
Phishing Analysis
Detailed analysis of captured phishing page
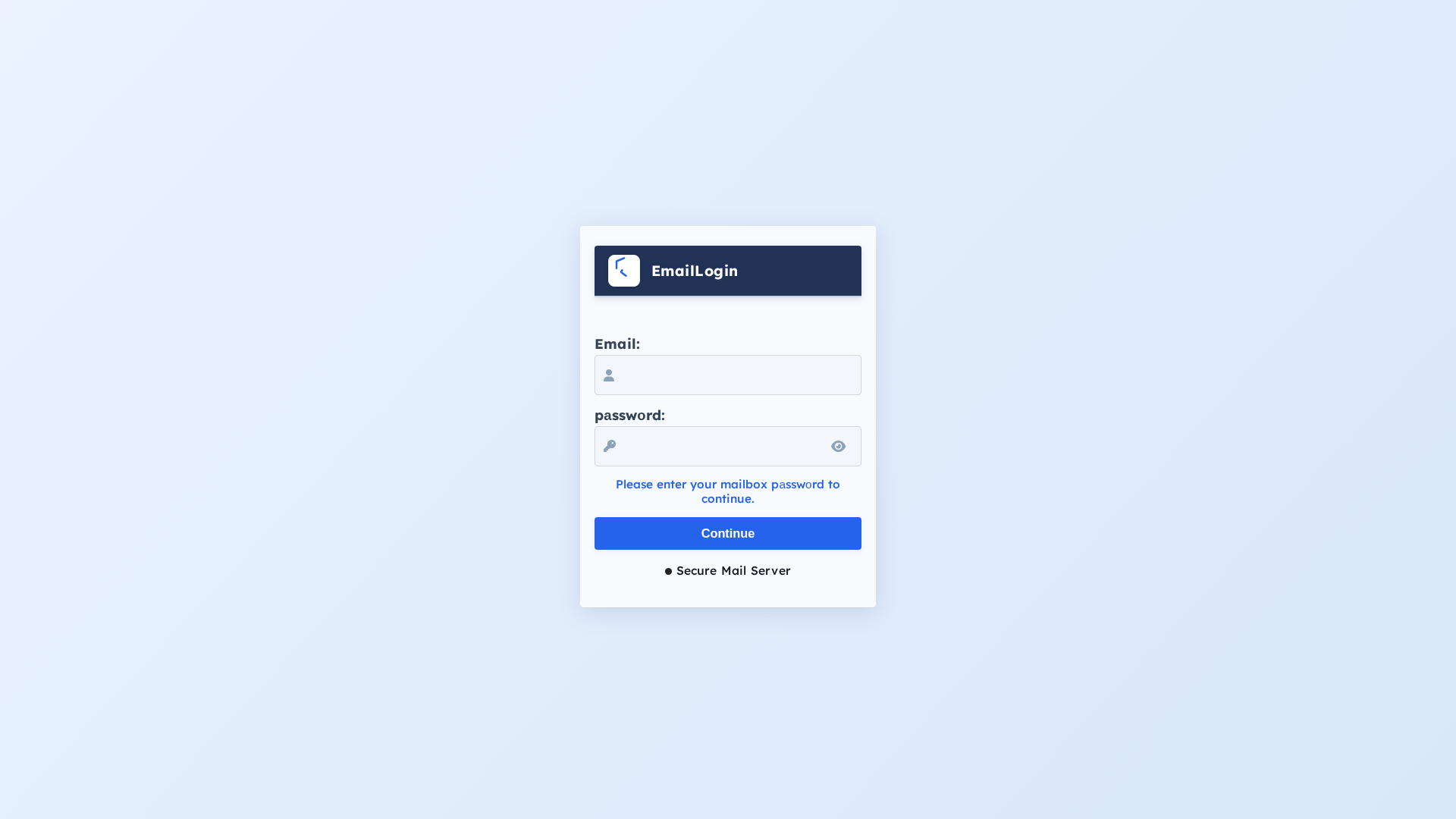
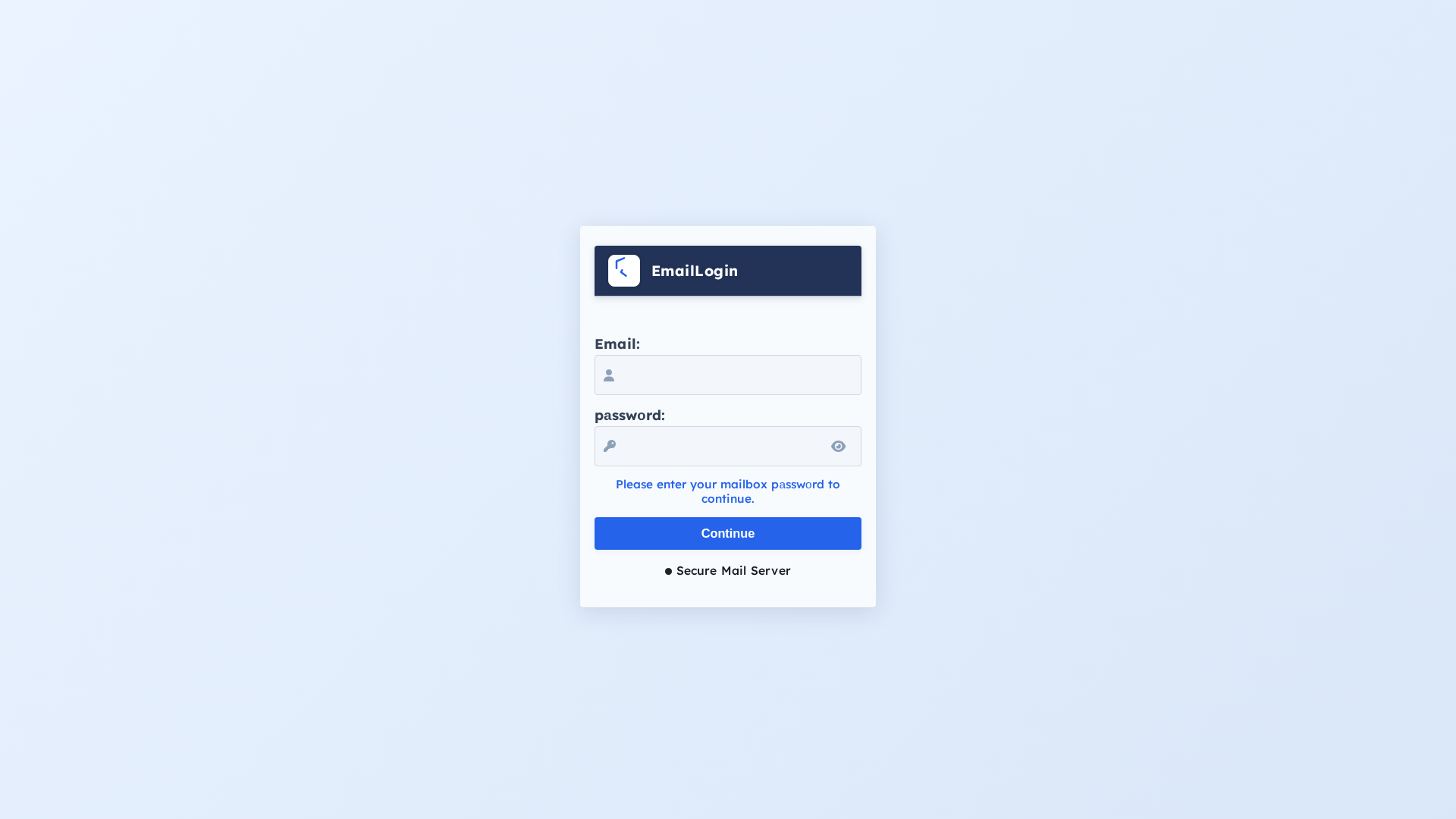
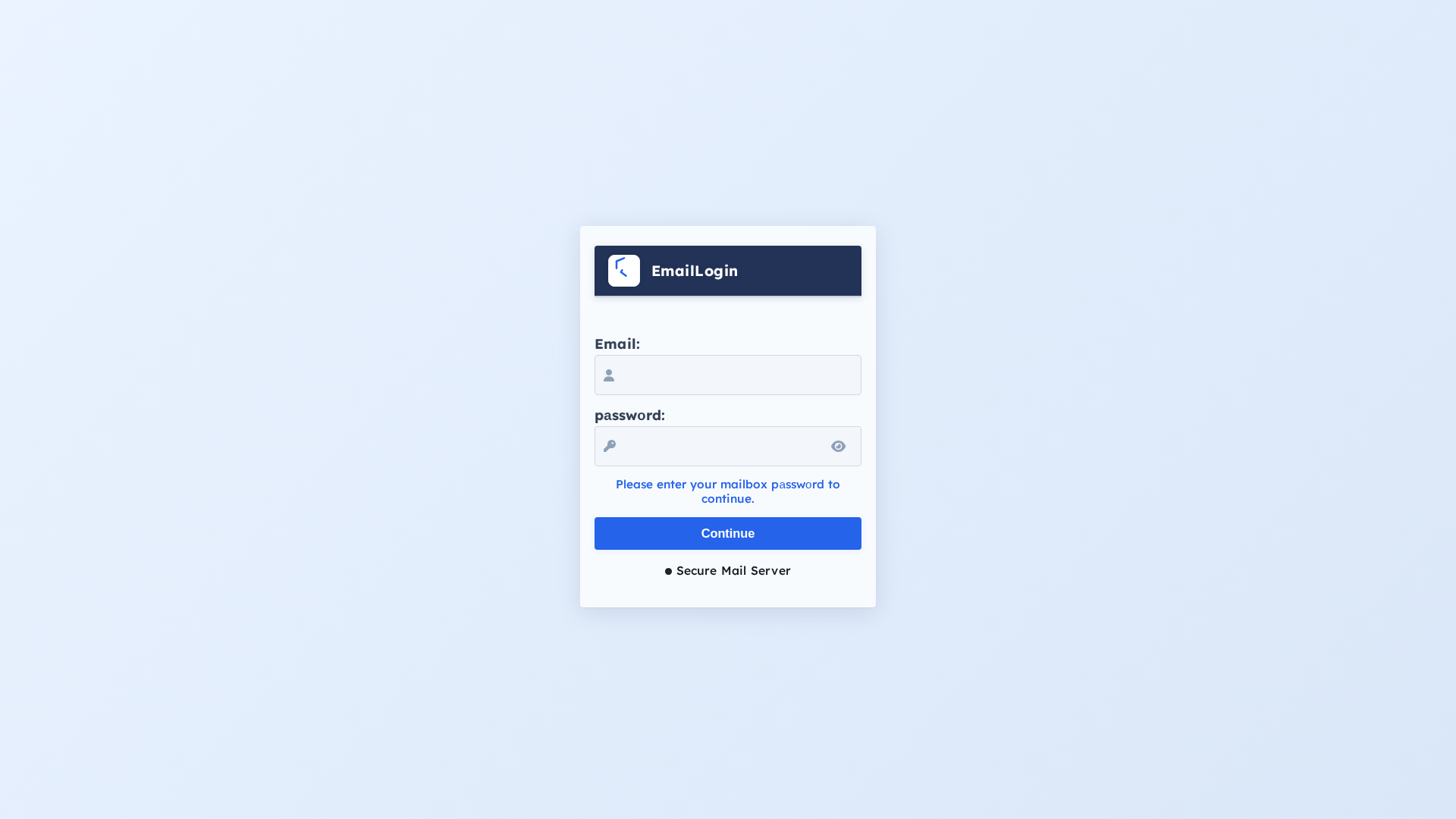
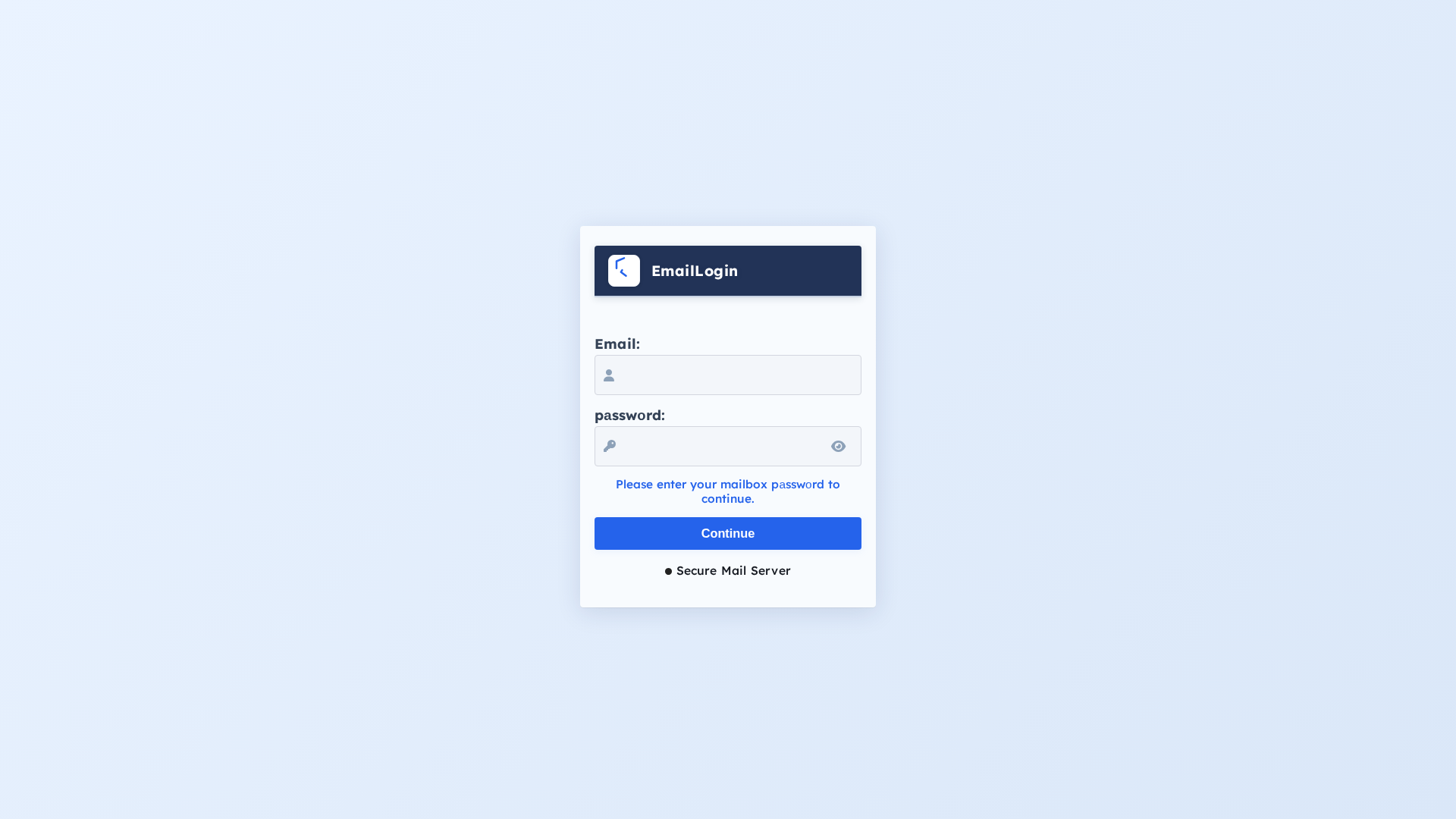
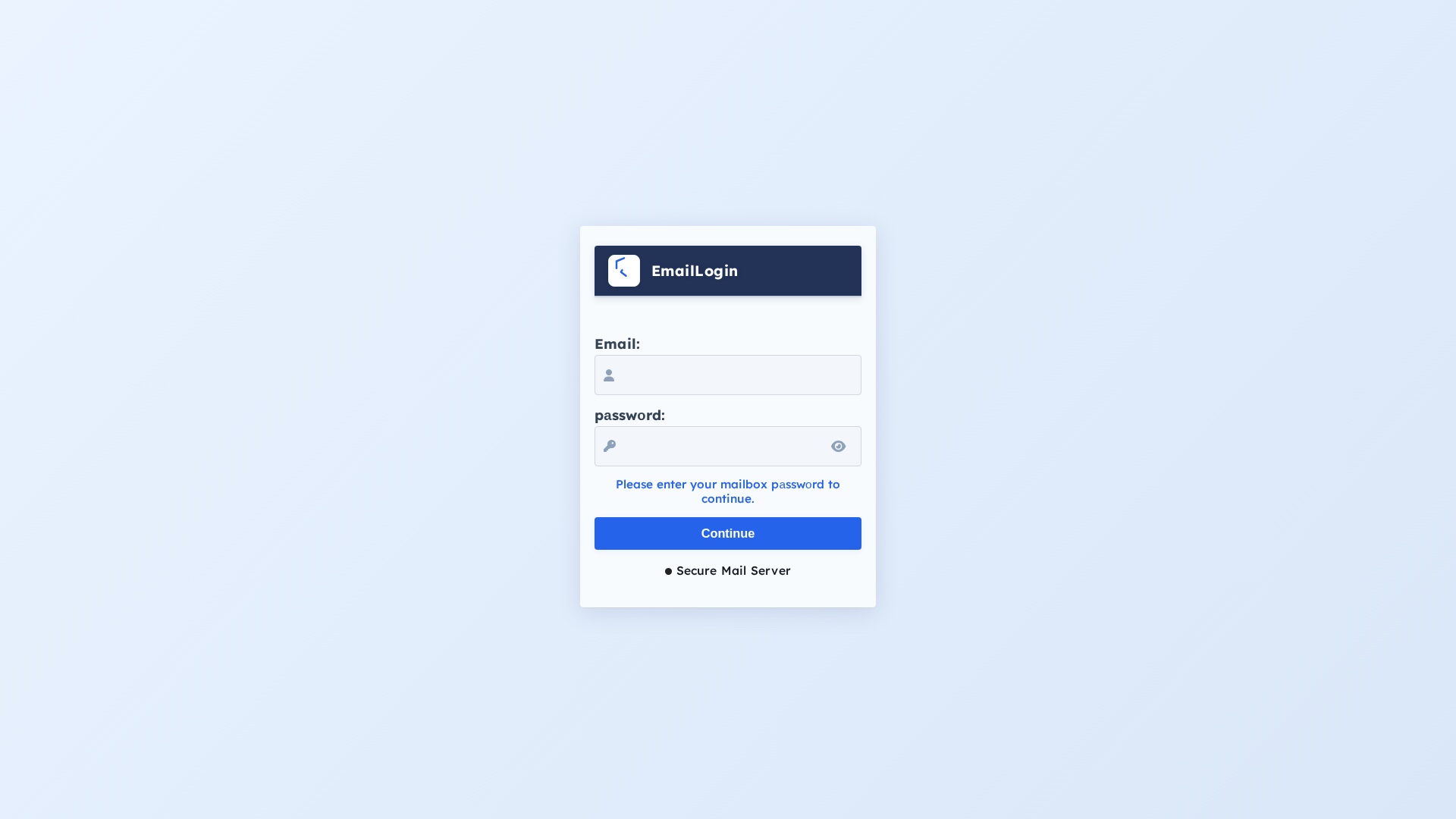
Captura Visual
No screenshot available
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13D414370A018AC671293C6D876E02B1F35D6C30ACF522B0163FC939D6BFAD09ED29094 |
|
CONTENT
ssdeep
|
24:nKCCcASZcmDGguDfEaQybnKn/9P6uCzRQ6yoFkNHziXKHVJFg4uB/eDzLwkxHi0C:nKWhcqGgC9bKVPTkFkBOK13DHHWN |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a6989999266666 |
|
VISUAL
aHash
|
ffffe6feece4f8f0 |
|
VISUAL
dHash
|
00304c10084c3000 |
|
VISUAL
wHash
|
fcf8e0f8f8e0e0c0 |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
00304c10084c3000,00202804242428c0 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários de email
• Método: Imitação de uma página de login
• Exfil: Desconhecido, provavelmente para um servidor controlado pelo atacante. A ofuscação detectada sugere que isso pode envolver JavaScript.
• Indicadores: Domínio IPFS, formulário para e-mail e senha, ofuscação de Javascript.
• Risco: ALTO
🔒 Obfuscation Detected
- atob
📡 API Calls Detected
- POST
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 3 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
This is a credential harvesting attack. The attacker is attempting to steal login credentials (email and password) by presenting a fake login form that looks similar to an email service. When the victim enters their credentials, the attacker collects them.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for bafkreietmq2owe4mmr4olp44ogax3zu5zxvomkq5cawnxu5vivaa7tzabq.ipfs.dweb.link
Found 1 other scan for this domain
