Phishing Analysis
Detailed analysis of captured phishing page
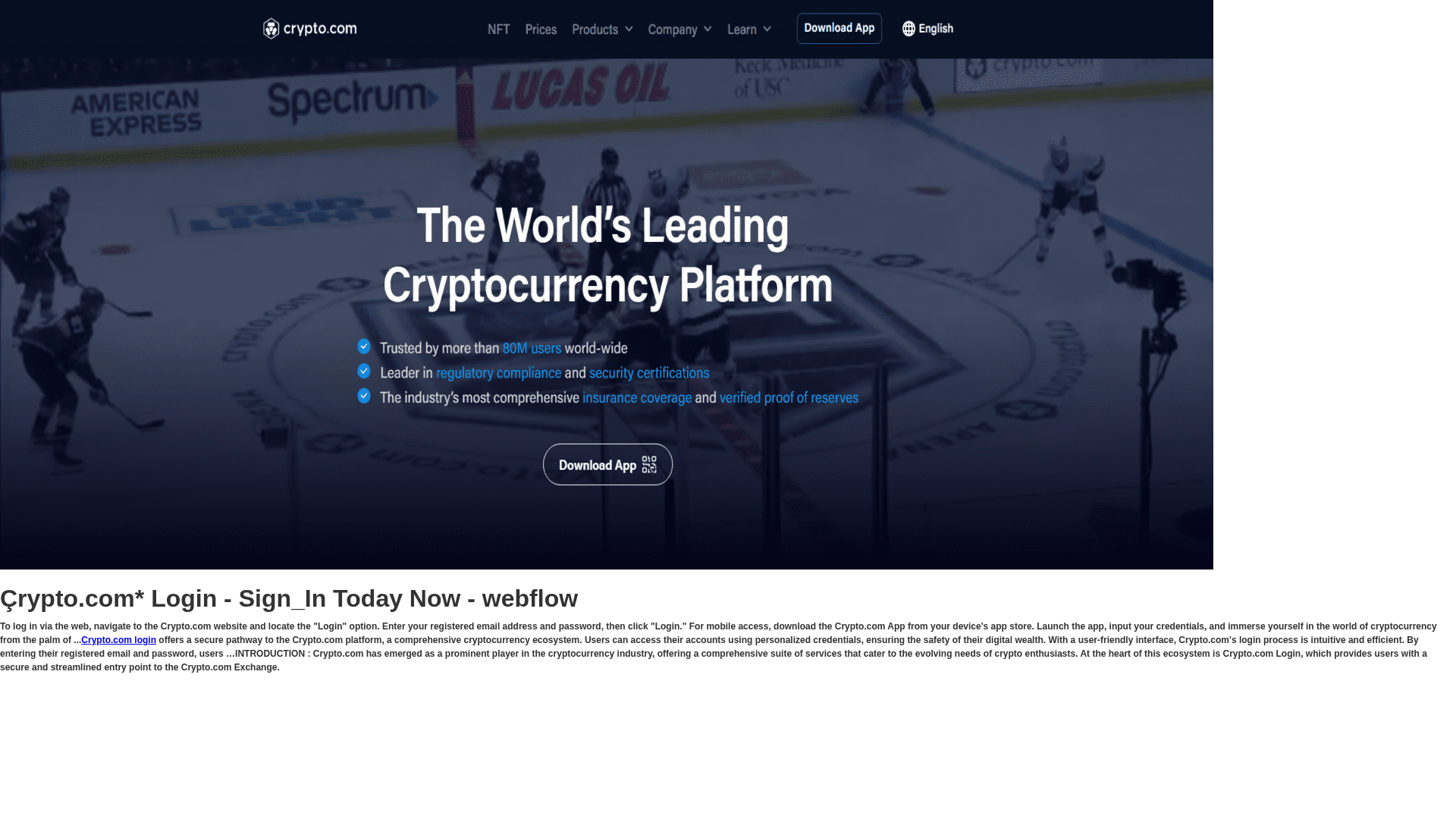
Captura Visual
Informações de Detecção
http://crrprorylotlogi.webflow.io/
Detected Brand
Unknown
Country
International
Confidence
100%
HTTP Status
200
Report ID
0de1b8aa-3df…
Analyzed
2026-02-14 23:58
Final URL (after redirects)
https://crrprorylotlogi.webflow.io/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C7E1855BD188722843E342B0B57E61CFAF5A01EC56A0DF69E9749A0C53F9B3D47321CA |
|
CONTENT
ssdeep
|
192:7WvaTPrpgcatqx2Kko2OrssXyTTsYX20Y:T7rpgcatqfko2L2yV2P |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ab29d42b2bd6290f |
|
VISUAL
aHash
|
010301010103ffff |
|
VISUAL
dHash
|
fbd3f3cbab3bc07b |
|
VISUAL
wHash
|
0303030301bfffff |
|
VISUAL
colorHash
|
0b007000000 |
|
VISUAL
cropResistant
|
fbd3f3cbab3bc07b,dcdac9a8eac6b642 |
Análise de Código
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do crypto.com
• Método: Personificação através de um site semelhante.
• Exfil: Potencialmente credenciais de login se houvesse um formulário
• Indicadores: Hospedagem gratuita, logotipo da marca.
• Risco: ALTO
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- https://crrprorylotlogi.webflow.io/
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Free Hosting
The use of free hosting (webflow.io) is a strong indicator of phishing.
Brand Impersonation
The site attempts to mimic the crypto.com brand and content.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
General public
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 4 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
crypto.com
Official Website
https://crypto.com
Fake Service
crypto.com platform
⚔️ Metodologia de Ataque
Primary Method: Brand Impersonation
The attackers are attempting to mimic the crypto.com website to trick users into providing their login credentials or other sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
crrprorylotlogi.webflow.io
Registered
None
Registrar
None
Status
None
🔬 JavaScript Deep Analysis
Sophistication Level
Basic
Total Code Size
36,5 KB
🔗 API Endpoints Detected
Other
4
Backend API
1
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.