Phishing Analysis
Detailed analysis of captured phishing page
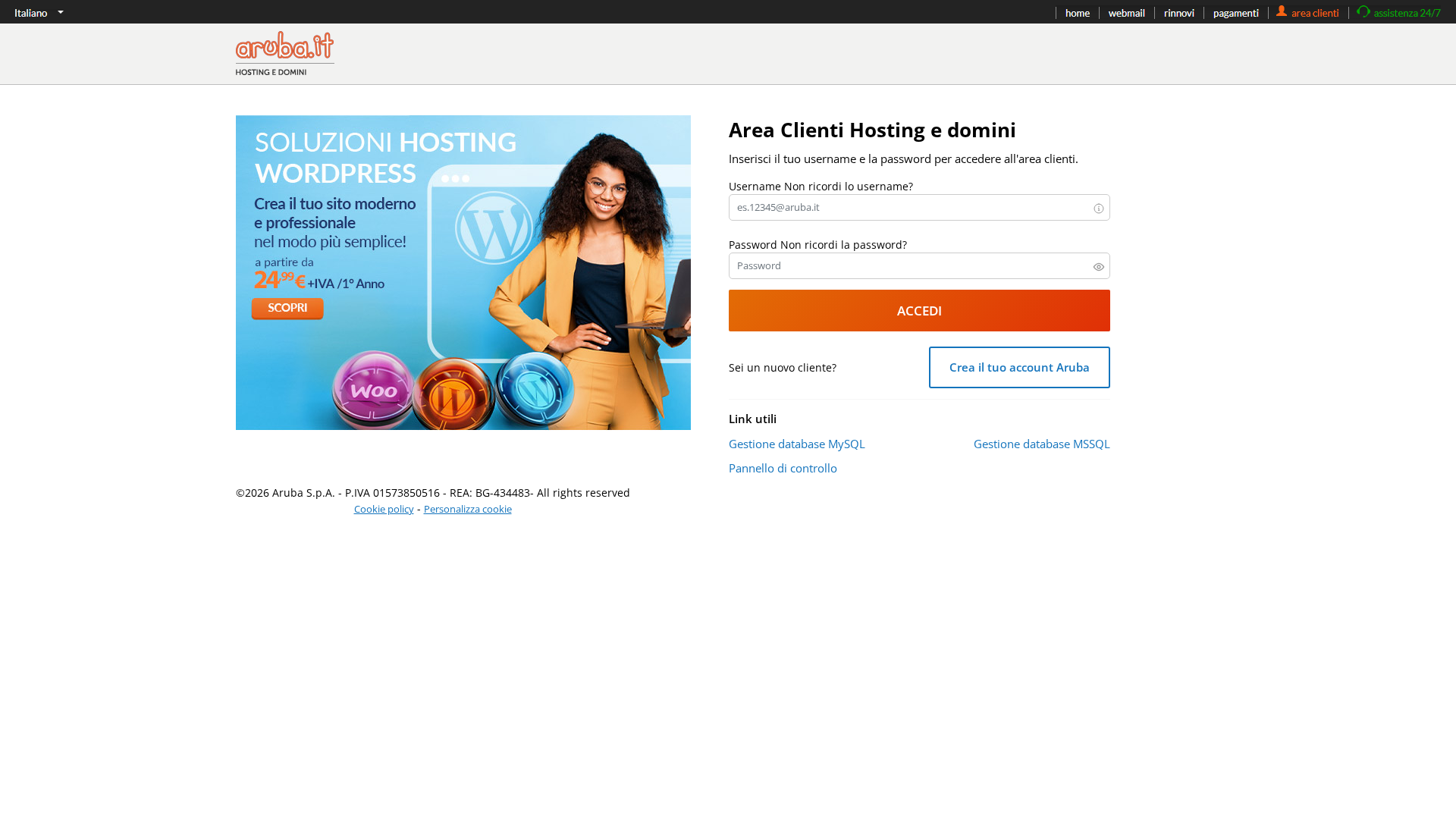
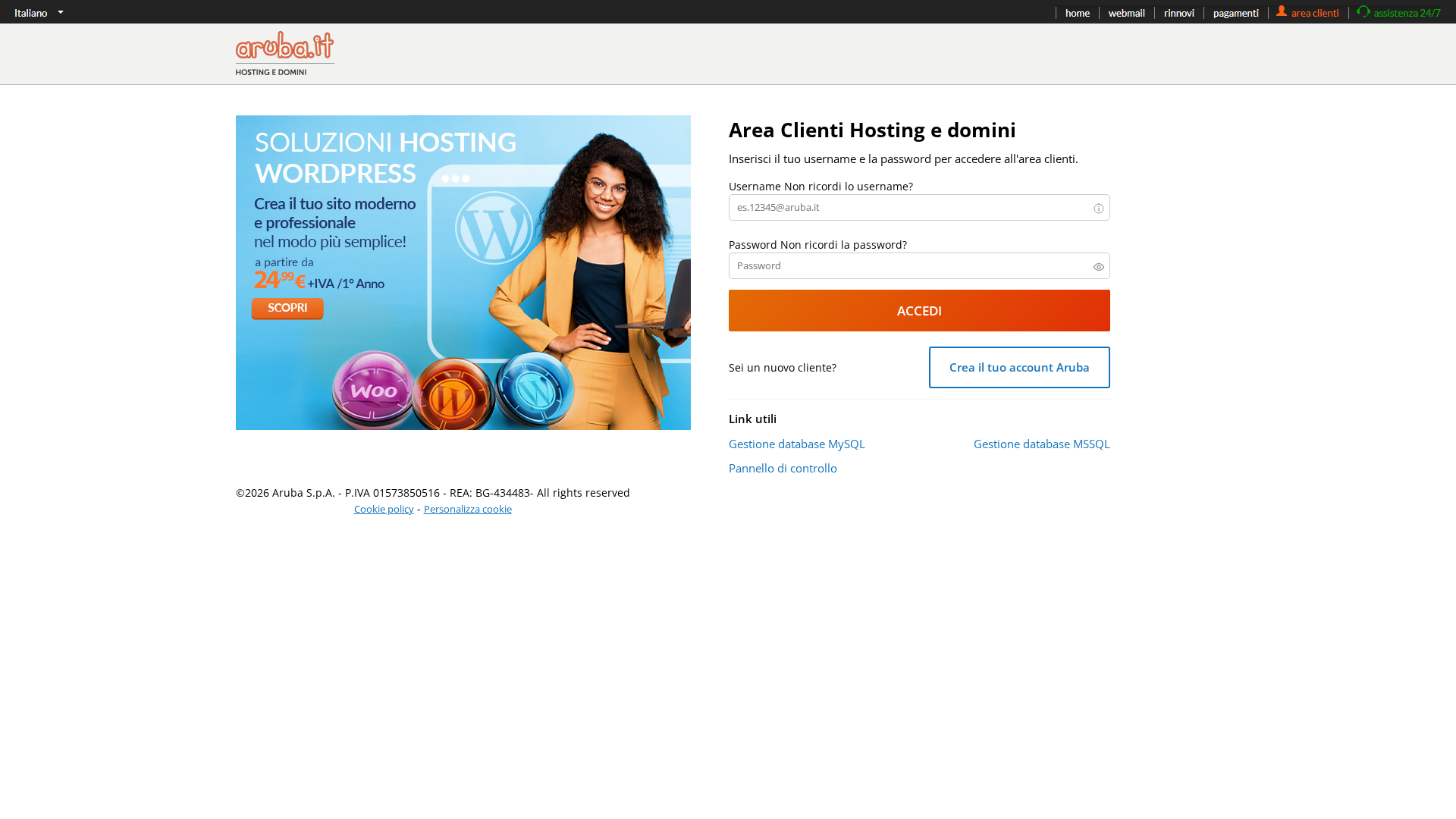
Captura Visual
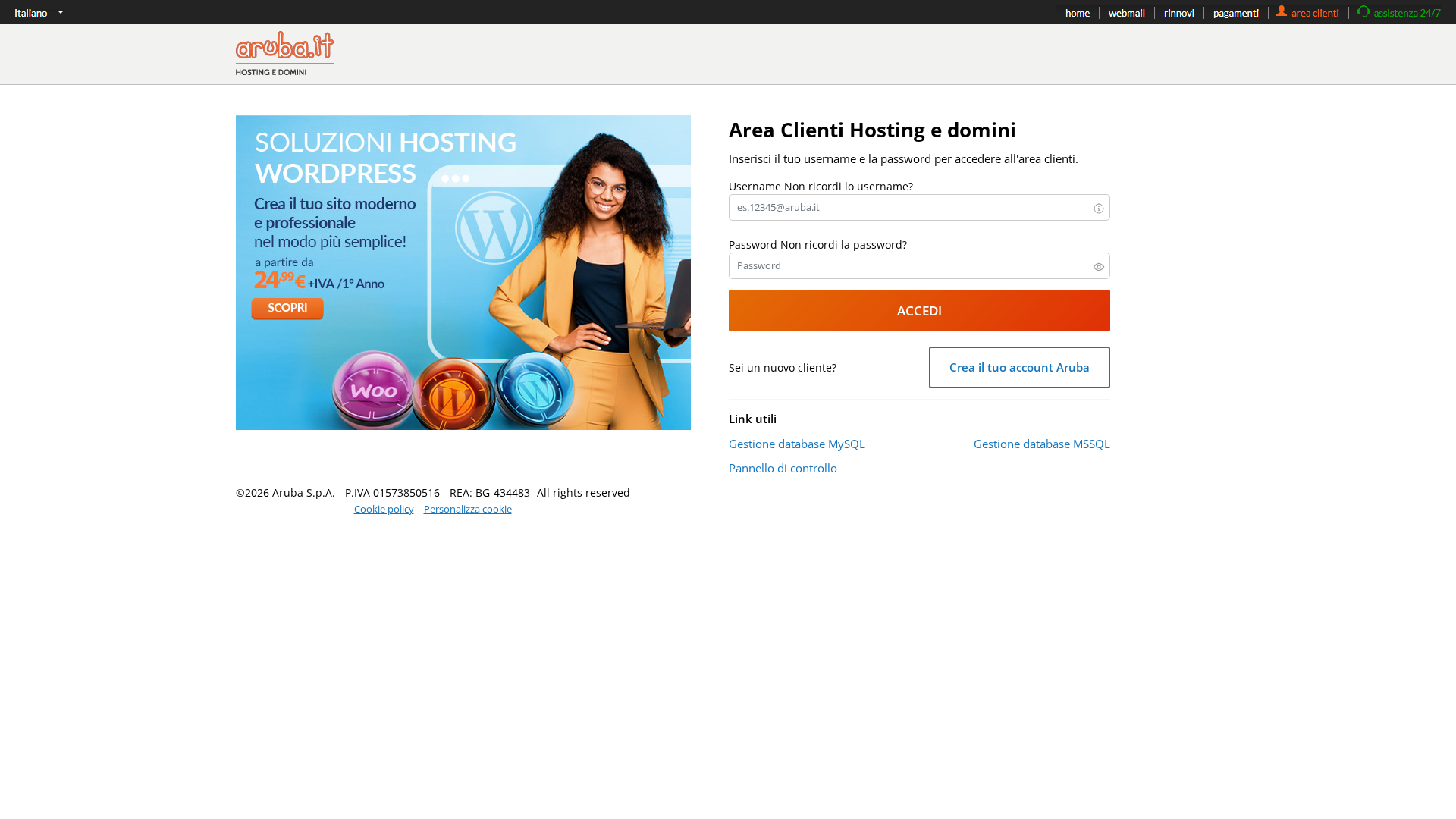
Información de Detección
http://ssosapahue.com.mx/oup/
Detected Brand
Aruba
Country
International
Confidence
100%
HTTP Status
200
Report ID
e2b8381d-dd9…
Analyzed
2026-03-01 18:04
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E6611F40D313693F1A33E0D89A9E7E13AAE8C435D28E291477FED35A92ECD4E6C161C5 |
|
CONTENT
ssdeep
|
96:nUuS5Fr+2XpvIWyoe9Re7bpSTJXOM041PAtWVu:9SOGvr97bYnzEWw |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b939c6c61c2d6713 |
|
VISUAL
aHash
|
008f83839fffffff |
|
VISUAL
dHash
|
661c1e1a38021000 |
|
VISUAL
wHash
|
0083818181dfffff |
|
VISUAL
colorHash
|
07003008040 |
|
VISUAL
cropResistant
|
661c1e3a38021000,0000814656560681,ce973331313371f1,5a585898991b8387,0000303030100000 |
Análisis de Código
Risk Score
82/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Amenaza: Phishing de credenciales
• Objetivo: Clientes de Aruba.it
• Método: Impersonación y recolección de credenciales
• Exfil: infos.php (basado en la acción del formulario)
• Indicadores: Coincidencia de dominio, Ofuscación de Javascript, Formulario presente
• Riesgo: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- eval
- fromCharCode
- unescape
- base64_strings
📤 Form Action Targets
- infos.php
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain ssosapahue.com.mx is completely unrelated to Aruba.it.
Credential Harvesting
The page has a login form designed to steal credentials.
Javascript Obfuscation
Javascript is obfuscated to hide malicious behavior.
Brand Impersonation
The page tries to impersonate the Aruba.it login page.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
Aruba users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 9 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
Aruba.it
Official Website
https://www.aruba.it/
Fake Service
Aruba.it customer login
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attackers are using a fake login page that mimics the design of Aruba.it's login page. When a user enters their credentials, the information is sent to a malicious server.
Secondary Method: Javascript Obfuscation
The malicious javascript obfuscates the exfiltration logic to evade detection.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
ssosapahue.com.mx
Registered
2017-12-07 00:00:00+00:00
Registrar
None
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.