Phishing Analysis
Detailed analysis of captured phishing page
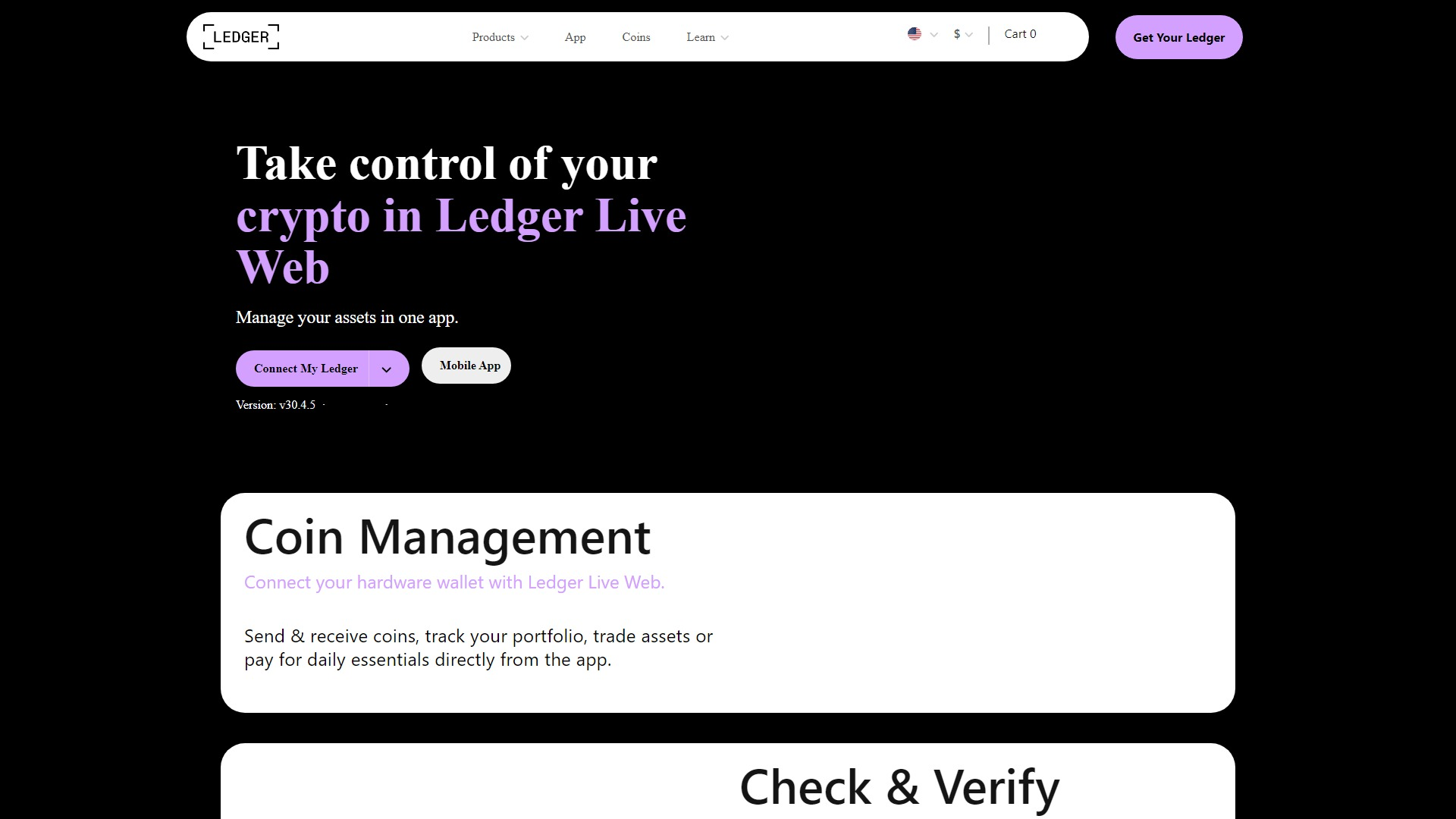
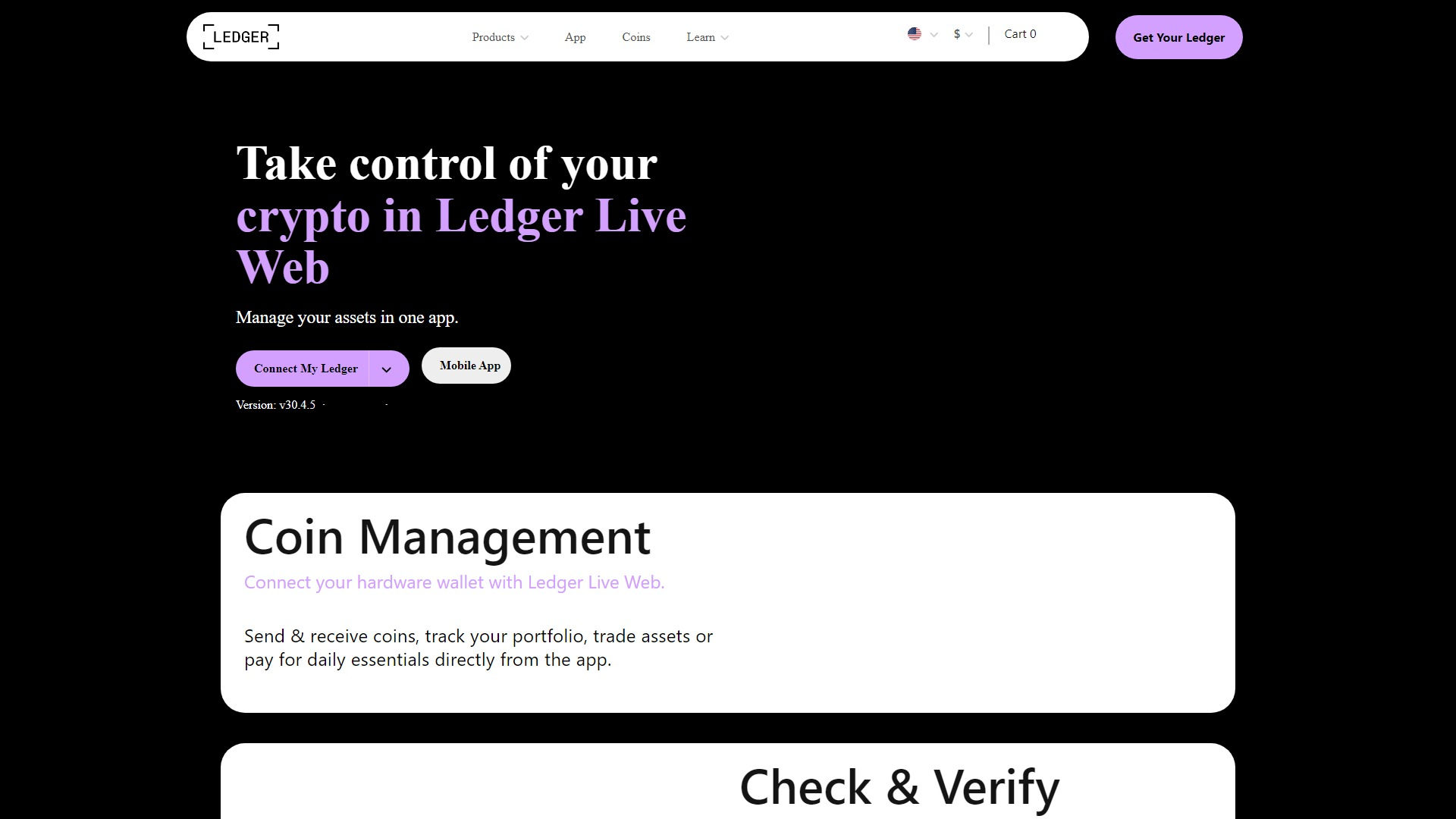
Captura Visual
Informações de Detecção
https://ldgeer-ledger.webflow.io/
Detected Brand
Ledger
Country
International
Confidence
95%
HTTP Status
200
Report ID
1aabbc7d-f62…
Analyzed
2026-03-04 00:11
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F7D1C827C544111E5F2702A8E69FB7FEC3E6405DB7A44CE968B8825E33D910A83F6DD1 |
|
CONTENT
ssdeep
|
192:+iIGPWw2gKatuaKy3/OYElsi66tKGrNu3:XWw2gKatuaKy3LECkt3u3 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c16bd4906bd1947e |
|
VISUAL
aHash
|
7c000000007e7e7e |
|
VISUAL
dHash
|
d8c0c0c0d0d0dcc4 |
|
VISUAL
wHash
|
7e0000607e7e7e7e |
|
VISUAL
colorHash
|
3a000e00000 |
|
VISUAL
cropResistant
|
a280c1899dccc0a2,c03030d098383080,a2808ba3a3a7a781,d8c0c0c0d0d0dcc4 |
Análise de Código
Risk Score
53/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários Ledger
• Método: Personificação via site falso.
• Exfil: Desconhecido, provavelmente colhendo credenciais de login ou outras informações sensíveis.
• Indicadores: Hospedagem gratuita (webflow.io) + logotipo Ledger.
• Risco: Alto
🔒 Obfuscation Detected
- fromCharCode
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Free Hosting
The site is hosted on a free platform (webflow.io), which is a common indicator of phishing.
Impersonation
The website attempts to mimic the Ledger website's appearance.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
Ledger users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Ledger
Official Website
https://www.ledger.com/
Fake Service
Ledger Live Web
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker likely aims to steal user credentials by mimicking the Ledger website and prompting users to enter their login information.
Secondary Method: Wallet connection
The attacker may redirect users to a fraudulent wallet connection to steal crypto assets.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
ldgeer-ledger.webflow.io
Registered
None
Registrar
None
Status
Inactive
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for ldgeer-ledger.webflow.io
Found 2 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.