
Phishing Analysis
Detailed analysis of captured phishing page
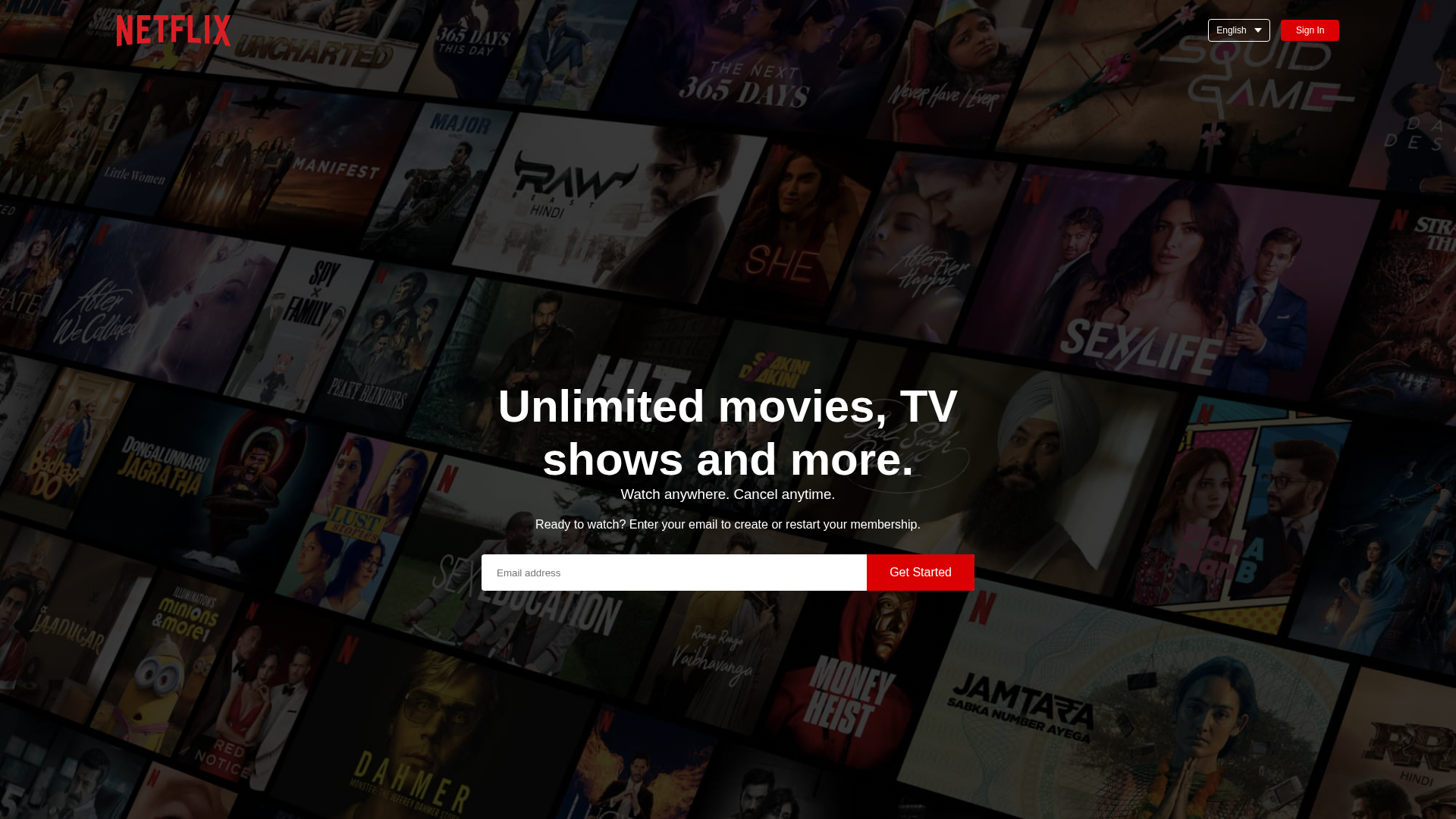
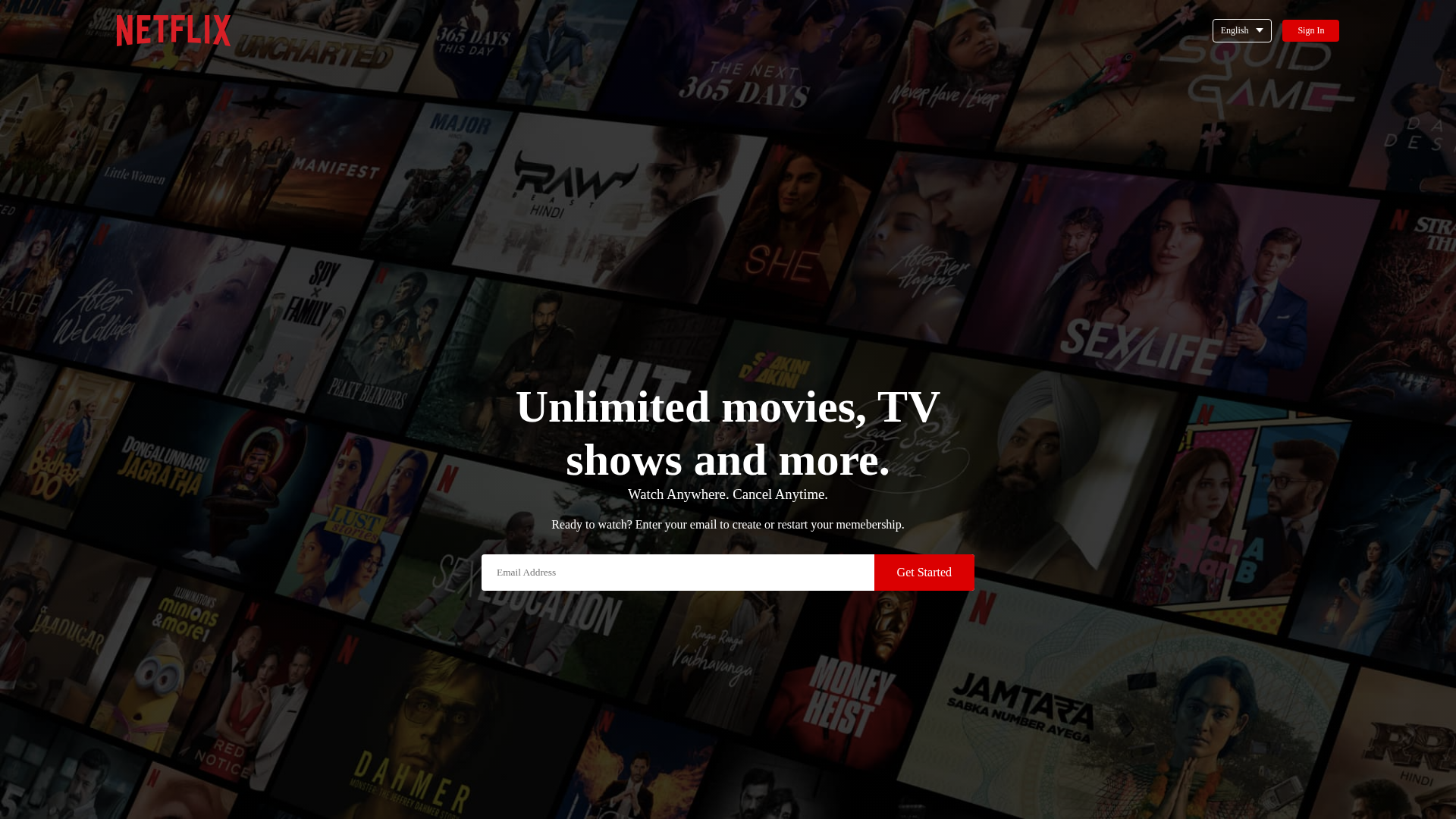
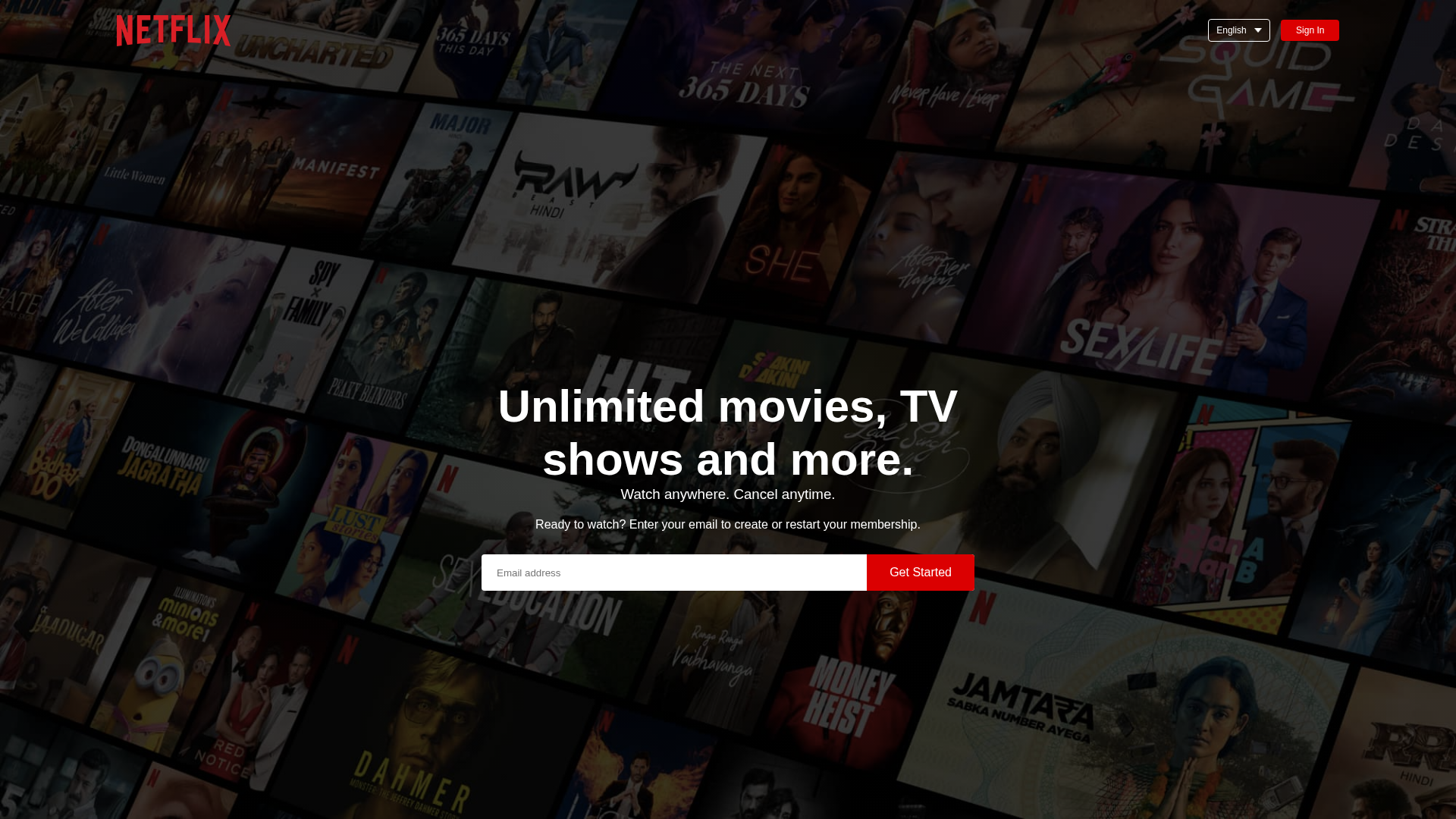
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A0E1A73A5644116F02C343A13B799B2BB7994190E717272824D9834E6FEAE09CD7F3E8 |
|
CONTENT
ssdeep
|
96:nusSIQ7HSmnUAhciW8t9BmRFn8lDUwO4TShBi0fTECCzJ7+/LRg4RK8oAsIp:uv5ymn+wE8lD/9TqACC+Fg4RnoAvp |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6532cd7131cd33 |
|
VISUAL
aHash
|
423060d83c3c0705 |
|
VISUAL
dHash
|
8664aeb272602c0d |
|
VISUAL
wHash
|
c63070fe3e3c8707 |
|
VISUAL
colorHash
|
39e00000000 |
|
VISUAL
cropResistant
|
80c0804040800098,8664aeb272602c0d |
Análisis de Código
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Netflix Credential Harvesting
Fake Netflix login page with 2 forms. Victim enters credentials which are captured and transmitted to attacker's server. Page may impersonate Netflix official login to appear legitimate.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for sekhariam.github.io
Found 2 other scans for this domain
