaGM87RjuC7DhiqN63oqxuf4ejo02RHHThpB8w+pdnwCGiDhA4SQ6BRM00WuIFgJhMCqITd0rg7l9xlJdq56SSN+stlyh0VMXNdeIEZYd1zYuCC4cgtkNaLS1fOXf75cP6XH0FIy3G2c8nJycf1nSYwWdGMXlNp4Hs0Vo+qOejKPZp1fnsklQz41HlhwN7N5pUjiA1/pSU6/t+gUT9M8yC2cyPvmiqvQZP7sOM5kRC/9xNYhj4hXtzG/sfL/TfW79980xPYurJqCvyXSQKZgS9jQZMj9tuRcNeCRocSDKXZl202+0Ad5Ipbj67nIpR2XCYdbvmu09dCrJt+975UNghG7SMGCo7tIBS9ZEaSBxAIvsoillRlgVBCKNBdjGKQ/thUuq38RSkAUHIZaHEd7koDiKSi4mSwCddJmucIiRB8o6f3LxZW3q5ZvglSep8lTcfHX1zY6umMxhJTKdr3qOAvIcqmp2A7DuvKE3lf5XmqPZ1QAtI4LiO+hXLKWls8CyqQpEJN5jJ4ac3tpZWzMBRAfkkAmveaNGTPvPsytqCvnLum2JP4klBRiPXo612UGhTa6sVbIcdXcKFprEPCCWvw0OzEU+mLIm5B3dSPCfx4bDLPRDqHr3UxR5pUeNRE5xDSLxPnerY4Vj1V5c/CyInWUKHgGIEgOw1oXeRSbzMCOl0GB3AwONxCg33pAQqzpdK3uQHyZLEMm57HIF00iIvCAWPqRP+MevlvcWxfWsNq9sjOktgxLA6efTAjcl6fXFPA9RrBl2zDlT7ntISV53PoNKE/LFy+h2O6v6CtrL3qlZ8b5MSkENoEzabhYA0ax0fo4G0PX22tLKFVNtnfpTAQhGULg1QM5Jr9bM288rcJwDy+lWXC0Caeu2sCyUvK84S6HQJ4ui6moSFBm7c7RaL2XC6+KdsmPaKPEOzIQSye+AQulKppWVTi0jkKCFRQr2oPKhCogwGwUiWlf1uBSTEPJ0Mi7wcSqa9MTsOpQssbJrrbG9vh1qQL1WrySSseZFxOe1cnOIIKpYS+IInEjc54XVNC9PFK4vX6i9nG0aGjYbF7cmm+sb2qrHhfYvRBiGpU+xPf2K3l3uxb7fGfhuQO6qtrOoDmmajKns/6oyfPNL3/QtM6+iC3piH72xsbcEDMJYAMv8dCcnZQOr1tsXFbyuVmxf7j/dcv5B33Y24cbwXZ1iaMEGidIYJHAw3OGJ05obP8iEASecAoLeUIuA3IhoHEnKMXjrGNCoZUr1NCWEEkI3+g8HuoHr0YhrisQ258pJ3ByQsbR6SoxwqoMurgCK8bHGwpvH2f7WaRNGb26ymC4VCiJEjEJFxiqJFNiWIhbsE18rNZDLj6ZlzH9b+s10ZabD1G5uxnzZqq5UlY3MzuCCbTdfcgEDaEm8TpFrSHN7dyf6ZiVQhAsadxrjSGb/SN3hhRW1DQugZLdjwpY2ln+AXPgP56JFP/jJg9lmMZh9JGs3Hb/1q7UVgoef4x1NTHghIPIpAsuDCrdYw48aRYicdDJqTIoRoKLm9JYnnc6lYLi04eAcTmn86OjqfVKWmZSdHHkJpEsKwo6sLYnIaHGVuRilvglpE2q1RUzgZFpiBQhI9q9PupNFuuRONQGxtFYV0rlrNFPL5Qp5h8E4Oj6OWBc/LeQ/t7E2VM6XxTGb6RG2r6bFP128zGGpL+sUbL1ctqAeE2QJghq69pwiNWhoCxvNKaXhY5Ti0w7FJw6g6H+UuQgRS3asJjl0o1o3Yzv6CwbKQqGy8huLGaCHvPprgo/0kZrFAQJI+8vyNAy8CgZ4zY8+nplwRuxVAyjRLO632zighs1BXfBXKOBiHKBxLyqLkAdkR0mJa8OaEU6fS3ccY5mn3U89flNwIAQlrexqBVK6pApQdXcHgcuNyY+P4MtLtGXTkQgNJJMMQj3mZxnHPAAsRR0AuIdCQ/E4uxkuwtDPo7wWZRTN441xMpkVHMj8ANU4uM547NzY2fWJidXvRaBm2GSZqi5WHb25P6AwGw/sWMoBZdFvvoYpGE5rBvsEfdxT7Z5K9G5CKgdQS5P5fDw0dPn36YNvgH26ugixj6uYhkpgXv3uN2uNG8m5iQowOkyA2mD5AYgstz76+GAh8++H1xBQYNnvUDhHJsAxhNTlxnA153BHXQEZEc+PCwv2S4HIxmXJOpNM5rxedcEYTfrrn59vARraoK7tRW9vaXdufoaPPGb9afCvVNjpxSkQgIGVGDoXyLEomsszHwlACchzXHo//7VVnMumt3s9cTdKhfJ5wUpwpToVFlpU/yA+4cDGXyZUBZOOns6vrIw3ksA+wrdcrjxcNYMWbGwwjAX1tq/aexvFtgtSE5q3U7H2H5G8ApGZ9hpSG7sFPTwx+sbi12mxEQTmxMrdeX0n8cLQO9aHPQn6VMLJf9pBKYbNA6v9+59mN04HAJ2cSzwc8LhZAmnBa9rAEGoWpgIQiOyPRA6EBhr5cFlkPmy7mBOd/qTrDnybyNI7zFxRCU5u1CbWm06YSaTVU20l6jGamMwWu9JhWcG+3kJDjOoGshltsbrqGyk7XqiWw4HVK4Fa3lIZCuF0JayIICHolKrAEUAyJpkf0hSYkvvGF7+75zbTAljcDLwb66fd5nu/z/H7MLxijhofRGYfPxGeeSetxdclB1ZYRnsqb84m6NlfbORTo1cvLeZCE0XfCJtI0yyd4y+nTJyBz9HX1EoQfWpuz7v9cOF3bywmLiwOcyJC3E6St1o9AekkmATnTZosLPfGREQjt36a100pFR43BmVt58gtm18grDgps/cnu3mrR4QQp6/HUHwUpz3TzGfLofksDcS0JMtoz8Ov/dmdXctlpjcaZHR3dyna2Tu1C0dEazDPzSXoGQFZoNRvrEezy86E7Gwvtl1s6bwVIlrbocZ2PseIMA0CNFh+PemyS4xic5xkiQ/m9JMllYpzRGBt2uerrblgH31vn+G4J5IEDkhVZIvXf1cNt9fFluB5HICeG69CqjdHnI0COrMjjFy/qThAxgaK6wAwR3irpQfG1fgQyJooMnwANgsG0VfmDDCEOsowvmBJi/WP9whUAiYpp2J7cfL25NG2OGAwVaClRgf12fmsrCyBbC4H97l10n+OZg7XsfIHJh3ahp5EVeTzq8orT2rXZodmhLNgfbM103tQ4b1/9UYkhRQLINIR2MqlZeBcxf/XXrQ3zP78Pt3RS/4I/2+IDC4SLJG606X3ScQksTxq9vQTJs3hgJODtYnAxLghWBzUxgUA2PXtP44Ou8up9My4JsqS8XB4Hbau3lxtSnz99Hofvl6ulJIn2rdhwGj2KmMXRcWo6I/SDqZRXDBJeb/NZtCGmmRPuLcZDIkPT5O+8scoI5gdin+J43ChQQnx8PNbYUz01jeYJLVhudHTz0VVMixa3VcASM5fNFs8WSSMfaZFGDmzgeCyvxwJIU4FkcfFJqNimPEe0veJmNFY16NQaNqFh2tzMQpKcXtrLzJhVpU5Mg0A62fkwplFAF76+8+3xJxH7xndPn7bcbuNCLGn0OXw2Cw02B6qN3keSaWjBcYYm0dJXJuXp7SIgSQr9go6TjtO9ccNDkyyaiUvU5Bypzgd3CcqbavUEtfjp40cgiYZpaE90wOohmDm4J5vgHeAT7uuMXE+cutYngq/01p49fdbf7Oaoe/fiXIigCR3L8kQtxD1BBlMBFkeVbmQ8zg1e+cexnQimMoedqt29pXVQJ1oCWwWQ9umrS8lc0f5ilzwUh4p96nCGRDmyLG98ThYc5JEv0FLNlBTZMeKSBnpP09brn4ZeJ9GKV3J9Mqz9swFTquwv55X8fAemUSWxjm+fP/gbhu3sLPw9E6dCnCh6bRBzDouRBpw66bHDaZ4WcZLGHYyDGwnSXQHgJsQnBJ0XbQOoa2jyzJFNruPAUS2ZcVSy8yDl6qOurqM+f3r48M22nCQnIEmiR38RLIic543gXPU6WzAej6XioVBvMFjl/ovbf8EdoDLXKCpEi4QeZ1mv0eanGaZXEEmil+Ni44uUmHgbtubgAAAgAElEQVR1c2wHQylSq1KsTS39Al0ctNg5qNwYZlcaVEUt+y12u5Qg0bLh/uaKvB8vkyiWHRpDSpGNOLb3iE8BpGotu/JiL5t0QnOjUc0/1sL9Ecg0lp43K5Ehr7nzMxVWbmyYdx6k4pQoBLp6bVClwTmyOIS1DjiiM5IIHId67jDGOFrsCsCbb4tTdUajtMOn4dl70lp3rrpcBqfeb2zUsh2qrByvDrRtf3r474c/S+VGqjZWq3eO5oEPyZAO6RwwItUfT2UEMPldP7hPu8EBeal71yghJHoZi4VhE0YL42WIQIhlgmIokBmPC4lWALkeUapa7IYKhbLGrAUnUqpa/ZCsKI1Ae+xUFB2MKtoPWXHJQh7KkXlF7ifIY8fkmh1t/3JwATgaVLkPuz8lsytOjVOpCqcxBNKAzUxik2kzplUY1h+NVSdqpjfs9o2ve7hQqK2vz4+mqKBJkvHpwfekoZVGMwOc9Ol9wZhIiH2hBMvfit1qt9qiCCQIcm7AJSdENSTEfYzoB9tAclu97LGOf0Qgt0uqlxFJVG08dAIim/RJ00YfNFFcf388A3FB9XW5z15odl8gBADJQbDX6nQWMUGjg/1E+OXglKzU+AjHsZfa7wBIrbMlAlnLXIMZnAZDqSKXy+3tXYWuTWUokha7AGQ0ul+xEUpTQZB/MJGQIWU9yl3NN++i7d2tcEt4rZ7ZHVpZeb0C7Y1hJ22GHIxpnTOT9sm0HdOqko+ef33FswEc7fZwZyjGcdevG0GRDnT+B4kehE2SPoc0fCF5h56BMGNCgdAtaK4HGqJt+Hf19a7uZ3Mk2l0hcyw5rEc5Z1ZWAsi56ucf37x5ACAlAySB9KDIdgBII+7T6S9KsQ06o+DVjMo2gFxMCQIXgG5Sb2FEAsTLsI8BJJsIxUduDDYOXnk09sU6pMgOlaIUq+lQghU3KFQfcruzo68jEUybLbp7eHY2dVCyCxxNZYVKc1SSpDSFRBzlFNl+d6FChXZxVORMxUd3z8xubR45szIfViiUdq1zctIsKVK7Njb29PdWCALMbu64lBEahetdhBefkU4vRCf4gUH3QYkBI+mAq6DgpemQ2AQgGxtc5W2T3e31rgYP21R/rmC+pSpzuNBIY4zlwEzbg8+f0eHbENvnCoqEFMGjz4rEffr7Pgc4/P749kg8nklV/dd9wd3sFRapkEAF/VV6i9EG5Y4hkX/neTYhjMQSjY2t7X86eWxHqQh3KCoU5poaDDhC1f5gerFXnH1hWtp6UZRvsaNSxT4lO8ir+yBNZfkiI8uxkCDzbvwm9NmXIwatwaBSGJLFz4c+rI6OXl16omjpVP2I2Z3J9MyCBFIzdf7XcCvoUQY5eLsldE2A9+V4iY5I0oMM06jNhq8ZNP7BQ5yHFMVQU0OCb+yOljdM3nWdc93wNKHxbYGdWn0gSHhVbktJcnhupq4SXW/LSbIO/UsYelY76ZPWeCGLkA5SBIu9OD4yci/zg/+E210rUot9oT7KX+W31dosOHRb4CJFpONQf/1g48CtS99vHjm1o9F2mhUKaK5BkVCzVYrc6Nu3Wc3S6Oj5ZNGrV92gx+i749/ke5rDgiyT8EmCLCuTrXi+yS6kyFcbTgCpUsAHtLY5u2t6u6mMTK+9mteWauzTq49ffgWiBPeV3KgJP+5AEyIAiZr71gF2Eucd93WQJV/6oNDowFQCxhmULllRpBHIgSvs48bu/3N1vj9ppVkcN/sHUCO5GvYmXIcMmMYINVBXSNziBAXE2Zq5MtLuVGIY6ZglrcECKWB6l2pbF4yOMAJxUy0IFWfYTAkai1N/FELj+KupisaESWPsizHx5e7rPc+9gO5CDOoLEz/3e875nvM8T55mnmtlhNfcpde71IBxoOp/XrVtF5I8lBy23fz99y41kieK7WYAiS6SDYC6UDJWqrS3oJgplEPz87HD+fn19Ufdn3/7l3abB0C2POq+QR/xVqlIUlXTqbQr7MrJiaVej7en/3hh716SGIb/iyWVmg18NIMUCj4uT53ubWe5kR1WGa1HE5MgL3vxhkvmBw0gEU9osjnFaQWdIk1O60JIgBFoB6tQQHzcPj/dwbNXr76wSCsIUXKbWnQ3xaVoQVGkScdX0QZovshMGcCSW6JxRUB7Cy0ka7UgSKjf2qY4Kthae5C0y6JBv9vrTu+OOJt5Tt8SD1ykVd1c1VZ1SYV0f830NHRkiyXiw7avXDRHFNvvmn+8AJkCkGBvtOiSWL9y4nB9fv5wPTzZ/fWf2msck2ilzIZmGY2N11Q1CvCc8CztytEJnaFnyHp/9f1gJbSIGguUbFxqsEhBOtBmn51vgTtPnkcyWNmlQpMYrC+C5JbabJrjPrdQaAolm1MS5OhytpXAhMLvWQKhEBzWToh4m99rWNJUYKJMRpO7/iYlYrPxVhEVj6LhL38YAoOiDAZDOmonc4s5GbokHHIXqt/wjbzmMy26A1YGFdOt86V9M85nzSbjjLprpEvdTAd22yWSbcyP5QWSErEY9Y70xyEi+U9kPjsCv/qVdnRVnd/WqEKzeH/w+txrADkfmxxDN2D0TU6Oz35n6+6WQ5fVKK+Bth+6rCjpnXBbjL3Wno2fFxqq3xMYRX2JSTG2YUWEQpvFOsuenU5dSUamklgZw5FXEiQCWQlyrGQsZDG6C+uvdKWh22ymZn9Tn38eItA+f6TJECb4A4Zf+eXFF2oqtH2cIKSpeFNcxGcTbI0ltQKRPcxnI5AgSoNlJU1qry3Sl0Nq6btem2Qpha0xJ9slySj4vqDO5zMYXWBw1UtLLhfSYxU9Myt68Etzn6pyRpAS+mjamnjtNS1JdLgOFPmrw+FHExGFsk+Onpgi6O0IzyFNvgv/8K/2z2qGYrPjMSg1NgBZo+qsUZIyBTxOnbXXaDF6rUv9b/c495IoRX4JVodNrWgINK4QZk9OlvMHmfwWHipDHJ/x/h9jaVxRqNlcbsFCMvshBwuCdPY07C8DPnRkAsEUhFgC9t7mi99eU4nI5mb+OB5PpTTDbKLVHE1Z0OgXQhtImqmNOz4AKW+/BRXG3pTT0hcQN6kccjmyzqRMlt7VGTcoy32TE95HAJIp2OVfuYodNqPI2pIbYlCK617XieuQJCUFkB36kb8NOTrs8MhUbgRSpiR1Hu9dCGxIkrNPblyrGZp9OjnebesE3CoAKe+TNwFIt9V932jotc4sPUzsgYvE+BaCJSWEfGrFDCAhTZ5lT/YjO0QGTx6UXXCshyZ78HJ+LJBE7/2SFQdFDhYyJAhyNHG+nwEXiTh+D8UbvBWefLscmWrJn06/+K16BUCa2aBIKp4yM+s6UnAPGnP/T+s6n+PR14sd9mg0lWNSJcSeUomGCxBZaZ/RsEoZfn4AINVHMy7ns1o6GzarSza8vJglL1ob5rgkvNbEtCTp4576ka6WPscbGTwphx9wKt3pYJu1p2o+Fg7HYmM32jvHW2KxJ52dNuhlVDK5X+5QNQWCQa+7p9/Ye7vHeJSYbpg+Zgs0hopWaBPZ5hUzLmQJWKyPDfn8cgZnZ84jCCTNsR50xuEg51N5Fb0LXpy7X1Ik02OjaQVtInkAcuZ1ZO/jeVZAnypDaRISJYHjW/vPux4cJAbyXEsqlRLxW7FWgx2F+DAbTx4DSZHZfPffr3R//+6WllSgYXkuB7qEmCNtyjSpUthlil0fZdZQ1OoxgHQBSFNhwnMxqGCWvQoLDfD7OQlHIlljDp6KxRDbc+UgSUiS4Ok9Q31KyMO3AJFC4fem/ZNW3+h8eBLt+WnvHh+PvRrv7Lb1+eWopensu66wB4M63czMxsztHt3te5/2EtNvCQG1ymILWjEcQLIh/ipYB6fPd3YInL9zMFVGc0QgARCiWFQk96JiMw7yarHSVCdoRaLInqmL/Pnq1HJWiAoNOuWIDqHgeKbhr6Oa7am7yaQljkCyQ0mfIipFghze2/uggejWrA6sH/4nsNgYUHSQUYhtLUlCtoSuOG1vguYmCiAhmWqG+cdOAOk08WjxXVqELRXuWkaRVaDHNfoEL1fMBZ6SajpLQmzrR256PEOd4Hu+veZW2vtaHFGy747v/kTY45mMjT+xPZpdf9pts7UMKdE9WI7OvoCCDAaCOqvL6ezxDkzfTSSqNhcwtiUpJCDkGJAsrIKVf3mGCQicjW+dlgHH2lokSAhsTgMHMFaiSnOFqTN0wUaKrCxacU41M0DjfTKZjpzZxB9Pnr9c3oGYrkBnb1kCQQgbzk9F1szbU9VSviEKIKV46FMglUa9PY4n1vYeA0epaKN3Yn138VEM+o5ovAk0eT0ADg81Zmi+m/YZAKRGSvCTx0fOIxOvnulkGIpz9IicYdnGsCynNYmyJFdcx+WWQKpvjuhHRromW5SkX/V5k14XcHvJaPrNqNXXo/Z4PbPjY+M/rK/bbGMtMYeqG232Q41QIBjQ9U4MqEfvrs2FuQ0LL/IZTEOxdrax0E4GciSfDu2D/RCGEQS/9fnLMijYiCOAZDhWXrKQjBr3mWVDptAgRdLe594/QJCfzrL57e2tLfjzrO9DrG1UvIXY+0hkak6T2Z/+QIPUiPDMPXvOwOfj7FZia/OXOVAk8uXmO8bc08NAsIuMgiYXVbqAIr2bJtG9m9FdowFCm88PhdjJh6BHXmEGPoe+ijtWqoprseijYCXFxdgWc6oZkHq93t9xM6bv9QwptEFvIL1LxtNR3Z3+fpfX6/FAflw/HO8cmn3VIq8Z86tsY/JdX9Ct03mt4XfhATCbkp8k9csLuGBDhL0/wU5Ov0AgUWMjPNgWAkecz86elgFHJkOCO+Q0VDIcK0tbnen4rqOXDYscB+lSwzOZHt++snWwvFUBzTZ9FvzjchadBseyp/m1yOrxwcIHPpUm42ZQ5IPUIoVCuxXPrG3WZlZFw8cPTI8f9+Z+fOjheQIr0WhuMZ4G37irJFVKOxnd3aAoSkMMh0Ks1owJPexyZitfNeiOWWWQMNtVapG5pAtRdbmEwxEjsyvmVorRpuzyKqjbI/rg9Y6R8Df/ZeL6X9pI83D/glQSRkkDmSDEOxGdFbUwhSusNPF2w+Jy9jjPtnfIUG04sZJ2FNcKudVwXW2vVq1GcphmNGkiCbRhIqcpmSQTcmQzGcMkMSIoQSLsFQR/2R/6233emcRrrf6gIK/P+3w+z/O83yaWtwb2ByY3nL4QTNzqXCbzcHFx5YUpUN77x5QpsLM29Zspa1/f1JSTdy4OrvS/fLn8h5XHz+I7ne6nacFhFsYcOLuZPqsWKBoxEppZTq0CSdAZdTrxWl1plMJurDNSxhH58Bohu+qLPnKoka8xjB2NuS4K0d60GnXG3KdczlsVOzAGyM+K3rH82TlH2nmnD4Bkpw93LWDMNawQDkv5JNfu8Zxeeob6b0lzey+bh2O+2P6uj+fp1Y317//yCnzkagZsO8GYcYZhzPnxhga0vQUooi/Kfs0VJdvkk9ByzRsQJWUYYcRaVNsg3P0/9fR87xzNz40NQ5xaWRzkAch96v2EfXBlY90U+Ly3bV0LlBPWu3fn+/p6Hk05V0dWVx8PT/74cHhoesHQ1hwuCWZj2rWDa5jezZOShIBEqz9gJdH2qY504Lpr451tdcmelStb/+XymSLate0uJdMo3uc5kprj9EVvuhQ9A41Rqy686ai3UFJDbet0TGFcEtw2wn4gA2nO7x6is/oO4aRYzM8uzJ2eui4vL+MffiCP5xbiHCTG0GGM5mlAcqDnlXPAR9tt0CRxSOnfqXFW7ERAoqo2oFiN2t//j6tceXJDN4yvSysj2YgoqW1Q5Kbnv3ce5p+OaTPUgfOnyZUNX4wP0Znh1dW/bvS9KAf//morUC4vLU1ZZ9b7ZqBFUiMHvtjI/Qejo/6F/NH0qMHbqtNc7AVTutYo/MnHFG0xyve/Xndgcmkbdfg1pbBnwR1qER2R76kdLS0qjFSMTxcal1+rWB83AvLZEdeRK0VvpIvVT6g15tBJt94TBhQHM2vEWU6Ig1zwoZCdNJrndm/JjGRSjkjRn39w6vJcerKebT5SeL9wTED+9v2Op6gRiuZBbVb5GGXjIACZAUi1SoWzQifacZWbI+ColbN0/cBKW01t0MKFARESASkPGirdjyjZ8/tA73Rk7/aEfehPf1t+ucLHYiHaPvyz07k+Ewh+2N4plxMm09SrpZm+nvmZAd5G0fuHIZrLvE1ylqO4N9t5M8Wkm1yRlPdd6cw1ClNsRHcSv0OMBBzRCTJgZOc4tL1aZdczjV5fy9kIzav9V0OtspUFtLcSAvImfIrI/ORKVVfVVWCYFtkRiFyyaLfZYochijRi0i+vnhIOoxnXaFLHyXG/x2PY6wp6rC882WA2TKJnLkL0+53PD6gY7/MNDsTsNo6j7A4MTwk5hiGZSL22u6/+1c70tclINnXK/RO6JDRzpUlCW+/SQnV/3d8TqN5zF7O3Mxbpfv83yw9pmvfR9OPBgYH17cSHgL9cLr8xWe9a52fW5+c3DmD+wf+GaIvdRljY7l9PbxezbRVhPHtDiFY3i55p+D4SGzUACWEEgCRxGcia94EBgNggoZE9pHwYoJYMFSRnkRkPy0pzDoR8a1ZhzEU0x5TOOhiVGK26vABkq1gRdUB3sy1/AZxCQIL2Er+8CaaMDgDS7CClsjfbHnk+Xmzv++w99bjusSDjtG/Qn/h1jOL5GO8M8XZO4ux2B8OeVIHkmCYFQBmUt17kKFg/adH0LXRIdFFESYnwc22jvqsGJdQRAPmfFe7M6wp6XYKFOH46ubg8CcT30fzqRt/Ai0Qi4IeguASEfDRvnemZt25QAB/4XwDSwuWJVDbrjwguT5q1FErM2VkxWuAQkPJZvtcqpbJJ6JFXOM7Kdd34pfW53l7UF68iTZ2PYUiH52NQ2Tj8LtVFJe2tdDAt6ehJa6/XW7yZLAItcR1m4y6AU7HDfUpDYtKfTU0s6TBjRlxDssHTbHgh7tJzdJs7G4+fpAiCoA+2dtANZGDLKh/ibRZJAtnGwt57Jyp0T1p0I04aDEqgRlFa3jZsknFU9sMMMs6KbiO5aYSc2LAz+uz5Jwj+Hm+YJaR0wzeTQ0MjdjoG8wVK8yGxtbUTSCzNrz2aQq9pz8zPQKIyWihQdkripgtEaq9RFMWitwCzkMMqFUEkLccSYYRU3KFGQJrRAoJOd83daUCarZ29WW+RiJFyXbfXG2SjNq7sZNc95Llc2TApHZVcZXNTBT03vSlEz4RoLyOefKwK5hawr6VjilKAVHG7/2qSSA14V9xISk9OPRFP9nJhYiMvRsaregfpICh6LzjGWWwUCA8filkIAHKEy0f91wUVblbjjIBgNNSeH6rXNlrYbW57IiOJHDlipIIkDBzxsW16uvV6+qKq1XsFjZQsuKcf299OICBDd5w9b8pbW8uBraWlNeiQ21Da1nnrgc2iIagYFEXYsxAmxRt5QUhFPMW8g8TVn3KVFPm0O0/qwI53ILEB+4MONMqMRIsVQEgEpL4VfVyZcf0Xi+Io0nQq1ge8z7OjCTOGqTCw49ULMJFY7jWzWcEqgoOBXHOS/K2KoMUUAhKcOKnm/rgSPCYgc2two9GS8Mb1l03nbGIlHz52f3SlCAdJ0wtud56wUGiFzecjcFayUZOearzAMiA5KkzUInejELK7hmSTUtptzejukux/gJGIjvAfpe6G5qHkWW/0U6UQLrw7M57fSAvvM3bqKAMGwXfLObW1FVhbWzOZ1kyP7m5bgZKLa2uUxaID2wZqFM7enjUmswVRSI43uhfC5+Phm2JFiJx3RxCQHSp1C4YxLTqZktdk64M0G/XHOoy1JV2o63itruXCnq3hKEtNBvIeepGg4i3lUM9V5QS8hWF0GiHseudicZJ2sDDzh4d2Ehj51TO/g8AxcORGYyZ4WnTvdc+mEispIRz0fiwmWYL6OZitukkSfLid8vksKsZhoSb3TsKsg8HMmBpjBAOCqZ5dZEbKt7+AkuiSJ5J12ZIjRiIDBHz8du6JNxq9yDHpwklVdLSHWVyy2enMBLiDOz/MrCUQiBC1Taa7JhO6BT842T8iSS1GGPjRud/jGgcgb0SS4cb4XlF729Xe3ituFke78qQGMRI9E1ISNTp0ZVABEgiJLGRjHUt9nY9xNLlfOvH6QuSP/5YgwwAnVeJmbwlHb4UhuW7BNf90hD0f30V0RIzQ2QDIfbA/qsxXX8+RBCuyuNkoTTQH78XdrqL08j4rev5HxfW+tJHnYbk/YJQMY7FTMiLMHCJmkLpys7ALK+e0NeRN7XGhdncpYlq50oasWmq77NB0oFi7rVaqkttYx46b3lniDeOxNeJk0yElZJJKftgSSMkGXwl52eNe3uczk3p30ReKIuOT5/N8nufz/RFRVTNVr4yNr21uy7IAwTAEfJAIQuYD6+uTMii5T2RcPiKn9WNyac7IOvrbmhIJOGLn7utzHDk2Tduv9bd1hSuJ3cNyrtbdrUXrlK5VKL1iZAJjYLhXVvz3Xjy/PfH0s6sTj58/evwc+Dg3HghffjCoKfDgU5ffqaPJFGlls5GTydZkzNqHdgpAlq8MawWWRl2bJzzpQwtxpPWWPvQ+NiHtfOj+1LNRIZNuB8fYcacB+w44IpB+GV0OcFJJq5AMEUmO5hhGJ+VSKbu7TRsvQw6QYH9cmT8sFPhKNWEyspx8N1lSs5GoUhkKz7ZmIwNpmlW08cub1W2W1icNL3ScjTHKJxrrH3+dNMGluSiS8bmguDuPCWlXN/ptp9cMO4zEbmNLZAfi+NV700yVj1yuo3pOVDyUIIALqFSCweD4k4dP/N8+mbu9NL20NPHZ0A+PXzy+d2/o6bgxuTBX1D2Md2rvznfVk0UbyM2e/pNvOiJauhrtbU0XV0+neFLEQRd4vqiKQMpsugXgsec+tka6cfOj+1ghk8DIjqZAdn4SyC4043cfZDg82s7R1O9yOPzxePCYHK0olilqxWzJpAo7U6zXBpKH0v4iXDC+T1Z1Ro5fCQt6SrdMcvZFm7r7IWJyMskVgueyX5qmmUyGJ28ZAKToy01+/Phr+EjmK1aOpl0+xQSLhiPw5gDcbjZ4XBsI2dWcVnba/gfefnBJw3e36wpu0HHlwEW4CJIXSJqVAciLD+ee+Ff83y6PPFiZub008QiKe2JoaH06aMSydwTSI0LbDoSj2/CQ1uarf7zStt6rWauWrpbqjcgrDdsmBQnO56m3Nkz77gmtpdmzO3CNod094HYWX0ut7mMj/mnmY1vxJiHnlgsEInmKZiBaK4gjA9+IOjNQrJiFtahJF3b20B0CkN44kTkIbH+XLWkyQ8ZDXgHk+Teazvw1u7u7W2VcpEjxU5djBTY9kF3LRj4kAxtTcd/R4Kv1haCVDyer0TSopEdJn3ZKu9cRSecsYhfeEdKsbdsAdbTjT08Mny8cmZiLPC6S4BgEEkqQBTeQuTH9wO+H4h7x35tZWbp59cJjKOunb8KhS1tFdRr0j+PHNsZmyzL8P3r42v1JQ0qqrdtm46cogLlZkHUo7XmO+neuXLJoBoAUrRZHIe2U7TRtJ88cKyQmw/8TSLA+185ffasAdiSGGFxg4DhRFGnSrHYzVkkjWR3eJn7npZd3gJQ9AOS7mNooiCIphLy8KIMTIsfuqB8S2RpDyDrH//KLpZFpNbv6t5PtYWljSpifNwtbV4KF4tqrZBT6hZJjNBtHd3NKZq8lQGF3DaNGgicHo4kjLPDhIKDD57c8wBuKA06SLrxlRuBZmsTxvBR8OB7wrwTeLv95ZXnlzNVvHv1we+7uxaDhDVqpSAA6MgVAShUTggVHog+TMtUvRwfT6Wgiz1QK+wODAyZFcLlaLVHGy2TgDTJbnBUGm5ADbrRfbnczYSed4O8sG9pIrvZcdwg5dNbAiQ/5I9Q2g08righl62HENKurOgt/mRZ2XkohG8iQTAUOnsUMU4EEQAoSzzNxkaEr01ulbEqHjmUmBowbGTkvblcjESAmL+3t8YRP4Svrl0PF7Ow2MMsqN6xUOyLZ6wDpLF3bjAQwIXLb258x+YAA9J/4+yUZL9+CduhjGBcDxBSgsklMo9Kl6UBgMbD41u8fWR5ZunDh6s17d7YMnpdDVrIk8bTHA0ZS8oJ/VTiWF7zSFL+t7qqjrYPVcr5S0JLg7hmCq9XKCbBmNBkXrWIL1rVd2Agkhn1nLA6xAHE83fk/fDxx/ToYjfvXvp67MKIQuGLI2peAACvhC2BkMpvV2GJJi+PqDH+wMyU5QIoA5ELMoMU4Q8p8iOdFAQgcfjGZ/LlIKoqn0Kj2jGdIUgQcN1NxEpL3RojyAYeuLEiTg/u87CGOEtV6oxe7ca9T2h1NjcQ7a5qBu68TjWQnBuw3d2WCwXZAEC68zoxwUQLL2Iw0ti7eD4wFFxf9/uXlmZEzZy7c/EvQKAgsGa+MqkWJFz0eQdqTeAIPUQrA4NdjgnZ4uKuqKnDQbVRABPOci6rXEzWGEWldK6lqS3MQaUukXdvYY0Ag7dYHfOxHgYzZSDqEvHbu4aOzhq9cLtfoU8BJ3B3JkTQl/qiXkquaXljTeEGIk5mDg9djexs7DpB/unWNBesDQHpDXhaBJEEis7sWg+1UsZIvtnTZaiQSliCIAnR7ifERpABAXtJm91OmFS03ompvB9bMfxnZhm2mq2mAetDJ4SwNmXp+y1YcPApMQKOhXAAk7vgAIMPB4K2gIS36xxdXZj5HJJduGDzkV31gNJGyQjwDTwRACkBnheEhbG1k9MbPPx1WD6O52ujkfqHSkfxe4fKNepqDiEhbkUg224Ip21liQBzbu+3aLtmzE0DRBvFYILvswj438ftlMXd4qFbTHO3cSwN1LbCCpsYKQqrSXeFxE6txsLMHEeXlzhQAufjF12GWwQVu0rtlyKQsiuyYvxQpwZtOKNtl692/Zi1rIK+YIgtAeuY04e8AACAASURBVMf2xkiXSxT2x6VMZd9IRdVqrZ5IdLdDzQAj4XXaHkicwFBj13bT/yCQuAz73nRcrgsQ5OzTB5BOweUKAm+EQhJ8Bm74F0f+ODIDHwEJsgmjFwdiFkd48UgcLl3zkPApgFTa29jPpxKJdENNl8vVgleL9WcPy8VEKa1Q8Dtsba17DYB0OrbNyO5PIgkGEtM/8hGnpX1tfX09Nh+7rpw7N/fN2QCVT6iRw8ZvaKFY+hSlxOFRttcuQkROTfL4EjIH/9x4Ddn/5ZSXpt5+HrvFUljQQnDzXWMfQOX3JFHRRYrId69GIv0LW7Ken6dAaZtAsoSPI0Hnb2zleSGvgvFIpNPwbL3uXgdIu2332Pd6NYsbxxqAY9vwV890D0dBhsOz/RSFQBI0MszeewQvSE9TgcWZjdev326MPDO8tEiSVrFeZAgKgJy39wDA7ysK44XAuliRazl7YnFULPGh611tkWIiWm8c/YeKMw5t287ieP477o9Ti4RTWpVoBOSjlFqU7sypsJSGIHZVzeA22GiWQTDNcTB6wanvaFmZuqKWK7Q932X7x5zTKMhJ07pOjRO6uLM9x1Hri6wYy3aGQTlNCHYYDPuncPvv3pOcbecESmhDnU++773ve7+fHvw9pLSqaawsDh39Wa0JjwwPBmfeo4ZvoiDhjXlyhDcKGP/w9y+++PTcdTGgq8lW8oZilk35Pksz1SbP8XdPlWKi2G0gRo6XOhub6fRmJlMUqcDWxOosxXggL33/2l2sCFmxWPOeFFP66mLKXJnmKQoSOM0InMCK0lacD0UIISvFZmvVLEebquGomn3C5/jlqSceSCgxXoo8j4rEUT+UbaD78p0173zYW7tFBut1gogQNIvnAgDy2losFpWk+Zkt4Di/O3+pyeGz+ZRmeSWE4+gIKlJkA4qpM1AvMw9lYAWJVrFDSp67euRoMkynLKHupHQcGDqFylhyaPjowVkN3p0agCwPD8Zmh/3sCHqEFntudOnxozufPr24y9KGNXko1Wpbx7osQGONLsRM+Xw0FiuVKg1PktLmRgf0uJkpclTg+sQs1BrMjPzCD6+T+8k8JaVLID8hUHfVEaN9NYoXiEmGwn+F1SbOBSMkmM7aQ6krc/crbstWtbrmyfEYRvcZf4rm6XF01O8SvZklBDYIEjKGbfd6AFJv10kigis00bHlh49cQ0VKM7vAMRqd/WS2ybKQUPMpt80wBANUD0A6aoWR0pvpKKvjU+6KYwcg2yzujE1WlYKlECnXoau6njPNxbEh/+hw2E+SXtk+NTyCrsfLNrhmyotrrNejS49ufnd7e3uiCW9Kcfp622rncZ0zy+q6KIpXnsdr1xbu1kqcKALIzEYH9DiBIIPXM1GOlrOCfJw7vLSn7pssP5PmgKMSqDsVmcyLUQ5AEkHwl0AUqk2cY8j/aubc3lIU71XKIMl237kBkjz2U2h7rTYu+PJAIkcE+fj9LiTIet8tqIVevZeyQ6DMID6FQAarKetSF69xxXZxhDzzzTelpgANAchN0yEdIEjwC1QsLrJGMmnQ8c3NYszUqjYZMiwbbGVlTNXydM8ylUTL1WxdF47nT7TzQ9ji+6PIsB/UI3hRYaBHyN2+HE+i8wGOr24/2P71fAincQShmFaFxTDmuIYONrtZqs2uLZUhvOGTk9IdkGQmg481MOm0xFEylBiZW3tzcX+s0Vh5Ns8LshCErMRTJIcg2UCIwdIOOQCSZExRIo76/erctMRnZUqwEz21XdiBYjNA6U9/RnFNzXms2xDab3iO6PcPsd5ay8tJtWD3Cr1AAiI84IEM6JbJ50tNMN/zH8zHa2vNEngIrHgEbqCBusSAEiMkHYvH2La6XhWKnU68O262TSJgpgwAyVVyMkU5ribYvbaVw30yNKT3If/IC++peC0hcvSMOCZtPLs7feQk5scrqMdn323/7aPtd2USbEWwboybhixz0CpwfN4AFUbnp6dqUwASPuBzC2N7swMgWfpsGkDhVQtZbE6tm+XyyJfPdnkgywTx+YcQjyCzoAec/QpBnpPi0nq7Z5grU1NLMzWW4mkmVNfsfhIwHvNInhl0NqP+zjnPAPn7a/4KFtLojyULltt3+poCtSZCBhiiXifJoDnONhbGnpi3frf6SakJwcPR2FGgeScTISbCcAAyRMeijXzbbTFCZiMj5fUwhHZAd+C9wjfgTQetoAQ0na5r/bBuwCs35B8WeSM07+jNH/h4ngd/vShIz4fPvXx08/On74EgaxE8ryB1bbx8yMzjJb0YlFUohtHL0/Px0hqEDWiyNAsgNwBkZgt63LOgSIGTs3K2tF6T18tvLBz+yxaLnWIADJ4AICUvtBlKYAA39Dbx2RXLda3J13s/3Jvm8OgY/lfF1oZPDV4DkD5HL7S95ubCy3dmwZNobqqQSoH57NdxBwqADDqFVJ2op8bl8OTiQqOyurd3VRRlnkM5BvDQIJIgECRN/CpBlz4cyWmqyQibG8VY1zKgbUAbwOAOcLxVVzcgusc0hbHcXE7L5cyh4R9fg1MurDNn/OPr08AR9HiQH+/cPvfgo4vX8xGCDIVszfg2by7meLztKPKVJh63FItxKSqhvYjdmtvKAMhMJxOHHHo2A6BE8Bh889alZHLySevDTBxSJrSWABIXOCDIIIFP+1GCkOVL0c921HZKHfv40uqFr0uKzNIKdimKdujUCGjyIEdeOOA46nMEQT4UcMpcb6u9HmRVmyTrENkEGDZXrUODZOZN0xoPL6zu7JebLMPiMRYJagwwoFwfZIRk1j/uGlpBD8jQn8VyLTvgdUchKIMitBsUTg311li7qrSSZhZXhQPIo+GfJDnsjykGHD3veAUnZ6NzSzfvvNp+8ODc2zUlQRL1KvQ1UAJTOe/aqChWG2C4igAyHgWSkiTOrs4gyIm3NuMQC29BaGdFiso2riwsuvtWoxTNRFlMmqBCMB/g7rwHxACkwAqCXuGk5ytlp25Xu7XS9KPLI8kcShJ+VPsQRDaQ9P34YOfhAUm87fx+k2AUgrShzIDX67WhZiNIXXXVvt3TLd3ItVwwb0+S+1aeCrBsCLufRAQbICIQgVoXipDHuxeuVTU1HCh1MsVoPqdWiSD4eui8ESSkRQBpj0NjY7fMJM5rcp4ij/6/Hr3h4xHIjMARk+OoL8jPt5/+8dy53Sz8OCHnBPh64T6bh9YZrERMrK7HBiCRJNi0z/Y+yHQ2Jr46m47Dr3AzLfG8yGZzOwu3upUFa3Lh8oSEa96DIZLhoc/6GUiKoU6ojVj09KITIZ312LW5e8/ftFotswrllFDCxw55ivxRkOcPJHnae/Z9lsGWxnbsvusW3OWW5eDyUUPFr1KGllKcXHL5xbI1pr5ICQxBC7gAiUiQJA1/BCM0zxCRRLU7FTY0d0SpdbBaKgVgBhwhsgcgCSLkgCOC4qUXqrLA3hgacPRfZ7x5D7SFAzmenBtFkHdHzwPI2/9+9d7Ft2uQKRLfOuH+SrsKzse7Wg8kmxUpvlUs+pqUgCU0DunOf377G9Qiz3XSUSjuPL++s/hnHviX979+V8qiIglQZBCco+iBBFPOCAytvdhZi97bMXWn0BKfvH70rz81yqpaMH4BBkYbgERFDnZwjnpVG1dKXnj8jzye3tZ7Wj/V7vWcglWwfwkpsv1P1+27TtC2A5qRAqhJdXm5DQWGYrB/DCUSJOWBpHiGjPyPqfONbeI+43ik7s3eHOhOl6ycxElod1E09U4TE+pVggwEFt7VS8lKmwzoJnkKQ4sGcuJJVEGzkh6EIiq5METkxiS3npOVGEPkWInNLoAvRml8R+TEThTJ4Hqe5lmy1DdM7bs9z+8SqA1JsPLCfPz9Pc/z/f15fvnyyuai0IiUnT6ITumAR7chobMAEnckKpBsKNGJFilWBMuVsRgPk2xpJTZmh2Mrpmsswl2KiPFTJHkYBbl0+d3OZxpkOJ9k5/NHdlkKmZQiIGVs6WC6JP2A0oyBtSrVSx8fdUGafkUtyMLi9P62Oc3DFGau/CakCQlQJOVRWKiKVJx11l1FclZkZS50ZiVyqiNnjJz+tLvrdxffjESMKu5lzQPHPXtdkDu9TN203TYAA/sCbmm3i418BZVGVyoVG7s8RqcMo1q1IV7qOb1aM6rRVsw9OMcGOcYHigxrdJgSf8IpnPRGY8/CYFKw1yNOEPNlgLMkXDWEzxwrZKJIsQL1gIRVVhnMDSO07HX3yez4QnTXu109EjGOus/Pb125vPRR59JxMDW8FKb0ovVNktSQ5NSMP6AILsgYgvQHQ3EEebKeOvpO1q8qagpwBhQ5Ic9NjxxZZTT5t7eehRIIEs/asTxRJLb5hhod882cM/fV45nJU3tmM9OqevXvN+7nDtUiRZ2WcGy/tYvEyDbSzv3wKCiSrDeAXQRPA4JsNJvFRgXTNd6WgiFSLxuRWrQKP1K5Km8Xq+u1SCYH+Hw86wtDgIS/DK73w9Bmwt/Zzv6FQdkxjNVsKl0qqckOS2JzNvgaFyTHAULHhhjCgeXCdh5ci7t2vXe/GyNxLxzUPVg6ktA4enZ09Gz/qPful/95ce+jzs6Dxx0Gyn/a6kh+Jiju6SO/fxn3cBCQQTPoJhxI1kHz5InUe1hBKoGU6cd5SEUuDNxZX2M0JTCWBfgJDdKfoLD4DmUPi83oyNDOR+fmvn1wMV9pHpp9VFCvbxxbzk8+hPJaggSbx2tLMEgSkD9Q5M/2QaYRRd7O1DLNZgYLHySEIPNTNWOqVoRRXMnZvK/YhH+OV9GLA0gfyBGQIkgJQHpoX6MxvfDnJBSOSTNVSsXlWcNhK0Xsp6WSpA3OjoWMBkOb9xSfcB5OY4giW9EWuis0pA7/OUkxo+RxdtTb7/XeunLvxeXOzuPH376PICUrnwCOCagXQZCLI8shF2QsHgviw5/tjSHIeuqdUnpeVkJEkWQuQ50zylAnBmIxVdESAgFJsRqom2F5eF+gSd4yjEdrM49HnEbViM5a6umXD+ZHVh4+nGrquBWhY49rEQEktid+FSP3Pf3ivE5O6pajOdBcnnTvgC9v0BUDk02Dlr6r6jRfyUAKH69VsMDkWMIxTIUZCFmUjxGgcs/Mzv17ywLTWDiYStVNrWw4etHmRBw4pAsc/E4ur7O4kArv18NxnpbWbT+zk6/ByuCcygCC9ALI/tEzXu8XX/71xdJSZ/t7X9eDuLQgOZaAN2DhrKcfjKE/JCewjIzBM+s3g8sH67FsFoZ2b6mUvj6ohXpj/sCyiq5ATayuQVAImGYgoSmgSFZJeHj4UQWQvAh2jedzD9cjl2a+H7Vy+ej4uiAvbnz/ycQKSCqnUyzNr+0hJMnG5rukd7YryMN3rxYkDo+o2LkiluLAkMwB+WgSFou27TTgRa4KiSYTbWA/9tdDO+yhwgCSE3jaLuaswhPLiWa20ql6yn+nHLGqHTBWBGLjEOSPc0ZeAo7YXIbHxswuyNZX59l3t7kTZjiDi4L0jvZ7h7q7j11+sfRu+/Hhr+sxACnZDQs/HFldHOw7P7IIMVFVArj7KWhCcDSfbZbq8awZO9nbmy6lb2xcOt9r4k5myE0JlUtoWDbGTFCkrOFstCbpioZNVkWehZrMA0m7FrFOvXy8lStCFe0I6vKtB10LRrmq6zpggnSzo0hshO9KEm8b6J4nZ8chdEmSDnkF6xoKix+KqoLrbhQzRsWu0HxzZWo8AykIe7IjSNqH1/yABwUvCW6f9lUzW4XCVjFSvl9K1dOBR+vrThOiJO+CBGMjijkw3pDWcGIbWTIt26Zmu1/u7lcY8dGPD+/QUHfXsXv/evH79p4hAIlNDGlHx3FqbY2cOX1/HsZyCDtwgkOMmfG4aWZv1/8Qz2bjJ3tTCHLg0Q0CMkDY8wLHJQBkUE0kZM0j6jJDSQn4sHmWZ0XSGNUprzmeucmNGRiBtVoeJHn67pf/i1jAESwzjenmrf3umYVtkEgSBUnx6OSgFKDdJ+3mGtzKiLNBtZqTK0KmXKuNN2kEuKNI4Ohj8lH9Rz5w+xAjizBoVg3jSE9vvR7burQ+XXRwHJMSDveecfkmjmxJxHajpOVRy97t+tHluNtNMq8x9nv7rw93d33S+esP2sc2N2/XTXIroK5B6bM1ePHCsh/+gDFUtUV/3+04goybwdgJUGQ2liYgb22MBHuzaB1luaDKYsIDqSVk+gGk4uGsvOqR4DWo33SeVOQin+QZnRUuLrx8PlUDRX6WnBzoufb0TlKkRFxe5XNY/vyC7LTfkSQKsmse/kssqcfdSwBQkTiFRrNhH5CqFjOZSrVp8xW6AX7HR25bEFkf7WYbKxOVIGYiyGqFEZTVR5FDt+v1+n8vzqyv5WHoiJyC5zEEXPxpOCJu/aHcrfgclj+tO73OMM20vdZjPyE5BHocGv7w3Pvtvxyb2Jz4Zz0u4JJSPiko8pPV+/5g8MIFqBsDqrYVghj5cTxtmj1/aQeQZjZ2sDd1spTu2Zi+nSIgUZBgsPltkIwia1yyWmBYVuASW+UqB6LkIN/ApyyyXGHyWwOCWZli8s+vD9+8uazxFC6i05KziyjyV/vIPRckc2O7ABAkQ0BKrznSCJIi7YTDxXKm2WhEK7wPr6KhSIj0sRIqEkHmMg14nRMs226E4Vty3Si/X6+ngoMrp/IM5Giew9N/MtbjeMYNr/VjcXsADzFTaCEc0dGgLWx7NbD7XY5exDg8/OG1c2NjEwRkWvDwYDO1hCIUFqH08fedxxCpKgXwiLGjoMdnN/7xwQkSI+MAMp0eG1j5GyoSaC/KqgZ2BqoIfxZBQt5mnAFLh7c9Nzl1ANQoMh6M4B7cUXxx/94n0fEyxR94Pvl5X9Ava+BwYWxL+gFSjyPILqJJzDdPu+Z1lhMRpIuReh0iQX3hSrTWyDUqlYwDptr3CqQo4XfI3+FcBfvPFNfKmSotfTPrbBkPI5fr9ZJ/wchpTgVLC5WUkQiSItcsSRLujuSxvV5L6zbHN3+YZ1COXiLHoeGhzc2JiWs9N+cn4JE+QUDaHQkof2Q/qXX65kGRAfSKQXAB6djNq3/8KWQZCJUHU73pdPrcVwN/ApAoW/hEPTsgQwAyoTH/5+p8Q9u4zziet2NwNjpuJVPxbQtSErJIlDimMmzFJj1mhIkTYxzXDSao1ggp1GhRy9oYNGcHdsbCtHjFRqtsX3Kyt8VzEJJRdI6lSqqGrbtzyN0pwXCqduiFKzgYg4L7bs/zOycpc17EJPGLfPT8+T6/3/N7Hpa/mrA1TS+uiKqb9eKeExAUNAghMNgNJm7JlJAuLl2bnI8GIcfj1AcfI/+YgOwbuDiDq4CImPzHXAFshnFAUkdB0tHjPhIizaaCb1iSOByOgCQxEuo0jJFxlwKlPGQoaVW3JMMwzUxG3Gr889JBPbySpiHXYK+4k7TBlxkEievoOO5ofY8jyM/hS4q33nodIAnGDxHjrRczy8u5nMMxDDksACKFanr4jQw5pgiRUwqMf8FYLpXvHUmVF3+1ubnZmypv926CRa4vPu88jyCjOxH4RLkNjoDEsIqXyRwb0VtizYTESMbe8BybUVi0SwjDASYexz4OT2DnxpX5GDbTMaS9tevcueOdZ/ouX8SdacS5/3wxDIrejdNPfK92IBGOSlPAtnmUOEJ7ULAUAtJFABKLJK7tUuSmr93+odohJVurrfFExVNN1L46OMjfurMhJ+W7p1g3Ju0ggsRLER8UWYoARS32HbAEJHy6x7s7oZ4BkLOOXw/gL2KQaI/LufA8cswNg6X7Idn7BNqT3QeQ0W0srEGTFzwQ9yaHL/yivp6713uA917l7fXNzfyF8wt3+t4dK8O/xfNeP4Dk6QD8aMzPBxEkH6kY2bSWzYCIhPAGDKsJwZ1W3G6URK5BBo976WcTD+6FcAoUdqEwaj+EIqi0L8+MjuLWtAF84FXABz6kScVpsEDPhoK7KlkMiZaghxTLVTUEyoXVzGvXxlqbQpOtSraL4iypZVqyWPJweuurSwepR89UvQdiDSCD+uvItX2s1xe3+zVRxjnhHgckNh19X/g44dFxbMQ4CRyJQeby8AH5Qcszgqxqz2KQXrZTECWv/fqN34Ki2ZlcGB4ZW19c6P3pWB2SzfZ6fTM//Pvy7cd/GRv+eA9cOxgLAEi83IKICSA9YJ0bEV6tZjDUeEFMM0Jaam2led1w0wASqg0Kh2/Tzy7/614utoEgwSEE42x35xkAiRs7R2cwTF7McW4C0ktA+hyQVVe7JTYJSPBeqil1iLYAyQhBxskeOR9aJPxVW1oRW6ftJuX2KU1L0cRKgFW1kycOooVsUatwgpcjHVgk2UAoBruvthLiVjHjJktnjnWd7SKNXZ2OY8/2zX4fI9pjDjiGCcdvNsEig967LFtK9qjBWCy0vR0Oh6/e/83V2xUAubiOR5C7T3pHNvMpFOfw+/Bne4Wl341df76AKSkCuYbFQ0yImFDl8NgPEKS5NV3OQFhkvRXbNGstMZ3Wqizt5p+CynOB7GDdgcLkwnIhiPNcsDVfnQaQfQMzo3Nzc/9F5/7rRIHCPlcCkjqySIGCQjHZJFDxfEcxJLNl+SzLReprF+6jieMjDwBpfwESwTAVH+1yHTYViJE40u3kifry44dFlVcVlpyhYdYGEQ6O3WwmE2KjJmbJgjP6WEeX04/0xkuOrzACxxnCMRciBpmbzx9AwRT0QvGh92sZP5465sLLM+9PvXhxMxuMhSZT9Xz+0+WFfH0EPDtaRov8dGIv4h8ae/e7RQQZgzRdOZ1BkODXQbxrgETOZRvFdKnCudVkMlvRVk1wdlPjK0Wdx6YdLB8gSt67Mk/m7UAgpNzy8e4zP8PtsUASl3SOgkGyzCuQPpJkGFWS+p3jNDy59bVtKJQsu0VAxp2NXXGfoyLt1URCXE0OUjTY+6EiarSHY5R3fv72bHGpxENk9XLkoi9ImtoYr2AYYn9/orFVdDbFHSMGecSx70iGk+h464UTHnNhHDCJ36TAHuv5AoDMmGtr+35sm4c09NH7t6embj96tLMznwJ+e2GwxJFUajsaRYvcA5DB9Q/+9CWAjEQidICuiMX9negOFjZY8CNIPlF7qif16X4xYZpQHrKVklFR0/ZTDyRVhnHjNsDC/QehEE43Ab+i3CrJNaNk0MIcuPdEgYG6DUE66ofCIzLGkmxJtAR0XYRptLZWE5LUZijnxIc6skhXnGqarS7ZENsKQ7cNa1BJqiC0m9Y7J57s3FwqarItcB4yRALPdWma8iqGbsqauLUl8zSHz0POnv0RxG3CcXa278PXHMEeQTiCPYZDDscyOPbBZr7AYbfLWa0AgmZqByDffn8KLxsKkR0ImeVoOFoeHuktg0VGcVhF+bNwJJg6uP45goxFuACbqW013gs/Cm54sOEUQAa8gTVx7abeo2vZqqbJAlvp75FZTVc9AdDLFPaq0x7/e/fnQ2iSLJqeMN19BHJ3d27uxo15DsyEVDUOSAYskLIMsQUqvIlJG2qcJpSIyUTSSFaVQafAHsRTH8AY9xmrkqxYp6t2tctuHg4eGoyXdwulty9tL9cSjbRVZTk+4Mf7Ub8H0jSeHSfSSk9iHC+2WXzU2UEeiDscB16qx8vEHh2/DpNJneDY9QP8gqy94S5NZ/djOHAmGgrj9nEIHLipIBCAlAPuvlC/8BEqTADZu3AdQX6wuHA+DCrJ7w5w/FKt8e0fp/wgbzhIzX7/Bnu3srKS1SoVedoqZaBUFKDE1tOaXQnghReWDxDQC9f2ojH4Ay+KnFPVbsw1yHF3YmJiqOCjcZEBEUdkKARWMlK1tVpVJJskHtcPDClpSlJLEsU2WSFHamw03fggZa9KEPROm6tSiXK1Bw9Bi/FuOfH1QTj995ooaxUGRRt2PqBvexgf0zRsVRdXKjjwxEMzx7rOdf8EOfa9lI+XESOkmRmSXwBkDkHmwnnCcbPu57Oq9sv9CIBEDQkMN16uqDz15qlTeJy2Xs+HUV5u5+sn9xavTEXWL/0h+skklEHPMvuaOV5rfPe354/1tUd4SB8E2e3J6EtLJT1Ds7Jt9liWnWiIVY5XOQ+LrWRufKRPQ2CFcoiDLA625xZktMi5XfyaGNrmQYIw3pcWSeSjIclNsSUdkodAOCii2Rw0peQXLclScDck8eo4eSwcd7UlXa2O66KocrJpuAbxoYvb2Pq6HrqjGUa1yjJ4iBrDO3t8Lw163DBbesd4IovT1xEkOHanY4+vk/UMloUORvKF3zkcQf4Es6Impws4cyYChvj/S87fhP/ven09hJjL+Xw9tffg4dXUpetXPvl88lpof6UhrtQajz/+8j/fNhoPK3f/zYEw8/Jc8c60aoolKGtkvSRYD2tbEIGSJQ/rJSCx4T3gj5WjIDorkLchrahnBmbAIId2h74ZehIDhYTHM3gYeZSzLcnytY2WaBuSHceduWB8iig229UmWYpEEg44PIUbx6mqmNQ6NIif8mk7CcEASk2ak8f/V9fVhjZxh/F+HYMICfdhu+Ex2B36wYSiE/JBGX64TUvYi9vcVJByW2QgKNF88GVQ1ENr24xo6ZQwtSd3ateQGu6kJm0aL8eNmrtryUsrhUoMGVihsE9Dv+15/v+rWmWphEq/hF9+z/P8nueel++z0pKpW03H5UBEJmjBIAoZLCOs7lxtFEFs4LQ2KPKurQRHEq13k9QashkM1whk/2scNR/H+1rU2WmKuZx/KTX1DpJYkMiWEEhprrCjUJkbXHygPTt//trdeyNSzqhWP2zcmDg4NH64/I9qgyadASBF1mg8MPIQriG1qdseZ0Cu49SnMjLp2OFY0vKOjbxSdweEoGe3da9795dAyJWVlelpTcb9nxwtRgZwt1Gw3dmsuLYLXlJtB9eyRbdTdGM4MZKO+f9wMQyubm5OqR2ga7vVbjQ2QrKNQLLOho+1mUJLqwAABqZJREFUmSUZa2YtmT6eShAfiWXPvOPZnkiODQOQQhc4SF+G76ZJIbyoWRNCximOK2s4Fkohr66nch+tXfd89z53T0IqVbCcIUHYLmhzAw/Gsj/+cvf8hX8fxvnokqXXIufifYfvlG/MKwAk+EhB5HLjqmFU1TLYrefYLaVdNzl9Q10WOMRFICcMeNCSyTPVZUVpdDqO9QFaNsI4XZBEXZdR+Qi+ZTOtYlNhnrfQnpUwBRLe3KITgMybIckhidphnN9Kp8P27dudxh/2c7dZVdXOc9zTEVI2G4XhiVpIWa47VgiBBMPGoI2zB+6qvWyD8wYgeQx0XdSuMVyfIaUeEq2JXd/0/ePkZB8qcWrYWpJV8nLo9ZXUty7Gb0LbTmCPAAIJujI7NzA2oYH8+XTk3r2fsbzMR+cPYpTnIdnE9rSILICgPZHRzcaoqgg5y9ZtS9yl1jmF5RkWCAPhmFyC0G9cnpw5YXPu9SedptX8a18/xfEz08wcqCsc7saklq20bTBkO63gfJZf4sW3FhfEZfZBEq6J7iE3x+EPQEjQOC/S19Xi7c6LGM6xee2npfhEhPc6dU/HtCZB+lWw3CMKirmqWqA6WMpIpqub2vVu6h+pdwQc+185SHglMWDfBzGerWSTnOWk1uP41itHtvERJEsL2ewPvRi1B05rw1dGhuZPmk5+fBEfO0ZyNchrsDSB+Q0rm/yJhjHlsLyct57aZnlK9Tgux2CjSoAT4GvnWX4mfvPozJLjOTtVO2SP9R9amday2e8ebgBF1QRzC9OYHWaCLvzmtKhn9OlI3rDBBxkJeU0wTX0kWnog7bqKgBS1lzudImSODB7YkpOPa1HeVvOejIMlkR4KJNanUoK6nV5sJtbCdeG8x0WE8QipPK7B6AvxONGRhfsLoMQLhYqWXZCElrXu3uy7SKJTJkBCtNmRvTZ0DoCcq5TmBh/uNy4ZRnl89LiE2X8OO3ZzACTWzHKhkL59PmOHzPyGzZ7pmMu7LE6I4slbEEAcR077gpeM12qZot30XM/cgvu0ISv9trqtOlp1wK5pv3OA3Bt+D7IRCuLaMwdMuQmQYTx7D0DiUgrMy9NEAwlcDAsYXmN1tRVkwqAVA3LpsREFX+bprIxyPEHquiEBLzVbbQssm0x0giJnui6SSs8RatW4hOymT0fA8ZEE7+DpFgDIQrZQ0iDlkwRLfvP+8TogNxEFRLovJGkWkCyAaY8szmg/JZOVgbuDgJ+Zz88vLvbCB4oAdjkxJ0fxGxZ5Uc7ZZsMWy5nlO7vanmcp2L3L4SJ/XB0RQh0cikiV+MlRSOYszlnadfarlels4f6f27q3jhY9IseRYDRBDNvXXTRsWi8nwSYGjIyRqIOMRDjJviJ8hAicZEQAMhjUgZKrONGO82ySZIByML0UWE4PNW0etA5AJ2CaIPonsDkwbT+tRhDRO+57BSMWv2nEABEDdMxiRaKgSYKyDsbU+sC9CV4pDG998YO4OuKLQ1dGLvdoX1cqewcGhmf/vmEumbXjLy/jE0UZx0QASCSmyKfkqNWo2uylKfWAWtYdCz6nEIEPDB4tQHaZcBwLlJw8UX3yJGOJXtRcIjj+1n3S2FL9VSE1a4aSD3VkUXUZWgfCbTq02BsGIOmxdlSPARd8KJFGiCWDjIy59UyxuRojQDL8sXO1vKnXvaciX5sgbXd4i10AUgqM6DQtBJKjj2PPnP0GfvwCxc01Og4DgI8kIgbBCSGQWTDrhQWt1KcoqfWMfAtIICXZWRrfL0lH+z//5d7ILOTaewd/H3w42HuuFpXnIxOjt7BhGnvKxYgcIfN3fA5grU7Z7FKmmplqio06SBomgnuqwxTICAtMiErJ3j3jEIh0izdbc5A7fbLnpJcfLXuKX4oEy0anF7RvA5C0NomL9Xz7ZmJIWUwM4f/Kcw+lD1ATQ3eYC4Jpt3DsJR3DaV8hXDt2x8g3DBw4jNwpzyao+uHxKxaUtqpa5IQP/FVmu5CJhIxg02/QMZmkzxFwAWQBKVmqnNKQln0KXgn7Xwe5iWY3QMl47+ytkaunzo8MJRLas9MvLwwODCfBNPT5aOL4cZx7kHn4iYoRbPgRQwArb0zl2Zpl5g3zujrqhDgmKisQjCEmgACKiCCD+JmhySMbwbRFrzbvzoKRXNV1xRxT24KfZisgeAAe3CzjYugJB/yyGgFSQCCx9+x9iN7tooegIpgogUQAMtzu1FX1BTVtpqdvRtbNug0RMGqMofwh/QH4cM6zNmc2ytj1I2K0Uf4D6ckPx2wyOdsAAAAASUVORK5CYII=
- data:image/webp;base64,UklGRthNAABXRUJQVlA4IMxNAADQ+ACdASpYAsgAPhkMhEGhBHbBUQQAYSytwVhNIQs9NMckSXZbca9vlUQDcMNGq5u2pPaI/z+r3NbO9+7/p/yA8BUrnfvyM9r24f3z8Tf3/5x8NfqP+V5dXJH+P/vX+F/6P+Q+dP/E/0n+H96v6U/335//QH+of+C/s37if2b/7fO9+t3vk/vn+y/6P7SfAT+ff1v/af2396/mG/03+s/1Huw/rf+S/6P9t/vXyAfyT+m/fR84/+z9kr/A/6H2Av5v/V/vl/8Pze/9f/M/v/9JP7Q/93/NfvZ9Bf8y/sP/L/OH5AP/B6gH/X9QDrQvx88Wv6z+Lv9q/1vsP+QfRf2j8av7Z/xP9v8qP+N1Cv+R6C/xT7GfYv7p+tX9v/6/+e+f/8V43/KP+V/JD+1/sX9gv4x/HP6d/cf18/rv/m/znre+FjOL6gvr78u/tn96/ZP+5ftZ7ZX7/+QHvN9of8N+VX0BfxP+Y/2X+2/s1/dP/h9e/9X/O+RZ+R/3P/K9wL+Qfz7/Ef3j/I/8X+1//f7bf6T/W/43/H/8v/I///39foX+C/1v+P/0f/f/wP///AX+N/zP/A/2z/K/7j++//v/kfdz7EP3D9iz9Yf+b+cpNgX1sx5Mp10yxCD+aQo5BvN3YGHLSCL/o+qlaKFuyhdnHCN8vIDiEh1nt3qZIYIPVyim+ixozKrr8M9BvkH22/ms+XnQA+I5yRTRPUG0cMofQlyaWWCLcAacrqhQUZ30YTTql5GtNOmXScOnqDwi1LUI2MPcdyWFwnQmnqxPkWVyl+61MkPJYnIHcmg1QJKK8HjYqKrB7DdM/oN7TAlWR1rEFG89Gi5I5DjJvkulb8kEX449eaIaDv+HL/cH/FcCcIlqE3BeD8DU1qCTkmCGmKe/HtdjLWATHYZEtC56lxWGIvd10bBCQ4tb+j0MmV7ZWhyPYakmEty576HMvxPfg6ylZxRkNlbdWV+FHibK+/mhshtXp8SzXJEfCQBNCSTubWqfs5NEw+9aq38m/UaCaxW70Mpiz40GuWftkT7LzHhd84b2Wopt273e49VZh0DnUd0nPP+W2jvxl6l6pzT0qBYE0GSPfq1o6quDc38R9UiJ4RTwlb6X0xdLLPSQlsAgJqMkwGRXnad+czQPW4HJtuB5WGxmocYZQ8uMv7nT7jxbDIyhqfxXKwdtO6FQWVh/59JvNQRriO/YNrslD62fllp1WBuGvWR/lCiJeKa5i0nSq9Uw8kRbw6bEGLamIVCoxuMcjNPHnuq64uSjloG1zLWGkhWQORkxF4DsJbyrcJmdX2vkSVzmmIXrWsG4oMzg54/mJ7NMgEG5SGbAhY9EWjPMTqNydgQ2Th/b/LZ4gLzMBkZE0/C/5t5ZgU/Ga4Lwx8QJI/SH2l67F1MeAuSeyw8bsEgEHlnI6KO3H8TFEDBKr8C4uw+JtGg2h8N70uAg/Tf4NWqMyjPHWVSTr4AIUhYDQxSw2dwFPid0Cj93rhib+jh/BnX8bcb9bbxhBYw1VlEf2FKgsqODtyL7yIfwOmWMn/T/4m5/uDhSZ+UcM8fA/QuOoYneCccJ3k59rRL8/UMKEMD+v3rlhCfzPMGTY4WwkVFTYLIc508xuldXOER1KglSapMXmp1qdxgk13nvQKPQf3jnHL+S/sIY3rlhA17npkRsbCHiOkFvfmvpCn7AvzVIrPfm0+UcgOsfrIQo5EUDKzK5TT6t3341hzqnxCtLGrCMQIAgjPOLJvIu3qmf1Js0KKAI+8ZWd+/PDtcVqbotKej4uLHzesT6lBd83ihppUVK1fcRlx1YQIafK15ExWO6bDi+PP23Ro3OWdFLunp9wuL9VATxqJO6cuTaJD6BiNFtuYYD8cMTwO0qt9RZQqJMbmseCnRD8V+yioNlE1crrG+3RHbH00En+gti12ETGRXbK9y/bbegHgh8KTWsnH9VMIigPjuqGIUVPBn20F6utncECK1eZ4CWUJkflg+4p1ntYFnm/e96IIe2tL+dDI/OP6NtZxy+17vDJdzH8JVHiGJYgxzy3YkAaeUUrZDSfjL0qTp6gcH/CXwtsVWIF8CX5jqI2anmUDFkKWOxUaTd7RIJdF0N0fL28UcPS7Nlu1LqVeNq5v/rV8iSPfecYrq3HKXFW8ZB1u2QV4iejoWFGve5xiUOPQ9thlA0POBnVi8TQmcwpW4UwwSDHB5hcP/G67KGof1GguQCkKEwrvEaQwSV7HbR5SUzjf+umHI1SDjw071vO97wnSldH4yh8Ef6lK2zVJYTNfrisnr9HJh0GadP2R+TYKVCTQAID76Ir4Cd6Fbofx4UDNYamhI+E27GkYcyIfE8gfSW/tJJ52o0cFkmpJ2leusPmIhk5+FWJdmbfm4GTRKoE56G7wDBQCBaHJDeMA4gqvSZWzquon95HBB4ScvZjeJHstsr5VWiUAkTV37E6dNlKnGEseGmdSB0Iy5ArtXsEWWHu6ArH1xd+7r5nAGvZ7/v3j+M9/QKG4HWWN5d/H8JWqdrGk8sTrfHHalgHp7jjmHe9jtOE5LzrtlsJgV4ZphGXISjjU5a4G2PTJJncNcIVcwt9lX7wSt99eeCwB5cFD0Wwj5vWTCw9162+RepPHWwWU54q/7/b78YFSlu+RXhpIOMm1jobXeSLCyzs6VDz7G7poAAAP7neLcu4/0Yn/Rif0XD4AW+/i/RazDIfg0klzFNmMN2nXCx3KbWUrJ2QToTALgsO/R7owFl7V7cIAJOF8KTpur5DYGJRGRL5SRQVUwXbt8QuPpQUvM0HAQWLlSAmmPRfzOB1JIolEo6nOqc5NWcagN4eub1Y3S4Wl+Lm7hb1YQsiUl/63ibn8lbsm5mN1vHSo5mM2SJALRVvszss90vmKx2nxaK78uEZIukij7fVoeT4hhuwGBlgGjPQQBYmGOsI5kAdbnSJkPzPO9+qTFRO5OHL5ga8mwBra8RrW9boI1T2fi8rgGzsXqeE+K1NdlNz25Tlz/uVFZo3VN1if3V+KFMOadLu9RKIse7t4vzf/yfkR3Birazf/2LaNy8mtWO7SZ0j8ui7g20OtSLIJ25yXZof5pfFzX7BWmQaezmJyxEdZaoKdSJ4nsX+77DgOKFb+cnoJRW9tEe/+2vpyjXpU7MD5F14tyv/mBZr5Vz4USpeYLGcViRI7yod6E9ndq5C+az+FAifE/2DoA2vsn7t6hpzd50frQFY67WWQKX+CmIg2nv7H38+wUuRxt7ZJbPH/8+zAzOaTPAL9MeX5rBomh6yKfLjZXCq1Cd4uk+stHkYN/53Vm9Sj6mWHoLLafq0zZjw6bWeHLFXZ+pJASdLPpKjm3m5RM38YXFxvuIbkIoh27SNkYGg6B1WvLVyWkgDSv4bgr/xzpug0ZfcNTaRrGk2qQZDPLQ2xzHLLKE8OFBJVPQCt5rzkgH5YCvISyPm6pk3VIbHXJJJm8rZUrCkHeZOR4suJWYmXjb+bYtOGpvhxNzuZhNg9SBz2mlBM6Lg7A5cZu1H01iv/9euEDNcAAdL8bnObMKAUTyr3Os3e3q104miZKecpkDpSRSmu8qSJ7mtSvR4hOQGTtOSjLcDK6D/5sOOSTqEy+6OS4ggbfoGQ0cf41vMEPQpXjhlFUcMMlIvDfaD16kvpGjA7qKLA75Yy4SmI0giRNpQrN66jDEuTDQfOpSBlEAcDW1YwDQcMEkLY2yrhCHgDZJFHsHZsF9Bu6jQ2hwsrF3CTIBFE4q7Ge5959jxdScNFgsMZS0s8sCkvCfHqlSbXncWmsoazk5nxBHFaEHbQ+cxEjZ71aaQX2Eou9J2rOgMxzuHoE/FtPvGDxp2Z+JpnxFhDfkZZ/Q8jfSG4ToWJQSbyhwDNbHggM4ohGecZ7oB2OS6USPYTcM4Lk9BSlMTOb8IyFCCrNpVo40vms9FDEXtIdKKFy1dCaSKjUZ+4EdbfIb9CIqo3rE2FbwwM8fORiE9zjo+zMkGQoTyO1HZPwzH36TtstgtYP/CgIHJsJYUdAfqrGuToRpwdf8Be7zdWGVRysocHetRZ6trO09lKW7ijc8H7LY7fIhm2U9LzesOR/9RW8iKV154IQ4FThoZ3/b41FYIM1sikxmMZioE42NzdfL3sKGSxsIL06lTIs1F9WdG7Sp9YyWOR/wcxG70iMWex50wa1i0ywyz4iK/Zxm8sbFTL7ZGSdV3cH6zfgYaQq6QPmeqTYx1YijErKz1ixYbootqldj1WQSvLxI6IJ13jL7GOH2o+v3h3qHtRB2uY7+Met1JYmu1gqv5cIBZ+h/ilCLoQcpYfO5uIZk0dIuMv8x8elUAlbrNz5I0n/wWUj//XZbq9FwfVglyx09Jc0UarOwP7WkcLmvbeebyn+ZA366TzKhPa/q4g1U5Av4ZBPvI+Wkvg6MjDkm7Sqq3kVKM0D5qwErm6gC8WvsDHERocvQt1QpmS/CV2mm4ASfNKZE5hbZv5vh7QpaRmjZ27fU6pZ9YlL7XYjPzg8Dl28nusDIM89fvPW33Lj5nCFi2inQF/jOQLcttSM4akTBQ8Jk/+ewje7b9XelsM02STxAS5l+TqcFOmqlD5UO5+/npAiXXM2H4L286BFsiOe6weJD7rhekL8itGfgiVSETjD7lmPe/Qp/k1AwoasxaK5S+iijwcROhki3pJNAItE2peEilyrRXiSJzD2K85ypiIwUmjATYuRQUz2YKBwOFNIrd2gHaUKvEjSpTJAxRP2yv5WROhMuZs4SMD1S0Ck2sBy7GstBFV8O8wF++rKJJY2lzxdMELGYMhGMUc7Fk7HFtLmkmpXUxfX0MVbxNpNZN4hZpstBgL/zA++qn4vHCXBV2IlOL4dU6V3G1W/GU2FXB5nYqbjH3naOemBboVwidiwxJjz9V1kssGRxlFi6fyXjIACmsAlY9hNA/4NWM2j2H5QpFd/rJJTk68jnitTgl+7zxnbRsgJQZHLJ8aC6iEK/ade1JOuVWnEl1IIkNG4aAZFw7Ha0SinfAG7n/WVJo2kxGji48tv69rHBKq/SGKVd04rD+aKuhcGM1D6nVfw9PJdp2IPlwOP+Rl2gRnMeOT3LR9N7DeGGYk8fT0BLgrfR7qCCt8vGp/n+Lkz/FxN5DmnB7msLFEdJXlD9OXfGxU+pMw1hJZr3KtudkB2l8+bW93/J6vObAs2nxrQQr1bNj1GcmuDNx+s971s/58jcCTDXoNUPREAaQlOvE2kk/HoB1uKo1iJkPVJ4v7Ve6dMJeRQXOG9JT7Bsd6XsVc7Ys+eYpJFIRQCg6hoZ0lOKZmJeCSjpRBbxN04fbscwFrIZAlVlWNtOhFJIuQloJFmlFdyb4uPV0BcONndlWes/fGsBa0sYpzEaWgOo1XvGgFo0yOsFJ1q35RNA13u4PLj6QkRaIN10hrqDvarCKv11jbiq9b+vei52z3dVREOqk5YiD1bqingF2kncQQV6VCtLLCcgUMQw2oPwxcxhRKmBfAfRsRXPHq96nfiDoiwBWlsEIJDx9+Bo7wagz9o3AS8bMS8K5PCOzef6vvwg/QjBpjHZOjp3GUCjapD/TAgdnkLU6MFQmiF5MhWfTXN32xonj1LAyrzgS/Lbn6JOF4wQrhhxayY/0ubZCwKUE8WV56XlOwm4LfXGGJrcAoGOZb6XJWMg6mkm4H5jELizvX1nX1T8AZ/t1kIHqVL6kPuZDavqWS7i25oPp5JyRyn/x4bRYLMKnXZKxtQalZSlhnvNGRSxULW8Hhb2qm3f9J86x1lXHitvx+VL+cUSrwc9Omf1htUqi8vXkTtXquedQvLmqQlyjFSUlyuXcnqmplXfabpIUCFyfPKZbT6RyWckI8gVlqTfpqnSzpzwT2C89AD6Z8Twu+eZ6H+OrZIcONqcRcoBumTGK1a4lMyKf47Ek47J0MnIViRjz7mm5IVH1tAiuTJVT2OlCJ6qGX3L6dUb6hpULKfmfNcp1cgA34WxrhBEkATjea6z6kBeNnOi4A67lzdZ6y57p0erfXtarimOsM8h9MUMl2WKr/+/vXSEDvkemRe4yY2L1GCpxuv1s5TZmLyhOXA06KSy/LYvS4el4/TDxcivwJPg/pZTC6Cd4tDoN8IXgDV2XOnqE8JbHOpK9Ilk4vVMXEytRPK9qWQwAwARxU0+B6YLNF5RW8d5FddixU0wCK5sPYjfzJEnIt99W9NkizJCTflTHq56RGjghNXWaRaS5/7Q6rSDr3ewW4bOD39UPEBpLoPk90Xeax3Gi786dxoQZwkpemt6GUS+PD+mUF2432hLOLqD1TnUoGIiwV35TtYQgm8mSbRMA5H2dV94NfVWwYH471+avEWYYdXai8VxaLkMGXKBahepDHPuF2AIgtseEcOfmVxMzaKyXlDORhvIOe5iJHRbBpPAR1JGDP9AebnhDuc5YWXEIMKWlqL7czxZcl3/7TUX/+KYm2Soik9o2OZoRjkltxNOTkrMxLhPN//F4wzLwm0ahzwhNu+VaWTjbBezVtsashWbAAMmiJxhUjd7XH2tR7ehET+f7jBUEG5bCsNdvnqxeiBrnbzHzESg6FhGBUzIBggWkJgRqMk0PRvOnRtrB9gVV2kqDZorU/tY48q3vqDVVgBcQb2LjiCOdCUgM14jmyhBNvDtpm3ze9U4YjgrM89jsV8F6Ia7jOSZUBhkwfhUSVn+XD7JiQHCLnOtMkXWWhLnDSNmEIeLtnoX/VmIGq99UvMyh+cfxXK0v3at/WBlWwzysO7pPmSBY8C9nyf0tEHD8LmvAtUklMJlRHvDIu69HsMrSnB+7P3sCovMxJ9cS8nmwFzFLCdaq99HHJODmHtneeZWiZy0uSW6ffl/NRnOJqs1/D8P+wJ30KTjqY5IfvFbywHfDUHT63lP473glkUPUioZxo62LE41rx8/tEX+/aLYc+PA2WoiTYCSBaFD86M6T0BkRFV2vEMuVxgGQNwot01G5/8IpDJfBenENujU4Gt6WVfQo1bwI3vKaVHXLkI5US6D8EBiyoHDLYuQ7cmKWKDRWZ5kSX7oim3rO7JZ47WIRtt+cLE6ZScqxGjphOsz1Ia5GOP8Jhial13aBaxIPmPKoueA5ZJp/C5zE9pml8XLrUjC/HGoLdnfyE/od/FGJpNTUtaIjhgBiJnZ2SXbqnakF9jRljhuzpA1uGPPiRtAmUW3VhGOf3akjp/nUVbAE0NUuOKl6STUtULvBcs2XULgxm9WG6GnbkU7z2FIVV5gIz0xU/QXCfxr38rtJS9GbXGAu5H1lO7z6slJ+Lu0HT4qtwe42UYuep3Uibytsihnm5OLoj/sPUbb/VUh6NgFgGDwpP8jt9F/kq6GJfo1coXVOpUPfAe86uS6J5pTUYzJ1L39BX0dkFP3eJkbauVdA3OssYYeHkYQXIC1+TcWSOMXwUKe+Up2azKAAZtdYN72CDdewtnjKfkO+VfAPpGdZuEC9/DBkIgdVIDNHzFC/wld3vhcAz33ygpSQLdy+RsRrCVAwJp9SYBT+j/nTmX9+RDN8B/kiHz3L+Ykmk2gycgdEXDOLaq0PqHiFvBPHEbsFSSNMz34gTO5lhT7uKp/oTcp0JVE5E2tqnlvjsxoCgAYJ82Ve3FLLPRTaTnWee8tFLoma60Sgd1zbWwmciOXAUDwAgFa7sFbJ4rFsph6zoE2bp15phmE2CHa+Pghx8RMckgKvypKOsijaXGwUHOBEfgGK8ED4972igqzyhP+zXfwC7FGE52tQOqswJEwOsX472N8M6jpLOTkjwKcuhw9G7N2WS5ApXVM+AUnjwZAr0VyxMSx0ls9pueahDuatp5nR0c3EMJyXuCiKL5gC3dFVJPNNg6/s7XSo5Qc6+RIBEBkv7QI5PSg/VxrBayCUmVl9kUQLDw2Z3EePaVjx6XdFMrcfcJ98ZuG4Di2IvhuGf8Rz5PBZbBJpL9d9ZrQDwxLNFs0/dJegRvyH4idcq5vdbUSYAy856pM5VvtM8bCLG42/1EGLDg7VpzU/81/IXlKuVYZEtTm0ScJN+OBj6ZwYSxzNpUlfsA2yZHqu1AhTmnX+5HX958/UHbSqlmckaMVzVGcL5J1vqeZTPXebDTRGewuN5oqujMzsakeAoVt9NrX5JiHLjS+CQwIrfZCPptFYZraL1j2Hm9/Dk6gVZIpiSel+dm9KBgi4cf6n0dEmqezKgbOIUcHmb6HFa1rk842mHAvHEjEkkTor83TRpPgLaWLURIyR2ff+oNynZj2m6YCYDg4Hxr0AauA88+MTf6/D8oXVcgyXB1SwshbQKCVwHGxVFXY4sqNlIAfnz7Nc1Mb0zcqplNIUtXlqdWYxWFmgujUtZrUkQo9fukwjtnSR6quvFYeWAuEiTGveYsKJi6PMPbg6Reo0NFvf+cTo0MNArJe889Fwf+QeP1bIt+5753aBhy18xA5M0As7c4x2zPtXga6RZLaSlSMX2I/hDPujDwUCHlXND9Wku8vh2W4lvMO1sPZCyCfD+whJQhTs7MRs0rRxfdbRLi+QspscBRGn8T76jVFvQelc1IrK+Qa/qBWFYdgHq+nh7ArVZElHpktTJ2YqL95F2Pc7peqmel+oBYESbSsvFVrbpgC0NoExG7Cn0ViQl3CciYuSQZ5Nd8qw+hb1BGhsuVzts5ckxsklMM2+LqbpmMKdEPgMuLvhdaXURpfLmFw5IMx1NqBdLQZx37Ed2oS4jSNsWso26N+QYRhziVw7z3ckJiL7E+FGJSo/Tn7F8jir8cmTOKYb6js/MzXxeEtQOqD4k95nFCghivtuZ8jTw05uHDAXjj8IbYN58YUR61PrPhHGjvz+Ovl24QOgXbQS+ftguTcUJAHmIsAWGONjvLhO5Cg0u8yHL58h+y38lBtjSVi+C1K1VsbPhUqJ1K80cshWZysAAr4Ghd7lfWcdaad1ggmu3Z9/jByN95RT+ZEhfkhfT0cKj+GCtfaNgxKogrgnJS1JYtYkeCKLRbO7lB792hQqWxWPYxUQzgYGqsDZhHFtzx36LoFOmaiFfPHLWJnkezulKPhQCHw+yLd38Cj7Ia7Tb0sjItNepZSJitj6TRp7VI8oldQsa6Jn5lldIwdtLEoJQC/RwT07zRR1HUdDeIUf0/OGIxcfohnzNnBK4eIWFLjB/FiowWtiqtdjEgh6Rx2Nad9mF5u5DNvZVF3WHsaGdxlIhfzcn7b8ioqkpPrtoyxvJqghGMn6ZjPnXQcVhsZhjkEaGrvbqxKjX51Jm4SxCc5iLX/s8JXT0uhYZK0/1XOC+NS+QyWb3OFc6/kBx4rUQfszBrBzkZ5JizE4aJ26vPWgK1AkMoAoQ1F+xS3raZzZbItAlvK9/tZJvLjTSrA2a+zWRhUVB4sNGf+SZxGJ2qKV9zDhN00e13QikW7v8ALbuIScUnB6V+7yi9TwoLK51Bi9iV3nAn2Qntjqs09cJk5qiiI8zg6rfvEFH/4mG/U+bIXCm1ZkUJhjoRwnl7NS5T4E9iJOMFnFrEmspgYeVp6G9TUtIg9Wge+3wE09P0g6SA92JtjaUNpR6L7zX4QZYqNO9KOBY/lZlEh4XFh622OjzMGD/zNwsO/WEUTeqoAQudLu/gRpMA/W2mlwTalEJXKnT2rEHv1Rj3GZFDQlHVEgaT/AsuoUiyti/JNw9lQrweNRhiL1EDrjX9+2m4Ijgr2nU1Uin6LfnKbUyyCRX6SHDEkT669uw8437Ek2iMTwAw2jNHQZDLCkGq+flpwBcjgQJdpM7Wqvas03TTm3tNpJANGo9ElkMnopN4zTe6Jd08wiASqgySy51el5imX+QTImW5M53NhEvfCOI7kUM0RKW3LWrutk/i4KKLXXK21ctuGesH0SexKqP3JBDCwq5czAURUotE16z6obKq9mdui6N3/tL0U3Lo+Xtd0Y9ZrsvO3/CJY74txJTBi2/iJy26Yabm6SQpVSiWoI8D6VQ/O0DY7jJ2of9a5bJT7kcOHL0x9XdTR9zINB3UIJVj8YBxjjqaSWzWdtsla7P2/ZgavzhWuTlhmvNMcWRy1aW1AYGqoa7o8Aa1MsUUsSSY1T6PAvsG/nM2bp8uiPxgnECr6UI9XaxHWa9kMNkijfZM0gMWSj/e+LpQdFnGRycg4Iit9o4YSe1qJUuh4gPcESZRMGOTE+K5rl3o+CoZ7lX2pOWNBg94xRBBfhOU12w5qqvz2iocjjX4ETA4T5HYgDiTDC8R8CpyR+r8q2EjUBF5rMrDlBv70Q67fswSsyH32PVXSZja++GKVVlrysdJDL7kcMpC0mLj5c+taySRhGLOlHwH+nnDw3mp8bgP7AmwkZU4MFl5dvSdn8EpBAeKfDkdWP7zIyzf1Ni3I2qeTRB4lsfG22Q/DESfL3TRjRggr3Ro1wpJLA/cdRdsReTazBuwKRdIPJDKQndstqLDWBPows0ptzsM0zPltBpKmZUGCZ/PXycIwHzR7gM70v5RQbhbQDzi87coSt/EgsqcJhkGdhCWwZ/aGCvjv+6b19Zfj1iPmwyF0onQjFrjH7ii+Dy7EXMEP5yos0KhLRVwdeq9XiD0UHKZMOdUkq4PUmniX5mPX5N4/X01llL/3/g8Y9nmj0Oj8y3bpvqZAPEiz1PkfMQM6eEJ9LAid/IFnXID/dv2QebbWkGIGC2Gu+fB/jVPik+8UXsFfVs4CHycQbsxrq0HrpnKhhdmajZSo0jGDkCE4TW8rYWxoPjyDv3QmajfB5RyIYVXgM7WdvUGRviDQmbA8KrnCnKKdPLFiJ3NcrkMjWfTtuu+seaA4qMOE5kdjr6N6ny+lvK8Ystv0/xqhkkNV+vMebk3OO6MqqDjIWGnjICdSxPHmvjWD2megwRW4SRamJvOA6fIWcLSrDU9B7wKdVJ3QU2qY3bPw9NS6sqijOp9Xre5+tLsrb2U2pUSQRdTvNvPYUlAlJ4S2ZVMmVVFLDwQUCULMW2U98t+GC6/wRiFwIyATcd1YPlc5+lZnm+PlFSKtItJeYYWsEkW/WLdwqDUTArRzC6VrRj6FLiEKdzFqCGdMin9233EU4OcEl9hElt8CKE1t5ptLZ5aHPAtHH+H2wAwnvCby7wB6hFffq+mArUAmLgZKbV6ugL7UPbTcxLY/+8LaRnEbbFql5dtg2Kh5BEhfnoW+8cLTrVVSihih/QSZxZ3u1/d7NHZpohvNlKbIgAhqsA+GwKh14jW+lUJg8t7aIXBnYxBiHoTXutUn62hZ1szAdmmrxG+67CVmaGDvyQGXV7ehKgxPwjBlRQFqbqDPD81Ab2k0PZp+BypqD2i5uze3JoekeLje3/fDSAmxOzNjS1YvDWdKJ8d5RT+b2etdEh7SJxAw4GDg62KPkRnNa4UCOLxcMGXklSQCk9RPDNT7yPc3C0ydK9FAZ03wXmmh9BjpaTO+D+553r1DwahfBCRi2sZw9H5FOZrYqhfgDzMYehHCUcpp9MHwQAWYvrN/HRV1KpiJsg583dGE+0pYJw99MFEtoFrVnfdJV02znA4VLHCfbluVecnnw2jr7NXzcs/msyr3swYN1W4yxjVVq6hhm2sJeP7+/YO9LnAix2tmCvwfYJilt+XYSdNbS4tyreJdGGjLG36bDrOw1SmgB/pGxYxnQjX9Is2luLMdlnSQgBBK1Xfxex1M78lnTx5uq4lDXz4l4eJqdBKs+AFxgQqoFYHHqcLiUoSGD6L52smk3uLQKsZbyvGDebFEJoZQvHCubVD1yUZz3NbohuNgaZ8TrW2zoXWueVs+oNXZl/Js33M5g8yVrUF9YKpkqsE6Ha/2cs++KXbb8pi/BSSY+1l8zXSRmMBdor1A8bGyYp0YIg45/sLOJiKmuCHl3cwR7SZKhXSBZiHf2em9N3w2/ZDlvDa1jL9Jkzu+6iGOQKKVuN9HniBr2kxNaySiboYlirnVVJGEQ776hZHyRtMtOK0/4JyLvcRCIqEXP+70AWvxDq4Nzglj4GkiLYufl6wTgnp0LfMGpH4Uf5yfILI9xdxC7DcoK5ni1p0VExr8A+Ndh9L9XlJJ708LFoBIpnKV9kVDKJmPLT+Tpmkvk37FZJEhE7Uo996brtutL8EqCQc8xtLu8AE4JUka+m0ClZcFYF0TXkI4jkjwuNIOepT1jpD35pNLsCvDPeegTOXwWs2jQTNzmq835zfrk/WLR2lWVON48J2D4ODMgppTux2R7GWQ8ceBRiu7kKlXycjfIbqwi4n0sehUl5almf8AdLNnHZd5Qu1mJBaYM2KAcShcboaPeJQmzWDujvodzT0kWDMp7onJ+/Zx+tI5NlonwYT0LNmWfzjagQPXAgP0JGEfH5YXA1EBinJHwz/DI00ojyIKXo5AYF6Mqkl7sVZkh7AYKTxstETxAo0r8oexE/xCtfTLM1LvfIMSX8S6QcaqZjM7Bz2V+qIYtPS4n8Wybolq5iyHy43ndA7Q5Kxez51SYyK7xCzPlLe4FILqSo2MKCsPupd68U9BlcHQRIHBAwZ6UJAhGSmnnfUDSgt3Zjn9j/MaEqJnXPe+8ZVhZPTVnGZWub3HxRihJTeIa/x0ZRJkRgewnamd4zB7fv6Mkf+/9PUPuLo4gdP/mFXPe0cx56wkbFLBUaDvS7ecPyakrhkk+XTYyd2v2NNZ9loGkxg61XWI930WESKT/aTT2kSejqkR10aFKbBJURc/Kr2KNhJUx7Uijbj1N4k9gRtS+0ipjwBzZWzCTFNfpwsw1GGaM6nNzm1aiyciRTrfGCCROW9nfry+99VkmP5zohXfcx7Q+pcE/s7ONr4qaRRiOObEoMbCqYf/WIV5IWGV5JRWbwRRnkHg8/eEiTxhCCVetuCB1/bBKYSBx4sO3ceGBy7I0JeZkiDkPPSAAkQVUL8olrV02t8/NWB9CcR9eYQUYOqy+7dQgwK+UVQMv3uZtc3GDJmylPUgMFELRNveb1aa6HbKW1jXrTuU4R8W47B4qty5lpcf2hQSXMv2O3eoHG23wVWI6kUOLB8MndE4TutB1KeDjuOgWwS0YLuGp0ciqermphZLCOWfsjONwS4igRoa75wTmzfwddpKNqUSfARRYvXSPCnwnFY3m1oEiVHZB2KrNtR/2X3mXPocZMuNjU7kdljhIiREcJ0XKs6SzlHFRTEnhL9A3g+sgRsc6384vJDXQrZ0wGDseCJrmsjbRu/gQ8KvuslvA3elxo2oeIxJT2SlbPqSeJgJnXg3cCgBu28xFrqSLDogGg5vB9Dellw/XxP+K5iS5UfwteVBjoEADJRhOdYU2aHg/NL2xPqJCbv+O+2yJUNXGggSbb2CwU3bb5YvWIJFX+XIQYcy2Cj4g/VFxt8ArQ4fOi8O1O0MF5ULHLYzZfunlwheDP5DlS5wKELZK8eQhMbXcoP9k5+XvZfeahwzAFOTPMEgxRSma5wq4XvzR1uUyHBDTzuwBA477roXMznuU+ADqUYZWadDSfUq6ULi0Y3dqFwJ8v9z5SbZIuRrD7K//bkolXqI7WYvrMbQAU1q+Z3T6QwGdmGZVW7rb21SPmNV//0adcDD7ozGr2bhI4neUqwRQVZzmxQoVwnVn5DTRS6psCVpYCAz8Mg+Hecf9J+/c48ZxqKPu+h+IvbgPL6zY44756yzUhZwoeqX5VrgZ8BJPc7F5Xg+IAwp+cPBvhttV0tq3CdDYdN4wOd9DDYDDloGVOfb+tuMHyANX/rZPVG6J7P/oUV9JkitZT0hquL3kcBWnQnqyeZLXCKqn/UwYVW1YwKdEWqnpmlIqrwzUhpJp6S0f8fk9r4g0Smsq6gGHegAT4w3Dgvvn5bCCZQELLvWCXgJHvARCdJkHEVOeUhqpPFoWqPwqybExkZXoYO18eIL+vsAKa73Un5KtqsMghNl2qlWJNqyh1wwXaUvqnYNVWrfr+GP2gVh/k4UXarEcAGV0fwANIdSreURlP4ncsA+IAgUBxCVxicqRbeGGTjK43KKnzqiEMt3xgpyeRhkkSDVo1E7t9kA4SeX3TUH3UowOqcLRyEINIKZixXVPfa20CVZSzm4PnNu00ipLWuz+7JPLHc1OM8kD4973QMR1uXNGcNgT5vBdzdqR9ZtmlwM6NE3D6KoN7cZ8HREgOCttzTxcNbheHPJXWRX1ibyJXc5ZzSgryTZWsHwnesfEYQHFQgYYatr6Um3WjjqDZ78MA4ALfCC76SgXXEYqlL63UaUevEgKQ1hl8WfEKbJbdFUxxj3ZmNhfWM0MyFIrHVHwkqX3ai6TfCkD/5OdxhwIaIikpFqHJpoI/HgbUd7vt8RiaHjxryr1P59Big/T+oD62EUnDhfE3KZmQ+XHMkvKjIz4sbkLqwRoig3wmFW40sP/JyTUxtshRTm10LDPoPRY8NVKDZCd4ixHwDlGnaiOcysuy7fpoIg2habtNhKaoLmvAJWjS0Udbj2iY4rE7eB3qiG/kiK/7Ql8JUQK8y2gDL68Z80/4JFLjM/bsfV7KC0SqJgANCrpz82OjFJ4DbXayDQYwVvTel4D3CKx74RFvQAbITaZSnyp5KwagrHiZBlejrE/HlFXysVi2zknrW9+anuKzAMjmXF2y1Zk0hqrz9ddhfGmZYMkm9MkUIgRlp08jr8pWBf2U/Hds0Qch5eums5qK5hXTckYYBADq4PkN3jH1Bgzl1OyLK+RAOQgx+Camf7xsxxc7bBPID69EePCzokyCWNEzcG4zGF6xOR06utaQIws9LOvANyWF5tyhcvFk3xzWm2E1mfRe3du1Hkk5Xc3+Nkcq0wE6YqsAMhRHY7W0dzgjm2d/gxXLPYGyppXC4aG8f59NafiYxPgpEcEQevjmkuhn/8Hu36ju7kl4aRHfdK1EgsPVnJCRb4A4pHr6dK2vHIcO5SbQxhZfeXSVu+KY1qez90CncDikWPVp6N+kcFKIocZ3E5s1Lt5hiem7FZlNfaXhCrv8NZ2Uzzl44ID33J9pnimM3EmLeQcFKK82OCVPSmgU2XPRJ+2/ctkfM2tDR4YfaAsqGrQirxL28qBOCR5JBaSzm0AghAuUA/ETMHfk+BQ4DfyQjcBDeHQZ2dxgwDNa7+F0TVd2cm6UGXzKSZjniV71v8HKN4v8bjTEak6mdv5M3KQ8Ylad4hsuXogX2vBWdwv6hEpBADnCtr4W2kQomjVjCwitZNK4UR+gC3aKmhgGctWRCMvpw94Eb12X/Qukatu6TdBCoATbYRWu7PgKFnE73tuEGYbTTRqaRTJ+t9WI5CvFuF1PgUySnXhruWEQ57hg3+jZyiJERRBrm/TpqrQYY7er4gJ6uVn0IHOfEg4oKULExXQrdjmBykrKqhboHswlLLHD65R0OQxQZMk3ZpCLg220ucWC+nQ8QbrUqmurQ2AfJrS02aLw95S1SrqI7tiUglKbR0Z/ErS2cjLcrqfcBERkiAVB7t5LnVbb3wh0z5r26H2C9+m5bVV8uODa20ePmFwOi76kqsMsKEK2Tg4EbO3mD4MIeWjGKw83yJxKvg7TqwyaTScg3ax7H+xT9vDDQlg3xu/kzzuO4kg7vrDSbdbUSHD/nXAAjO1PUlYDJmkZ5Hwwfs+lD0sip9JqvSHo2jCckOarklKRoDR5ZGvupgCOvbAxJ4hfCTKjdKgEYcOxwPEMFfY8ji2b22BRn2UIWVbRijJzDLbV/74uWYKLIwWUZeh4ooT/f4vhpP+LxgHOXYyLUp6WazNkBpiDdQWSYLf8Mn38SAcQYRxLwxPcGdj6UleinUYO3m+gAVOcs2JxJLn2nlqIc4kIRJxXahyb4G2mVXiYOrFphizQG8LnydBEMVzhUCgJ9XHTUf5kb6CuOOWtH9srrBL6cpRpKcBTbSkPW+fjGPLLibvCWW2YIac40WaMXHnHr/CuFXZw3PSG1QmuoIlgfyh/O2YIk3CGplIcT+3D3o//LoftRdbkA9NmOnNzAsI99iyEKFt1u8E2B8v/nC4rPyGZokSApVmwcLYjXr7Q9M3WzarGxtfXzsramNi10oQUGF4Gs04OBKP64upaKH11T2yteCNoQJ2+jdmFzMs5xNspiDSJ5lutMDPuRQ0DDpIctCutMlTgZhcG2E3g+K5pKbCE4MrsGGH8YHyCtuX8M4PBJWebq6GwGFyuLbtd1PkoYYcyGiQd7cJgmmSjq+PcgRmMu01HxdE6QzKV6ofuk4e9T4LZpU15NJh7kblze3uyAUwpA2XXvCMC0W7htAjh1qQjxqqAiAv+wyySl0Du3X+ktuQ7aa2HpHhn8BHItmj6xFnqrmzg8jeDIKeXj9iWZJ6O9tN7Rk7tM+loVZzKhy6i5hy4U0US8M530cjzMdkdngNFD3JxwgtZvpOe3B1JQ1ITh0VZHIGdoonTEUHvGcfXRWG9CX58HTk2xkEaEZ1jM5lzDnAfGM66dFCoaJn2WWCf2TmL6wQ6CibEYARpvnu1qL15cok0seoR1Xm8hxHNOY2db/nVhvL5yfKpBrgTd953DWl6HzPrK5XpMhiJmZZx1DAKGl2+sEWRytB2WqdAmGuP9ghs7P0Eq12WhJ12YXCkTsxoDU800B5DLi6gn0IcLVZKuIYCl7WM///iupG+bW7UWIW+JY4y5Zq7dda0CW86zvM/Zk9oNmpjNHhqYCD56h2G26nLYloLBsVHF4wkAZnn0NpUfMYDHArgx8el5bO+S9rzlFXEgVyULlf/HRXFFNkqe2WAh3MM4dNADfCK+d/8yXGCXW/M5ekLqISAoT1hcR42/Y54rBKTZ7ayvNYIiO4EZxt3W/lXepPKX3c7W2CXCSjY5PbTYdYSHRSYBsi5SeFv4Hgqsr7MB9vUKg/dStDGpQO6bhv/Cg+0I5wqrR35+hNZ8ShgfPKlMIupZWHD5PPK0xgvVdnMaiBOORvJhDc5aCnNEgZBZUU5B9Xkc8nQsVEvHPrYJ3O+KAwxfM6eqwZkQ2WiUAM4SkKVdmKVTLKy6arXEwW7TS4w7GVlhOzgr3X8B62H5rYW0ToszXaQ7/6nsx5lhhckcr5yV6fSIZKb65MnOBa+gYANBPpGe0n+ffd8kGB25c8MO62DC7aOjsN70Xsjt+uCL9GphJ28edRqZr9YQVCQhDJXg8sAg9I9CCuOU3Ia9y4sQ3nnZrAN0gDT8sQrEPY2Y+Q1Inuu44XpAgi0Gzmp95WUnf5gqw/mQS9aDbOMgiAOrsfq1S8YrkObDmwsIR4vKUSno0/UrH8tBP//IONQwLfpKc+bs0AgOExfzRwBx8fx0TbMwGKpyiU8Tq8cZcoNUOpsMaRgqdAKwekiKWS9FAB7Kggc1LYnmHpxk7vyWKe7rMO70RGBnWygGqQpN/dSZPjmrKzqEJSmBfdCdHWJLK16jeeFPMWpxNpZGSGVa/52nGJ1tI3QNDSwwHi18Cj6vzKUx8LO5oAfj+TFBffjlFFGC3ThITt71MmGIiM+3CwomvhnOsi9xK8UdVAsMa05O1fPBwdKg9+iDuidqoXLg/nnVlveD4p5LY4spsmauHlayWD16ODUcum199qk6GwnbjHzA9BLdGn6rE0foYzXIq+6OB6ndlpfZxBGEgIK+OHLDHMO+46CedL87klGdAx5N0jgPFe4OUxzUz8Ic3X2bjmYxJdAfCAo8+aUHyMROrz3m4qIFWpsmBY7NEgBlmHhG0bF8pLc7AwON+YTT8BzGuWHRx48m4ArFgWlb5zww0+Z6onvt1HmqEreAdkJZ9zb0fXA4PP9J6XR7zWxkykoNxMYgfKaCsc5N67jyfNEMhLT75k1DNqsziR/0Og1kgmiznhPTx/7jvDu06SUyS7lY5kEDmPytm8CeqtzOngjVZZ2V2fEJe02+sKUrHMgKv3yvo+bW8ciUMvRwKbqdTUtc7plYIn1m8z9FVSZHMD9agTq8OLy2N7+FL+eo6qvGC3m6qChZQhK6CovfVZObunA9jAKvEaOm9FqhQ3fdPVbsgrS+HtAMSPaGFThybD0DUqgifEaQemk6NdeoTuyqGE2O2A1UOHYHTZaQR/GitvDzDnsPWkApODJMorFcQd85ols67/i5Cvt/wXEqmHqN1zAZaRqdWoXGAGKML1+Te36da0p7X1Te9zk04qCVD1Yqk9BjN4MVM4o/Yfom2OLrlR1dysveR09kH0OUkair1lj+jhTWyQ2B27qyUAZ8UqVFSNCcl5xGIdw7qgrL8108po2hYgJZFkZPOjirABFy9FY9WBdnqaKlo9ePqo0jpJVLZ058cl6TAiR1zl7nuyN6Voda/Rj6GKoyrHZe8qcuDJUCIDfEEENRnTmtwQHbMSIU0bxSBgq4oyTHjk9p1yTuHdQyVGA2DJJ8WBQqSWEFCMjMLsk3KLxehLC8riZd0darfypw+gcBtGzVLb4fsEJTx//0qaGz+v0i+S0xsW+exTyMMwn7/1MbFi4b+mpufONB991UJVd9dMD3rmP2N3fRKw+2yY6yV9YMUH9OmxiHUN+nTYw0FjfO1M/72ayoBeNT6yPhh/4Rap9yDNBItSsN/OzeYmdeozTvPok62C4iOVobS09XJ84wVVjdZlp3FmyrXk5mGtIPpt3I4/VtpS2+4OKOkciUI+R/ImK8R9uNAnod5HIc51d8Pr6GMM3taAWkVTsvcw9D5Ui+cOXrmf+EkMr+dy7xVRK/BhIa7JKAAfaOREkESs9ihe4OUCvKzwj6QUx5JcydNgjQzz/CZnaOdCJtDcV5/k7a5RfsUGDfmDwlFYyjRk7Wl6hjBz2ciK/YhYZi3FXtgTBq7hUtZszC34yDSalb4m5yXV6a3r+IPRLgiJIdxjX24Xm5U5Ad03fuo3dhnuQUAntTEtKZTeinrgg56llsWwkvl1I2UUtf+3cnXhKuqoCesh0AKQsD5cDEgOaco7DEJFn0t0FKNn5A0ET3kpxH/OnxMrguS0lNTgA624RnZBiZsbiIXsZpyxeyrAbzCZgw2iGi9ahSAk4uZwFy4sfroEvLEbO0h11SQ0BxaleOZooTEp5K5I+XcVcIkYn6BPvllAbc9jsygGVIdZNuEizzqMjNq7OSk/NrS303jCaOtHiwcAZ/mF98N6l+dECS6YAt2cteT6G6HsY4UhNrKiHo6ZkNPRra8jtcUC/qTym1LcP/XmBV4XvfnO6ezQFsy1Ygiuj3xbibNd7LtbzzHk04hk9yTlVFoctKVvEme20Vrl7q5/eMXgETqUVXhEM9ZV1iHFuaCT40tAjIrT38c4fE+cCfxFRsidRBqJcSQwq1jqVed+bpH1CQZnzdX4nKLKqz27cF9cLsXfAUpSL4r54epYGTldSdmJFWcxpVdnZAJaLn5FPNafsUTSC/izKN7o0ckb0qH0AdqhIgUkEibf8ZgOeuroTZwSy0xkweet4AeO0w2KFj3Z49Vn5aYKWH3PoOqgPoy4SkBvBsj8ZiaTWhYa23+6WG3zlG3F1p/H/HMtwCUzXc6N9SjGwy5XeQeNazqj3+aY6wWsks942MNsayqMpYNMxSJaEOIMG4M4t80U++C/eezKdyp9jIbsVcVlgERCn7fM7m1+HbenjwSvMzEq2G+JWwEXqADFJ1NhRrzorDfsjTyKGAfm0pUtP/mIfBV38yfAo38h1l/OMpl3pto9TQzYvsdA+WxoWysPveUSImSNS9mFX40o5y0RrgBC8A/6ctnwqrpc2b7amiPPOXFKANAWqyUpW5yvrcw/AKcGdzyzH526Ngza3CV3tO0qkdsKfjkA8RydSa6P12/Bh8B9Hrl9nwK3pPEjlXV0rjYrp8EJvD/fRiz+FEfy7IALF9Ab0a0ofg2njiq7koYs20CjVKAertDPIMaXUKNAFEu97BYZG4paoPV/wf6ulYwjVDFV9M7VbMxI/c7uTR+kCRSldeJXuFG+7eZ/Tc3FYdzc45B4Ax7oJA033Lwv4FbpOa1GfVSV3B/829BGXY2dQEs2VCidW9u1tBjjc7bp6DkL15JZolWuM+BenTw+MUO6kusqGLEY38Zqdo3M7F0OVTQ85fxKpe7ngT8vTMhe0NuWGX/7X8pBIsNIqPls+TpDgz1CXQKJyTimDOoG52lu8WsSxOaEYmDppR2Oc3zWdHjxnv30KnAIsq6gJdaZWGdfKRS8bNaJR2fgq6f66pxBinhsWhcV3pmsOSjmIgFQvRs1REoZ+IoqKWPhaBq0kduMQlbOMtYYkhwlD6U36mWlxg6ZRJ/WvmC10zT4OXmG2ioK+g/MGdxvo3La0u2SXzJbZ2kI9+hMeuyeP8/gl+cb6AJGhRrzxl+mSt7D0gVysAcDWPuzVbEbFYpfX/j8cI4P7CJOWbGat79MkEaHP1l/jECnw057Cpkrow51OphdfT2x5AmefojS83i9b/VFHIKnn0OVZzaDusy6aEMd3sinBUmClJrFvR1qEXHg0k7xkm7l+MHRNbo4kYkYFgRvor/UCtsFVI/gz8hudxYzqxGwemWtmFbbwk5TaUQkZp32l3/BYKLUM8PVRszCFo3Ox5O36orpQMEaA7QEDPD7HTalVMVTNpF5gjy3Pj7x/J6FDG29Z8iPaKwGpAlzJ04yLa3CdeG0rjctw5OB/tEBhuCQFOBMtRRivcIKFry6zU5vmCBmGXn8f1QuybZZhYf19sUjL/w6Om8PhoIhM+V1cmpV9CQVgJe2ms7p3UIIH6TNWZKtChydEH1i9pA9BVX0aoLrByAJfwWsjXA53a3xv46a+XMyOj9Kr3/JKlepeKPMZANq57m3GBk/f6q1RVwtfFbrWnhy3mAn11CmaEvu201jG8hJrkKRvmaSebGkCfny8eHXpSDJne+bZf7AhhVhfxgCQVvIuzHNdro3J4n72uNWPMr4a/WqKILyvLYu8isgDURc0RcbgEVC5fBmAYyNkU7NBYHgBotAaIyuXKqL8xxQ4gFLV595wNbbTX4wYSFel/g2mQG66dg59NibmOo3vEOAN+ML2KaWAxThYLCN3OWeheiVh1fTCRLZ9oKWNeWX60VC4fK9+5h8P9oDJeKA2xdICo0r2c+Wvb0Wv0bBU+ywYRUoj3scIvL1PVpn6NEJqnujQVHfOCmnXTC2ATo57fNzx/46Hf1pSNI4yRleVpXPah3fbD5HQz7tfr6kosv8pdpxxVpo6jSE37tQzY8w/8SY7fUguo+04m4ta4qyIwkLRFzpzzHqyauqs4GXKJF3OBIQ5v+bZ4HTTMyMP64gAFr446o4oeHUwULDO96MMXh5MO20qu1h0YeNJSCjRfjlwlLn4vTamihTyeoIhAmhXI8vFBmSy4h/uEvm82xlvEBstYuEmRE7ft7VyPAgQkBZbclZRw7TzNUxsSGpSKdMPRQWQCDrbt86BTfUzHwUhFgJM8hbvQdJ+bn497l2GpRM+Qv7FdLfazxoLNMkB5b0ZefCpD+Aeq9O0cRCoMSdHX/cm/GfC1XTFo6ML4QDowBhmuT07GeZJDWLaiSL0gGxOE+l/APuyo9De9uPB/3pVkVY+a8LOgmMTpUikK7YYRDBVt/W2d8XhBJVtk+kkGAYUSe0nb6RL8UKipsRbubJfs09TgmIs9AF/Yr4vmMtNuemS+/EOr94QqA5v8WhI30TIaBpisN2zSfDjysFrSdQmKKtCknPuxBOJks54NosML6R6g0z4qdBNSPQOrvRZcSdhY6xPtXrvTdJFUO6gqUHLv1vshGFXpx1mR8tIdxbrbGnsq/Odj9W8NLW5qabM3y9wc3uaRGgNUAF6hpmjLBjBKDKbdF5Z98/ziLfKpSJ1MD3ocfywtMV5Bka2v5BI9vHmwGmhdy+RhfYIpdw+b5chKTxw8pJ/TRnBef0KbMxkMuf1sC76h2vNIwHWzUFffGKyjTUMqlCUeJ1luRJaJGmNyWB0SGBZavA4b1PtvlUOhKKgnUu6LHT8JZTFZ+hmOq630rNJkiIVGkSGZmEU6XdnlKE/69iDUHA9/dTJPXv4Y79oeT2yxWUMOyzG0WQDEm+58RY82mBcePv2Y8WxG7QbCn+81EQPvwqscN2LvkvdQXZtN4MvGodnySg7uBmrXEQ911zxYyYZXgPMv7tRWd/FsyqKmn4Cqh9hrq11WycOnN5p3lUAiy10Tp0zY/m8xAyw2Cnewlop3sKBn6MfSkW4sAEhYM57WEmnQahas1jD527PEriX2PNWjiuQBJjl8Xdz1NsIXD8GUv2GGjczjofovtBnWn8xnMEfSdS/3mnj5qz3tD+tome5UVV+O5f7deOeOuLvXkDDQkkBGP+e15qeSIXqhLklXO0VuwXL3FM4XR6ZvA7PlZK9Oriz6o7t0+j9PgqnPkG8YPaslMm1tgcyGRzbgUMgRZARO87CR4bKbEK8enDlc20C18sMIc5J6caGnjjTwCG/NChATxwnxVz+nvrgK6Drms1PyIDJbbh6uaEJeRx9cSlqn9FroB8PHbNiVCnTKH6RxKsR3eyoxOKERsrCg+Ngkqua3tEVc/wh9zg/ajwN++Z82HcfqSB2hoy3YnfQg0Zp9avVM7J7aOD3cUbzrcamo4KJBxRlU4ejWsRrlUTBNUjFt9PFcUxg8pICFBH/REujtZMe6E5E229lFndhpZk6Edc4pi3SXNno8eHG5x0zq/VhCJPD9y7u+hfvqJ3XChuMVu6RZkoq2zOmmGt9U6Ex9apW3BqYOnMuzuXFfCcj8jMbJzF/IpOPStMrUKuPtbkBLjxOPW1AvIHiVV2iBuqDZoGAp09fnSvN+K6C9Zzai6tnIPos4Dem4sRWb1a5PqPluEi6pF/bGK3bRSnwYw6XQuxUpNy7s+Wd4iL+Wq739K88+x9XqQ7N8dhwkGhTalxe4sxfaA1fo4P8FpRmnvaBwkVnQqg9ERFLF4JAzV+n+63IykA9v5nf/BZrTbJeQ1ekkI7DjPxIxke6fjmpI0QYV3P9VEpwJ/whdUD2E+0rb/akOL17WDH5gUngzGzdjy6LLPon37R5GnMiW9S/e/tMetyfEgal6oMT50jyGQXm/E3lwp8NbI5RQychAh25E/f5PvlQ+SaWA7YLoCt+XyMJz98SrEbV48cTEVHD1DUOMT7JRyW31Ifd0JThllQ7GBv+mpA5FkCL0qSM4TuTHL7xvd5xIWBlm4aNF3S4xQQvizknbeu/dYQ67MDNfXwMpULKztR3YHd2I7rQBAQQVlBVR9i5X0h/ZwF5BWTZjEWZc/U+9XrmPRI0aJkIUpBiBg1KcEqT4u8k8GfOBMHyEKEXnYgf7xYRtcBlCjjg9shQXkLiZMJPr5xsjozBu8GYopOOp6ITWPFtvkNwmbC5uevr6MUbOEVlo+GpML8mZBrkklozwRG/HrXbK/P5Y53uB2rxnlMMp6hdgeA/8iFkVb+4atF7MlqkzasM1eJ2dvWN8jGngbaUrOJCWwip+FCIYzVT5OWaTPuJFTQ/9EcXHNNC3J9WFWeFpd+W6NSVc5QGvHlzFoAO8Ngb25SrRwFQuiUcBB0Xenei7/RRacTxN6C6iGxRTqwluNHqnq5vNIC+TO2Ga1cF03IDePqKwvE+gu4EIXaP0LpWUKbuMLHnmDeABMHQ8PE0luivMfQO9fUixfvE9A68rWutVp13V9pplt+GpcIa1+G558FX/lIEPvQRE2XyBfRFBJkuuAzFA3uNjDxG0PysRMg6R15X5BM7IzKf2HKpLAqSVsWCKJQR6yikE8kmnGn8hWUA+pvrI8v/1khf2RvdE1/INVU0A2RfDxzRRwRnUgTFkF+odZvhSSYKVJTPJWud2ed8YCV/1g3x9lvQsKUNaeKB393iFLWHln3sHCcgQ7WJYjTjtU8WgfRVxMsSHFWU0MlX4qVoojznfHMHj1XvHQtyoF4H0JU5zLiAzdls8bs81HQ9/JY5oZS2KXdRx6xjrUvNq05buJuUgPSoFR0AhW0QKlmPRfV1T3/nh+nbUPszI4Us1ngRt+D3VoNFucSXJqZV4NvQ5ecC6zjUc0OFnEBl/GsUjZoiG9/3dwSNV3GE1vTfkHuEgMOB7EXNELxt0tG4M2sP7UbwTi+HRPZVt8slVyORo4o93fCc8mmwJSmD74yRj5TbDYgALF4l/mRKnXTTIWTcGJ2uWM0c7tAPIQi0DvV/DUNP5SkzhKLlUNW4OUSzfFYYaRkloD+p+ITxflwXjYNeStUxU/IQDClJbV9rg5zX7cL8O//LUOIiWVvusTPkzhn00Q2xOJqpasBL1hfrvExHEoP0daTfJv+8QTaD/nYQ9YWfPo46eSCyXnlK9tSYJNKMkOjUm83yfXZCS5Ef+mPq090No+5rsV8FwMOCLlaFASAJzX1PLlpq2uTcMXgoSc3y9uEZdPrtyKsw04JhDC7GL7oV74FdkqShuIYHb0tPDV6/1hfA0Ehis36Y1Dh79xcKkXeZ5WPi4HHuoK94UZFjRwzgmT5Lin/0n+/Pg6cai/lV9SYKe2F9DYHceuTrOzddtxrxXNJRNyfI3ItftCAnil9HIZwpgETKB2oC+W1YjlVIrYi67M5XcwFjfiXGV2ddriJfFcLPV9O7Ol7P+0bSad/MZKkh4axdRL4PbESS8B2EFKoqcq2t+ipE3MmGOPnkG4s23bvmUu2FQo6Zrtjs+V2XMG/mbFbR8EKqlhix58e3jC7P1qSx5zD3jGDlFPOXc9a6WiRQWsiZryUx4Muiu0CZU3dRZB3SSl1Hzb9vR4zC9n/wMza8v/6Mq/EpNcFTEmAT6YImYTY1dLPq8483FTX1jadGjv16J9aeqK4YIN562EjNOrgkTtxaVYRkRjgTljxz2NKS/yriMuZuLLQxUdiFkQczQecw6rLM0ssTMF+17wP7QjqWVkONH7yHKYclusu/6uDQnccswMoMmwCrbdFZKpKf0uuoZ5692oK2QL+5WTDOMk1zUXxkWuj51BHKRq9GQm3M8W2XoXXbmWw06W28x0+l3cz/WhhCoFifyqGfA7VpJmhNVE03YzwMytJTeJzlyUcfBjP7gFxmTS7t4HCWEZTKa9iDglrCgpBfNgcWSWAcqjz+/7d+QAxl7Mby6hDobQE7SARFN8+0MWde2Ph+2j1IbE+Jfn9ulb+7Fksnfk7q14S9vOucw3rrW49iCxUq/FXp2bbR8Jq9oYw9YKr0AyO1hbZpWMBxTZHTdidtSeaMBdBT3y9AJxnPBVEOocQgq1PDFDTQbcTltka6fh1yQB348ZiVH5ru2hVH55QxkYDAoPcRrSnmokPr3q+yWFikjzHAmEyliA1T69JInamTulFnfBGuqlk9jssk3JCMbXxObmSJomc0rLS2zh+t8oAla2BM2OeFd6vMFU9LUrY7aS8NjN+ge27SJLQDi4hVBaEn6TKf8tNXvsy1IOwDoE8ge5XssvWQOgMmtOoc3YORkvlbPIXGPAXHEHrazZ24KWeMOVbgn4KUCESbktPdAjelbs973odkvpYczxWuZI9oXbz09GWOHq0gvWttDuMYkb8Ut0OQxFdqR4Av7PXDd9D0EnmAAUqf0r7fBknglmqhkkoGvvrv9mSGWPJ5oYerB1kBX4xObQ41075cQMKXxJRsLrooEmFvLPVloBLLHXbT7XShlHDAKqjfqjzTIXxHrJZ/RIw9ZMPA3yuYE4NqqRn+0/f5ayCKnIbGS9HNmBRCfwQFwcHnbWqp8S/Yii/axfkBSjg4Q3HW2pwTaULQYij5rPZtHlOl8WOAYe8k+zI1Sm5jWsmHpLmM0Z1HEQS1iymhWhQGJadi224Mje8JZgYlOmoUHd2073OFQqmHZMuGf+AZM0UaF242qEuwuUlWriaRKG5GgMqEaKBrMCA8NOtYPhBTiR484jIbVacM1JtNZOXNVBed5UzaJFj1u1uPgZeybGBz7Uv/7e3rs7KidazyxdJx5yfJSxj9MsV13++nvhDfcFzJvGYz9PN/ETkBGcD5ihB4/O4LDhiw3v9m+dwq7M3E2zZ8sfQ7i7VO7dZ27hAcKD46u9zByksLXzwvnPv+Oo0ODRLPJtlaMwlj+zQItcwrAhzmFJXKi3CyxvW7R0yxPFP7tA/1QSKjznjK6y6DflzXapDTGxunfQshRDCBJObat4bI1kpIVyd4H2ES5dKp7QzB9cJ8138q1xMbvXISBHpneMejjHKJKiyTealFR97BROHqblnRw8QMEkZIXHoIWmdd1g2TsnNX304R/YuL4KvoW/+Yjfs+M1skcuvNW0HxPU/Ru8ZWgf3k2rYcFL1n9bXXfw8QxrgT/kj1hVstElkKZg5ZrNyixBWMNGsppG1xm/DA/kCa5ZLIAnwE5Cz5x//NuSumPMAkSVN9G8sVtqCpyxcti2OzFgESlkgoWE3DSPI3GS9P0TQr3ym4RCKAomA53+RR8CjWZoGI8Wr/2zvKAUkI6b2gXY5MqIRPokyqFWLbSjMKUx88ZHBKXFywIWkB5RODSIGvkLbA8eKSDIlthdgRHOnmqmmRKYdphkBjuOE6fdP8/4PuwV0TT1/4IKO7WfmjEHO6en8Q6DXbvHSRoZf3sY4/saDP3EMAHJBxYJHoz0wG8HWZGi/gUCMOJaX2BdIr6XS/yC6btlqE6KwJPuPWj3Pc9JzoyKvrejcL0CogEen0q7NIyT7eVUc2RO37tyJVRFhPsTKBv6UVrxb7s95Fxp+4E5BMfErWQvhYFHL0XGCB4or4DSqaWEtjnw3bGGluDZ+FJlABhzSmuAAA==
- data:image/webp;base64,UklGRpBTAABXRUJQVlA4IIRTAABwBAGdASpIAUgBPhkKhEGhBIZbaAQAYSxtwVqM/QvZOjL0OyVbNH3itnlC9ff6H8me85B55v8kf67/1f+B80ltfyn+A/VH9//8Pwq/6Hjf1b5p3MH+q/uv7r/5b5lf7f/n/4f3cfqz/k+4F+r/+w/wn+d/8H+C+ML1nf4H/mfk78BP5l/af+n/nfdU/1H/B/ynur/qn+Z/33+V+AL+Vf1v1tv+h7I3+I/3vsEfzL/Df8z2cf+Z/8P9t8IP9V/3n/u/2P7//Qb/O/7t/y/zb+QD/6eoB/5fUA64P8PfMz/M/138Yv2l9lfyL6B+u/3r9Z/8L/tP9R8kP97+SHatf3noP/GvsZ9V/s/60/3T/n/5z54/x/5S+l/qS/Iz+yfsP9hH4p/Hv6Z/bv1o/t//Y/x/uq/1X4zeePbf/e/iN8BHrd8q/sf95/X//DftJ7a38R+Svvp9nP8D+Uf+J+wH+Lfyv+r/3v9lf7f/7vr//e/27ycvvv+w/zP5jf3j7BP5D/Pv73/aP8z/w/73/8vtx/of85/h/8Z/x/71///gT+f/3b/Vf43/R/8j/F//z/n/oL/Gv5b/ev7Z/kv9x/df/3/v/u79gn7P/+b3LP1R/5H54OJ0bk19fbcq2+B3U6LbOfQ82UXlPI3vZdqajwBWNW3a+B/WKeQXaLn8qXaXqDptrITeHyHA+BQW+vH8xk+FbFqtjF5Rp6h7vV0Br+i54VW1sKPf0wX5Dw7t2flh2ZCzKTZS9FLs7rAX4FZskHpgN69+KrzEDnooiawnPi8iX2ilRKKoYKk4j4OwzGcfOkxtbuO5xpJmgwCwQLYNkPt+yRUOMbdfA/v2xnZhzXghNt1Cz5TX5spRpY5tPyWt0MUW4JLSH9ZVJ3maZMGP3IbUhHJcabImufm0rdhdHgI83JcOS++HNhf5Uu94QO2Ron8NahFsfzfQKhsOqInZ3aowXt3T2MegKC+qMuloFvP/ZDpDGvulWPimMnrINpuAr9WgWbLsGleYRtqmnAA4DGjOR7k0WFdUu1GHOqbgByAcrI7pKG3D3IzkSqBKKJWfmRjOWE4jd3bUIbKfMx+zs3ekSGFKssN4U5l0jYl4gFMYWsQr+6nsJg9HkkGlO7B7LwwYxIjjp9zw63TQn5guNd0rvkyOvlgrG2n6YHYIRo4mKxVpaNo3xQcEZpMKJilUmgl/I9WbH6MqibTf/HFqEJPCkekoOihfsKmdsd71ehn/S5GoNP7VmAfSNnOgM4JoLM3WIHFjmCEGJ/I/KAr3lB3fopHEXfSaN05849h+4t3AOD6E+6elgFZazeMSkU+Hre8L5w0yHpzGsqDFX5ew3mHxzU9jL5hLOpdpmOToFNq1wRliV1IDmf7I4TCiGYHXUB2nY+VrGHFP1D5+EcDMnV67OrIi3rrU4JGPnydpQXcUvGMNAuNZHn/lcW96GfAv9zrZAWhuw5wKGcrauwSFxmpedLEba8cIw0an3h6wg5GaoASLkUnEz7CmfDav6RzcZXIsnyFJpEmfyDmXVU9GdSZ3bXRwOxUTS8XUHutpfKxfWEV+DeNod93ex4mmCTvBtiawgLrZH8cYD/4LSaBWBDjBpgxr/Bk8Ozg2qDA5nHXSHyHbb3eegOu0+xr3o7iq+etoKMT0Cdvt9XnfxZyIeKLQLBLLsxehnWbw7apNHtj1LRj/XqOQ8qt8+mrDs3mnz0I0J8UxMUSuLGgSdPV8z6JPI4/tFODxjJz5maNv2gPSf8XnC/b7KlVOybbNgUVqfbV5JWb4zYx1FScpxoTXRg1+IuR7U/N2+A24zh4P2eBorWgh+fqFBYaDCzRfk4TXtcuhv/qHIzoc/fS0jVvcnjkW39IwrrMLa662vhpoO2klRseAY+ZfXKd3qxAorPcKuGN1aVodrNzX/ZiMS6JtdNWov7DNU5A8iQdZH11SwIupVpv8LVPOhOaeRrpC6kGjyFd/EOEuckySCeX64uKWkSU0kOzGlWqR/4TVpJhdkovYjkw4/r2ygB7AySvTOK+UHCMV6oIrdqvnjY+qKgDLKCBgMJP5frk95inNb4qJF0B8Cpv/bJrLi1X24jDuMI/NdMLxa3Dvf8X79CNKmL4f/AcKSFpJWN48EhQDfaBDGfALqzSycdHTKC3I7nUoX/xSygtqme5mUf2ST8MbwBQO80PWOWwM+DJnWzWoPMybkiZCVMNE3WH0f7BCZbpI9MTDvLudXfP27BJHN+yYfM3Wr+dFVzhLVlQMMI/SO7TGSk+dSBib7GqBuXQT9RGIz0ExACzL0DMUJajxxoScfviHZM384rMEWTzshF19FR96WisSMx0E4BqRBMhuQqBLzsqXXRXFsVycqBAe1Ai09EQ9uOTAWM/n+i50z1vXo3zj+xLIs6RHqFWdSKu8W/exW1oATzrLX8QtC/KTnhin5qAJZ7/BtXQahq9Wk3VwbDy4qK4qyhYhcV9mKIO0QlXyiqobrY2zS1gxjBnXfN7lH+2PueSyLwQEPoTO6B0amj7RMgdwCwK6ZVNxzaLfKFRVGoa1+2xEg3XdDYpLSHARLa4UHjCaxu5uPxY/Fn5Bqy+F2CVqZyKBtAilyrpF2Rd7fN9NG9APXho/0FIZboY6iVMhm/gcoMNPgAs+gEJ0rqpMTc0C3YAyg/223SQj+ImkEKct1Qjp6WUujqHWEnG6vcdI0daSNOayMH5zf6SKYgzOJ1qxC1hLaBgCvQdwjV3f/dtQ1h4QL7RfjcdeEoMtDJws2hyIVrTa2iJYSJNcC5P19RmqyK7GahWpO/kff7JNfoUAAP5D+g5m4wKzX41t2i58NKSFsm4pJAvfExHjMpT4fw+oLKecYumcwcaAhcM54zCYX2tuzHNTINh7ZkboQqiXfzhvoBaVvz8Rz1mXkL/MP4v9xyyiZ6rdhrSVmbRe62BhNLIFkddNBpUZBSiz9l13iVyFv60ItURN3R9CFM3308IYM37nGKvWoKxm4sJAnuFu77ah/nyTcH1/SM/2B+RRkEOMTXrCI8LHgjX2YM5pkkMHb/BdkovzolpnftV5+RhPpkdB1hBcUm0oeZNllPSpruWCuiUAbZ+8l2azpZelqNLVYANwXyneM1LT+lflrqm+qOUXZuAa7cyOXlD80S8bZ4KLM1yuOZnDPhK9m3gYc+U6KnJjPZRspK9kf2TyYy2HOkUHcH/SiXE4G4mng3XID2W+V+a0M5BtbVwCxAbwZDoqVSswVWKuntUe6MGDfDDa0M1tgcZdBQezSRnNu2RHoA7ILXkkkAz1qTBYjXmMVbDmY+8iFCuXmfA8QfitKHGgFxPCU8WUtajRiKLFYYtUmztW+vEmj9Zr5B29zvqTlfVdICYBmbPgLnEv+rxGuBcswJ0g5BxXdyCpzWPYrNHmk1Oxjg/sBOlhCo/3ydSA3PUv3VYaK3rI71E9mDbFgMhelJ9o3FW9w2k98fdQ2+/M+B9H6tTrR+tLzLnI/CxmzNxWjO3jopXoq0L/KmA4ZvtDRA07aY0lFl7hAGXUVF0mI3g5PT11FzMUoXZH8c+gup+woErz+9moduqtyzXWaD2kNNT9llV9BGJsB0A3WgbJyUaAWTRWfDmecnirTKChhTXWgFvfC+YrF5PJmbw/e9ryO+BqgdzxFthdAW+uITH1IKxhQBVn2ykK+TrNKIjHAX2X8wOluNTEWcpJCrtRPE08wuP/WWf+vOCAHUoXZkM+jSsla8vwXmcuwkaEiIPrpvl6eLvsqADsIzRF+sMsZDKnGflvgHGBmpnxZhwTSoQnuq++ynNs0zLx/dRPe14DLLZ0vuDws7w6lnZeQud6l6FT/V+u3ClWV/CpjJcWURDCVnUDAN8YDAplSEIN0oUgSOg5CiPY2tK3RSPS2J2Qly2wdpkQcrXOBOjuJDIwVppozL69hRRHPNVIFfdDOFE/pGQY1iokgaTHnQwOFrY7xRulHnhCdeVlw/ZOHkxCYxrjpEBuIP5KGqUYDROwkr21Tpvyz6e6qlH02nB0U4LCHG27b4b+9CBYLan0pBh6Iu1327IhuqM/+ExokKVhFfXMlx8khbZVWCkneoiMOrLYji4MwgBntcokh8b1IRPPlfhIBaWHN1XjgDLTWR6WR5n9Au+YRb5nn4MX/Hb+m3J56w7lIwES7/y1IUCW70F7ooMAfQQZstwfvEeNiI7vm3QK6imeQuqt99J4NhY/WElROlqca1E/tzTnTM3CUVPl/sNp34YMqMYsacqwDBrkJbx2z1oNkkvxZxAmbnE9EtaoYsg/wuk5ZBxnhcmeviob7vt2NLqyR1UlmDNf+giUs9CIZ2N09trIVGeuwiZm+vHfXHWzmB7LT0uVKh0VtUGedxxqgjyURvaquoxwxHLnF9wIv9Z2TZQ5sFF70sw7b+pKsYhNdh9iJmPCVr01JTsMPzKDTj6SngKoCLrsF8xQOq9QoEYfzy55oL1wqk+qxTaC+unOa5a67MTJXIzhv1UKMgPGX0hGNM2J7Am8MIdFiPN9RQhL1IZ8eln1ZHmSR0yfgEEewEXcKLQiUbOW5ziEEjiFFpVxypT61z3mI/YW/tg/RzabluCsxf8biQnnfhuWZMhwv+ORtSmPguH50c9LWof5PX2ycCKCvM3p5N4DQmHW/K1qrElLd+q8AbKgEL1W+qMuEJ0s+im+pD8mpXD2PBeHynxqDVHCHctDHoyVnpLX/PqGuauh3iABP/OSVLa3RJUeSIOFe5o6x+vMHvbYZoxStfO6Pv769Bl2mUuXBTn++0d1MaQxCtG1GsTsN0ktXG/9zo80/9+JpWKDh+Z/TF5UqFX02pXhcB5TvYecP5p/lTlOM3TO0Lg9Zg1GXxUMausseNZ7KO/Y3aQlp5uIrp55otgOIUJGlmQgvi7Yhsx21sAJPlnVOK1CNlga4gyeJuDglDWG6mENncyzPOM9wujUsRNZB0RVAo3UakhQOveIhnNdzYsEse0QbDHcPPu+Tf6UDF9Ipc+NY/raIZuyE3yWv/9T/VV2HsZqr0V6fMbrDOpx1L0HTqcIV93DtZ0F7gkGPkMpm6OMIqM+UnhfqUTxTEfGcghanl7/uDrQ3cIan2vSynvgHAOEV2olBChKA45qGrQxRNiR4vlcy5XsaxZ1p6Z7CBrZBMHA4gTk+wgsp7XOKSWtd2Tw2MNDI4rRCoMew15upI7FFyaMwzAMPme/X+qfveyXMZ1FPigUoWvIL2Gj4Eb1IqNWyIWt1/6/JF6C+es+RD1Aj3x6oEWltYn3yN8d/DeZKivoqH/faKJiRaj+l9xvaXLj0Xnfodz5I8fJ0XlwPPSe73ajDhDgqRKGZkMLsa3QYUjnUGG1y1QKAUy9Zfm/EaekmBgrgcBe4A0hIEhwrzXMecn2foUns8q0y3SaqYdeEGJmZG4SB//o+XWXPh9L1xUhgudkwIBIal7ZoQhrDoG2vZYjRWoZaEQpN2t/SMJyDYoSx4tCT/8REIRpF0X5H3/InzdVVNuH/eR8wrC4nXD+HyEzDVvn9hf3O+lHlGXd3KJdtrDR/kTUC22ajB/aMCgVGi9oXphhq+l786NT13tXkZ3ewd48j4OmKGGIsGJkSH/Dj0sJOwr34/e0SQfYto98pUJkwQkRX17qrOFYMV3EKZqzl2oPDaQjdnTf7cB78Xc+mc0dgE5oyL8iwUybP5JC1axj+nIHXfIbOZtNJoER8ebiYAeiDn/8TkJqCUAspqNP0vvZj3O2nX7nzC2um/sIdBUTaxqsDLYKZJ45Q0fhp39ZV4MzViiy+iYB5C5kLco8ABSlM9HKzVrSTQtL3A42TCQ7nv8U2Lp8AE890kQZVVPnW/sUxYfthdcEuL4DC9+XbZGOIQ/7+XutVR+ytzd/2wGuLB+YTW2EzNlMKz2BFF2uAj3NCZ0RaL8jdX0Z/1H/sPHpuauKd8p+3m8eQFGdsCxJZ5XnNI/kWM6gqjz8yotNqep/PqXA+RHN5RS/5dhENNBGhv+xayvZgcxORLmzfT4KdzENSfM6UiyOBKDSyxlbmx8k0xHD02jc8i2WWrBj5TDrw2ZrWMlwiptOj0UvE+iTza6kg9i1gmYdPE1bH2WkzxJTB11rNkQTADNhdl745QFM/gzAXycMjl1fnWlBbZ5Pfs58yozScGLM5Kd575pnKg8li1gD8mXjXaIrpfULGCd2fI61JTYYIi0Fazo2v3D1uA+o23k8S3lDa8K9zQ2e2lOfCgILt8TW0K6BHpH5NAx5Ffi3MV/JBHwcdwQ8l5IY4ogzX/S7wuaJCCWrkdO6NSwFciHr+RdP2HPPYVo5HBxDKeZkv2wZZ1hcepxjLB6+OEwKxGDMBs9ltb9CFalbNI9BqfA9gigbYIP2XqqfQtm4Xy7L3DDV/GTwtjezNiBDaqYBcmZUictFfP0A3MWglKxiDxZvN8Slie+z2vXGte1gxDaSGbUVZRbK4UCLdXgNcX+mxhYxmkLhbr7RPGO4XZ0fULIln/nApCd7gNJci0trAzCkRfFD0H4LC+X7yaxzD2AS69imBb4ehYWvyw/CL1zhMdG43F7PKVp5+E5MUikTeIE8jqUL1/bd3G/tC6+bPN59+nqhtCJYKVEzEVozC/Sy6rjmSupRl2yPqd6vNNmqs+NFT0Fc0SlsNo4HMmMzCMPaPWOLbvc7cv3rNUzAG/Tt4n39l7k/mKwincVRxCjEED2DxGK6p/8V24/IRedZhLkz8dKJrC/Z6pMuSainZ/mBZh5UYDKBDyXggTtgDJFO1azRwj4ISH5z5s4Xt9/I88IREepBKd2LbeHH1K0N9AqpPH6FjEAbAWHYbqMCgNjcq4TKjLFnQkseRTTzWZ9jE8ztpByxAA+grxW+W/tZaja9+sFcL7RlhJ0Da7XMP4Ib9f5Q7tgHOd9aIpVBQGncE9UaRbEx9Pj4Q45ygAVaQZ/WzIQHxFxrN8ODkWBXUVD0XPstlFSsfFsNeFd2FCttwprjywqF3WvhFmfaudpUebjqgogbVPtfxKzcylhMhIITl5I9NUIOWrqzUbmLARmdkGzS9AH3wGJu2wACXjcx9Jojf/kXhd13C8QbsawcUGpz94xOn4SKRiJJCQiLQ0uVSFGUQI0HimHz+M8iqjiDa/NX7VsfGkrZ74YEnhPDrz/2Cu1QtEyjtGQeWe0MeOaMf0Sl6eRnE6Venxe9H2YvC9ZyLKoHdW2/3wWyRVMhkJpKAgyqBGDtyhE2ChL/DL94XeqhhGyn9eFtb0Sij+GNtVnYfPMCk47ppBS/Qdgyffgdj+POsQ29Q0/BNW0zbmoBsqbuoqUhjrFv7Y2Oz+1sMByc8wwCrc5REYHMBw83uStm/AFPAdJmTAt2og9MDA0QRb+3q3sv3CwWUmIX0jH1uckm3AKWI2GWdm9I8KNgXlQJe2nrDSVruwUhIjyWCAz4ql1a2bBWLx/TFHCk7WLfGlU/UPtdOhNYepJMKOR/OlAoUzp9pSDTXh6FZkHJQPbo7EqZpO0/rKKLlJND26ZWnkCOUywoMLorcG/bQjW5JJw7mSWRvE9j8qo5pcsP7LskaWOlxkpT7OqsI80YTCJs889yqeltRraadOFjW4RMkl9sJbvg0ssz4pl+32RQ07TCLr+aLH6AZRe+QbnvUo9BQZLcHPPZ/80u+Zvz7+76KU+DdfmsXVKXND2zBDq3OK5hzCCbBw6STNEPakgLAADV/1p+nPaiIF0TIXxV/R/rdxkVqa21yOWDgXCx+dNt2OxUoaRm+1j7O/znDcpeo5qzEMxG/E99ORvsp3LzGSLv9IM/Vpxqb0DpEmND82/F6HwFrsDTOjbAAQGgnhXq2Ux5trS8l3mFKPAsnCzR5xQmT8DPiYAXDprGEq3RBrdN3ieLiLuLwEJIPI7uGAXk0PdqA331AuURjs62edfi2nQp5ZXd7YmBCBFtK+y3poQa5uEOSEG5lzqBY4/z0kBL7uEjnW4/qN6PjxuryfYKaxFRFV/MDHMV8me/xkAC2JpsEthcnRDjEpIoCVxhPXUGGXaP6cQgDNvsxrDCbAihVpSq5qbKIHec02kcUA5tC8Qo7yxNd3I5tUzL9buGjfGH7oW1yGctSsHmaNirmo/zOpmuVryCfG7i4ImFxGA/MaKh2vJBh/xdxc5xLq+2XcpQYjO0okoCQjgg3KgBT2xdu39A6Ch0Q7EdVdQGF3rQY4507MIWJioVF2yKWU33YpZScUFxORbz4lL6N0K38oj4Za4RnAJ13Ba6M72GZPdYo7MQ7R5S0zqU2Dwpx7DlWScn9qg3HAp7xPVLVVWL5iZInRsUp+YbSym9VjPPFT6sK8DKlPvphmogvLihcLtkcj2sUrk8+B66SHG++br2y2Ky3OAlHSppaNZuwb35I2sQ+6prvZXa/xHrhMkyjF0ioBVAFea+tak5bmZE1Qs6jo2gnPw8ka2U+hfbxyqBc+M8NR9s5yoSI1r/6LO094AnauCmePJ7PFAIPFp9SS8Ezw901yLo5s1seWhk/WG0el09CZGsKg/5ZkXAShKNSkBge+QKNoEQKQ8Qyi3GcHvWa0mUY2udUJtCDU3Nv3DtmSPSJ3LhERdIYr7kfoKxrDfxzrdfGC1pZpJXxtstF14NhnZJOmp2r261C8TBWgQ58l5zgM9EQNHo0W/s1agWLx5KraqIPvERDlxDU9CVWCEwGagKoz3WpPyAcd5QAF+uzX6GvomltNeOMCiJTZRgGEYPrXXVUCGRU8KupGF9hgdYxkjJ2rza2K24V8CIGyIkT0WSMlPCcI0MGlyILrQItj4F4wf17PFBIGtjlwitVPzs4aVTKWM3nKN+SMIkuGSKNElsqHULgCrZxBKq9pBrfhW7Dc+GIzJOoB1Xw1BuIGB4RHj6GNFqusUplVvjyWTgtxhLmIjdhd5VW6OB+tW2Uj9ixi9Eo7NsnCq+IeSxprw3IMKR6NVA4Obu9BSch4w82RzeMEE6K+KMffpZb0I31RiDqbBsZVC9KO7p8aqedD94ofVlNPm1Uya6dWThjd8QpjaM1+dtTS97ztY7e12Igx2AhG2zSFu6J/5SQ6EkvJbeBVWFMA+rPzxJgRTP8+RUlj5pe36+GfLFMcTFjs8Se9vg7FCUFFmm/q/Zp9FqDNGH1rggSOaN7FbXVRUC7zlHuuLExyYWeEyokKBzehO+DEDD2o6dkeXtEPalNQt64L9cJOnMh6TiQAbARf4dOIjqQ+6080ctzw/7JLlkQSvqv0ft9sxmNi6dgtLVPJ0N1UDfHVs8pws4dvb2kN2BcDDiU6lvgvspvo6skl92ejYou2AwDFYBImSCPhepfYJNJ8veASMjclNzNPZzcxTPpbRTo8CbCZW+F1eOYSUidFPIz3LXTVqHAYcZ4O3KrxvX33KCJUFuqMVbCoNxz1TrmTdLyo38uGcT1g/dO4Q5JV8DPSr3zIUDlTdC3G5STkJmSHXN+IB8vmXljYEalRsOUS7WFgq/rsExSnUfO7cgP+kKaMEPjxIRG+QJ5Sj+05TkFDH38OkhRF+a3rAaXKlFrP8kQr4SSqZByzqRAJ/wfksa71+RxBSCz0fbSKQxO1MPGgkUpptdWej6vYf71v+urQC8eogH0ld/OvpkC7cPMu42AbtmocibppSPJqn5fOczfpPXe0YdvmhJl61rYv9aKRQ5iDSK+dnnL0ZydI344btlgwNo2ZvgJ/ELQjG+ftcAWEkRqerBC3RKhmtNotPiNuJNSjA3x6sHtH0AnEZCv4JPC9O+Da4DrWInLTgkhz5dQRFwJIlyjKMiBcf5UlvXPfOCapRXPXPQCHVy+qnff4OQL/NQNSJlNxocpkav0olBDU20lkIK85cuhGZn3CToEwWJPFhOr7HOmemSE4WRXBXf4JzqAYdAfiiTdgqbXLC1PyaorxiAmeC5DH++Ih+Fz3uHLWrfdLR4Bkp8K4e3+ZxH5V2KtU2VVdE2u1GJgJM8uEyATAggMg6opPbGayw6hQByOEXIpnX3dZAhzX+rK1ptpqq8SmsjGxWzRGJc4lNxVBqFxf1gtXt3kemmKUd1+UfbE0a5VcxVGUg1p+7jTC47Vo6NdUvcqML5Ndk5N8EDZJdQgyGkVtDiM+ZtRm3fUln5IvkJpn+WZUjKfSHdF5KyELI3rQOi/vKyTVnbM+r2gUuIp+220qQfXLvJRjV0fGPDpwMBNcr7RC/ZdCNr/n/zYTVcQSqjWwVaP8evSJpWn7oYX8tPIVbZqo4YGEuqf/7yw6wlvLzcsHrmBV1J5+Me2DqumiR6w4uMcY1d8vJE3GwqGGBEXhzIWq5OTj+F6EjmUi1rTQ6p2fdl+VvYymA1OBZJHy3/J6athnXtbNJdh161Q0pKNtVKIdg8Cof0FkUgDeXV2DtpSLzItTL3n/BXXynt5L7y0XStourDEd7J1KsCFSFEDZMpK1a/ssviOowI7KmfwgGmxRMU/as+ydnR9FeKawdnP/Lzzn5Wn0dZSj+fYAaXrz0p4lcN3rJ7hMEbFdMVai3d8ODkfupTwrAbUSt/+TgjUSrpQXpfGN+n1Xfa7btmr1Er75LDGGakzysvxRFnQ1+GiROpkIsudNj7r+kLtj2ZSEJryDGMWYoiSB4jmj24+bSzTeWrRihpWc4P+cZxg+nuI3C824VDy29tqgSSXzmDhcnJbs1Nj7oRZipSdOBE7fFcxX8oyOZkSuvelsJ1PhAGwcfAJwyMkSRxVJT9VeFkEs88maTyIBLzpfW/gHt/ns6V6TwyxkaZ3U4iyEVVsODipsodV0mufa2Uckk88EwiXXvfcX9E11cXekogJYRZ+ZhL3pfoaAC7MvmBAyGsZTnlnhwLXT/hnaSg7deKa6JGwZi6orybsC9ni1AuL07/urJEhnl+REKhv47rykR/UrYYsVlAQ3L9kJvvnmH1lIKIt2tvAVHqkGsYax0Jel4izF9A5N42eNi7a70+uJ97q1yghoC2lNESWuJZ4lu6HQEIl/J4WaSMFEy26wOThZbKed4hBr3PkrZ2BV2s9HhCk4tHpB8O/XdRsWpJ+9LmOISMNJdd14cg5/NgjZ2FxVbkL538RIsv7iYnOZT/0NG6AVBApP+aCPkhAnkXUQt8Y4x0gbASAHqgrJZHJOcKuwoeuHRtwuOaFfxtfUb5TlPnm4nxXhYs5DsYpBwsLZBELEibzQMRtGVGOoAARd8CxoTPXVuzcpigO+iLibfT7tCoHEWCsiV9tiv3IPRzCWhMquIDnl1Uo+7kOIgWxTPMtvExHfLP6pd2GLW59oN7pRtEX2hAsvm71hy3Zmy7ib8+/KKPOM1hokSgG7Ex0lTdWNa1SrH9AQL5sYzE6F2xD4oqlJjFrpyk5dFm3FISpbBlpz+wN2JR1/TsLcWv+1GvzYcPxW0D7ivDMLNZ755Hd2GFZS0nP6lkK3e1S2Kcg68Y3xdwsaSx7wXoAeXZndQpyoLvJQvQ6EzUrgKZW4sUoeGbya52ApZNS61cpHtOr562PJInLmIZHQz5fh/pE43ibiaEdT3mwlVsm4/uTX/4UTj1vAtCMCbQIs4v2KOwBL6ZYpupkZnfXdrKomAEFKGSFfBGNyq3ftoyzCxaZjpIFHvQjisISOQrtJoOD95cgPOcYXSo/u4rUPYRHPUDOBbDEXR2ggReKixXsxxcK97wRYX5f/6Cs43Ecx3co76ot9MqvLtplHljJ+Ympk4ZbIhANUR+bNe2BqnemLSinK8HKUfWt57oQzkae4/Zb3tUt/VniA+eS7qiXHJBdoIEIMH9a2PfFCIes2VovPXI1OH3jzfy8pX4JYPoob7NZ/QeYAGCPiLdrbnqkXbrxwo5nY8lvmu+waQfMdha1TepcQf2Yhs/dDSOZqUL9e1GPKgRQi6FNTZuaaIA1A7KueljaibYRjhEQnPaOUEl7gJHOc7suXJ8jvX9+GzpOLOdtehDoxlztwQcjoZlRby03UG3JNLw/AE9hO4vqjgRnca82TzD6UqmUZJVFSYu3frkcvEcTPoseyIlfmZrsqmW6lIuU4E0FnkE7PbL0HkyxuiwPRmSiIVh0beiICJuuJmLpiDThpDSB5Ft1WnlfFKYvPafM6GrkhQ7x/YM3ejzP+ZwRXX5kUP+WNZhmah4pBmHq8Lj0BdJsbH4l8XNjgzXvjrCbyArc84WG0NJMhGFFwU1nNrIjJNI8yP8dV4S0BH3yCDbuuKhF8kpJ2cQEeCLNHoWTM5bZvW3Xkk1qj4x3W+uHNuRbaj0G2as/YkockcAZKUUynW/IpOuJU+Z6BFkMCi7pnXRKitJSMui2SZucpiDq/3YGmMUmOcvRe6OTnZ7DutjMHdwd+K0jd0r8ugmleGSBIUi+JF1vKMG3kkdorbwLlbqEs+X0lsRkJmVoR53EAD2ZDcoYXRAp2UDlpbHTnyT6yNU6tIwAFP4Dp8VmLYMt/kF74srC/tbheQR+CxwzWeXqx7lDu1rRvTgupHu4zuxTJiDiQvcsb31WfZ9WZURVBsWav6fezud5JtgDNvl4cTmq0xbefgicXCyPZgfjw6Joa3HhYO0sxTYrYa2w4FW9iCrvzqvcHLV41sleDAEWLYNaxiFokmF0wv6PzMBQTtabUMyF+f4ukXR4viSj8pjLzgoB9eiwH5PozsJEDWzPSxoFolgR1lpMP7VzDsEbtEhJuH0MIwzk8umMObSez6rb6xBddLkU1EBIT8/jZIJ0ZBUjjC5oaHbQRsjzaFmfQtM9CO1t3Nl5B/wnRZEINoZV0aHw0FFHY0B1XKnRS+LFsHzcuHB7UWBQ8Gr2z8JLWFGilN9osa5hRvpOBDpiSKmQAAzflXPKARsorQbw7kxhVUa99vQAb3wxQYakeo2dl219LBlfyrU6vkX5DyzCtq6MstyXfd1g2ligPGdeSewLmWGpm2EujV4Hic3l66/oVQmuq/INKsLw8cro+GW8sq2UsFnB4qlsPF8jaall5W93VkzYhP53pYX8KMR2sH45CU1+RgZ32jAk/L5nX/NxinxN0V+8cvUd3EoU1B1mrZazblaG0hrSE+5Ak90adCy+2Jc/ATqHTx/no0VSEyHe1JIdEDlAgq6Mpbb1RRqdtKBVAloA2BniUK001Bj6EH51S9NNDKnIIIfx/z3bUUTgm84AlrEn03msRfA3duvqou3be0NbT+Pz16F8lEH3iNAnfBJVnfOm/hM2/uWYH/gbHPyldXgH7Rq9qQMuMnoiKHP8Z0ZkUALuuWKXiSQcqp81lb2PlKWWno/PlxthEDYUrGlKo8UdWhSRwAqu3VRwDanktJAyoJX29veW1OrWpToAZDB4x8Ke4t+Q4l/WBW/pnF9pmg8ix3PxphYG3AxMCBSQwaBXIGMFCSUBu1rSD9k6pTgQsPpDfX3gpkg+784Ob2LnM8wcYgW7VGHfseXyOrrmet1pMqJiN3OQZE1mRjr2SZrhtQbFaVw7stGTwnAEv/hQ6rtcautfAKpytl4XG4k6Vy8+gtH3d8eezEL1l3WoJUxMfuo/ddfAcdewVXWG1ABqbiT984/OzQpV7vTDxhY3CwRQaA3lSL65kt4FZC3iSJapXwhlzg8E75mVpg526RgAWgDl3EgvyvaGyYgPOPBXf31VAOs2Sd6yyDcaqDvksfXABkUZ2BXgykpYOjb0hJR695lHs4cSj9ZCVZ7B0ijK+B5eVRAbpmqnDd/qsMEefcSroGacy9o3pmfIvy7XCQnAZwZUS4zFXsbL6nw2ImjBDB0qjfHOfgG2yBGEGY7Q2Q6lNT9ODWx+Zqeh9Vk8sDekxSoaNmzwkqc2ev5acoL705YQmQE93/4OlJQFc0jZRzLnCuk29qOpg1g9B07tmHhvxv/fi4yJmOiU7mdUfZq5//DY92j+axLdcU32N5bciu3eK9/cme68PBUmrpRsgw7Qp/CsV/6yQV/YT/TyA6pdVL2mVDyGlei+vJXo39z91qjBllqDHDmY0oQhp1JY/U7fhbD00PfCNAf1uSfFAioHS7kmfKmo8xBzvewXoM+byJ+CTR8XAY+A63cwwzr/K5oaRuXUDksWSghfO+oJ0Nuvn0vGwIBQK3LGS98DnyRiwCN9kXdc6OS1veUhrpDoiKN5nOcBlyGJEI8lhQN20P/4lz+HpZTZuq71pAuNUuJnxRoxJRaSPwbBMYkq8eTDO/d/P2zadro0ufl1Z/xjw58nsM/t145zS+NHaTJv4gF/tHlws9K5Ym6s3efJBAZRuXunrcFayJVyQ/5zsIcGC6L3ox95/4J5B2LKspYthduJ/UN2aLuz1qCFSrHhp0Rz/qhNgK9wukJHUiGscRuaib4B09djJsiFSlwkBAj10niRqGKL5g8X50+oLPKyNnhpDyYbUan2wEDtGFNNu5lq0Msh4Ly+Y2eEa0PhqKdW3AOzGr1lasadNJFFH7EWagJhVCkZQXyPeI64nXPi5Mr9GgpH3SmzP4+SPasqH4JdfwN+5a4zkJJUSO/XuDmxpu79ugx1ufIwmW5xbOjAR/UuGyjmVoNdTP34jhCvP6TL4ym06ExDCofeNIF6d06Md1fPhzLjA/MZ8nE0tkK9/Vh1DmpRKSag8OFe7DL7sAhK/xLcREvmrtfuRzA+S5NbWImrV1wCEh4xC/Gfil589qKouXis5ikdW+HZjEfaSun0E6Y5JGYKQZRjnoLl84foNyxSuOIWAiypaz7gFMowJ2sK6/Ie2DoUH1qjJ5JvlWLqQpnx/5kKJBxxqAXeg/E6xO0PLdpGZ3vF/NB5UX8gFLozYQts8Yu5Vu5UG+TwZW6KnB3r7/Ek3Otzuj/imT+w5wbKYMFsxlqUUoXDPmvyyq0g+6qCCnQwwqz+LMqykqZrYdEYKioZ00RLJJjA3XHLtcBe62fv3K1EkyuYQAtApuC1jJkjC6F5J5nJYTqrZb4gyukf7/MN3s5qG/UjkS1K8RLEc8Ek8y1WlwsN5J4fBtLe08E9wW8lQ3Q7AqwXxroIINHi4F1xGXcr9vBKJqJkvocHxSTcnaYC7gp27ol7v0AucFgxWknlc2Ss+zQ+5vgqcU7odIrDcpqUHIASCsv3jOsNAnL6KADMZIf9Fcuh/Lxtczf4IE88t+p0m7/428IvY0eguYGXqWzMUdONVG3xPgVtc53hy7T6iakrFEoyjZC7FjcrAcZbUIyDdAFscpS3MaE0IvI/53RZX5XKAXzZtYHDzOKiArcfqw7XjTN7uQpZJj0v203nSf/wvrZrol2F+ZsNp3DbUf4Fd4SUduPFuYVHeHGTm2IfKJs5ulGpxaCnBY7NtYBsK6qtpOd9WJrm+5L4ToR9T8lMc+vUkPb4hwjYPLxRsASQ/hdSRKjiIgOnhnObYc5gXKmf2hRWqcESZ/rmVFCgI119wq5tbEPgookNGL5rmp0YrMCmYPUgCOMlcl13+nUiM7Cok42qceN+iHXjzZ3Eti17DTEfZssziHCFNLydYS0gLyWbTqd6xU8iOP8fYn4PmeOpotsHhwCrLwryvMGSCvWs8h+9n7wB2DN3wPX5hqf77sWdBR1ilL77du5UqtvHSC72Fy6Yd0P5F0w9b2+8bB0ZcZFUiFyKrK0df9WeNIZFs5sJHTABGsG0rNxkNFocDhlYp2ipYQAYSzgpNP6fkMbnrZox5C8jw5j9oaVEHnH4E70YwZsJWFZNO61uExc1h0yr/LnF5LvrKrUYqE6gktJpsdslwTrE6+lHhwv6J8eM6n5pKAUnRhxRvz/LvJWUkYa25lraY2LL2xbkN7ZgNzloNYcxdrMOFmk6wJLaVLtGzkc0uBj1bzENuDdantqCaW03DLF9ZnoZwLiUioVX5Tmrw216ZHQPjEVUZ2oK73YOeaK6JUWUWteuJn0Jn06WSBve2RpipgycujJHoROHU7YxnITruJFNeuidlH29sbsTjxVYtPuj5wi8SZLa7KL12FKxs51p0sqWLGDWkux508L1ZRAhKfbnpCTmns+c4X52FkRMhnL9A19dlRITlzsoFxFdjG/WjJ+1xoNswFqpMIdhaaB4IkH9Gq5k2a5fLPKRAsMI7+6Yw170wUwZmcfa0GFI9FSyzE0i1yTDjwAWRIk91HrczfX95oWagqFzESXiOWxJ5AK3n27DvoM75RPf4syCEE6t3s6A2AGJnYE+4ONdFUvuPwP8B3dCQeEqli7BeZdEymePSl0ZMJIuXfx2pOJMuQ6LI/0+T/wEPHAkK798rfoLplMIJd1qOtNpr3xGOt9AeC0HvEmIQI1RYU5iT3zmD2Wiku3HRFax+cMXMZ6+RGacBCaRBhR0SF5BLXIJHmYExpBRmcX8XTQMEaCtX8iMxn8iBVm41vI8Kb9iu+dwgFwFWxfvSqKV1GXdTzxw2bitg78j76H/JZovDPfegaqzlep9t6nPhRuc2mIdQ4MZFV7dYxDylOoMfOKA/GdVy/8ehin27+6ZM3gZ2gbuDHM5cEejbHLu22SFL89Iqt6pSlZ8KdPK9hlb1xuj251z8JetI5L1Np04Tuf3oWv/vZdESgIoZ0fCQqMqT4ok2qD3B2Pe3Ee4P3I3sRWD/Fh6KkZ1ibTqf5+S/NYpufY07NKrLVPOZtH39FhfEyfpLaYVLBHq2S+XLyyXytV6vKyeHfvkXvDNLXOQHOGE3O6Xd/w55KinyMXyOY4i4LlY6yMo/8GquXF2urlPApf97ItEn8KwWI9kicdWmGaV406jKGvNd2Yw7wpgJDhzMnieq33NbVkmAcrP2eDjV7JdMQ0b+0JjR4bl5dvaALKc4v4t0HsGI+Maq0MpvGDaRH1HnH8RMiOfivMkHdPSLxinq+b5/XGrbW7VwyDQZhbyY6xh8jO+0tNQFMFeH0myQsqphBlbR2+3Tl7hSBX3GQL7tHHLYnImUIBxgeMWZoQ62Y7yhSXRHy4rmuwZJNQY1CFoJOELcO1rQK1gIOgXej9shIQmVh2nSwRyjtEy/HlnR9n5lJRW17eqoroDvE1LndpSgOUpG5J+wqNMSHGwoiLvcmF9kfYNHbHJ+9QhaK3KncFJCcsQqj1MnfUK1FGXh5eiHT8rDsUXcqNqvoXv8l2RIWBOxwVfAAJPLEuT/1IwIO4Q2gc0TLp9XocWmzNmFKbSMSkTdPmppPmyl+UDBnYJboi3fl8Xcj+HvisCJ2oRTIt0I7BfKTbBpz85P1MJ9R9V+bSWJYdWLOf6GPcEu8ydZBe/IY0XV7huBzMSBM1axcFSCiypmecEWovU9frbntvEU+JTR4cx/+hqp9uA59Yw5BTEFOF2BXVXZJVSjcBClJXuvqd18L93KPYnJ/0LX/l/H5UgKMopKynCqXq7VWSRnjrh1IB64QnZZf9IQonlE78kKkSHNNs/HATy9XyicndyhG6sX/hIh8xHCKDOaSyNDuIPA3oDqa3zOBamLrHuJ0ZZcEOE6ZHtYVw4C7liUWItP3xb71uaded5XgF6olZnDrvstgiMrcUdjAdBDf5dLTq02vG9vTcfebHkwQ3hk5D3qDkx3LjFt/p7m+ApAK5cvSSFNC23iWWq7McuJkSPS9/UjdxZWRCcCQi7pVJQ1hFCGd5tAIc/qFAFMQQcY6eTUm7TpAnw6waLlYaU2O685qMArPXtZQR9o2c2DrIWXHDyOVzvLFEUgebLawV8xLEwQAHnfM01uFB92oNyZkmdC3vGW7PEMVeEXk0WYZMQFiuGI+Dcnq2KtCFJb4jOFhePX5nFUEIPWbhRMMi70nnENo0L4h6hTsJZqywNrlfEt94p6zWYsnIoPt3DU5IyrOSfteeNBXoal//1U+tHdjGbdDawXye8TLxu/A1WPqAHdg/Xj7bXDuHPIPMWPS8yF2nyXp3X6EcvaZlnzQc/05g0z0xx38dlYJ9ZhuEvFQH6s1HE3MoQArxQ5ise0BtNyIXf0H/pfM2Fl6tKMutpTPJsfaK+1sMcCegOKdn5DMapIsoilV+Sw6jnEBHeBXaSb0IN/xGvR2vE/ovm/GI6aa7FZHJH5j4WCnElit3IEvJ6iA2SLP/kWgwT2s4TtEN37hnEzgduqOaXRHP/svkcLhGPOkWO/mZW1ZZGUebuQmRL3INTEQVpOMy0Lz6FLGwvFpM40WktIG7ARThyj2V2tiKWSbwF7N8xhQ6A7u54UM0K/qGadBmnxurP7kMhH/q/BZdWK36yJxv6i6DphZ2YCuruEQ489235U55/5UYj4nvrA8JLrrrSO6pmT0xRC7saTZs7ejupWhlqUjdwINvYBeFRHgIXg0MBOXsUcZWqVj9u9k7XXhJaXHPwTmmPoXltUf7bvl3qIH8s+Pie/sTQzh1Y9xp2qclPw14HGUJtkERwz8W72AQ95aIQcbYy3LPTewufkP2DMAHbb0w3Agm9UESY+26hFRLC27zVgFdZasAFVaIER88Gz5goWjqkDqIrkD5R5+6RUyngKXhynNCiiF7CzHxtu6jIGOWfUzTy7cECIG4xSlNM8Vk5VrenOSQHWxz+QTAomSjFORmkfmm8kQyIu7JvbLgJ/ORXegT0bGDixXk5CpzvfCNGPIOnzssz2wlHxDecCn9zHkt64v5Cfp0dju4RBsF0DBAcK9G/iLOHFVWCNgVMLYpdR4ZX2SxrD0HbZg6dUMgEO2XolX4qyoQ3gS+u61PXxRaoPdtgWxokqCcqg5y0YzXut0fZ3em+1/j4jhDSPJCd/tSFDjrt+htMeffrWCscljUKVRf+MxArKzd6aKrxZWqRPpjJSHu7FmZrpqGKB5kCtqv08qq8Z1bcbKo1zfYMzfxp9GICrp4PpRmCZ/wtSf2vFiiiSdQEf3szQ3rNNjoMGgzxz/L7VyfhHaSFkJ1Rp+LrsJOgqeoycW1DKIAUenxcExdpVGGUJ/5drS/CKZO3j0zdxSBPyUG6/1mjp1ipyLheIqMkYFK6l5vptIwdMHeYzJaFz9HaPcu31IzFYITdNY3yW1tZW8DnQLwJ0ekBHUFu+6p3ckL6OQ6a11VR9XIGmu+CIRDzBZdeRIT9aFUe2iWsMbHmikyy4gjs9oqBvWiAaOyyF+yglM2QHYOtNStxM/2Qa8MRv/WEletEh4/YgKDab1JViXx73GVphgqjtAM0ui73f+rKqq076B/U476zfvy6TDPW5S3iSeagVXDpAWJdyYTr+UWTCrXhzSsHOObSvRig4U/ZBfsvtyFOnuOqRbXmNkDRtRzQrBQKFPfLCihI8o+WrUEicRJdFS/agoByEQsNkMbgmmcQjlNtKRGnC3HapF+TFOqzs5Gb099w/fMGQdfL2yRocy+i1Zc2A3OwODIUDfis7vOAhdb1vvNQiBjkH7EajCX5JaaCll/RYpeRllGtDbbQGAi2/WHCHM7hhVDof4D2zB11e8U9+Yz+VMVvwFHbPLOnXk79Dz7NmNKmiFxam3Nppm4g5lI2bni50qutgHTCHH49ZJ0VTI5G+LQ0Hcp3lYusGLEeXWScXEKLnJfcRcTXe/YOcggKTHrjawcAbwujb/5sRv3sbnSPFD0z6otHQGK1nxHACEjjAnSnjluQw5eD7wumwjoV8rZHe/ZmlglpLKpmnD3YPWroGl1RiYf/+3jq/bZOEzc7+LafJASvaRiPWWL1jmEQKMyHasYu9XMvcqdmtLYGRdtMmaBnJDdpp+0cQ4Wnm7UJSNwPRB1GjquAQ2dSMi3gYiWfRn9C6fyt/RLbkDTSJyYXwHOI7BSzZoS0NfsjsOtk2bJrFspf5RRrHO/8qa6t/892fGqWmDxTFD5XhAuxCImYAbvAqQj3AMmrZXrBzyVOVAyDTnoFoIrEHmBng1U24A9Rv4Cz2AR9G6GDbkL6Eof2Gru3dg2Ve3VmlykL30pIfDGvIZXfewYHrUUdMiVHYsGXL/KMNGqK8r7VQir6k6QJPKpEYO8k0t3PJ3aglsDtGuh+CqvNm9ESModxUJXRtP3e4DJfkiWVIBwQNNo5Dm/g8e5eV6CEsx2o++F1dAdZUwX2e7YmwjAuURlQyZcyOLWguFMMp64M/zFKNGT5tPcbwcV5FcQdcnvpV0w7DAI2coVhgHKpHhKMS/qa3zHIhgnckwEXmPAsFbyODy118p8cl8W0SjgR8V5TFvlRO1sxBebghdKpcxtT+DrGWoDaZ9SJ4w8ayGDkIDTDDgbzj7HLWcrEBdpcWEfdQqlPKhuO26jOFcTRYcIuJh+R4DEIaCTdY7Wqd0x3Vqi1SHeoXorxT7nuWPK6FGoACHxEW70XJq/uaPr7yIupnTmr7XP2XeGira9ocgopaKruUiMlUUmb+H7CTjBPxgfWTI8aen4NWSch4EiiIN7AD+GyXYIOHn+oz1kZc8W1KWFZttxH6NR3RQmWAWqN9K2H9aWtdCkbMGTbw3uNtYU9PEAr/OIyEuM/Wo46+Fk5/5gNd8wLQ0wWWiDSAA9xbHJgnyX5PMHAWMo7JeYRUDzohNewK4ZbQZ5h4YM8bnS3TuXYLcbnpTBwTzlWHUQVQ1T9Hnsn5Y57pUAPyg69XoybSszGPy6/ASyKgZaUXgQIbRtX0MHTdvolbMkv54bBIX/EukMg2OujKNMiXbA3hCcfpm+YzLm8qQwxK49fgSwPvC00XpttvqxXWUujWDVxY7IoXAHrZBkfHLNixfjT7/Iln3+EF1qTbwKY/CQ+SjyLBddAVHq68TrSTaXpxYmUbp+KDbgIGBKMTONYlVjwtNrcgnxUGjdulDWvE2PMuL4Wq37o2GEBH0vK1F2IKInYo3NkTueY/N9xq3scnv8NAHO0tZNXT/0zpMXajhwUaDEtATsm63wezHb/FdbDKaumhv72z5qYvZYPALtCFzHXlFRJDpjrXvyUI189Lx28dTAwJ1MrrVTna2YZz1GVpkKC4+tRBav5a0wAoJFYRAbDfxq/LkuL5JLAnGCd60Knkz8rhzvKNwcnG4eujZ5kXgwP3UmZdT7e/xDN7pRP1bexyHVc5kRiCWMp33zH085FsHoQFSf2wEMibDdXWekxL4UR74ISlLv/VSv8tpn5geXUSKKXkh4YnWSncShl1sZXZ9zJoj+os35IEOexhsA+sPYMgpIibmirNTOY8n8RSQqgFa6a/wYnSXddKOjUaYchDkAP+3vkF7HVYbegjh+3uo3z4Ej1HpkuX2Osh8hHaKgft3PQjMazAKgyjsD3jd5pyja1FImpv6RLDaMTt72k3rASA9oWRrqV4SynXLK9X8rkCushCB8DYbYRJuHylVW1TASfkOGSbeiABtdtOhx/uzEMbcX5GbmfvHWto5s1U0cYFsVYIfTxVJJmcWeWtTFJIAZtX3tdvPM7sPF8YeBsY0RetM+HaJaicEHKd4SH85yguqo+5rEJAmtngpBL3bxSM9gkEYuz3+hZy6Ar95/IYo8roEsw0v5fXPGC+Ac/sveXhlQ9KdE8Af0teMqyJqhkGnNNYo2+13ufk6MX0vmAeM+fm5yMpAZCSBRyIquhMn0dZ/gAxGsutkBf6Ehdl6BBGcHH56uOWWchvKis49VO1O8np0XxwmJJiRbxeq0VmkHwAnLOgqH3QLs21JTN4VeFTHsE99jYojUF7BwSWwt2pvPbnMlaja1pv8X7KuP4IH9eHNDXZZQnB9qr9cy5l3Z9TPbkvjWMUbOWLDaVOmvAHvhgjkLh4FcERe8U/fXI2SNOb3gmTPXaZiJsV+1MqjnbWKoTJ1yPNa9Ug6+RnFYfK4CEGihhT2fU2VAaRlOhEA37Q5m7Oz68e6OiaWQ9i/Vor506OA+lFgbbq3O4/T0M7Rk4LWcvnQT8hddptyv/3BmRpmUuozDZS98pe5CxH4uffazWRvw+hE8Mxp8jj4ik3BARvh0z649Dx+hjh6+54w1zjsTf9589mZg7GJhSfFILgeP/vdorDnB+KeuqD/RvcaXZq41IDMJumXtj62/L0TK0XYOyYEvCUrf0RfHmqseZuvRoq8kOkML87tmmfV9Atdyvd/W8zkZjJUEq5WMxtBLsbXDXwU5rChEIMjJL234IxjludXmqSMrMpzyKffUDd+4cPCuxL3qynenbIF5awcx0Co+9qJbNbSeGhDNbbh7e+bEsB82J5FELWhT4uccH3vB8HsmRqqWnIzIjozyZkNo/czo+rRCeA6W5aimOvxyOOFD2eGGecnvZvrI8rSBBp+Y9/v3kllfQ8w4C3oPaOiMxoOnjQ6YaKpRr37GQILldyfCqvOZJOBRHx0HDUtON1V2uHAmwjtmvVGn3vCevOiDsa18psj40RI1YUXpab8UptKfbSPEaFhRdIx1cyrWSQ78FgFokPh+HlhnQX8mCslYRhFeCVeuHo841hUFBkDZSai4bwYaqLvP2t2gxQ1SnbnerKx38WXRNKmEFlskLYRlV+jVVMbONRi0OF4BB0qJRWM3LEMSs3IuXcMP7a0jgLTwszZO16Bd7vClIUl6RTNoHzz3nwJTdxsTiURV/Irp4TaiPFuTNGhlSVjO5o4nbsxyBAZv8G4NbfdX3b0EU/0vnLicRO97Q5FBSAtpdIOuunlGK5//Gt5TqXu6B14ocIC4MM6e22fgdR48mH8qk4nGniSXnO2I7yH0gI6DWKaCeJM3PELCPfOF7wYvU2ViGc8uq6fWs3T3puL8gwQoNcPvuvIE6/oFa/y9Yq0Axt2HtEi6RH0+x9cCvm7RvMUpzFIh9mzz48SEyvSs6ZwyRlSLJyj1ru99YmyrOUHZ5AANlx0wc041GoLhTxMXGdenQztlriUZ17belU5DGIfeW/vOvKbL4zVFODhhGKgpI71tTLzQKDXEakaNn9AsL64fC12JpuWVHwGQIcqExw1ri+65TcDeXKjT3wYZyuEm34T8/V4iiDVeQ1b3xBLQFTHv5oyb3K0xgRCVXGPVjgF7YJRk08lEh8XNIHFzL3CBt+YjIyDQf7DP47Z2VQfOFrMM7BtBowqJC++Sk15vnDktGgIvVme08vTyHZeRi1O/t1dsiuEQKCeAb+OSw4v9DZAXu5SIhI2MvUcbDY3lP3GLH6j6j9WzQ2+VMCfNWCvVovEXryY/z0UCQJ9cWLVv5hSFB0EIg2QUIWOW2UD1LlCRcyjc6OawXuRSVe+H5Xv4lGxdg0wo3Gz3KNgIUYPJBy2+OYOrR/9Q8cTIN6qFDqV401OFMuOqZ9v0YsU6hE9tGXwPDN77X8q+6d77nQjWXePOpnKJzjcT9r/C+j0u2I27gljp0EZNz7uFS3iKrTGivrSDpiS/QYGmZPEHJL68ZUyXsPzxClTBLzrNEDkU7R2ejmZNAhitQ+Tza17SiyT24UcfBNb3G/LqaG0OhLkfwmAYf/k2xXAD4OFXyxoOFPQhRdLr+n++JNV+NmsSkUaan4JTfzMReh1xcvZfqkOFYw5s4DTNmVl2Ih5O8qxqKlC7L6F6ttQranM4P1N5Tv+4WFw7kPxRTmrkehhF9p79y5+QgeGqcmNeGjiYkk0EsZE2PA++1Z8eg2g0QlL0+gluJ04PmzSouhKpjwv5suBU1bQBVQtLhsPLZS05b0bPc5d3NmJ7G/BGXi9UL5OUgsk1cpQ0a/nTHacO2jvfSOX6PbEnqyfhuciIAM/tFZqD+Ow82brLN+zhiyrKRxA35Epj+D+VyVXoe4KD3NwpvVC4wGInw7FYSfTFH895qPl1K33Dn060pkwnGafoIgLsVH7VPMBOyEDqUf8sz+wEpSfRFXyQCHQ9rVp2Npw6jMspu+kENKXkYmkZOZutkxo2LyuokvGuanj2UKxBhsZkO6A8LBZ6Fbk8B50+g2hNJi7znG6s7jvi9MvZXHdCf+KJreOnBgvK1kEqcjcI47sSp4TMw/F2969o9ut9K9C9PDyAJun68Ns+gcIInQGBkZwrbmrPuAZsYRg672ua36KqEhfjBVEXRVgG6ID+55Lq+lcHCb//jV9z9Y5Ew0TuT/kWUKQl1Nmj+KNoNisxtZIqFumK67AS5cCPkTdkcK49okcW4knVD51Z3K23jhTRP1JLuVDabozqtwnZEtStzbZR8Qts/kNyi3kf//eJUqscDqBeIlFzERYUTGh7Dww7UtfIO6pnI+N+z1UVbdJZTJYQd0T3E49UithTQpVASGOQAy8MjJQhGTd7M8fDUzKtEztV1Yet/rM4vRfE+yotU0xvlBZhYEer++IBC/jMFsR6SiF/op3s6fIF+iAACHfHkt1iBKotg+nYCNuWUtB7Q3JnP1r426QUZxIjfKhRiKoxXYFhldLQLDMLTias2l4JxHY9vhZkgVuKjNoZ6hRzotXQUUuA/6QUDy3sg22O064uYrNWH/Qqf/Y1bxbE+PJCVothDNge1RTJf/nAytnOEpqYj956/7rXbo3yc/N1gDvUhuAa6z0fLT7pOiP9cD0T31oBI679Yn7uV8TYZQlU+GnVM6JrKEeqoWAZQ3gOpMvosnISL3BhZcQHxft+1/HkKcNNynJgxnvurCwRHsLts2J9DchqKNbhHBt92AQr37K9MY+G3Ltv/IAT/giR7Dm9vypZDWYWcQRHJyUs5mQyC02vOOSlLYqrM4VNJnjPQ1b0SgRIUT+yD09rpeH0/YG+oq+wATfsSfY7dcyyoDuvEKI9Eb/lX5gMpm15CtNtxRvl+4DKFFS8+TdHwgSVKP9XPKHB0kUrIrNbxybOyVokyMW0liT8M+M4cy/4I2f6kreHL8R9vDI2++kJMW0hUxqTLyZ1VlGxqhlv5HFoE7JjBt7ZiDlBvPwEaGhftrW12xgi1xrvFPhbWgeUmZvemadztcMTV1X/W3EwwweB0K+kdb4XX/E8YD216EcnExkT1wbXUNkEHGuIFGgYyQwp0l+LWxcNrkXfVxF26dVJnR4jdqVyxRGuoQu6UbDRg8rIObAcGzUrlVNwPssp/7r/jx2DpMID7naoMJNSf+9+mGA0vEaBJqS1jADT3yJH7f4m2Sv+t3Y6CzpZw4ffaxxXsBQn9FRChLwvtyFzrTJorlv4V9SczKjZm/RnL/z7vpPvMT0vFsKRi19uz/n12cYE4NwEdNSlchQPYEj6kMGC8KeCfalbrtfMXFpbY873an1oN3RY4yaKEWx+z2Vdm8hjpbas43M1C8ltehOiNcYVOAmCL+u4yQsRfz0hQhDGmQf6v54ic91juA5L9EAFTJOm1QpbC+DcL8SJtcs8EIo2eOd7sThn+CoX7xQgmIv+Fmpc2ZR/yy73+I7cdTydCOIr08OTJ2vj7qA3uHoOvrvxx6Ae4D82BtS3c/HvKwb6OKlR9xRBGpGZqjlQZXD4POfQWus/9OvZOEOLAFDxsAtKN5KPKSYr+7v6n6UY2oKQXXnGfxLbwH8HXglbPpj5V59ITSkkG83fWKJDdOq24Bx6ooYm48vsFV9Iy1PNCCZLO+eDpfNgvVLaBd9sgaWCWp2x9WkwYCDIc/tUqcU7KDPaLGTIqezSuqBvw6Bgv4F7ScmTjJUyNIkZk3SmtTSLhBA1lv51xm5ID3TcocbzSas0OgIHiP2ROXzvEJExBoN4oceOmhicTRXZJ1P08hzLXZG4oP7BpuoSx6pL3XxeKdHjtOEGAYlvdgpuQrIh4C7KX44ir6jPkjTfjVIOZU2G0ZEH7cMgS514penDxish6R+51oAcYx8MwV/LgnI3ukB02tmK8SZe08LHvUKCwXvpqquC9m/OgldJxJAsAawqwdsEa2JTAogYIG4lF+VwtVtMGtOu/W2fVajVr1RjJpFVH0ByoB55jTaSsEjK9izZX6HLFD6Z+agvb1AJ12K5CZeoJ0eqrbboP4BxUKMzKIRceayL46RWKOmnK0wdaP63MVcxvZkaGfqTd4no773UQzfO5Pt7ejeUmdttcHXjjlVD+VmiAGWR5g8XEqtd03p4q/TE96FeTRPlJD0V6s3Cx0YsrxfVRPy3YyHwrDzqJqS1PySD9byWNhZR84g7nk6jr2mnArv1IAGsWUGwiMWeBbGW0fcFqxKrb2bcjlK1gjqMYBYWQI+OJ6xDKKLYs/BYPfJEKLAvhF+SzEwMFfM1IdTl2BTFdmFuH///jgq8xT7Z60QBWHR+hhSacBfGEYnITatRutXBXVnuyywWvjOPfZaT6WhiSVWN8BcL+C25MdhL1buB7XxSkc4sPMSHRmsN9Q743E3STzoAlQGRQm4lz2/ewmU++Q+VnyQfJhx6B6O3x8aDU7pXdxpHYEcpQ+aorSUmJPiZwyg/otwcaFpcXNA2EN3JrOyU0iEQ/R8yP7dEqjmayEPmCMTwqblebDLNwOObBVRgweH6QF3TiFnxZ4SfeQjYnV/JK8zJuHdP0LBPfxq6hfl87A5I4Gg9uRNbT/GrcMo9xoMZcR38rDWyj9DcrqHAoHRZZXQCIlZQMu3l3+Wtzuq9g+/s3tQDSee7MrQLtQmNMyfnjI9tf5xs3VPhc3aN6gbFtyXvK0gk3+7nAfR3mkR4wtezXq1dDbkVvKajEcshPRHZJ89b2zDJ+Na2IZcbHNnr3l4PwqvS+n6NSTnIDKHZBXRKAzoXe9lCPpZTa2pS/LxZ6rKT7N/Fcgpcwl1pL97PWzUwXP/ZeYNY1PdWcxd22wWQ5WQbMuqpgV9G7Nq326EqK8AVyMxDmY+nPZanBDrYbklA0veRnOZ5lgKzHZ4llcHToED3h8/elkGf1BfXNraJOf7t67j3g9CHD7A9jpXasrHwcDcTzr6L7UeXPUhl2kMnfAfZ7xGXIrhZfnBjyYBq4m0OYLp419AFm8AzAsjwKrpUkqyvWrFRSqDxSYHaJ08RmXDzSWUN7eHp6V/9VRi+2cPP01RmoHD6izcf9fWS9WfCv9Niq2fQ66vbdHSH1FZnnvcEKx+RNwFYZw+oHVGVbVRpPioW9zK02MoytWTtaxZaJ75HQrq+4wc8BAszS840NviztYJ+ROuVdDTgqwP6Wtmzm4vNZYlWZbAqYQdUQ2e05cZQWqgoJJ+HVnX03yLGv1ft/rz3DjJaF9yVy5q18KLalwU8WN2DK9JS1kiFnk6A4Dv9mclPPLgV3hmFhCUsV9g2N/uWFTTnVsTjJCVEpSSDmsveo6eEpnIyRxbmSIejxuqde1/1CzzH/baWtTdIqTWpANw3N32XAyZzRYPGYF1z1SRVl/23D2nsu4FvI7tdpaoalI4iZCgGunGoiNLguPQofKZtEf8jA/g/Mw27ppS9OEGf2a7dn6RM4JBJh1uMhH3sj+Z4ncxThbq1f32NRupsUoER+edkpe8Cvye7ENknlmfbuuI4DNRXHY/8x9gZw732uDuiXhrZ1dOhex+GZIPMU8A5ekWHG568RjD/vmyBL/7HwamrCCtlO+eNyNtqeUfSeQJOrRwepFhOtBnCHdDc4hzuGfPV/gNiHJ4arLhWtPSLQlM9BYVu515zZN85f2Mrn0HNuTUA/pXxIUDYK2APNZC/8S96qm60+W7TEH+r6q+Pwy5g3w51gTSg6/cI2TbMovzQz1zgX6lqDAPs9YfBzpnzDfVZfJbNGTxvpo4cxpYmEEvf+gjbWHb5dqxfc3O361EPJehXReeJNt8y9V3VUtdkdtxOq3j543I7jbAR+JY1t03+yb0pLLuDjjo2L7uiHUp28jKFlVTO3GC/onDIXbzB1S1RQRUHJ7+Jx46NNU8viJSdnizFpTyQnowzB3457p+dUh4LsXOKDQZkdgguygONIksM4AUm9IJrpG/D8X09Fw0i2k9F+VmFJECvGb36EfFCGfUEJe1/PnQmejbNVjOoNvz5HKZv1lWHub17YvMSixpzg9iuAWp9sMyeRu9bdGJ3ga0ZGauNfa2N3UiQqyXQKtLadf9GVC7ICo5HeHzM5Qmlt5/eA+1fwv9mmasAnZK9Onv+J5E1WyPEm9paXMb7Dp5q2ovjoWRiNeMxyKMTIeYB/PvImX5IA2XqLlnRPe0L8COPmApNmOK8MZ0Yp0FQLDf6DgFsvYaBuikRzMW/GkTrOHXumR6ZuO/vU2B33n8Z0r3u4xi5zvFnwXAKvDNVIV3AWJGolQz47AbJEqVAgXGXBQhzF9Wr+/7KY95m37YEYjPl1BWYwyCmzAlw6jmZZrcwWr9meDlmct9I7WssDtA3aigC6xMg+peJy4LTIw02FVsHEeWfPQRW8LDWGGaif8XfvLodUZORFqEpsRkHfOWFgptYy0SfsTKygAI0JhYtPkMQeZVF7zEmJL06R48hJgy54mpPPGxGVdjSusQa9SEvvGq7yYfE8uM4LH2ApTXhCp4YrzWE7hn+qeys1FppOqifbyBLkjiFCFomVXCfx3+YwsilO80vNy9fjGmUajjOamTlrEK315jCUfmo1osZpXMsg0OJaQZLhXBs4VxJCV0eDVMaQGZ7ikMn+eT+2PVf/VHz6pYBpo9AkT3hG4O/3sAh0lW8oedeSI5wUgMvms53E3TtzirIvdpJum5YgqlqKz9/1F8aFcrc28bp32Ew1S4eDCLT19aZaQVwm7frI0dBv+J3QJfzh94R8sxzYXydwAhaU6SVarPNWqCkQOb0/M4IAJDG7HBjG2wvqAhwWuKqChO2Hq9l4fM4x+NNrJ6VKRECwLsrUnq3aLpnlU5MPVCqgwbpa6n/SbXeAvhm0ZMtHTD0wnT/FRyqbsvJzOujq0oZD2Jgt0Yj85W4/TYeiXbSfcOGcpiRYaiZ/xrfF0H64R8gUtwiBBYPOAAAAA==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAYAAABS3GwHAAAAAXNSR0IArs4c6QAAIABJREFUeF7tnQeUVEXWx3/1unvykEEko4ISdRAxoCwoJiQqQxQEUYKYPtPqquu4hnXNqIsCgihRBiSKccUMSBQkiCJRch4mdver79SDwWGYofO8nqHqHA7nTNe7det/61+57hXopBE4gxEQZ3DdddU1AmgC6EZwRiOgCXBGm19XXhNAt4EzGgFNgDPa/LrymgC6DZzRCGgCnNHm15XXBNBt4IxGQBPgjDa/rrwmgG4DZzQCmgBntPl15TUBdBs4oxHQBDijza8rH2ECSJGWhlizJl2kaqw1AgEgkA40abJWpqU9JUHIAD4NKGvYCTBgwII4cnKqI/MuEVJcZ0ANE1kJKVwBaaYzn9EICMw8MPYjxE5TmF8gYpYQF7dr/Ph2OeEEJmwESEtb4Ny+LqOlV9JDIDsgOReBM5zKallnKAISD4KNEjHfIZhWq1Hy0rS0dp5woBE2AgzqMeshibgXqAE4wqGclqERKISAF9ghkG+Mndb15XCgEzIBhvWZVzHX7X0BwSDd8MNhEi3DDwS8SMbGuhyPvj2540E/8hebJSQCqPm+kXXkYeBRICEURfS3GoEAEcgCXjATyr0UyrogJALc3n3mdRhiCohKASqvs2sEwoCAPIApe4+b3u3zYIUFTYDbO89OFnHiS4lsFWzh+juNQKgICMRPMke2HzenS0YwsoIkgBQDus8eZhi8CcIIpmD9jUYgPAhI0zS5Z/z0Lm8Hc14QFAHU3F9kHv5ECNE2PJXQUjQCwSMgpfxaJpa/MZi1QFAEGJg6q7EQ4lOgdvBq6y81AmFDYJuU8ob30ruuDVRicAToMet6gZgEVA60QJ1fIxB+BMReKen1XnrnrwKVHQQBpBjYY05fIRmJIDnQAnV+jUDYEZAcEsIYOHZap1mByg6YAGlpacaWNSlDEPIVgYgPtECdXyMQAQSOSMyh703rOjXQhXAIBOAVAZoAEbCmFhkwApoAAUOmPyhLCJQsAZzrE+82pfgPiDi7UDQTq0Cl2mDYdAxheuHANsgM6SpKSPBJdQRTsRYi2ca9CNOEg9swju4LqS6hfCyQR50i955Hpz7+voCA3g4EPAWSA4hz57ledkrPXULIgL8PpaInvhWCrL/dg6PPCxgxsWERGagQkZ2BGD8MuXh6YIgHWtBp8pvOePJ6vELcdQPBJj/HZl4u3smPkfDNGyADanthQ0IiTFMa/3XEeh8R4wnovUDADVj2oh6CWQguDFsNAhUkDHI7Pokr9Z8YDptGgKxDMOp2WDozUO3Dlt/riCO3xysk3DQMRMCmDIseptfEk/4vYuY9A9IMi8yghEh+RtJVTGVzIN8HjJrsRR8MPrD16rPhxOz5AkbHBwOpa3jzZh6Akf1h5cfhlRuANK8RQ173/xDf+T7bCKDUlfNeQXz4KJhheaMSAAInZfVi0l9MZXIgAgIigOxEAkl8jMDWKxBmTBLu294htm3fQOoa3rwZ++CtPvDLF+GVG4A0UzjJu/l54ro9ZCsBcr+ejOv9oRh5Qd1HC6DGPrJKvuYoN4m5qKvSfqXACNCHdsBngK3ve70JlckbPIn4S673q5IRyXRkD4zoAeu/iYh4f4SaOPB0e5qYW/5hKwGyl35OzKg+OLL2+6N2JPO4gevFZBb4W4jfBFCLX3IZg+BWf4VHKp8sVx3vvTNwNroiUkX4lntoF7x+M/y20HfeCOWQCMyuT+Ho/k9bCeBZ/yOON25BHN4VoZoGIFYykVju9Hcx7D8BepGCgTpqrhOAOhHJalauj/nQPJx1GkdEvl9CD/wJr3aBTcv8yh6pTGbnf2CkPmPfdjDg3bYO8fJNGPs2Raqagcjdimkthlf485FfBJBtcVKT+5A8C9i2959fIXeN5ngf/YK4ytX8qWNk8uzfCi91gm2rIiPfT6me6x+0toOF0z4HHLn792K80B7XDnuxOA5ZDoIn+JMR4mt8rsr9I0AqVXExQc2v/LRLRLN56rXCfOJbYuLtOQOwKrd3E7zYAXasj2hdfQnPbXc3rv4v23YeovTLy87F8dzfcGxa7Evdkvr9M9z0E+ns9VWgfwTozdUIpkXL9Wdv4/YYj32OMPxS3xcGwf2+eyO8cB3s+SO478P0VXbrO4i5/Q0ccfZdy5KmxPz39TjW2rcjVgjO/Sj/VFPweT3aZwuSaqXVl9FguT3xmT9Mdj2tmMzWw0i8a2RJFFV8GTs3wL/bw/5ttuqR3ao/MXeOxJGQaKsemW8PJ/F7m23yFwLqSHoskxgsxOkP6n02aNmHBsD3gI0T7pNte7jLS5Tv8ZCtBufPdfBcOzi821Y9slJ6EjtsNI7EcrbqcST9VcrNsvFg8tTa7wGuFJP57XTAnJYAMhUHLv4B/MtWdAsVnjvofWKv7m+vStt+gWf+BupE2MaU1exmYu8ehyOpvI1aQO6CCcS+a7NNTkXgn7h5XqSjPMoVmU5PgF7UxmAOcJGt6BYoXBpOPA/Mx5Vyrb0qbV0FT7eGnKO26pHdpCMx93yAI7mirXq4V36B85UOCHuvQxTGYCUmncVUip2nFksA5ZOaPvQERgH2jq8FquWNSSL7qeUk1VMzMxvT5hXw1GXgybNRCchtdD2ueydhlLPxSjSQufl34p5OwZFnb4dQyBhHgCFM5sPirkkXT4DOJJPECOA2wKYrl6e2LW9CRXJf3ExCRZs5+ccS+Oeltl0BzkfGff7VOO6bilG+qq1EzDqUQezD9XBk2TslLASCup76Pke5T8yhyItKxROgH43woq461rcV2cKFVzgb843t9l2Dztfn1+/gX21sh0Y2vApx/3Qob+8ehWlKjHtqwqGdtmNSSIFNOLhJTGBdUYoVT4DePIzg37Zeey5C46x6bUh4zr4LaCdUWvUZ/OcG241tnnMp4oGZiIpn265L1pNtSfgjCmxzMhLKk/RjYgov+U0A2YeKSBbY+uilGHMebnk75f9vrO3GZslH8PottuvhrnURjofmYFS130fZ4dfvoPySKLBNYauoxzKCdmIyp7xfLXIEkL25FcF7EH0RXnJueIy4fs/b3vD4YSKM7Ge7HrnVGuF4dD7Os+rZrkvOhMeJ+zQKbHMqEh4kA8UUJhb+6RQCyL6UQzIDaG87ooUUkMKB2ecVHB3us1+1r0bD2CG265FT4Vycj3+Gs8a5tuvinf8GxuQHELLYbXc7dfwSwS1iEmpn6EQ6lQDHHr0ot4f2TyoLwWU648ge/CGJrTvbCeSxsj95HSb+n+16ZCfVxvnkl7hqNbRdl8wf5xA/qieGJ6B36SWlt1qd9y38WOYkAsgbiaUCTyJ4xO5XX0WhYsYmk/3QlyQ2joKQBLOfh2mPl5Txii0nO646zqe+wlWnke26ZK5dQvzL12Dk2vw0smgk3Ehe5BDPiE/Izc9yMgH6UgtQfj4utR3NIhSQiZUw//kjjlrn26/etCdg9nO265HjqoTj6W9w1W1quy7e7b9i/OsKhM3XQ4oFQqDua3cXk9heNAH6oOJZq8WvvVcLi6mBu0pDHE98gVHV9kdpMOEB+PQ12xtdjiMZ59Pf46zf3HZdzL1b8T53La69G2zXpRgFMoGBYjIqDreVTowA1sU3J/MQ1qMXn7dE7ahhdr0riXloOo6KZ9lR/MllqgWwWgjbnPJEPI5nfsRR3/7rWt6Du8l7uTvxm9Xl4ahMEslneOiYf0HuLwL04lKEtfdv38sKH5jlNe2A8+4JGMlREJPv7f7wvXokZ2/y4kQ8swjjnIvtVQQwMw7geas/Mb/Y5yvJJwiSbCTtxFRrOnSsp5eDcXEU9ZrhDp8CbMsg8F7WG+OOtxHxNt8DUh7Q3ugBP6ndYnuTeq8kn16EcZ79GwMyOwP57lCMRVNUq7IXmNOX/i5J3CVG4z5GgN40AWYjsH8zuRjFpeEg9+r7iOn7HEaMze/ylWPcVzrDyvlRYWT337/C1VztXtubzLwc8iY9TuxXIxAKo2hNko1AFzGFNUKmYbCBu4AXiWJ//9LhIrfTU8R0exTD6bAXWq/n2HvgtX77X4qovlnDZ5Nwhf1nI6bHS97M/xA7Nw3hVT6qojZlA4/QkJFCplIJF+OBjtG6+LVgdMbi7fkixo33IGxyBHvCnOoNwLNtbXWKVbBpZQycRHL7Pra3Nikl5qdv4pj6CHhObLXbrlcRCqj52TzcDBCyFy0xUJG27X1S5AMmdQjmHTAKV5ve9gPqzj32GGbLSvt1AQ71Gk2FTndGhS7u76bgeG9ItB6GFcToICbXCdnHeu/7RFT3/sr7WGJV8oZOJb7F1fYbOi8H/pECO+31CZQPxMFur1Gx+/324wJkL/+KmHd64cj06ZLHbn3VKPCsIoBycN/Vbm18lW+Wr4Hn/tnENGzpK2vkf8/Lgocbwb6tkS/LjxIOdXiOCn2V7wL7U96GpThf74JxeIf9yvjWYJYigPLuepnvvPbmkFXrw8PzETUvsFcRVXpuJtx/DigP0VGQDl/7BOUHPBMFmoD8cz281AGhPOdFf1qkCKBcm0XXs8cigHPXbgkPz8NVOQpOgXMyYHhNUP9HQcpo9yDJd7wcBZqAe/9ueKkjrm1Lo0IfH0psUgRQVkyKdm3zGl6DeGg2rsQouKaUfQSGVIEo2erLbnMX8UP+GxUmdGdmIl/uQsyG/0WFPj6UOCpkX+to2OaTJd9YmRd1ggdm2f8YXqmasReG2vsIvSBinqsG4Rz6rm8QSyCHihkmX+2KY+XcEigtxCIEOWoEUPEt7XUq40c93G3vwnVndPRy1uL3vrp+aF0yWczL+2AMn2hrkIyCNXWPGY7r66jxE3o6I+xXBFgD2Bhpwr9GktF9BMnd7vUvc6RzqYXeI/Y/QMmvZl7zLrgenoEwbD4hP65QxswRJE+Pjm1ZH01hrZoCfahcSUe6zYQqP3PIdBLb2O+FwaqHigrzRBRsxx4HNavBtcQ9MR/DxiAZBe2b+e0MEkd1D9Xkkf9eME2NAH8Hy/9PVL4BsFAwHJiPfYnR2NbglH8ZZP138Iz9TrHyFcqo1ZrEZxdguGyNXXgCH3PN11bEGKL5Qtyx66qPCdmbKxHWVYiofQfgiauI+dSPxNSJgjMAZeYocYqV3+KOVE0h8cWFOGJsjJhToL/O27oe4+krcOac4oYn8r26/yWozZ/r1F2g2gg+QxA9k9pClXBXqIP3mRXEVYqChzBKNxUd/rWb/Yc6wjkPlz+fpNdW4oiNjs28nAMHcDyZgutQdJyUFwm/ZB2S64XsRyJeXgdujyYnuAWV9lY/H/nv1ThjomOIjxanWCdGgPi6JL61FkdcQoSp5p94T54b8VgzHLt+9e+Dks+lnOaOw8H9wnKD3pfeSN6OJjfoBTFxN2yL66nouHtv6RUlTrFOrAFcZ5H49kaM+Cg4JDyulPvpdrg2fF3yTdu/Eo8gGMYkphx7EXYrZ2NanqBT/Pu+ZHNlXD6E5LvfKdlCT1fap6/DBPudYuWrmOUoT9yo7Rjx0XOgn/HWUJIXqtASUZlWYHCTmMjOvx7F9+UupBUPwL6As8VgldnpGRJ7qRvbUZKixClWPhp5Ig7XmN32v5UuYJ7MKc+SOO/JKDHYSWp4ENwnJllv4Au4RTnmE3SaWhkjomhLVBh4bxuJ41r7/XBaMEoJ0/8Js1TM8OhIJgZi9AFEor1xwgqi4f38HRwfDAflQCBaknKKonY8BT3yfYSe7BmuF1dhWE6DouDK5THUTFcCnmGTibm0S3TAqAw6+RGY/0p06HNcC88bO3FWrh41OuUtmo3znT4Y7qyo0QnYjUmqmMp3+UqdTIBUYojhQaT1QiwqthRy4qqROWwmlVteER1Aml6ylRvwz19UDkmiQqcc4slMW0XlBudFhT5Kif1LfyDx7W7E5UTNy7AcyzdoFZ4XbxbjG9Qa4VOpjsvyEKFeWdt6ucSNi2/l9ay94F56Dr6CatXt3+XYtyeLeWP+x2VrHucCsdr2BpdNArO9vdmXMoheAy+kSjX7+609uzL5cNSPNP71DdqIz3Bhs4cIgWm5/Dd5sHDEyKIDZPSjGh7GIbjJTgt/L9szw9uPo0YFGjerRv/BzalcxT4DZ2W6+XDCGhZ+u42zzc3cboygrlAuZuxJyivc/8ybmG32xu1I5PKratKjX1MSk+w7L9m/L4sPRq9i7eo9JJmHuMUxgSvFl/YA9Fepn1keINLZVViR4mOEpVITJyMR3FjSrtLziGWhbMs07wByjs/EDEPQ8rIapN7amEqVS/7WxtGMPGan/8o3X27G67X8sXGeWEc/YyQ1xPYSnw4pjBabVzHNvJ2s476MHQ5Bm2vq0aVHQ5KTS/5axIH92aRPXMvSRTtQQfNUiiOLHo7xXC6+JuavmUdJEUK5RFfO0IeLj/7yCF2w8NPHCb6Vc/Fa8QKU1+gSaXWZJPGl2ZH/mR3JJPkkoBxOg2YXVaPTzQ2pU788ihSRTsrXzY7tR/l45gaWKMN6/5r3KxLUERvpZKTTVCwrsaH+oKzM/+RNLDBvPNFB5OOgMLnk8hrc1K0BNWoll4gPJdXYt246zNyPNrB65R68npN3fhLJ4BpjHu2NeSRSYnGE1V2fdBw8w0Q2Bhwn2FoPqG3SblQinlstT1pQI5INbp+sxiyzL8vlpeQWwzdhCKpXT6Rz9/O5+LKzcTgiF8JYNf51v+xn5tR1bNl0yOr5i0rlOUh7Yy5XG/OJQzkdi1zaIWvzkXkrv8gWuIkpsiA1EtStX4FuvS6gUdMqESWB12uybNFO5kz/lV27MpHHe/7CisWSTQuxmK7GJKqIiDsTUC4pXiSbiczkQHGNX+noVxdquU53cAUGjwKtweqaw9Ly1GRC9frrZTPmenuxHeX737dacXFOrrq6Du2uq0elKgm4XGFRx7KbMur+fdn8sGArX32+GTX395UceGgultLBMYOabCWW8IUJUvv8GZRnpdmK+fIW9kn/dqkTElxcfX09WrerQ+Uq8WHtLNxukwP7sljw+Wa++2orOTkeXxBZXWotttLJMdXaQFCjQRh30tSwo963/4DJC3j5Md8F+ukU893Sjn9tjQb9qeT1cO0Rqgx24m6TSIbDILiDDmXUA7IKv9GYZebl/CqbkhXg23zlIfHsmslcfOnZXNSyOjVqJhMTG/zGlTvPy+5dmaxavpvlP+1k65YjpwznvqxcSezjIrGYFLGYeuJ34skK2sheHBZGa+WFLJNX8JtsjJr7B5LUtLFO3XK0aHU2zVPO4qyzE3HFBI9RXq6XHX9msHLpLpYt3snOPzOss8FAUgJHOV/8wsXGQhqwFoVZKO0oUyZ5TIwFSeLQOIeTL/jg9L2+X2uA4io0LTXVsYy2dyeLrH83NlbGp4hFVBc7/Br6VW+v9qx3ypqsli1ZIS9lr6xOLnHWEV2wyek0SC4Xy7nnV6TlpTU47/xKlK8Q69caQc1fM4/msXnjIWuOv2Htfg4dzEH1cMEmB16UkeuITbQQC2ksVlpGduK7l7QwkgnsoJbV6H8xW7CPalbDDwUjNUKWrxjH+Y0rW5sJ9c+tQGJSjN8YHT6Uy++/HmDp4h1s/PUgGUdy8RSa6weCl+r51ShZVeyyOotmYilniz+tduTPqKDa0S5ZgxXyMtaZF2bkyLh7/9Xk3g9EWmA9csCtLi0tzdiyJmUIglcExKuV/VliB/XFb9RhI1XZba32VSNQvXweMWSTyG5qsEPWYZusyy5qobbwIpHUqFChYhy165aj/nkVrYWgMrQrxrCMrQ5y3W6vNa3ZteMomzYeshZwavsu0J7MX/3VIrCW2GxhVIstlOcQLgsjRQgDN05rzbOH6myR57JFnscuakQUI7WdrDYSFBGq10giIdGFy+VAGFg7OO480+oYdmzPYNPvB9m25YjVMUQKI4VFdbZTW2yhhtjKWexQx3vEkGeNDmo0VJ3AXs5iK+eySTZgt6yRPyIekZhD35vWdSqoC87+p5AJcHJR0toJceI+QQC1UPPgCqn38r86p+ZUhIiJceB0FSCAcuOd642YMX3p6yIP9U91EqpX9+C0DGnadO5oYRTrwOX8iwAet0lenn0YqVFAtSOFUz4BVDtSfylijRgtBPBlev27RiAiCGgCRARWLbS0IKAJUFospfWMCAKaABGBVQstLQhoApQWS2k9I4KAJkBEYNVCSwsCmgClxVJaz4ggoAkQEVi10NKCgCZAabGU1jMiCGgCRARWLbS0IKAJUFospfWMCAKaABGBVQstLQhoApQWS2k9I4KAJkBEYNVCSwsCmgClxVJaz4ggoAkQEVi10NKCgCZAabGU1jMiCGgC+Aurev3kdDlISoohIfHYs8zsLA9HjuRaD+Aj9eQvXz/l1kW9zy1XLpa4eCemaXI0w2090Qzlja2/9VfPQtWj+HLlY4iNdWJKSdZRN0eP5qFegZXSpAngy3Cq4at3sJe3qWW5WaxYKQ6n89iLUOXvR713/Xn5bn74ehuHD4XPpcmJhi8ENWon07pNbS5oWtl6p6x8GinfQ+oB/r7dmaxcttvyqnbkcK6v6gT8uxCCmrWTubJdHethfGKiC+N4+Yp4+/dmW54eFv+wnYwjeQHLt/kDTYDTGUB5Q2h7TV3adzjHevx9upSRkcfHH21g4ffbORqGhmA90q8UzzU31Kdt+7rEJ5y+/L27s5g3cwPLFu+wRqZQk2r4VarFc33H86zG78t/0sED2cxJP+YFLzvLtz+kUPUL0/eaAEUBqRqf8gyhvMg1blbFb8dQqkdUPm9mp69n987MoG2kphvnNqzIzb0a0bBRZb/lqPJ/+vFP5s/6jZ1/huZKUJV7S+9GnNOgol8uUJSSysnVkoU7LF+oB/dH1tOd36CcPqMmQFH41DunAgOGXkStOuVQZAgkKR+gG9bv553XlwY9JVAuWQYNT6Fu/fIBuydUrkmUg64PxvyM8skTTDq3QUUG3d2CamclBl7/4+VPeHeVNT2M8qQJUNhAylFW/zuak9KqesCNL1+WWhArV+iT31tNdnZg0xG1yB72wMVc0KRq0G1HrU0+/3gjM6eut9w1BpJULIUh912M6gSCTWok+mze78yd8RvKa14UJ02AwsZRPkNTb21CbAiuEpXMzKNuJo5dZU0J1ILVn6Sc097YpQFdUs/3e9pRnFy1Dhjz1nJ+XnaKa/tiVVHz/A5dGnBj1wY+5/y+6qMcho0asYyNG6I66rsmQEFDqt73kbTW1q5HqEm1+aWL/uT90av8XhQq/5t3P9zK8lUajqRcjo8esYwsPxelyhHuPY9cannHCzUp0ivnt++P/jlUUZH8XhOgILopl1TnrgcuCbn3zZe5f28Wrz6/yHKl6E+67Mpa9LujubXPH46ktmX/+8oSv3th5Qj3zntaWB7xwpEOHMjm2ce+DXotEg4dfMjQBCgIUO8BTWl/4zlhw125URz95jJWLPE9DVGOejt3b8gNnRugpkLhSLm5XiaNW2WdUfiTVBSdGzqe54+XeX/EWeckI15YxJpVURPwrrDemgD5iKhGd/dDl9C8RfhChqpp0LQJv/D5x3/4bDCxcU763t6MK9rUDnjnpTjhajE6e/qvfDr79xOhh06nyP2PXWZF0glnmjJ+NV9+simcIsMpSxMgH0017N/7SCsaNQt+96Uoy8ydsYFZ09b7NFp8gpMBQy6yXJCHK6keWJ0JqBBEhcMPFVXGE8+3sbw+hzPNnb6BWem+6x/OMgOQpQmQD5aagqgFaDh7QDUCzJiylk9m/+7TJmref+ug5qh1QKBnD8UJV41eEXD+7N+KDdNU8NuHnrzCCo0UzpQ+aS2fzvFd/3CWGYAsTYCCYA0cepF17B+upC6JjXtnJYu/3+5TpNqCvLl3I2sNEq4gfmoPXoVn/fqLzX5d1lPnH3+7tp5PXf3NoHaCRr661IqaE6VJE6CgYVTssNsGXxj0AVhhIx85lMtrLyyyAmn4SqrXb9O+Hr36NwnbLoy6nDb6jWWsXe3fIrT132rTf/CFqNEwHEmFiH3uie9QAbCjNGkCFDRMlaoJ/D2tNZWqhB7ZVU1/1qzaw5g3l6Magj+p7jkVuOuBlig9wpH++O0gb738k9/bkOoKxj0Pt0KdBocjqd2vka8u8WsBHo7ygpChCVAQNNULd+1xAR26Ngh5GqK2QKdPXmtFQ8wP/uzLQGoapNYB4ZiGqenHpHGr/Z7+KN3U6XePfk1oc03dkOuvboSOfnO5dS8pipMmQGHjVK2WwJD7W1p3YUJZjP66dj9j3lrGwf2BXQhTcbfu+/ulIfXCqvGvXrGHt19faoV0CiSpW6h33t2CqmcFPwoowi/6fvuxu1BhuJodiP4B5tUEKAyYWoCmtKxO74HNrMcvwSQVAnTc2ytRU5BgkjqR7jOgWVBTMTX12rTxIBPG/MzWzUcCLl6dh7RqXZNe/ZuSlFx0QG1fQjf+doCJ765m65bDVtT0KE6aAEUZR8XIvTClGrcNuSjgRvDntgyr8f2+4YBfOy9Fla8Woa2uqGlNR5LLBdYIFfnee+dni3z+XsIrrIMiwcWX1bAW5OUrBNYJKPKNfWsFu3YeDbr+JUgYTYDTgV33nPKk9m1C/fMqoCLMF5dUr5uT7bEavdr33rHtSMjGV9OvBhdUpmf/ppxdM+m0t1NV+ept8LrVe63y9+3NCrkNqZGw6YVV6dLjAitk7OnuBx0rPw91+W7GlHUc2FcqHsMojDQBTttSBJQvH0vTC6txQdMq1KxdzpoWqWsLKuXmeDh8MIctmw+zdtVeqwGohhjOVKFSHBddXJ1GTapYb4PLlY+1QpNKU1q3PNUaQ5X/y8o9rF+zzyJiuJIiYcVK8agpmXoPXKNWOetRvHocn0/6A/uzrG1eVXdVfpTP+QtDowngT2PJj4ebmBhDYrKLmBhFABUU2mvd+1eeESIZP1j1xop0iUku61G6aoBqoZmb47XKzs50W0G8/Xx24E+VT8qTX35SuRgSEly7D031AAAGp0lEQVS4nIY1tc/L9VjlZ2ZEtvyAFfb/A00A/7HSOcsgApoAZdCoukr+I6AJ4D9WOmcZREAToAwaVVfJfwQ0AfzHSucsgwhoApRBo+oq+Y+AJoD/WOmcZRABTYAyaFRdJf8R0ATwHyudswwioAlQBo2qq+Q/ApoA/mOlc5ZBBDQByqBRdZX8R0ATwH+sdM4yiIAmQBk0qq6S/whoAviPlc5ZBhHQBCiDRtVV8h+BkiZAizuEkK8B4XF8439FdU6NwCkISFBvVwe/l95lGoiAnu8H4b9bioGp83oIYY4GQo/AoA2qEQgRAQkHJcZt46d1mhuoqCAIAANT51wthJwKhNcFc6Da6/wagWMI7BGQOnZal28DBSQoAgzoOrOeEWN8AZwXaIE6v0YgAgj8LjzO9mM/umlLoLKDIkBq6rSYZBE7EUgNtECdXyMQAQTSM2TurenpPfxz3lpAgaAIoL4flDr7Jin4CAjM41MEaq9FntEI5AnJzWPTu3wcDApBE+DGG+fHVk90fyAMaxQIWk4wSutvNALHEZDSJH1Xpqv/J590CCqaeEgNt/8ts1OcTjEdKcMXkU7bViPgLwJC/OHxyO4fzOiywt9PCucLiQCpqdMcSUZMfyHFf/SOULAm0N8FicBeKeTfj5p5H6Sn9wjMdXY41gD5MgYMWBDnzDrS3St5XAgaAuEJSxIkKvqzMo+AKSUbHILnPAnlpo8f3y4wv/WF4AlpBMiXlZaWZmz9+eJmOM3nMOR1SOEq82bQFSx5BIR0Y4rP8RiP17lw2eq0tDQzVCXCQoB8JQZ3mpvgjpO3IuQQATUlspxAqF2i8IQsD7W2+vvShoCa2qjFbYaEP5FilCtHTBw9t1PobrOPIxFWAuSj27fv/HKxeZ7mCNlImOZZUhgVEbL0jApStEJwSVmZzkmQArEGzAWlhQESkYeUB4UQe5BiXW6Mc9WkSR0CjxTio8IRIcDJZUoxePBo58GDFUugrPCYN4mk84Rwvw1cVfq3eNXlMLnKFGJoppmzPDwIRV5Kk71VzbSv23oDvdwWqGalplEGWrFQ8w/sOacFpjlaCNGi9JLAuhm53mt676nf9OcF4Zgzh4prtH2vCVCsRaS4I3VWC1MYr4K8EkSp2t2SEimEWCEdPHzUk/NNKFuF0dZow6mPJsDp0RS39Z7T2OGVIyVcJUrPibfq+VeYQgyv12j5T7rnL97ImgA+u5PjIwHGO1JwcSkggYqpt1YI7qnTeMU3uvH76OF82l9nUGGUSst0yJRSrnA4HA8d9mZ/p6c9vhuvHgF8Y3Q8hxS39Z5rTYeidHdIIlgmTGN47SbLluqe3z/DagL4h1N+LnFH6swWXsSoKNsdkiDWSMnddZss/043fv+NqgngP1YnRoKBPeemCGk5BbjS7sMya7cHlgnBg7Ubd/4+LU2EfD0gYEhK8QeaAEEa746e8xp58Y4S0iKBTTgKiZTLDMyhY9K7LhcBekQIsupl6jObDFc2MBzUa36KabrfFZBiAwmklHKtwBg6Lr3TD5E+MS0bFju1FpoAIVp2UK/ZKXgZIYVsXYKHZSaIZQL5f2Ondf5RN/7gjagJEDx2J74c3HvuBV6POVqKEpkOqUDyS53SHDwmvdvPVqh7nYJGQBMgaOhO/vDYdMgzRiAjeXdINf5fMB1D35vecaFu/KEbTxMgdAxPSFDTIdPLCCFoHe7doeN3e5Ygxf3j0jsu0tOe8BhOEyA8OJ6Q0q/nR42cpmOUCO90SCL5CY8xZNzMTmrao1OYENAECBOQBcUM7DmjBaZrtBBhmQ6pOb51n3/8h50W654/vAbTBAgvnvnSxG2pM1s4Qr9KbYJcjDQfHJfeTU97ImArTYAIgHpcpLjtljmNHY6gr1Krac9CE3P4+PSuP+uePzKG0gSIDK7HpUpxW+rHLRx4A71KrU54V5qG967xH96spz0RtJEmQATBPSY60KvUUt3lWSi9PFi32col+mJbZA2kCRBZfE+MBIN6zmwipeO/Pl6WqQXvD4aX4e/O6LxaT3sibxxNgMhjfMp0CMHFRdwdsp4xeqQ57IP0rkt04y8Zw2gClAzOJ0hQ9EN7Ne0RP5pCPDD+w05LdeMvOaNoApQc1ie2SAemzm9UwO+QusT8vWGKYWNmdFqrG3/JGkQToGTxPlHaMb9DcowQYEhz8Lvp3ZbZpMoZXawmgI3mH3TL7BRcMHZq8P7tbVS/TBStCVAmzKgrESwCmgDBIqe/KxMIaAKUCTPqSgSLgCZAsMjp78oEAv8Pd6MIoKe72RgAAAAASUVORK5CYII=
- /logowanie/52648
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Card Stealer, Banking, Personal Info
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: Payment Card Theft
Victim enters credit/debit card details including CVV and expiration. Card data is captured and can be used for fraudulent transactions or sold on dark web markets.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for allegrolokalnie.89457-752.icu
Found 3 other scans for this domain