Phishing Analysis
Detailed analysis of captured phishing page
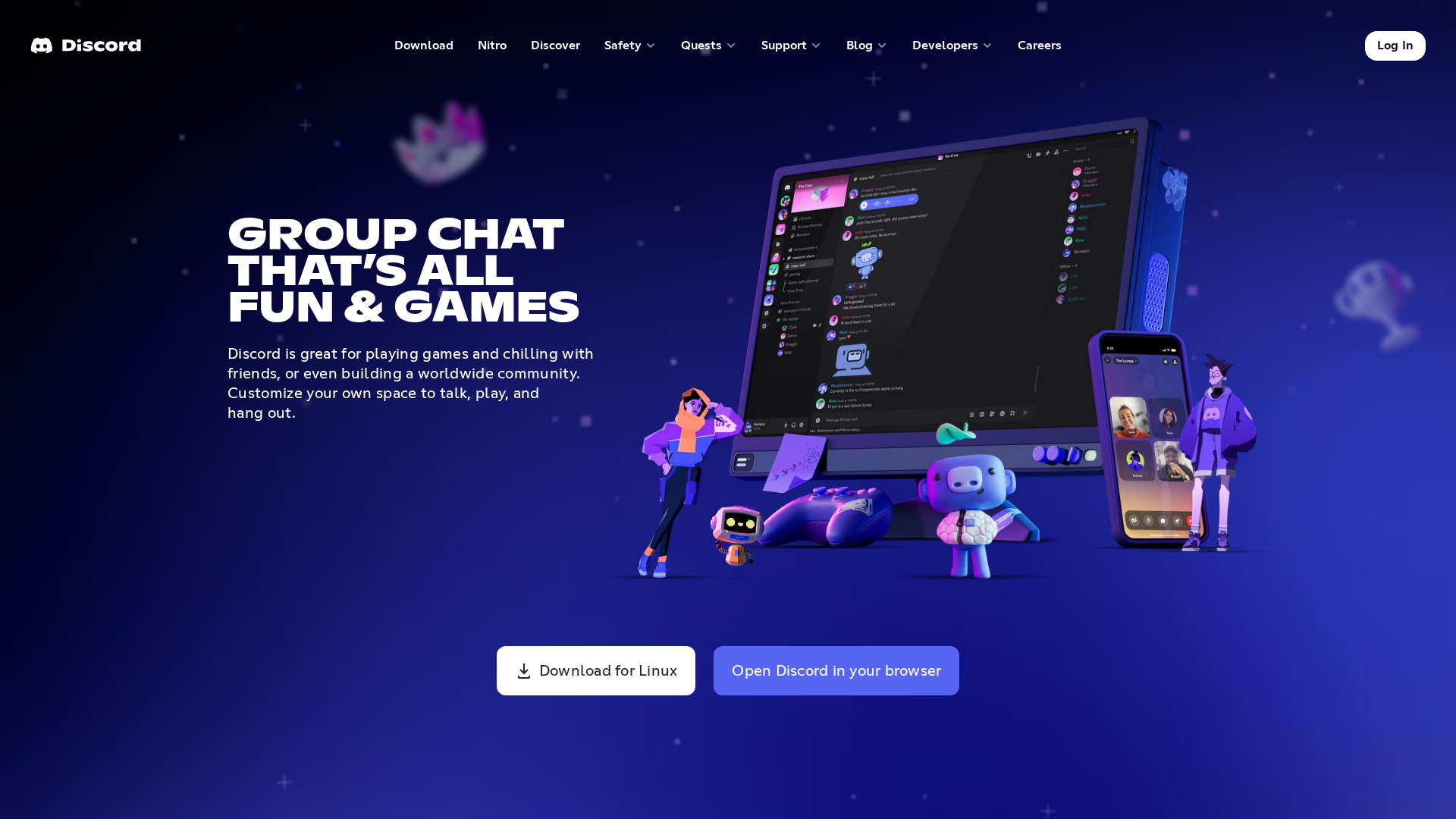
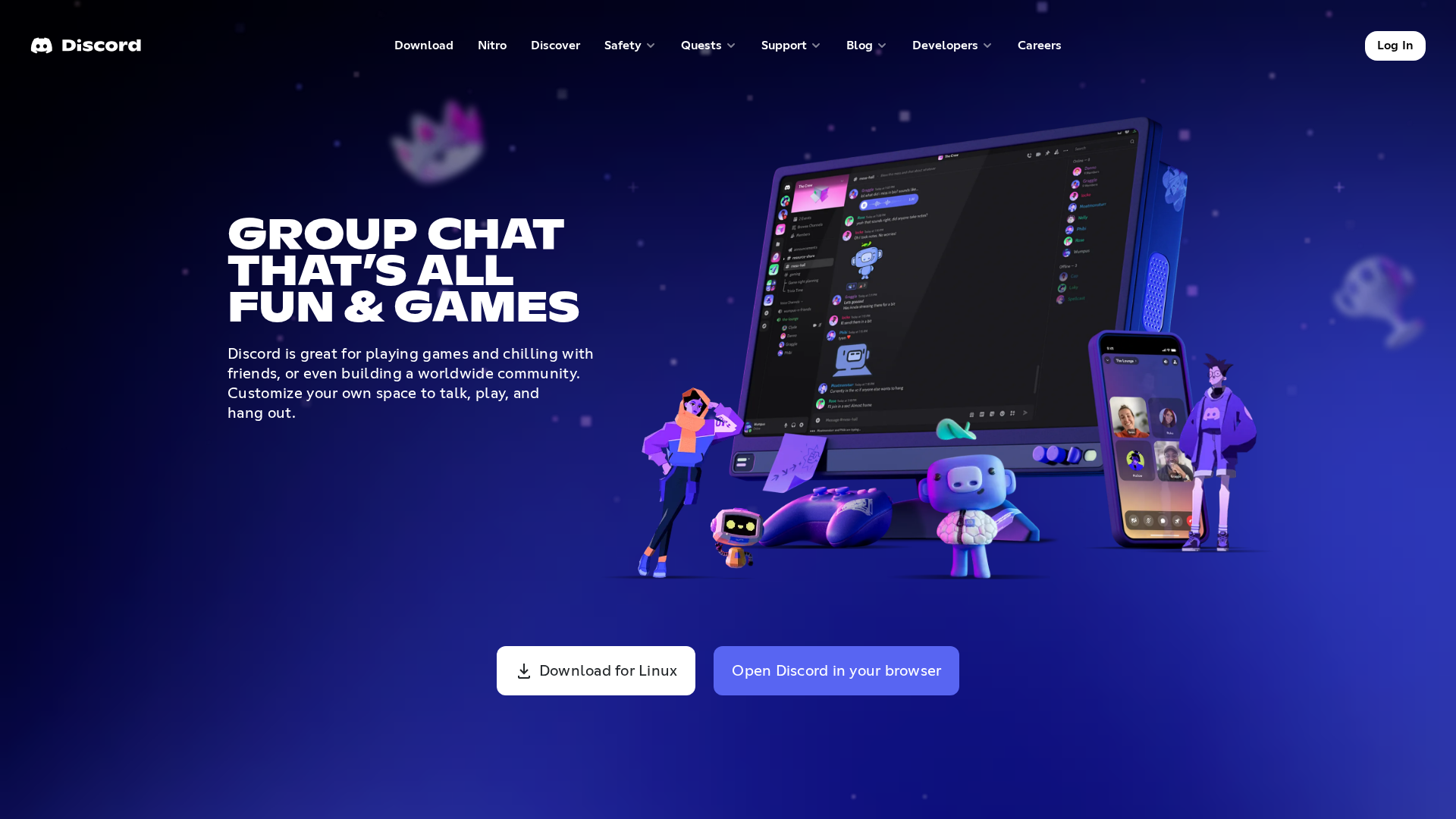
Captura Visual
No screenshot available
Informações de Detecção
http://ai22.hgva.net
Detected Brand
Discord
Country
International
Confidence
100%
HTTP Status
200
Report ID
09a40f50-a40…
Analyzed
2025-12-20 18:22
Final URL (after redirects)
https://ai22.hgva.net/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T128A3953BE8444017252349F1F7A07F0D5ACAD18FCE878C86ABB887463BD6CE2D85596D |
|
CONTENT
ssdeep
|
1536:XT4PUwPfBMgxPjncPjncPjncPjnS4MF/ahRyrM9sP3/HlxElnf:j4PUwPf+gVahAgf |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
83737e1c3cce6388 |
|
VISUAL
aHash
|
01006b731f1f3931 |
|
VISUAL
dHash
|
6ddacbc7f6ffe3e3 |
|
VISUAL
wHash
|
01006b7b1f1f3f71 |
|
VISUAL
colorHash
|
30000000180 |
|
VISUAL
cropResistant
|
a280c0260d4280a2,6ddacbc7f6ffe3e3 |
Análise de Código
Risk Score
70/100
Threat Level
ALTO
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Discord phishing landing page.
• Target: Discord users.
• Method: The attacker uses a fake Discord landing page to potentially trick users into downloading malware or giving up credentials.
• Exfil: No form is visible, but the page could lead to malware downloads or social engineering attacks for credential harvesting.
• Indicators: Domain mismatch (ai22.hgva.net vs discord.com).
• Risk: HIGH - Potential for malware distribution or credential theft via social engineering.
🎯 Kit Endpoints
- /blog
- /login
- https://discord.com/blog
- https://discord.com/login
📡 API Calls Detected
- https://hubspotonwebflow.com/assets/js/blockedDomains.json
- POST
- GET
- https://www.google.com/ccm/geo
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.