
Phishing Analysis
Detailed analysis of captured phishing page
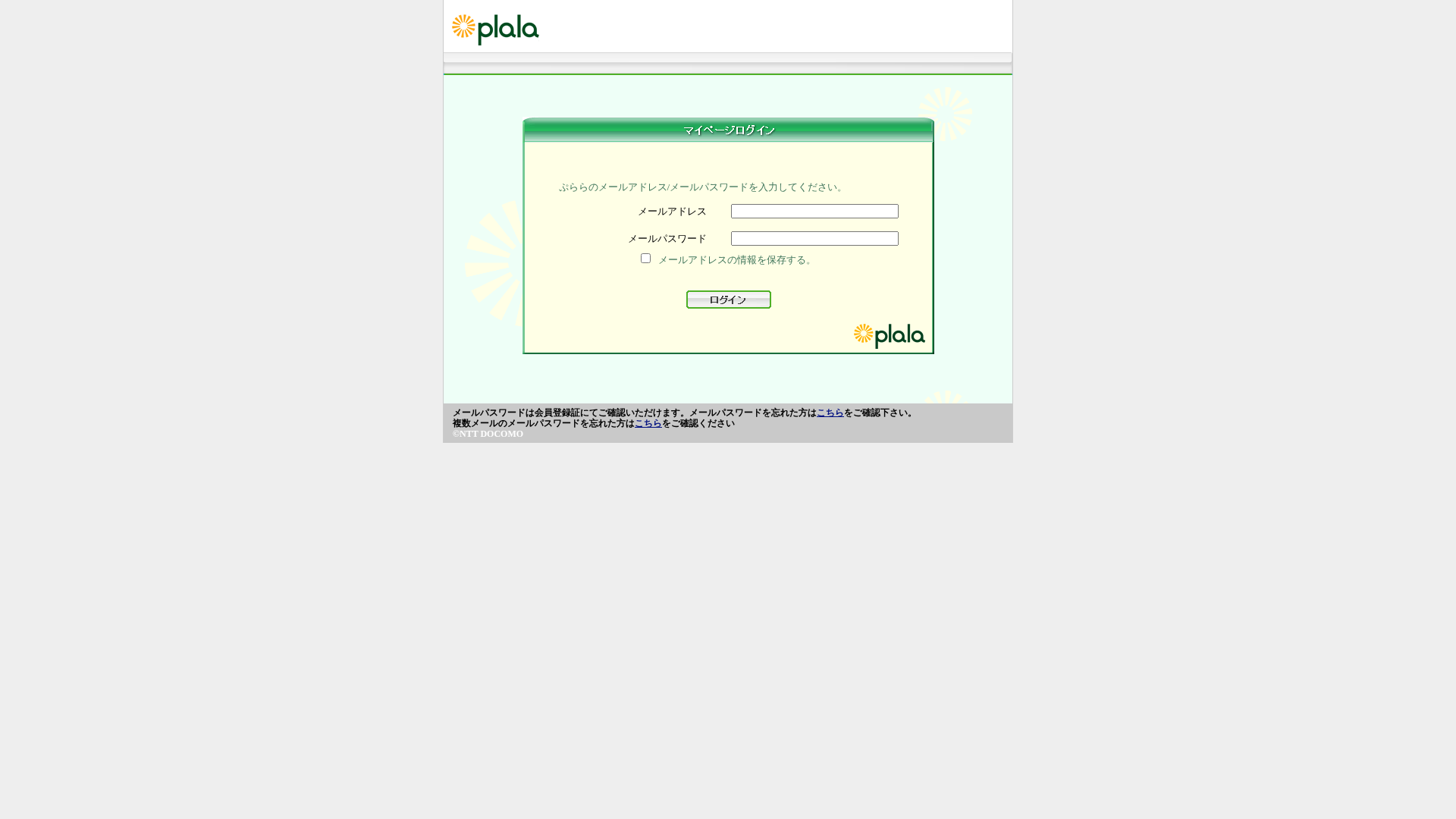
Captura Visual
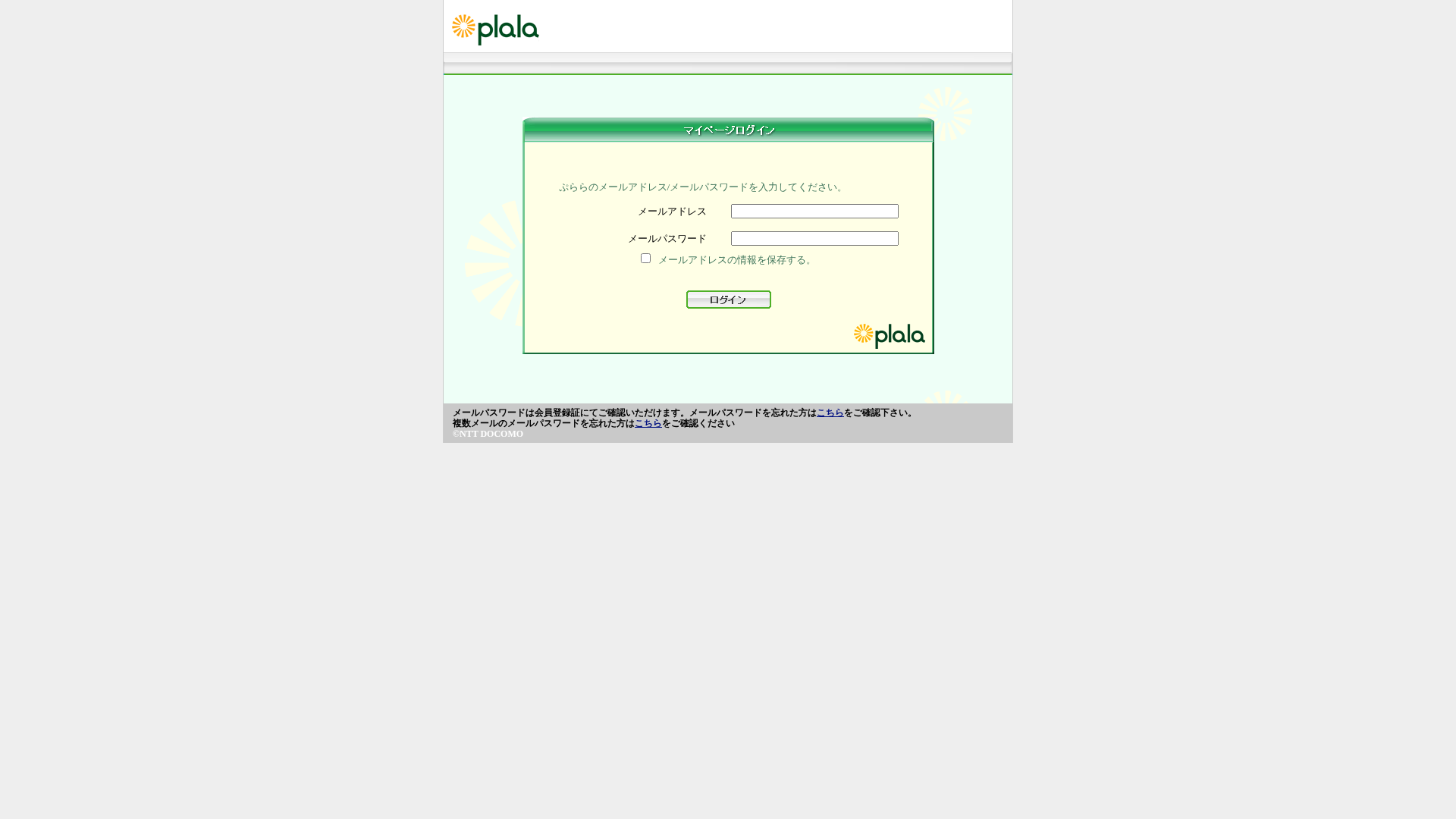
Información de Detección
https://salalatour.com//updateplala.or.jp/jpn/webmai1/index.php
Detected Brand
plala
Country
Japan
Confidence
100%
HTTP Status
200
Report ID
f4f45767-80a…
Analyzed
2026-03-19 10:28
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13FA1101813853B4F99A552A3D3752E9493E2941EC7324D48A85EE72F1C8814EEC7FAFC |
|
CONTENT
ssdeep
|
96:L3ydpoIL/N+lglAtyHL5ZiNr2t5CLJWfsT3yDSxyHJHAPboRbDY7YoDSZHlfd5D:c2kcRMgc0QD |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b29e9a3131dccc99 |
|
VISUAL
aHash
|
dfe7bdc3c3ffefff |
|
VISUAL
dHash
|
394c68049e600800 |
|
VISUAL
wHash
|
1c243c3cc0d0fcfc |
|
VISUAL
colorHash
|
07018000600 |
|
VISUAL
cropResistant
|
394c68049e600800 |
Análisis de Código
Risk Score
74/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Amenaza: Phishing de credenciales
• Objetivo: Usuarios de plala
• Método: Impersonación a través de formulario de inicio de sesión
• Exfil: cgi-binsso/pf/agent_sso.php
• Indicadores: Formulario, Obfuscación, Envío de formulario JavaScript
• Riesgo: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- hex_escape
- base64_strings
📤 Form Action Targets
- cgi-binsso/pf/agent_sso.php
📊 Desglose de Puntuación de Riesgo
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain is completely unrelated to the brand being impersonated.
Presence of a Login Form
The page has a login form, a common phishing tactic.
Obfuscation
Obfuscation detected in the Javascript. Indicates an attempt to hide malicious code
Impersonation
The site mimics the appearance of a legitimate brand.
🔬 Análisis Integral de Amenazas
Tipo de Amenaza
Banking Credential Harvester
Objetivo
plala users (Japan)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltración
HTTP POST to backend
Evaluación de Riesgo
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 126 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Impersonated Brand
plala
Fake Service
Login Portal
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by presenting a fake login form that mimics plala's login page.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Domain
salalatour.com
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Plala
http://salalatour.com/updateplala.or.jp/jpn/webmai1/index.ph...
Abr 01, 2026
Plala
http://salalatour.com/plala.or.jp/jpn/webmai1/index.php
Abr 01, 2026
Plala
http://marutitraders99.com/plalaa/jpn/webmai1/index.php
Mar 31, 2026
Plala
http://marutitraders99.com/plalaa/jpn/webmai1/index.php
Mar 30, 2026
Plala
http://nisha-interiors.com/plala.orr/jpn/webmai1/index.php
Mar 27, 2026
Scan History for salalatour.com
Found 8 other scans for this domain
-
http://salalatour.com/updateplala.or.jp/jpn/webmai...
http://salalatour.com/plala.or.jp/jpn/webmai1/inde...
https://salalatour.com//plala.or.jp/jpn/webmai1/in...
https://salalatour.com//plala.or.jp/jpn/webmai1/in...
https://salalatour.com//updateplala.or.jp/jpn/webm...
https://salalatour.com/plala.or.jp/jpn/webmai1/ind...
https://salalatour.com/updateplala.or.jp/jpn/webma...
https://salalatour.com/plala.or.jp/jpn/webmai1/ind...

"Nunca pensé que me pasaría a mí"
Esto dicen las 2.3 millones de víctimas cada año. No esperes a ser una estadística.