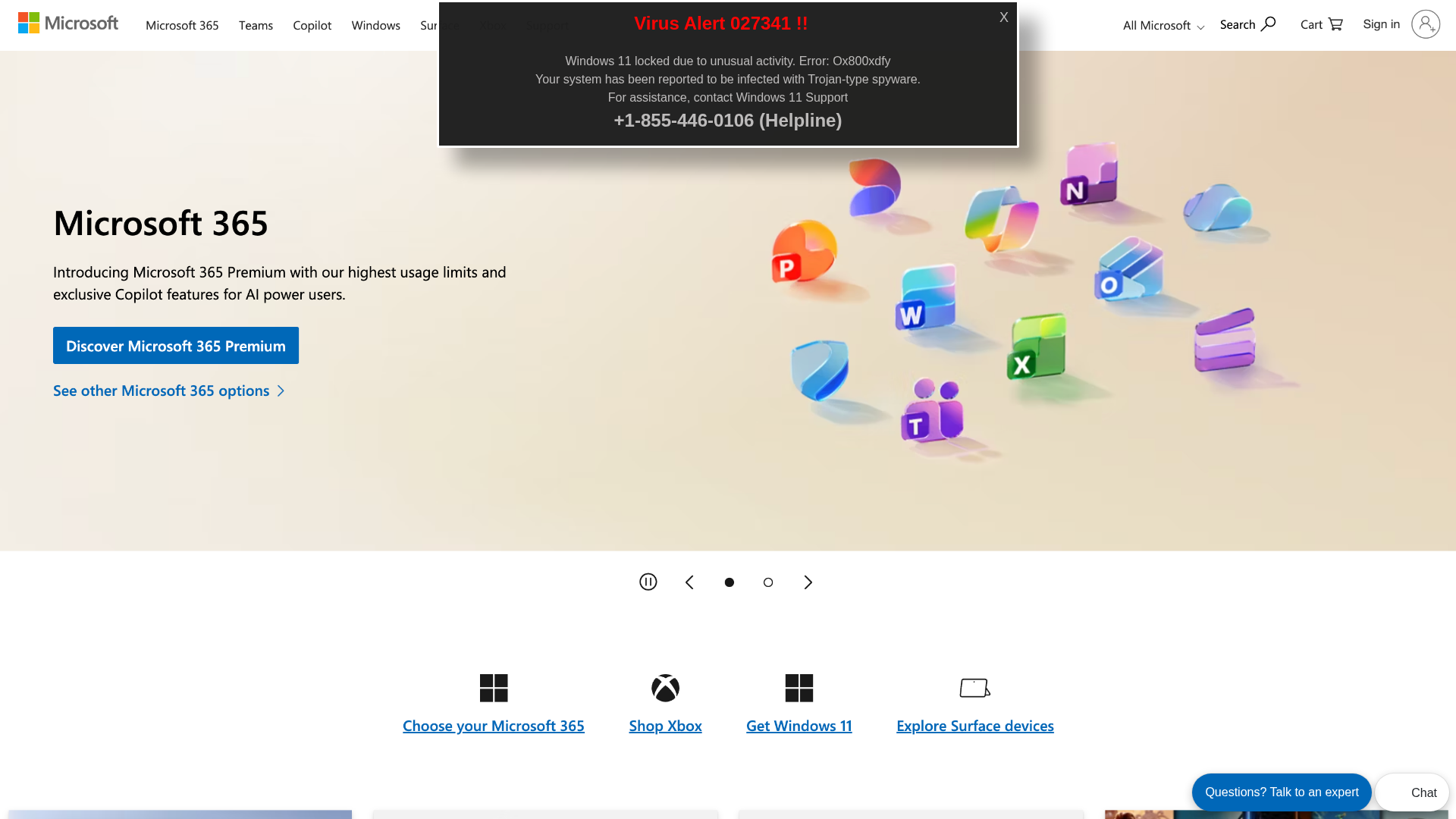
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
Informações de Detecção
https://hgyvtftres33-fjbwgfhucehvfzgy.z03.azurefd.net/whelpxxx/index.html?bcda=1-855-446-0106/
Detected Brand
Microsoft
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
05212c3e-ead…
Analyzed
2026-04-05 02:40
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C5B19361C1240D23A2A746C4FB977BAB32518645E3520F1426F4C37AFFEDCAB8A563C5 |
|
CONTENT
ssdeep
|
96:TwxIbwdcq8uZmiXNb/YW7R/gvRN7WA3VaHaoBQ63x7zFSe:oIbwdh8uZDYW7RIpN7WiSBF3x7zAe |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e465703174a5daad |
|
VISUAL
aHash
|
c3c03830f3fffffe |
|
VISUAL
dHash
|
9696614706080c15 |
|
VISUAL
wHash
|
c2c01020e0fffffc |
|
VISUAL
colorHash
|
070010000c0 |
|
VISUAL
cropResistant
|
9696614706080c15,71714dd5d1616979 |
Análise de Código
Risk Score
53/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔒 Obfuscation Detected
- fromCharCode
📊 Detalhamento da Pontuação de Risco
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
Credential Harvesting
Credential harvesting detected with 5 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 2 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
Microsoft users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Token swap/DEX platform
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
hgyvtftres33-fjbwgfhucehvfzgy.z03.azurefd.net
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.