Phishing Analysis
Detailed analysis of captured phishing page
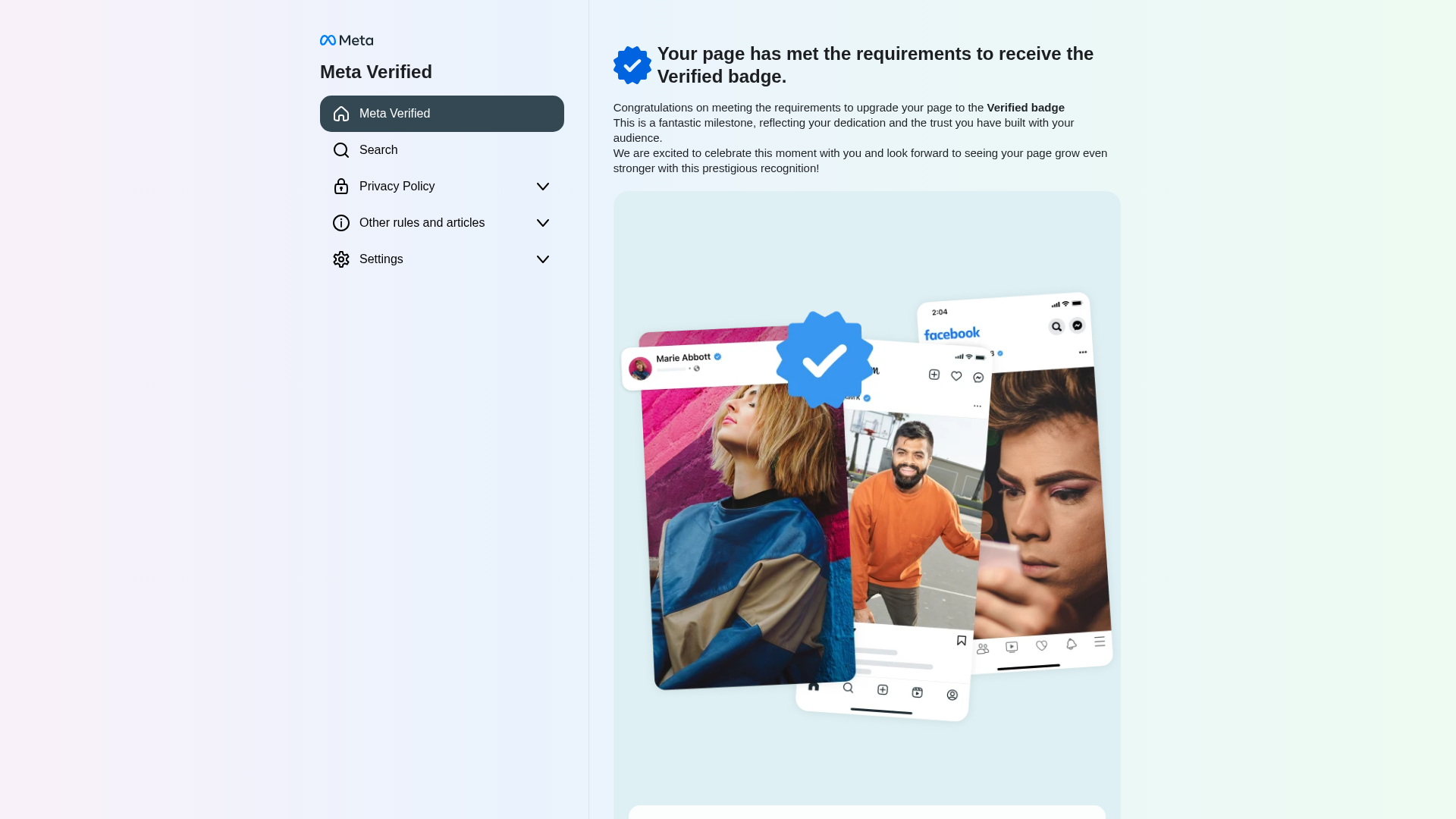
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E17384B1521DA6BE41C7C2E897770B5A33A9C6D4E723012466FC93B80FEBC96DE27150 |
|
CONTENT
ssdeep
|
1536:u2Rk9FAYNbXIAV8MxXNQpfmpqC6XE2Qjxmp1o7x:u8+6MrIAGMxXNQpfml6XEVjxmHo7x |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6989866d992c5c7 |
|
VISUAL
aHash
|
c7cfffe3e3e1e3ff |
|
VISUAL
dHash
|
3e3e2c0b4e4f4f12 |
|
VISUAL
wHash
|
838383e3e1e1e3e3 |
|
VISUAL
colorHash
|
07601000040 |
|
VISUAL
cropResistant
|
3e3e2c0b4e4f4f12,801024e46430c000,08223c386031652c,cd4d4dac2f6fad3c |
Análisis de Código
🔬 Threat Analysis Report
• Amenaza: Phishing
• Objetivo: Usuarios de Facebook
• Método: Suplantación para robar datos o credenciales
• Exfil: Potencialmente varía, basado en formularios y acciones ocultas.
• Indicadores: Dirección IP, JS Ofuscado, Promete una Insignia Verificada
• Riesgo: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- http://185.199.224.13/server_process_data.php
📡 API Calls Detected
- https://ipapi.co/json/
- https://ipinfo.io/json?token=0916643fd922ec
- ../../server_process_data.php
📤 Form Action Targets
- //translate.googleapis.com/translate_voting?client=te
- https://transparency.meta.com/vi-vn/policies/community-standards
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 20454 obfuscation techniques
🏢 Análisis de Suplantación de Marca
Fraudulent Claims
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
The site impersonates Meta/Facebook and tricks users into providing their login credentials or other sensitive information.
Secondary Method: Social Engineering
The site uses a 'Verified Badge' to lure users, creating a sense of urgency or reward.
🌐 Indicadores de Compromiso de Infraestructura
🦠 Malicious Files
Functions: buildAndSend, sendToServer, setForm1
🔌 External APIs Abused
- account: None
- purpose: to retrieve user IP and location information for exfiltration
📊 Diagrama de Flujo de Ataque
User fills <input name='full-name'> → setForm1() → buildAndSend() → fetch(http://185.199.224.13/server_process_data.php) → exfiltration of user data
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : None
- : Moderate
- : Moderate
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='full-name'> → setForm1() → buildAndSend() → fetch(http://185.199.224.13/server_process_data.php) → exfiltration of user data
🎯 Malicious Files Identified
config_sys.jsMalicious Functions
buildAndSendsendToServersetForm1
🌐 External APIs Abused
-
ipapi
Propósito: to retrieve user IP and location information for exfiltration
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for 185.199.224.13
Found 4 other scans for this domain