
Phishing Analysis
Detailed analysis of captured phishing page
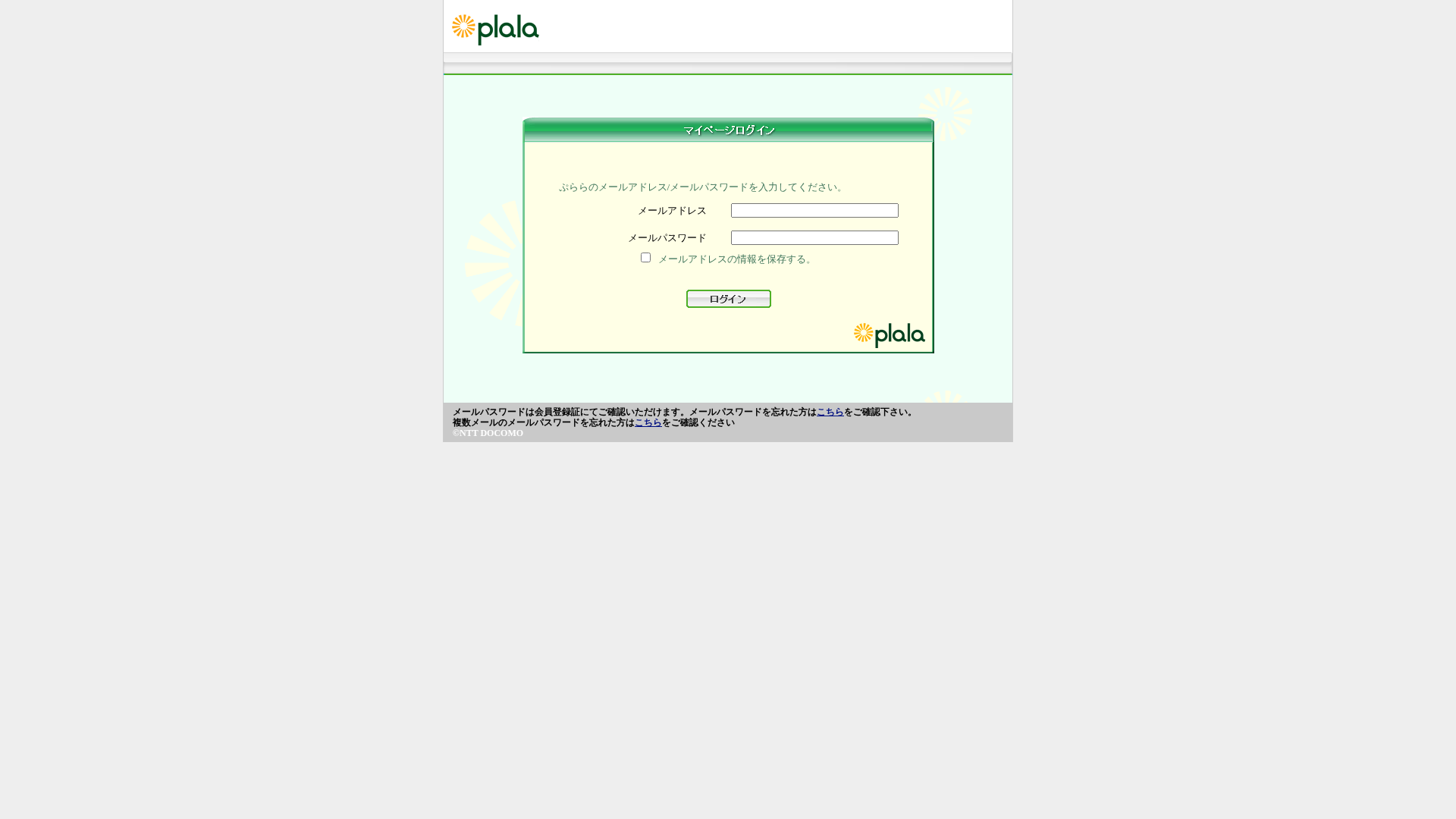
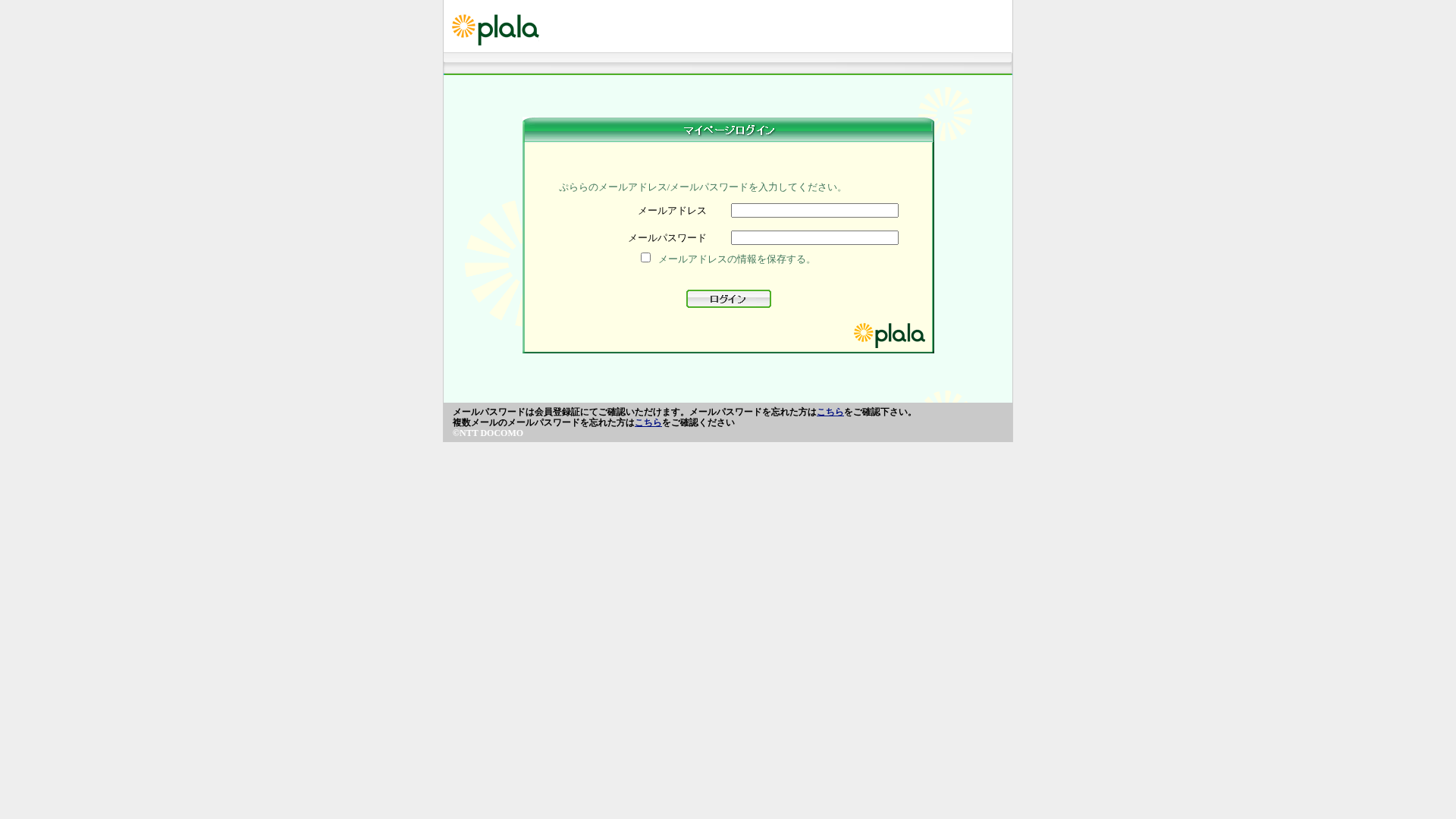
Captura Visual
Informações de Detecção
https://hyperlink.cl/checkingupdate2025/Sites/index.html
Detected Brand
plala
Country
International
Confidence
100%
HTTP Status
200
Report ID
22a11089-f98…
Analyzed
2026-01-29 22:14
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10BA1121C12853B4F999952A2D3752E94D3E1941EC7324C58A85EE72F1C8814EEC7F9FC |
|
CONTENT
ssdeep
|
96:A3ydpoIL/N+lglAtyHL5ZiNrft5CLJWfsT3yDSxyHJHAPboRbDv72oDSZHlfd5D:j2bcRM3a0QD |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b2969b3131dccc99 |
|
VISUAL
aHash
|
dfe7bdc3c3ffefff |
|
VISUAL
dHash
|
394c68049e600800 |
|
VISUAL
wHash
|
1f273f3f03130303 |
|
VISUAL
colorHash
|
07018000600 |
|
VISUAL
cropResistant
|
394c68049e600800 |
Análise de Código
Risk Score
77/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do plala
• Método: Coleta de credenciais via página de login falsa.
• Exfil: cgi-binsso/pf/agent_sso.php
• Indicadores: Incompatibilidade de domínio, javascript ofuscado.
• Risco: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- document.write
- hex_escape
- base64_strings
📤 Form Action Targets
- cgi-binsso/pf/agent_sso.php
📊 Detalhamento da Pontuação de Risco
Total Risk Score
95/100
Contributing Factors
Domain Mismatch
The domain 'hyperlink.cl' does not match the official plala domain.
Form Submission to suspicious URL
The form submits to a suspicious php file.
Javascript Obfuscation
Code obfuscation used to hide potentially malicious functionality
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
plala users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 91 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
plala
Fake Service
plala login
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker creates a fake login page that mimics the plala login. Users are tricked into entering their credentials, which are then harvested.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
hyperlink.cl
Registered
2015-08-14
Registrar
None
Status
None
🔬 JavaScript Deep Analysis
Total Code Size
2,3 KB
🔗 API Endpoints Detected
Other
1
🔐 Obfuscation Detected
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
plala
http://goldenbitesmfp.in/www.plala.or.jp/Sites/index.html
Fev 27, 2026
plala
http://sobiznet.com/ww.plala.or.jp/Sites/index.html
Fev 25, 2026
plala
https://indianplacements.co.in/www.plala.or.jp/Sites/index.h...
Fev 06, 2026
plala
https://indianplacements.co.in/www.plala.or.jp/Sites/index.h...
Fev 05, 2026
plala
https://kanodiadecor.com/mpp/Sites/index.html
Jan 27, 2026

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.