
Phishing Analysis
Detailed analysis of captured phishing page
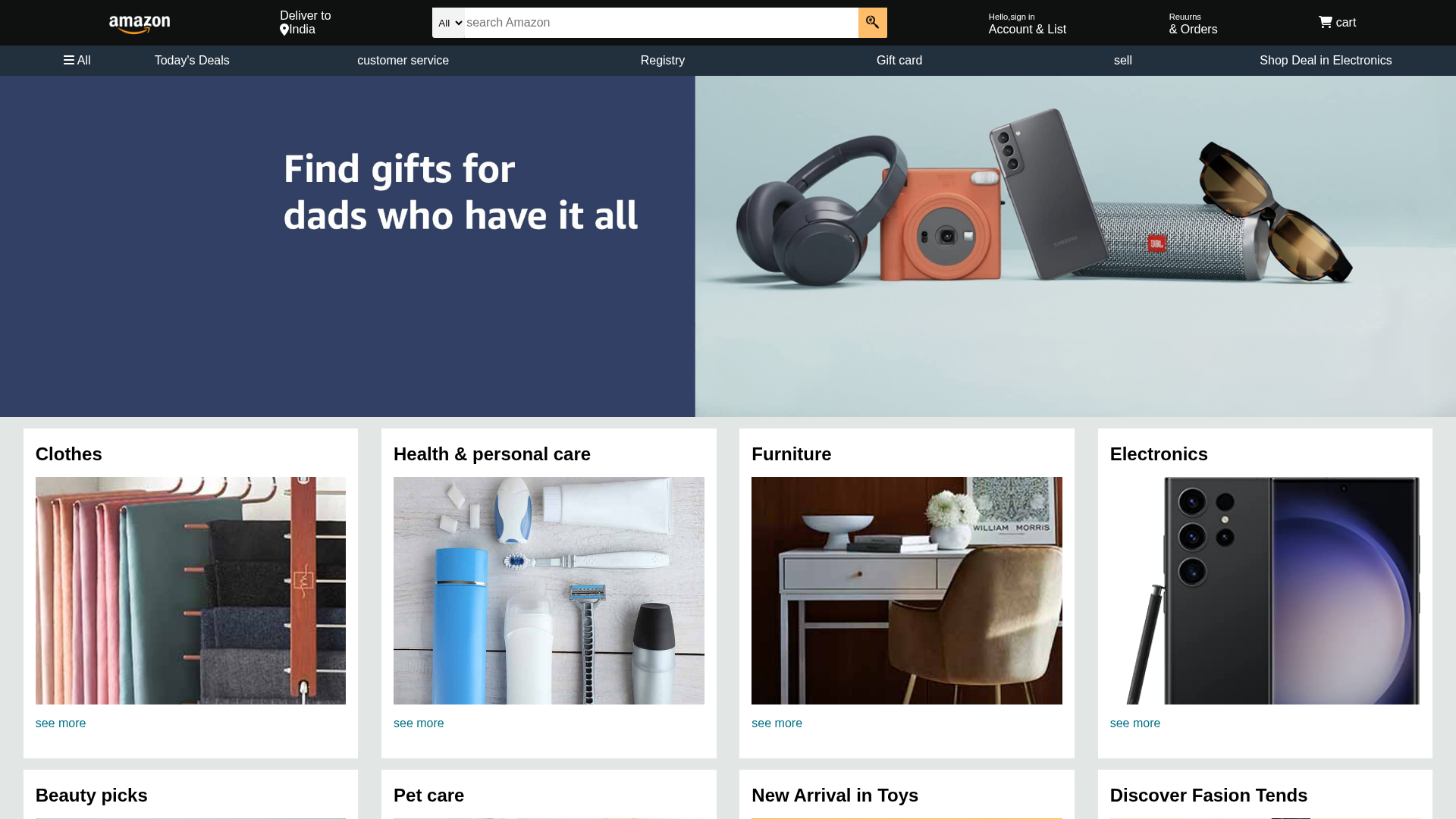
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C68198709042BA3701D3C2D6EF395B9F62C486D4EA435B0A03F4D39D8ADAF9EDD22954 |
|
CONTENT
ssdeep
|
96:TNnJ7rwlX1M08RXL+GpVuIN7XiTN+e5F/9rXGKB:hnJHHiN+e5J9rGKB |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8e194d4e991f4ecc |
|
VISUAL
aHash
|
000f010fff34b3ff |
|
VISUAL
dHash
|
72dbdd1be46565a5 |
|
VISUAL
wHash
|
000f010fffb0b1ff |
|
VISUAL
colorHash
|
07006000000 |
|
VISUAL
cropResistant
|
828262eaeae28282,dbdf599a646565a9,621adbdbcf1d5a5b,d9e6766663697926,4c9736666d595932,adccd9b3b7b7beb6,616c6c5e1e7e7e7c,0d06028206029a9a |
Análisis de Código
📊 Desglose de Puntuación de Riesgo
🔬 Análisis Integral de Amenazas
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Search Engine Manipulation
Fake Amazon site positioned to capture victims through SEO tactics, typosquatting, or paid advertising. Serves as entry point for multi-stage attacks including credential theft and malware distribution.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Scan History for amazon-clone-pi-nine.vercel.app
Found 2 other scans for this domain
