
Phishing Analysis
Detailed analysis of captured phishing page
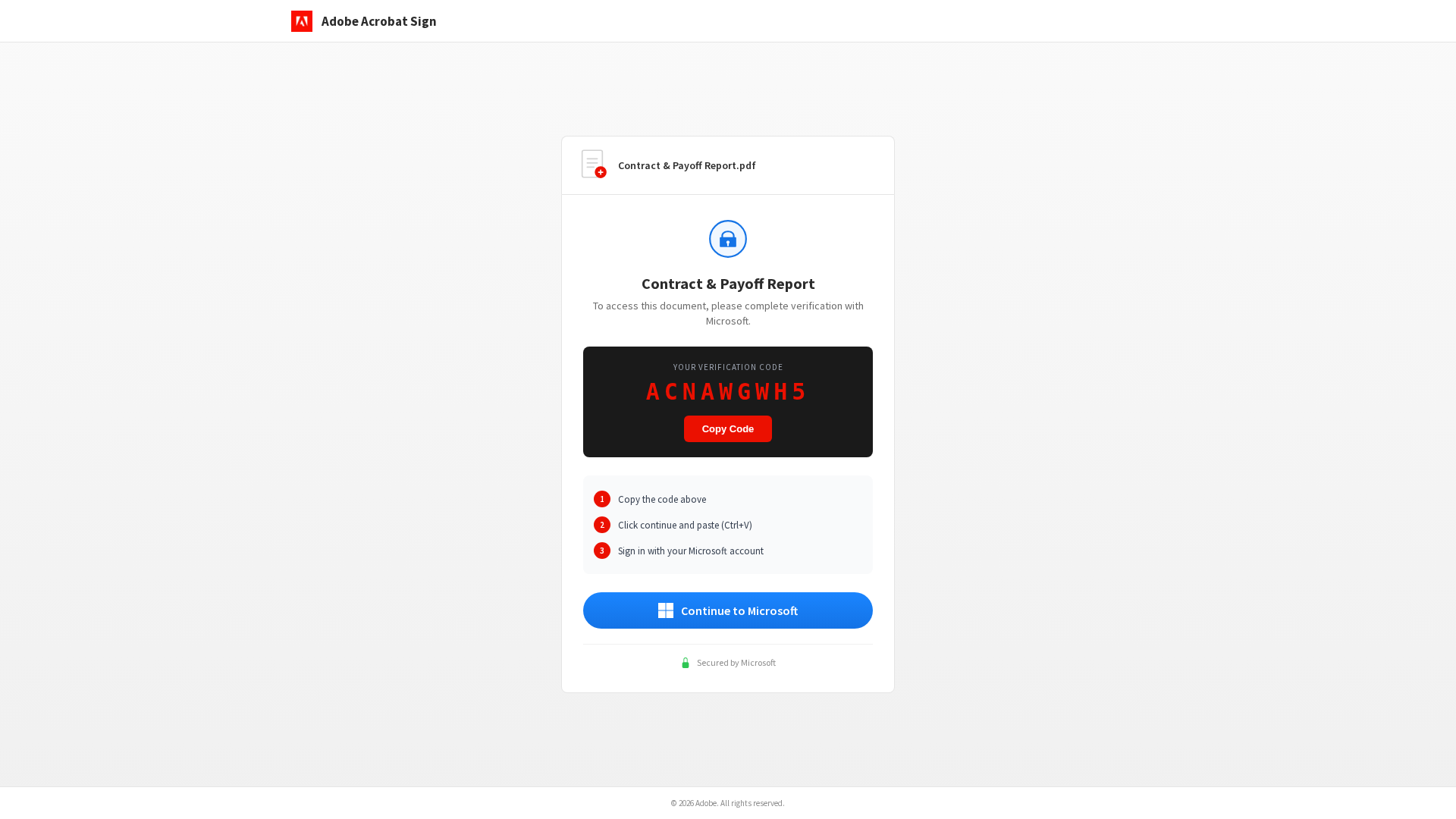
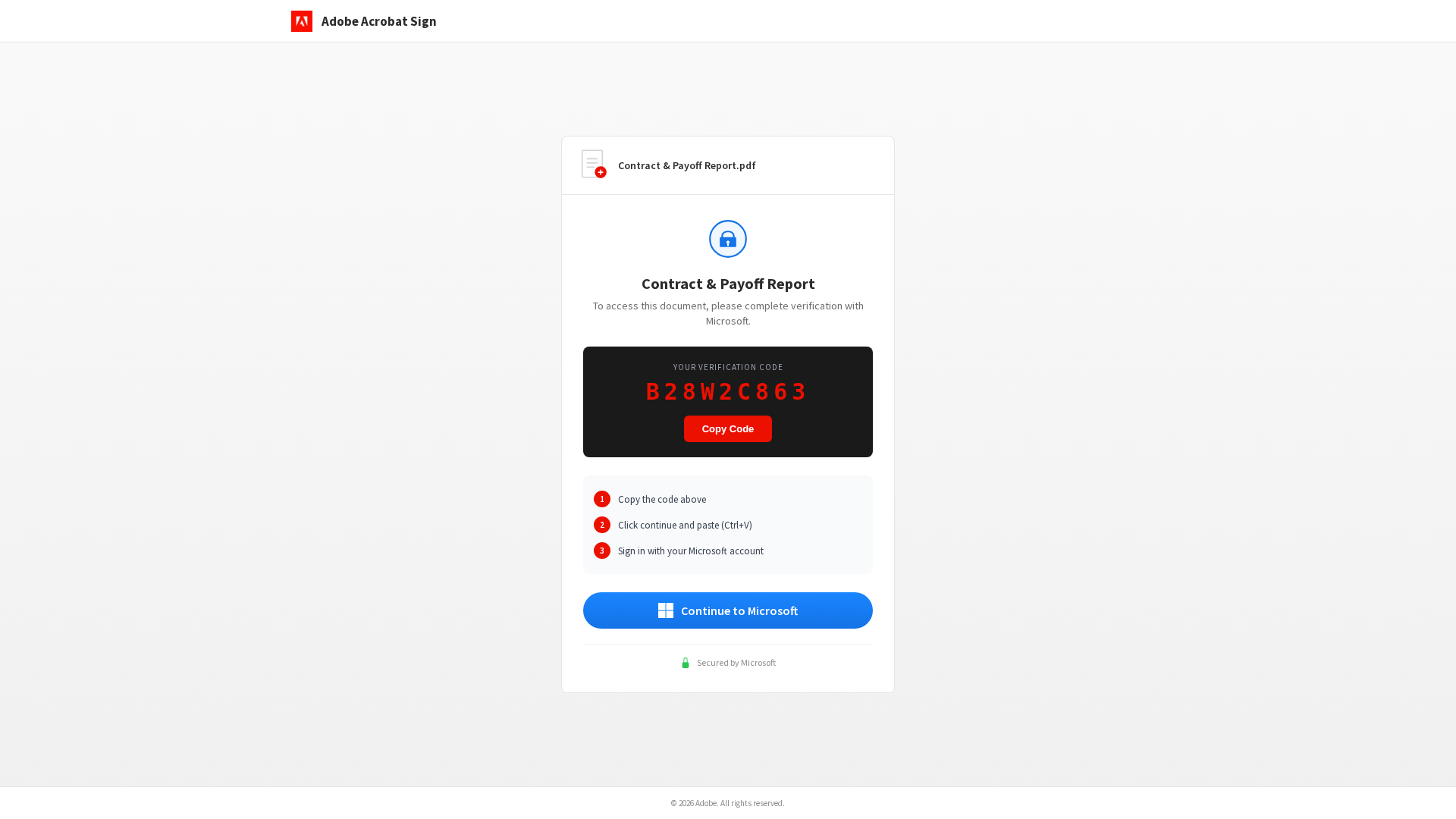
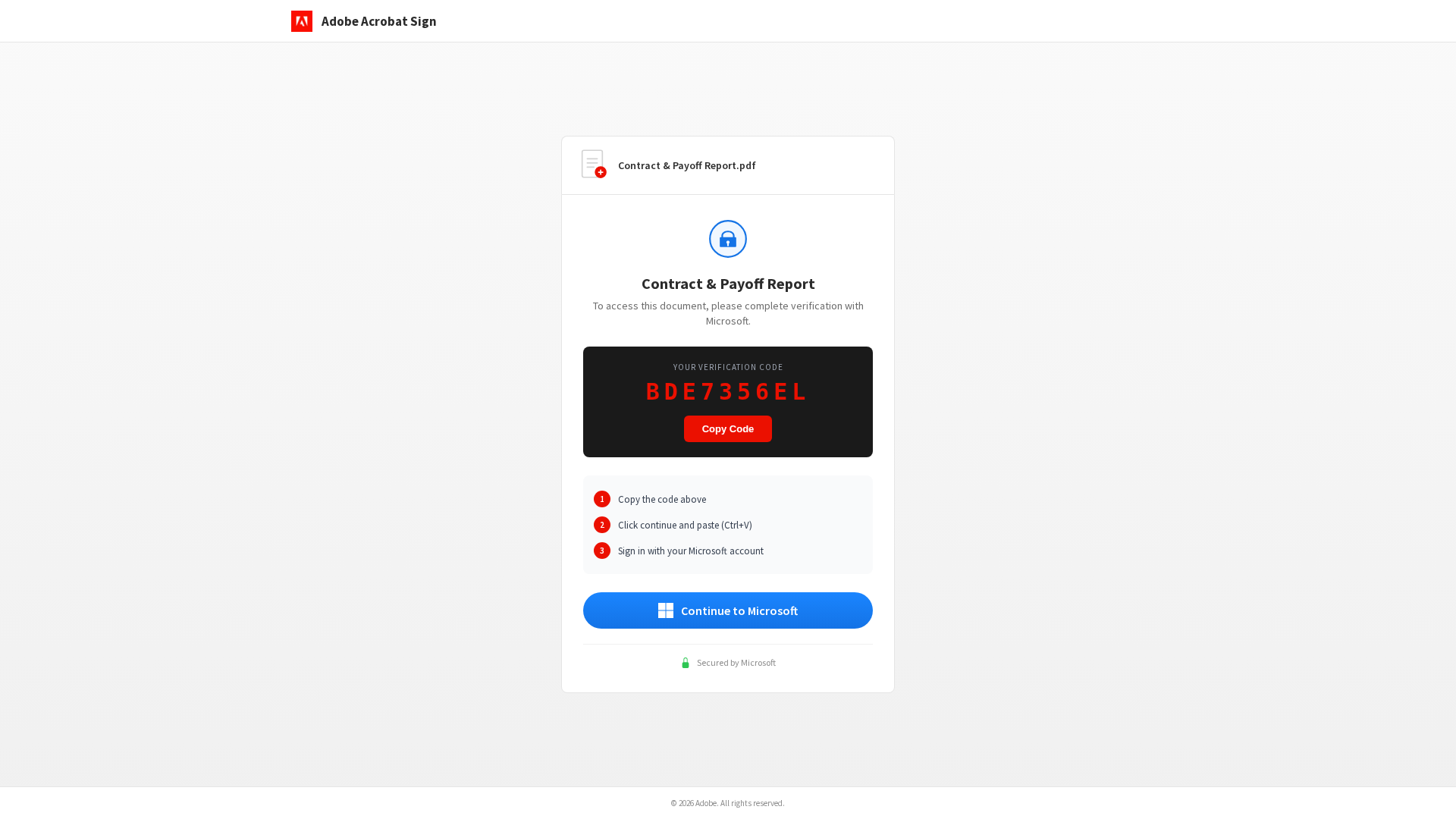
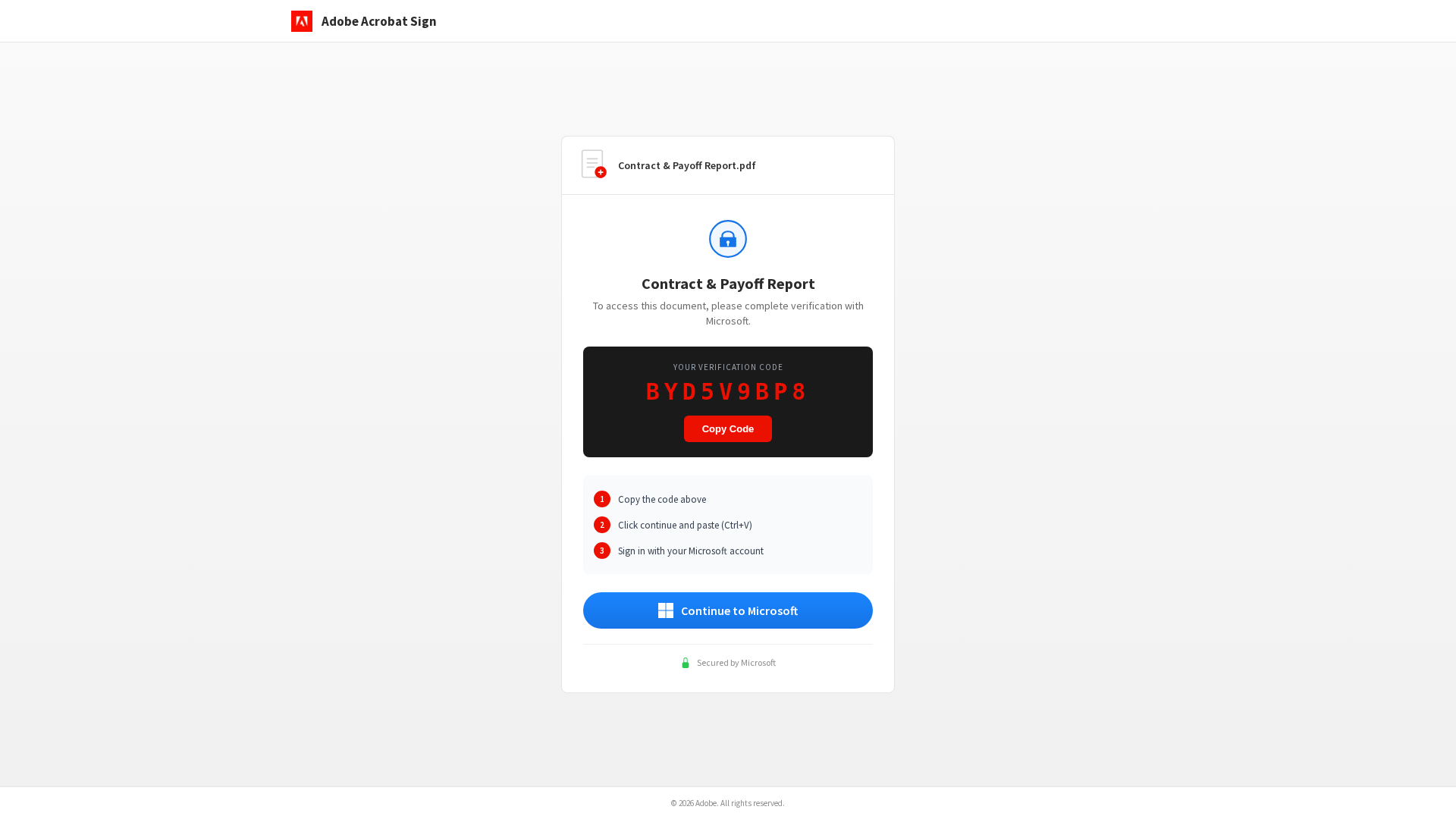
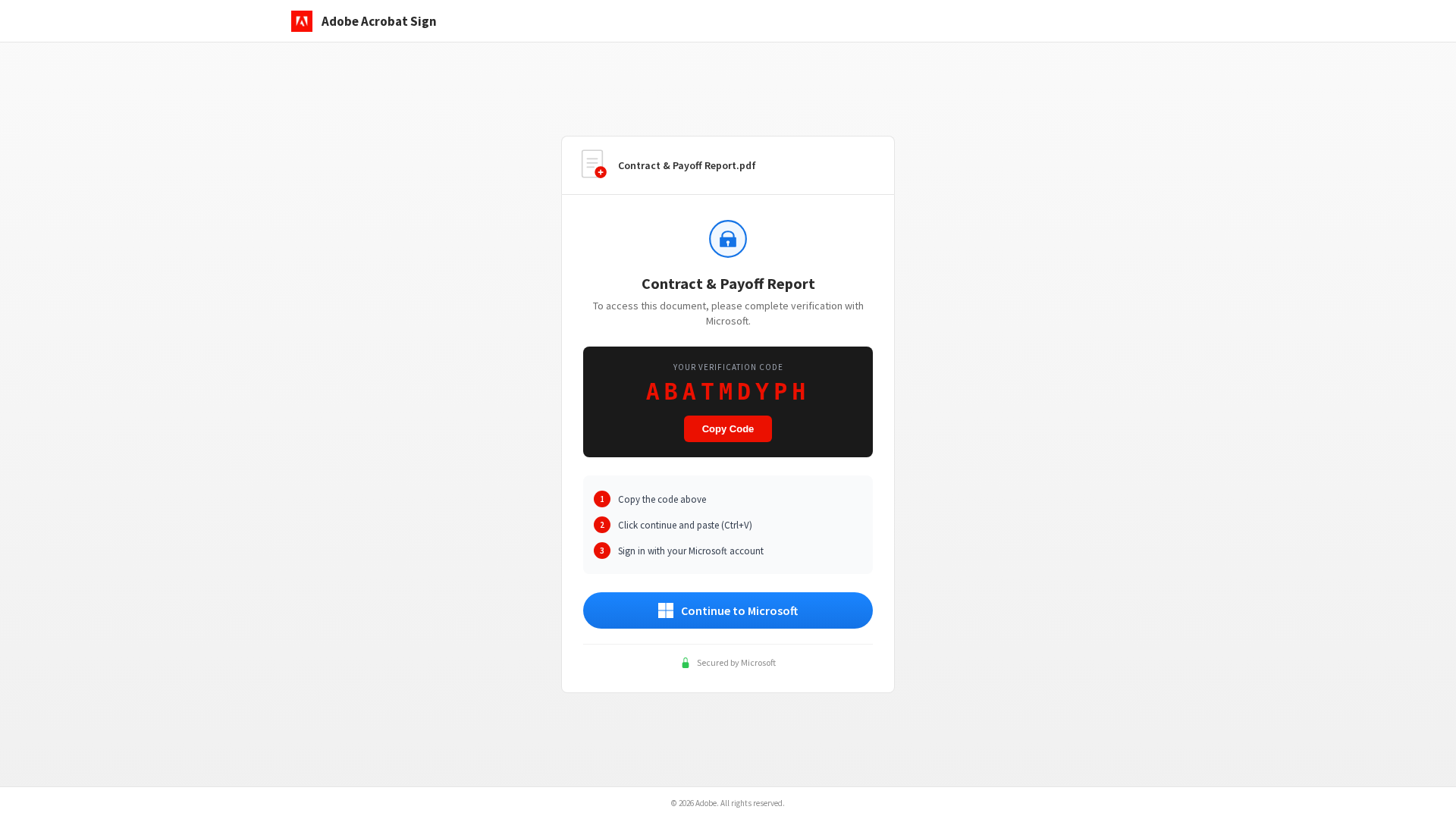
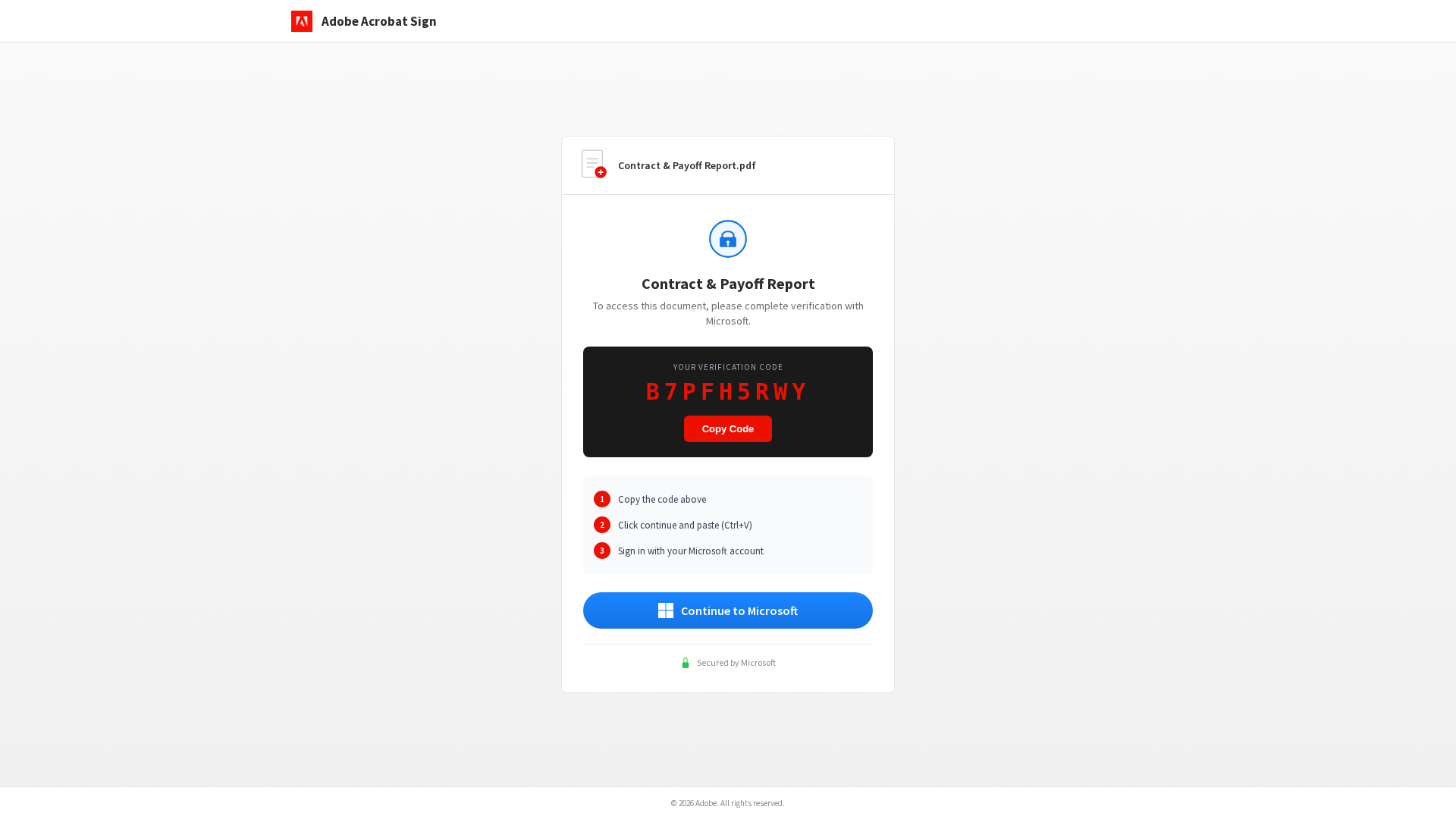
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B7811231925C1D7D260B4BC9EA39336A31EB974AEB0E20147ABD13B056C6DADEC77094 |
|
CONTENT
ssdeep
|
48:TU9q4mSud5LcdWwsd1o1Pl1Pgz2i93SEgVgGF706vVbTspaxhHe8rSA4ie14nZYQ:TU/ON8WroPogqGFlVbgehHU1ubo5S |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b39c9c3936269c9c |
|
VISUAL
aHash
|
ffffffe7e7efe7ff |
|
VISUAL
dHash
|
204a224d4d484c31 |
|
VISUAL
wHash
|
ffffffe7000000a0 |
|
VISUAL
colorHash
|
070000101c0 |
|
VISUAL
cropResistant
|
204a224d4d484c31,6161697949313369 |
Análise de Código
🔒 Obfuscation Detected
- atob
- document.write
- base64_strings
🎯 Kit Endpoints
- https://logo.debounce.com/adobe.com
📡 API Calls Detected
- https://microsoft.com/devicelogin
- /api/device/status/
- /api/device/start
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: OTP Stealer
- 4 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 4 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for adobe-7t9.cfreda-radonh2o-com-s-account.workers.dev
Found 7 other scans for this domain
-
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
https://adobe-7t9.cfreda-radonh2o-com-s-account.wo...
