
Phishing Analysis
Detailed analysis of captured phishing page
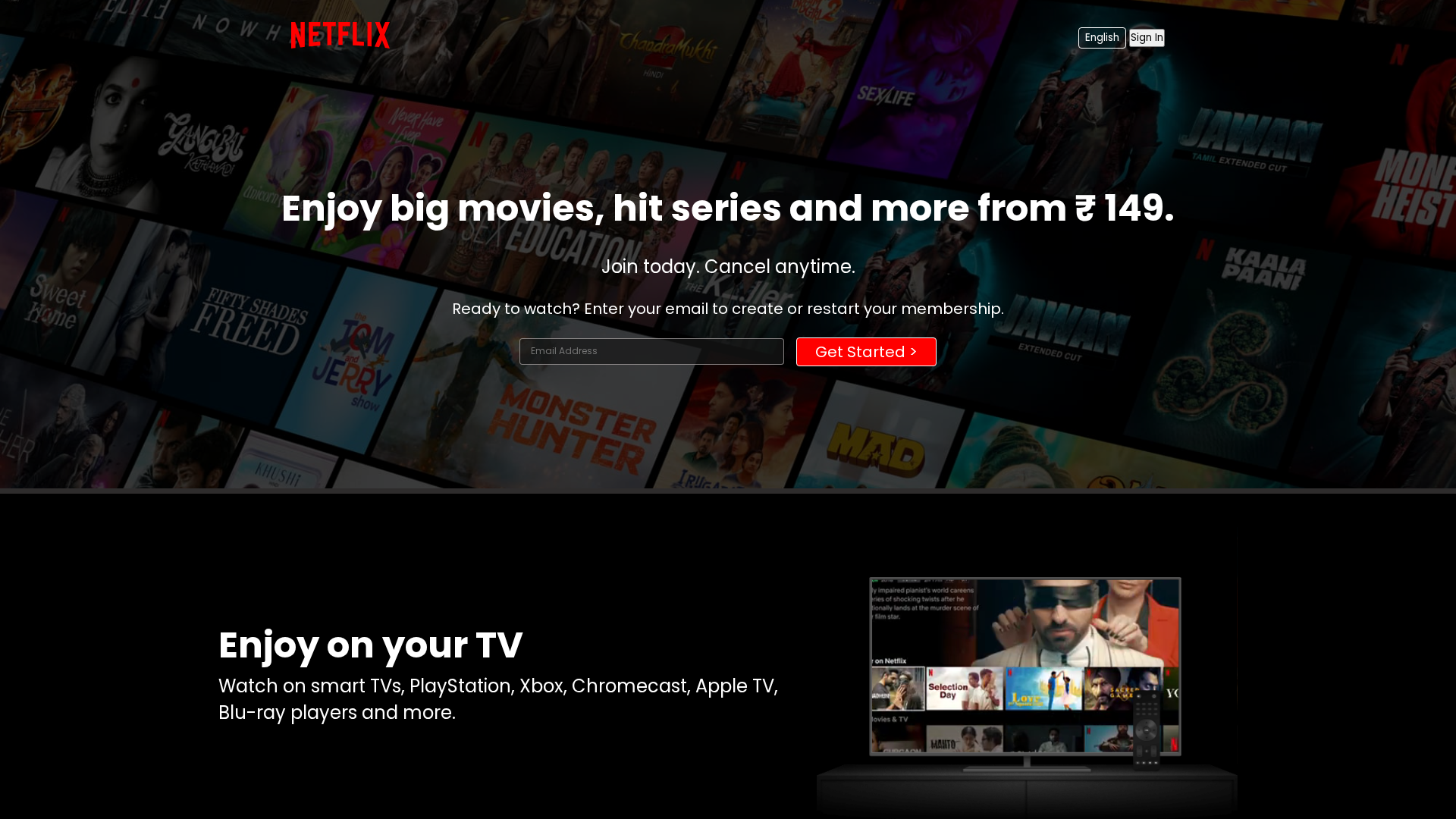
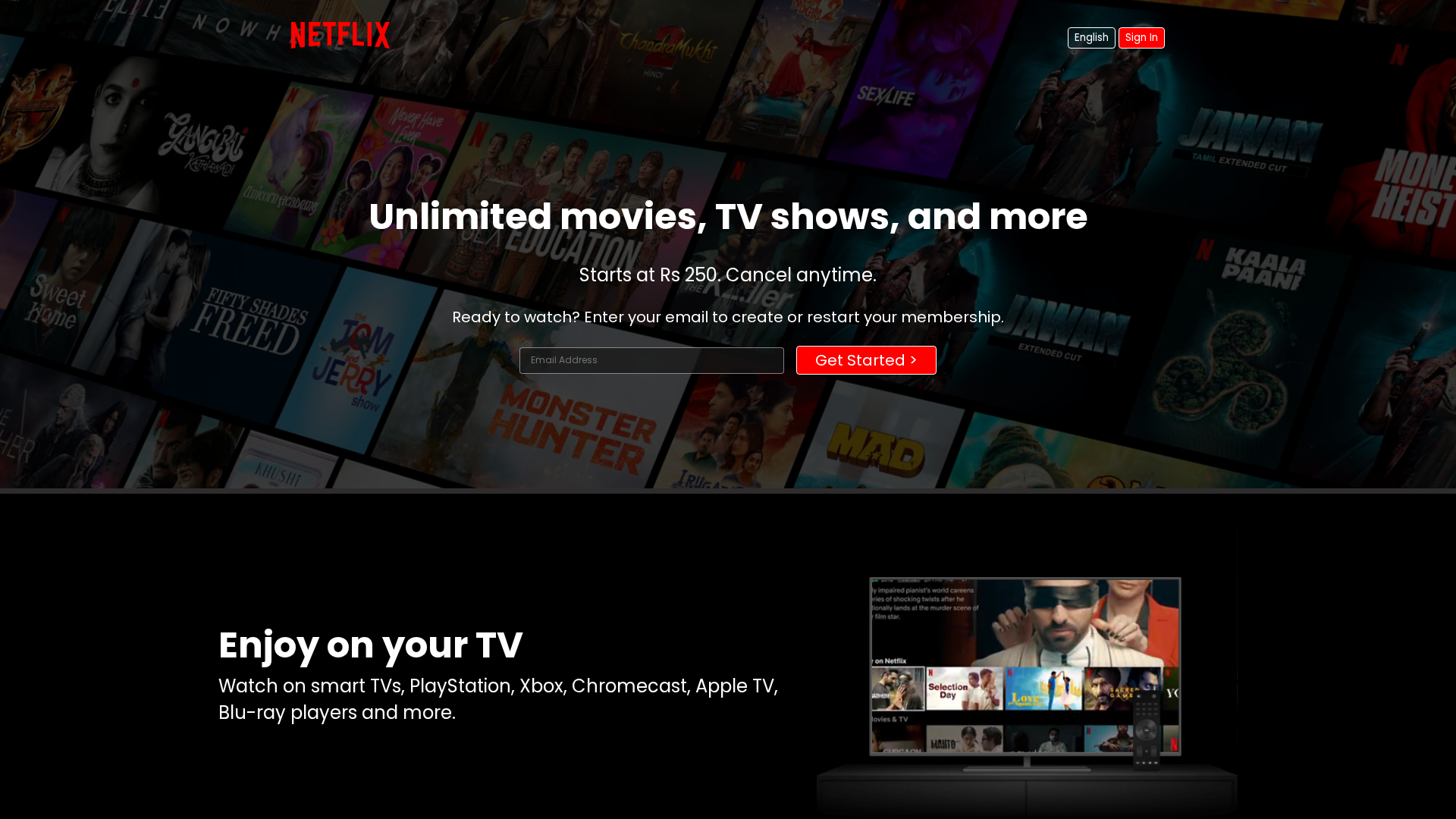
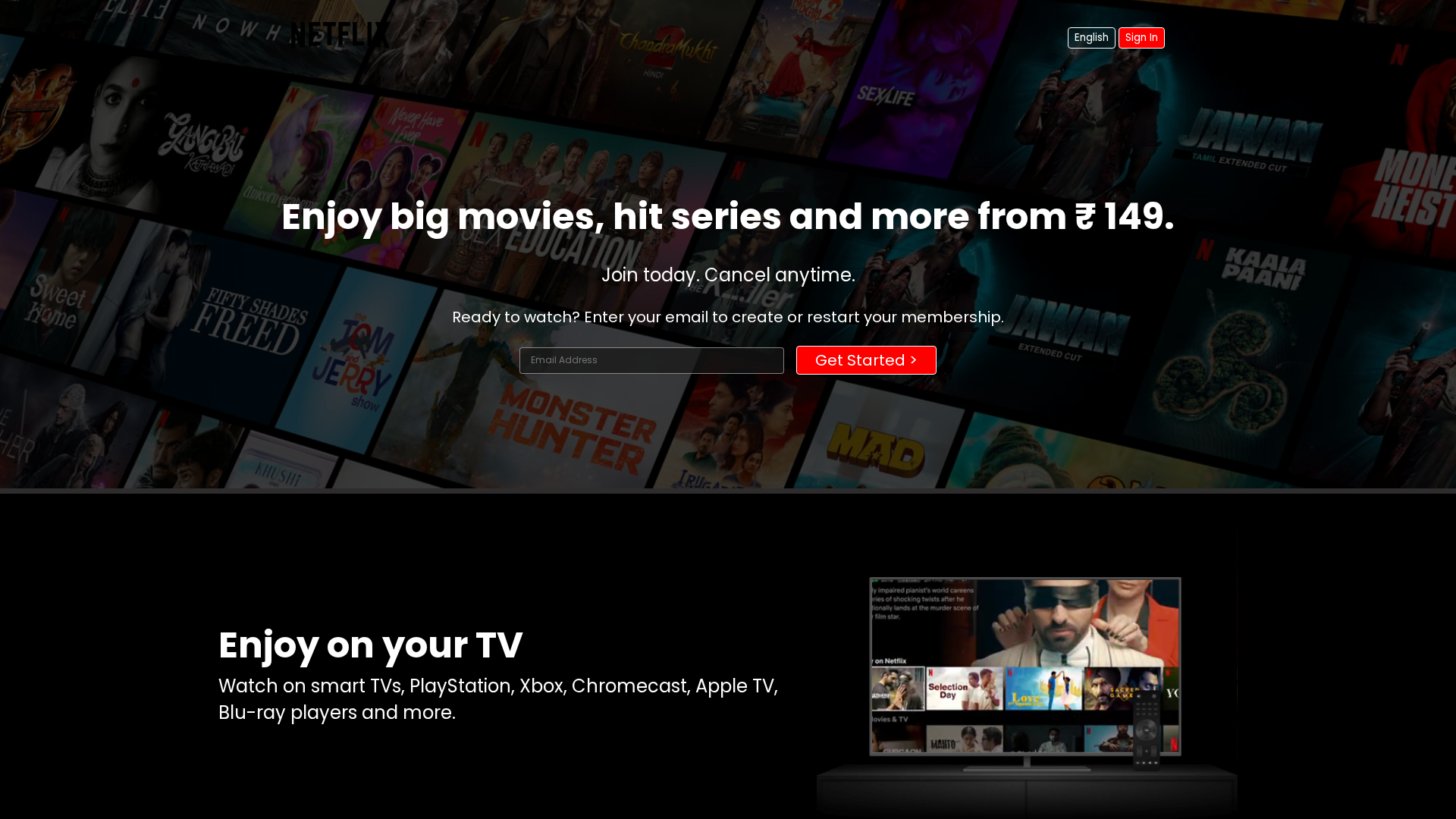
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CE9122B312C5E5270693D2D2B632AB1BB2A3828CDD83176194FDC74C1FD5D56EC53A88 |
|
CONTENT
ssdeep
|
96:TcYK1R6jd7kJLoWKjRzkHo2f9me2RbbwuGN:YYSR6jdkloWKj5kHo2f9me2+vN |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d2c9363469966dd2 |
|
VISUAL
aHash
|
007c7c387c026604 |
|
VISUAL
dHash
|
d4c5f1ebe884cccc |
|
VISUAL
wHash
|
2a7cfc7c7e046606 |
|
VISUAL
colorHash
|
31601008000 |
|
VISUAL
cropResistant
|
e4f43230e4a1a1e0,d4c5f1ebe884cccc |
Análisis de Código
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for pradeep-patel06.github.io
Found 1 other scan for this domain
