Phishing Analysis
Detailed analysis of captured phishing page
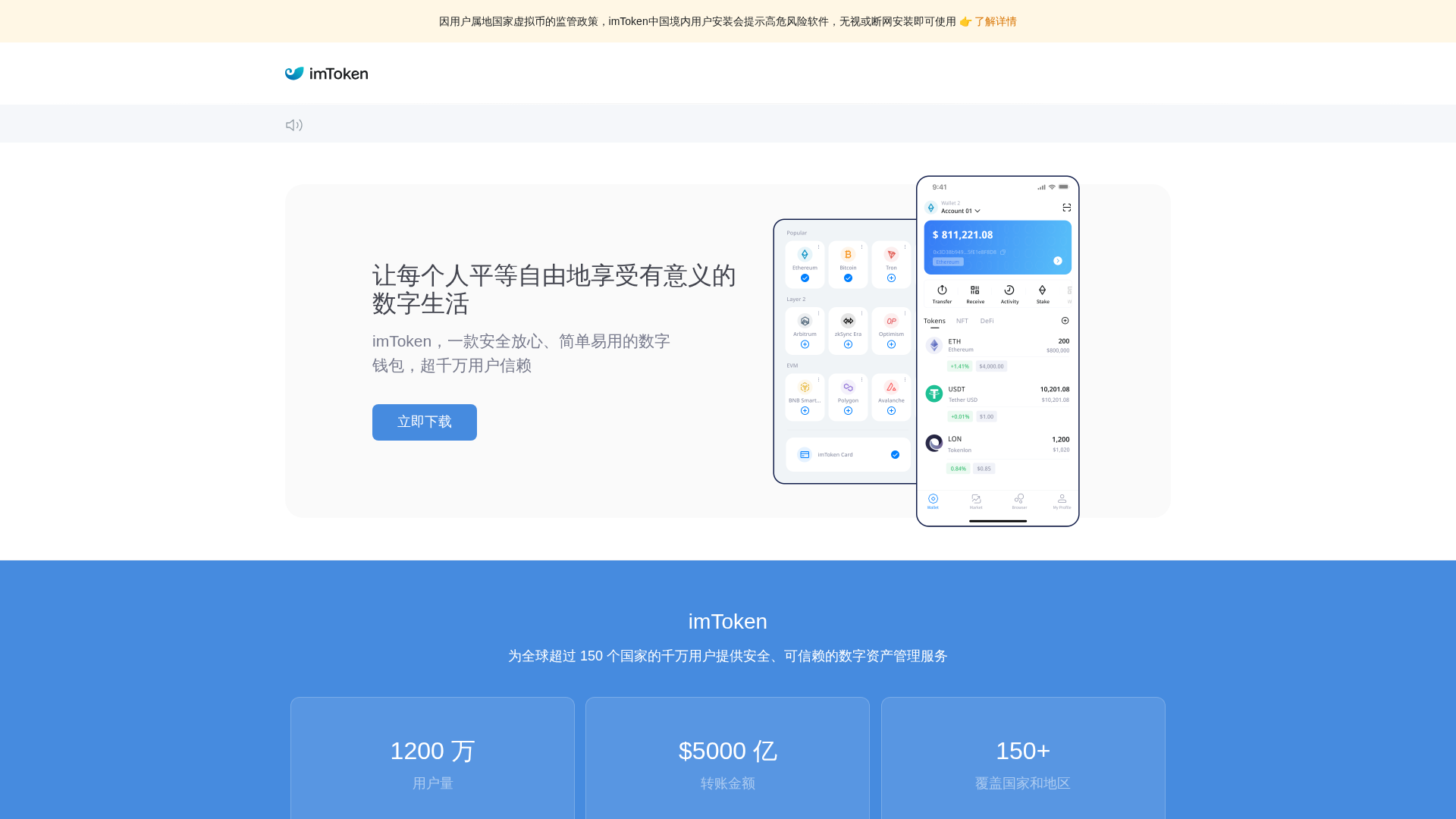
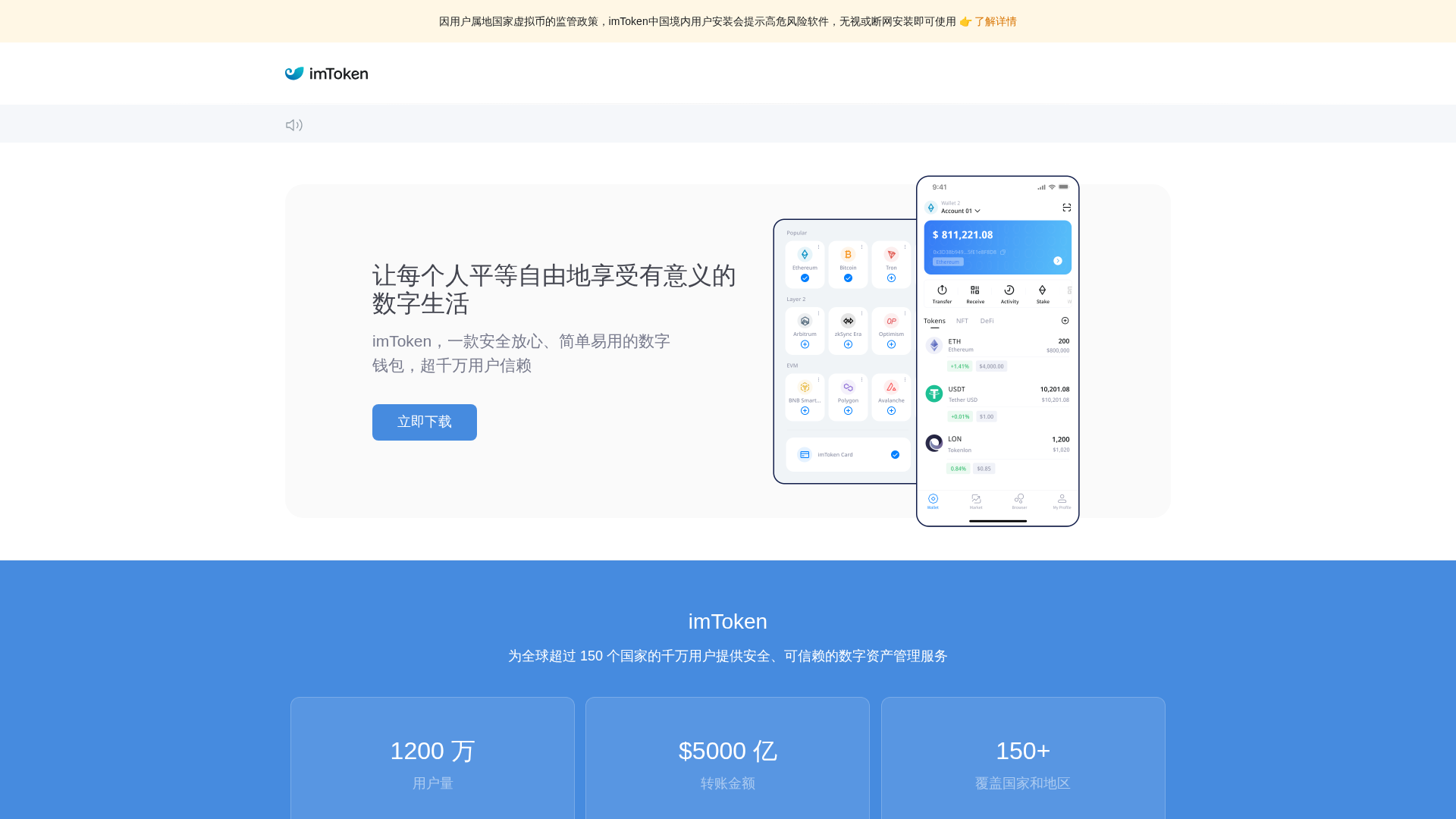
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A56224705889EE3701E7A6D1CB71AB3DE1C192A6CA765D05C2F8878D4F46FADCE03906 |
|
CONTENT
ssdeep
|
192:VjoEJKsPVzRACInJ+PmifkYK76AL4zKSpwj5bXkTRLTT3SPo73q:Wpsa6Zw6nlb6Wa |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
aced43929238e1ed |
|
VISUAL
aHash
|
fffffbffff000000 |
|
VISUAL
dHash
|
1c2213372452f0d4 |
|
VISUAL
wHash
|
ffffc3d7d7000000 |
|
VISUAL
colorHash
|
070020001c0 |
|
VISUAL
cropResistant
|
163803121f372642,0c3232320aa49409,809248b2b2969680,00143070ccd4d4d4 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Kit de phishing para roubo de credenciais
• Alvo: Usuários do imToken internacionalmente
• Método: Formulário falso que rouba credenciais de usuário
• Exfil: Dados enviados para URL de ação de formulário externo
• Indicadores: Domínio suspeito, JavaScript ofuscado, marca não coincidente
• Risco: ALTO - Roubo imediato de credenciais
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- POST
- text/html
📤 Form Action Targets
- https://d0a5ba0b.sibforms.com/serve/MUIEAEz3dQk0fDrweVnmTpQQbZ2rw7qQ0gwoG6uu7cmDs0Qbh-IH9n_9vnkOQcAbKkvvwJN3s6pdlocND15cgu8iWZpPKmLHrRotNy0Y7OWZCbE6s_ufjQdZ1gF97q8wMCufNErgiw-O2ZXG15IuswkxLv9-ibQzyNEr6vAKCXMI0DSy_0nRpnTgnUV27alZPD76WvkNNHW5Ylmh
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 3084 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Wallet Credential Harvesting
The phishing site mimics imToken's interface to trick users into entering their wallet credentials. The Credential Harvester kit captures input in real-time and transmits it to the attacker's server, enabling immediate unauthorized access to the victim's cryptocurrency wallet.
Secondary Method: OTP Interception
The OTP Stealer kit may intercept one-time passwords or 2FA codes sent to the victim's device, bypassing additional security layers to authorize fraudulent transactions.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🦠 Malicious Files
Obfuscated JavaScript file containing credential harvesting and OTP interception logic.
📊 Diagrama de Fluxo de Ataque
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL ACCESS │
│ - Victim directed to fake crypto wallet page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE INTERFACE DISPLAY │
│ - Spoofed wallet login form presented │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL CAPTURE │
│ - User enters wallet credentials │
│ - Form collects sensitive information │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA TRANSMISSION │
│ - Stolen credentials sent via HTTP POST │
│ - Single endpoint receives harvested data │
└──────────────────────────────────────────────────────────┘
```
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : Light
- : None
- : Moderate
- : None
- : None
- : None
- : None
- : None
- : None
- : Moderate
- : None
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : None
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL ACCESS │
│ - Victim directed to fake crypto wallet page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE INTERFACE DISPLAY │
│ - Spoofed wallet login form presented │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL CAPTURE │
│ - User enters wallet credentials │
│ - Form collects sensitive information │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA TRANSMISSION │
│ - Stolen credentials sent via HTTP POST │
│ - Single endpoint receives harvested data │
└──────────────────────────────────────────────────────────┘
```
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)