Phishing Analysis
Detailed analysis of captured phishing page
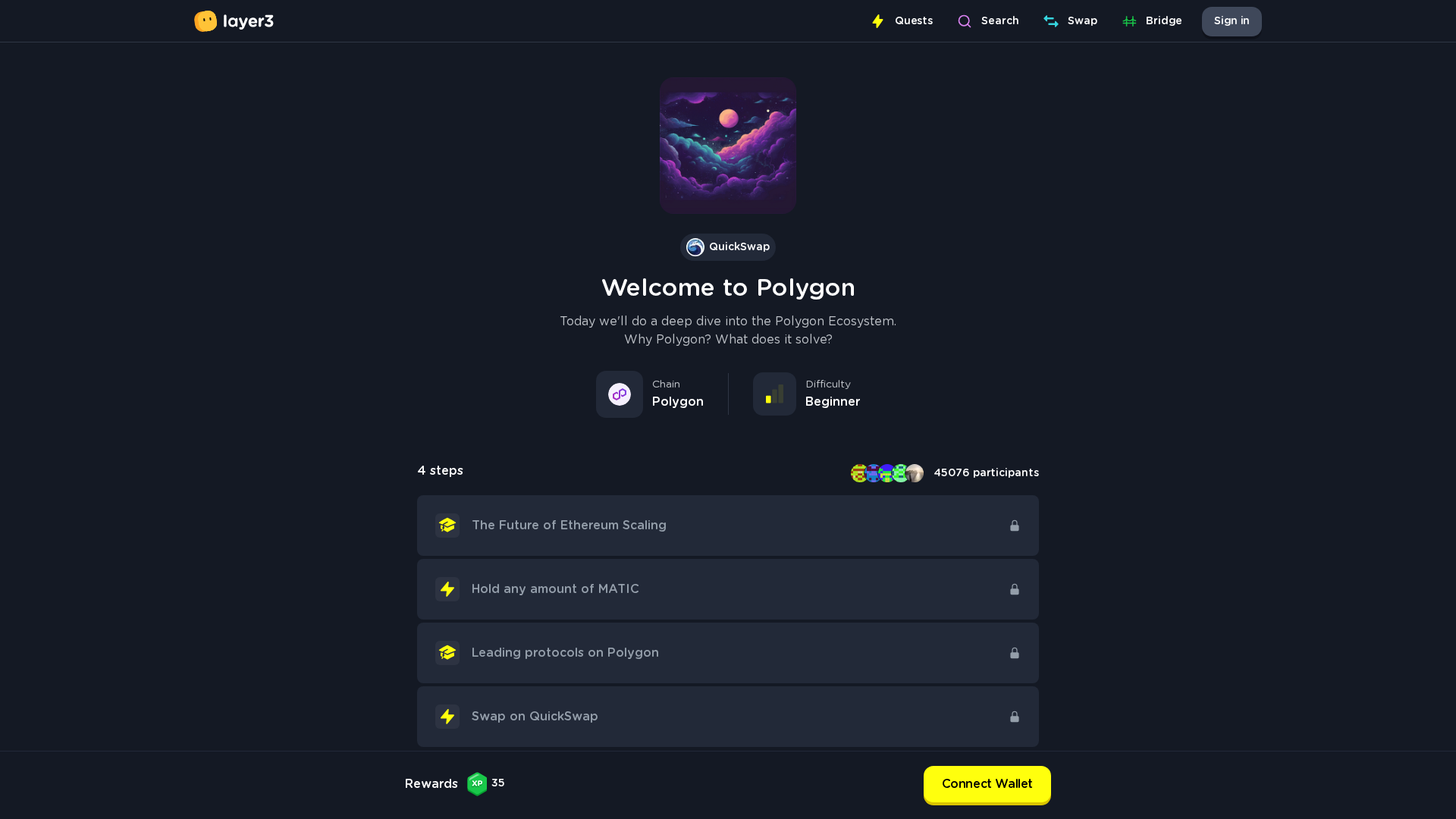
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13FA2DBF01315CAAE14D78778DB35A247635AD7A8F6060A4AA3EC875B3DC3CD1CC972A4 |
|
CONTENT
ssdeep
|
384:uLPynrHIZl73pZJqtyVM4uXoyBQgVVVV0nbAdm:uLPynjIZlzLJqtyVMJXouQgVVVV00dm |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9a6db2e532cd9261 |
|
VISUAL
aHash
|
421818183c3c3c3c |
|
VISUAL
dHash
|
b27132326969616d |
|
VISUAL
wHash
|
ff1818183c3c3c3f |
|
VISUAL
colorHash
|
30007000000 |
|
VISUAL
cropResistant
|
b27132326969616d |
Análise de Código
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMgAAADICAYAAACtWK6eAAAABHNCSVQICAgIfAhkiAAAIABJREFUeJzsvVusbll23/UbY861vsve+1zqcrq6qlyVvnc7dqfdzsWd2ODQJlLskERBPEGCBC+AeAAeIgTigZvEC0ICEfHACwkPPCCIkJCQEEgkSDERsWPHie3Ebru7q6vrXPc5+/Jd1ppzDB7GXGvvs2ufqnNOl+MI9WxVn3O+b6255ppzXP/j8smX3/gZN0YQ5iGAX/r78w177iufHvqMOfTqhZ/gM3+w4R9/yQuN6/b4k37G845pLVef/3F08DLrfXrO5znvadgz6FPn7y8P59k0ffHZh58vmshGwbzMV3p7gDggis8Pu+7hz88+zx71GZ+Xp//5oRP4mGc/79JelBKuuexlpvDLN16lyisTfBK7/FzrufLMFyH6l13jxTPqlQdeeboIePzx7LnqBTe88Jpqe6YSNC4kIIsA7vOSFMAVU8AcRduTpgVflfgvsIzL7zyfgD/9b5meIU9f/yEGnxj1Gc9/nqXNL3zNtJfX+Yzpn7W059FrevnZz5JB8vzz/aDjund4MZn+Az7Xn/mP9gADFexZ8tnbHRN9T3+8EJcIYMilm/LVJbkD6vPDHMAuU+qLG1/zeIq3Lr8RFydil57xkSd0vTqd16bP+OpZ63nWZx8xPQD+YUn7PITllyd46gb50Kvppa+mW35gm+eKirjuHV5Eg7wIM10e8zP0qjS8TGfWztNRvfTiV6SUX759+uPjaOCpfQwusEtMkuePrxy0z3ca6NXtaot+aTuGNuel76Z/PvdOX6fRptHW9rFzPQcJKHzoPe3Dh/GCs/Ls9V9SH3plvsua5mWY/+pjPuKaF/UpXuz6667WZ3x/SZsol0x+rpEc1zzlefZhHoLI9EGsIUNjjqeklly9k6fF19O22keP6+yYiwX84ONZm/1xa3vWuq4bV+Z6WXE5P/fyJM/SP9fYEnrNZS87ftD7X3q8DD18pK3NC5v6l8d18kmaOhK5MLGuv+GSFvnIBT7P+P3CZa4bs0H5jO+vCoiX2fyrGvfyc69+f919P4Cv90/s+Lh9f9a47KBeVn0f44e+zFAJf6c9YzbTLh5xnfkkV/5t11zzT9K4fBCX//vH9ezp+dN/V5//PGv5x7nm6579ezXni9LNdfT4SSOpz3isc40Gea4xmTDP4y3+fo2Pgqg+TopdvfdFMJrrNMSz7OvnGZfNWfi93++r5vPLgDLXwZUvuwdXtc7VM/29pcEXZJCrpsfz+iG/X+NZ9v3zSvCr973MM5/3eR8352Wz4vdqv6++81Vz5iks/iPmeJZweVnTavr7dWu8vLZPYJiHD3LZSX+xcVXVfdzCLtuNv99+yMs+//d73fC0BP0kTIyJ0K8juMvPuvrc53n+dde9KA1cppurQvnyHC/LHM+nea5hkBdBqJ4lUX5QVP2H49njBzH/Lo+rGmKa++qzrj73456vV65/1nzPOy5rrstrfpm5rtOQH03jz9Agz8Mkz5Jo02fPWtgPxw8+Xtb8uzrHixKaX/nzuue/KBhx3bjqmF9lzusY+WXDDdddczH/R5hYV53Dq+OTlhQ/HC83fpC9/iTO6aPmeNGMrume5xHM098/KqPi8riOsT4MfriCGlh7/Mf4IB/FdZ+EpPjh+P/P+Chf5LpxHc08jy9xlemehW49z/M+nsHyNPWzSfyHxP/D8XHjusyLj/ocPuz7XA0CTp9P47LD/nEWy4ukWn60efaScZAfjh+O5xkfJVyvCxdcvfejiPyj7r+OMT9KDTw7w+HDDPKiec4/HD8cz+UAP+/9H5eOc9lZf5Z2ehkU9frvf6hB/nGOZ9V9vAxtfRLpcZ/o+CSCoc8z12Uk7aOAomfN/WLj+RmkHchcz/RC42XQjOvH1VkEPgGt9yJIyDSeI/7wrIToCaS59O/5vfTK5c94jD8rNWma4wrzPRWxunK904LHH4fWX33ei2zbdQw9f3aJPp4jPf1irxxsokm/tkLK21vLhz67Zj1PjakexKXtzqUVXL30Eupm11/y7AfNN1xJF7crjpHSqsZaqjF+rSmpyFMvPX9tlyULXM+UfvGufvmzVuPsFqsU/dBt88t8qMDmyrhcE/os32/2R3WeczYC/OlLnprnkj8Z11/c/9Ro232ZGZ6KST9j66+dZ7rgunGdAPAgwKdI8mpa14cEml3s23W0dQWNnfeq3XZBYh8mGG0324c+i8VM81y8gmACgoE5OS6xZ0phscu0HOQ5DX9qR41LZXKXZwAgSX5K6gUNKtIW6wguFdxpBfFBD23jgikus0b8LYkyiWMRQUVphcIgMq/x8v/PO+PS5jdwRyThlHZPrGnGTeSCAe3Km+NOdUPc8PafYeDWdubyKsIcEAdxBzJihl2tWGsjpx4rIybQp57Bt2B6kYdtl6WvzFsuXBC9Thh/2znxiWSmz0G0A6tcSwiXKkrjVFIctQtJFXeJd3ZHRUiasPbu7m0vvczbPwuCSxwsnqaHfWgPooYp9v2y8JRpafNhzCfPxScOJigp5tY2TxvtNea3u8qJOc5ML3b0KbRNcXXUWhmigHuHtE1RvbSYy+YD4CqoB4HmtJwJfVpWkkSWjItcYhIwqzgVr/EyeBxJtULXdYBTShTnJ+lIOSOiCIkkmT4tURXEBTShJiCJZMFI1X1mcnenk44+r1iveobtyOh7dmWId6dAdooXRC8fjlxIHgfEKeNAsRF3x2xgKOeYD6j0dN1N9vUDzMBtRHUFYpS6A604HdqIYDIVJvJVllRxEko1oZNDUKiMqDUhoo5Rp0ObSUTE0ZQxg4TM/zOgzzmI10cMI8ka9x1GARYoDhrnrjMPOrUaiJOkRzST6NGuQ0XBICXFENwqhjeB4TiVWncXLOkefQ88hFuSDqjUug16mElrEkiO+HihiJo8DjlRcFXUEheqc6JHAxXEBEMQM9C4ThlnITgdpqGoNY2jzcSa+UH0khb3WYYajqjgJqQkVHNEps0OyR56ScJia5pBc9s4tM0FZmEYqGbcg6tFDTyRyBQpIErxEcdJkhANIugXC2qtiAvuiqSMeEiHlHqydI0RBdzxWuk4JPsSRdEkDHVsZlQI+D5lsioHqwX77YBbYiELRDuKDe3aHYV92xhHzJuwmISrINrRkTgf7zOOA6KGeUFTzzA+DoKwpgfrrh3QIcYJ2qSKCY1RYgdNnbFsQcHcSKmjlCH2NiXIcbi1xuEqAjIVpYbQkZRIbrgGi0zUZbWgmjEXVDJmW0QNlRxnbmPsrcokA0JZCah2mO0RBnLXoSSydkgKQSu1UERwD2rSpJgJXbfGzeY15lDNjQ+alsFDKKNNUBii055rozhHNTruhKLKZF02IeGxVouuOCkvQJUybC/EsxlgIcQBM2PiScVx1WAsb056KI1gk6lkPf4ei1cFQxF1qlW6bgEsQTJKCdUsqZkoMtvxl70CcUFU0ASZBK50uQeg2khOC/q0YjM+wTzRdWCuiBEMZImyrzFX6umko9RK1o4+9Yik2WRyD4bO1tHpmkwX5ozDMmsjlFiduVJr5eGjMzAhoSAdWRJd6sKg8MygC8wGigTjiguu4NXoGjEOPjAMO8AZxxFVZygnoIJrD+xR07AZ3DA9b7LLg05MEOmaxKxhSjGlPoSmzakDoJSCaNP8UhudOW7ShFITdRWcJlmbqaSa8dZuKc6+BqF4/Et9iLljZegkWRFcDWNonqBgVFZ5hUx+m4DkoCN3Z7ARq5UkTUimNGs0T3W2b9wqZhXVdGECqTfTKLSIugIjSMVMG4ELmYS44haavjZNCU6xCrUyVQqaBoMIwQQTrdOY5PJQ5qYNdmmDQDW0RnCwzo6zTz6DZUgZdQHtYTIfQ33gk43QNrRNhRqhkiWTUgJP5KyYjyDCUDaAkZJglkhAWnTUsZI1jitpwg261NM1e1facxEPF0Zjnct0SLYONDYk7GZvwjWx0AXuxkDF3ckpgVeKG+opzAsE1SWddZiuQzIlsHYdGna2a+FkuIvJSPaOT6+/yAebX8fVcVuAHqG2A4lZkdpUeYiu2SdQodMlQzkHrWCpEa1Sxz2hrRI3b73C6ek5XepJnbPdnYTQ6XrqWGM2nbCAMDFmv8pD2IWZIqhlXMP8SKmjln2YIjOZyexDh/6vzXF2atnhfSXRY17bmTdRq85KEqMPjF5wCUIUcVw8zHR3rAmbpEtqHVA3TGqj16aFdKLSjmTtbEzJkulSYiyVpEq1gjYNJQhuxmJ9g3F7inZKHcdZiIdKsNlqunDYvX0D8qU3/rhXL2HuyB48NYnRbHgEd0hpiZmRpENzB+jcIohGlODhxniYPNIkQ5iFgpLJeUGWjAiopzCJVHFzzEdMCmYlVKgIYkrSTJJM9ZANiOAWjCyTFPS2JapkU5Z6RPZVONceDldoFyGJsJYFR+kGaolqhZwSD+wDqD3VwNRRdybrXprJ6aG/Y1Ml/JizesLZeJ+T3V206xiHHet0g005DnOA5rSLNCdSwMMcCLptx9P8QU09brs4ME2oTYiLIZKZzN9Vf5O3Vm9wMp5yb/t+SKAagilppoo30AMSmamTjHv4F0qYfdpMCge6bsU47nHfITIZf5PNHmsw2yPaYTU0+qq7wa2Dd6nN1wjTqoEqEqZ19UqtY+gra9d4nGGtBXPDvaCilLrFZwaZxgSRNVsnJzIZaphKYNQy4l4RTTiO1YowmZzSTLPmBnhpoKmC+SWcKzS8tD3MQcSAVNYHt9iePQl3otn5E6JkBjktEEnN93gaFzQLvlRJ5NSjnsPsSWHXdjnMqqR5JpKO3JCQBVV27KuQdYFJ43Jv90+mnoSTrmJNsHqYL4BKqLHelix0TfZlKGZX+pRxd9QTi5zpJUy0zjOGsiKz7hf8vbv/EO07XuvfZekHmAYhqrWDxzEPGzW5UK1yOtzjkb/Pfn+Cs8fGOMfz8jD2zsM8gtT+HmZFSETANN7Hp7c03MfZ4J0OT1XBha7vwGBf9lArfVqR6obDxS3O9g+Z+M2shtQXDV+DFkCQ5pSag2ZUKzMK6DAOO0QFvAvNhYUJ1oAa1/C3Jl8SUXbDE071A15Zv0P1cqGxzRl9xNSaD5hwd5Ja+CIe2kmzU31PLYA0o84NE2cy+2PJwfDdogdJYI4nRazizWoWTc05nDp2KqR4dh13mEiztgRNCasB84ukEBLiiF3gyvLlT/8Jr7ZvkkUbrtwggtQh5qE9JGzAnBZ4MDLLfsVQB2iIlWrXoIVM8sSqW6Ca4lwMiofT3+mChaxDqs2yISDCarF5IyOuBaMwMkz6h2oTohQ2aLJA09SEha7ofNkkZTDxmhVH6Si0mAazd5JYeqJY4oZm6Ab+5qP/i42foaJ02nOUX0N9SS8rUuoJaLZSbGS0DefDCY/sHtvdMUZFWODda8jwfUQcM7tAgiykqaaE18IUAplMAMdQTdTG8Nr+DGkpsYfW/IRmX8dBNgKgIWtaUcl4rfT9AbUUJPVUV5yz8CUtkTRjDqmhOWbhw8TpOG6FKkNjUAPNYDWYuwnLCW0LhCtTvHCweJXXD99FvGuaPnyHfdngSmgccajS2K7Oxk5Kid3wGKtO8fBxqu1nH9486OLWW29h2rF7cA/b78mLBTYW3AxjpNbK3DBXFFLGSgkfRh1vAIuKYNUuiXgCCZNYp6g3ipu+BESsOXlhXk1Cxyw2OkkOv0ETy+UR+3FLTos2uTQnM5FI9F1oG3OarwKv3rrF9lFl6SvwsP6SQPGCIlSvZAkfpaM2I7Gysw1JMlkzNY14MzmkOY5KQkURTxNEQAU6W7DOB8HN2lA3F25Ix+cObvPdzRa1xIP6u5yXh3R9z+npMZp7OITz7Q5si8qSlHtyt2Qcdgy2Y7ffge9Ae8Ll3aHjtj05NY1WZuIzwGoJqe7aJHDF6IGeame4Cjl3+DA0NzUOzGtFtWntZhZUq7g0KE4VrKKWkLwANux35413RlK+iXDA1H+2RZ2CqLwEHK8BslQE1Ry+gY2z828NOg/NJrF+kYh9qKJV2O4e8f2y57WDt1jkGyTvUVFS6nCMUQecStXKvu6ASrXKaKeU/R63EWol5Q400y8XDJtTQOhXS1wzFUfKGFZDl6m14FSKFZKGsJzM7f7mLVQSw7BDUqLuB3KX2Z+dhFROKfbEwpwPYeUzyCSSyLMDPTmlKew3mgSYUAZxR3I4xDn1DON25ixBEFdUEp3m2RTDlAV9mHU4n379VT54dE6gy0ZGKLbjSfkeuHMzv0OyBaK0TpSKGSx0TWrNixMJEoh52JIp/BRUm/PlEd8gc5DXJBRNzf8wZZUypj3f3e3AhdwZv3j/F9mOe1K/oNQRwTh+8oDbr7zJyZM9LoXdfo/uzpGU2O3P0ayUUkkuID34HvxeaFBsRkVUUkNKAlqMk62I3MB8aJ/3we6m1HEI9MYnMg79OpljCNTm1zGzERgpnORyHgbT4gAbz1Gv1HKCpA51UK9YaXAq4ZS7JGrZkqRD0iJMtBaHsoauiEWcRVMwas6JUkpolBoWiCiM5ZTvP/lNVt0Bfb5Jn9Z0aYmrUGs462U8Z+/neClU21GtkhcHkDLd8pBh8xjqiFWdIdhhuyN1HZt790n9Eisj7iNeangBOHW2qhTJme7oBvn1V1m98XpA2e8/YnzwANXMsDmDGoyGeKBngcE3ko+9zfMWa2KONk6qdnK2JeEe2qGTfr5ZEHJKuEOWPnyP5guYwYIVh3rAWAvLtObRbw0kVlga2ZVTTsv3ON+dQnbqOFAXA7e6N1jLq6hmkjh7l0aEF7EUJQg+YBrHJYWtbeEIL7RnpUdkU1KW8EFwVtrRW4/UiK283i35dvn7PN49RKXjZPMozKUGB262G0wFQ6m+ocoCHwecHWMx1IVazwLJM0e0b9IrTFSdMZKWIdDsBZ0j547KAD6AyAxlRrzBEI/IPqqICSI14NYW1Q8zIkwkSM2crSHV634+J3xEyoB7whbK+uiA3fFZyL9imA64V5wc9zaww+3Cy4xnGVSNxoPND0+5i3snR7vR1vn+nIEdZVfIKQSAI6g4TqGWOmu/lDI+nmMi7K2AB9JVSlOCJhgF24d2Gc4fN5CjxVhKjfNPHVO4gvUaffctVl/9CuSMfP+MmrfUfkl3cBNdHmBlpGxPGXbnUAwVowqBsDZAIFdvzrCEBVoJf2IKm5gLqqCSUXIsoo7hbEsXvkG+YAwn1P7aj1jqARu7zzrd5Hj8Nsf7e9xevcHj7V325ayxmON7B3HOhoc82v4Oi3ybhS4QnHePvkayJYMPdCSERPEC0tJEEmBCdki6YKELFtJHkCs3O9vgIC1ZE2biLYEbkrm1XPJXv/W36LwDSYzDOJto4iObzeOAJlcZ2RmVc6LFvrQmyhGUkhoEb2YzUYYv5wilCZcwg2w2C0+C6S3UpVpDxWgBvwlJMwlJ3pzo4LFGoRP2KuFxVZuiwqnZ0WFSKkKlgDr9oqdfrdgcn8W1XhpqK1QfoQREnBr6ZCJxTTsrxJtyDA1Ta0G8Yl7plweMteJVSOrUEsJirHuS9piVSMnRFIFOV6gVkyH+Lok0gSHWgnxe8Bqoppk3JKy9uhu1TmC0wLLHRVi9+yP0dz7F+se+hKMsj8/YvXeXzfe/Rz0/Q/qMkBAxtFuwzIqNhToGvF1rZI3k3CM//plf8M3mIcpkWtEgwNyEXqLrFuS0RgWS9mBKlxdkXeAm4SyqoJbI3tOzBDfO/APuDd8N6M0FzT11HCPtQRKl7HAfgAh+9YsFZRzBIfcdaOFQb/LO+g9xpK+QJFExdnWPKfTNLESEhXckDds/wI/QPEt6buiSg5w5cOGQPois3/JYTvi1k3/E33zwd9mWHW4DKhXtbqG6wNlQ99tAiVWooiBrxPfUukcXr+H7YyDseNFlCIm6waQ5fHiLVIf9HzGm8K8UxcUiyNUQGywix1OEXrUDxgbHCmLenHxtNjNNzLcoswuSbmK2CeakTgAnUyKKaELkaWKzyUB1DeZvyFDOC5ZHh2xOHjH3jHKL6xs8vB8HbnzxK6y/8mOktGD89gfU83M299+jnD4MlImEilPN6PsF47Bvtr6h/QrpMnW/g3GcGb9fHDDsNy2MYE2YEIDGOOKq5K4nL9d47sl3XuHGT3yN5Y/8CHU/Mjw+QTcD5fsP2HznO9jpcZjnTZvVusfKADhuFaljUxwT5NyRx915MEML7wfObvOGaepRabFiD3Qo50U465LJvgBpqQYOxQZO7HuclQeM7FF1oA882irdckUthTrsQKYfPCm4JYZhy7I/YnVwi8cPv09eCI/rA8rm7/CF9U9yp3+b5B03BHYMVPcW6RTWKcyDAUgK66QcseJ1XbJGSCmCnUkqrx4l/voH/w9/6/jXOd2fQF6jkqhEZN3LOZ5Gatk1c86pBi6OprDFHYe6DzBHJkl7jlrCJJO6jA9DM1AqmkKDYBUlYTKFsiJ7VN3DfdHIBAgijYObyD8g3/BDvAUZVaXFmnxKDsB9g+oSsz2qXeRtyQFWT0KjCtRJ2zVYcwI2JUUaSYsuBbQ6Oil1jAzMuU3VGfZb8nrFna9+ncXXv0E52TG8fx8kByN1GVkdYOcnpAaIgTEOIymFlnPtWN25Q0qJ07v3wgwrgfSV3XloaVXMmsFqAknIh4csb9xEFmtkvcbM6W4dUc/OOf17v4btCvXRE+zxGVIGxtNTVCG5MAznqAjeQBNxAvjxhLfYjrTMEPnKm/+MlzqgeYHVQgSjwgzIeRXBvLwgkxERsvZ0aUnyTJ87yrhj2a14tLvHMJ5zbicoLX/KwzRDlFLGCzSsWzFun+A2tjjWFCQDmU25ylBG+kUPnjhcHfGjN7/Kj3ZfhxKIW/HK6JVqTkcXAIKE47lw5wDltdRFNFuMWweJT71yyH/yy/8df+P+r5JSaJMAosMlNvWIOk8+zoQSEb+6NWWpxu8P1fhTLohpSvNwY07XiNwmQ1IzHbSjtkQujeSrYDif0lCkPbIxQeqoLmD7WXMgIQcDEY5s2kjCCwDDXFE1zBIkBy8N+JCA7C/wmvBpJsRSg1nRFGtu4EhoOIexUqqzfudNXv3qj3Ljqz/G2Wll++CU+t176FDwccPJe7/V9snxYY8Nu7BIvLb3jW3rD45wzaQuMW53lN05WTOOYmXHRBgyrzsEorm1DOAJUnKmQKpZ80mmcxEha4q4llsgnioh5HPPfrMlZWlnW1ksVuzKHi0Z+cqbf9LNHacHNbJqwLUpgytZEpp6RIREps9LVDp6WXH39NfZjI+b1ZsR7dGUL6SSpkjTygRysDtDRZCuw8o+Ng6Y6y+mOIAkqu0RMoKxXB+QiETEt9Y/wpeWX+P19BpLXcTLmnCoyhrnvMAoyo1+oJfEIgk3FqC651vDXf6bf/S/8O3NXZayaHGRRnDabBWzyKwxDbXuDVJrmYRirV7AjZpuIr4lWZmluVGC8OUiCdRbtrS4YRIBv/Al6oSVNJJx8MqUK6cS91ozjyIWFTDt5D2HWdQeNN1kQQCxltj7QMJipsh5aqkeAavNNRCBaLYExSnQIQldr/BuwZ1v/BEO3rhD9/abDPuB4e4Ju4cb9t+/R9oNDKcP2R3fbaihNUKu+G4XaToiIVgMNEVGsXQZL5G+IuMYzI6QUqLW6af4MlhhagsqqYFB1WLfzUg5RTIrU8g1hJSKzb9MtViuGXZ7Uo5A42jws3/2F/j7v/TLPHrvOwiFCizTDf7IGz+PfOXNf9pLLWhaBKQrgqYFWcPxVlckCeqZrAsW3QJ353jzHXbjaZhkHmF5aSmuhpC7DmHJ1/74T/Jrf/uX2G3OG3qxnUJbwekNoaH5Em6RWCbeJLBDSj1dn1mtDtnuz0g4r3Wf4lOLN3m9f5NPp5u8298OlCqFA7tjx1k5ZVNPeW+4z689/hb/4Mm38WQUs+YfCNP/IwrVGlzc6M0bgbcAY+y4zQhr1Q6xirYfXfEGeSOzq93iBA11ChtmxrYual/a8ATasMqWyybaA4vItm2aYqqzmn9MJvjvAvkVqET+VjjV8e0cQFMLLcGU7C1h8lm7KqAjpmzt3C9ZfvoOixs38JtHFBz2kRW9e3ASyNZ2B0kYTo+b6SJz5NtrBYZIGLXmETXES1NCNGM10DqqheltSu57xt2OVz/9ad5694v85q/+v+y3W3LuqNUDHIDISphiY03zqbbQejtjJ5Jl+0XHWEBqjfeswue/+hMcP7zP8Qffo9ZmFnvmzuEfiHqQcO52Yedpj6IkIt9KNJGlZ5F7kibO98ec7R4w1m34HaJUCi59QxbChEA7xgo/+bN/ggcPHvJbv/JLaMooURhlHohUmBENnjFDU1g1EYGmpdePyN7Y+imlDnjK3PW73N1/j+wdfe456o/oXEkmnJ2fU9Wo2TjdbznZPwFN5JaeoBKEyhTEm/Q9LYu2BTYv6lAnU6ntOWEKJQtkyG0yVWiSWhuYZXOSnVqYX1P2qMwBPvCWTRua6qIGI4SIAbuIp5gRqb1cctRLkEDTeFO1nJiASphaKaLGYb5prMN9fqdIZYp38pbtQHPcMaHsd5x863cipoZNv6cZ8CxcChgGU7vQMm8jTcgdLHnLv2oM3jKHrdaWEdBsPLfZSfcaAnR3vmW321BLJaVIYVJaDUgTtJMuBBpzGNOP0HqFxcGSYb9j2A6kLkdWhwew8Tu/9ncxAbcaZmBSsMKD82+HD1J9aBLLIvvWEqodmtcsdYkIFN+x2Z2C17lAKYr5erIu4l6rWOrolgeM52ek1LE9P0Ul4EXHKcM5Ttss0VnF42E3ultzypyk3lAVGspmsa8VUqdUg6TCWAaQwOeHYWC1XrA930WEXfPs9Nr0i7qmjSpqQNoShAlO1YLKKix0Kw3/CaYwwsw3Dwk3JUJOPKNGSGyPtUS6yWQLNfRpEgpzAZageinlwTTyhWKXsCmFfzb5vPkf1lBGn5nA57RubSkgIaWbMoq4i2pbF5gK6i0i39JWRHxOew9fqiaNAAAgAElEQVQ0M8yTuKT9u/k3eLCYqNClzDgMF2lALadqCvRFAVvL1NDw5XJK1DqtMLSdtk32loOWUoJilFLpuoy39UcSYjPDSg2onIjwRxZz5GjNdSOTDG7BzloKOS+pZQwfePLIRKPeSYWDg9vIV976plcbuKgjbuaCXah/awpcRRtBJXJaxbQi4LXZ6pD7NfvtGV0KW5taGtE4tQy4l1CDzbacgpCR2t0yRiXiDNWMqTpAJgeW4PDAqltqQY16lJTCpBGikMY9QM441mCGQI9a6fCEHBkXNn2LS8xahLClA55lsqNQ+kB7WvLfrM3jjjDPVKbdjGS/6ffvTJsp3Yp2JnODcHUwRcSCOVoeFM0fCf+kBtO0e2Ay5cK89BZAhRYLsdSYeZKxNp+ratR8RKBTW9LpZLrpnLs0wb8hrSfmsklmN5BhzmVof8ZeBzNag2u1+XmhxbQxDkxrbjUa7bqUEtVD88UaY54JacJlTs5UvXjFKUU/TOUpUJvaB9oES5uoZTfP6yICmqQDMq6zWo3rG4LScpfco9wzaCNgYG3pCMUc9wpeSR2IZsoQOTWWV9iwxW2Pk+frQqqMTXJGgp7QoM/WFFWltnqQZlcCLk1dq1FqiXk8nMDJ8bTJgXXaARC2MCWQj2aezNmzU+Zmk7Zhb0y7H1ol+L4xSSMas1Y0JBNx0hx7GiHLfFhP/aKXNcZsyNVUlmgSRFSJGocLTpnIv8nY5qPJpRYkEX1n1gyokJCGxjVtIQ2unRifyazyYB4m+mx1Hg24kMlH8aZBJmaBZsJFvtlsIrb8ulhLzDX5m9O2JpEoH5DYi4C4pZ2jtGwanT2HcMIvTNYpmySlTC3WYO64xt3pup4yFlQKZi07IR+xvnWT3ekxZmPQA9LoJAEJ83JxmG5YUrrazPF+eUjXLRESt195PXwRD8mukpEUEcqUVkhaYF6pdYhDyBkb94zbDcP5KePuDK9OGXZYHYk6gxFpm28YaXWHaesUj8CYGVm7ppEmFCLSPNCEaCQzhoYA1ymxTGPD28aGT9Uk4URIHmkYk6s6E7TrnCaNtvoWVy6oG6RtqCCXTpsZBQJvxNPW4HaRisEFdUwZvai17wQ3p8tdpJ6YzSCA2ZSNWhtokQDFvGKN4c2jVic03aI5pvG6Zs6c7q0NvmxxINXYi4lpVSfp3orDfH7FVs5q8z+kdX/Rpk3CZQiTLuoPmhabdrq5FUygBFG9KQ1F73Km67omlBtQW8JMstYfoVsetv1qmc2eo9al2qxNw5ULFT6OzSfzaOiRu0PMtmwe3qcO+2C4ifaaQ4+PTYolTJTl0QFuwnp5A9WUGkEJmjueHD8haw+SyWmFpgNEelTXOJVx3DDuTillB8OWsj1Hc44NttASwoCP26gx1oZYiKDSI2qU/eOwC5sZ4Ciq3hCESMdAEq+++SXEuybpmMxUTBSrwQDW6oujtt5Rj+o4nUT6bAZIoDlqzT9otfHuMzEEgGCzyDcfsZt30DvvYFTsAu2lYb0zo09MMlVQSFMQ0RYmGDfgxoSmbi5aGscmtUME4y50KZFazb+6RCaCRaZvdEPpyN1yTiORmXNpjvKEQAUsrX5hDhmluRuRAdHcptjzpiq0tQrRhujRiHXG25o2UbsAJkL4SdvnJtEbCCEWGkE1NJ00TWhjYdF30e/AheqJo1dep+sX7X1aqWpDq7rFIvKRPUIBoalTEzbKcnkUMRRtprsu0LyIEIFGWUG/OIC8bn6VNKaNnLJ4F2HqFLPZPUHFhbIfot5AJFLaJbFYHEa6uo1hJpUNZdyGNpAW4TUL86pfBRFrZP1MGxp1EY5JQrXHbAj7rw7NOQ+bZJLq0nY/pSCitz/3LqQUNjWTeRCELw3muejU0UBbTUhLwTCVSNOmYlZmh9kssqFMY82mocVcNZzJoOYo+tpvYXPaHOOLUjG7ZH5c0I03TQYmTSvQMenCKdHQWoqHBvUEP1ZnfXALXLl1dItF1zVb2xug5qxXSyKImPE6hiQUcNs3ECPD9JYi0C05+PzXYH0Y90GgaQYq/fQG7QnBHOH1hb81SXFE5krlKMQPZg9ULBJFsZnF5iCnQDSvkDgds9COKXdR2KSw22yjbHa5JiVh2G4o4x6aphuH1uUEKLXS5US/WNN3ayJ7IBz/5IqkEE5YFEAt1kfUuo0cMwlhMm7P6ZKQ0qJpj8rhjVvkbhFCwY1hN7BcrqIu5Q++9afdxPAWcKkt1J5y63jhlVLGhgTY7NzCZAXTwvWX0+Qrahe2tbtHJZobU4Uiri0yGuLTvTamCckRxfut60krfZV+ge83XBRITvlFl7zsaUGXcpZsRqJsZhCd7fHJu25wrEzmnTFV+03EHYQ/NRLQYLqpGYC01filSrbmj4iEfTvFSZx0kSKCILmn1kIxGHcDmlr1f1IWixWljOQuU8aRg/UR2+15+HQSiBE4mpYhaaeSRhFYrli+82Psv/Mb+P5kjpibNuDCnSkrdsJnwuxw0OZXTLCzSuxbCgjVWuxqRsWaDwCgWaljS3AUj7qNcWQq7e0PlngBsUp1p4rQpQVlv43MYElN8ET3HMxJfRelANDUlkBNrI7W1LJnvx+DkRIzmkVrzuAyREYBICoIgZJJqphBt1xhw4iLsx+2mDu3lq9xZ/0u8uPv/ll/+4uf5/vf+i22Z+czkU9h+8XhEVZGxu0J1SrS+r9EYKmhI+2uiNhqJPLNAbCGVkgOT81acqIKUwK/Teq81WkHOi1hN9cpctyR+gV1f9pszwubO2SxtNQKv4Szc+FBQxxs81FCIsa7GtbsfENNmtmhmLb+W5OamNAhTVQTEiWeLRP7TMwWJtrTzTAsCKcWhB5JyjiOjKNB2fLOm7f4+hff5s3X1miXeHI28JvfPeFv//K3MO2R5PSdklxbBLo2h396tcmubms1qJpAldRKUE0dlS7sdq8NLTLUWt2clGZDMgfeZl+xIVzBQDVSahqYYa2VT84ZSJQyNGaozXeMfRF1lsslu72BDdF2qV+2rGPHxqjPSLrglddf4/7d91BNLJcHbM5OgYpmBc1o7hGEYbdlqlw8WN9kt9sCxmJxSBm2lHGHElnquJE8IX1P7hfsz47DUgD6o0NOnpzyM298ky/f+DrDVlh2N5GvfPpP+VjGCI40x0Ul4xhlHOaqNfexmdzaEB0hLw4oZY/jeI00CFOZ4wfefAORqFijIU40uFAn2Sw54EnaZxFsaBBfabaytOuj2EemiLdN5k6adMAljcFkYE981DKPabGRCVNnhqGMHIdbhhCsOsGPje5aPCHQHGnfaYumt/QSn2GrABIUrDp33vgUDx8+ZrvfcfvGgq9+7jY//43P8nN/7A9w59UllE1baNMAXUc96fmVX37AX/0/foO//a1jvvfkCYcHtxh2jxqUOb1cuDpJerBg3HhPm1M3pmo7aekeEHsz4ZQmk0BpyRpz0K7BIVMXR2lOsLbzwRuCJ03TNH+r5XxFBoGiOWIW3/xTP8o/9xf+JO+9d5f/+r/465RdCLc6FrrVmpyW7McdVraodLgFerlaLTnfbJrJnFgsV3iNFHrzSuqOEArj7pzFwauMm7OY1yDlnpQX1LJv2k1RKVQrmAtfOvxxvnb7j3Fn+Skebzac+5ZdqsEgxVqktiWDSavzGPdbSi10eXI8L8M4/pSUCQKJgvnKSJdX9P0B280DpghL3HlRtok2z+FSKsRk7kzJcqHSp6Kg8Cca5XMxpvsmY+iitErxsPO5sO4mX8Z1mm+CsqCmnpxX1N2TEBjoRazkqac2LdFMLms+XCisiUHadQ1uNHdONnv+7M98mb/4C5/np770Kmsdomy0Qf2Xs1oUkKrYoyVZ1vzSLz3if/i7v8n//Cu/FdnX6QCzDXOzPErLQoj6FmwDKCmvcBswC2IOZmomr1+cSXSrgogeAQ1ChUDMpnSUKXIuEsE4Y1LSraEfNVojTSlENNTLoV8Yv/grf4WSnaNVz3/07/41/tp/+zfol0ru0ky8KWdKGTi89TrDbsdYttQ60nVLbBzw1LNYHOBEPfqwO6db3MB9pI47+sURw7CfETuz0noC7C+sYDHGofJzn/5z/PiNn8BH4dhOeFCfcOZbdpzHefQH62iVYtHWs5SBcdyQVmt++s//HEOJuIM36YnXCM7NaEJtkc8CLTRX3RjGXYPwohxWpaUhaEMG3cAzmg8umIKw/92a31N9lvJCKzFTnVGfSFNpTuUl0hWcOfnALyE1DpN0j7SSWZDGwdQdtn+MzgwXzRFmVGoeE9c0BzWlIBqNGMs051QFbibsxh3/+V/+M/xX/84f5ac/v6YbzhnG2tC1JghUmsKK1Y/ilGJsxzO+8PoBf/ln/ij/6Z/+Wfa7XQiD1IE3YWXRM0tsRGyH6BIhU23fIsyT8IlOhZqiVMEaiqbUaPxAdDec877a67ppVPA16Hqqu5k23S18DmuAShSVNTuhtfrZ70YObx8gnsh5QSkDi2WHdgmrsecHh69QSmIclZO7j9kPiXU+YD9mNsNIf/Qqq/VtXFpEfLHi9p23Gcdo6od5MEkfQMRy1VNrpQw7lss1KS1AjP2+8Gfe/hf4yaOfpg7wuD7mvh3zhBOOywcMdoZ8+a2f97xIDMMZdXBu3rzJ2emTJvgqVlusgqmIp/koEr5CdVpUslkps+PbSKg5wykpQg8StckBiwYa5ZZQH2dfJKK1TmS5XsC0UfqWg3BtvHAoJ63WnEZg9kUCvg1NJanD6tDEnTfpqRO+NEfZteH/LTTY0KZJrF+AFMH00xomsUQz/ywCdRguHdoP/Gf/xp/kz3/jDfZnG5IYSXRWaFMsLGRuAy/EqOcd5WFE0M8/yLDPjEPHr34w8G/9r/8Te4nGCmIOKVBHbSnz0MXcFqkY5lGMFaZh5Nl1XR+tUsXnKLkLSDNr1C7gWxVlqlFXaY6uCOZhGjdco8HZ4R+JT6YmpLRgv9nzs9/8An/5P/5X+Du/+Kv8+//2f09eKn1ezBaEV/j6Fz7LF+4s+Nd+7ht8+9t3eWt9xL0T2J50/O//6AG//OQ7POEUT8L5foO3miYvI5snj5omTZFRXPYsFgeYF8b9EOisG3/w6Gv8/J1/nmEoPPYnfCCP2NmO43qXbdmyyEvkG1/4i/5w+x6lGllCCoTkCCfLcVJaUMZ9qOSmmqJOODXlHFFqndQrrdKvHbekTBJF10ekrmf/+EEYQd7C/UR6eGxw8wmmRrDA1DxAmSRWSO2LZl+JKetw9j1w5oj1bKOHbyPYJZ+oaRaR1rN1JvOG3kRS4wyDTqjR/H7aYiMtDcIa1NwcH0PYDjv+w3/9n+Jf+uZnqbszshtJwgryGembYhcBj4NQB8EedlHSPiTO73XUIuy2io8r/s9v3ee//Dv/G2cl2uNcRNgjoKgN7tbWbX0KYEZwNoHkmViwIdqbti2IZpVRxTd1xA0/xVswUUldF5V9DvNvZDRBaUxMGh9MQsYsMewGNpszct/z+huvsjk94cbNW5w8rvyzX3+Ln/nMG/yJz9zhtvac3uvZbA7YnCm1VB4e9xyfC7tcuevHyNGGv/nB7/LbT77LwcER+7NN607zmC73lP05PowXdTwKpcJab/Nn3vhzvNN9nkf2kLs84jEn7OsZtio8OX7CMi3J6+Vtbi+OqLblNx/+Brk1ZRBtrXPyMmaN7JBo5mVR1B+Ja7GRczHOU75Ba4YsQQhzFKExjFNJArWU1j+VOWt16tTIlMUaGGRrKtA0E5cd6Iir2Gz6TzGT+cTAGj6nF96Uzfc2eHf2N6YGylMbgICmAymb/KiJvWI2aw3hJlABhM1+x1/45uf5S9/8HON2Q/ZKSiFZxaSVwjT4nOb8W6KeJ+wsRfHTqOwfB3K2ORPEEmenxpcO7vDz7/5h/sff/b+jTkUbvD690gQwePgRjsVPE8BcrxF5b9M+WANZiFanCKnVWsyZVR7Gq6hHR5HpG2dmwHj+RcM30JbbB+6Vbr3g1rqj73t2G+Po9mss3flzP/sl/uU/8i6vpo7hTHh0d812u+T4ZMHxY2U3Vs5t4LwO7HcVoadshB/jC7xyeIu/v/0WJpWxFlK/YHl0xP64sN+PUywCt6gJeUVucbu/w6aecZ8n6JHg45bzJ2fUx5G7dee1Q7R6YcPA4ep1vvTKl5Dk5EWem46t73w6esJKRXI0htPWqTC8yoAFfa6emw5c6RdHeM6YtRiKj+xPnuAulHGPjzvKbhfM1dquhJoPh3DiemVKG59OPhIP50xgbZh3a9DAnHB4iVcbAUabfJhzQ6CBD00fiUKagk4eyFDqaQD7dNyzhqHBhy4SPzXQwI7UdVRzbh8l/sq/9wuU3RnJo3eTTATWUjzcoYyJcZMZHy0YP1jC455kmfE8sT/u8KokcQ4OhfUh2AjJhJ/51Jd5Z3mHsf0cAo2Zo3k0AcdqIiVBPWrCxabu7oLLnlqbo+0av7eitG6I0hz7JmwIX2lKaowOkNGzS/XCrI2U9ql9rTTEPZH6Ff3BAa+89mrrAJPJywVnDzf8sc+8zb/50z/KURV2x3D27Rvsz9d87/2e9+8r57Vyv2x4OG45r5VtLeyssB0M3SfeLK/z0wc/wc3ukP24Z9ElTu7fh8UKXSyjPqkJjeXiBjf0dZa65p4/ZvSRew8f8eTxGUULlgok4f17J+hghf048MH2Pq8efoqjdINxbN0Sq/Hke99tAa3cUkVaS1Ek6nskRyRTWvMtkajW0vhNDwDVjODsz89ICVS9VYcq2vetXUxCU/zWh0lkv8YB1Sb8IyAXAcRG0B6RWpnSy70SjasnTCtixeKhEaf0ClQj6u80UiptjtAYkW0yReudauOcr4SDaQ5faHZ6U/gwtUTTZzHqODKWPf/BX/wpyvE9xCCpX9RAA1KhDMp4f0G922PHPb6JpuB1p5x9H8bHHV6UcScMQ2JzLhzf67EaKThSnD/9I388hJA2Z4YLjQER0bdaWlJqRbSgGNULagnVaHXj7Vq8NSnX5nqphVOeNNJ8WnLrFHCcai8kTXUmErBuywbGHV0sMA2U6vGDRySFftFR9wNffPs1/tWf+iKyGfGzJdvv3eLJWea3v9vzZJMwBh7tzzgrhfjfyEjhfNyxLSPntud4HLGt8ln9DAtRtrtTlgeHdMujEFwlMqBz6qgM9NqxrRt2vmXjWwY2FAa8thCFF7p1IrsVxlrIwIPdE9555S1+93Fl7x4R3BZYs2YOJJdIP9aIPYhqU7uOdBmqN+qMh1AdWa6iax5OLaUllYb26boVIwOpW1A2p6AaLfJLZOCSwlcQU1zrrGGqtr5Tk9/gIFPztKnaaDLTTJtDXqeyj6bnJk5aAZfa789tPqepphhJA9G4gJ3hcpvRFBWWZaCa8wc+fYNv/KFXoqOfxp6IRCo7LpRtpp50zJFsab22Ns5wOv2UQcRQcGV73HH6ZM0w0soH4rmf7m/y5aPP8A/Pv0Mn0iCVCT9y0A6h4lhAtOYkbd+3ZtxxyokqLT5UPVLum98WmrJppgkVt2bqtqi1Jp33aPpORVqwP8p/49ennK7LnJ8cA0v+xa9/jrfXK/anzua9FSdnynuPVpxXOGfD+bhjVwvVjOJOlcpZGdl4/J5LtWimty/w5vo10sFX+O3hAzZlZHtyEnSSc5RnizBuz1gfHXBaN4wysqkbBt9g0oSjRP+AcV/I1cPZFTV2tWDS88VPfZnf+P5vYpoCAVgdgQvVC2UYcDf61QFqMJQRkwxSozWoh9O2XK/ZnJ9zcHSD3W4DZURzR6XiLqTFAXXYMIzxWxR13EGX6bTDNJhQakgmi1IR1FqbHG2BLbuUZTvXPyhMVYHQfJHWU7b5JOF4l0iFMbA0BMqlUwpF+D5iF9GfcDNa1Lx1n5+Sr0N7VNTjEDUtGGrha5+/w+11Y3BacFNa84d9op5F1WYwRgiWunG2x7nN24qrRmW/T5w8XMV6GoMN7mQC2/+pN/4gv/4Pv0PuWtd2b61+FLART1FlKNZBS/eOBtKOJMG0lWh5gpzQOrTsZgNzxgrUPaQwJVOKzvw2NZCYEkdnhDAqKKef1bM6oC2UgBr7fWWxOuL1LvPzP/Yuw2llc++A/djzvQc9W3Pul8dsfaBYwcwZPX4g77zu2bnz6luvcPeDY8quYEV4fXnEOwdvclhf4+3FV3i0O+P+/gF1PfDb9/8BJpXNcMrNxS1+5PAL3B3vMqQ9SUdKjV4C5pC9Y6wjVStZwnPCDMZUKeOeBHz2tbf5ztl9Ts/27HbnWKnk3LFcHdDljs3ZE6oS1WRZKKNhZQh71IXNdot2qfU1MlAhr1bY2QnaLaIZGJGqnlNirAPqymj7QNGawR8t7MOeNm3lorT+T61E1a11F3kK1bLZ2YaprqMlGjaJKdJ6vFoA2YaSVHCL1HqSthLxVhYsMqeiwMiUGi+T79Lyo6yMeN3y2bcPubHoo2N6kjnN26tQtwmpk5MexKkYwzktZ0thaXhWbAfjk2h947SfTCBKEWrd02V4pd5mlXuqt1T4RDCX1Qj8VmOR1tw5+AwPz95nW49b4VmN40kSDSVqxccI/NRSkcWKg89+jsPPfZbFjVvs37/P5tvvsTu+Tz19TLTtlBbDaFoydHWrgwq4rs+ZcRhxTWjfk3LH6aMT/tLP/iQyOsOTnrLN3H0kbDAe2ClnPlDqnoowRksZ9l7wXtB94e53HrB3Y5kXfOnmO7zR3eJxKbx/9ojRDeuM5eKQ890ZX7j142y2j/nqp/4wHQveH+7yRJ/gdaRYmWmj6zr2w8BgA1mEXMseEaGUQq/R7W477Hh9fRuRR+RuNSfluRWcnu3+LHzjHL2DUiesDo7YnZ9FQVVOeIlfnqplIHdLUKGakFc3qcNZqHvtSRTKbkteruKnxIaB3C1wVcp+SxKdW9FYs2fRqbotovHa1PnkbE9MMQURoRVqzbESa4KxZ33ndbb33m/VZ4HfT/PkvKBKxUtk3yZv9jhMgD9zWW1LoNOqVCmslyveefUA9YokCZNyTlFJ+CATKhoelkDZJsZ9aLJ8O0ys8cSwvXDw2oj0Tzi9t2bYRCvVJImcMlKjC/4rqxvc3z6OZuyltnw4QXPGyz4Cj2mPyTgXQMVvGLZfYcJbZ5Aon15/8Uvc+ae+gdee3e98n9Pf/V2SQF4csPzUgro+oDx+RBm2pGQB+0s01ia3VPUa4YKxZQYnqxy99irLgzWbs4HX+4yfd4xPOvZFON7C1gdObEClcOfWAccnu1ZmDSf7HcOu4CL0q8Ryv+Czh+/y5HzPd8b32OqOM98w6sB+v+HOu7d4/7eOebd7h6+9+nXu7u7ymLsMukHdWKaEZOVkrFRGtuOW4gXXGv2jiw0N4lfGcaBPUEX54PyMo3SALMGonJ4+orrhw4bcrciLFQcHt0Ayh68dsiuVQy+c3rvH7cNDnhw/wayw94B+1RyzDd36FepwijL9UE4P/x9TbxZrWXrd9/2+ae99hjtU3Zq6utkDm1OTTapJUSQViiYd2pY8hI4SS7ZhKDEswUAAJ0Dy5Ic80EBgBEaCPObVeVMC5CFG4hhWFMSDQlGyFGqiKA7d7KGmO59pD9+Yh/WdW+yX6u46deqes79hrf/6D9qQvJeHZeSqLjmzWBwwDEOVVhasNaIZqc0ytT8qei8Wfj7ag31DX573EzcbZ8+/Qvqp529WlXLy/iVO+z9YjQ6Q3BRK9YEVWLekhFEtOXmZAyWNaxW3Drvad1Q+2p7XVOQW+UkVIkAYpDdgrpnOFP7KEKJFmQxNwrjAbBmYtm2dlRSEPCLs15mdocy6ghmCxtE5OLpN+eAR2SYuNx+QKSjrxNg6CQsgIVY6JcvnOX7zk9z+S1+nf3xF/uA90tWARhF2K/I4SI9CRs+WWGOljynx+WFa5ZTCyxPdeqny6P7imvFizfJgydm2ENctYdKsdomgLE4FPny0IMZMCQrtLBsibatY+YmYM75kUh95ZfYyz7ZbtqlnXXb0ZSTkAZ88RWXeefuaA3vEg/Y+T8annKtzYp6wWXFoLX0MXE0DI5PcviqSSJVPVrDaWHzcYNQcUiIQca5hPU3cOzjhJfOA75//gMZ0HB894HB+xPWwJtsG2y5IZNaDorQHuMOO1z/7OUIpvHhyi1Zr3v/Wv+PPfvdbLJczUI5+dY6tdpMaRUkF21iSD1I2mRrQkwtT2GfbaYyz9dRLUtfuZxpZqBPUpvT5TKOWQqVuG1WeI2F7vDYlptNTME5IfT5jGpkya6NuuGaiw5ehm9D2qwFEbVSFZRCkEVaK7uAIlQdaIzBQURVJo+qny95s7jlNg6IxDei5Y3hkGFcGHzSb647ZrQm/NgSvYWoqgl2wtVtOMZJKwWDlECsStBOmUSSujx9jrCWkiLOWUjIxVXFbPSSUc6DFocbevsXyC59n/MEp4YePUNaglSLu1pRhoBRwWuO9xrk5WbUYXd3bQ4+fepyz+DigjaJ1jhgVs/kBk19Jk37Q4HeRH157dhvFxkcudpq7xwld5jy7DEwo+hjwJDyBzZCxxvHyySGPnp7zsRde5eIicRYuWNuRsewoZFKFn1UFbl50rzCkkXP1jKgikcRdPePae3bZM+qJlIJUCyXfUKpiHrElFaxa1EQpoSPkVDBGc7q9ZuUaPnLyEZ7GLbkotlPi5Rcf8sHFtUQGGCkvgkmkMfL29x6hMNjukqOHd1h88Yt86qMf5d3f/D+JFxe0czlxvJ9wbcuwXaF9oT08wfc9VokmRRmDSUJPT1FzcHSf3eoc67oq3Irso6jzTfH0HNHS9cbIWlGQ7IyyR2j2L8q6ug4WirLc/atf5em/+A0avV/4z9evrlRvlEZZTQpJ5iNR+GaqSmMVMOy2zFol5s1qT1W5IbzApNhLBtR+kp4L2RvGZxA2Mu3dXB/gfcY/m0l7U4et4ifxXJM/5UQk4suEyhFwhOCFnBeeT4/koSfhahOaEcsAACAASURBVJW9WUMWSXV10I/Bs3zp46hRE947w1iB1QuePPToitTFGMVeNWdSlAjsXISwOZstCXGUX/1ETIWSPcMmoKyhDwOLxnLfHvArH3mDbZ/ZjZnbC0OMhifryC5HNnFizIkxSx6kyAo0Fxc995e3MTvD+bRmy8BYtmSdySmTSUSdIBdMscxMx1k6wytx97xrZoylsEpjpVNFsko1l1EO1ZQnphSxghAEnOlwlZdfKrfHaAh54jzu2I07si5YbXl2FmjbDms0U4jEeYs9WZKvgwypVKFMgev3npFjorl/m5e+/pd59Jv/F2q3I4RIiYEpRKyzUCS11TWOcbfCmhatIYWItTN++s99ma/89b/IP/3v/keuT59IKZAyxjTEKCKavHdnLIkbljB7QwdTrTO5uVW0Ns/7iQKqJFbf/jbW2uc3x36mUADTCI+rVPcVtXdmURjnKMFX7LOgTCYmy/nlAOWEQpTJHpY4WfJm75RIdRpVxEET1paSFCFahuuOECMUK9Y81Hlo/UwFiGSmlNimCaVkQSnTQq5ewCnVVNdSIWyp6STGsOCajilGZssDfMzQFh5+8UuYOy/gz9boWBGq6InjFm20iLsmL8BJ8sTQC+iRyw16lrMGhNpuXSPDydoDjj7yjbc+zt/8qU9wog9xZ0vOgicWhcVxuVVs0sAqecYyMYIsdGXptBbkTht6n1jFa67TJd6M0h8bIzd8arhd5hw0S1o6dnnLwJasxM4Wd8TFuGHIPaVkkqqU0orKxeQZ48DB7AirSiTj8TGCm4sBdehxTUvXzpi8pw89RYm+o6jE5BWHrcZkjU+gNp4SrsXf1zbVTaSgUmZzesmMwvzBbW5/5i2ufuf3mB0d0J3c5urdHzObt0y7HcZY/LTBuFbYEV4mtKkEzi6uOHtyRb/ZCEyqqmB3b+xck12FjQqgqkdahWK1rqtxr0ARzQLAT3jDEK63YPb8r5spWd0k+0a/6l6UpKpK6f0TREsSyUMk8s67I+m8ITpkpjBqymgFktYyuUYXStRkLx17LoppcIyTuLqkauOji9BDxGFF2ourMbDxgSklJle4HlcYa+VZlfrZ9lafIDpwwDUNIYz4FDBNQ8Rx+NIJL/7S1zg/G3ArhY+XhDoPiuNAngZxUCRWFkUSBSAVKkYmoKrSgpSpPlM5Y6wl2YZ5zvyjv/mzfO1DDynvQYozLvqJ7QROGXZjZqsiV3FiLAGvCp2Fh0czTq8yayL+WLFaD8xay/nFFb3akUsk6gI+cqSPuWseEDPMaNiw5jw+wyhYqpZb8xM+GFZMeaTsCZrCniKXTCoJHwe5bVPAylBJMHjvtxhjyakwhVGa9qa7IQpGpfApYYBbdsHWT8wODlAdvHd+gbKeMpuj7VzMDyhk75lOr1FK0b7+KieDJZIw8xkvvfYJrM588G/+FX5cE8eJxeIEHz3KgnWGfnXFj7/3HS5PzwnTFudg8jKhzznKIC1EfmL+x95UTHrt6hFMpXVQh1WVFnGju9Z7Zm4WZaQqMtvQuiIzEWMPUWUSNV+CRMSYOsvIYp2ZouKzf/4X+e3f/HW+9f1HXJ99nHln8RmBwGubVLIRKbGFUjI5Sj56mDRjkL5L1YwPbkRO9fNpuBpHtiFyFQNJKd7bPiMVj84Z1xyIijGPwmZQtoZdBsgBv4sS450ypTEsP/oKd77+Oa4ebQnvjwzRo84u0DGJGGkaKO0Md7ggPD2XHjEEKp/1OfiQM4mM2csanCX6BLHg2PFf//LP8hdev8PuTyem7YzBBzY7Q4iB+UHHZixchB3ZZO7NFN5rbjUtmxEmk3maBnanG0CznjK9mkjKE7VEah/bO9zTL+Kz5Fs+KU/Y5oHXFw9ZLhreu7zgvd0abWFKe6d6OUxSJc4OYSPPV2nGscfmmh+h8nMdhy5F3OdSIBVHSfDg+Jiz3ZqxFLLOfPfsXWaLOVwr7iwW3Go7QtG4lPBlZGwaCdnUmqZrkXMs4ptEPt9UHmEmAPc+/wXUvKHEwHh6ytX3vkvc7UA5lFUYBcP2VLhcPpCLEt/WaaplTapRwLBnKz7vNPbMYvbglpRQCmEHsE9Fqa58qpBLRCvzvK+RmoQUB/bxzVqrm4l6t+yYhoSy0tL88bf/d9pG8ydPL/mD99Z86dVjGWAmgYlT0PheY2dgG5lDSOBSwQdNHKomuzKU1d6xBTnlViFKUxsGdnFAW8vvPfuuoEkogt/ux5vVd7tglSHqxOzBhyndkq5xuBcesLx/j2Z+xNWfXeGfnpHPt9i7BxVpy5QUKF2DPr5FOK2bIydSnKp+XDhxezmbMUaAiBhxjUHpwjiM/OKXXuPPvXafzTuFfmXZDIV+EP+uo+M519eBkcLcae43hmnUbH3inSGwjpG1GdhNA4FEKoFEYqZaTDNjGEc+88abXP6wp8+B3lwyqS0xFe67u1xNOx77S6bsxT+4BIGi63wtFfF380FuDqNbUvbkPGBevP3GN0MMdRparS01In6poTfsYVqlJSJL7cNWJLm1957DboErGlsUS0BbxZiFIpFt9aRNGXfngOXDE0rnoJg6MykUY1DHc2Z3T5gf38Zfr4nDQEkizlKmCHfICNoSfaxEuHpv1PhfpaX5Lfuh3HOQi2oaW9ENxFtL1VKHWgaVSo8omWIUN4TMIlEFYnqydw987iiYYyKnQErQthZVNJ7C1cXANz76BuM2ESYIE8TeyDDSQxwdYdAQYdw2hNESRnszLFR1m08potBcBM9VmDjzfaW5Gz4YL/i9qz/Caot1LaaZo8iVECh9AN0Ry49/isWn3sLObqNnC8IuMK4Gth88pTw5J213ECcJEZ0kXCaFEQ4X6JwoqxWlJHKaBNIuInZGQ4wyW9E1crlxlhhkOj1ut/yTv/t12o3CP225XFs2g2W+6AiTYTcUpgRNV0je4GPhyXbkOgbWqXBRtqxyj+kM88OOPMBtd59jfcLd9g5GtVyf9ZRSGNSWrVphO4OLDl8i69JjLCgLUxjxJbA8bEk5EqJQ4WOcxLxOOXL2jGGF0grro9j4UBJJekxsdRUxriWlTGs1PkaGNKFsnfoWUXPlXHBtx6kfKSGTxx6joNgWmhnM5sR+JLEiHXaYO4dwfMTwrEf1EdNoMBB2I8uFI+hEc3KHk89/CXbX7LZrct9z+fbb4hqeIiVmtBPjtXKjr97PQupwDCHKiX6qLuZ9s1in6nv/I3juB3xjTsCeyCgIlBgay3vpKqwqJaG1JYdMyoEXX/sod+7f4Tvf+m2cayAm/u3jM/7n337EX37jZVTTo3SkqITKNZWkNkN+0FydLTDLDVotqAQgNDBGT1Ca89BzOvSs/UREAk0nk/j22XdwtpNProwcHlgxOCAT84Tqz9n8yTlXf/ht2TyIBNYoUyFr6YG0E3TM4KRyzAl92YAxzJxlmgZSTjR2JtNyIwYUjWkopQi6VRJ6NiOFiRAyf/XnPsnD1rB+T+OHGY/OJz78cMFq44lBsfOB+dwwazPvnG95MmSmJCXxRgd2eSThiUMkT5pDe4chZUYGroZ1tZQt7NSOwIQyMPSZY71kWzYcHy24Wl+TSmBKgUThuJvTD0NtyvcJXk7QtukKTEYXh/nEq1/4JqoIlS1Ebt+9xdBLsqsYG8DoJ2JJEhJftQVin1IEniwZZVtRsxkj0g4nSUa5ZLklgBI8cRihn2DwpJKljAsRgjBObdOwfXaNNhZ3/y7dg3vMXnqZB29+kqM33+D4E28we3CfcbUWx4wk+Xa62hXpvJ+GpGpiLCXUXvIL5bnzkJKCfs8pEnc/sf4RFew+Gk0+p9IV4SsaVKp9gVzPxjjWV5c8ff8DKXWKWCfFEvnDp4/59O03aYZbhFDz8bKiRIsfGjYXS64vO3w0pLElx0otL7JAz8JEUoXHuw2b6GuaFRQDv3v5x/xgeBddKoM6BUQQJTedbVvS5GXh50JjJdlJNg+1OBLGgdDXCtqIiXhOCdcIE7sWAOQYUUrmUq7piEngZK0Vzmrmi4Vk2VdAxEfNz7x4my/dfZHrHzdsk6VpHY02rLYBnyMnhy3rLXz3dOSpD9VNpuCTYcuWqQykKgG+Ze7jkyeonl1eMZahVjSZQiLZQNSREBOz0rFTW1a7NSFHfA6EJHD0+npDiEka/OQxuqXkQB8u5MCt7pHmpTuf+eZ2swEtsth+12NuvFBLpUco2tZWDpOuTng1XRYoUea5OeWbUzhlwZeL9+KC4iTEReVMXPfgE6URU7UKuVCGwLTeUqZE7Edi31OiNFKx0rD1wZL2wR1uf/KTzD/xcZpbJ7jXXka3M2gdcbsjh4mumxGmcNPYirN3qRwu8XDSN6XSngKib4aUek9MRFcipOT6iVncfggpt2k7PyCFEesamrarjb/GWINRsPEj71ye88bhh7DDAdcXjtXlnNV5w7BqmAZLSQayosTq35s1icLjsWflA1eT3BqlyK1jXcMfrr7Pd66/z94SQzIaBX3LtcY2riEUsE1LSVkInlqDMmhnyUUcP5QRNxcx3ZN+FGNx7YyUIlZL6YQx1S+34H3AuaZme1SmNvL93j6ZsZs80Q/8wmtv8EJ/n34yrHrDaqNwBq62iXuHjvfPIpdx4tRPKJVotCFmxWW+Zqd6ksqknDjghLZrGFTPNqxAp/p7HqsNXg0MaYSkMMUQ8IyqBwUxedkcqtrXKullpjhWE72CT1tS6iv4p7DKYv7TX/svv/nk/UcM25693rIoGbOXUv9da4KPdYEIQiHDKsXe2rMkj66szvITPkjSOCfBqUcv5IgkRELVOVDPCSBVvSEYlM7kkPC7kRwicbUlrXqUBt06YQSbFvfiQw5eeoXF6x9m/vE3OPrYJ1ncfQH3yofQB4cYt8BqiOPI3vbwhvpRyg0zHmqQj6LCpJUwrqtORNWSrvYdxjR0R4f4YZTyLQndW4o9g6QpGQ6O7kIKPN1e852z9/jaK59jXhpykgJKaykOVf5JWZJmGxPv9zu2KTDmyC5EQpKbTFvNty7+iN+9/jOwnQxMTSsM5SJGdyjhr6UQUM6hbQt18duuw7qWHLxsLWWEpFiFX65pianUklWcMm3bSgRB43DGEGJkNpuRi0RbmKaVPs1q0IZSAn/hY6/ya299kbf0Q4aN5rTXPL4qpAKzRqIrxh58hMd+YJsTX3j1hPUucjEOXJQrQqk1QNEcmTtcDZeMaYcvAtOWXIQaogpDFhfGTi1wqmXHFoj4GAg51gm5GI+HOJHyhDEtKUXR/KhR1mepFYdRqC9//u8W3/dMuzU+BnGXqNNXpRyuaYgxAJp21uAn8aUyTUdRhn0O3F69VqxDa8feoWPvEZXrNY1CYtqKUKzNfIZqWpRxN3QQUbplDCLAyQiJTmNQJHJnKX7i9Pf+LdEP5CSv11oEPcraKiNJ7I9dW0r13a2rsKibXoKbLVq7erWfzNd/srm5bQTdi0LeDUUm/1QHQGpk2342oB0lGw4Olux2W5LKPHCH/MqrX+HL994g5RFTElMCXQwWRZ8jT/3IdZTvOeXA4CvcqgqjmviNJ7/Nj3aPsTSygZXGNC1x2IojZk14MsaIktM1pAKlJKg8wkT9flRBqRarU7Ub1kTvaZdL2rZje32FcxqlJA7NKFVLKIttWwF3jMbZjra1hAIpbvhv/9bP8XBzSHO+ZLdSnA2KZxvNKk+0OfPGvSXBGy6uR97PE4/8Gq0Lt0rLRe+5SgNXXErmC+L8ctc85DpeM6otIXsUFovFaYNRTqj/GKbk8QwUlwgh4LMk2ebqoZUqiuVUR0ojEugkmyYX6cl1Eesh9dbHfqmM0wZTirBpn5+ncrJUYZJ4JAnl2xh7Qz0XU2pBfSQawUrDq/bXPVX5x81GEuTDVOdMhTq6LXi/UpQYSZfvE/q1yH6dhKykYcvs+DZ+14PrKH5HnrY384Fct48YjuzRKDl5MPs5SN2gWVdJqTSkFYiRor66f5CrlqL+uaKfDw0l9VZzdPsO24szik7YbgEF0jhJX5M9ynYS75CiBNwUKfNi9Hzl5E0+d/RRPnRwj4wkb4USmKqzyD4SIOnMLoxcTlt+PD7l9y++y6b0GD2ncZZp6jFaFHNi+GLIqWCtZKjkkmnmS+FTOSfGabupBmwFTDfHYPC7HcYZMgrXWikmjCL7UA+FOlXXomvX2pFKZNYtKyshcdDO+PIrh3z51ft86fg1zt4tXF0rEobvP4lscyQVxZt3l+Azl7vMO+PIRerZ5ZGldWy2EVUiqSR2emTIE1s9kYsM/kJJjGmUjV3l3yknEgVbHeflNtj3x0lSAbL0iqXEG8Xqw5de4MmzR4zDVsCMOMpBW0ORrLU1gk0XsA2khA5RFrQTG1FSqRl9tZAv9dqNimxilciq6hmVq8C/cpwQCvTeFEApS79+BCmIjkI7URpuHtd+R/xq47CV9KE4kr2VykhnhutnaKVJw1aaQOPqsEd6prQ/8vUent1fqaVeErq+vt5q5bmVJjflRH0LLX9OVdPnvdBHpvSi3Rg2q6pDV4ibuKE0BqsyySeKNph2Rtpesw9rsdXu//8rT/mjs/e5d7bkxe4e9xe3OTILWtug0MSYWMUtj6cLnvaXPPXnXE9rjDHV12kPlFRHYw0pi/WoIkuJZDTLk/sMqxVMnjxN2KZFuxpAZDRhN5A0uOWCg+Njrs7PyCFincZgCEpGP6bS12WKXtAWVBYu1vz4kDIO/Ff/3mt84YWHpPOGZz8wrEe5BZ+e9txezjjIjk6B8pqrYeI0JFYM9HmQ7zlDQMpEC1i0DJUBciES0UoR8igy7tpbqDqUDok69M5VhQlFyVgi5qnOrjSmQCDw9o/fgSJ0EyqruwZk3fxjc5lEGqsdxjWycEsm1hrWjz22dZBy9b7SlFhXYzQ11RZpDCmkKdJ2M1JOxCKiqBtHiZKIYURsrguYFqtgWq3FQTEGsA3NrGMcema3TtCmYVxfoVQmRuTkaDUqSMMJ0rRqpSm6wpcUKdduqOR7DYe87ua/lRLfr5v9VGRD1wdSSBg3Ex5VRppoXY0c0KToQRlcMyPEwtHLL5BTZPP4qVjw5JG0N6O2HbbpmLZrrIKw6/Gl8KP0jEdmg3/03ZvIA1mIUcwc5ERCa7DWiPt8SaTUMya5dVV5nvCaEW2JMZZY9kO9SNfOoHGM6zVt1+K9lB237t1hfXGOKtCvNhACOItG46triZs3rDc7UX7GiNEamwoHyyUK2K7X/JNv/DSfcYdcvg1+qxnzwLAWZ5Q3Xz1mt7Kc9ZkQ4d3NSNNqLmPPJkoPNzOa61H04KEkrtmyyz1oxaGasVMjVomfcUPDNq1xphPUsXLUxDUn7UkNZLKUgygaLSZyIQdCrCTF3Nf5lkh2Nbmaj+zXjMIWDLqVOLU0TbSzTswV2hkpQXdyTH99iSmGrDwxGXQzA+vIu2tMavEp0LRtXSyGfnche8YZQghkY2hdRymF2fyA3W6DpZDGNUm3uK4heg9OtCE+BHTRTL2nmSuIBbqW+aIljKNQP5L42IqjYZIZh7oJGZBCcc/OuGH67XVj+6JMy2mjKztWdkGl1ohjbQpicmebTmQoKVJUIaYkDiUKgp8w2jCs16TdhFWJcHOl7VWMI3E71LJNNPdGG4pVTLsR17QkoiR0Fcfy6Bb99bX0eAahpdQPlWu6kzZGaOzTBNWdXza2IuWEdZbx8kKMCmIgF4+2meBH2rYlBM/l6Sld21DCgE+Bg6O7+DARcyGrwnJ5gB6u+Q+/8CoPFx2ffPlFfvzokh89u+a33r8k6oZvfPohP3Ow5Nm7Dbsri+o0p08Ui7nl5XuG9XnhbFvY5sx1nwDN5RDZEPBkTtyc034gt5FxHPAqsGFLMhGdNOuSaXRTjbtbUg7EGNF4SrI30Xa5gNWKXALei8uiUoqYAqoUYkm1FVCi+ixRNkeScrzs98VP3iCmW5DCBpWTTLNtg2tmNLM5w27HtLqm6WaMw4CKYvViuzm6WKaSKDZjSiGGQU5N7Sha08xnjOMkVphKEXOEFNhNowifYpZNGDOhIDV6lk4iF42bN/hhwMwaStcSc2YaerIXpqrcEnvPLIkKyDUju1Rzs7wfpe9dEam1SEV5xDgb2Tj6hrMoWpBihX9a5FSJ9cSVmQho64QtW8RlMJdMXl2iSiGlhLGOFLUoCq2mZCVlZ0pkhOuTKKgIZtaBtugkUIHWMK7XcvFqwbUy8cZnVos1jNTV9e8SWyXIRky/S5I5hqyc+ndqK5u8RGIy2KbFGBFypVJoZgum6AVFVJo2Z/7Oz9zll7/6c7zUtkzXMG00P9vdoXm949+8e8ZvvP0OP//SC4ybhs2ZQ3eKq3PRu9y/rVldKK62Dp8Tu8Fzd2n4YJ24yhObkljalutxZEgD88NGBn6bHVlFVJLnl8ms4pZYAif6FrEa+UkSl68JDnL3+pRrsy0HWYn7IfieqrNnAEgv+bzKEICiGvHfbBKrjMKpGTl6FgeHUmuPPTkXrHN470gFmsUBqkTJwfYT03SJUlRnPVUFTQalDbNmQZg8bdMyjSPtbE7oBxm85HxjdUlphSJSP/DeaVHrSE4K1zr660uUdsyODhinCaVF863J7F0Wcyk3ZZ7oo6uBXH6eXyH0Wfl1bza9BxD4iUNDA0pb0XrkTPbCz9FGfs4CtIsD/CSiHKOfh7bsf1+qN4exhewrOJAlxRdjagMsyFgoCqdtbaUslL0LoKp8sVSbYyM2r1pg1JzBNA05JJLOWCXReForrDNM/VA3mCKkzOzggHG3Qxcxj5AsvxFVIOVM181JCK08TBOdi/z3v/oVfvZjt2AL1+8G/GpOvymMg8WPijvjIf/FVz7Fcddw+qeWgmW11aynwr2TwthHroaWmAvrPnCwtFxNcJkiT9OOpDLbMbPNE9oqTp9ei2G0Eag2l0yKEY8s+IN2zm7qyUZu55CnGo6qUCnfcKr2eYy5hBsoWGlB9EQ2Lr2KsKoMkITcqQs670NQ5RGYu3ff/KbSiil6XGMZt2vSMDD4CVOQAZJz5JIJWznVUpKHdhMhsF+k1CitGFAmMw0Dy4NDCU9pLCVKudF2czkVo8e0Hc4a4hSIKtN0M+I0ElC4tkMraBYLyS6JAeOssHjLfpZZcFZyr63RlbpRiVj76qr2VUXtIxT2nVg9bdXNuFCArgI5yGK3XcvepVxR0FpM9ZwzkmehSrVkzTUUuKCt/N0xpvrz7tG7PTGysFe8GSvvo4InBS9+uJKzJjmRKMmB1NA0C1LOAlEbhT2a8+qv/QJv/IO/AeoAtCWuNqgQKVqg8X2MtJ8mHn72pxj7HpMg+hFSISvFnYcvsVmvmc+P6NfnFCL/8D/+PD//U/dI20S5tAxnLVcXlsvrhuuVZrsJqC7x4octp3/asO0t55PlYqWZRvjwfcsHp1qYA01geZB41rd8MPT8OFzhkd5ol0Z8Dkx5IihJQZ6pJba0jLHetHtyodYMYcvWb4ThUDe7pBxTYxDEriiRb8AXo21VokoZoZXw+YwyUlyUattU9rmWUnVopTB3Tl7/Zgojadyxvb6iaeUkms8WDP2WHD05JdI0yimpZLBlZ0tc0+J9pFsuSFNAOyuik9AL0qMM3o+QIslHgRDdDLHyCeK8kZI0SHspa/AobVge3aJkCDGIwhAwRleqw74UsuzbMzfrxBxMHOloWncTD533CFZt4DU1sLNSnW9stIpCu4acM0Y7EQghyI1xdbgnkzXxMnYSOpoV0kMEoadLOlfBdZ3k3xmZqovfhBi0Nd2SlKt3WMmVWKkqNP0cdCvY+jOLUbi5fYh7+YQX/v3P8uFf/Q+w905Y/dkz0nkC12AWc6ZSqgWpxLXp6jq5u7gEP8lGdobbDz9Ev7ki+QmVa6KLdnzyxVv8vT//Kp0BtXP0Z47L84b1tWUcFDEm/Fj40BuF6UzR7xw7DBeX4JrMg3uaYbSsdpp2GVkeFN592nE+ed7317W/iUzZE3UhqojPnkVZcls/YMqBTZAOZcprxrwjpsQYtkzZixG60uSSnus5ikixVYGi8o1/msVWOpFQVWRM0VJyrBQjmf4XbTCqoRT5/wpqCKi2bHZr2m6fejRSQqSPK5Q2tYQouNkcjcIPO4xzeD+iupncICGgGyfkN2dIQxE0zCmKj6SsbtAurYsYYRtFzhZSQFtLjIF2sRR6iNEMmw2ubSgp0y4W5BilJ7EyFzGmUKylaxb4QdAIM5uhnSNst+S0702k5JKju2YE7suzLOzTkvclltAlUBrTtvhpwFREKISA2w/hqudtKnLDGG0Ydlu0lcY5pgp/p3qrZmFJS68gA8oQJLDUOEf0viKEhVz0jQn2nidmXEOJYkLQLma0R0es3r1g+z/9H0ybkTLW2c7Yo5KipIDtOorXECNxKlICp/3kGaxu2Fxe0LoWYxxKF4Yp8LEXD/nGz3yI+wcd9IV81TJuLDHJwLZEcK3mzh1FHgrTSnO10pxvwbaZe/cMft3xbCvfU4fl7DKzjZmzvGXKkaxCjX7XqMqNWjCnMS2PhydEPTKkDVGNhJrneFPmJunxBJyRuIWiZDOQlOjKc5SeDnVDSM1V42EQz4M9pV2y7HU1+vbPuXfIzMoOuy0lTYRo0bqF7GmWBwzrDYe3b7HdrLHdDL/b4honD7IorDGUlCgKUpBjWCDFQONmhBQoqdA0LaY9YJo2lJwZBnmfUjTLwyMp6cjMDo7ww07MhecCE4/9hna+JIwDJXhcO5OrNAyUxtG2HT55dNNxdP8Ou9UG2zYApH6HWy6Z+lGihguUWGtN6VzZ06xuwnxqsI5Qa0ZMtQdSStWNlaRUSwXrZigrb6Csoe2WlBQIUbL4tLU41zCNQknP0VNSIuaIMQWK8HFzjALd1h5KnPM19uQFwtU5ztkb21BdCrsff8D03mOS2tN8EtgOpbU4ohTpuaaCUNI1NwxldKEkhbJyi/ndCtssCWPAOcd//tfeBX8IJwAAIABJREFU4G9/8WXaNFI2EZ4eM61F1z5ziglo7mRO7mvWzxL9M8uwhWYZ6foFx3ciw5XlakhcDoXbi4wpmqu+0OfEOnhiiYw1bIgMuRhO9G2McjwaP2CnN4xhTVReNjTIIi5ZxFl7in3eQ+HPmRz7ICGlTKVJ7WUZSoRtWQ4cciHmANXEUP8EhqNKzdas5bKNYUIby8HBbVbr9U0/0M5aNus1tmlouwPibkWOiW4+ZxxGbj14gSl6Dh/c4dU/91mumwUPPvKQ+S3Du7/1e2x/8Jjt995l8+4p43pL4wRrFgTLY3TD6uocbcAoS4yia267jqnfkDPMFocM2w2u6ygUkh/JCozVxABq6Ti4dUSJme1mgz5e0L16n3bVs/vRY7rFAt1tKaEwbbeYtoUYIUm8Glk9T3QqCucavJeSUsvSE1+uFGicJaFIWZCoQsSortI3EtlP2LbB2CrDzZnofQVIFLbp8H5ivpwxbgeariOEhDGa0mqinwRuLLKA8+rZDWQJivnBEcNui5sJ9ScBrW3QjRMLUrF8uXG331vCmqYBLCn0hJQxyuLyQAwOaxtsihzcus8/+IVX+eXP3McPhTw1hK0ibTURcWSZ+kIz8xzfbzl7Z6KdWxbHmgcvG86eajZ6gY8b+t6xqTeiU7DaJnrfsC5rpsqHapTcsrFGoLVqztvju0QTiWkgF1/pF2B0NbfTcq7vmdipqi33sP4e7aIUGttK3+WnypiQZ7A/xIsWC919ZHfOVSJcZB2oUiqqqVBvvfm3y9XlBywPj8UkQMyfhH9VpFHOWoEPggyEjD0+pn34It2HX0Efzjk6OWbcBZTS2KVF353T3p/RtIWz/+1f8/Rf/jv8RmBgP42SQ4JGO4NWYlQmpYQ04NmPsqi6BSmI9iP1PW7eEWMN1uw6ZodHFGuwt5bMXjrh4Muf5vDNl7FLy+P/9f/h6l/8IboPjGGCKTCtd4hgap+AK7SMGxfGG7JlRlensqKEyp1iwDQtRiFIG/Jl26aDKBl5tulIKZALLGYdQ7+jFE3TtDIPSsI8lfBNCbBJKeJMC1aTfSD6USg7CpRBnocRBMtQpGGvgIjk0yeMsQKcFAXIgLGdzSQxbIpshx0fOmn56qdf4qc/fpevf+ol3n90SfZwqzlkypF7M0u8NOweWVBObH5SIk2KEDRDLNy65bi+GJkfWO6etFyfOh49tmy8Fd/kYIgq8mzKjCXw4tKy7mHt4R1/xroMkCGUQFSRkD2t7mhiw9P0mKBHNkGyY0pW1TZV0CmtZbaj9vmW1aDuJn4B2Oeq1GE/+zClgsRzKK2J1dU+pSD9Ymm4Nz/BuY4pjqymKwa/qSCPwhwvP/xNXSLB70h+Am3l1FOKdj4nDD0lBlLyzE8eoOdLFh/5KPbkPiWAxRIHL1QBpSg+w3UgnI2EULj9tY/T3T3k7F//ATkn2vlCHqZWtPMZfgpY53BtyzTsMErMD7R2RN9XZ+5ILp6mXZIoxJBo3ZyAYvnKy7gX73HwxY8RncZvR7RRHH7qZeYvnRAeXxC2ksIkULGvfUep2LngStoIdi+Q8fOIB+GhFRo7k7o3R6ythtMlY60Tcb+1aO2EJo2AC9o4sbKMgabrRB9eMk3bihdVKTSvv8Dhlz/D9HSNGqLoUIxMywu5ll263mAFpS3OtbhuTmW1ySDTteQ8cbBcoI1hH9e96Xf89c+/yn/zK5/jl372BT59f4EdCnfbOXfbGcdK020WrB9bVk8UOIv3mhBBGYF9VZHZz/nTzK2HhoODlvPHhaePOnZpnwGcUEUzpMg6RzZpQmHoPXww7djkHgr4ujE8Hl0M9+0dLtMKr3umtBGIu+ztTKu8YM94LtRGu4r26pgLCvsMRFVNPVRN79qjlwL3ynsLnV9e/+btn8I1B1yO14zJy6GDiKi0MphXHn72m/040M46UsnMZi3jboc1DRFhQC7mh/gw0M5vYRa3MBO4rMUQLQuao2OGmFFGEa3sfLVO7M4Gjr76BrdeOeHi23+MioWY9sM1ha1iquiD8H1SEhfvFOhmM2HStgZtZ/hpQBvNYn6X1h3gjk7QxweUVWJ4tqW7f0AJif6qxy5b3Eu3Ofj0a+TtjnyxY9oFQj/V9KRq8GykPs2IH5d2phpViF4kk+nmC7RtpB5GNvDRyW36XU9OgRwDTbsgxUDIibab4/1A27QSS5x97TVy9bIysgFmlrf+l2/SfOENLIXt7/9AQI6YblwOjWuEY2Wt3FZa3BynGDg+OiTEiDWGiOelD73EerNi1jXMZh390PN3vvIy/8N/8lmOnTivhLWB0eE3mqQKfjCsP7Bs1xbTQPCaGA3zo0xcWfqx8Oxac3ZtOLpnWc4N66eB62HBdphTSGgVWY/wxEc+iGvO/I4pgy0N1z7xOJ2TgaKSqPdUJubCnDlbRnZ5Q9GeKe9EVi1HFo1xN7fJXt5rzH6ulSvErm/MN/bOKkJMFI1P1gLb73PcdZ0/lQz35ncxzHncPyYykvJETJ6UPfsYWHP35FPfjOMWnxLKWPw00c4WFC28l7aboReHdAd3mR/fhTGQsdC2KCuEObYj8XIQwqCPqJDRTgyjjYdhvWX2xn1Y7VhdbTi8f59yOKOZdYJb74VWVterz2BsA7SiOIwFXWn0XXuAszOKUqg+wmrALGaQFLGf4Hyk6RzxdMAVQ1k6lm+9zsFbr5KmkRAiTFEw8rIf68nt0bQtOcQbsZG2lbpRFE3jyFn4UCVnht0O5+TnbGczhmnAYLjTLjgsCuUafJJBZQxByiVlsNXFMZeCXXbc+vmfZYyF6U/fpv/O21BCBdw0rmnAyu168/NWrL5rWsZpEuQtJYyyTNPIci4CphgiX/jwIf/wFz+JSRITkK9b0rZlXGVU0jCJvWlBo0wmFYXfOrqZooyaq2vNk61hPWmMLnz0Y4qrdwubzSHbdUNWgZjhybbwvvc8Cldsk2StHNsFRVkehysmFUS5pxKJhC2WB+YeCzWn9z27siEjZZeUTrlGZAjNX9f+Q++5aqpC/kXhjFDx96gTgG2sVAgonG1wTUOKIu5KKROrwZ1VM9ZhR6An5kgInpAmYgxiiK4tNoyeYoR4Z42jcS1hmoSukTKRgnXi2Df0QvPIpmoHQidyWePQB3PSNKFwoBRpXTCLhtw4uAzEXvHq3/8bHH7/KabRmMax6Cz96RXr773Ps3/1HeKzC+ljmgY/jaTUY8wcpSylaHF/DwM5elByYqRVwrKiaEt+X0oN/qBUlRzYWy25UZiiYZo4uHfIpt8Rp4I7PCJttyQ/0cyXRD9Jb6Bq454yzWyONooQgzAFjME2ljz52gxbxhA4NDO+dvfjvOZOUEXz/c0z3uWCU79h6BRDmESFqRXWOaxqSOvIe//on6If3GL3+z+kkMnKSMqXdcToq2Sg5rDUrPFSEjFGSskCoswdsR/QJeFcRwiemXN84/MvcjKzhJhhMqRRMa0myC2TjuSs8dFU1gQoJ9SMHBSbHi52Go9B4XntZcvmvZEpHLAeHVknQixceTiPkSf5glgynWo4aY7YpsST6RnBeHKJMrhLmVY7DtQhqzywSVtmzmKzYSgRVVEmRamzjFgZF9DYBjKig6/lbesMGssQBqwVBFYp0es0XYcfJ1KYiEEIGzEmWregJDkAo8qMaUtGuHxCXhULWWp5Zl+79TrtLLGYz/nR+z/k3bN3pEEsBeUabp/cpwTF1I/YRpNCwc40abVBDYOgBc4yf3hION2I7uDuLYEmyVin0MkQznbskpiqpQzKe6KP6HbO7a9+hpMvfYw//se/Tnh8yrDZYa0h+0hIa5LORC8T+JQC81tHjOOOxsqcxF+O4g0bRiZtsFrjQ6RpZ+Qsji3GdaRpIoeJ5d07lHZBcY4XfvUvkvqBi3/5B9itcJva+YycMtM0osioItEKqtLa0xRJWoAGKNx1C77x4C3ulwWT95xvttxlQasVJXk2WdhUOx1rHxMwzqGsZvWdH9I6R1Eat5jTLRaszs4wTYP3gaZt0M6gZgshOyK09jiNFGuEutOPtHOHKeAnjzKW2wvDz3z0DmVQpI2FYJlWhRwc2XhIluGiJQ+Gvih6r9B4+q3C5sJULBOK3RRxXSFPE8SWq604JYaieTJlUoHrssarhCmK+/YOV+PAk3BGsgGKxL49bO7SWE1Imae7a3Z5SyZwmXcMYQumOtGg5LmWQsiiWVFKpt5Yha2BpEUVYpCh3meO3uL93QccLQ94vHlKYoc14HWNpU6iMackcVsBJj/hq+O9UpmSPUmlGwCl1KG49Wg2qy1XW89HXvw0H7rzOu3hgiH2vPf0bfrtjlIUJU0oNaNkTRxGjOtk8VgxZ5h++AS9mAtK8d4p5uGxpBUNhqxbuPKwtJSLETOzqFase7TVjKfiofTT//jv8+yf/Q7bR6fEq2uaOwfYk0PMg7scfuUNwsUzNn/yHuf/9x9yZ3fI1eljlHY4LXkg7eKAqd8yOz7GToHgR3St6Uuj0bpFOdiuNth2ycO/8mle+M/+EjNaPljMePzrv0Nu5UtvF3MRde03xl4wZcR/t2kcd0rLZ7oHvDG7x2ad+bG/kpq8KDyR03FFiIlWOe6h6XPgqoykKj6zrpV+w1mIMqTcXF7RNC3jMPGJL32BH33nD4i95/DlB3gN4XINJeMOjnjprU/z3m/9vzSdo6RIt+iYpok4Rv7eX3ud2+GQ7ZPENAJbBY0M1VLfMO1aUtDsvOG9x4opQckdUGg7KduueitzFRQlFp5dNvgoKN7pBDEpfB4ZykQpcMiCnBJP/RnFpr1JPrfVIeB4d3sq03F2ZBMZ844p7CgULA05jZSSaJsZMSVUSjhj5SAqmkjGqiTD1Jx5yT3gC3e+hE0L3li8xToOPFxccj4+4mI8ZSqXxOIRvp70juvtujbyaS9BEpFeSeiy53rLaxVgDeKCUXLi3dMPOHRzSlQc3Dnmy1/9K0zK8yff/m2ePfqgQpBGXm8MqkhdbrSVa2qaUMahrSZuemzpSEZj5w1xG9AhkZ6O7H1GytzCwmIWItI/PRuYf+ETlLfvoZKheXGBO56hYiZdRWYPXuLoUx/mI3/r67z3z78F/+z3mU7X+HEQD9iYaBcH7DZinVpQNLMlnWnx4w60ojk4ol+vmC86cJYmFdI4ojCY1lGmQEoTSmUa26BUxJoZg99RdEH7wv1myee6e3ykvcU0Ka6uPT7mG0r1Wej58e6UbKS9KTVbcZkVc9WwjhO7XKCRcjKliGpaUBqnBV5vmob3vvs9tAIzbxh+/B7Zi77cKEPXKt7/nd9hcXRAzAEfMmO/4fOv3OY/+tIrfO3lF1i/PzGtDEyGmBRuEQiXLeO2Iyu43mY+OCuEApRI28isYBwVY9SgExOJTYic7w7ZTYYdiVVQjAW2DOyUx84teqcwquMibog6Snox0lsGk3g6fAAmSyNuJ/w0ELLHGsm7lGQyOYzGqa/T7Pz/U/VmvZpe6XnetdZ6p2/cQ83FeahuNskeSKhnKZYsS4ogWYhlGwoyID5IAiQHzmkOAqQCxOf5BTnOX0jgDDACGIoVa7Ck7laTzW42a9zTN73DmnPwrL3ZIYEqgihy1/7qfdd6hvu+bnwItK0oNjpTY5LirdlrfKX7gNvtbZ7ZDU/SGXvX0+cLercr5XfFvFmQUs0YZVls7SSOyGpOcL3cWDERlS/WcJGyylxMVmXmrXs/fJyiozZaDCnJ44usgzAyPz7hzfe/yud/9ynBRYwR6t/1JEEbDUZLll1penNdQxCpgVrOyEZm2t2iYnhyEBI6kEIkHzy5j2QbaGpD0hkzr6lWDdE5/PlORLiVxu56wqXFhsDpd95m9soJu7/9OVVUIoZUmnY1x7QdbhjplguZkE2DeDe0Yn50WmLkNPm8Z3h2Qf9Xn3H+f/0t2XoBLxT4gY5wUs04TXNu5TW3WfJqfcxXqtusbMehNww24L1sY7NKfGEveTZekI2UVQkKzEJOJoWiUplZ1hgrTWtEsbh1V0qnaUKpFtWpEixaRphIfkc7FyicnSbaboa3VmKPcfzXv/se//x3vsrbzYL+hSMcasLBsL0yZKMx0TDtWhIQvObpReZgM3XjePSNzJvvBG6tAioo9gfYJsdFsuwCdKGjUzUXQTHlyHnY8zJOhCpzdKelv1TUteIq9jg8qIRLUtqYCiZcCXWNTFZuDVEoiM1XFtyBRJTPsgAmum5WYOKGrur4avMWv3Xym7hU8bk75zJdsnWXbMI5h7DDZ0fAMvmx2Bk0bd0SogxfRPOWyg5FGvtMKFIkkaWIqBWRHL175wePc5YlVgZuLVqOF3N2kyd6R21qmsWcdz/8Or/45GeS46HKCKzMoTWSVpvJIoxrGml4xom8ELCAyZrxyYH07Ip0OZAOIyokOWG1RjtNcBG1rvEmo48q1g+POHnnNuOTS/LeozuNSuB3gfHlxOK9e7THNRd/9gk6yWJNR5nlVwbsOHHr7l3GqUebWiB4yxlV0xaXZObizz9FPeupqwaMwg4jc1NzSy9YqxnHeclJtaYLmq5uUSkTVOTCDTiViHVkaCJP846dnngW94yNx5vAqDw+W7xW+CYxREue1aS2YggTymTmqiaqxDgdqHKmbiqaeyve+Rf/jPHnTwkvroDMbLnAOYd3YuCqqwo961idLPDDBf/b//jHfHR3Bi8C8ULj+4bp0nB1pVCqIVhFv6swyrA7RPpoqVYBpQLf+XXNURu4/Jlm89ygkzAHPhssCs1X1jWvzVvOB02fM2fBcRF66cdCYtjIwCQQcdpi00Tw8IOTd/nO6Zu8qo/4zF3y/voV7jV3qfOSkC0YLTbarMQ8RiQV0qH4rDM5CousqRsWvuOfPvxjnowHXqYNu7Tl0p6xDRvGNODzhMfjg8PlER8HpiSTqRhDESwK8C8lT0oelcIN2jWpLyn6wlrQmLfufu9xCl7MRSmztwnrPafrmYxXjWy8Z4sFdx/c5eef/J3UwLOWGCRTXUVVYgg0OC9vZS1Bj7k1ori3AeUjcduXxVMGG4i9k8lRWwk8zoAaJDUqTJFpsJx+/T7xMGL/qidsI8wMqUrY7cTJh69w+NsnTLuR6nhBrFLJELFUCbyPVG3Lcr2iUrLoi8ERJ0tVG+q2LY49RYiONFrMrGLSkVGPHGaeJ+mKL9IZw0nFU7PlrBm4Wma+qDZsb2s+dS954i7oV5lNHrg4XNDrwCGNhM4wktiGkcnAkBOXY483ENqaczuSa0PbzuRGTUBIuIs9l3/xY9pqVsbfgcVyCWTqqiWmTNvN6HdX/Dd/+HW+fW9BuAjUh5pxV+G2NdZpfNbsx0RUihg1zCx33w28+bXM/VuZ119L2G3myY8a+kPD1tU82UNfIvk+fnjCq13L6DLPhoZw7LmYAo8+PObFL3fFm5JROnCReiZGWtXw+3c+Zq5m/M3mGT+2F2SVGZznYhqYsoTVjPFAUh4UhFhyOnIoAUniEVdJ9Hy1mvGPXvk93Gh4Fi/Zpkuu3AW7KGpfnxxeRWKYsHFPLIYpIfGXMIycIYs6XAxmXxp1E4mH7btUVcWQBpkYKo157fTXHocyzJMwF4VLCZNrHtxac7XtiydBMz9ZcPXyDG9HtGnki6CJRAiRumlEv2JqVFuRlcHEjPKAtcRhQk3FVFQ87CZrsvWoRpSwjBEzAVOGlUhBwt7RvXaMXiQOPz4nj3Il50oxeM+tNx/QvPIKD/+D73P7732T+Qevc/eDN6mjJttAnEaCk/CWxf3bVN2M4AO6apgtVtihhxRp2w7dtui6EX9MVRFjZr5YgqmxgxXEJtJke+cZDxPeTWQ34aeJYC11KxOo2eIIrRuGcRJJdQw456grIbsHP31JYTQN1k20rTB53C+eYxI0qyXBTuLDSZG6aW/yQruF5u3Xjvln336Nzia4qnC7hnFXY4PGBhiDInoIY+TO25GH72bqlJkuM/1lRX/Wsnk+42JT87I3XIwVU8zMjOIrd2Y8uYhsxsB2rBii4tlhZIqBl78c0drgcIx5YlSOmCNV1vxw/T7Phiv+5vCUl3HDIfXkLCVXSJY+XzKkDV6JojkkDyYRvAMVb7LVVVaYsv9amCN++873+Nn+kl0+sIlXbP0GnyasuEsIwWJTX4KJJGmLfC1YTJCDCGxzQc0WEHkJbyAoh83jTS+klcY8OP34cb4OmddKxFoaBudxLtKqitsV+GFCHa25OnvJ7uqSbrUSn0e8ftsLWM2IiEjSnxT6uIMg4ON4dUAvWqrTJep4TrXqiHbCTIHkI3rRyd5Oa9QEesjopSalyLibWL69Iny+J1xN5JBRBryCyswwYUaqDG5y6MWc5v4Rp999l+3PnpA3IyFlsvdEO5FTwtQ1VV2LFmrWkKOkurazllxp/v5/9id8+m/+nKoyVN1MPDHB0rYNShlBxETxseQQCCnSLhcE7xmnA7WpyYBzAyomcvG9QC7OtihtaKmvYwqolMuLkMDUtPOOmK5PO9AqY0yNT4mmqojJ8db9I37r4THzfUXsDeNVS4wGHxJTUzHuA/XK8fb3F8yNJVwo+ivD9nzG5nxOv1lyuTPsHRx8xGX5fT04Nvz83HIxwj4nvI6EAFfRSRyzChzSxJRHgnbi2gNumTXKZJ64HZfpkqAcKMWUeoZwIGrHGA/4bEX9naKgeWIAkrC3jClJVoa6btG65lurr3Dq7/I0bNnFK/bxEotlShM+exIJGw+k4q9JpBtOQfCT9LwxFLemdB6mnkuJpRu00vjoioVabNlaGcy9k68/jjhsFkRobWquqeKjl8CVEOFbtxZceY9Zzjh79oxwOBCKwWe+WooDLyt01kTvMYslKSl0a0h9T7jYoU9XeJXwZzvi5Y44WWav3cEeRhpjSIuGujG0D+fMH91iGgcZC9cV1IYwRurK0P/Nc+qTOWmMMFfEPqD3mbgbUXWF6yf8BLGFhz/8kJf/94/o5jPmx3PGyx3NXLRMxlRszi9YHq3RtWG+XrDf7DFNxebqnDBMNHXLME2s1keM40ROFd3K8I3vf8AvPvsC5SOL42NpgmtJX2oXHd1yRd12NLOWtu3o+x6jIadMbcTya7TBukjb1egKTK3xzklyrYGYFIrI6nRNCI679+9g+x3HRwtStlBVrGzgdx7eYZ5qpl2L60XC4zycX0wMO/jgd1Z0DLhfGPbbGdvLNcNgiKmid5ErG9iGjC3Ox7YxuGh5MURUDVfeMk6OxrTcbxdoHclGceF65AKU4YxKitPumJfDll24wBkPyeDyxBgHUo7lxB+kDyilT0ZUvTmnL91rSqwHpjIoNK/OX6HLx1yEHbu8YR+vcDhitoSc8VjBhmYxuKUYyVqTlSEHL6praZhv3KQ5hVJ6XcMcctF5JdEWGo25f/KNxzFYMQFp+R9fM16V0oQiNT47jNxdzrjY7dltdzSLjqptiC7irCt8NuEkmW6Grio0keQC4XKDMoZ0GNHnexgmcj/Bpmd8doFpa8Lljry1pIOFWYftHebOjOXbR8Qr2cUkF6laTfz5TmK9KgmBUUqhbIBWwdbdxKtll7BV5P4PPxS75ost3WxBMhrb99SLBkOinc8JIbC/2LBcLdDa0J9vWSwW4msJkaHvmS8XxBj48Psf8I//o9/nX//Lf40PHu+TjLb7ATNrcdYXqHONtSOH7e7G4UfOghqqxNV4684Civ8/ektKiqptqBvNcg6zxqDcyOmiZXd1RVVVBD+x6mo+fnfND+6v+friDm4zZ7jUSFx54moPmMTrX4eTOew+URwODdt+Ru89fdTsbORyTGxtxqWIU56NmrDKM0QYyJxNIy0Nj9Z3WbGiqhoOaDZuJKhAQ81xtcapSbRtJGLKTEZuiE7XjMGyyEs6veCQL4VVVbzNKQVilomfwAMrYkwsm2OOmiMaNaOl5bXmdYYAewYOYcOAJUdZkYfocWkQuDqJSESv1kQ7kr1F58h1clFtZuTiIiwGa/lbqeIkFSmR0hKFUKlUMi+KrBgyVa5RiJQ6KyVqVKO52mzpZhVH9++xPTtDm4g2Shx0EXyYBO6gFNmOZGvF+5wVua1JTq5vQdsI2Ew5RXCOqp2RjSelBns+UEk8H25WMXvrFH9psdbJ0spkmYStOrhKqEMk1hq9qqkWGnUxkmON6zRmUEwnDYv3XyNcHYhfbFAE/G5PnBw0NWlWkb1l/eod+vMN86ajqQzTONJv9ixWS8H+FK/Vv/nf/x8+/etP2F7sma+O0FrR73fMuo4IzGdLTNcQncVI90FAzFfzeYe1Isg7OlkQnGXWdqKjWjSQNLM5zNoGbWA4TNy+c8xuf2B9esy4veK337vH33vrIa8t58z3JxxeauJgSvqXNOQhB979ZsXJrczus0DYzzn0Fb1LbA8ZGyI2KkYrY5spe174HZfZorLipJkjQV6GN2YnXNrMmduzTyM2OZIKGJMEFaSWJas+sAk7wXhGT1SJOjWs8ppJWVzakvVUIHzqhvyYSy5NThodNT+4+30etPcxcUGfLS5FpijoJM9AxItqQCUmPxEKT5d8LVHJzJdr3OUlprx4qiijQxhv2nKlNapotrg2XJWsy0SmIlIllVFZUP45a5KOuDChKo3SVfnCEVTi6jCy6m7x8Xe/zdAf+OKLT/jFjz9lHC2VrlmvT5mtT7h8/gKlpc7TWZSVGVH7ukmaoGsvedt1qNSSrKfqIiomVAj4fqBuFPZiQnWG2aKhfzaRlCUMgWQD2kdoJb+cKaG+cISjmvZuhXru8SsjIZAXE/PX1jz8T/89fvwv/hcWx3dYn6xo3r3P3e9/HYKn0pDXC/Z/+xmX/+ufM3x+JtJ8pUgx4uzEbL5kcdJih55p8NSLOVnB8e1bODcxOsf9V17hl5/+jJU5FTd5Ttx+9QH7zQbXywKynWuW85ZFA04ZjAmcrE5IydM2LQ8frNju9oypYaaTbNuJHEfHP/+9b/DDe7cJZ0uuftIwi8z3AAAgAElEQVRwPlW4GJhsxnm4tVQQIg/fVKwW4DYwndX0wbDvM1djIkbN6o7h8Cww6sRZ2HEZJvo0kpG8wMF5fDbc1h0+Vby0B57HLVOyohnLiawVKVme2ieijtYep2TfkXUS6EQ0DHlgyBd4emkxlZz6EnVGsR5o5nHGrz/8Tb4ye4ersefSjbgcZQjAyKQP2NCLJ56JKUpDnpOQ2uWOTkLfOexlY17YziSNLtR6WWjUmKohuvHmJtEgZrpSMibA3Dv52uNrM3tWGZPl0W1NjUmGaATBWRfDSoyBOAWO7t3i9a9+lQdffYdf/yd/gFYVL754QehHot0LYC064UHljE6K5BwxBkHPlCtOKY0xjXwjIYjJJUTUvCZSrLwVZJsJP7li+uIF8XxAGUO8nGA7ogaPqjTJGDg46tsL0i6gXgpK1PiECxEza+jaE1I3o3n0Fov79+h3OxmF7jyDm5i9dZf1dx+RtgPbT35JZQzdcsHieMXYH/C7PcNhwDS1LKCCZ3t+TgiOWTdn6HtmTcd8vWCynpwz02EghCBuRmC9WFPpxGKxpG47qqblanNJXXc0i4bD5oK5qtFXVxLYue35R197h//+D3/A67Fj87MlFy8a+kHxbBN5dhXYDonDBC8OAR8tH3zUMbyMbF/AwS54eglTNoSg0HXF2SZxUImfDC+4ChaXZBKktHgtQrHEzs2cFDVf2A1jngq9MhfpTQYVickTr/cf2cuvSWXxpwKREZsPsqfCyL8vwwdywhhD8op/+Oof8G79Hs/HDWOy9GngJU+55KVMrcKGqAM+W8Yw4tSEj44QBxISbR1LaFLVzojDoaxTFKr4fcQPIpL3FFz5fn4VVX4dta2olMbcPfna4xyF3k5Bnhit8CGzblZMyB+qy7lQRRwpevwgtWO3XrOcd7z7wTs0TcUnf/43sjkuPuLryOUcsozxoESfZWFxF2cdypBDwffrGipdJmvytU/u3WLzVz8lPtmJmpcoOB0yOSTi1YE8eVRd4TeW1Gp0zKgpExcGgkxouttHuLOBNCTcdsRe9gQKCshn/G4ixMDs66+TL3r0diR4y9CPzOYdShma5ZzV0ZrN+RntYkHV1KyPj4ufRoSOPsNyvSZa8Z+8+sarOO85PhVm2Mm65u6iYl9GzI/uLvn4zdu8vtD84w8e8YevPOA//s7HvO0f8g8//Bq/8ZXX2H6euHjS0u/Fp/F8k9lNSfqtkq+YIzx8zXB6FBk3mvPLlp89VdisWL9lGDaRwQZ2PrNfH3i2237p1Sg3vS+MqUrXpKjJKJzyDMnJWauLHV6FMh71sowjihynuPwCXqQlaSIbSXByIQhVvjC8QB7gj04+4qvtB7wYLjiEkV3cca6eMcSeIQ4yflUZG0ZCnPDZFhzQRFJBloxFht0d32XYnWPSteFMwa/YG5SuyKpCKVEQo69zyVQBo3FjGjT3j95/HPBQGvzrLn9eCZ4n6Fi+gHgYjMkk70QSkQ2mrojOE3JkdXzM7fu3+NG//TF1LfgdUxkJVtE1KbqypSzZExHqtpXoNy1ptGTxAlArko8il+8ajhYzXv7LvxKVsUpyGgeLLohJM5uRrScdJnJt0G2FCgU+3QfUIREaTZpBV3f4MRAPE5WFOATyGEoOY0Z5hZpplt9+C+0z2UXauoOy+9CdTNuU0sxPj2nblrMnT1guFox9j3eBO688YHG6ZtrtmXUdPlgM8Nbr9zhcvOQ//N67/Oe//h6//u59fvO9e/zRh6/z9996lY+X93iQF2g74+lPWxYsuPOq4vIXlv5MczjUHCbNWZ/pvYgPcxKSpDGKWhteeZhoge2m4fl5Rb2qGQ8Ju4PtGPBJcYiep5srppSJOhbeVqGeaOFKhRixWdGnkT5ZsdXmIPsDo5jygZEyMNHCpfoSZBkKoyyVUS/EHKlrsRl37VI4VgXg8NHyW3RhxSaM9OqKy3zBLm2ZmHDJEkik5AhEfHZEEjFOBTubUau1VBCmIfRbwRvpa98CZdeRb2QtGiOIHw05V2KaU55rNnLKSdCu907ef5xiuIktuG5YtK6x+cvwea0VISFb9ILOT9ETXaaZz7AHSzOrufvqHT783kf86f/5pzRGk4IXuEGSb1ApeWjzNdgtJeqqLljNIEEvWeMnSz3r0EEC4g+fPIWzAW3KCK/gRVXOEBx5cJiTFTkm2FmS0YWbBbFJ6DsNqtaoHqr7Lbe+eZujrxxTnTbE7US88uQxwK0GpigX6q2O7ltvsPr2I+ymJ77YUBmBce+enaFyZjwM9H3Pa6+/wtX5JXVTo8oyar/ZsFwtiSpByCxXc16rD/zP/8U/4NfurVhouHdU8UrVUvca/0WH28Jho3nxiyO2uzmrexamAb/teLk1vDxU7F1iDKE8NFl8FFpx92RG8Jr1KqNCYL/VnG8UKUpWS4ywd6Bbz60HLT9/fiBqgVNoo4glii8kUbrO6hYfE55AUANTGgh4WajFAVf8F0pRRqMJoxU2HohK4HUhW1TblV7Oy6ROezQziYvTNUfNCR+tPsZNsPMXXOk9W32JzxNT8mSVCEl0WjF6UooijcpeHnBTExpgs0FPEyQpFeUmy+V5FrKi1i2oipzsTUklVJR4o5eTHwUSaO4ff/A4Kn8DMqhUi1EVOtcy6r1+Z7LEbqUyrmxrCNGisyK4yGwpRpRMZr5uWC4X/PxHn9yoNUMYyhRIPlCVy1gvy1iZlNCmLiM2hYmJ5CaSj9Qp4T87Q0fJfiDngmUR16JOgvxPtQSP5pTRy4akNLkCM6+J+yCW3pkhHBzDi4n91Qi1YfHOMfWqxp1N5EEWW3XTEkaRwqhWs/72m9QPTnG/vEK5wL03XmU4HNBtzentEw6HnvEwMF8uGOwkkWU5Y4eJk+Mj/LTjt95d8j/8gw+Iu0h2lWx6g+im/HmHGxOby5qriwW5UlSVYrk+EHvFxbbl/NAw4phCxEf5c2gazbyFRSfLwdEHvEusl9CPDcNUcTFMVLXGTjKMmbzh4irgCexxRJ1IOuOiWIaF/qGKNZoCeRsJKgplJRdjUzYYZaR/EUAuvjTLAFFnMBqfBehWaUNUhq45JoYerRRtcyQKXf02gcDLfMVBbRlzz+yoZposLnoiXhrxJAQXCb0JMlrWkEeLSpHrXGCdKXs5qVYoP4sp0wsAo/zqm4FvLvp3xU10trl38t7jFGUiQRY6R6YYTXLG5JpON/hfCXtMMVFXwkPPOaNyJRbGupYPxxhmiyWXz19y2G5JwcpvpGwoVZYepWwGit8YdC3NOkUOL5O5RNz3YANUilxpEUMakW6IiraoXaOA4FTbkA5O3HcR4jaQi+Qlj0FeoCQjvTRGwt5RPZjT3FswfrZFhUxKcvLqANEHcfk9PIZZhf/ZC+I44ifLfLlmf7XB5Ey3mDFZsXbO5h3tfIHW4P3Io9OW/+p7b1FfVoRtx7StiH1FGiriRpGsZvMS0rJjed/TLh26tpASw6Hi5abiynlczIQsBA+tM71TeBRGJy5Hz6yrmbUVm13F5aHC5sSzQU7L1+8eM4aEcxVDspxxwGbJz/AxEHOgMTWtaqjQMs1KllA21VFFTK4wqqKNCxoaNBVaGzyjII/I0ELuWinJMLxW3+Xd7h2Wac1Rc4SLPTaOVLpmtAOn9YJXuzfYhZF9vWUbL3DZ0/eSF+iiI6YkJVEWkHeI15A3hU4RFeSQvyFnloMdJUFNkq4nL4T+crVZfkzlR5FB5bJLUqrC3F4/elx4jcJ3VpRUHo/WhpgzKSWWTYdHsrANkkhQVYoUInWj8VFT1QZjasZ+5OjOHVQFL372OVnHL8FeSRpvpQqupdwq1yr84EfytTS55KAnG2+uQFVEbbk2QkWfQvGzZAgBHRJxcOhZS7SJeLCocSQdLPFiIO0talJEC6qTKR1BPqL61FC1DeFsZH6rY+wlCIfCZ9MrzezVO6SXPS/+8ifMlwuss6yOlkz7PVXTcnxyTK2hbirsfs/yaMF+u+c/+bUHvK9PiPsZMWk0Fcka/Ag5aYaDYv6VGdo4nv9C8fQXmvOXLduNYkyay0PAa4WLgUSSGLWscSnRx8DeZaaomNeG4QAv95mQAheTZV4p7iyOeL5x7IeIrTyH44EXm56khZ7ikjyElapZqjlTKWWyytgsB4Sg8xJtnlPHVpKRVcDqEZt3BDUyxR1meYKPluRHfnjre3xUfYv9ZBlx7N2hkGMSvRt4c/aQ3733O+wnz4v0kpf5GVFbnBc8kksBHx2oIFByJRv3SIBUNhrBcZ2VCWIRUNINiBtUN7I11+rLF0OXTlzJkCATmS3uEOJYDnEJLTX3b6ZYufxiyqhPTnZdLI62YFAaI3EGRLky762W2FBik1HUiw4/JtpZzStvv47SNZ/96MdUMuMT7lTiZsSbkwj10BDDVHwC8gZPh514NLTgO4mivVQpo5wjKiRaoGmoVwvyZG+u0eSCJOuW0vF6pJitJ/QOkxW6j+S2xtSa3EdUpzDLivDcEnuPHx2mNgSXqFJN7D3mVktTadKPnjDuDpy8cp9x17M+PpGg+r5nvZwxDj2r5YK60tyrK/7ko3fodkuImrirOJwb+r7i4qLl7CWs36xJB8dP/6zh7Epjc02fI5jM5hDxCbQO9AloQOWaMQb2KZY8FMVxU7EZMztvmXzg+dCzDZY2Lwi2ofcWpyNfjFec7yeiimWfkbApSIRZgn0a8crhC7ROacWYJ2IOdHTM0gqnLY6RXfUcy56YLT7LQbg4vkVyE29Wr/C15hv86OLnXPGSjb8ovo0NIUVebe7zR6/8+zw5bHkRrjjnGS6MhBTxydH7g/QeRQqSki8/R3QWjKzEgMeb2wAtbbY4ZiURXlJsp5tj+FcuD/lHJdeG9b28N0mRtED2zL31Vx7HFKmaBlVC7QWgJmPanK4bdV2QK3KjmEpoiIGKjo7j+ZJdfyCnyPrkmO3ZFbqueO2dNzgc9lw+e4EpCbhVJQhTkjR1OYPJmohHGS1AgiQ0C679JiVtNucs371W5BhRKaFsYdu2leSHKIVKEsOVlQIf5BbQgFEyrSoMYDNESaxqDH7nyZ0Cm7EvJnSE7BPCZwt0VUv2nvbdu0x/9XPmszmqrqmVhISuc8M3qrt88/Q1YhjZe8ubS81/+7tf56hvoM5wGmEmy7pnv0zs+pp6rVnfV/zyLxJno8a0sLeWIUSGGPEqEVIkRfFI2IgMUGpNRotnP0e2PrCzE7vomHLEtPKwnOgVPkeehQ2XscelKFovFbE4pui55kRJT5vIKgj2qdHYOJG1QMNNaPAEDuoMpycxl6mAMjWLI6FFomG1POZRfsRhnNikCy78BYco6tuQAq3SfOvkY54PjsuwJWDJOTKmAzY4htAjK7QAOROzL9vw6yVeIkWhj9xMX8uaIiMPvGaGUoaUJgEGXvcnN2VU+aswAzTlNtFCG9DKYO4ffe1xzL5oUbIIvApeRisZe4byIPsYqXVVQF6GnDU2JgbvpL7TiuA9yTv86LFjYHa85NHH73H59IzLF2ciIy7Eu+uvqbVmbha4ZEXxWvzDqcgATFNLnHGBFadQmjUgl8x2nJi+9LwrcdMSnqmcRU8TynmUE6SOquRmyVPAzBsIidxWpJiJNqJcJOxKhEAuvVBdIYQ+jT3VVE82cL7F70fuPLhHf7blj5cf8n66h3lm+eDBnN/5zh1+89EDHuYWEJVpvNS47ZLcWOa3HH5bs7yl2V3Bi4tIyjAqzxCEuhFSosFQk3n4msHZhAvSgDbdHFNDSJl73QKTZNQak4Dw5qph2XRcjY6kPFtGcgN1K6wtlxxT8kCibVopoXLEa4fLHmYtLjg8jpi8hIQGQ8wBm/dSrxvRxFVHC9rjFSEqovNMuytu63ts7I6L8JIhb7DRYRS4PLE0S07MA/pkgUjMjpfunEPo8coRsysvQ1FhELnJuS/S9RRCuTGEj0XJsc8JKjWXTBAkYlBnfROzB+r/94KofL0mTDflmaKkB99bv/dY6rkvR2FVU908vKpc4CFLZFVImVk9Lw82N43R6B3NrKKpFMGWLalSxARHd45RCT7/8adlOaSL2rKINxMY3cgpqeRaF/CXWHWjk+w6KR3VzSmnqkqaeyVjY53lBW0WS/Fvk2XwoGUESYoo54TFVTfolPGHCVU1xL0jXTnUrjBiepnsoDQqJHRjoECN7TSwOD5G/eQpddPSD1setkvetrcJQ+DdrzW8/82W+7qBXxo2T2aQMrUK7D5d8uxJSz9FdOdx2xm5ypw99RymCp8z2ynioIj/BOH/1u2KR9+GZz9PnN42jE7hgmYKsKwq7s4WvDhMhJAZkwRfbqzj3A3slWOXJnzOzBcdlYGzw57lqmPyI7EQ770PeFUmRkA96wjWcVSvyTkx2YFGzfCqL7c9Uv8vW1TVsDu/wB8OuMOG5CPr6jZb29PHLUM6kJLnwfoVXvZPWVRrls1dpuhZdIan41N28RKfe0KJY844IfOrElCKPCwxOKHVlAojX8dYZCW6PxVp69Py/7GlLZeIiRLJKhNE8dyWWyWV1kI26bIH0Zh7R/KCaORUktIllQmyom0EcZmyyEBy8gJQ01p6lqL6TVFGr13XkquKo9tr3GBJMdOsZkQFz3/6GXaUpKlrb7CSTQ0hedbdESu9pjMtYxwxJdtDG/Vl0E1M13tv6YUKtFjyLcAohQ+Bxa0T/DBCmWrIp1D6Gy9zckwlccsqQ2fEfZaisHZ7wdhI3ySzdDMT/H6zV7iqZv29t6mc4+1Dxx/pjxn38ODUcK/z+EPm8nPF85crXpw3nJ1rzl/WnG1nTBiCN0ybGYHEsIHBGWxKRJOYYiRo+T6XVUMA9iHzo59YFvMKow1Xe4lh9iriYubZ4cDGWibEWupjwlUBOlEapHJrD25iM45kndjZHq88PnpCCjRHNZOz1PMa09boVPFG8yrT5BjzKNOntMczykyzArNeQk7Y3YGwuRKucpYxaUNHSJ4DO3we0UTu1HfYph3L6phaLRlTjybwzD1jir1otCiyd0peShnDpuiQ+DpFzvF66Y1SEiuhkJdF0WBo8OkARmGMSOAVpvS3X5ZhXH+tLBt3XQoxkdMYzN2jrz5Oyd/wXAXTWNKjUMQkojLB/8tDGZOlMR0uDKKjKuBnHwLzqqGtKvb9yGxe452kLB3dOuLzH/2U/nBV3uFUvlGhcysyYxgKHn8S2cSvoPtTmVJUVUvSlKY9FnMM5KqiaRoZ4cYkkedGM1vOceNQBJOldARB61e1vKhGwaItL1oiDREV5erWSVTHOYJZ1KTkiRGqQeGWNavvvM7po3v0IXPeZLyKpAtPtA3Pzlq2B1PS2RTOVbJ1BpIHHxIXB8/5kDi4iE2RIcgfn86apqowjWZKkdFHhgynC83zc4OVd5aYE3sn+eq6kTzwrtLoRrOLjtn9FdPlULLrEzY5XA44JIogqyw/k4kqU3UV4zARgaVacrk/4JUn4JjilpQTpmnJKVItluhZQ46ecDiUSZH0fTlFbBoxGmycSHhctiQPH56+x4vhCm0axnRgl/a4OBLShGS38OWGIstiVpHLS2HK5xPJ1wdfeTmE7gGNXpKzJjKhdU2tOmKyN8jRXKqY8h+X1QLiE7mOTFAULdb60eOYAiqLCzBr2XdIRoxo6EFkIQYBVKekmHUz+mGHMZUg/EtRZ9C88eA+daXY7Uasl6jkw27LL3/yiVDjTSW+hlBAagWnqciEa/mzAn394WhEipJFbyNTikhdYolVko0yGZL3JALJeZFPqEhwkW7dUTWKOJXRci7W37pBh0QevUzHuprUO9LljqwVxpQU1bK3aY46cq1kwtVn+hhwH6w4fyuz/bUVT99b8/RRw+zPItVoSGSSLkODDEFllM9MITKEwMZmYi0POhnRQFVCvb9z2rEdIqhMoxNjNPhYE5KorqcMhw6RA4XrQErFmBMhwmxWMV5a+XwzRJXwSTINY/LEkuwUc6Ze1ozeErwrkOfEYdyjjcamPVPaywItWVBaQBvzjjBZonMYA2Ecik5LSY+qPEPs0XXG1OC9o49bjGvJaoZTjintcXkgkeUwJqHzdY+QS5VQTn1V4g+SDJx1uUMKuatYbCGhaeulRCkk+V61/jL5WOdrN0i6qbK0osjii/xd0lIxt1ePHpOEgtg2JZpKqh65jkoJdXx6W7hCWaFVRak9CMHR1O1NqTR5z9X+wOlyzuglo7qaG/YvL3j++edcX3AxhJJMW6q+nAr288v+45phey0kE6WLcF6NkVxwfmXZGIs4zdQVuq5oW8PYD3TrOdZZovN0ixbryjaYJEauykDI6IMl7Qa0E/trGkey0RJj1hhUUISDhzHSrRbCER4C24PjsNMoKtKqJr9yjxfvz5n9xRXbq4nzKdCHwBg8BxswC9hMniun8CVPr1IZiYszmKqlmxl2u0zX1Lx1d0VrjukIDNEw5cQuOa7uKg6/saR/tqMaDN2iw1tP8oqT9Yypd/iQ8UQm7TEAKjGlSFQeWx7ImDPt6QKvPSlqzFLAdcHvsYyM/lx2IsmXFz1RnxyhZ4bYj8TtFm9HeWCyojaNbExSIhEJ3mHtRNc0JA/v3n6b58MLgvKE1BOSE8Cbklviuq8EXaoTmVoZZYjRkbNDtnH55qaRcbTcAkZXODuW5zeDymjdFVqiVBK/qs2qm4YQClWx9MQZ4Sqbh7e+/tgG+eZSKuBkpUvDU3QsCvpeFihZizBNnIeS6ea9o6qbchWCjx7vFYu2YfQObwMpey6ePyvZcUWFeyN7F3J3zrKZ1yX2TaE4mt/idH2Peyf3mXcrOSlSLN9QmewpLWscU5oxk8EY3DiiTYWuKlSlqLqWbjXHT4GqrlFNjdES06aWHXHeoK34869LzGwD1DKx050onk0whO2AOWnJk5Rzap7x1qNURaxgPKnYvdrS/PWGahJVgitX+X5MTKX0rZRCJ02jWwI1KTeEZLBOY43iaKH49CJxNU0EpdlNDurE1mX8q4b00z26RzL2ssFbi6lk431wkSkPTDhqDWP0+CwPrU2epD0+QfPGXcYKjn//I8yjewzPDxJ5MfUyTcoi70glOgCAGFFVi541RBvIMcjnn64J9urG66HLdMh5j6bmpDnmpXshGYNkltUcoxVTHIu8qWRJJiUGqFwmTdkV/sGXBZLS130oxVFbU+tjQu7JREzV0nRHOHvAmJqcpEoqrnPRGIayykCRMlRmRcqTaLG+evzdxxt7LvW7FGiliRYpxnV5plUu2XyILbGQIWpd4+KEMZXcLFlo2z5MdFXNvKqZkmO5nnPY7emHXnzGpc/JWqYPkjH75V9aV8zaFW29wDrPMI40ZsbJ+phZ2+Ctx0ZXtGZS96rSR8UYSzyUpjlZsvj6G9z63nusPniVernAH0bsfqS+e0xeGNTFATWM8qAvZ6gxlNqUouERjBEukV0g58jszhw/OVRQpEk0R2qW8VPE2UjVVviHc6IJHP3FDtM2QhlEvM4+J9qqQmdhVWllSFFiGLIGb6S32tmMU4EpBq7SiP/2KS+/Msc+qFA/3aJ3mXxsCCGQDh6vPTYmRj/ismXCSpmhE0FFIGBjIK0bzKO7qLfv0330Grap2f/ijOHTF8SDIztLsj3Z1GQiuTTPSsnYnapBdw14D6Mk5hYZr/S7Rf2tiCT9ZVPcVgsOfmJm5szaBdb3QMDoihC9bMiRiSSKkhESidEVBW6JDC8HY6nE5NnMicYcoTCEPEoicQqEMFFXHVo1oiUrqvHrpbIpi1bRl2VQUQ5IpTH/3Qf/0+Nlt+KL/jNCkodBl31DzIramDIky9eP7s04WE5fTUxO4tVMIzQKrul0imW7oPcTi9UKZwemYRTz0HXTXTb1XwalaNp2TW06UAYXvCBdYiQR8VPAWmjbBZFJepFmJtdiymRlWNy/R7tcoI+XtN95j/rNO7iHc/LJjMVHr/Lgg4ccfnKJtw7jAtGKrCFPJVxy0ZJDlJm5koGA7lpiDOTBk32gu7dgfL6nOV4QXULtIe0Tuc2ElAljxCwM/mtrlv/qgqPcQYa6MtIHADYlxghTiuxiICZweuLKXqFVRZUNViWmJdiHmfTb9/nkoeX5+Tl80VO/FHts7j1mkmVayAGXA5Me6REpSb0yTKMnhUhvR9T7t6m/+wY7F7CHifHpBlImPrskX/bgvURcxyiE9egLRiej21aWrymTrSPt9mQfSEai2lKSlYEAGcqoPCWq3LHu7jIFyxi3TGli8gdc6hnjgPeOrprj44QuATm57MhSulZX6NKjlB4V8ZFfS0g0DXPzgCGd3xzgQo9JdHpNYCSTMaYjMt30zar0OmIF1jcriiprzK1bP3j8anWP7979Bv/u8GMWixXWHlBoum5BigFT1YSU6OpWFoYpyEQgZ7FXlsQeU7US3ZVkKuJ95r3XX2PX70kKnj15wnDYoQxljGxuxr35+pRB9FfWHUDJAkkEA4kYPZkS0Gh8mShN5CRLs2QMs7t3iNqgTEdzckR4tiF8tkdNEOvM3g7ouysWs5rtX35O6ie0qkhKoRNoH0iNKbdkLoOCTN5PZA0pBLKL9E/3VNFAV1EftRKD7UBdlFhio4g5E480rY90fzlitJEYBqWY1VAZQx8cNR2rdoHFs9ORsFqgjg20Bvd6zfhf3mb3e6dsjlr8Xz9l/Rdb1p+XQJmIIIViwpPF9WkmhjziTYKHMwblSFWN+vZDFn/yEemDO0ybifBkL392u5H4coM6WBlpx0zVNDTLNTkFgh1lGXtN/Khq6kVHZTShn2g6OVBSdEW/l0oFItaGlDN3V++glOIQLsXDgi+7DgXakAl0Zo5PE5mqHNJGvCfJlufMQ5kCopD/VmVUUqX/0XT1iRi0VCoKY+j0MVobQpbbSmwXmkpXZH0dEU3Z65UlIVKym/cf/ubjTkVuVXfZ2gMX7kVZ4mVOTu4wHQbaqmYxW6KTLg8ONE1HiJa2bnGnwqQAACAASURBVOQaVIbKtKQEpycrUc8GsM5ztFoyRcf26oLRDlTXkyuUxPOiZVSXc/E5BzCpoGDkw4xxImYrLwWWfrwipklGgloRQ6KdH5GUpjk9oTla47Z7KicTDv9yS95YqmWL05p23eB+ekEmCvVRLm7ZuCrIixad5PekYmnprEePgew9VdsJS3c3omqNXtRkV+TWfSI5iUiouopqZlj8qws6XRWmlaZuG+qu4uV2YNUt6FTL2sjv//PZCw73E4c7jsMbFdPzPcO/vaT/u+dUn4/UPxOXYogycfIp4bJHA56JUY0is2kM5s0TqldvkX/jFYYHcw4/ecn2L5/jn/XE3Z50tScfpptJEUqxfHAPN07kacBPvQTYaM0NfjnKjiCGSNU2+HGUm0ZLsoasLlJZ6CpmzRFGtTyfPrmxT+hcuoiiKmyN7NtCDjdrBpUC+Zp6UiaBGlF7UMY9In6VCWjMst86qd/kuH1ApVumtGPV3EepjMt7jK5Jkgh6Y7+gML2uh0HXgyStNdUUe55az36IfLj+gBebF6is2U9bXrx4RlMZ6nqGiUoM+1mToy4q3wqXYtmxXA/IMs46ulnHFD2b7YH1asFyueadbz7i//0/zgr5TgAtuvQgSV+PauNNE6ZUCcJKZeyXIaaJWHRV6lqOYiSHPUyDnHiXEq3Qzjri2ZVYM7WmmbXkL3bUFoY3jrn9B9/k6k//js2ff0o3WwlPCcA6sA2pMuh5Kx4RKxT8pOTFZ99DbVC1IVwOEuVsDF5njMroS0WcHH0M3H7vLvuZRk8JnRTbkNjud4zB0uiKi2lgo0cW1Zx96nFfXJE+D5IKlWVEmnOmLg8KpiP4Ca0TFqhqQ3SJSfVSYg2B9lt3Wf3GOwSVsSqz2xyIP9mS9xPJZ+gH/j+q3uzX8uy67/vsvX/Dme5Ut27VrbGrmz1PnKQWB1HUEDm2CcSSAzj2Q+AEAQw/BchTXvvPyEuAPAVBAsRviYHAjmBbCSSLlkJTbIrsZlcPNd/xDL9hD2vnYe1zmyJANtiorq57zu+391rf0fYbiAl3fRc3n5FOLrCzhtXTR4TVipxGUizGIlvrIVYbJrs7JB+pJw1xtS7gTnm8RNQHIhq6bbIhqbWrIFPlYMQAFdNJQ993ONMoSmZc8ZwYslGkMqONWKUAWnm0rXi3oJuIwZIZ4guirJnEI67PXuLMf8mkmuFkl03UgtDKWL21ZJvNZRHUl5Tkqwo4APfu0Q8/bIyjNQ3GO7618w73F/f43uE3eDieEEKHk5qj5h7fW3yL/+zG7/Cjm9/lh7vf4PXFA3bcnBf9BdV0hqNGJBJ8YOxGqqpCMKxXA41pqaZT3vjeuzz8619cwXaSVehmMJB/DZkSW6BmVQ9vQx5yKUWhCOvIYGttdNVTJ5HWK/JyiXQ9OUdVD4sQK4sVQ3i6IhsI05Y7f+9dlj/5nMpVWuwj5d/jg7rTNiM492veFx0bSIK1glnMlDuxriA2kMcAPsHSE7pARaD66xXDRpCoXMdlXnIeO4SKXWnopeez8JilbJi0NSmo3H/a1tqqayoNC8dpsr4RouhzO4ZEu5vZ+BVSW+7/dz9g8+Z1zhlJQ2J92pN/cg7nPQJUIcBqBUlwixa3v8v46Bmy6RkuzvCbNSYFTXs0WipUzyaknMijJ+VIFCFerNQxOmlJ3hfQRTNtcxlbsOo+dZUrOrvy98uZHYtQ0mBp3IQxra6SOm3R92EEMancOrrrbGWH28Va+Qyj/Bo915uvsYkXrHhKyD03qldo6z1C3jDmgYpagZ0oqidD2X99tCzGlGTFN27/3ofnwyWXcUOfAmNyHMhN9rnN7974Du/tv83C7nNcvURTXWOdMiZYrpkpd8x1vjF/nQ+uv8PZes2l7xjyWDwjtizshmwNloo8GoYhcvz6LZ5/8UiPAau8ioh2jxs3B0T9wdnhrI5hW1OULRyOqWqqnQXVYs449vi+o240N9dYg2sqTD3V9JMoNNf32HvlDofvv4SThDztMF548cVz9m8dMa46TC8l5b6I5LZ8jESsqaFy2LoqV7p+WdKP5DFishZEkjXxIw1eI0fXgp84XEikQehut6x2I8uJL/tMpDIWbxNdHjFWRwUqQ0pZkwsNbHvDtxi+ANlGhhQYjUdcJLUV+//V+7zAMHw+YjaBcOGRX5wiqx4ciATs8pKcClBS1Wo1uLgg54QEr6qJFDCiMKwxhtBvNB5pPqWaTqh2p9SLCWnUOmVbq9iTAmxYMZitls0YqhLOVwziNO1EJUoSsMYwqefUrmJMG305jEVSLJxd2X/yV53nGXv1LGSUBKegUkngtd3fobYzQh7o4ykDK641t6iYsT8/ovOnWGOZtHtIaqmqBUk2+pKgpOu83sMdH3zzw5EN3oz0bsOKcy6lY4yZLkZ22OXV2V16s+QT/xkda5YuICZTC0gSFrnhW3tv8GB6ky83zzlPlxindkxHpVdvrlU2kI2eOPSszs5xxhSdV0GyCu6+rT2jJJsoBK1MqZktqK4d4m4d0r50zPVvv0q7N2f98BHO1eWDKrNpNhin9dT+dM3l41Oq/QXD0mPFEp5vkLpi5/5NwsUGv+yxlZpuNENX4e6UikbLlwXUGsRC5QxET9x4xEctNPWebC0SE2Yz4M86lhIYblWsb1jiO7vw/iHupV1y8IzDCh8HQo5gM2PUWu22qjGm0oVyWmmD7qL0QpIIJqlnwwTGIEx++DLr+YRwmkjLkfR8JJ92yNm6LLGJPA7YYVSUZzbB1o54cgYxXKUckgJIvHo59HbWXU68vhB59PiLdeGtDHYywbUO8QE3nyLBl5tecNM5xjli1+NqC5JKFbjOSUaM3h7SkWXb/WiLrEmAfHUrmcKUW8qyUw4xkqGZTIgSqVxFW89o7Jw9e0TtJuxO9mntlMmioTUV67CiaSY0zZxhvERMTyax0xzgTMX1+REzu4d76cZvfZiyB1HL4a3ZbW411+jqDedpRS0O7zOvz+/yVJ6wjJd0seMyd/gqElJmkIzLieNqj2/uv8W/PftLUinZdK4uc6PDpBaMVo7lWlidPS/oQVZ5wna4tFtGRIWGkoG2pb5+E5oJtplgqwmsI3LW0T/dsP/Ba7hFzfrhYyUBs5ZAuqaFIDhjyFEwvSecLoGKcRNAIJ2vGZee6WtHpBdLYoF7s6tob1zj+nde5/5/+j4Hrx0zdp7+VGvQnFH4W3PwyvgxaFoKgyd3AZqWoIpyYgS/9IzPNvh+pH6wB+/ukh+f4Z91ZKcjh8UxaVpCAqzV0Aeb2XiPL8LCLo9lKS2j1s0p9oP7DM9G0qMBliP4QFxvtMzIoWTwpocoUDncwYJ4doEMQ5FkJBSV1RsxG6MOzjL6xpxxBeJNYwBRO4CtG8RZ6umEXFdUbUvYaEkOKdMeHWKrEq3q9ZYkoyN2yhwsjkgpEeLlV9Ij9JnYBi8oIW7BboMI9SZ127ps1+ClBH/XmcvNU6JZ89YrbyPJsbAaqj2GNeuw1FYpIIyJ1lUMsqS2E/aaI2KOkITzsMQd7r764RjXCnPiWI4jy3Hgrr3OtK15Hs9pmZNEuDe5jhHHy80DdmTKI3PK4AIyQsIw5sDCTPjNa+/zr0/+grZpqIymnFe2wlEh0SobP3VcPH9KlqDMvRG9Ja7cLMVyW7Bqm51mTEnWuoScy02TsTHRfXZK++Yx4ekJ+KQSkRJYbJsWyQlb6cljY4LBYyZ1sfWC9ZnxrGN264iqqahvHjDdm8HRASFa+tOOi96TjxbsvXWH8PxSHY7OQbZkZzE4TIwKRSYhJ4uJicpa8moDFxpUkGtH7iLjkw3Ma/LxLu7LNQyR/b19xnFkE/RlGMXT+ZE+DFCBrTTuUyRCBbFy5MbR/s4DVqtEejwgl2viaoVsVpoNRhGHZpVwVPMZNBWQkHVJujQFek+CIaopzlCinrTKwqIksRT9m0Fl6KYqn6P35FmLP1tiUsK6SslX0Zo7V9dIVBejs+0VT7G/s8emu0AIV5o0vZmKOkJKUN1Wn1VWUIr4EB3OOd65ye/f/wE/Ovz7/N3jH3FQ32K52SAEonRs/Iohahq8c5b93QOIlp3pAqJj4mac9I8Y0lI7QkhUkUAST5TASE3jJojt+LPNkrfDK8RJ4pl5Rh1vszPOMcnSxYEb1SFTM+WX/lfYqsyJbkrKS+6aa3zn4G3+w+ZjGlXFqxmrTE3GZCrXqCQkFIV+1hCIK7gKW0RvUsibUB6+qDEvXdCF3lhM21IxYXh4Ck1NuhyprN48OXmsFEGjcxir3ItLCblYkq/vKyoVR0BYrXpsU1PXlhQS+fMzEMtQ2Fozb0g3ptjXjpBNYHptj7BeU12bY1pDer4ifnrO+OICRyCh6gSOdrBVQ16uET/CzgzpR5b/dk1zf4f2W0fYPnFRN8hZjVmO1LfmuOsz4npAvlwyfPyc4FUOwfGC5pUjmlmNbRznFyN5MyDnPW4cleQsor9spIRUZKTrFcZvwEzUq11YVibTmm4VSr2e8hfGGbIYvTlco4eSMYgJWFosCRl7VROUtP/21iFh1emo1m0gJdxkquprY1Q5UClfggFrakJO1NVE2fRcam1ED0HLVlL4FbqkP58rddTwteld/vj4R9ytb7Hsex6mZzzpzrjMl4zoA+9LuJ0QGIYVw7ihaSbYnRmrs7MywWu/oTVF13dz7+0PMyqt0L6KQMwB5wxd6DmY7PI8nrLr5tQ4ztMlz8wJY44c5B3GPHIiS2xlOLBTVY1aWNQTfrr5FcZpfDPW4nKtUJ8F4+Ds5AtNqtiKTKwueFd2X71EFSEyroSkiUqdLVyVpCRlfo2zxGUHIarsxaqV15TMLee2iFjZTZIU4slqAN2qxwyDMsN9Tz5bkYexnE/63WQfMSsPlx66QDpZIxsPQyA5Q727wH3tkMpWjI9OcNZhSOQYFUCYTjQ3q/NIH6GPhNOOofcMJjNMK/LCkV7dIe5Y9Yg0Bo4nmAT+2QVcn+G+eQefhHEYWT+8RE56ch+wKRZFAapG3toXRo/pPLkfdJOtK4gBG5OCHiYTfNn/cFRNqy806AFTAAKVDZawNmO/Uhq4Gpu1K1J2ZtTXdvEXK4wP2KqBDNV0SupGslPXodsu4FkPo0kzp7ULLBmfvbr7jCn5u0oEbhNwtuLVKJlvH7zPP33wjzgyezwNS34ZlnwRHrOSFZ6RZCJiR5q5ZQgDoVQLjqmjHy84uXhOdukq9X0ri3G2pgJPDCOu0lFIsrKam3BBXTuehxckhIfjF8ybltOw4sSc4SYVeYwcLfb4YvOYk2zZncy4bWdsxp6pnbKoJvR5awdPmmUklrzOjJcdklSyLFa25rCr/5ir/6+eD0ylD7MtH2oKiGmxNqlUPwXC6RIThHralGIfU+KMdJZNMejNIrm09EKThXCxJDv1Iu/duUP34pTY9dQ7DdZUDMuNLnFNQz2fk5OiHM5V+kCNQuxH8os1sZ1gj3ap3rzNPAndX3+GsxV2HGD0yNJiD/dIooYsvc2MvnAXPenLCzYCuTa4tsYkD0Ew13axx3vsvHeX/mTJ8ucnODFXD60xlkxUWUbtsE0Fwwi9J4SIu74Lr+/TzmtYDcjTC+LQEZedKqELsWf3Vebjz9dkI5CG8j3odxRL+iLlMC1iuK1SkLjcQIiYa3s0zQSqCr/qWVybgcvQOCb3j8ljYHx2So4e4+Bw/5goI3H03D16FRMrHp7+lJBHvWWswzqDBH3hRfQmfW3nZf7h3T9gkmuejxuemQ2X8ZxVXCImEEzPKpwTxMMAPo7szHdYdktS9jhXMWta+uGSbKz+zGXSt9biDucPPhQZryIgTaHvMWhgV1HXVjiu2Wvca4+4CGechEtGk+jxrKVXdp0J15qWMUYSmZ91D4kmYXDliTc4VI4SpGMzPiVZ0QLOvP2vKdospZS2JidMUlgwc3UjkfXl2RJSEkecsaSgaSzWqJJXhcnbttitQLpAsikUFbEUknNEwghZCDER/TasLOvCGgLZqfsw9frrki8Va1kwvkcKZGwe7JOfLtUjby1FfUFMYGtF26QkE2JAUB0c1iokG0bNsd2ZIpc94YtTxsdLwmrAhYCN5ebf7lHlcTWArHsYI/ZwQfut+3B8ABtP+Pyc+Hytt8XoFZL2HiNZK+muX6M/udT5n6SfxRbNyhlJEVucoHkrJ896i6gnQyAEHSXHATebYHdn1E1Df7ak3p0SxxF/eomta4ytCOOKIa7p4pqRnvP1KSY3WGvog0p0RHJZxiuMq5EktGbCj45/yO32Npej55PhjCf9c9btGqaey2HNyJqYRzWtkYgyqNo8DmAySTKgAdxbLl1V8xZrWqqcpcR4RlKMuGqGyXVpGg2MeYBocXXFL8OnfMO8wXuLt/iT0z+HqWUZOsY0UlUWbwKX0VM5g8kwW7SMfQQjGLE4a4uDbWRIl/rwl9Fy61bMeftHLH+3KIiNgNiEsRNlZdmap5IiTtZgxJJyGYey0zDlbHHFuyIJkIFsHMYlJGXuvHqHx1+8KGNeJvXpSupA0i9FtkSUybi6Be+RbBj7jjprt2OsQtFkK98r40jT3qR++Sbpb77Ej6lA1hnrB8gBsRXW1bqTOIuZTqGtsJOKPI4QnKpwT5eYjb6EaRywFaSkJ7o0jf5zoiYym0R/TeNwd46ZvHHM+OUl+cWJGsF8Rx425DQSx4jZX1Dfv00ePNQW340lnE2Qviswqj46qVgV5CrZvUzGVi1LkgPW1Vc8gsUQ+xETIwl9IcdNx9W8mhJ2fwfWSVExNO6TKnMZX3B39gAfenpZA1YRq6x/bdqKm+6Y1xavcdl7PhsveRZPOc0XhG6kSxvERHBWSWeTiDESsxCi9qXHq1SUlqaeU9mGkAZC7HG2xdkJ7mjn5Q8V76bMk3oiaZC0PjaucBo5Z3ZouWP3aduK8zhQVZl3bx3zdLlmXs0YxLDTtCCZj7tHasrJFomaFq4P7shF95iY+u0FXZyKGm+6fZO3t4caW3IJvkbx/IJo5K1xxmiYdC7fm0al2iL1KcmNzoBEnTJFMDnRr0ZCHMuvKTOvqMlHcoAUr/gQk4UwDkzv73P7v/g2t//B1zn45h1sazn/6EvquirjnJQ9xlPdOoDre0zv3QBnCOdLDAlC8VD4XjtRMKQxIIPXlzFnzPmKvO6xoaQG2q09tHAxZI1q8kFl52HE5EROA6Ztmbz5ADnviE8ukW4kDRukW2FLF9+1D96kvXOL1OsplS7WKt60SkUmP+hnr8aOEuJRTqviwdk+MwAOV2J2ymcgYGcNkhJhueaqYm373YVAtVhAAhm74lzI6rxMkYPmBvuzI553jwoPUqgw0VC812evca96hafjii/jC87TGRFPtJGekZwDISVSTvShJ5acX2sMSTyCljtd27nN6EfdU01TAAoPZsRd3/nahxD5ShVfUkKsu4JcHZWOO2JwpuKV9hbGJj4enxKInK08h9WcioqYhTFFdlzL0q946s+ZT2a8/ubLPH70hCADSTyXw2NFDErMUJavmOivXpAyMthtFUKRO2OvEiq2Jz+5MK0WNIJZl03B4K50WzDZ37kaJ5UTS1cZwdFrvH+KmiApkkqpI5jaICGz//4drv/O29jOk2JkevcaB997md23bvD83/xCi3hK/XD2ifH0kvzsgrTsYG+H9vZNwvkSyIqkiX6uJgkmRWyKyEYLjLIzmO1SvfVll6AKYlSYc7uvFXObBkQn2ndeIp2N8GytuWB5JPVrbEqIger6AfZwn/7hBfHykvT8TPmSsji3TUPwXfFH6Lhrs2Zpbc1M+i+2VFUL1Dinp2yWqCa0LEhQtYAFsIbKTbBVhaSkv+8YcG2DwSIpYG2FZGGnvUZLw8PLj/S7tk7zAbJVx2Iw/Dev/GNedCMv5IINa3weiS6xjmvIkWg04LpPAwYNqM4FGla9o6FpZnTDJSGt1S4gvRaBWsHicEc7X/tQiqf3ajF2NdYovq/ORwNSsrOy5a69zl+HzwmNli8KWuFljaExFdEkWlNzd7JPY2s6H/j4s890ljRCNAM+rVTKnLXsxE1aUhjQ1hCKkUqJoe3toVwNYKy627JeKVW1g3MtoKkX29sO53BborGEZRtj1dOcuBqbsigaZp27aqI1Bc40OSMGJCZsXdMc7HD208esPj1n+fkJ/ZMzzLUFdn9C2vT4h6dXKfkmZ1zQ1D8rCdN7UkpMXzrG7u5AXSsnkTM5eD2UjT5YeRixW91EVtg150wKQdM9UtI/k9EGrNmkVk4JzcVqjq+Tnq+V3R974tArT+EA66j39wknHbJakdZrjEmQoo66KeCHDSZJkV5Q4BKFy3NWibg+YobKtdoOgC2Lu9YgZGPLvrJ9wdSUlJIKP0G/lzR66nYG6M1Ru4aZ28NHzyael+DCgl0Zi60cs6rlvd1v8iwsGWzHOgx4ExjzSJCRaLXy2YtHjGg+tLFXBwoiOKcFSDHp2HfVW2j1krS2vCCUkhxT/tfZSkWClHT3snw5Z1nMp5hcM9CzoWOUkTFrz3rM6hGvcIw5sl/t8sHuA97eu4OrLE+6E87Gx/i4IUhfHiKDm8ygqklDX0h0LRElZwUJsi3Gm69Uw18J2bZpJQmRoIt8+eLU5u2uNDzb9tOr+njdz3SsKw64ssFvzXEF5lQ5fz2bMTxfKjZgDLJODMsNaVHTr0fi2UB4eIppa1Jd9Fq5kIYxQUi4KKTlRuOD6ilmOqG6eaAPzqbXm8egJ7ekXxsZMykX+X/SRlaTVeEqMTCbapVx8hp4J31QuDsb0tiRN315ycA0FbauSZuB1G3UHJc8KXbYnEjBw9YabYzuf9u+D+t+7aEvn3MZt0R8GWHclVBxu2c6Z4tIohjkbDnkrKpwpXh9KudIItSm5WjnNufDY+pqijUWiyOIZwgbfuP6dzDpgJN0TiLRy0hPp7XUKJeTiNrBbrYpm4IhqU2iuFhT6in2rK8QT6OeJGut7iBfWZV0ebK2KB0N5KwSEIelaRzNrOJ8vea9ydt87h8x5EhCGE3AGUskMXMtLjuGJOxay0Ge8u7iAd+//Qb/+sv/wCqdM5vv4lxDil6DwHyH5qaUnSPrtXp04wbr9aqIGu3V8peLP0C/pVSM/OUHQ8A4XKagXbb4CVT4aI0uiKZ8MRorNCpSZYz6P0THGhFVAzdNQxpG4jiQR49ta2gtZhDyrQV52tD9u7/B9IHo1Defskf8NjbJqPjPe5wxmDGR+gHWPTF6ZFbrohzLjoTBD+canEYkZX0hDBRzUijst5JmwzjinMUHrX0zXr0i0Ufae9eoX75Fc/OAnMoiFw0y9JjiuJOcMOW7YPsZblNCCvhgymiby0tMGcdTymR63Rezw+QCyIgm+TtTUVU1KQl1PdH0TQRc1oczowdr02pfeeiZ1wsW9oDn/guctcRoyFXDrdl9fuvmH3C7foVPxy/ppcPnoN3psiahO6MXT5SkfSZBuyHJWV/inDAmE1MpkzVcveRX+INBLbdHO69+mCWWOVPhT+tqrKnKIqhEn3WGFLLi0K5ikzp27YxLWZe0jKzp4M7SmUiVVfYcTYUXoSZQi+M/f+t3+dNnP+Fk86IEOJTBzrqSmmgLb6In+BjUU73lSbYZvZSFztotNO0Aq+MVGVv2Dy142f76AgaUxRt0vDImFRKqmP8l6AOTDVXVsNhb0F+eK29T4OWw3tAkSH1HfPic4d/9As6VpMxjxMaA8dsi0/IAFlUBkwqaSsPuJJGjgFeRnvig40xUb3YKPWzbYMNA9B1I0KW5SG2wehtGHxBbIn5sxBwdsvfdd6hvXAOfMOc9rAfqSYuEgTSOyoGkiMmamu9crQ+sfLWM67/HICbpzbIduzIFHgeTHXXVKuezFXOKulExaBGpMUQJmAq9abLZrlfqMxLRuNAcGcLITn2NnWafi/4FR9Nb/N7tP+bO5FUG73nUPWElZ6w5Y5OWDPR6U0hijKPetiZSAbvNLovJbpEnWaq60XjWMoWUCba8HKp7MwX4cUeLBx9utTg2O5xryeqJxRpXHkCHAWrXUFNjrMPnQGsb1rLRBdJoblFIKt8OlBzfXLMRIWaIKTDLjteu3+PPnv+UZEQ5hsIRUNSfxmqiYtkKFakqaReyVfUaXRr1ERRc1kVcpfOq/tw+5Cq2K3xDVn7eGvTBsLYIJhWlyeWfIUOUSEoRv9mof8V9FejtyCQ/kn0g9wM2C5ofm7SXpEC62qYl5FT2BUBCIvX+6qU1GXIUYt/roSTapIQoA29rR9pyImrOVl4HvSElq+1URAqnA/bwgMmbr5E/Oyd88gR5fEK41HC3NIxIKG1Pog+9JN0drHH6QpqkI5CoULF8ePrzGxUSVlVFFh29sZovYLFghRB7zNaSbaCyLXXdKohQDsZsc2kWyzTtpBDCBRXLmYP6mGk1wWTDt6//IZfDhqf9F1ykE6JdM2btRhcC7aylG7dh2kJMkf16l5vzW4TsOe1e4EWNWymlMkIHdS1aCkOfy6SiMhtnHVWz/wbd+U8xYhFj9aUoy3mWoj8qV7mIEG2izhGyZdFMGUPA5kzjWl1uMThnqVCiMUtSfN14OtPwol/z8t5N3jt4lT978RNceZj0mtVkcLtlh7fbgmuozETVnqacWmLJJKp6V3eVsFIuoKBcKQUdkUzE4khp1IfPgUMNViYnJAo4S8rbD0bYwt5GyktqLYgQoy/XsEVMhTWpzNJAimAsuaqLf5vS6AuT3X1m+7ucPnqKcVblIEnwMehpBoizOAPBb1PMdfkWEWQYygCc1H2JJs9Ikctk65jfv0N785AwerpPvyDfuUH8/AXm6TkpDJBLnFGUUn+n3o/8t0CJrC+i0Z3Tit4eIopy+qQd53WjB2blGlIswkY0QWQ2n7IZVoXt1gOJJIgdibGMVleUgoIx2VLGrkT2Gkh94O5wWN/mZ8s/5Z2j7/NsOKGz50Q34qMa4TxB26schDK2jaFOFgAAIABJREFU2dqQ+8j7+18Hgc/6h5z6p9S1rg5DP1x5fHK5DcumdFXqJL8mKHfXmusfShaca3C2uUIcoMLVNZP5XKXiog9/42qUhQYvGhNKuZpsecFaM9UkRltT0egDHB335ppFW4ljE3t+uvplQQ4Uh7fWFThZMLYi56qcapaUNprTml25ScqDmjySB6oyWlGQCmv1pkN0WNOQbcG5BZJ6jLUq9wDdS7LuNZWrmcxnjF3P3vUj/eBjwNUqw9bEGL31tukeIlFRm/LvMdaSgOrwmGr/kPHsTLOjRNPhYxzVmGQVPifq3hCCR0bVQ6WhV9UslM8nM51qwNkW3iULrp5S11OCMfjNSE6WfLgHl2vys3Nk7HSME11Qc46kqP2SOSuJq4mVBVovh6EpCR+FSCIkz9u/+QHvfOsbfPrRz8utFlTfJpaD69eZ1A3nyxP9+TO0dXtli1a0MGGrCdpepkBJLhIXYxWlrNqaFCKvLr7Bk/4LEoH96Uus5Clj7LRqmkQtNW9Xr/OdnQ84bI6QbFmPF0gUPtj/DlWa8XD8kvP4BNEMKHKQq1sKAibHq2ZcuzXkod+rKX+vwsQy4lT6VmdDXdfYQurloCcPZY3PQJDEbrPDedhgbIUxmVpabth9VllRAWstIwOP7cA+C65l+GgJv7G7T86Z1s5pbYUv2hdQX7DG/6jM3VYtIn25R/TGUK2MUSa9uMrIhml9wDqc62Bs9KE1xlHVE4Jfl2AwZdRzyXU1WYhWF/JkEwRLrBJpHcBmLk+eXY00MaAW4ox2Z8hA5ab6e5UbY3tziZS+vvMXuINDsgS6zUiKesikOGKzkDI0LhByRovuQfDEUWuSzTaXvygG+m4so5UO7ir660jjAJsLTFWTZ3PV1QVfGHGDsxlJ2uuSoqjIU7SZqxxN+rlpPSG5MEk2aU+I+i4qPvqLH/Nx5dRvU07/lFUCdHl2BpKo61aTCn3QGNkyEc8mc9bdinTlGESjbcVibSamzKze5dr0JtEGGjelqVqMPeSif0Y1g77ruT+5yzem7/LG9GW6PHCa1/Te8ICGG4sbdNIzesfD+HPW6Vxr5ZopYRjYetohXzkRv4p/2LoVv3rWwVDpL9YQY2ccuJajGzc4efECSQNWWj1dSiSKZCXVLsJKx5KsD2Q0kY14btQHrNKaDQMTN8HlimXeKIqULX+5OuMHh8dsSa+cdLY3piInEJMKOCAgHVyxt1v4tnQjWleS93R3WYezq9PO5LLIZwh+qcreIp2P4zkYzfS1RhTCNBm7tW4WAqupa/zogS2BKcQYaedT0qDGpiiDHi55mzq4nWMzVix5s+bi8oxXdu9yqz7kzet32K3nfLY+4/PuKR9vvuB8OKetJ9joEHS/Mb92IOnsqcJLcvqKTC1kkSlLZRZLTh5ZRXJVNGjld0kxF/KzjBblBaMQfurFLmNdLmVDBiSXKrxCyjqn0PMVoFPEkjkLs8kC6grJiXHc6H5VlnSbG8ZhpJ1MCH7E1TUh6CFks46Kt+YPuDd9lUzF0Gw4j+fgHJDYpBP82cgPDn+bb8/fJ0fHL9NzLvKK8/SMi3hGGKWga4ZNfMoqXxLygMmWyjl8MVlJUY/nnL6KKOIrEGjL+Wz/U6nxPevVi0bcPHr0aUF+HM4Kk3rKGHuSBcme2hi6MFBVM2JILGYzjIGL8ZxV7PjW4k1+6T9hFS7ZrRcYU7NKG3bNlI1knsaeu/NjduvrpGnmonuCzXpS1U1L8B5jU1nUTRmT1JV4Zaq6wr8y4K5+hp2dPS4vLwvUqz+ylKQUnY/qAmeV8OptDk0ZNXJuqOopftxc8Sdbll5yYlgJ1aTVlI0yCqYclXkOyjIbMkP03KwP+cH93+Ew7DOamjZZDpoFx7NX+N4M8jH85ebn/IvH/5LBdDS2IIfbVMHC+GuWdODg2iGXl5f6k5e9SNGi8ucsKTAm+rJ0qy04b3Vb2/PSov6YIjQ0uejNCqCoZJ9h0Vxj6U/LXretmCjPS+E0dtpdUhBuHd/lk8cfESUwm+0z+JHgR0LQng0MVLnVqulY6qNxJBO40bzMvekbXI5nbGRNwJfvWfC5J6ae3z/6A747+w5nccnTcMIL85zPwqf0cU2KgZhS0d4JQUZNaCw/X7/p9HAoQXjONYCUXOh85Wcvx/LVXy1g3rrzn+QkelLmIgvPxmoMi9MY0YqGaTXBSyCK/sEhU5laX6SUqG2rV6KZME0TXt+5yy/6T7CmYq85QIA9M+dePuJoWvHu/nX+p8d/yo8v/j+64bTMqgUWNToaVNUcSYNGs5STS/kRPaHFqBwAKHOmPsyUv5/LJmi3EnnAtdfIyZOTdvTpyVESNFBUbEsBKAxoC4FoaadT+n7DdLpgHDblD+PKQhqpbK3xQrnmzZ03eWfxDYI3rKtA7TKjV/RrZioiUJmK+/Uhrk78z1/+LzzyT3G2LiCF1VEtB7WaYshW2XJrILsKSyl62aYBbuUYqCdH7cr5ar7ejlJbdYDZ3jG5WAMQvWlsg0igchUhjYVbUsiEzNUC3roWR83NnTt8dv4LTCVMzIw77R3eO3yP6+0tNmFg9ANYy88u/4aTcM5ge7q80t8vCu/Mv81luKBno1XTJdwtZk1KedDc50d7f8xbb874k49+xcPhhCfylJQHjAuMYcAnIWVtKJNcJDNJSKXFV1Ikir9CzTKjymWsvgq5PEVbshzQbN7ruy9/KDnqLyoy9y18upWbgHIcB4vr7NcLduyUhZuRxZQYTUVecja0tkXItNREAmP21LallpqIsu2BzJASNydT/s3TP8fVFdPJnDAm9g/36cZB/cplJDDlAVXIvyooUiRfdUdspyv9s9oy8rgSYWkr9S1jDDl6kG11168tZtuHRfRGapqWJKrdsdYWWYwSib5EpxYeW4PrRKibhta2/PDo93hQv8Hn3TOeywmbdIEcDJxv1mzSwFoGBjyDDJxIh0kV7xy8xqfrX9CnDdY0ZZTRV1frjiutLMiikptcvAtkpot94thrd7wtn4mq+sooqyOSkrDKb+iuqoidWlodkkYd40ytXGI5ODHbQ0SJWLKhNRPu7bxOZedYa1j5M15dvMbfu/0jPrj2faq0y2nfc+4HXsSOizQwMQfsNgcFIm6pbcPNnXsEP9Lntaa956Dst3NUzYwcPV+ffou53eUvv3zEQ/+E5+k5oyzp0oCPI4FETCOJUHZUKRFDpd6cUq1Q+lCM2RLMZRIx+lkYUD+U2dICFne48/KHqdT9GrbTS+EbSFfETzZJF9Ws0fbGtEzdDq/Mb3M8ucaX/SNc5ZiYiWqgsmNaTQjJ09qFXqd5pM8DG0ksJfDq/Bbe6JU3jhEfVoQcCTHhXFvkIV9dlcYqT3Njepez4VTFhCI4XBEIUjiU8sgbzTdKSdlzI4q95608pTDupgxsSlw6mqolpljKHPN24C6seqadzklBvwxjMikmmukUkuG1+Zu48ZBP+i9ZmxWBkT5vOL9cMYomQwYiTQuHN1pOz3p9ufKEtw5e5cenP6Zy6uRLaUAEYhK899y0B9yfHbEwDetxTUgBbyIS9LtT911hukstmXpQbOEvVJWsbkAp+50WpOYY9NdYyDlR2eqK3NSMhRKTYGzhkSqm1Q6ZxKV/wVuLN/ij4z8i+Am/XD3l4fCY03TJOm8Q6+nyhgs55ZJzovU4a6lsUyJT1fWXjSEmT0L3E2OEKjW8PXmXe9f2+GX4jFO5oJeVJqAYQUqEqdYtpDJ2F2LVGgVgSqV5bSdIHMlGRZOqI6tK57qKRm1VKy9klEurnK2IogkPhu1cW6A3U+ZspwuvZ803vvseP//oc56dnlHZhi50/LP7/4DWNPzF5V+xMStsqJjbBUfNIUs2DLLRsDE8WEdOhnXe4U/OIr9/9APuNtfZrWaEmPjTFz/mX734f/nF+CnWWJp6gXGZoeuYN7u81N5jx17n/Ztv8N1bv8H/8eX/yb9/9h8IOVIb3S8yGppsy35C+fAURgaTwNWaWp5SIhpDhWXSzBhHj0++NGclkkl64pZYGRGLHzT71aLCR+syY79mvz1izk0epS/BZIJs6GSpWrWs2WAWg7UtnexzNm5wNEpYBuH12V1emb/MZ/4RRiyjBPak5g9v/jbfOHiDbx29iU2WkDKzesbzzSn/25f/iv/r2f/D4LSnxRpLMuDKZ6D28gI5qSFGex+zwVhBxONSrdljJRER0MT+QqKa7biGXMH9gZHleEbTVNydHfOP7v8TPj57wsPxCZeyIZWuw5B6VkmJ1myUEzEGItobGVLU4ThnkvRUxtLWM4axx3vP1DTkDH9x8gnPwnPWccMgvYI5KSM5Fe+SIrCptN4qlKwAUo6WxfSmjnTW4OM5Io5IxOYKa2sd0a2B5IuMRhcTd7T76oeCXLU5UdheW5Ya9VQYsA6TDQ8/fUqOtXbO2UyymT+7+Bm71U0wiVE8k2oXlx1GDOu8wWc9FYxV9tsYCDKySQOnYeRs8FwOA10cuT+5yx8ef49XZy/x0eYTAoaahp12h1cXX+fV6dvsuj0at08cMt/e+SZ//97vYkzii82XJDQXKRecPZGZVLWOS1n3i/nBIWO3Vhl7dkxdq4w3lt3JAdYYfOoKEqaMtatbYhy+yt1KobDyWdWtGW5O7pNwDLKhy+es4wmRUD5Hx5bN166QjpwpqS+Kf/VBOFzs8NH5z9gzC/75/X/Mf3nvH/L9o3e45vY4O1+zGkfWQ+By3TF6w7vTt/j9W9/FiOXpcELdtLRUjFI6441Rc1VJKFTpjdNQNmtxGMTaAu8Kk8khVFOMMYSkltSUs+6BGayrtZHKTHhv/y3mMuc7hx9wtuz42D9SH3j2eOnpZEVHR7ait/UVkpRUoSC+LNb6IsXscZWhoua1xZt8f++3+I293+AkrvgsfEHIni6tkaxSoUjSMAnUH2IKiSxlhNQ0R8GYhv/2v/9n9OsVL148J4sl5UA7mxKDjl52W6WwHU9RJt0d7n7tw5xCWYSFrLmfutKZUmop+otVTJSZNXOGuNEZtzRQ9bLhoD5gHZa0Zq4owhYdsJmGFkdFVdeQDJV1JISOnk56lkTO4sCL0HExdtyf3OatnZf5WfclGcP12X2yqTgPSyrrOJ61/Gp8xlp6bLB8Y+ddpvWMj9ef4qPGnppS3TCZzhnGnqppyCJqMYWy/Foqawmi1cM+j7qYZsHVTVGlGmzVkJJHkvZ5G2vKNawokLMVN6cPGKJnlEvWckaSUHJrRZNEslqBt87JaAKQqExFlKyGrpRxaeC/fvDHvDP9GhINZ95z6gNPxshpCJhjy9Nx4DwJ58bT58xbO29yc3rMlxeP+e2bPyRhuAgX3Gru88rsZeZuh5iBbAjGU9m62JEN7c4eIUZSCkztjFcmX+PV2WtM3T7H7W2MOIRESJG3D97jmwff4r3pW9yZPuCOu40P8HF4Qi96GPamo88rYg6Fp9WbJ+eI5KSloXhS0kQdXcgD5EgcA3/n5t/l9dkbmGC59Gt+6T+jz+d0ccTLWNBJVWarbCwV7ZVC1TqaG6rKEkLAmMxHf/Uxjx8/ZhjWJfVdNIs3FSX7Vp4MOkEZJQrNm3f+MOsfMqG2Rs3XxWxDfCFnS1PNAMXWnbEqU85GN303xWC5095hp51zES/wwePF47DsVjtU0jLakS71RRBWNDcYaluxU+9yLR9gzITKOOau5a3ZMWdyyf99+u8ZXKABgmSqNOH3r73FmVmx7AMLt+Bee4PbzZz/9fR/53P/GaN4+jEUrVOmqRu6visfgsE4exVvUztX5lCuIFYkl4WuIluYzPfw3mOSJ8XEbHdBt1qxTR50ueWt69/hpDull3OCGYjJM7ET3WeMzu911WBzo3m/WZXJO9UhzsyYM+Gm3eUPjl/ngAWnw8hJDIwZUrb0pufSay/kzM4xrirKB0tlDItc08Vzfto95NKseDC/zZuTl1l3Iz5HVvkSkch/9L/kSf8Jtq6pZhOW6xOOJ7d5v36HHXtEiAmfE332SI54M5CsZ+M3fOvwdWrfsIoD6/6MZTVSVcJ52OCDNlpt8qYgidpNLiXCNMd8pZ2SHIg5Fd1VIjDgo+d3jn6PW9UrfD58wZo1UTwDG/w48J2j7/Lp5iFfDJ/RthPWm7WOhpQbqnQM5lxGrxJ6RxasqXUfLYc6Etjmo1CEk/rASyERE7VzmDfv/EFOsS+noSOLKx7jUX/A0tNgbc1ksmA6bbg8XxbVpzLmTTXD5IraNFRUTKo502mLeE3q62XEk8ikQkzbkvtqyLZEyGTHznSH6xwxMXNs1u6G280uSznnz5//FaNdYQxMzIxW9nhtdo939l4mVZEvhwvea+7yUf8T/sWTf4ltVHwYoi+nFwo6VDU5OoRYhIHa5KQcAsW5tiXNBNc2pJggO9ykIQ5qrjHF/CPosmtlyps3fpMnyy8Y85KYA68ev8M4Djy5/OKKoLK2ona1fqa5AmupqZnaXeo45Z/c/i327B6Pxo6unLxkw8YMfDY8QpxQ55Z7ezdYbZR32b/m6FeR2DcsbMtT95wn6RlkoQ0N12b7nPaXiA0kK9qngbCYTPnV8Amv77zGob/BxkcGM5BSLDuEWhmQpF3qWZtrZ7YlSMLagct4gZGaw2qfw8kREzehqjKByC8uHrJihRhPCJl6UjPfmfL4ySOM0RO+Gy5xpuXe9GWOpnexwXEWXtDJkpSlFHwKWSwfHH7Ap93HPB4fk7P6PVJStM8WVbP6ZvS5i1nHN5PtlbJCWYlUHINbLYGO/qrk053NoBWD7nDn3ocJr6x01n8w5wj6veBcg7WWlIW6rminLX3XY63FmrpEi9picDK0rgJjieLZpA0J2LN7OsZsr0G2J7UuibZUFHexp5OOqoS7SU5choGcKm7Ob5MROtngc+KG3eN4/xqfdSdMKsPT4ZKpm9EY4SfdfywnSCQlmE4b1TlluHn7Ln7QQhZ90o2qgJ1RS6h1VzfLVn1rrdWkcwpZWaL9oaA7GRaTA67Nj1iNZ4Sslt1+7BiDJySVlatq1BRJdy7atUwUrYz7rf03eDC9xWfjBi/CmDtO0gXLvOFpeEawKuGOeBam4sn4nEs542zYMIbImDyb1NNKRWdXpOyJNrGMy6sHXnIk5sgoPX3seLX9GtNxn9OwpmdDyD2ekSi6ZEfxBDMS8GzknDF2JDxdPOdcLtgxO3x95z3e33kHFx3r3PH55gUSHPvNPq2dMLMLknhmdkHTTVlUe7x343UmTJEID2av07gFp+NzzuQFq3SKZyDkNUKmqSfU1HyxfkwyQuWcwuE5K4AkCn1rfYWOskguam5FK03dYkS9+MVVw1UGFqXAyVDMYNsiUYe7vrj3oZSY+20YsEqWtjJwXS7JkHyg64okG9VuWasjRspR64XLS5CBxlmmds5ZOiNmobaaeJFEodurv269GWXZ6mVDyJEhD6Ss9V8uGXbdIZHAOl4wNzNOxzVnYc3zcMHUTanEcXdyzAVPuJANzlpshmEcmU5nGGCz2ijSYUzJHcjUrdNF1tivCMWmRqzFVY6YhLsv3eJg74Dz84srKBwokGm5FfOUzq/IBIy1xBR0n0GKS/DXbL3WFi1ghU+JnTzn63tvs/QQiKxYcZZWrKRjmVb0eUCM571vv8azk1Oebs4JedQO8+TV2UnHQM/KnjMxLQf1nIu40k9WtM2WrSRGhDkLGllwmVakPBCzL82zI94MdKlnMBtG6Rlzh08DURJeBsbcs2tm/N71HzLNu/x88yv+xn/CF+Nj1rLmNJ7z1D/mhX+BRDiorlNLQxfXBT0EKxMO7E2ytTzuH9LLOXZm6MY1VPoiq1fJ0SeN7xmlZ0y9EoDl5pficDRlZ96qHkyRrSdgMT9mHC+xpd1s60bdtikXfBtjUhEoGJyxmDdufT+L+L+lQVGJh/IDOTuc0f4LZ5S1rqsZVTXRqmRRKYExCmE2tlb4TBQrj5VwXF1nEM8mjNTWFYRFs1f1usuImO27jDWOxrVM7QxLhRHHwsw5cPvEnPho/WPIhnf33uaJP2ET11RVy3F9l1end3lzssP/8Oh/ZMWA954gkaquCCERo8fVlpikOMtapvMJQ9cRU2TStoxDoJlPwRiqpqJbrdQEtCXryVd6MSkEpKHmaH6PFBPrsIRSS6fQYmHlKRJ1VOCXTcU0zfmj1/4OzdBgwowMnORL1qmHnZ7L1YCpYTOsCTEweA8uM6mmygQ7CMXHbbPT5BNU91bZik1clVv7b6uMDJYmzcp3KojLJDyBgUEGvYFN0DE4JyT6IqJJ5GwI/cg/f+2f8nR1wS/jI56HJ/jksbWhDx1dWBFlLAwuLOw+tasZ0oZshMo0VLkhJcNutQuTkdPhBFdVhJIwUvQsGNHkmmjKjWBU3ClF5WyuJDXFz2OUPxPJJTUqaeyp25ar/dqzLrncGAbQMHNbDHnWVrijnfsf5pLevZUibD3RW7JEclQtjgVrlGGOsSOWznJ9a1VSHSUzd8qu/v/tnWmTJMlxnp+IyKyqPmdmZ3axO7sgCWGBJSmY6SBNomCUYPqmL/oBNNOP4c+TmSiZRIkgBYBrxIpY7DFHV3d1VWVmhLs+uEdWVh8zPceCoLRhM9bdVXnG4eHH66/HGKEIq7JlEeZWB6MMpGhRXnPJKaJGnN3EhiY0BEwFaVNj2V4Ifcx00nHAEUTh6/7XLPs1v3/8Cd+99z5/e/5zOrasgzBvT/n49COe8hWD9vZeqiDCfLEwlal4KegYKEMmzVorL0egXbQ0bUMZrAh98gQyEA5PjmibGV3fEcKMZn4fKBwe3qcfLJ22SA/B2EPApBFiUB5RYXF4SBmUx81H/OTDP+UXy8/41foZ32m/Q47ChRu6l3lNl3s23ZZBC710VgckmGGa1bxBl7qmly1NaglinsaCkRYMMXM+PKeEwlA6Ch259KY6MbA4FpbDkq1eslZjBikV7oGn++bM0b1jNpuOh4/us1pe8B8/+A90A/zP/mcseUqX7XrbYc02X1C0c6iOTb1Ot/Tak6JF6HsdGHRDYculLFkPGwiFIQ87Tca5nK1cNB6TUZDgVcocjm8oWnOy+q6B5p2dXB1U6t4qF8WmCFQcmhhMJ9oaECzFu3ENjeCAtJ2IcQM2WN098YcusrECNWHhgDNGSIT52MVoV4JJuYP2gHW/4awsOWjno1ehBPdiKW5zGO7LcYi0IVlGmmYkJqL0bKNwwZIZBwya6WXD/1r+lO/kB8QQWQ/nnDUtP71c8KPF+7SbQ/rha5qmBRq0mbEZtsY03yYEQ+K2yaVRC0OXOT25T58HVAKL9hBRIfdbSIGmSWy7TNIWTQpizIzb9ZLjxbvkYrU7al0LgCIWhhURHi0e8sHiEfPZEfN0yk+f/y1Py1e8P3vMhWzY5oF12HBZtpQ8MIjZC71zJksweMtAb/ZRUfcUwUV5bvk3YhHkWVxQcmY+X9APHVqExeKAfrP1opZrnlyuTfUKNhNK9d4JrhoK2YF/Ipkvvvo1j2YPeTB7j/+y/kv6xYbuoqdIx6A9fVm5mu1IBY89Gd/Y4CUbAojnYjjxXorY+6FQbB6RA6SIlEAIhmIoxdARqma/1l1EgVhs8miA5CXJidnBqb7YBEZcP+YuTlU1iHEcs4pWbOp6iL7xVpCKqEIFxEm28mrqL1wCJXQOWvOaggFimBHjjDYeM5vNuezW9LGnbWf020v6fMnJ4pQui69Rg35ktQq2lr1oGYxZEjnBPDQjxBpNrFlxGI4oAdayJQflYmU8wm0KXGyfMmvvsdJ3+Jf3/5iP9DE/ff5zvtr+mmYembVz1us1P3zwPT4+/CH3Zvd5EL/DMl9SQmBbei7COY8eHPPp52e0UXkqT+EksNw8ISRlU76AWEzFLBuODx6CBIa8IectntRr239rNcxnHPDj9/+ER/MPuOhXnA0rngzPOM9LpIFVXvGFPkMRNnFtAUYEgun82W08PDVUXSkowfmn1CDtHRt3mkBXtrSxZXV5SRMDJRRWl1tLBxYjZ9YSnNrT9HbbbNUWuWYvGSk8/fprYoQhbzheHPHl5gnP+mcURx4MWIyoOKmfZU+7URytDgghoHFOKD6lncrHnEBlvJci9SskR0dxu9oThFIMrasOl6/hC6XmzWNBxNjsEr/GRaKMzAwoxhmtNYmCiuQ1t1YgPTz58M9Vs8EmUFDDbWoMEJJlwdEaWFC6Hb9trD5mp6OsTIYaybox4GJ7SFcu6IeO+fyQwauy7hCyYmTItGQZyMXSISvtigWATOLkYlWt1D1Pv9N+wHsH77IqK2YHkTIYlkdKITSBjWTeie/xw/YTfvLw3/Jg8YBfrv6Og+Ee/+l7f8a/u//vOcjv0m8PWHZKHpSzbsVX6ws228Kz5Ya+FJ7LBV3u6XsBnaNDYj4/JOcONHB09AAZspGO5S0h7FjPxXVctOHH7/0px+0jvtic8dXwnGVZkkNHxqAsEjLzYO7TgQxa6FmzKWtfHGbvmYbgEt/jNYjBOFw193IWnfF5UaywJ2sLdEZXnxzdINKRdWCQjsWspes39GXDUNYo0YJ3xcjURDMSCg/SA2Yc8jQ/Me+YFnLJDNohIZvgYKDIdhKdNlshVkb4GmT1MmyVBjSL7UaqxSPmGaEbOc2yGCjRQIbOSRyooDObxWY8e1jBEc+OPbOYh6lUIdR663HchUbgK+bFshoBNZc7WsI9NW1YjHZSyDBimexBKr20xUxs0IoIVrg70ZVzN7aPLHCWE22asx02HM6s2EyfNww60Kbs27IzfDQLEu1Yr68rRlefvY6hhjVDmnPAEd8/+gG/OP8ZOSopC0kjZdiyjEv+YvM/+FI+5OPhu3zc/iHHjx+CLlhvhL+4+IyCkUxc6gUbvWSNwR0GNXaQnp6ce4v2BqMHKtpTnES5aWcMnUWCrYREcCI9YyaZNQeUDD84/YTD9A5fb5as5cJVps6Sk+KAaKCTLRfhggX2EhriAAAff0lEQVQnaCmswjmbsvT+FoZittDB0YJ+6NlsN56zY67oUCxWEdXUxb70NCpomjOWkCNDbsYFVvm+miag20yXO3LpaBcNUhqGfo1553DgphnC0grLfI6GwjYbxFxjsfqOIUDInvNhXkGLNogVEqrAWE+AU18cAfUS4MVNYZfqUUEKuWyddXFwlUecxGKE5U5aHPNorJKypfvi0P9qNoTxTN07e2Jo0ATMatfpt74lWacEy2Zjx80anX81pJrI5BjHBG04IqZIly/YDEuOFg8JQRnKmsXsARqE7dbSVZECsZDzBg8JG6Qhd4TGAJIxWFXYRhNNSAyyQWjIpZBTpi8Lvn/0CQ2BZ+UJZ/kZ89CSROiD8Fn/92zTmgflEQ/bd1iXNeVoTbsofPX5mrWs6bRjyyVbuaBZJFaXGxDLksyl92Qsc43WJCODKNjntW/atGDBKUfxhD50PM/PiUR+7+iHPNme08mKLVty6B2Ko+RiomYIHU+6v+ckPWIR79GVjfNRObNkjBQRnp09d+mvjm0zlKqGSC6m3hUHHuYaB5Ds9oQBFit62bJgvFZKjAxSLEZTgueH2OJUjeMcAGhjy8VwwVYybTTBZaWei+1m9EaIoSaFK5zDMv7UmBVTgxYxGqBoKb7GZrhTUCV6diPGmmPOD8/e8P63f3HPfjboutkqgLEX+Q6jKF6z+Mqy2F9mlnWoFgcpyHhKcBVG1VYxGgiOCo1NSztvKcPWVKyqV/oWJyoMsiGGhSesdCDBqgnljhTmxBQR7Y2lRDvnR2LMErT1LKP6UEm0VYOjUE39s7xyw9y8O3vIcXqHf3HyIwLCrzdfoFFN6kZlEzuWuuKsnPG4fY8HnPDp8nOe5CVD6FnrGau8pJMtXdcZ2RiD2UXB3MElG5m1MTPahAtufM/iIR8e/JA/evhjTtrHfHz4+3zv+GP62HLcvIMS2cqKddxQgklqgowwmKw2ufrS08kaCQOdrF1NK/R5g1Doho3ViXc4hUqFWShD6ccYlDlPLDEqy0AJhkdCjEA8xWZUJ7IMxjaiO6yYqlKKv2OwyRU0UKIyDJmTeI8/efSv+ejgd3ivfczp4gFrOoMpaabPKzR4jpHuJLyIlZZW9zIVxGp+uI0ZK5ReFYnOjFnRrRRTySi+c9guETyWweR/XQyBypmmk12iVj3cqVN+1N4nFr5IhE/e/7FmdU4kLJhVrXmROKJPcR3SDJpJ6qVGzx2O1OQq1ci7jz7kyZMvmLeHjijtWTRHNGlO118wb+7RySXGJWXSLIUqtWzizZu5R7WFeTiwBK7oR8fGF03ihCMktJzqKb87f8wvur/m5+v/TfLYTNPMOGlPWaRDorZ8FB9zOjvhr9Z/yUov2Ja1SSeFLJakZa5OrwXoNJ8q6khRA7sJcBgf8MP7f8xBOGYll2goNDSsyoYYdoQOPVuGYoFPDcUwQWKqCw7ZHsRYGNEKujOmliEb57B6zGKHG7JxoF6nypmpTBRBYiQINMGyFNULYdohYcynsx3csigjjGgDDfZ8Mz3gj+79Kz4++QHLYcMX/ZJVOWMpT8ihM2KImNkMZ2z6JaiarRZrBoUViiVET8pz11KcJK05ZWOIFTKrlgpdvU/mq3W74VVbNQYmu4WE0bywuYblogAxzmkIbrBT/cz1UpWOx3ifTt/9gPOvPyemA3Jqafpz6+RYmQMTxJmdXDLvPn7I06++dNi5uYClZDItJ8eHzNsDtmcXEAJtmplbznXHGFoa8y+gsXLCWvHKGKId69WmFOFMz4naMLBm05/zePY+v9r8H7bhkkxgGAbW/Yp5OuCd2UN+yWe8p++zKVZHIiaPxsaWSGGb16ZSRfcWaaBgEJwwpgXPWcQFv3vyz1BtOOfMnA5S6MLGVRwj0UMM+5W1Ny+Lx2Syx45UGANgxSlRCz05dzRhBk4PFLT4hFVfFKZuSKxRrDAdelPPQiA4Xung4ITV+tIcGdGPVffdKJZg5FF2JZCi5W4PItwL9/nTd3/CafOIz9ZnfCVfs5ZnbGRtu2zJFtPKmRQPmLeRLi+piAPXlDiY3WPbXdhOEWsAc1f2rE5GK1pUVbY3WRT7i4O9HgoexK3fX4mDoNXNu9t+bKE4XUu0Og8xBLqLM4vUwmg7jJeWWO8FBEpMfPpXv6DWwTYXXkZjcixMSwmWmN+kOUXNdWfSwX6kOKdJDW2cISmxzZ1thT5ZCXheeu3ogQ2ZrWy42K5o0gHb7owQAnOd8YP73+fh/JRVN1Aa4en2C7ZsaOct2+0FokLpB4oOloyjNkjWO+qBTZtoqoFe1nxw9AkxKD2XxsXr/K+GXTUv37ZYFae+dEgwytDi9UpA3LA1VWnIPbW6q6l0mUGVFOx6RTKRBg1xxBFpMCwcGryUXfL5IK4qZ4qsCQrnq849Q0rUdlQ0QkzEkJxe1Ch5VAQpZmi3OuffPPwJp+ld/m7zJU/LUy7kGRI6gsd8FCWXPF4/uO0aFMs/8T5EvYSFe0NtYnokL2LH+A5t9vfV2PebLY5dq3Y1VJa4gI5HOgcmDVpJT4qzFppqldpIyTZhoypDMe9CKIWGHmEBcfB7KzCzN5TArD0kD7279BLIGtUeYcaiCZxdGB4nJJDcI764pMZpAhTZMIiwCYmD5pBZsnyMIfe00aAvknzyaHJmj8hBs+B+OqJp3+EP7n+fkO2lhxxYbeC7i8fMYuK/hp/S5Q3DsKFtIlFbct6YC9TLiYFa8aDYMvQDMc5ZHB5wcfGEg3jM6fw+XTb9XqMapY4D5no1wJ8EQYvlgRcR1yAswzGXDMFoRlVdYw5iqIh0RJElaGYoebTOCmqEGgQrBxfcu5gORhCe4EapZvDcFutTLzMWQOipoX6VDnE2/9TMbeIGEwxZCz86/UPux0d8uv6CZ/KEc3kOoTeWkPouTkkqWtw9r6S4gMaSo8w7qmz7pavwdeI6RL1Gz12ltXd5kx3jZYvDXfDVVQ5Vrxu5n5XoO4gzBdapHiNWe4LoLjnAK4ASstkk0bmaCOAVZVUzTbPAsPaZJh6iahCHhhlNaOi6C/MjxGh4mriTIGan2wDv4AHCerikbQrzuICyJWMpwqm4eqHKLM5AI10RPu+XSCrEPnGQZmgJ5CC0oeVp94xQGk6a+/zB6SM+W/2MnoEZLSzu0UvPJi/ZDJbTgCaGbAVhVJW+7wA4XrzDkDMSLDc9u2990N6YCyljFl4JxUkSjHJ08DrnMvpSnEnfdXAjFTC4dSkbEzSTgc66dVd8dHMxEUqHpEhUQ0KXIqg6dVFlNQnVw89u8gWxe7pKmbOVSRANHJ3cY9j2HIdTngxLLuQ5K3nisQmD2pci5DAw5MwPPvl9Pv30b2gi5CH7TtASyO4Vq8E5t518cQhClOLPqK5Kvfm+Me5Ot3w+Zbsxh4KYylr1wQiNBh23GKEyJwk41KPWC0wy2Swivji8jkc0KtIQZxYL0YGUZihCKWtSaJgtFgxd7ym8JmHAoBIkK7dQGUaid2SoBruqFTlJShMbStla56cWkYbWV/5GOhAxZvNiiVhryaMLOeuWKBFSwyavOcpH/N7BJ6yGFYvmEEJkyIWwKCz7r3imX3C+WTqjYiGEljkHhKYhlsRaLwhByJJtkjVYNdWodh2semxlKzSD2yLZUmH/OCy7egTFENSAkUTEKzozMtkpdCftZUOIMwjRqjdVcjk/rqpkoc4PdghjopWboJi6agTYgcv1ktPZOyxmxzzbPuO5fO2weSe2VrG4Ud6SpefTT/+Gvt/Szozfq4At2HSI6hbRHhl9SJapqmBQj1DfM73mYriyAGRi5O9tRGH3OUx2M7d9iGYZeOC1GT2qY/dPvCGOx6r16GzFWYzELq5GeE31pzQG/stm5Ikzv0dge7lBQ7CKgmNtdCMVRYsvqDRG5OtDK1XwJZOmySoRDTIQtBBDImviXM9HaSlZCFHpQ8uiPTK3prs+iwSCZIpGJA2sunPj8e2WBnMhMJOGeXuffzr/Lj/lv7HsvsYQBh0hHXPaPuDdD9/jfHlB1w28d/Ien5//Cu3EdouiCJaRaQyCGOlzaImppR+27kFXpGxRHcyVTSClliK2qAyiMbgtV5fJ9KcaN5REUmqI0oLXlwwkUliwzWcm8QNEzLVcbfkooNHGajeKgUEjDx89put7kras+kueylMyG+Oa8mDeUHq2eU2Fj/f9Fg1K39UMyoB6UpMhoH2ixfqLqZ420mFqkdw86V+ocl1VpXy39IBhxf5OF8zOpzVtTiTn66IhghSpwElDnlaXG1CDKzUyaV6G4ruJkUsbRD1SxCqxmvrUu/1hful3HxmQ7/nzLwgxEeJUgvaUIqRkEPPiC9CcBN55QRAN7natlJeFlALzRctwmW2nEeXeg/ucn1nprmFYQXNgxq3rbVqMxVFdQls6ijhfU8ulCiEnNvmc4+YRQy7WqaFlFg9AhKdfPnPITOGL8y9c5RA0W0JTdmZDAC02WbIwUg7ZZCmIDg6VMI5gUYNn5BE/tz9dXKRU+UfQZEQSISHao7kQ08x3Ngi0VAI5hRGo2W1X4MHHWGuARIt/zZo5si189/hjjtsDlqtn9GHtcHI4vXePs/OnbPsLq85rS2QXbggWN9Ia9fbItU3bGm0zruXq3q2hvhcrVjctkptsDEbXsWWMutCPLz1r/8tQwYp+YsSKmFjKIaMuFp1jiVh95omKokzNAmKi9JdmYGLFa4xny37mEPjoo9+FEHn6/FcGd3e1yPR0JQQl57XR7YSIun1TVM2t62ppqdyx2DMtDuY8/ugRv/zlr1mveiLK8vkzYjTOo6DJBqsRJIedbYPFPNrQMpQtMbU0cW5u6WDuzktdEaThaPawriIzJlNDGxMxRbadMT9qLgx0VpyH4juWPWewH66aVCFk/R7ESLutHiPUs2K8KtnGMXOJqE4c7glYYWd0S+kIseX03imXqwEZgpPBKTG1jqJONM2M0iuz2YJue4FopgkLPnzwCffn73B2ecbF5YrMwDsPTlhdZLb9wLPnT9iWFaRq05j8F1edSt66x6+6nt2LJYbaKBO1z1TG11WrbjPAJ30XGRfKi8667SrNeEb0y0YjRBaz3ZgvFnQbg7hHSUisMt1T5WWwMl6e31H1uoBFeiOBNGv473/5ny10n6pfQFzv9M3Pg1JGreMYo6LENHfCs2gBHKlql0VRl8slXz8xpGkMyVKE3RvXDYZsDSERhr6aw1U1RxGy2CSLsQWkorOJAc8lERILI6cjU7TQhMRmcEPUXaKdrN375fxPUr1ThVp3UUPjhMkDIzUqOkESVEMvuOoRnFwZN9RrfcadTYP2o/vUJqTZNFGgnc+Ia69v3rYcL465XF8AyvzgmL7vOZyfMF/cYzG7T85bjmf3aaTh6eqZuZ9TIfdrur6WTrMsSXamq08hc1Lk3FNLzuFxv4C4p8ie3H2mCFXUyi0xjsmOsbd5yNhVOztCxqAfcXq1MAYA910dL2iuVQSF8MkHP9ZcBmLcrbugNoEtC9EwMiRDZBpuqw5tsmh7xLdMV400uZ/bJIQBT21HCGHqa7aJWisK1y80prEGR5NOENmQ0gJVf3F/LtXseRo6PnwIjTEThh3ZJuo55B7HMVxP8WslIjPaNKPPHaW4IyECktEkUOYczo4ZpHNY+E4tqbW/VQWhOPR8oBRTlSy7zW202PpgGYNjAI+5eICsMqoAFChxIIZD4x8bOle3dqgjExY7KU4IlmVI9IAkDmiMJNKunwPM5yccLA65PN+aehdsEZ4c3qcJDeIpyFvZINIzeHCxFPUa4/be9XEr35XkWm0rWCBT/B2lpjhbYdLsAWbjGk57lkB1GY1NjEs4uhbjlAGjA4lKaF41C58joXqVAugkCHmXFgRSM9vlg0yb5aLbBJjPF6SmZXO5tidQ97G7JI8x2cfOEmGer52zS/EaHjsfyigBRUxNSGDer+hOARHLBw5zI68mezJ9wjimTFqV3I+FIKl8Xmos31FTRS1YxphENHoabCkeqGwJJaGxp/ROdxmjxzSUdjbn6PiE87NzLvul9Uswb8WgPaqWxBMlkD3rspYcq16ZKuWM2jTXwLJNFHYq1XiCd5NEgQL3Hj2inSW++vXfud1kk8fSTB2Rm1qa0DAM29Eh0KQFpdgOOJsdWU5Kasg5k1Jk6M7ptktSsyCFWWV3NaBoNEDqdlgzOAypaSJDFktcUiEkezMFDw6a2390r4yeH5/osfrTTPewsgsmxOoOUnui2iJ1p995TdVtWpukEor3YEA1EmpxowryHINrFWtYA20vXxx13G5cILvpHIxDtW3MLiCOsAaSSbC9vVYZicIiXsdiqhMGIw8Q31yJMxaHpxAK2/W5Xw8z7lNLKRvAiJVLyYRUiMwQMmSnyA8+G30UQhA095Rgdo7BR4yQGLEEI2NtcViBOOgyNWY6hirJlaEfWJ6dWZadmgs0a3Z2+GHspWo2i0+ECvlQMGkax5Va9dhdXgfsVhKyswc1ICny/Mlnvus1CMEFUtn1IWIQnhQ5PL3H+uIMaEENioMGg6ykBU27QGRFSpFSAKzilIZmdKf3ZYOWwVAP1LxwQJPtjlT1zlDApWxQ7Q0f5u9vVQLMvpxOS8VpedyWjarjLjPdPAN22xJMUBuLjLhJL+bhb2ZQBhMUwexB8blYKDa9vEzf+GB3WBxj82l7q9+sTuttN7C+3PiyrpPR/pvHVyyvYf/1EBmQ6Nj+iG2NKkiA2eERUuDdD/8J/aZQihmM5vgLO308RGKa226lnblEKaiX8t35cibNSyUH9cEvlutcwwLBoS4xtOSyoWiPak+NnJeSvUqU816VgepqznmN5BVaehMz7n2qKooZ92F0YATUGeqFSoVq/lt/VhcWgtFlmls9IBLc3o5OiGFSMEgZvXi2zdT+VaQMbC9XoIGH7z0yyk13zWvIDPmSzfY5KgN9b+paSq2paaWQy8C9hyfkbCQXxVOJRQuDCAcnB3Slpy/FMFuqY99Ffy+Fib5sgiJO54Sq8/+aGorkveN91MdpZO5+U43UbUYBK/FmK9xHTZ2EUE0oeypvxapFZ3LZzd0bmkx+Tg5Jj06+++eojOoIPuYEU01O79/jd37wfZ58+aXZICojxFgVZrM5pGjF7T1N0WaLScFKsGbXNVVI+oH5wREqMx7+6J/TXSyt/rgznAR1F25MJgEqilLd9gh51Jmnqtu4HbvyHzzYUzwTz+DWa2JorFNVLC2zDmCpWKtagxD6fEmgd7jExjmM2d1z9MWM28BIVKduWBlzuFPNjK5Qzy2p7B1h53zQnb/UrKgQvb+dgECFGI1sr27S0fURqxQV6fLGOiOEWs3ZF6mtGnH10HhwTNBsNmaPWCFTW+RZMyKZy/XGXd3mdTT1vjfCtmp/Ri/VoM5B7CoVohQXJLYrZedo9vz3qiZNerUWEiVYMVHrE+MSVufODTGSYmu8ytGSxUI0F7LNYZtLodaTHFfADfuChnEbG02EkMxIlzLsV9lxD5MFr0wtiqlxENtEI3By59G28IzDGhBS7/igydkoqivQtuHjB++T7j+ie/6UfvUcHZOT6lNWFWSXEGNaWLhi1+j+AtFJB1Tr393GGjyGI8ZRJRUnZKxuIEalitYKVP0uX0HVuYv3L6+2DHbPwS6Lbn9nvaJli5WBM+kaIDa+gGxG16y76qIMNXU1Bvfi1IxOi0Es5gcM/YbB6TWjTw5x9S2G5Ajs5CnXZpuFYAHGEKpqaONad7yqQBYxphSDnZsAmvbESIc02h5VBTVpb2BLcQdKbbdMWKRaWt5vcc9uU03MD0959J2P+OzTv6bxbFghEEUhZNc81IXC1RGbqlxu+/quXT20TbxipIcr14iV5WGC0yLG8fJ10MS7wdIrAxITtU5fCUIKBSQ5lN6losDl+VfEi2c2SWsnq1oMQHAjrnbWeMOxWydLFcCDmRXdaw8sLsGYDOaIApBMTArOu2Rw60KRNeaIDG6Y+9c1+b/uiEydDeroX8t0q3Bp9p8QnIjPdOM6iVw1oEBMHD/4HpdnnyO5B7wqYwjMFjO6zdqrSMWRsd0KBsGQe4rvmri9EKU4+tcxT8Ge1zyFFlVW6d34V0JoqUFVk0FmcZRihvjoaHb7hr3R2P09FRiBQJGBEKxI676Sc3PgTwhWJo7onk8ZlYMavO67NU+//tzidMHVrABW8ppRk6nByV2r8+bldknjjgF3xznOZzIJJgrztZOnMhP3Vqm4hyK6muXfacAnEhYEDFjyjksjK0BvEPoxFFAN30nXV+k7ifvsPCfRCdk01D3yysY9fXhfiHWw6zGixFBzLPeHzwZnt2Mp/k5BkDKwq3dX/fB7SgPRs+EkNqMhv1skJnQlDVycf4369ax4qRK00G0ylQ94BNUFSyENEUsPrr3lD14EII97mtKiOlCKnQdWCiB54SGCuxvqpuuR6MoRsRf8GIXOZBcfP6mCzBa+Uvx+V1sdSK9yLNOZZgljIRpiw2ZHQMW9kZrZXC6pm5aRhliRUtuZ3bN5m90xfYSwe5Ppvt/Yh+Kd4SslMg7M/hKostG3d5eRUzluvvqBGj2N46vZYI/qkyt76jQsSnVb7Kqsulq9MwDHpr4b1YnqxVLGE4qv3oSpY/uS3Hi+qt5e9q7sYtP6hGATrIquSqc0LlxDAJjhLHWLZW/HG5+8jLA2NJs8dHhJ9IUsKkZaUZ5DaDAc0WD9HON45YCXpUCZzxeUUii5GA1TfdNx7gZ3eVouiTDYruN5JcXJEHKxchWNJiqNoMmuSi9Ud7qr73X97+DCsAq5wmBQIW5rFmC1xRFJbUMp1Q6KnkNkODqJ6qm59VncBUZBJGAUyx4LqQGTW11RdcD3HMt7rTGjtKodVTsL5iHZe/Ep/1C9p1z5O4xTNjrLx9RKCHtX2zUtE6lx9bbTz/ba9KWu2wUCUIbJU+6fedPn9Vy9+neZWA+6b03Y+t3tKDDx6O1tQfaZivretOu7Sl8aqeBNNTUBHIi8k6yjReO/dNv17p3H59S9MQF1mTFRZalYMUHKbrvJN6kddYedbtsvkcpVVk175paB3I1XsGPKIONtq3teoyNbZLov70ahglWqnBzf4oWLw5+tVgy+4ZX2bBDVKuVtZMeti2mXiWWeRVwdseNHb3eshp7dfKrtTefLnooUzS59+ctM2xS/MxlQ78x487e3N5fu4/tOnBFjvKn+Xp/ddyGt8M89XLXspE5diu6ouDZwYjfUmh8erneEhOnBu4lhiNn6eW2OlXYDytQSP82xZjvId4Wf45JYbxmHOrZ3bPWVYzXx47V5ZD+ic1Pt9ncmO34cVWB/gbATAuPzEkc5ELzfdwGAK37bV2y7BVKXXWWiQyt38JVdNXrU3BfCGAi7ugx077J7qxpftNMneaXFMT7M9RZf+O3tLV55xnj92et1x2cfF/XVt6sPstspxmNugjtMAok7d/v+cbvhrtfd2TD2yQ4uvjunKsOTh47RY3/jNLt+k1fvvb1W+8h+t/ee4MOv3Mwmut4wh2M9/9qXV/tS/d1usptftjhe/H0zvd/+A9hnut/jkyP8mODbU5wedNVi2P959ZZvNhxvt92mWd/07HJTn10/ipe/aR1wP/yK+3RUVaqk3Zsw7lcKkz7V8TQmyuHuMeLL+vzNR+bqDLh+pd0cswl+/Z7jb9f6+TY1cDqr7rpzTNSBG22QG9vkwhNjeP8Bp3++XofefPTND/p6bWopvOi6exbRna58yzDd0O521N6E2Snk7E1scaX1ht22qlB607pker27tIm685sSX68AJLT2ove5687hx42HTzUhe579BSLTg6btakfVwdzzX73kge7Srj/gm18LblL9bj6OW465uem1hXXVDfHKhpU/wvSZrgqr2865crs3Go63KaResV2bTlcdrzfNz6vtrsIgXPvr6tJqrn2j08Nhf8Bva/HKMTd17qsaSq9vWFmbvmr9/WUT9up73OUe03Nvu/6rvstrGpZvQ0Zda9/kYpn6N71de4eb+uJN58bLnmk3js3e5y884VW+v+pDusuqv+v97trCDb/fdu3pQnrde0wX4fT713mXb3IC3LW9SDt4GwvmqmPnRcf9Jtu+8txc++7G9qqegJsk66u86DctIb6J+4YrP9/GNf+h222C423aJm/mhn37bX8H2YmGa56sN73Jb9NLf9verAWuj+nbHOMXLTad/P/Nt30V621oNnvtJrPn2/aPu93k1Lhru2rPXo2W3hLv2Dvm6rO87fYiFWtqj721xfLt4vh/r121ve7apjGK6WcvWRyjCzheOf0lwve2tfsK6+x6HORbof9te6X2OvGVm5wbN113B0d5rVvetnZf4ZFvDhR+uzi+bd9Iu20hvOT48Joz/RXn8TTGWk9t9m2fb7eP/x/aTaP72wT3ud5+M/Pxprvcymrybbtbe1Fo9E2vqy/4+3WuV9tN8vi3ERf3TbebgxO7wlEgVxfI9U3mddfureC0Wx/vRZ/+9ra3CbS5et2r/ps3ucfV8OVt338jwfg7tLvgNd52u8kXt3//WDMKbx+A13Vm7V/rpiDLzarcW/c0f8PtdWPwd7nu24jJT8+/y/f/UP1/k3/rm263uwq8t2XCzRsmEGgDh+i1i7xKu76D3PTq14/67dpB7v40uyNfpKS82tuFK9fb7ek3KV9vp+defpXXUcJeroi+2Q5yk4v4Va8wuYaDdjUpTaAlpr0jv1F42j+udodemOYuAS8e4jeZXNMb3qR8fUMj9kaw+dq+aQXqbur7na/hp8fQ8n8BFFAVKhfO/MgAAAAASUVORK5CYII=
📡 API Calls Detected
- account
- logs
- https://api.wallet.coinbase.com/rpc/v2/desktop/chrome
- proxy
- stats
- 0x3b3b57de
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 241 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 241 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)