
Phishing Analysis
Detailed analysis of captured phishing page
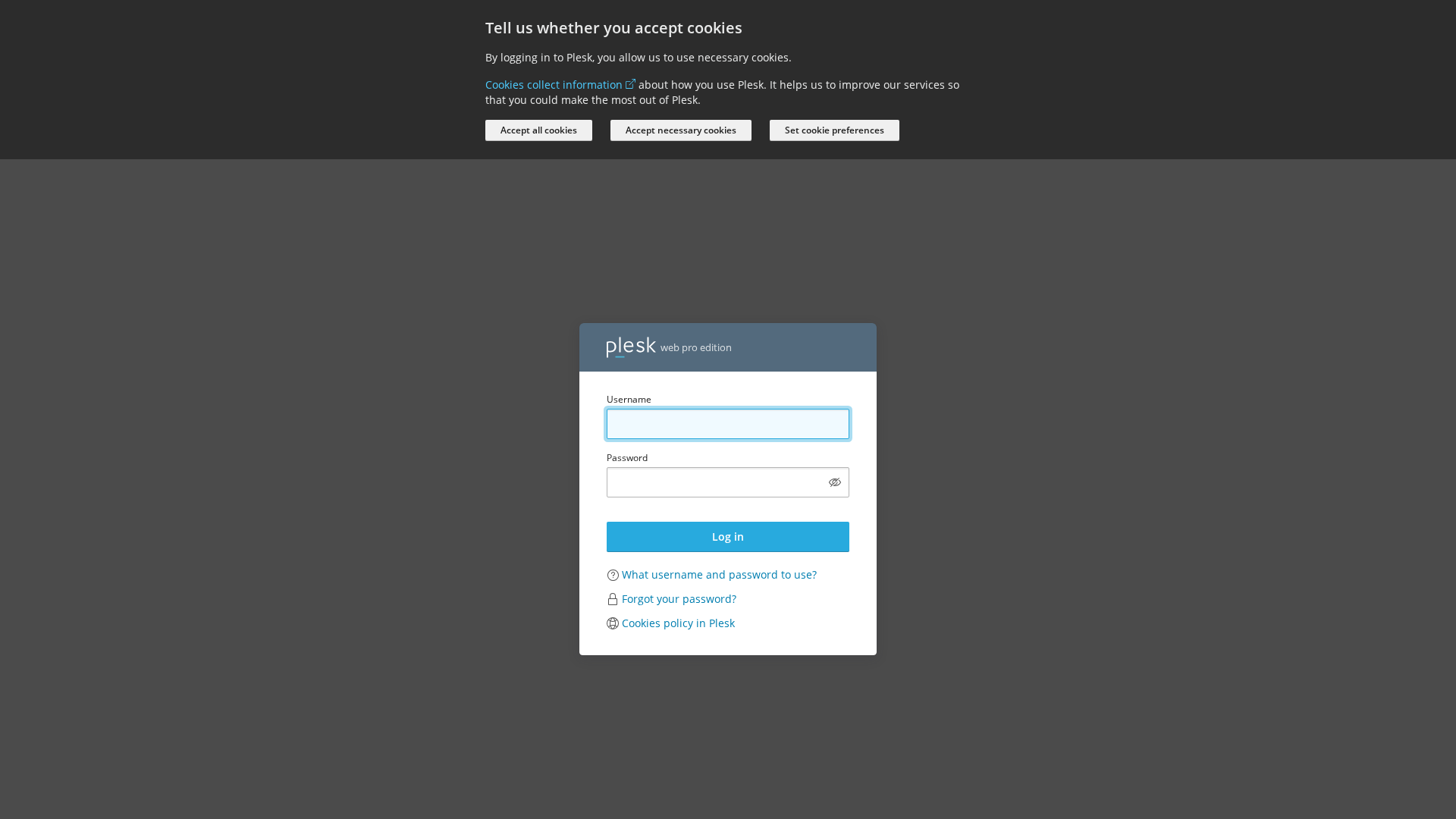
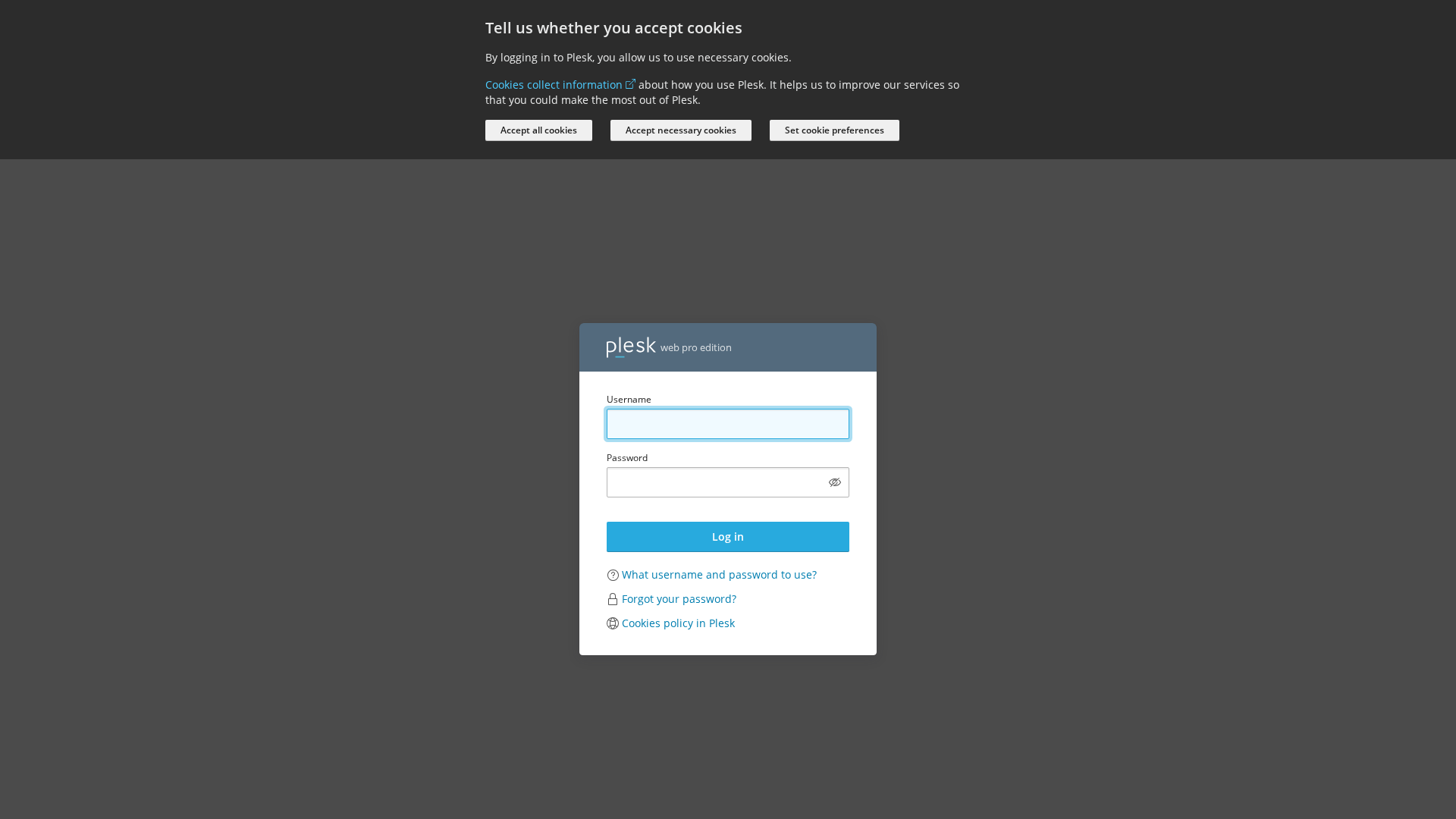
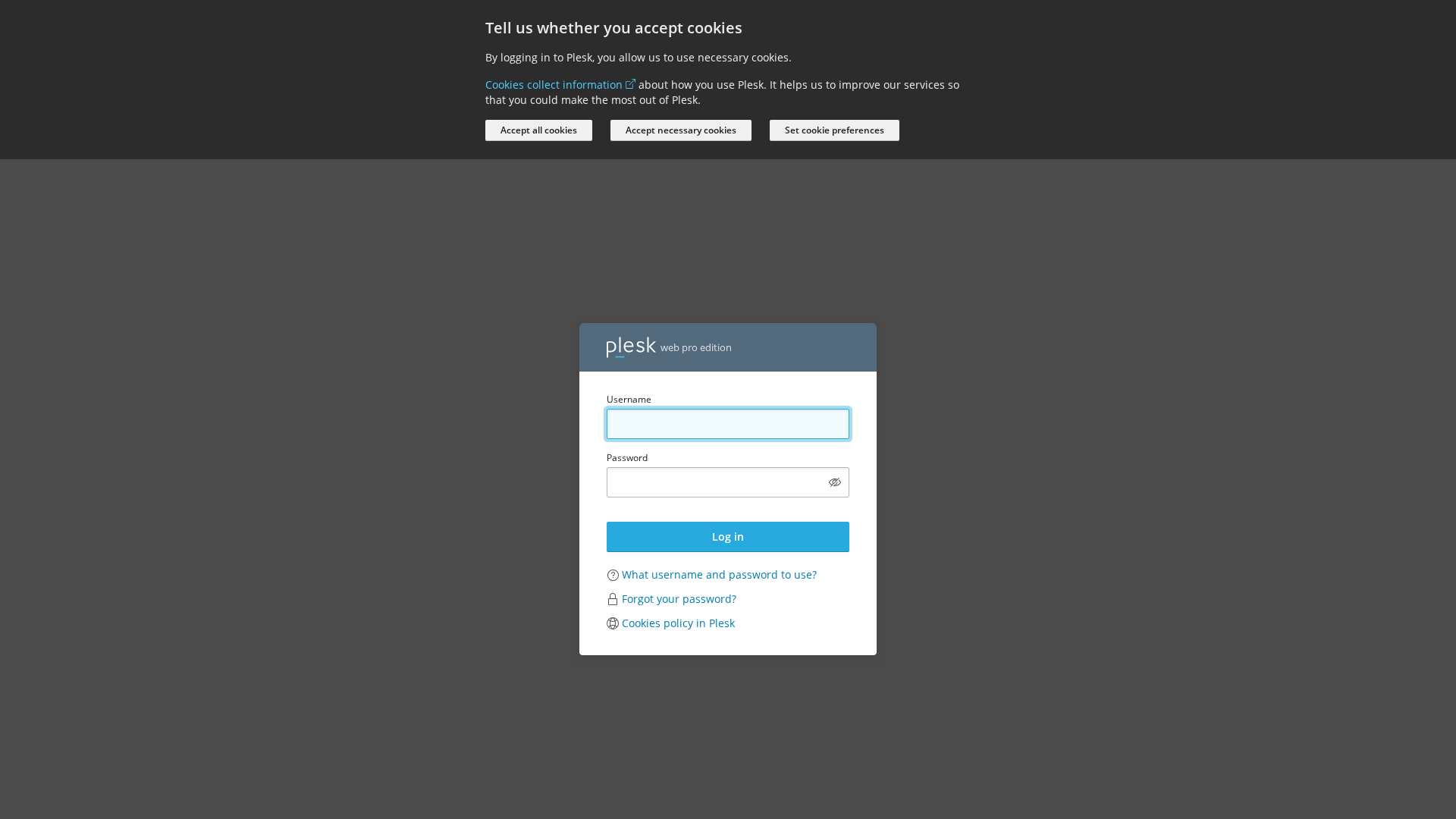
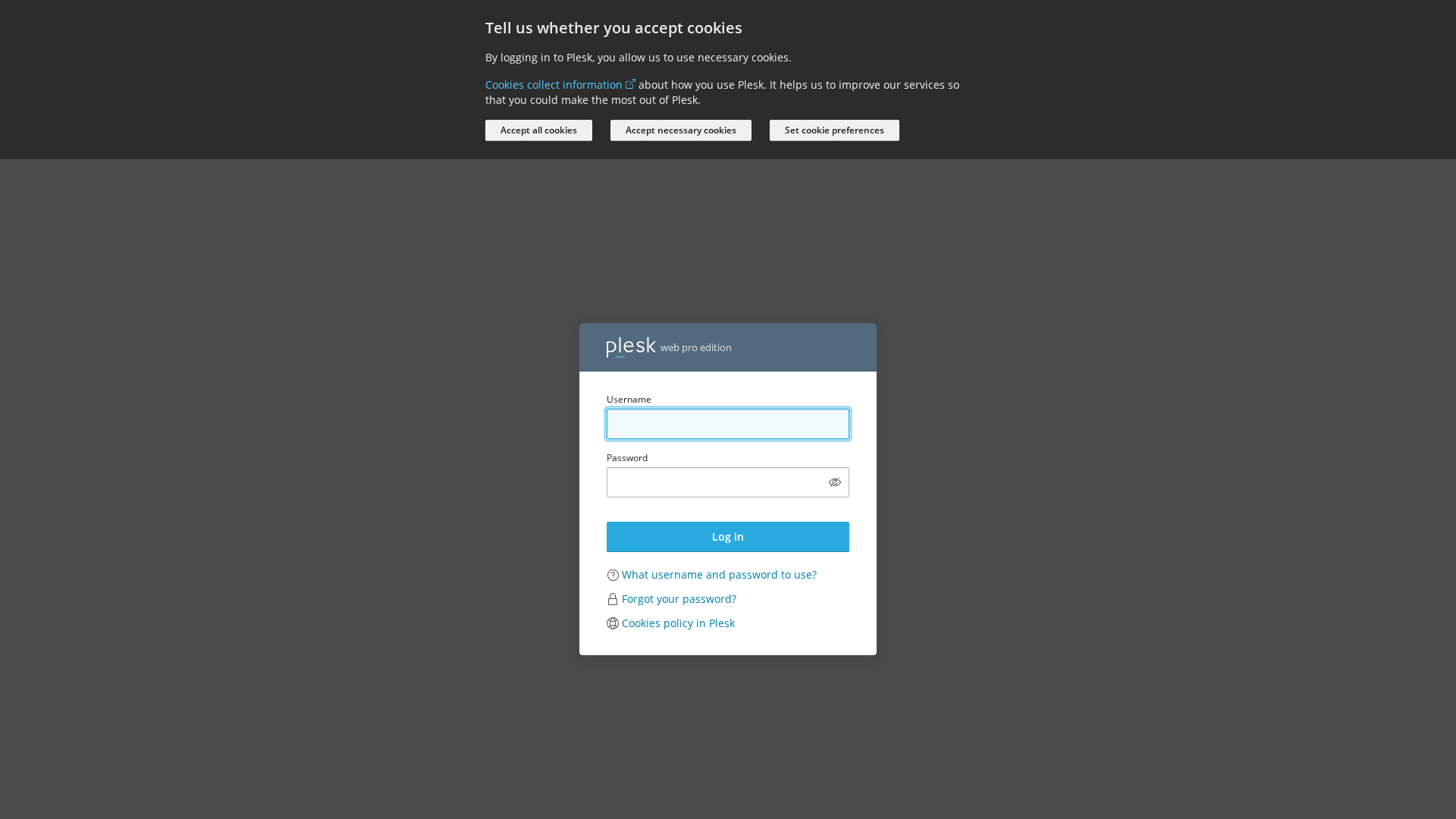
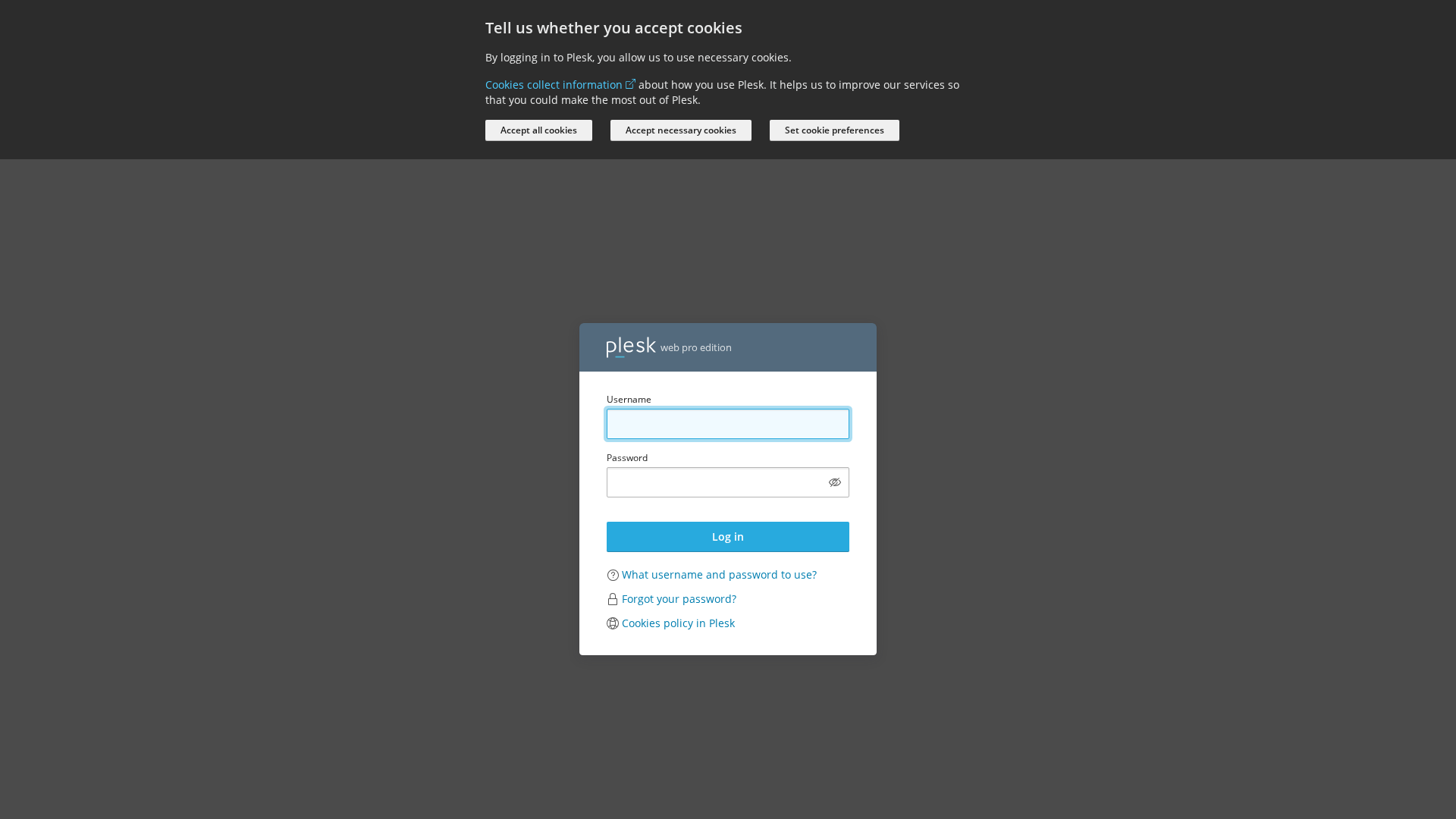
Captura Visual
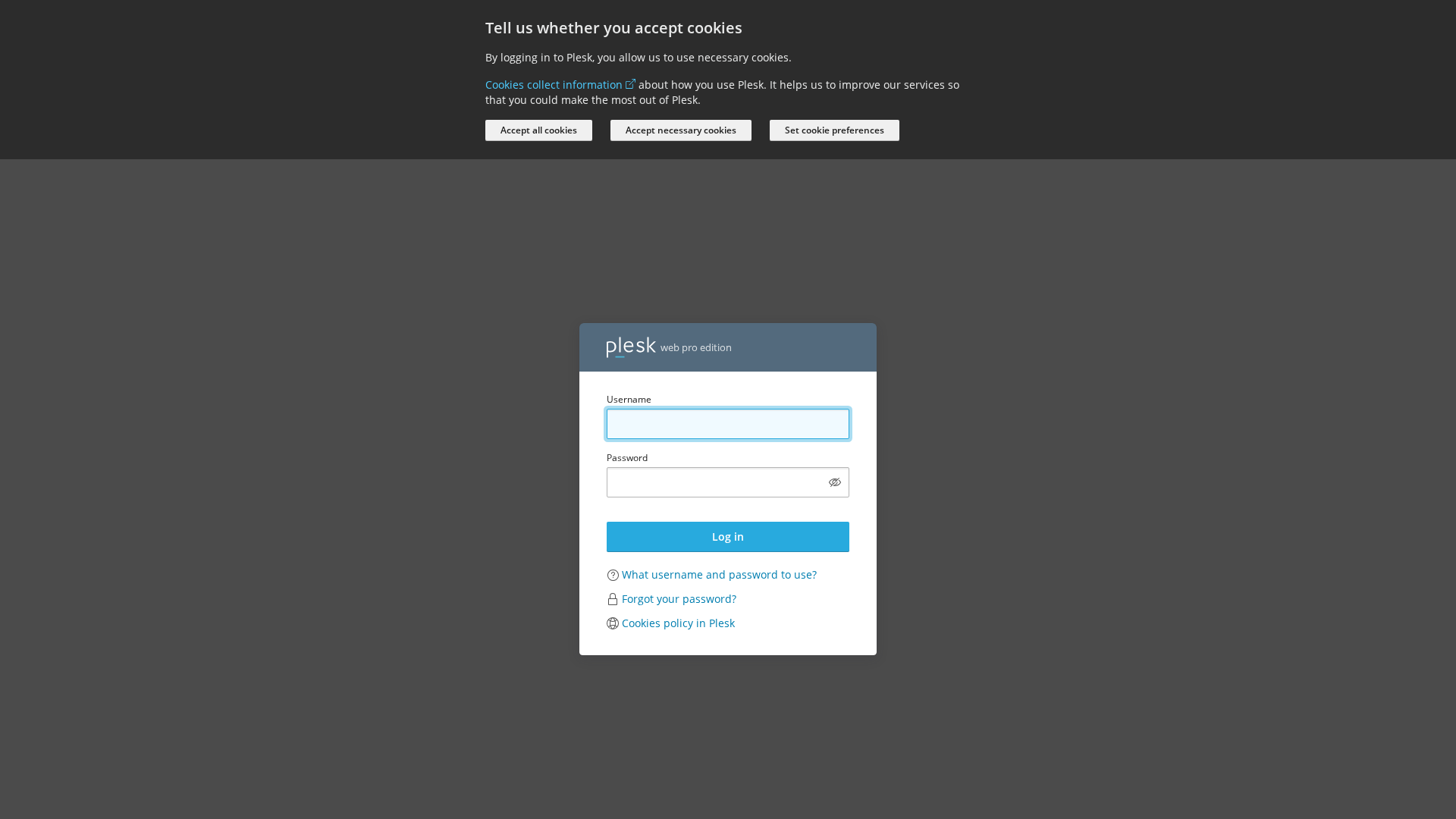
Informações de Detecção
https://sncf.service-avantage.com/?wl=Ks93KqA9Ln12
Detected Brand
SNCF
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
012a2307-e3d…
Analyzed
2026-04-03 11:25
Final URL (after redirects)
https://sncf.service-avantage.com/login_up.php?success_redirect_url=%2F%3Fwl%3DKs93KqA9Ln12
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T176F1FC32644CEC3B23235BD1B492B705E2D6C66ECA421610D6BC439D0FFBEE2E44265B |
|
CONTENT
ssdeep
|
192:EHCJ+kYMHSTCuCgEGCBdDxe8LTjKkrfjg1r9j3rr7dv:WCJ+kR+3jjCxe8LTjKkrfjg1r9j3rr7J |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6666cc5c763233 |
|
VISUAL
aHash
|
0018001818181800 |
|
VISUAL
dHash
|
62724cb2b2b2b24c |
|
VISUAL
wHash
|
001810183c3c1c1c |
|
VISUAL
colorHash
|
07007000080 |
|
VISUAL
cropResistant
|
e2a2e28033b2b8b8,62724cb2b2b2b24c |
Análise de Código
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- log-in
- https://support.plesk.com/hc/en-us/articles/12377667582743-How-to-log-in-to-Plesk-
- /logout.php
- /login_up.php?modals[cookie-policy-preferences]=true
- ${(0,m.default)(`/admin/report/download/file/${encodeURIComponent(n.file)}`)}
📡 API Calls Detected
- /admin/copilot/stat
- GET
- /admin/copilot/gen-answer
- /modules/notifier/index.php/notifications
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 11 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 103 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
SNCF users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 103 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
SNCF
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 103 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
sncf.service-avantage.com
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/c5b4862273b1.png
Abr 03, 2026
Unknown
https://cdn.gosafemode.com/screenshots/1b9453a733ed.png
Abr 03, 2026
Unknown
https://cdn.gosafemode.com/screenshots/1a8df245dccd.png
Abr 03, 2026
Unknown
https://cdn.gosafemode.com/screenshots/5b7110340dfc.png
Abr 03, 2026
Unknown
https://cdn.gosafemode.com/screenshots/1519accbd074.png
Abr 03, 2026

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.