
Phishing Analysis
Detailed analysis of captured phishing page
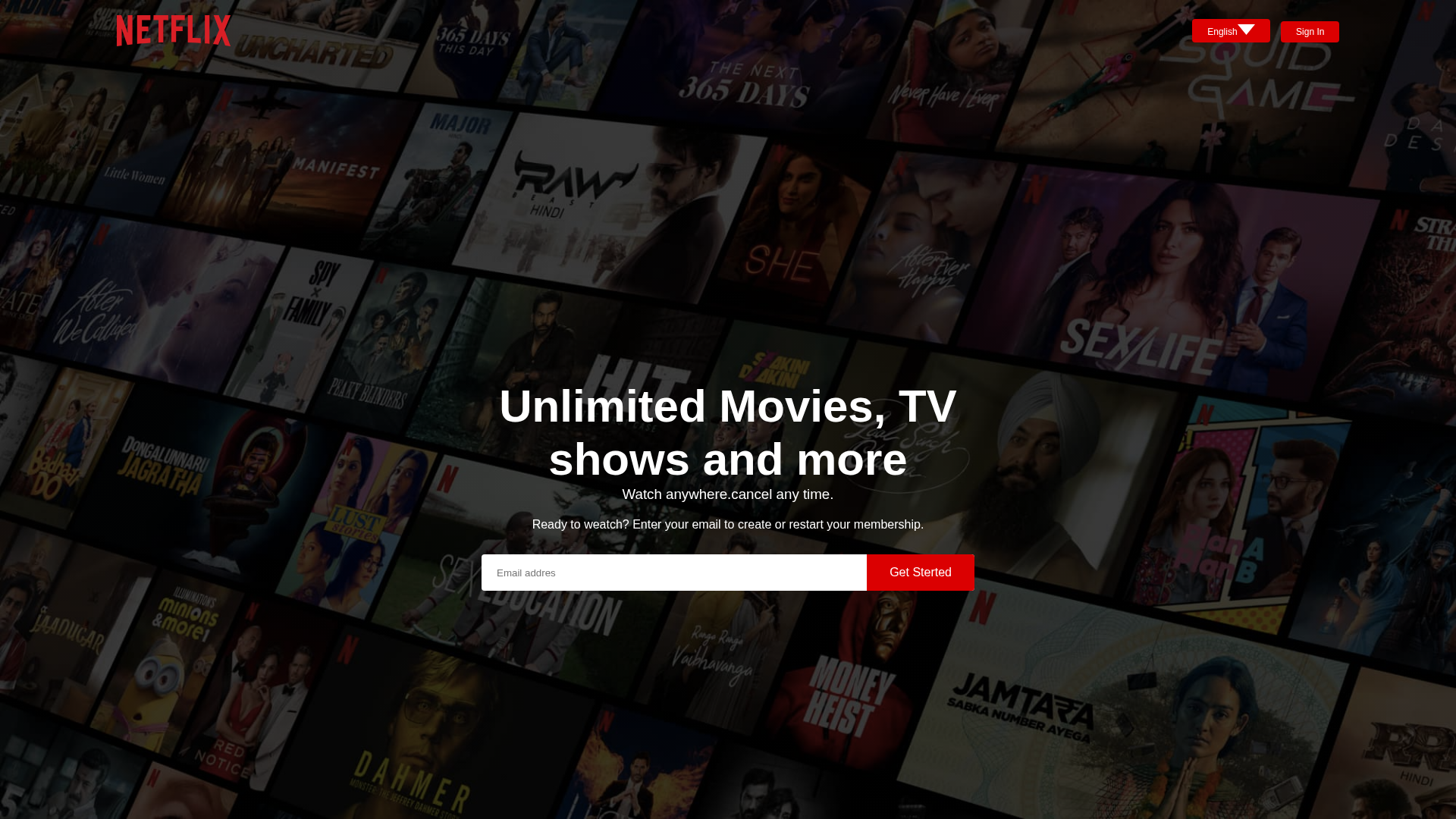
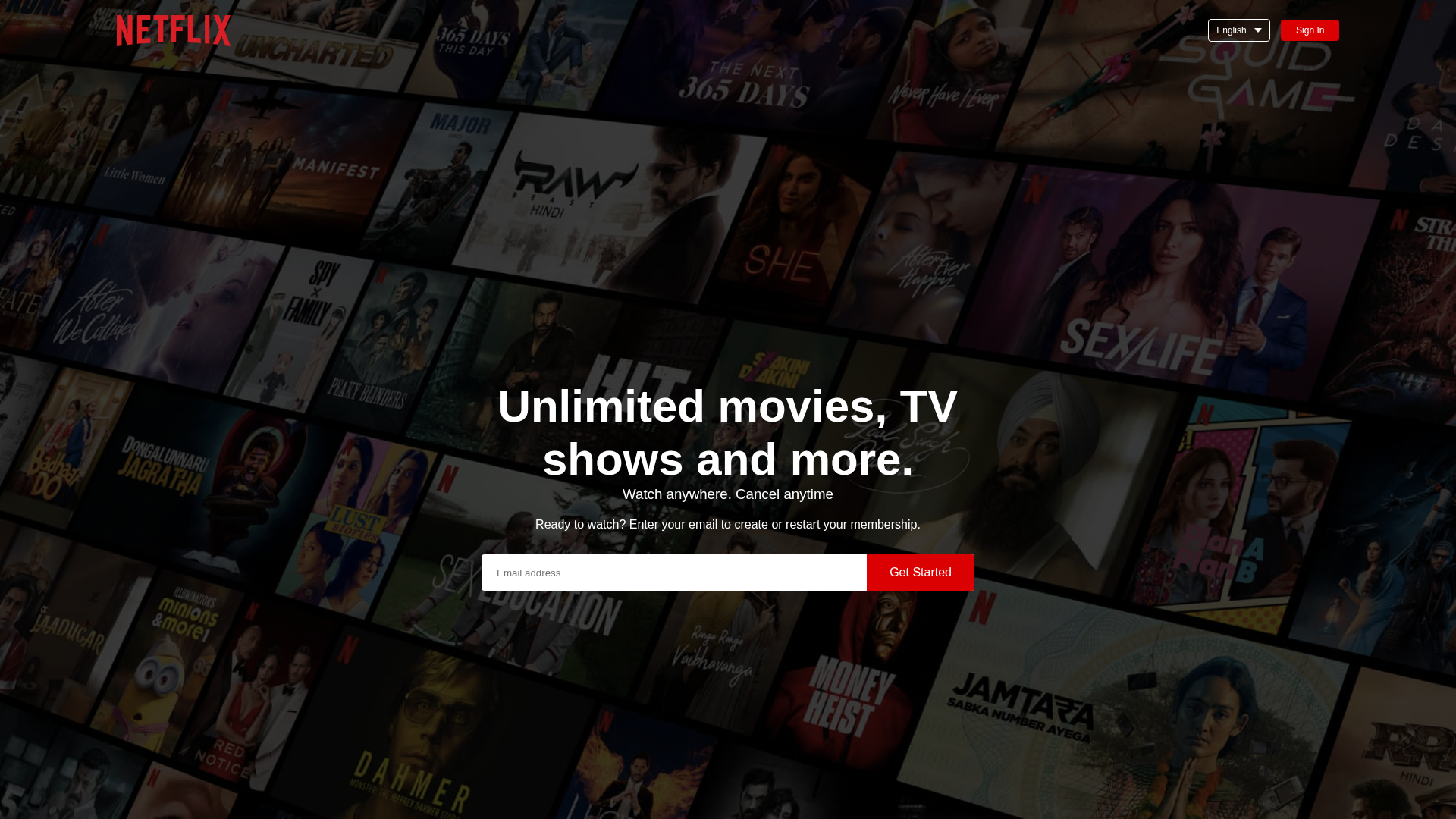
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1EDC184B0A0445AAF159346E4BF697A8AF706C274D7671B4410DCCB1EBE8DF1ECC892D1 |
|
CONTENT
ssdeep
|
96:it4V1KMXufnvVAhScPEqza99cPEqzIcPEqzNcPEqz0cPEqzUcPEqTsijoGEM+:iI1K3v3cPEVcPEZcPEMcPElcPEzcPEwQ |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6532cd7131cd33 |
|
VISUAL
aHash
|
423060d83c3c0705 |
|
VISUAL
dHash
|
8664aeb272602c0d |
|
VISUAL
wHash
|
c63070fe3e3c8707 |
|
VISUAL
colorHash
|
39e00000000 |
|
VISUAL
cropResistant
|
80c080c0d0800098,8664aeb272602c0d |
Análise de Código
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Netflix Credential Harvesting
Fake Netflix login page with 2 forms. Victim enters credentials which are captured and transmitted to attacker's server. Page may impersonate Netflix official login to appear legitimate.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for deepasureshadhiladhik-sketch.github.io
Found 2 other scans for this domain
