
Phishing Analysis
Detailed analysis of captured phishing page
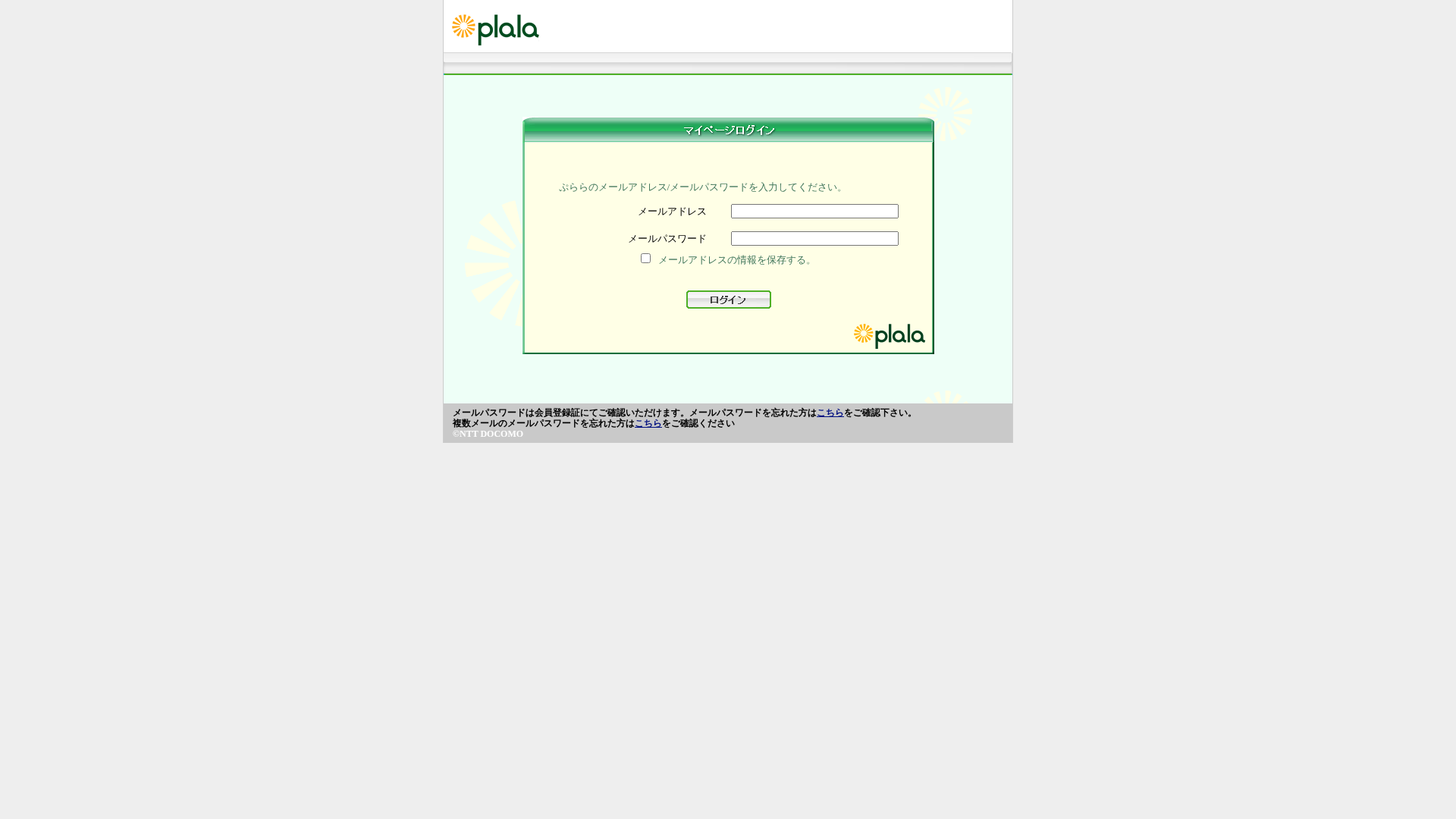
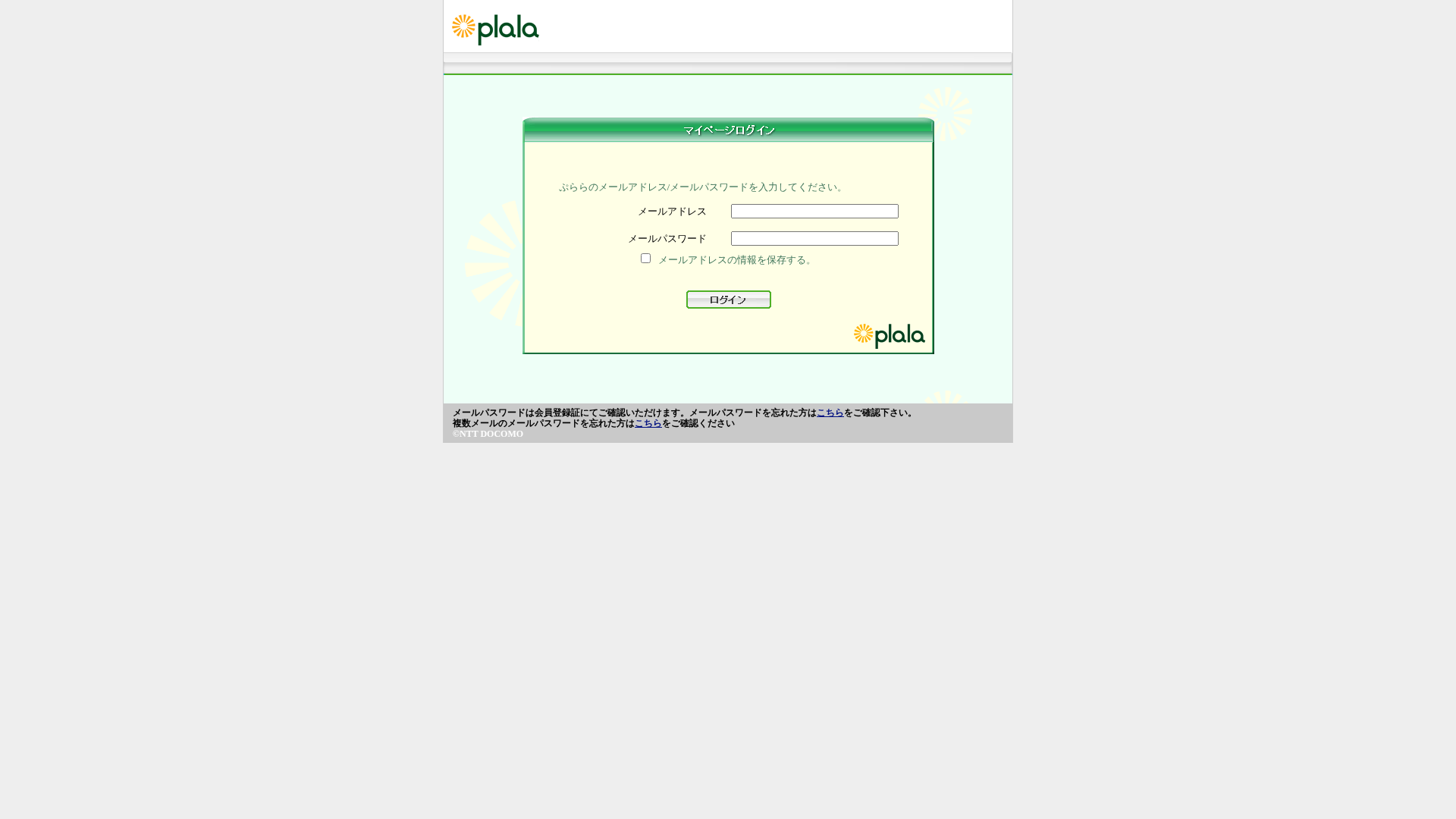
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B091F01813853B4F99A552A3D3752E9493E2541EC7324C58A85EE72F1C8814EEC7F9FC |
|
CONTENT
ssdeep
|
96:A3ydpoIL/N+lglAtyHL5ZiNr2t5CLJWfsT3yDSxyHJHAPboRbDY7YoDSZHlf5D:j2kcRMgc0Qh |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b29e9a3131dccc99 |
|
VISUAL
aHash
|
dfe7bdc3c3ffefff |
|
VISUAL
dHash
|
394c68049e600800 |
|
VISUAL
wHash
|
1c243c3cc0d0fcfc |
|
VISUAL
colorHash
|
07018000600 |
|
VISUAL
cropResistant
|
394c68049e600800 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários do plala
• Método: Imitação com um formulário de login.
• Exfil: cgi-binsso/pf/agent_sso.php
• Indicadores: Domínio não corresponde, formulário com campos de e-mail e senha, código ofuscado.
• Risco: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- hex_escape
- base64_strings
🎯 Kit Endpoints
- https://marutitraders99.com/plalaa/jpn/webmai1/sso/pf/js/tags.js
📤 Form Action Targets
- cgi-binsso/pf/agent_sso.php
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 124 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker is using a fake login page to collect the victim's email address and password. The form submits the data to a malicious server.
Secondary Method: Social Engineering
The page is designed to look like the legitimate plala login page, attempting to trick users into entering their credentials.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
Functions: td_4H.td_2e, td_4H.td_5g
📊 Diagrama de Fluxo de Ataque
User fills <input name=username> → td_4H.td_2e() → fetch('https://marutitraders99.com/plalaa/jpn/webmai1/sso/pf/js/tags.js') → credentials sent to remote server
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : None
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name=username> → td_4H.td_2e() → fetch('https://marutitraders99.com/plalaa/jpn/webmai1/sso/pf/js/tags.js') → credentials sent to remote server
🎯 Malicious Files Identified
tags.jsMalicious Functions
td_4H.td_2etd_4H.td_5g
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for marutitraders99.com
Found 5 other scans for this domain
