
Phishing Analysis
Detailed analysis of captured phishing page
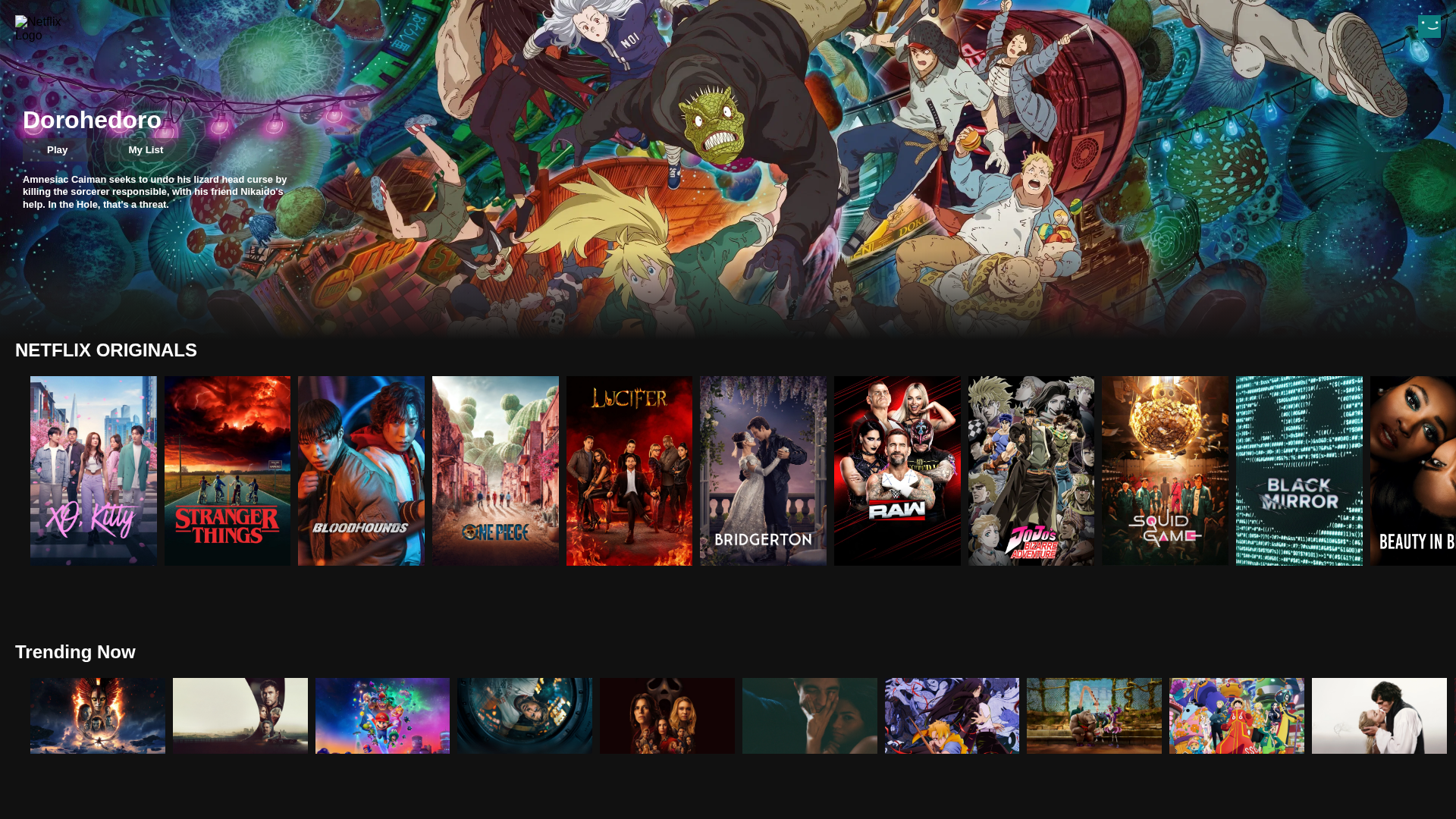
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D7A27FA28D5640DBBB15B2D054172E38AD85CC3F42F24A4CA1BFD2E0F7B69D5EA1D348 |
|
CONTENT
ssdeep
|
192:29rjfQykAn9GWMW56gQjHDnyx99fIz+r3DIruLy:6fQnyAWfQToYaTu |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
92d6a0ffef290c82 |
|
VISUAL
aHash
|
7ffe7c80ff004141 |
|
VISUAL
dHash
|
8abca44e4a748f8f |
|
VISUAL
wHash
|
7ffe7ea0ef004101 |
|
VISUAL
colorHash
|
19201008040 |
|
VISUAL
cropResistant
|
6e64383870b11a6c,60f8f8e28e4c58da,80b6f17940f131f8,86da72ea9ab0b2b2,a5a6a6868d8d8989,8abca44e4a748f8f |
Análisis de Código
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- https://images-wixmp-ed30a86b8c4ca887773594c2.wixmp.com/f/12c6f684-d447-4457-84fa-12033cfd581e/d9z3o32-2c299a83-49a9-44c2-bc23-b0b5070a546b.png/v1/fill/w_1024,h_512,strp/netflix_logo_background__2_by_sixmonthslate_d9z3o32-fullview.png?token=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiJ1cm46YXBwOiIsImlzcyI6InVybjphcHA6Iiwib2JqIjpbW3siaGVpZ2h0IjoiPD01MTIiLCJwYXRoIjoiXC9mXC8xMmM2ZjY4NC1kNDQ3LTQ0NTctODRmYS0xMjAzM2NmZDU4MWVcL2Q5ejNvMzItMmMyOTlhODMtNDlhOS00NGMyLWJjMjMtYjBiNTA3MGE1NDZiLnBuZyIsIndpZHRoIjoiPD0xMDI0In1dXSwiYXVkIjpbInVybjpzZXJ2aWNlOmltYWdlLm9wZXJhdGlvbnMiXX0.WKy-rj_8y7ziLuhhtAES7jddy-eUpz6PQQ331bp7rRI
☁️ Cloud Backend
- Firebase: netflix-clone-fcedd.firebaseapp.com
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking
- 10 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 10 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
