Phishing Analysis
Detailed analysis of captured phishing page
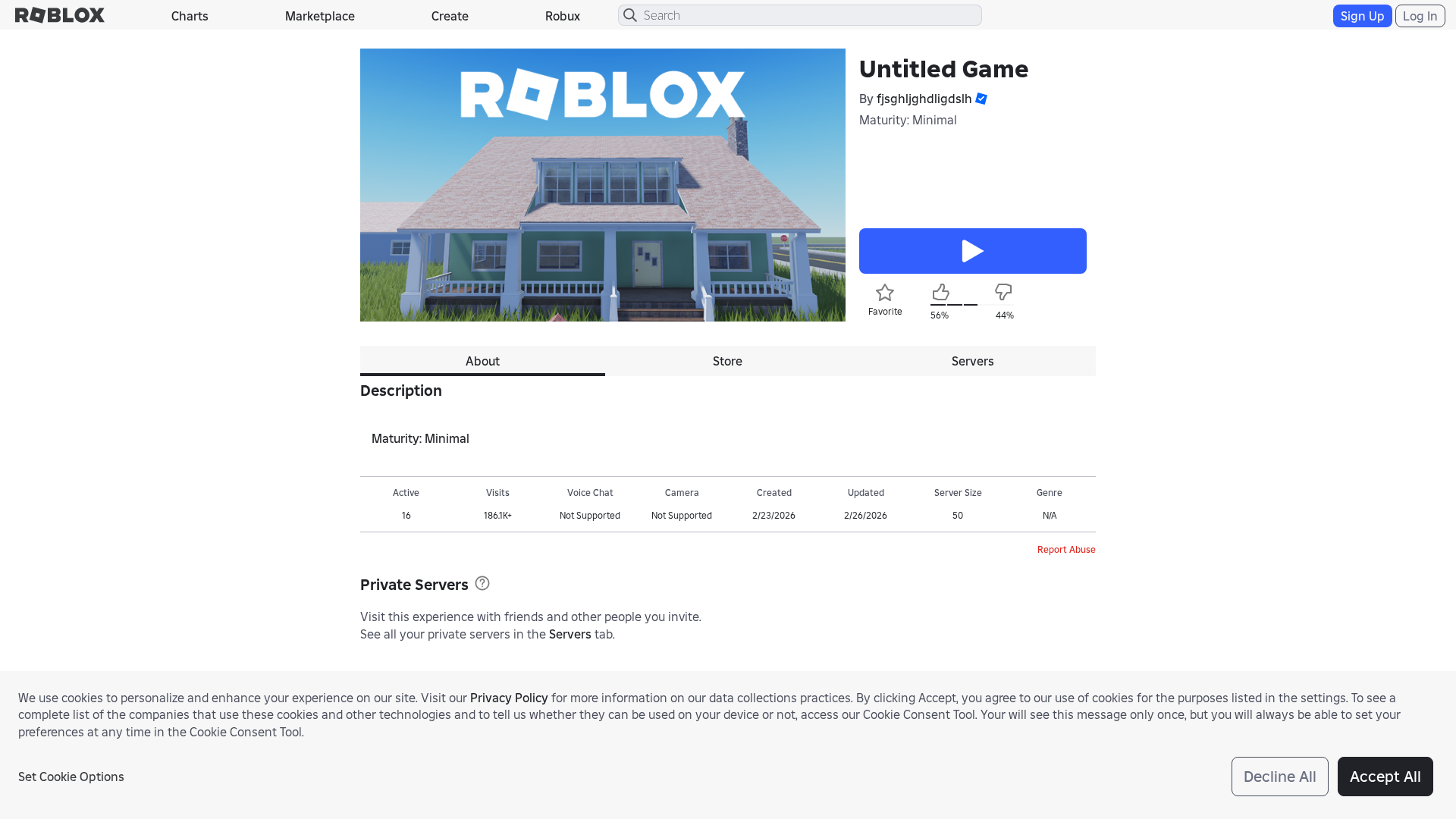
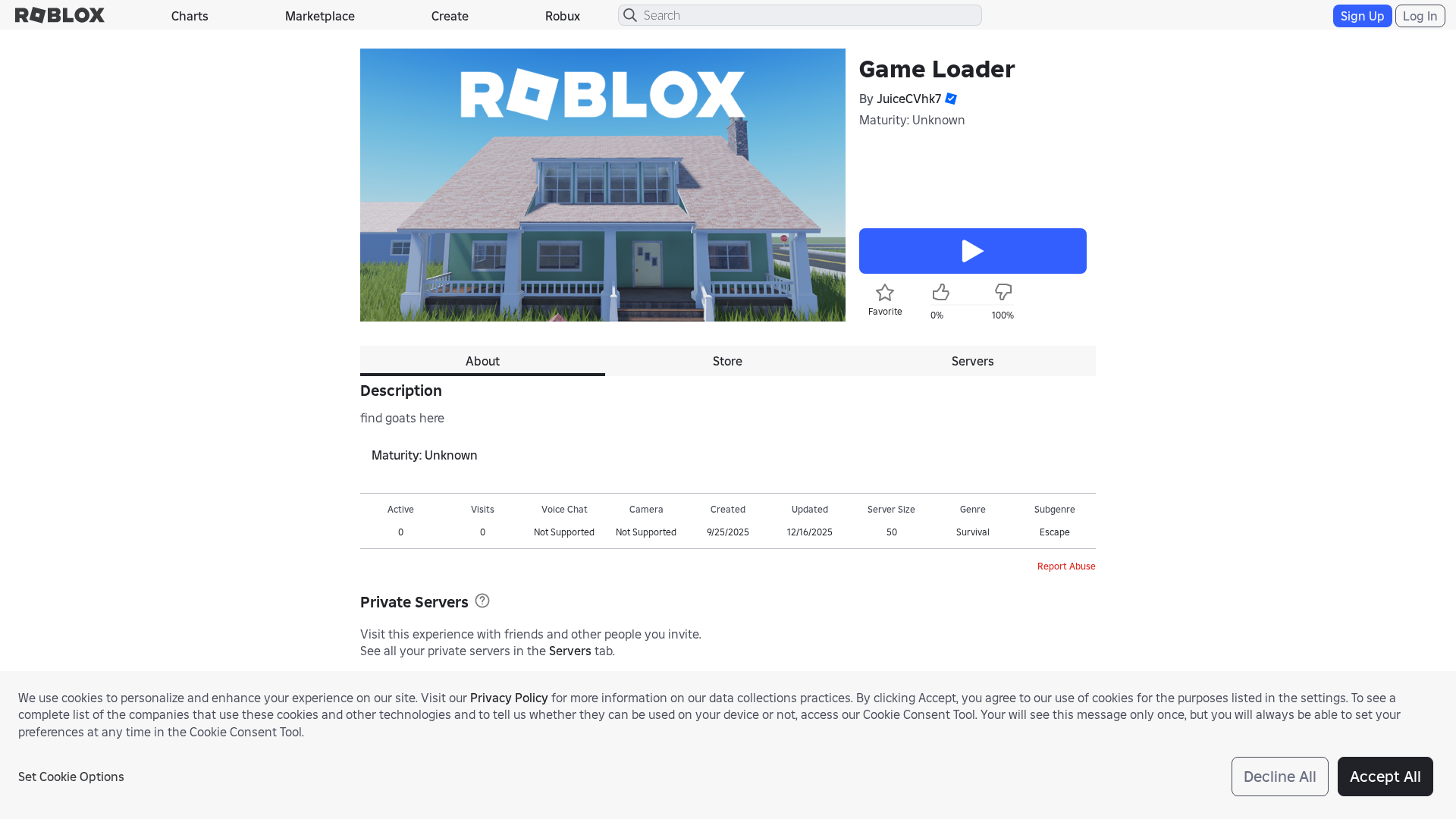
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19E13DA72A120283761AFA3D5F515B70691D3E70ECB839BE2A2F463760AD9C31FD1341A |
|
CONTENT
ssdeep
|
768:eHXB1ly+QtF8uB1bykQPKrvrvEZ3RkWPvBRG8AEF9NpBxJ8m8:eHXB1lybtF5B13jMpRXZ9NTxJ8m8 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03057cece2c7569 |
|
VISUAL
aHash
|
c7c7c3c7fffffffe |
|
VISUAL
dHash
|
ae1e9e1e221a31c4 |
|
VISUAL
wHash
|
42c7c3c7ffff0000 |
|
VISUAL
colorHash
|
07007000080 |
|
VISUAL
cropResistant
|
ae1e9e1e221a31c4,171f1b1b17065555 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Falsificação de jogo Roblox e kit de phishing para roubo de credenciais
• Alvo: Usuários do Roblox
• Método: Apresenta uma página falsa de jogos Roblox com potencial para roubo de credenciais por meio de formulários falsos.
• Exfil: Provavelmente está a tentar roubar as credenciais do usuário ou informações relacionadas ao jogo.
• Indicadores: Domínio não oficial (roblox.com.py), potencial para formulários falsos e imitação do site Roblox.
• Risco: ALTO - Risco de roubo de credenciais e possível comprometimento de contas Roblox.
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /catalog
- /login?returnUrl=5405063603844235
- https://roblox.com.py/info/blog?locale=en_us
- https://roblox.com.py/catalog?CatalogContext=1&Keyword=
📡 API Calls Detected
- GET
- https://en.help.roblox.com/hc/articles/7997207259156
- get
- POST
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- https://apis.
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 258 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The phishing kit is designed to capture Roblox account credentials by presenting a fake login form. The form likely intercepts user inputs in real-time and transmits them to a remote server controlled by the attacker.
Secondary Method: Personal Information Theft
In addition to credentials, the kit includes modules for harvesting personal information such as email addresses, phone numbers, and payment details, which can be used for further exploitation or sold on underground markets.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🦠 Malicious Files
Large JavaScript file containing obfuscated code for credential harvesting and personal information theft.
📊 Diagrama de Fluxo de Ataque
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Email/SMS with fake Roblox offer or alert │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM CLICKS MALICIOUS LINK │
│ - Redirects to fake Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL HARVESTING │
│ - Victim enters username/password in fake form │
│ - Form captures input │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Credentials sent via HTTP POST to attacker server │
└──────────────────────────────────────────────────────────┘
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : Light
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Email/SMS with fake Roblox offer or alert │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM CLICKS MALICIOUS LINK │
│ - Redirects to fake Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL HARVESTING │
│ - Victim enters username/password in fake form │
│ - Form captures input │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Credentials sent via HTTP POST to attacker server │
└──────────────────────────────────────────────────────────┘
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblox.com.py
Found 10 other scans for this domain
-
https://roblox.com.py/users/716626416/profile
http://www.roblox.com.py/communities/2085346245
https://roblox.com.py/games/2753915549/TIGER-Blox-...
https://roblox.com.py/communities/649025031/
https://roblox.com.py/games/920587237/Adopt-Me?pri...
https://www.roblox.com.py/search/groups?keyword=
https://www.roblox.com.py/users/1592667391/profile
http://www.roblox.com.py/users/4010614575/profile
http://www.roblox.com.py/users/6768773838/profile
https://roblox.com.py/users/474590525/profile