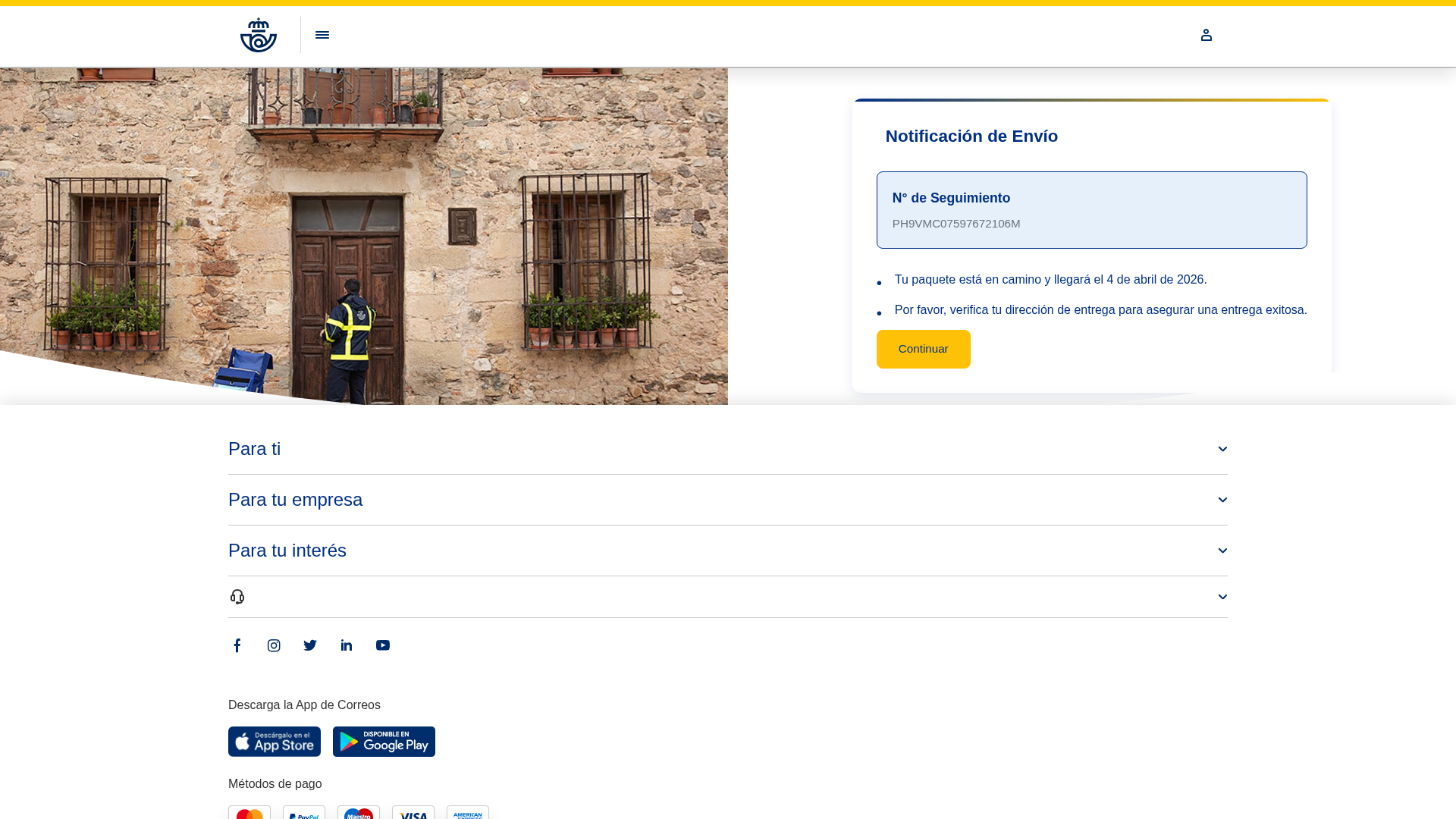
Phishing Analysis
Detailed analysis of captured phishing page
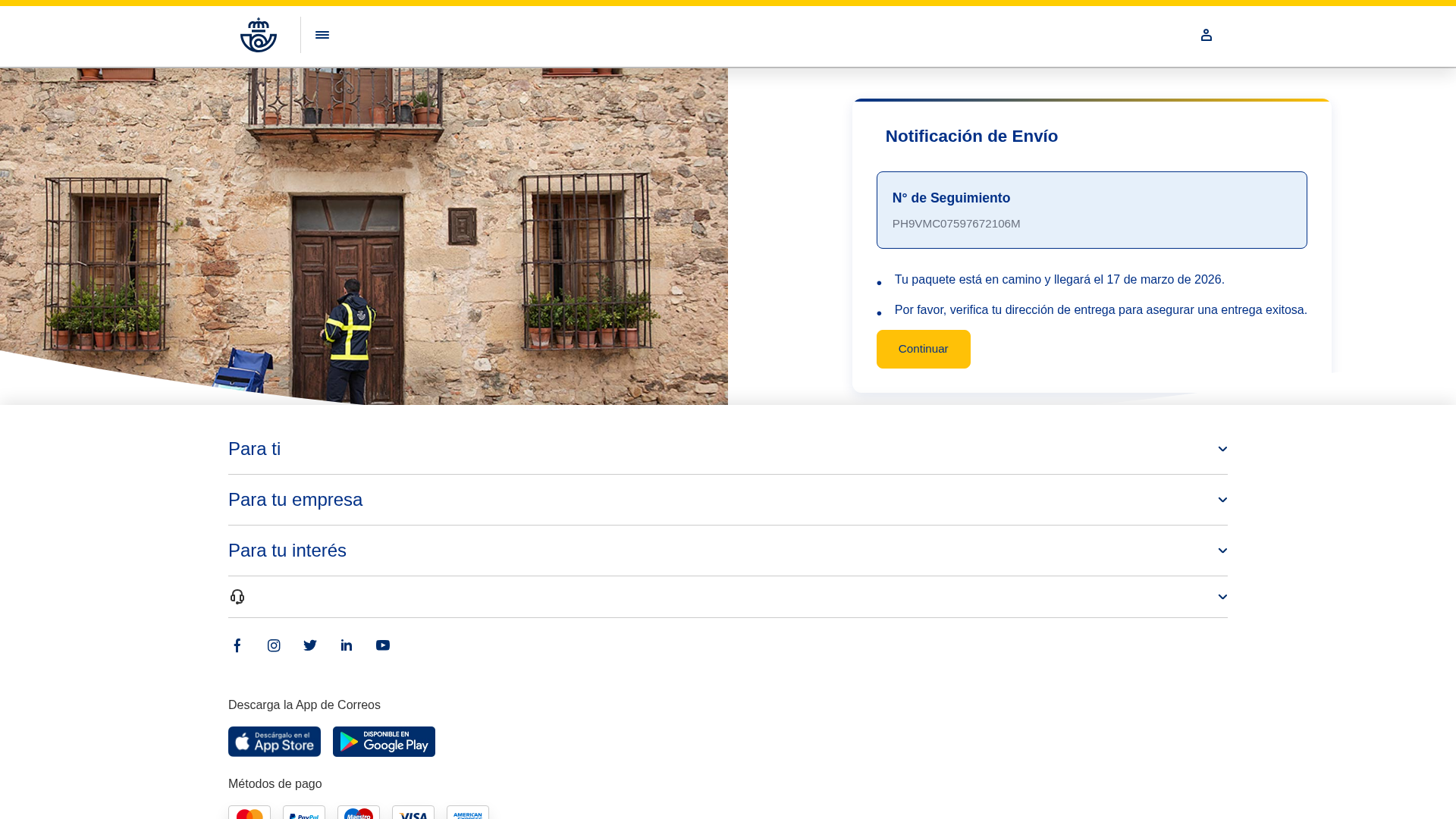
Captura Visual
No screenshot available
Informações de Detecção
http://vmi2945452.contaboserver.net/cc/co/corr/login.php
Detected Brand
Correos
Country
Spain
Confidence
99%
HTTP Status
200
Report ID
1bb3d993-3a0…
Analyzed
2025-12-23 13:17
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T143B3DB30C6F65D7BA47C7289EAC8E74151A7C3C3F3866BF6619491EE8A40D05CC43ADA |
|
CONTENT
ssdeep
|
1536:K7ONB8lG0XD48lG0XihUM689wGXsMvkYG:SE8lG0XD48lG0XihUM689wGXsMa |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bb39ccc6fe11c1c0 |
|
VISUAL
aHash
|
0f0f0f0fffffffbf |
|
VISUAL
dHash
|
3b3bdb3f28412820 |
|
VISUAL
wHash
|
00090901bfbfbf9f |
|
VISUAL
colorHash
|
07e00008000 |
|
VISUAL
cropResistant
|
3b3bdb3f28412820,9e9e9a9999321327,1f93b793232f6b0f,3736333733492b07,49cdcdcdcdcd4943 |
Análise de Código
Risk Score
70/100
Threat Level
ALTO
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
🔬 Threat Analysis Report
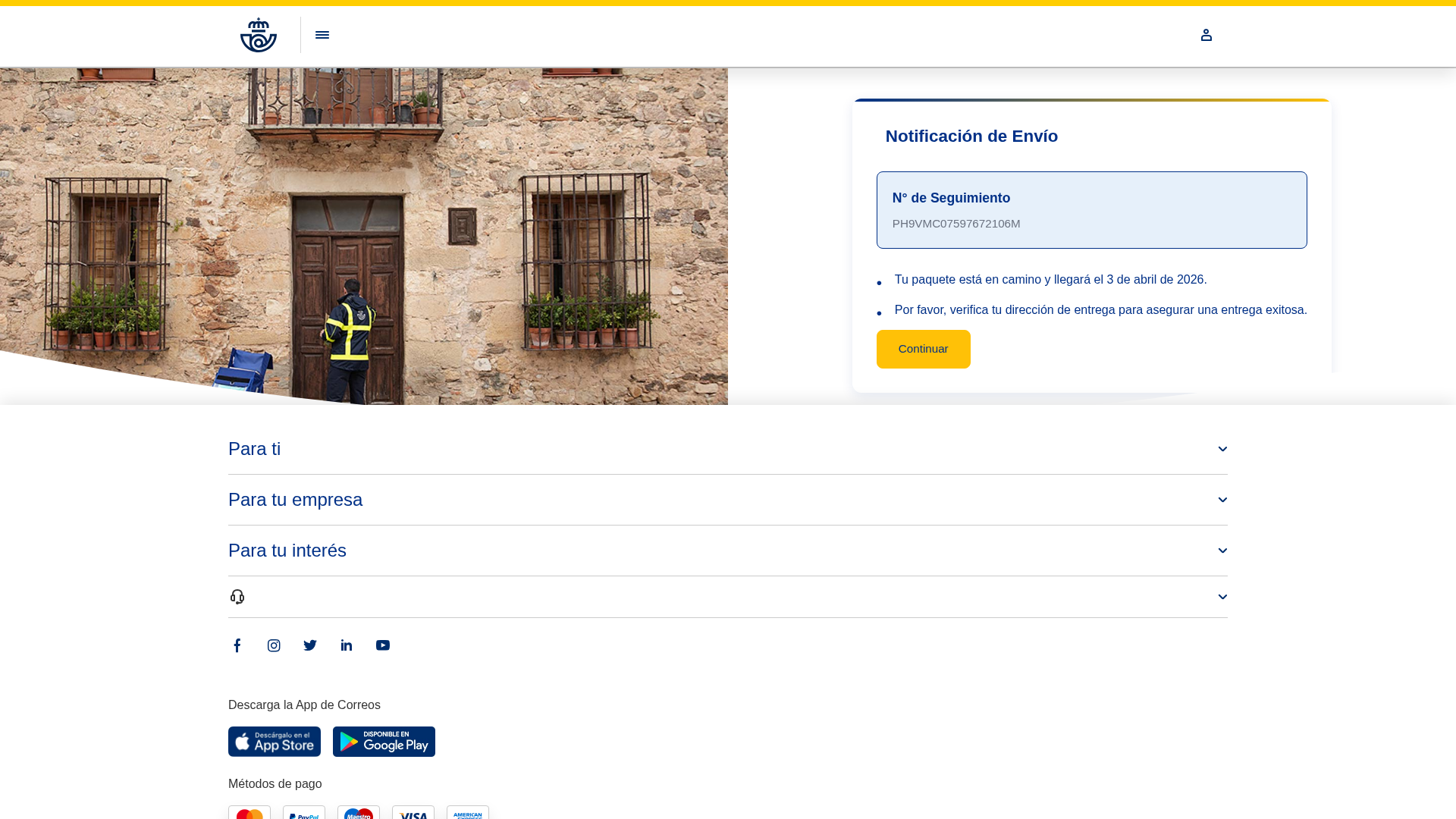
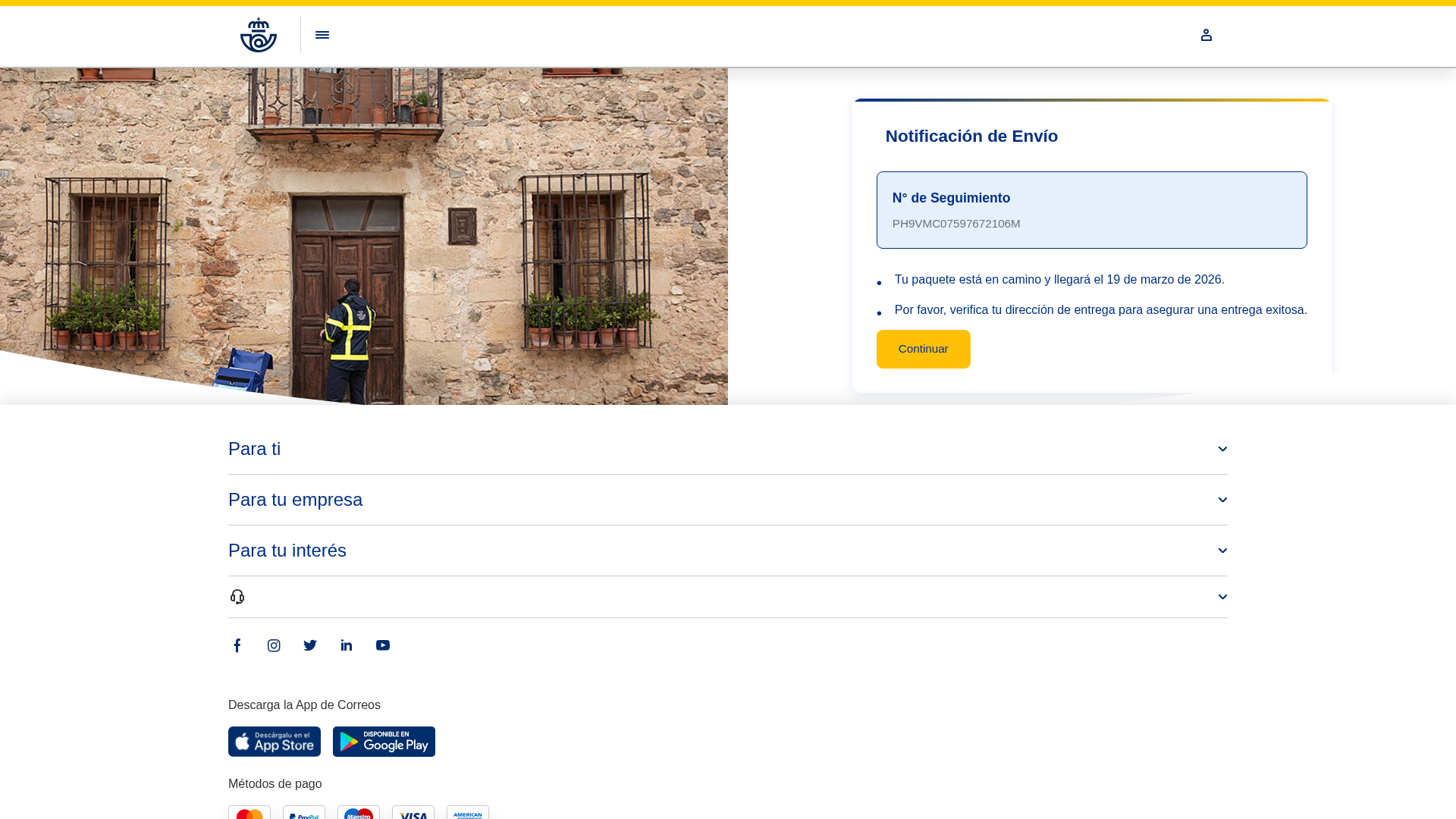
• Threat: Phishing targeting Correos (Spanish postal service) customers.
• Target: Correos customers, especially in Spain, expecting a package delivery.
• Method: The page imitates the Correos website, prompting users to enter their tracking number.
• Exfil: Likely to harvest entered information (tracking numbers, possibly more). The exfiltration point is unknown but the entered data will be stored on a fraudulent server.
• Indicators: The URL domain is not associated with Correos, using a generic server, which raises suspicions.
• Risk: HIGH - The attempt to steal package tracking details can lead to further phishing attacks.
🎯 Kit Endpoints
- data:image/x-icon;base64,AAABAAYAAAAAAAEAIABXKAAAZgAAAICAAAABACAAKAgBAL0oAABAQAAAAQAgAChCAADlMAEAMDAAAAEAIACoJQAADXMBACAgAAABACAAqBAAALWYAQAQEAAAAQAgAGgEAABdqQEAiVBORw0KGgoAAAANSUhEUgAAAQAAAAEACAYAAABccqhmAAAoHklEQVR42u3dZ2AU1d4G8Ge2pPdeSYeQBAgkoYSOQKSDIKBUxYLlXgR91YuoiOLVq1692AA7IiBID0rvIZAQIIGEhIQkpPfeN7v7foho6HN2N5ndzP/3jTAzObvZeXbmzDn/w6kToAYhRHw4GSRCt4EQIhwKAEJEjAKAEBGjACBExCgACBExCgBCRIwCgBARowAgRMQoAAgRMQoAQkSMAoAQEaMAIETEKAAIETEKAEJEjAKAEBGjACBExCgACBExCgBCRIwCgBARowAgRMQoAAgRMQoAQkSMAoAQEaMAIETEKAAIETEKAEJEjAKAEBGjACBExCgACBExCgBCRIwCgBARowAgRMQoAAgRMQoAQkSMAoAQEaMAIETEKAAIETEKAEJEjAKAEBGjACBExCgACBExCgBCRIwCgBARkwndANL5fooJxAf7wm752RuTzmPuoDShm0Y6GQWACFXUmyC10PaWn1XWGwvdLCIAugUgRMQoAAgRMQoAQkSM+gC6uDWH+uBSjsMtP0susLtju1/O9sDFG463/CzCpwTPjbos9EsgHYgCoIs7kuKBPZd8HrjduevOOHfd+Zaf1TfLKQC6OLoFIETEKAAIETEKAEJEjFMnQC10I0jHuVpgh4rbBvn8GheAzw/3vuVnL41NxIzwjFt+5mDZhB4ulUK/BNJROBl1AnZ1Pd0q7vhZXJbzHT/zdazG4IBCoZtLOhndAhAiYhQAhIgYBQAhIkZ9ACI0rHsBPpoVc8vPhtD9vyjRUwBCxIqT0S0AIWJGtwACKa01xZkMV1zKcUBGiTWKqsxR2ySHSs3B1KgVjpaN8HWsQYhHOSL9iuDnXAWOx3EVSgku3HBCXKYzUgpskVNuicoGYyhaJTA1UsLJqgF+jjXo7VmGAX5FqG4wRlyWM1Ly7XCj3AIV9SZoVkhhJFPB1rwJnnZ1CHarQH/fYvTzKoVMquL1+rLLrHAmwxWJufbILLFGSa0pGltkkHBqWJq0wNWmAf7O1QjtVopI/yI4WDQK/ScRJQqATlRSY4qNsYHYGueP+CwnqNR8Tuk2vo41mB5+HQuHXEXQbc/2VWoOh1M88XNMIKITvVDV0DHVfWzNmzGxTzbmR6ZiVFAeJNytd4+Zpdb48XRPbIv3u6Pi0P1IJWpE+JRgVv90zBmUBkdLCoPOQn0AneBGmSVWR0fg5zM90KSQanUsjgPGBOXizSnxGORXhJ/P9MCHv4chtdCmU19TT7dKvD4hAXMGpiEpzwHv7onAnos+UKr4h9rdmMqVmD84FcsnnUc3u9pOfU2iw8koADpSk0KG1XvD8fH+vlqf+HfjZtOAgiozQV+jl30tcissmK5m+DCVK/Hq+Av418TzMJYpBX2NXRYFQMe5nGePx9ZGITnfTvuDiVgvj3Jsee7AHbc9RAcoADrGjgQ/zP9mDOqbqYtFFyxNFNj47EFMDs0SuildCz0G1L3vTgVh5lcP08mvQ7VNckz/fDx+iukpdFO6HAoAHfrlbA8888NIrTvCyJ1aVRwWfT8KW+MChG5Kl0IBoCMxGa5Y9N0onXeGkb8pVRwWfDsa5zKdtT8YAUABoBPldSaY/dXDaG7VfU8/uVWTQopZXz2Myg4a6yA2FAA6sGTTMORVmgvdDNG4UW6JlzcPFboZXQL1VGnpRJo7NsV213h/F+sGRIXkIMy7FG42dZBK1CiuMUN8lhO+Oxmk8XHNjFoxOjgXg/yK4O1Qg42xPbAv0ZvXvpNDs/DYwHRklVkhNsMFR1I80NCi2UeFA/D0iGSEeZXCyaoBShWH/EoLJNxwwoHL3VBcY6rRcX+MCcRTw5MR6U+zGLVBAaClf/02SKPnqMHuFXhnahym9M28x/j6EI0CwN6iCf+akICnhifD2rTlr5/HZLjyPoavUw1mD7j217+rGoyx/kQwPtgXxryIqBrAAN9iPDk05Y7/Uygl2Jngh5W7+uMqw9BhAFCr2977E6/vYH6PyN/oFkALJ9LcEZvhwrQPxwHLJybg4jtbMD08464nf6tKgg9/78fcnvG9byDl/V/w8sMXbzn5tWVj1oxXx11AyupfEBWSy7z/B/vC7vpkRC5VYWb/dFxatQWvjb8AjrH/9GSaG84wBBu5EwWAFtYeC2HaXipR48dFh7F6eizk95lVty/RG1mlVkzHXjTsKvYsiYZTB06kcbFuwL6le7FgcCrTfunF1jhwxeue/28kU+KDR89g/cJjd0wwehDWvwG5FQWAhuqa5dh98cFLbrX37xmxmM/j5NkQE8h03Al9bmDdgqOQSjp+UKdUosK3Tx5lvhLYENPjgds8NSwZ7z5yjum4OxN8Ne6fIBQAGjuS7IlGhg/eqJ75eOXhiw/crlEhw/7L3Xgf18GiCT8sOtwpJ/9NMokKPz51CLbmzbz3+T3Jm9dj0tcnJGBY9wLex61rluN4qkenvfauhgJAQ8fT3Hlvy3HAJ7NPg+NxeXsmw5XpG235xARB5s+7WDfg9fEXeG9f2yRHHI8BPBJOjY9nx/A44t+Op/L/W5BbUQBoKCHbife2w3vkI7RbKa9t467zH+VmbtyKRcOTBXsPnhlxBaZy/lN1z2Xy6zCN8CnGYP8i3sdl+VuQW1EAaCiNoQDHI2GZvLdNKeA/fXhMcC6sTHTX28/KxqwZI3vm8X9t+fwf9T0Sfp33tmlFNoK9B4aOAkADTQopyupMeG8/0I//t1lOhUWHHLejDGL4ps6tsOyQ11ZcbQqFkj7KmqB3TQM1TUZMk368HWp4b1vFMNCG5bgdxduefxtYxu+zvLZWlQT1zXKh3wqDRAGggVbGbxsThvvk5lb+xzY1ahX6rYCZMf82tCr5hybra2theN/I3+hdI0TEKAAIETEKAEJEjAKAEBGjACBExCgACBExCgBCRIwCgBARowAgRMQoAAgRMSqlogEr0xb8e0Ys7+1ZVrd9+eFLKOc50ainayXv404OzYK7TT2vbSN8SngfN9i9nPd74WTFv26BqbyV6T22MFHw3pb8jRYHJUSsaHFQQsSNAoAQEaMAIETEKAAIETEKAEJEjAKAEBGjcQACKa4xY17+q6vydaxmGiNAdIcCQCC7Lvhi8U8jhG6GXvj2iaNYNCxF+wMRZnQLQIiIUQAQImIUAISIGAUAISJGAUCIiFEAECJiFACEiBgFACEiRgFAiIjRSECBWBgr0M2uTuhm6AVzYyrnJRQqCUaIWFFJMELEjQKAEBGjACBExCgACBExCgBCRIwCgBARowAgRMT0diBQfbMcfd+eDXTRYQqPRmRg9fSzHfo76prkuJJvj9RCW2SWWiO3wgIlNaaorDdGfbMcCqUE4AC5VAVzYwVszZrhbNUID7ta+DrWINC1EiHu5Qa77t7OC754bWukoG3gOCBx1RaYyFuFfjvuSm8DQK0G0outhW5GhymuMdP5MUtrTXE4xRPHr7ojJsMVqYW2UKo4rY4plagR6FqJSP8ijAzMw+jgXDhaGkYBz4o6E6QX2wjaBo4D9PlLTG8DQCZVgePagoDcW1G1GbbGBWDbeX/EZrhofcLfTqnikJxvh+R8O3xzIghSiRoD/YrwaMR1zOyfDldrfisOC6FJIfzHm4MaMqn+foiFf4fuwUimgoRTQ6nW7Qe6K1CrORxM9sTXR3thX5IXWpWd15WjVHGISXdFTLorXvl1MMb3ysZzo65gbEgOJJx+fdBrm+RCNwFyqQoyiUroZtyT3gaAhFPD1KgVdXrwR9QXrSoJtpwLwIf7wnAl307o5qBVyWHPJR/sueSDILdKvDY+AY8PvAaZVD8+8BX1JkI3AebG+nnvf5NePwWwMmkRugl6QQ1gR4Ifeq14DPPWj9GLk/92KQW2WPDtaASveBzb4v314tatpMZU6CbA0lS/P8N6ewUAALbmzSioMhe6GYJKzrfHixuH4Xiqu9BN4eVakQ1mfvUwhnYvxBfzTqC3R5lgbcmvtBD67YCtWbPQTbgvvb4CsLdoEroJgmlpleLtXQPQb+Usgzn52zt1zRXhK2fije2D0NwqFaQN2eWWQr8NcNDzz7BeXwE4i3S9uLRCWzy+biwu3HAUuilaUSgleD86DPsSvbFp8QEEuVV02u9uUUqQUyZ8ADhZNQjdhPvS6ysAVxv9fcTUUbac647wVTMN/uRvLzHXHv1XzcTG2B6d9jszim3Q0olPR+7F1YYCQGMetuIpmaVSc3h9WyQeXzu2Sz75qG+WYd76MXhlyxCdj1W4m6Rce6FfMgD9/wzr9S2Al0MN7205Dvhj2R4Yy5SCtXfd8RBsORfAvF+TQor534zFtng/nbeJA+BpV4fenmXo7lKFbva1cLJqhLVpM0zkyr9+f3WjMYprzJBTZolrxTZIyrVHXoWFzsewfXIgFJmlVvhl8UGYduDw2As3nHhv28OlCmsXHOO9/cTPJqG+md+pw/IZFoJeB4CfI/83T61uS9tg9867z7zd70lezPvUN8sxdc0EHE7x0Fk7HC0bMTE0G1EhORjWvUDjW6mCKnOcTHPHgSvdEJ3ojbJa3TxX33nBF+P/Owl7l0R32DyDs9ddeG8b4VOMEYH5vLYtrTXlffIDbJ9hIeh1APg7V4ED/5HUyQX2ggYAq/oWOSZ+NlEnvfxGUhWmhmXiyaEpeCgoTyejz9xs6jF7wDXMHnANrUoJDqV44vtTQdh9wadtIpEWjqe6Y/ynk/H7sj2w0HFV4EaFDPFZ/K8A+nmX8t42pYD/GAwJB/g5Vev0temaXgeAtWkLXG3qeY8FSMq1x8yIdKGbzUtLqxTTPx+n9clvYazA4lFX8NKYRLh34P2mTKrCuF43MK7XDeRVWODTg6FYdzyE6dvwdqeuuWLamgmIXrpXp7duZzJc0KTg/+ixv08x720v5/HvW/C0q9X7kud63QkIgOkb3ZB6zrecC8CBK9003l8qUWPxyCvI+M/P+GhmTIee/LfzsKvDJ7NPI/3Dn/HMiGRIJZr3FBxO8cAT342GWodzPg5c5n8rZiJXMl0BsHzGDOFqVO8DoLdnOe9tE7Kc9GIIKh/aXEKHeZci7q2t+Hr+cTgL+JzZ1boe6xYcw9k3t6FvN81H/G0+G4BVeyJ01q7oRG/e2/b3LWbqjDzPcGvR21O4UZB86X0A9PXin84ltabIKLERuskdRipR483J8YhdsQ39GN6XjhbuXYKzb23F8okJGs8IXLU7AtGJPlq35WqBHa4W2PLeflTPPN7bVjcaMfUB9PWiANBahHcJ0/an012FbnKHcLBowv6X92DVtHOQ68lsu/aMpCqsnh6L35fthZ05+/h3lZrDwm8fQm6FduP3f41jewwbFZLDe9uz112ZxjBEePPvWxCK3geAv3MV05yAEwY4bv5BurtUIfbNbRgdlCt0Ux4oKiQHZ9/cBn9n9t7v8joTLPx2NFQa9geo1Rw2xnbnvb2zVSMiGDoAj6e6MRy7Ad56PgYAMIAAkHBqDPIr4r39kRRPg+kH4KNvtzKcWr4d/nr+OKm9AOcqnF6+HX0Y+m9uOnrVA+uOh2j0e4+nueN6Cf8ycpNCs5g6MI+kePLeNtK/6M9yYPpN7wMAAIb2KOC9bV6lOZLz9WMYqLb6eJbj8Ku74GQgNfjac7ZqwOFXd6KXB3tP+L+2DUKhBtPA1x5jC44ZERm8ty2tNWV6AsDymRWSXo8DuGkkz1FaN+1L8kaIB/u3jz7xcazB/pf3wM5cN9NJmxVSXMxxRFKePTJLrFFSa4r65rY5B+bGCjhZNsLHsQa9PMrR16tUJ8N02/otdmPw6hnIZpiZV91ohNe3ReKnpw/x3ie3whI7E3x5b+9k1YiHGDoA91/2Yrr/HxnI/9hCMogA6OdVAjuLJlTU8RuKuvuiD14bnyB0szVmZdqCvUui4aJlwc2aJiP8Fu+P387740SqGxpa+P25TeRKDOleiOlhbYU/tQkhN5t67FkSjcGrZzDV6NsY2x1Lxiainxe/TuDPDvZherTKWrpsz0X+TyicrBqZHl8LySBuAaQSNcYE8U/Uc9ed9aIajCY4AN8/eVSrQSQFVeZYunkoPJY+gUXfj8IfSd14n/xA2+Sgw8keeG7DcHgsW4hnfxyJzFIrjdvTy6Mc3z5xlGkflZrDih0DeG1bVmeK9SeCmY7/xNCrvLdtaJFhP8PgorHBuXpXIPVeDCIAAGB8n2ze26rUHLbF+wvdZI08OzIZ08P535u216yQYtXu/gh4bR4+O9hHJ1VxG1tkWH8iGD2Xz8XLW4agtslIo+PM7J+Op4anMO2zP8kL8VnOD9zuo9/7MU2hjvQvYipVti/RG3UMQ55ZPqtCM5wA6J0NGUOP7aaz/B8H6Qsfh1p8NPO0Rvsm5Tog/J1ZeHtXf6Zve75aWiX474FQ9H7zMZxO5/84rL3/zj4NL3v+Q5bVAD76o+99t8mrtMAXR3oxtePFh5KYtt90ln8hE6M/50wYCoMJAAeLJqae1fNZTkyjtvTBmrknNZoe+2tcAAa9N6NTqgVnl1li1IdT8eWR3sz7Wpq04H9zTjLts/OC330HB63YPpAp8Dzt6ph7/1mmeY/omQ8bPS8E2p7BBAAAPMpwaawG8P2pIKGbzFtUSA4m9sli3u/zw33w+NqoDvnWvxeFUoIXNw7Dih2DmPed0jcTo4P59+e0Krl7/h1jr7vg5zNsZcaWRl1iGkn5S2wPtLTyP00eZQgXfWBQATA9IoPpj7chJpBpWqhQOA54f0Ys835rj/XCkl+GQiVQf9PqvWF4Z3d/5v3enx4LljEyP8UE3jFbUKGU4PkNI5hGDTpZNeKZ4cm8t1erOabORSOZCo+EXWd+P4RkUAHgZNmIscH8h8OW1ppgazx7ia7ONqF3NvPknj8ue+HFjcMEX3bynV398fOZQKZ9InyKEdWL/xj8rFIrnMu8tTPwoz/64VKOA9Pv/b9xF5jm5x9NdWeaWDS+9w2djdvoLAYVAAAwf0gq0/ZrDvURuskPtCzqEtP2ORWWmLtubKcU13wQNYDFP41g7m9ZFnWRafsdCX/XS0zKdcCq3WzThz1s6/HCqMtM+6w5GMq0/fzBbJ9NfWBwATClbyYcLPmnbEK2I46l6q7enq4FulZhBMOoMTWAp74fhYp6Y6Gb/peGFhkWfjuaKZBGB+UhgGHC0L4/5/g3tsgwZ/1Y5sVGVj1yFqZG/Ec3phbaIjqRf+efi3UDJmjQhyM0gwsAY5kSCxiT9sN9YUI3+57mRaYyTRrZGheAQ8n8J6Xcztq0BZNDs7Fi0nmsmXMSa+acxBuTzmNSaDastCjQGZ/lhG9O8r9f5jg15kXy/zteLbBFXqUFlmwahit5bFcb4d6lzJ+Zj/7ox9S/sHDIVRjp4TTtBzGIocC3WzziCj490If3H+jgFU/EZTkz1X7rLCy9xgqlBG9sZ+95B4CerpVYPuk8ZoRn/FUO/HaNChm2xfvj/b3hSCuyYf4dq3b1x4LIVN7ftI9GZOCtnfxG+6kBPLdhBKIveTO1ScKpsWbuCaaRedllVkxPF6QSNZ4dwb9zUZ8Y3BUA0FYjYHxv/oMt1ABW7uL3QetMga5VCHCu4r391rgAXC9hG5Irlajx9pR4JL67GXMHpd3z5AcAU3kr5kemIundzXhj0nnm4ayF1WbYwNAhGOhayVQ3gPXkB4BnRqQwTScHgPf2hjPNK5gcmmUQc//vxiADAGh7nsvij6RuOHVNsxFsHeUhxgIfXx1lG/FmJFNh6/P7sXIqWxUhI5kS7z1yFpsWH2SuPsQ6JZdlRh4rD9t6fPDoGaZ90ops8VMM21MN1s+iPjHYABjZMw/hDNVcAeC1bZF6VSxkcEAh722vl1gjlmGxCwBYv/CYVs+lZ/VPx1fzTzDtcynHgemJAMt7wILjgPVPHIW1KduovDd+G4RWhm//gX5FGNrdMOb+343BBgAH4PUJbFN+YzNc9GpcQBjPqa4AsPeSD1N4zRl0DQsG85/xdi9PDUvGzP5so9tYqvL2Y6z5yNdzI68wj8k/ec0NOxhqCgDAvyYa7rRzwIADAACmhV1nrjjz6tbIvwphCMlEroSvE//7xmMMtQ5NjVrxn5kxOmvrx7NimBbuYKnLGOBcpfPe814e5fh4FtukKqWKw0u/sA2sCu1WhkkGNPPvbgw6ACScGm9NiWPaJ6fcEu9HhwvddHjZ1zIt38Wy1NXsAelw0+HS6p52tUxPKxIYSmcZSVXwsNPdoiaWJgpsfX4/0zN/APj6WC9cZBxZuHJqHDgDmfd/LwYdAADwSNh1hDH2BXy8v6/gdQPdbfmfoFUNxihiqJE3swMmpLAEQEm1GSob+A9UYnkv7ofjgO8XHUGgayXTfvmVFlixfSDTPgN8izE51PAG/tzO4ANAwqnx7xlsPb0trRI8/eNIQYfS2lvwL/SZV8l/mW4JBwzyZ3vsxUdkQCHvCTxqgKkik67Gz6+YFI8ZGhRTeeHn4ahuZCt08sGjZwz+2x/oAgEAAGOCczGOYVwA0NYh+CnjWG9dMjfmf4laxTDs196ikbnnmw8HiyZYM8xzr2K4AtDFApqzB6Rj5VS220GgbbrvboZ6fwAwuW8W7+XE9V2XCAAA+GRWDPMz6zd3DMQVhtVedUnKcP/PMijFgiFYWLGEloLnHPqKehOkFfGfcXc3IwIL8MOiw8wDl3IrLPGPX4Yx7WMsU+LjWbrrYBValwmAnm4V+MdotlJPTQop5qwfiyaFbkZEswSQUsX/rZfL+B+3rgOfcLAc21j+4KcGR696IPSt2UjI1nxV535epdj1z333HeF4N0oVh/nfjEYl46Sql6ISmUZv6rsuEwBAW6+sB+My2Um59li2ZYhOfj/Lh5DlZLI143+PXFZnzNQBx1dprSlqGvjfJzveZzGT2iYj/GPjcIz5aIpWawGGeFTgwMt7NLrleW9vBI4zLiPnZV+LNyfFa9xefdSlAsDSpAVr5p5i3u/royE6KSJqbdrCe9tynmscAICHXR3vGYNqNYczHbBAaky6K++OSJlUBU+72rv+344EP4S88Ti+ONJL4zUAgbZn/Uf+byccNFg16VCyJ97VYDnyL+ad1El/hT7pUgEAANP6XceMcPbhr8/+OApJuWzPgW/HUqcgv5L/Yz1r0xam5/pbO6Ak+laGVXcDXaruuBpKzHXA2I+nYPoX45Cj5QrAET4lOPraTjhZsZ/82WVWeHxdFPMToMcGpGtUs1HfdbkAAIAv5p1gOhkBoK5Zhqmfj0dpranGv9fNhv/tx41yS6Yx5xE+/IfMbo0LQJ6WJ1l72WVW2N6uIs+DRLYb359ebIN568cibOUsreoY3DQmOA9HXt0FB4YVo2+qa5Jj6poJKKvlf/UFtK0ivIaxmrGh6JIB4GzVgLXzjzPvl1VqhelfjEezhoVEvR1qeW/brJAig2El25EMs+aaFFK8/Ktu+jUAYNnmIUyVcccG5yIh2wmPrY1Cz+VzsDG2u07GXCwckoropXtgacL/VusmpYrDnHVRSMxle+rDoW1SlSa3GoagSwYAAEwPz8ATjPUDAeDUNVcs/E6zNeo97WphxjAENSGb//DeyaFZjJWD/LH+hGbLbLf35ZHe2HmBbYLMe3vDEf7OTGw5F6CTE18qUePDmbH4ftFhjecNLNk0DHs0qCfw9IhkTO6bqfVr0FddNgAAYM2cE+jhUsW835ZzAVi2mf0bVCpRo6cb/2GoMQyddd4ONRjCOHX2hZ+HM61qc7sNZwLx0qahzPuxVuu9H3uLJuxbGo1XxyUwlRJv7729EfiScfUgAAhyq8B/H9NspSZD0aUDwMJEgV81mBgCAP871Eejmvd8V7MFgMMpbMVKnx/FNs6hVclh3voxeG1bJNP6CI0KGV75dQgWfjsarQIOl470L8KFlb8iKkTzpba+ONIbb/FcZLQ9c+NWbH3+AMyNulav/+2kK5/FSqEb0ZFcrBvgZtPAPNwTAI6nuv+1VDZfZXVmvH9XRb0JHhuQzrvDMtCtCr/GBTA9QlSj7Upjy7keMDNuRXeXKhjdY2BRbZMcP50OwuNro5iWw9I1mVSNFZPP44dFR2Brrvmw5vUnQvDiz8Og1uDa4ftFRzCasWKTweEk4NQJgq8t0Sme3zACXzOWq7rp/Rln8a8J53ltm1lqDb9X5/E+9qpp5/DmZP6DS7af98OML8dp/D6YGbVicEAh+niWw8mqAQBQXGOGxBwHxGS4oLETlxi7m2D3Cnz/5BH099WugOu64yF4fsNwjfpy/jkmCf97vGv2+t+Ck4knAFqUUoz9eApOpGpWF/DNyeexatpZXtsGvDaPdw9/gHM10v69kWlm2fhPJ+EPAb+hO4KJXInXJyTg9QkJTMVH7ubTg6F4ecsQjcq/jQ7Kw+/L9jDPKzFInKxr9wG0ZyRVYvsLvzMtRtHeu3vC8eLG4bx6tSeGZvM+bnqxNQ6nsD0f/2bhMeZxDvpsUmg2Lr+3GW9PidPq5FcDWLFjIJZt1uzkD3Stwtbn94vj5P+TaAIAaOtRjl66V+OT58sjvTDzq3EPvExmLcT53wOhTNu729Zh07MHIDPwD2o/r1Ic+r/d2LMkGv5OVVodq0UpwZPfjcbqvZpVe3KyakT00r2wNbC1/bQlqgAAgO7OVdi7JJppamt7OxJ8MfLDaSisvvdQ3sEBhfCy5z8o6MDlbojLcua9PdBWA2HtguNMYwP0RS+PCmx9fj/i396qk462inoTjPtkCn48zVbO+yZLEwWiX4qGn6NmV4eGrMs/BbgbD7s69PMqxbZ4zQaq5Fda4Ne4AAztXnjXclYc1/ahPJnGf7ZZVqk18+KS/bxK4WLdgN+TvDTq6e5skf5FWDPnJD59/BRC3Ct0El5X8u0x+j9TmeoQtmciV2L3kn0GXdpbY2J6CnA328/747G1UVAoNfskmsiVWDPnJJ6+y5rzOeWW8Ht1PtNz9B3/+APT+rFPZNqR4IcF34zu0FoAmjKVKzEjIgMvPHQZA3x1W6ps87nueOaHkRq/brlUhW0v7MeULjzS777E9BTgXjaf647568doNeBl7qBr+Gr+8TvGqM/86mFsY5iZ52lXhyvvbYIVw7Tim1IK7DBn3VidjsLTFMcB/X2KMTcyDY8PvKazmn83NbbIsGzLUKw9xn8x0tvJpSpsWnxQoxqCXQYFQJtf4wIwb/0YptJbt/N3qsbPzxzCwHbr0J3PdkL/d2YyvcFPDr2K7548olEbWlql+GR/X7y/Lwx1TZ17NSCVqDHAtxhT+mVieth1+Dl1zP10Yq4D5q4biyv5bCsEt2ckU2HT4gOYrsWqSV0CBcDfdl/0xeyvo5iGzN5OJlHj1fEX8Fa7x1kTP5uEfQzrzAPA5sUHMXvANY3bUVxjhk/298X6E8GoZqjiw4JD26Iew3oUYFRQHsYE5XbojLlWpQT/+aMfVu2OQHOr5n8jU6NWbHt+PyYY+IIeOkEBcKujVz0w7fPxqGEsEX27YPcKrF94DJH+hbiU44Dwd2YxdTZaGCtw+o3t6ONZplU76pvl2J7gh+3x/jia6q7xVYGJXAlfx2oEuVWit2cZ+nmVIsK3GE6dNEX2wg1HPP3DKFzQsKPvJhuzFuz65z4M79E1KvpqjQLgThdzHDHx04koYFiI424knBpPDUvB6hln8drWSHx/qifT/t3s63Dmjd/gzljj8F5alBIk5Trgcq4DMkutUFxjhoZmGVRou3IxkSthbqSAtVkL7Cya4GzVADebenjZ18LNtp5pFSNdqW40xts7++PLI721npTkYVuHfUuj0VvLUO1SKADuLqfcEpM+m4gkHZQMtzdvxnOjLuOzQ32Yv4GD3Stw7LWd9y2w2RUpVRx+OB2EFdsHorhG8wpNN/XtVoY9L0UzF4zt8igA7q22yQhz143VqIiELoV4VODgK7vhaq27tf70lRrAvkQfLP9tIC7raL2GaWGZ2PD0IVh0sWKeOkEBcH8qNYeVuwZg9d4wrSrYasvXsQb7lu5lXvPOUKgBHLzSDe/s7o/YDBedHFPCqfH21HismBTPvGCIaFAA8BN9yQcLvh2NCsZFJHTJ1qwZG589hPG9s4V+O3RGqeKw84If/vN7P6bVjx/EwaIJG545hHG9NC8kIgoUAPxll1lhzrqxOKOjbyhNSDjglXEX8O60czDScsqskCrqTfDj6Z748kgvZJZa6fTYQ7sX4pdnD8BTh0uOd1kUAGxalRKs2hOBf0eHC1oqq7dHOdY/cUznQ2s7kkrN4WSaG344FYRt5/10XnhELlVhxeTzWD7xvCBPLAwSBYBmzl53wRPfjUZqoY1gbZBwaiwckopV087p7FGhrqkBXLrhiK3xAdhyLgDZZZYd8nuC3Crx41OHEeGjXRUh0aEA0Fxjiwxv7xqATw+ECno1YGrUiqeHpWBp1CV4O9QI/bagSSHDqWtu2Jfohb2XfHR+id+eXKrCKw9fxFtT4mEi77hVkbssCgDtXbzhiMUbRiAuk20+v67JJGpMDM3GE0NT8HBITqf1EdQ3y3E+2wmn011xItUdMemuaOiEuoKD/Irw9YLjWo+WFDUKAN1QqTl8ezIYK7YPRCnjslMdwda8GeN730BUSA6G9chHN/tarasFKFUc8iotkFZki5R8OyTm2uPiDUekFNhpNYmKlbNVI96fEYuFQ67S4z1tUQDoVmWDMVbvjcAXR3ppvLxYR3CxbkAvj3J0d6mCl30tnK0aYG3aAmO5EhynRqtSgpZWKRpaZKhrkqOywRjldSYorjFDQZU5cisskFNuqdVEKW2ZyJX455hELJ+YoNFy4OQuKAA6RlaZFVbuHIBfzupmTTwxk0rUmB+ZhrennmMqs0Z4oADoWFcL7PDunghsjfenIGAkk6gxa0A63pwcjx4uXXMEpOAoADrHtSIbfLS/Hzae6SHoZbQhMJW3Yv7gNLwy7gL8O6ioCPkTBUDnKqo2w9pjvbDueDCKqs2Ebo5ecbOpx7Mjk7F4xJW/ViwiHYwCQBgtrVLsvOCLb04E49hVd0EnGglJwqnxUFAenh6ejKn9MkW1IIdeoAAQXlaZFTae6YFNZ3sIOrKwM/V0q8ScgdcwNzKVOvaERAGgP9QAEnMc8dt5P+xM8EVKgeZFL/VRiHsFpoZlYkZ4Bg3e0RcUAPoro8QafyR548CVbjiR5tbpVX61ZWmiwPDAfESF5GB87xvwFeGqO3qPAsAwKJQSnM9yxslrbjiT4YK4TGe960R0tW7AAL9iRPoXYmj3AoR5l9A9vb6jADBMagB5FZa4eMMBSXkOSM63Q2qhLTJKrDv8SsHSRAF/p2oEulYi2L0cvT3L0derlOrtGSIKgK5FpeZQWmuK7DJL5FVYorDaDMXVZiirM0FVgzFqGo1Q3yxHo0IGRasEyj+fPkg5NeQyJUzlSpgbK2Bl2gJbs2bYW/5dHdjDtg5eDrVwtGykMfhdBQUAISLGycS3PDgh5G8UAISIGAUAISJGAUCIiFEAECJiFACEiBgFACEiRgFAiIhRABAiYhQAhIgYBQAhIkYBQIiIUQAQImIUAISIGAUAISJGAUCIiFEAECJiFACEiBgFACEiRgFAiIhRABAiYhQAhIgYBQAhIkYBQIiIUQAQImIUAISIGAUAISJGAUCIiFEAECJiFACEiBgFACEiRgFAiIhRABAiYhQAhIgYBQAhIkYBQIiIUQAQImIUAISIGAUAISJGAUCIiFEAECJiFACEiJgMnEzoNhBCBCHD/wOrxXQgqNu5/wAAAABJRU5ErkJggigAAACAAAAAAAEAAAEAIAAAAAAAAAABACMuAAAjLgAAAAAAAAAAAAACzf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//As3//wLN//8Czf//BM7//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8MvOT/H6C2/zCHjv8+cWz/SmBQ/1RSOf9bRyj/YEAd/2I9GP9iPRj/YEAd/1tHKP9UUjn/SmBQ/z5ybP8wh4//H6C3/wu95f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//D7bb/y2KlP9JYlT/YT4a/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2E+Gv9JY1T/LYuV/w+33P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8RtNj/N3x9/1tIKf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1pIKv83fX7/ELXZ/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wPJ+f8nlKT/U1M7/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgH/U1M8/yaVpf8Cyvn/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wTH9f8xho3/YT8b/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2A/HP8wh47/BMf1/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLK+/8ti5b/Yj0Y/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9qMgb/WUos/01dS/9GZlr/Rmdb/0hjVf9OW0j/Vk80/2E+Gv9rLwL/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9iPhn/LIyX/wLL+/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8bpsD/Wkks/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2M7Ff89c2//HKW//wPI9/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wTI9/8TsdH/J5Sj/z1zbv9XTTL/ay8C/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/WUot/xqnwf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8GxPH/Qm1l/2wvAf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2I+Gf8tjJb/A8j3/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Iwez/J5Sj/0phUf9pMwj/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC8B/0FuZv8GxfL/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//GanF/19CIP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAf9Bbmf/BsTx/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wfD7/8ti5X/Wkks/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/15DIf8Yqsb/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3+/zGFjP9qMQT/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9pMwn/Jpan/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf7/H6C3/1NUPP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2oxBf8wh47/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wPI9/9GZ1v/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9dRCT/azAD/2wuAP9sLgD/bC4A/2wuAP9sLgD/aDUL/xulv/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x+gt/9ZSi3/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9FaF3/A8n4/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Hw+7/UlQ9/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9oNQv/MYWL/zODiP9sLgD/bC4A/2wuAP9sLgD/bC4A/2swA/8gnrT/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHL/P8do7v/O3d0/05aRv9YTDD/WUou/1ZPNf9PWET/RmZb/zl5ef8pkZ//Fa7N/wLK+v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLL+/8viJD/ZzYN/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9SVT//B8Pv/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Cb/p/1hLL/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/U1M8/w+33P8GxfL/ZDoT/2wuAP9sLgD/bC4A/2wuAP9sLgD/NX+C/wDN//8Azf//AM3//wDN//8Azf//AM3//wHM/v8pkZ7/XkMh/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/aDQK/1BYQ/8yhIn/ELXZ/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Oud//UVZA/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9YTDH/CcDq/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wnA6v9aSSz/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/ay8C/zd8ff8By/z/AM3//zCHjv9sLgD/bC4A/2wuAP9sLgD/bC4A/1dOM/8Cy/v/AM3//wDN//8Azf//AM3//wDN//8JwOv/T1hE/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/V04z/y2LlP8GxPH/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8BzP3/NYCD/2swA/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9ZSi3/CMHr/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8GxPH/V00y/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2Y3Dv8hnrP/AM3//wDN//8Azf//XEYn/2wuAP9sLgD/bC4A/2wuAP9sLgD/GqfC/wDN//8Azf//AM3//wDN//8Azf//C77m/1xGJ/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2Y3Dv86eHb/CcDp/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HqG5/2U4EP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9WTjT/BsXy/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Asr6/09ZRf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9hPxv/FLDR/wDN//8Azf//AM3//xatzP9sLgD/bC4A/2wuAP9sLgD/bC4A/1FWQf8Azf//AM3//wDN//8Azf//AM3//wPJ+P9WTzX/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9nNg3/NX+C/wTH9v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//ErPW/19BH/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9OWkf/Asr7/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9Ab2j/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/XkMi/w653v8Azf//AM3//wDN//8Azf//Nn6A/2wuAP9sLgD/bC4A/2wuAP9sLgD/JZep/wDN//8Azf//AM3//wDN//8Azf//N3x9/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9kOhT/UVY//1FVP/9kOhP/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/XkMi/x2iu/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//DLvj/1xGJ/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8/cWv/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//KpCd/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/19CIP8NuuH/AM3//wDN//8Azf//AM3//wDN//9RVkH/bC4A/2wuAP9sLgD/bC4A/2g0Cf8Ex/X/AM3//wDN//8Azf//AM3//wq/6P9oNAn/bC4A/2wuAP9sLgD/bC4A/2wuAP9fQR7/I5qt/wHL/P8Azf//AM3//wHL/P8kmaz/YEAd/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC8B/z5ybf8DyPf/AM3//wDN//8Azf//AM3//wDN//8Azf//C73l/1xFJf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8okqD/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xKy1P9oNAr/bC4A/2wuAP9sLgD/bC4A/2wuAP9jPBb/ELba/wDN//8Azf//AM3//wDN//8Azf//AM3+/2Y3D/9sLgD/bC4A/2wuAP9sLgD/UFhD/wDN//8Azf//AM3//wDN//8Azf//M4KH/2wuAP9sLgD/bC4A/2wuAP9sLgD/XEcn/wq/6f8Azf//AM3//wDN//8Azf//AM3//wDN//8Kvuj/XEYm/2wuAP9sLgD/bC4A/2wuAP9sLgD/ZzUM/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1ZOM/8Nu+H/AM3//wDN//8Azf//AM3//wDN//8Azf//Dbrg/2E/G/9sLgD/bC4A/2wuAP9sLgD/bC4A/2g1C/8RtNb/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyfn/WEww/2wuAP9sLgD/bC4A/2wuAP9sLgD/aTMI/xiqx/8Azf//AM3//wDN//8Azf//AM3//wDN//8Kvuf/bC4A/2wuAP9sLgD/bC4A/2wuAP86eHb/AM3//wDN//8Azf//AM3//wDN//9UUTj/bC4A/2wuAP9sLgD/bC4A/2svAv8Vrs7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Wrcv/ay8C/2wuAP9sLgD/bC4A/2wuAP9PWUX/F6vJ/0tfTv9sLgH/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2I9GP8Wrcz/AM3//wDN//8Azf//AM3//wDN//8Azf//Fa/P/2c1DP9sLgD/bC4A/2wuAP9sLgD/bC4A/1dNMv8Cyvr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zZ+gP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8okqD/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xWuzf9sLgD/bC4A/2wuAP9sLgD/bC4A/yuOmf8Azf//AM3//wDN//8Azf//Asv7/2kyB/9sLgD/bC4A/2wuAP9sLgD/T1lF/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9QV0L/bC4A/2wuAP9sLgD/bC4A/2c1DP8BzP3/AM3//xmpxf9XTjP/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2c2Df8bpsD/AM3//wDN//8Azf//AM3//wDN//8Azf//JJmr/2wuAf9sLgD/bC4A/2wuAP9sLgD/bC4A/zWAg/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Qtdn/aTIH/2wuAP9sLgD/bC4A/2wuAP9sLgD/Qmxj/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//G6W//2wuAP9sLgD/bC4A/2wuAP9sLgD/I5qt/wDN//8Azf//AM3//wDN//8LveX/bC4A/2wuAP9sLgD/bC4A/2wuAP82foH/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zd9fv9sLgD/bC4A/2wuAP9sLgD/bC4A/wq+5/8Azf//AM3//wHL/P8yhIr/aTMH/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2c1C/8aqMP/AM3//wDN//8Azf//AM3//wDN//8Azf//PXNv/2wuAP9sLgD/bC4A/2wuAP9sLgD/aTMI/xC22v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//01cSf9sLgD/bC4A/2wuAP9sLgD/bC4A/11FJf8FxvT/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP8hnLD/AM3//wDN//8Azf//AM3//w254P9sLgD/bC4A/2wuAP9sLgD/bC4A/zGGjf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//MoSK/2wuAP9sLgD/bC4A/2wuAP9sLgD/Dbrg/wDN//8Azf//AM3//wDN//8pkZ7/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2U4EP8TsdP/AM3//wDN//8Azf//AM3//wDN//8DyPj/WUot/2wuAP9sLgD/bC4A/2wuAP9sLgD/TF1M/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP9rLwL/GqfC/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2iuv9sLgD/bC4A/2wuAP9sLgD/bC4A/yaVpf8Azf//AM3//wDN//8Azf//BsTw/2wuAP9sLgD/bC4A/2wuAP9sLgD/P3Bq/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9Abmf/bC4A/2wuAP9sLgD/bC4A/2wuAP8GxPD/AM3//wDN//8Azf//AM3//yeTo/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/19CIP8JwOr/AM3//wDN//8Azf//AM3//wDN//8Wrcz/azAE/2wuAP9sLgD/bC4A/2wuAP9sLgD/HKS9/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3+/1VQNv9sLgD/bC4A/2wuAP9sLgD/bC4A/0JsY/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HaK6/2wuAP9sLgD/bC4A/2wuAP9sLgD/MoSK/wDN//8Azf//AM3//wDN//8Azf//YT4a/2wuAP9sLgD/bC4A/2wuAP9hPxv/A8n5/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//A8j4/2I9Gf9sLgD/bC4A/2wuAP9sLgD/Yj0Y/wDN//8Azf//AM3//wDN//8Azf//M4OI/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/09YRP8BzP3/AM3//wDN//8Azf//AM3//wDN//89dHD/bC4A/2wuAP9sLgD/bC4A/2wuAP9VUTj/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8foLf/bC4A/2wuAP9sLgD/bC4A/2wuAP9mNw7/Cb/p/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP9EamD/AM3//wDN//8Azf//AM3//wDN//9GZ1v/bC4A/2wuAP9sLgD/bC4A/2wuAP83fX//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//84e3z/bC4A/2wuAP9sLgD/bC4A/2wuAP9HZVj/AM3//wDN//8Azf//AM3//wDN//9FaF7/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/zODiP8Azf//AM3//wDN//8Azf//AM3//wfD8P9jOxX/bC4A/2wuAP9sLgD/bC4A/2wuAP8eorr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//1BXQv9sLgD/bC4A/2wuAP9sLgD/bC4A/zV/g/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2iuv9sLgD/bC4A/2wuAP9sLgD/bC4A/11FJf8Azf//AM3//wDN//8Azf//AM3//x+gt/9sLgD/bC4A/2wuAP9sLgD/bC4A/2svAf8xhYv/Acz+/wDN//8Azf//AM3//wDN//8BzP3/MoOJ/2wvAf9sLgD/bC4A/2wuAP9sLgD/bC4A/yGdsf8Azf//AM3//wDN//8Azf//AM3//11EI/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/aTIH/xKz1f8Azf//AM3//wDN//8Azf//AM3//y+IkP9sLgD/bC4A/2wuAP9sLgD/bC4A/09ZRf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8TstP/bC4B/2wuAP9sLgD/bC4A/2wuAP9lORL/BsXy/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HaK6/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/xG01/8Azf//AM3//wDN//8Azf//Acz+/1dOM/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9XTjP/LYuV/xqow/8ap8P/LoqU/1dNMv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9aSiz/Acz9/wDN//8Azf//AM3//wDN//8Ss9b/bC4A/2wuAP9sLgD/bC4A/2wuAP9MXUz/YT4Z/2wuAP9sLgD/bC4A/2wuAP9sLgD/UlU//wDN/v8Azf//AM3//wDN//8Azf//A8j3/2E+Gv9sLgD/bC4A/2wuAP9sLgD/bC8B/xKz1f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//z5ybf9sLgD/bC4A/2wuAP9sLgD/bC4A/zh7fP8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/OXl5/wDN//8Azf//AM3//wDN//8Azf//F6vJ/2oxBf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/azAD/xqnwf8Azf//AM3//wDN//8Azf//AM3//zp4d/9sLgD/bC4A/2wuAP9sLgD/bC4A/yWWp/8cpL3/ay8C/2wuAP9sLgD/bC4A/2wuAP9sLgD/I5ms/wDN//8Azf//AM3//wDN//8Azf//MoSJ/2wuAP9sLgD/bC4A/2wuAP9sLgD/PXRw/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvr/ZDoU/2wuAP9sLgD/bC4A/2wuAP9qMQX/C73m/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2iuv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9kOhP/BcXz/wDN//8Azf//AM3//wDN//8Azf//LoqU/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8yg4n/AM3//wDN//8Azf//AM3//wDN//8GxfL/ZDkS/2wuAP9sLgD/bC4A/2wuAP9pMwj/BsTx/wDN//8/cWz/bC4A/2wuAP9sLgD/bC4A/2wuAP9bRyj/Acv8/wDN//8Azf//AM3//wDN//8Hwu7/aDQK/2wuAP9sLgD/bC4A/2wuAP9jOxb/Asr6/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x+ftf9sLgD/bC4A/2wuAP9sLgD/bC4A/0lhUv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HaK6/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP83fX7/AM3//wDN//8Azf//AM3//wDN//8Azf//MIeP/2swA/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLwH/NYCD/wDN//8Azf//AM3//wDN//8Azf//AM3//zd8ff9sLgD/bC4A/2wuAP9sLgD/bC4A/0ZmWf8Azf//AM3//wbE8f9iPRj/bC4A/2wuAP9sLgD/bC4A/2wuAP8ll6n/AM3//wDN//8Azf//AM3//wDN//9EamD/bC4A/2wuAP9sLgD/bC4A/2wuAP8eobj/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Qmxk/2wuAP9sLgD/bC4A/2wuAP9sLgD/IZyx/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2kzCP8RtNb/AM3//wDN//8Azf//AM3//wDN//8Azf//HKS9/15EI/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/X0Ee/yCftf8Azf//AM3//wDN//8Azf//AM3//wDN//8Ss9X/aTMI/2wuAP9sLgD/bC4A/2wuAP9sLgD/GKrH/wDN//8Azf//AM3//yyNmP9sLgD/bC4A/2wuAP9sLgD/bC4A/1VROP8Azf//AM3//wDN//8Azf//AM3//xylvv9sLgD/bC4A/2wuAP9sLgD/bC4A/0FuZ/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN/v9hPhr/bC4A/2wuAP9sLgD/bC4A/2Y3D/8Dyfj/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2iuv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1hLL/8FxvT/AM3//wDN//8Azf//AM3//wDN//8Azf//A8n4/yuPm/9UUjn/azAC/2wuAP9sLgD/bC4A/2wuAP9rLwL/VVA3/yyMl/8EyPf/AM3//wDN//8Azf//AM3//wDN//8Azf//Bcb0/1lKLf9sLgD/bC4A/2wuAP9sLgD/bC4A/09aRv8Azf//AM3//wDN//8Azf//Asr6/19CIP9sLgD/bC4A/2wuAP9sLgD/bC4A/xSw0P8Azf//AM3//wDN//8Azf//Acv9/2I9GP9sLgD/bC4A/2wuAP9sLgD/YEAd/wDN/v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//ErLU/2wuAP9sLgD/bC4A/2wuAP9sLgD/SGRX/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HaK6/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/0teTv8Cyvr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Hw+//GajE/yOarf8jmq3/GajD/wfD7v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLK+v9MXkz/bC4A/2wuAP9sLgD/bC4A/2wuAP9rMAT/FLDQ/wDN//8Azf//AM3//wDN//8Azf//MIeP/2wuAP9sLgD/bC4A/2wuAP9sLgD/PHVy/wDN//8Azf//AM3//wDN//8Azf//Qmxk/2wuAP9sLgD/bC4A/2wuAP9sLgD/EbTX/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8sjJf/bC4A/2wuAP9sLgD/bC4A/2wuAP8pkJ7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/0pgUP8Ex/b/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Ex/b/S19P/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/zt3df8Azf//AM3//wDN//8Azf//AM3//wDN//8Hw+//aDMJ/2wuAP9sLgD/bC4A/2wuAP9fQR//AM3+/wDN//8Azf//AM3//wDN//8kmav/bC4A/2wuAP9sLgD/bC4A/2wuAP8rjpn/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//0RpX/9sLgD/bC4A/2wuAP9sLgD/bC4A/w643v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2iuv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1ZPNP8OuN3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//D7fc/1dOM/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9XTTL/A8n4/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9IY1X/bC4A/2wuAP9sLgD/bC4A/2wuAP8TsdH/AM3//wDN//8Azf//AM3//wnA6f9sLgH/bC4A/2wuAP9sLgD/bC4A/0NrYv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//WUsu/2wuAP9sLgD/bC4A/2wuAP9iPRj/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HaK6/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC8B/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2c2Df8wh47/A8n5/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//A8n5/zGGjf9nNgz/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/YzwW/w653/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yWWp/9sLgD/bC4A/2wuAP9sLgD/bC4A/zCHj/8Azf//AM3//wDN//8Azf//AM3//11EJP9sLgD/bC4A/2wuAP9sLgD/WEwx/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLL+/9pMgf/bC4A/2wuAP9sLgD/bC4A/01cSf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8dorr/bC4A/2wuAP9sLgD/bC4A/2wuAP82fX//ZTgQ/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9fQiD/L4iQ/wjB7P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//CMHs/zCHj/9fQR//bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2Y3D/8Wrcz/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//CMHs/2svAv9sLgD/bC4A/2wuAP9sLgD/SGNU/wDN//8Azf//AM3//wDN//8Azf//SGNV/2wuAP9sLgD/bC4A/2wuAP9pMwj/Acv8/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//D7jd/2wuAP9sLgD/bC4A/2wuAP9sLgD/Qmxj/w653/8Oud//Drnf/w653/8Oud//Drnf/w653/8Oud//Drnf/w653/8Oud//Drnf/w653/8Oud//Drnf/yeTo/9sLgD/bC4A/2wuAP9sLgD/bC4A/yGdsf8Wrcz/YzsV/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/ajEF/1BXQv82foH/Ipuv/xWuzf8Pt9z/D7fc/xWuzf8im67/Nn6A/1BXQv9qMQX/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9kOxT/F6zK/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//WUos/2wuAP9sLgD/bC4A/2wuAP9eQiH/Drnf/w653/8Oud//Drnf/w653/8+cm3/bC4A/2wuAP9sLgD/bC4A/2wuAP8Oud//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8cpL7/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/IZ2x/wDN//8Pt9z/WUot/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/Wkks/w+32/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9EaV//bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/xumwP8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yeUpP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8hnbH/AM3//wDN//8Ex/X/P3Bq/2svAf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC8B/0BvaP8FxvT/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zKDiP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/Jpan/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//L4iR/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/yGdsf8Azf//AM3//wDN//8Azf//GajE/1ZPNf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1ZONP8aqMP/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//JZeo/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8uipP/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//81gIP/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/IZ2x/wDN//8Azf//AM3//wDN//8Azf//AMz+/yCes/9QV0L/bC8B/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC8B/1FXQf8hnbL/AMz+/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8cpb7/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/zSBhf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zh7e/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8hnbH/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8OuN7/MoSK/1BYQ/9nNQv/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9nNQz/UFhD/zKEiv8PuN3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xaty/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/N3x9/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//GKnG/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/w643v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHL/P8Qtdn/H6C3/yiSoP8ti5X/LYuV/yiSoP8foLf/ELXZ/wHL/P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//CcDr/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8uiZL/LomS/y6Jkv8Yqsf/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ipyw/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/MIeO/zCHjv8wh47/IZyx/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9MXUz/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9LX07/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//0xdTP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/0tfTv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//TF1M/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/S19O/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9MXUz/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9LX07/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//0xdTP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/0tfTv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//CMHr/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/DLvj/wy74/8Mu+P/CMHr/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Ex/b/UFhE/1BYRP9QWET/UFhE/1BYRP8qkJ3/AM3//wDN//8Azf//AM3//wDN//9JYVL/UFhE/1BYRP9QWET/UFhE/zSBhf8Azf//AM3//wDN//8Azf//AM3//z9xa/9QWET/UFhE/1BYRP9QWET/PnJt/wDN//8Azf//AM3//wDN//8Azf//NYCD/1BYRP9QWET/UFhE/1BYRP9IY1X/AM3//wDN//8Azf//AM3//wDN//8qj5v/UFhE/1BYRP9QWET/UFhE/1BYRP8DyPf/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wXF8v9sLgD/bC4A/2wuAP9sLgD/bC4A/zl6ef8Azf//AM3//wDN//8Azf//AM3//2Q6FP9sLgD/bC4A/2wuAP9sLgD/R2VZ/wDN//8Azf//AM3//wDN//8Azf//VVA2/2wuAP9sLgD/bC4A/2wuAP9UUTj/AM3//wDN//8Azf//AM3//wDN//9HZFf/bC4A/2wuAP9sLgD/bC4A/2I9GP8Azf//AM3//wDN//8Azf//AM3//zp4d/9sLgD/bC4A/2wuAP9sLgD/bC4A/wXG9P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BcXy/2wuAP9sLgD/bC4A/2wuAP9sLgD/OXp5/wDN//8Azf//AM3//wDN//8Azf//ZDoU/2wuAP9sLgD/bC4A/2wuAP9HZVn/AM3//wDN//8Azf//AM3//wDN//9VUDb/bC4A/2wuAP9sLgD/bC4A/1RROP8Azf//AM3//wDN//8Azf//AM3//0dkV/9sLgD/bC4A/2wuAP9sLgD/Yj0Y/wDN//8Azf//AM3//wDN//8Azf//Onh3/2wuAP9sLgD/bC4A/2wuAP9sLgD/Bcb0/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8FxfL/bC4A/2wuAP9sLgD/bC4A/2wuAP85enn/AM3//wDN//8Azf//AM3//wDN//9kOhT/bC4A/2wuAP9sLgD/bC4A/0dlWf8Azf//AM3//wDN//8Azf//AM3//1VQNv9sLgD/bC4A/2wuAP9sLgD/VFE4/wDN//8Azf//AM3//wDN//8Azf//R2RX/2wuAP9sLgD/bC4A/2wuAP9iPRj/AM3//wDN//8Azf//AM3//wDN//86eHf/bC4A/2wuAP9sLgD/bC4A/2wuAP8FxvT/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wXF8v9sLgD/bC4A/2wuAP9sLgD/bC4A/zl6ef8Azf//AM3//wDN//8Azf//AM3//2Q6FP9sLgD/bC4A/2wuAP9sLgD/R2VZ/wDN//8Azf//AM3//wDN//8Azf//VVA2/2wuAP9sLgD/bC4A/2wuAP9UUTj/AM3//wDN//8Azf//AM3//wDN//9HZFf/bC4A/2wuAP9sLgD/bC4A/2I9GP8Azf//AM3//wDN//8Azf//AM3//zp4d/9sLgD/bC4A/2wuAP9sLgD/bC4A/wXG9P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BcXy/2wuAP9sLgD/bC4A/2wuAP9sLgD/OXp5/wDN//8Azf//AM3//wDN//8Azf//ZDoU/2wuAP9sLgD/bC4A/2wuAP9HZVn/AM3//wDN//8Azf//AM3//wDN//9VUDb/bC4A/2wuAP9sLgD/bC4A/1RROP8Azf//AM3//wDN//8Azf//AM3//0dkV/9sLgD/bC4A/2wuAP9sLgD/Yj0Y/wDN//8Azf//AM3//wDN//8Azf//Onh3/2wuAP9sLgD/bC4A/2wuAP9sLgD/Bcb0/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8DyPj/bC4A/2wuAP9sLgD/bC4A/2wuAP8+cm3/AM3//wDN//8Azf//AM3//wDN//9hPxv/bC4A/2wuAP9sLgD/bC4A/0xdTP8Azf//AM3//wDN//8Azf//AM3//1VQNv9sLgD/bC4A/2wuAP9sLgD/VFE4/wDN//8Azf//AM3//wDN//8Azf//TVxJ/2wuAP9sLgD/bC4A/2wuAP9gQB7/AM3//wDN//8Azf//AM3//wDN//8/cGv/bC4A/2wuAP9sLgD/bC4A/2wvAf8Cyvr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9jOxX/bC4A/2wuAP9sLgD/bC4A/1ZPNP8Azf//AM3//wDN//8Azf//AM3//1RROP9sLgD/bC4A/2wuAP9sLgD/YzwX/wHL/P8Azf//AM3//wDN//8Azf//VVA2/2wuAP9sLgD/bC4A/2wuAP9UUTj/AM3//wDN//8Azf//AM3//wLL+/9jOxX/bC4A/2wuAP9sLgD/bC4A/1NTO/8Azf//AM3//wDN//8Azf//AM3//1dNMv9sLgD/bC4A/2wuAP9sLgD/YjwX/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//05bSP9sLgD/bC4A/2wuAP9sLgD/bC4A/xmow/8Azf//AM3//wDN//8Azf//PXNv/2wuAP9sLgD/bC4A/2wuAP9sLgD/J5Oj/wDN//8Azf//AM3//wDN//9VUDb/bC4A/2wuAP9sLgD/bC4A/1RROP8Azf//AM3//wDN//8Azf//KZKg/2wuAP9sLgD/bC4A/2wuAP9sLgD/PHVy/wDN//8Azf//AM3//wDN//8apsH/bC4A/2wuAP9sLgD/bC4A/2wuAP9NXEr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//LYuV/2wuAP9sLgD/bC4A/2wuAP9sLgD/XUQj/wq+5/8Azf//AM3//wDN//8bpsD/bC4A/2wuAP9sLgD/bC4A/2wuAP9kOhP/EbTX/wDN//8Azf//AM3//1VQNv9sLgD/bC4A/2wuAP9sLgD/VFE4/wDN//8Azf//AM3//xKz1f9lORL/bC4A/2wuAP9sLgD/bC4A/2wuAP8ap8P/AM3//wDN//8Azf//C77m/15DIv9sLgD/bC4A/2wuAP9sLgD/bC4A/yyMl/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Hw+//ZjcO/2wuAP9sLgD/bC4A/2wuAP9sLgD/X0Ef/yCetP8AzP7/AM3//wDM/v9ZSy7/bC4A/2wuAP9sLgD/bC4A/2wuAP9kOhL/KJOi/wLL+/8Azf//VVA2/2wuAP9sLgD/bC4A/2wuAP9UUTj/AM3//wLL+/8okqD/ZTkS/2wuAP9sLgD/bC4A/2wuAP9sLgD/WEwx/wDN/v8Azf//Acz+/yGdsv9gQR7/bC4A/2wuAP9sLgD/bC4A/2wuAP9mOBD/BsTw/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8zgof/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2BBHv9KYE//SmFS/2I9Gf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/YzwW/0xdTP9kOhP/bC4A/2wuAP9sLgD/bC4A/2Q6E/9MXUv/YzsW/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9hPhr/SWFS/0tfT/9gQB3/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/zKEif8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLK+v9UUjr/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9TUzz/Asr7/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wq/6P9bRyj/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/W0gq/wnA6f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wnA6/9QV0L/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1BYRP8Iwez/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHM/f8sjZn/YT8b/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/ZTkS/zp4dv9XTTL/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9XTjP/OHt7/2M7Ff9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2A/HP8rjpr/Acz9/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvr/Ipyw/0BuZ/9VUDf/X0Ef/2BAHf9XTTL/RGlf/yaVpf8FxvT/AM3//wDN//8ZqcX/O3d1/1JVPv9eQyH/YEAc/1dNMv9EamD/R2VZ/1lLLv9gPxz/XkMh/1JVP/87d3X/GanF/wDN//8Azf//BMj2/yWXqf9Da2H/V04z/2BAHf9fQR//VVE3/0BvaP8hnbH/Asr6/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Rs9b/T1lG/09ZRv8RtNf/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xiqx/9sLgD/bC4A/xeryf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wu95v8Nu+H/Ipyw/2wuAP9sLgD/IZ2x/w274f8Kvub/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//XEYn/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/1pJK/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9cRif/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/Wkkr/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x2jvP8inLD/MoOJ/2wuAP9sLgD/MoSK/yKcsP8cpL3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Yqsf/bC4A/2wuAP8Xq8n/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xaty/9kOhT/ZDoU/xWuzf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Czf//AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAoAAAAQAAAAIAAAAABACAAAAAAAABAAAAjLgAAIy4AAAAAAAAAAAAAAc3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//As3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BMf2/x6iuf82fX//SmFR/1hLL/9iPRj/ZzYN/2Y2Df9iPRj/WEsv/0phUf82fX//HaK6/wTH9v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHM/v8foLf/SGNV/2g0Cv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9oNQv/SGRW/x6huP8BzP7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AMz+/yWXqP9aSCr/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2c2Df9bSCn/WUks/19BH/9pMgf/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/Wkkr/ySXqf8AzP7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//ErPV/1NTO/9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9pMgb/QG9p/xaty/8BzP3/AM3//wDN//8Azf//Acz9/w+43f8ll6j/Qm1k/2M8Fv9sLgD/bC4A/2wuAP9sLgD/U1M8/xKz1v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//LYuV/2kzCP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9ZSSz/ErPW/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvv/Ipuv/1JUPf9sLgD/bC4A/2wuAP9pMwj/LYyW/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvv/Qmxk/2wuAP9sLgD/bC4A/1xFJf9aSSz/bC4A/2wuAP9YTDD/B8Pv/wDN//8Azf//AM3+/xaty/8qkJ3/LI2Y/yWWp/8YqcX/BsTx/wDN//8Azf//AM3//wDN//8Azf//HqC3/1xGJ/9sLgD/bC4A/2wuAP9BbWX/Asv7/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvr/SmBR/2wuAP9sLgD/bC4A/z5ybf8RtNf/ajEF/2wuAP9nNg3/Drnf/wDN//8Azf//FqzL/1hMMP9sLgD/bC4A/2wuAP9sLgD/bC4A/2svAv9XTjP/NX+D/w264f8Azf//AM3//wDN//8DyPf/PXRw/2wuAf9sLgD/bC4A/0lhUv8Cyvr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8BzP7/RmZa/2wuAP9sLgD/aTIH/yeUpP8Azf//N3x8/2wuAP9sLgD/Nn6B/wDN//8Azf//GanF/2g0Cv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9rMAT/Rmdb/w643f8Azf//AM3//wDN//8llqf/aTMI/2wuAP9sLgD/Rmdb/wDM/v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//NX+B/2wuAP9sLgD/aTMI/x6huP8Azf//AM3//1hMMP9sLgD/ay8C/wq+5/8Azf//Asn5/15DIv9sLgD/bC4A/1dOM/8uipT/LoqT/1dNMv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9oMwn/MoSK/wHM/f8Azf//AM3//x2jvP9oNAn/bC4A/2wuAP81f4P/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//G6W//2swAv9sLgD/ay8C/yOarv8Azf//AM3//wPJ+f9qMAT/bC4A/1hLLv8Azf//AM3//yKbr/9sLgD/bC4A/1JVPv8Cyfn/AM3//wDN//8Dyfn/UlQ9/2wuAP9sLgD/TlpG/2Q6FP9sLgD/bC4A/2wuAP9MXUv/BcXy/wDN//8Azf//IZ2y/2swA/9sLgD/azAD/xumwP8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BMf1/15DIv9sLgD/bC4A/zZ+gf8Azf//AM3//wDN//8Mu+L/bC4A/2wuAP9KYVH/AM3//wDN//84enr/bC4A/2wuAP8hnLH/AM3//wDN//8Azf//AM3//yKbsP9sLgD/bC4A/zh7fP8GxPD/PXNu/2svAv9sLgD/bC4A/1VQNv8GxPD/AM3//wDN//8zgob/bC4A/2wuAP9dRCP/BMf2/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zZ+gf9sLgD/bC4A/1RSOv8By/z/AM3//wDN//8Azf//D7jd/2wuAP9sLgD/SGNV/wDN//8Azf//O3Z0/2wuAP9sLgD/HKS9/wDN//8Azf//AM3//wDN//8do7z/bC4A/2wuAP87dnT/AM3//wDN//9KYFD/bC4A/2wuAP9sLgD/UVZB/wLK+v8Azf//Acz9/1FVP/9sLgD/bC4A/zV/gv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wjC7f9mNg3/bC4A/2swBP8TsdP/AM3//wDN//8Azf//AM3//w+43f9sLgD/bC4A/1NSO/8Azf//AM3//yqQnf9sLgD/bC4A/0JtZP8Azf//AM3//wDN//8Azf//Qmxj/2wuAP9sLgD/Ko+b/wDN//8Azf//VFI5/2wuAP9sLgD/bC4A/2wuAP88dXL/AM3//wDN//8RtNf/ajEF/2wuAP9mNw7/B8Lu/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//80gYX/bC4A/2wuAP9Da2H/AM3//wDN//8Azf//AM3//wDN//8PuN3/bC4A/2wuAP9oNAn/BMf1/wDN//8Iwu3/ZzYN/2wuAP9sLgD/PXNv/xKz1f8Ss9X/PnNu/2wuAP9sLgD/ZzUL/wnB6/8Azf//BMf1/2gzCf9sLgD/ZDoT/2kyBv9sLgD/ay8C/xmpxP8Azf//AM3//0BvaP9sLgD/bC4A/zOChv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8BzP7/XkIg/2wuAP9rLwH/EbXY/wDN//8Azf//AM3//wDN//8Azf//D7jd/2wuAP9sLgD/bC4A/ymRn/8Azf//AM3//yyNmP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/y6Kk/8Azf//AM3//ymRn/9sLgD/bC4A/0BvaP8yhIr/bC4A/2wuAP9WTzX/AM3+/wDN//8OuN3/azAD/2wuAP9eQyH/AMz+/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//GKnG/2wuAP9sLgD/UVZB/wDN//8Azf//AM3//wDN//8Azf//AM3//w+43f9sLgD/bC4A/2wuAP9eQyL/BMf1/wDN//8Azf//LoqT/2gzCf9sLgD/bC4A/2wuAP9sLgD/aTMI/zCHjv8Azf//AM3//wTG9P9eQyH/bC4A/2wuAP8Yq8j/Asv7/1lJLP9sLgD/bC4A/x6huP8Azf//AM3//05bR/9sLgD/bC4A/xiqx/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zh7e/9sLgD/bC4A/yyMl/8Azf//AM3//wDN//8Azf//AM3//wDN//8PuN3/bC4A/2wuAP9sLgD/bC4A/0VnXP8AzP7/AM3//wDN//8LvOT/MYSL/0VoXP9FZ1z/MoSK/wy74/8Azf//AM3//wHM/v9FZ1v/bC4A/2wuAP9OWkf/AM3//wDN//8kmKr/bC4A/2wuAP9KYFH/AM3//wDN//8pkJ7/bC4A/2wuAP83fHz/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9SVD3/bC4A/2wuAP8Oud7/AM3//wDN//8Azf//AM3//wDN//8Azf//D7jd/2wuAP9sLgD/bC4A/2wuAP9sLgD/RGlf/wTI9/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wTI9v9EaV7/bC4A/2wuAP9nNgz/D7bb/wDN//8Azf//Asr7/2I9F/9sLgD/aTMI/wXG8/8Azf//C73l/2wuAP9sLgD/UlU//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8AzP7/ZzYN/2wuAP9iPRj/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//w+43f9sLgD/bC4A/15CIP9qMQT/bC4A/2wuAP9cRif/JJiq/wLK+v8Azf//AM3//wDN//8Azf//Asr6/ySYqf9cRib/bC4A/2wuAP9qMAT/Ipyw/wDN//8Azf//AM3//wDN//9BbWX/bC4A/2wuAP8eobj/AM3//wDN//9fQR7/bC4A/2Y3Dv8Azf7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//C73m/2wuAP9sLgD/Yj0Z/z1zb/89c2//PXNv/z1zb/89c2//PXNv/z1zb/9DamD/bC4A/2wuAP9GZVn/Ipuv/2c1C/9sLgD/bC4A/2wuAP9lORL/TF1M/z9wav8/cGr/TF1M/2U5Ev9sLgD/bC4A/2wuAP9nNQv/Ipuu/wDN//8Azf//AM3//wDN//8Azf//J5Oi/2wuAP9sLgD/UVZA/z1zb/89c2//YT8b/2wuAP9sLgD/Cr7n/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xWuzf9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/RmVZ/wDN//8RtNf/UlU//2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9SVT7/EbTX/wDN//8Azf//AM3//wDN//8Azf//AM3//xatzP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/xWuzv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8bpb//bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/0ZlWf8Azf//AM3//wDN//8cpL3/RmZa/2Q6FP9sLgD/bC4A/2wuAP9sLgD/ZDoU/0ZmWv8co7z/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Mu+L/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8bpsD/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BsTx/xeryf8Xq8n/F6vJ/xeryf8Xq8n/F6vJ/xeryf8Xq8n/F6vJ/xeryf8Xq8n/F6vJ/xeryf8Pt9v/AM3//wDN//8Azf//AM3//wDN//8Azf7/DLzj/xWuzf8Vrs3/DLzk/wDN/v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Asr6/xeryf8Xq8n/F6vJ/xeryf8Xq8n/F6vJ/xeryf8Xq8n/BsTx/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xulvv9OWkf/TlpH/05aR/9OWkf/TlpH/05aR/9OWkf/TlpH/05aR/9OWkf/TlpH/05aR/9OWkf/TlpH/05aR/9OWkf/G6W//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8mlaX/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/yaWpv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//JpWl/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP8mlqb/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLK+v8GxPH/BsTx/wbE8f8GxPH/BsTx/wbE8f8GxPH/BsTx/wbE8f8GxPH/BsTx/wbE8f8GxPH/BsTx/wbE8f8GxPH/Asr6/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8xhYv/XkMi/15DIv8ZqcX/AM3//wDN//9aSCr/XkMi/05bSP8Azf//AM3//yWXqP9eQyL/XkMi/yWXqf8Azf//AM3//05aR/9eQyL/WUks/wDN//8Azf//GajE/15DIv9eQyL/MYWM/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//OXp5/2wuAP9sLgD/HKO8/wDN//8Azf//aDQK/2wuAP9ZSiz/AM3//wDN//8rjpv/bC4A/2wuAP8qj5z/AM3//wDN//9aSSv/bC4A/2c1DP8Azf//AM3//x2ju/9sLgD/bC4A/zh6ev8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//zl6ef9sLgD/bC4A/xyjvP8Azf//AM3//2g0Cv9sLgD/WUos/wDN//8Azf//K46b/2wuAP9sLgD/Ko+c/wDN//8Azf//Wkkr/2wuAP9nNQz/AM3//wDN//8do7v/bC4A/2wuAP84enr/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//81gIP/bC4A/2wuAP8ll6j/AM3//wDN//9jOxX/bC4A/2I9Gf8AzP7/AM3//yuOm/9sLgD/bC4A/yqPnP8Azf//AMz+/2I9GP9sLgD/YzwW/wDN//8Azf//Jpan/2wuAP9sLgD/NICE/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//H6C3/2wuAP9sLgD/VFI6/wPJ+f8Azf//TF1M/2wuAP9sLgD/J5Oj/wDN//8rjpv/bC4A/2wuAP8qj5z/AM3//yiTof9sLgD/bC4A/0teTf8Azf//A8n5/1RROf9sLgD/bC4A/x6huP8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLL+/9cRSX/bC4A/2wuAP9WTzX/K46b/0FtZv9sLgD/bC4A/2oxBf8+cm3/QW1l/2wuAP9sLgD/QW1l/z5xbP9qMQT/bC4A/2wuAP9Bbmf/K46a/1ZONP9sLgD/bC4A/1xGJv8Cy/v/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//GKrH/2g0Cv9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2g0Cv8Xq8j/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8WrMr/WUot/2wuAP9sLgD/bC4A/2wuAP9eQyL/ZzYM/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2c2Df9dRCT/bC4A/2wuAP9sLgD/bC4A/1lKLf8Wrcv/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHM/v8ZqcX/LYuV/y6Kk/8bpsH/Acv8/wbE8P8jmaz/MIeP/yeUpP8ok6H/MIeP/yOarP8GxPD/Acz9/xqnwv8uipP/LYuV/xipxv8BzP7/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//85eXn/OXp5/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//84e3z/WUks/1lKLP83fH3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//QW1l/15DIv9dRCP/QW5m/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8/cGn/P3Bq/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Bzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAKAAAADAAAABgAAAAAQAgAAAAAAAAJAAAIy4AACMuAAAAAAAAAAAAAAHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wHN//8Bzf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8MvOT/Jpam/zl5eP9GZlr/TF1L/0xdS/9GZlr/OXl4/yaWp/8MvOT/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8FxfP/LIyX/1ZPNf9sLwH/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLwH/Vk81/yyNmP8FxfP/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Acv8/yyNmP9hPhr/bC4A/2wuAP9sLgD/bC4A/15DIv88dXL/Ko+b/ymRn/8who7/P3Fr/1VQNv9pMgb/bC4A/2wuAP9hPhr/LI2Y/wHL/P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Mu+L/UVZB/2wuAP9sLgD/bC4A/2wuAP9pMgf/MIaO/wPJ+f8Azf//AM3//wDN//8Azf//AM3//wDN//8Kvub/L4iR/15DIv9sLgD/bC4A/1BXQf8Mu+P/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xasyv9iPRn/bC4A/2Y3D/9LX0//bC4A/2oxBP8im6//AM3//wHL/P8dorr/OHp6/zt2dP8zg4j/IZyw/wm/6f8Azf//AM3//wLK+v8uiZL/ZjgP/2wuAP9hPhn/FqzL/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Fq3L/2U4EP9sLgD/WEsv/xC22f9QWEP/bC4A/z5xbP8Azf//Bcb0/0xdS/9sLgD/bC4A/2wuAP9sLgD/bC4A/2kyBv9OWkb/IJ6z/wHM/f8Azf//D7fb/1dMMf9sLgD/ZTgR/xatzP8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Mu+L/YT4a/2wuAP9SVD7/B8Pv/wq+6P9qMQX/ay8B/w264f8Azf//P3Bp/2wuAP9nNQv/QW1l/0JtZP9oNQv/bC4A/2wuAP9sLgD/bC4B/1BYQ/8Pt9z/AM3//wbE8P9RVkD/bC4A/2E+Gv8Mu+L/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wLK+/9RVj//bC4A/1hLL/8GxPD/AM3//x6iuf9sLgD/W0co/wDN//8GxPD/ZzUL/2svAv8dorv/AM3//wDN//8dorr/ay8C/2oxBP9Bbmb/ZzUL/2wuAP9lOBD/HqG4/wDN//8GxPH/V00y/2wuAP9RVkD/Asr7/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yyNmP9sLgD/ZzYM/xC22v8Azf//AM3//yWWp/9sLgD/UVZB/wDN//8Ss9b/bC4A/2U5Ev8BzP3/AM3//wDN//8BzP3/ZTkR/2wuAP8RtNb/D7fb/19BH/9sLgD/aTMI/x2iuv8Azf//D7fc/2Y3Dv9sLgD/K42Z/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//BMf1/2I9F/9sLgD/MYaN/wDN//8Azf//AM3//yaVpf9sLgD/WEww/wDN//8Jv+n/ajEG/2oxBP8Ss9X/AM3//wDN//8SstT/ajEE/2oxBf8Kv+n/AM3//1hML/9sLgD/bC4A/2Q5Ev8Pt9z/AM3//y6Jkv9sLgD/Yj0Y/wTH9f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//LYyW/2wuAP9eQyH/A8j3/wDN//8Azf//AM3//yaVpf9sLgD/ajEF/wfC7v8Azf//S19O/2wuAP9eQiH/LYyW/y2Llv9eQiD/bC4A/0xdS/8Azf//B8Lu/2oxBf9rLwL/Wkkr/2wuAP9PWET/Acz9/wPJ+f9cRSX/bC4A/yyMl/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//VU81/2wuAP8xhIv/AM3//wDN//8Azf//AM3//yaVpf9sLgD/bC4A/zOCh/8Azf//DLzk/1xGJv9sLgD/bC4A/2wuAP9sLgD/XUQk/wy74v8Azf//M4KH/2wuAP9XTTL/ELba/2g0Cf9sLgD/H6C2/wDN//8viJD/bC4A/1VQNv8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8NuuH/ajEE/2oxBf8Nu+H/AM3//wDN//8Azf//AM3//yaVpf9sLgD/bC4A/2c2Df8UsND/AM3//wbE8P8yhIn/TVxK/01cSv8zg4j/B8Pv/wDN//8UsND/ZzYN/2wuAP8nlKP/AM3//z1zb/9sLgD/TVxJ/wDN//8LveX/ajIG/2oxBP8Mu+L/AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8llqf/bC4A/1hLL/8Azf//AM3//wDN//8Azf//AM3//yaVpf9sLgD/bC4A/2wuAP9iPBf/HKO8/wDN//8Azf//AM3//wDN//8Azf//AM3//x2jvP9jPBf/bC4A/01cSf8By/z/AM3//xG01/9rLwL/ajEE/wfD7/8Azf//Vk40/2wuAP8ll6j/AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//84enr/bC4A/0tfT/8TstP/E7LT/xOy0/8TstP/E7LT/zKDif9sLgD/Vk4z/1VQN/9sLgD/azAD/0teTv8nlKP/Fq3M/xatzP8nlKP/S15N/2swAv9sLgD/VVA2/wfC7v8Azf//AM3//wHM/f9cRib/bC4A/yuOmv8TstP/SWFS/2wuAP84e3v/AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9FaF3/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/UFdC/wXG8/8/cGr/azAD/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2swA/9AcGn/BcXz/wDN//8Azf//AM3//wDN//9IY1T/bC4A/2wuAP9sLgD/bC4A/2wuAP9EaF7/AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9EaV//YjwX/2I8F/9iPBf/YjwX/2I8F/9iPBf/YjwX/2I8F/9iPBf/SWJT/wDN//8Azf//ELba/zl6ev9TUzv/YEAc/2BAHP9TUzv/OXp5/xC12f8Azf//AM3//wDN//8Azf//AM3//wDN//85eXj/YjwX/2I8F/9iPBf/YjwX/2I8F/9EamD/AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//D7bb/zp3df86d3X/Ond1/zp3df86d3X/Ond1/zp3df86d3X/Ond1/zp3df86d3X/Ond1/w+32/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//HKO8/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/xykvf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//D7bb/zt3df87d3X/O3d1/zt3df87d3X/O3d1/zt3df87d3X/O3d1/zt3df87d3X/O3d1/w+32/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//JpWl/2E+Gf9EaV//AM3//xatzP9hPhn/VVA3/wDN//8Hw+7/X0If/19CIP8Hw+//AM3//1VQN/9hPhn/Fa7O/wDN//9EaV7/YT4Z/yaVpf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//K46b/2wuAP9LXk3/AM3//xiqx/9sLgD/XkMh/wDN//8Iwu3/aTIH/2kyB/8Iwu3/AM3//15CIf9sLgD/F6vI/wDN//9MXk3/bC4A/yqPm/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//KJKg/2wuAP9QV0L/AM3//xWuzf9sLgD/YzwW/wDN//8Iwu3/aTIH/2kyB/8Iwu3/AM3+/2M7Ff9sLgD/Fa7O/wDN//9RV0H/bC4A/yiSof8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//ErLU/2wuAf9pMgb/G6W//wXG8/9lORH/bC4A/yuOmv8Iwez/aTIH/2kyB/8Iwez/K42Z/2wuAP9lORL/Bcb0/xykvv9pMgb/bC4B/xKz1f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//0hjVf9sLgD/ajEF/1VQN/9mNw//bC4A/2svAv9aSSv/ay8C/2svAv9aSSv/ay8B/2wuAP9mNw//VVA3/2oxBf9sLgD/SGRW/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wXF8/9GZ1v/ay8B/2wuAP9sLgD/ZDoT/2kyB/9sLgD/bC4A/2wuAP9sLgD/aTIH/2M7FP9sLgD/bC4A/2svAv9FZ1v/BcXz/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Drje/yKbrv8co7z/BMf2/wnA6/8gnbP/JpWl/yeUpP8gnbP/CcDr/wTI9/8cpL3/Ipuu/w643v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Iwez/O3Zz/zt2dP8Iwez/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8jmav/XUQk/11EJP8jmaz/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//JJmr/yOZq/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAACgAAAAgAAAAQAAAAAEAIAAAAAAAABAAACMuAAAjLgAAAAAAAAAAAAAAzf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Ac3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Acz9/xWuzv8okaD/MoOJ/zKDif8okqD/Fa7O/wHM/f8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Cb/p/zl5eP9iPRj/bC4A/2wuAP9mNg3/ZDoT/2svAv9sLgD/Yj0Y/zl5eP8Jv+n/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yqPnP9mNw//bC4A/2wuAP9QV0L/Fq3M/wDN//8Azf//BMf2/xqnw/89dHD/ZjcP/2Y3D/8qkJ3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wHM/v8+cWz/bC4A/0ZmWv9nNgz/TlpH/wLL+/8cpL7/RmZa/0pgUP89c27/I5qt/wPI9/8Iwu3/Qmxk/2wuAP8+cm3/Acz+/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Onh2/2svAv8sjZj/JJir/2wuAf8Qttn/HqG4/2swAv9XTTL/V00x/2wuAP9sLgD/Yj0Y/yqPnP8Azf//K46a/2svAv86eHf/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//x+ftf9sLgH/MYWM/wDN//85eXj/XkIg/wDN//9NXEr/U1M8/wHM/v8BzP7/U1M7/1dMMf9FaF3/bC4A/0VoXf8Cy/v/MIeP/2wuAf8fn7b/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cyvr/XUQk/09YRP8Azf7/AM3//z1zbv9dRCT/AM3//09ZRP9NW0j/AM3//wDN//9OW0j/T1hE/wDN//9dQyL/bC4A/z9xa/8Azf//TlpH/11EJP8Cyvv/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yWXqf9sLgD/Fa7O/wDN//8Azf//PXNu/2svAv8LveX/J5Sk/2wuAP9KYVH/SmBR/2wuAP8nk6L/C7zk/2svAv9QWEP/bC4A/xykvv8UsNH/bC4B/ySXqf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//SmBQ/1VQNv8Azf//AM3//wDN//89c27/bC4A/0VoXf8Azf//KJKg/1RSOv9UUjn/KZCe/wDN//9FaFz/ZTkS/wbE8P9VTzX/UFdC/wDN//9UUjn/SmBR/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//9kOhP/N3x9/wDN//8Azf//AM3//z1zbv9pMwj/bC8B/0RpX/8Kv+n/AM3//wDN//8Kv+j/RGlf/2wvAf8mlab/AM3//ymQnv9rLwL/CcDq/zZ+gP9kOhP/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//CMHs/2wuAP9eQyL/VFE4/1RROP9UUTj/Yj0Y/1lKLP8nlKT/ZTgQ/2oxBP9ZSi7/WUot/2oxBP9lOBD/J5Sk/wDN//8Azf//D7fb/2wuAP9ZSSz/XUQj/2wuAP8Iwu3/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Iwev/Qm1k/0JtZP9CbWT/Qm1k/0JtZP9CbWT/Nn1//wDN//8Hw+7/K46b/z5xbP8+cWz/K46b/wfD7v8Azf//AM3//wDN//8EyPb/Qm1k/0JtZP9CbWT/Qm1k/wjB7P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Hw+//J5Sj/yeUo/8nlKP/J5Sj/yeUo/8nlKP/J5Sj/yeUo/8Hw+//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//xOx0v9sLgD/bC4A/2wuAP9sLgD/bC4A/2wuAP9sLgD/bC4A/xOx0/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Acz+/wPJ+P8Dyfj/A8n4/wPJ+P8Dyfj/A8n4/wPJ+P8Dyfj/Acz+/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//GqbA/2U5Ef8NuuD/MYaN/1xFJv8Azf//RmZZ/0ZmWv8Azf//XEUl/zCGjf8Nud//ZTkR/xqmwf8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8bpb//bC4A/xC12P8zgof/ZTkR/wDN//9LXk3/S15O/wDN//9lOBH/MoOI/xG12P9sLgD/G6W//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wjB7P9oNAn/RmZa/y6Kk/9sLgD/NIGF/1FWQP9RVkD/NICE/2wuAP8uipP/RmZZ/2g0Cv8Iwez/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//yaWp/9nNQv/bC4A/2gzCP9rMAP/bC4A/2wuAP9rMAP/aDQJ/2wuAP9nNQv/JZan/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wbE8P8XrMr/B8Pv/wq+5/8kmKv/JJiq/wq+5/8Hw+//F6zK/wbE8P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//0xdTP9MXkz/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//ELba/xC22v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAoAAAAEAAAACAAAAABACAAAAAAAAAEAAAjLgAAIy4AAAAAAAAAAAAAAM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8FxfL/F6zK/xesyv8FxfL/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wq+5v9FZ1z/YzwW/zp4dv81f4L/SWJT/0NqYP8Kvub/AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//w+33P9QV0L/T1lE/x+ftf9JYlP/U1M8/z1zb/8dorv/UFdC/w+43f8Azf//AM3//wDN//8Azf//AM3//wDM/v9OW0f/DLvi/0xcSv8nlKP/KJKg/yiSoP87dnT/X0Ig/xykvf9NW0j/AMz+/wDN//8Azf//AM3//wDN//8cpL7/NX6B/wDN//9UUTj/HqG5/0xdS/9NXEr/HqG4/0lhUv9LXk3/NX+C/xykvv8Azf//AM3//wDN//8Azf//Nn1//zp3dv8qj5v/WEsv/09ZRf8zgob/M4KG/09ZRf8Jv+n/RGlf/z1zbv82foD/AM3//wDN//8Azf//AM3//xKy0/8hnbL/IZ2y/yCetP8Vrs3/LoqT/y6Kk/8Vrs3/Asv7/xG01v8hnbL/ErLU/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8FxvP/OHt8/zh7fP84e3z/OHt8/wXG9P8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Nud//PHVy/0liU/8kl6n/JJip/0liU/88dXL/Dbng/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//Asr6/09ZRf9cRif/V00y/1dNMv9bRif/T1lF/wLK+v8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Cy/v/B8Lu/x+gt/8foLf/B8Lu/wLL+/8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Ex/b/BMf2/wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wDN//8Azf//AM3//wAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAD0AAAAwCAYAAACi/HI3AAAEG2lUWHRYTUw6Y29tLmFkb2JlLnhtcAAAAAAAPD94cGFja2V0IGJlZ2luPSLvu78iIGlkPSJXNU0wTXBDZWhpSHpyZVN6TlRjemtjOWQiPz4KPHg6eG1wbWV0YSB4bWxuczp4PSJhZG9iZTpuczptZXRhLyIgeDp4bXB0az0iQWRvYmUgWE1QIENvcmUgNS42LWMxNDggNzkuMTY0MDUwLCAyMDE5LzEwLzAxLTE4OjAzOjE2ICAgICAgICAiPgogPHJkZjpSREYgeG1sbnM6cmRmPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5LzAyLzIyLXJkZi1zeW50YXgtbnMjIj4KICA8cmRmOkRlc2NyaXB0aW9uIHJkZjphYm91dD0iIgogICAgeG1sbnM6ZGFtPSJodHRwOi8vd3d3LmRheS5jb20vZGFtLzEuMCIKICAgIHhtbG5zOnRpZmY9Imh0dHA6Ly9ucy5hZG9iZS5jb20vdGlmZi8xLjAvIgogICAgeG1sbnM6ZGM9Imh0dHA6Ly9wdXJsLm9yZy9kYy9lbGVtZW50cy8xLjEvIgogICBkYW06UGh5c2ljYWxoZWlnaHRpbmluY2hlcz0iLTEuMCIKICAgZGFtOlBoeXNpY2Fsd2lkdGhpbmluY2hlcz0iLTEuMCIKICAgZGFtOkZpbGVmb3JtYXQ9IlBORyIKICAgZGFtOlByb2dyZXNzaXZlPSJubyIKICAgZGFtOmV4dHJhY3RlZD0iMjAyMi0wNi0xN1QxMDo1MTozNi4zMjFaIgogICBkYW06Qml0c3BlcnBpeGVsPSIzMiIKICAgZGFtOk1JTUV0eXBlPSJpbWFnZS9wbmciCiAgIGRhbTpDb21tZW50cz0iU29mdHdhcmU6IEFkb2JlIEltYWdlUmVhZHkmI3hBOyIKICAgZGFtOlBoeXNpY2Fsd2lkdGhpbmRwaT0iLTEiCiAgIGRhbTpQaHlzaWNhbGhlaWdodGluZHBpPSItMSIKICAgZGFtOk51bWJlcm9maW1hZ2VzPSIxIgogICBkYW06TnVtYmVyb2Z0ZXh0dWFsY29tbWVudHM9IjEiCiAgIGRhbTpzaGExPSJjZWNlOGVkOGQ2ZWE5MThhY2ZhZDBhZWQyNmQxZGYzNzc3OTIxMGZlIgogICBkYW06c2l6ZT0iMTUyNyIKICAgdGlmZjpJbWFnZUxlbmd0aD0iNDgiCiAgIHRpZmY6SW1hZ2VXaWR0aD0iNjEiCiAgIGRjOmZvcm1hdD0iaW1hZ2UvcG5nIgogICBkYzptb2RpZmllZD0iMjAyMi0wNy0wNlQxOTozOTowMi42NTdaIi8+CiA8L3JkZjpSREY+CjwveDp4bXBtZXRhPgo8P3hwYWNrZXQgZW5kPSJyIj8+aSpnmQAAABl0RVh0U29mdHdhcmUAQWRvYmUgSW1hZ2VSZWFkeXHJZTwAAAWZSURBVHja7JpraBxVFMfPnZ3d7G6STXdT2/hCGq3FCmlL0JaiVBNRabFUP4hSKwgVPyj6QVChHyoI/aZQC74VrKKg32yl9f2qNmDxge9og5gqzaNpHpudTebl/2bumt1kdnY2OQtq9sAvzJLZO/Ofc+65555Z4bouLTXTaAlaXXRddF30/8v0woFr5MnuPYkjsZBx0iADEmqAKTAGBuXQfl8QMTzxtnL/nbE4OAc0qfu0waQa06jq7lwHIyRJtLSXirZ7+2h0/bXK+SLMw7oa3AA2g/Yi0dKmleg/wQnwDvgAnP0nxC4gSu7DgVUi/GJwI+gCHUWiIwB3TlkwBH4AH6pxf64o2sqTtqKTYjveLxU9G+2BouXT3wXuAZ0Bl4mpG5asB7tBPzgInp55GIXLeJeSD+4BsFWJLDcVUwr5cLYrjx8FT4KPA2exEOXmtAiiGxwDz4HOCuf6cSHYA+B5cZ/ryhvRluPP8+BTcCtoqnJMRJa4GXwEXlXXmH+eECWODJvIHgXvVvBuWGtzSTugJ6cPC9v+hCJitwrfxdpO8LmacovK3jL8XwZ7uTK9g2Fi7QalNg1ti/UMrxVTmKoRwZWY4Wk6BO5ajOgXwZ1cdyQFN1yUp5buMyQiLokxk2JfIi9ZEK6xCY+Cl8DtCxG9l1MwJJKeMSnVdQZLhestQLg9kYXwb0c4RRfsBbCpGtHXKNF8hlmb2jICDzue4CK/aIN50k+OI+ez1kpJ5fHmMKIbwP6FVin+XtYocXmW9JVYvk3/BU7vGycxbnJ7/DLwcBjRO1VhwGSCtLhNyY5xr07zP2Um5KMQTjp7mN+vElxZ0VF1EnHO5YbVOdKaHK+mClgntAGDxAS7t2V43x0kWk78dazPGfcfvyTnH9ZzvW25FDltcC5hBbtNVZO+orcRs2I9bc5QkryCvD0M0fwtrNVgQznRV3GHtr4CySvqBu2mSrytTZokDLsWm97NfqLl9nAV+941PR1OcCHETTwqwyrZIDBZh5/ojBLO26VotoMT2PzwIJG3a1GsnO8nOlE82dlW6KhT/ddMh2pgKT/RgrMg+Te3xopFy26HyXsdQa69gIwUqUnrLucnWrZ3xrmv5BhadfEjz23Qwie/8DboJ1r2nv7ivpJ9Nlrd8oONiZPAgu2wq/7FT7StmnisZg7FwmdvnOfGdXITkVoUKD3lipOjvDPaIWs4Ss5EJFxDSK5uGSwgUfbwxiaejpcT/R4YYJ3TpkZT/QlvKxNG98pEuJK1OpPOHC4nWvalX+FdJ1zK/9To9bdFsJfdZTFyWuFpm32dfqrSflo2EEY5CxRrJEb5vkavPREg2lqVohqkbdko/KKS6FPgMebVmiZPpMjNa/5XRHXgIKzttsTM9pLR5GugR+bqLLeY7Ffzm83bzoRO2ePp+d6WGbshQubatNcw5LWHwI/gFrC2kmiZSmQntJczkxu9Scp90+y17NTmghxB5rqMt0zxrs3PFs3lQ8VagsqG0+S9L+rjS2oOTfYsI+P7Js/jUvCGVrKXx7k3Ga+De4s+y+6cFUZ0oYrpnpsIFuvx7Gdpyn3XMmpubHUszGMxzSr4CXAHBSx8YQrE38H1ajCLSfgRoz91hd0a3y5MhyuSZAKWndwHqUINqFWRBeVgW8BhWnj58JXywlYRcX5D4nobxxvBvuINQZU2Ah4HV4LXQnVzZlOXjbwyRhXeT8swv0ndqOwwXgcuJe99dDn7AxwDb4AjagtL7pg6slApubQHRwdUlt1B3tvRTMCYso74GrwF3iTv5X/ABsAA2dlIK/x4zhkYovwzB6vtI8jiUr4gX0NeQz2lBsipRCgz5q9+W1bRgi93lQ3E89SY8hcOreqhmsqrfSrXnApfC1skGs+lyJpdpaKXktV/UlUXXRddF/2ft78FGACJ+I9vjeK39QAAAABJRU5ErkJggg==
- data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAASABIAAD/4QBMRXhpZgAATU0AKgAAAAgAAYdpAAQAAAABAAAAGgAAAAAAA6ABAAMAAAABAAEAAKACAAQAAAABAAAA+qADAAQAAAABAAAAUgAAAAD/7QA4UGhvdG9zaG9wIDMuMAA4QklNBAQAAAAAAAA4QklNBCUAAAAAABDUHYzZjwCyBOmACZjs+EJ+/8AAEQgAUgD6AwEiAAIRAQMRAf/EAB8AAAEFAQEBAQEBAAAAAAAAAAABAgMEBQYHCAkKC//EALUQAAIBAwMCBAMFBQQEAAABfQECAwAEEQUSITFBBhNRYQcicRQygZGhCCNCscEVUtHwJDNicoIJChYXGBkaJSYnKCkqNDU2Nzg5OkNERUZHSElKU1RVVldYWVpjZGVmZ2hpanN0dXZ3eHl6g4SFhoeIiYqSk5SVlpeYmZqio6Slpqeoqaqys7S1tre4ubrCw8TFxsfIycrS09TV1tfY2drh4uPk5ebn6Onq8fLz9PX29/j5+v/EAB8BAAMBAQEBAQEBAQEAAAAAAAABAgMEBQYHCAkKC//EALURAAIBAgQEAwQHBQQEAAECdwABAgMRBAUhMQYSQVEHYXETIjKBCBRCkaGxwQkjM1LwFWJy0QoWJDThJfEXGBkaJicoKSo1Njc4OTpDREVGR0hJSlNUVVZXWFlaY2RlZmdoaWpzdHV2d3h5eoKDhIWGh4iJipKTlJWWl5iZmqKjpKWmp6ipqrKztLW2t7i5usLDxMXGx8jJytLT1NXW19jZ2uLj5OXm5+jp6vLz9PX29/j5+v/bAEMAAQEBAQEBAgEBAgMCAgIDBAMDAwMEBQQEBAQEBQYFBQUFBQUGBgYGBgYGBgcHBwcHBwgICAgICQkJCQkJCQkJCf/bAEMBAQEBAgICBAICBAkGBQYJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCf/dAAQAEP/aAAwDAQACEQMRAD8A+mv+C9X/AAXn+L/w5+L+sfsS/sTay3h1vDzfZfE3ia0x9ta9xmSxsZOfIEGds0y4lMoKIUCEyfxteNfip8T/AIk38uq/EXxJqmv3U7F5JtSvJ7qR2PVmaZ3JPuTTviv42v8A4l/FLxL8RtVlae68QarealNI5yzyXc7zMzH1JYk1wFf6GcI8I4TKcJChQguayu7at9W3/Vj+P+IuIcRmGIlVqydr6Lol00CiiivrD58KKKKACiiigAooooAKKKKACiiigAoorrpvh/49tvBEPxMuNEv4/DdzdNYw6q1tKLGS6Vd7QJclfKaUKNxQNuA5xiplNLdlRi3scjRRRVEhRRRQAUUUUAFFFFABRRRQAUUUUAFbOi+IvEHhy6F74evriwmHSS3leJh/wJCDWNRSaTVmNO2qP31/4Jh/8F8f2r/2L/iRpXhn43+I9T+IXwuuZkg1HTtVne8vLGBjg3Gn3EzNKjRD5vs5cwyDK7UYiRf9Kzwp4p8PeOfC+m+NfCN3HqGk6xaw31ldQnMc9vcIJIpUPdXRgwPoa/xXq/b34T/8Fd/jX8NfhZ4a+HOleIL+G18P6VZ6bDGjkKkdpAkKqvHQBABX4vx54R4XM68cRhl7OWvNZLXazt3316n6Xwn4hV8DSlRrvnWlr9O/y2P/0P5N6KKK/wBOD+Hword8MeGPEnjXxHYeD/B1hcarq2qTx2tnZ2kTTT3E8rBI4oo0BZ3diAqqCSTgV/Ux+zZ/wae/tYfE7wZbeK/2g/HWkfDe5vIxKmlxWr6xeQhlyFufLmtoEfPBEc0uPXPFfP5/xVl2VxU8fVUL7btv0Su/wPYynIMZjpOOEpuVt+33uyP5mfgp8H/HX7QPxd8NfBD4ZWv23xB4r1G30uwiJ2qZrmQRqXbB2xrnc7HhVBY8Cv7r/jv/AMEt/wDgnb/wSH/4JY/EP4i/EHQdM8a/ES58O3Ok2/iHXoI7mabXdTga2thpttNuS1WKVzKvkjz1ijZ3kbaSPz2+Ff8AwQW/4Kh/8E1f2u/CX7Tf7MWleFfjQfDc1y9nFNeDTVVrm1mtPMu7e8lt9vl+d5iiC4lO5R9K/Q79oj/gij/wUs/4Kj3Nj40/4KHfHPQvCK6cGk0rwr4V0mbUNM09pRhifOurTdNjhpGe4bHyrJsxX47xlxlhMbisO4Y6MMKrSlytucnf4eWKckrJb2Wr3sfo3DfDeIw1Csp4VyrvSN0uVK2927X9LvTpc/z/ACiv3+/4KK/8G8H7Xn7B/gO9+NXhvUbP4leBtLQyahfaXDJbXtjEPvT3Ni7SYgH8UkU0oQZaQIo3V+ANfteS59g8xo/WMFUU4+X6rdfNH5lmeU4nB1PY4qDjL+tuj+QV/Sv8QP2rpf2Hv+Cc37J+q/Dn4afDzxHN440XxFc64/ijw1Z6pJetZau0USyTOFm2+W5U4fOAACMCv5qK/fVvjf8A8Et/2iv2K/gD8Hf2ofG/jXw1r3wh03WLO9s/D2iwXa3Y1LUWu8R3NxOiIwQIAShGScjivF4uw8ZvDupTc4Kb5kk3pyTS0X95r5nqcO1nBVlCajJxVm2l9qN9X5XOe/a1/Ys+H37T8P7On7SP7DvheHwcP2lLq90OfwkJmNlpXiLTbxLS6e2kfJjsJjJ5qJg+SiNgAERrkfEj/glD8G/+EM+Junfs6fFi/wDGXj34O6Xd614h02+8N3GlaZe2WmOE1OXSdQkuJBP9jJyBJFGZ0BePisT4j/8ABVnw9pH7THwM8S/sx+DpfD3wl/ZzuVPhXw7fzq95eLLcCfUru/njBUXmoYzJs3pE2Cu75i303+1F/wAFGfgf4x+HvxF8UeAv2kfjj4nufHNtdQaN4Dvbh9P0/SDqBIlh1O9N3dR31nDE7xrDBDGZBtVmAJcfNwlnVH2NKPMo62+0/jdozdpbQsr80db+82ke1JZZV9rUlZvS/RfCruKut5XdrPpokfMvw/8A+CZP7Peifs0fDf4+/tZ/FjVfAq/FqK5n0W507wzNq+jadFDO1sjatqCXMQjeR1yYYY3eNSGbuB86fs4/sNeC/iL4W8e/Hf48fEK38H/Cb4d6nDo114h06yl1WfVtRuXcW9rpVoWtzKZY42maSV4xFEVZlOSB+h//AATu/b1/Zh/ZY+HngvVYfjb8TfBY0SV5vGHw8OmWviHQPEf73dJHp3nT28Fil3F+7mM0LSKzErJ8qufmv4cftofsqfFbwd8ZP2Vf2gtL1H4e/DL4leNz478NXfhu2ivn8MagrzRx28li0lutzaGzmEBETxshQFFIOE644zNuavF8zSkteVaR5nfli46tR6p1E9/i0fPLDZfy0muW9npd6vl05nzaJy8otemq8B+Jv7H37NugfHzwH4R+HHx40DVvhv48tVvj4pu4XhudDiUuLiDV9Khee4guo9mIo922fchVlViV+zf22fgrovxQ/YO0D40/s9/FvUfHPw6+CN5a+FBoep+GB4ZS0XVjJKmpWqxzSpdm8mQ+fLL/AKQTtMjHAFcb8C/2kP8Agmf+yV+3f8NPHnwn0LX/ABL4G8JabdWmt+I9WtoX1C91e7gmjj1e00maSW2hSxd43ghdi52FjmQKT71+1b/wUh+C3j/9g/4n/sqN8X/H/wAZ/E/iPXdE1TTdb8WWn2O0SC0nkee2tbQ3VybYRrtZpCy+ezACKNYgXzxVfMJYrDckZtJxd5RWzk4ybSg7NQ396Ds/h+JF4ejg1QrqUopu+ib3STSV5apy8pbb7M+aP2uP+CafwC/ZX8P6X4PHxbuPE3xX8X6T4e1Xw14Ts9FdFlTWvs+9b2+M7Q27gyTeSi7i6xKz7PNUD6T8J/8ABFv9l3xL+1jo37Af/DRkX/C4o5hFr9hH4fnOmQypbG5urSwv2uFW5urZQSVkSFJAGUMkq+U3w7+3r+2R4N+Nv7XvgX9oL9n+Scnwp4d8KWcLahF5GNS0O2iR8qX5jE0fDbhleeK/pM/Z9+GnwN1b/gsXoP7WfiX4T/FHwd8RNWnuNf8AEOm65aWkfhLQZJtMle91X+24nk+02p3EwKREPOky7rtEB8rOM2zPB4GFWtWkpunOW0L86UbJpx+Fa9L3er2R3Zdl+BxGKlCnTi4qcY7ytyu92nf4n+Wy3Z/Lj+zj+zZ+yZ4usvEuuftOfFq68IDSNT/srTdE0PRJda1rUWAYvciHzYIIbaMAZZpWZmyoUYBb9Y/2Gv2NJP2K/wDgrnb/AAlfW4vFmi6r8ONc8RaJqv2V7NrvTdT8P3U1vJLaSlmglHzK8ZZtrL19PEf2OP29v2e/hZ+yn4y+Ch+Iniz4I+NLvxnP4iPivwbpUV/ea7pTwiKPS5JTc2c9v5ThpI/3ywgvuILbq9l8T/8ABVv9l3xL/wAFMvCf7XDXPiGXw1pvwofwleS6lH9r1Q6rJpV3aHzpNy/aCZp18y4+Xedz7R0rrzqtmleeIoRhJwcJq1tL2XLa0Vvr9qXnbRGGWU8BRjRquUeZSi731td3v7z20+yvK+p+Lvw//ZNvtZ+Bkf7S/wAV/Ell4I8FX2rSaFpd1dwXN1c6lfwxrLcLa21tG7GG2R0M80jIillRN7kqOH/aS/Zs+IH7L/jqy8GeOpLW+t9Z0qz17RdV093ksdU0nUE8y0vrVpEjkMUoBG2SNJEdWR0V1IH6DfBn9or9jL47/sNeGf2J/wBs3Wde8B3fw317UdZ8NeJNC02PV4ZrTVgr3ljd2jT27rIZUDRTI5XGAwG07/BP+Cjv7WXw2/aj+JXg7Rvgbpd7pfgD4XeEdN8E+HP7U8v+0bqz03zGN5eCImNZp5JXYojFVXGOSa+twWPx0sa6VSDUbyvp7qivgal1bW6u7a7WV/nsVhMLHCqpCSvaNtdb/aTXRLo7a6b3O3/Zg/4J/wDw/wDH37N8v7X37UHjbUfBXge61p/DuiwaFosmu6tqd9DEs1w626zW8cFrbq67ppJDufKKucE+3+Gf+COV7rX7d+m/sh3PxBtk8PeKfBc3jvw14sNjJFFe6SbKa6tpbizmkWW0LPC8U6szNCUY4fAz2P7DX/BRvwZ4T/YxT9i74g/FXxv8C7zQvEVxr2j+LfBcct2lxb3karc6fqNnDdWkrgSL5sEiSEAkhlGPn0/AP/BRz4E+FP8AgojL8dfEHjL4geN/B2l+BdX8K2eteM7ganrN1dXun3EQkWJWxa2j3U7NHB5khjUlmYsxUfOYvF537bEqndWU+Vct105Gny2b7rml1ulZHtYbD5Z7Oi521cb66/3k/e287Lpq9T5v+Mv7AP7OA/Y41/8Aa4/ZB+L8/wARLbwBq2n6R4ssdQ0OXRnhOplktbuzMk0plgklUoquqPgFm2kba+Rv2K/2SfGn7bP7QOmfAnwbf22ji4gutQ1HVbwM1vp+nWMLT3V1IqAu+yNSFReXcquVB3D2X4CftM/DH4d/8E7f2gP2ZvEb3Q8T/EfUvCV1o6xw7oDHo13cTXXmyZGwhJF2DB3HI4qh/wAEyP20LD9hH9q7TvjX4gtL680O60+/0TV10qUQajHZajCYnnsZSVVLmB9ksW4gEpt3LncPeTzGlhMVCDc5xb9m5JXfuRa2STtJtLTpZnkNYKeIoSklGMkudK9l7zXVtrRJ/M9g/aA/4J4/B/Rf2ZPEX7VH7JfxD1XxxongPU7HTPFFnr/h6Xw9eWyamzRWV/bK9xcJPazzIY9u5ZYiV3KQcjrf+C3UEFv+0r8PUgRUB+FXgskKAOTpq5PHeuy/bX/bN+Gfiz9m/VfhP4K/aP8AjB8a9T8TX1tI1r4mlk03Q7HT7eQT+VeWktzeNf3XmpGUdGiiQrvxkBT8n/8ABTD9pn4Y/tU/Gbwl45+FLXT2OjeBfDnh+5N3D5L/AGzS7MQXAVctlN4+Vu45xXm5JDHVMTSrYm7S9pZtWdmoWv7seqlb3Vp33fdmksLCjUp0bJvk0TvreV7ay6Wvq/lsvzsooor9CPjgqQSSAYBP+fxqOigD/9H+Teiiiv8ATg/h8/rL/wCDTn9lvw38Sf2mPHv7Tviyyjuz8O9NtbLSTMgYRX+rtKGuIyekkVvbSR57Cc98Gv79a/jt/wCDQbV9Km+DPxr0KEr9utta0i4lAPzeVNb3CxEj03RSY/Gv7Eq/hjxlxlSrxDXjPaPKl6cqf5tv5n9TeG+HhTyek4fau363a/SwUUUV+XH3R/Jf/wAHOP8AwU8+I/7N/hXQ/wBiX4EajJo+teOdMl1LxDqMB23EWjyPJaxWsLjlDdyRzea6lXVIwo4kOP4D6/rc/wCDtL9nLxvoX7T3gT9qeC2kl8MeIvD8fh+S4AZkg1HT7i4n8tz91POguFaIZ+cxykfdNfyR1/dXhBgcLSyKjPDJXlrJ9XK7vf02R/LHiLiq9TNaka20dEvK3T13Crmnadf6vqEGk6VC9xdXUiwwxRgs8kjkKqqo5JYkAAdTVOv2z/4N9v2Tv+Gqv+CmHg1tYtvtGg/D/f4u1LcMp/xLmT7Ghzwd168GVP3kD8EA191nea08Dg6uMq7QTf3dPnsfKZZgJ4rEQw8N5NI9D/br/wCDe39qT9g/9la6/ap8b+JdF17T9Llso9TsNNW48+0W9dYRIzugRljneONip5LAjgV+BNf6P/wE/bR8If8ABU/9pf8AbH/4Jt+NrxJvDBtpLDw0eH2W1rCNI1K4iPcJfiG6hI4zJkep/wA7L4i+AvE/wq+IOu/DDxtbm01nw5qFzpd/AesdzaStDMnb7roRXw/h1xHj8WquFzW3to8stFb3ZxTX3O6fmfVcZZLhMO4V8B/DlzLv70XZ/fo0cbRX9Rmj/wDBtD8Q/id+zX8Evjl8FPHqX1x8T9P0rWNbXU7IWlh4f06+0s6jPcSXCTyPN5TlII0EaGRnBJRQxX2jS/8Ag2V/Z/8Ajb4F1SL9jv8Aam8O/EDxhocf+lW1vHaXFkJiCBHO9hfXU1oGYEBmSUjH3T27avihkkPirbOz92WlnbXTTXa+/ocsOBc0ltT6XWsddL6a66dj+Quiv0i/ZW/4J0eOvjH/AMFINI/4J0fHG4uPAWvXGo3+m6lN5C3clpLY2U92CkfmRpKkohGx1k2sjh1LAjP7J6r/AMG0Wg/Cz4ueLrj9p/466N8NPhNol7a2Gi+I9dS2srnW5prKG5m8qK5vIoII4pZHhDGaR3aJ8RgfNXp5pxxleDqKjXq2k4qSsm7puytZO930WttdjhwPC2OxMHUpU9E+V3aVmld3va3q/Tc/lKr6EvP2t/2q9R+F6/BHUPiZ4rn8GJELddBk1m+bTBCOkYszN5OwY4XZgelfuD/wUO/4N4vG/wCy1+z5L+11+y54/tPi98PrK3F9fyW0KRXNvZHreQtBNcQXdsnWV42Ro1+bYyK7r/N1XZk+dZfm1FYjDSU0n1Wqa8mrp/I58xy3GZfU9lXTi2u+jXqtGj7I/Yl/YM/aV/4KC/Fg/CL9mzRRqF3bxi41C+uX8iw0+Bm2iW6nIbYCeFRVeR8HYjYOP6NNF/4NKPiE0Mej+Lvj14esPEUkW9dOttMluAW/2XkuoJSn+15H/Aa+sP8Ag2IEeuf8E2Pjv4S+A97Z6d8XJtWvhb3ExUtC0+kRJos0wwT5CXYuSMqRkSYz0r+RL9p79m/9tz9nD4n3uvftUeGPE/h/xIb0zyaxqiXDG4uQ+fPi1HLR3B3DIljmcE9Gr4GpneZZlmuIwGExMaCpWSTipSldXvaTWnofWQyvBYLL6OLxFB1faXbfM4xjrtot/U9P/wCCh3/BMf8Aac/4Jp/Ea08FfHqzt7nTNYWSTSNd01nl0+/WPHmKjuqPHNHuXzIpFVlyCNyFWPyL4b+Bfxt8ZeBdQ+KPhDwdrmq+GdJ837dq9np9zPY23kIJJfOuY42ij8tGV33MNqkE4BFfrp+1N/wWy8Zftj/8E6/D37EHx48ELrfiTw5JZTweN7jU2kunnsndFmktTa5aSS0doJHNwS5JlbJO2v63P2E/2Iv2UfhP/wAEivi5+zZ8Ovjxo3jDwL4tGuvq/jW1azNno7X2lW1vcrMYruSEfZYkWZ98yfK43bRgnXM+OsdlGApyzWkvaufLpdqUU176te109IuzbvZE4HhXC5ji5xwE/wB2o313Ts/d1tfVbq6Xc/zW6K+4v25v2XvhJ+zr+0z/AMKM/Zi+Ilp8ZtJmtrJ7TWdGWGVLi6uuDaxraTXKtIr4XarliSBgGvsSy/4IX/tPeH9B0rUP2i/H3wz+C+q67Ctxp+hePPE0WmarPE+djC2jiuNmSMYkZCrfKwVgQPvKvEuBp0qdapU5VNXV7pv/ALdtf1006nyVPJMVOpOlCF3He2qXz2/HU/FmivsP9sX9g39qD9g/xraeC/2j/DjaWNUjM+majbyJdadqEIxmS1uoi0cmAylkJEiBl3qu4Z/YD9kT/g3t8Vftof8ABPvwd+158KfHLJ4m8Xak9kuh3NgBZ2sEOry6dcXMt4sxfZDbxPckCHLEeWOSCccx4ty7C4aGMrVV7ObSUlqm3fqr9nrsjTB8PY2vWlh6dN88VdrZ2Vu/qj+byiv3I/by/wCCQXhP9n/4tfCb4AfsbfEm3+OnjH4jTahY3FnpQtF+yXlkbbCsIbq4EKMs0juZ3URpEzM20MR+hkP/AAbifsufA/SdJ8O/t1/tV+GfAHjnW4Vlh0hWs4Y03ZA2SX93by3CbgV8zyYVLfKOevm1/ELKadGnWlUfv3cUoycmk2m+W10rp6tI7qXB+YTqTpKC9213dWTava97X16Nn8ldFfrx/wAFRv8Agjr8fP8AgmPqel+I/EGo23jP4f8AiGTydL8TafG0UbTbS4t7qAtJ5EzIC8YEkiSICUclXVfyHr6TKs2w2OoRxOEmpQezX9aejPEzDL62FquhiI8sl0CiiivROM//0v5N6KKK/wBOD+Hz+i//AINmf2ytG/Zn/b4b4SeN7tbTQPi1ZLogkkYJGmrQyebpzOT/AM9GMtsg7vOvQZr/AEka/wAUizvLvTruLUNPleCeB1kjkjYq6OpyrKwwQQRkEcg1/ok/8EhP+Dgf9nv9oT4Lad8Lv21vGGmeB/iV4et1t7jUtbuI7HT9aiiAVbtbqYpBFcsMedC7LufLxAqxSP8Ambxw4Cr1qqzfBwctEppavTaX3aPtZeZ+3+F3FlKnTeX4mVusW9td1+q76n9N1Ffhl8f/APg4u/4JZfAbXP8AhG4PGd144vE/1v8Awitob+CP0/0p3htpM/8ATKV8d8V7D8Bf+C5v/BLb9oDQW1nR/i1pHhmeIZmsvFMg0W4jPJwDdlIpeP8AnjJIO3XivwWpwZm8KSryw01F9eV/5H6vDiTL5VHSVePN6r/M+0v2yPCX7NXjH9mXxlZ/tf6bZap8OrLTZr/Wor8Hy0gtFMxkRlKukqbcxNGyyB8bCGxX+Px4rvdA1HxRqWoeFLJtO0ue6mks7R5DK0FuzkxRNI3LlEIUseWxnvX9VX/BwP8A8FvvBf7WGiD9jP8AY/1R77wLFcJP4j1yMNHHq00D7obS2DAM1pFIokeQgCaRU2fu03S/ybV/Vfgpwni8twE62LunUaai+iXW3Rvr1sl6H4J4m8QYfG4uNPD2aho5Lq+1+y/O4V/fL/wbP/sj+MPhx/wTy+If7TPhqS10nxp8VXurPw7fX4PkQW+lxy21pNJgFhGdQecyBQdyxp14x/Bt4Y0KbxT4k0/wzbXFvaSajcxWqz3cqwW8bTOEDzSuQkcak5d2IVVBJOBX9cf/AAXx/ap/Zr+Hv7AvwS/4Jxfsd+OND8Y6LpSQSatc+H9Qtr+MQ6LbrBbrcvaySKHu7iZ7hlJ3F4tx68+x4l0K+Ojh8mw+ntpXk7XSjD3nf1drJtXtY8/girSwrrZlW19nHRXs3KWmnyv00ufY/wDwTT/4IH/tVfsDftq+F/2pbr4seFtYstPe5g1izh+1ia9s72F4pk3OmC4ZllXccGRFya/Gn/g5v/ZO/wCFAf8ABQ6b4waFbeTofxY0+PWUKjEY1K2221/GPViViuHP964/L+dAEg5HUV/ZP/wUx/aO/Zt/4KRf8EOvhp8YNX+IHhpPjN4Cisru70S51azj1q4lQ/2XqsaWUkouMXDKt8oCZaONSucjPjVsszLLM7w2YYqt7VVL0pNQ5bJ6xvZv7XV7I9KljsFjsrr4OhT9m4e+ry5rvaW6XTp1Ppb/AIKo/Fz4g/C3/g2q+Amk+A7mazi8Y6B4F0HVZIDtY6fJoJu5IywwQkslrHG4H3lYocqxB/l9/wCCM3xb+IPwe/4Kd/BjVfh5czQy614n0/Qr6OJsLPp+qTpaXUci9GQRyGTB+6yK4wygj+zv41+M/wBjfS/+CHf7Nvwp/btF1afD/wCJPhnwb4cl1mz/ANdot4fD/wButNQXCSMBHLaBGIRgFkO9Wj3qfhz9ij9h3/gi7/wTB+IEP7b/AMQf2nPD3xHu9AimuNBghurFvIeWNl81LCyuLu5u7lY2Kx7VARju8sOFKfJ8N8Q4fC5Pi8JVoylKpOoo2i2pt6Wuk0mno0+lmtz6HOcmrV8xw+JhVSjCML3kk4212ffpbqeu/tV+C/Dnhj/g6t+AWvaJGkd14j8Itf6gVA3PcR2Ou2au2Op8i2iUZ5wo7Yr8Ov8Ag5++LfxB8b/8FOtT+GviS5m/sPwVoumW2kWxOIVW8tkvLiZUHG+SWUo743ERqpOFXHuf7If7ct5/wUO/4OUPAX7R0VrLp+i3F1qOnaHZz482DTLPRL9IBJtJAklJeaRQzBXkZVJUAn9Q/wDgq98Bf+CYP/BRH9tvxB8EPjj8UYfgX8YfhxFp9gNU1L7ONP13Sruyh1GLm4ltojPA908Sjz1kwPuyIVEemVyeT5xg/r0G3DDJSsnJw9962V3pfldr79jLHRWY5difqskuas7Xdub3Vprprvr27nk3/Bpz4z8SfFj4B/Hf9mT4gmTVPBNhJpslvaTnfDH/AG3DfQX8KhuiTJbRsUHy5LNgFyT/ABEaxZwafq91YWsnnRQTPGj/AN5VYgN+IGa/uS8fftX/APBN7/ghp+wH4q/Zu/Ye8f2fxM+K/jNJ86hp91b3zre3EPkC9vJ7Qtb28NnGc29rvLs+ODvllH8LdffeH8J18fjs0hBwpVZR5bqzfKmnKz7t/M+T4ulGlhMLgZSUqlNS5rO9ru6V/I+r/wBlv9of9rT9jbxjF+0P+zNqmreGriBTHLfW8LSWVxDuw0N0kiPbzxb8fJIGAcAjDAEf0gfAn/g7Q+NdrbxeGf2tPhXofi7TJl8m6uNFlk0+ZozwzPb3P2uCZiOqAwqf9muE/wCCIf8AwVB/ZI0H9lzxT/wS9/4KGSJp/gPxO93/AGbqtx5gtFi1ED7RZ3MkXz2xEoM8Fxjars2502oT7Dqf/Buv/wAE2dT10+PfCn7YeiweBGfzRHLLo9xOIM5x/aSahFBnbn5/suO+3jB8bijHZNWxdShxBhHFx+CaUnzR6WlBXTXZ6I9LIsLmNLDwq5RiE0/ii3Fcr66SdrefU7//AIK5/sQfsC/tdf8ABM5f+CuH7C+gQ+E7q3SC+u7axtksYr62kvl0+7iurKI+TFd2lwzM0sXDhJMmUNG4f/wSP/5Vrf2n/wDf8Zf+o/Y14r/wVq/4KO/sPfBT/gn3pn/BIz/gnBqg8UaHEILfWNbhk+0WqW0F19vlVLsKqXVzeXYEs0kI8hVLqv3gqX/+CBn7Wf7Ger/8E/vjL/wTe/ap8eWHw8uPG91qcltf6pcw2MMtnrWmQafL5FzcFbcT27wbwkjAvvXaHAfb83LB49cOOdWM3CNZSgpJuapJq11v3+Xke2sThP7Z5acoqUqTUmtIubTvZ7f13PmP/g1k/Z+8DfFz/goHq/xJ8bW0d7J8PPDs2qaXFKAwTULieG1jn2nIJiieUr3VyjjBUGvyI/4KcfFDxz8X/wDgoR8ZfGfxEuJp9QHi/VrFUmOTBbWN3Ja21uPRYIYkjA9F9a/R34L/ABs+HH/BB7/gqbb6p8G/H9l8bvAMmkx6fr+o6GbYLcWWoFZZoofJurqH7RaSxRSAGYbymxvLDkj9WP2nv+CdX/BHP/gpp8XL/wDbR+Cv7Unh/wCHMXiyQajr+lXz2Subpxmeb7PfXdjcWckrfPL5qSKZCzrw2B9ZVzuGDzuWa4mMnQq04qElGT5bO7i0ldX31X6nz0MrnicrWAotKrTm3KLklfomnezttuZH7PPhJP2xP+DXHxnY/Gofbbn4VTavd+Gb65w01uujbLyFYnPO0pNNZgHpE2wcBcdz8OfHPiv4df8ABoPfeJPBd9Lp188F7YGaFij/AGfUPGbWVygYc4kgmkjb1DEV8m/8FQv+CkX7GX7PP7A+n/8ABIz/AIJnaqfEuh7Fg8ReJo2EkMkPn/ap447lVRbq4u5/mmliXyEizEhIbEXQ2P7Rn7Pif8GpF1+z83jvw8PHrSZHhs6paf2uf+K2W64sPM+0f8e/77/V/wCq+f7vNfKVMtxNSjSrzpOMKuMjOMWtVB3u2ul92n69T3442jCpUpRmnKGGlFyT0clbRPrb+tjyb/g0z8F+G9e/b38Z+LNXt1nvtC8F3L2LOAfJkuL60hkkTuH8otHkfwuw717D+2x+xL/wSW+PH7W/xF+Kvx2/bQaw8Warr98dQsJtKeU6fJFM0QsFYtnZZqgt09FjAr8Lf+CUP7f+p/8ABNz9sTR/2gWspdU0C4t5dH8QWMBAmn0y6ZHk8ncVXzYpIopowxAZowhZQxYf0Q/tL/8ABNH/AIJGf8FNfixqP7YP7Nn7Unh34dHxlOdT1vR9SFo7i8nO+4mFrd3un3Vq8r5kkWRZFaQsykKQB7vE9Crg8/njq9WdKlOCSnCKlZreL92TV91Za/l5WRVIYnKY4WlTjOcZNuMpcuj+0vejfs9f+D0P7Xv7Sv8AwTZ8K/8ABDXX/wBgTwF8ebL4teIfD1rbf8I7NcQTQ3rtDqsV1DFGGRlUW8BeFfnH7ldgwOK/iYr+jD/gqnr3/BI79nL9mjQf2Jf2D9M0r4iePLaSNvEHxFVVuJUWGUzSRw3iYillnkwuYC0UVuPK3MzHb/OfX2Xhzl8KODqVYKdqk5S99JN3trZJWTtdKyZ83xnjJVMTCEuW8IqPuttK19Lu92ttwoopcGv0A+QP/9P+Vjxd4euvCXizVPCl8Cs+mXc9pICMENDI0bZH1Wuer+lH/g4J/wCCSnxT/Zh/aN8TftbfCrRp9U+Fvji+l1a5uLSMyDRtRu3MlzDdKg/dQSTMzwSkCMBxESGUb/5rq/0c4cz6hmWDhjMPK6kvufVPzR/GedZTVwWJnh6ys0/vXRryYUUUV7h5YUUUUAFFFFABRRRQAUUUUAf0hf8ABR//AIKgfst/tP8A/BIj4B/sX/C6bVH8a/DpfDI1dbqz8m1H9laDcadc+VNvO/E8qhflG5cmv5vaKK8XIshoZdRdDD3s25a927s9PNs2q4yoqta10ktOyP0R/wCCT/7S/wAMv2PP+Cgnw6/aQ+Mj3UfhrwzPfyXrWcPnzgXGnXVsmyPK7v3kq55GBk9q6D/gsD+1T8Kf21f+ChPjr9pP4JPdyeGvEEelLaNew/Z5ybPTLW0l3R7m2/vYWxzyMHvX5nUUPIaH9o/2nr7Tk5PK1+bbvcP7Wq/U/qOnJzc3ne1vusFFFFe0eYFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFfeHg/9iD4m+LPCWl+KrC3kaDU7SC7jIjYgpNGrrzj0NL/AME/f+CeH7Qn/BRT42WPwq+DGlzLpiTRnWteliY2GlWpPzyzScKZNufKhDb5WGFGAzL/AKpPwr/ZY+Bfwi+GHhv4T+GvD1lLp3hfS7PSbV7iCOSZoLKBIIzI5XLOVQFm7nJr8v468TcJk1aFCT5pO7aXTa1/XU+64V4IxGZU5VVpFbN9e9vQ/9T+/K5tre8t5LO8jWWKVSjo4DKysMFWB4II4INfz/8A/BQX9iT9jHSNT/tTSfhF4Ltbm5Ikmmh0DTkkkZsEs7LACxPck5Nf0DV+S/8AwUW/1sP0T+Qr9e8Jf94qfI/PPED+FD5n4Jf8Mpfsuf8ARNfCv/gnsf8A4zR/wyl+y5/0TXwr/wCCex/+M177RX9BH5EeBf8ADKX7Ln/RNfCv/gnsf/jNH/DKX7Ln/RNfCv8A4J7H/wCM177RQB4F/wAMpfsuf9E18K/+Cex/+M0f8Mpfsuf9E18K/wDgnsf/AIzXvtFAHgX/AAyl+y5/0TXwr/4J7H/4zR/wyl+y5/0TXwr/AOCex/8AjNe+0UAeBf8ADKX7Ln/RNfCv/gnsf/jNH/DKX7Ln/RNfCv8A4J7H/wCM177RQB4F/wAMpfsuf9E18K/+Cex/+M0f8Mpfsuf9E18K/wDgnsf/AIzXvtFAHgX/AAyl+y5/0TXwr/4J7H/4zTH/AGUv2XOP+LbeFv8AwT2X/wAZr6AqOTtQB8//APDKf7Lv/RNvC3/gnsv/AI1R/wAMp/su/wDRNvC3/gnsv/jVe+UUAeB/8Mp/su/9E28Lf+Cey/8AjVH/AAyn+y7/ANE28Lf+Cey/+NV75RQB4H/wyn+y7/0Tbwt/4J7L/wCNUf8ADKf7Lv8A0Tbwt/4J7L/41XvlFAHgf/DKf7Lv/RNvC3/gnsv/AI1R/wAMp/su/wDRNvC3/gnsv/jVe+UUAeB/8Mp/su/9E28Lf+Cey/8AjVH/AAyn+y7/ANE28Lf+Cey/+NV75RQB4H/wyn+y7/0Tbwt/4J7L/wCNUf8ADKf7Lv8A0Tbwt/4J7L/41XvlFAHgf/DKf7Lv/RNvC3/gnsv/AI1X1V+yh+xj+x74j+IkNl4h+FHg6/hJXMdxoWnyqef7rwEVyNfYX7G//JToPqv8658X/DkbYf40fvf4F+H3gL4X+GoPBnwz0PT/AA7o9rnybHTLaK0to89dkMKoi59hXX0UV/HGb/71U9X+Z/RuW/7vD0R//9k=
- data:image/jpeg;base64,/9j/4QBORXhpZgAATU0AKgAAAAgAAwEaAAUAAAABAAAAMgEbAAUAAAABAAAAOgEoAAMAAAABAAIAAAAAAAAACvyAAAAnEAAK/IAAACcQAAAAAP/tAEBQaG90b3Nob3AgMy4wADhCSU0EBgAAAAAABwAEAQEAAQEAOEJJTQQlAAAAAAAQAAAAAAAAAAAAAAAAAAAAAP/uACFBZG9iZQBkAAAAAAEDABADAgMGAAAAAAAAAAAAAAAA/9sAhAAGBAQEBQQGBQUGCQYFBgkLCAYGCAsMCgoLCgoMEAwMDAwMDBAMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMAQcHBw0MDRgQEBgUDg4OFBQODg4OFBEMDAwMDBERDAwMDAwMEQwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAwMDAz/wgARCAL3AZ0DAREAAhEBAxEB/8QBDAABAAMBAQEBAQEAAAAAAAAAAAYHCAUEAwIBCQEBAQEBAAMBAAAAAAAAAAAAAAYFBwEDBAIQAAAEBAIGCgMBAQEBAQAAAAAEBQYBAgMHFgggMDIVFzcQUBETMxQ0RDU2QBIYODEhQScRAAEDAgIDBRELCAcGAwcFAAIBAwQABRESIRMGEDEiMrMgQVFxsUJSYnKCk9MUdDV1NjBhkdGi0iNzNJS0gZKyM9QVlTdAUENTY4MkocKkFnYHwaMl8ESExGVGhuHDVOSFEgAAAwMGCggFAwMFAQEBAAAAAQIywgMQgqKy4jMgMFAREiJCcpLS8DFx0VJzg4RAIWITI0GBoUOjs1FhU2PD8uHT/9oADAMBAQIRAxEAAACyub3Xe180AAAAAAAAAAAAAAAAAAAAAAAAROd25ZRYlg2MuAAAAAAAAAAAAAAAAAAAAAAAAKj5zc9vVzrBsZfPZHAAAAAAAAAAAAAAAAAAAAAADyl6E9Kj5zc9vVzrBsZfLBqcAAAAAAAAAAAAAAAAAAAAAArk4pcBUfObnt6udYNjL5YNTgAAAAAAAAAAAAAAAAAAAAAFcnFLgKj5zc9vVzrBsZfLBqcAFOnfJIcc+xAi7ipDinJPSXgVSXQAUaXQRwqE+5dxSp5Syj5HEIoCaELPuXYdcoUvsr87xIgCuTilwFR85ue3q51g2Mvlg1OADEBY5aZCD2mODdxnk1GY7NgFSlBG8DrEZMKGnz2kJOucoqo1EZjLKLFKwJefQjJ2TiFoGOzZRWpYhZoBXJxS4Co+c3Pb1c6wbGXywanB5j8mKyyC0SEHvKaPGe42iYeNwmBiwSVmjTMJzCAGizORFjexiEtciROy3isycHOM5kVN5GWiRHFJqWIWaAVycUuAqPnNz29XOsGxl8sGpwV2ZlPYXyZ9PCauM7FvFAm5DDxpsoYu8zIbnMMmmjPpODvHyOaUaWiQYs4t8rMnBzjkAh5CzSBmsnhEiRmsT+lcnFLgKj5zc9vVzrBsZfLBqcA5p7z9nPPoew+J9j4H3Pgfo/R+zzn2Pkfc+Z8z6H0PMAeg+Z+z8H6B/D6HkPsfU+R+D8g9QK5OKXAVHzm57ernWDYy+WDU4AAI6VSXSVSXKZgNInpM0nHNMlNFtmbjpGlzOJpkosvUo0nJJyoi7wfAymfsvghhW59jVoAAK5OKXAVHzm57ernWDYy+WDU4AAIIYSNrlOl5mQTQ5+jyllnOMyHqNXEAImZxNSFXGxTD5JzURlo2KDxGNjXBjokpa5IyxAAAVycUuAqPnNz29XOsGxl8sGpwAAQQosgROTznyIIXeTAsU5Bk0+BuEghSpFT5nwL1KHImbZM4GxQeIxybTMLkqJmSguMAAFcnFLgKj5zc9vVzrBsZfLBqcAAEJKvPWQ0jhqgzkXAZ9PgacM6l2FEHyNVmcDRRk0kBpgrgj5TZPS/SamDCblmEOOKek1wfYAArk4pcBUfObnt6udYNjL5YNTgAAAAAAAAAAAAAAAAAAAAAFcnFLgKj5zc9vVzrBsZfLBqcAAAAH4MukdNFHHKOO6aPM0GsTOJJioixz7FqkAOiZ4NomQTSRTxDy0S8wAAAAVycUuAqPnNz29XOsGxl8sGpwAAAAVIQg0AQYy4boM/H5MxmwClz6k/OkQgvsqM7RmE00ZkNKEDNeGHTaZ7wAAACuTilwFR85ue3q51g2Mvlg1OAAAACmyNl8lfGXzd5QhyiNEUOmXYfQzOWaXgVISQqMrMsksciprIxGbJOmAAAAVycUuAqPnNz29XOsGxl8sGpwAAAAeYyUc00KRsqM+5qIpYsQqIkJXR3C6TN5+zUhUhWJc5MiizkE0NJgAAAArk4pcBUfObnt6udYNjL5YNTgAAAAAAAAAAAAAAAAAAAAAFcnFLgKj5zc9vVzrBsZfLBqcAAAAAAAAAAAAAAAAAAAAAArk4pcBUfObnt6udYNjL5HO8fwAAAAAAAAAAAAAAAAAAAAAEcLhLdKj5zc9vVzrBsZcAAAAAAAAAAAAAAAAAAAAAAAAVHzm57ernWDYy4AAw6fgGlzIBrw4Jmo1gZZPUW6fUpw+paBJzP50CzSUFAH8NjkpMOl5F4GOCPHmNFFbl9FJFZH1NeEuAABUfObnt6udYNjLgAD/PQ1yfomJgwuE4RAjVBW5pAwQXUSEsIyAX0RcuMkpmEmRLicHjMrnPN6GEzUBDisz4lulAm8CsDO5tcAAFR85ue3q51g2MuAAP89C9D+l4mPz4npOKaZMmkwL3IKQQr82iQcq4sYsYkpTZSJo8rIFVG1TJp2ysTfZlQsIgJssi5jU3kAACo+c3Pb1c6wbGXAAH+ehog/pPjMB7SRlbmmCtzVYMrlhHyKILYK6LNJEUOWAQwnZQpp0hBySGmzTOB7yHmhDIZoQqktM0MAACo+c3Pb1c6wbGXAAFVngBOjgnVPWRcmByCbAhR1SQFSkgIsDsk9KhOgWERUsM+JV57CwAVcdolp+SpySFlAAAFR85ue3q51g2MuAAAAB8D6n6POfk9B+j4H1B8j+nzB9T8H5PqfU+B9D4H6PQAcs9h6AAAAACo+c3Pb1c6wbGXAAAAHyP85TThoM/z8JIRo16ZtNSHyMykiK6O4XKZ9OucI0EUyX0ZLJwfI3EY4OecA1OWsAAAACo+c3Pb1c6wbGXAAAAFNlUEBN8n+fhvgr0z+eMsE/BBiRHyJqWkY3L+IQewgRfRShtMx0TkqM3QREx6bwAAAABUfObnt6udYNjLgAAADER6Cszbxj83wQQzkfEsk/BXxIjoE+J+YsLcKGP9ADGRfRShtMyESYrU3CRYxmb1AAAABUfObnt6udYNjLgAAAR0xObIK1K9K6LCIMajM+mpD5GZSREQJKWaZ2NxmfyPkSL6MqlnkKN1GJySEKNGl1AAAAAqPnNz29XOsGxlwAAAPEeU65+DgH6Pgdg95xDqA5Z9TnA6B5zun8I4eo95xT9EiP2fwhx2DtAAAAAFR85ue3q51g2MvF8HY5Gb94AAAAAAAAAAAAAAAAAAAAAAltFh9L7vkqPnNz29XOsGxl6rgLOHTO8AAAAAAAAAAAAAAAAAAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAAAAAAAAAAAAAAAAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAAAAAAAAAAAAAAAAAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAAAAAAA8ngAAAAAAAAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAAAAAej6PVP7CZ5Gd90PmN0AAAAfv2fn8fj9PAAAAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAAAA/X78TirnbBr5j1fR6PB8v00byno3z9X6AAAD9LY6HFfD1eysIKw/P48gAAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAAAeUqosayLWT6f2/GAK6jqqv4unAAAeVjW8rP62YEcxtaped23n+f2gAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAADyeDyuDpULJdrIAA+Pr9lGcq6N4/j94AAmVVg2ndxgA5Of91Qc5uef8H1AAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAeUl3smY0uDVPPbR+XX1fhu3p/Pf758AAQiYoqxga8ACRbuXcHRoT9/r8gAeT5/fS3Megc74PqAAAAFwdJhZLuZFR85ue3q51g2MvVcBZw6Z3gAAHl19P4bLuJKR7OSKqgbSHzG6LR6BHTSlnwAP5480hy7onKzPsA6un8d0dM5/6Pd6gABFMHbqXnVs/IAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAHu+357Es5aZUmB/fPgDwfL9NG8p6N8/V+vZ9novTq3OPr+/wABGMTYqHm1y8PX9Xpujp/P+l9nyAADh5mjTfMr35er9gAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAEmoMi3+iwoAArmNq4BGUwsK1l7DsJYAAU7ze8j+Np3L0yC7urmgADn/J9VL8x6B4vj94AAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAHlcPS4SSbOSAB8PV7aM5V0byfJ7vt7/xeXVec+36fnAA4ubocv4fsl1BhgAD4er2UvzPoHJy/tAAAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAB2Nb4Ls6dz7++fAAEHl6KsoKvE0qsC0buNAAAAAH88eaf51dRvA1gAAAAABcHSYWS7mRUfObnt6udYNjL1XAWcOmd4AAB5Wn0CNmVJgAAfnx5pDlvROXm/Z/f0uzqfPexofAAAAABV8NYwqToAAAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAD2/b8959U5z9fZ+AAIvh7NRc3uHhJN/KuHo0GAAAAIfPbtcxFX/QAAAeP5vf8/X+gABcHSYWS7mRUfObnt6udYNjL1XAWcOmd4AAACxLeWsGulwABTfNr2PYeo8rh6VCSTayQAAAAAAAAKX5l0DhY+iAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAfb3/i8+rc49n0egADiZuhSvLugvy6+r8N29P57/fPgAAAAAAAAUvzLoHCx9EAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAE0q8C0bqNAAFVQVpD5fdFodAjprSz4AAAAAAAApfmXQOFj6IAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAAP7+/F29S5719D4QAPB8n1Udyrony9X79v2ei8uq85+3s9YAAAAAAAFL8y6BwsfRAAFwdJhZLuZFR85ue3q51g2MvVcBZw6Z3gAAAAJNQZFv9FhQABXEZWQGNpRYVrL2HYSwAAAAAAAFL8y6BwsfRAAFwdJhZLuZFR85ue3q51g2MvVcBZw6Z3gAAAAHlcPS4SSbOSAB8fX7KK5R0fy/L7vp7vzcHSIT6+z8AAAAAAACrYGy5GX9wAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAAAOvq/Dd3UOeAACETFFWMDXgAAAAAAAAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAAA7uznXR0zn4AAgUnTVvDVY/nnz/AAAAAAAAfp4eAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAAA8ro6hAd3UzQAPN6PdRXKej/D5/Z9/o9d29Q579vZ6wAAAAAABUHObriZOgAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAASylxLZ6BEgACsoivg8jRCyLqTntXNAAAAAAAAUvzLoHCx9EAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAH79ni8Oqc66X2/IABy/h+ykeWdE/Hr89HQ+W8Opc6+n7/IAAAAAAAFL8y6BwsfRAAFwdJhZLuZFR85ue3q51g2MvVcBZw6Z3gAAABO7Ccsq1kQABUnPbiKzmy8rX6HFy6hwgAAAAAAABS/MugcLH0QABcHSYWS7mRUfObnt6udYNjL1XAWcOmd4AAAD0/T6r06tzj0e71AAR/J1Ka5jevDubGddPTefgAAAAAAAAUvzLoHCx9EAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAsq7kp3VTYAApXmPQeJkaDyufp8D3tXMAAAAAAAAApfmXQOFj6IAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAOjofLePU+dfv9fkACIT27VPPLR4Sqjxbb6FEAAAACHTu9VnP7MAAAD+fk8AABcHSYWS7mRUfObnt6udYNjL1XAWcOmd4AAB5Wz0WJlm/iAAfj8fqjeWdG5/wfT+vZ4vDqnO+n9vxgAAAAVzG1cAjKYAAAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAHe2s25+lwAAAgMnTVxDVYnNfOWZbSIAAAAAFTc/tonNbYAAAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAH6XR0+A7upmgAeT0e+jOU9G+Hz+z0fT6r06tzn0+70gAR/J1ORnfdN6edAAH4/H6prm19wsbRAAAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAJZSYts9BiAABWcRXwaRohZFzKT2smQABS3M+gcTI0Lf6TDSXayAAB4/n99L8y6Bzs/6gAAAABcHSYWS7mRUfObnt6udYNjL1XAWcOmd4AAej6PVPrCanlVNfv8Af5A5nxfZR/Kuifn8eeh9/wA15dU5z+/1+QAIlP7lT87tXh9/f67n6dAdfQ+EAAcr4PtpfmPQPP8AP7AAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAD3/AHfNY1rKTCiwhUfPLiLTuy8rX6JFS6gwwAPx+f1RvK+jc/4PpA9/3fNdPTuf+36fnAAEcx9Wn+a3f5/HkAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAeXb1s+XUmHW0LWPDubOddPTOfgACBSlNW8LVgAdrXz7m6XA/X9/gADnfH9dNc0vfB8P0gAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAAADyuXp0FINbLAA83p91Gcp6N5vm9oAAlNHjW50GHeQHCy9KoucXPk+X3AAAAAXB0mFku5kVHzm57ernWDYy9VwFnDpneAAAAAAEg2syybeS7mpnACs4mug0hRgAACd2E3ZVrJCJT+5VfP7P5+r9AAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAAAADyl9Lh2LZynR+z5eZ8X2Ufyvon59fkAAAPKz76P83o91cxFU8AAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAAAAAfT2/mcVc7y/h+yLzuwAAAAP7+n88HgAAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAAAAAAAAAAAAAAAAAAAC4Okwsl3Mio+c3Pb1c6wbGXquAs4dM7wAAAAAAAAAAAAAAAAAAAAAAuDpMLJdzIqPnNz29XOsGxl6rgLOHTO8AAAAAAAAAAAAAAAAAAAAAALg6TCyXcyKj5zc9vVzrBsZeq4Czh0zvAAAAAAAAAAAAAAAAAAAAAAC4Okwsl3Mio+c3Pb1c6wbGXjuLq8v4PsAAAAAAAAAAAAAAAAAAAAAAEn3cf3/Z81R85ue3q51g2MuAAAAAAAAAAAAAAAAAAAAAAAAKj5zc9vVzrBsZcAAAAUIV8a8M9FOn7LqPIU6f00IQ0/RV5zCfnxI6fA1CWIY7LWLuBUxwCsDkn9NWkvAAAAKj5zc9vVzrBsZcAAAAYOBtQzwSElZmwsc7R1yvQXQdgzIbQMMGoiqj8l8GOD4m8QUiRop000essw+gAAABUfObnt6udYNjLgAAAV4ZFJcTU8pCSuzbxTZEzuHiPYXQdgzIbQMMHeK3N/GdSLlemyiUlSkaKdLhPQaEPQAAAAVHzm57ernWDYy4AAAGRCWEpMwlvFinnKSJkRskZXpMi6DsGZDaBhg2gZfJaUQadIcQwgpLi6zOZbB6S6CWAAAAFR85ue3q51g2MuAAABBScH6IUeg651ivjsHDPoTU4Z1z6keJaQwlx8CFnsJofgg50ThljEKOeCYHVAAAAKj5zc9vVzrBsZcAARU5x2CRkVOcCVHRBEjmk+P6RE5ZPjnHlO+RElxCTzk9IqSU8R5DwHQOsQomZ8iCErO8AAAVHzm57ernWDYy4AAw+S4gZosoMlx0S8yWlGlLnZO6Skpwm5CC8DL5/oMYXNIFBHvLFKnNgFfFflaEiL0MPG+jIBchUJrQsMAAFR85ue3q51g2MuAAMPmvjiGcTlnsPYavOwYZNgkjPwYWNnEgMHlyFHFxlUmtDGZZJpQySbAK+K/KzOgTUrMuwiRrYqMqk1kAACo+c3Pb1c6wbGXAAGHzXxCSnSNGqyQHSP0YtNHEjKqKdNKE9P8/jRZ5ymTlGqzpkTKZPmaoICRQqonxVhPy0ilzbRn04ppwAAFR85ue3q51g2MuAAMkEXPqa0M3kWPoaNLOIeZPPMadOuZRPwXed055LTMJqcyYfw0QfYzcfo1uZvLwKgOmXuZ+IGe82CdQAAFR85ue3q51g2MuAAAAAAAAAAAAAAAAAAAAAAAAKj5zc/nwkWzlgAAAAAAAAAAAAAAAAAAAAAAACHTe9/9oACAECAAEFAEtLicmwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzDCswwrMMKzCBWPmGrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtdZQ+Rau11lD5Fq7XWUPkWrtBUXIFKmLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZRi2UYtlGLZQnHfM0RD5Fq7QdPqerm56MQ+Rau0HT6nq5uejEPkWrtB0+p6ubnoxD5Fq7QdPqerm56MQ+Rau0HT6n8EuVqVpiDYllDjTYUp9VTpzTzRhr256MQ+Rau0HT6nXySTTRT2zNMC5WnRlB0rLXpVqM1OfUSyxjFDSIF5FhBlrCeSMsda3PRiHyLV2g6fU65PbtasCafRLw0HOQ1LfR/06VZHkNSmS1SjPrG56MQ+Rau0HT6nXIah5ijo1qUtSQ8UmL1dJBRo1I6CgnUzUh9PqFZ9W3PRiHyLV2g6fU6pOQK1cV29R8vNLGEQkH4lq0IwjDRcid3lPRRUiJmeSSEsNEyVp15FInAvW1Tc9GIfItXaDp9TqCKRXMggh0C/S5E/u6nQ2z8KtLRjCEYKpGJat0padMaqFy8lGTSW1eBeSaaMY6puejEPkWrtB0+p0iZCqYmT23SpCEOzQOlZa9KtSmpzgibmL1aVSWeXRXiHf0OgmUnMVCJKQtT0lRTkK069aarPq256MQ+Rau0HT6nSb6hGjW0nOn9LYUO2GkvJ3l61KlNUmSkyQrT0jpyQvTPHZzNTWNz0Yh8i1doOn1OlCIRFDzFHRr0Zash0pNQqgvXmpTlDUteloqxGBmghpEC8mlWrS0pFRTnNVNa3PRiHyLV2g6fU6aOf8tXhHt0nKn95T6GyofpPrJpoQgtq8TM+ubnoxD5Fq7QdPqdQ3D/AHtLRmlhNBWJeWriSaMsUs75mhq3AsfvHXtz0Yh8i1doOn1OoIHJi9WlUlnl0V5P8xR6EBR7itqlw1WhLu4yN3GBu4wN3GBu4wN3GBu4wN3GBu4wKlOaSbSbnoxD5Fq7QdPqdS2VHthpLqd5et0Iah5ij+Gver0m56MQ+Rau0HT6nUl681KoVMy16eirEfM0JpYwiEc95avCPb+Gver0m56MQ+Rau0HT6nVNk/8ApPpOUh3dTobZ/vaX4S96vSbnoxD5Fq7QdPqdVJPGWKYegZo6J0pKYpV6M1OcEDcxerRqy1JPwV71ek3PRiHyLV2g6fU6tvqHcVtJzp/S2FDth+Cver0m56MQ+Rau0HT6nWIZ+Biho1qUtSQ4VmoVRQrTU56S2Wmk3yVG+So3yVG+So3yVG+So3yVG+So3yVG+So3yVG+So3yVG+So3yVG+SoWK0tQzpNz0Yh8i1doOn1OsSD8S1aEe3Scqf3lP8AKbnoxD5Fq7QdPqdYiJ/ma2k5lD9ZOjsiOyI7IjsiOyI7IjsiOyI7IjsiOyI7IjsiOyI7IjsiOyOobnoxD5Fq7QdPqdXCHbFHI+WoaJkxLRpmTE1aoCpeatUpJ9GSTydEeTojydEeTojydEeTojydEeTojydEeTojydEeTojydEeTojydEeTohbkhKb0m56MQ+Rau0HT6nVtxP72rpOdQ/abobKf+sn4K96vSbnoxD5Fq7QdPqdVSpzTzECcpeloqJyBejUqTTzBNJRM1qdOWSX8Fe9XpNz0Yh8i1doOn1OqbCf2zaTiP99W6G8n9zR/CXvV6Tc9GIfItXaDp9TqShaatVL0JaUmitH/L0Ix7ehEIeYr/AIa96vSbnoxD5Fq7QdPqdS2k/wDSTSWVCJmsIQ7QjkIFqP4a96vSbnoxD5Fq7QdPqdQmEYma0kkJYaLhUO5pdDdTu+q6pcSY1pYzTQH7xH7xH7xH7xH7xH7xH7xH7xEY9um3PRiHyLV2g6fU6hvEO4o6NSeEkqkciYrCnTjPMnk4F6OrcCP+A3PRiHyLV2g6fU6aGQ8xX0nOfjLL0Ngh+02sjALyP3E2ubnoxD5Fq7QdPqdKEIxikEPLUdE0Ylo0zRiatUBQtNXqF6EtGnorJ/y9BBWIVZdKpJLPKsJUxWfWtz0Yh8i1doOn1Ok3E/vauk5lD9puhsp36S6S2oeZrSTxlijK0pqTSNFpK9NRT5ytTWNz0Yh8i1doOn1OkXM1KMyc5pZhJUlnh0qByBejUnjPME0nExWkkhLLouE/3NHoLGJ6M6aoSGqekop8hqmZLT0amrbnoxD5Fq7QdPqdQTUKxeYg46NUQj0OJQ76t0N4h3NHRnnhLKpHImK3Snnpy1Qobkr09JYSoGpKlOaSbVNz0Yh8i1doOn1OqT1msWFdy05i8Y9vQiJ/ma0IaTmUP0l0UlVmKz0qks8uidPUy0igdiZq6puejEPkWrtB0+p1yMQ8tQ0TFeWjTNmZq9TSQleNCaEe3QU1WmVlNnKhifVtz0Yh8i1doOn1OuTlysWBFXoGdFzn/wBptQ31js6VdckLwq1Zqk2sbnoxD5Fq7QdPqdfCMYAg5KtIEz9IxKFA5AvRqVIzzalBWO+lWHB+gjGMY61uejEPkWrtB0+p/BpVp6cye54wDgU4GKmqlmjCOvbnoxD5Fq7QdPqerm56MQ+Rau0HT6nq5uejEPkWrtB0+p6ubnoxD5Fq7QdPqerm56MQ+Rau0FFEpmqmFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQGFKAwpQBEnKWpCHyLV2usofItXa6yh8i1drrKHyLV2usofItXa6yh8i1drrKHyLV2usofItXa6yh8i1drrKHyLV2usofItXa6yh8i1drrKHyKScr0Jt8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+N8nxvk+IV6nmf/9oACAEDAAEFAFBQgWhiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYilGIpRiKUYigPMQ7hxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbPWXsXFs9ZexcWz1l7FxbIT0iJmTDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiMNxGG4jDcRhuIw3EYbiDxXuKg9i4tkN7wOrlz1I9i4tkN7wOrlz1I9i4tkN7wOrlz1I9i4tkN7wOrlz1I9i4tkN7wPwa1eSlKccMYhDPxqyaqeeEsNeuepHsXFshveBr5owhA64JZRXM1K0wJmY0Ksk8s8upWFPv5ktajSEIwjDWrnqR7FxbIb3ga46t0qQNnqteOg3jnbDULapCbpTVWYvGjWkqy6xc9SPYuLZDe8DXLJLuKujSqzU5yxiWtT0llU7qGgRP1C0xQ5TMSatc9SPYuLZDe8DVHVmlQFFcq9/0KJOBilGEYR0UA7+k+iqKUC0s00Zo6JYzPRnJGY16WqXPUj2Li2Q3vA1BxRolwdWK1fpQjveUuhfJfpU0YRjCJA3AxS6Tx2UtTr156s+kkJca82rXPUj2Li2Q3vA0jJulQlOr1SoIx7dAmZmoVZJ4Tyg0XlrU6lOaSbRRTvc1ugwYloyHTk5ippJqdMZnp05ZJdWuepHsXFshveBpLJKFajpN872w6HAS00g739KeeEsFJRmMz6RMpOYqFi0lCTWLnqR7FxbIb3gaawR7iro0a01OcsYlrUxVpS1JTRaajU0Uw55essKffTaVGjNUnIEZS1PWrnqR7FxbIb3gaakT8xRjDs0m+d/SfoXyXeU9ZCEYxSk2BeTXLnqR7FxbIb3gahfJ93U0ZZowiQN+YoiMIRCkT8vW1aKmd3DXrnqR7FxbIb3gag0Wlr06lOaSbRRT3c1ehYJd/R1SMWpft52gPO0B52gPO0B52gPO0B52gPO0B52gJJ5ZoaS56kexcWyG94GpcBLTSTvf0uhYI9xV/DSPS6S56kexcWyG94Gpq0pakpkvNRqaKYc8vW6FEp5ijGHZ+Gkel0lz1I9i4tkN7wNUvk/3p6SCc7yl0L5L9Kn4SR6XSXPUj2Li2Q3vA1UYQjBRJxL1dEmamoVadSWeUGi0tenVpTU5vwUj0ukuepHsXFshveBq1kl31LSb53th0OEl+Ekel0lz1I9i4tkN7wNYsEu5raNKrNTmL15a1MVKcs8tRGMyzboNDdBoboNDdBoboNDdBoboNDdBoboNDdBoboNDdBoboNDdBoboNDdBoJtKamX0lz1I9i4tkN7wNYok4GKMYdmkgHf0n/KXPUj2Li2Q3vA1iod8vR0m+S7Y9HZEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrEfrHULnqR7FxbIb3gaxVOd/W0S9CarPSpS05BWrS0pKp6rPN5qqPNVR5qqPNVR5qqPNVR5qqPNVR5qqPNVR5qqPNVR5qqPNVR5qqPNVQlTRmLaS56kexcWyG94GrXDvdUtJvkv1k6HAd7ZvwUj0ukuepHsXFshveBqppoSwPG4mKuiQKRMVZZYSwB01ChSnnjNN+Ckel0lz1I9i4tkN7wNU4Dn6y6SIS7ml0Lp3vav4SR6XSXPUj2Li2Q3vA1NetLSkr1pqs+ikEu/rdCoc7ij+Gkel0lz1I9i4tkN7wNS4Dv7TaSYS8vR6FU75ir+Gkel0lz1I9i4tkN7wNQdNwL0p5ozR0UIj3tToWzvdUtUjKcKUeyA7IDsgOyA7IDsgOyA7IDshqFz1I9i4tkN7wNQuHe9q6MkkZpiZWFCkJpoSwPm416urRFTt/AXPUj2Li2Q3vA01U53FHSbxPtj0OA5+sutR1Pv5dcuepHsXFshveBpqp3zFbRLF5q1SjRlpyCvWlpSGK81WfRSSXf1lpL/SOlJPGWZNUZTMmtXPUj2Li2Q3vA0lw73VLSQCX6y9DgO9sdJLJeXoxhCMFVMiXm0ixmejOSOSGKesXPUj2Li2Q3vA0q1GSrKdb8YCeSaWPSQKxr1ZZYQgDhqFClPPGaOihEu9q9FWlLUkUCMxappED05apRrS1ZNWuepHsXFshveBqDRSlXgcQatPpRCXc0ehdO97V0ZJIzRJlYUKXSbKSV6ZorPQn0kpSiWnlmhNDVLnqR7FxbIb3gao6mUTAooE8tfoVDvl6Ok3yXbHRUU+UzJUpzSTaJMnUMTkysKFPVLnqR7FxbIb3ga5WO9/W0S9CarPQoy0pNJXTIV5Yw7NBOTZzMxcvJRk1a56kexcWyG94GuOpNEwDiXWL6LfJ/rLqFtL/bpTEeasJJJZZdYuepHsXFshveB+AcQqVQGiVWhMCBWNerLLCWGpWkvu4paJ269c9SPYuLZDe8D8GeSWeB1vyzBGIRoU/wApc9SPYuLZDe8Dq5c9SPYuLZDe8Dq5c9SPYuLZDe8Dq5c9SPYuLZDe8Dq5c9SPYuLZBFWnLyYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUYjqjEdUGzU1eoPYuLZ6y9i4tnrL2Li2esvYuLZ6y9i4tnrL2Li2esvYuLZ6y9i4tnrL2Li2esvYuLZ6y9i4tnrL2Li2esvYqRWjVhusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kxusmN1kx3VPuP//aAAgBAQABBQBsNiq4K3CuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdccK644V1xwrrjhXXHCuuOFdcQSqu/rV+P1lDmBavxxfW+txmbcbjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIcaM2Q40ZshxozZDjRmyHGjNkONGbIKl/cz6Sn2OfSy+bciHMC1fji9H+surcxXJXKdySEOYFq/HF6P8AWXVuYrkrlO5JCHMC1fji9H+stA5mSRStybvXkTbaUmG7i7vaN2bpELcINurkknuzWLmpajpdAZWYdIdVwHbmub7bc/8AaDYCXnCbigpuVfIN1v27zPNx6OzpeOa9rNt0JKmSVUu59wyjAa39oNgE85rLnqtZ1ILpRFjN+3EtXhnQa/bbK+DIuFNd69CZbQObMejILP8A7QbA/tBsCbMEky2s/tBsAnnNZc9ZpO5vu1EmmlllI5vmcacAu7d9OtqUt68yz0aHTmK5K5TuSQhzAtX44vR/rLQXf9T51vRZeOTOcrl3lj5GlCx+aSxF0qL+ZliP9IqFqbbKR5yoSNRzFUbQWuoGM4b3gSbzgZ7kt3O0nIRczZFzHdI0GIisRYcDNykvOmr2/wA2fKLKuw2Q4WJmGt1Z9Gt1krqqMSjRJIx3MKaYuXmWhbBNoVMw2dfZtGzWq5bN5sGOz2238vVtbfrlpcyzfREGyeVdhshwsTMJbm0SPbbJVUOxp5inxBqWxq25VqVscv75g77Z50/hMtXJTpzFclcp3JIQ5gWr8cXo/wBZdCgppqaXS1hJViq5/qfOrLHd+XaaE1mM5c0OHuWSWMLGZVUQguuxrH1mxt57BVy9fMYHX/qIXTeCU77xX3vRa9/MnJw85jSGM4747JbXXjs82LXWEe9BnXUzZ8oraWIdlwG4QbieQeFu2W12g16bTnd15amSxahKwnc47IXJzrbNgeTudH61lg5KZs+UVsrDuu4LcItwgQeNtmM1Gc182j0nWbgq95LNmbOZRXrIkvfOn8Jlq5KdOYrkrlO5JCHMC1fji9H+sui/jHPPG2lp8wK7bNJsa2nJcG8WZK26m9mLazMO57bJ1yrrvK8arbhlVmXajJvzIzOWvg7GdlZ5zB1/6iv++MIWzyy2YbbyIwyzWU7UM0cs9fWYyXkLItKpeC/Ucs1lIxzMWjRWOqXOesjxyu5NeXWae0W+0nKhdvzZWDsrtK8U2dB1fq20F73lufnW7IS2B5O50frWWDkpmz5RZNeXWae01NdQMuV8i6I1LHMqW6Nz/wCZrKC9rMja66WaVyEnNb232Z5dZbQlznueM0k37SDMVyVynckhDmBavxxej/WXSoNltqVehQoF6IUW631OdNRUdMkjCEYUCJIvMKSeQo1BFPIRrVyhUwKNChQkFZPIV5+6p93QIEaE4rli5iWCcnwpUCxcvLGEIwkS0ySeZLTJpoJaZKJZZZZa5QqYFKlSpU65UqYhSo0aNOtQoV5KBYuXljCEYRR0mIoFCpforlChgRTk+NLdKUN0pXTmK5K5TuSQhzAtX44vR/rLSuG5zDWZNm8y9R7uxwKVRLQbE31WLkKwdGcJST3IgrJJbRThwqSKPPON3Kkl5x3iVOM93oTvb7GzJrrjuk/7gttioChnHexsy1s5R3z6OsJa0lpub07B3STyVJKGYdbqXnF68xxlguqzVy4XDZjmVaiQ3LHZgVq4zp6FAzMVIQzoOjspZ0nDCe1l3WxcVLvnf1Ytw4/7Qc4JZyHOZO6WYrkrlO5JCHMC1fji9H+stK+3KFNJLxEi1rjFn9ZTJf8AZ77vSo0bYt61xhWtHlIfO+GTm9c5hMt9lLt+jFWZdW1yHcFuWcs/LbUlZv8A0lmmcCitXat7bxuMdAzNW2Q1xhZNHWbMJppFUVZw5U7qVF5BJ/63VFIolpjHbJ6890MqTwMN1/3D+gZN+ZPQufC5SqNGtdVwsJnOFOs8ZOMbMBnM++s+8tkCjSR7tWVV1XSzFclcp3JIQ5gWr8cXo/1lpX25Q5YWilu+37XXl20juyX/AGfOA94KDoZOZFqtq31jHxI0LoZ0E0xVbmVhXLHrPO10JTVbjBuqyX5JZv8A0lmCkqo9+CRwseJX+XCaRaTJclmJljL1JJUv/c5qLVl7rM9fIuHMvmue8qFbyyF6kW2hN5vkuq3GVXEVctmcm/MnoXPhcovNgIFSVy5mM5n31r5TLdqzZauVphNpx6WYrkrlO5JCHMC1fji9H+stK9hQ0btTk/Q1pKSs0tozDkScqyYvNpRtcwXM+bzxtXbKMcztnJyC4hpUbr2TLJt8bGrjneF8rx1LJ2poW6adpGq6CuYS/wDYyFwibbuVfm1ZdTkvte1VtRbYhb5o2DbDlI33vBbYpcBl2aZLyTbuXyIva4V3U+0FsyafmGssgG7f2LPumW0bAr3dYivxzzMCxzoejkZa1LNOjsTiyyFtTuZmfcpTLtYBSZxzNy23EqvhLvHmOTEyN88zHYSqVahPRzFclcp3JIQ5gWr8cXo/1l1bmK5K5TuSQhzAtX44vR/rLVGDFAtQf2a1wqC2bvhmUaVW0V3kO5CJeu/KTbqkTvHmfc8jFzZOROWV5chSZlsM1bpMPCP/ACwd8X89bg33zBysAxC62auoSsVmSMvBYzI3gejBVbcLh9eYWZG57rYKSx7guNYsLQzZXZlrJ54soEHdmruLQdNm3Sruq2t18185BSq3WzVkStl8zBB4ndVmK5K5TuSQhzAtX44vR/rLVZpFw2l2iyatdO3I5G+muJBtfYVrW7UiZeNzswBMmUJFM4DJS67XsO4zSrl4R2oqK6HlquvjFp5TOb+bBtrKXcpq5yGwZpsK11jHI686XztmOVGdL6/a7/J7cbNFUYtvLk+XywYaLyWsbS+YQcoGT5mEFR0DMY2i7Mu631SCsg6nMVyVynckhDmBavxxej/WWqzYJpg5aPJmtFajScC0SQ0O09/m7cU61Dklv8wFOpJUkzgOcgUYuX1EMEsvuTgqWNrS2nrdiby5S55J7vOu/ttYOty5WbTLEKxNYtHefOpQngqWON0DVpM6ZmjBJttQmo5UMtiHv1DT3mZJ2/uK29xZckhHrq+TfJo5iZRfGaNwUHBdtrpk6U2dTmK5K5TuSQhzAtX44vR/rLVKaaQVE50Zd7psRyLLdzRXClsbZ0vbdAv7l8qPowlFs17NKNnLjdZ7OJYblApb7K3bV8tBcvxbGD+Y+Wy09w2rcTMJl5WHeskz2bhKI2hy3vM0773Wpp3GaaI2Mz1u5i1lr7XJcSw06ZC1eVm2z2aCo8MuVxq1wcylu3G4WVZFuKqHai5mVx1pS9WPZuzxSyOWJQSFnVZiuSuU7kkIcwLV+OL0f6y6tzFclcp3JIQ5gWr8cXo/1l1bmK5K5TuSQhzAtX44zJKR9DzB/wBlKo/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKw/spWH9lKwuNmbVnkycqlCtQssIcwLV+P1lDmBavx9K6t1Lkptyt6ZoezemaIW6Ou+SxMLyXWhDLe9Dzrtjmrf6s12onXhunVUcyq8tIVr0V/36XZ1J45jEYtl4zELC4sZs3q7W2oJLtzFLBM66MyaWWy95iHIsuTNg63K3G8jPXMGuUN6Zohl5O3qrXAzF32PMaUhHMU8KJK698GAtW0fyc+2gLp32e59/wCVe46m6WwMwdyrgIl2qC3mbMUFG4GYVuy5d74G3+VzQXBfDfuRZZTUVS1l78z6jRUiJXMa6KCZea97CWbY3KQrgtrShzAtX4+leWPZdmlmWsrLSjmYspCDjPFT7Ctq3qbhWsmbm7hwZq1yqvXXfKKTQ7pZsOUGSv5h6LDYSWzayiZr3Qzq/I5aLiMVAtg4b9WgIJVk002qXdzofV8st2WAy2t/TFlAyrosZ7Vc3yApFbiWyzXtIg2nSQsxfSS2FsUa3aJfF5U2lbLL5a6k+j9jncYYd1xmc51sm7dsSbLv9eW2CjbjJ+jnzNx833NVJctdt5T8ubKIuy58IQhDMQw05022ynuaulXT0ocwLV+PpXlh23Yp5LUuenHJUm9ismSpVtsrcsJrytQ1JbvMLbKlUf2Yi7MOy9+bDlAw2G/HdWky0XwO1LG5c6DGOZ1fkbcZcnC/WisNo22HVYdj2rSm7nQ+r2SsETuShfxWlizdji1szT3qW0VUtx5Mm/Xhciyb6tzLlbuaru5r5wXv590WOvtbe3bNuy4mw5H1ZJ5Yutpmc51xyovcw0mkVaUHGwGc0Gq3M33NVaJVjeTfJ+pUC1zhdFSLptt8txOsavPpQ5gWr8fSvLHsuxTzlMWSn/ZjGCLcVMf9rMrEP/2XNk3N13SyZt2NdyXbh2XxzYcoMlnzHRnV+Rymco8y1oJXc3cuF052Y886H1ewt+G5blvf2Yxhb/Mu1Xs7M0rFOoVxbdZuUMq379Zh09+o+VBAnbLKTC565l2v5DtSLyZZWq2mFk/fG73Pmc512++hZrbRTEj2Uu69SafN9zVs6kkliw66gva0b/bmcdm1069+Yc8/y2VS0igglNKHMC1fj6S/lqtgvLn8nWhH8nWhDUts2Wu1GVYC3rNX7h2lZz/Fv7cNhhpa7lztsuON8MdCeqDb2z7NYBjouHaFmv8ArMZjILJQgp5XrSqKk5bNtBytv+TrQj+TrQhnZfLctFxLKIkLacp5RrUHK7cyu2lRTToaaS5G2xrD29ZS6DxIseJImWe2SIrvHL3bl3OFKTSyYmKiYRVU1Nyv2wTD77sWwnwttduJraQHO0m26Ew9lCtWYrs7LvaxrGtOHMC1fj6uqoEKNSnVp1aYqKSdTn3slinUp1JBWPkKM9OpTqSVKtOlTonyNeeudJl5t7JQ3slCgcKGI1FFPpVN7JQomitforKBCjUiYoS0d7JQpqSdUm6TzraxCsSUU8/R1cOYFq/H1Ro0XKFX05DDreWT98RUWuL7c3qWVa7lUupo92rTK1irrSXDaObPm7ZTlNfTlFlG5s50fszLsDcN4t/+T7vjLbaF5sFQzE85yWVq7Bwm8bP3Ot4Wyr3XWXQQzUc5Fv8AyexGG4Hutnsrd4yZe2V6nxbxyEj5M8RvlmBcTkX25lXuutJ7iZt1rQq1gbyy3CQdVDmBavx9Vmne8G/bfLLa6Djbll3TVYV2Bfbm8j/EZkEAor2hyhK9Ypc3Nnzdt7mlt+22PcjNEwXOxco3NjOj9ms7mSarGYX9mMYWuuYlXEb+YrnOh5r7XEUS+WZFqvFkZNWgoyn81HORb/yflF5sDOEgFCL/AGc8TtDKPljbJNeuyLttoo47cZbFuulXh1UOYFq/H1WaV5SuC5zAzNKbJaj5dErqdVhHzjC2l9ubyP8AEZhlQunWeyjJlY1dXNnzdtzlitu4mJczLNbhtMLKNzYzo/ZrG2Bt48rc/wAnWhDBt63GIj5iuc5jKEgnme1TiQ1Xg1DrePNzNRzkW/8AJ+UXmwM5SoXrvdoNk7WygZWV4qk3bF0l8ogW7y6JNdSvFqocwLV+Pqbhu4s0WXZNoVH5dONmbURjmFsy0aNs8oL3lTHbfbm8WzivguVfF0rkXXP5drT1mG082fN2ynKa+nKLKNzZzo/Zrd5knSxmr/Zj5Fhb8OO4zizE852n9WzY2mkrlMp11pEtTzUc5Fv/ACfbK4qnb9yHM5Fw6tBlsN+3deSYipiYjXoss42C42xnBeyam3Eu+/7pnsttmTLJSNVDmBavx9SroaMtFEVntNCrivQoGKBK3NvyJo9bxgqBzhbbMJLfQUeQKzGZaycIkSRAmfTyKiTSGQzEY4tNBqLtXhbbMcLbZhFZzSQ66jb5hqZ2jSpUaVehQMUKVsLb0p1VhshYO1ENGqJHC22YpWytxRno0aNCkJpZZ5T9m7Vn67eZTRbkNXDmBavxw53xTQlDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaA4s0BxZoDizQHFmgOLNAcWaAbyzBZSxDmBavxxdL7D1dbr6oIcwLV+OLpfYerrdfVBDmBavxxdL7D1dbr6oIcwLV+OLpfYerrdfVBDmBavxxdL7D+CQTzygZQLX0aYuK2pE09qqNCtXq6+3X1QQ5gWr8cXS+w6+nTqVarftiarhNSk5MLBdSaKulGS1cqY1H/sYsRoQSSzxYFJQjPJUp1Nbbr6oIcwLV+OLpfYdcgW8WVKKK3EhGo6F0UH9Z9OMYQhb1nT0o9DtZhRcon086nmtZbr6oIcwLV+OLpfYdcwnDMro2ieJlzpNXSzCUpaTCZsyjW0HE2k5dKLiCoIp3V26+qCHMC1fji6X2HUxjCEG8wllWChbpIlQYwmhENVenRFiSeWeXRuY3oGSOizWnUXjdGjSo0dFVSSCqScKTTSVbVW6+qCHMC1fji6X2HUIbUW1qLfYiKkdNyG/MRVei2i/KbTdGeSSeRzIdRFWOltt42uqKcnE04npPh4SJBaMYxjqrdfVBDmBavxxdL7DpJKIqqxhv20TiU0ssssvSupFBWSjBeuWMBHVK6UplDVA2V0bgIG9EWEYRgEpMNqh9AQSSInaTrdJZBImjRg0Z1duvqghzAtX44ul9h0mA4J0ta0roN+WnP0WwcMe3SfTegjrNChWMVmk1iyCR0l5bKIqarq55XP6y3X1QQ5gWr8cXS+w6UYdsGI4t8I+ifIlz5JVTDKWogmcMEjaKrFlZM0XegyrSKw2huorpHjxUgUcrjNrqhrbdfVBDmBavxxdL7DptNe3ItSzSzS6NzkCYyS6LaL8pNQ1k88lOR6O2ouG9dbr6oIcwLV+OLpfYdRbReicTNGpTkqU3MiTIy0JZp5JmmuQWkTV3Ad8TtbX26+qCHMC1fji6X2HUIytXSVQoaoGyujcBuxVUiEYRgGI4YJCzqn6qrPl4N5fhDDzgGHnAMPOAYecAw84Bh5wDDzgGHnAK9CuXraVuvqghzAtX44ul9h1NsHD2y6T3b0UZZEYQjBhuLe6P+G+ftulbr6oIcwLV+OLpfYdSTNmCRtIVC6om6LwQYLSJ/wCwiGquTIq1LNLNL+E+ftulbr6oIcwLV+OLpfYdVbNeiUUdK5KDAiq9Fs1+JtO/CfP23St19UEOYFq/HF0vsOqknqSTtVepraPoryPQWEo0WrlTIRlUwkqZI4XOlPwXz9t0rdfVBDmBavxxdL7Dq2C4YpSxpXQb/d1ei17g/CfP23St19UEOYFq/HF0vsOrjCEYMNfgrImidJlzpRUTTKYoAsZMFTJV+teqWxw0hjhpDHDSGOGkMcNIY4aQxw0hjhpDHDSGOGkMcNIY4aQxw0hjhpDHDSGOGkHacKnXHpW6+qCHMC1fji6X2HWNVdnRFmWaE0NG5rfgYI/lW6+qCHMC1fji6X2HWM1AitLcIdmlc9wd3Q6IzyQj3lMd5THeUx3lMd5THeUx3lMd5THeUx3lMd5THeUx3lMd5THeUx3lMQjCMNK3X1QQ5gWr8cXS+w6xloO5kPRU1EsmkDx0weOAgQMqB0k3kcqU3OkDc6QNzpA3OkDc6QNzpA3OkDc6QNzpA3OkDc6QNzpA3OkDc6QNzpA3OkB60qVJ06VuvqghzAtX44ul9h1dum/BRVdK5y/Ewd6LXoEKZb8F8/bdK3X1QQ5gWr8cXS+w6qjRrV6zdRKKMk6LlW6aKj1q1atWDfRqqyrFy9EvQ/BfP23St19UEOYFq/HF0vsOqtggTVTWlcNflU1gRjCELcN+ZPSvwnz9t0rdfVBDmBavxxdL7DqU0hXUVBOIF08hovdfijokIdkAzUHfK5CEIQ/CfP23St19UEOYFq/HF0vsOpti3oUSujGMIQd6/MtLIjHsgy29BFRtT2w1T5+26VuvqghzAtX44ul9h1DeRKy0rUaNKhR0bjOHd6X/AM6LeN6Kkr6p/NGopUv3nH71B+9QfvUH71B+9QfvUH71B+9QRjGOnbr6oIcwLV+OLpfYdOMYQhbpAinJGjXr0S9BfWKiwrilSq1qrbRaaMj6u4TOjJNr7dfVBDmBavxxdL7DpspBlWVyEOzSugvTU6PRbBBlMG9ZGEIwfbQikGNdbr6oIcwLV+OLpfYdKEIxizG/uVG0VVTLJicfPGD50JyeZUTyYnF05P0Xu4Nzotv3jA5R0jBeiYoOxqmEE7rbdfVBDmBavxxdL7DpW6b+8VfSua4fMG+i2De7uhoxjCEHk4IrazJPPJOy3dTXCukrJRNVIL6EcRFHWW6+qCHMC1fji6X2HSIqB4gYb1z6U4oV6Bil0uRapIyPUqVatQIKPWWFajRpUKOjcZf3ekf86CJ00RNthxlV1O0nI3Sa6nnyBpPO6u3X1QQ5gWr8cXS+w6hHXVVHrINyUk9CEYRgLhL8VNZ6LcIG70jRrVqVCivrFVYVulDWjiMoo6wSVyGk82nTXSVWlVpVdVbr6oIcwLV+OLpfYdUgO9aRIn7mkqyB0M5vxW1mEIQho3PcPd0NFqugygHihoubLaK6vJ6KSXVmusqWqt19UEOYFq/HF0vsOuZLf3MjaKmol05PUVAyontJju+dHNSzQmh0ul2kUEuqKp9UOau3X1QQ5gWr8cXS+w65vPZZRQgvJEWdG569KYNai3rw8vN0PB9lkmUxXrmK+st19UEOYFq/HF0vsOv/APqDchWIBGcCSs0A5FqRGR6tWrWq6iMIRgwHjE/TeFw+7m11uvqghzAtX44ul9h/BLmDBau37nmKIfrmkWFHVQjNCMIQhDXW6+qCHMC1fji6X2Hq63X1QQ5gWr8cXS+w9XW6+qCHMC1fji6X2Hq63X1QQ5gWr8cXS+w9XW6+qCHMC1fjhwslPXDvCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGHCpGCGj0EdOEOYFq/H6yhzAtX4+qzTXWWWoTsDfV4GLjDNe/Hg1TCU/cySuTPXIzKINHL1mCUXmfzXvx4NUwlP3Mkrkzt0MyDdky+3yq3BKZqbhPVrOVQdV1lDLmdeWZ0iUR7s35WjdtF/MVXf+YS6txG/dWk680lalWvPmEapqyN2aVx2uL534eUlx8rlzlV3N3ozNOhwNq3OVJ7Ot0pt9LtXIQ7rSOnNLUp4mzUC0RhyGLcamHMC1fj6q5i0cuhem9rM4c3QYjrKuxoZ1/U5bbisNBtbca99pJWXllR1BQvDnX9Tlyujb5uWwvLfW1Ru3mTtoK1Vz5z/tmWrkpevlNlB5qjNFzoa93bXlWxmeurbtwMjJakH5KNyHZTaTGsFbmhcJ42Yc523d3ujN7ypyV/EZj+dSNmQsyWR45mLKQgVM0TRbUw5gWr8fU38ekzSthZB5tFmPTMBeG39x0nJw+JqhfOv6m2uW1VfjLUG1Ua7vsq3rZJ7Szr+ptTlqi/mc4MmjgJpuW+9ThS3PnP+2ZauSl6+U2UHmqM0XOhQymuuDStsXt/O620hN5DRc5D3jCWwl67eW4bV5HU1XW+rJvWm6LXkXW1z53N7ypyV/EZj+dSbk5bRxOjkubXYnE5SKfqYcwLV+Pqc4D3goum1eWFkqrBq5TLSzUmStKNsbsZ0qtOtUyo8n8zVp8WtfLJdaRoOnOv6m0WZMgwWWu5zzFZMy5sJYdNyM5/2zLVyUvXymyg81Rmi50M76jmstJKkqeVG69A6huI6audeP8Ak60Iu7lkZyMwcrbnlmPspyLlpLmX4zAEbiJGVJlqLft7mP51JuclLJp39qJQtc/6T9aOphzAtX4+pVrG2qV1OlSp0qQX7L2wcCuuWot8ukGw1G+10oG7AWeNmHJbBiOYv/PFmRSy/wBnKUySjpKORdtsWI7zbebqK3EdYR01ZS2taa3jUUw5LN20cysUKlyhVZRktaSytgrRlKzeszbFuq4r0KJigk2MtSkKT0tcwnoG/l6tEhnAv2Xtg4Ff+eLMj+eLMhstZAbCTqYcwLV+PpOC6lvG8p8drQhCuOwV+uHBdS3jdU+O1oRx2tCEBxIjhTOhzXatu2K6Pfy0CtXlmlnlDlu5bVtGEvMFZxSMFjRY0XcjqbzZT2u/ma6pgXu3bcwthwXrtW3zCPfq0KvWknknkcF1beN1TJHSp4k4nMgttNaz8Z7riu3ZtwgqrWfTQdcD58mnkYX3tB2JikRVE9ZXUVEJV8x1l6Ndsv1mOiTThzAtX4+lmq5xN3J/OtNy6diXhbSTLXdo4921ms5xNzJ/Fabv8UTC1jDixGWMz93TrRRbP5c1u4KfdDKkpNlBykXIXqh/NHd9RayfaLLm4bgEHZk1NF0ywt3FdgOzN9yqtNcE0w3unKJJSINf/R2aJ7qTZtxZHL9PcdNvHloNMZv5RHwtH0vNVzjtzy9zX8oMlHi5l5YzXtypLlZCurmeX4pFoaxIzRL28WiCHZBbXH1ee4SbktKbvuPa952jcVjroS3CZelDmBavx9LNVzitvy7vyRoHbQZPTNWnc/NZziRM2Nw0dFjnGuZ2M1YMrbRGaJQqm7y2yTy6dbupTp1aZUqVKUMy6hWOXmt6llkpiDMmmFk+8mYE/WUcuKJbXfdn8o90alaRr/6OvXbWFwGOUUbrWoW29nGexWa3Ny2w/wBEzVc47c8vc1/KDJR4uZnnXc2tFl5ic5jnhVP3pb0G9SuEfrlMo+TFMLVnWM06YXOWcyXn68jm0ocwLV+PpZqucVt+XeZl3J6HazJsgmq7yzWc4reNluVWBhRrClSpUaQzbNwynXPsG8iDntjcB4p7PaNksxyu/XDmvbZhLupYV8kHZbc8fJJ5O46/WuFdTM+lSJFjMnNGjXYN22Or2muXbZUqq17r3XuN2zq2sfqLdRkXqshaqDGyknz9C62bMpUoXcs+skVe2GbpTKFrXZKik8pLMzzrzhNzu66WaVLl3MzjyQluKvNow4cqWVp8p7ZuEM3T9TCjSyYtozJS0ocwLV+PpZirW3CcV0S7SzRFyyVlyvW61O3Vv0RiNfMXa24TiugWaeaIsWw3mqGXok/CjFF1LaJFwmsbs7fq3asZt/mFuCfsdZgpbdFuvaxEuK3D9kL6MNXPt3Mm94WIy4zMw/mba7gctucrDPczXaV6raUbgMm19nLnpdxrt20T7hNGpaS/lv1dQamY59T5f7Gz28KX/spPcVLTmhmKYleW1N/LgLFprbkbfM+/tqLjL118wbGUXZavLfZ98I1y80tuHy6HxbBNOptubt5UVaKmTp5nkQq0ss903apthtI7ZQdKHMC1fj9ZQ5gNRYW02tjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3GMnuMZPcYye4xk9xjJ7jGT3EDqhiH/2gAIAQICBj8AXr/b0P8AbSb0vqT4Re0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsXtC2L2hbF7Qti9oWxe0LYvaFsfY0v6n2tP8AfR0tERZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfyn7h8RZj+U/cPiLMfkJBo086dJrR/wBfpF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkXdOyLunZF3Tsi7p2Rd07Iu6dkFEzaGln1d2T3D4izH5C8sqy8np7VVpPcPiLMfkLyyrLyentVWk9w+Isx+QvLKsvJ6e1VaT3D4izH5C8sqy8np7VVpPcPiLMfkLyyrL+C0UEajGlGPSPwJZnK5eJQKIgs0Nf+myu1zYvRSWkr/b4BPaqtJ7h8RZj8heWVZfwGZJZzGlHPRLwJas9GRowy0S6cUioZ7QNCmk4nMQ01l+VX9tPh3vFwg4kLVi+HZiW+n1DMosxljk9qq0nuHxFmPyF5ZVl4/PE/Ej6m+HmpDMgvn4tviwSjpL6YjineHE/eiFrf00v8suctWL43V9NUGhZaKsantVWk9w+Isx+QvLKsvH/ADbh6qnVYRoUyogcM9nDKNELUJlPjsYOiprZX4enhGisvlsq2VYxPaqtJ7h8RZj8heWVZeL0lfjh/wCqnUg0Qy/I0lamtIZjkJWwrVXujOWF91LcNry7OFpKuktfV9IJJFmIsI0LLSSDQStMi6a31YtPaqtJ7h8RZj8heWVZeJzpLMjxqZ6boz5vuL8anU9FfVL91LERrzLTXFL9o24f+Ozy4WYwadlpG7gaJMk2rwgkILMlOHoJP8qv7f1cozni09qq0nuHxFmPyF5ZVl4eaGWf6tlM4aUX8qvD/Tt9NUZiwFQz2q2yDSppMiYhbIJSWVYRmTcPWS8mUkJ6zBITOV4lYec/mtTCemyDWo86lYxPaqtJ7h8RZj8heWVZeHoGxF1Z2yrDKOndiOqd4ZTgK3obyXuLDzpu4msl5IJKSzqUM39RTand3DNav/pQNa//AJxqe1VaT3D4izH5C8sqy8QWc/yI1VuqwjQplQOGrZkJaWkmCiJ6lYRp2i1kb1oaay/Kqgno1hmtR5kpGc/kgmE45PaqtJ7h8RZj8heWVZeIJRsK1V7ozlhFFS1Da3LMpwVMxGd+1y43OfUNBN0mn9ePT2qrSe4fEWY/IXllWXiftqPXhf47PLhZj6jBo2WkbvTVkIy6yBL2mV7/AE1sYcGGeoTavHZ+AT2qrSe4fEWY/IXllWXiSWX6VQSksqLSws6byHrJeTLoqP8AHE1TdVi/tQUrUam1pSpnwi7icC+4XcTgX3C7icC+4XcTgX3C7icC+4XcTgX3C7icC+4XcTgX3C7icC+4aKiNKi8WGntVWk9w+Isx+QvLKsvFfYV+mtDeS9xYecruJrJ5ZsuY7yHqqdV8Iv8AaqnDT2qrSe4fEWY/IXllWXiiWnrSYKInqVhGnaLWRvWhmOQlGweqvdGcvg1/tVThp7VVpPcPiLMfkLyyrLxZwVHqrY37XLh/dSzEa8y01xS/aU1DZ8uxy/Br/aqnDT2qrSe4fEWY/IXllWXiyMusgS9ple/hHDParA0KaSchRC/SqCWllRfBL/aqnDT2qrSe4fEWY/IXllWXjNBV3E+U7ZVhlHTuxHVO8MpwFb0N5L3F8Ev9qqcNPaqtJ7h8RZj8heWVZeNLOevD1VuqwjQplRA0K2ZCWlpJgjNZJMyZDaf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5Daf5C1JPSSeaqWGntVWk9w+Isx+QvLKsvGkrYVqr3cP7yWobW5Z+LT2qrSe4fEWY/IXllWXjSzsI1l8s7DKCnrXrL3dnpzfFp7VVpPcPiLMfkLyyrLxmYEk21ay96zhGtTKQa1dajkJCetQJOik9EvCkMI4UhhHCkMI4UhhHCkMI4UhhHCkMI4UhhHCkMI4UhhHCkMI4UhhHCkMI4UhhHCkMI4UhhHCkLIizF8qqcNPaqtJ7h8RZj8heWVZeM+4piFXstYZQU9SdZe906aspxlNL1UbvTprfBL/aqnDT2qrSe4fEWY/IXllWXiySn5qUChlO+peEaz69nfBqUedSpCQXVtbgJKSzJT8Ev9qqcNPaqtJ7h8RZj8heWVZeLOOovkWrD3vFh6CWIVfal01NxamzzcPwa/2qpw09qq0nuHxFmPyF5ZVl4pMNPWowSEspLCMybXqo5pspEbCNZfLO+EX+1VOGntVWk9w+Isx+QvLKsvFfeUWstjctdGsMzJhGqjp9UpEbatZfLN+EX+1VOGntVWk9w+Isx+QvLKsvEkgurb3ASS+RJwtBLcWptcvFL9xRakOvs82L+5DvU/3E8yemzJ1jrHWOsdY6x1jrxCe1VaT3D4izH5C8sqy8TpKbi60zZ5sI1K+SUg1n1bO7ISS+ZqBQy/Rrexhx4ZeYn/05uLxfAJ7VVpPcPiLMfkLyyrLxBaTCNZfLOwygpP5r1l7uzKcZRM6qN6zjvuQy/Er+2rl8PDj09qq0nuHxFmPyF5ZVl4eYgSTbVrL6fThGtXUkGtXWo5CQnrUCQllJYRmTa9VHNNBQoh/kJn67WGaVFnSoZy+cJTCnd7pu41PaqtJ7h8RZj8heWVZeH9xTEKvs82GUBPUnWXveGb0Zl+8rrVqo3fF0ew/kwjVRzTgRl1kMx/KKlr6vrwzQtlQNCurZV4k41PaqtJ7h8RZj8heWVZeHpIPRUNGOWif/ACJeTy8KRpJPSSfhwFLObv7INR9apCQXVtboJJfIk4WgTcWptcspLQeZSRpE1tp8OHoq69hXhUDQstZOMT2qrSe4fEWY/IXllWXic6Dm7KgRRPxL/t8WzO45dBLEKvtS6ZtxamzzYRqP5EkGs+rZ3cAlpnJ8SQS0dR4fyvUscgNKizKTi09qq0nuHxFmPyF5ZVl4vMR6SPAp3wgzRqxmdHw/XpdN2X5sI1l8s7DKCnrXrL3enTWwv9Yam0vbwJSTzpVhaaz3U7SwcQyJOfw4tPaqtJ7h8RZj8heWVZePIjbXrL5ZuEa1MpBrV1qw/trP8Sv7f1c3FvYHz1ohso5vpGms854xPaqtJ7h8RZj8heWVZePzNw/Apzw1fpGZJ6K/Apq1glBSbOsvexJQYh/L+mpzllNCNaLRh2vp4vqNSj0lHjU9qq0nuHxFmPyF5ZVl/AfIEmL+VP8Ac4tqdxDPDPP9O0mRUQ/0Z3galfM1YooUQ/yJZ/7LQOHBa2onJzcPiGc8cntVWk9w+Isx+QvLKsv4LSSeioaMctL/ALEtTk9JwJCDzw0UlYvOXwCe1VaT3D4izH5C8sqy8np7VVpPcPiLMfkLyyrLyentVWk9w+Isx+QvLKsvJ6e1VaT3D4izH5C8sqy8np7VVpPcPiLMfkJalKSZJ0dXMGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujyhpdHlDS6PKGl0eUNLo8oaXR5Q0ujygoaTMyLxSe4fEWY/lP3D4izH8p+4fEWY/lP3D4izH8p+4fEWY/lP3D4izH8p+4fEWY/lP3D4izH8p+4fEWY/lP3D4izH8p+4fEWY/lP3D4izH8p+4fC/tI+7pZtL5KVoteAXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQXB8EQfc0fy/d0/t/XpMaLQ//aAAgBAwIGPwBOrp6c1nN/sLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsC7pWBd0rAu6VgXdKwLulYF3SsD7ujsfc0aQhznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznJDXpaOto9X/AOhujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQbo2g3RtBujaDdG0G6NoN0bQNGfSzSeg4Ic5yQ986qcnq7E1ZPQcEOc5Ie+dVOT1diasnoOCHOckPfOqnJ6uxNWT0HBDnOSHvnVTk9XYmrJ6DghznJD3zqp+C0lnoJ6cQ0YJaP/YpqanZBw1HniIpos4vOo9FJfAK7E1ZPQcEOc5Ie+dVPwGc/kRDRglpn41MTU7Q0lnpHISy2eigSksq1k4rQQf4k/3FeLd8AKHE1oeyrah8yOiRnL5keOV2Jqyeg4Ic5yQ986qcfmR+Vf8Atd8XLxDOs5uxw4JwVH9UN9L3Fifswz+X9RX/AJ80uY9aEew8jprDSQeknGq7E1ZPQcEOc5Ie+dVOPzpYiayXk4RLS0kwURPUqttJwzhIvFNK/wCO3Vwc6WTaRsr6eIaSJydpGMV2Jqyeg4Ic5yQ986qcXmL8kTwpZnL5QSln+NlSEs6PNKadotaHv2hmPC+0pmIz5lvCzFeqZ+n61OgzP5meES0HmUCWadDP00k/Ti1diasnoOCHOckPfOqnE6x63gS3ZnDMX44fgS+raqy/bNuF/jsS/dJmI15lpriws5Al7TK9+01gaR/M9hPiVy+IGtZ51Kw9Nd0n+59HPjFdiasnoOCHOckPfOqnDzrPRrK3UjRhfiT4v6libxYJLLZq7QJSWVayZDhq2q2yoGlTScLRNiJqqcVKa1MppfSDWqanwJw8zKEtq6bQJKSzJSzjFdiasnoOCHOckPfOqnDNRNwtabtpewzgq/TWhvpe4pSjJ3Yji3cP53kPVU4sGpR5kpaH+kNLCXt7DJCf/lPiBIR1VvqVjVdiasnoOCHOckPfOqnEZyL8a9ZDyJuES0tJBLT1K6KTIaFMq+QNCtnppYRKNk9Ve7ZaGgg/xJ/uK8W74MMkJLOpQ0S+ajbX4rGOV2Jqyeg4Ic5yQ986qcQaSaLWRvWsM4SuqIx5luUoqWobXl2MbmLrGdV6pr6Po58ersTVk9BwQ5zkh751U4n7iS1Yn+S01hZy6wS9ple/01pMx9QNGy0jc6auMKKsvyGx9CfFvqo/AK7E1ZPQcEOc5Ie+dVOJOGe1RVsqBpU0n5YWiq7iaqt7ZVLnK8h6yd3bS9i/uRVIIksIUomvFupF4jiSG0cSQ2jiSG0cSQ2jiSG0cSQ2jiSG0cSQ2jiSM6T0k4auxNWT0HBDnOSHvnVTivvJ3Yjq3cP5tw9Vbq5c5MRNZLyJvwiP3rKw1diasnoOCHOckPfOqnFGhTKi0QaFdacIlGweqvdstSmjaaRv2mfhEfvWVhq7E1ZPQcEOc5Ie+dVOLKKTUNry7GH9s2oX+OxKUVLMRrzLbXF8Gj96ysNXYmrJ6DghznJD3zqpxeY+oGnZaRuYRLL9KSdoEpLKtYpDhq2qKtlQNKmk/BI/esrDV2Jqyeg4Ic5yQ986qcZpE3D1pm2l7DOCr9NaG+l7ilKMndiOKd+CR+9ZWGrsTVk9BwQ5zkh751U40zItSJrIeTNwiUlpIJaepXRSZDSplWqoGRINReIMKDCgwoMKDCgwoMKDCgwoMKDCgwoMKDCgwoMKCUqLRUWethq7E1ZPQcEOc5Ie+dVONNO0WsjftM4f2jZiM+Zb+LV2Jqyeg4Ic5yQ986qcaZk2vVRzTcM4yupOrD3tpU34tXYmrJ6DghznJD3zqpxpmTCdVG7awiQlpQJCWUlmkNamUg1aStY/EGlcSg0riUGlcSg0riUGlcSg0riUGlcSg0riUGlcSg0riUGlcSg0riUGlcSg0riUGlcSg0riUEGfzP51jw1diasnoOCHOckPfOqnGaBNxf8AHtcTPFhnGNpeqjctSlBLqTrL3/DN+CR+9ZWGrsTVk9BwQ5zkh751U4s1H8kp+Zg1nN+lGzhEj9Nrc2gRF8kpkNZzd/ZBqP5qV8Ej96ysNXYmrJ6DghznJD3zqpxZQS61ay93ZS9h6Sm4tTZ5pdBLEKvtcvwaP3rKw1diasnoOCHOckPfOqnFGtXUgunEDWppR4REbCNZfLOlMybVqI5pvwiP3rKw1diasnoOCHOckPfOqnFfZT1Ib37FbDJJtq1onLMlMyYRqo5p3wiP3rKw1diasnoOCHOckPfOqnEms+vY+pYMz6zwvuKYh0omzzS6BNxf8e1y4v7cS7Uyf/GrkVtcXwKuxNWT0HBDnOSHvnVTidBLELVn7fLhEkvmagUMv0a39qQzP5EkGv8ATZ3cYUGIflK/8+Th+AV2Jqyeg4Ic5yQ986qcQZk2vURzTcM4ytnVh720qbKUJPWvWXubKZ2O0F3qf7iefxcWPV2Jqyeg4Ic5yQ986qcQZkwnVRzTsIkJ61AkJZTIa1MpBrU0o8Is7CNZfLOBxYZfjNtP/GrkVRwyUR5jSP8ASIltL6fpq45XYmrJ6DghznJD3zqpw9Am4v8Aj2uXD+8rrXqo3NpU6UoKepOtE3vDNwyI21ay+WaMx/MhpJ+cJTP0/QrprYZLR1l00RppnJ8CujONV2Jqyeg4Ic5yQ986qcPRWRKSNKCel/1qamq2ujQzKLRPAJBdW1ubQzF8iKQ1n+jO/sgzPrPC0zYhV9jmlNCizpUNE/mk2FeJPRrD0k9W2nxp6MglpPOlWMV2Jqyeg4Ic5yQ986qcTmiFpfVtpnAzh/lR/c4eWXSNuLrTNjml0CYhV9vlwiIuswSC/Rrf2sA0Kmq8CvEDQvrLppYeY7pTfOnprAjI85Hi1diasnoOCHOckPfOqnF51For/wCRLU7xgiXrQWtLxfRo/VKZk2rVRzTcM4ytnVh7/im4WbqWlhTqvpqg0qLMpOFooLeVso3gSCM1ZvF01cWrsTVk9BwQ5zkh751U48zJhGqjmnYRIT1qBISynppTsPTSX5U/3E+He8HDg+GGTS+X6hoILRTW+pWMV2Jqyeg4Ic5yQ986qcfnYX40vp2qwzqLSR40s2Z2CcVXWvVRu7Sp2JONDLW/qJ/9OfilJa9WFSibv0/WCSktFKf0xquxNWT0HBDnOSHvnVT8Dnh/iV/bsTeEZllm+rZVOkJH6bW4CIvklOK+7DL8Ztp/41ciqIKJG6tmH/8A05cersTVk9BwQ5zkh751U/BaKi0knsqGlBPRP/jUzNXzcQNSizRF0UeF74tXYmrJ6DghznJD3zqpyersTVk9BwQ5zkh751U5PV2Jqyeg4Ic5yQ986qcnq7E1ZPQcEOc5Ie+dVOT1diasnoOCHOck0Ukk/npawZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeGUUu8Mopd4ZRS7wyil3hlFLvDKKXeDWosxnJ6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DghznMp+g4Ic5zKfoOCHOcyn6DgT9xf29FllP+niF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBfFxIF8XEgXxcSBoaX4/t6On9GZrwj/2gAIAQEBBj8Amok1Y3kyj1qnmzqXbDhxa9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+Mr0uvgl8ZXpdfBL4yvS6+CXxlel18EvjK9Lr4JfGV6XXwS+MorP5SuPlYxdfgvZKObLj/szVd+m11XP6zL1qPKrV36bXVc3IGymykCHPWfDYeZZeYeefN9551tADVut446sco5a9gx/hc7x1ewQ/wud46vYIf4XO8dXsEP8AC53jq9gh/hc7x1ewQ/wud46vYIf4XO8dXsEP8LneOr2CH+FzvHV7BD/C53jq9gh/hc7x1ewQ/wALneOr2CH+FzvHV7BD/C53jq9gh/hc7x1ewQ/wud46vYIf4XO8dXsEP8LneOr2CH+FzvHV7BD/AAud46vYIf4XO8dXsEP8LneOr2CH+FzvHV7BD/C53jq9gh/hc7x1ewQ/wud46vYIf4XO8dXsEP8AC53jq9gh/hc7x1ewQ/wud46vYIf4XO8dXsEP8LneOr2CH+FzvHV7BD/C53jq9gh/hc7x1ewQ/wALneOr2CH+FzvHV7BD/C53jq9gh/hc7x1ewQ/wud46vYIf4XO8dXsEP8LneOr2CH+FzvHV7BD/AAud46vYIf4XO8dT9xuexjEKBGHNIlP22Y22AqqJiRE+iJpWoG0d4BhufJdkA4EYSBrBp4mxwEycLijp4W4XrUeVWrv02uq5ubB9za/xz39XbVeahy7dWj6+Z+JPcL1qPKrV36bXVc3Ngu5tf457+rtqvNQ5durR9fM/EnuF61HlVq79NrqubmwXc2v8c9zP/IpWaSUpbk3a0mI43q8zrgto5lwzZUUt6rW7Otz1wS6E8IIyYBk1CAq45t/NrKt20keOcVm4gRhHcJCIMjhNqiqmhdIVFvE2C7PblShiC0yQgSETZuZlUudg3R7URoTkNgDfb8mcISP6DSq4jo4VQbA5bJFrO4FqmJT7gG3rl/VtrlTH6QuAK9nl3C2MYs8iNJE5Tay3HAIMYqEq8FEx4WSrpYH7DLfdtkg4xvg62gmra4KSIqYpXs5N8M1UOA3s9MA5j7TAmTzWAq6aBiuCc7GrhfJ64Q7cw5Iew31QBxQR7Y14I9tULZxu0yLc/ORzUyHnWyDWNgrmTRgvCQSy9tzFxsI2iTcFtryx3ZbLjYgTgaHEFF08A8wd7US5wXEdhzmW5EdxOubdFDFfgWi2glw3JzIvtMKw0QgWLqqmOJaNGFezk3wzVIMuxXFhpV0m2TDqp3qm31aj3qxyhmW+Si5HBxRRJOMBivCAx64SqdbHNn5jjkGQ7GJwXWsCVk1BSTFOflrTs5OROeqOsrTka1OOxLqyOsctkwRB1QTQptqJGDgIu/lLOPXgNWry62v3D966/JqDAMnk+rxxzb+bWpWzG0z1mkvM7TA+bMcHG0JnydRFcyqmBZs+jCvZyb4ZqvZyb4Zqg/7hfuiR5GczyJIOsDWY51HPmwy87er2cm+GaoRl2K4sNKulxsmHVT38qk31aZvVhljMgPYihoiiQGPGbcBcCAx7Eu64pDSkSogomKquhERKYti2mU1EflDG/eRON6sWyPIjxDxsnXknY7ltkzbc9cBuTjjQiyYgoaoUJVXNv45qgbSxoxw2J6OqEd0kIx1TptLio6NKt48xtV5qHLt1aPr5n4k9wvWo8qtXfptdVzc2C7m1/jnuZT/qiL+JbrZL62d+ixWzH1Dv4l2rP63b/DP099fO6iU7NiA5lg5HXn28UVrE0ADVU0j9IQihdlTT0hxP39bUGPeGk0Kp4LkfROxfEc31msDrad84uv6LtPz5+zVvlTZRq7IkOsARmZb5EqppVaWyswWW7Qu0EWN5AAILGpN9sSbyJwchIS8Gm5DOy1tbfaMXGnAjgKiYrmFUwTRgqVbtj4zmEi6OJMnCnOjMFg2K+849wv8AIrY/aRDJt+5xmrtCNUUdU+25n1S6dKiCsGX1uWrZf4K4xrjHB8R7EiThgvbNnmAu2HcvO0K4a2FHXyUV3ikOKjbKdLWmGbta2n2xEyNuxOR1fRUzK8sk1R0s3RaTK4fanTuz7zqlOsDyiIEuKrFkKrjSp7wnrQ7XKFPefReqVXOXf7LCuMpq6G02/KaBwxbSOySCilvDmIlqbOjQINovbRN/upYmVpx11TFCb1Yr9IOrzKWI8Dj1tU0WP7tFyIbePFR8kdQ8vvqAt5u8ryW9NMP2t29TkktSkFWSFDeVEND4OGZE36cWRb9nmmUFdY4px28o89c6EOXusags7Gkb1oiXZ5yI8KkuFubIsxERcLIUfgYnx83ZFWyHTuH/AMtWx43+1RrokWM4sZJTYuZFcdLPlx3s2UcasDths0S2Ovy3hecjNC2RijaKiEoppTGrNcrvs9BnT3jlo7KfYA3CySnQHMSpiuUREUpy3WWEzb4I3COYxo4oAIRkSkuCdGrnLv8AZYVxlNXQ2m35TQOGLaR2SQUUt4cxEtT50W3QbTeGSb/dhxUFp1x1XBRW8gr9IKt582KcDj9bW1ja4+RIUIhx3kdVHkXDpig5u9q4ky5kuN3T92wcOMivoutNOhkZRzhdnkpjb0sfIn7iUBGsvWCGKPY48VXRcZ7oatsh5zWXK2j+77jjxtYwiIBr9Y0rZ49nmrZfzmTybdbOdKV+Me5jarzUOXbq0fXzPxJ7hetR5Vau/Ta6rm5sF3Nr/HPbvlNxlsw4+KDrpDgtBmXeTMaomNeV2qaxPi5ib8oiug83nBcCHOCkOYV4yUP/AFRF/Et1smXOR2ai/lFj4q2ZVP7l5PgkupVnHnrdgVE6UZ/46cVeuenqnwYf+FbSWW4hrINxsMiNIHRjlckMJiOKLgY8YC60qODdFU7chpFnmmKC/AfJFCSApjiQcF3L2YOM9lRPxnEejuvXQ2XR3jAgdUST3iTTuf8A5ND/ABDW5Nuk95xNnwmNxBcbFHCSFGJGyJscRx1mU3RHHjOU1bbUzNZu1vfbetxOsA22g4at1tSFwsoq2ubi8ZsKu2yMhzFy2mk2AKrp1D65XhTtW3UEu6f3LVsVGPf/APUrjgvOTM3HBf8AzHFT6ul2PurM9965NvreyajtqBnKRQJBVXEVUBrI2hYdZmqG4j5FZrkZW2U4aZMWXjRGnSHEkHI4jZl2I56e8+i9UqmXqyTobAxJJRVjSTdAjMGwc0KAGOlHERM1HYduHpVjBh1Y855plH3GHEVMCIMw52sOFnbU+Bw2xcqLatmxzW8kSQstSRw5JuCn05mOCGpig8XgZcohwam7NhJSGVyu81pJJAriBg66eORFHNxeypVb2ojEfOQorgp8KOF1Kl7N3eNFeiuSGmLu4gIrisHlIH2JGUXciAYuo0fALi5Ac4Y7H/8A+h/8tWy/mpcqdbN+eP8AJJVi7uZ+Mep7z6L1SqZerLPhxwiSSirGkk6BGYtg5oUAMURUcRNNFYduHpNjbYdWPPebZR9xg03iUMyZ2+fnbU+Bw29ZUe3bMprIL6JJKcpC4conBRUeJwUQSzDly5EyZeLTez7Jf6LZ5pGyTHQUmQIuOl3oapvugOj/AO3cZLiKNwAYjySit5VlMqjoukiO4prJA5zw7Kpezckssa/tJqFVcESVGQjFMN76RsnE7oW62X85k8m3WznSlfjHuY2q81Dl26tH18z8Se4XrUeVWrv02uq5ubBdza/xz27cbZbg1tzjk3NhMpvuOMKuYE7Y2ycEO3y1O2dk2ZLjH15ussuuFFdjvqiC4J4g5mHEE+jygQlm4VDtlOYUYMSad2uMxAUWdfmVxpltV67WZeDjwWhoP3O2r93s73lceMnGebUFF1sO3wymCddkyddTmzc61JcrdHdNWojxlFkRjIsXAzKDnBU8xZDbzZ83Cq3WiDaVaYYNShWmJmkOG6aZVccPKObKmhOAAAOaomz8lRWbHiPOTVBcw69/O64iLz0BTyIva1dfU7v4mPS3y3R9Zf7EJOt5E4b0TfeawTjqP61tO1MQ/WVavqJf4c9z/wDJof4hqrnKZd1dyuA/u+3YLgWsfRUIx+ra1jndCNXi97UwSmW5kwiW9vWOsorqJrHjzNG2q5RVsex4ZV7PY/8Axc3x1KzIIghW+aUWUq/2lukKmBr0foTB7uxpZROikYQV1XsUyICJmzZt7LhpxoTnobkC5zTefBFVMlvjCpC3mRcQxZbBrMnXl2Vez2HveVzfHVabhs3EKJY7g0TJtaxx1AlMriq53SM/pGyFRTN/ZnVtvBGhzUkxItxRN9JLCqDmPd6HU7Vwau/rdz8KxS7a2ZhSu9sby3RkExV6GGK6zBOvj7/bM5v7oKXYG8yMZMYVcsLri6TZTS5GxXfVrjtJ/d5x4rQ1P2jYjhKet12muBHcVRE8XXAwVU0pxqXLs7BQucquvKnwaKG7TopmxMktvXWYAEEWPFbURUAIsU0NDq2gzE4Zd+dbHon/ANQ0fdq2X81LlTrZvzx/kkqxd3M/GPU959F6pVd/W7n4Vil2xtMZVvVpD/Xg0OJPw03yJE3zj8fN/dZ+wCr1YdopSK3ZYjtwsutJEU220VXIgEu+WfKTAcbhudaA1OnbTNlNt4C9cbumY20ddfJUbbzgQmOLhqfBLitZa9nl+9zPHVFl7NgUK3lqblZeEbiNm0SIbec1Uyyuhm4Rfq3BrYS/wlRY9yV58RRccpE03nBe2bPMBdsNQNmotkiy2IGtQJDrjgmWtdN1cUHRoVzCkT/lyFpVP7Z2hLooi/DubVeahy7dWj6+Z+JPcL1qPKrV36bXVc3Ngu5tf457mEkXG0w5r6YIjsiO06aIm9wjEloGWGxaZbTKDYIgiKdBETQm4h3K2RJxomCFJYbdXDpmJUQW2BHggXGGM0DKLh0UBBrBdKLvpSmxHbaJUwUgARXDoYom4jjMZptxMcDABEtO/pRNzXLGaV7HNrFAc2ZOfjhjjQ+UMg9kXEdYKFgq6NGKLWrZbFoMVXICIKYrv6E3FN+M06ZJgpGAkqp0MVStVkHVZcuTBMuXDDDDewwrOxGaaPDLmABFcOhiibiA+0DoouKCYoSY9HBaVlIrSNEWYm8g5VJOeqYYY0oMNA0KriogKCmPRwSlRUxRd9KEwiMiYLmAhbBFFd7FFRNFKRRGFIlxVVbDFVXfXerREZTpNh8VIIoiCmhETQiUPlDLb2XHLrBQsMd/DFKFtoBbbHQICiIiJ7yJSI+yDyCuIo4KFgvvYpSNsgLbabwAiCiY6d5K1b7YuhjjkMUJMU3tC0oMNA0KriogKCmPRwSlRUxRd9KRFhR1wVFT6INCpvLvUWoZbZzYZtWKDjhvY4JuDr2W3suOXWChYY7+GKULSxWlaBVUG1Acoqu+qJhgmNfY2PBh8VfY2PBB8W7tV5qHLt1aPr5n4k9wvWo8qtXfptdVzc2C7m1/jnubvG0MZkJD9tjq82y4qoBKiomBKOnn1/y9ebdHtjslojtzrThEjjrekmlz88gzEHcdtVyubYI45BivyQbJVRCVlsjQVVOcuWrpBn2yPACBHbeA2DMlIjPKqLn525coFqssWZbIkk2I0px1xCdBssufg6OHgpD2tQLxBLPEuDDclhefkdFCRF99McCp6ZLeCPFjgTr77ioIA2CZiIiXQgiiYrTsTY2ztzIra5G7hPVxNauOGIMNqBiC9bnczl1zYULe0Gz0N1lCTWBGV6M6grz01pPoq4b2gai36xv6+DKRcEJMrjZjoNtwdORwF4yd8OYCEqj7GP2eKxGelSoyywccVxBjg6YrlXg4rqtNOXm+vKDSLkjxm0Qnn3VTFG2hVUxL31XKPXFShY9nYLIKq5G31flOZU+rJhPk02xtZYmgikWV6VbyMTb7bUvKefDnjrQ/3ajXW1SQl2+Y2jsaQ2uIkK/7UVN4hLhCXBLhU1a7zZ40W0JMKNKmtOOKbbWdQ1uVdHA0Efa5stC42SGBohAYriioulFRUpdgFtMZISXI4HlqG5rcgY8LLxc2jcZ2ftVtYuLwRxfnG8ZjqzdVVBtMvP1aZy7sKC+ORwiTWn3Is2M2SkAOBgQ5VXhYE2bZaaut2abR1y3w5EoGiVUEiYaJxBVU5y5al2Wdao0FqNBOWjzBuESkDrbeXAtGH0u7JkiKETDRuIK7yqAqWH+ytOzkHH616kV7ZqIYY8IQkOiqp7yqJdSnJNrUo0+LlSfbHlTWtKW8SKmhxosOC4nfCBcGoFqhWqPPalw0lE48ZgSErpt5Uy6MMAr2cheGdqPHXZ6EKPOg2pa13QhEiLze1Xmocu3Vo+vmfiT3C9ajyq1d+m11XNzYLubX+Oe5vanzIv0hpvau3qTLNvmtMhNbLA2ZWVXml6KfqyUS7WrreUyhcG7bMjXVhOsktxizKidg4io632p5etraPzJnlau1wjmrc+SKQYBpvi9JxHOnvtt6xxO4raLbdsXFetMthtgE0CTAp/qiw67JrWSx60QcqRs1KczTbA59AirpWI+qkHT1bmsHtR1dQ7PHNQK9y0B9UXDFiOOsMdHRcVmk2vkRW3rxcn3RiynBQiZjskrWVtV4im4Lmch43BHraetsxtpm5CiLbrqraG7HNFRdCookTZJwTbzZS7sRKp8Rm9PXRmeTbptONCy2DoIoqYChGSKY5RLh9YNQvWVx5GRTtkRxXI1obYiwmE4qOSGwdcXDszIxAl/wwqPa7REbadFsEmzMqa6Q6icI3D4xYljlHiBxQyjVw2jaittX+zAkkJrYILjrAqiOtOkmkwQFUwzcQg4PHOr5su+amxBJubBRetR5SB4U7XMLZd0Z1e24DWuciLMmPAm+jMciN0kTn5A4Xc05sddXlO52VtCt7hqmZ2EioKB0VWOWAfVG32FF6/d/3ql3KaerhwmXJEhxetbaFTJfzUq+Sp5kHlDEy4OEi4ZCUdXEbxw4rbhsj9U2VTdkLkqsM3hCbRk9GrnRcyoPvKQa1teyPV1tN6qnfhjq6ep3fxMfduHmz3JrRg82LgfuyTwTRCTjtJvLT1vu1oiyGHhUVVWgRwFVMMzZomds060hWo1n1iqA3B+xyudrANwmRVcP8UWnO9qy+qh/EPVY4k68QgmxrfFZkgUZ0iF1tkRNFVGl3iRaiWu2XOFJuExxGorAxnEUnF0omJNIKb3XLze1Xmocu3Vo+vmfiT3C9ajyq1d+m11XNzYLubX+Oe5vanzIv0hrbnZ65jjGnORQRxERSacQHFbdDHr2zRDStpNlb8hhBnxJNuuTQJmFVNk/JZTaaMycNFH/AAXT66to/MmeVqBsnFcxj2ZvyiaKbyypAooiv1bOVf8AOKouxh7KvSogxnGJ7vlIDrykZlfLLq146mWVM3F4NW2chkFrmuLAmoS4r5PIJBEiww/VOat0tHWVs3cRFVjxZb7DpJvIUhsSDHwBVborRoT1sflRpAJviRPE+OKe+Dw1O2gupEkC3t6x5G0RTLFUERBCUUUzIhEeFxqkrs5MOQ7DQClsOMuNG2jmKBjnFALNlLiEVQvWVx5GRV1mGKkOvhzWtHGFGGl0d8JDUebFcR2NKbB5h0VxQm3BQhJFTnKK1tG5JNBWZGKDHFd83ZP0aCPSRSPuQKtpbrlVIzUdiLm5ym4ZOYJ0kb091SgYoQGtyEhJMUVFbcRUVFqJf7AhN2p15ZlnPrMmP08I+1ET1fbMGBceoF8gZ0iXK7rJZFxMpojgqWUk08VdFfuRhzLcNonPJ0RN9IrWBvl330bX+YVXPW2N25XC5ON5pIPi0gstCuRtEUDXjmZFp7Dsaf20sEVy0vOyWp7bBmjitygykZoQoGKG6Os76rlfouhm5WGTIQMcchHENSBffA8wL3NXT1O7+Jj7tw82e5NaP1ZJ/Ta3GJVvXWsSdpTmMkOnMwzJJ9S8E3mqy+qh/EPVaLo/cbsD8+FGlPCDsdAQ3mhMkFFYVcuJcHFat9+g3C6OS7a8Mhlt51hWyId5CQWBLDpFze1Xmocu3Vo+vmfiT3C9ajyq1d+m11XNzYLubX+Oe5vaaNEZckSXYZC0y0KmZLmHQIiiqtbTBdLfJgG6/FVoZTLjKkiA5jlzoOOGNM7W2SOb96tQIzLisipm/EUlVFEU4ROMESlh1zZH2A1tXc7taJ0Zpi2I6AOx3WydVolNQbQhTOZYcERpLxthZpTUF19+63AZkVwWHFRczbH0ooBBrCAcn90OWsf+U7P9wjfMq2XrY+yEkKa0seXBtkZcjTzOkXNWyOA60C6HGa7ao9p2pjybfcnGhjyzeaNt5uZFVECQgOIOZDwF0k64TNupS2+Ib9skKmseBkpVvkiGOQiyYEy4mO8pMvf5dR7OlqdKEJoSQoEdxiLrE0I4+66RImH+K9qx7qvIHXQk3icaSLrJbRciuIOAtN44KrbSaBIuORGfBzZBhz5NnnMQUuFwJZTkZ4GkEmn0FVMhQcFVUw00zdbQ43H2mt7attazQ3KZxUkZMusISUiZPi8MgPglnbWwP2t4oDCqjEO6RXXWm8V06h5tW1VtV3kF02uwqK1JgO+QsFiz9CUO3R82CE4RnjnLDtnnsv6saZsUZ3ymQRlInzMqBrXzREVUTnAIiIAmPFGkmzbTNiw81w/1L0d1trhAaDwyFB046NNSbOao1cGl8ptUlU4kkEVBRV/u3EVW3O1LNxhGtnTn2OfGajTsH3nIzothlQkXFzLkw7bNSQoNonJaorrdot8oozyMYazK6+p5UDIrpGuszfqgCosNdmLW/wCTNAzr3oUc3XMgoOdwlBVIywxIlpyfspYY0O7Wp0ZGqt0UG3H2S4Drai0KEeXEXR+rLsq2x2Nu1pnRnodvmv2jXxnm9Y3JZNDZDMKZiF7hIKcItdT122fsE4JciOUVxXre+6OrIxNcEUE05mxr0K9/CHvm0dx2wjlGuyTHmhbOOUVdSIgorqyRF3yLhVOAEUjKO6giiYqqqC4IiUt6sOz88ZpMnHzPW99wcjioq8FQTTwUp2zt2y4MNyxVp5YlscZNQJMFTXKGLSduJh3VFtTtRkC9m0TMK3NkhpGBzQZuGKqBOknAQQUgAOuIj+js71rtcyeyFsQDcjMOvCheUOrlVQEkRcFqHbYtkfGLBYbjMIVpeVdW0CAOK5dK5Rr0K8nv/uh35tMOPJg6bYE4mGGBKKKujp81tV5qHLt1aPr5n4k9wvWo8qtXfptdVzc2C7m1/jnv6u2q81Dl26tH18z8Se4XrUeVWrv02uq5ubBdza/xz3ubkiQ4LTDIE466aoIiApiREq6EEUTFa/cv/baEhtKeqZnOME/JkHzlYj7wgvW6wHHD7Fri0zN2ljPDDdLgN3K2gwya7+RHGm2CzYdbrM1OSojaw7pDURuVtMsytqeOUwLBM7R4FlLAeLwhpu3xWBuW0kpvWMw1LK0y2ugXX1ThcJU4DY8I8vGb41Fc7DGknb8y5VgWsHY+KLpETcaeI8Ox1hFSWn/uLBFY4nqpE1lkmJcc+erzHFMR64QBtwf8T9XVxvtqeB5G7c9OgvjgbZ5WCdaNOcQrwVqHC20ejLY5n+nckNMo0TDh/q3SUV4mbgudiJZ+spaesd9ejuQG4b74iywLZZ23AEeEi9AlpuxWWM3N2iebR50382ojNmq5VIRUSccPDghmHLxy7Gv32Eaelrya5HBtLWp1WGbOiqwpq3l0583F66g2Y2pYZj3d8SW3zo6KDb5AOYmjAlLI7lQiEhLIfEyAWXPZI+zzrDbU5h5yQjzKOqpAYoOCrvaFqw3m4EJTrhCZkSSAUEVMxRSwFN6rJK2ecZbdmyHm5GuaR1FEARRwx3tK09tpNNor43AuUkXBbQW9ZEJ5Gvo00YfRDmponn4bjImKugkYUUhRUUhxx0Zk0VGnxSzxpbQPsH0W3BQxX8orV2Ysj8RLOzLebt6ORxMlZA1ECUsdOZEzd9Vlv93IDuM4XlfJsEbFVbkONjgKb3BAaesmwbDUp1g1afvD4q42riKqKMZpFTPgv9sfAPrGyHK5S3iZFnjbRTWGT1pbFkQTTmJUYExDtlKmNntpGG7ZtA/wYj7OPkskt/IiEpEy6qcUCIxc608+Rv3ParzUOXbq0fXzPxJ7hetR5Vau/Ta6rm5sF3Nr/HPe5zm4xq2VykMQXCTf1Zqrhindi3kLtSq9bTuMCdwKV+748gkRSbabbB1xA7HOTo5+4Gp1kubSPQbgyTDwKiLghJoIcd4wLAwLrTHNTtztU6fKmvsLHf8AKHG9SQEQl+rbANKKHBxIq1F0MjjXa6u65EVUXyONmJGhXfHCOzq0WmYcNkI8WOAtMMNCgAACmAiIpoQUSoe1zLIt3WFIbiSXhREV2O8hZUNeuVtxBydqZ1tNb5JKZWVi4xWCVcV1JxVeBO9JxwU7Wr3eISIbNhBl6a1p1mqfcVvOKJvi2WGs7EeF1tLZbm7m2gsQA06S8Z+Lhlae08Yxw1b3bZD/ALWpXq6VyrVNbTEwrlruLTHk8hRzNI9GFBJk+dmwBHMq8cC7U6aZ2ms8m3SMEFyRDUZDGPPLKStugPapru+pdttkb5JlT485LmsFl5tsGDJzWIBRjZB9tlSxEULreCJ1sx5rJ5QK2T9WRv0ErZnzuRyY1K9U3v8ATk1tbdt+VYv3e+2ib6tvvkw5+mBd7Ui8qf8ArbBDkWwVx3ngwbi/Jej1/wAzF9pevn7tbToNtRNcfwk6H5tJco5ZJAwJTDR88SkznI6EnvjrcyVddo5rQvLY22ghCaIQi/JU/pUx69sGiQfrNwpNmFIjUxti7RW20QRadUyEsiDhgmuZJzvqtt1QUFLhFYlIKbya5sXMPle5bVeahy7dWj6+Z+JPcL1qPKrV36bXVc3Ngu5tf4573N51kFNIE6NJdypjlDhNKS+9i6lXyyq6PlcecktGMUz6p9kG8yJzxzM4VPvE0xbi29hyQ6RllTBsVXDFeeS8Ee2o7ZEt0yBdWWFkSGnEF1gQFRFcr4KmPCNMM7beamTuy+Tx7Zd348l09CCy8ps61e01butx7ChcbJDbNEIDFcUVF0oqKlQtnkdFbjc5bb2oRUzDHjoSk4qb6IrmQR7Lh9jW11xeFRG6N3FyPimGZpmJqsyf5guj3tbVRJTYvRpEBpp9k0zCYG4QkJIu+JCuC01Liib1tbNXoSrigybe9iJsku8rjacAuxdAHewqSYY5Ct0pRzb+CutYY4U9/wBv7/aZMjPMCBOOYxHKCimQojhZ3CJWkzCeZWu3oziQ37LIPSjkF4smb6p7Wt4dqAhQQbdcfKnrXKYAn2eAj8d9AMmXQRS47Z5HAx43F60q2VfwXIbEttC52Im0qp8qtlXGTQxCA20SiuOBtYtmPTEhVK2XjZk1xSJTqBjpyiDYquHQxKnkJMFOzXhz8hlJVP8AZX/ca0I3rDm2dGWQ/wAUtbq1/I4grV52QXPqblNiTEwXAU8nFxHBJO3XUL/lVsG2QZH58124P4pgqrKaM218DqkpYccFN4YUiSIDpVfJbgcgsETf4LS1fdnX3EB+5ssyYaLozlFzo4KdEsjufDsWz3HIdvLyj91x2bZ9HpzPoZuGKYdcJvasu3GrRa3P1kCFHinhpTFloQX9H3LarzUOXbq0fXzPxJ7hetR5Vau/Ta6rm5sF3Nr/ABz3ucm3XBkZMGY2TElg+KbZplIV6aLRXv8A7ePvzYbZKUR+K6Lc1oC/snW1UUeTrV1ecXevbDi0zab5EuDsMSRVblAzAjYp17iIjAuZd9MUcLsKeCQ6Eu/3FRO5Sm0XVigIuRlpSRC1YYkuYkEnC4XYiLe0OzzrUbaJsEalMvKoNSmw4iqaIuR4E4KEo5THKJZMlJYrZGugQmcQZabZYntAPQacUX0AegIFlobvt489AivGhTZct4XpzgCnEabRTydgOtyC0PFbPLqyuGztjio20FrfhW+IGCaVYIGxxVd8lXjEvG4RVfJG0dpctzMqK0Ec3DbJCIXFVU4BHzqeixGxK+29Vk2gyXLi4n6xnMvOfBMung6zVkXFo7ptBZXYEAre+yj5m0SawzbURwAyLSgrzq/5q2VJty6ONi1cLc8aNa7VDlbcacLgZ8iCBC4QDlEeHQ2WOzeEjtDqm1WMzIIRTQiDJIHDwTrS1vc1H2p2/FY7Ed7y5YzzyPy5UlCzgryiR5Qz8NzOesPiZOHnFIDLwRbxBcWRa5LmOrzqmU2nMqKSNupvkIkQEIHwsuQn7fYYdwZimakTcUGZ8Yi3tYAqjwCRIiacoH2dNz9rkfiBwW3rjc1EFbaRcVBmMGBc8iEAbbaz8YwzVcdlbEwTiNWaRb7eximcyWMTYIpLlHOZLwi7Iq2ge2ktTlublsRwjE4TZZ1AzUkTVke9im/V0btVmcOwybiZRZyGygDHeczIWCmhfRiWng9bVgs+yltOcttlIisNk2ORkGCbFeGQJ2KVZLJfIixp8duQEqI5lPBHJLpohZVIVzAaU5ff+3Ra+HrPKGIDbyMS4jmObBlwiATAF0tlrBeHiZTy6wlszjd5Rok1auIw0wapvaZYgDnfa6o+023Gq8piEj0CztmjuV5FxF2Q4OIKra8IG2yMc/CI+DkL3LarzUOXbq0fXzPxJ7hetR5Vau/Ta6rm5sF3Nr/HPf1dtV5qHLt1aPr5n4k9wvWo8qtXfptdVzc2C7m1/jnv6u2q81Dl26tH18z8Se4XrUeVWrv02uq5ubNbSMW564t2mHBlKw2hIjisS3zUNYgnlx6OUq/l7K+9n+yV/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stfy9lfez/Za/l7K+9n+y1/L2V97P8AZa/l7K+9n+y1/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stfy9lfez/Za/l7K+9n+y1/L2V97P8AZa/l7K+9n+y1/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stfy9lfez/Za/l7K+9n+y1/L2V97P8AZa/l7K+9n+y1/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stfy9lfez/Za/l7K+9n+y1/L2V97P8AZa/l7K+9n+y1/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stfy9lfez/Za/l7K+9n+y1/L2V97P8AZa/l7K+9n+y1/L2V97P9lr+Xsr72f7LX8vZX3s/2Wv5eyvvZ/stXbZlNiJUFbm0LSS/KDdyZXBPHJ5MGbi4ccatLbzZNOI/MxA0UVT/Unzl3C9ajyq1d+m11XP6zL1qPKrV36bXVc5vaaBA2luMaHHuL7ceO3IcEAATwERFFwEUTnJSLjtXgqYp9FN3l72v/ALr8DN+bXle0Tk1raNqFcXHXZyOBLEgN5WiLWIjiKgIGTHrctIibWXTBNGmU4q/Cq1FfuUo5l0t770OZIdJTdNRLWNkaqqkq6pwBzLxstWqHZJ71vutymKaPx3FbdSPHBVcTEVRcCccaqI25tXcyAnm0IVkuYKmdNC6afuFmnP2+aMuMIyYxk24gka4pmHBcF59PBZLvf7ocdEJ8YZSH1BCXAVJG0LLjhoxopl0m7RwIoKiFIlhJbaRVXBEUnBQdK0zshtg8kmXKRUtV1VBAzMUUtQ9lRBJSFPonMM2bgHnI81bNDYLxLtYyWpayBiuk0hqBNZVJBVMcuZcKSbaZ20lwhqSgkmKkp5vMPGHOCEOKY6acmzpO00SIymZ6RIblC0A9EiMcop3VR9kdr3hmrOQhttzURbdF0BUkadyIIGJiOAHl1ms42sz8Cwv2G5ybY89MdB44rhNKYo1iiFlVMyU5Isty2iubDRat12H5S+AnhjlIm0JELDThX/3X4Gb82iDbP9+/ujyF9R/ebckY+uzt5NLqIGfDNl66mNntncibQzWte9MMUcSKwqqIKIFiJPGQllzplAR4hZxpLlCe2iuEU8VbktuyG2C0rjq1zA0un+7puPc7hcW3mcDO13pHXQcbVexf4eQsNBtGHaHUPaGEGpV7FuXFVcysyG9DjebBMydcBdc2QFuXh7Z7aCbBsrTyxoLEV8waVtj6PWogrh9MSE5m7arlbb5cHJ95tcnWI9INTdKM+mIYkS5iyOC4PajkHcvdutO0M+DAZGLqYrD5g2GaK0ZZRRcExIiJaakMObUux3wFxl4G5hAYGmYSEkHAhJFxFUpqTdrjfrc2R5WnJ4PA2RppyprxyFvcWpVnvqNjtHbmxdV5tEAZLCqgq5kTQDgEoo7l4HDDJl4oswbHfZtuhlbWHVjxnjbDOTjqKWUVwzKgpWzk+4yXJk2RFzPyXiU3DLOSYkRaSXBKk7N7BvAy3GJWpl+FBcI3BXAgi45gQB4qv8Ij/scgiLjg3OIe0k2MYobUlHpLbRiulFaVSACH6ugi3WbOI2URXbTfAccztquj9dg8IrhwTacH82m7xbF1TwKjdwgGqK5HewxUSw4wFxmnOvHsTzgPNF61HlVq79Nrquc3tWv/ANUkcotAK7RaUFEX/STd/D6msf8AmL/hJviauk6Iesiy7U+/HcwVMzbkciAsCRFTEV59T7UraOPu2q4OQ0X/APkMRyeb+Em8tX3Zt08AnRwmxxXe1kcshonvkDqL/l0xYon0n7qjswwbTnyZK60sPfVHGg72ptnhphHt85qMGCYYq3kEl/KSKtSfPYv6a1tT5vE/Tcq4StpnWW7NqHAlg+qYOgQqitCK/rDcTgi2PCKtlwgISOfvaIbfRQAfEiVcOgCFmrZP6mb+kzTUG9X6Db5qTZJrGkPg24gko4LlVccF51Snnr/EuIo2SeQxV8ocexRU1aCKKPD4vDyh2ZVsw1CBRJu4NSjQcVQWoxa5zT0MgKlbOefO8jV2hbS3TyGVJnI8w3qJDuZvUgObFptwU4Q8+vaL/hJvialtbM3Ly9yCIFKTUvs5UdUkDS8DebHIXFqNenGiW3XKG23HfTHLrWFUXG1XnEiKB9/Vsse0lukwpFuYahjLhgL0c22QQBMgzA42uUeEAC7/ALtW1iPtGPl0AnCYCMQMTCBxEzgrUkNYQIoiXBDg1Is9plypcaTIWWSzCbIhMgBtUHVg2iDg2POq83BCyy5LSwYGC4Lr5KKAqn1Y53f8utowlsiUSLa3WY7x44NzpXBjGmH93kcPvah/vBVjxnnTtV3bLRkFw8mJfUviBl2oFuX/ALmH+DZqwRZW1FtZkx7bEafaKQ2hAYMAJCSY6CFUwWrpY4FzYvNyuKA3FYjYui2QuCeuNzDIGry6OFnIuty5ssy5tCqQrfAcGS51ud8xFsOmWUz/AMuo/qqPyr1MXeOWSS1alZjmm+Lsl5WAJPfAnM1Qo1xZGRbbc05cJcc0xBxGsotiSbyjrnG8wrxh4NIiJgibyVc5Jsit0sjDk+3ycOGOpHO83jvqDrQkmTs9WfWU1a86pEvkd2O631quMgr7Rd0mrMB+s5svWo8qtXfptdVzm9q06NzkcotCf/NT6ZkRcPIw56fW0uG1byLzlWGC/wD71TbWLivDAszsZHVTKpozFUMyppwzZcatSKmKaiZin/wx0LSmjMG3Xd+C6ZaBSI8ZM5i94WjRzvaj3KQmdp65P3d3HeRuORPtD3OYWm6v3rdf0xqT57F/TWpjWyMU5LsQAKYjb7UfATVUDHWG3m0iu9SeU2lB52sfmxiw/NdMv9lDtDfpDc7aNAIIzTGKx4qGmUlEiQScdIODnygIiRiIlx62T+pm/pM0m0Nsu0SNmedYGLJF1OE1hpUwQ8EXHsKOybVRno5wngG4MsEGtVpcCUmTJCbXO2uZouLTe0GxKuTiuIKD1zmEJyxRFxKOaCgAzkLjgADn4BETg6sq2c8+d5Gp9zfvLltKFK8mRoGBeQk1YnmxUww41e1b/wBzDx1XV9i7nc/3mDIKJsIzk1KmuOKGebNnp+ybYTLaUJxURyNMktMkJpoQhVTBxtxMeCYKJ0bmzt+kwjVVIGJrYSG9O8KG3qTEU6Ko4VMT7ojL1ucdRti5wnFIEdwUhEkJG3WzwFVTgZexOp1qvcgpd0sRtCMxxcXHYzyFq9YS6TcAmzEjXhEOTPw8xFA2SjOYxrO35TNROfKkDiIr9WxlVPripbXMhXKRd5b5ybg/HaYJvHiNgBG8BKItiO+HHI6uN/2cZkx4NzUZDzEsAAxkEn02CNm4OUzTWcbjGVWa6OOa2a015JcF67yiPwCUvfcFBd/zKv8A3MP8GzUXaC03CJPOVEamt27htPELraOIAESK2TnCw4RANBD21KfDteJMyHIKNpIZdzIKEYPCXABcdaKDrOxzFwKjwdlWAC2viMhJIlrSkK4KKjxu6dZnHDKvEy/q8oVH9VR+VeqOLWkmYcZ5U7VucJF8A4rUuI6qIc+2PNsY76m2606qJ3gGXe7m08x9cGwtkoUx55uMkAD3xkI1s7qkxRk5Dzi9AQjOf+OCc2XrUeVWrv02uq5ze1a9C6SOUWhH9yXRcoon/u/OT62vQd0/4fxlX2/W6K9EjpHnRtVIyZ8zbCqq8BSTDhVa/ejy/wAOVFcWwysXqIzJzJvK62isOJ08GwIu7q+7QuBwIMVuGyS72eSecsPfEGfl1fvW3+8NSfPYv6a1tT5vE/Tc3dk/qZv6TNNefyuqNLtDZ4+baSzgpKIJw5UUcSNrRpJxv9Yz37f9pTduuEjV7OXokYmI4S6tl5dDUjoDwvo3S/uizH+rGtnPPneRq5W26W+ZMfmS0ktnF1WRA1QhgWcwXNiPQr0HdP8Ah/GVC2agWqfGlTUdUHn9Tqx1LROrjkMi0iGG9Um+txzS0X5Afbkon0aSUHK80pJvGqhrsF7PtSqJbdsIMv8AeENoWfL4Yg8D4tplQ3BM2ybcVE4eXWCRcPgcSmdnrDBfjWsHxkypUvILrpNoqAAtgriACKWfNrMxcHgh120W296QokCWIkybiKOMWEBuOPJjhiBEaiK/4VNA8h63aO5q5IQVxJqObim5lXBf1LCFl7iv1t0+8t+Kqdf9mDmuTraQPSGpDoOiUbHK6qIIBgoZkcxx4gHU/ZKU7ljXhvymCJLoSUwnDQffcZxx+pGr/wBzD/Bs1s16qhfhwpdvrMwqw5ZIN9aBNDb64CEjBN4HuI5/i5S/tqPYC7vqSYE/YXHC3sqZnYyY+9i80n1vaVH9VR+Veqx2mcCOQ59tcjSAXng6RiX+xaaIs0W4215XrZPQV1MhpNCGGPBNtwCyOh1uYmjoF2htU2FchFNaMQW5DBkiaVAjNsxx7Ax4P94dJY7RGctuzYmLjoOqiyJJguIK7kVQBsF0i0JHw+GR8TJJ2xvsYo0+4tIxa4zo5XG4yqhG6QrpFXlEcnXasexd5svWo8qtXfptdVzm516uDMwp1xeORIUJBCOdxcSyiiaExr7PN+9F8VfZ5v3oviqVsvageG1TFeV4XXFNz/UAgHgeCYcFNFMX6ytShuEcHGwJ59XAwdHIWI4JzlqAu0LLplbtZ5MbDitFg9lzoSoi4pwBp+2bPtONx5L6yXiecV01NREOMuHBQQ0JUraKe1LK5S30kvEEhRDWIqLoHDe0UdjvYulANxt4kZPVnmbXEeFgtTZGzzb4OTwBuRr3VdTBtVUcMUTDjbsF7aFt8zt4uBH1DqtJg6oqWOCLjxBpLJYxdGCLpvIjx6ws7mGbhYJo0bkq4Ow5LTkt033GmZBA0JGuYkAETgjivF62rRs/ejmSoVk0Q3CfXXLgGRNY5hw8Br7PN+9F8VfZ5v3oviqLtBZmZQXGGjiMq7IIw+lbJosRVNPBMqett3hsz4D6YOxnwRwCw0ouC9cK6RLjCXFonY5XG3CS4ozHkCQJ7ya9t4/l0EpyE/d3W1RQG4uo62ip0WmxabPuXBMakbOztY1bJQA263FLUlqwJCQEVE4ILlQSROs4NJe7JHfSeLRsgb7yuiIuYZlFFROFgmXHsdyRClAjsWU2bL7a7xNuCokK9MVqFd7aM5mfAeCRHdSUS4G2SEmKYaRXDKQ9cNS7/eGpRXGYjaPE1IUA+ibFocBwXDggNQ7bFRUiwWG4zCEuYtW0CAOK89co1Kts9kX4Uxo2JLJJihNuCoki/kWo1wgJcI06I4D0eQ3LJDBwFQhJFy9FKG9X5qSc0GAjIrL6tjqwIiTgoi6cTKoVitiGkCA3qo6OFnPLiq8ItGOlaK2bQW9m4wiXFG3k0iW9mbNMDbPDr2yEqVxh+6QwVcdSzIbIEToIrrTh/LpubFtiz57KoTMq4n5QQEmlCFvAWUIV0ieqzj1pe4F61HlVq79Nrque6K27JabcTfAzEVTHe0KtC40YuNkmImKoqKnvKm4TbkpkDFcCAnBRUX30Va+2MeED46Q2yQwXeIVRUX8qbmrektNOImKgZiK4L7yrQuNkhgSYiYqioqdFFSicdNAbFMSMlRERPfVa1bMhp08McgGJLgnPwRaQX322iJMRQzEVVE6GK19sY8IHx19sY8IHx0SMPtvKOkkbISwx6OC0rbspkHB4wE4KKnTRVr7Yx4QPjpVYeB1E38hIXUXcVt6S024mlQMxFURfeVa15OCjGGbWqSZMvRzb2FfbGPCB8dIDcpkzXeEXBVV/Ii8wrE68QYjyLgrT8llskXuSJFrXwZLUpne1rBi4OPdCqp7oXrUeVWrv02uq57m9KkuI1GjgTrzpaBEARSIl94USr1tASEXl8lx8BXFVBjHK0K/VtIAVP2TlO5pNmc8ohCS6ViyFxJE95p7Nj9cG5tT56X6I02+1GhmDoCYYSgRVQkxTfROjTJPrNsEh5czD8d3GO/kVFVMzZEy9hwc7R5u3CvKZWRu/W8kYuzDegVJcVbeEecDwp3rguDT3mMXqFWynq1j9GtqvMT/SSi9Wyf0m62c8ye5VKYv1lZinb5BuA2rr4tni0SgWIqnZJX2aF96D4qvr20TTDbc9qOEdWXRdxVsnFLHDe4yVtN9cz+GaqPMYjwyYktA80qyRRcrgoSYoqdBaZvNyjFFiq4jY3CE+ho24ukUIm1Q28cOCSpl7bNVw2bv8pydcrWIyIk14s7rkYlyELhrwjJpzLwyzEQudpVy83icgNN/9NQ+SapbLYhaOcLJyFR40bHI2qIvCXHTiSUb4W1iVq0UlbjymlcVE08ESUMy+8nCpuDeH5kiytOeT3OyzVcU2BQsCVoHeEy81v6vgifEPshYnxHhehSWhfYfFeAbRihCaL0FFcak2LZae7D2bjGUcHIZkDk4uKRkY4HqSXEW2h4JjwzzdYE55mLaBdHM2xcXTbfVF0pmbbbdJte1dyH2tMy3XH7UTy5Y90gPKrD2XTkUwwx3v1Lw8Iesy05GuWRvaa1iKTwFEEX2y0BIAU3seK6I8EHOxBwB9zL1qPKrV36bXVc9zctTB5Z+0RrDbw30jjgUguko5WV+urbG6ShFG58F6xW9w0VUR14Eccc/y1SPlJO3qC7cUVhlH3LXdgLRkB0tUal9U6gOF3G5tT56X6I1B83a/QSr2TwIT1tEJ0RxU0g4yaZlTumicDvqkW9C+guVvdEw52dkgcAvyChp31PeYxeoVWSwzYF0cl22I3HfNlphW1MEwVQUnxJR6YjV6sEGBdGplxjEwwbzTCNoSqi8JRfIkTRzhKi9Wyf0m62c8ye5VKh7O3C2TpUuM6+4bsdGdWqOuqY4ZzEuu08GvQd0/4fxlP3u2RH4cdiUcQm5OTOpAAOKSZCJMuDqVtN9cz+Gaq3wnm7kr0WMyy5ljtqOZtsRLBVdTnpT2zOz0OXnnOtFLkzG22xBtk0dRAQTcIjIwHseDV52tebVuATH7tiGWKa0ycB11R6It6sBx7I+1Krl5tE5Aab/6ah8k1R+rJP6bW5b7rHBAO7QUWVgmGZ2Oat519/Vq2PeVcJqOKkm3xpVtbdTjIjr2qbVO4B8UHuageWAjrFqZduOqJMUVxnKLSrj2DrgOd5ubQWyQAmSw3X4xKmOR9gVdaJOhwxTvasiASo1cFdhSBTrgdbJRT8jotl3vuZetR5Vau/Ta6rnub9vYLGHs+0kAcF0K/jnfLpoZapfqqhbOW3Z6I4xEQ1N9x13O644amZlgnPx3quG0KQW7cdxcR5+K0SmCOqKI4aKWn6Q0Vwu2KrZNecz3GCPkFx6KvR0RENffdaVtxe2OtqfPS/RGoPm7X6CVtGbxIKyWAisiu+RvuCGCfkUi72iliK6qBb5Drhc5FcUGhT8uenvMYvUKrFfJ7lxSbcYbUiQjT4CGc0xXKitFgn5avl9tzlwKdb4xPR0efAgzIqcYUbHH4aL1bJ/SbrZzzJ7lUqDfr0zKK4PuyAcJp8mxVG3SAeCiL1o1+onfei+KnbRYBdCG9IKUaPuK6WsMBBcFVE0ZWxrab65n8M1TNxsN3mBepENqSwzMVo45um0hq2qgDZgJEuUTxPJ29K3tjs6l2jxHVjz7Y+bjLrRgeBkKAQiTgYL9G9maPi8HjjbpeziMjY32AO3hHAW2haVNAi2KIgZeKQYcAuDVy82icgNN/wDTUPkmqP1ZJ/Ta3LNbmyQnYVvVx5E61X3SwFffytoXfVd2UAtbMblXFsMNKtx5Anve+MbNUNqSaNhdYz8ADLQmsPK62nfm0gD2xbm0N0kmgC1BeBrFcMzzoK00HfuGI1s8LYqoRXHJbxdiDLRFivTPKPfe5l61HlVq79Nrque5XbaF9RRYMcijgW8b5cBkO/dIUqDHuQLMiI6dyvJOYkhttrnJHOjrnSBsvrKVf+U7Zp6EZtP/AAqbc9mbFEgXC0uBMccitC2ZxxxB4VUU0iIlrdP93U7ZWU7ljXtvWw0JURElR0VcqY/3jKn4MK2p89L9Eaajt2S2KLIC2Kl5Qq4CiJpwcToVEtshlXxbNTh2W1suKCuYYZ9WiuuOGg6MxEWQc2TJmOjfuraBtFd1F2eHBJWWwx1TGZMUXLipuYf2h5esp7zGL1CrZT1ax+jW1XmJ9VKL1bJ/SbrZzzJ7lUqPs5b7XBlRoxuuC9I12sVXTU1xyGI6FXoV6Dtf/EeMq42y6W+HDYhw0ktnFR3Op60QwXOZplwLoVtN9cz+GaqzeYxuRGh29s0b/UsZWr820PHawwbkqic9vDVul/d6suK0VHsNdn8sG5OK7Z3DXQEstBM4rvC+icBP77tnquXm0TkBpv8A6ah8k1RX62xWJcgo7kbVSM+TK4oqq8BRXHgUbca1WuM6SKgvZHzUceeiK7lxTts1LNlrIfZlvZ7xtA8C6psRwzIJYI2riBgDMcO14INDwY1liMCFtiMDFajqiKOqAcmUkXjYjxuyqRdLVGfPZgnfKLfcmMxeS4kio08Q8Jk2j0NuF+s4GU8+cQbh3m2Rr080KCE1TKO8SJz3cqGBl74g3UW2OMqMVHP9FY7cDho46uhCIUU3H3cNA9j/AGYDmPM9fL6yje0l1BA1C4KUWNjmRpVTH6R0kE3exyth1pe5l61HlVq79Nrque5eRXiDHuMPMjnk0poHm848UshoQ4pzqcfstlg2x94UB12HGaYIgRcUElbEVUceduOR5DYvMPCTbrRohAYEmBCQroUSRcFSmZcLZq1xZcckcjyGYbDbjZjvEBiCEKp71PTZ+zdrlzJBZ35L8Nhxwy3sxGQKRL069k7P9wjfMogtFti24DwzjEYbYRcN7FGxHHcWbd7Db7hMUUBZMqKy84ojxRzmJFgmNMwoMduLDjijbEZkBbbAE3hABRBEU6CU9Cnx2pcOQOR+M+AuNmK9aQEiiSdOvLbRYbfbpmRW/KYsVllzIWCqOcBEsq4Jopp692aDc3WRUGXJkdp8gFVxVBVwSyoq17J2f7hG+ZXsnZ/uEb5lOSLLZYNskOhq3XYcZpgyDHHKRNiKqOOnCnp1y2ctk2bIVFfkyIbDrpqiIKZjMFIuCiDpoGWQFtpsUBtsURBERTBERE3kRKcjvti6w8KtutGiEBgSYEJCuhRJNCpQONbLWltxskNtwIUcSEhXESEkBFFUVNCpRzrts/brhNcRBckyojLzhCKYCimYkSoib1fuZyBHO0apGP3cTQLH1QoiC3qlTJkRE4uXLXsnZ/uEb5lIbWytoA03iSDGRU+RQMsti00CZQbBEERROciJoTcUSRCEkwIV0oqLvoqUr8nZa3K6S4kTbAtYr0VRvIi0SWGzQ7Yppg45GZBsyToEaJnLvi90L1qPKrV36bXVc3AhlDWQptI7nRxAwxIhwwyl2NejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZXowvDJ8yvRheGT5lejC8MnzK9GF4ZPmV6MLwyfMr0YXhk+ZTc9GtQjikmrUs2GUlHfwTobhetR5Vau/Ta6rm4x5qHKH/V8bu3eUXcL1qPKrV36bXVc3GPNQ5Q/wCr43du8ou4XrUeVWrv02uq5uMeahyh/wBXxu7d5RdwvWo8qtXfptdVzcY81DlD/q+N3bvKLuF61HlVq79NrqubjHmocof9CSNBYOQ+u+AJvJ0SJeCCe+VC/e3UfLfSG0qo2ndnoI/yZR7qguERtAgy8AJsEwFt0U3kRNCCYp+dm9zBlhsnXnFwBoEUiJcMdCJpXR/QI3du8ou4XrUeVWrv02uq5uMeahyh/wBAFpoCcdNcAbBFIiXoIKaVoX70ax2l0pEaVFdXuzTFA6Q5i7YaSNAYBhpNKoKaVXoku+S++W5IgOrlR4eAfPE00iSdIkp2NIHI+watuj0CFcF//T3FERFVVVERE0qqroRETo0k6aCfvR8d5dOpbXrE7Zf7Qu9p242tEauC8N1nebeXn9w4vZcUuv7KjbcAm3W1UXGzTKQkm+hIu8vu0bu3eUXcL1qPKrV36bXVc3GPNQ5Q/d0dmotuidFwfpiTtQXi90f5lI3BYQT698uE6fdGun8nF5lq9MBoLBmaqf8Almv6H5nuGK6ETfWhvVxawcVMYLBppFF/tSReuXrOxHdV5rLHuYJ9HIw0EidY5hvj7/GD5NHEmskxIDfAuenOIVTQQr2Se6xu7d5RdwvWo8qtXfptdVzcY81DlD93QHyUpsLBqQS75phwD75N/ts3NPRJA52HwVtwfeJMKft764mwWCH2YLpA++Hm27rOHC3tFmjtEn64xXQS/wCGK/nl2vM6mUmR4MVjyR47ZL0OiK9cC8alizQ39LL4ourdFOeK9FOuHjD7pG7t3lF3C9ajyq1d+m11XNxjzUOUP3LFVwTo0LzwrBgrp1zg/SEnaNrgvfH8qn4lvbXy79Y1KcXM4RimgVLRgBcXKPBpRJFEhVUIV30VNCovS3GpSqvkx/RSx6LarxumC8KkMFQhJEUSTSiou8qc0N4jj/qIaZZCJ1zGO/8A5a8Luc3NKb2IWxhcJDiaFMt/VCv6a9aNAy0CA02KA2ApgiCKYIic0cOc0jrJ6egQkm8QrviSdGn4DckZQtYYODvpjpyHhozj12Hucbu3eUXcL1qPKrV36bXVc3GPNQ5Q/cUKIzkjLvy3cRa73rj7yheMPLJyb8h1EVBX/DDih+l227+8mR/0s9cXFTeF9E0+ERM3dZt1bU8X+pgp9FiukmFXg/mLwPzeaIDRCAkVCFdKKi76KlPw1RdQq6yKfZNEuj8ziLzCRWVUGQwKVIw0Nh88usSmocRtGmGUwEU/2qq88l5682sKGaFdHx0YadSC/wBoXbf3Y0qqqkSqqkSriqqulVVV319zjd27yi7hetR5Vau/Ta6rm4x5qHKHzepgRydVFRDcXgthjzzNdCdLjUMi6Ek+QmkWsMGBXuV0ud/we0pBFEQUTBETQiInMSID2hHR4B88TTSBJ3JU7HfHI+yStuh0CFcF3I9wY0mwWJB2YLoMO+GmpLBIbLwIbZJzxJMU5on2RzTYOLrOG+Q4fSB+UdKdsNYppRd7cagxBxeeXjLjlAU4xlh1o0EOMmK8Z55eM4a75F/4J1vNoaojs17FIsfoqm+RdAB66nZUk1dkPEpuuLzyXqJ0E90jd27yi7hetR5Vau/Ta6rm4x5qHKHzYR3C/wBFPJGnUXeFxdDZ/DwC5tu9sDghqLMxE6O82f8AuF3m6djkFoRCdhKvQ33G/wAnHHvubUmRwgzMXY/QEsfpG/yKuYe1Km2GAV190kBpsd8iXeRKw0OT30RZT/v9gPQAflcbm3J0nFRHgttpxjNeKA9OnJ00szp6BAeIAJvACdBPle6xu7d5RdwvWo8qtXfptdVzcY81DlD5vChB480+Jg1Jx3yTrHO/T5Wbmnockc7D4KDg+8vPT3051PwJP61gsELnGK6RNO6HcZlxiyyGDRxtffTnL7xcUqYnx14Dw4kPPEk0EK++K6OadjiieVN/SxS6DgpvdI04K15fObRLo+nFXBdS2vWJh16/2i97zbsuU4jUdkczhr0PjXnUsh3FuO3iMWNjoAV56/4hdcve+7Ru7d5RdwvWo8qtXfptdVzcY81DlD9walnj5M4mplIn92S8bvF4X51IQqhCSYiSaUVF5oLwwmLsNMsgU31ZVcc3+WWnuc26dqfLBicuZhVXQLyJvf5gp+cPupGZIAAikREuCIiaVVVWtTHJRtccvoR3taSaNaScmnu8bu3eUXcL1qPKrV36bXVc3GPNQ5Q/cTtr55pMHBGsd8mF0D+YvA/N5om3BQmzRRMV0oqKmCotPwURdQn0kUl57RcXTz8q8DvdwTAlAwVCA030JFxRU6S0xLLBJCYtyRTnOBoX87jJ3Xuh2iA5jBbXLLdH+1NF4iL/AHY9d2Rf0CN3bvKLuF61HlVq79NrqubjHmocofuMe4M4qTJcME69tdBh+VN7tqalMFnZfBHGyTniSYpzSyGAzToWLjSJvmHXh+VOEPbDWKby724jb55YM3Bp/HeE/wCzP4eCXal7mtrtESS446n+qlMtmoiC9YJInHLrsOKNYJa5SIn+CfxV6MleBP4q9GSvAn8VejJXgT+KvRkrwJ/FXoyV4E/ir0ZK8CfxV6MleBP4q9GSvAn8VEzIbJl4NBtGiiSY6dKLzcbu3eUXcL1qPKrV36bXVc3GPNQ5Q/cjscgtI5nYRL2O+bfe8ce+5stUOEGZmdjYbwrjw2+9VcU7UtzBd5aRt4sZ0PBqR0STDgOd8nys39EuPdByQ83G7t3lF3C9ajyq1d+m11XNxjzUOUP3JmZHXK/HNHG152I85feLirUefHX6N8ULLzxLeIV98S0c09HBE8qb+likvOcHnd+nBpUVFFUXBRXfRU0Ki9LcZlkqpGL6KWic9ouf3i8OkIVQhJMRJNKKi89P6Hce6Dkh5uN3bvKLuF61HlVq79NrqubjHmocofuZ2p48I8zhsYroF5E0on1g/KHmxuTI4Rp6rrcN4X0TT4ROF3WbdO1PljIgoisqulSYVcE8GvB7nJ/Q7j3QckPNxu7d5RdwvWo8qtXfptdVzcY81DlD9zFxslBwFQgNN8SFcUVOktNS9Avj9HKbTrXR3/yFxh5p+A9o1o/Ruc8HE0gSdIqdiyByPsGrbo9AhXD4OhuMXBjSTJcMOzBdBh+VPlUzLjlnYfBHGy94kx/oVx7oOSHm43du8ou4XrUeVWrv02uq5uMeahyh+6JHeLCDOVG3cd4XN5s/9wubbvjA8FzKzNROcu82f+4XebrljfLezPQlXoY4uB+ReGnff0K490HJDzcbu3eUXcL1qPKrV36bXVc3GPNQ5Q/dFRd5aAHTzTYaIzJx31wTgH34p+dm5p6JIHOw+Cg4K9Akwp+BIT6VgsuPZDviae8Q6dxqVHLI+waONF2w6fgXeWmnXZ7bLpghOMlihASppFdHOWvSbPwr8Vek2fhX4q9Js/CvxV6TZ+Ffir0mz8K/FXpNn4V+KvSbPwr8Vek2fhX4q9Js/CvxV6TZ+Ffir0mz8K/FXpNn4V+KvSbPwr8Vek2fhX4q9Js/CvxV6TZ+FfiqbKiuI9HdIFbcHeXBsUXD8qc3G7t3lF3C9ajyq1d+m11XNxjzUOUP3VqWqr5Mf0Usei2S8bpgvCpCFcRXSipvKnNDeGU+nhplkJ2TKrv/AOWS49zm/pcbu3eUXcL1qPKrV36bXVc3GPNQ5Q/dW2nBxhx8HpS85RReCHfl8nNWCb3NBZI5cN9EcmKnObReCHfkmPcj227gpIi9DGuMnw1xk+GuMnw1xk+GuMnw1xk+GuMnw1xk+GuMnw1xk+GuMnw1xk+GuMnw1xk+GuMnw1xk+GsU0p0ebjd27yi7hetR5Vau/Ta6rm4x5qHKH7poTFecib6rTTTg5Zj/ANNLXn5yTi94nB5p+dJLKywKkXRXoInvkuhKfmyVzPyDVw/ex3hT3hTgpuMwoo5n5BIAe9z1JfeFOEtMxhiMmjIICGbYqS4Jvqqoula+wx/BB8VfYY/gg+KvsMfwQfFX2GP4IPir7DH8EHxV9hj+CD4q+wx/BB8VfYY/gg+KvsMfwQfFX2GP4IPir7DH8EHxV9hj+CD4q+wx/BB8VfYY/gg+KvsMfwQfFX2GP4IPiq4NtALbYkGUBRBRPoxXQic3G7t3lF3C9ajyq1d+m11XNxjzUOUP3RZz6YxLeqEiL17y6QTpBx/zebCzMr9DFVHJKp1zqpiI94K5u67ndO9vJ9I/i1FRU3m0XhGndkn5o/0K490HJDzcbu3eUXcL1qPKrV36bXVc3GPNQ5Q/c22GAVx54kbaBN9SJcESmYLekhTM+52bpccvh3u15p+cWBOImSO2vXOloFP/ABXtaceeNXHnSU3XF3yIlxVdxiAGKAa5nzTrGh46/wC6PbU3HYBG2WhQGwTeQRTBE/oVx7oOSHm43du8ou4XrUeVWrv02uq5uMeahyh+5uXp4foWczUTHrnF0GfepwPzubSKwWaJAzNoSLoJ1dBl3uGRO+3MV3k36WfIHLLnohIK74MpxB6ZY51/odx7oOSHm43du8ou4XrUeVWrv02uq5uMeahyh+5R4LH62QaAhYY5U3yJfeEcSpiFGHKzHBABOfo56++q6V5oyZLLNk/QxeiiqnCPvB4XdV8e40y4OaHHwel9BRReCHfl8nNWCb39DuPdByQ83G7t3lF3C9ajyq1d+m11XNxjzUOUP3I71ID6WSihEx61pF0l/mEn5nNKqrgib604+BYw2MWog87Ii6T/AMwtPc5dzH/YlADg4TZGDssu2VNAdIE4P9EuPdByQ83G7t3lF3C9ajyq1d+m11XNxjzUOUP3FmA3ijZLnkOJ1jQrwl6a8Ue2oGWhQGmhQGwTeQRTBE5r93sHhMnooqqb4M7xl33EGsE3txJrw4woCoa47xvb4D3vHLvfc/3lbhX94spg60KqmubTnYf3gdb2XE7GuOf5xfHXHL85fjrjl+cvx1xy/OX4645fnL8dccvzl+OuOX5y/HXHL85fjrjl+cvx1pVVXorp5uN3bvKLuF61HlVq79NrqubjHmocofuGK7yb9eWPhhLn4OKippFpE+jH/fXuuacfeJAZaFTcNd5BFMVWpFwNFEXVRGQXrWh0An+8vbFuAyyCuPOkgNAm+REuCJ8NMQRVCMEUn3E65wtJL/4J2vujt7t4cBeFPYFN5ee8Kconf9l/QI3du8ou4XrUeVWrv02uq5uMeahyh+4NtOjmhxk10lOcqIvBBe7L5IlWCb3NNWVgsFfTWzMN/VovABe7LSvc7rt4fDFuMuqiYpoVxU4Z94nB773VUVMUXfSlnwg/9LfLhAifqDXnfVl1vY8Tsfd43du8ou4XrUeVWrv02uq5uMeahyh82iIikSrggppVVXQiJTbTiJ5Y/wDSyyTs1TQOPQBODzT86SuDTAqSpz1XeEU98l4KU/Nkri/INTPoJjvCnvCnBTcYgxkxfkFlFecib5EvvCPCpiDHTBmOCAPRXoqvvkvCXmjJtcJknFmKnQJU4R94PCoLRcHVWc2mEZ410vAibyr/AHgp+ePC7Lm3GHwRxl0VBwC3lEkwVFrBMXLc8q+SPrpVOfqz7cflj33u0bu3eUXcL1qPKrV36bXVc3GPNQ5Q+b8ueT/S29UNE7J5dIJ0h4/5vNhZmCxZjKjkok57uGIh3iLmXtu53TvcgfpHkVuGi85vHhH36pgna91zSqq4ImlVWjdbX/Rx8WYic5RReEffr8nLQuNkoOAqEBiuBCSLiiovRSlYkYBc44prgTecHe1ge8vXJ1pc27BmBmZdTfTQQknFIV5xCu9RwpPCTjMPomAuN9kic5ecQ9b7rG7t3lF3C9ajyq1d+m11XNxjzUOUPmxkwnzjvj14Lvp0CReCSe8SUMe+AjRbyTW0XIvdhpUO6Hg9zQvMOC60aYg4CoQqnvKnMPzj0mKZWA7J0tAD8PyaN101cdcJTcNd8iJcVVemu5Ht7eKC4uZ4061odJl8HBTtqBlkUBpoUBsE3kEUwRE5ryFksJc9FDQukWk45fl4id1WCb241MiOK1JZLM2fVRU54kmgkpJDeASG8BlR8cVA/mlvgXNrGfTI8GJRpCJwmzw306Ir1w9dT0KWGrkMFlMecvPQhXniSaR90jd27yi7hetR5Vau/Ta6rm4x5qHKH7jrbe+rSKuLjK8Jo+6BdHfJwqBi4p5BLLAcxaWCX3j63HoOfnUiouKLpRU3FitFjDt6q2OG8Tu84X5OIPfbvl7wYS56IelNIsp+rH8vHXuuaN54kBpoVNw13kEUxVVqRPcxQXFysAvWtDoAfg4S9tzAToq4kPBdaVcBcbVdIL/ur1pU3OhnmaPQoroICTjASc4h5tDZwC5R0VY7i6EJN9WzXsS53YlRtOgrbrZKDjZJgQkmhUVPc43du8ou4XrUeVWrv02uq5uMeahyh+5oDDmvhpvxHlVQTuF4zf5OD2tPHDAmLsf0QMHpyKW+4JJoIQ/S62uj767+4DTif6OPg7LXnKKLwQ79fk5qRETBE0Iic0Fkjlw30RyYqc5vHgh36pp7Xuua1iIrsJ5USVHTnonXh24/K4tNSYxo4w8KG2abyiulOaWVMPDHQyyOk3C7EU/9stOT3mgZNxEFG295BHQmYuvLtvc43du8ou4XrUeVWrv02uq5uMeahyh+7gLo4TZOD0pegSpwQ7weDzT86QuDMcFMuivQRPfJeClPzpS4vvlmJOcKbwinvCPB5sYcs1W1PlguP9iZLx07RV/WJ3/ZUhCuIrpRU3lTmEQvppzqKrEVFwVe2NetBOj+bRTJzquvFoHnCA9gA9aP/sXukbu3eUXcL1qPKrV36bXVc3GPNQ5Q/dxaEvK4Sf8AurxLwU/wz0qHS4QULbDuplqmKxHuC57+XrT7xeZas7BYhGVHZaouhXFTgB3iLm/N9xCy3Bz6AlywXiXiEv8AZEvYr/Z/mdjunCgKL903i54M488+ifYt/nU5IkOE8+6uZx01xIl9/wB1jd27yi7hetR5Vau/Ta6rm4x5qHKH/QEXeVFxRU0Kipz0WhZuCLcIqaM6rg+Kd0uhzv8AhdvSuwH0cUcNY0vBcBV5xAulNyROJEJwEysNquGZwtAp8O/2tOPPGrjzpKbprvkRLiq+44LvLQ2m4OYzmh/07xb7wCm8v+ICb/ZDwuyp222UkVxMQfnJpQV54tdkXb8UaVVxVVXFVXSqqu+qqvu0bu3eUXcL1qPKrV36bXVc3GPNQ5Q/6EL8Z02Xw4jraqJJ+VKGPewV9veSY0iZ07ttMELug/MoGIjme3RU+jJN5xwk4R96nAHvvc0UVUSTeVFwVOkqVgmhPd43du8ou4XrUeVWrv02uq5uMeahyh/1fG7t3lF3C9ajyq1d+m11XNxjzUOUP+r43du8ou4XrUeVWrv02uq5uMeahyh/1fG7t3lF3C9ajyq1d+m11XNxjzUOUP8Aq+N3bvKLuF61HlVq79NrqubgS5D7rRg2jSC3lwwRVXHSi9lX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tfa5HyPm19rkfI+bX2uR8j5tNwGDJxttSVCPDNwlUucidHcL1qPKrV36bXVc/rMvWo8qtXfptdVz3O0WPZ6a5Au001mSZLOCGMZvEBHFf71xV8DUO07VXh+42+8CsNlH1RUakkqEySYInHJNT/mbmzI7O3V+2JLGaslGFRM6tqxkzYovFzlQzrVLv1whERAMmLHceaUh0EiGDZDiPPry+5Sr3BjASCsibDUWUIlwRFV9rV6ac2Y2oRr99o2r1vmshqxkg2mLgOAnBF4U4aZBEDDNwRIPpNmR2dur9sSWM1ZKMKiZ1bVjJmxReLnKhnWqXfrhCIiAZMWO480pDoJEMGyHEefQTLpNvEBlSQRdnw8rSlv5fp2si9KpNqvLbbO0tuBHXCZTK1IjqSDrRHFchgSiLo8XhCYcbI3ZI+z14kW1iRDccebYJEQjR3BCXFF04Vstedn5VynbTSrg4M2TCbJ+QTAuSh4aNiS5EUGRxy9jT0ya7tDGiRxVx+Q9FdbbAE3yMyaQRH31pYdnvV2uUtAVxY8QFfcQBwzFlbAiypimmrCzf0v6WY5jaTvKYrwM6rTm1hK2IoPTWrra7LfpUG3stxVajNEiAKnHAywRUXfIlWgeaXaNxl0UNtwYbxCQEmIkKo1gqKi4pTJXedcIquaQj3WIKC6I76IjzQkqe+BU5NeYCJeIDiMXOK2qq3mIcwOt5sSRt3AsokpEJAY5i45Vcbfste34FqtWEHJHUUFx9pV15roXFdYpN9y3Vzt1+nHOvdskI4jzuGcor6cDTozZHBcTtRIN1q42Kc7bpq3FhpX2VRCUCbdVR0ouhVEa2id2hub9ycivxhjk+qLkQwczIOCJv5Uq/wBqtG0EqHb4xsIxGbIUAEKM0a4You+REtC43/zIbZihAYw3lRRJMUVFRrSipXF2l+5P+KqxvbS+Ufvw2TWb5YBNyM2tNB1gkgki5Mu+nuRetR5Vau/Ta6rnubrFuLO1Klt2i0rvijDZ6sXN/ikSm+vd0gWUSjQUGNcLMelVHJgi6V3yB9o/k1atooyIIXGOLrjaaUB1OC63/luiYd7WyHcT+rHqLAvN/g2+aMqSRRpD4A4gkeKKoquOC86rzHW8xLu5KiPR2rdGLXk6boKIiuVFERxXhGXF7qrM9FEtVbhflTHURcAaRk29Pdm4Dff1sh3E/qx6i22+X2NAnjKkmUZ0lQ0EjxFcERd+r1aYVzavU65xjjRYjAGSI4aYC6ZKIgCMlg5xs2YeBVx2rNsm7TFinCadVFQXX3TAlEV67VgGJ923Wz3mDnLLWznSlfjHq2r9Wv8A6NP+qpHKs7l5+qh/hW6tEeRtTbW32YMYHW1kt5hIWRRRVMd9F36j2OzXBi73QpjcgDj4mLANiSEauYZcxZtXlEuurae7kKjAeKNFaLnG60jjh4fVi4HhKvW0BEguQoxrFzYYLIPgMDgvZOkFXJm6oTkOPAkPPvriv+pfTVMkS445hMyfTtmqjs3JfJ2lkHZ7yCqqIIm5q1JfqnhBzuQ3WfWkfknq2q84ifoO1tL9ZG/CM1BjvbQZXmY7Tbg+STFwIW0QkxRnnLWP/MP/AAk3xNMymCzsPgLrR4KmIGmYVwXTvL7kXrUeVWrv02uq57ldZrBq3PmilvgEm+jslFFSRei20jjg9sFJtHtJHlShiMODb2ojbbhJIdwDOWsNpEQWlc74qtq2mHPjXq2vFkdlNMi2cd0fpAUm3XCzIYtkHB7OrtsXKcxVn/1G2iq9aSoEgE6Ras0Tt3K2Q7if1Y9BtJBvbERx115kIb7JqmLS5UVXRJcMy/4XB7alsu2UOSyEN5AuLEUwB9Wl052HHBNssw8NslHIdM3HYJpChXERKTNcJTlOGGjJIJdIm2qr9EOVseMA8PMWyHcT+rHpnaNNof3drXnWfJfJNdhqiy459c3xu4p+TZ9oGbnLZBTbhOxyjK5lTHIJo48mct4MyCObjENW3Ym8PLIsM0khwWzEUOI+qrq0BURFUHD+jMD64s49fn2e8wc5Za2c6Ur8Y9W1fq1/9Gn/AFVI5VncvP1UP8K3TV+s90Yub7kRuYls1RtOkhto4rbZZnBNxMcBRcmemYu3yTGbUZI3rYxi2jbuZE/1KKJOanfz6ogcCo1u2eisxLS2KFGbj6QVD0582Kq4p8bWEREfZVaNjIrnG/8AUbkIrzkxbjgWH+aaiv8AhlUyNcoVxkXm4yNbKejNMk2jTY5WW0I3myXLi4fF/tKl7Q7NsSY0W4A25LZlgDZpJRMjhCjZujlNBA8c3HI6tF3kyEOVGZ8lubpqiKj0VMhka7yZwQXu/oYMC8QZc0hJwYrElpx1QHDMSABKWUcUxXCmfWkfknq2p84ifoO1tL9ZG/CM1ElrtDNApDLbpCjLSoimCEqJp9+lw2km4876Fr46iwhJTGKy2yJroVUbFBxXDo4e5F61HlVq79Nrque5QNk4rmMezN6+aKbyypCIoov1bOXwxVaLrtOzKW73FrypwWniaEGnVzMjlw39VkIu2KnBbamtuEJIDiySLKSpghYYacq6cKjPzkVs7PNOHdW065hSVl/BOu4Cq433lbGutEhtONTiAxXFFEljKiovv1E88lcpX7/tbGfaGyApIIcd+GmJONYJxjb/AFrX+YA8JyisV0dyWG/GDauFxWJfFadVV3gPHVu/5Z8VutkO4n9WPTOzr1idnuNPPPLICQLSKjpZkTKrZ73Tp9my7N+ST3AUWZciSjoNKqYZ9ULQZ1TnJnGrfdkaJbVZJAT7hNJFy6xtdY02irxnHHEHg9hnOtnvMHOWWtnOlK/GPVtX6tf/AEaf9VSOVZ3Lz9VD/Ct1Y/V8XkRr/nq0NZbdcnEC7sgmhuWeKo9gm8D+HD/xvrqd2KvEnLNtQG/a3XVREKEOk2sy8+OuJJ/gl2LNPFGMyG/XMI0MlTFQi50aaVU52rYFCKv1E770XxVc7xsq1JS6W0UlEDrxOibDa4vJlw3xbxc7yr9sBLe1cbaeG8kJS4oyhaIS8IyRKv1I15VPgKcy1m7EuUA1yKbZplLIeC9q60eGU+D1hVb7Labe/CgRn/K5Lkkgzm6IE2AiLakiCKGa4qXC7EctO3C4tKxIv0hJbLRJgSRhBAZIkX+84bg/4ZBW0v1kb8IzUWIuy75rGZbaU/KwTFQBBxw1S9CvZV/74HiqY2jahFbwfddaSMTiOqmqNQxzIIcbDsfci9ajyq1d+m11XPcpV0uVgalT5rpPypBvSMxuEuKrgjiIncjwaBpoUBtsUEAHQiCKYIiJ725IvF4sDMq5S8qyJCm8CmoCgIqoBiOOVE05atcC72gJkSys+T2xtx176FpREcqEhoRcFsOOpcWhtNhhjBtwGbgxxIzRDcXElxcIi0r7+4/If2aYV6SZOOkLj4IpGqqSogOCIaV6zLlq3x79aguDVqbVmAjrj2LYEgoqZhMSPFGw0mpV7MMeFkeNpCHZeKqp2RPGnwEa03b7TCYgQWsdXGjNi02OOlVQQRExXn1Hl7R2lu4yIratMGZuhlAlzKmDZgi6ejUezWWKMO2Rc2ojCpEg5zUy0mpFpMiLSVSrVc2Uk2+a2TMlhVIUMCTBRxFRJO9Wlumz9mbgTyaJhXwceJdWaopDgZkOlRHnbj93vljbm3KQIA9JJ18FJGxQB0A4IpgKYaEpmJHBG48cBaZbTFUEARBFNPQRKk2q6xgl2+YCtSY7nFMV6WCp0UJOENC/F2ebYeBCQXW35QkiGKgSYo7jgQkQlTF4s1hZiXKLm8nkIbxqGcVAlRDMhxykqY5dxxh4EcZdFQdbJMUISTAkVOgqVFudt2fajT4TovxZAPSMwOAuIrpcVF6RcGgLaO0NTJDaZW5YqTMgRTSg65pQcUEx4hFk7WgmxbA2/JbVCbOY47JEVTeVG3SJvFOjk3JF4vFhamXKWorIkE4+KkoCgDoFwR0CIpoSvZhjwsjxtezDHhZHjaC0WGIMG3NmbgRxIzRCcLMS4mRFpX3/AHIvWo8qtXfptdVzmztd7vsaBcGxEzjuqSEgmmIroRU0pXtTC/OL5tDHs+0MCbKPQEZqQ2rxaMdDSqji/m7h2u932NAuDYiZx3VJCQTTEV0IqaUr2phfnF82vamF+cXzabullmNzre6pC3JaxUVUCUSRMUTeJN0o172giRpQLg5FElfeBegbTKOOB3w0jEXaaK26WhElI7EHHupANB8qkMFQhJEUSRcUVF3lRdw4t52hiR5baqLsUCV94FTnG0yjjgL3Q0LEfaaO24S4IsoHooflcfBttPylTcmK8D8d4UNp5okMDFd4hIcUJOlSXG/Tm7fBJwWUfexQVcNFUR0Iu+glUgdnbvHuRxMqyAZLEgQ8cqqioi4Lhv7g2Nm/xTuxyFhjDRSzq+hKGr4vGzJl3CjXPaSIMkFUXGGFKUYEmhRMY4uqBdqdIzE2nig4W8krWREx6GaQLQ/7aEwJCAkRRJFxRUXSioqU5a73fY0G4NCJuRnVLMgmmYV0Iu+lR5sRxHokpsHo7w8U23BQgJPeIVxornfJrcCAJi2Uh3HKhGuApoRd+pKbO3Vi5rDyeUowqrk1mbJjiicbIVPWm8X+LCuMfLr4zqkhjnFDHHBF3xISqSuzt1YuaQ1BJOoVVyazFQxxRONlL82pE+c8MeHEbN6S+4uAA22ikREvQEUrH/mmF+cfzajXG3vDJgy2xejPhxTbNMRJMeilLOvE+PboYrlWRKdBkMy7w5jVEzLzhrUltK2RY4KQR5Rh+eLSj/tpS2fvMS4kg5jZZdFXhHHDE2lwdBO6D3AvWo8qtXfptdVzm7h5rE5FKtd4DapGFuUNiZqFg5kDXtC5kzeUJmy5sM2Uaj3c5Tc61k8IM3KJnbcZeThBrAXS0q4cAwMx4PGEstP228uq7f7JkB6Qu/IjnijTpdFxFEgd7w/7Sp3mkTkkq1XhNqtR+8obEzUeQ5smvaFzJm8oHNlzYZso17Xp/D//AOzUTZpZ37xWKbx+VI1qc2udJzDJmcwy5sOPuR9nbG+ca+3gFccltLlOPERcqkC74uPEhABjxBFwuCeSlv8AcZ/7qsjhkLD2rV5+SQlgZAKkIiCFmHWERcMeJUm/bPXNbtFgtk9NhvNo2+LQJibjZCpA5lHEjHBvgDwc/Fp3Yq4a+XalaJ61vqJGMZxtMxsqfWNOBiQCvFcHg/rajbLWCQsa73RpXpkxtcHWIuKgiNqmkHHiQ0z8YAAsvCITFL7LnDabC4Zi1IUFeffICykrbeIDkQkIFcM+N1h05J2XvizZzQqSQJrYtI7hpwB4SURPsUMMnZOBQ2C8G4mz0x/yafDeVU8jfUsmuEV/VqB8GQPXB24BTHrWPyT1Qb6CmUNF1Fzjgul2K4qI4OC75DgLof4gDUa4QHhkQpbYPxnwXETbcRCEk6aLUT/qcvxhV5PbHCYmXuQkFZAaCbZUCN3KvOIxHV9yZVLvMu7pbrZFfWKLbII7IN0QEyxRVEWwyuDlLhkXC4PXUW0dpuhXS1xyAJzLzWreaRwkAXEUVITDOSCXEIODx+tuWyV0V1xu1A3ItbrqLiDBqoGzivWAeUm+7MeKI1cPNonIpWy/qmD+GCpXnkX9Na2v7mB1ZFbQCm+XkaJ+WGzUmwTPov3rHeim0WjCTFXWjj0hB4e+q5tgaA9dHGYDfRVHDzuInTabcSo8hwFFmUhEwXZIBKBL+cipVgvFwPVwrfY2JMgufkbYQlRE55LhgKdlTDA4vTJjhN2yBmVI8RhOEXciADnecwzuZe5Ch/ee0ziXAhxNI0cVZAsN5M5obiJ2X0XcjUKWExSaM1ctN8h5mlzhviSYqrTqIukMxiQFwTPh03PkILd5gl5LdmhTAVdRMRdBOcDw8LtTzh1vNl61HlVq79Nrquc3cPNYnIpWy3qiB+Gbrahp4UIW4avjjzjYIXRVO+CpjIkurftT6GPOVReZJF/JU7zSJySVb7RGt1pKNbozMRk3GpCmQMAjYqSo+KZso8LARrRbbPj9TJ/aKsl5lCASblAjS3waRUbQ32RcJARVJcuJcHEty7tGqqEJmJHaRecPk4Or8t0q2Zhx0wbbtkRdHPI2RIy74iIqJtwUNs0UTAkRRUVTBUVF30WgjxWQjx20ytstCgAKJzkEUREq/I4vAi+Tx2U6AjHbX9MiKtn7fGFBZj2+MKYc8laFSLpkSqS7l+COiCEhWJRCnZvMAbi98akXfVstPeVVella3nVXfU3IZkS/CtXfa+ChlcrDcckxvHgnBJltSJB7Nkyzr/hZ+xp3YC6PIqtCcmxmarmUccz0dOjl0vN/5va1E/6nL8YVP2hkxaucc0l2t09AeUNiQoBrgvAcAyBex4J9bTrTRTdnZxrg6y4KKw+gLoXKaHHkCmK5XBz9oVNt321QbrHH9YbOeK+SdHMiutf+TX70sbpZmlQJsJ1EF+O4qYoJiiqmBYcAxXIfdCYjcPNonIpWy/qmD+GCpXnkX9Na2v7mB1ZFbQ9KJ+CZpbxFFGI7c2FdGecKtPA2bqdypK6BVs9s2y4hNtNOXF9BXHFXV1TK6OgIO/n1sPasuRwNmoz8kd7B+TIkPO49+eWrODSqPlcC1RzVOwVWzVPy5MK2guRihPw4TTLKr1qSHFUlTwKJuXKQ6KK5b5EWTHJd9DJ8WFw7x462it6EuofhNSCHnZ2Xcgr8Dxc2XrUeVWrv02uq5zdw81icilbLeqIH4ZurnBceBLjekGHCjZkzmJGKvGg8bIDSFmLi5iAevq8X3IqQ4UHyTWYaFekOgaIi+8DJ490NTvNInJJWzLrtqhuOnaYJGZR2lIiWMCqqqo6VVa9DwfuzPzaBpoBbabFBbbBEERFEwRERNCIm5+91bVIl7itONu4cFXY4ow4HdCINEv1g1ZSZfE5tsjNwLgyipnbcjjqxU0/xQEXBXtquV/muACRWSWM2aoiuyFFdU0KYpmIz6HW8KmtnLlYQalqw4+9cYbhakRaTfNk0IgQiUQRdcfCMaeuatqkW9x2ZDTnWq4yCMOD3SasDL6watJtvgVytsduFco6EiuA4wmrEyHHFEeANYK/NKnps59uLDjgrkiQ8SA2ACmKkRFggolXGfaWzf/e0xuLa2sFQzAUGOxwd9FMREsvbVZrUC5gt8uBFEk3lRmM62i/JraBh9sXWXbioOtGiEJCUZtCEhXQoqm+lMzrMRsQCeS4bPy9KoKASETKr1yskuQhXjtEGf9ZVhurwC29PvjUp1sNAiT0jWEg9qiloq2AFi/ejdzB1QklIVgANlRRQUUaczaDQuMFJNnwopyAdNm52k0F8GyQl1aqLiLiLjeBCRD2Y9bV5vjNvj2CfbYrkiPLhpqGycBFUGjZHBktceVviazMXAKkisEXk0yDIGWCY5creUwJU7U0QRXt+2p10kVBlQIroL0URCa6ra1szJhui6LdujRnsqouV6O0LTgFhvEJitNwnHBGTOnsCw0q8IkaQjMkTsRwHMvbD2VbWS1RcjjkJoS5yqAvESfLGtoelE/BM1svtE2GiRFKBINE65nB1rHukcd/MrZ6LcEznJKBbnExUk8nigDbhd82Djp9sRVaEFMBSztIiJoRESTIqBCigrktiywZjDYpiRLFEHSRE56k2JilHDub4RoF8jrF8odJAAHwJHGVIl0IhYG13bg7jWxzD4OXW5PNPS44kik1GZXWCponFVx1G9XjxhE62g2ldBRYe1UCIapghqCq69gva4s82XrUeVWrv02uq5zc252SxSp8A48YQktCigpA0iEiKqpvKlNRY47RsxmAFphhuW8IA2CYCAijqIIimgUSkk31o4SGoo9crtJR13Ki6cBEnXiVE4qFkHtxqPYLUimDaq5KlGiI4++SIhunh0cEER6wBEKmXKyWKVPgHGjAEloUUFIG8CRFVU3lpqLGHaNmNHAWmGW5bwgDYJgICKO4CIpoEUrj7S/fX/G0+1tss5butweJv94uG89qFbay4EZGuTOh5Ux3HLLOPyaQBa63zxFDNh5EwQsFwzAScFwMw5h7EspUcixMTXFVMqXCxOOOi4Cacpthg7l7V1rLTCXi33aUoLg07dc0ZhpFwQiFH9WA73C1Y5y7anlkPBN2huGVbhLbRdWIhxWWcyIWrFVxUiQSdLjCOUBH91zzWNMjkrttuIDmNh1UwXEcUztnvON48LtTECryuyxZbrgIotXOxumakK6VFRDK+idkLjWUu2oLbdIV+mR1JFRicLkWNmTeItdqWcR7Iq/5k2ncYl34RUYEVnE2ouZMCcUyQc7youTQORvhZSPNwGbdYYLtxmjcWHVYZRFJGxbdFS0qmhFIau8TaC3PW2S9cNa00+iIpBqQHMmCroxTCpFrbyhdoy+VWh4lwRJAIqZCXsHRVWy7Hgn1lbN3C4bOTI8KJcY7smQYjlAAcRSJVRd5ESnrK+aR5rZeUWyYqY6qQKKiZufqzRVBxOx4XGEaORZoNwB7BQSfZDN8HQxxwVGfpMmKcR5oe5pqJdoF7nNAWLbU9DjRxLezYP6plC08fjVKud4dakbSXEEaPU4k3HYRc2qElRM5GSCTpYZeCABxc7kSXanGo+0dtxFg31UWnmD0kyZChKJIXDaLLxswlx84Px7Rbr3AFwsXht4nIjmSaEJdRrWSXDruNTb94gXFx5UQPL70RsNtN446EewJARVxyMtl3FMWKO75TJIykXCXhl1sg0RCVE5wCIiAdqPZVe7rZ7BKm26R5LqZLQooFkitAWGK84xIacg22KUu7QHY8uHGBMTIg+jcEff1Tji01edobM/bodvivm07IFEQnnR1IiOCrwsjhl3tWybs/ZpFyis2wGXXmERRFxJDxKK4qmnKYrWzduuDBR5sW2xmZMdxOEBg0gkJJ7y1JvOwSNPQ31V1yxmaNONGS4qkcjwbJvfXIZtk3xQ1lDZ4jG0rMUE1bTTTcl0AFNCC24iGgCnO1Z15ftKh2iK+5nmTbiauzHMV4Si1iThOfXk1UOxWdnUW+C3q2Q31XTiRkvXGZKpmXXEXNl61HlVq79Nrquf1mXrUeVWp37rt6ztaQ63KBnkyqWXib2OK79ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9ez5+Bfr2fPwL9FO8m/1/lgveSYFjrcyrky8bjaMONX/2Q==
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.