
Phishing Analysis
Detailed analysis of captured phishing page
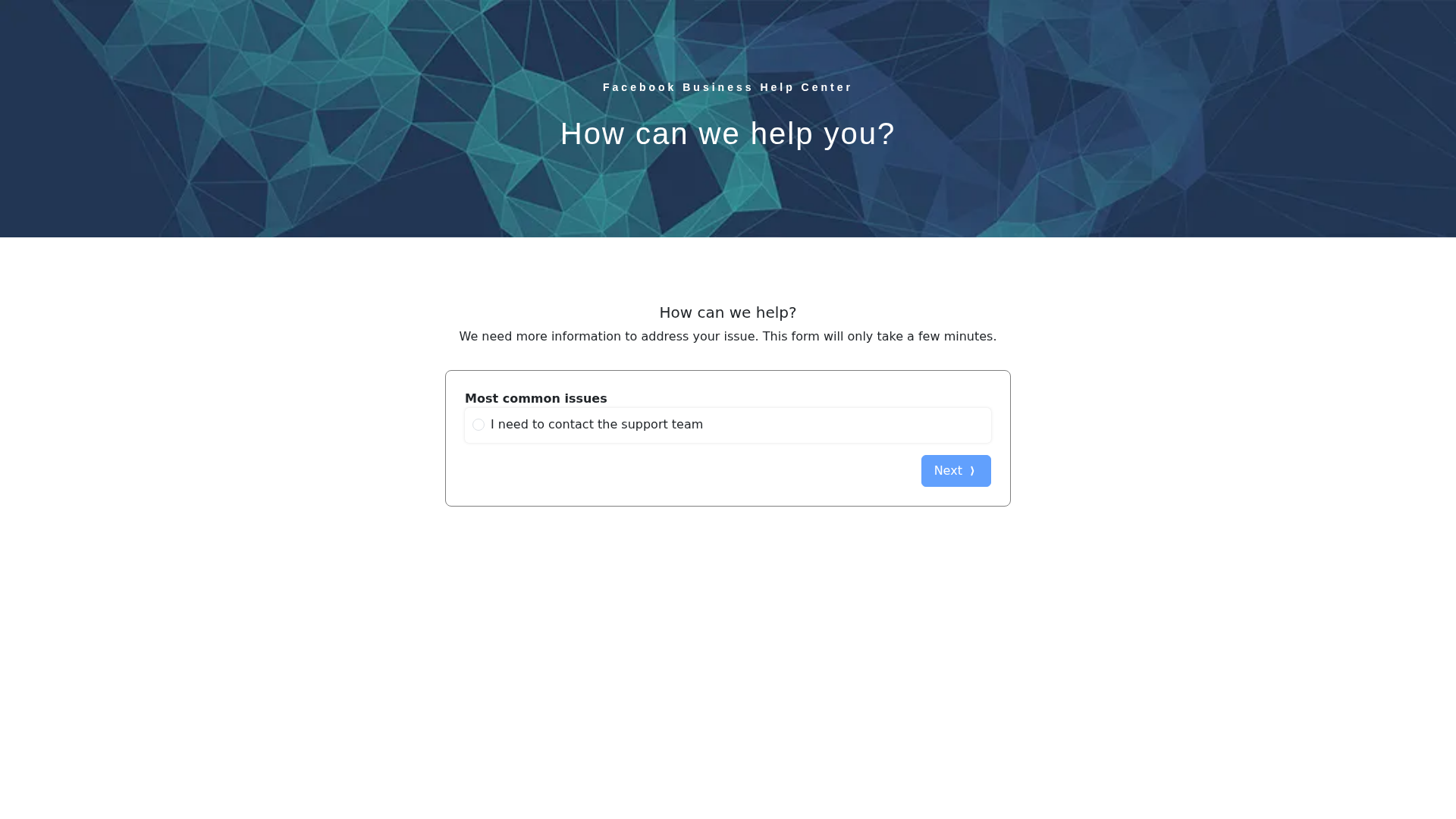
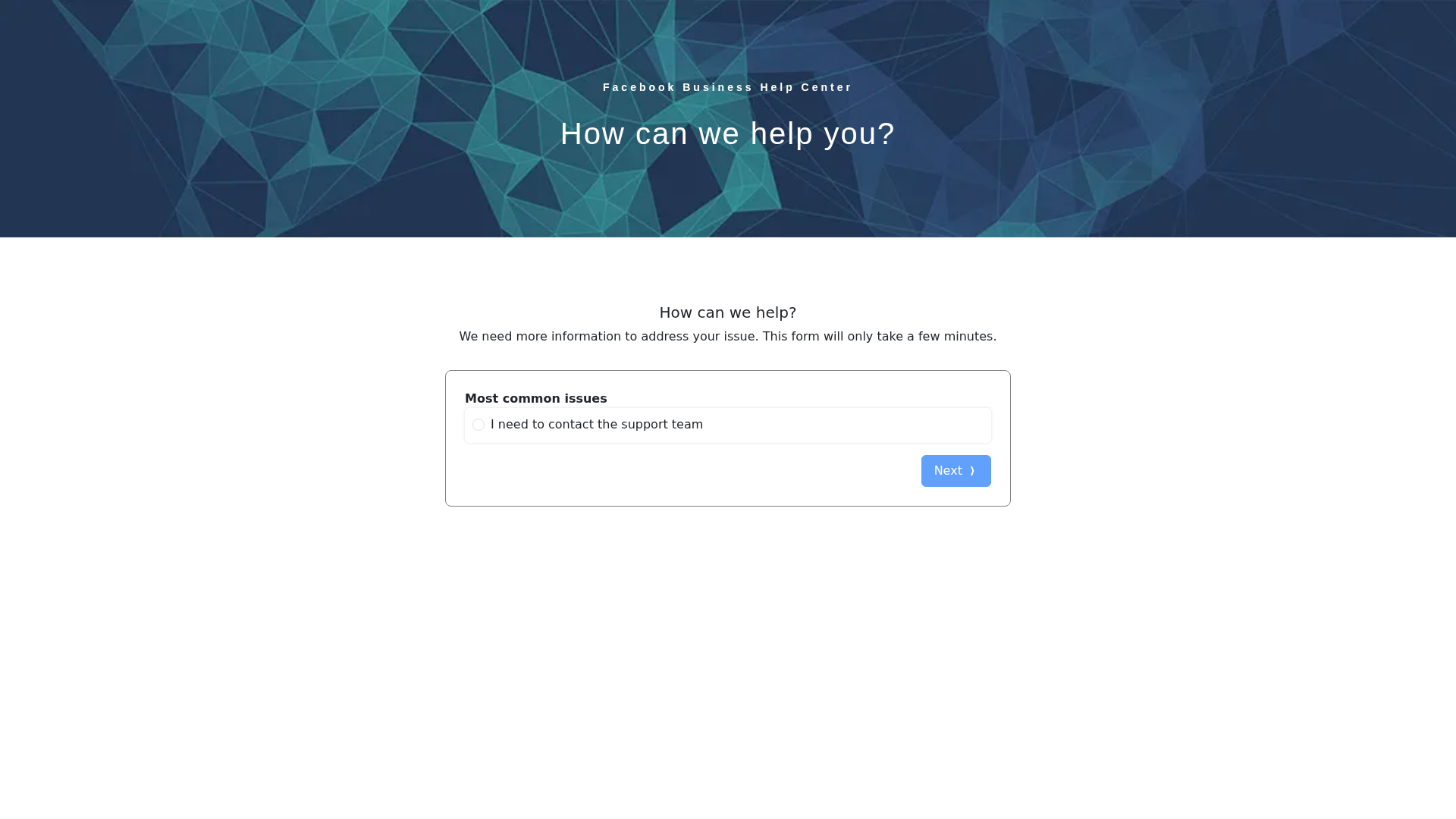
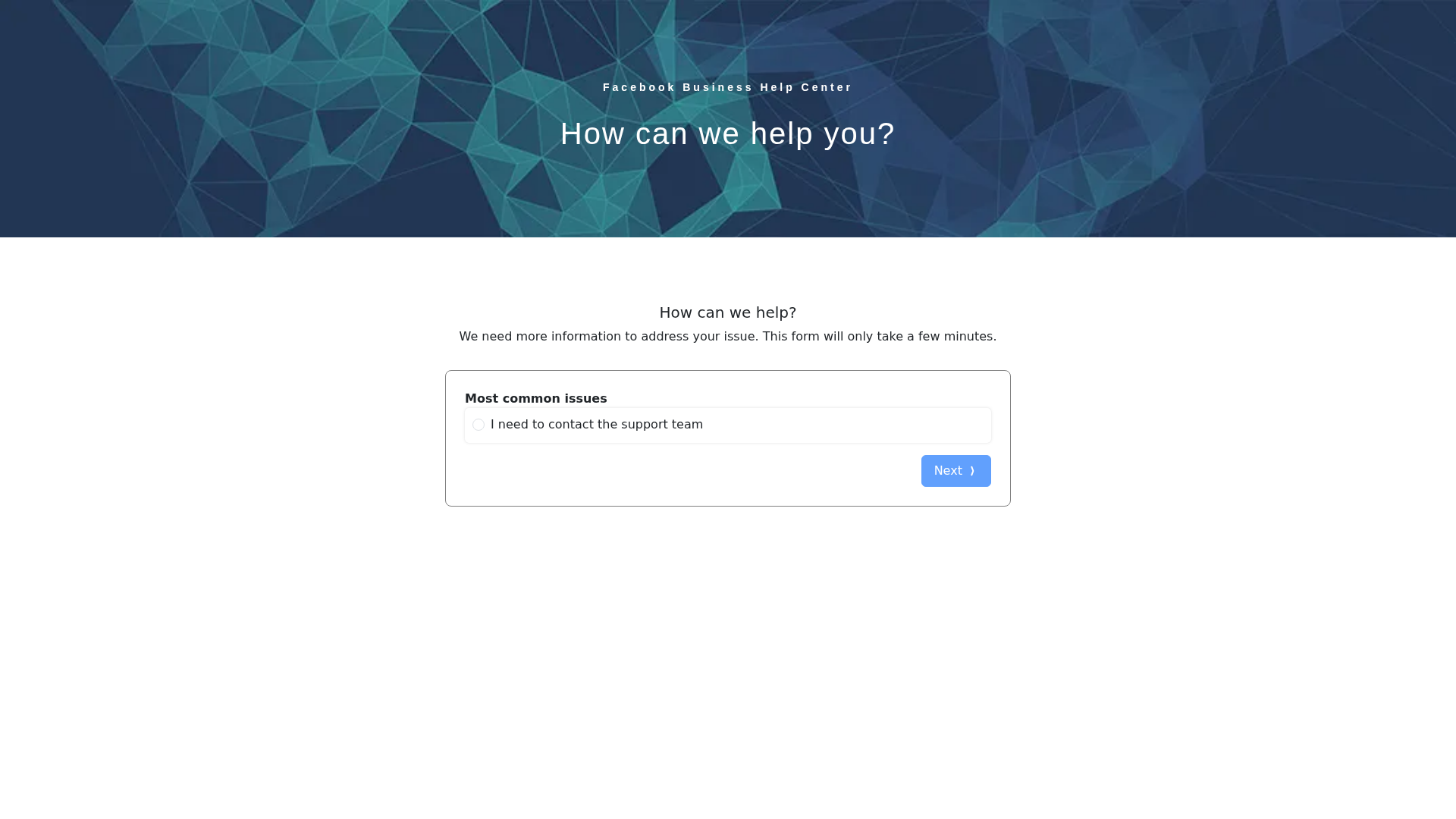
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1464186354010563A55630DE1B0E2E706A2C3E34ECE9724002AFCA39947DED45C86B7A0 |
|
CONTENT
ssdeep
|
48:nxCCG94X8idMC6BeWR2pe27+FTh/TEu9l1n:nzG9Q1B6JRRhwm5 |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c4444461f1f3f376 |
|
VISUAL
aHash
|
000000ffffffffff |
|
VISUAL
dHash
|
94e0ac1016060000 |
|
VISUAL
wHash
|
000000c3c3ffffff |
|
VISUAL
colorHash
|
07007000000 |
|
VISUAL
cropResistant
|
2c0c120600000000,949494e6f0e4a4a5 |
Análisis de Código
🔒 Obfuscation Detected
- fromCharCode
- unescape
🎯 Kit Endpoints
- https://d5t1-api.vlhentaiz.com/LoginProcess/
- https://www.facebook.com/policies_center/commerce
- http://fb.me/use-check-prop-types
- http://jedwatson.github.io/classnames
- https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax.pages.dev/assets/index-f75bfe1b.js
- https://www.facebook.com/business/help
- https://api.ipify.org?format=json
- https://reactjs.org/docs/error-decoder.html?invariant=
- https://freeipapi.com/api/json/${e}`).then(t=
📡 API Calls Detected
- https://api.ipify.org?format=json
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 18 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 18 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
index-f75bfe1b.jsSimilar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax.pages.dev
Found 10 other scans for this domain
-
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
https://lmoriw-iekascma-oqmmcq-213-cmakwe-fgacsax....
