
Phishing Analysis
Detailed analysis of captured phishing page
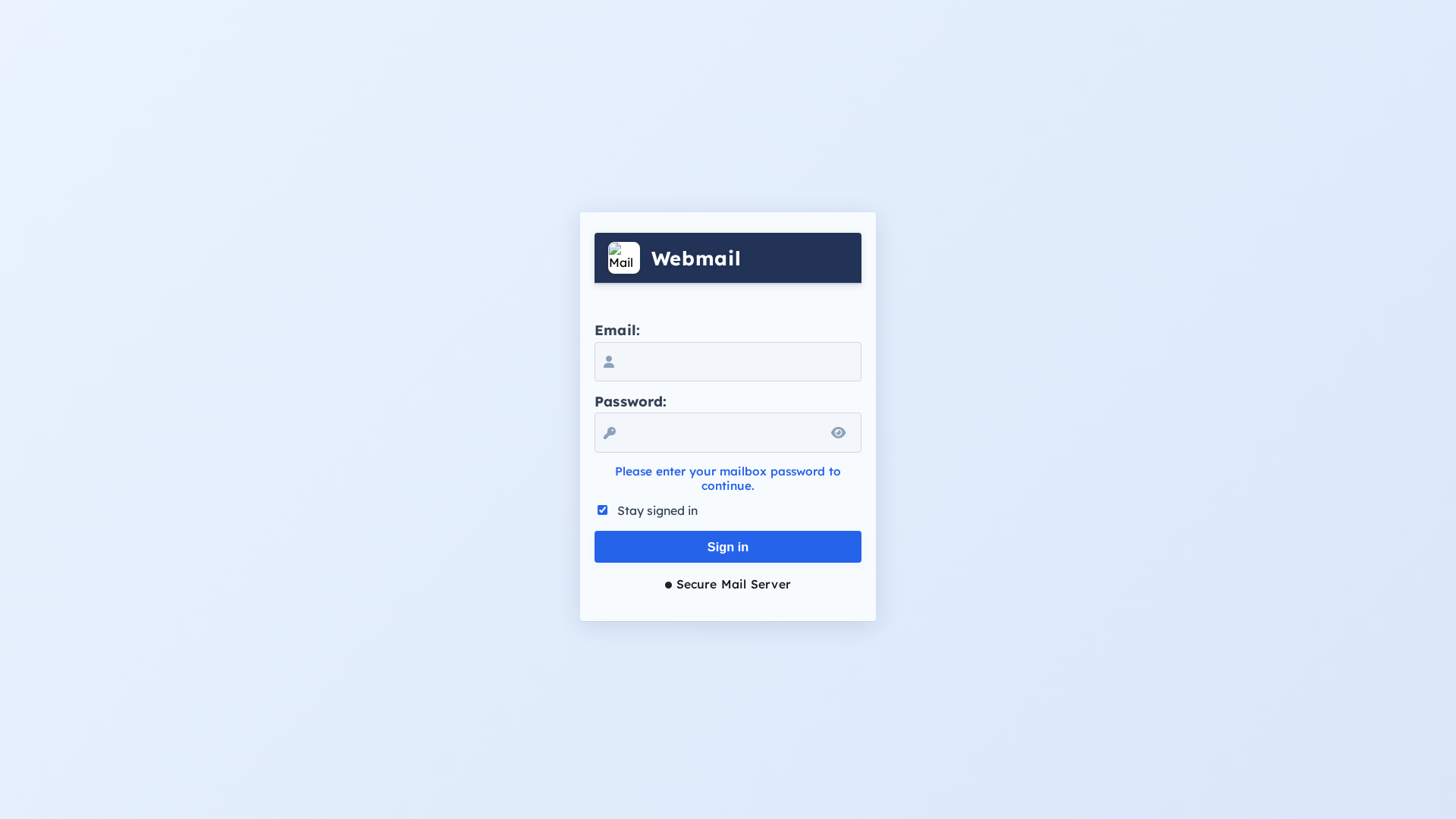
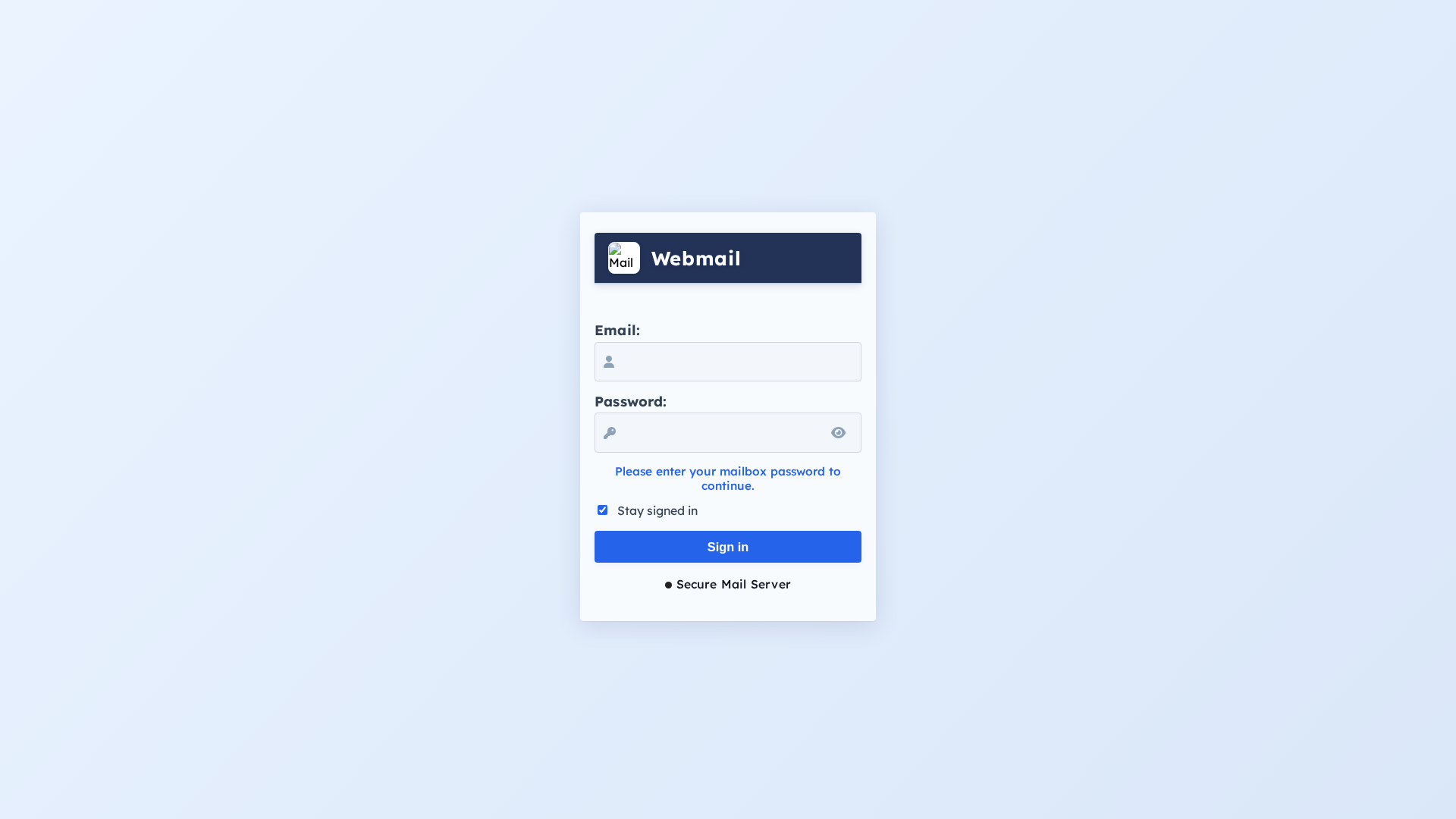
Captura Visual
Informações de Detecção
https://bafkreia5ihvxa3nwohacg5auov7n6ah5rmawhnhm5vo3cddhnmq3mdv7gq.ipfs.dweb.link
Detected Brand
Unknown
Country
International
Confidence
95%
HTTP Status
200
Report ID
257f8c7d-4fd…
Analyzed
2026-02-22 10:26
Final URL (after redirects)
https://bafkreia5ihvxa3nwohacg5auov7n6ah5rmawhnhm5vo3cddhnmq3mdv7gq.ipfs.dweb.link/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A0514471B004BC734282C6E4B2F16B1B35D7C219CF633A0467FC879E5AF6C89DA19589 |
|
CONTENT
ssdeep
|
48:nkJWhc81C9bK3uBiOylgFxIvJhh6J3ZWADMDwcnpHevk:nBJMKunjFOvvh61X4bpHes |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a6cc9999886666 |
|
VISUAL
aHash
|
fffee4f8fce4f8e0 |
|
VISUAL
dHash
|
00004c10084c3000 |
|
VISUAL
wHash
|
fcf8e0f8f8e0e0c0 |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
00004c10084c3000,d0243202642428c0 |
Análise de Código
Risk Score
65/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do Webmail
• Método: Coleta de credenciais
• Exfil: Potencialmente qualquer endpoint capaz de receber dados, especialmente com ofuscação
• Indicadores: URL de hash IPFS, formulário de login, ofuscação JavaScript
• Risco: ALTO
🔒 Obfuscation Detected
- atob
- fromCharCode
- hex_escape
- unicode_escape
- js_packer
📊 Detalhamento da Pontuação de Risco
Total Risk Score
95/100
Contributing Factors
Suspicious URL
IPFS hash is not a legitimate domain.
Login Form
Requesting sensitive login information.
Obfuscation
Code obfuscation used to hide malicious code from detection.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
General public
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 1806 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Unknown - Webmail
Fake Service
Webmail login
⚔️ Metodologia de Ataque
Primary Method: Credential harvesting
The attacker aims to steal user credentials by presenting a fake login form that mimics the appearance of a webmail service. The user enters their email and password, which is then sent to the attacker.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
bafkreia5ihvxa3nwohacg5auov7n6ah5rmawhnhm5vo3cddhnmq3mdv7gq.ipfs.dweb.link
Registered
2017-02-24
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://bafkreiegwxj3pfnc2yw57fzl7tfjmdhqqa3qczjjcretig7quyw...
Mar 19, 2026
Unknown
https://bafkreial2cuys7iusfolkwwkfnlitggozipsvdyq7lg4wo4z7tw...
Mar 16, 2026
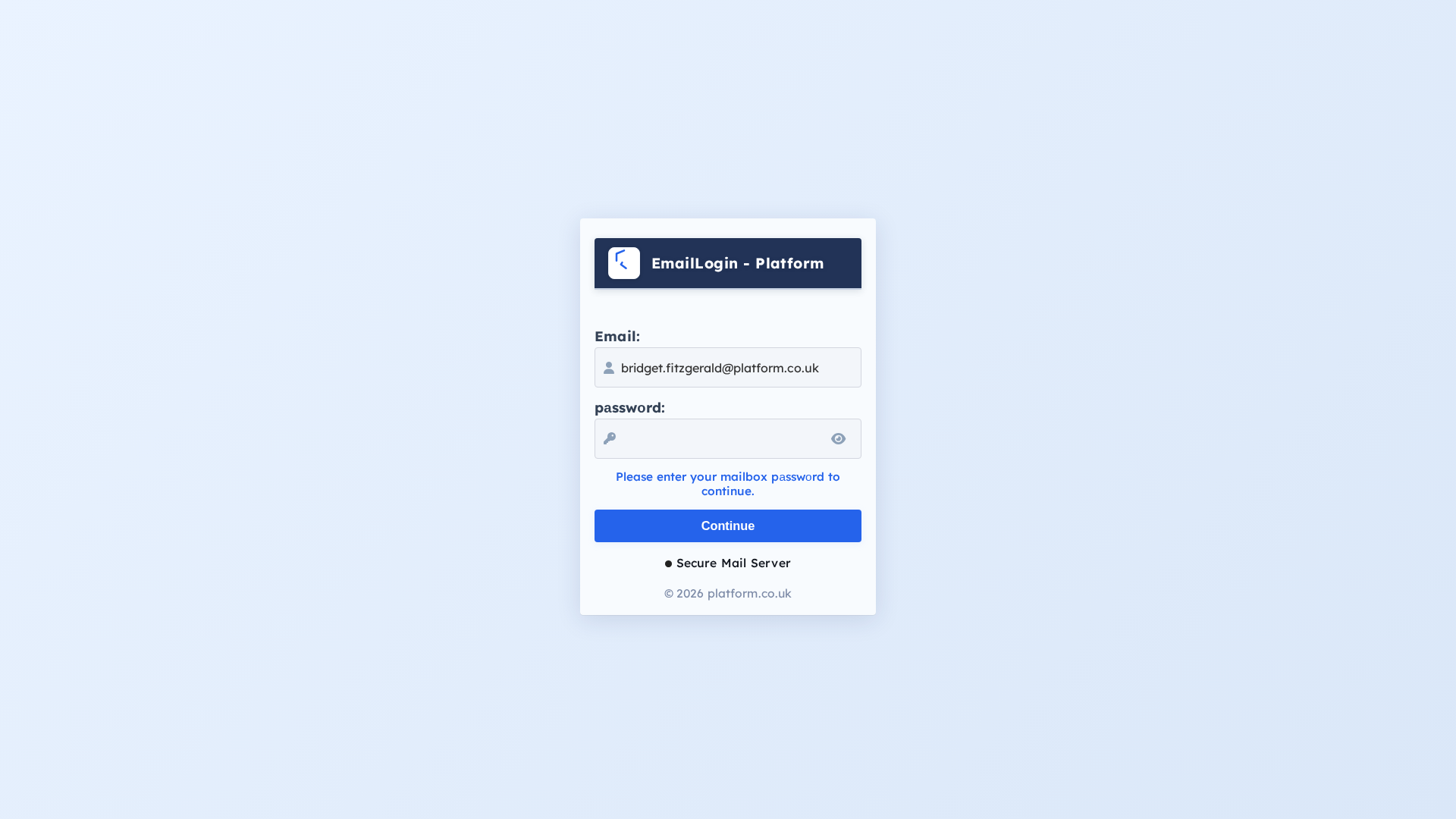
Platform.co.uk
https://bafkreietmq2owe4mmr4olp44ogax3zu5zxvomkq5cawnxu5viva...
Fev 27, 2026
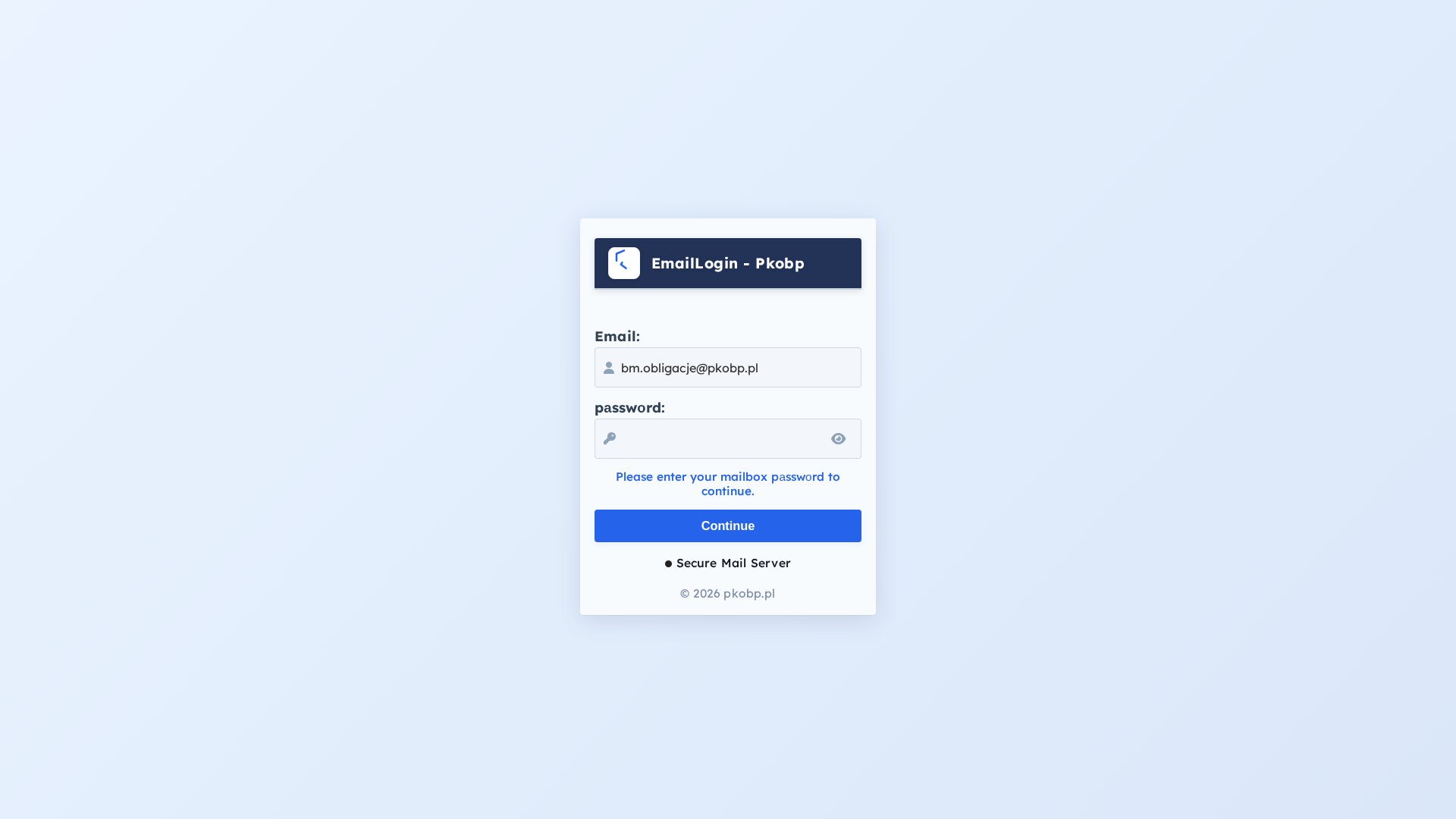
Pkobp
https://bafkreigpc2vwbbztkll32zobc4asja44hmms2qxkhvypcw4moxt...
Fev 24, 2026
Unknown
https://bafkreibrbyrcuoxifhtpqgkshrysa5uq2u332vhtmzvui7gtius...
Fev 05, 2026
Scan History for bafkreia5ihvxa3nwohacg5auov7n6ah5rmawhnhm5vo3cddhnmq3mdv7gq.ipfs.dweb.link
Found 1 other scan for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.