Phishing Analysis
Detailed analysis of captured phishing page
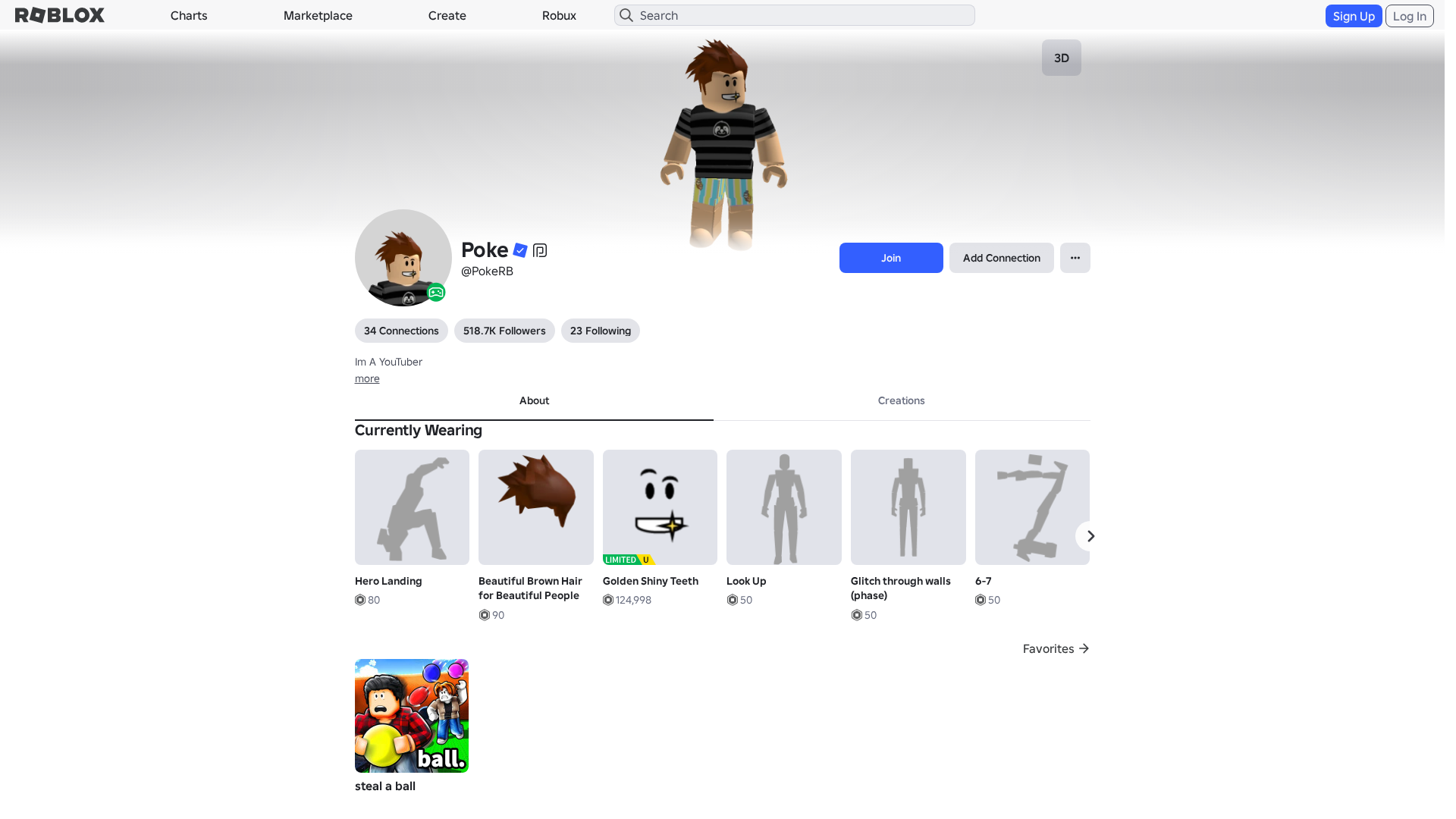
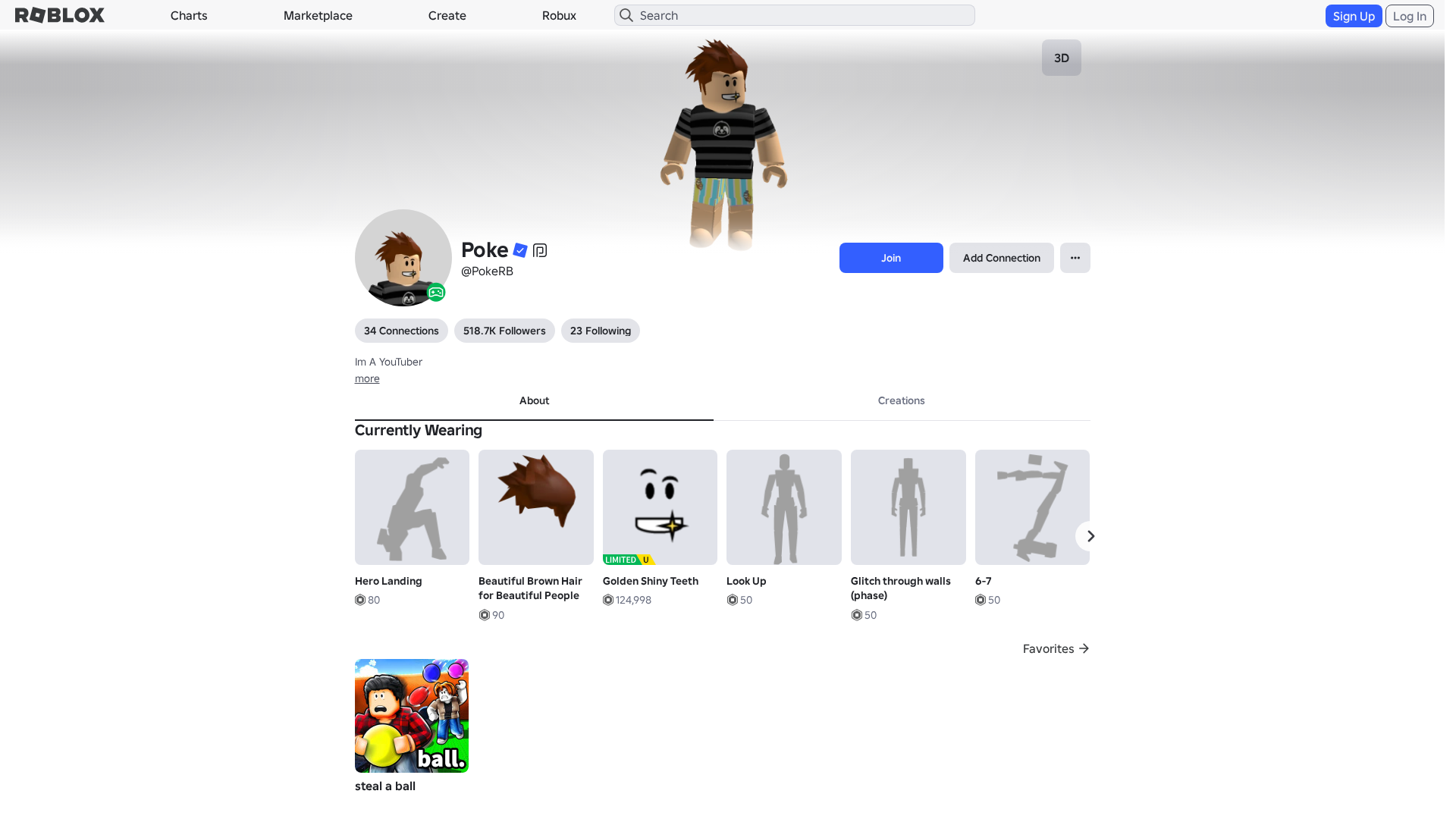
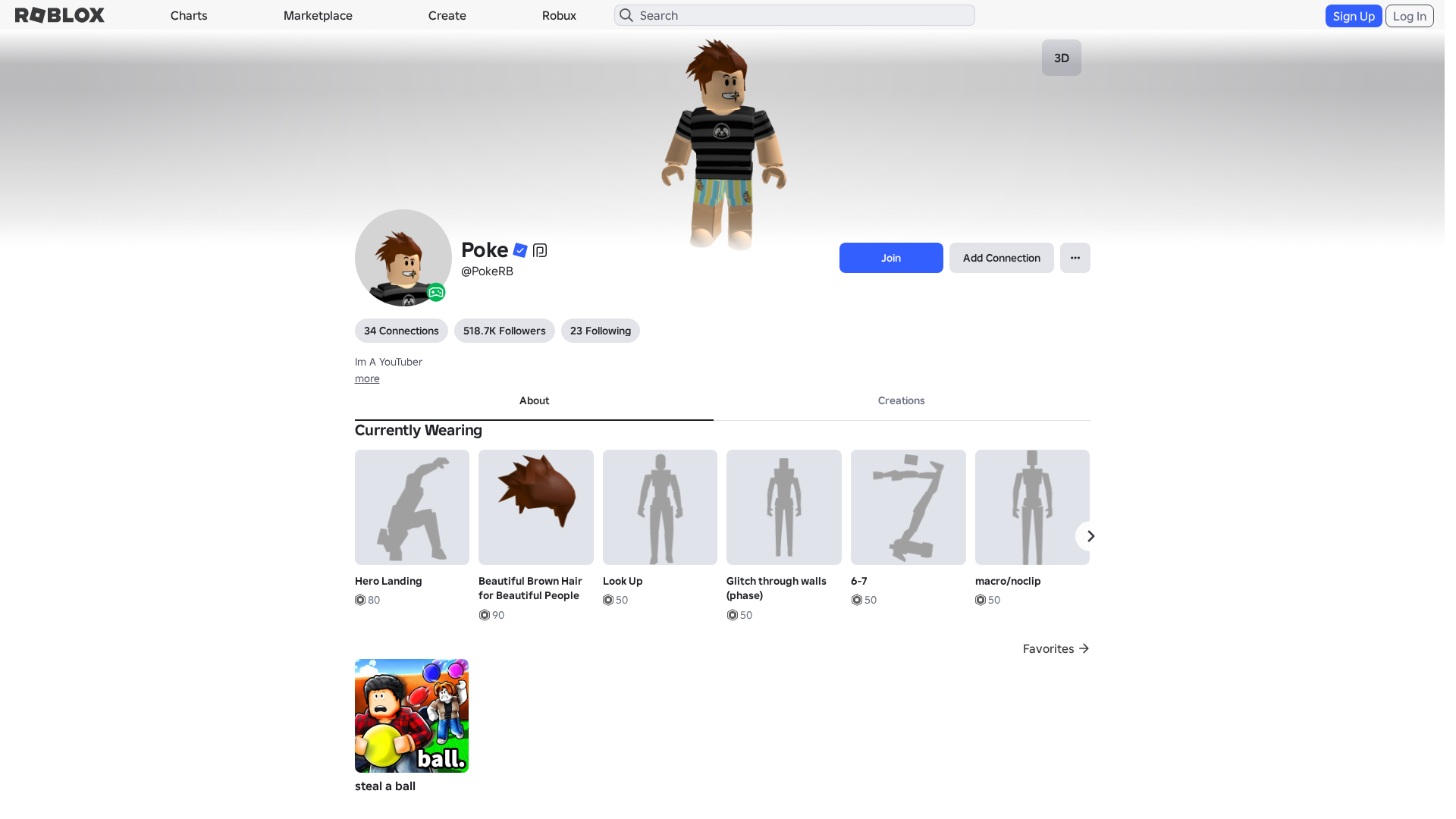
Captura Visual
Información de Detección
Hashes de Contenido (Similitud HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12663537291142837617B79DAF064672AD2D3D70FCA8346E1A2FC939A0FDACE1E95340D |
|
CONTENT
ssdeep
|
1536:xAfXWn+rs/AexLsgs/gWagaygCSg8Ggq2gm4gIsgIhgkrgJ3gAvg2jg+TgLNgI2Z:efXWx/A5eGoieC2HAh3vE5Yj7P6Q |
Hashes Visuales (Similitud de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc430663999cecbc |
|
VISUAL
aHash
|
0000d3ffc3c3dfdf |
|
VISUAL
dHash
|
e8c8263096163030 |
|
VISUAL
wHash
|
0000c3cfc3c3dfdf |
|
VISUAL
colorHash
|
07400010040 |
|
VISUAL
cropResistant
|
e8c8263096163030 |
Análisis de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/86500078/Man-Right-Leg
- https://api.injuries.lu/catalog/17877340/Beautiful-Brown-Hair-for-Beautiful-People
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/106367055475970/6-7
- https://api.injuries.lu/catalog/135495007276592/SLOTH-SZN-SECRET-BLACK
- https://api.injuries.lu/catalog/86500036/Man-Right-Arm
- https://api.injuries.lu/catalog/5104377791/Hero-Landing
- https://api.injuries.lu/catalog/107583431008996/Golden-Shiny-Teeth-Head
- https://api.injuries.lu/catalog/86500054/Man-Left-Arm
- https://api.injuries.lu/catalog/86500008/Man-Torso
- https://api.injuries.lu/catalog/3360689775/Salute
- https://api.injuries.lu/catalog/17093030399/Sloth-Shorts-Season-4
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F286858877668%2Fprofile
- https://api.injuries.lu/catalog/74986315009518/Golden-Shiny-Teeth-Mood
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F286858877668%2Fprofile
- /login?returnUrl=
- https://api.injuries.lu/catalog/135023653330251/Look-Up
- https://api.injuries.lu/catalog/132366431744296/Glitch-through-walls-phase
- https://api.injuries.lu/catalog/107939524113763/macro-noclip
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/3696759798/Superhero-Reveal
- https://api.injuries.lu/catalog/137006085779408/Speed-Glitch
- https://api.injuries.lu/catalog/86500064/Man-Left-Leg
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev/api/shorten
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://ro.blox.com/Ebh5?
- https://apis.
- get
- POST
- /api/shorten
- https://kyxn.dev${e.endpoint}
- /api/pageview
📤 Form Action Targets
- /search
📊 Desglose de Puntuación de Riesgo
Contributing Factors
🔬 Análisis Integral de Amenazas
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Análisis de Suplantación de Marca
⚔️ Metodología de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromiso de Infraestructura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for rblox.me
Found 4 other scans for this domain